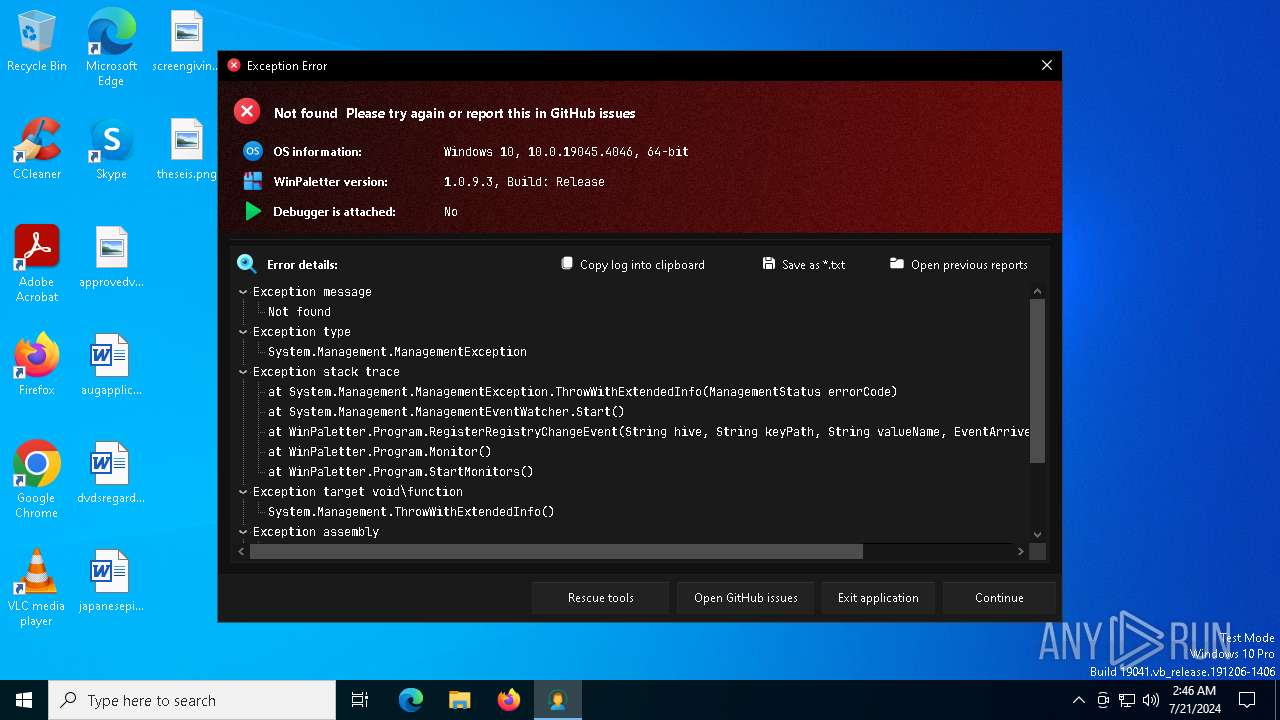
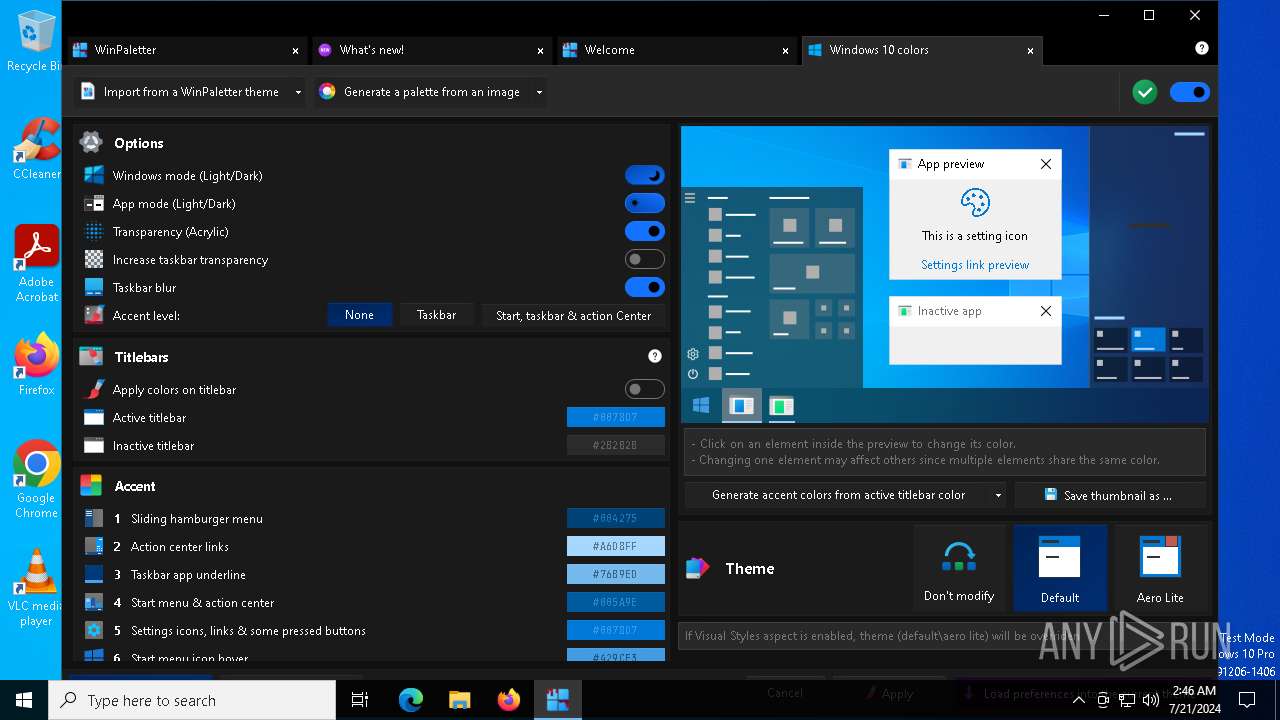
| File name: | WinPaletter.exe |
| Full analysis: | https://app.any.run/tasks/180e73fb-ca50-4e88-8861-177b22dab96e |
| Verdict: | Malicious activity |
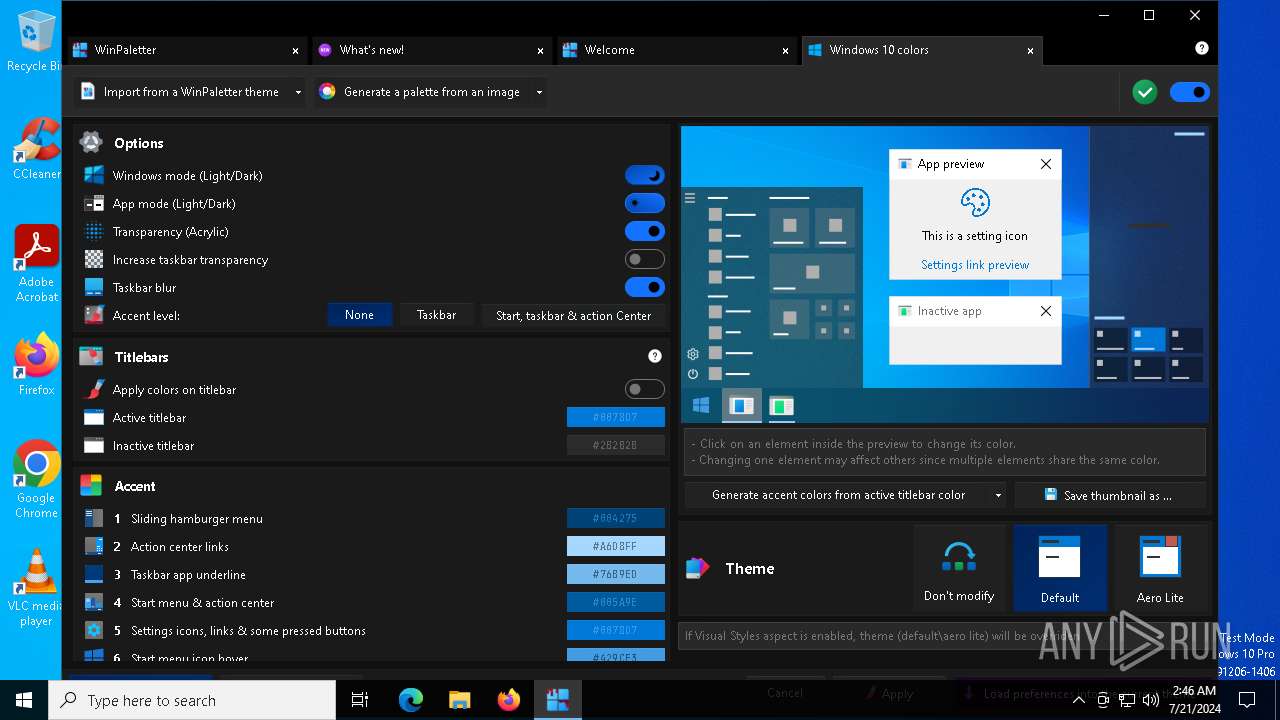
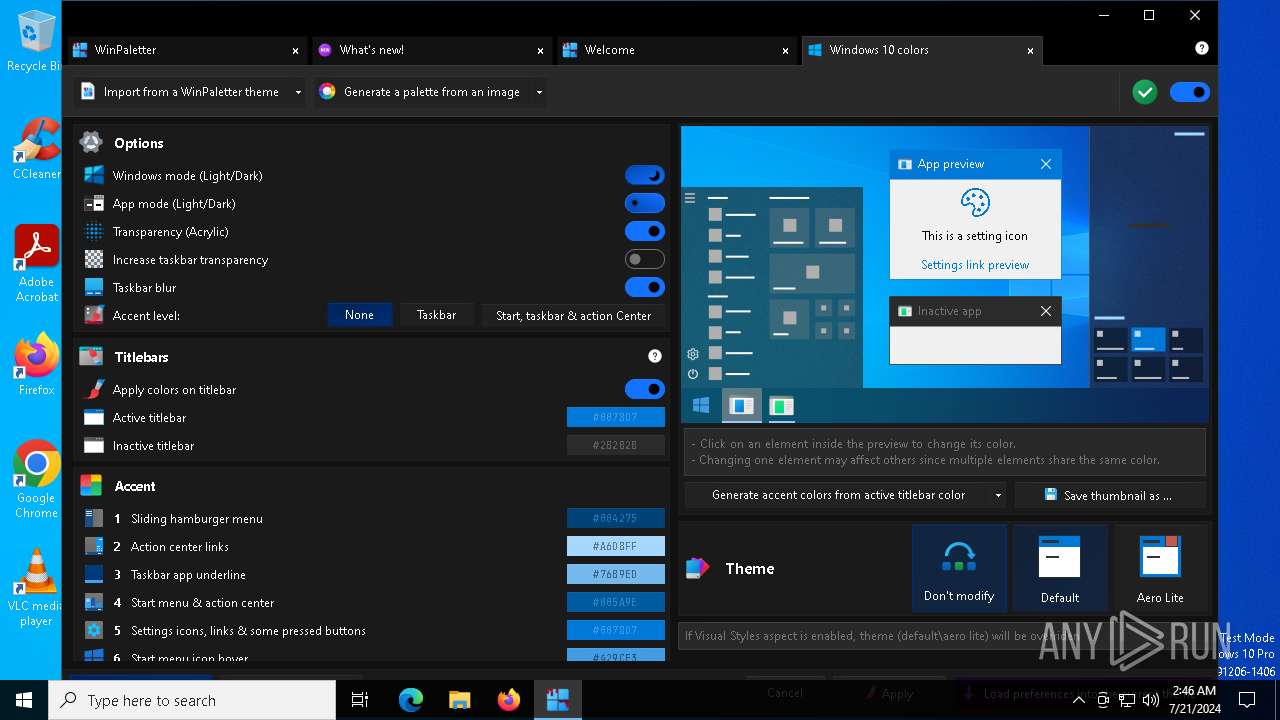
| Analysis date: | July 21, 2024, 02:45:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 26780DADF3AC28B87FC619E710ACC548 |
| SHA1: | BE26D8737F4B551EED11E0C6620EED2164B8AF47 |
| SHA256: | 8405E6341640123A7D8ACA7886C6A98AADF9E7A1B75B5962CD4C186D8AF3F2C4 |
| SSDEEP: | 98304:XLcbtdahlQyVGuAjguadaDVfPdgOkFySRyEnnknnnO2GGymfDuDQqov9Bfkqv7nt:7m8L66HaAtk |
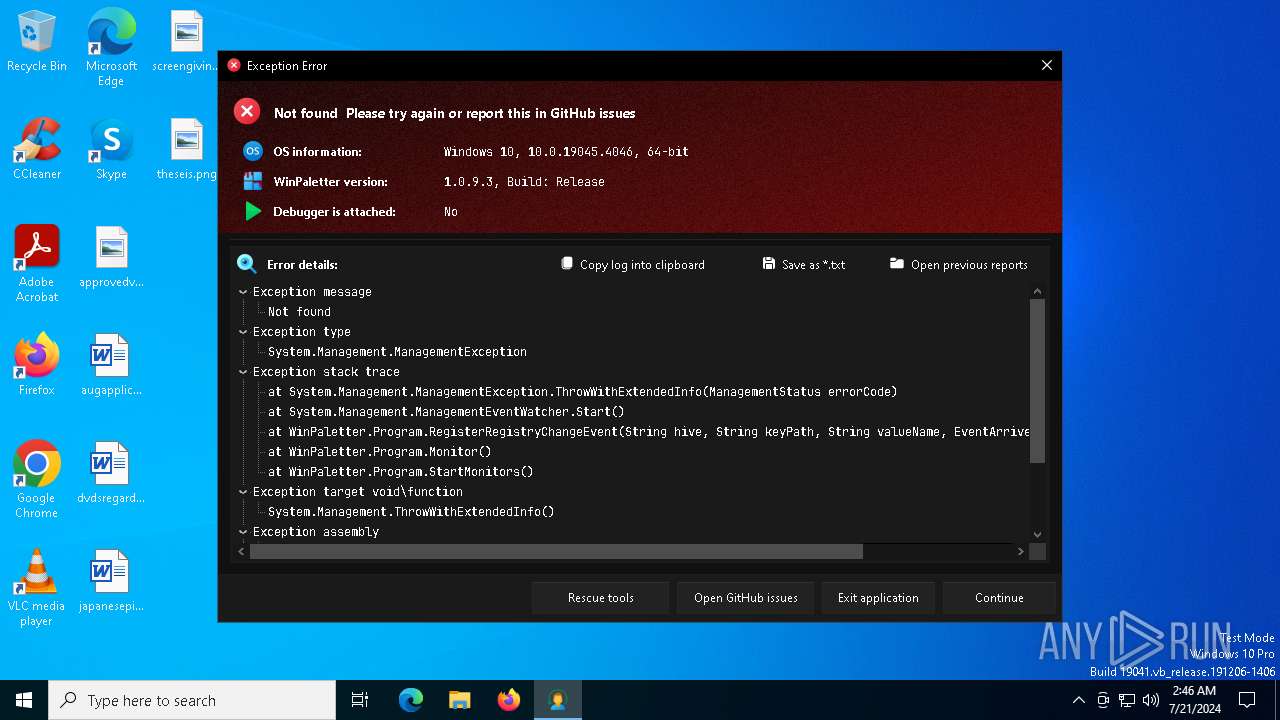
MALICIOUS
Drops the executable file immediately after the start
- WinPaletter.exe (PID: 5636)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinPaletter.exe (PID: 5636)
Reads the date of Windows installation
- WinPaletter.exe (PID: 5636)
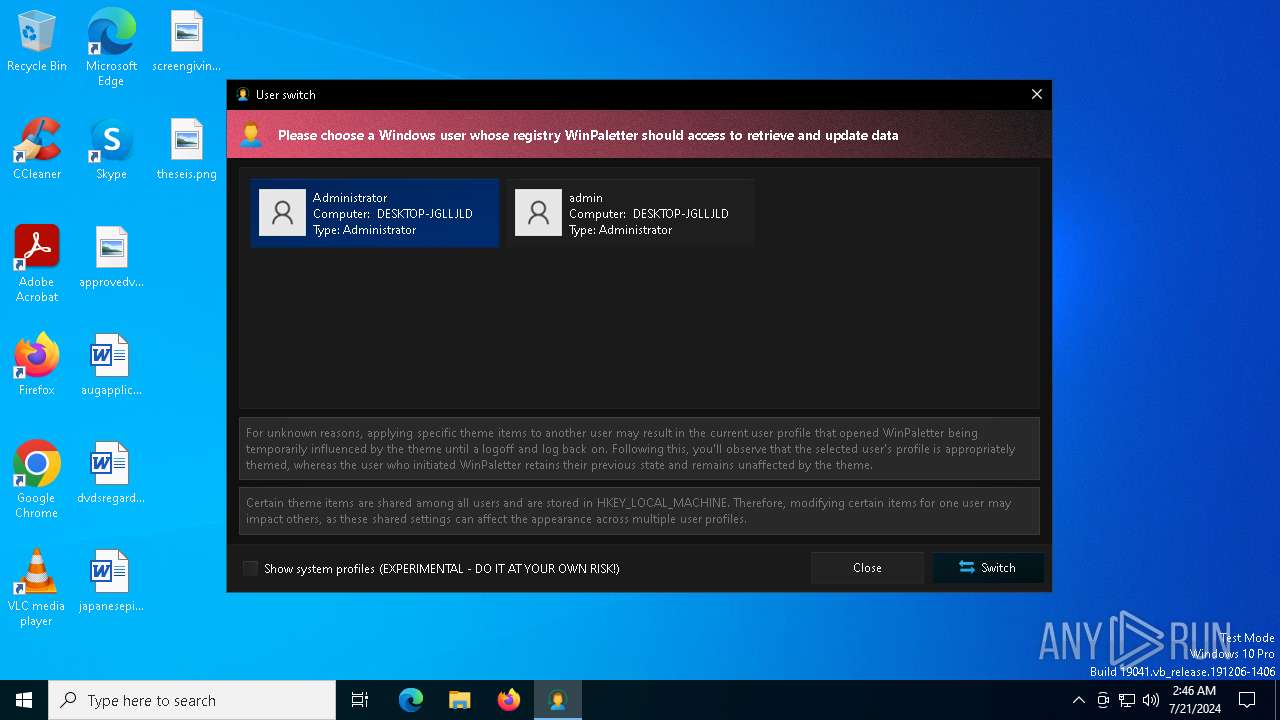
Uses REG/REGEDIT.EXE to modify registry
- WinPaletter.exe (PID: 5636)
Reads the Windows owner or organization settings
- WinPaletter.exe (PID: 5636)
Executable content was dropped or overwritten
- WinPaletter.exe (PID: 5636)
Searches for installed software
- reg.exe (PID: 4732)
- WinPaletter.exe (PID: 5636)
Creates a software uninstall entry
- WinPaletter.exe (PID: 5636)
- reg.exe (PID: 4732)
INFO
Reads the machine GUID from the registry
- WinPaletter.exe (PID: 5636)
Checks supported languages
- WinPaletter.exe (PID: 5636)
Reads the computer name
- WinPaletter.exe (PID: 5636)
Process checks computer location settings
- WinPaletter.exe (PID: 5636)
Creates files in the program directory
- WinPaletter.exe (PID: 5636)
Reads CPU info
- WinPaletter.exe (PID: 5636)
Reads the software policy settings
- WinPaletter.exe (PID: 5636)
Reads Environment values
- WinPaletter.exe (PID: 5636)
Disables trace logs
- WinPaletter.exe (PID: 5636)
Create files in a temporary directory
- WinPaletter.exe (PID: 5636)
Checks proxy server information
- WinPaletter.exe (PID: 5636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2046:05:08 11:12:47+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 9516032 |
| InitializedDataSize: | 193024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x915126 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.9.3 |
| ProductVersionNumber: | 1.0.9.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
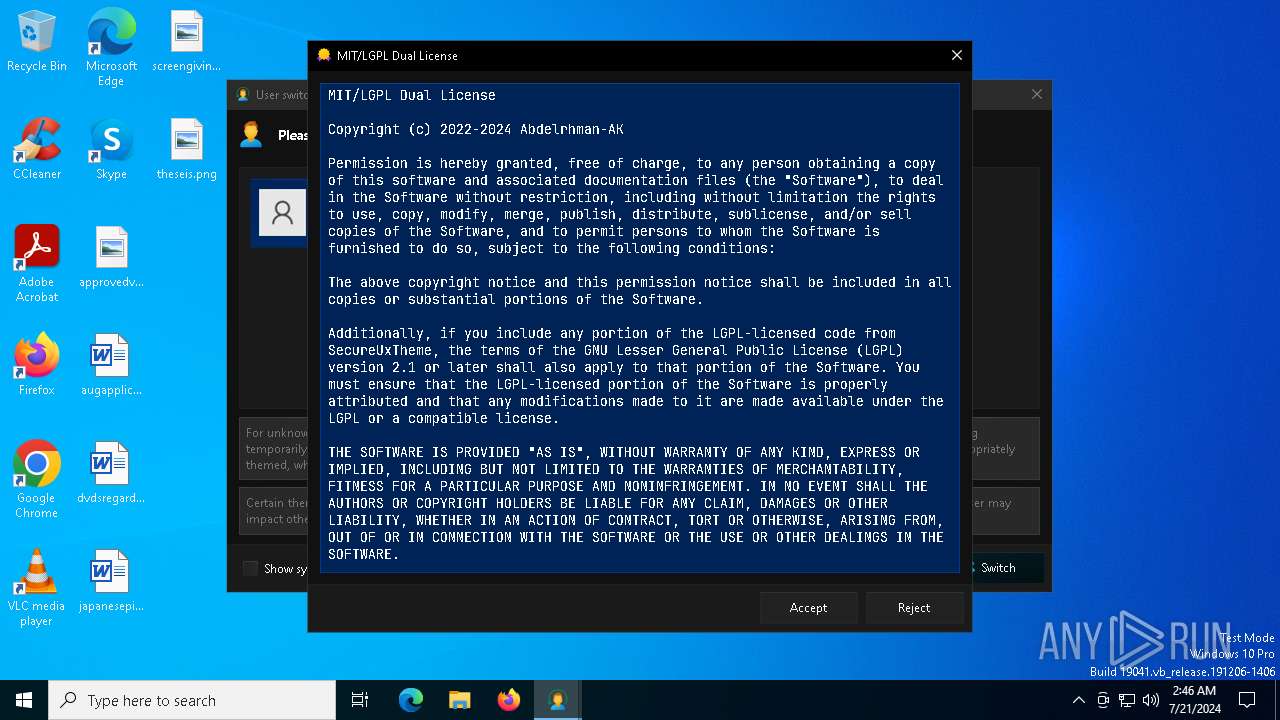
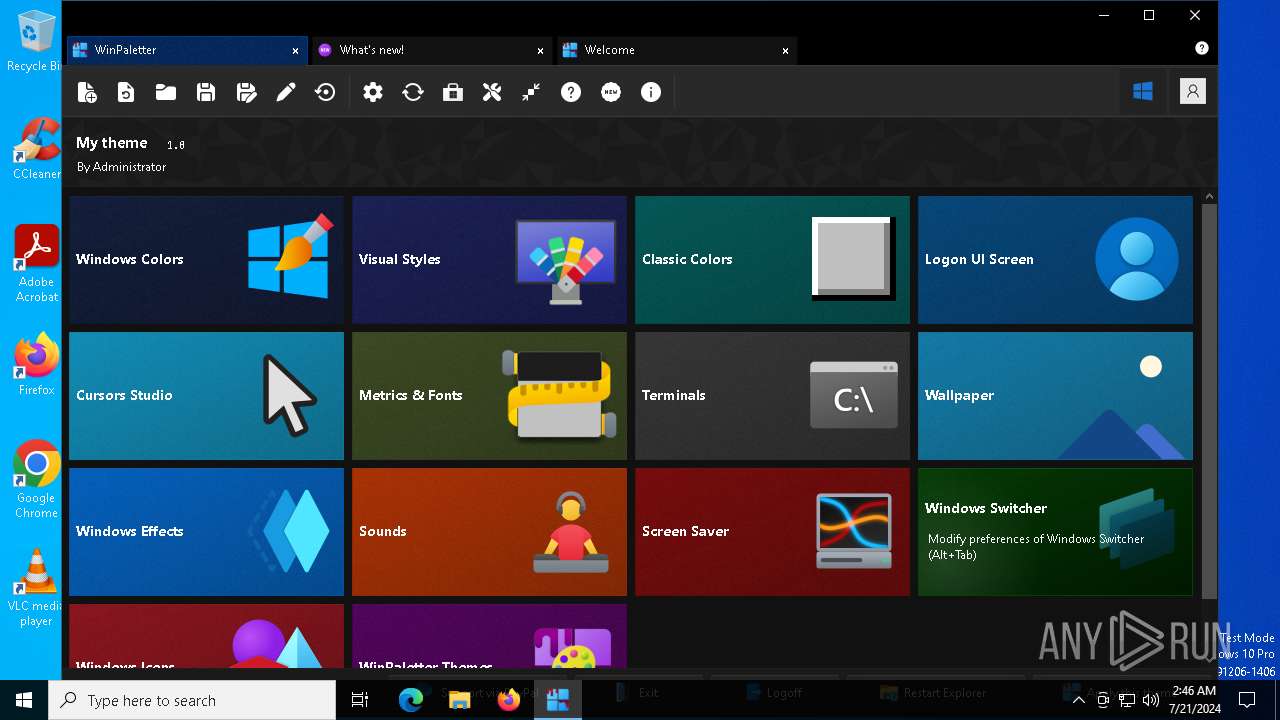
| Comments: | Advanced Windows Appearance Editor |
| CompanyName: | Abdelrhman-AK |
| FileDescription: | WinPaletter |
| FileVersion: | 1.0.9.3 |
| InternalName: | WinPaletter.exe |
| LegalCopyright: | Copyright © 2022-2024 |
| LegalTrademarks: | WinPaletter |
| OriginalFileName: | WinPaletter.exe |
| ProductName: | WinPaletter |
| ProductVersion: | 1.0.9.3 |
| AssemblyVersion: | 1.0.9.3 |
Total processes
188
Monitored processes
50
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Windows\System32\reg.exe" add "HKU\S-1-5-21-1693682860-607145093-2874071422-500\Software\Classes\WinPaletter.ThemeFile\Shell\Open\Command" /v "" /t REG_SZ /d ""C:\Users\admin\AppData\Local\Temp\WinPaletter.exe" "^%1"" /f | C:\Windows\SysWOW64\reg.exe | — | WinPaletter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1004 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1340 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | "C:\Windows\System32\reg.exe" add "HKU\S-1-5-21-1693682860-607145093-2874071422-500\Software\WinPaletter\Settings\Miscellaneous" /v "Win7LivePreview" /t REG_DWORD /d 0000001 /f | C:\Windows\SysWOW64\reg.exe | — | WinPaletter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2220 | "C:\Windows\System32\reg.exe" add "HKU\S-1-5-21-1693682860-607145093-2874071422-500\Software\Classes\WinPaletter.ThemeFile\DefaultIcon" /v "" /t REG_SZ /d "C:\Users\Administrator\AppData\Local\Abdelrhman-AK\WinPaletter\fileextension.ico" /f | C:\Windows\SysWOW64\reg.exe | — | WinPaletter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2344 | "C:\Windows\System32\reg.exe" add "HKU\S-1-5-21-1693682860-607145093-2874071422-500\Software\Classes\WinPaletter.SettingsFile\DefaultIcon" /v "" /t REG_SZ /d "C:\Users\Administrator\AppData\Local\Abdelrhman-AK\WinPaletter\settingsfile.ico" /f | C:\Windows\SysWOW64\reg.exe | — | WinPaletter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2360 | "C:\Windows\System32\reg.exe" add "HKU\S-1-5-21-1693682860-607145093-2874071422-500\Software\WinPaletter\Settings\General\MainForm" /v "MainFormWidth" /t REG_DWORD /d 00001110 /f | C:\Windows\SysWOW64\reg.exe | — | WinPaletter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\AppData\Local\Temp\WinPaletter.exe" | C:\Users\admin\AppData\Local\Temp\WinPaletter.exe | — | explorer.exe | |||||||||||
User: admin Company: Abdelrhman-AK Integrity Level: MEDIUM Description: WinPaletter Exit code: 3221226540 Version: 1.0.9.3 Modules
| |||||||||||||||
| 3328 | "C:\Windows\System32\reg.exe" add "HKU\S-1-5-21-1693682860-607145093-2874071422-500\Software\Classes\WinPaletter.SettingsFile\Shell\Open" /v "Icon" /t REG_SZ /d "C:\Users\admin\AppData\Local\Temp\WinPaletter.exe, 0" /f | C:\Windows\SysWOW64\reg.exe | — | WinPaletter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 196
Read events
8 024
Write events
172
Delete events
0
Modification events
| (PID) Process: | (5636) WinPaletter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5636) WinPaletter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5636) WinPaletter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5636) WinPaletter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5636) WinPaletter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinPaletter\Settings\General |
| Operation: | write | Name: | LicenseAccepted_0 |
Value: 0 | |||
| (PID) Process: | (5636) WinPaletter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinPaletter\Settings\General |
| Operation: | write | Name: | WhatsNewRecord |
Value: | |||
| (PID) Process: | (5636) WinPaletter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinPaletter\Settings\General\MainForm |
| Operation: | write | Name: | MainFormWidth |
Value: 1110 | |||
| (PID) Process: | (5636) WinPaletter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinPaletter\Settings\General\MainForm |
| Operation: | write | Name: | MainFormHeight |
Value: 725 | |||
| (PID) Process: | (5636) WinPaletter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinPaletter\Settings\General\MainForm |
| Operation: | write | Name: | MainFormStatus |
Value: 0 | |||
| (PID) Process: | (5636) WinPaletter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinPaletter\Settings\General |
| Operation: | write | Name: | CompactAspects |
Value: 0 | |||
Executable files
1
Suspicious files
2
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
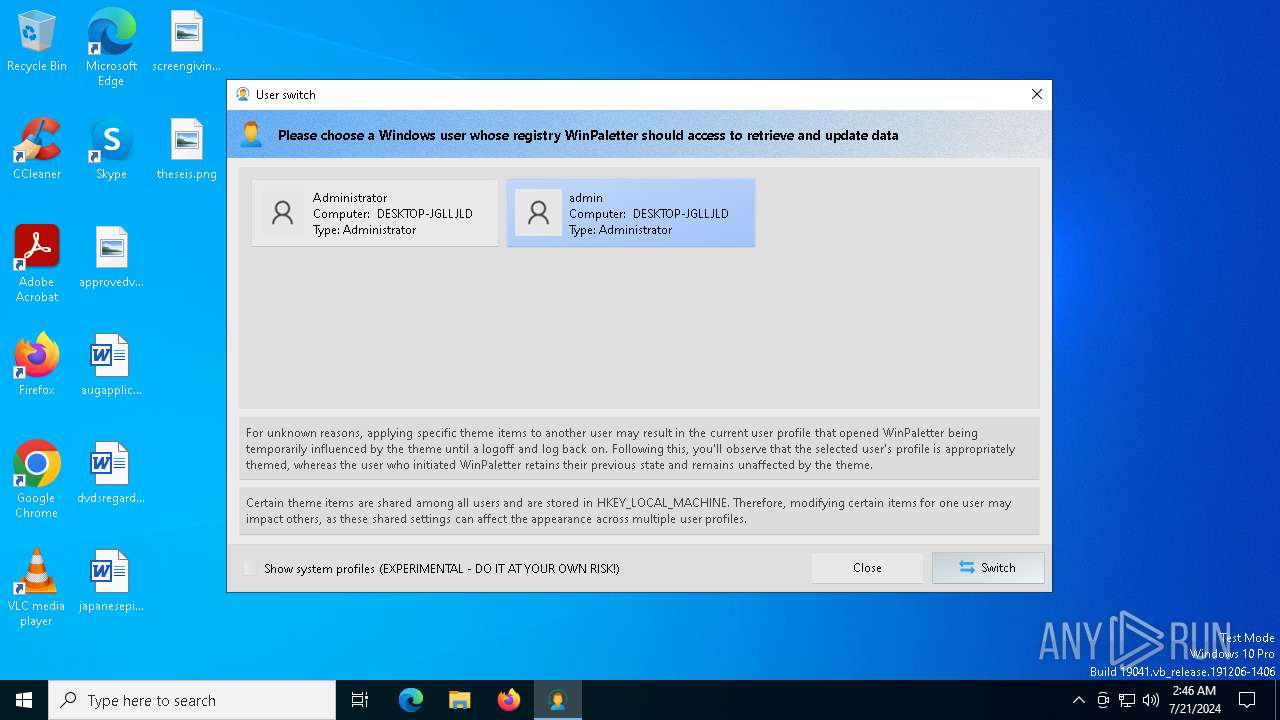
| 5636 | WinPaletter.exe | C:\Users\admin\AppData\Local\Temp\admin.bmp | image | |
MD5:908FA2DFB385771ECF5F8B2B3E7BFF16 | SHA256:60FF5131DBA68A8FFE7BA0475BF3E192B432E1969E5AC52D7F217F6935F4035D | |||
| 5636 | WinPaletter.exe | C:\Users\admin\AppData\Local\Temp\Administrator.bmp | image | |
MD5:908FA2DFB385771ECF5F8B2B3E7BFF16 | SHA256:60FF5131DBA68A8FFE7BA0475BF3E192B432E1969E5AC52D7F217F6935F4035D | |||
| 5636 | WinPaletter.exe | C:\Users\Administrator\AppData\Local\Abdelrhman-AK\WinPaletter\themerespack.ico | image | |
MD5:639501D0A5A00493B21C325452C3A181 | SHA256:3751F9B1F8FDED58E2302297F12729BB1434012957A3ED8285DB7F5B23F894B5 | |||
| 5636 | WinPaletter.exe | C:\Users\Administrator\AppData\Local\Abdelrhman-AK\WinPaletter\uninstall.ico | image | |
MD5:EF84F5DCB4814CE361EC9F8B43B47CF3 | SHA256:4938EF9B09EC7D177D3338F23809135FD5BF0719DEFDEDEC89780021051C782B | |||
| 5636 | WinPaletter.exe | C:\Users\Administrator\AppData\Local\Abdelrhman-AK\WinPaletter\WindowsStartup_Backup.wav | binary | |
MD5:155F2A0F886570157416EA85F4B4C613 | SHA256:1D31BAD8D79FF31B7917C7290C8B96AA5F3B45A984313247B23C6996C7A29ADE | |||
| 5636 | WinPaletter.exe | C:\Users\Administrator\AppData\Local\Abdelrhman-AK\WinPaletter\VisualStyles\Luna\Luna.zip | compressed | |
MD5:FE2288DD17873CD4E8371871164AA3E4 | SHA256:60472AA1BCBC8118FFE8AE08BD3EFABC8F98CC05894DCB5F9B14840404358A66 | |||
| 5636 | WinPaletter.exe | C:\Users\Administrator\AppData\Local\Abdelrhman-AK\WinPaletter\fileextension.ico | image | |
MD5:CF6F6985B9EBDE7E25FD04B5F2C4A094 | SHA256:9FBE8D92FA191E7A389850BA1EC9E30CF36CA7ED94AD59DDEDE408090223C0C2 | |||
| 5636 | WinPaletter.exe | C:\Users\Administrator\AppData\Local\Abdelrhman-AK\WinPaletter\settingsfile.ico | image | |
MD5:FA68F00273DE4F8B8980688BC239F48F | SHA256:6CC2E720A201A670D97DEFE9DF4F7B416B9D5F614F764BA0EC735B9F3DE9513A | |||
| 5636 | WinPaletter.exe | C:\Users\Administrator\AppData\Local\Abdelrhman-AK\WinPaletter\VisualStyles\Luna\Luna.theme | text | |
MD5:77326336D9FDAE5DF86705C621B74B9B | SHA256:D3A71884B262B3089705F758883AAD1B565DF4D8C779D1AAE76F6E032C174533 | |||
| 5636 | WinPaletter.exe | C:\Users\Administrator\AppData\Local\Abdelrhman-AK\WinPaletter\Reports\2.46.17 21-7-2024.txt | text | |
MD5:76A3649B57889FAFA1303B0C9A80E3C1 | SHA256:6BCE2B27F8643AFA5C91B0C77450E7766670760440AA0144BCA4C871171EB4D0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
37
DNS requests
15
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4716 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5620 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.115.3.253:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7856 | svchost.exe | 4.208.221.206:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2760 | svchost.exe | 40.115.3.253:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3228 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4716 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
github.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |