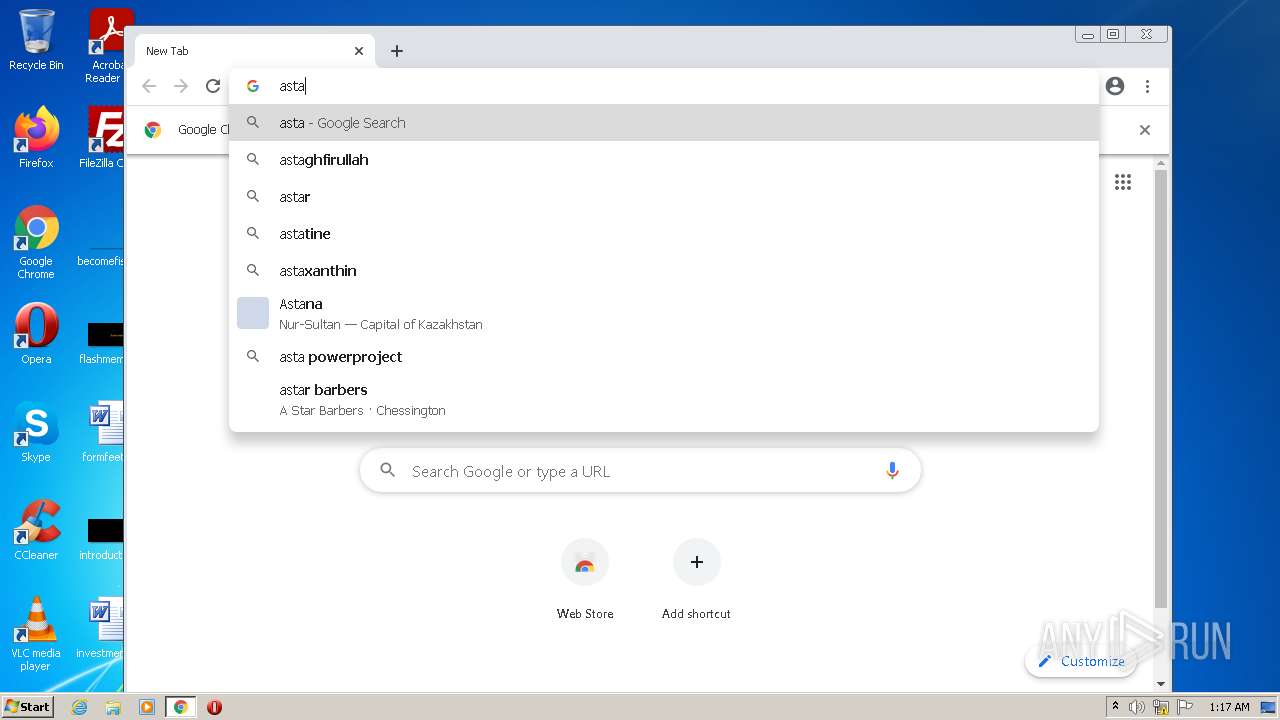
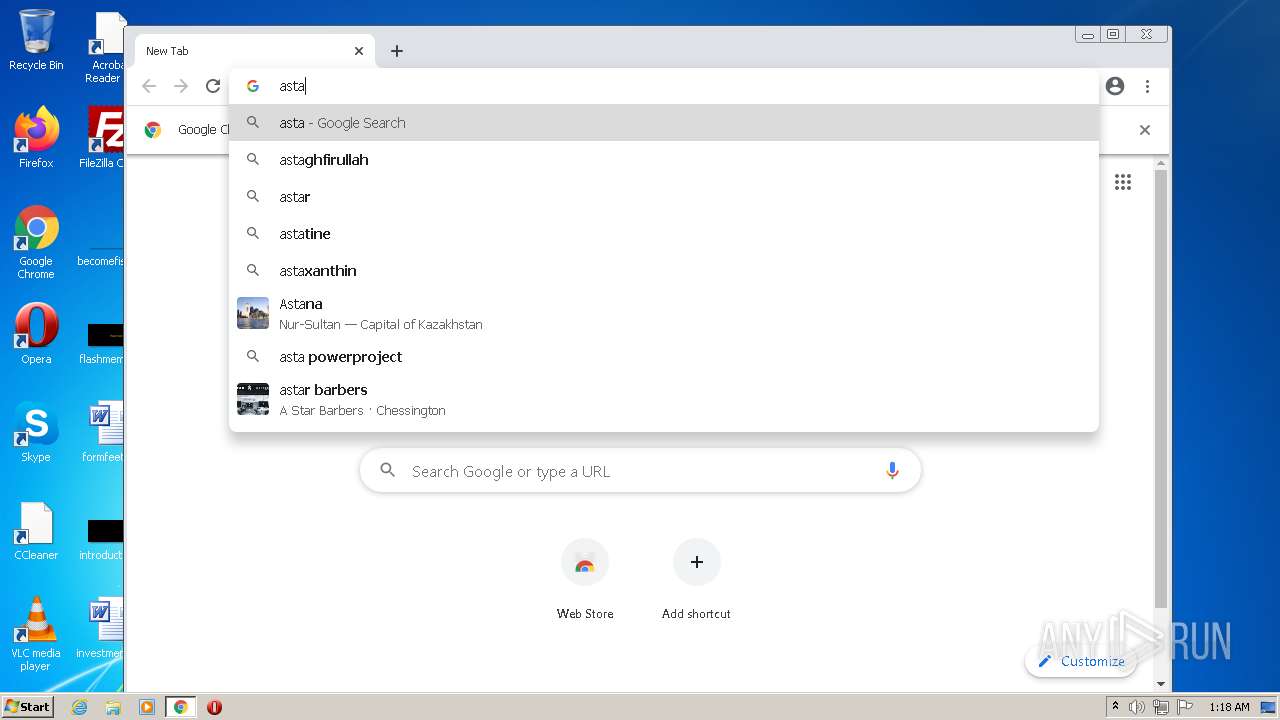
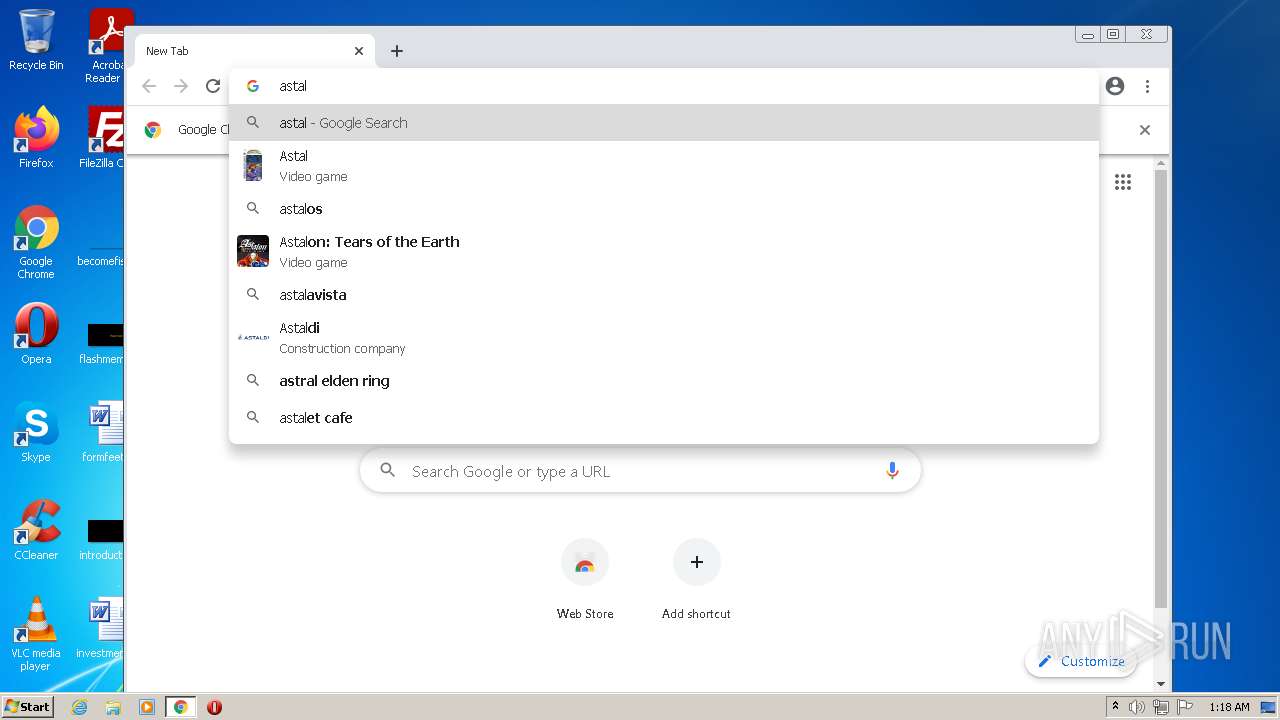
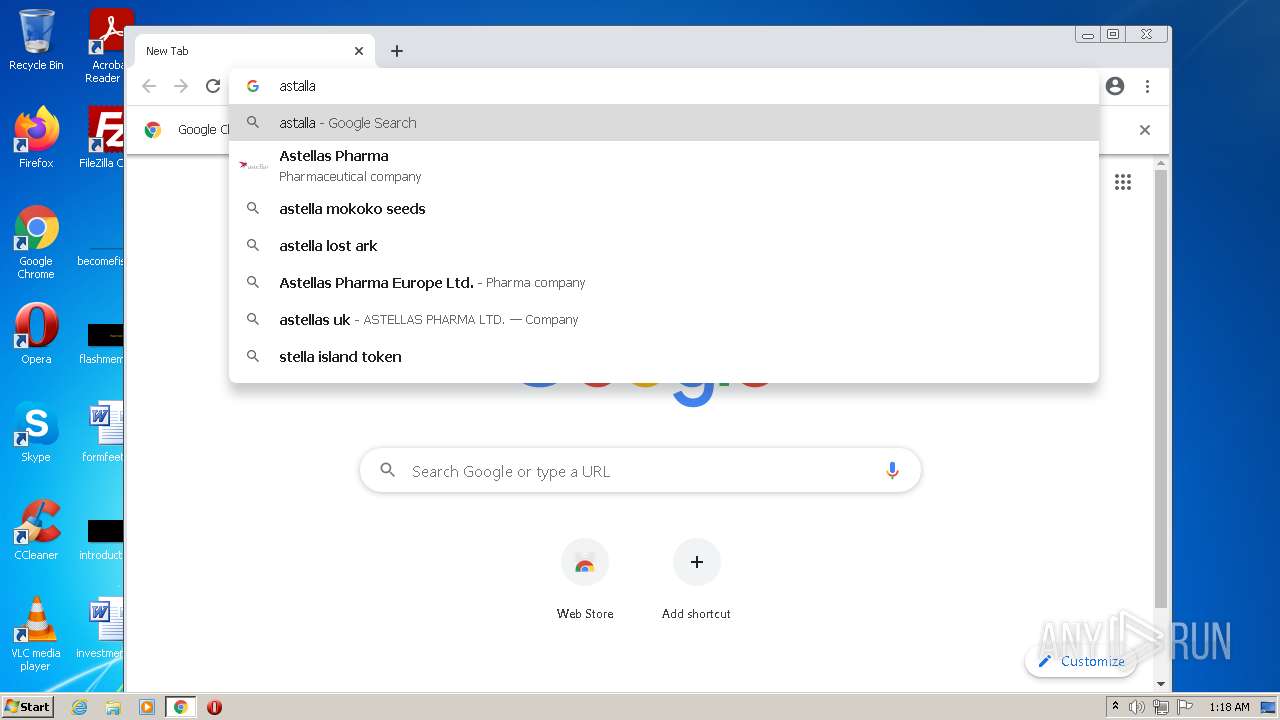
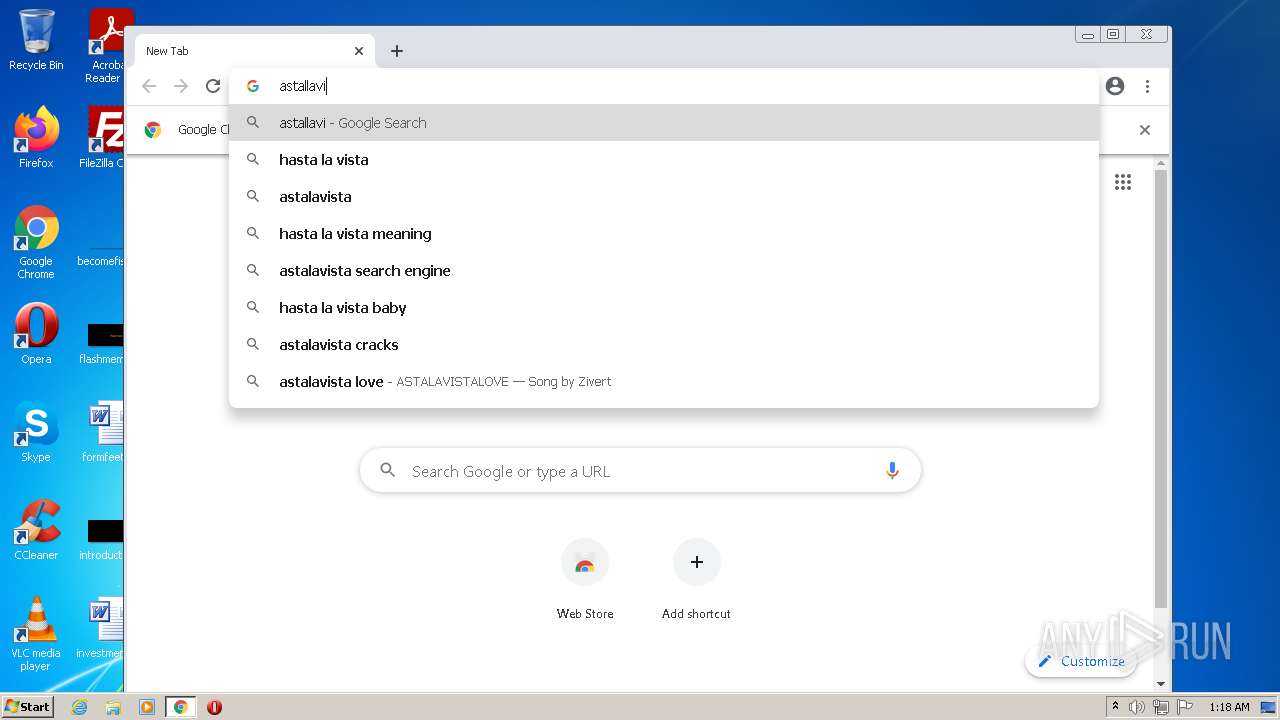
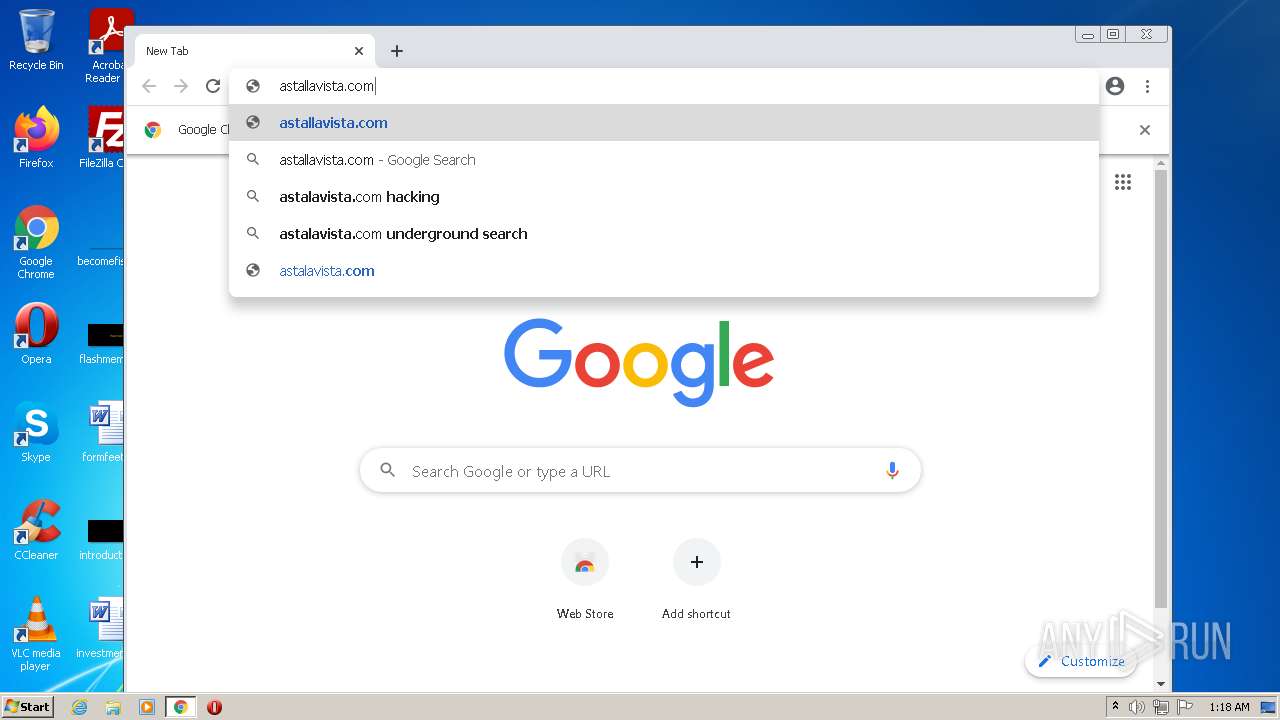
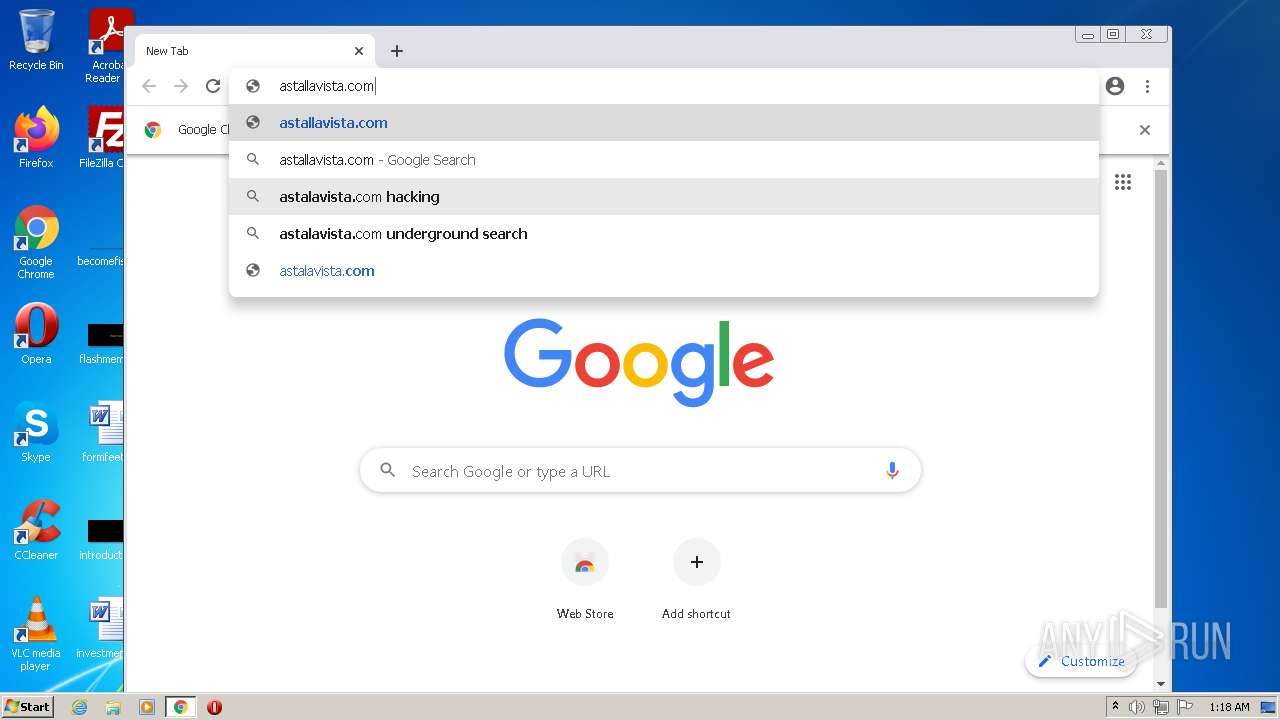
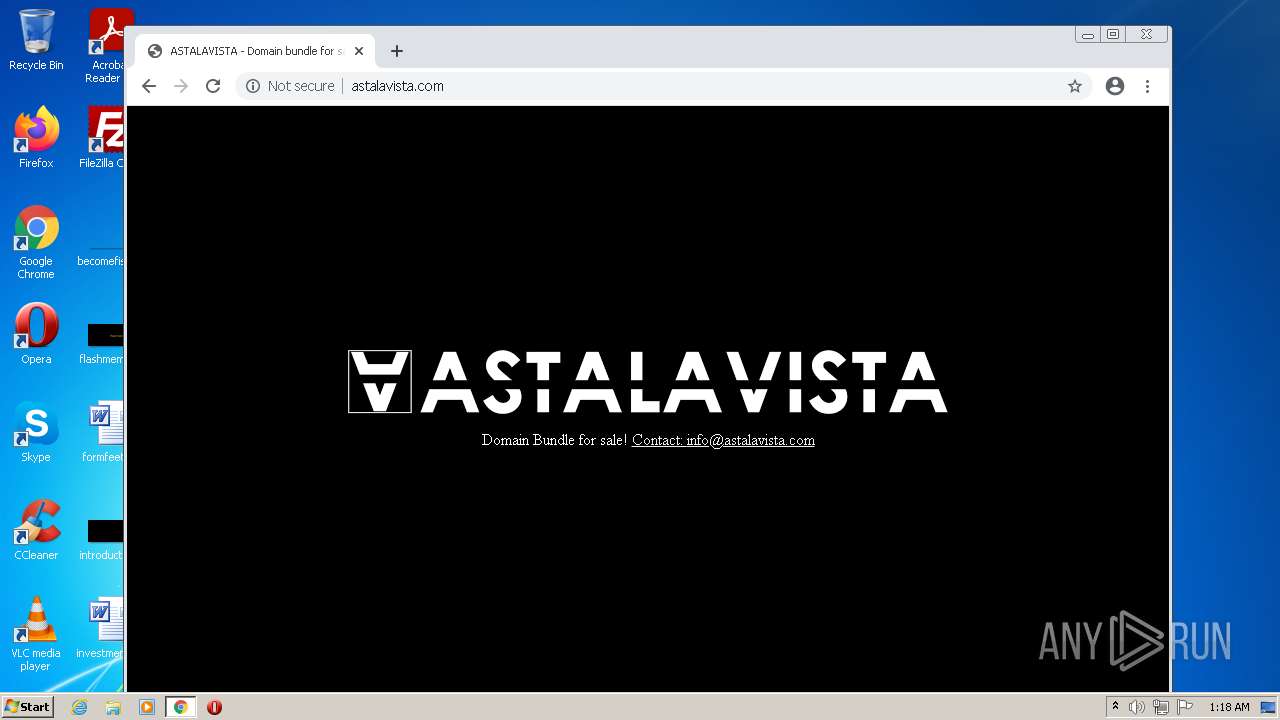
| URL: | https://Astalavista.com |
| Full analysis: | https://app.any.run/tasks/1b7c35e5-2fa9-4ec9-b477-9275acec7cc8 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 00:17:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A8428D1438102C369CFFDA851473A8E1 |
| SHA1: | B0BC2B6AFAEEE478F5D6CD1F170380A826DCCBFE |
| SHA256: | 842F73094224EBF05872E8F1EAD069CBB1E9916D8A394B0EBA41DD34CF000CB8 |
| SSDEEP: | 3:N8KV6yZIn:2k6y2 |
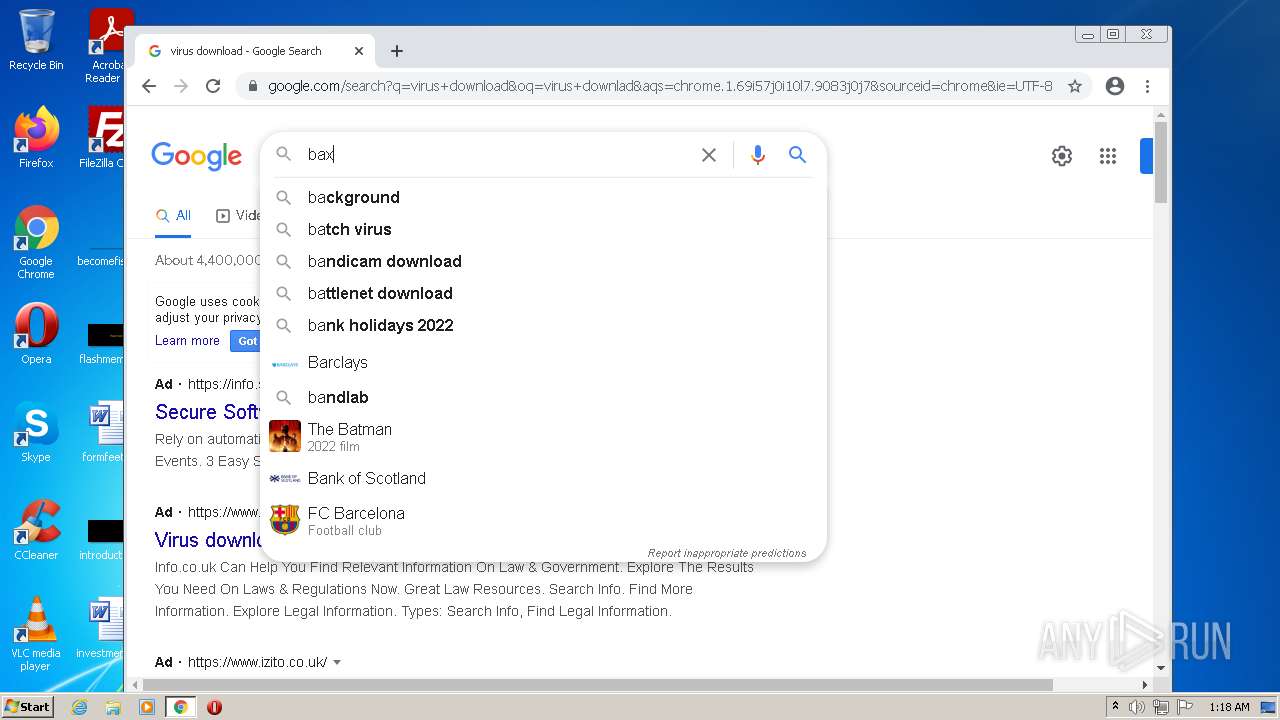
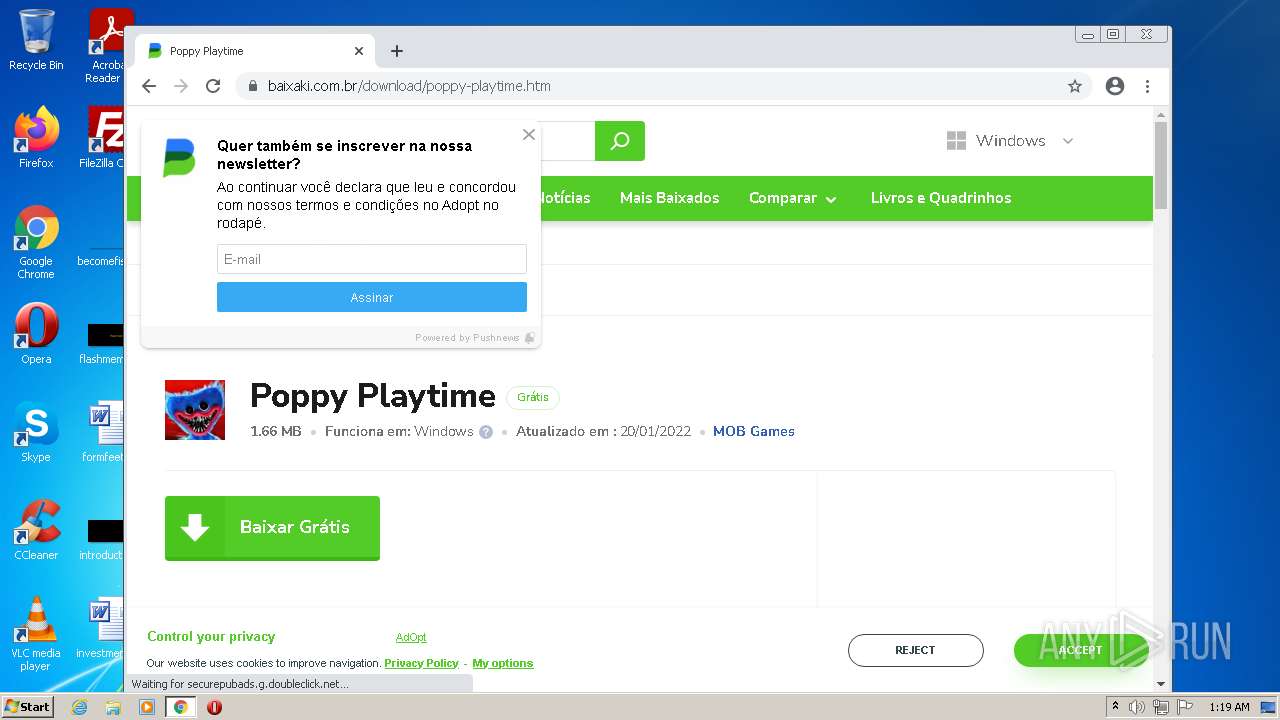
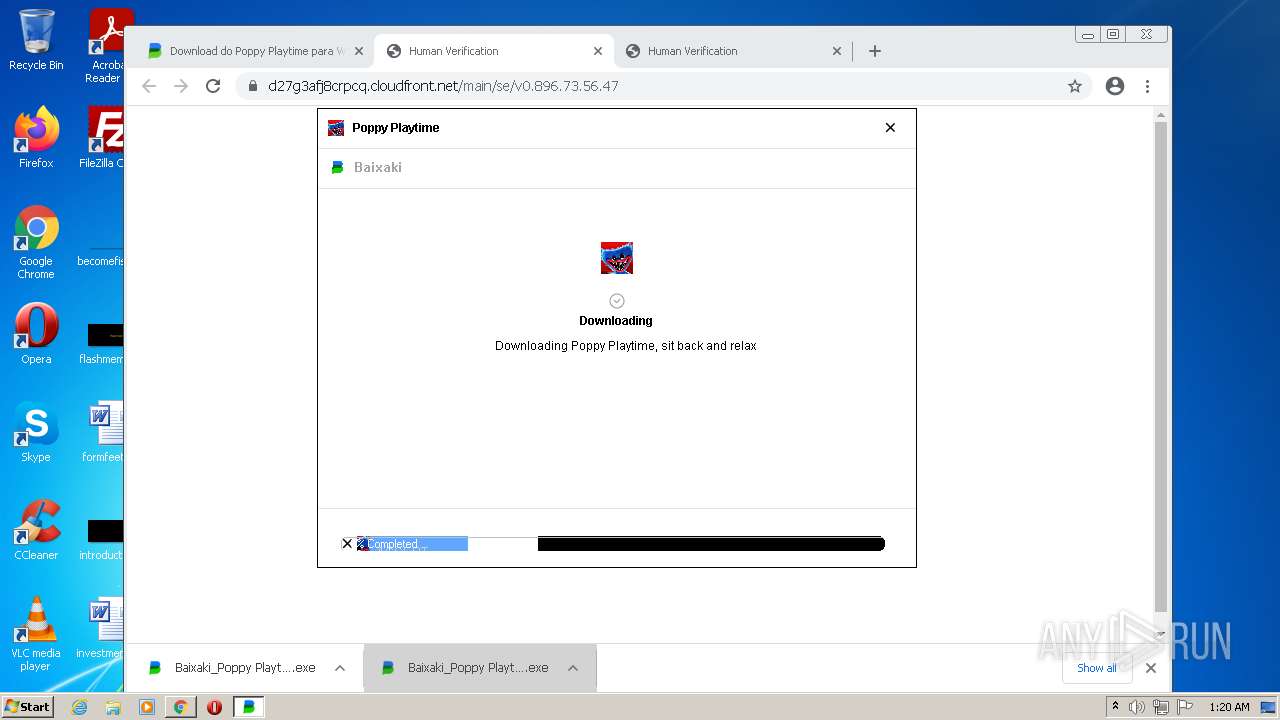
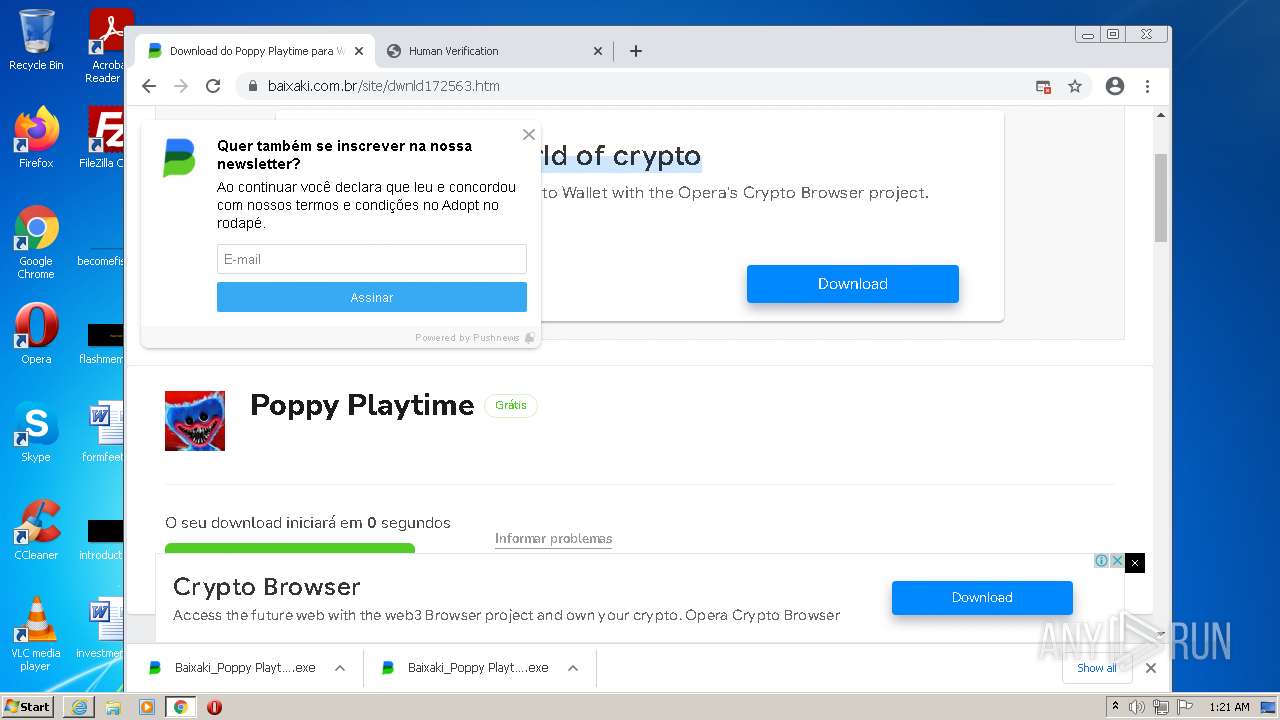
MALICIOUS
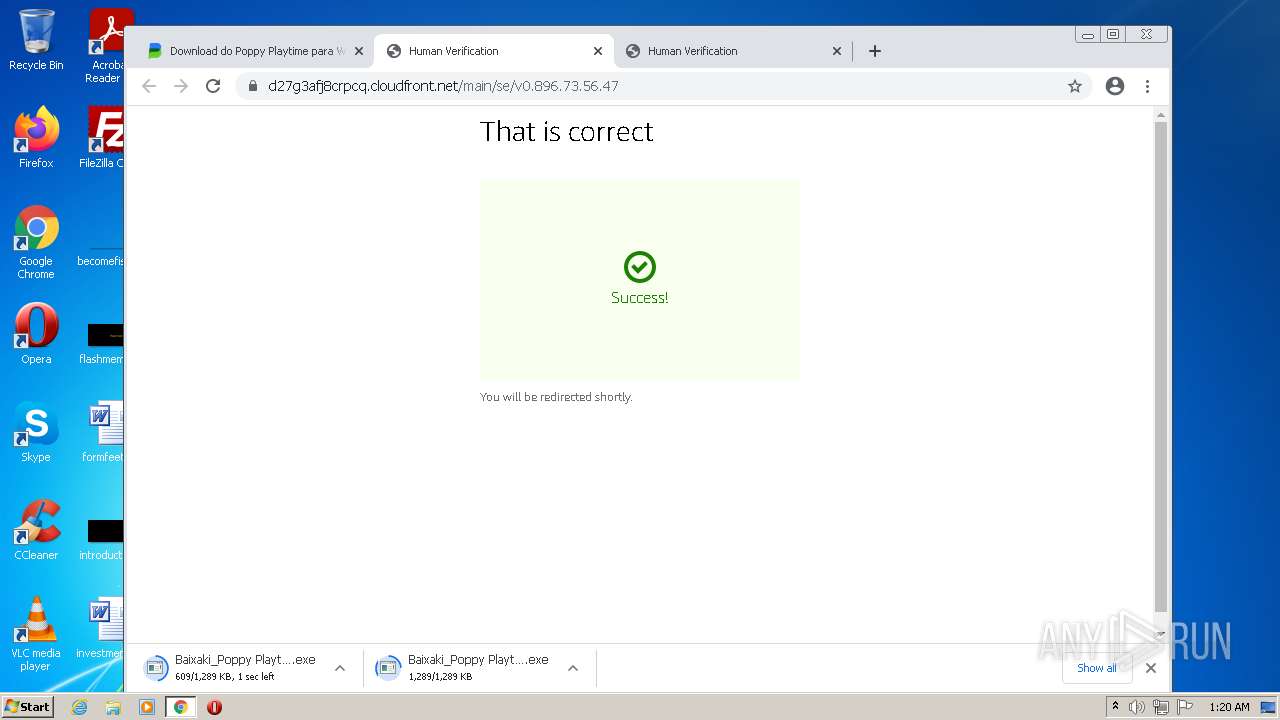
Drops executable file immediately after starts
- chrome.exe (PID: 3452)
- chrome.exe (PID: 276)
- chrome.exe (PID: 2728)
- .exe (PID: 3920)
- steamservice.exe (PID: 4016)
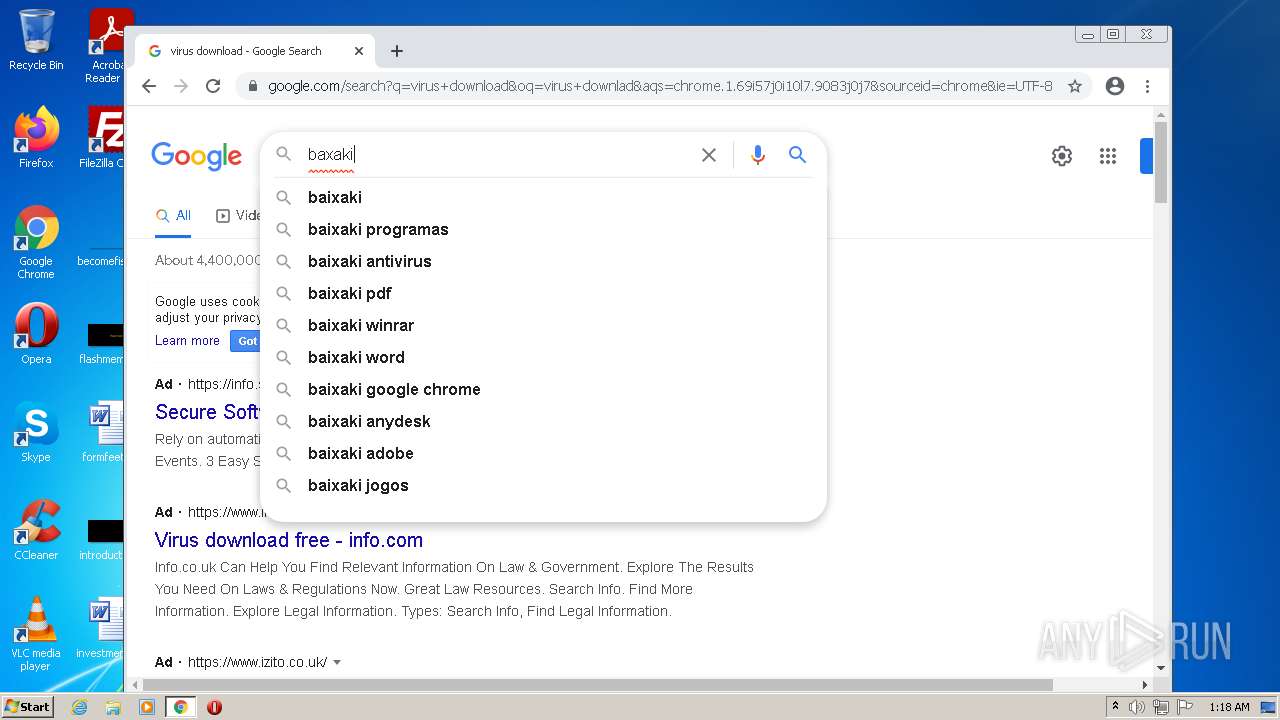
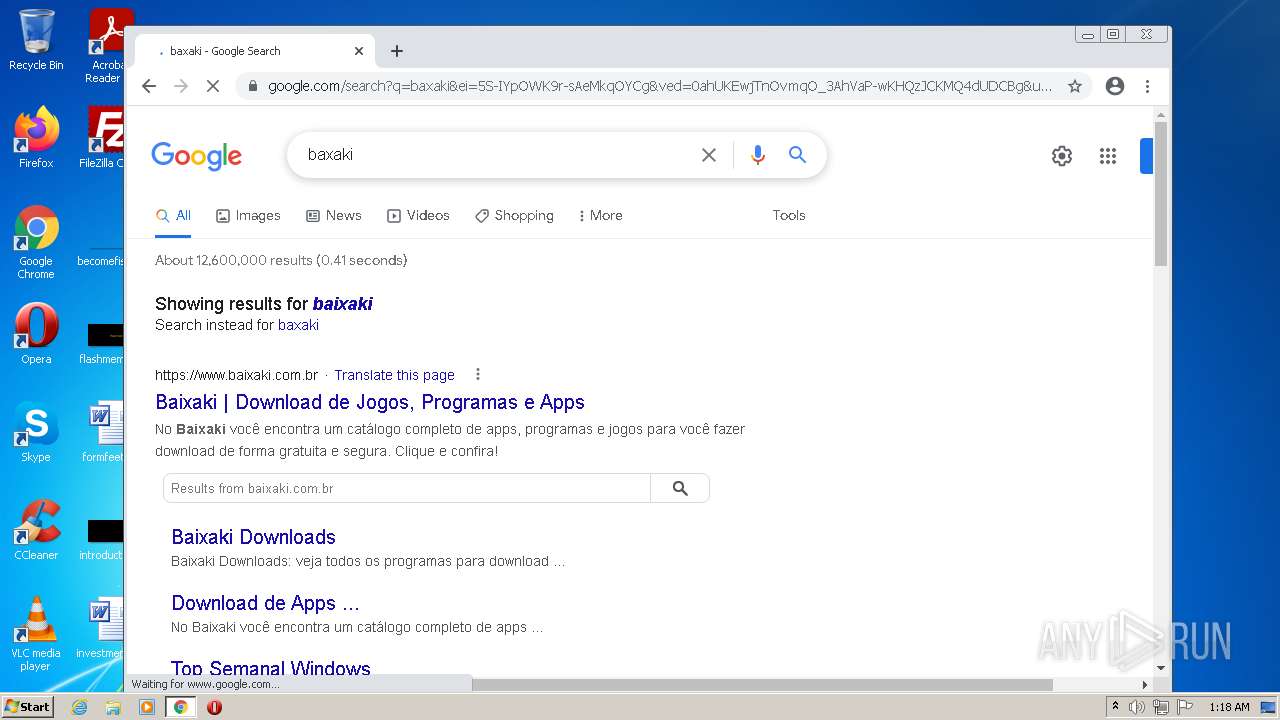
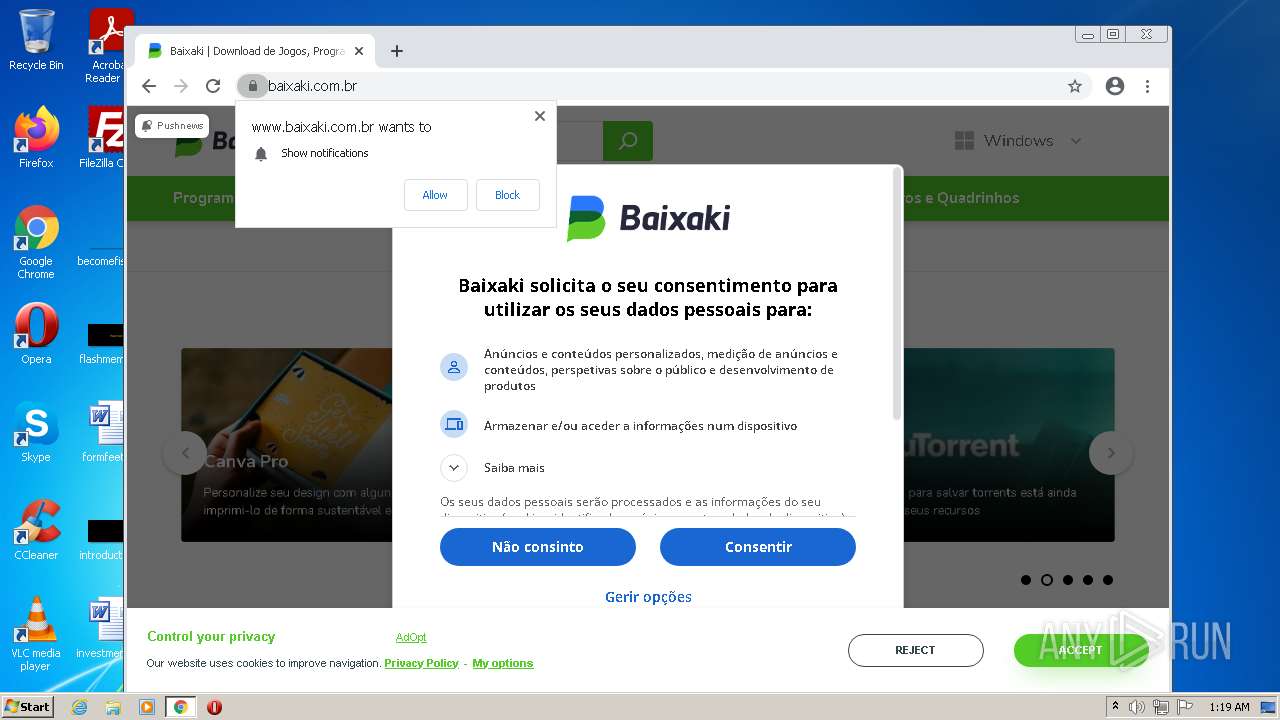
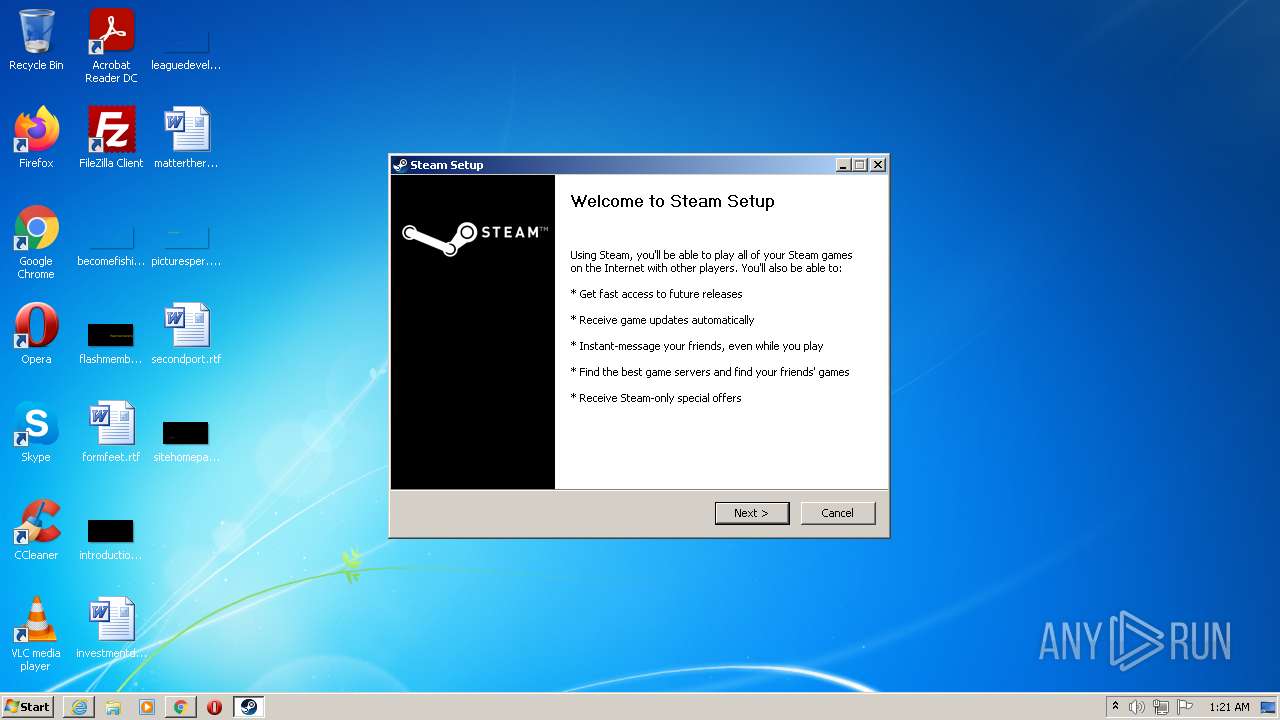
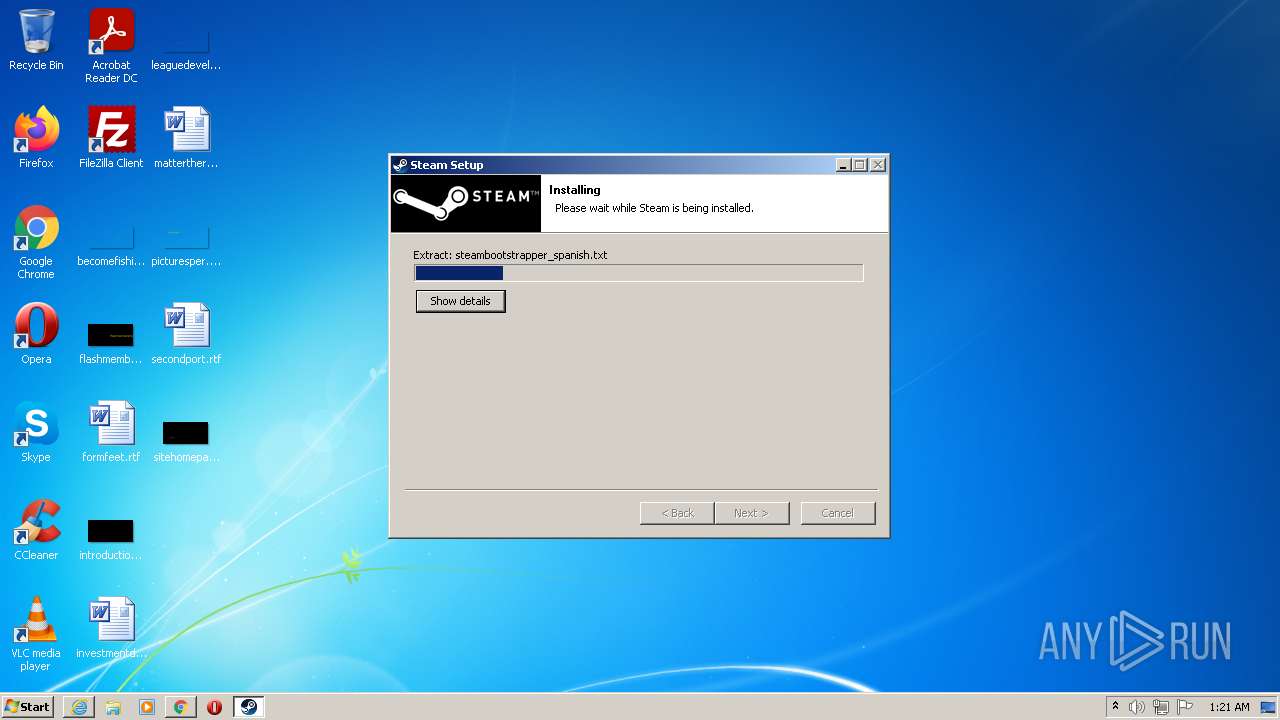
Application was dropped or rewritten from another process
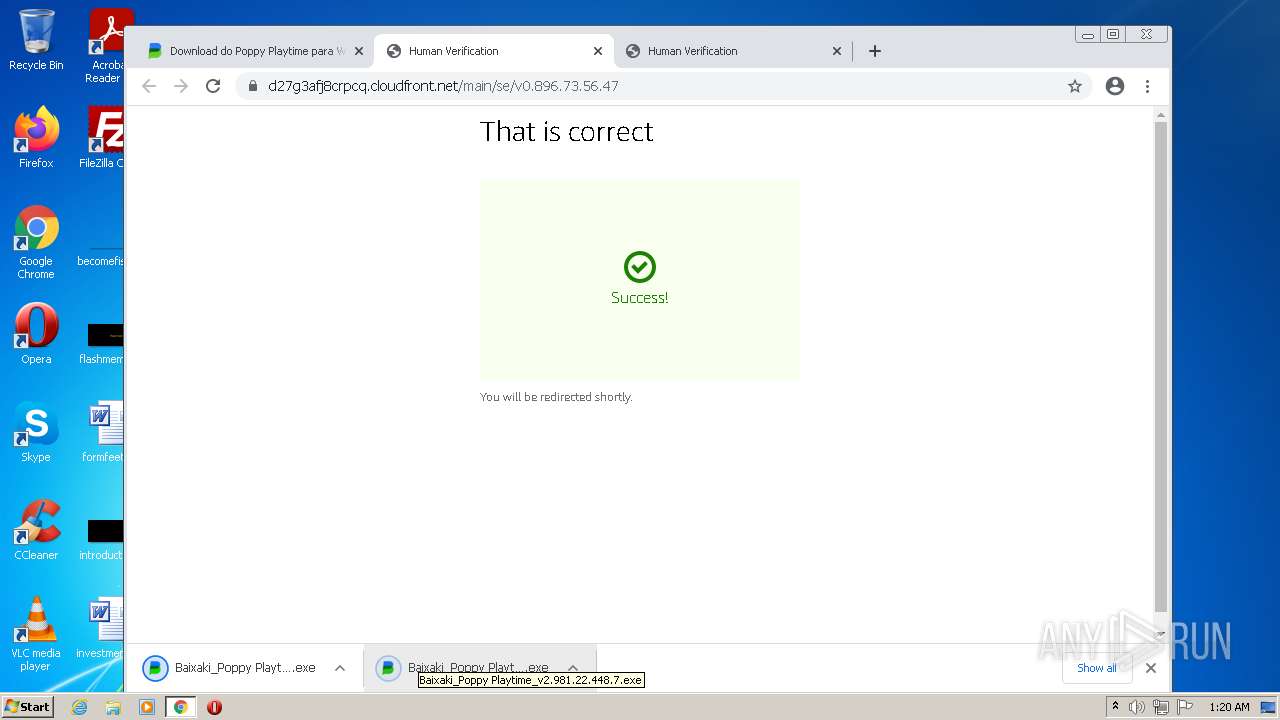
- Baixaki_Poppy Playtime_v2.981.22.448.7.exe (PID: 2980)
- Baixaki_Poppy Playtime_v2.981.22.448.7.exe (PID: 4028)
- .exe (PID: 3920)
- steamservice.exe (PID: 4016)
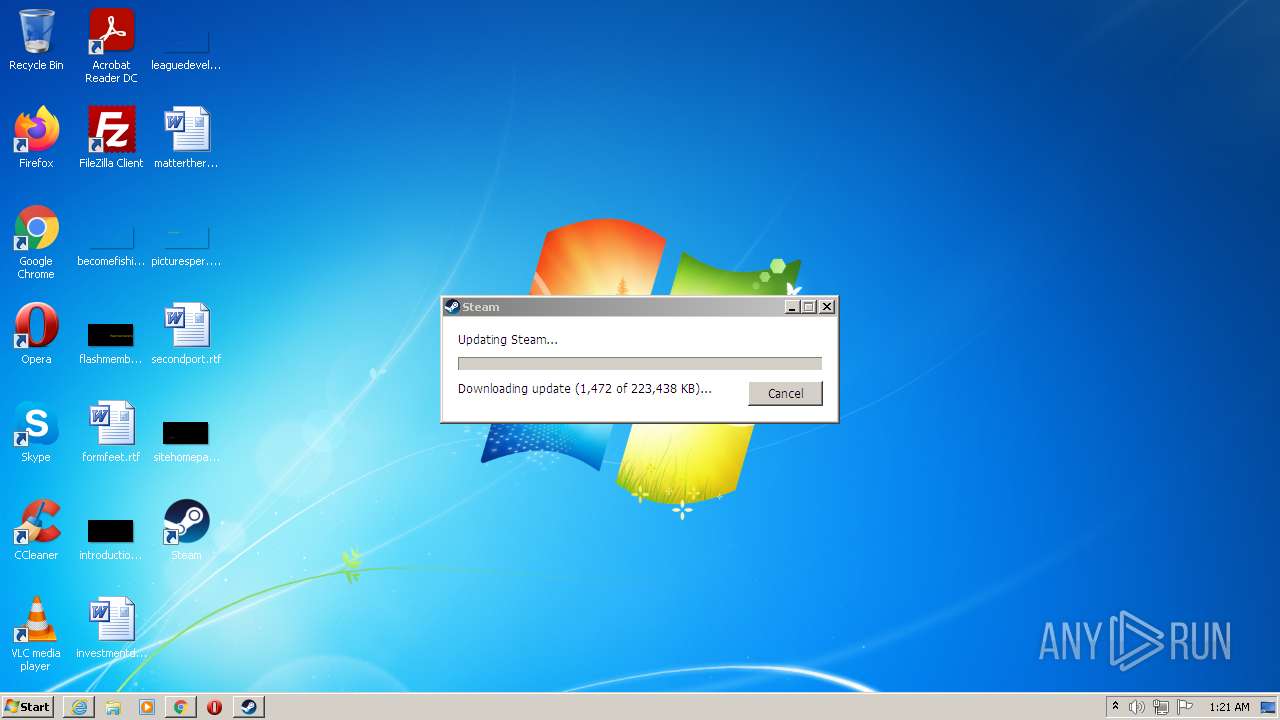
- steam.exe (PID: 932)
Changes settings of System certificates
- Baixaki_Poppy Playtime_v2.981.22.448.7.exe (PID: 2980)
Loads dropped or rewritten executable
- .exe (PID: 3920)
Changes the autorun value in the registry
- .exe (PID: 3920)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 276)
Drops a file with a compile date too recent
- chrome.exe (PID: 3452)
- chrome.exe (PID: 276)
- chrome.exe (PID: 2728)
- .exe (PID: 3920)
- steamservice.exe (PID: 4016)
Executable content was dropped or overwritten
- chrome.exe (PID: 3452)
- chrome.exe (PID: 276)
- chrome.exe (PID: 2728)
- .exe (PID: 3920)
- steamservice.exe (PID: 4016)
Reads Environment values
- Baixaki_Poppy Playtime_v2.981.22.448.7.exe (PID: 2980)
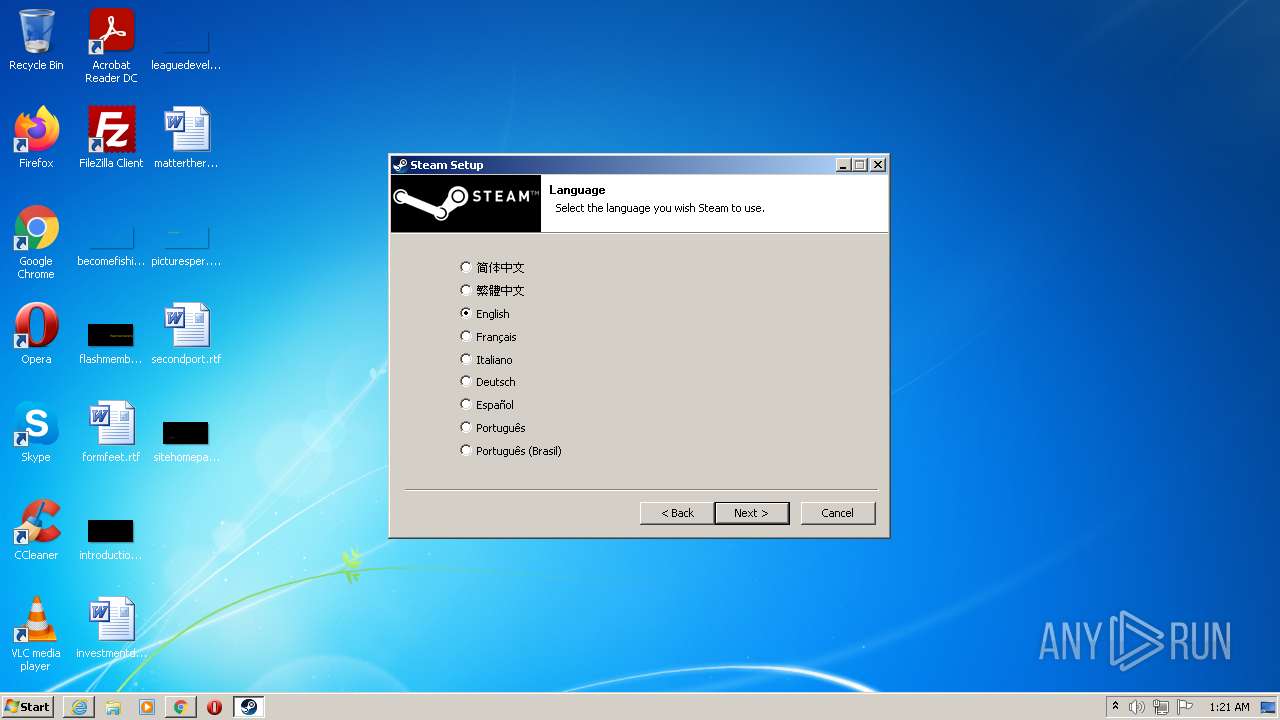
Checks supported languages
- Baixaki_Poppy Playtime_v2.981.22.448.7.exe (PID: 2980)
- .exe (PID: 3920)
- steamservice.exe (PID: 4016)
- ns9DBD.tmp (PID: 4028)
- steam.exe (PID: 932)
Reads the computer name
- Baixaki_Poppy Playtime_v2.981.22.448.7.exe (PID: 2980)
- .exe (PID: 3920)
- steamservice.exe (PID: 4016)
- steam.exe (PID: 932)
Adds / modifies Windows certificates
- Baixaki_Poppy Playtime_v2.981.22.448.7.exe (PID: 2980)
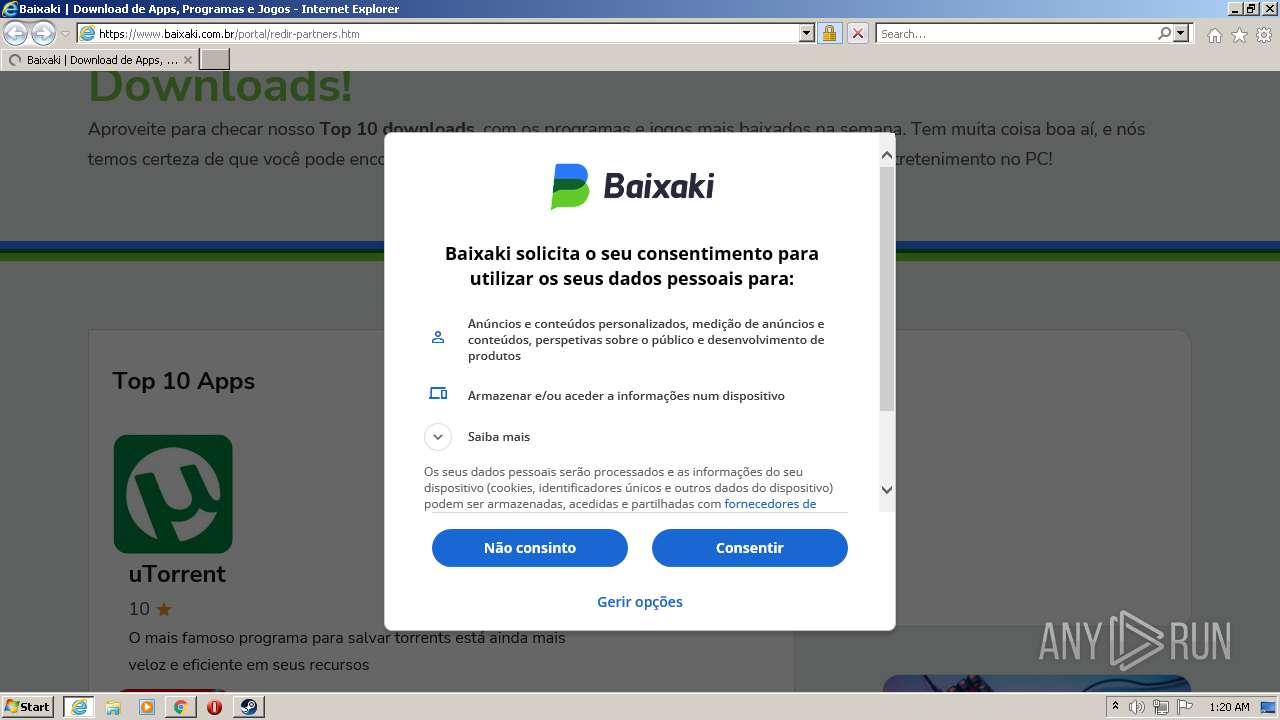
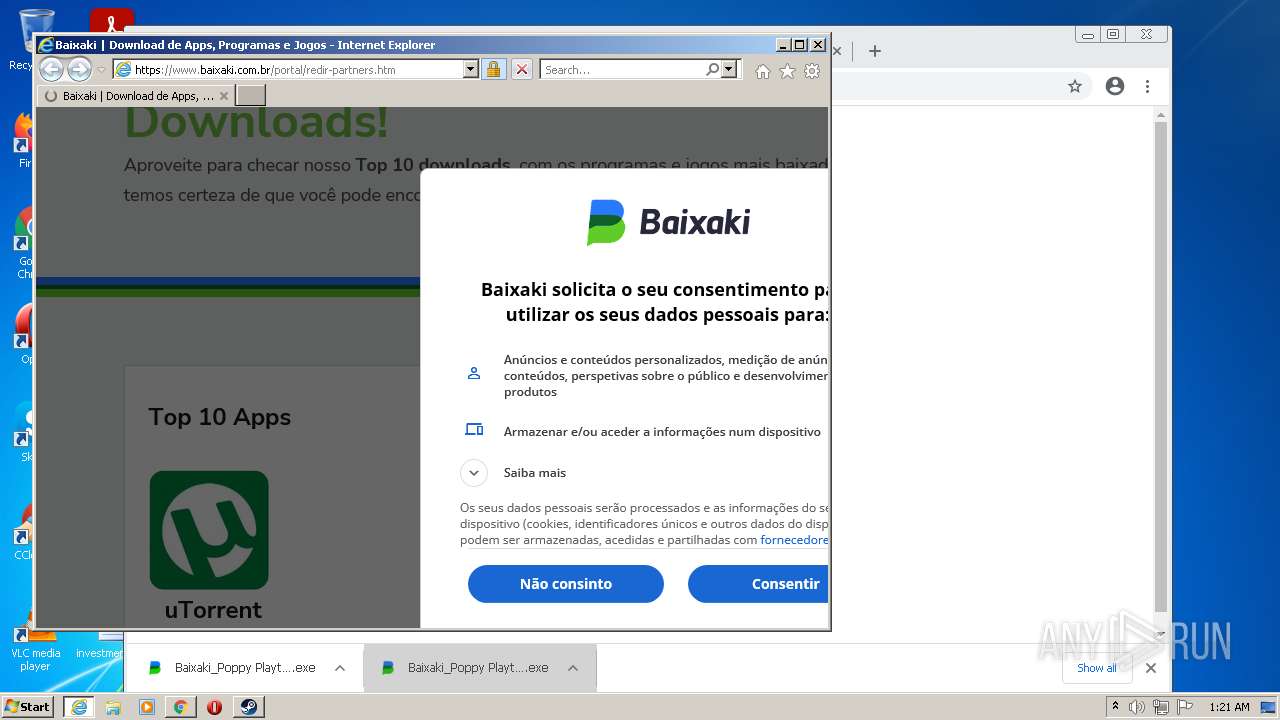
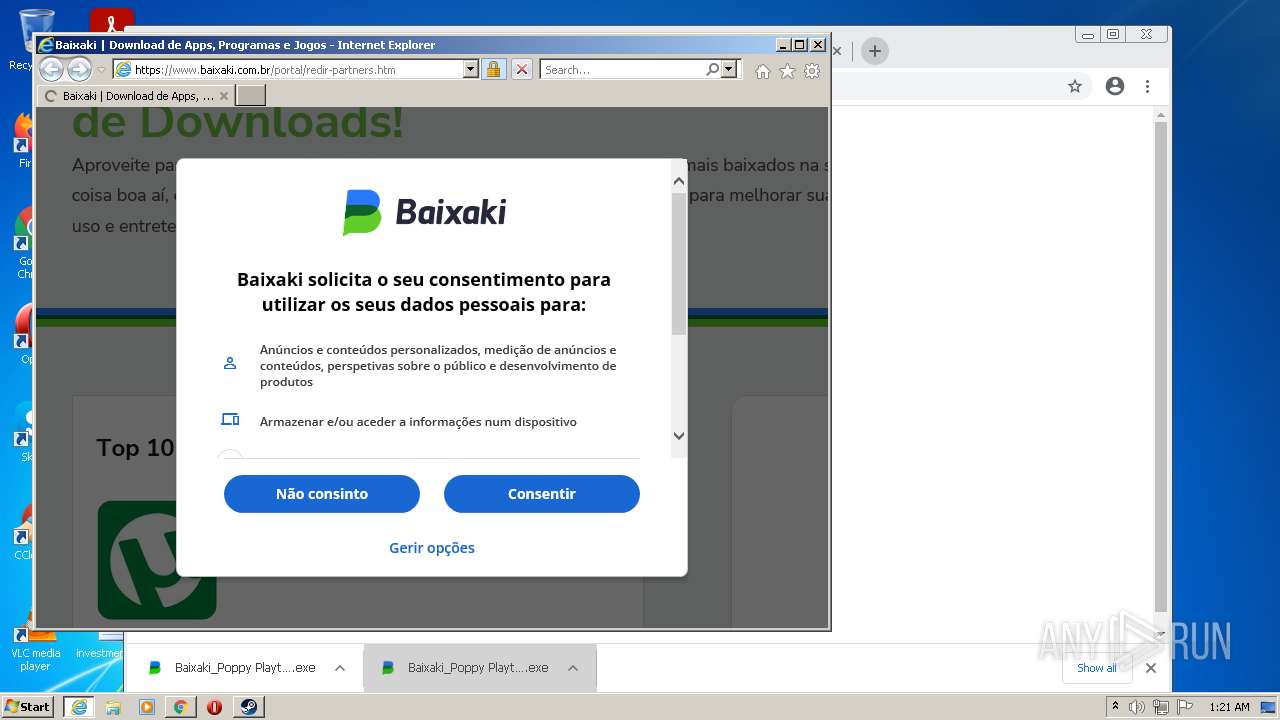
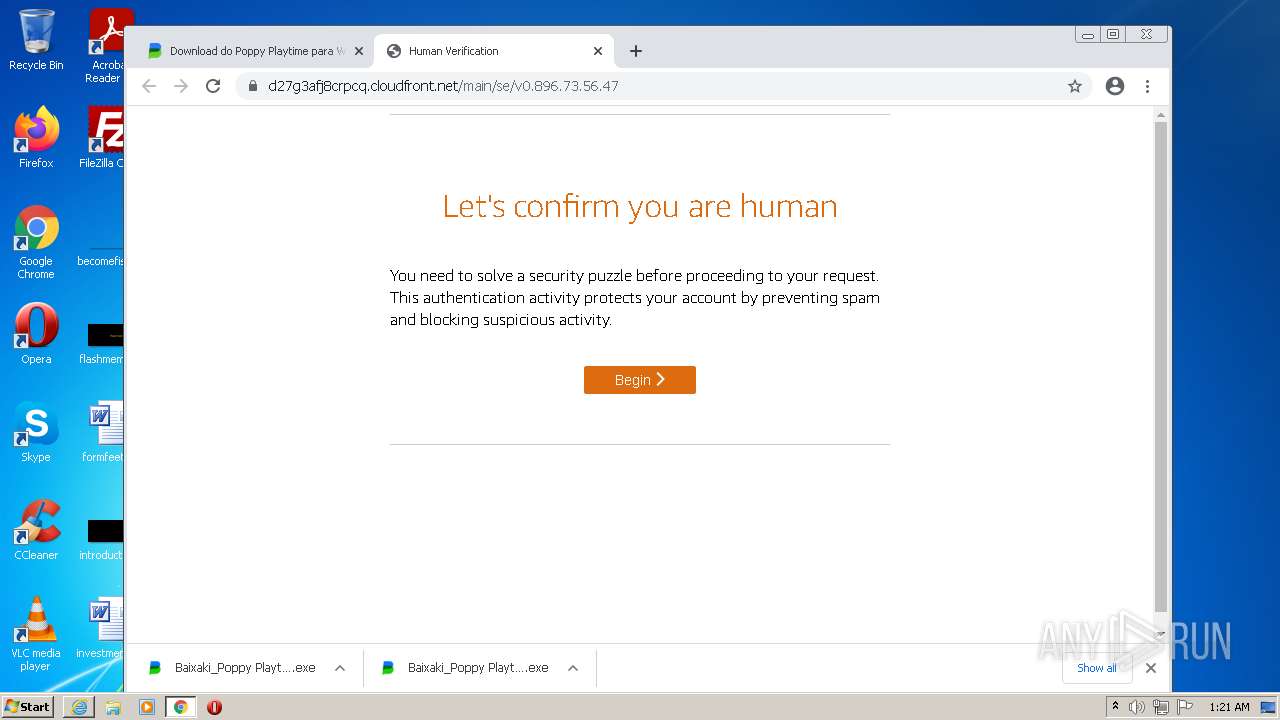
Starts Internet Explorer
- Baixaki_Poppy Playtime_v2.981.22.448.7.exe (PID: 2980)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3612)
Creates a directory in Program Files
- .exe (PID: 3920)
- steamservice.exe (PID: 4016)
- steam.exe (PID: 932)
Creates files in the program directory
- .exe (PID: 3920)
- steamservice.exe (PID: 4016)
- steam.exe (PID: 932)
Starts application with an unusual extension
- .exe (PID: 3920)
Changes default file association
- steamservice.exe (PID: 4016)
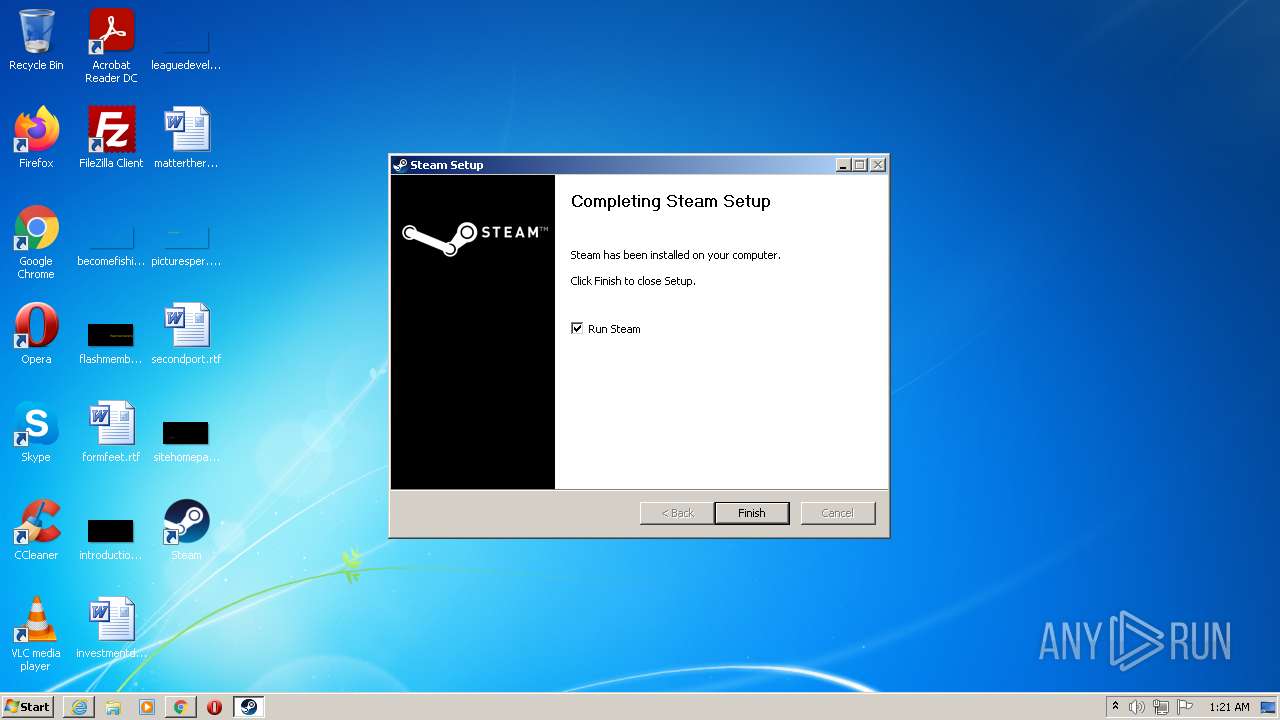
Creates a software uninstall entry
- .exe (PID: 3920)
Reads CPU info
- steam.exe (PID: 932)
INFO
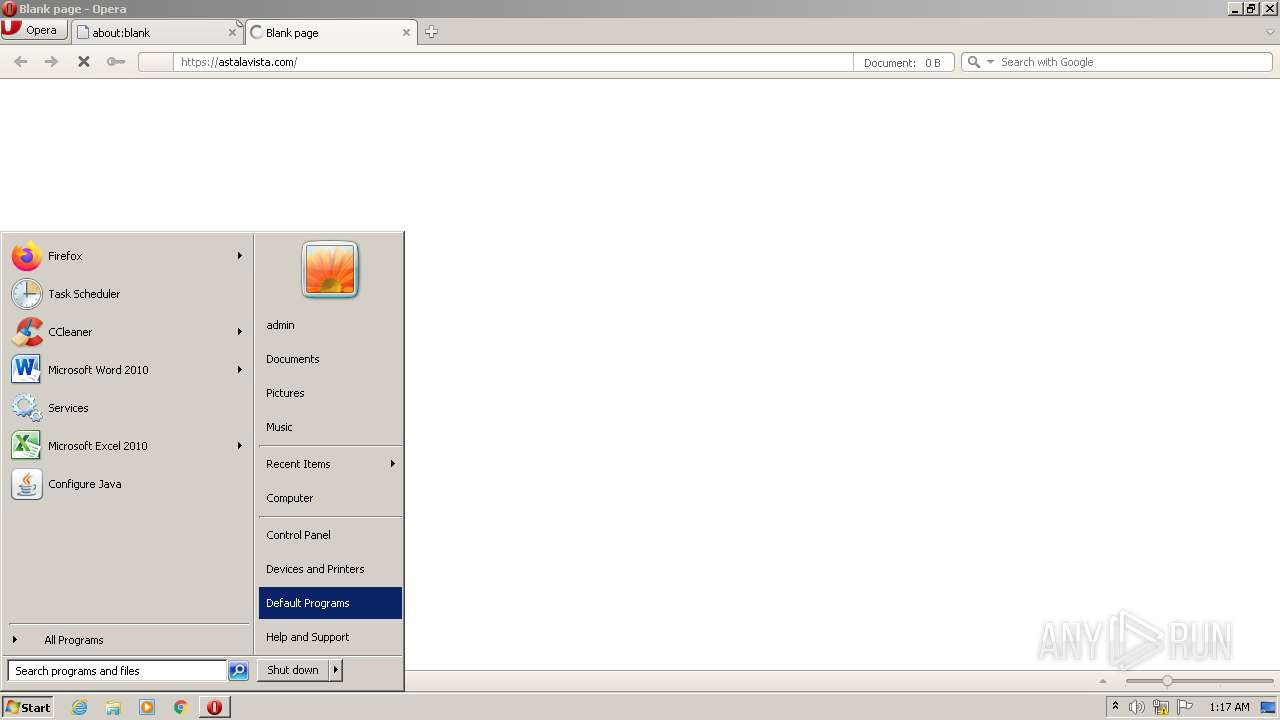
Check for Java to be installed
- opera.exe (PID: 1364)
Reads the computer name
- opera.exe (PID: 1364)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 276)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 1012)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 280)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 1892)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 448)
- chrome.exe (PID: 2900)
- iexplore.exe (PID: 2152)
- iexplore.exe (PID: 3612)
- chrome.exe (PID: 1068)
Checks supported languages
- chrome.exe (PID: 960)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 3380)
- opera.exe (PID: 1364)
- chrome.exe (PID: 276)
- chrome.exe (PID: 3912)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 2284)
- chrome.exe (PID: 2620)
- chrome.exe (PID: 2716)
- chrome.exe (PID: 1180)
- chrome.exe (PID: 1836)
- chrome.exe (PID: 1868)
- chrome.exe (PID: 1252)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 996)
- chrome.exe (PID: 964)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 2936)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 3772)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 1012)
- chrome.exe (PID: 1800)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 3664)
- chrome.exe (PID: 1592)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 116)
- chrome.exe (PID: 660)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 848)
- chrome.exe (PID: 1600)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 616)
- chrome.exe (PID: 764)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 532)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 2312)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 2876)
- chrome.exe (PID: 3436)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 996)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 1664)
- chrome.exe (PID: 388)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 2692)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 1224)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 280)
- chrome.exe (PID: 448)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 3876)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 1396)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 1892)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2264)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 1792)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 4084)
- chrome.exe (PID: 3956)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 3368)
- chrome.exe (PID: 1012)
- chrome.exe (PID: 3152)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 448)
- chrome.exe (PID: 2900)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 1868)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 3404)
- iexplore.exe (PID: 2152)
- iexplore.exe (PID: 3612)
- chrome.exe (PID: 4028)
- chrome.exe (PID: 1068)
Reads the hosts file
- chrome.exe (PID: 2728)
- chrome.exe (PID: 276)
Reads the date of Windows installation
- opera.exe (PID: 1364)
- chrome.exe (PID: 2104)
Manual execution by user
- chrome.exe (PID: 276)
- steam.exe (PID: 932)
Creates files in the user directory
- opera.exe (PID: 1364)
- iexplore.exe (PID: 3612)
- chrome.exe (PID: 276)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 1364)
Reads settings of System Certificates
- chrome.exe (PID: 2728)
- chrome.exe (PID: 276)
- Baixaki_Poppy Playtime_v2.981.22.448.7.exe (PID: 2980)
- iexplore.exe (PID: 3612)
- iexplore.exe (PID: 2152)
Application launched itself
- chrome.exe (PID: 276)
- iexplore.exe (PID: 2152)
Checks Windows Trust Settings
- chrome.exe (PID: 276)
- Baixaki_Poppy Playtime_v2.981.22.448.7.exe (PID: 2980)
- iexplore.exe (PID: 3612)
- iexplore.exe (PID: 2152)
Changes internet zones settings
- iexplore.exe (PID: 2152)
Reads internet explorer settings
- iexplore.exe (PID: 3612)
Changes settings of System certificates
- iexplore.exe (PID: 3612)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
171
Monitored processes
127
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,9941967689217039519,14442393190193705826,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3216 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,9941967689217039519,14442393190193705826,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2740 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,9941967689217039519,14442393190193705826,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=68 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,9941967689217039519,14442393190193705826,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=82 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1052,9941967689217039519,14442393190193705826,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=5368 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,9941967689217039519,14442393190193705826,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2136 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,9941967689217039519,14442393190193705826,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4452 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,9941967689217039519,14442393190193705826,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,9941967689217039519,14442393190193705826,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3244 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
62 518
Read events
61 859
Write events
649
Delete events
10
Modification events
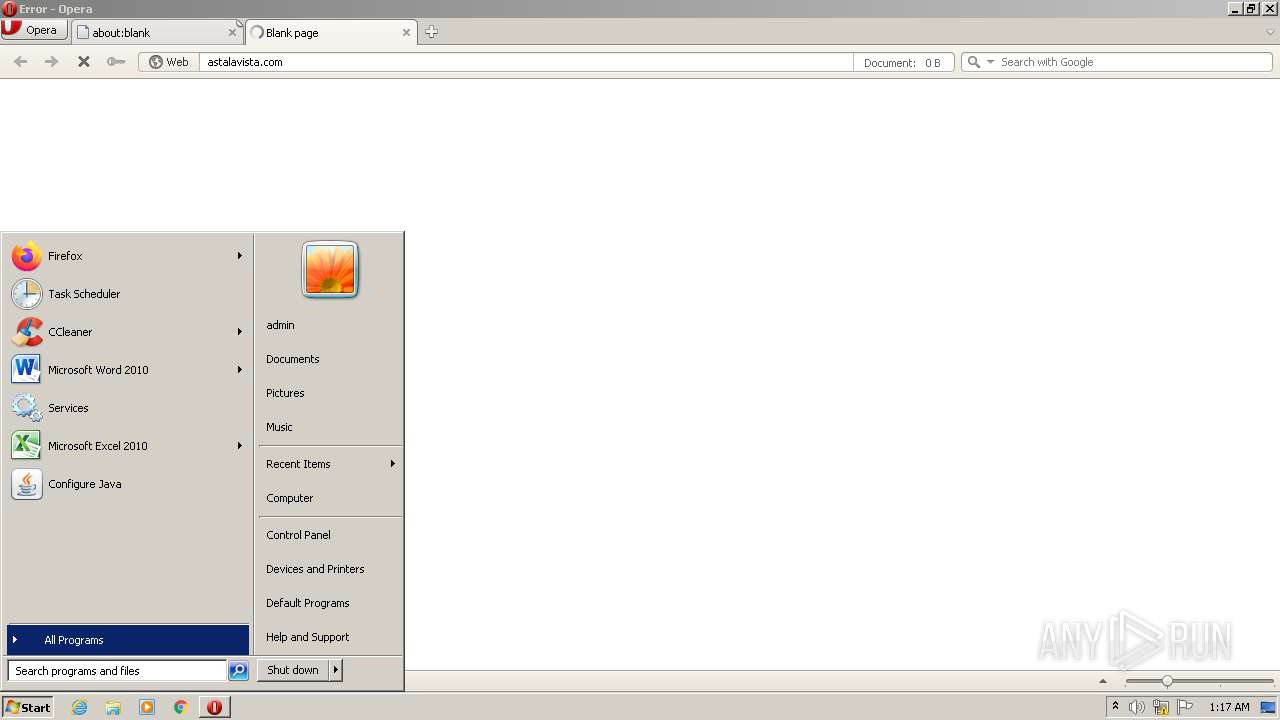
| (PID) Process: | (1364) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe "https://Astalavista.com" | |||
| (PID) Process: | (1364) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (276) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
19
Suspicious files
417
Text files
371
Unknown types
70
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1364 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 1364 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprD7F9.tmp | text | |
MD5:— | SHA256:— | |||
| 1364 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprD867.tmp | xml | |
MD5:— | SHA256:— | |||
| 1364 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr4377.tmp | text | |
MD5:— | SHA256:— | |||
| 1364 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\global_history.dat | text | |
MD5:— | SHA256:— | |||
| 1364 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00003.tmp | xml | |
MD5:— | SHA256:— | |||
| 1364 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 1364 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 1364 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TYCU4TQBAU3C0UL9VMGA.temp | binary | |
MD5:— | SHA256:— | |||
| 1364 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
80
TCP/UDP connections
289
DNS requests
164
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | — | — | whitelisted |
1364 | opera.exe | GET | 302 | 172.217.169.100:80 | http://www.google.com/search?client=opera&q=https%3A%2F%2FAstalavista.com&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 355 b | malicious |
1364 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
1364 | opera.exe | GET | 200 | 142.250.185.227:80 | http://crl.pki.goog/gsr1/gsr1.crl | US | der | 1.61 Kb | whitelisted |
1364 | opera.exe | GET | 200 | 172.217.20.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHJSVeveG6D0EsJQMIWt0yY%3D | US | der | 471 b | whitelisted |
1364 | opera.exe | GET | 200 | 172.217.20.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDe76Bca6%2BVQAq8hUxeKqi3 | US | der | 472 b | whitelisted |
1364 | opera.exe | GET | 200 | 172.217.20.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCNxxDLaXWgbRJCQBURGN3%2B | US | der | 472 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 5.63 Kb | whitelisted |
1364 | opera.exe | GET | 200 | 142.250.185.227:80 | http://crl.pki.goog/gtsr1/gtsr1.crl | US | der | 760 b | whitelisted |
1364 | opera.exe | GET | 302 | 172.217.169.100:80 | http://www.google.com/search?q=https%3A%2F%2FAstalavista.com&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 339 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1364 | opera.exe | 188.114.97.10:443 | astalavista.com | Cloudflare Inc | US | malicious |
1364 | opera.exe | 185.26.182.118:443 | sitecheck2.opera.com | Opera Software AS | — | suspicious |
1364 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
1364 | opera.exe | 188.114.96.10:443 | astalavista.com | Cloudflare Inc | US | malicious |
1364 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1364 | opera.exe | 172.217.169.100:80 | www.google.com | Google Inc. | US | whitelisted |
1364 | opera.exe | 185.26.182.110:80 | redir.opera.com | Opera Software AS | — | unknown |
1364 | opera.exe | 172.217.169.100:443 | www.google.com | Google Inc. | US | whitelisted |
1364 | opera.exe | 172.217.20.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1364 | opera.exe | 142.250.185.78:443 | consent.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
astalavista.com |
| malicious |
certs.opera.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
redir.opera.com |
| whitelisted |
www.google.com |
| malicious |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
consent.google.com |
| shared |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1364 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1364 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1364 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1364 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1364 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1364 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
932 | steam.exe | Potential Corporate Privacy Violation | ET USER_AGENTS Steam HTTP Client User-Agent |
4 ETPRO signatures available at the full report