| File name: | SupportTool.exe |
| Full analysis: | https://app.any.run/tasks/7e4aab43-0e09-472e-8035-818db778ce1f |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 13:57:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | A1FA0F25D56CB8C98DA495A98E380BA4 |
| SHA1: | 7D2616BF2F9C0556FE9E02B772ED4D5C76B889BF |
| SHA256: | 8427B88A9CC51F318157350F9EE8D2E07350EF8C21D0B6707A94952A7C660356 |
| SSDEEP: | 12288:IMmtMSpKnRYB4gLuDqCOor70TPp3dtqZZrAttJVVVVVVVVVVVVVVVVVVVOVVVVV7:IMgpKnRy4Hm3osBfBe |
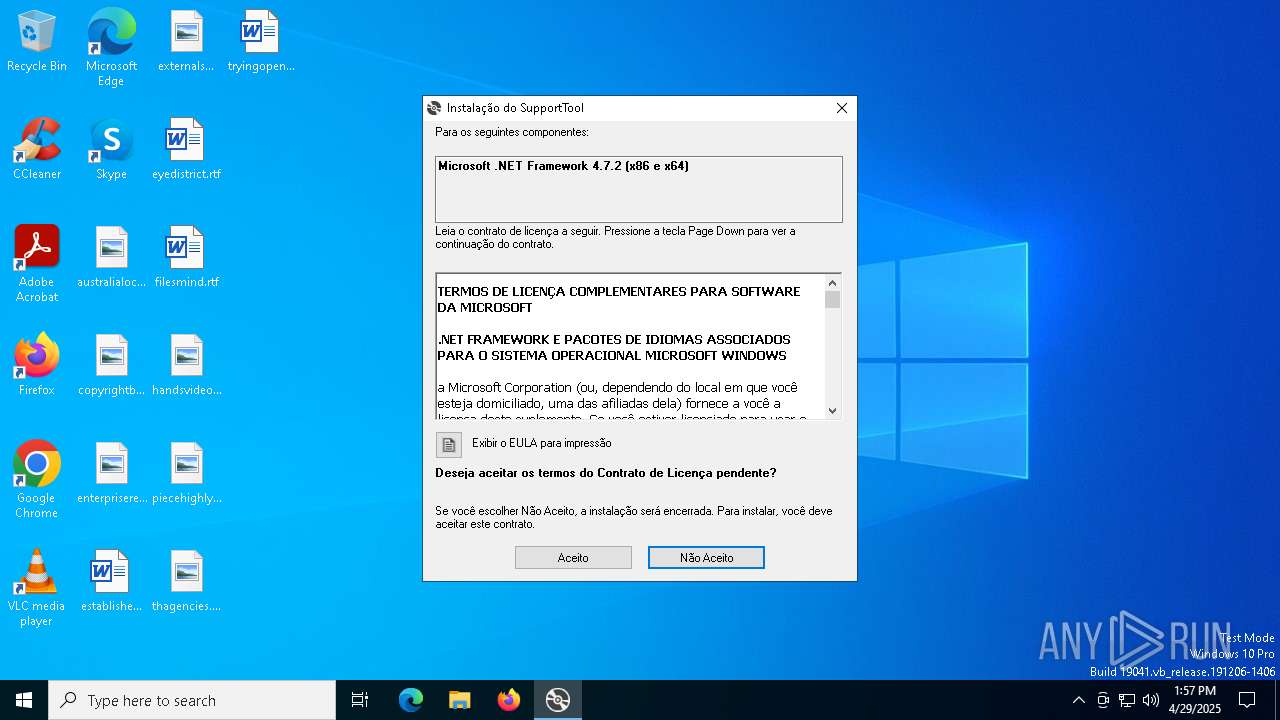
MALICIOUS
Executing a file with an untrusted certificate
- SupportTool.exe (PID: 2568)
SUSPICIOUS
Process drops legitimate windows executable
- SupportTool.exe (PID: 2568)
- NDP472-KB4054530-x86-x64-AllOS-PTB.exe (PID: 896)
Starts a Microsoft application from unusual location
- NDP472-KB4054530-x86-x64-AllOS-PTB.exe (PID: 1660)
- NDP472-KB4054530-x86-x64-AllOS-PTB.exe (PID: 896)
Reads security settings of Internet Explorer
- SupportTool.exe (PID: 2568)
- dfsvc.exe (PID: 5324)
Executable content was dropped or overwritten
- NDP472-KB4054530-x86-x64-AllOS-PTB.exe (PID: 896)
- SupportTool.exe (PID: 2568)
Creates file in the systems drive root
- NDP472-KB4054530-x86-x64-AllOS-PTB.exe (PID: 896)
INFO
Reads the computer name
- SupportTool.exe (PID: 2568)
- NDP472-KB4054530-x86-x64-AllOS-PTB.exe (PID: 896)
- Setup.exe (PID: 5956)
- dfsvc.exe (PID: 5324)
Checks proxy server information
- SupportTool.exe (PID: 2568)
The sample compiled with english language support
- SupportTool.exe (PID: 2568)
- NDP472-KB4054530-x86-x64-AllOS-PTB.exe (PID: 896)
Reads the software policy settings
- SupportTool.exe (PID: 2568)
Process checks computer location settings
- SupportTool.exe (PID: 2568)
Checks supported languages
- NDP472-KB4054530-x86-x64-AllOS-PTB.exe (PID: 896)
- SupportTool.exe (PID: 2568)
- Setup.exe (PID: 5956)
- dfsvc.exe (PID: 5324)
Create files in a temporary directory
- SupportTool.exe (PID: 2568)
- Setup.exe (PID: 5956)
Creates files or folders in the user directory
- SupportTool.exe (PID: 2568)
Reads the machine GUID from the registry
- SupportTool.exe (PID: 2568)
- dfsvc.exe (PID: 5324)
The sample compiled with portuguese language support
- NDP472-KB4054530-x86-x64-AllOS-PTB.exe (PID: 896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:10:10 21:21:30+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.38 |
| CodeSize: | 382464 |
| InitializedDataSize: | 179712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x36fc0 |
| OSVersion: | 5.1 |
| ImageVersion: | 10 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 17.0.35410.144 |
| ProductVersionNumber: | 17.0.35410.144 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 17.0.35410.144 built by: d17.12 |
| InternalName: | setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | setup.exe |
| ProductName: | - |
| ProductVersion: | 17.0.35410.144 |
Total processes
136
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
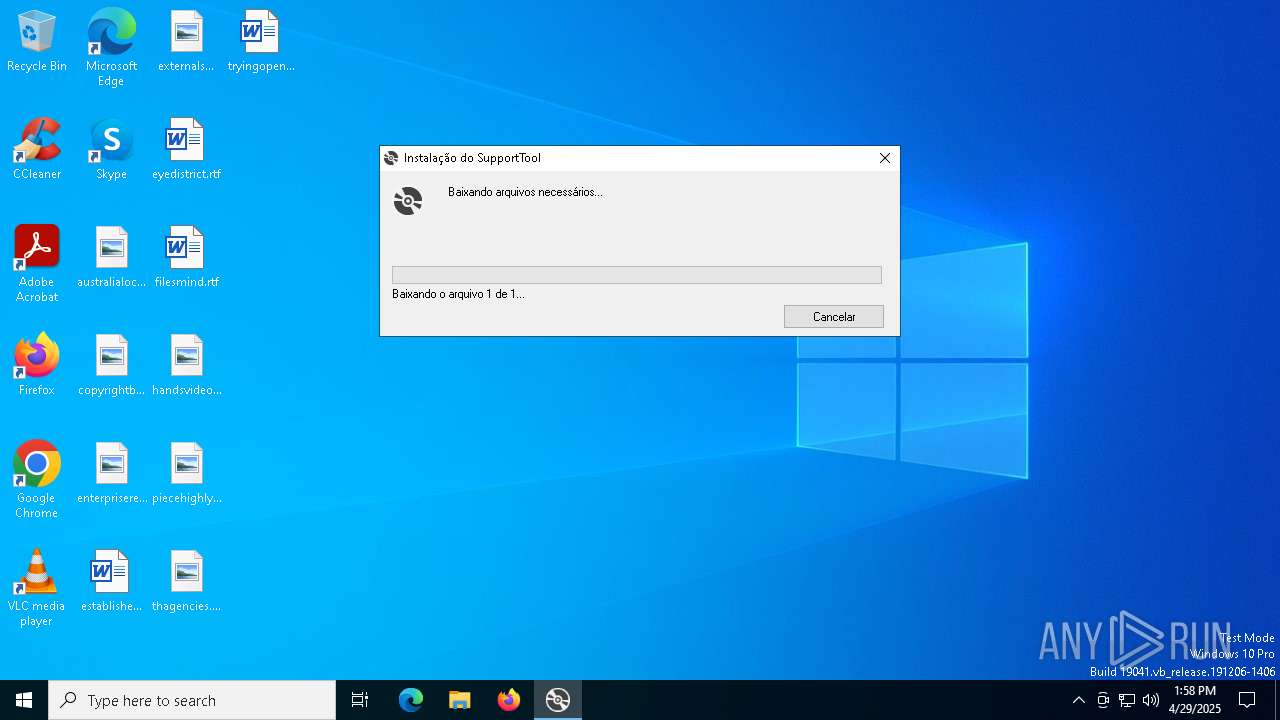
| 896 | "C:\Users\admin\AppData\Local\Temp\VSDBEFC.tmp\DotNetFX472\NDP472-KB4054530-x86-x64-AllOS-PTB.exe" /q /norestart /skipenucheck /ChainingPackage FullX64ClickOnce | C:\Users\admin\AppData\Local\Temp\VSDBEFC.tmp\DotNetFX472\NDP472-KB4054530-x86-x64-AllOS-PTB.exe | SupportTool.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.7.2 (PTB) Setup Exit code: 0 Version: 4.7.03062.00 Modules
| |||||||||||||||
| 920 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\Users\admin\AppData\Local\Temp\VSDBEFC.tmp\DotNetFX472\NDP472-KB4054530-x86-x64-AllOS-PTB.exe" /q /norestart /skipenucheck /ChainingPackage FullX64ClickOnce | C:\Users\admin\AppData\Local\Temp\VSDBEFC.tmp\DotNetFX472\NDP472-KB4054530-x86-x64-AllOS-PTB.exe | — | SupportTool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4.7.2 (PTB) Setup Exit code: 3221226540 Version: 4.7.03062.00 Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\AppData\Local\Temp\SupportTool.exe" | C:\Users\admin\AppData\Local\Temp\SupportTool.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Exit code: 0 Version: 17.0.35410.144 built by: d17.12 Modules
| |||||||||||||||
| 5324 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe | — | SupportTool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5936 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5956 | C:\86cfaf43b1398da7c31f6d69e96f95\\Setup.exe /q /norestart /skipenucheck /ChainingPackage FullX64ClickOnce /x86 /x64 /lcid 1046 /lpredist | C:\86cfaf43b1398da7c31f6d69e96f95\Setup.exe | — | NDP472-KB4054530-x86-x64-AllOS-PTB.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 14.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
Total events
4 576
Read events
4 565
Write events
9
Delete events
2
Modification events
| (PID) Process: | (2568) SupportTool.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2568) SupportTool.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2568) SupportTool.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5324) dfsvc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5324) dfsvc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5324) dfsvc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5324) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: 7E775C7DPLRY1V69L9EJ69J6 | |||
| (PID) Process: | (5324) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete value | Name: | ComponentStore_RandomString |
Value: 7E775C7DPLRY1V69L9EJ69J6 | |||
| (PID) Process: | (5324) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5324) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: XZ84HNRLYVPBRPQYA270E1LC | |||
Executable files
10
Suspicious files
4
Text files
35
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 896 | NDP472-KB4054530-x86-x64-AllOS-PTB.exe | C:\86cfaf43b1398da7c31f6d69e96f95\x64-Windows10.0-KB4054609-x64.cab | — | |
MD5:— | SHA256:— | |||
| 896 | NDP472-KB4054530-x86-x64-AllOS-PTB.exe | C:\86cfaf43b1398da7c31f6d69e96f95\x64-Windows10.0-KB4073139-x64.cab | — | |
MD5:— | SHA256:— | |||
| 2568 | SupportTool.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C0018BB1B5834735BFA60CD063B31956 | der | |
MD5:9B2509CFF42DFCEC25276BCC225CC4A4 | SHA256:7335A1BD971D1CAF943246E1705CE2D10F83FE6A34438128D2C0CF3738FEE8AB | |||
| 2568 | SupportTool.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | der | |
MD5:3B5E0BD6640456A749D9155E6C135727 | SHA256:C362A3D2B661C6066A02FC169FAAA1976C2F6160DA5837C7E68B7E0F67B794ED | |||
| 896 | NDP472-KB4054530-x86-x64-AllOS-PTB.exe | C:\86cfaf43b1398da7c31f6d69e96f95\Graphics\Rotate4.ico | image | |
MD5:267B198FEF022D3B1D44CCA7FE589373 | SHA256:303989B692A57FE34B47BB2F926B91AC605F288AE6C9479B33EAF15A14EB33AC | |||
| 2568 | SupportTool.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C0018BB1B5834735BFA60CD063B31956 | binary | |
MD5:0489731753486DF58F6B260991056152 | SHA256:4FFA2CB607F82DA62050B91EE2F0740EEEB5A6987FAF78CEC6819DDCDD33A66A | |||
| 896 | NDP472-KB4054530-x86-x64-AllOS-PTB.exe | C:\86cfaf43b1398da7c31f6d69e96f95\header.bmp | image | |
MD5:41C22EFA84CA74F0CE7076EB9A482E38 | SHA256:255025A0D79EF2DAC04BD610363F966EF58328400BF31E1F8915E676478CD750 | |||
| 2568 | SupportTool.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:450EBEE1AF7F8C483896692BCF8F127F | SHA256:022E4AE40312C184BA7347C51D8CCD04A0BAAC09774FCAF7C661D403728C82C0 | |||
| 896 | NDP472-KB4054530-x86-x64-AllOS-PTB.exe | C:\86cfaf43b1398da7c31f6d69e96f95\SplashScreen.bmp | image | |
MD5:BC32088BFAA1C76BA4B56639A2DEC592 | SHA256:B05141DBC71669A7872A8E735E5E43A7F9713D4363B7A97543E1E05DCD7470A7 | |||
| 2568 | SupportTool.exe | C:\Users\admin\AppData\Local\Temp\VSDBEFC.tmp\DotNetFX472\NDP472-KB4054530-x86-x64-AllOS-PTB.exe | executable | |
MD5:767A072E38E820FED2FBF5FC5A62DC6E | SHA256:84057CC0C20982BCAB3CBF24C9D0C7704B7E0F3A94F3F72A5C3925AFFC887D5C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
20
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2568 | SupportTool.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2568 | SupportTool.exe | GET | 302 | 95.100.186.9:80 | http://go.microsoft.com/fwlink/?LinkId=863258&clcid=0x416 | unknown | — | — | whitelisted |
4220 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2568 | SupportTool.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2568 | SupportTool.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
4220 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2568 | SupportTool.exe | 95.100.186.9:80 | go.microsoft.com | AKAMAI-AS | FR | whitelisted |
2568 | SupportTool.exe | 2.22.242.82:443 | download.visualstudio.microsoft.com | Akamai International B.V. | DE | whitelisted |
2568 | SupportTool.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
download.visualstudio.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |