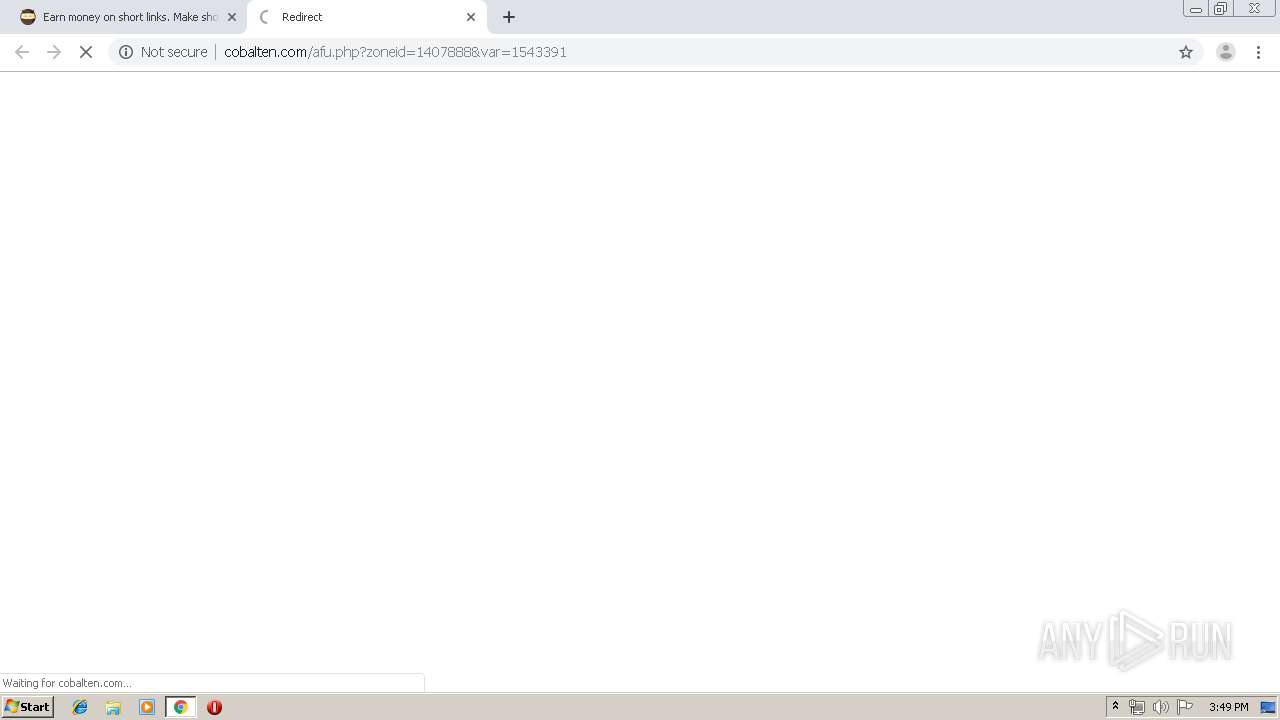
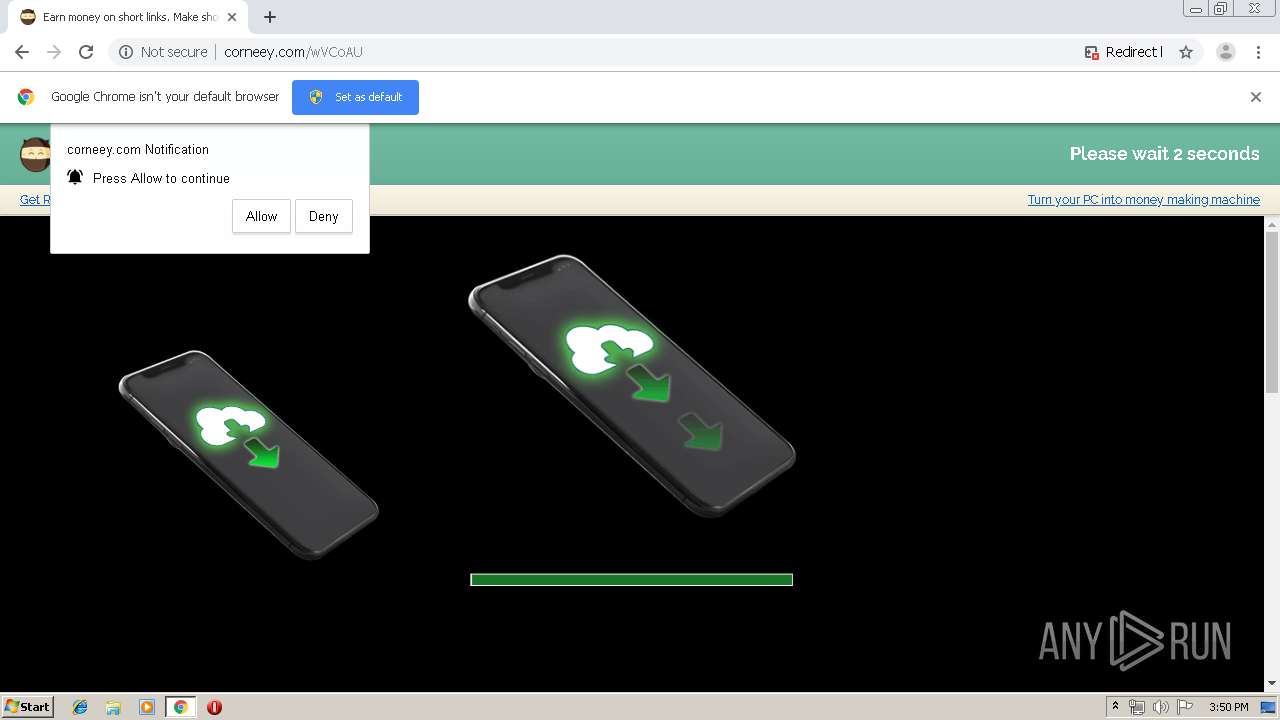
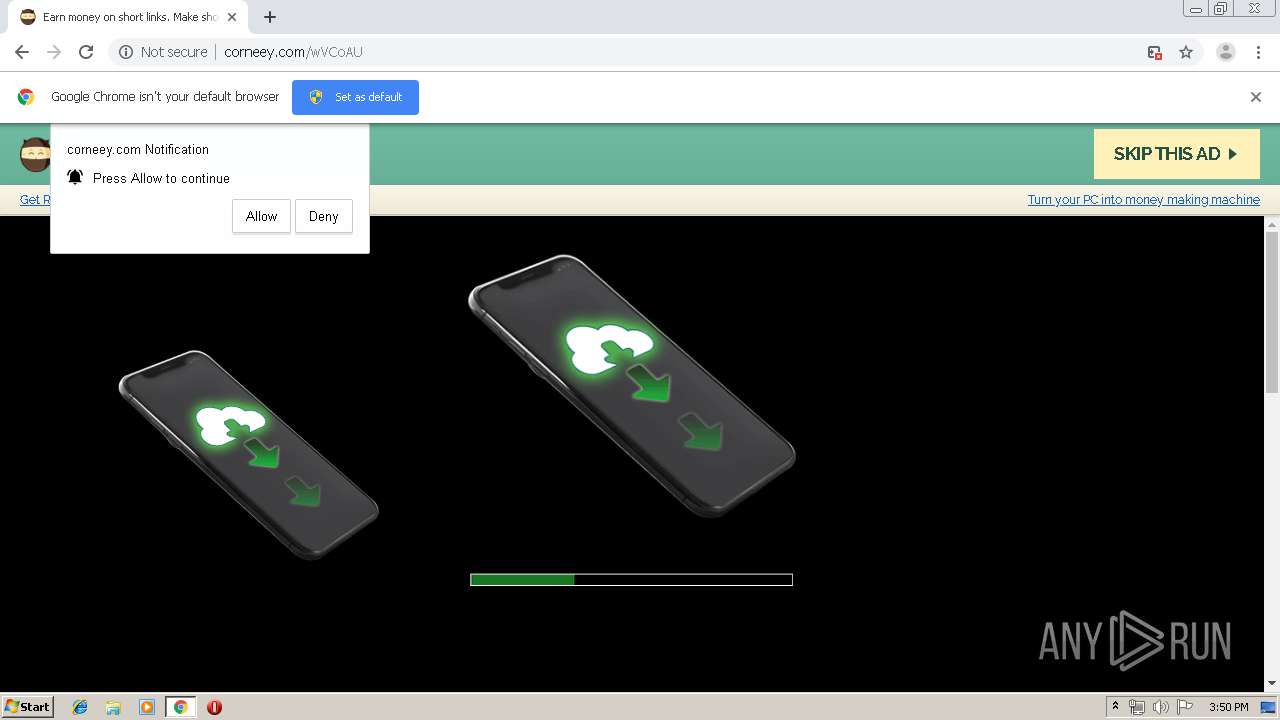
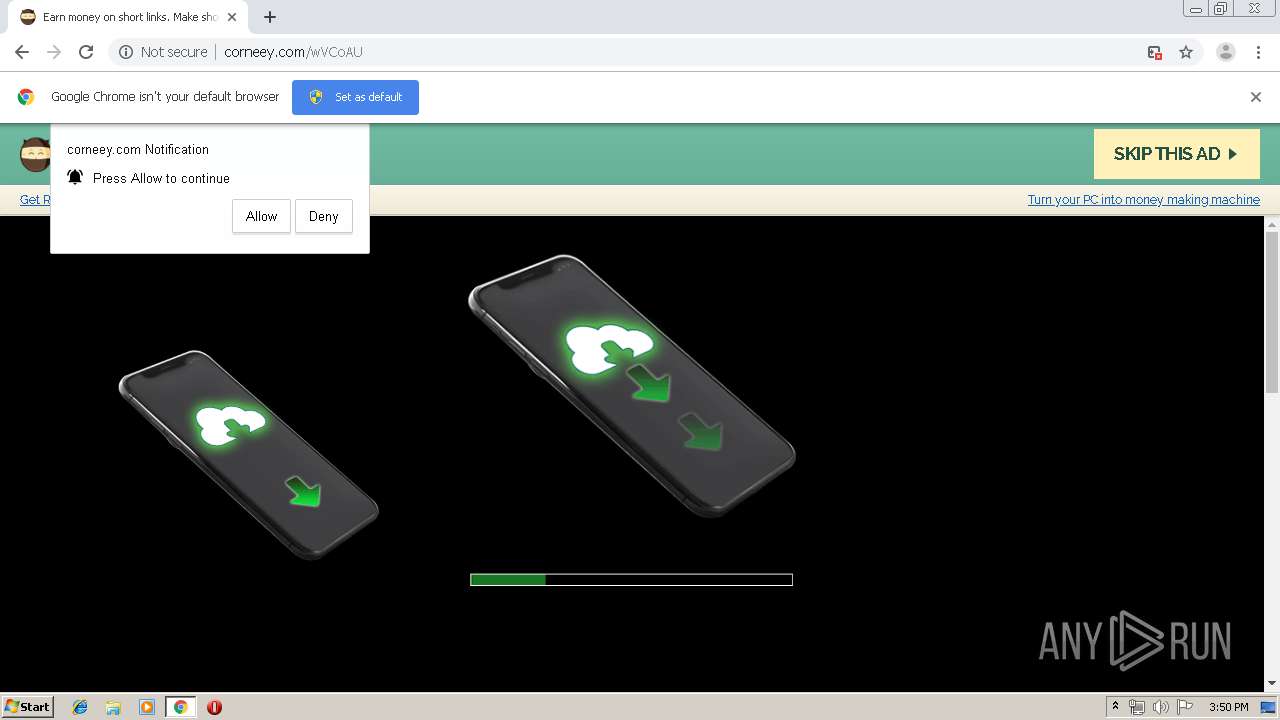
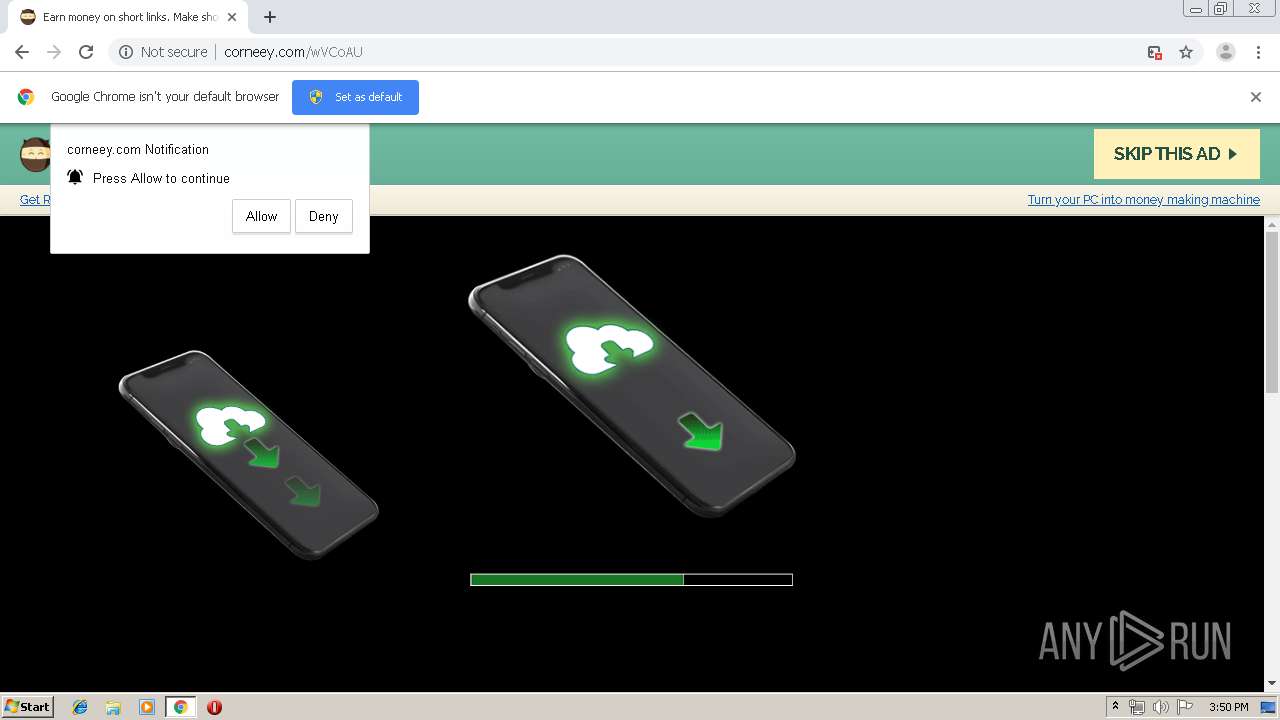
| URL: | http://corneey.com/wVCoAU |
| Full analysis: | https://app.any.run/tasks/947ddf27-f9c2-44d3-a061-c78c9f3c060f |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2019, 14:49:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1D9520149BEA1E59E7D472AC1D94EE14 |
| SHA1: | AEE1BE66B4B1F5E6E61F40C57C13350ADAFF05DF |
| SHA256: | 8403555BF6512EB63FEABC7BE3C21B063BACFDC3DD6E8EF6219015896F272658 |
| SSDEEP: | 3:N1KdKX5Fd:CIJFd |
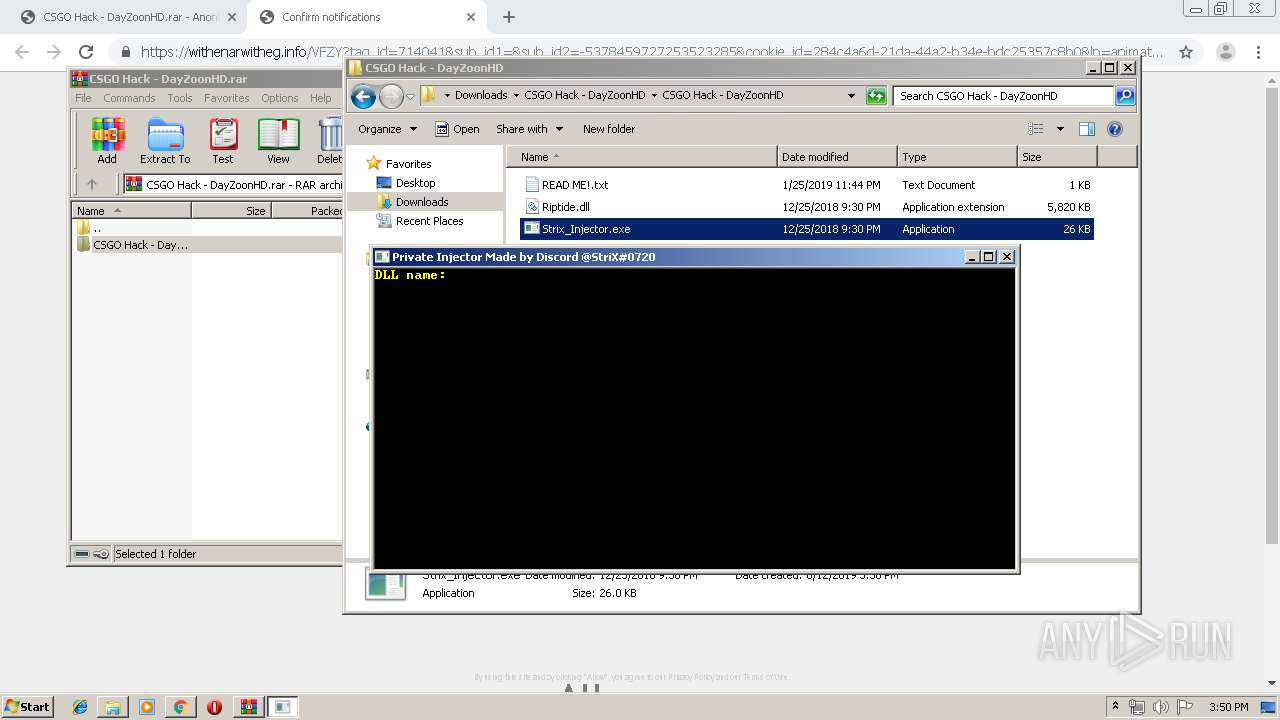
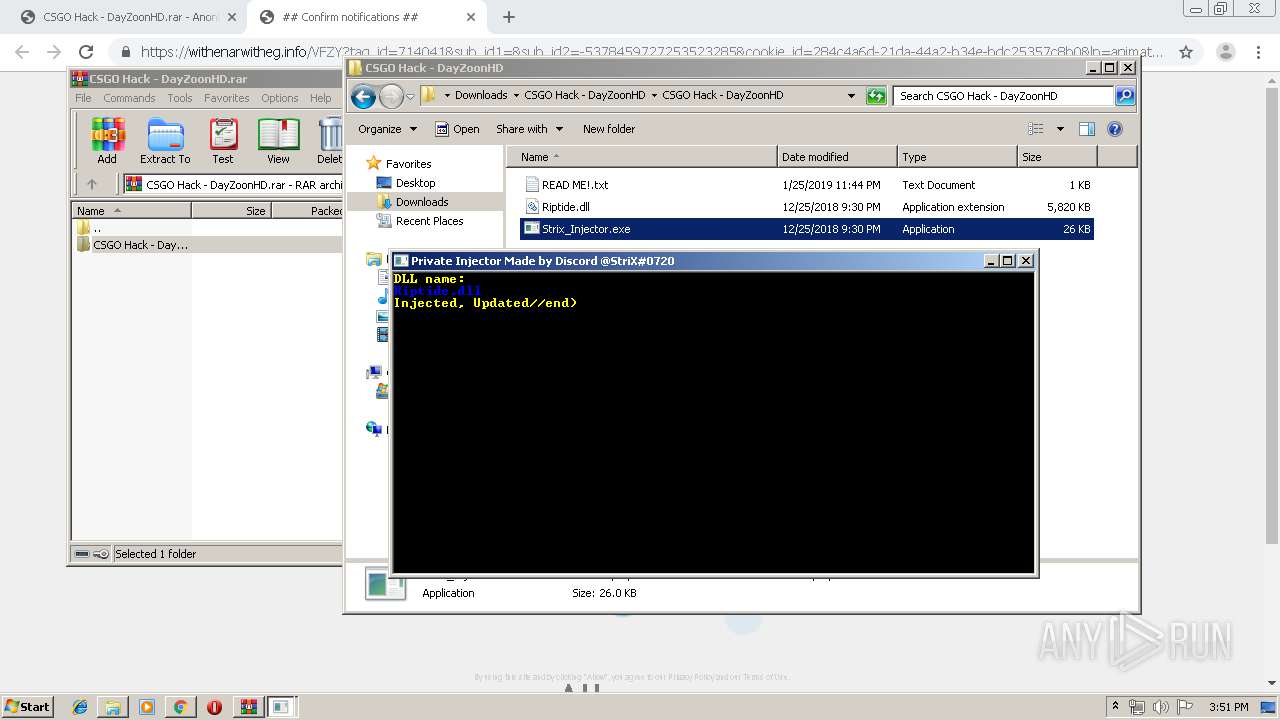
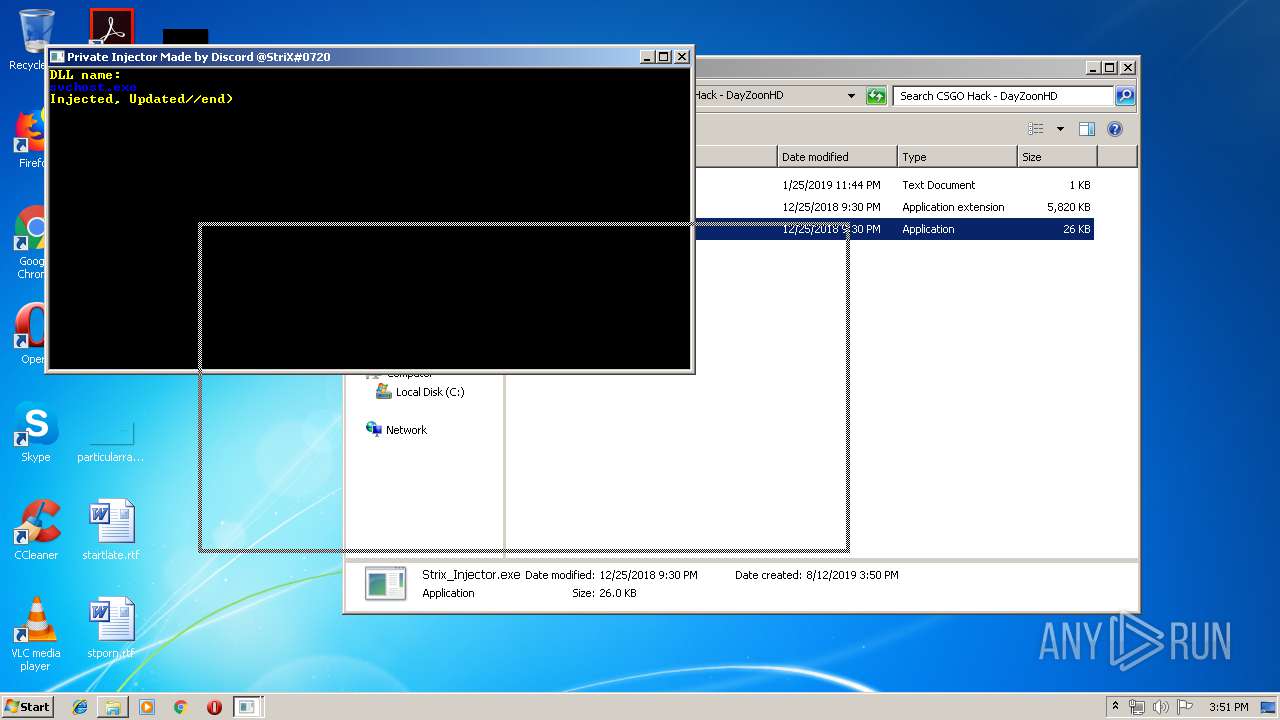
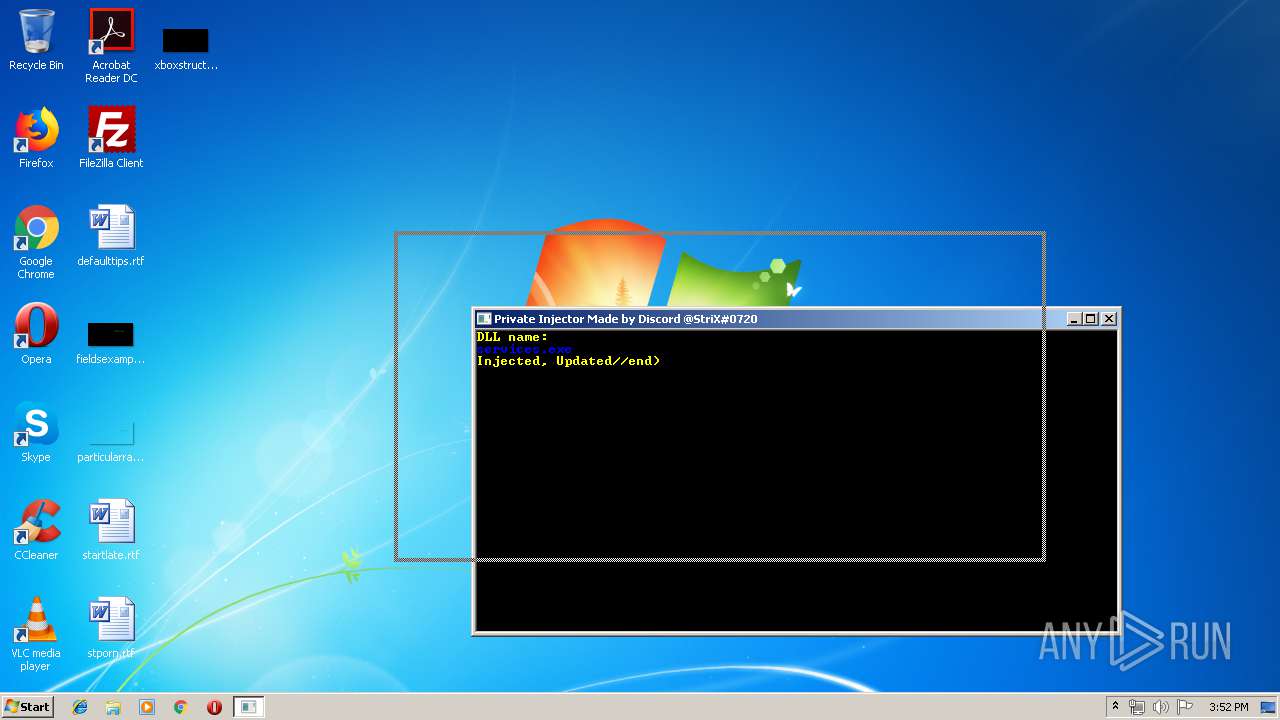
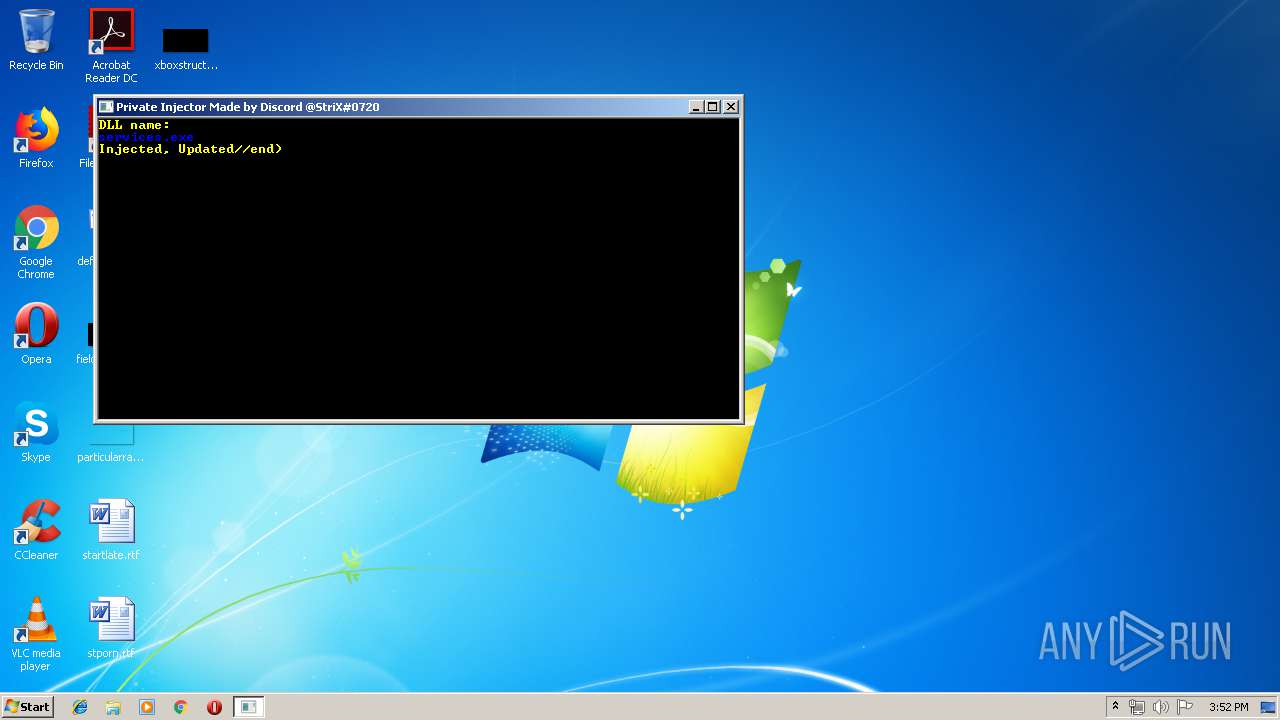
MALICIOUS
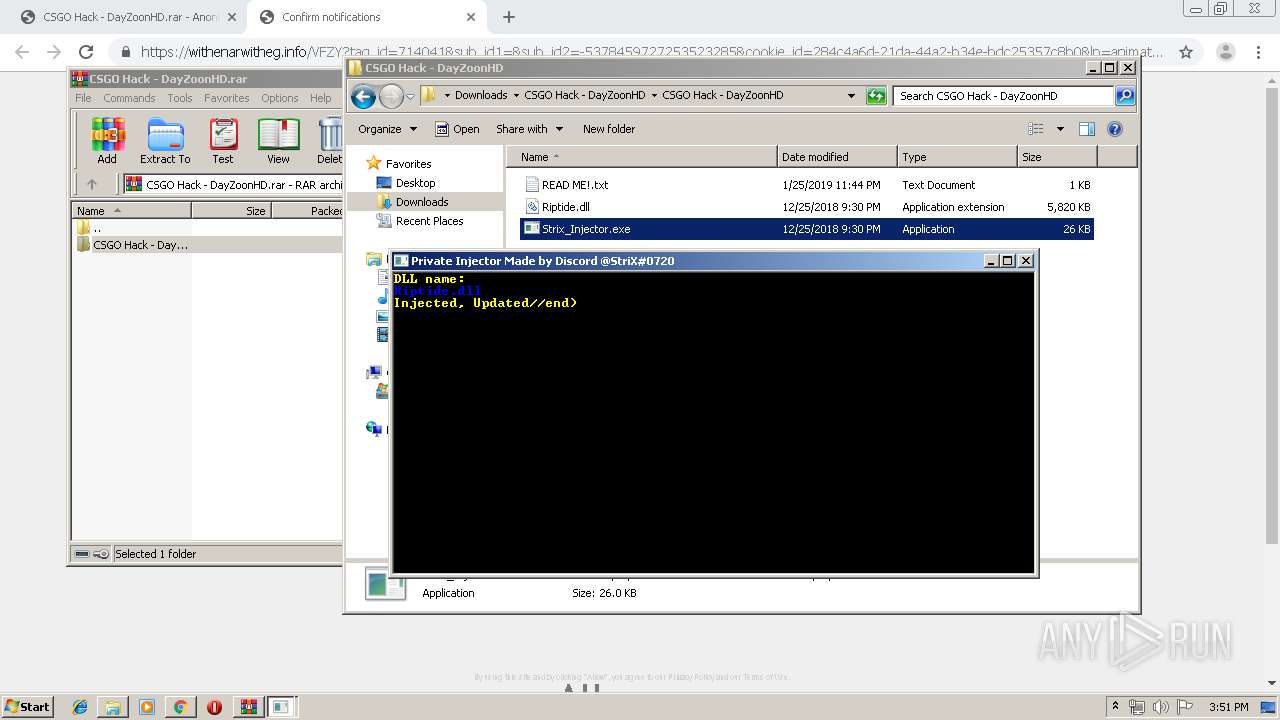
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1512)
Application was dropped or rewritten from another process
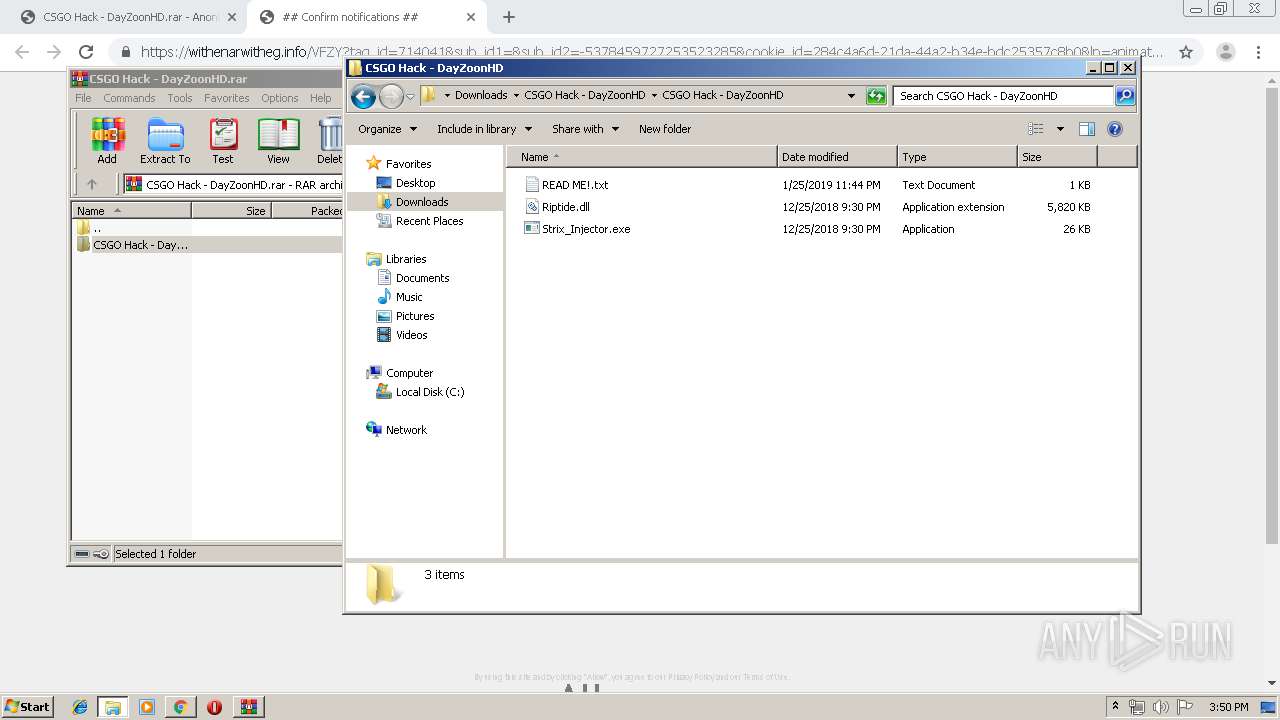
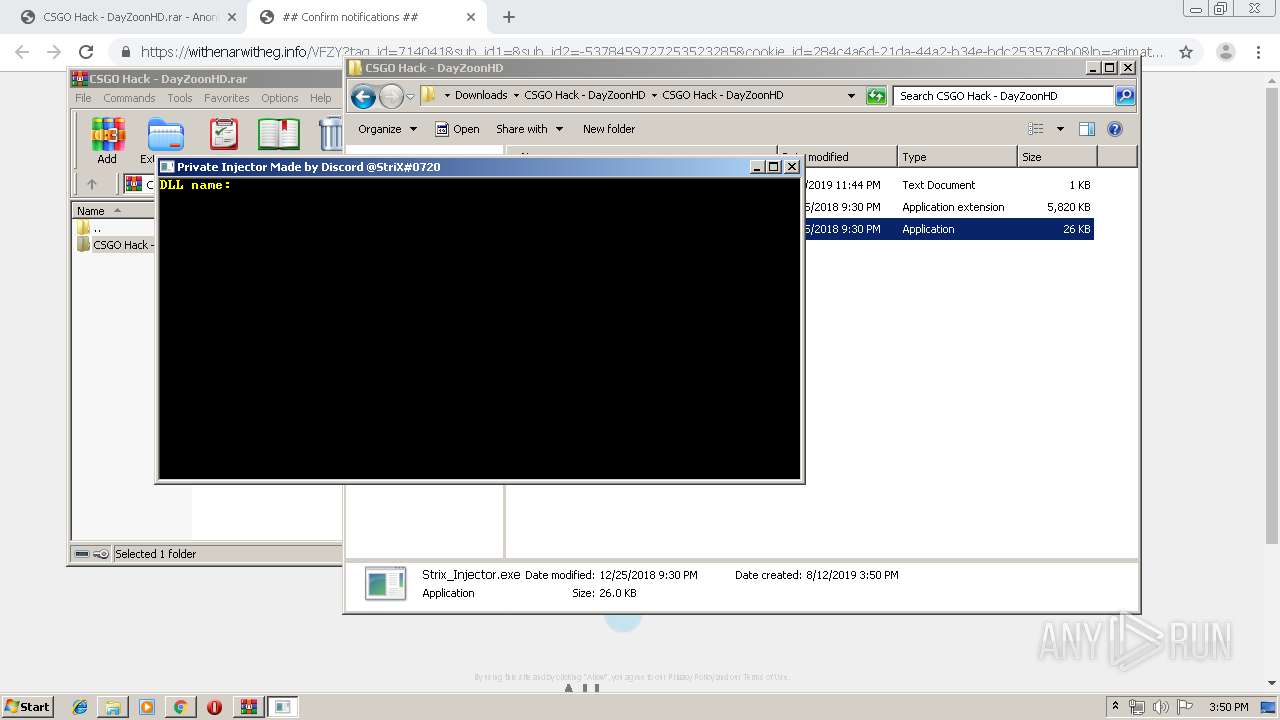
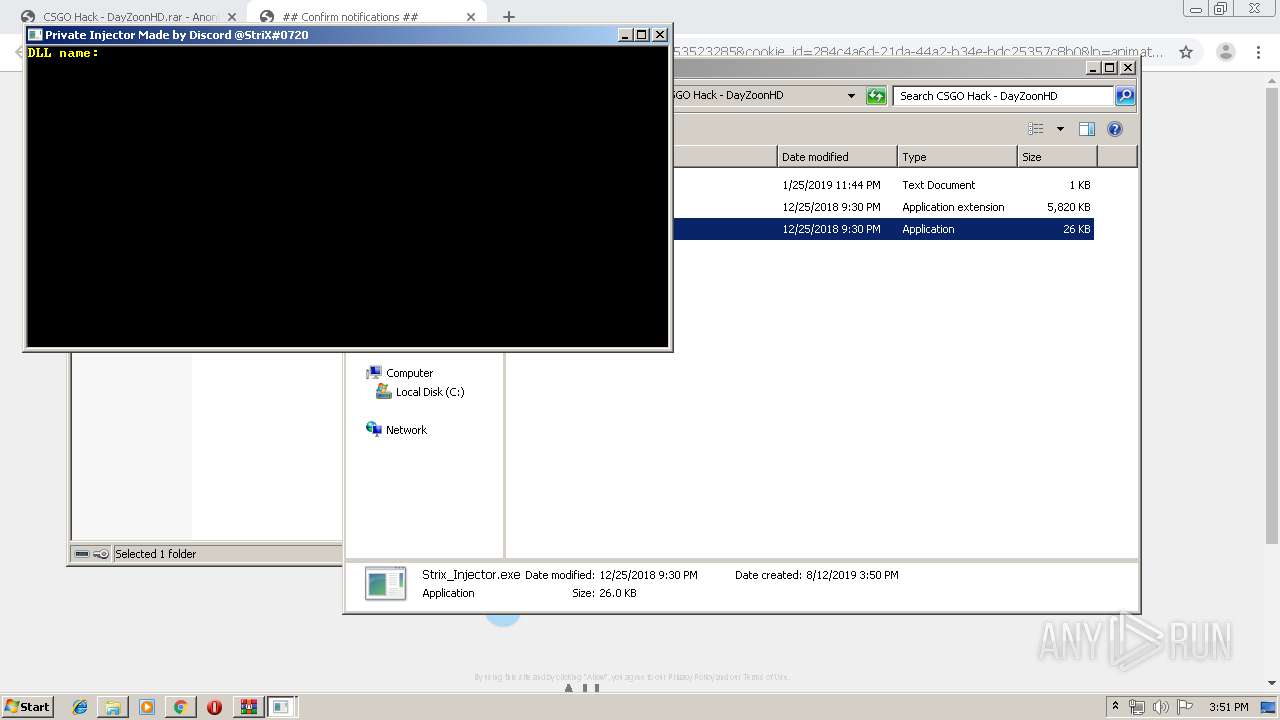
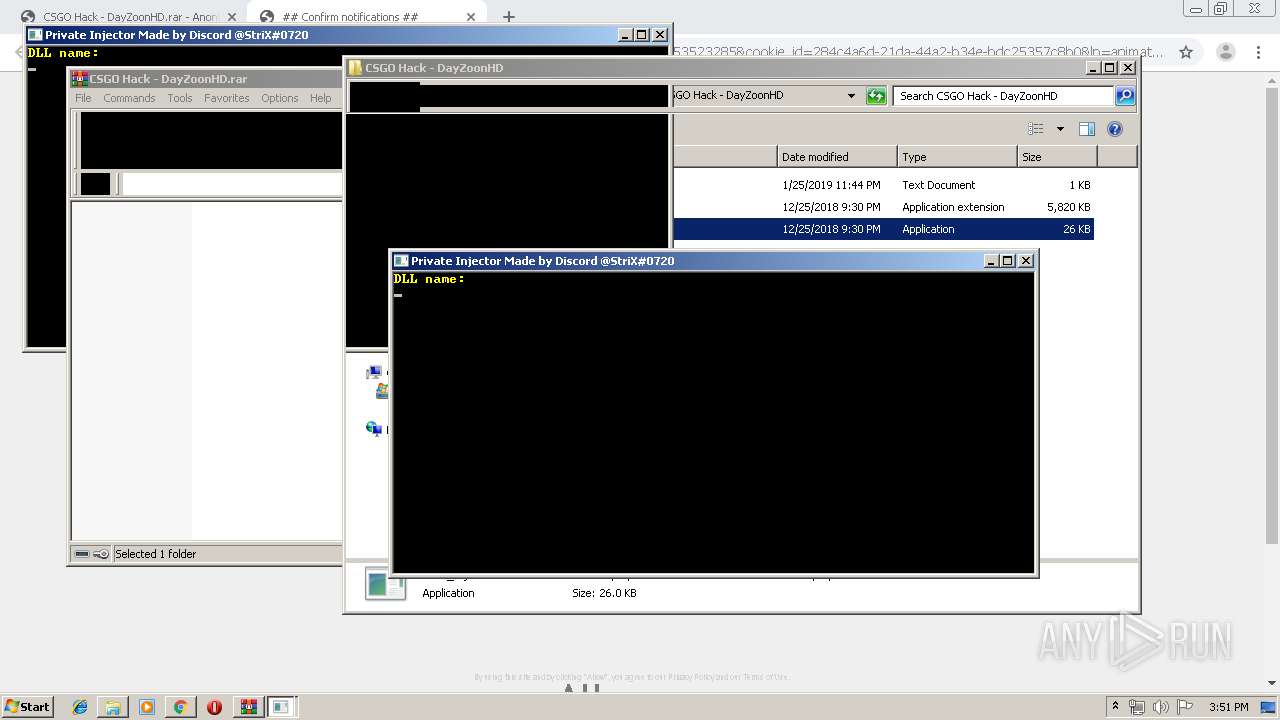
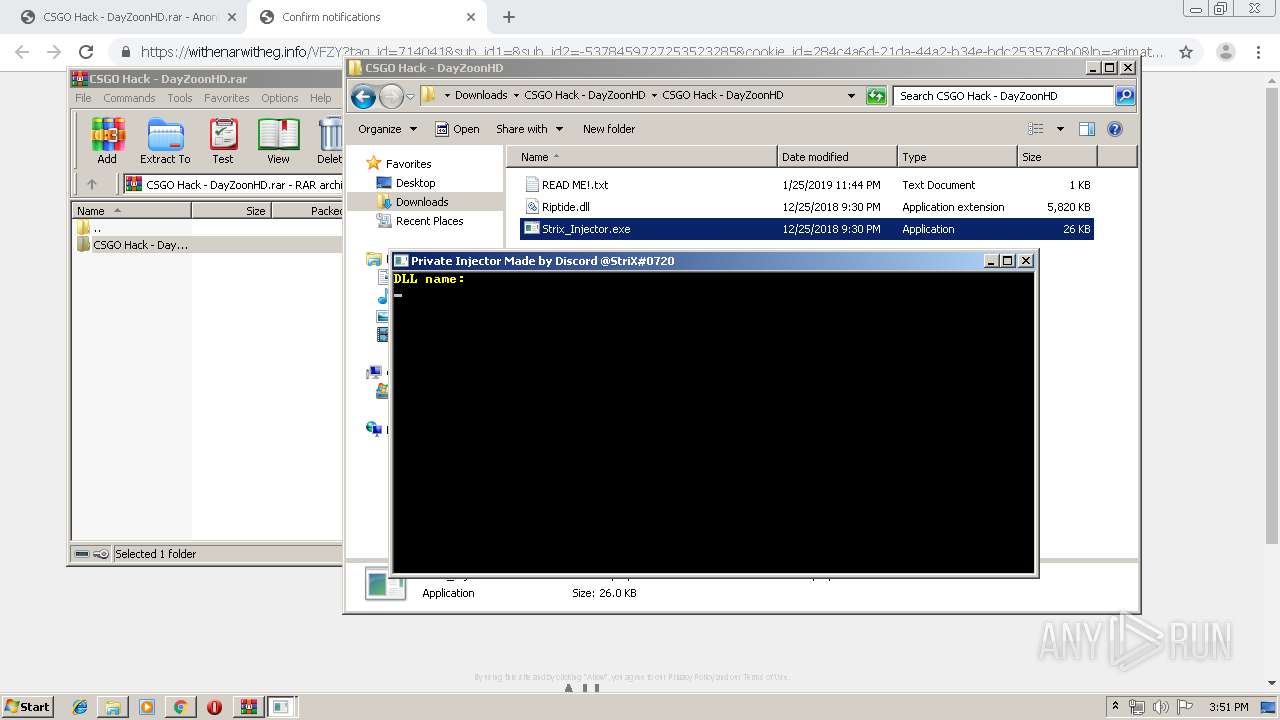
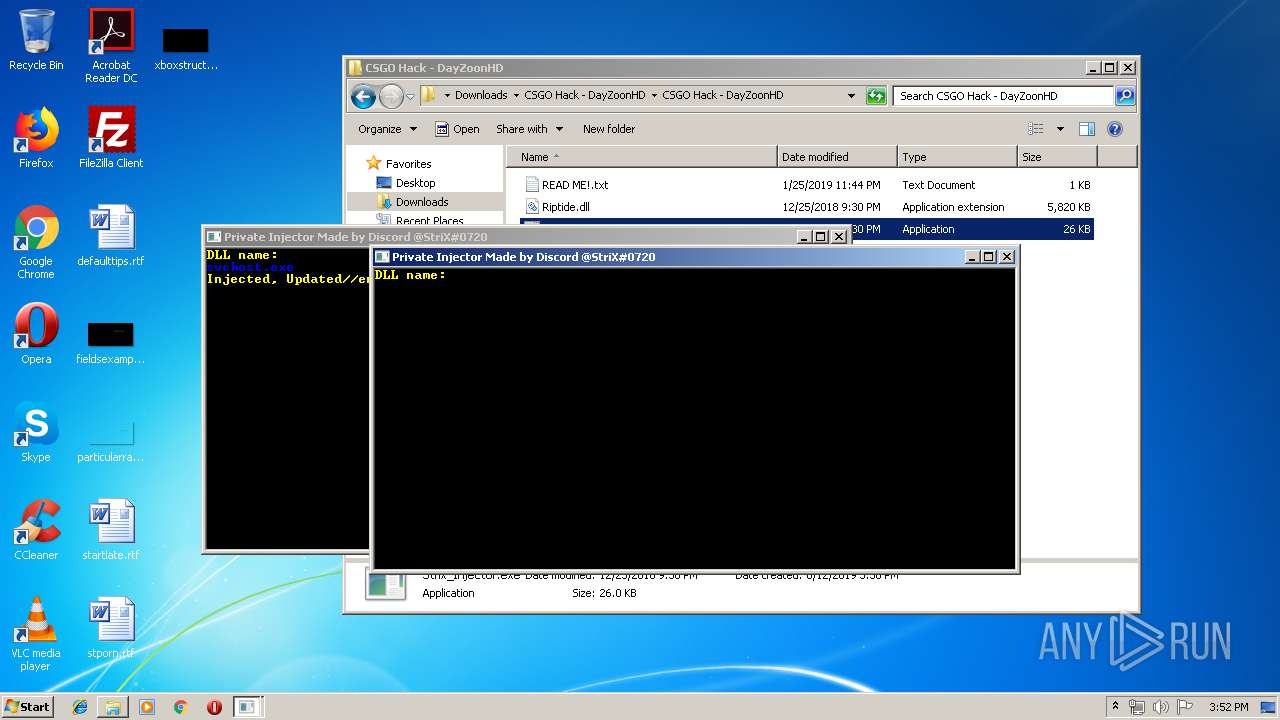
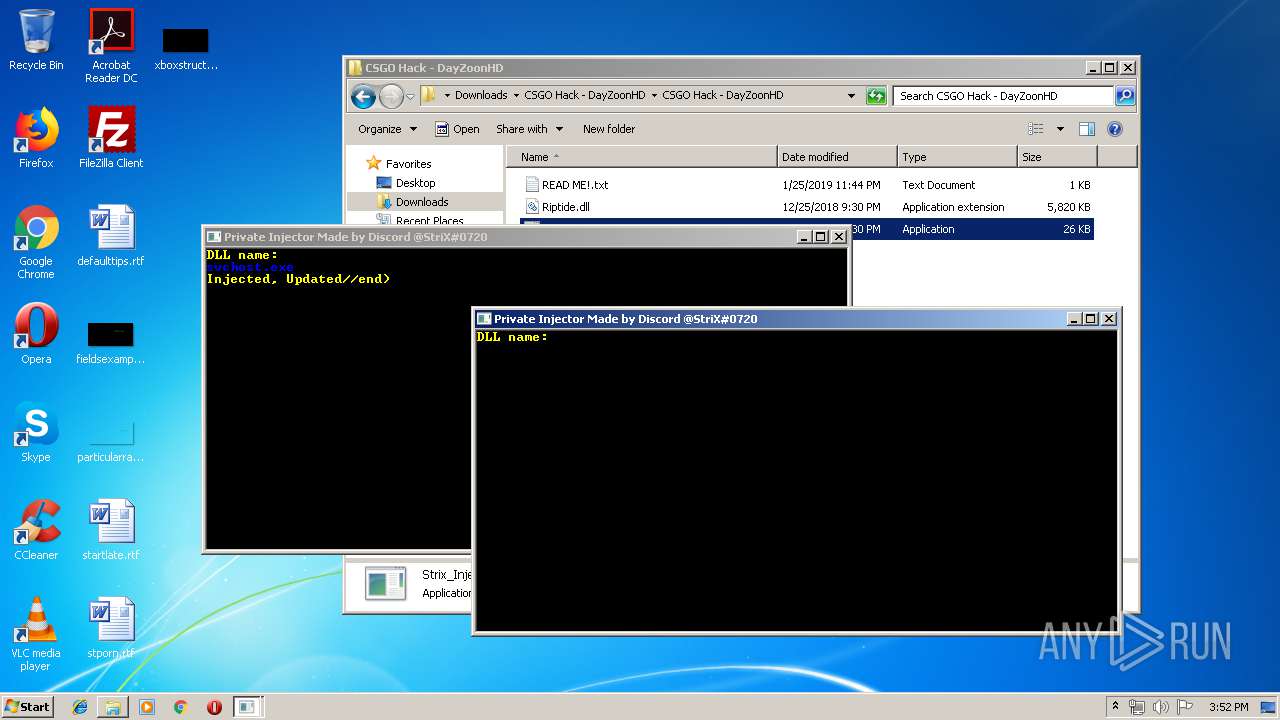
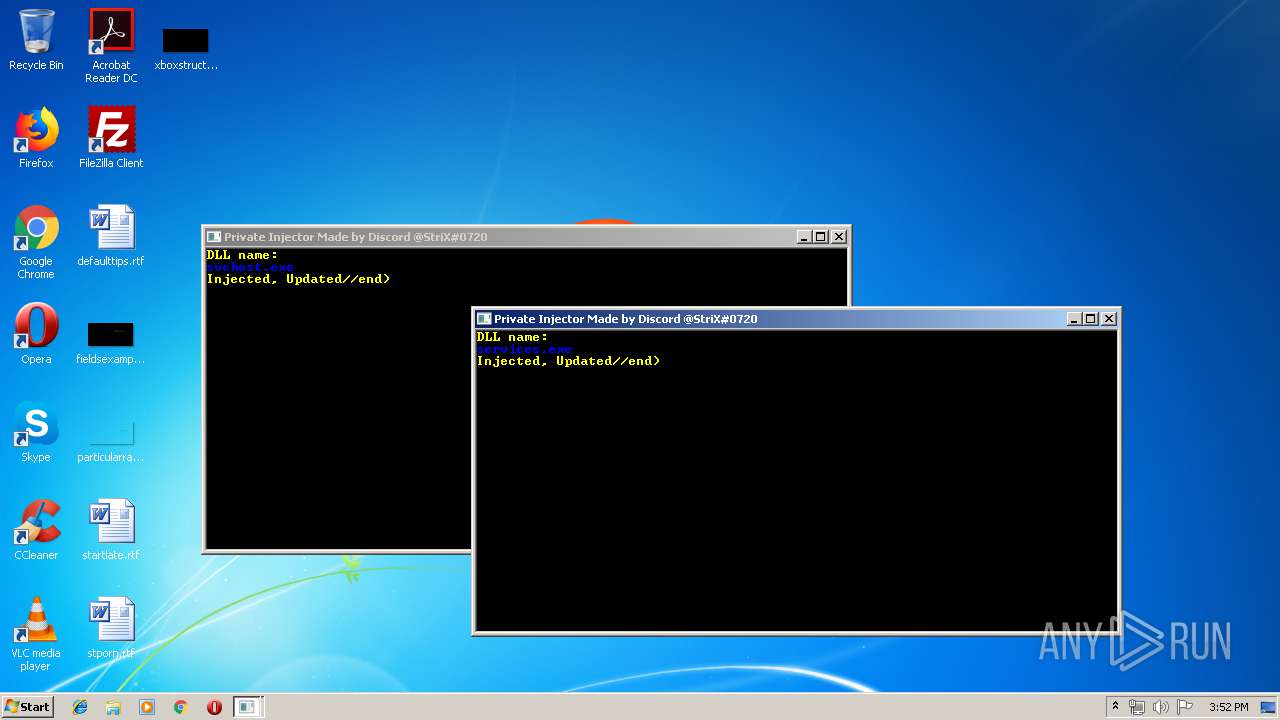
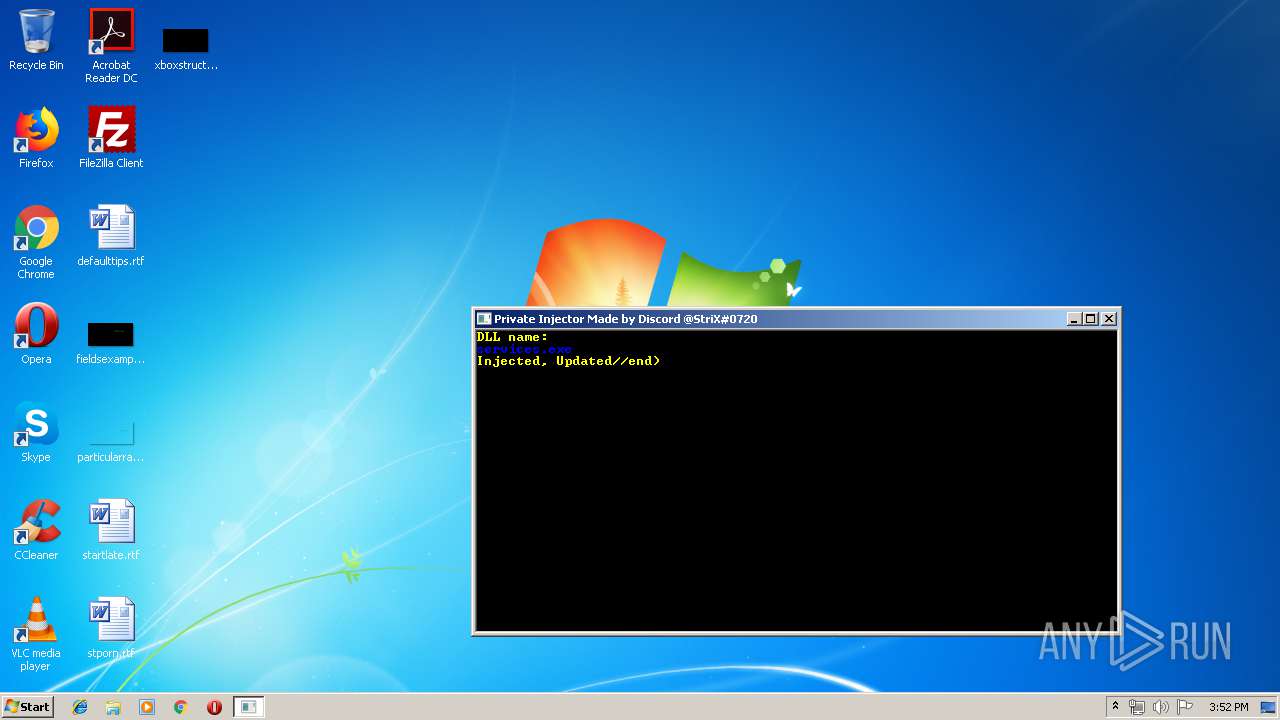
- Strix_Injector.exe (PID: 3628)
- Strix_Injector.exe (PID: 1580)
- Strix_Injector.exe (PID: 2352)
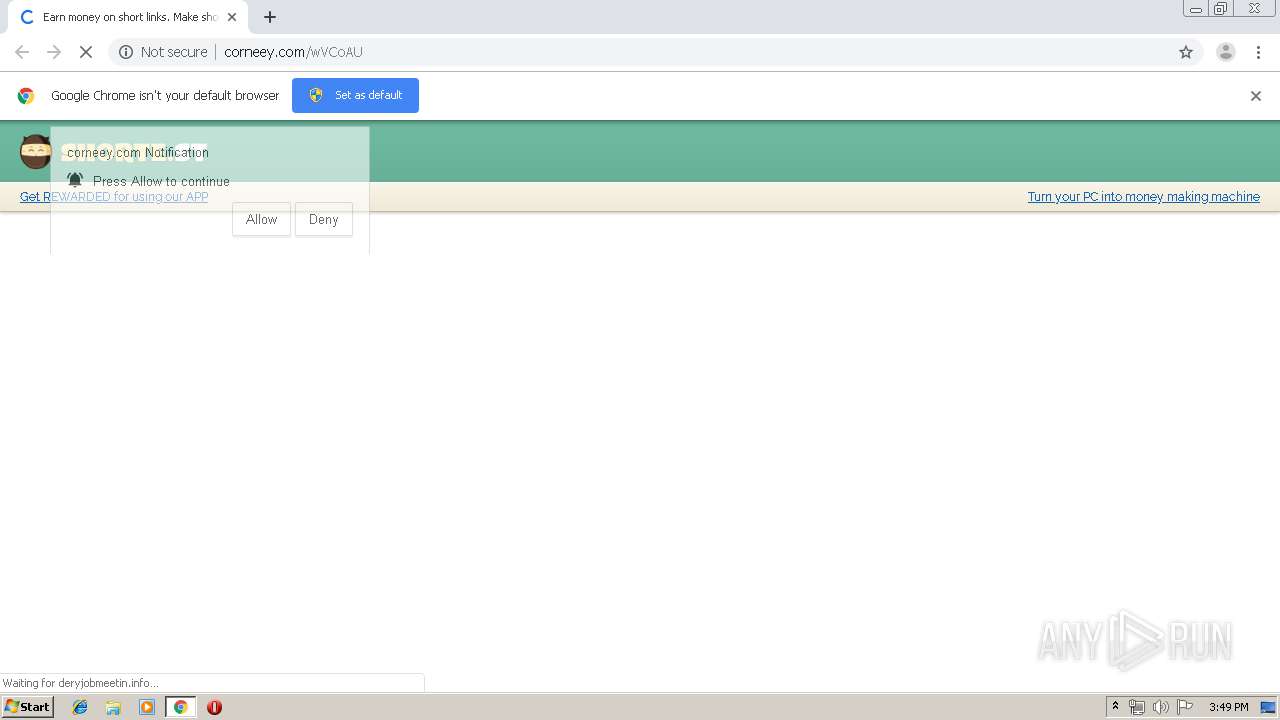
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2308)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 300)
INFO
Creates files in the user directory
- chrome.exe (PID: 2308)
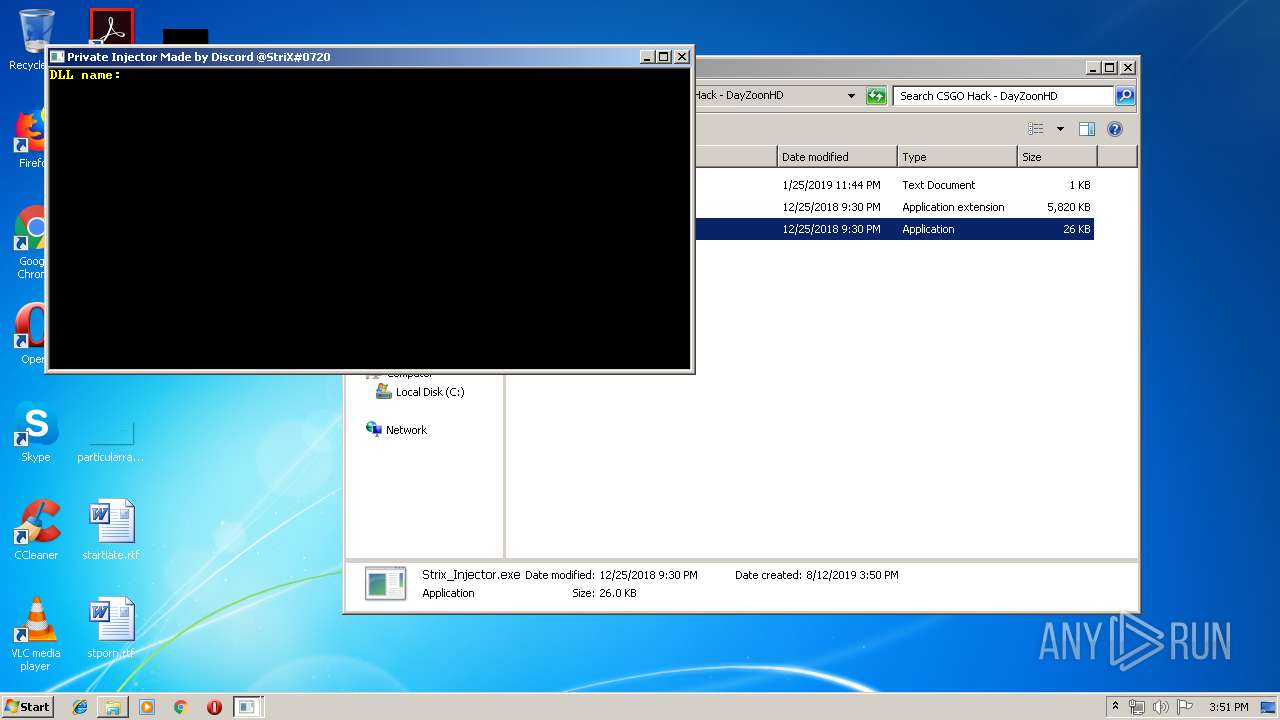
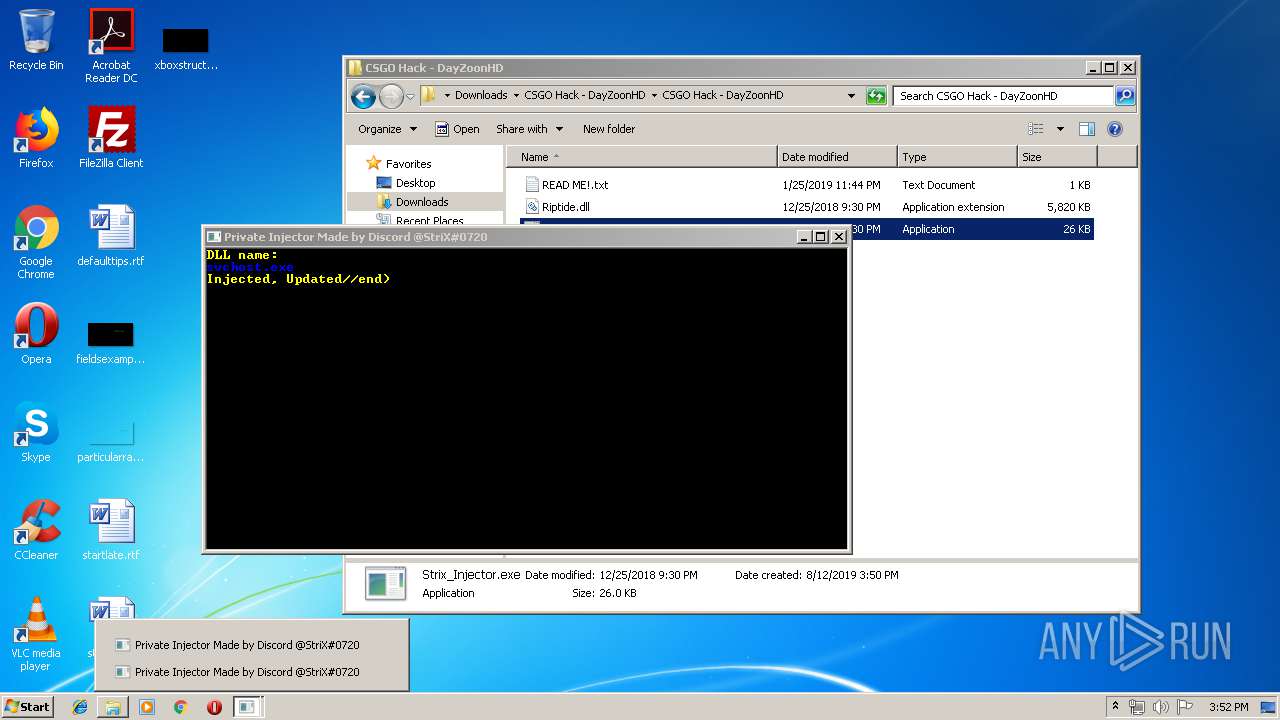
Manual execution by user
- Strix_Injector.exe (PID: 2352)
- Strix_Injector.exe (PID: 1580)
- chrome.exe (PID: 1212)
- Strix_Injector.exe (PID: 3628)
- explorer.exe (PID: 2860)
- NOTEPAD.EXE (PID: 680)
Reads Internet Cache Settings
- chrome.exe (PID: 2308)
Application launched itself
- chrome.exe (PID: 1212)
- chrome.exe (PID: 2308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
101
Monitored processes
61
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
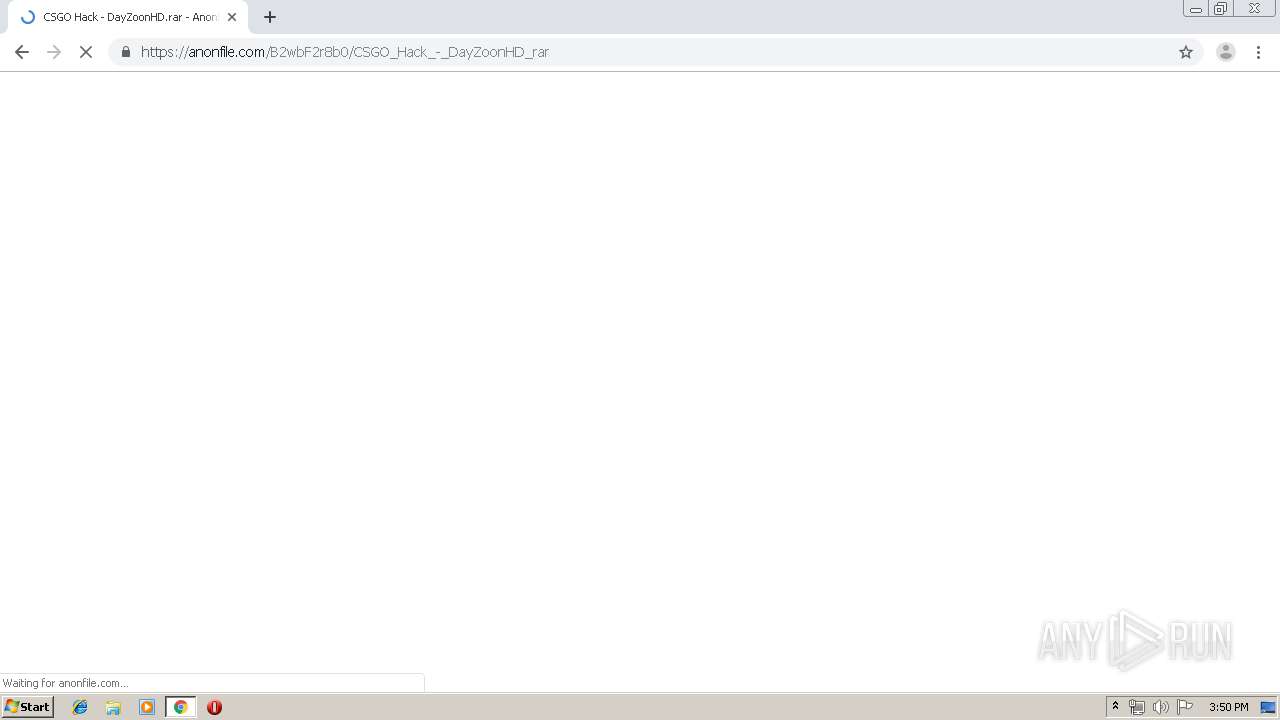
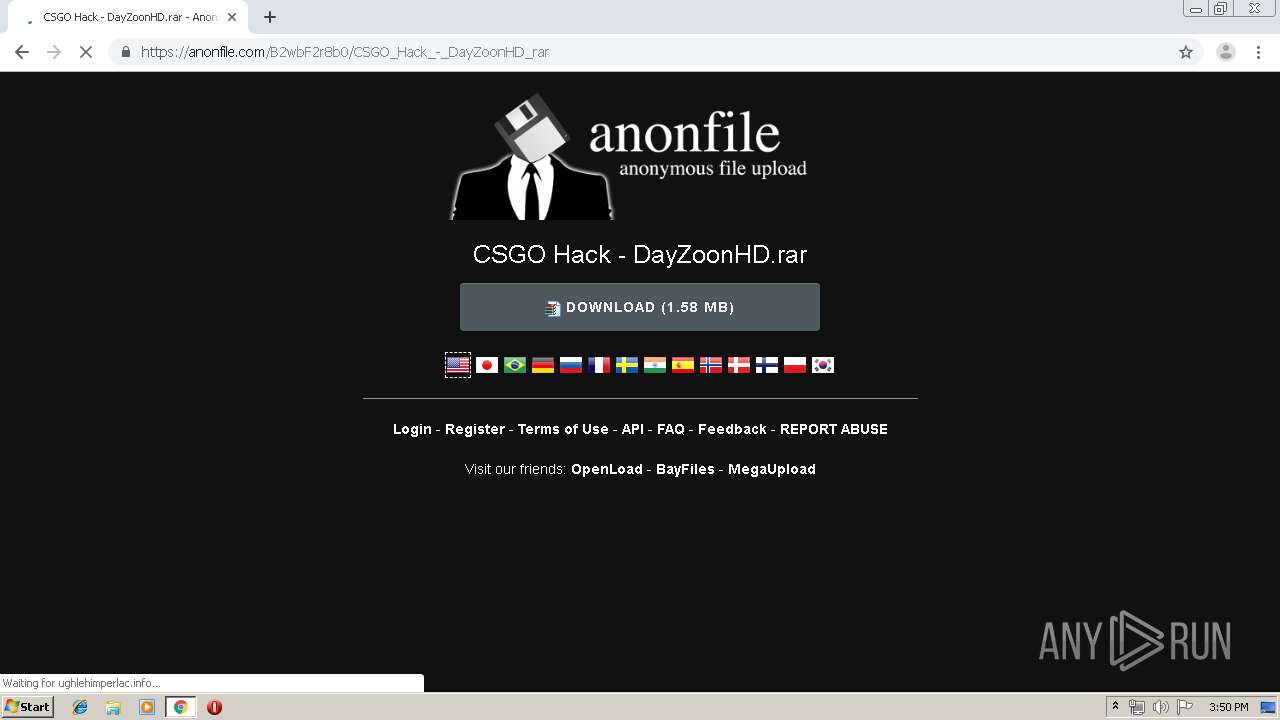
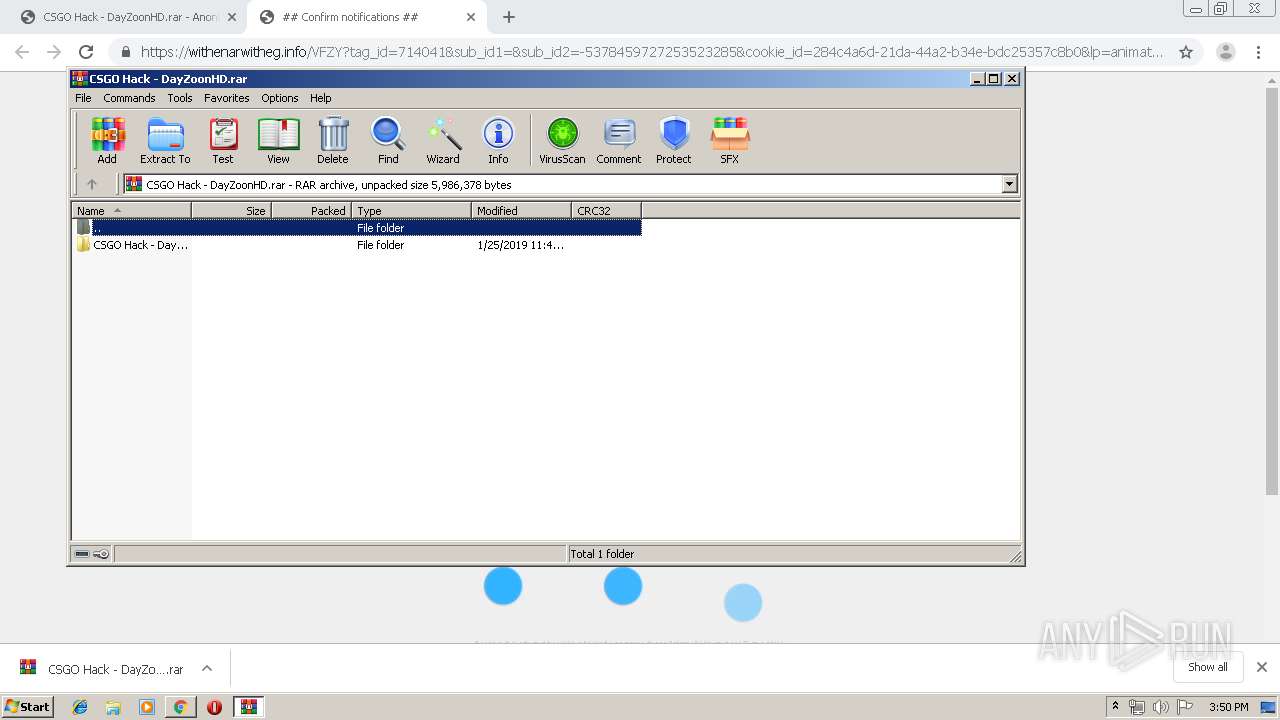
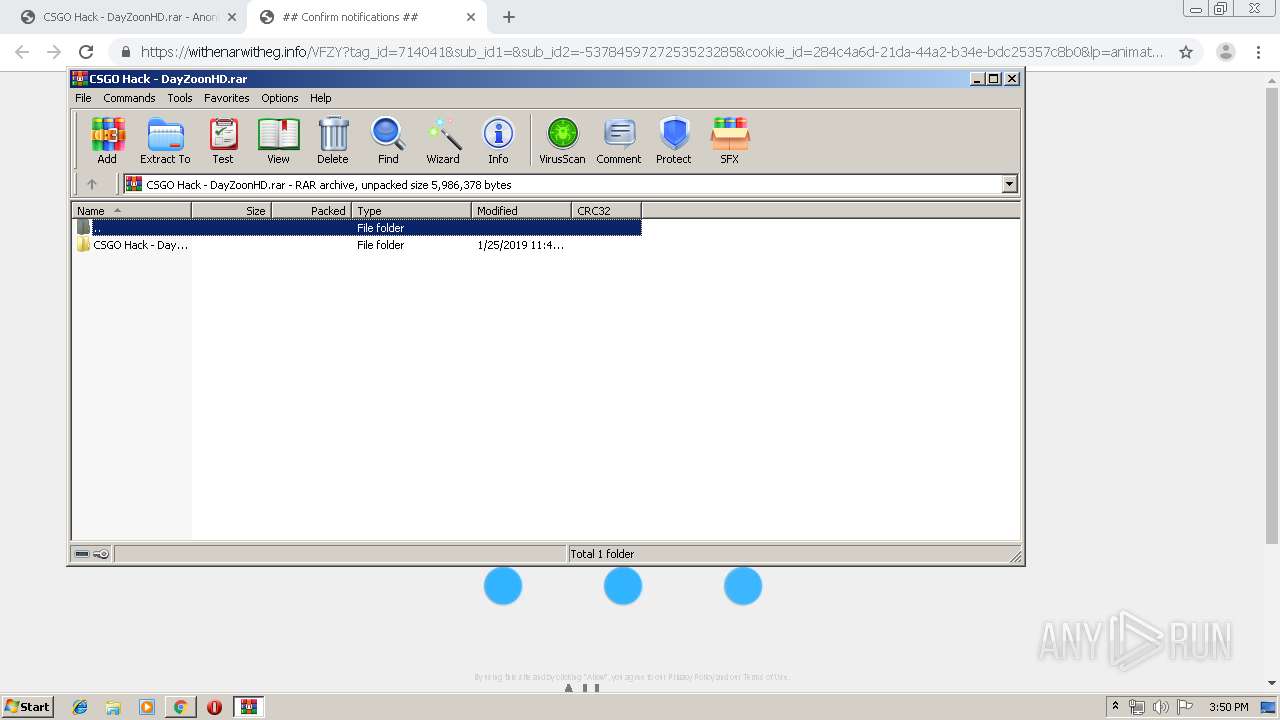
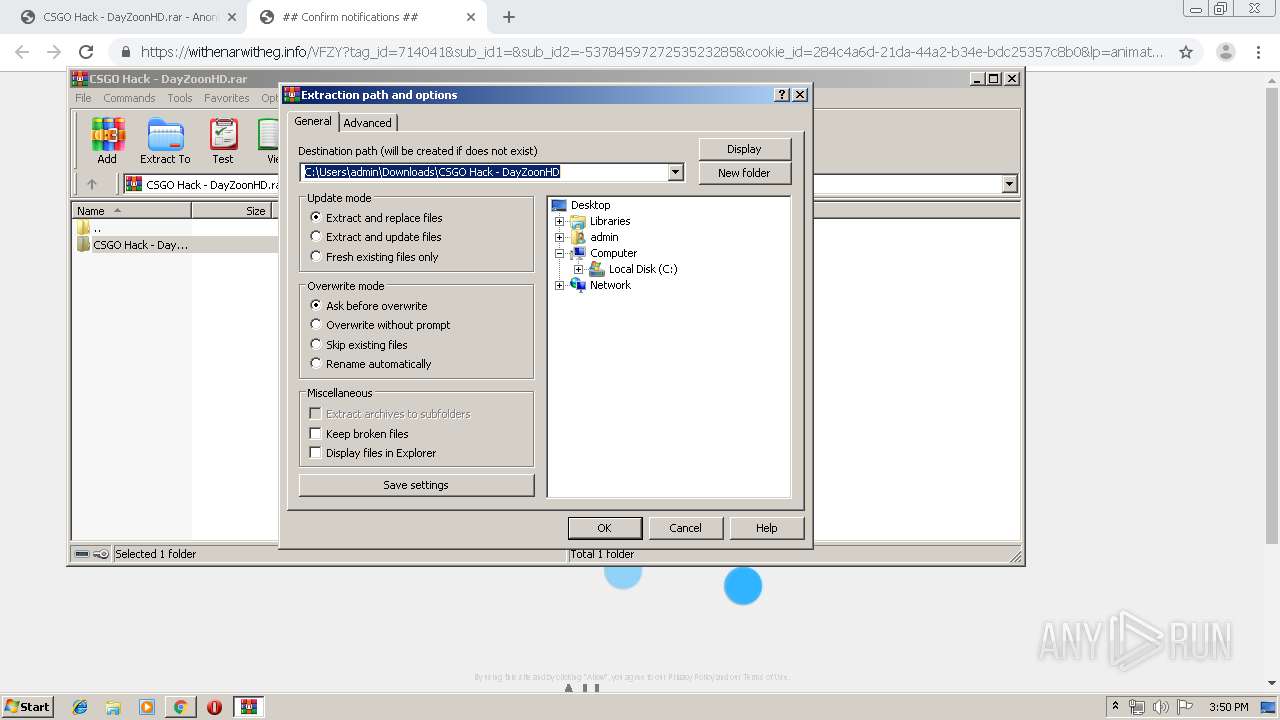
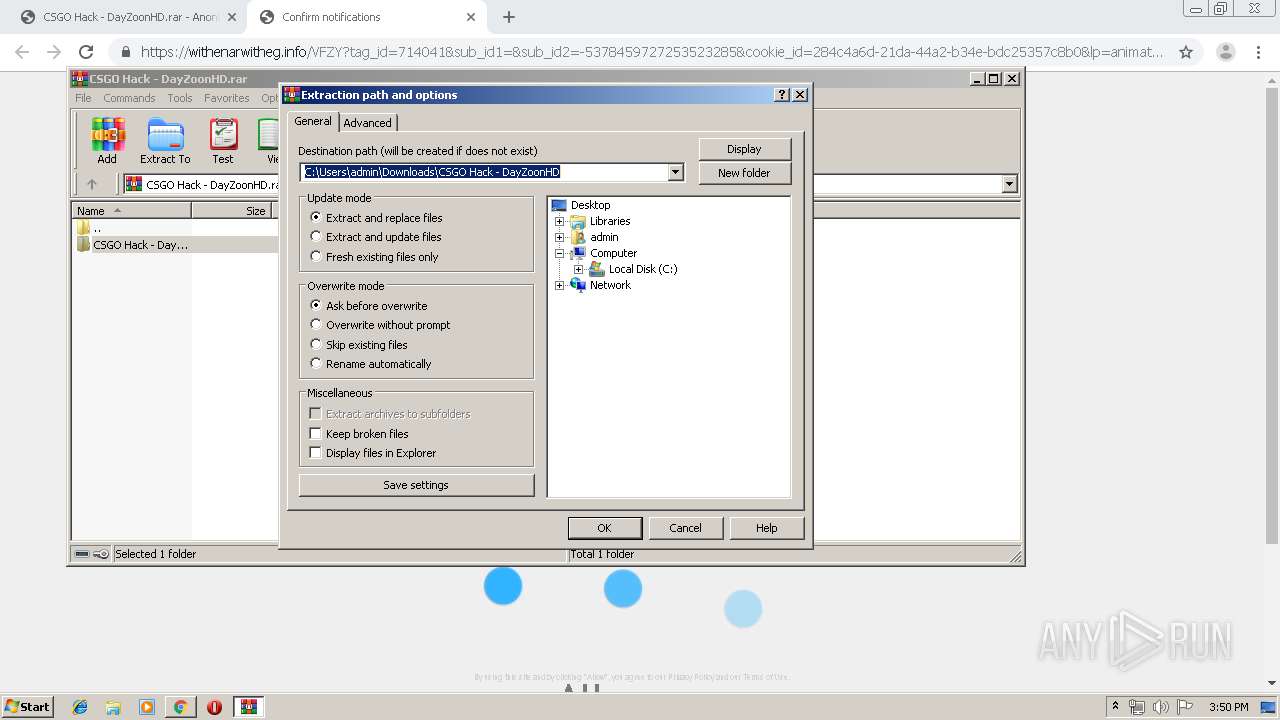
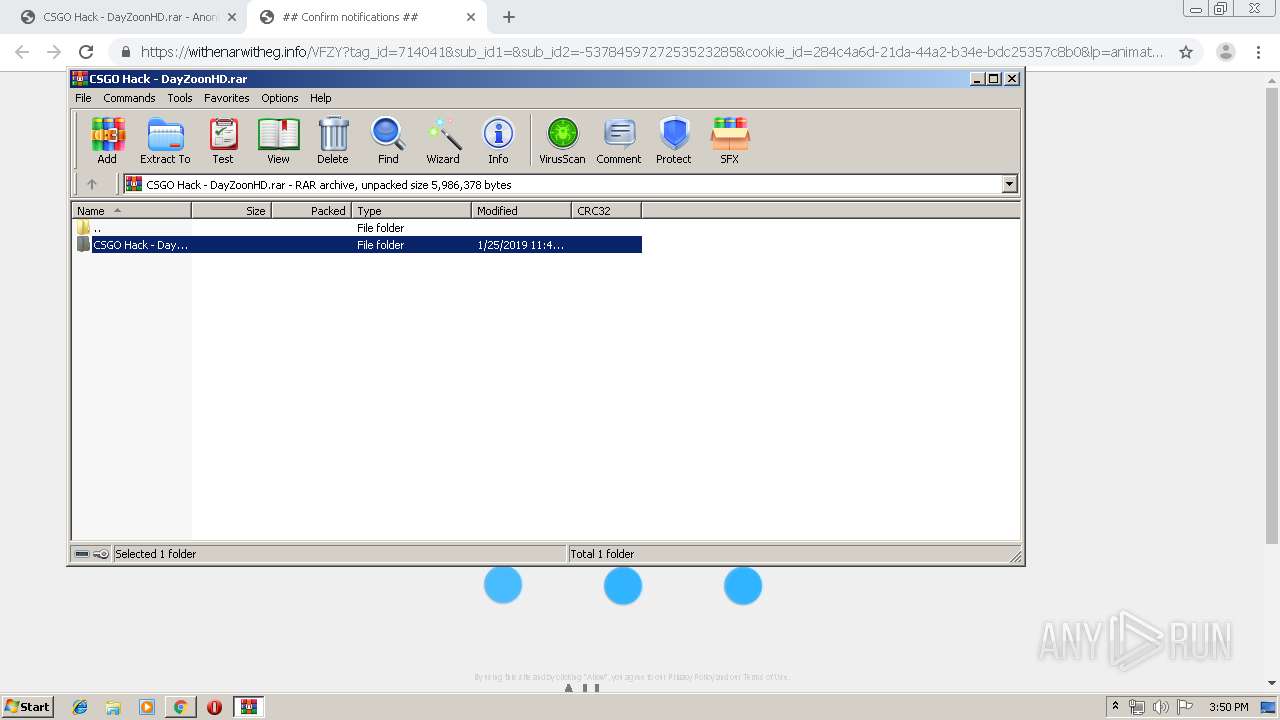
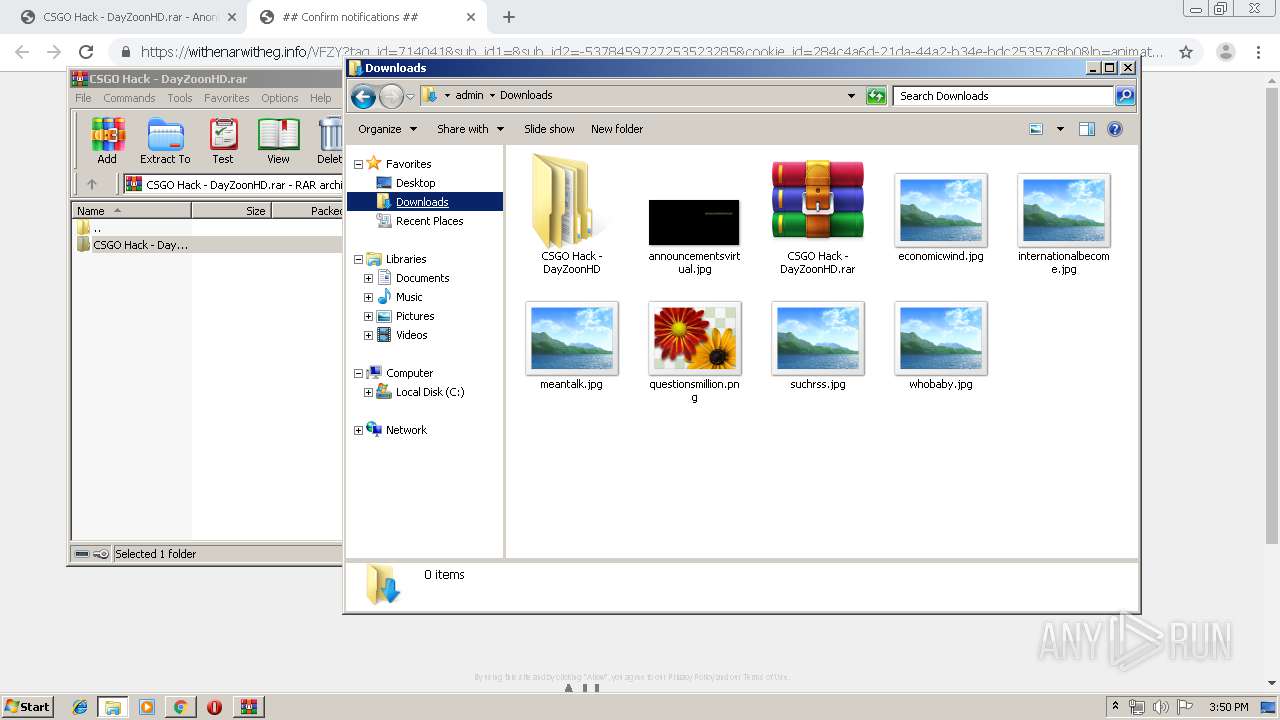
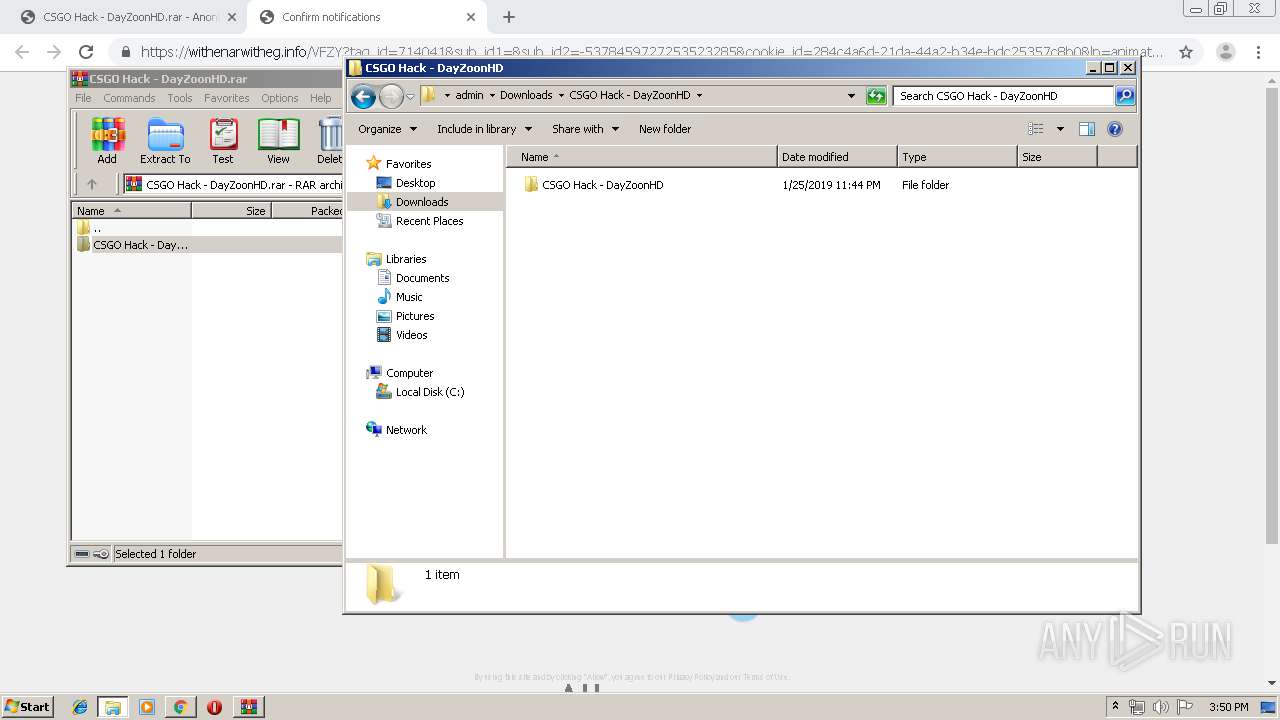
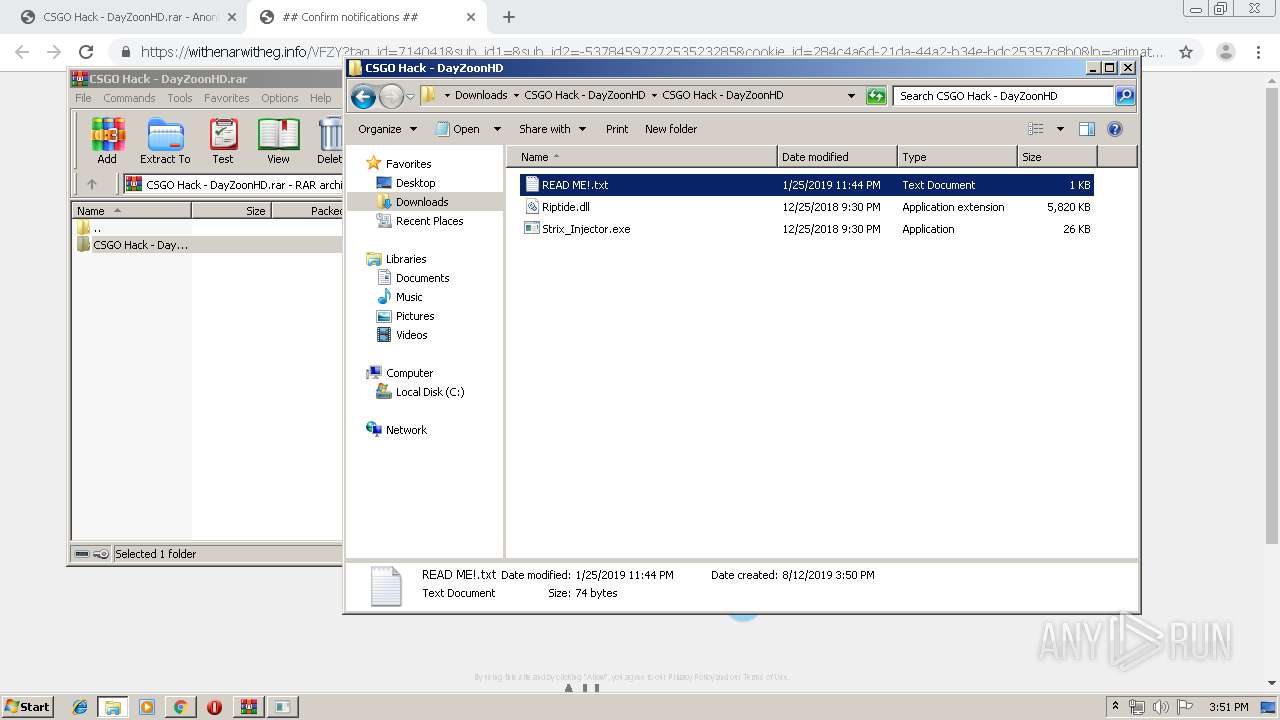
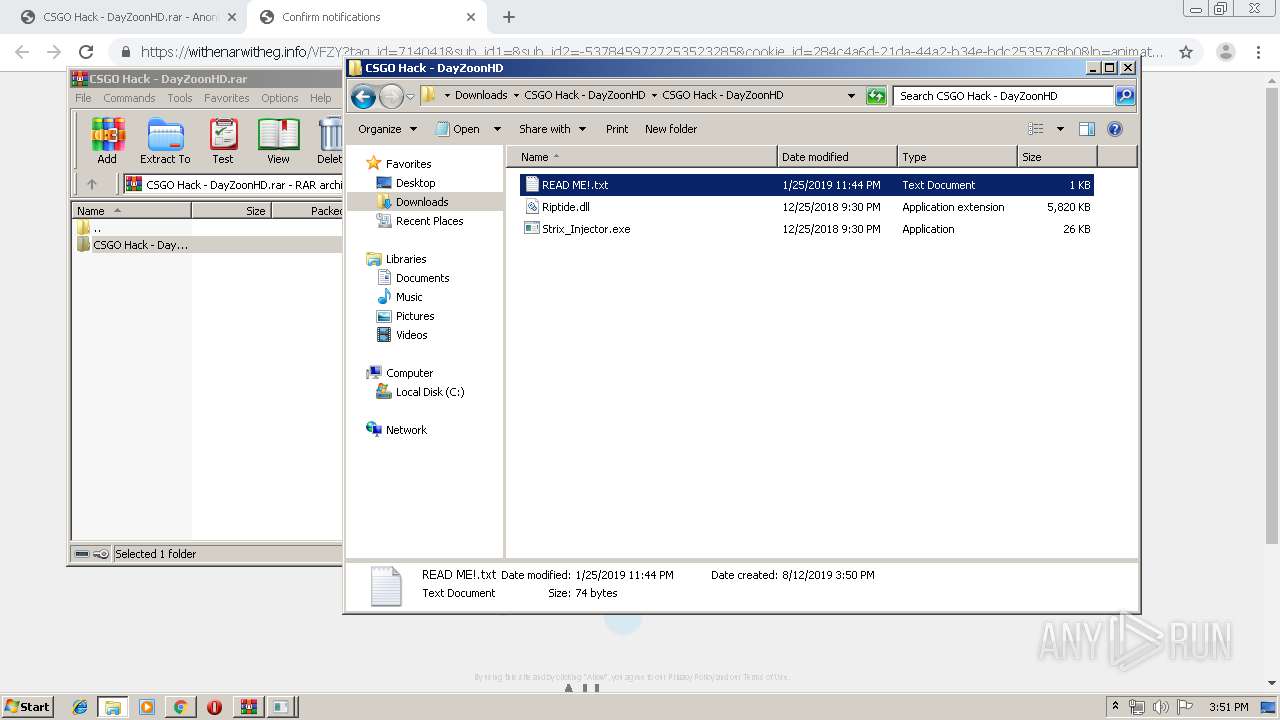
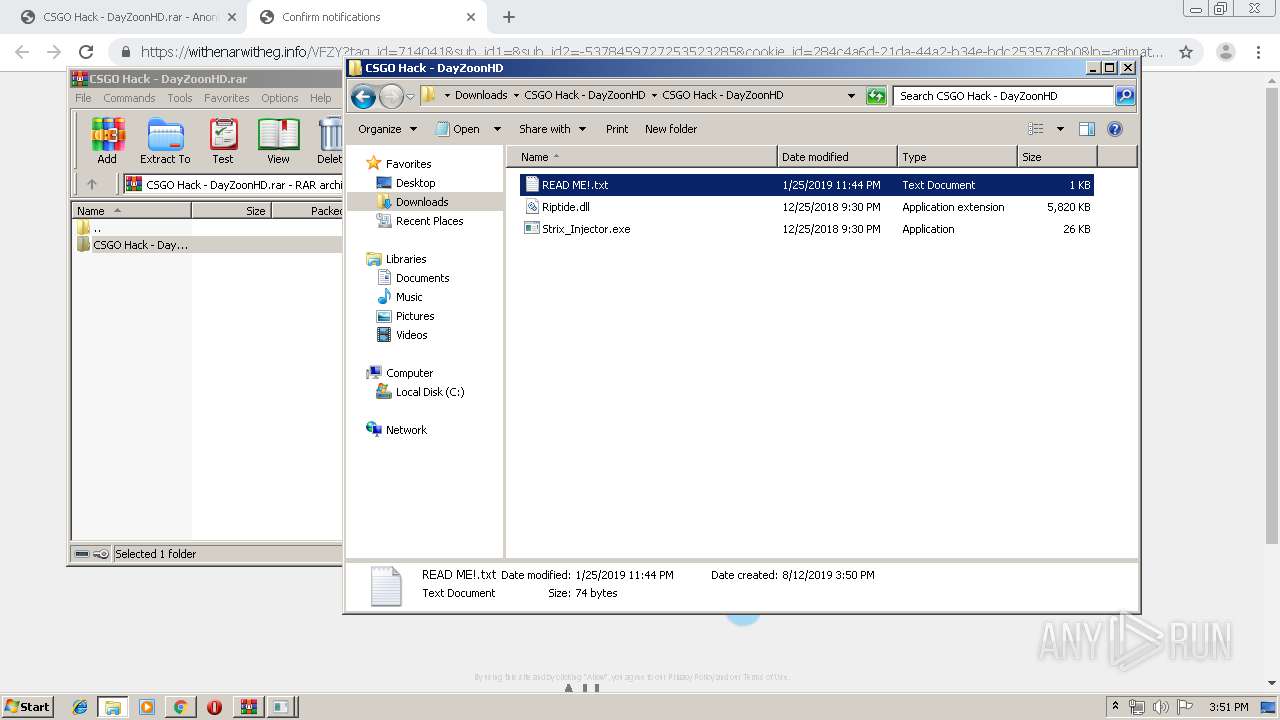
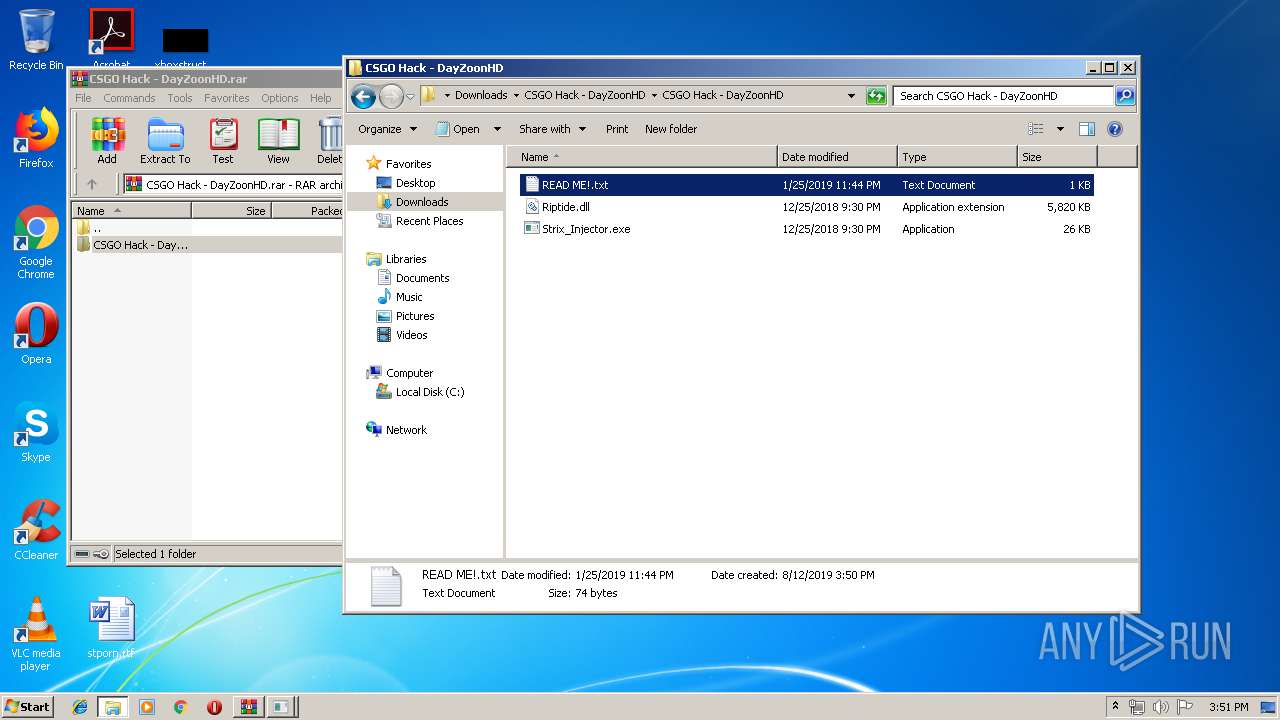
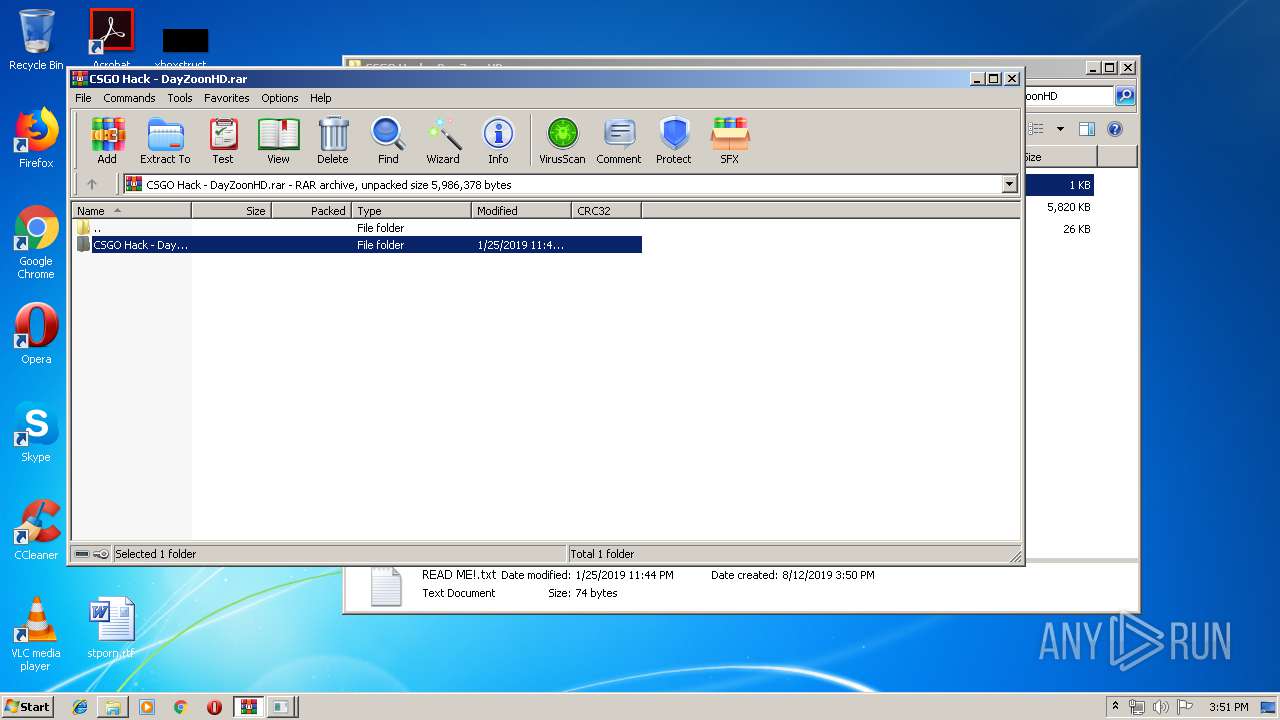
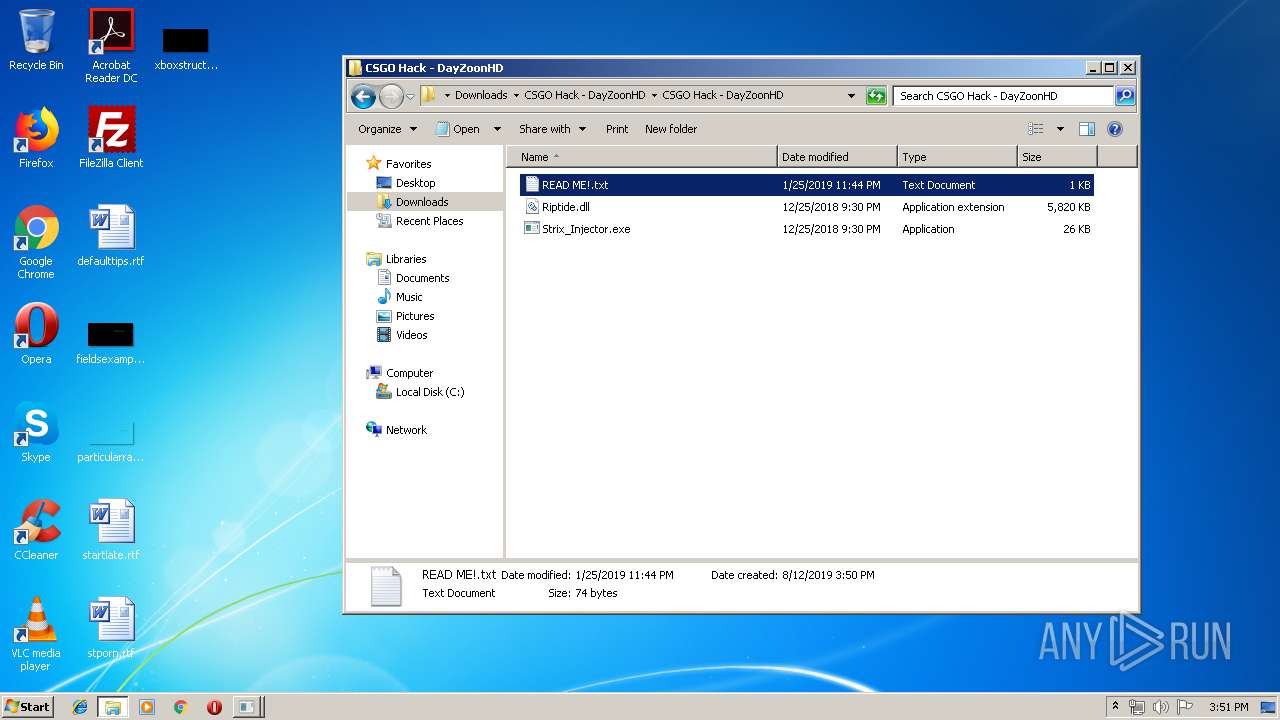
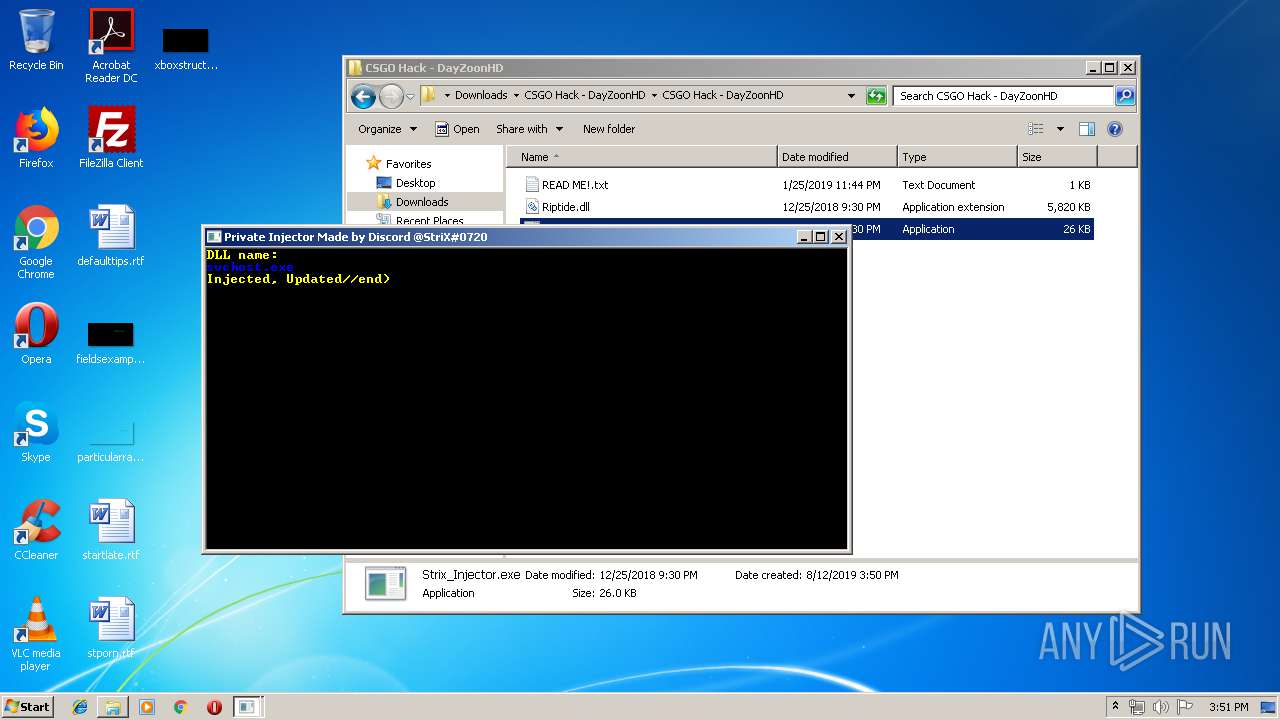
| 300 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\CSGO Hack - DayZoonHD.rar" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,7171244953509097964,16700812939857532439,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16526085298790530592 --mojo-platform-channel-handle=3540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\CSGO Hack - DayZoonHD\CSGO Hack - DayZoonHD\READ ME!.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9471699801765543440,5754924135880875235,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11475583249601490146 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,7171244953509097964,16700812939857532439,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7383496492319763294 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9471699801765543440,5754924135880875235,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16604731905328638066 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1512 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe13_ Global\UsGthrCtrlFltPipeMssGthrPipe13 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\Downloads\CSGO Hack - DayZoonHD\CSGO Hack - DayZoonHD\Strix_Injector.exe" | C:\Users\admin\Downloads\CSGO Hack - DayZoonHD\CSGO Hack - DayZoonHD\Strix_Injector.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,7171244953509097964,16700812939857532439,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16618972949746387307 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 975
Read events
1 784
Write events
182
Delete events
9
Modification events
| (PID) Process: | (2308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2308-13210094984517000 |
Value: 259 | |||
| (PID) Process: | (2308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2308) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
145
Text files
321
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF36d2ba.TMP | — | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ad5a6bee-f51e-42d1-bf34-d1f98dba8d51.tmp | — | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF36d2ba.TMP | text | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
94
TCP/UDP connections
136
DNS requests
91
Threats
1
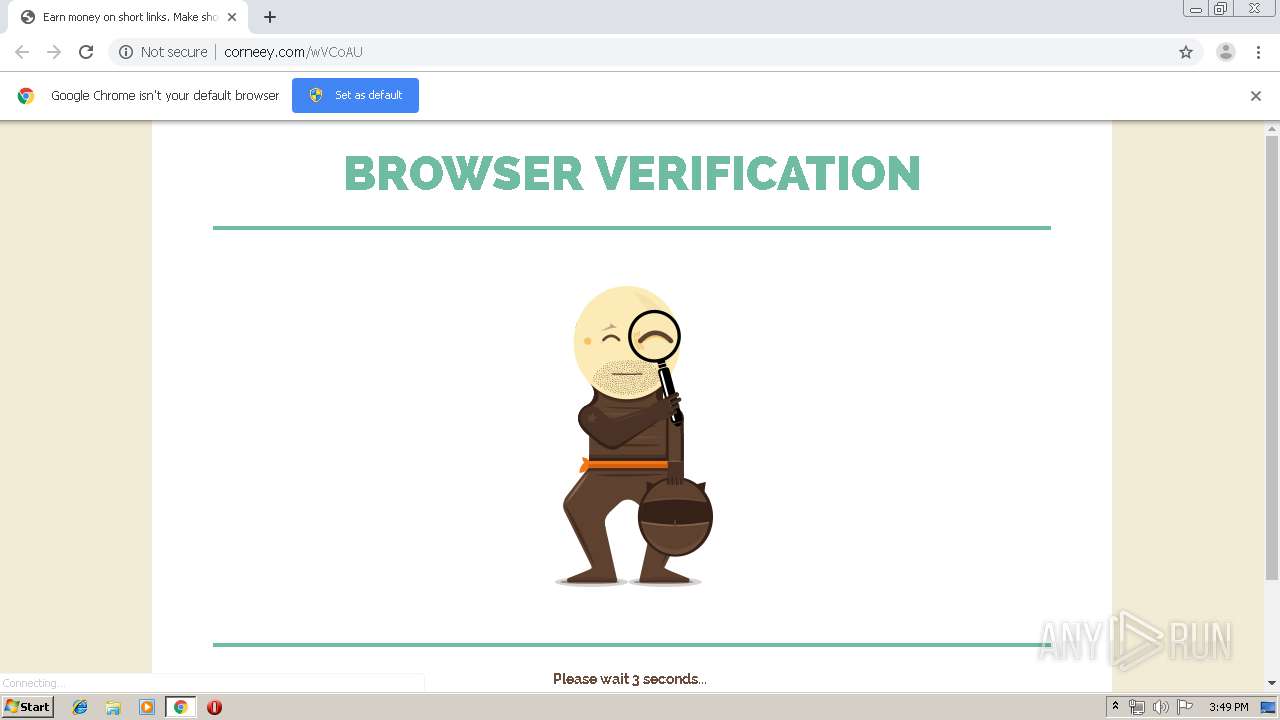
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
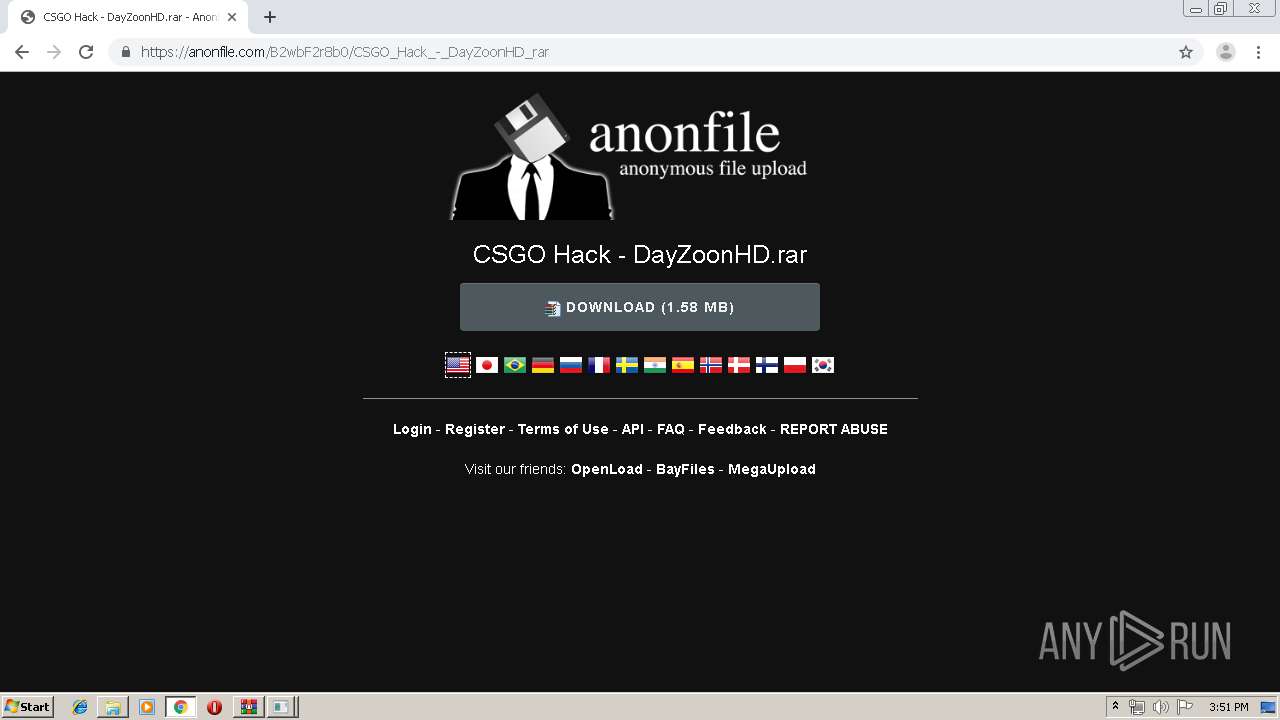
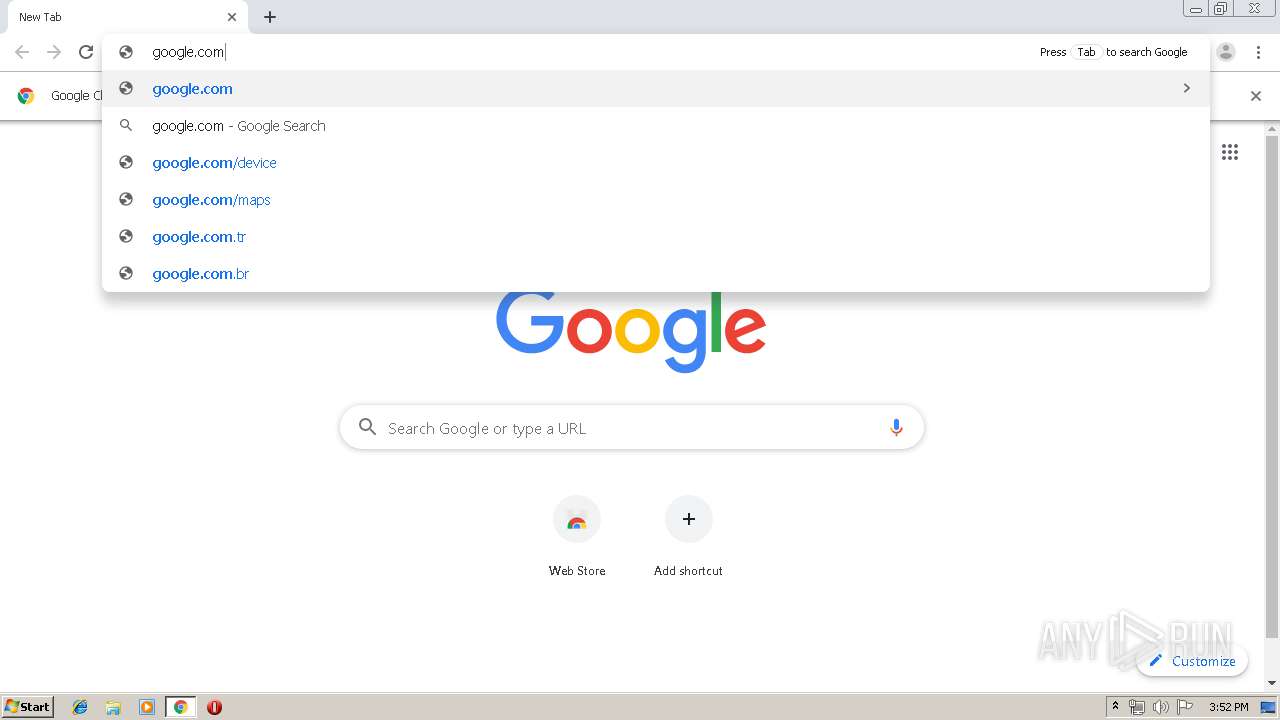
1928 | chrome.exe | OPTIONS | 200 | 35.227.234.224:80 | http://analytics.shorte.st/displayed | US | — | — | whitelisted |
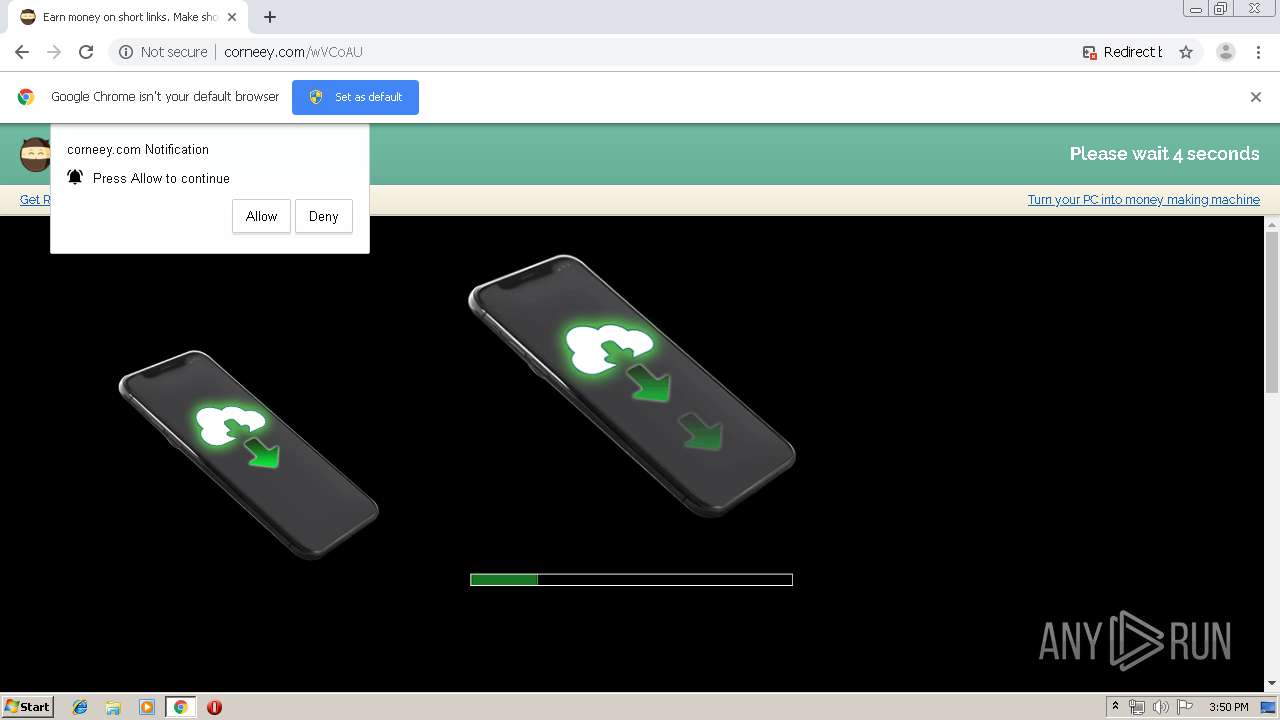
1928 | chrome.exe | GET | 200 | 185.66.120.52:80 | http://corneey.com/grey_wizard_rewrite_js/?b=KVtYrbk6ZaAP5EPa6u1QBrs1KO3D%2B71rTVLld%2FeZtZs%3D | PL | text | 2.05 Kb | whitelisted |
1928 | chrome.exe | GET | 403 | 185.66.120.52:80 | http://corneey.com/wVCoAU | PL | html | 1.94 Kb | whitelisted |
1928 | chrome.exe | GET | 200 | 185.66.120.52:80 | http://corneey.com/grey_wizard_rewrite/shst_en/error/smeweb_error.css | PL | text | 375 Kb | whitelisted |
1928 | chrome.exe | GET | 200 | 13.35.254.32:80 | http://d3ud741uvs727m.cloudfront.net/?vudud=716233 | US | text | 32.8 Kb | whitelisted |
1928 | chrome.exe | POST | 200 | 35.227.234.224:80 | http://analytics.shorte.st/displayed | US | — | — | whitelisted |
1928 | chrome.exe | GET | 200 | 185.66.120.52:80 | http://corneey.com/wVCoAU | PL | html | 29.4 Kb | whitelisted |
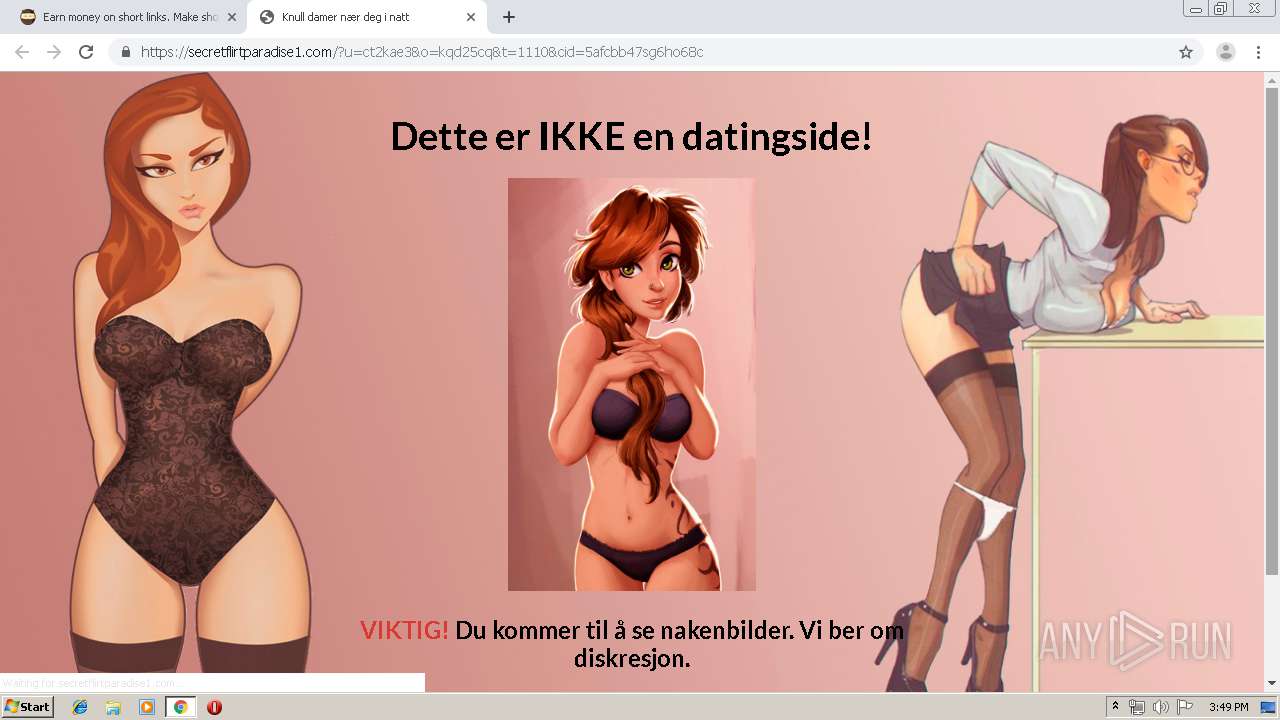
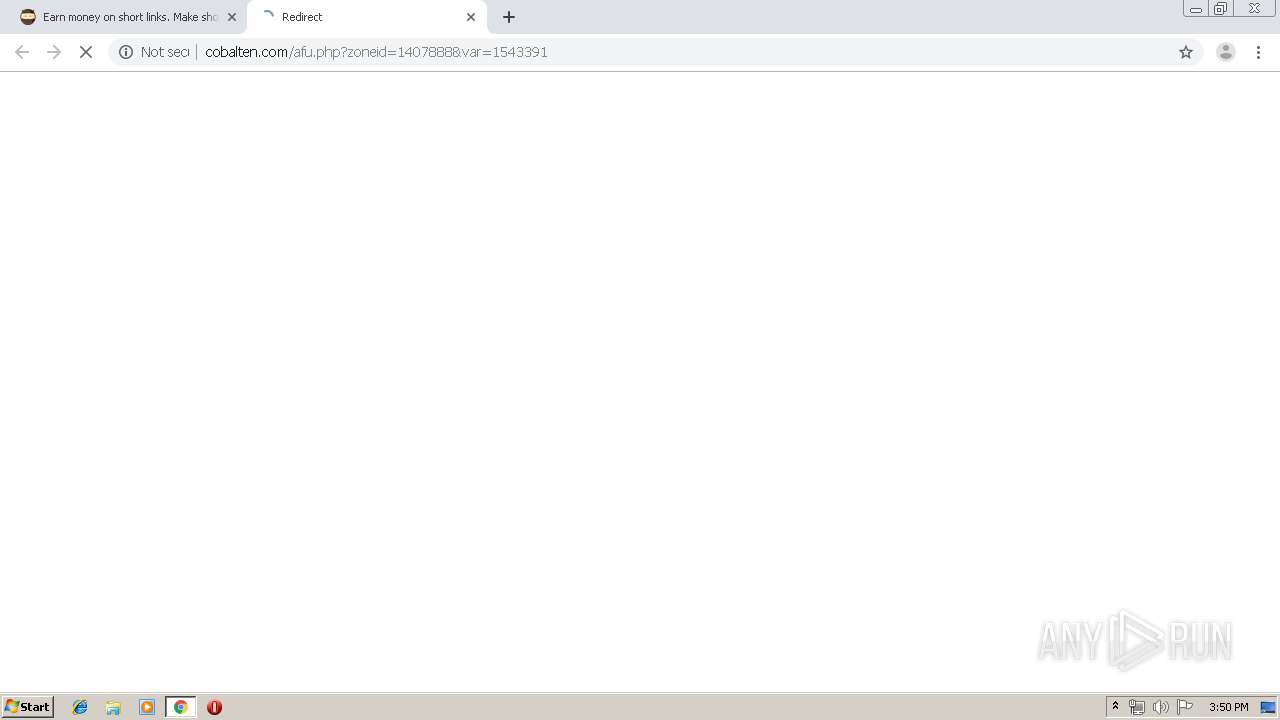
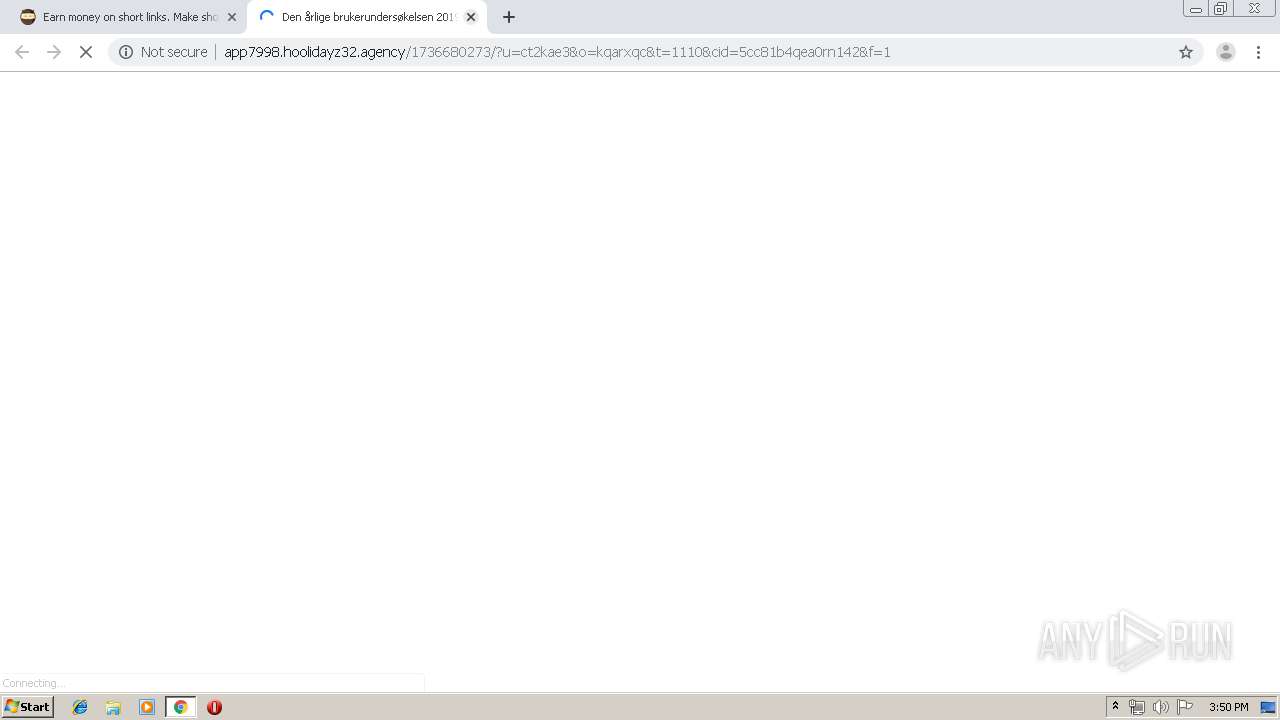
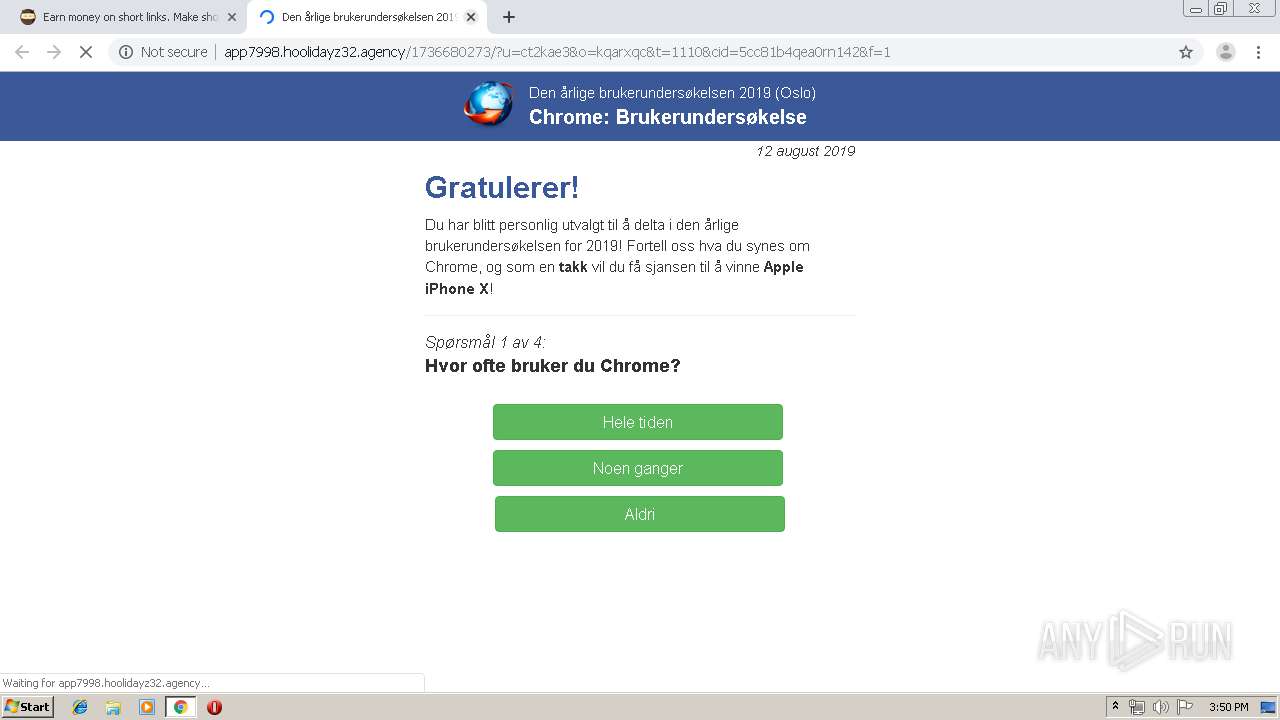
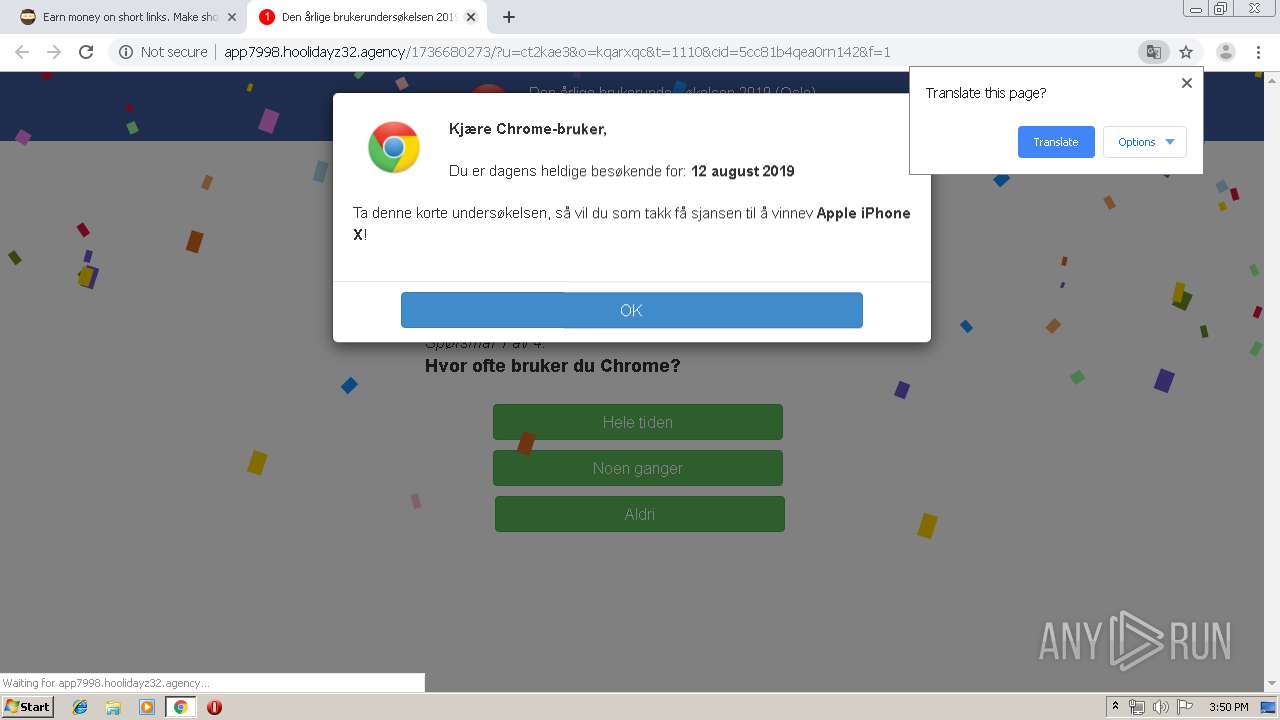
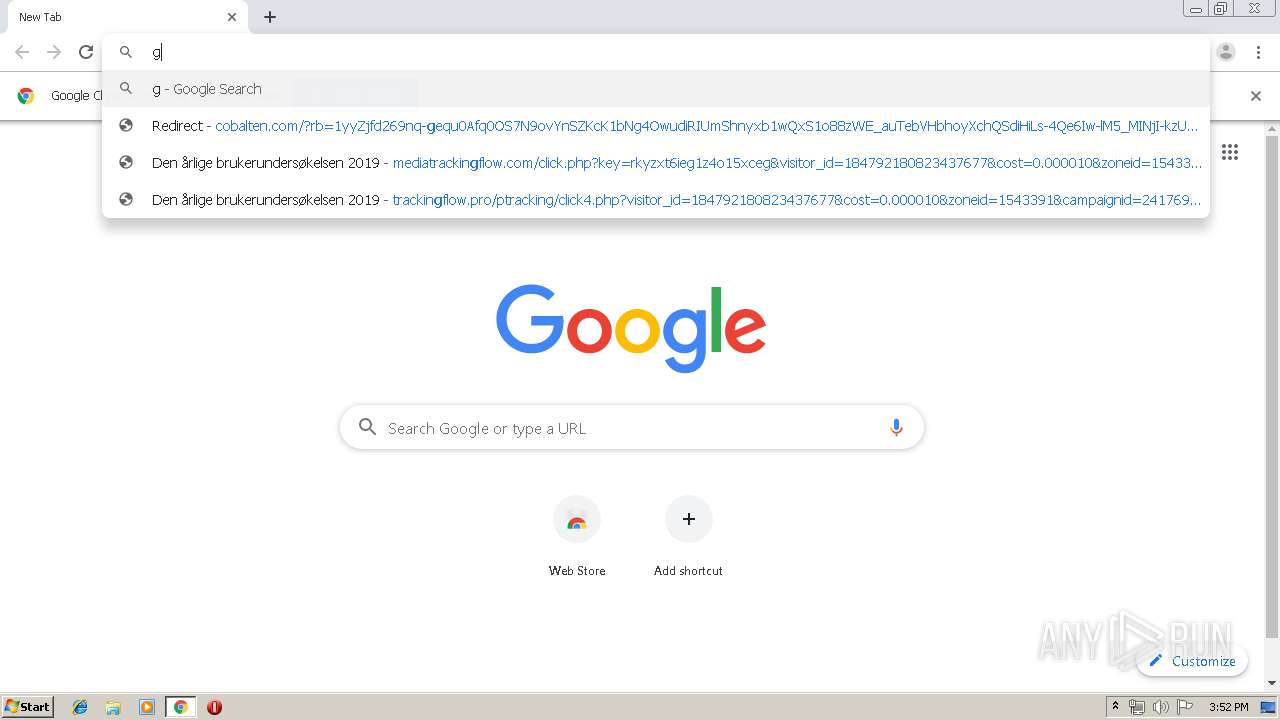
1928 | chrome.exe | GET | 200 | 206.54.165.217:80 | http://cobalten.com/apu.php?zoneid=1543391 | NL | text | 21.2 Kb | malicious |
1928 | chrome.exe | GET | 200 | 78.140.188.190:80 | http://static.sh.st/bundles/smeweb/img/widget-sprite.png?2019-04-23.0 | NL | image | 82.5 Kb | unknown |
1928 | chrome.exe | GET | 200 | 78.140.188.190:80 | http://static.sh.st/b5/4c/45/48/be/0d/ca/35/64/1c/e2/75/9d/8f/9e/2c/logo1707.png?2019-04-23.0 | NL | image | 6.08 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1928 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1928 | chrome.exe | 185.66.120.52:80 | corneey.com | Grey Wizard Sp. z o.o. | PL | malicious |
1928 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
1928 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
1928 | chrome.exe | 172.217.23.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1928 | chrome.exe | 78.140.188.189:443 | shorte.st | Webzilla B.V. | NL | unknown |
1928 | chrome.exe | 78.140.188.190:80 | static.shorte.st | Webzilla B.V. | NL | unknown |
1928 | chrome.exe | 78.140.191.213:80 | go.onclasrv.com | Webzilla B.V. | NL | unknown |
1928 | chrome.exe | 172.217.23.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1928 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
corneey.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google-analytics.com |
| whitelisted |
themes.googleusercontent.com |
| whitelisted |
shorte.st |
| unknown |
static.shorte.st |
| unknown |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
static.sh.st |
| unknown |
Threats
1 ETPRO signatures available at the full report