| File name: | 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe |
| Full analysis: | https://app.any.run/tasks/4cf8b38f-ca43-4cc2-9f91-405a91be6153 |
| Verdict: | Malicious activity |
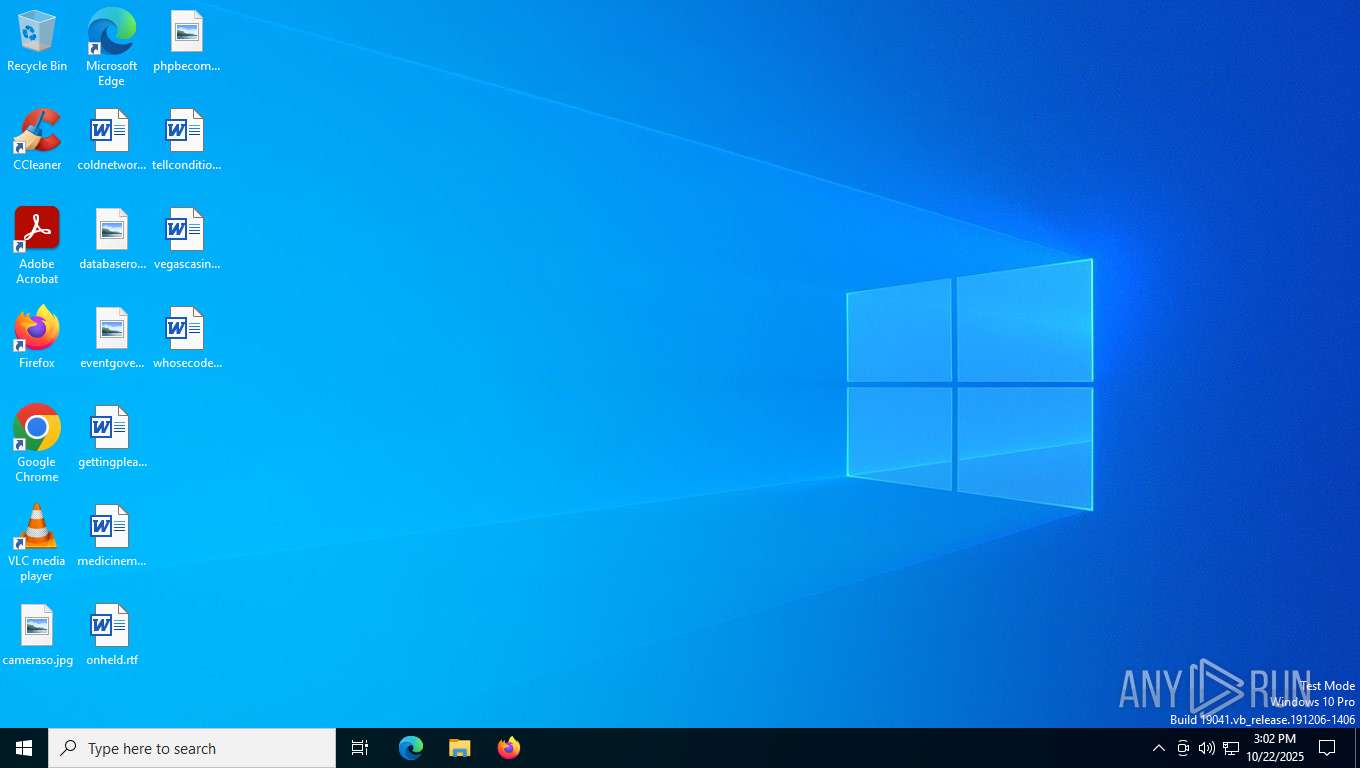
| Analysis date: | October 22, 2025, 15:02:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 12 sections |
| MD5: | 66DA00659FCF818E1CB7E6EBA6E8DFF9 |
| SHA1: | EBABE18CC8068BD58799678EC1E04251B3556EBA |
| SHA256: | 8432BA9E32EE5A8FDF84481A425CE65F808FDCDDC62207A77AF75126487956EC |
| SSDEEP: | 98304:W16qAZY/9ffduyaex2Qt3fw8YEqQOrMGQxJa/0f1TdXsT7bjq+j5Dyx2KCHWRwMn:O/twid2R |
MALICIOUS
M0YV mutex has been found
- 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe (PID: 7920)
- 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe (PID: 7948)
SUSPICIOUS
Application launched itself
- 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe (PID: 7920)
INFO
Checks supported languages
- 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe (PID: 7920)
- 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe (PID: 7948)
The sample compiled with english language support
- 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe (PID: 7920)
Reads the computer name
- 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe (PID: 7920)
- 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe (PID: 7948)
Creates files or folders in the user directory
- 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe (PID: 7948)
- 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe (PID: 7920)
Checks proxy server information
- slui.exe (PID: 7376)
Reads the software policy settings
- slui.exe (PID: 7376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:10:13 02:03:59+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 4314624 |
| InitializedDataSize: | 1571328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29b3e0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.17 |
| ProductVersionNumber: | 1.0.0.17 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | The Chromium Authors |
| FileDescription: | QuarkUpdater (x64) |
| FileVersion: | 1.0.0.17 |
| InternalName: | updater_exe |
| LegalCopyright: | Copyright 2025 The Chromium Authors. All rights reserved. |
| OriginalFileName: | updater.exe |
| ProductName: | QuarkUpdater (x64) |
| ProductVersion: | 1.0.0.17 |
| CompanyShortName: | The Chromium Authors |
| ProductShortName: | Chromium |
| LastChange: | 87ab01dc9ce9054c23408a092956b46d4ebee506 |
| OfficialBuild: | 1 |
Total processes
142
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7376 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7920 | "C:\Users\admin\Desktop\8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe" | C:\Users\admin\Desktop\8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe | explorer.exe | ||||||||||||
User: admin Company: The Chromium Authors Integrity Level: MEDIUM Description: QuarkUpdater (x64) Exit code: 9 Version: 1.0.0.17 Modules
| |||||||||||||||
| 7948 | C:\Users\admin\Desktop\8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe --crash-handler --enable-logging --vmodule=*/components/winhttp/*=1,*/components/update_client/*=2,*/chrome/updater/*=2,*/chrome/updater/quark/*=2 --database=C:\Users\admin\AppData\Local\QuarkUpdater\QuarkUpdater\1.0.0.17\Crashpad --url=https://pan-api.quark.cn/monitor/crash/collect/ --annotation=_companyName=UC --annotation=_productName=QuarkPCUpdater --annotation=_version=1.0.0.17 --annotation=app=quark-updater --annotation=app_bid= --annotation=app_channel= --annotation=bizguid= --annotation=dcheck=off --annotation=guid= --annotation=official_build=true --annotation=platform=win32 --annotation=prod=QuarkUpdater --annotation=sver= --annotation=ucVersion=251013103640 --annotation=utdid= --annotation=ver=1.0.0.17 --annotation=version=1.0.0.17 --annotation=xtm=1761145351792 --annotation=xtoken=4308c7 --initial-client-data=0x2e0,0x2e8,0x2f0,0x2ec,0x2f4,0x1404ff0a8,0x1404ff0b4,0x1404ff0c0 | C:\Users\admin\Desktop\8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe | 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe | ||||||||||||
User: admin Company: The Chromium Authors Integrity Level: MEDIUM Description: QuarkUpdater (x64) Exit code: 0 Version: 1.0.0.17 Modules
| |||||||||||||||
Total events
3 675
Read events
3 675
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7920 | 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe | C:\Users\admin\AppData\Local\QuarkUpdater\QuarkUpdater\1.0.0.17\Crashpad\settings.dat | binary | |
MD5:C98EB299D99A545FDAD932FE24B0311D | SHA256:A8664DFB9CF19F75413B7D0B9693165FE729C96D2C03CBC9EE9BB9FAC8E3A639 | |||
| 7948 | 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe | C:\Users\admin\AppData\Local\QuarkUpdater\QuarkUpdater\updater.log | text | |
MD5:59EA70C88EC12CEB4EAF8F3563646EDC | SHA256:5FAA473D6A9867BF66080F2D5966010CFD894629C520C33FA5643CB0EF09008C | |||
| 7920 | 8432ba9e32ee5a8fdf84481a425ce65f808fdcddc62207a77af75126487956ec.exe | C:\Users\admin\AppData\Roaming\26b799fa89ba8c8f.bin | binary | |
MD5:031D7C12A8FD03A027E7C8BA1D21E73E | SHA256:2BAF126B036ECB3B816ECA8E5B64BBCC669DCA0E533DCBC47A91A558995E7BE9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
52
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.27.74:443 | https://www.bing.com/dsb/scenario?name=TrendingSearchWithCache&cc=us&setlang=en-us | unknown | binary | 650 b | unknown |
— | — | GET | 200 | 2.16.27.98:443 | https://www.bing.com/AS/API/WindowsCortanaPane/V2/Suggestions?qry=&setlang=en-US&cc=US&nohs=1&qfm=1&cp=0&cvid=d78f227ba78a4992a181fb0a7816f5a0&ig=58675b63539747e587d5330cfb32391c | unknown | binary | 489 b | unknown |
692 | svchost.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
692 | svchost.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.159.4:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
— | — | POST | 200 | 20.190.160.131:443 | https://login.live.com/RST2.srf | unknown | xml | 11.2 Kb | unknown |
— | — | POST | 200 | 20.190.160.131:443 | https://login.live.com/RST2.srf | unknown | xml | 11.3 Kb | unknown |
— | — | POST | 200 | 20.190.160.131:443 | https://login.live.com/RST2.srf | unknown | xml | 11.3 Kb | unknown |
— | — | POST | 200 | 20.190.160.131:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
— | — | GET | 200 | 20.223.35.26:443 | https://arc.msn.com/v3/Delivery/Placement?pubid=da63df93-3dbc-42ae-a505-b34988683ac7&pid=310091&adm=2&w=1&h=1&wpx=1&hpx=1&fmt=json&cltp=app&dim=le&rafb=0&nct=1&pm=1&cfmt=text,image,poly&sft=jpeg,png,gif&topt=1&poptin=0&localid=w:AC7699B0-48EA-FD22-C8DC-06A02098A0F0&ctry=US&time=20251022T150225Z&lc=en-US&pl=en-US&idtp=mid&uid=9115d6d1-9f4e-4053-9297-2a8c833b3912&aid=00000000-0000-0000-0000-000000000000&ua=WindowsShellClient%2F9.0.40929.0%20%28Windows%29&asid=bd8069d5f0bb414fb4421f61035c59cf&ctmode=MultiSession&arch=x64&betaedgever=0.0.0.0&canedgever=0.0.0.0&cdm=1&cdmver=10.0.19041.3636&currsel=134045512450000000&devedgever=0.0.0.0&devfam=Windows.Desktop&devform=Unknown&devosver=10.0.19045.4046&disphorzres=1360&dispsize=47.3&dispvertres=768&fosver=16299&isu=0&lo=4272901&metered=false&nettype=ethernet&npid=sc-310091&oemName=DELL&oemid=DELL&ossku=Professional&prevosver=15063&rver=2&smBiosDm=DELL&stabedgever=133.0.3065.92&tl=2&tsu=1663431&waasBldFlt=1&waasCfgExp=1&waasCfgSet=1&waasRetail=1&waasRing=&svoffered=2 | unknown | binary | 1.34 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5812 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.27.74:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
692 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7088 | SearchApp.exe | 2.16.27.74:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
692 | svchost.exe | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4312 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |