| File name: | Resize.exe |
| Full analysis: | https://app.any.run/tasks/14cde9df-350c-4a05-9765-811dc9e186fa |
| Verdict: | No threats detected |
| Analysis date: | July 16, 2018, 15:48:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BB4E40B3364E63D3FEDE06C0F5C47B7A |
| SHA1: | C1CDCE4D47BBFA97EDEC860432B952DCCF83D887 |
| SHA256: | 840930CACE8C5FD0DFD7BDB3F35A6378A37ADBC9A48D8901CCEC2401CA785B71 |
| SSDEEP: | 393216:+z75QyFfHRyLehKUzoRDxA7jMtH1BZM4zzwSP:M7lTE3h |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Internet Cache Settings
- Resize.exe (PID: 3672)
Creates files in the user directory
- Resize.exe (PID: 3672)
Starts MSHTA.EXE for opening HTA or HTMLS files
- Resize.exe (PID: 3672)
INFO
Dropped object may contain URL's
- Resize.exe (PID: 3672)
- mshta.exe (PID: 3896)
Reads internet explorer settings
- mshta.exe (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (50.3) |
|---|---|---|
| .exe | | | InstallShield setup (19.7) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19) |
| .scr | | | Windows screen saver (6) |
| .exe | | | Win32 Executable (generic) (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:08:26 11:25:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 10440704 |
| InitializedDataSize: | 2647040 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9f5a58 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.7.3.1 |
| ProductVersionNumber: | 4.7.3.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
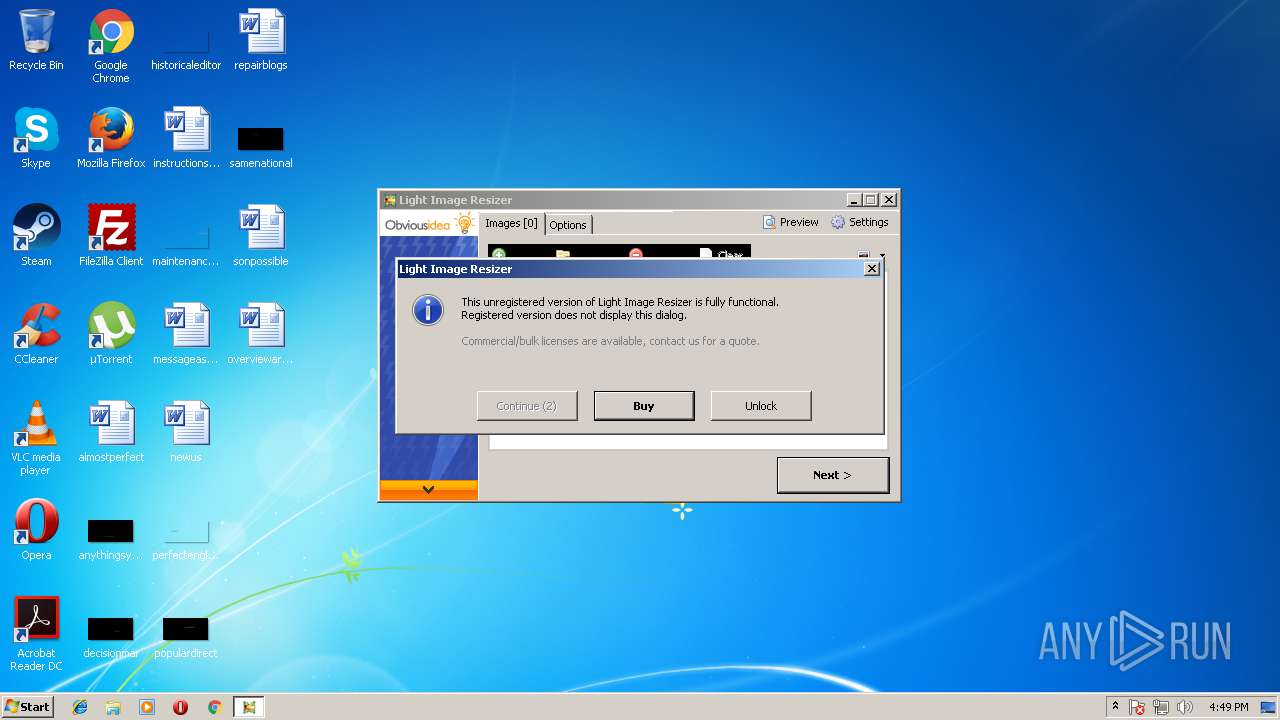
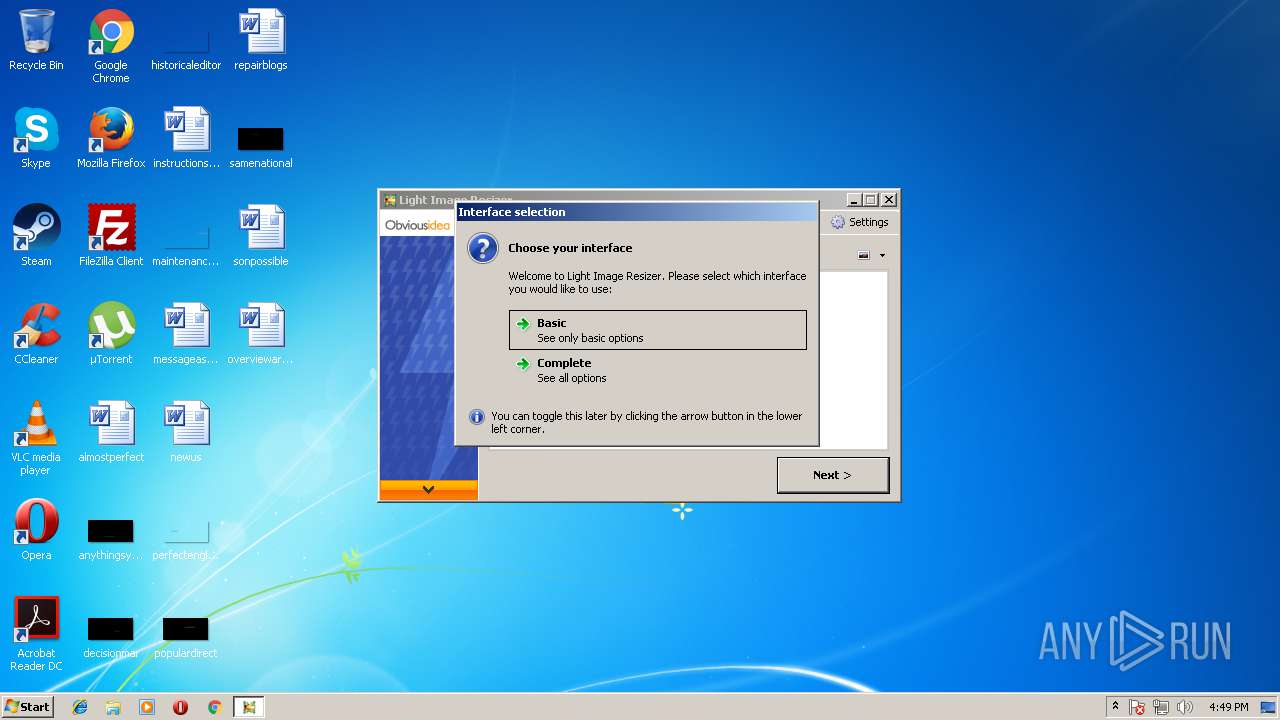
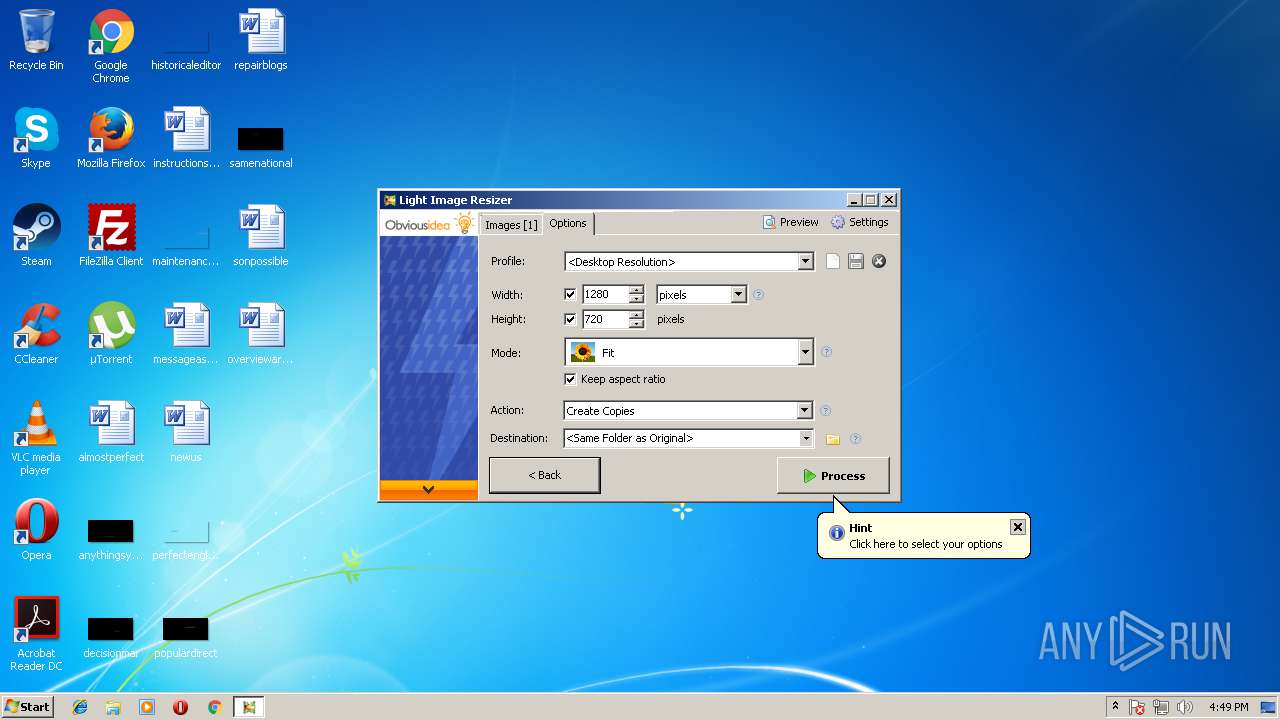
| CompanyName: | ObviousIdea SARL |
| FileDescription: | Light Image Resizer |
| FileVersion: | 4.7.3.1 |
| InternalName: | resizer |
| LegalCopyright: | Copyright © 2011-2015 ObviousIdea SARL |
| LegalTrademarks: | - |
| OriginalFileName: | resizer.exe |
| ProductName: | Light Image Resizer |
| ProductVersion: | 4.0.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Aug-2015 09:25:02 |
| Detected languages: |
|
| CompanyName: | ObviousIdea SARL |
| FileDescription: | Light Image Resizer |
| FileVersion: | 4.7.3.1 |
| InternalName: | resizer |
| LegalCopyright: | Copyright © 2011-2015 ObviousIdea SARL |
| LegalTrademarks: | - |
| OriginalFilename: | resizer.exe |
| ProductName: | Light Image Resizer |
| ProductVersion: | 4.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 26-Aug-2015 09:25:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x009EECD8 | 0x009EEE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47018 |
.itext | 0x009F0000 | 0x00006140 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.24676 |
.data | 0x009F7000 | 0x000B5598 | 0x000B5600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.64525 |
.bss | 0x00AAD000 | 0x000CABF8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00B78000 | 0x0000BE84 | 0x0000C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.42087 |
.didata | 0x00B84000 | 0x0000049A | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.24184 |
.edata | 0x00B85000 | 0x000002ED | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.40367 |
.tls | 0x00B86000 | 0x00000258 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00B87000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.214733 |
.reloc | 0x00B88000 | 0x000AA7A8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29343 | 1679 | UNKNOWN | German - Germany | RT_MANIFEST |
2 | 4.31472 | 872 | UNKNOWN | German - Germany | RT_ICON |
3 | 7.9656 | 77336 | UNKNOWN | German - Germany | RT_ICON |
4 | 5.95379 | 9640 | UNKNOWN | German - Germany | RT_ICON |
5 | 6.31459 | 4264 | UNKNOWN | German - Germany | RT_ICON |
6 | 6.48429 | 2440 | UNKNOWN | German - Germany | RT_ICON |
7 | 6.51368 | 1128 | UNKNOWN | German - Germany | RT_ICON |
8 | 1.49923 | 748 | UNKNOWN | German - Germany | RT_CURSOR |
9 | 1.45949 | 748 | UNKNOWN | German - Germany | RT_CURSOR |
10 | 1.81975 | 748 | UNKNOWN | German - Germany | RT_CURSOR |
Imports
Advapi32.dll |
GDI32.DLL |
Kernel32.dll |
MsVfW32.dll |
advapi32.dll |
avifil32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
gdiplus.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
EurekaLog_LastDelphiException | 1 | 0x000C85A4 |
EurekaLog_CallCreateThread | 2 | 0x000C85AC |
EurekaLog_CallResumeThread | 3 | 0x000C8640 |
EurekaLog_CallExitThread | 4 | 0x000C86E4 |
EurekaLog_CallExceptObject | 5 | 0x000C7D08 |
EurekaLog_CallGeneralRaise | 6 | 0x000C7B74 |
ExceptionManager | 7 | 0x000C9FB8 |
EurekaLog_PasswordRequestEvent | 8 | 0x000AA7D4 |
EurekaLog_PasswordRequestEventEx | 9 | 0x000AA81C |
EurekaLog_ExceptionNotifyEvent | 10 | 0x000AA8F0 |
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3672 | "C:\Users\admin\AppData\Local\Temp\Resize.exe" | C:\Users\admin\AppData\Local\Temp\Resize.exe | explorer.exe | ||||||||||||
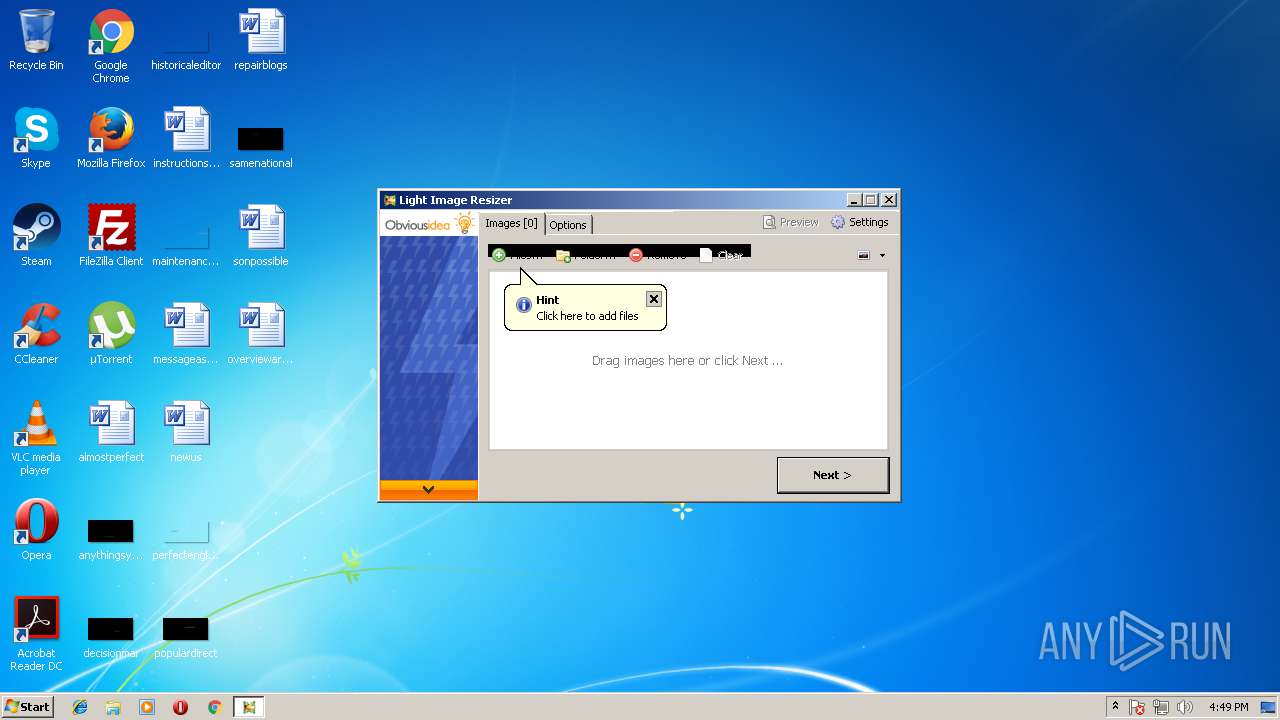
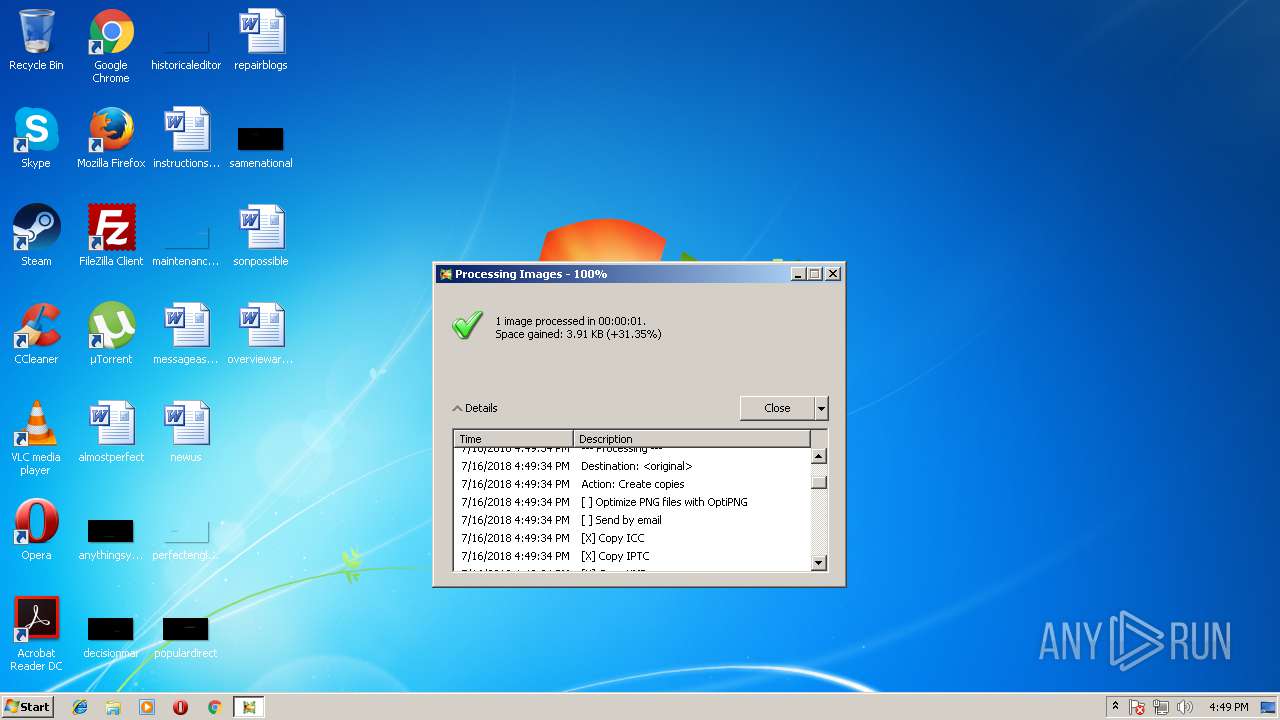
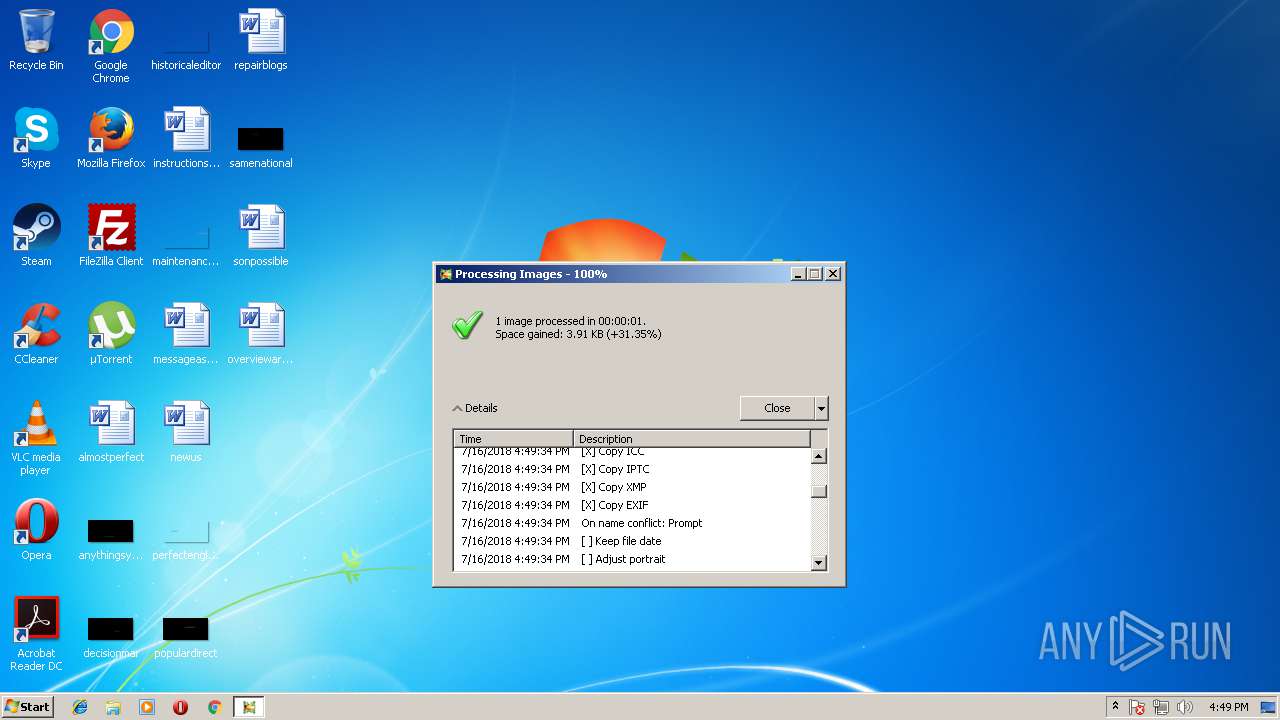
User: admin Company: ObviousIdea SARL Integrity Level: MEDIUM Description: Light Image Resizer Exit code: 0 Version: 4.7.3.1 Modules
| |||||||||||||||
| 3896 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\AppData\Local\Temp\lirpopup.hta" | C:\Windows\System32\mshta.exe | Resize.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
769
Read events
613
Write events
155
Delete events
1
Modification events
| (PID) Process: | (3672) Resize.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | vga.drv 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
| (PID) Process: | (3672) Resize.exe | Key: | HKEY_CURRENT_USER\Software\ObviousIdea\ImageResizer\ShellExt |
| Operation: | write | Name: | HelpText |
Value: Process selected files with Light Image Resizer | |||
| (PID) Process: | (3672) Resize.exe | Key: | HKEY_CURRENT_USER\Software\ObviousIdea\ImageResizer\ShellExt |
| Operation: | write | Name: | Submenu_Name |
Value: Quick Profile | |||
| (PID) Process: | (3672) Resize.exe | Key: | HKEY_CURRENT_USER\Software\ObviousIdea\ImageResizer\ShellExt |
| Operation: | write | Name: | Submenu_HelpText |
Value: Direct access to selected profiles | |||
| (PID) Process: | (3672) Resize.exe | Key: | HKEY_CURRENT_USER\Software\ObviousIdea\ImageResizer\4.0 |
| Operation: | write | Name: | FirstRunDate |
Value: 7DEBD76D3624E540 | |||
| (PID) Process: | (3672) Resize.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Resize_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3672) Resize.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Resize_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3672) Resize.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Resize_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3672) Resize.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Resize_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3672) Resize.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Resize_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
0
Text files
61
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | Resize.exe | C:\Users\admin\Pictures\WRITETST.TMP | — | |
MD5:— | SHA256:— | |||
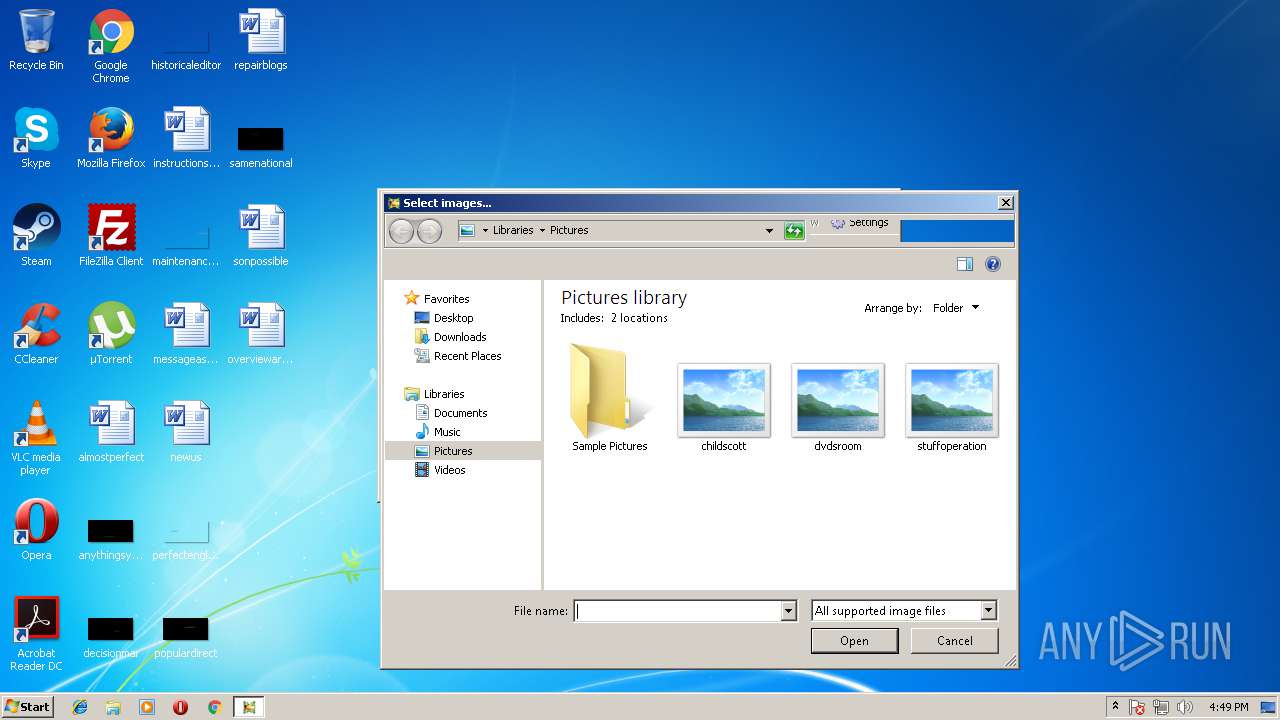
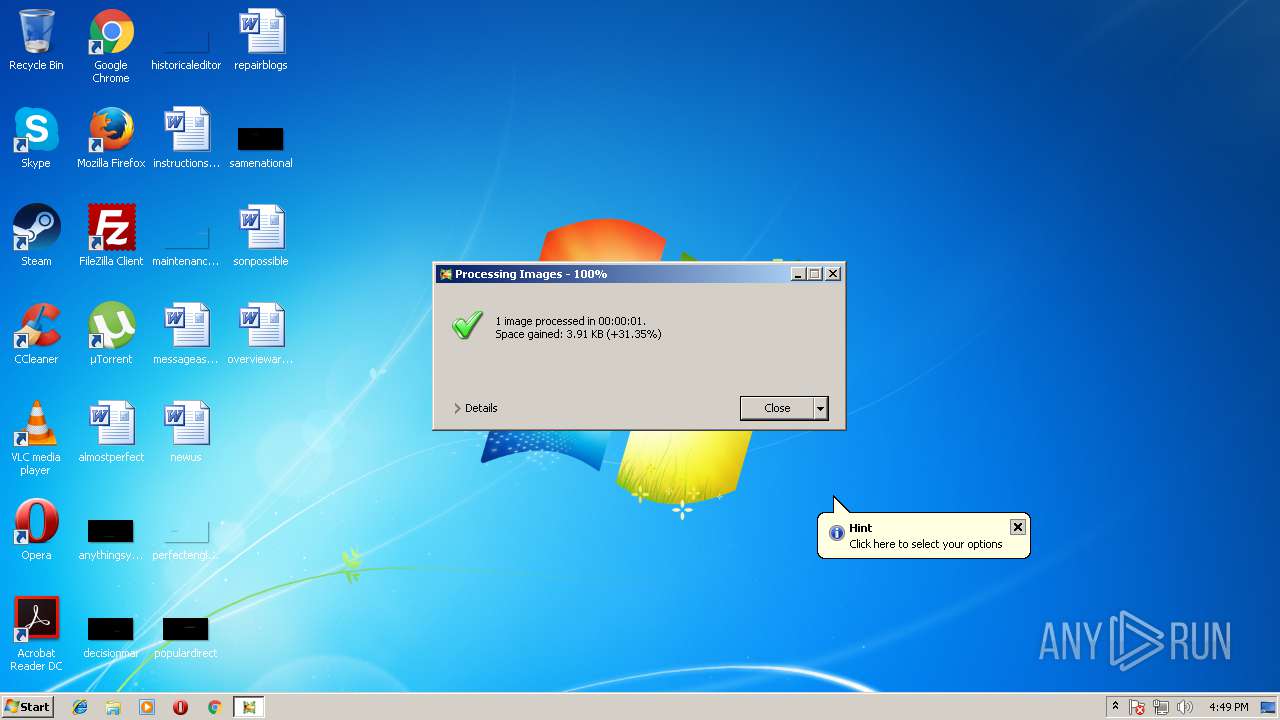
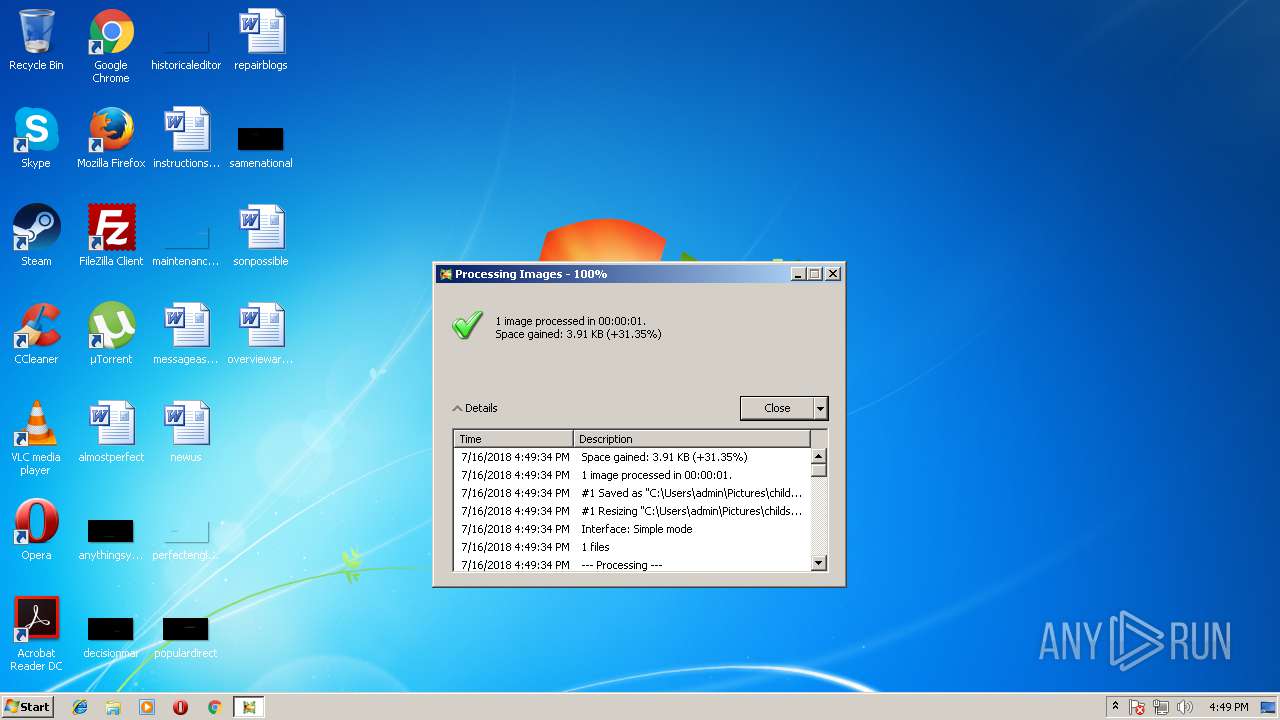
| 3672 | Resize.exe | C:\Users\admin\Pictures\childscott (Copy).jpg | image | |
MD5:— | SHA256:— | |||
| 3672 | Resize.exe | C:\Users\admin\AppData\Local\Temp\lirpopup.hta | html | |
MD5:— | SHA256:— | |||
| 3672 | Resize.exe | C:\Users\admin\AppData\Roaming\ObviousIdea\ImageResizer.log | text | |
MD5:— | SHA256:— | |||
| 3896 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\XB3OCR2W\twitter[1].png | image | |
MD5:— | SHA256:— | |||
| 3672 | Resize.exe | C:\Users\admin\AppData\Roaming\ObviousIdea\ImageResizer_crash_PID3672.log | text | |
MD5:— | SHA256:— | |||
| 3896 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GUFVP8I9\buy[1].png | image | |
MD5:0F533FEB96A72DCAC329EE0AD2DD032D | SHA256:676173E65687F1EECA8FE0C3770DA039024898925F402E60D4B1E08DFBDCFBDC | |||
| 3896 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\NBLQPZGH\google[1].png | image | |
MD5:— | SHA256:— | |||
| 3896 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\paypal_btn_en[1].gif | image | |
MD5:— | SHA256:— | |||
| 3896 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\XB3OCR2W\lir[1].php | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | mshta.exe | GET | 200 | 62.210.215.13:80 | http://support.obviousidea.com/popup/paypal_btn_en.gif | FR | image | 2.76 Kb | suspicious |
3896 | mshta.exe | GET | 200 | 62.210.215.13:80 | http://support.obviousidea.com/popup/google.png | FR | image | 1.05 Kb | suspicious |
3896 | mshta.exe | GET | 200 | 62.210.215.13:80 | http://support.obviousidea.com/popup/twitter.png | FR | image | 1.22 Kb | suspicious |
3672 | Resize.exe | GET | 200 | 62.210.215.13:80 | http://support.obviousidea.com/generateEvent.php?cat=LightImageResizer&act=FileExt&lbl=.jpg&val=1&lng=en&sig=e8d793103d6c87b6da99596304659c4d | FR | text | 2 b | suspicious |
3672 | Resize.exe | GET | 200 | 62.210.215.13:80 | http://support.obviousidea.com/generateEvent.php?cat=LightImageResizer&act=ProcessedImages&lbl=1&val=1&lng=en&sig=fd90f7081413b4f70297c5d1fdb66188 | FR | text | 2 b | suspicious |
3896 | mshta.exe | GET | 200 | 62.210.215.13:80 | http://support.obviousidea.com/popup/lir_banner.png | FR | image | 93.8 Kb | suspicious |
3896 | mshta.exe | GET | 200 | 62.210.215.13:80 | http://support.obviousidea.com/popup/facebook.png | FR | image | 1.06 Kb | suspicious |
3896 | mshta.exe | GET | 200 | 62.210.215.13:80 | http://support.obviousidea.com/popup/buy.png | FR | image | 325 b | suspicious |
3896 | mshta.exe | GET | 200 | 62.210.215.13:80 | http://support.obviousidea.com/popup/bullet.png | FR | image | 677 b | suspicious |
3672 | Resize.exe | GET | 200 | 62.210.215.13:80 | http://support.obviousidea.com/generateEvent.php?cat=LightImageResizer&act=DaysUsed&lbl=0&val=0&lng=en&sig=c95da01d41b0d092d95ff3194b635609 | FR | text | 2 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3672 | Resize.exe | 62.210.215.13:80 | support.obviousidea.com | Online S.a.s. | FR | unknown |
3896 | mshta.exe | 62.210.215.13:80 | support.obviousidea.com | Online S.a.s. | FR | unknown |
3896 | mshta.exe | 216.58.215.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
support.obviousidea.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
dns.msftncsi.com |
| shared |