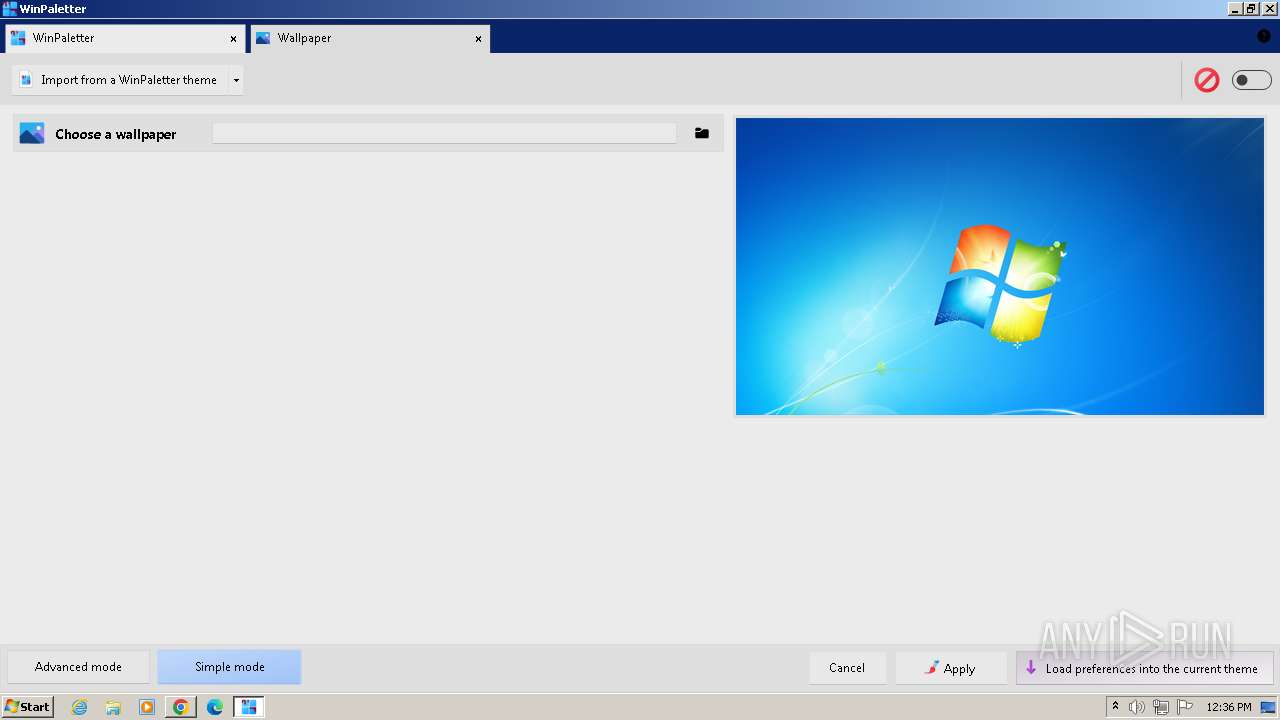
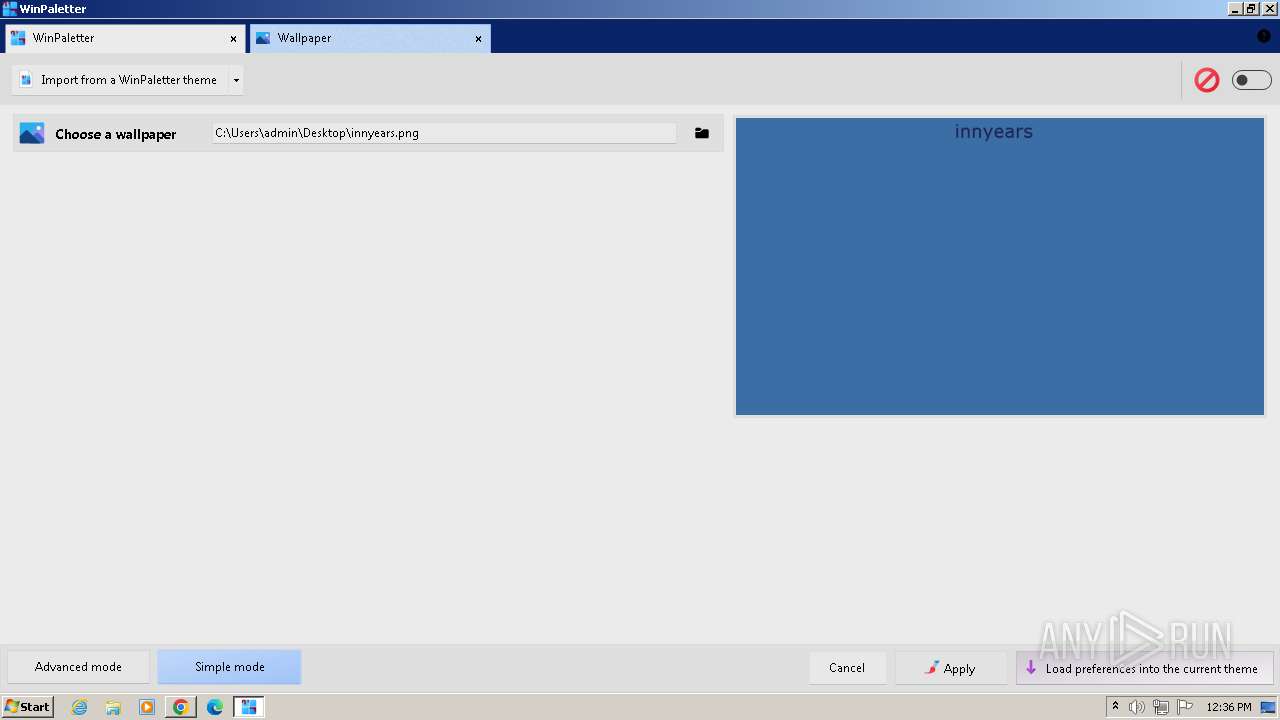
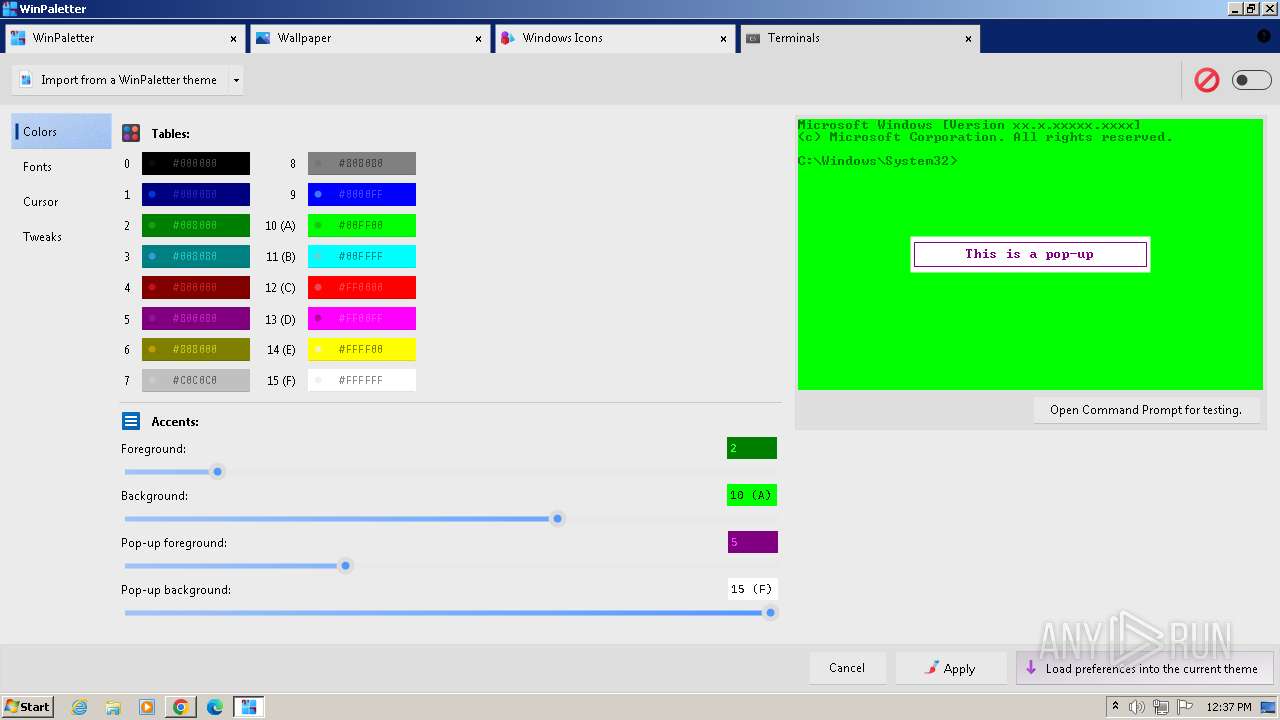
| File name: | WinPaletter.exe |
| Full analysis: | https://app.any.run/tasks/2642117a-58a6-4f91-8e76-2574122f213f |
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2024, 11:32:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 26780DADF3AC28B87FC619E710ACC548 |
| SHA1: | BE26D8737F4B551EED11E0C6620EED2164B8AF47 |
| SHA256: | 8405E6341640123A7D8ACA7886C6A98AADF9E7A1B75B5962CD4C186D8AF3F2C4 |
| SSDEEP: | 98304:XLcbtdahlQyVGuAjguadaDVfPdgOkFySRyEnnknnnO2GGymfDuDQqov9Bfkqv7nt:7m8L66HaAtk |
MALICIOUS
Drops the executable file immediately after the start
- WinPaletter.exe (PID: 4084)
SUSPICIOUS
Reads the Internet Settings
- WinPaletter.exe (PID: 4084)
Reads security settings of Internet Explorer
- WinPaletter.exe (PID: 4084)
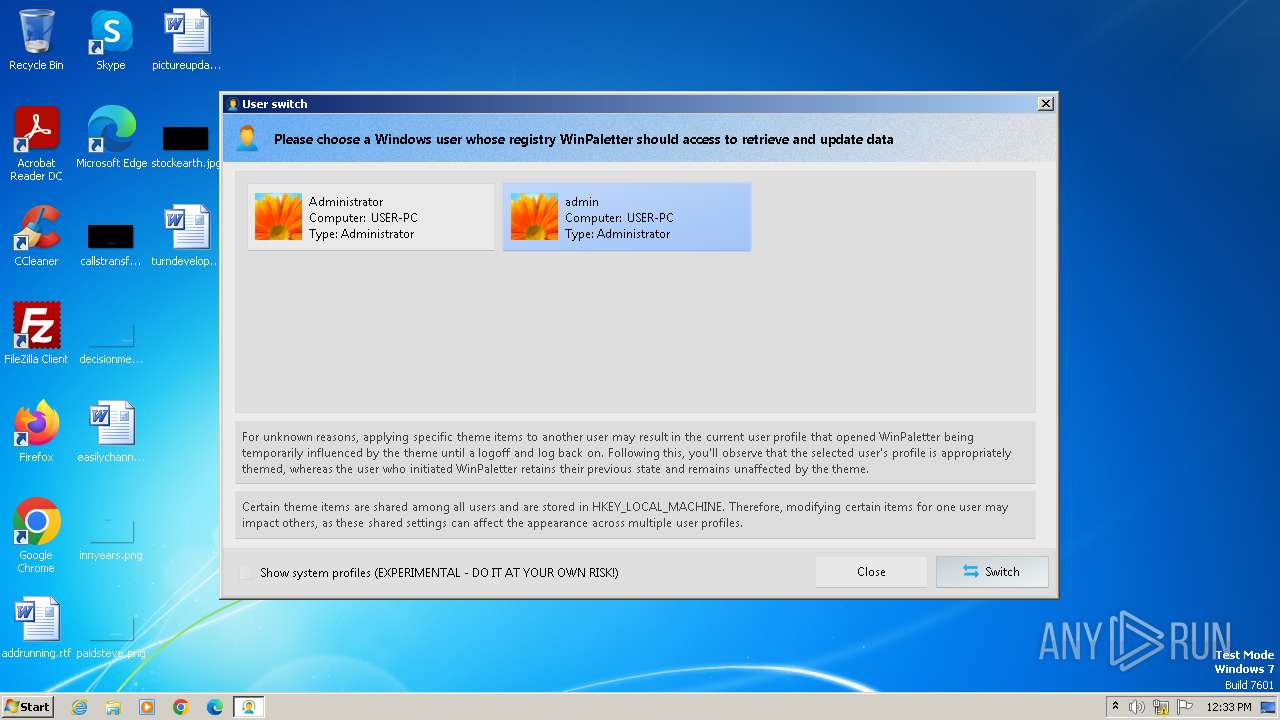
Uses REG/REGEDIT.EXE to modify registry
- WinPaletter.exe (PID: 4084)
Reads the Windows owner or organization settings
- WinPaletter.exe (PID: 4084)
Executable content was dropped or overwritten
- WinPaletter.exe (PID: 4084)
Creates a software uninstall entry
- WinPaletter.exe (PID: 4084)
Searches for installed software
- WinPaletter.exe (PID: 4084)
Reads settings of System Certificates
- WinPaletter.exe (PID: 4084)
Adds/modifies Windows certificates
- WinPaletter.exe (PID: 4084)
Reads Internet Explorer settings
- WinPaletter.exe (PID: 4084)
INFO
Checks supported languages
- WinPaletter.exe (PID: 4084)
- wmpnscfg.exe (PID: 2012)
Reads the computer name
- WinPaletter.exe (PID: 4084)
- wmpnscfg.exe (PID: 2012)
Reads the machine GUID from the registry
- WinPaletter.exe (PID: 4084)
Reads Environment values
- WinPaletter.exe (PID: 4084)
Creates files in the program directory
- WinPaletter.exe (PID: 4084)
Reads CPU info
- WinPaletter.exe (PID: 4084)
Create files in a temporary directory
- WinPaletter.exe (PID: 4084)
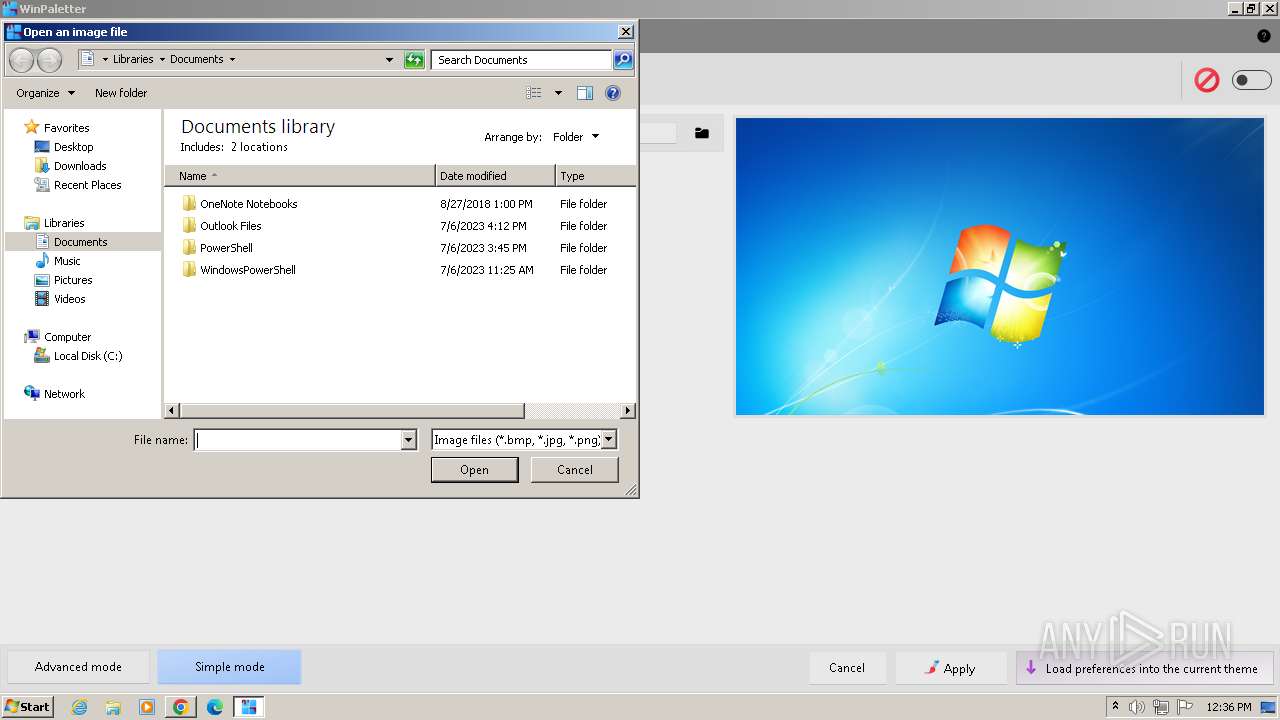
Creates files or folders in the user directory
- WinPaletter.exe (PID: 4084)
Checks proxy server information
- WinPaletter.exe (PID: 4084)
Reads the software policy settings
- WinPaletter.exe (PID: 4084)
Manual execution by a user
- wmpnscfg.exe (PID: 2012)
- chrome.exe (PID: 2472)
Application launched itself
- chrome.exe (PID: 2472)
The process uses the downloaded file
- chrome.exe (PID: 4076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2046:05:08 11:12:47+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 9516032 |
| InitializedDataSize: | 193024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x915126 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
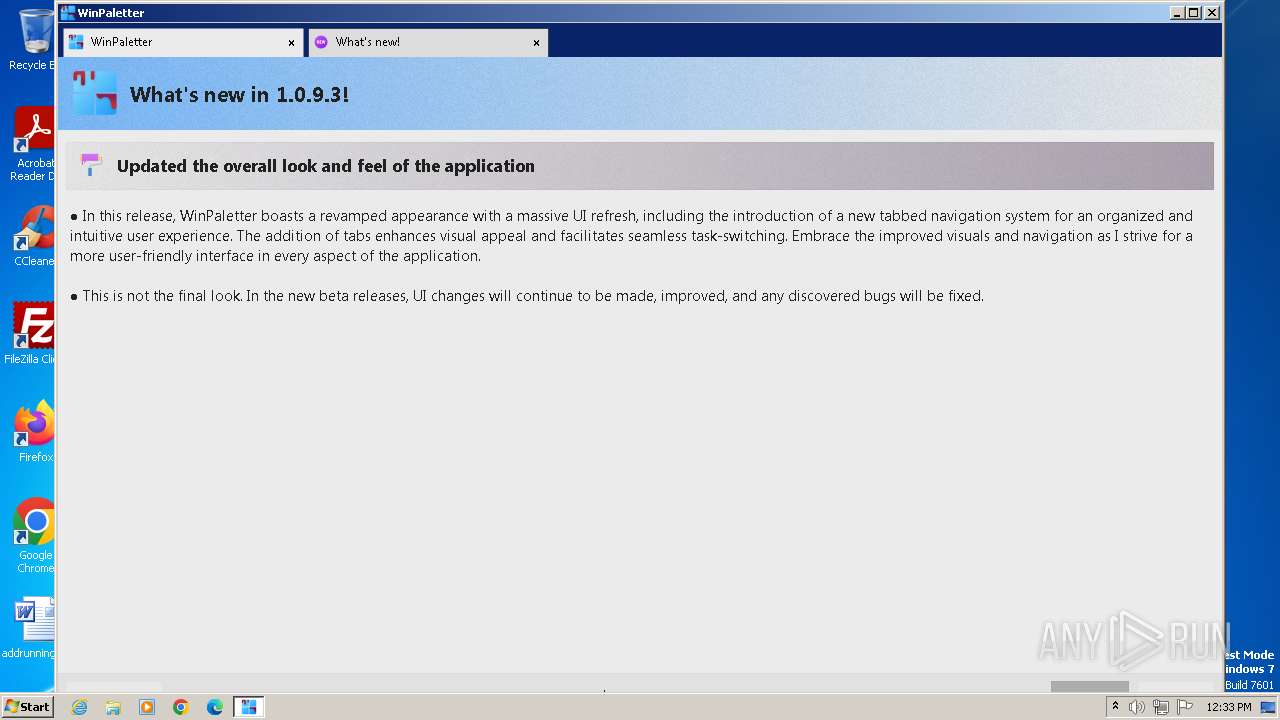
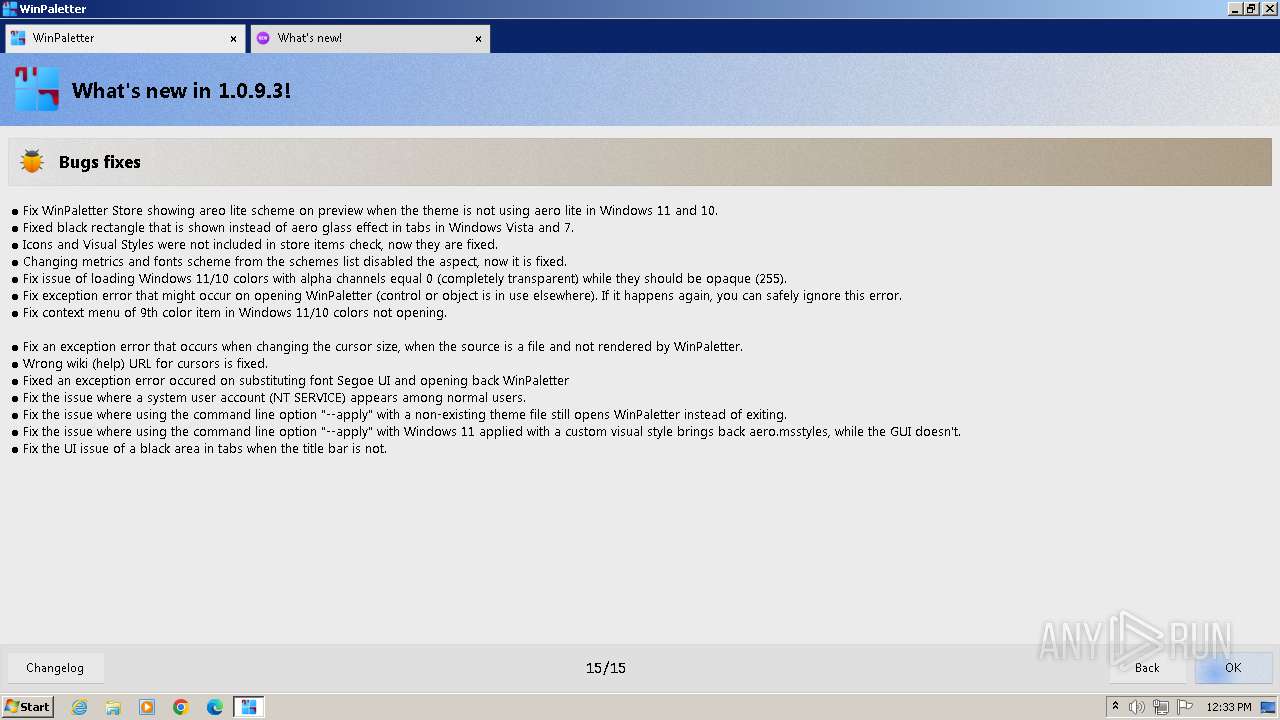
| FileVersionNumber: | 1.0.9.3 |
| ProductVersionNumber: | 1.0.9.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
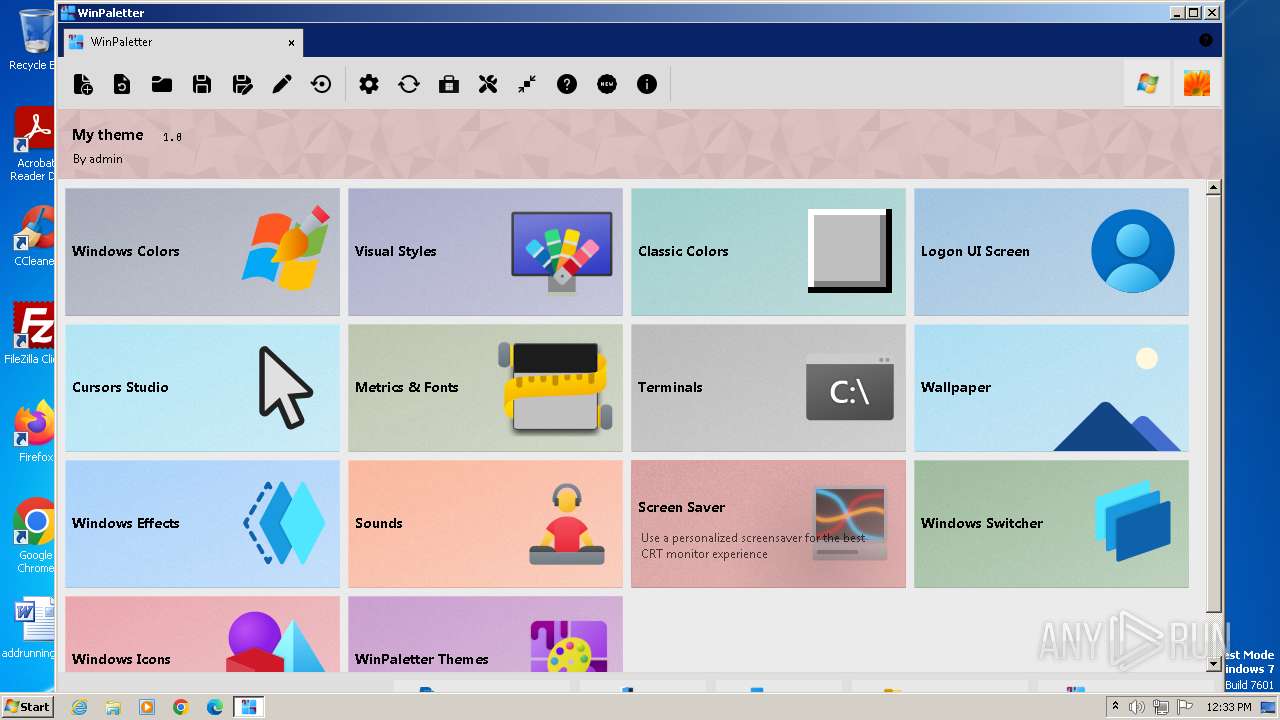
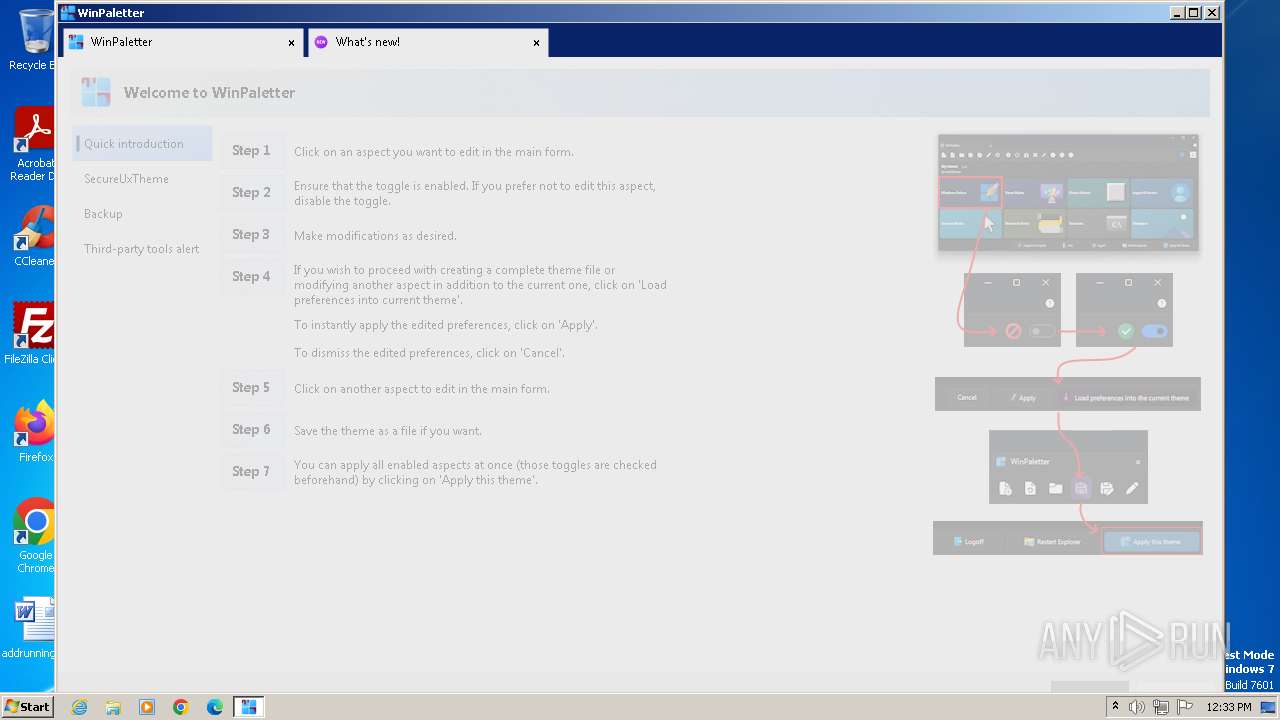
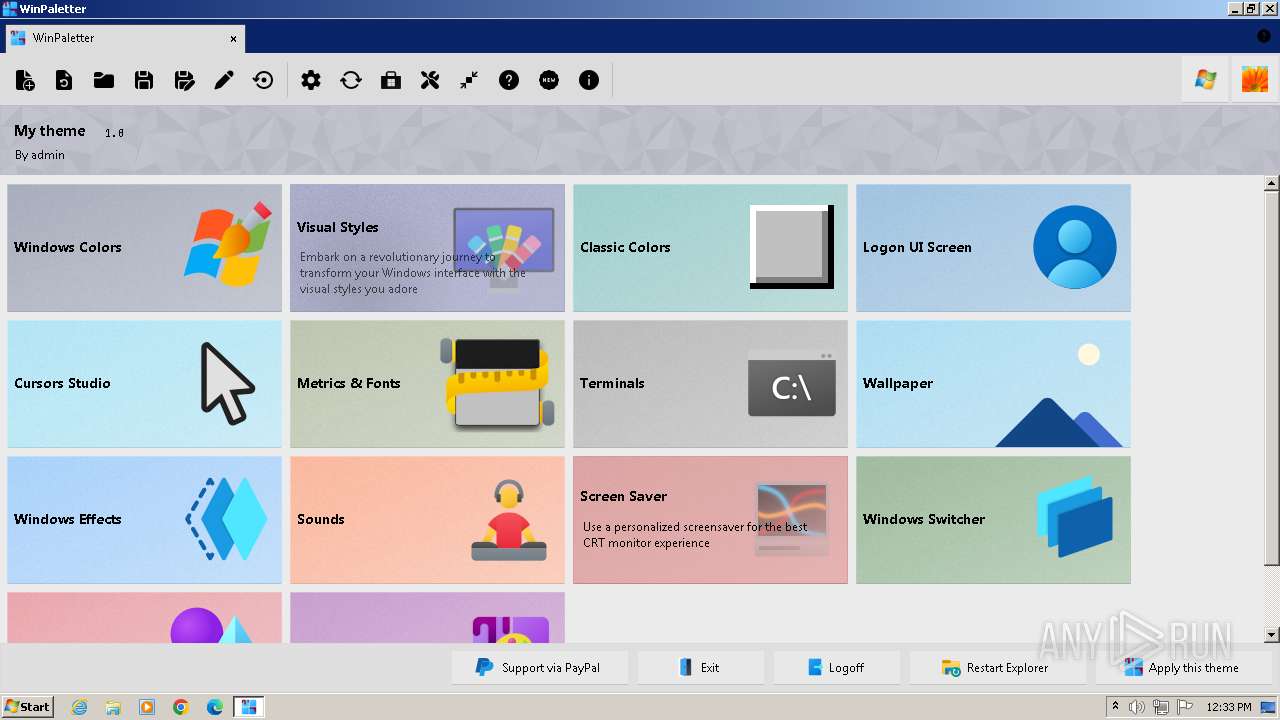
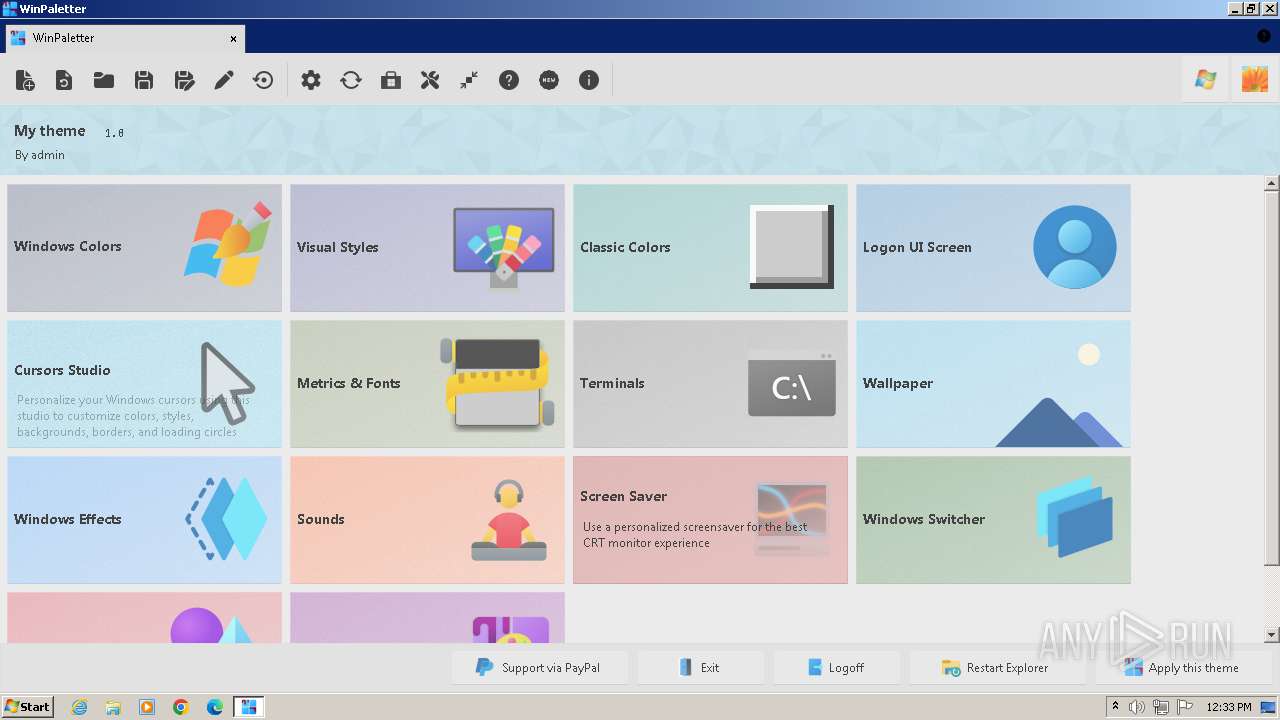
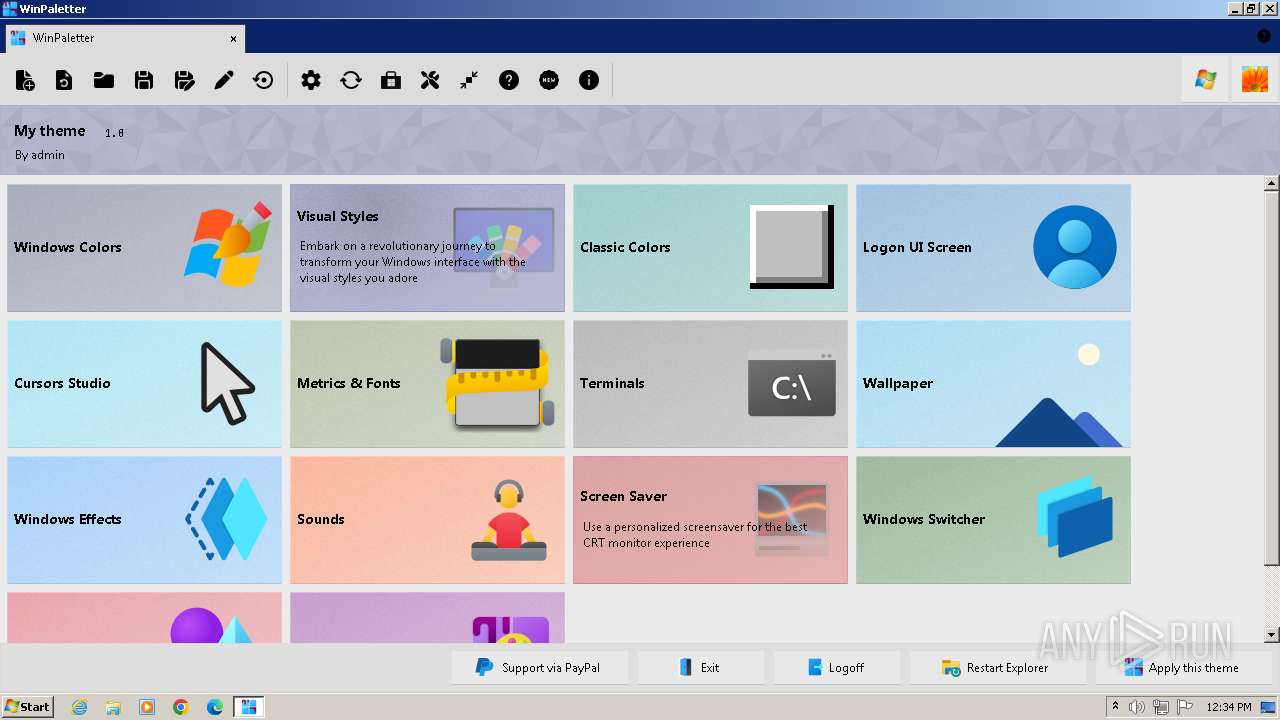
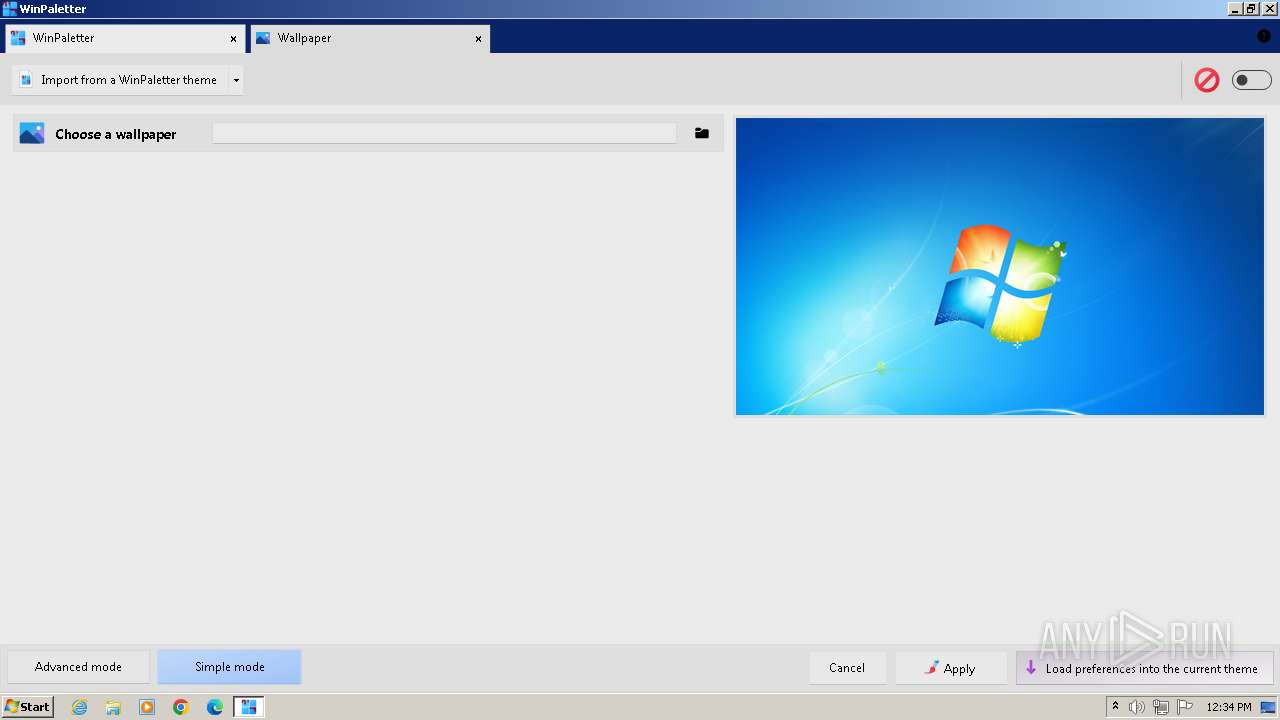
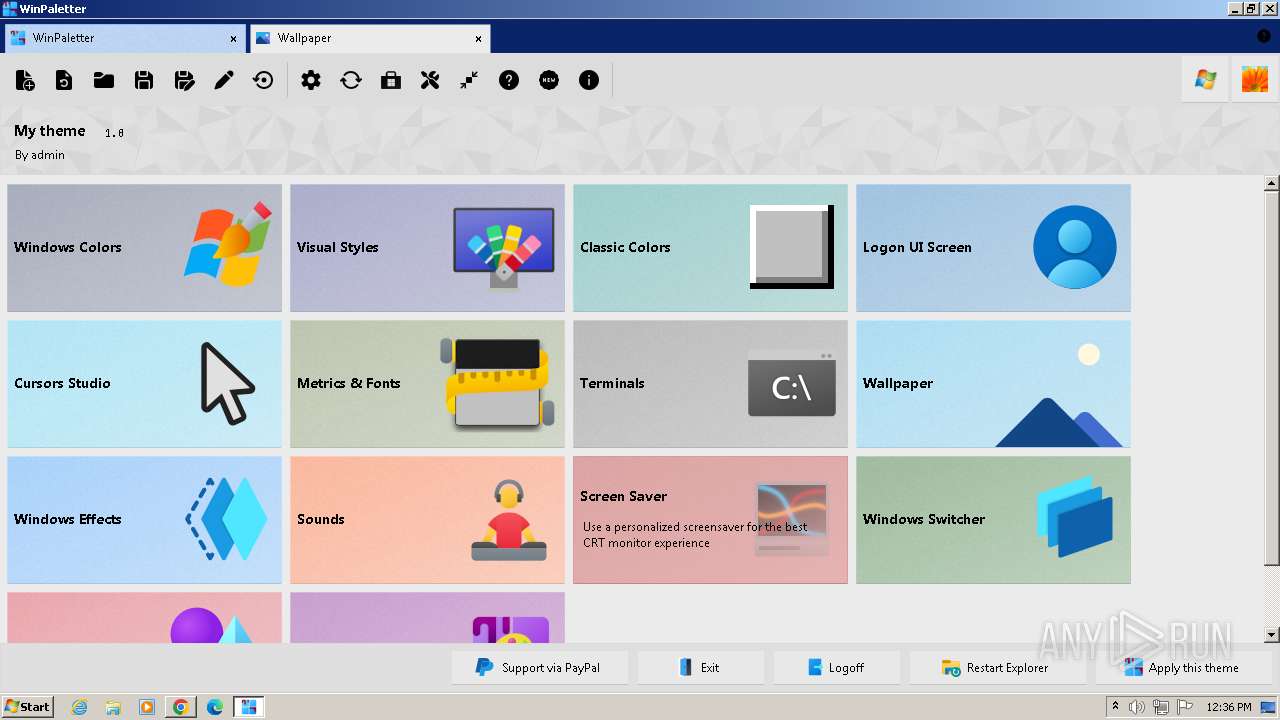
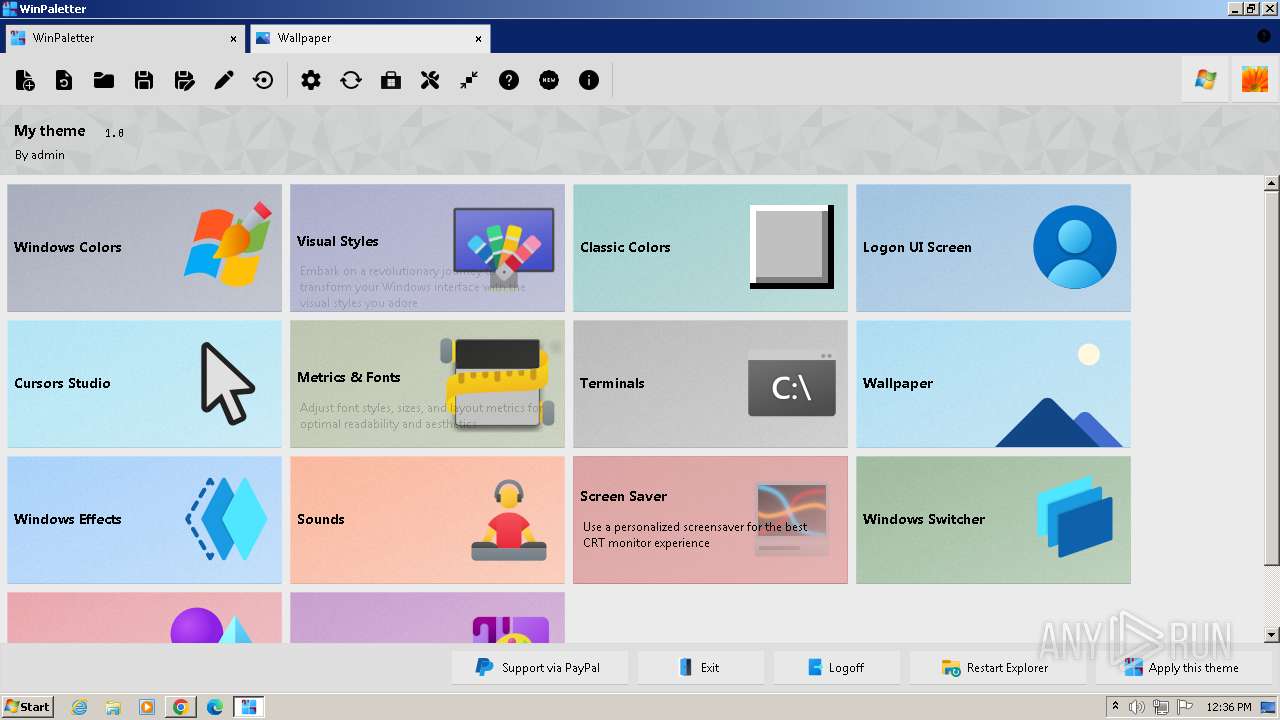
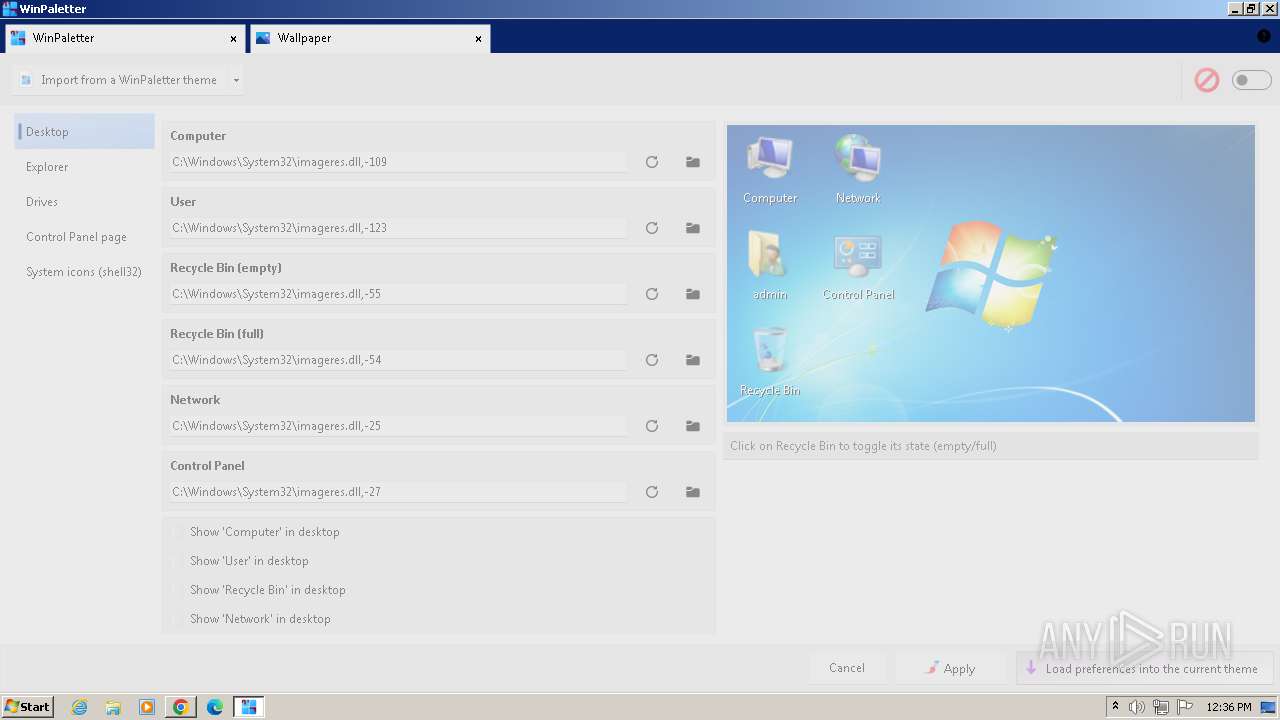
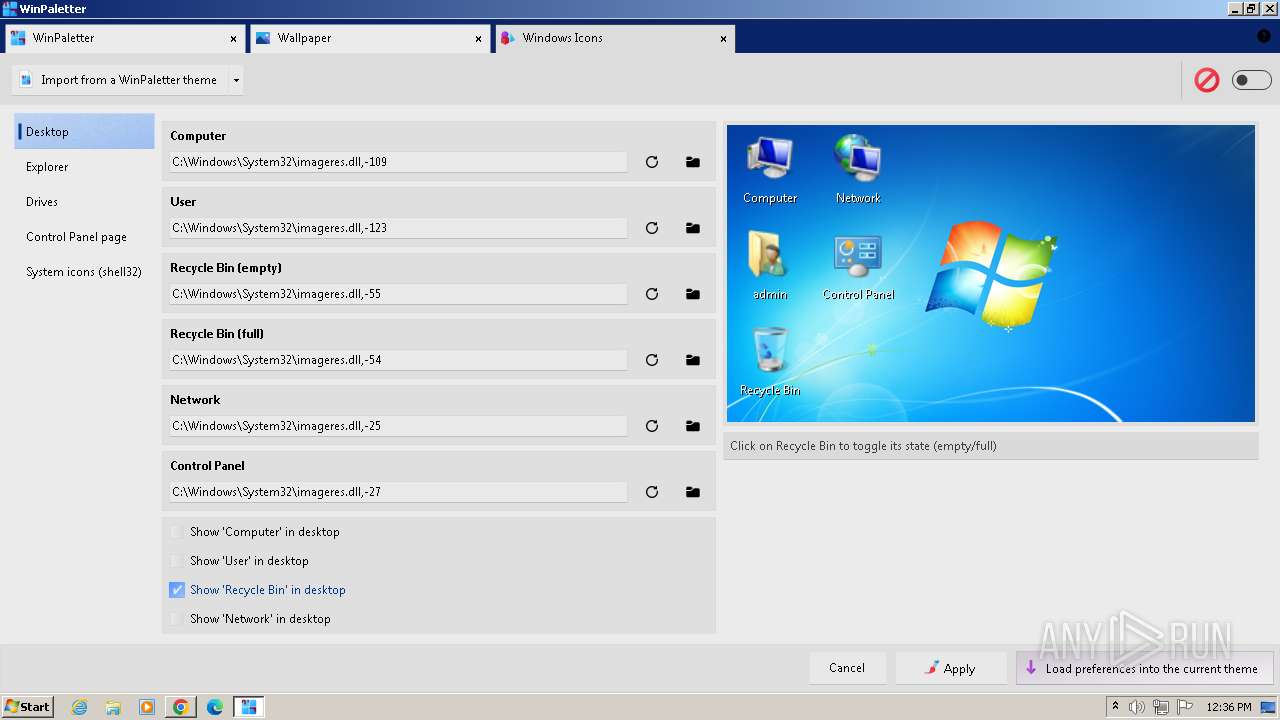
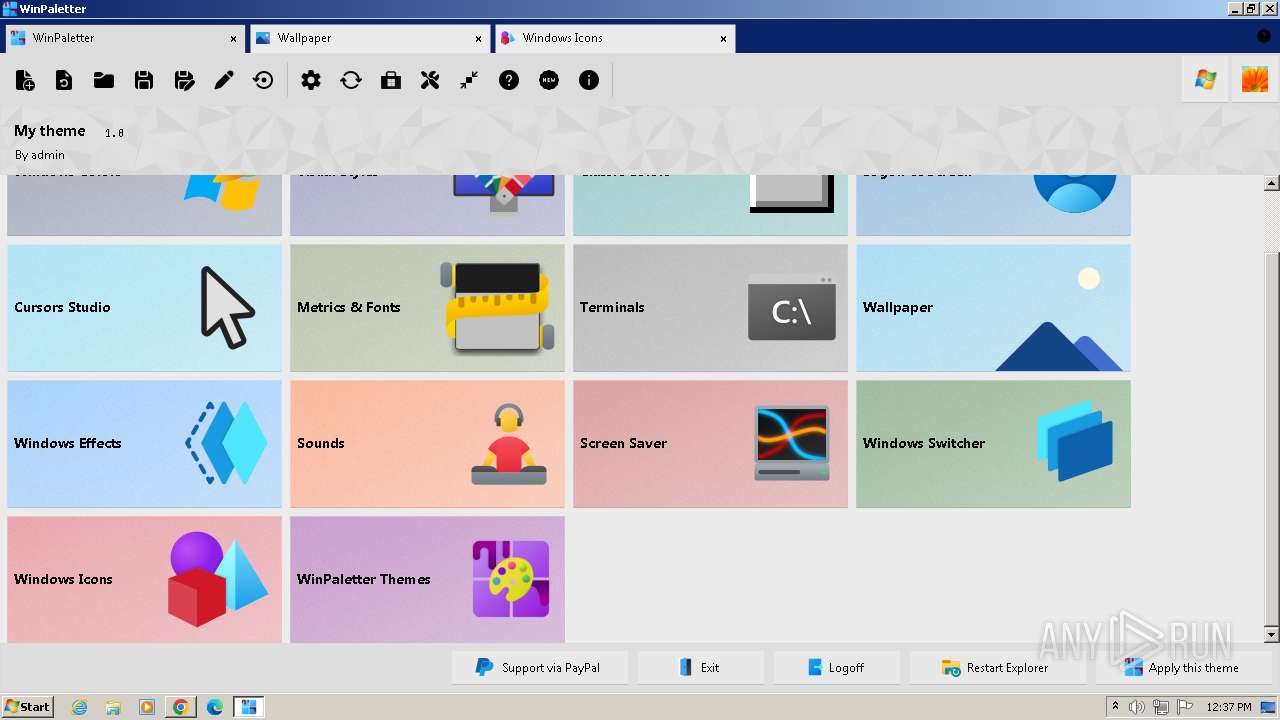
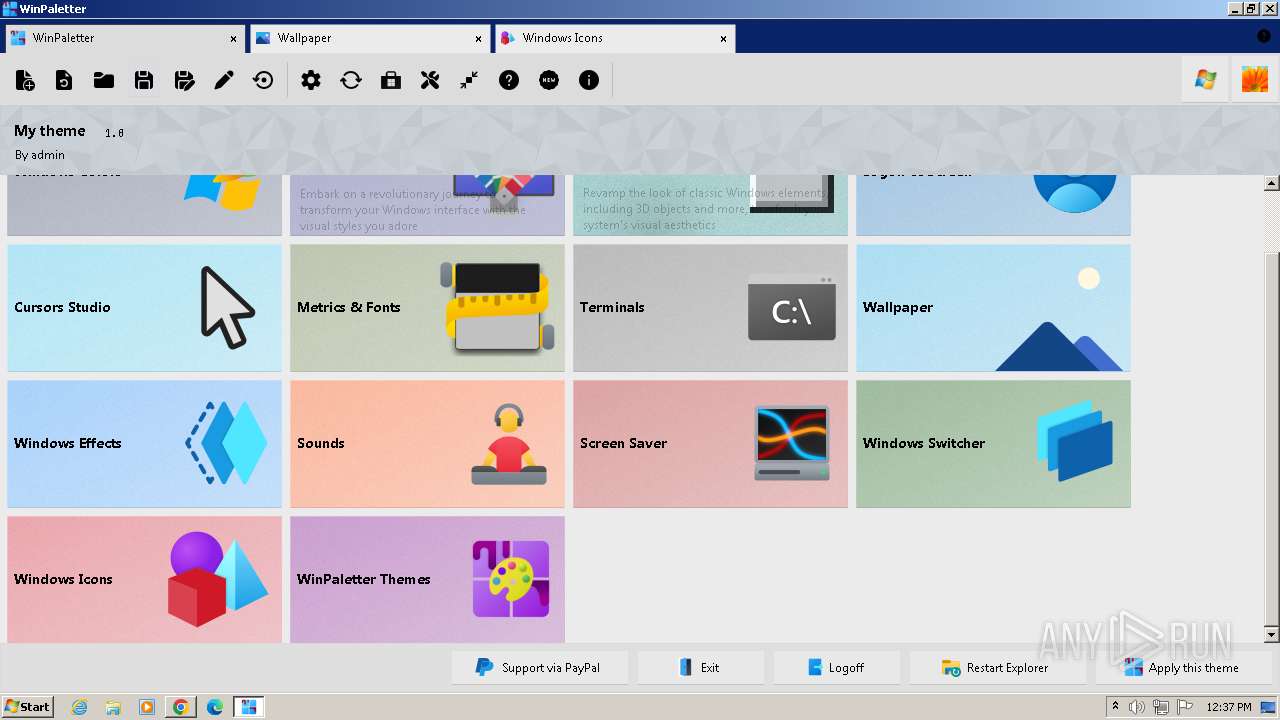
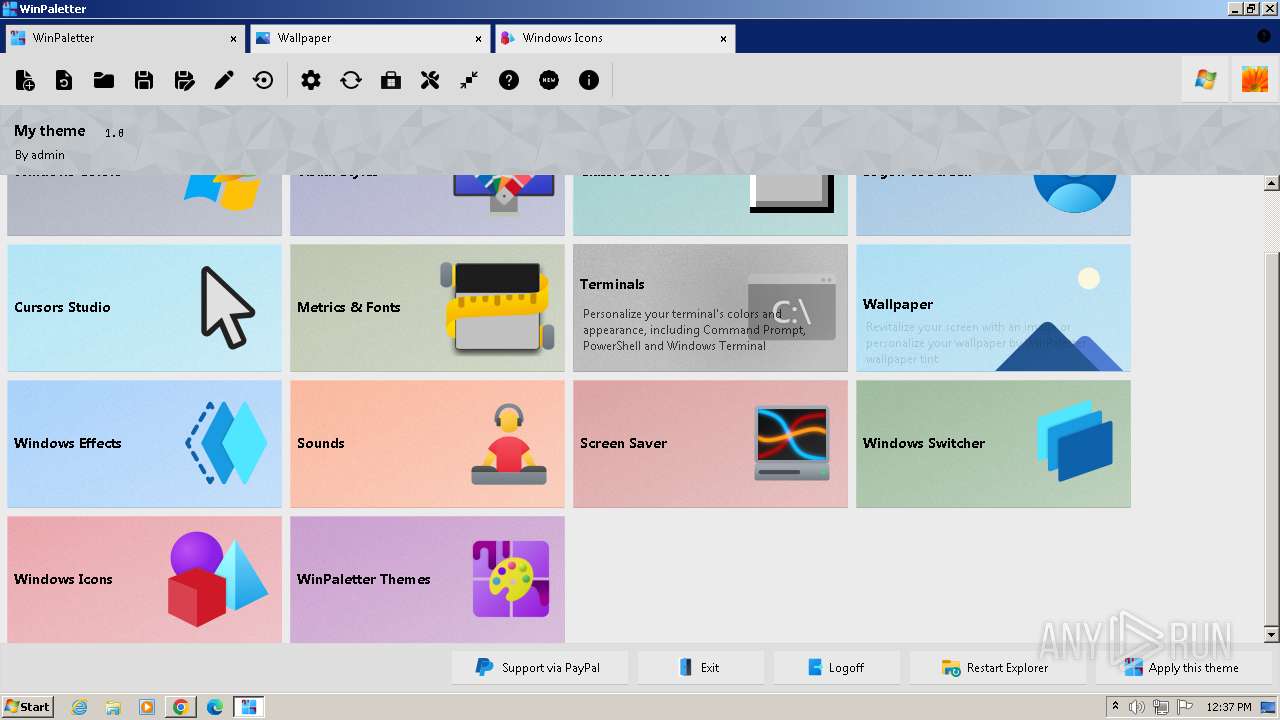
| Comments: | Advanced Windows Appearance Editor |
| CompanyName: | Abdelrhman-AK |
| FileDescription: | WinPaletter |
| FileVersion: | 1.0.9.3 |
| InternalName: | WinPaletter.exe |
| LegalCopyright: | Copyright © 2022-2024 |
| LegalTrademarks: | WinPaletter |
| OriginalFileName: | WinPaletter.exe |
| ProductName: | WinPaletter |
| ProductVersion: | 1.0.9.3 |
| AssemblyVersion: | 1.0.9.3 |
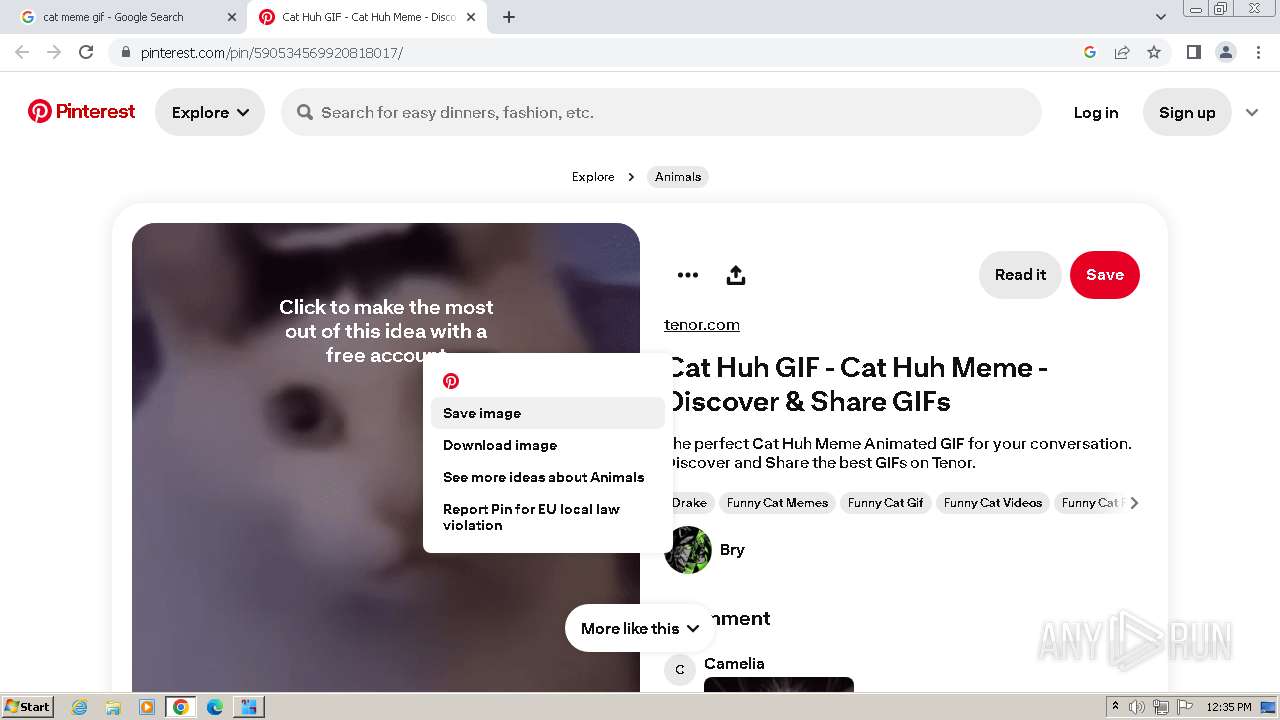
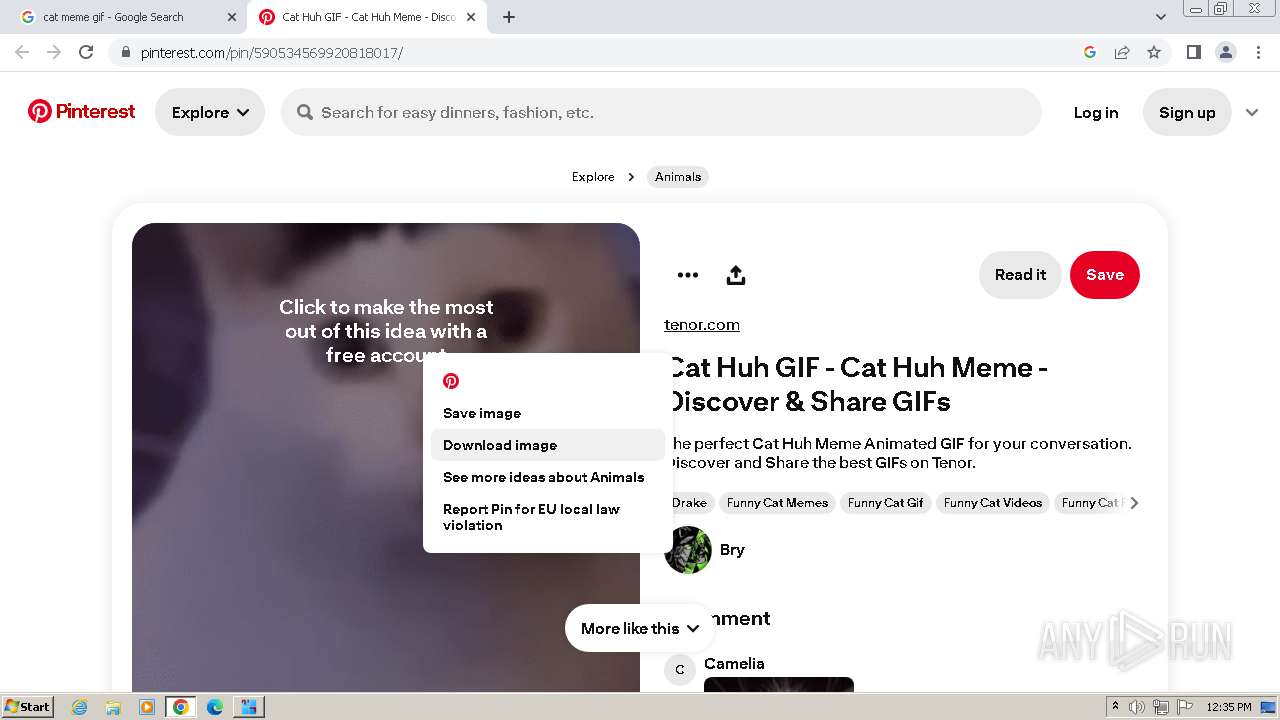
Total processes
72
Monitored processes
26
Malicious processes
1
Suspicious processes
0
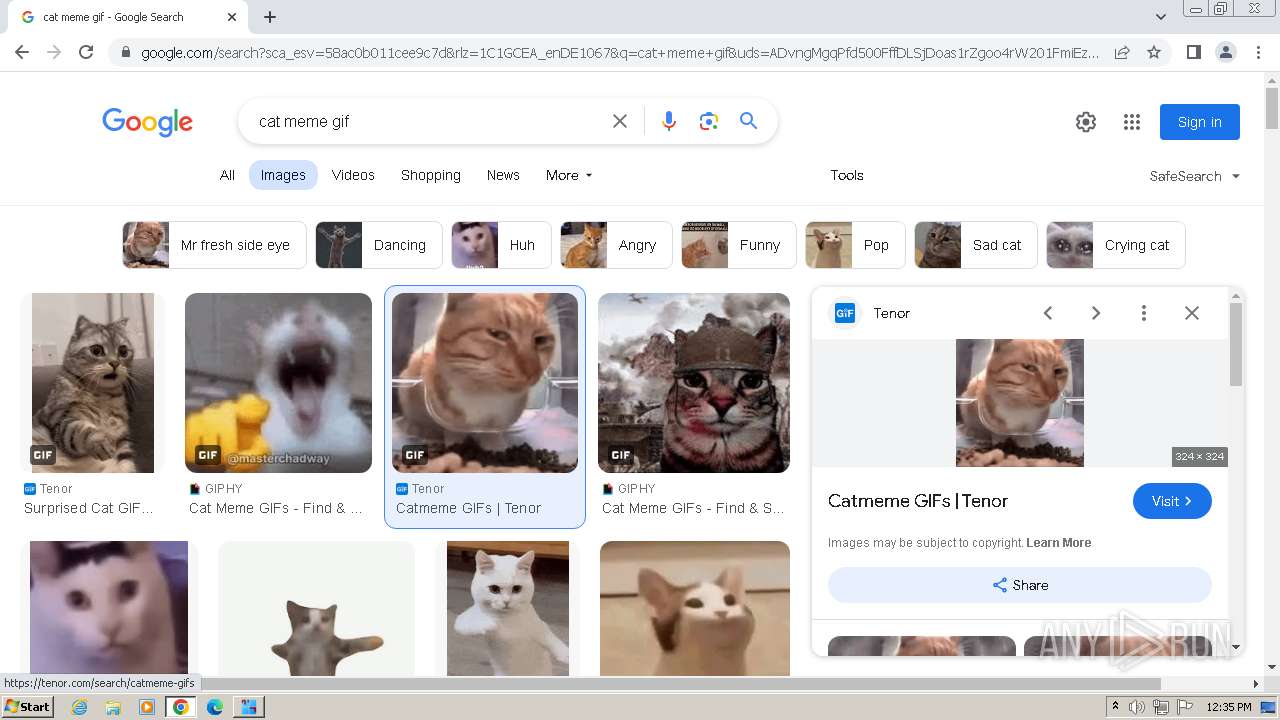
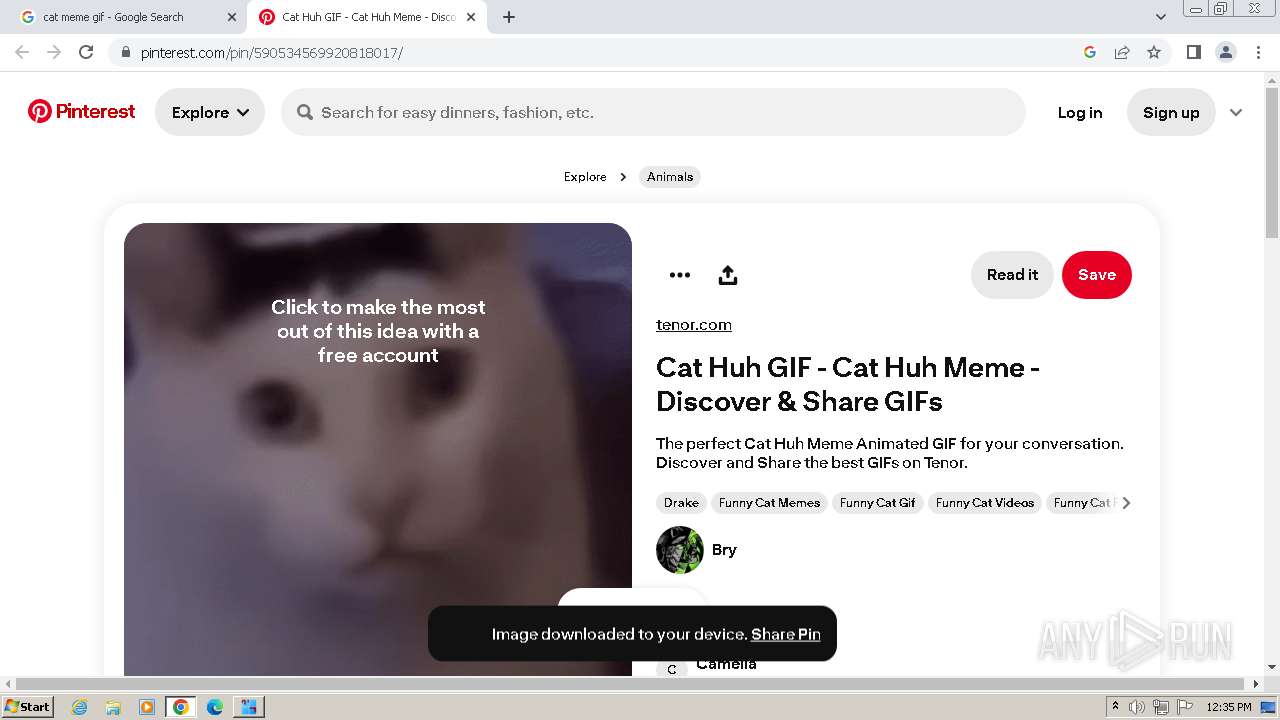
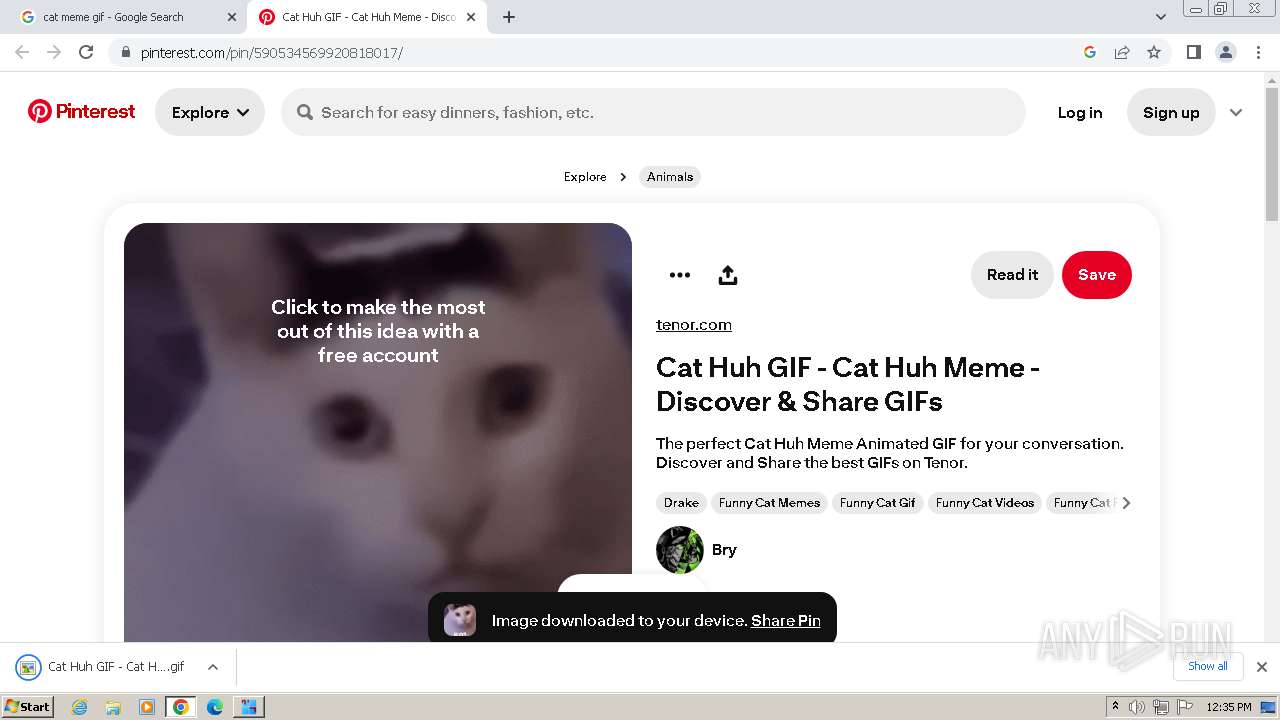
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1320 --field-trial-handle=1148,i,16567394463969044393,11461919123145667636,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
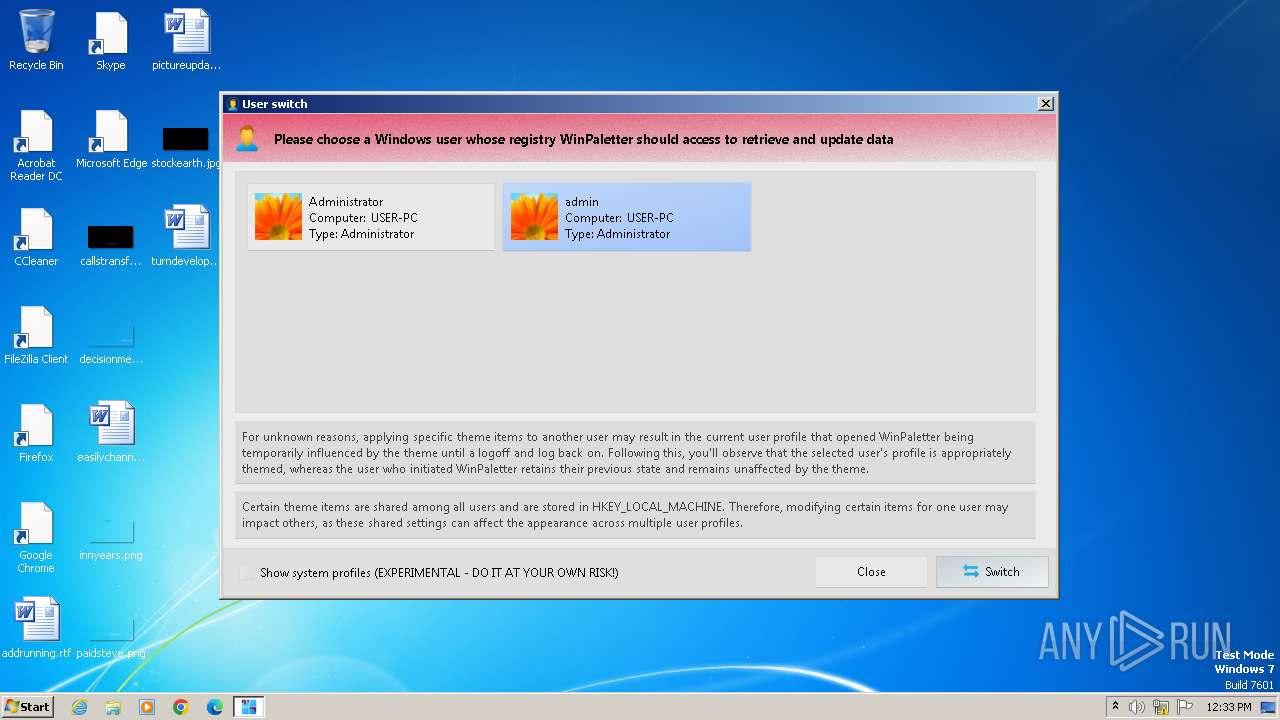
| 1876 | "C:\Windows\System32\reg.exe" load HKU\S-1-5-21-1302019708-1500728564-335382590-500 "C:\Users\Administrator\NTUSER.DAT" | C:\Windows\System32\reg.exe | — | WinPaletter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2012 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1100 --field-trial-handle=1148,i,16567394463969044393,11461919123145667636,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2128 --field-trial-handle=1148,i,16567394463969044393,11461919123145667636,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2160 --field-trial-handle=1148,i,16567394463969044393,11461919123145667636,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x66eb8b38,0x66eb8b48,0x66eb8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1604 --field-trial-handle=1148,i,16567394463969044393,11461919123145667636,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3740 --field-trial-handle=1148,i,16567394463969044393,11461919123145667636,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
27 907
Read events
27 372
Write events
505
Delete events
30
Modification events
| (PID) Process: | (4084) WinPaletter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4084) WinPaletter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4084) WinPaletter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4084) WinPaletter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
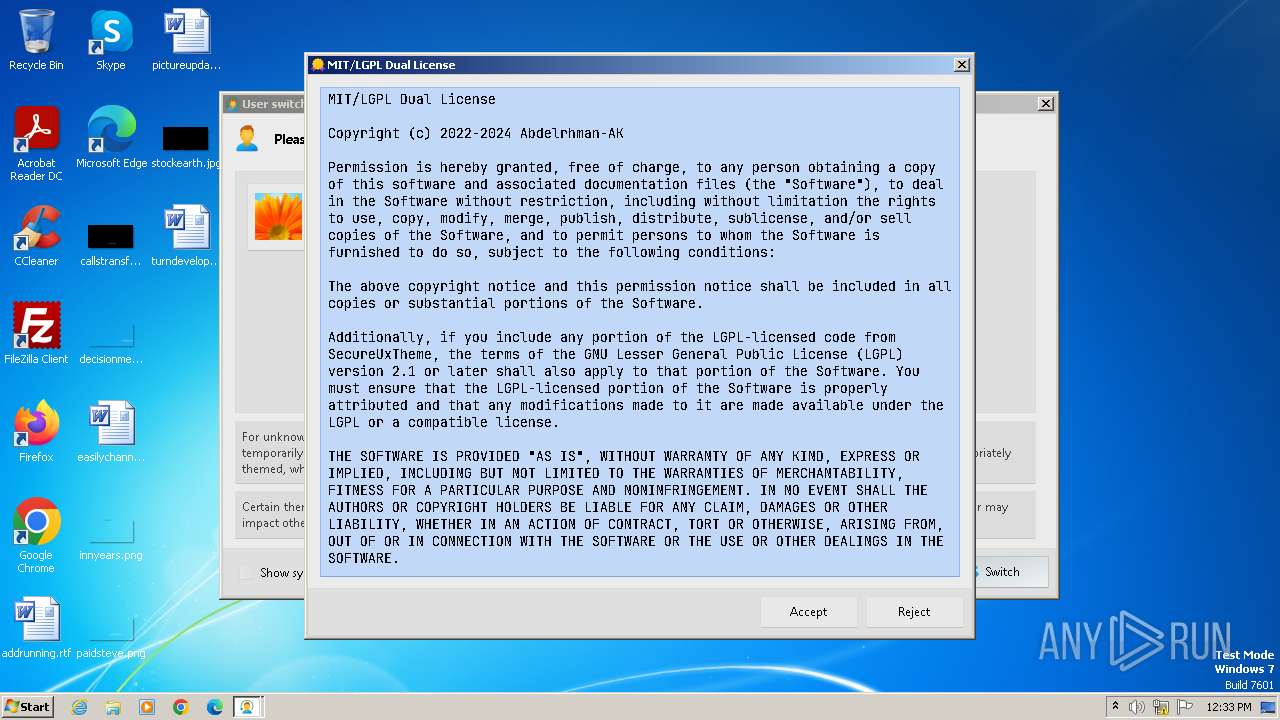
| (PID) Process: | (4084) WinPaletter.exe | Key: | HKEY_CURRENT_USER\Software\WinPaletter\Settings\General |
| Operation: | write | Name: | LicenseAccepted_0 |
Value: 0 | |||
| (PID) Process: | (4084) WinPaletter.exe | Key: | HKEY_CURRENT_USER\Software\WinPaletter\Settings\General |
| Operation: | write | Name: | WhatsNewRecord |
Value: | |||
| (PID) Process: | (4084) WinPaletter.exe | Key: | HKEY_CURRENT_USER\Software\WinPaletter\Settings\General\MainForm |
| Operation: | write | Name: | MainFormWidth |
Value: 1110 | |||
| (PID) Process: | (4084) WinPaletter.exe | Key: | HKEY_CURRENT_USER\Software\WinPaletter\Settings\General\MainForm |
| Operation: | write | Name: | MainFormHeight |
Value: 725 | |||
| (PID) Process: | (4084) WinPaletter.exe | Key: | HKEY_CURRENT_USER\Software\WinPaletter\Settings\General\MainForm |
| Operation: | write | Name: | MainFormStatus |
Value: 0 | |||
| (PID) Process: | (4084) WinPaletter.exe | Key: | HKEY_CURRENT_USER\Software\WinPaletter\Settings\General |
| Operation: | write | Name: | CompactAspects |
Value: 0 | |||
Executable files
15
Suspicious files
223
Text files
42
Unknown types
97
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF11ef7d.TMP | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
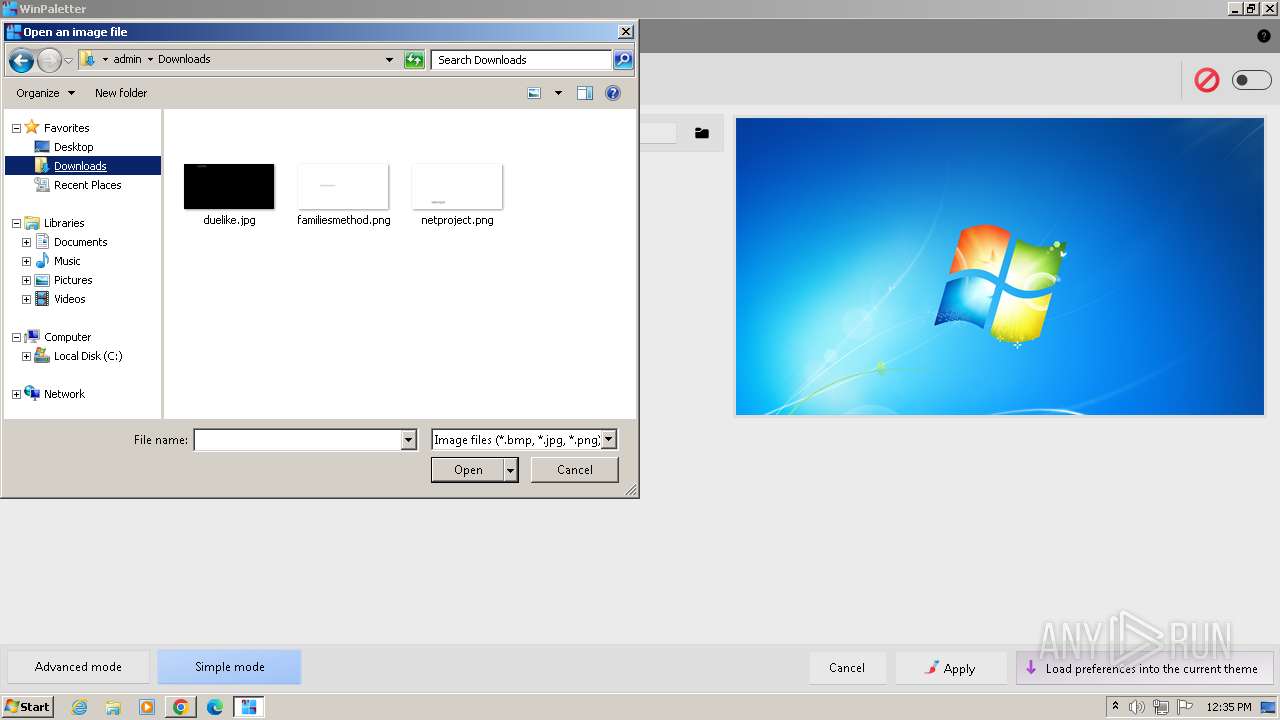
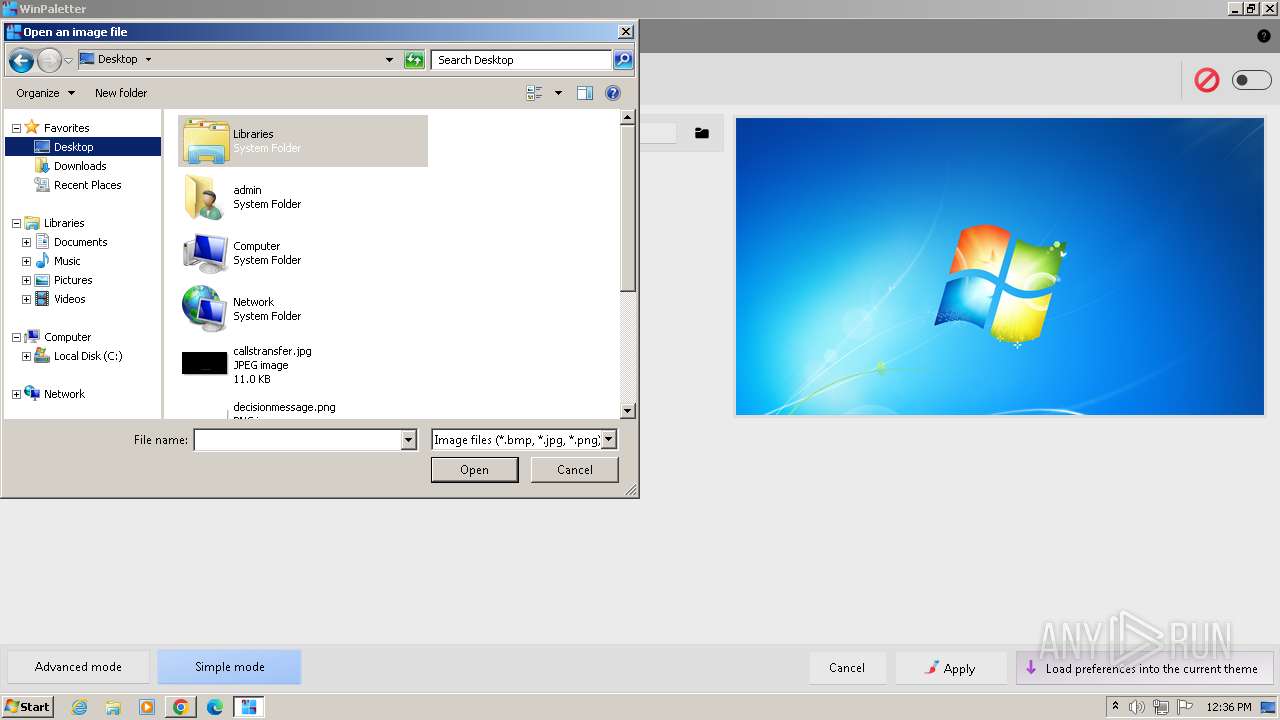
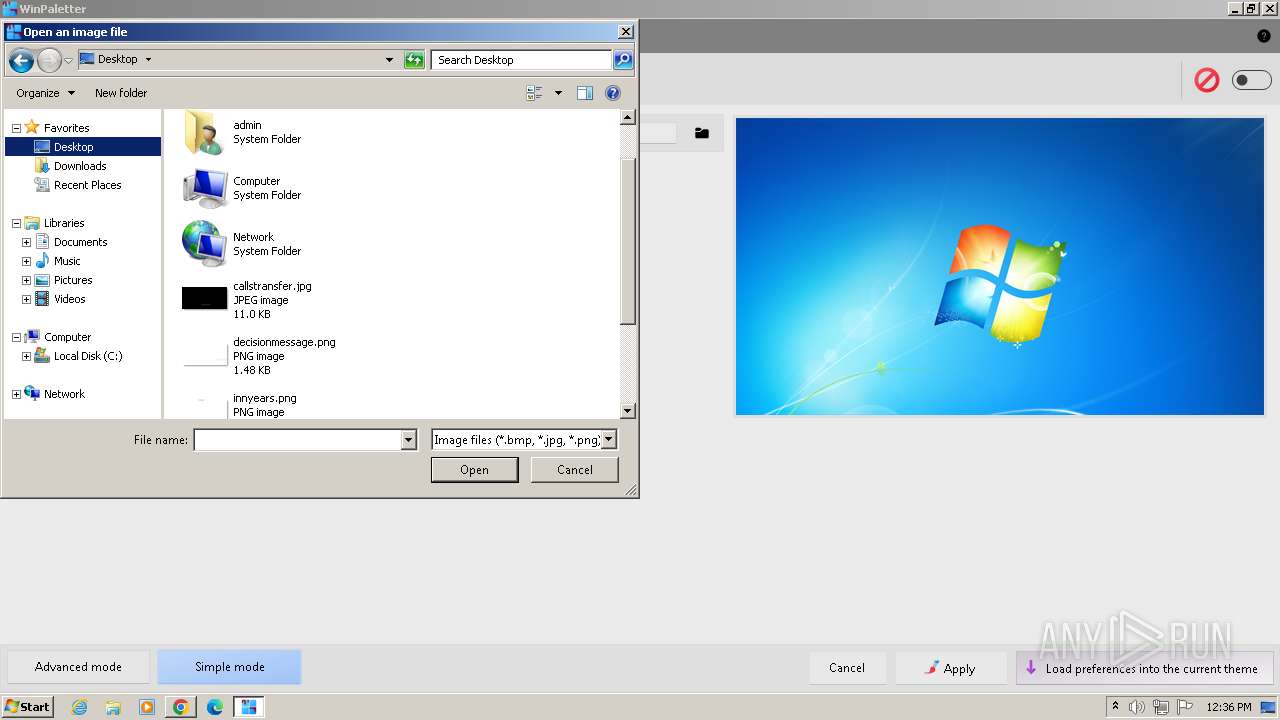
| 4084 | WinPaletter.exe | C:\Users\admin\AppData\Local\Abdelrhman-AK\WinPaletter\fileextension.ico | image | |
MD5:CF6F6985B9EBDE7E25FD04B5F2C4A094 | SHA256:9FBE8D92FA191E7A389850BA1EC9E30CF36CA7ED94AD59DDEDE408090223C0C2 | |||
| 4084 | WinPaletter.exe | C:\Users\admin\AppData\Local\Abdelrhman-AK\WinPaletter\VisualStyles\Luna\Luna.zip | compressed | |
MD5:FE2288DD17873CD4E8371871164AA3E4 | SHA256:60472AA1BCBC8118FFE8AE08BD3EFABC8F98CC05894DCB5F9B14840404358A66 | |||
| 4084 | WinPaletter.exe | C:\Users\admin\AppData\Local\Abdelrhman-AK\WinPaletter\settingsfile.ico | image | |
MD5:FA68F00273DE4F8B8980688BC239F48F | SHA256:6CC2E720A201A670D97DEFE9DF4F7B416B9D5F614F764BA0EC735B9F3DE9513A | |||
| 4084 | WinPaletter.exe | C:\Users\admin\AppData\Local\Temp\admin.bmp | image | |
MD5:343FA15C150A516B20CC9F787CFD530E | SHA256:D632E9DBACDCD8F6B86BA011ED6B23F961D104869654CAA764216EA57A916524 | |||
| 4084 | WinPaletter.exe | C:\Users\admin\AppData\Local\Temp\Administrator.bmp | image | |
MD5:343FA15C150A516B20CC9F787CFD530E | SHA256:D632E9DBACDCD8F6B86BA011ED6B23F961D104869654CAA764216EA57A916524 | |||
| 4084 | WinPaletter.exe | C:\Users\admin\AppData\Local\Abdelrhman-AK\WinPaletter\VisualStyles\Luna\Luna.theme | text | |
MD5:5CE65AF9CD8DE0BB9E877DBD0AB2FC0D | SHA256:94332505364C341325A977CBA4C061028C1F80F61CCBEB268554FD42DA9D7470 | |||
| 4084 | WinPaletter.exe | C:\Users\admin\AppData\Local\Abdelrhman-AK\WinPaletter\VisualStyles\Luna\luna.msstyles | executable | |
MD5:8E356DA331BA56B7EB1FF16B66D8F50D | SHA256:DD8E86E5A7C19EA9FE0E34992BABEFE592055D68EB8659763C8300558CA5DCB4 | |||
| 4084 | WinPaletter.exe | C:\Users\admin\AppData\Local\Abdelrhman-AK\WinPaletter\uninstall.ico | image | |
MD5:EF84F5DCB4814CE361EC9F8B43B47CF3 | SHA256:4938EF9B09EC7D177D3338F23809135FD5BF0719DEFDEDEC89780021051C782B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
76
DNS requests
88
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | GET | 206 | 142.250.186.142:80 | http://dl.google.com/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | US | binary | 16.3 Kb | unknown |
884 | svchost.exe | GET | 206 | 142.250.186.142:80 | http://dl.google.com/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | US | binary | 90.1 Kb | unknown |
884 | svchost.exe | GET | 206 | 142.250.186.142:80 | http://dl.google.com/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | US | binary | 165 Kb | unknown |
884 | svchost.exe | GET | 206 | 142.250.186.142:80 | http://dl.google.com/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | US | binary | 371 Kb | unknown |
884 | svchost.exe | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | html | 593 b | unknown |
884 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | unknown |
884 | svchost.exe | HEAD | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | unknown |
884 | svchost.exe | GET | 200 | 74.125.104.73:80 | http://r4---sn-4g5lznlz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=kX&mip=216.24.216.13&mm=28&mn=sn-4g5lznlz&ms=nvh&mt=1714822097&mv=m&mvi=4&pl=24&rmhost=r5---sn-4g5lznlz.gvt1.com&shardbypass=sd&smhost=r5---sn-4g5lzney.gvt1.com | US | binary | 3.07 Kb | unknown |
884 | svchost.exe | HEAD | 200 | 142.250.186.142:80 | http://dl.google.com/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | US | — | — | unknown |
884 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4084 | WinPaletter.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
4084 | WinPaletter.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
1596 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
840 | svchost.exe | 239.255.255.250:3702 | — | — | — | unknown |
936 | chrome.exe | 142.250.184.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2472 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
936 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
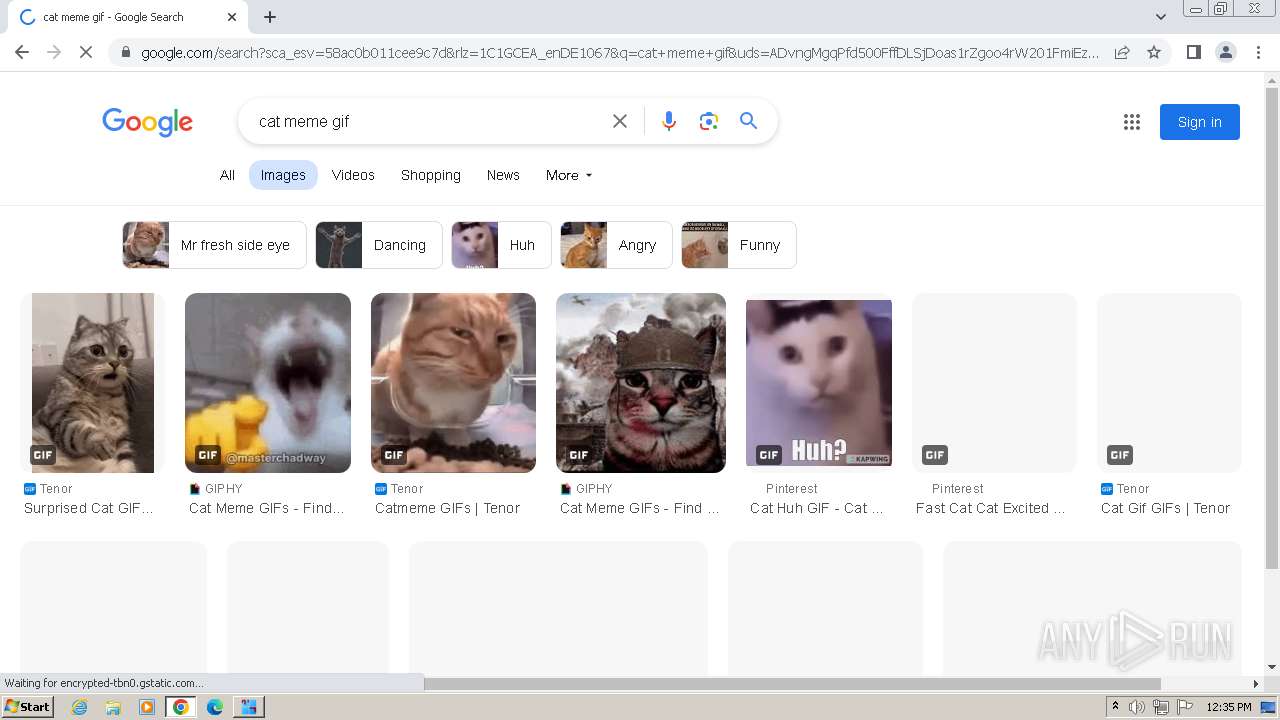
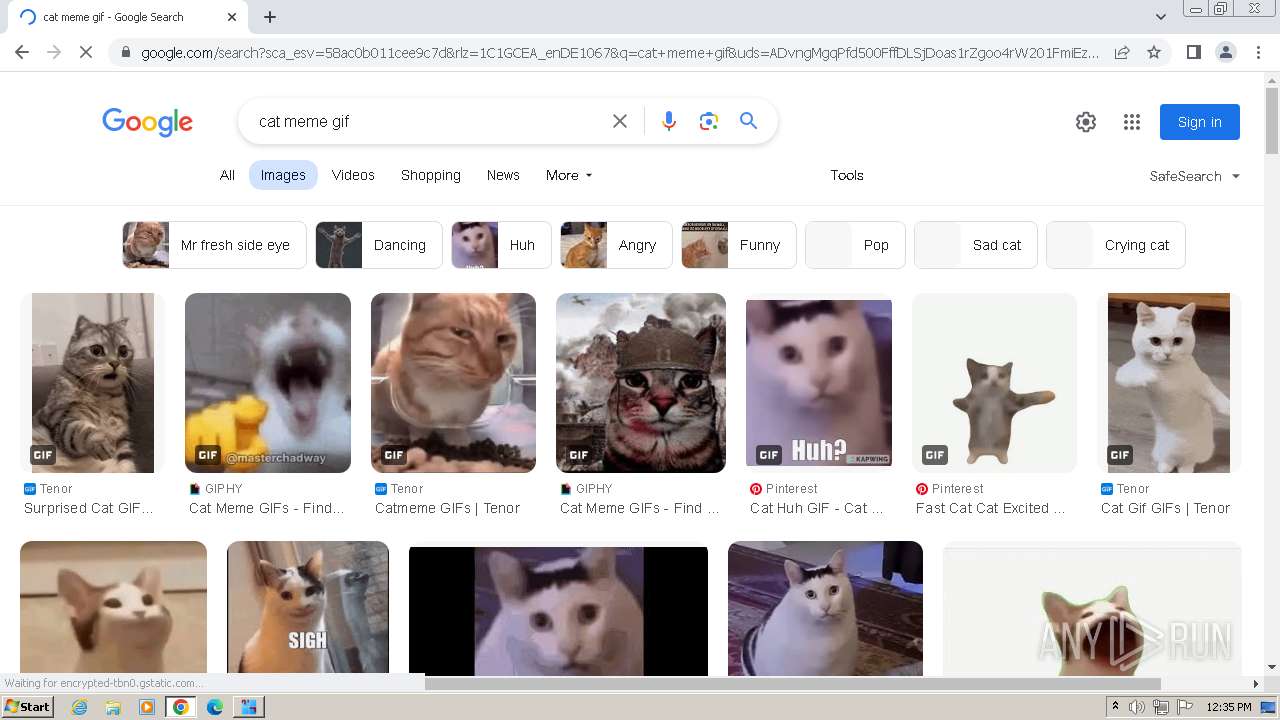
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
raw.githubusercontent.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
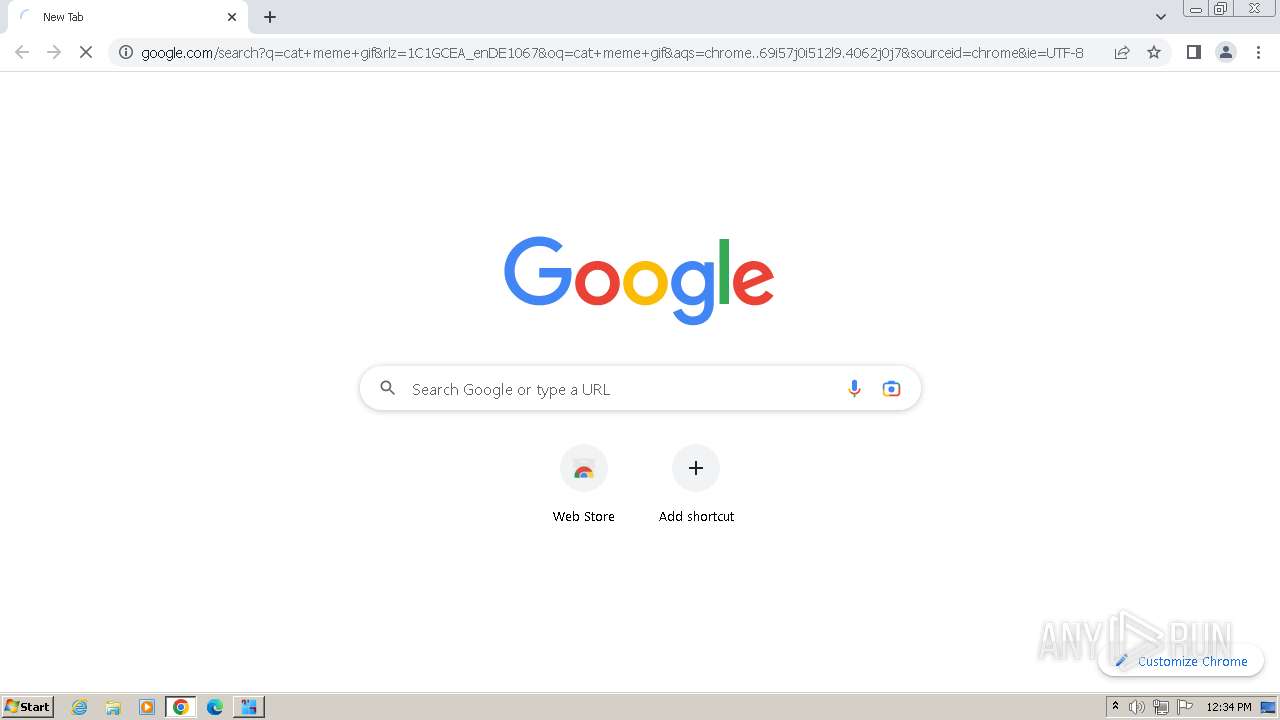
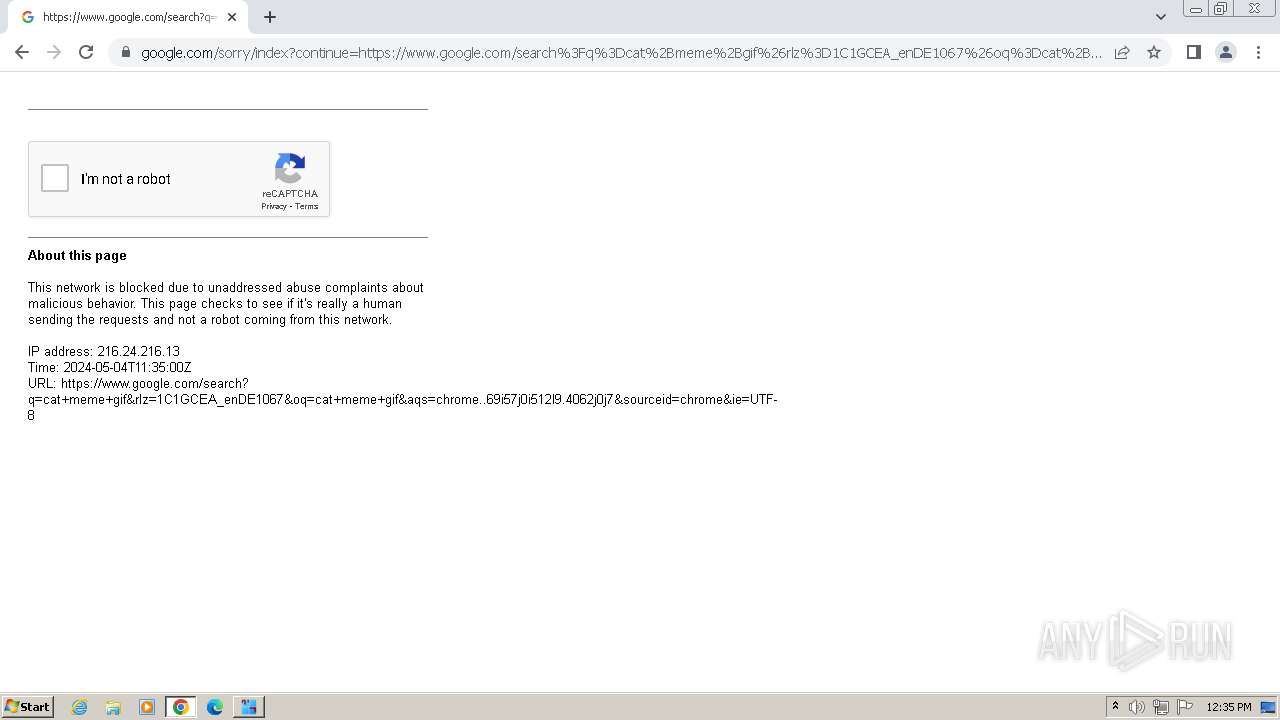
www.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
update.googleapis.com |
| unknown |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |