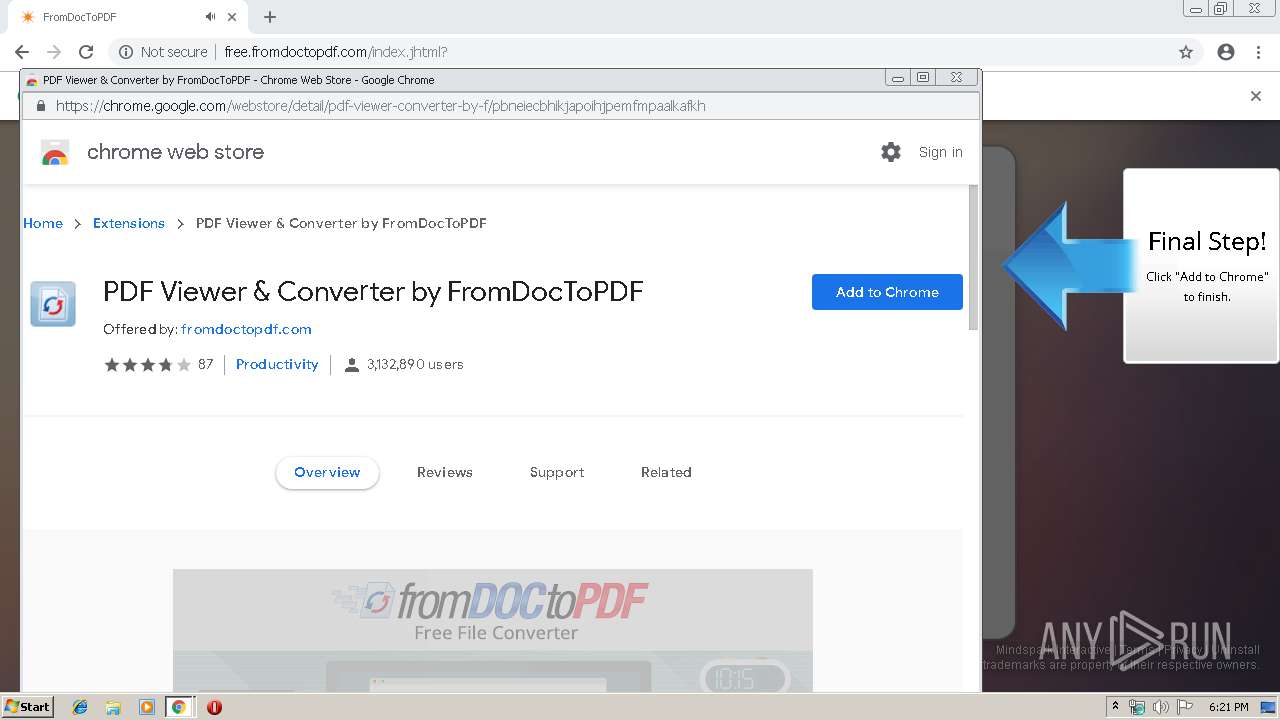
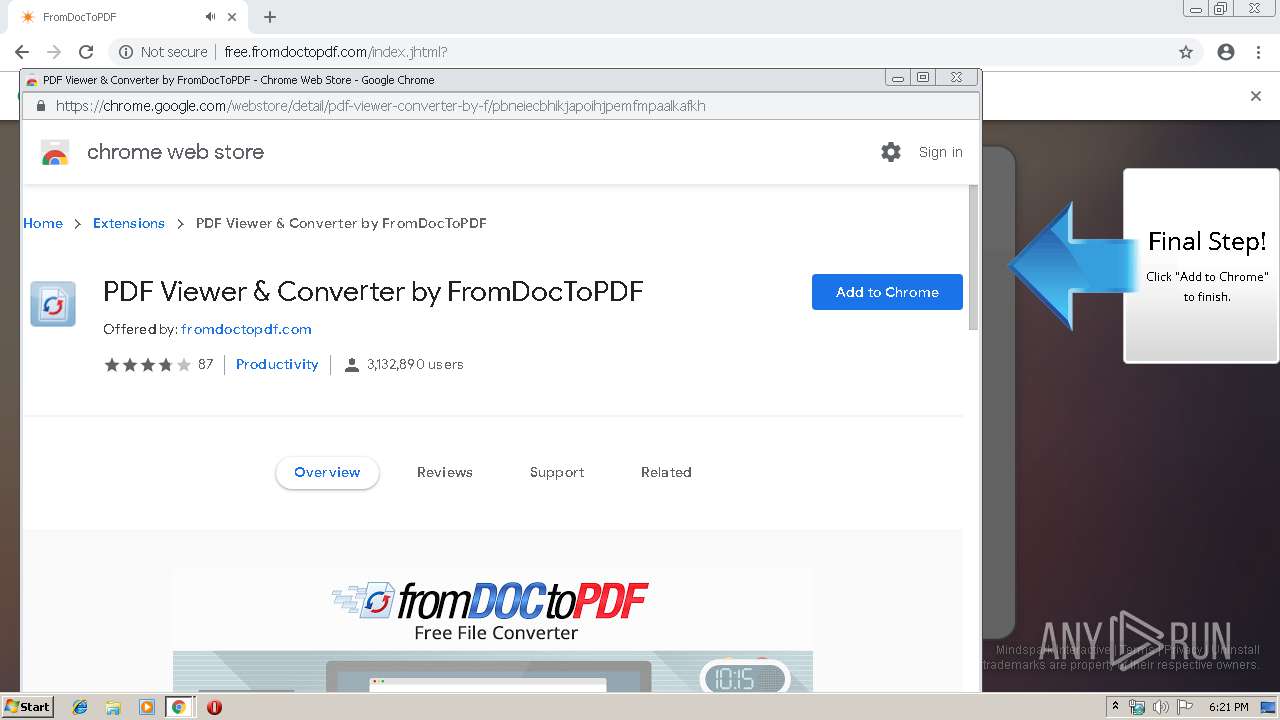
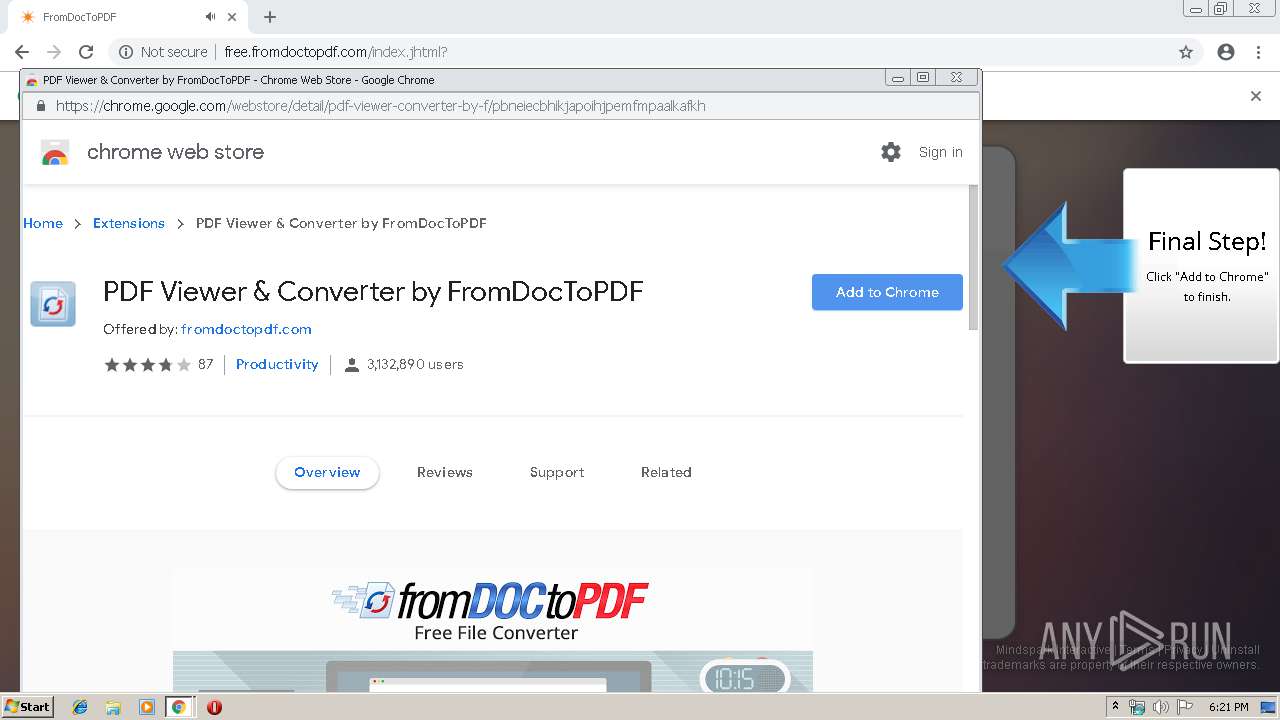
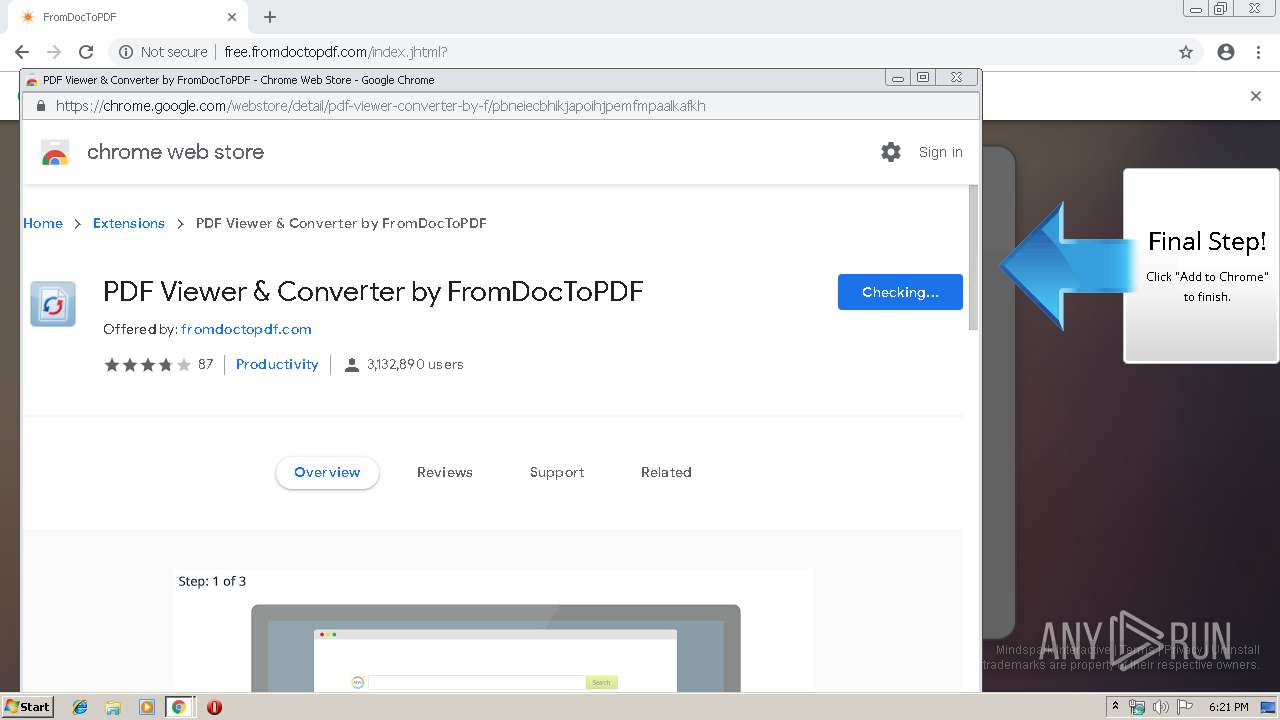
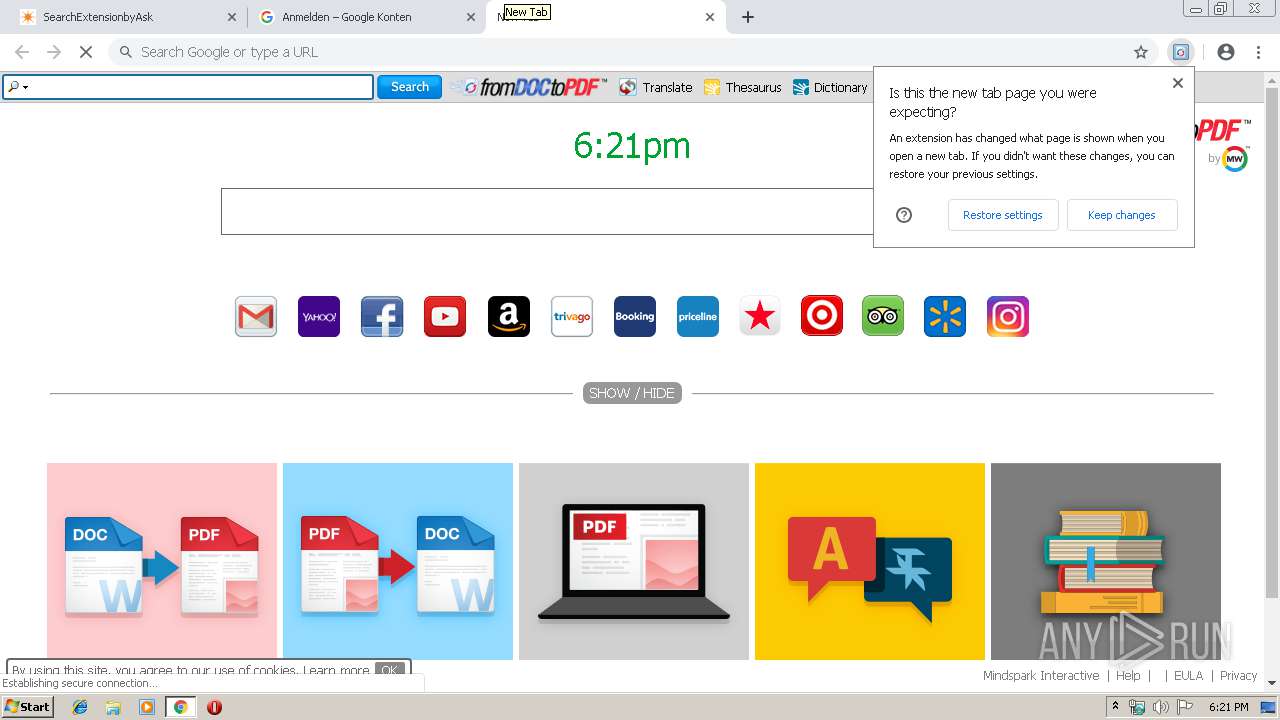
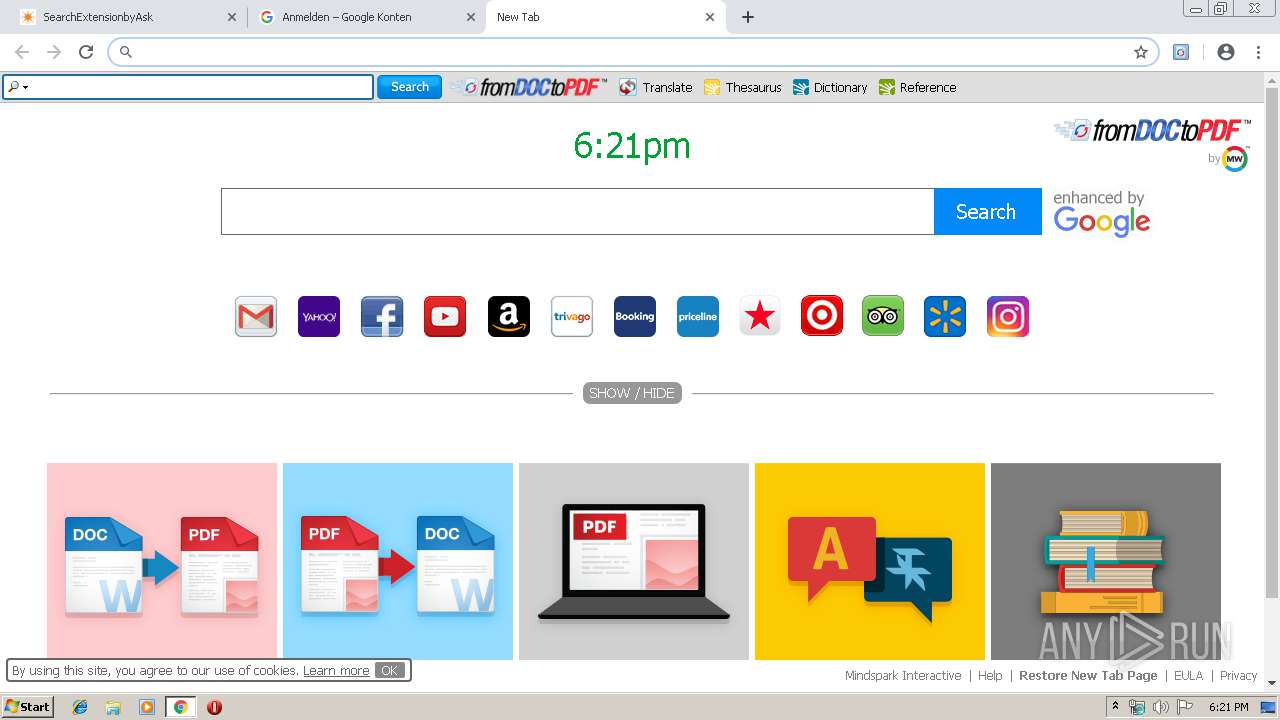
| URL: | http://free.fromdoctopdf.com/index.jhtml? |
| Full analysis: | https://app.any.run/tasks/ceb43f68-c398-4713-8f15-9e61a0ac7189 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 17:20:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B068A06B79C382CAC21B07E039052199 |
| SHA1: | 1FD4360C1B70FFC9897366029411D3C0C0FE25C1 |
| SHA256: | 8423CA46730347342AAE00414B76C59862AFA8FBA81DB009B23C41A16FC23989 |
| SSDEEP: | 3:N1KYQu+8KGO1yGLBUUn:CYrcLBUUn |
MALICIOUS
No malicious indicators.SUSPICIOUS
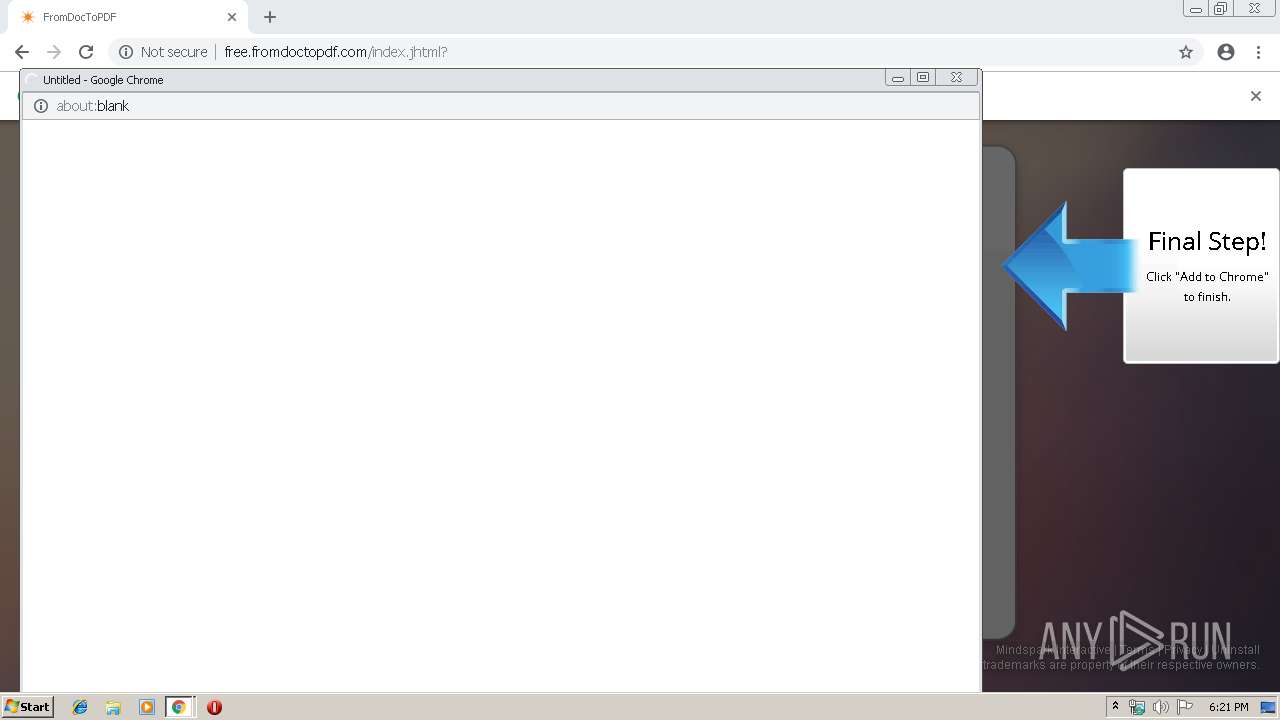
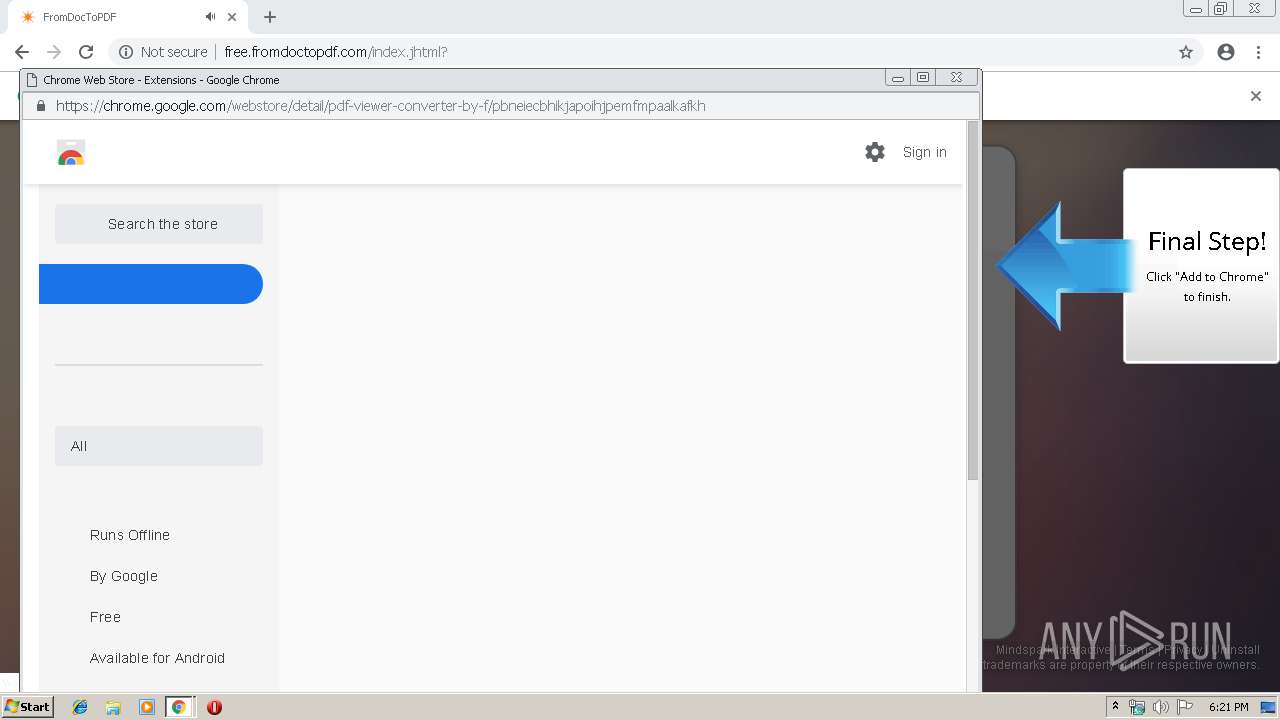
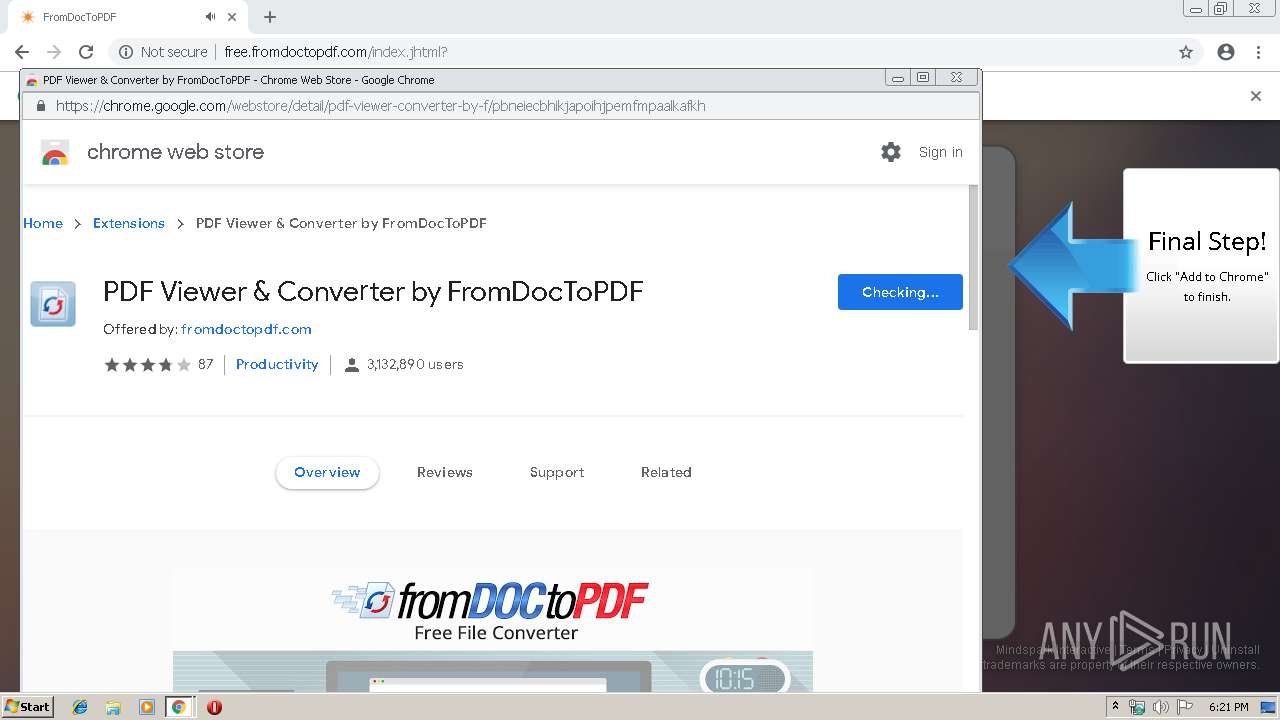
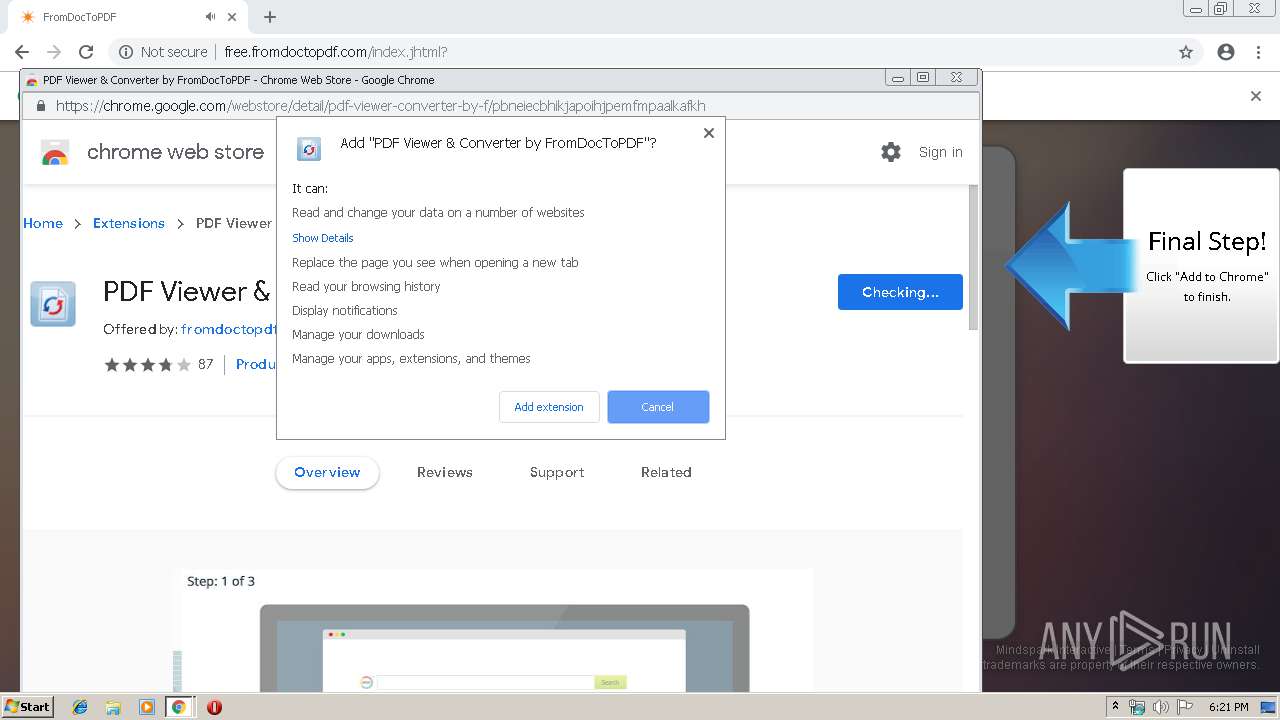
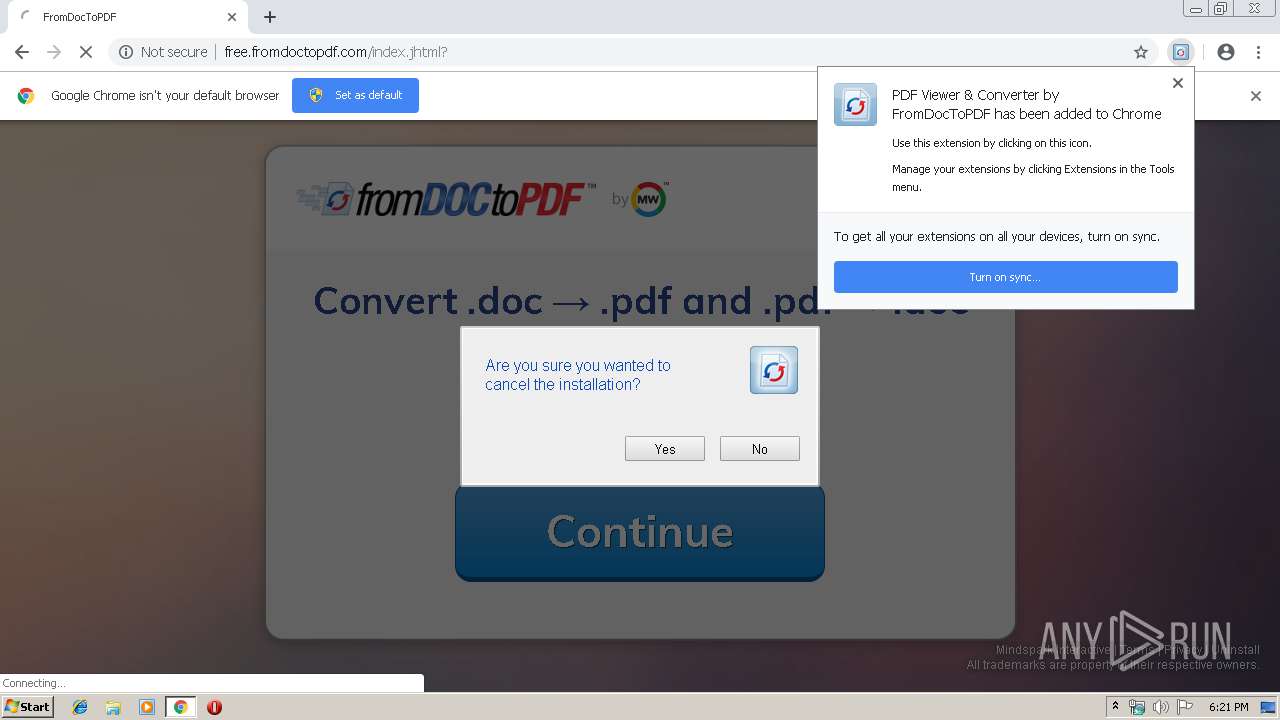
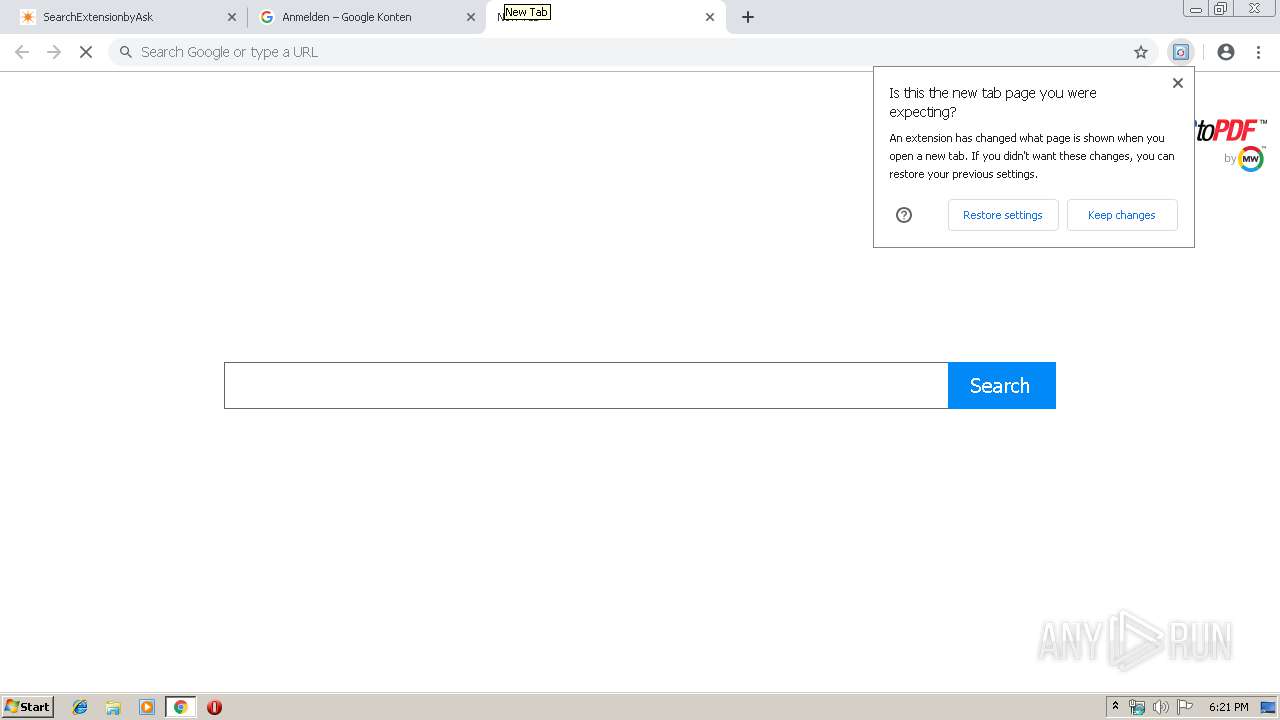
Modifies files in Chrome extension folder
- chrome.exe (PID: 2984)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2984)
Application launched itself
- chrome.exe (PID: 2984)
Reads Internet Cache Settings
- chrome.exe (PID: 2984)
Changes settings of System certificates
- chrome.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
42
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8182225227843311164 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8182225227843311164 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --service-pipe-token=15642648064140135313 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15642648064140135313 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13034622458037434619 --mojo-platform-channel-handle=5268 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10082666127499526608 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10082666127499526608 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3656 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15120584539628655734 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15120584539628655734 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15136980131037277033 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15136980131037277033 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5812 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18293631733405915933 --mojo-platform-channel-handle=4864 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8912019663346484606 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8912019663346484606 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3037114320993778186 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3037114320993778186 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --service-pipe-token=12735527877377163818 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12735527877377163818 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
686
Read events
572
Write events
109
Delete events
5
Modification events
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2984-13202414463182750 |
Value: 259 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
55
Text files
269
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bba3b1ae-e562-4241-8ad6-5251d14aeb71.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
86
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
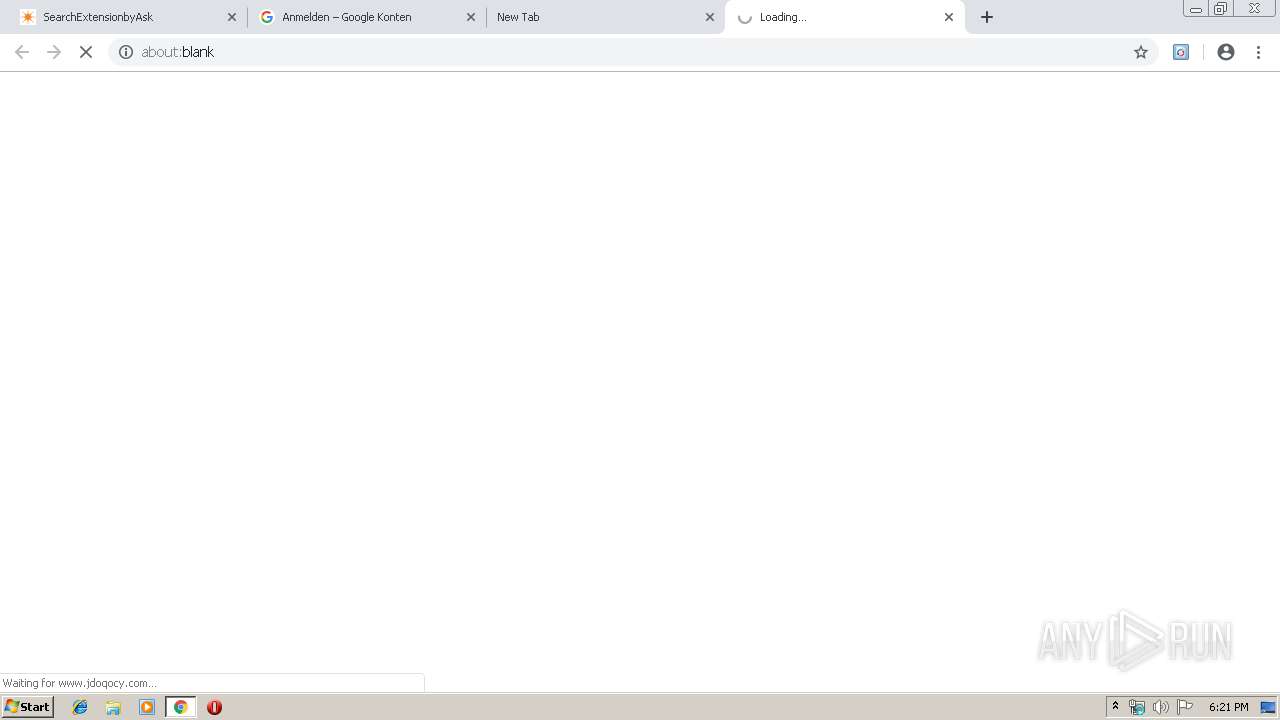
2984 | chrome.exe | GET | 204 | 35.244.218.203:80 | http://free.fromdoctopdf.com/anemone.jhtml?anxuu=877AC811-6D73-4C1F-9699-4D242B093F0F&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T00%3A00%3A00Z&anxsn=prod-dlp-europe-west1-zmkr&anxu=http%3A%2F%2Ffree.fromdoctopdf.com%2Findex.jhtml&anxl=en-US&anxlv=1557940865234&anxsq=5&cookiesEnabled=1&pageLoad=846&anxe=SplashLanding&anxr=2083929917 | US | — | — | whitelisted |
2984 | chrome.exe | GET | 200 | 35.244.218.203:80 | http://free.fromdoctopdf.com/index.jhtml? | US | html | 45.2 Kb | whitelisted |
2984 | chrome.exe | GET | 200 | 104.111.214.175:80 | http://ak.staticimgfarm.com/images/webtooltab/ttdetect-2/prd/ttDetectUtil.js | NL | text | 3.81 Kb | whitelisted |
2984 | chrome.exe | GET | 200 | 35.244.218.203:80 | http://free.fromdoctopdf.com/static/cws/audio.js | US | text | 649 b | whitelisted |
2984 | chrome.exe | GET | 200 | 104.111.214.175:80 | http://ak.staticimgfarm.com/images/download/assist_21.gif | NL | image | 39.5 Kb | whitelisted |
2984 | chrome.exe | POST | 200 | 35.244.218.203:80 | http://fromdoctopdf.dl.myway.com/mirrorCookies.jhtml | US | html | 93 b | whitelisted |
2984 | chrome.exe | GET | 200 | 35.244.218.203:80 | http://fromdoctopdf.dl.myway.com/localStorage.jhtml | US | html | 2.20 Kb | whitelisted |
2984 | chrome.exe | GET | 200 | 104.111.214.175:80 | http://ak.imgfarm.com/images/download/chrome/overlay_bl_2.png | NL | image | 18.7 Kb | whitelisted |
2984 | chrome.exe | GET | 204 | 35.244.218.203:80 | http://free.fromdoctopdf.com/anemone.jhtml?anxuu=877AC811-6D73-4C1F-9699-4D242B093F0F&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T00%3A00%3A00Z&anxsn=prod-dlp-europe-west1-zmkr&anxu=http%3A%2F%2Ffree.fromdoctopdf.com%2Findex.jhtml&anxl=en-US&anxlv=1557940864751&anxsq=3&present=false&anxe=ToolbarDetect&anxr=326845527 | US | compressed | 649 b | whitelisted |
2984 | chrome.exe | GET | 204 | 35.244.218.203:80 | http://free.fromdoctopdf.com/anemone.jhtml?anxuu=877AC811-6D73-4C1F-9699-4D242B093F0F&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T00%3A00%3A00Z&anxsn=prod-dlp-europe-west1-zmkr&anxu=http%3A%2F%2Ffree.fromdoctopdf.com%2Findex.jhtml&anxl=en-US&anxlv=1557940864745&anxrd=none&anxrp=-&anxrk=-&anxrm=-&anxrb=-&anxrc=-&anxrs=-&anxsq=1&anxi=8D390C3E-7CE3-44CB-BD00-B2F15DE254AA&anxe=backFill&anxr=83061189 | US | compressed | 649 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
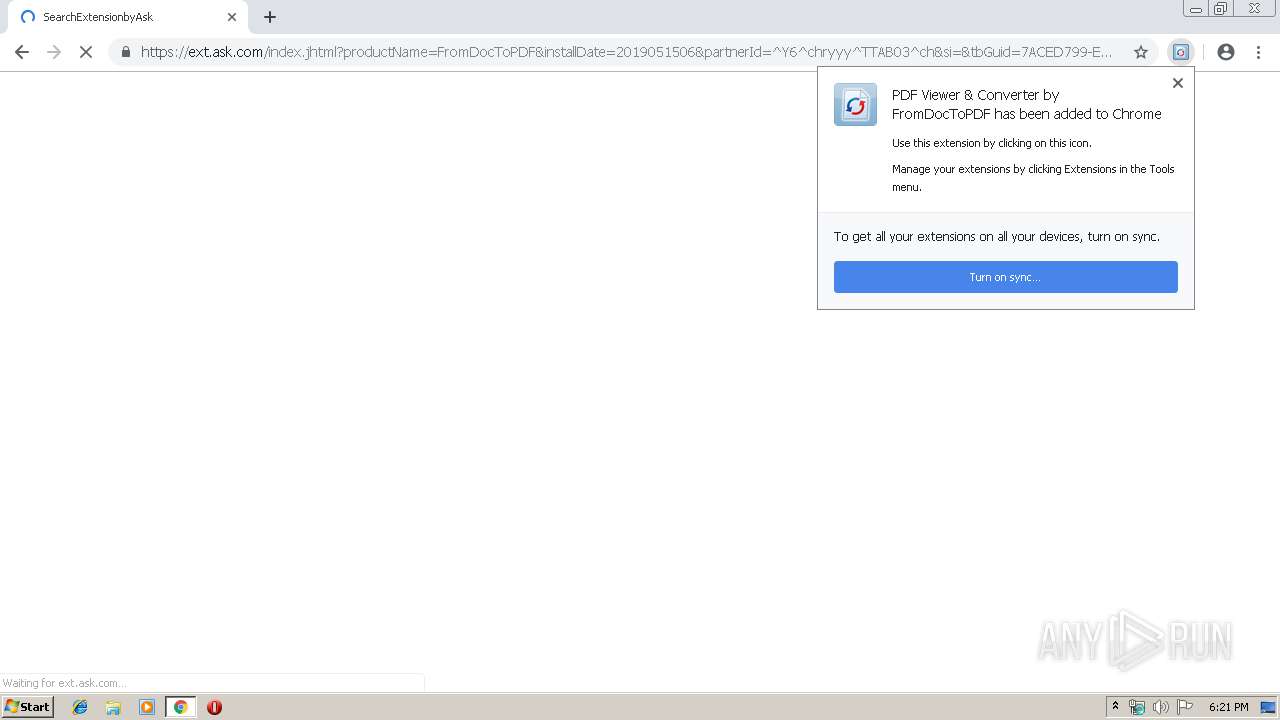
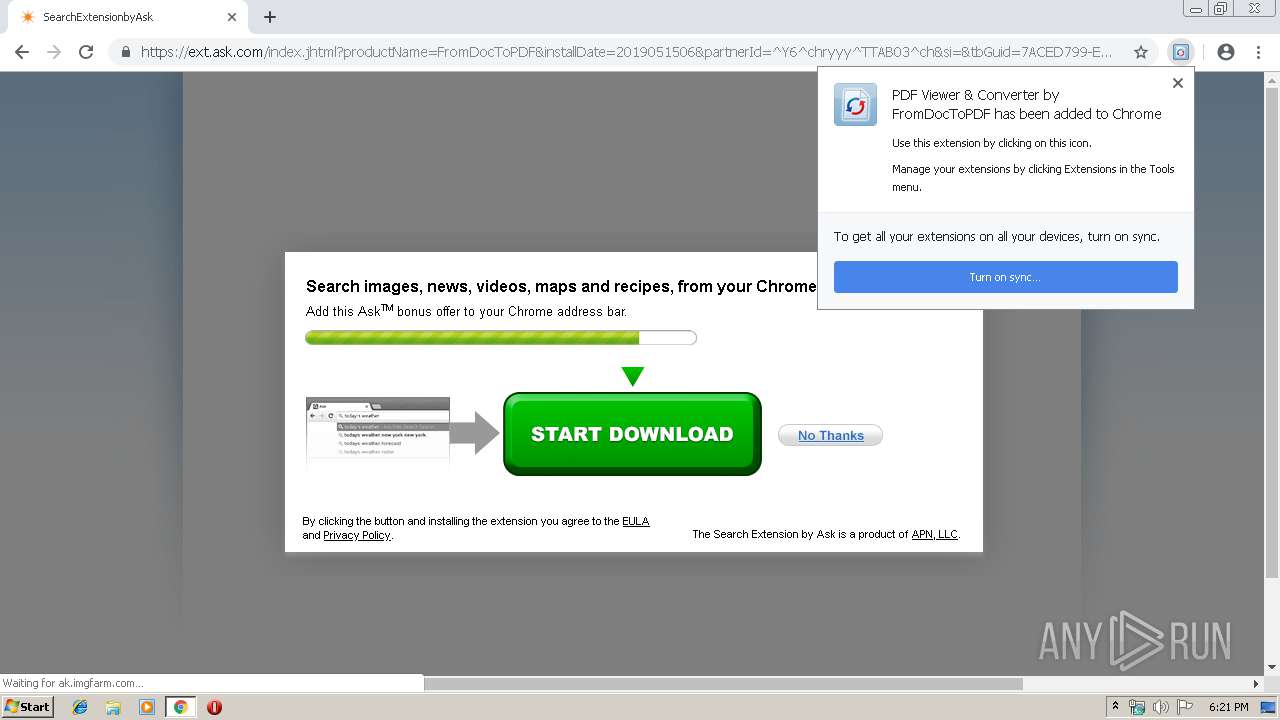
2984 | chrome.exe | 35.244.218.203:80 | free.fromdoctopdf.com | — | US | whitelisted |
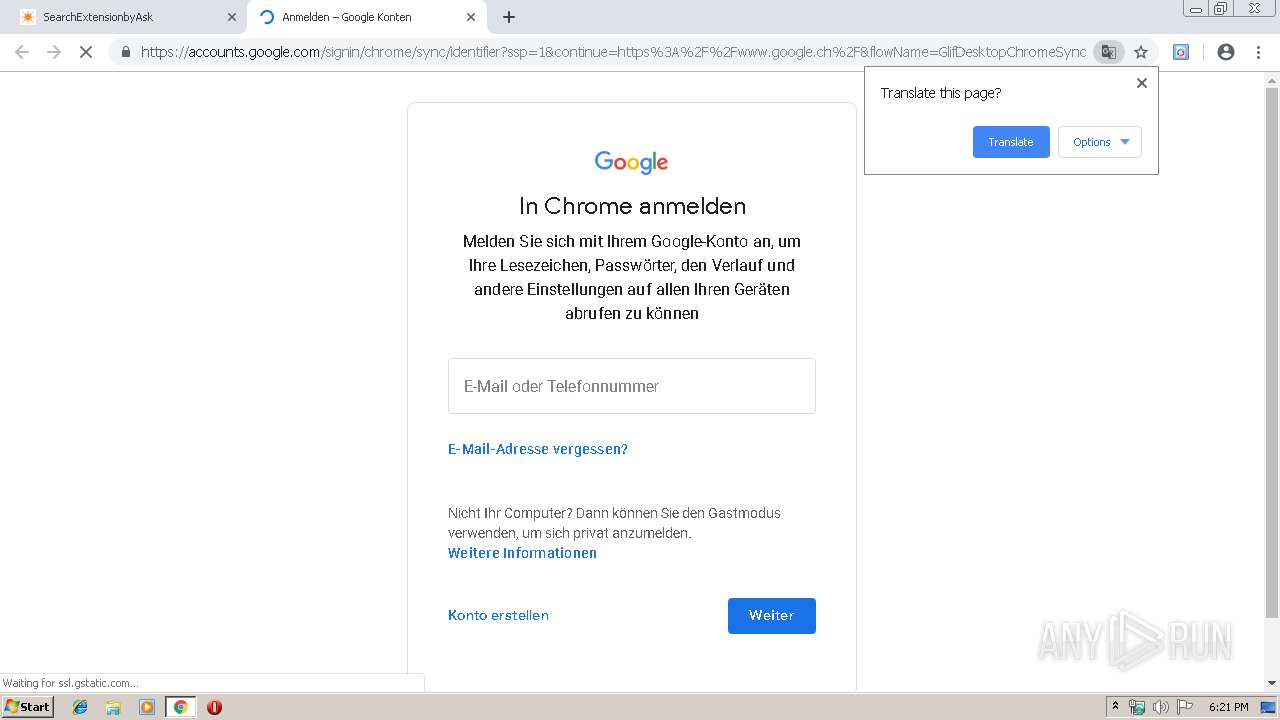
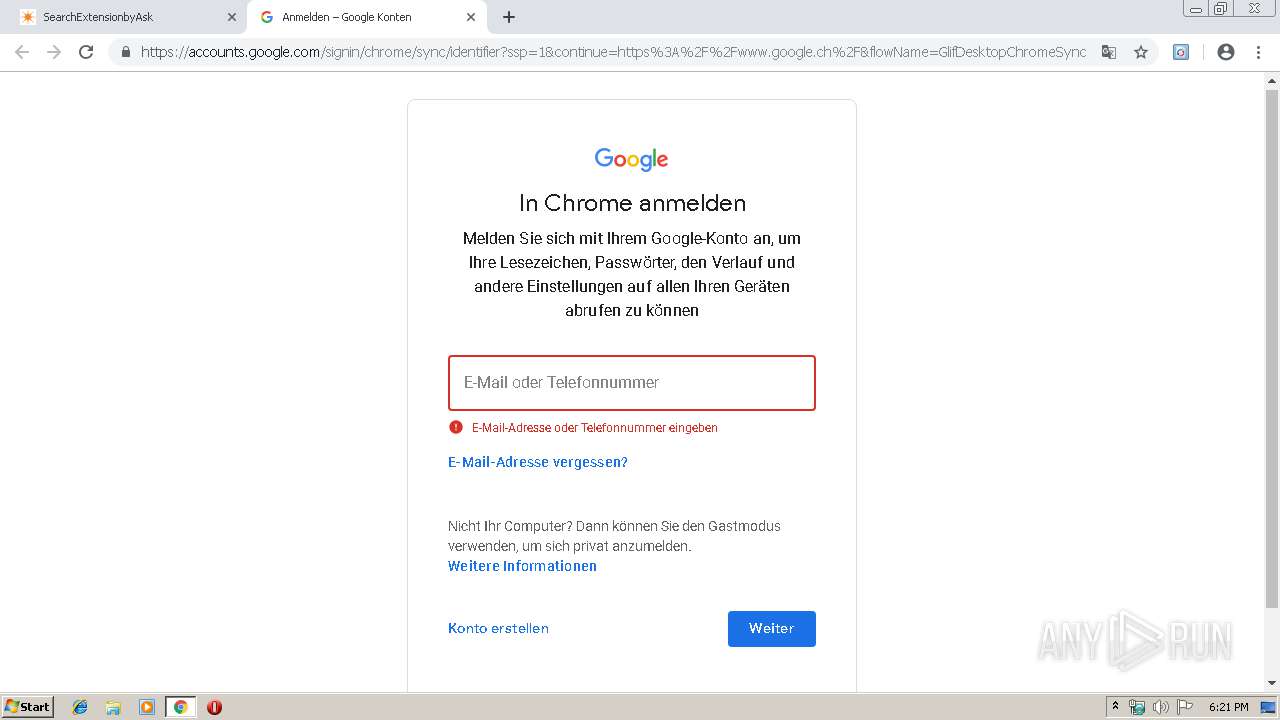
2984 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 104.111.214.175:80 | ak.staticimgfarm.com | Akamai International B.V. | NL | whitelisted |
2984 | chrome.exe | 172.217.22.34:80 | www.googleadservices.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 104.111.214.175:443 | ak.staticimgfarm.com | Akamai International B.V. | NL | whitelisted |
2984 | chrome.exe | 31.13.90.6:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2984 | chrome.exe | 216.58.208.34:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2984 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 2.21.36.155:80 | akz.imgfarm.com | GTT Communications Inc. | FR | suspicious |
2984 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
free.fromdoctopdf.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
ak.staticimgfarm.com |
| whitelisted |
ak.imgfarm.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
akz.imgfarm.com |
| whitelisted |
support.myway.com |
| whitelisted |
eula.mindspark.com |
| malicious |