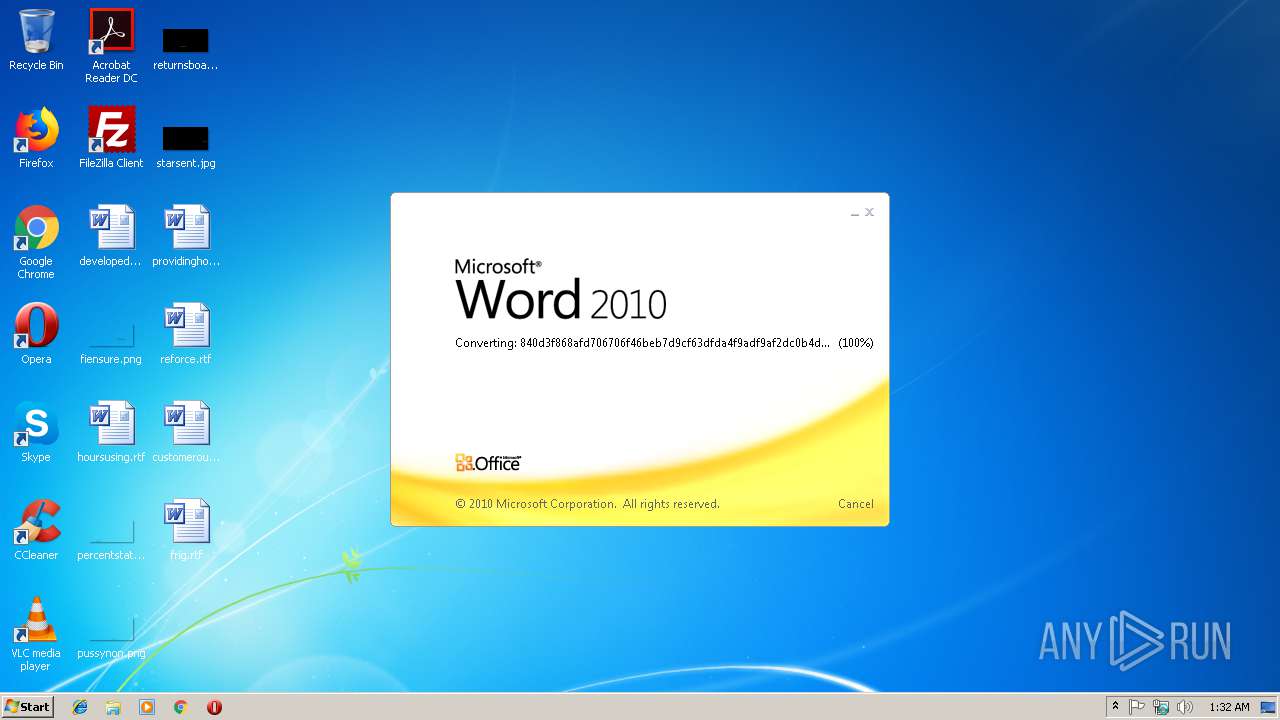
| File name: | 840d3f868afd706706f46beb7d9cf63dfda4f9adf9af2dc0b4d3dd471fd38819.doc |
| Full analysis: | https://app.any.run/tasks/7b7d4bb5-09a5-443d-bcc8-0586163489e6 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | February 11, 2019, 01:31:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 272310F5C8CCD9CFFD04EA74C58145EA |
| SHA1: | DBB90628D11DBFD0208968565A0798DED0CCCAE3 |
| SHA256: | 840D3F868AFD706706F46BEB7D9CF63DFDA4F9ADF9AF2DC0B4D3DD471FD38819 |
| SSDEEP: | 1536:fBAFUViYC8t09AnFET9iPTs96n1sd78wIcz4y77b3QC3Qsng:fQQiYC8Wg |
MALICIOUS
Application was dropped or rewritten from another process
- 4.exe (PID: 3456)
- 4.exe (PID: 3076)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 3548)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 3548)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3548)
Changes the autorun value in the registry
- 4.exe (PID: 3456)
LOKIBOT was detected
- 4.exe (PID: 3076)
Detected artifacts of LokiBot
- 4.exe (PID: 3076)
Connects to CnC server
- 4.exe (PID: 3076)
Actions looks like stealing of personal data
- 4.exe (PID: 3076)
SUSPICIOUS
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3548)
- 4.exe (PID: 3456)
- 4.exe (PID: 3076)
Creates files in the user directory
- EQNEDT32.EXE (PID: 3548)
- 4.exe (PID: 3076)
Application launched itself
- 4.exe (PID: 3456)
Loads DLL from Mozilla Firefox
- 4.exe (PID: 3076)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2736)
Creates files in the user directory
- WINWORD.EXE (PID: 2736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Fonttbl: | {{*02020603050405020304}Times New Roman;}{{*020b0604020202020204}Arial;}{{*020b0604020202020204}Arial;}{{*020f0502020204030204}Calibri;}{{*02020603050405020304}Times New Roman;}{{*02020603050405020304}Times New Roman;}{{*020f0302020204030204}Calibri Light;}{{*02020603050405020304}Times New Roman;}{{*02020603050405020304}Times New Roman;}{{*02020603050405020304}Times New Roman;}{{*020f0502020204030204}Calibri;}{{*02020603050405020304}Times New Roman;}{Times New Roman;}{Times New Roman Cyr;}{Times New Roman Greek;}{Times New Roman Tur;}{Times New Roman (Hebrew);}{Times New Roman (Arabic);}{Times New Roman Baltic;}{Times New Roman (Vietnamese);}{Arial;}{Arial Cyr;}{Arial Greek;}{Arial Tur;}{Arial (Hebrew);}{Arial (Arabic);}{Arial Baltic;}{Arial (Vietnamese);}{Arial;}{Arial Cyr;}{Arial Greek;}{Arial Tur;}{Arial (Hebrew);}{Arial (Arabic);}{Arial Baltic;}{Arial (Vietnamese);}{Calibri;}{Calibri Cyr;}{Calibri Greek;}{Calibri Tur;}{Calibri (Hebrew);}{Calibri (Arabic);}{Calibri Baltic;}{Calibri (Vietnamese);}{Times New Roman;}{Times New Roman Cyr;}{Times New Roman Greek;}{Times New Roman Tur;}{Times New Roman (Hebrew);}{Times New Roman (Arabic);}{Times New Roman Baltic;}{Times New Roman (Vietnamese);}{Times New Roman;}{Times New Roman Cyr;}{Times New Roman Greek;}{Times New Roman Tur;}{Times New Roman (Hebrew);}{Times New Roman (Arabic);}{Times New Roman Baltic;}{Times New Roman (Vietnamese);}{Calibri Light;}{Calibri Light Cyr;}{Calibri Light Greek;}{Calibri Light Tur;}{Calibri Light (Hebrew);}{Calibri Light (Arabic);}{Calibri Light Baltic;}{Calibri Light (Vietnamese);}{Times New Roman;}{Times New Roman Cyr;}{Times New Roman Greek;}{Times New Roman Tur;}{Times New Roman (Hebrew);}{Times New Roman (Arabic);}{Times New Roman Baltic;}{Times New Roman (Vietnamese);}{Times New Roman;}{Times New Roman Cyr;}{Times New Roman Greek;}{Times New Roman Tur;}{Times New Roman (Hebrew);}{Times New Roman (Arabic);}{Times New Roman Baltic;}{Times New Roman (Vietnamese);}{Times New Roman;}{Times New Roman Cyr;}{Times New Roman Greek;}{Times New Roman Tur;}{Times New Roman (Hebrew);}{Times New Roman (Arabic);}{Times New Roman Baltic;}{Times New Roman (Vietnamese);}{Calibri;}{Calibri Cyr;}{Calibri Greek;}{Calibri Tur;}{Calibri (Hebrew);}{Calibri (Arabic);}{Calibri Baltic;}{Calibri (Vietnamese);}{Times New Roman;}{Times New Roman Cyr;}{Times New Roman Greek;}{Times New Roman Tur;}{Times New Roman (Hebrew);}{Times New Roman (Arabic);}{Times New Roman Baltic;}{Times New Roman (Vietnamese);} |
| Colortbl: | ;;;;;;;;;;;;;;;;;; |
| Defchp: | - |
| Defpap: | - |
| Stylesheet: | {Normal;}{*Default Paragraph Font;}{*Normal Table;}{Normal (Web);} |
| Pgptbl: | {} |
| Rsidtbl: | - |
| MmathPr: | - |
| Info: | {Windows User}{Windows User}{}{}{}{}{}{}{}{}{} |
| Xmlnstbl: | {http://schemas.microsoft.com/office/word/2003/wordml} |
| Wgrffmtfilter: | 2450 |
| Pnseclvl: | 9{(}{)} |
| Rtlch: | |
| Themedata: | 504b030414000600080000002100e9de0fbfff0000001c020000130000005b436f6e74656e745f54797065735d2e786d6cac91cb4ec3301045f748fc83e52d4a9cb2400825e982c78ec7a27cc0c8992416c9d8b2a755fbf74cd25442a820166c2cd933f79e3be372bd1f07b5c3989ca74aaff2422b24eb1b475da5df374fd9ad5689811a183c61a50f98f4babebc2837878049899a52a57be670674cb23d8e90721f90a4d2fa3802cb35762680fd800ecd7551dc18eb899138e3c943d7e503b6b01d583deee5f99824e290b4ba3f364eac4a430883b3c092d4eca8f946c916422ecab927f52ea42b89a1cd59c254f919b0e85e6535d135a8de20f20b8c12c3b00c895fcf6720192de6bf3b9e89ecdbd6596cbcdd8eb28e7c365ecc4ec1ff1460f53fe813d3cc7f5b7f020000ffff0300504b030414000600080000002100a5d6a7e7c0000000360100000b0000005f72656c732f2e72656c73848fcf6ac3300c87ef85bd83d17d51d2c31825762fa590432fa37d00e1287f68221bdb1bebdb4fc7060abb0884a4eff7a93dfeae8bf9e194e720169aaa06c3e2433fcb68e1763dbf7f82c985a4a725085b787086a37bdbb55fbc50d1a33ccd311ba548b63095120f88d94fbc52ae4264d1c910d24a45db3462247fa791715fd71f989e19e0364cd3f51652d73760ae8fa8c9ffb3c330cc9e4fc17faf2ce545046e37944c69e462a1a82fe353bd90a865aad41ed0b5b8f9d6fd010000ffff0300504b0304140006000800000021006b799616830000008a0000001c0000007468656d652f7468656d652f7468656d654d616e616765722e786d6c0ccc4d0ac3201040e17da17790d93763bb284562b2cbaebbf600439c1a41c7a0d29fdbd7e5e38337cedf14d59b4b0d592c9c070d8a65cd2e88b7f07c2ca71ba8da481cc52c6ce1c715e6e97818c9b48d13df49c873517d23d59085adb5dd20d6b52bd521ef2cdd5eb9246a3d8b4757e8d3f729e245eb2b260a0238fd010000ffff0300504b03041400060008000000210007b740aaca0600008f1a0000160000007468656d652f7468656d652f7468656d65312e786d6cec595b8bdb46147e2ff43f08bd3bbe49be2cf1065bb69336bb49889d943cceda636bb2238dd18c776342a0244f7d2914d2d28706fad687521a68a0a12ffd310b1bdaf447f4cc489667ec71f6420aa1640d8b34face996fce39face48ba7aed51449d239c70c2e2965bbe52721d1c8fd898c4d3967b6fd82f345c870b148f1165316eb90bccdd6bbb9f7e7215ed881047d801fb98efa0961b0a31db2916f9088611bfc26638866b13964448c069322d8e13740c7e235aac944ab5628448ec3a318ac0ededc9848cb033942edddda5f31e85d358703930a2c940bac68685c28e0fcb12c1173ca089738468cb8579c6ec78881f09d7a1880bb8d0724beacf2dee5e2da29dcc888a2db69a5d5ffd657699c1f8b0a2e64ca607f9a49ee77bb576ee5f01a8d8c4f5eabd5aaf96fb5300341ac14a532eba4fbfd3ec74fd0cab81d2438bef6ebd5b2d1b78cd7f758373db973f03af40a97f6f03dfef07104503af4029dedfc07b5ebd1278065e81527c6d035f2fb5bb5eddc02b5048497cb8812ef9b56ab05c6d0e99307ac30a6ffa5ebf5ec99caf50500d7975c929262c16db6a2d420f59d2078004522448ec88c50c4fd008aa3840941c24c4d923d3100a6f8662c661b85429f54b55f82f7f9e3a5211413b1869d6921730e11b43928fc34709998996fb39787535c8e9ebd7274f5f9d3cfdfde4d9b393a7bf66732b5786dd0d144f75bbb73f7df3cf8b2f9dbf7ffbf1edf36fd3a9d7f15cc7bff9e5ab377ffcf92ef7b0e255284ebf7bf9e6d5cbd3efbffeebe7e716efed041de8f0218930776ee163e72e8b608116fef820b998c5304444b768c7538e622467b1f8ef89d040df5a208a2cb80e36e3783f01a9b101afcf1f1a8407613217c4e2f1661819c07dc6688725d628dc947369611ecee3a97df264aee3ee2274649b3b40b191e5de7c061a4b6c2e83101b34ef50140b34c531168ebcc60e31b6acee0121465cf7c928619c4d84f380381d44ac21199203a39a56463748047959d80842be8dd8ecdf773a8cda56ddc5472612ee0d442de487981a61bc8ee6024536974314513de07b48843692834532d2713d2e20d3534c99d31b63ce6d36b71358af96f49b2033f6b4efd345642213410e6d3ef710633ab2cb0e831045331b7640e250c77ec60fa144917387091b7c9f9977883c873ca0786bbaef136ca4fb6c35b8070aab535a1588bc324f2cb9bc8e9951bf83059d20aca4061a80a1eb1189cf14f93579f7ff3b7907113dfde1856545ef47d2ed8e8d7c5c50ccdb09b1de4d37d6247c1b6e5db803968cc987afdb5d348fef60b855369bd747d9fe28dbeeff5eb6b7ddcfef5fac57fa0cd22db7ade9765d6ddea3ad7bf709a174201614ef71b57de7d095c67d189476eab915e7cf72b3100ee59d0c1318b86982948d9330f10511e1204433d8e3975de964ca33d753eecc1887adbf1ab6fa96783a8ff6d9387d642d97e5e3692a1e1c89d578c9cfc7e17143a4e85a7df51896bb576ca7ea71794940da5e8484369949a26a21515f0eca20a98773089a85845ad97b61d1b4b06848f7cb546db0006a795660dbe4c066abe5fa1e9880113c55218ac7324f69aa97d955c97c9f99de164ca302600fb1ac8055a69b92ebd6e5c9d5a5a5768e4c1b24b4723349a8c8a81ec64334c65975cad1f3d0b868ae9bab941af46428d47c505a2b1af5c6bb585c36d760b7ae0d34d69582c6ce71cbad557d2899119ab5dc093cfac3613483dae172bb8be814de9f8d4492def097519659c24517f1300db8129d540d222270e25012b55cb9fc3c0d34561aa2b8952b20081f2cb926c8ca87460e926e26194f267824f4b46b2332d2e929287caa15d6abcafcf26069c9e690ee41383e760ee83cb98ba0c4fc7a5906704c38bc012aa7d11c1378a5990bd9aafed61a5326bbfa3b455543e938a2b310651d4517f314aea43ca7a3cef2186867d99a21a05a48b2467830950d560faad14df3ae9172d8da75cf369291d34473d5330d55915dd3ae62c60ccb36b016cbcb35798dd532c4a0697a874fa57b5d729b4bad5bdb27e45d02029ec7cfd275cfd110346aabc90c6a92f1a60c4bcdce46cddeb15ce019d4ced32434d5af2dddaec52def11d6e960f0529d1fecd6ab168626cb7da58ab4faf6a17f9e60070f413cbaf022784e0557a9848f0f09820dd140ed4952d9805be491c86e0d3872e60969b98f4b7edb0b2a7e502835fc5ec1ab7aa542c36f570b6ddfaf967b7eb9d4ed549e4063116154f6d3ef2e7d780d4517d9d71735bef105265abe69bb32625191a92f2c45455c7d812957b67f81710888cee35aa5dfac363bb542b3daee17bc6ea7516806b54ea15b0beadd7e37f01bcdfe13d7395260af5d0dbc5aaf51a89583a0e0d54a927ea359a87b954adbabb71b3daffd24dbc6c0ca53f9c86201e155bc76ff050000ffff0300504b0304140006000800000021000dd1909fb60000001b010000270000007468656d652f7468656d652f5f72656c732f7468656d654d616e616765722e786d6c2e72656c73848f4d0ac2301484f78277086f6fd3ba109126dd88d0add40384e4350d363f2451eced0dae2c082e8761be9969bb979dc9136332de3168aa1a083ae995719ac16db8ec8e4052164e89d93b64b060828e6f37ed1567914b284d262452282e3198720e274a939cd08a54f980ae38a38f56e422a3a641c8bbd048f7757da0f19b017cc524bd62107bd5001996509affb3fd381a89672f1f165dfe514173d9850528a2c6cce0239baa4c04ca5bbabac4df000000ffff0300504b01022d0014000600080000002100e9de0fbfff0000001c0200001300000000000000000000000000000000005b436f6e74656e745f54797065735d2e786d6c504b01022d0014000600080000002100a5d6a7e7c0000000360100000b00000000000000000000000000300100005f72656c732f2e72656c73504b01022d00140006000800000021006b799616830000008a0000001c00000000000000000000000000190200007468656d652f7468656d652f7468656d654d616e616765722e786d6c504b01022d001400060008000000210007b740aaca0600008f1a00001600000000000000000000000000d60200007468656d652f7468656d652f7468656d65312e786d6c504b01022d00140006000800000021000dd1909fb60000001b0100002700000000000000000000000000d40900007468656d652f7468656d652f5f72656c732f7468656d654d616e616765722e786d6c2e72656c73504b050600000000050005005d010000cf0a00000000 |
| Colorschememapping: | 3c3f786d6c2076657273696f6e3d22312e302220656e636f64696e673d225554462d3822207374616e64616c6f6e653d22796573223f3e0d0a3c613a636c724d617020786d6c6e733a613d22687474703a2f2f736368656d61732e6f70656e786d6c666f726d6174732e6f72672f64726177696e676d6c2f323030362f6d61696e22206267313d226c743122207478313d22646b3122206267323d226c743222207478323d22646b322220616363656e74313d22616363656e74312220616363656e74323d22616363656e74322220616363656e74333d22616363656e74332220616363656e74343d22616363656e74342220616363656e74353d22616363656e74352220616363656e74363d22616363656e74362220686c696e6b3d22686c696e6b2220666f6c486c696e6b3d22666f6c486c696e6b222f3e |
| Latentstyles: | {Normal;heading 1;heading 2;heading 3;heading 4;heading 5;heading 6;heading 7;heading 8;heading 9;index 1;index 2;index 3;index 4;index 5;index 6;index 7;index 8;index 9;toc 1;toc 2;toc 3;toc 4;toc 5;toc 6;toc 7;toc 8;toc 9;Normal Indent;footnote text;annotation text;header;footer;index heading;caption;table of figures;envelope address;envelope return;footnote reference;annotation reference;line number;page number;endnote reference;endnote text;table of authorities;macro;toa heading;List;List Bullet;List Number;List 2;List 3;List 4;List 5;List Bullet 2;List Bullet 3;List Bullet 4;List Bullet 5;List Number 2;List Number 3;List Number 4;List Number 5;Title;Closing;Signature;Default Paragraph Font;Body Text;Body Text Indent;List Continue;List Continue 2;List Continue 3;List Continue 4;List Continue 5;Message Header;Subtitle;Salutation;Date;Body Text First Indent;Body Text First Indent 2;Note Heading;Body Text 2;Body Text 3;Body Text Indent 2;Body Text Indent 3;Block Text;Hyperlink;FollowedHyperlink;Strong;Emphasis;Document Map;Plain Text;E-mail Signature;HTML Top of Form;HTML Bottom of Form;Normal (Web);HTML Acronym;HTML Address;HTML Cite;HTML Code;HTML Definition;HTML Keyboard;HTML Preformatted;HTML Sample;HTML Typewriter;HTML Variable;Normal Table;annotation subject;No List;Outline List 1;Outline List 2;Outline List 3;Table Simple 1;Table Simple 2;Table Simple 3;Table Classic 1;Table Classic 2;Table Classic 3;Table Classic 4;Table Colorful 1;Table Colorful 2;Table Colorful 3;Table Columns 1;Table Columns 2;Table Columns 3;Table Columns 4;Table Columns 5;Table Grid 1;Table Grid 2;Table Grid 3;Table Grid 4;Table Grid 5;Table Grid 6;Table Grid 7;Table Grid 8;Table List 1;Table List 2;Table List 3;Table List 4;Table List 5;Table List 6;Table List 7;Table List 8;Table 3D effects 1;Table 3D effects 2;Table 3D effects 3;Table Contemporary;Table Elegant;Table Professional;Table Subtle 1;Table Subtle 2;Table Web 1;Table Web 2;Table Web 3;Balloon Text;Table Grid;Table Theme;Placeholder Text;No Spacing;Light Shading;Light List;Light Grid;Medium Shading 1;Medium Shading 2;Medium List 1;Medium List 2;Medium Grid 1;Medium Grid 2;Medium Grid 3;Dark List;Colorful Shading;Colorful List;Colorful Grid;Light Shading Accent 1;Light List Accent 1;Light Grid Accent 1;Medium Shading 1 Accent 1;Medium Shading 2 Accent 1;Medium List 1 Accent 1;Revision;List Paragraph;Quote;Intense Quote;Medium List 2 Accent 1;Medium Grid 1 Accent 1;Medium Grid 2 Accent 1;Medium Grid 3 Accent 1;Dark List Accent 1;Colorful Shading Accent 1;Colorful List Accent 1;Colorful Grid Accent 1;Light Shading Accent 2;Light List Accent 2;Light Grid Accent 2;Medium Shading 1 Accent 2;Medium Shading 2 Accent 2;Medium List 1 Accent 2;Medium List 2 Accent 2;Medium Grid 1 Accent 2;Medium Grid 2 Accent 2;Medium Grid 3 Accent 2;Dark List Accent 2;Colorful Shading Accent 2;Colorful List Accent 2;Colorful Grid Accent 2;Light Shading Accent 3;Light List Accent 3;Light Grid Accent 3;Medium Shading 1 Accent 3;Medium Shading 2 Accent 3;Medium List 1 Accent 3;Medium List 2 Accent 3;Medium Grid 1 Accent 3;Medium Grid 2 Accent 3;Medium Grid 3 Accent 3;Dark List Accent 3;Colorful Shading Accent 3;Colorful List Accent 3;Colorful Grid Accent 3;Light Shading Accent 4;Light List Accent 4;Light Grid Accent 4;Medium Shading 1 Accent 4;Medium Shading 2 Accent 4;Medium List 1 Accent 4;Medium List 2 Accent 4;Medium Grid 1 Accent 4;Medium Grid 2 Accent 4;Medium Grid 3 Accent 4;Dark List Accent 4;Colorful Shading Accent 4;Colorful List Accent 4;Colorful Grid Accent 4;Light Shading Accent 5;Light List Accent 5;Light Grid Accent 5;Medium Shading 1 Accent 5;Medium Shading 2 Accent 5;Medium List 1 Accent 5;Medium List 2 Accent 5;Medium Grid 1 Accent 5;Medium Grid 2 Accent 5;Medium Grid 3 Accent 5;Dark List Accent 5;Colorful Shading Accent 5;Colorful List Accent 5;Colorful Grid Accent 5;Light Shading Accent 6;Light List Accent 6;Light Grid Accent 6;Medium Shading 1 Accent 6;Medium Shading 2 Accent 6;Medium List 1 Accent 6;Medium List 2 Accent 6;Medium Grid 1 Accent 6;Medium Grid 2 Accent 6;Medium Grid 3 Accent 6;Dark List Accent 6;Colorful Shading Accent 6;Colorful List Accent 6;Colorful Grid Accent 6;Subtle Emphasis;Intense Emphasis;Subtle Reference;Intense Reference;Book Title;Bibliography;TOC Heading;Plain Table 1;Plain Table 2;Plain Table 3;Plain Table 4;Plain Table 5;Grid Table Light;Grid Table 1 Light;Grid Table 2;Grid Table 3;Grid Table 4;Grid Table 5 Dark;Grid Table 6 Colorful;Grid Table 7 Colorful;Grid Table 1 Light Accent 1;Grid Table 2 Accent 1;Grid Table 3 Accent 1;Grid Table 4 Accent 1;Grid Table 5 Dark Accent 1;Grid Table 6 Colorful Accent 1;Grid Table 7 Colorful Accent 1;Grid Table 1 Light Accent 2;Grid Table 2 Accent 2;Grid Table 3 Accent 2;Grid Table 4 Accent 2;Grid Table 5 Dark Accent 2;Grid Table 6 Colorful Accent 2;Grid Table 7 Colorful Accent 2;Grid Table 1 Light Accent 3;Grid Table 2 Accent 3;Grid Table 3 Accent 3;Grid Table 4 Accent 3;Grid Table 5 Dark Accent 3;Grid Table 6 Colorful Accent 3;Grid Table 7 Colorful Accent 3;Grid Table 1 Light Accent 4;Grid Table 2 Accent 4;Grid Table 3 Accent 4;Grid Table 4 Accent 4;Grid Table 5 Dark Accent 4;Grid Table 6 Colorful Accent 4;Grid Table 7 Colorful Accent 4;Grid Table 1 Light Accent 5;Grid Table 2 Accent 5;Grid Table 3 Accent 5;Grid Table 4 Accent 5;Grid Table 5 Dark Accent 5;Grid Table 6 Colorful Accent 5;Grid Table 7 Colorful Accent 5;Grid Table 1 Light Accent 6;Grid Table 2 Accent 6;Grid Table 3 Accent 6;Grid Table 4 Accent 6;Grid Table 5 Dark Accent 6;Grid Table 6 Colorful Accent 6;Grid Table 7 Colorful Accent 6;List Table 1 Light;List Table 2;List Table 3;List Table 4;List Table 5 Dark;List Table 6 Colorful;List Table 7 Colorful;List Table 1 Light Accent 1;List Table 2 Accent 1;List Table 3 Accent 1;List Table 4 Accent 1;List Table 5 Dark Accent 1;List Table 6 Colorful Accent 1;List Table 7 Colorful Accent 1;List Table 1 Light Accent 2;List Table 2 Accent 2;List Table 3 Accent 2;List Table 4 Accent 2;List Table 5 Dark Accent 2;List Table 6 Colorful Accent 2;List Table 7 Colorful Accent 2;List Table 1 Light Accent 3;List Table 2 Accent 3;List Table 3 Accent 3;List Table 4 Accent 3;List Table 5 Dark Accent 3;List Table 6 Colorful Accent 3;List Table 7 Colorful Accent 3;List Table 1 Light Accent 4;List Table 2 Accent 4;List Table 3 Accent 4;List Table 4 Accent 4;List Table 5 Dark Accent 4;List Table 6 Colorful Accent 4;List Table 7 Colorful Accent 4;List Table 1 Light Accent 5;List Table 2 Accent 5;List Table 3 Accent 5;List Table 4 Accent 5;List Table 5 Dark Accent 5;List Table 6 Colorful Accent 5;List Table 7 Colorful Accent 5;List Table 1 Light Accent 6;List Table 2 Accent 6;List Table 3 Accent 6;List Table 4 Accent 6;List Table 5 Dark Accent 6;List Table 6 Colorful Accent 6;List Table 7 Colorful Accent 6;} |
| Datastore: | 0105000002000000180000004d73786d6c322e534158584d4c5265616465722e362e3000000000000000000000060000d0cf11e0a1b11ae1000000000000000000000000000000003e000300feff090006000000000000000000000001000000010000000000000000100000feffffff00000000feffffff0000000000000000fffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffdfffffffeffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffff52006f006f007400200045006e00740072007900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000016000500ffffffffffffffffffffffff0c6ad98892f1d411a65f0040963251e500000000000000000000000000e6de274db3d401feffffff00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000ffffffffffffffffffffffff0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000ffffffffffffffffffffffff0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000ffffffffffffffffffffffff0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000105000000000000 |
Total processes
33
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2736 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\840d3f868afd706706f46beb7d9cf63dfda4f9adf9af2dc0b4d3dd471fd38819.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3076 | "C:\Users\admin\AppData\Local\4.exe" | C:\Users\admin\AppData\Local\4.exe | 4.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3456 | "C:\Users\admin\AppData\Local\4.exe" | C:\Users\admin\AppData\Local\4.exe | EQNEDT32.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3548 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
672
Read events
634
Write events
37
Delete events
1
Modification events
| (PID) Process: | (2736) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2<$ |
Value: 323C2400B00A0000010000000000000000000000 | |||
| (PID) Process: | (2736) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2736) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2736) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1313538078 | |||
| (PID) Process: | (2736) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313538192 | |||
| (PID) Process: | (2736) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313538193 | |||
| (PID) Process: | (2736) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B00A0000B6BE189AA9C1D40100000000 | |||
| (PID) Process: | (2736) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8=$ |
Value: 383D2400B00A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2736) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 8=$ |
Value: 383D2400B00A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2736) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
4
Suspicious files
0
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8802.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{6B26F1C4-EAFF-4501-9D65-2F185DD4AD84}.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | 4.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 2736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$0d3f868afd706706f46beb7d9cf63dfda4f9adf9af2dc0b4d3dd471fd38819.doc.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3548 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@bit[1].txt | text | |
MD5:— | SHA256:— | |||
| 2736 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3456 | 4.exe | C:\Users\admin\AppData\Local\Macromedia\StikyNot.exe | executable | |
MD5:— | SHA256:— | |||
| 3076 | 4.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.hdb | text | |
MD5:— | SHA256:— | |||
| 3076 | 4.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.exe | executable | |
MD5:— | SHA256:— | |||
| 3548 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\4.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
3
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3548 | EQNEDT32.EXE | GET | 200 | 202.170.69.9:80 | http://nationallibrary.mn/nm/enterw/zee.jpg | MN | executable | 672 Kb | malicious |
3548 | EQNEDT32.EXE | GET | 301 | 67.199.248.10:80 | http://bit.ly/2UV2As7 | US | html | 130 b | shared |
3076 | 4.exe | POST | — | 185.126.200.154:80 | http://kichitov.xyz/ret/five/fre.php | IR | — | — | malicious |
3076 | 4.exe | POST | — | 185.126.200.154:80 | http://kichitov.xyz/ret/five/fre.php | IR | — | — | malicious |
3076 | 4.exe | POST | — | 185.126.200.154:80 | http://kichitov.xyz/ret/five/fre.php | IR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3548 | EQNEDT32.EXE | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
3548 | EQNEDT32.EXE | 202.170.69.9:80 | nationallibrary.mn | Bodicom ISP Ulaanbaatar | MN | malicious |
3076 | 4.exe | 185.126.200.154:80 | kichitov.xyz | Tebyan-e-Noor Cultural-Artistic Institute | IR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bit.ly |
| shared |
nationallibrary.mn |
| malicious |
kichitov.xyz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3548 | EQNEDT32.EXE | A Network Trojan was detected | MALWARE [PTsecurity] PowerShell.Downloader httpHeader |
3548 | EQNEDT32.EXE | A Network Trojan was detected | ET TROJAN JS/WSF Downloader Dec 08 2016 M4 |
3548 | EQNEDT32.EXE | A Network Trojan was detected | ET TROJAN Windows Executable Downloaded With Image Content-Type Header |
3548 | EQNEDT32.EXE | Misc activity | SUSPICIOUS [PTsecurity] PE as Image Content type mismatch |
3076 | 4.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3076 | 4.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3076 | 4.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3076 | 4.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3076 | 4.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3076 | 4.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
5 ETPRO signatures available at the full report