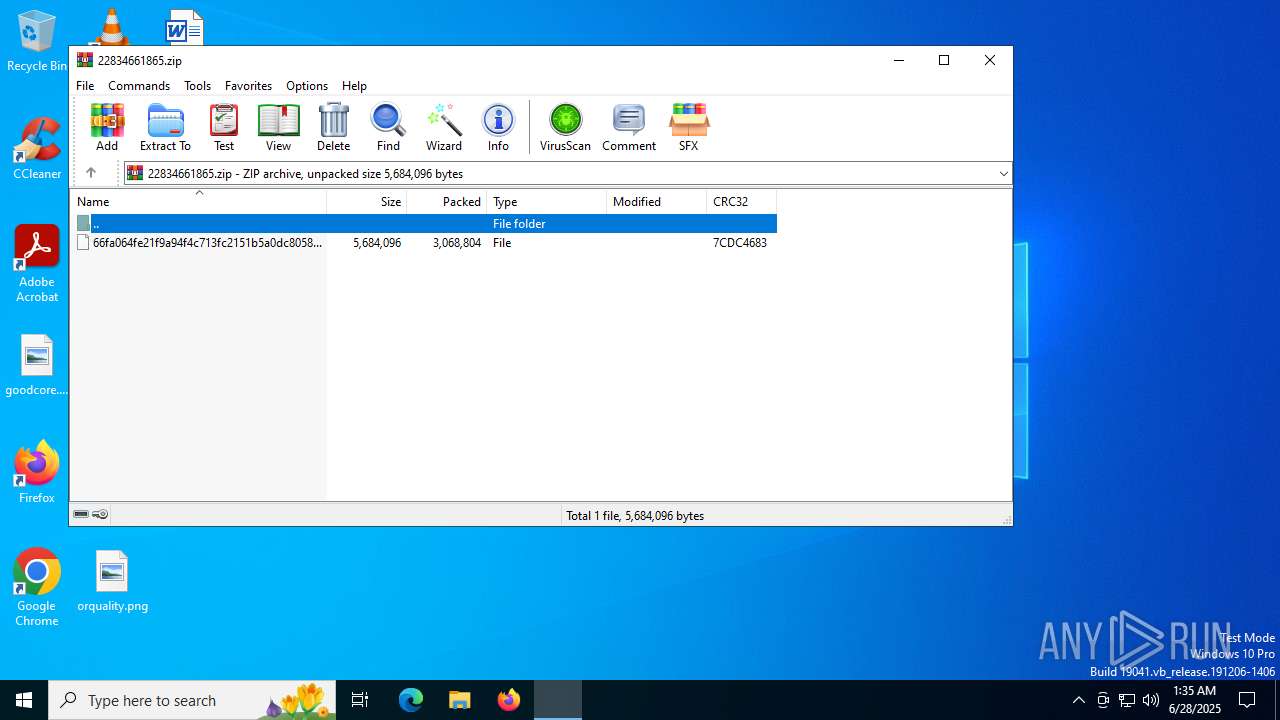
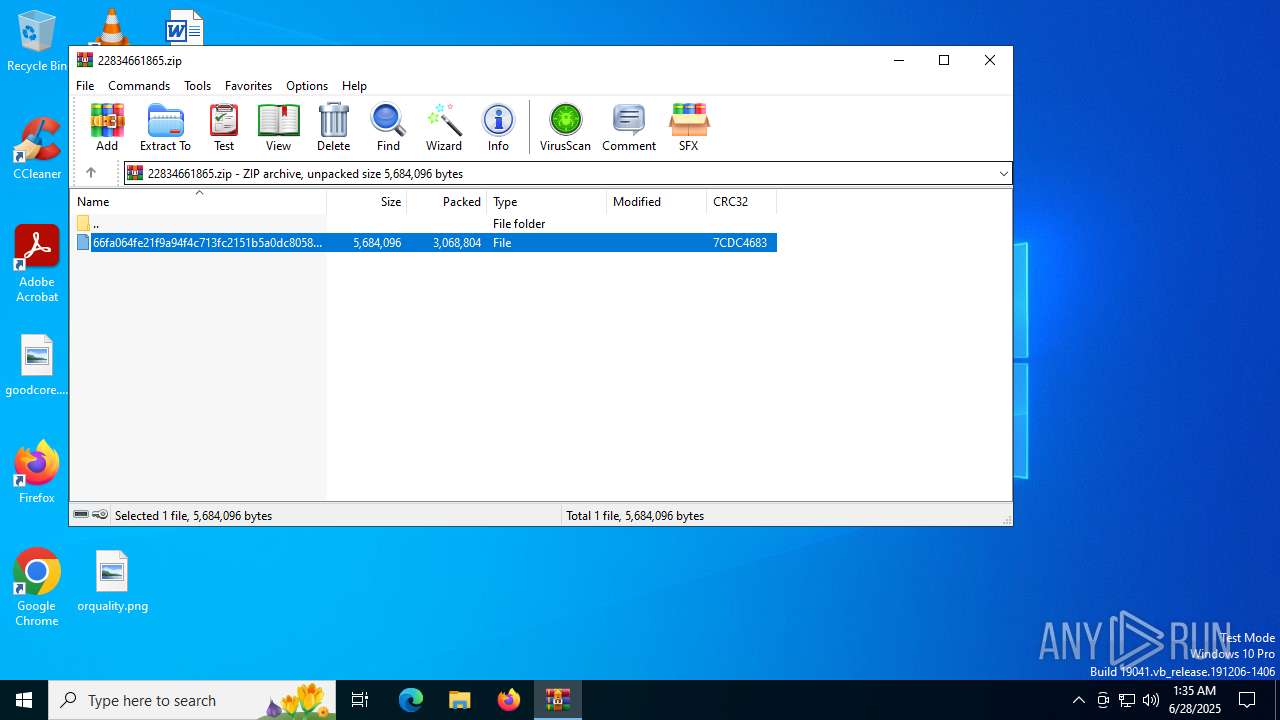
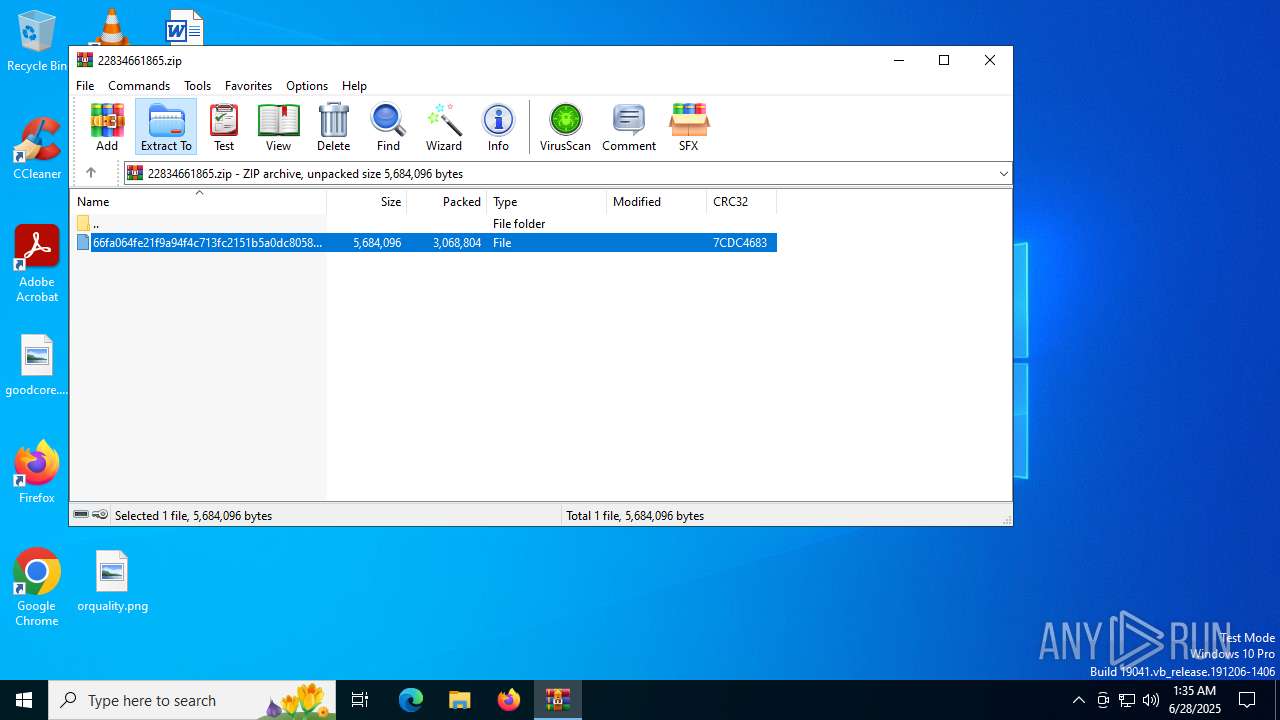
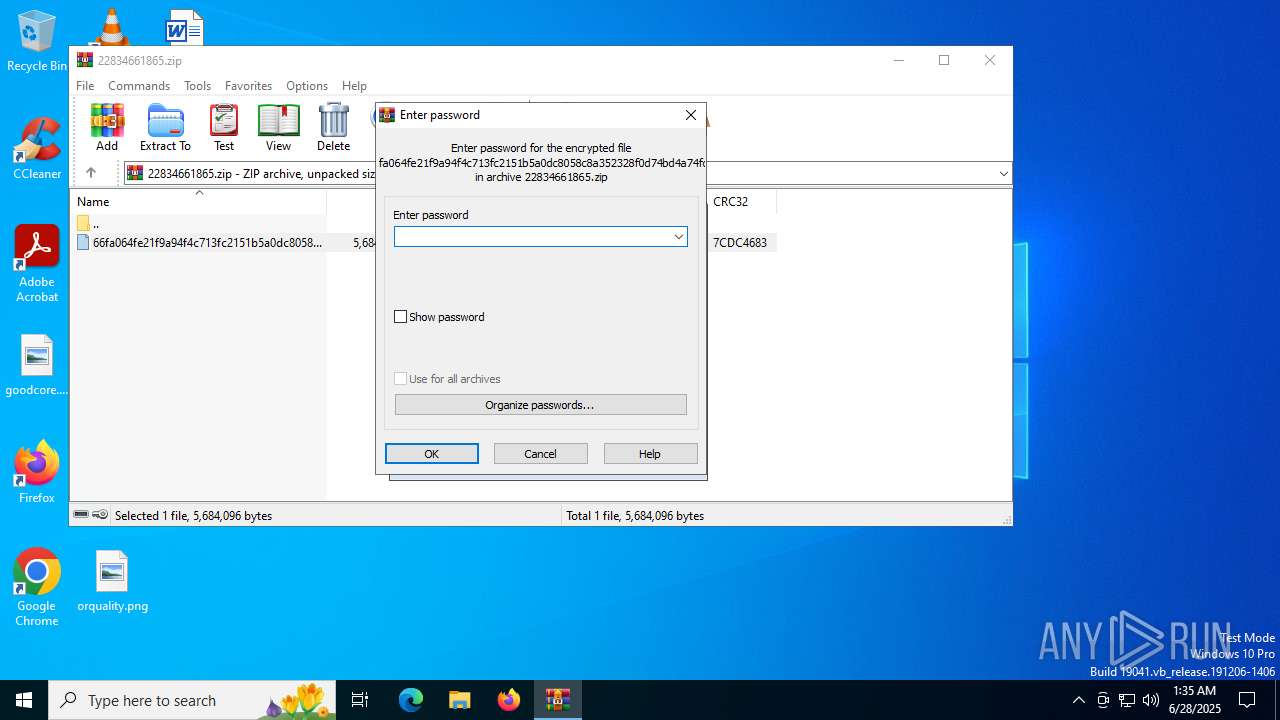
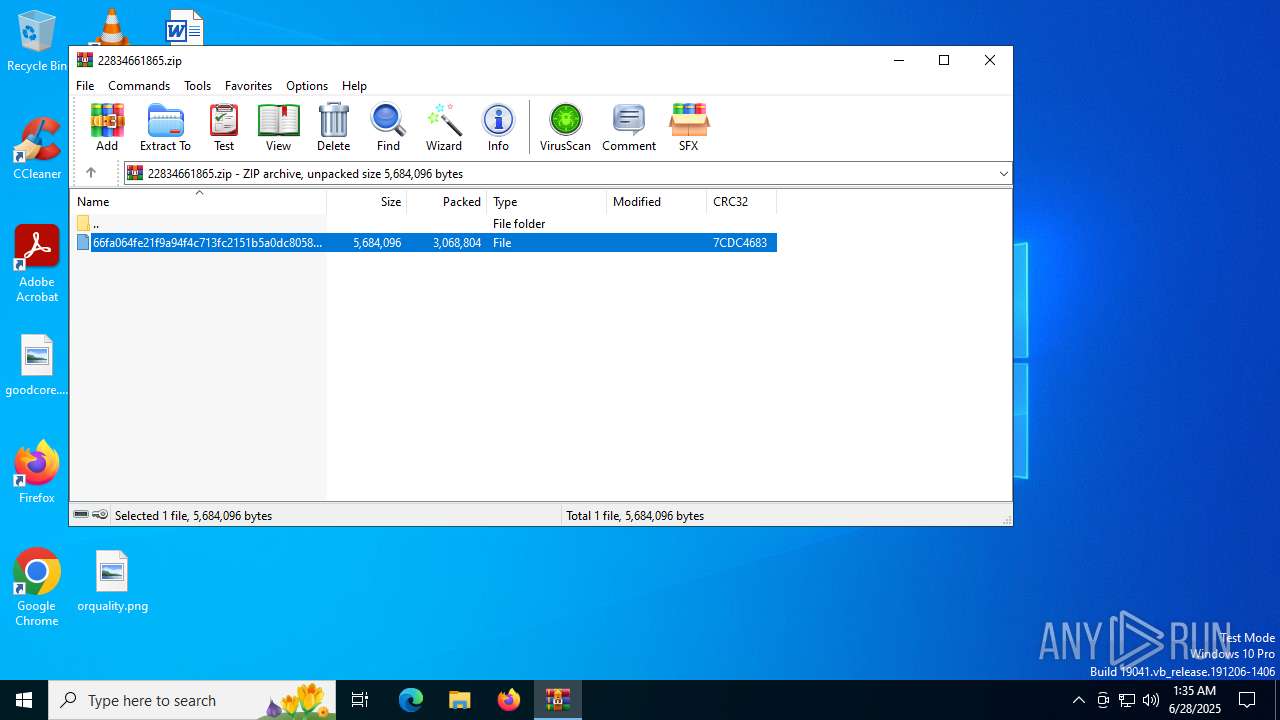
| File name: | 22834661865.zip |
| Full analysis: | https://app.any.run/tasks/eecc2e91-3865-409b-b9f1-7e451101e13f |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2025, 01:35:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | F75358E47CBDF9C2E0109B1D80C134BD |
| SHA1: | 916E0BD72AFB8FDF1729654563CF2CFA876F9AB4 |
| SHA256: | 83F94F8C9DD5DA2083FF111FC9B09CC60C487E06B4FAD92DF4910A0F8F1DABA6 |
| SSDEEP: | 98304:Oik86P0g4sbbowltsjKTzboNG6p2II8wcEiuW++yUlbbnQedc5c0ejvo3LXjw9Jm:ZJr1N6ES |
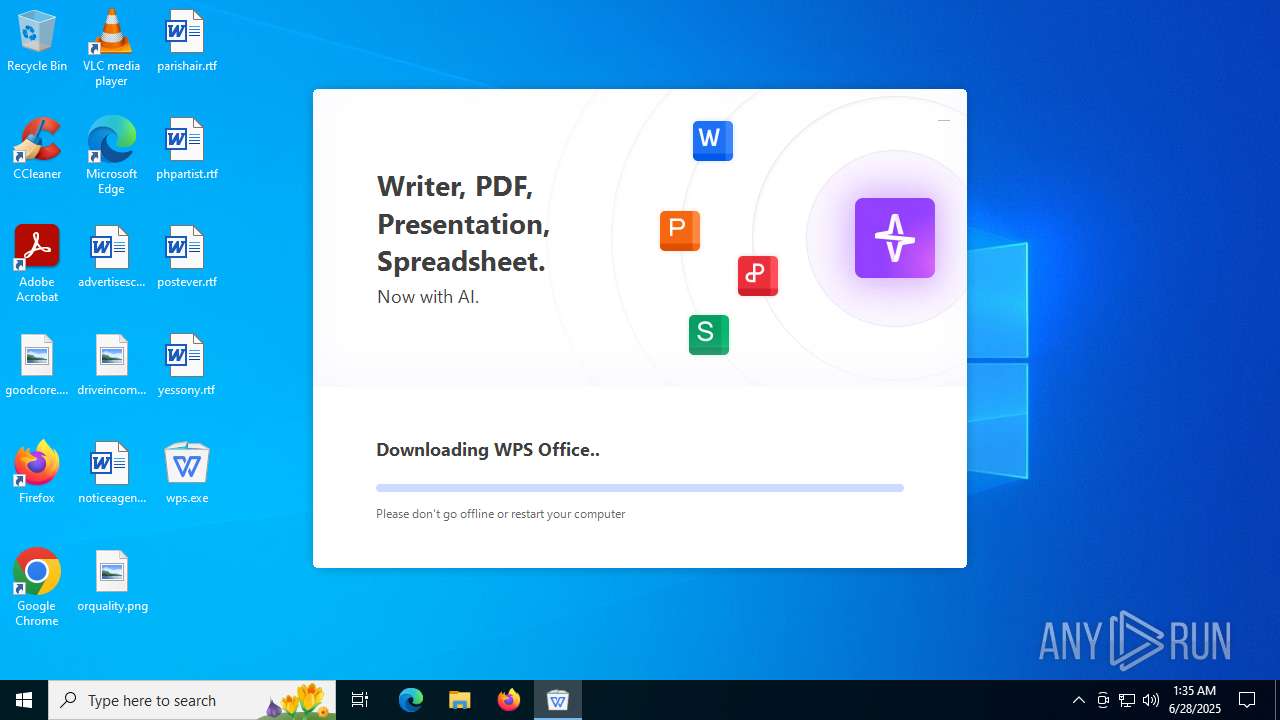
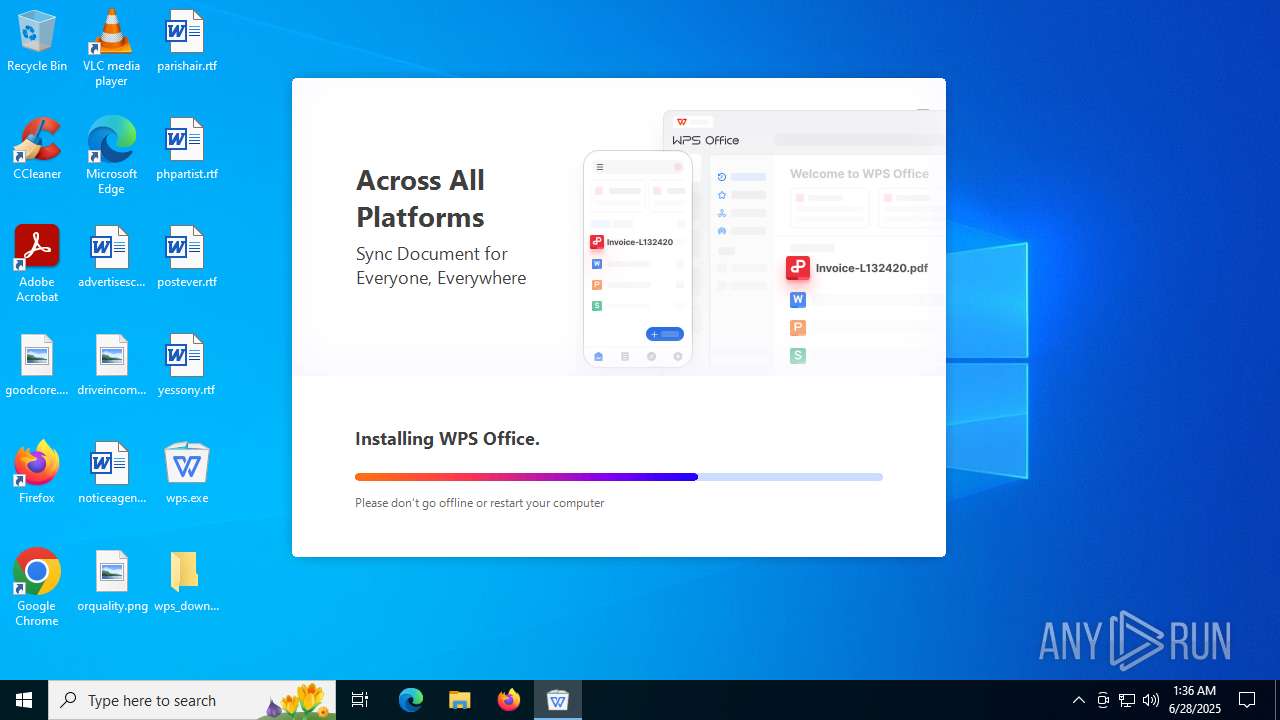
MALICIOUS
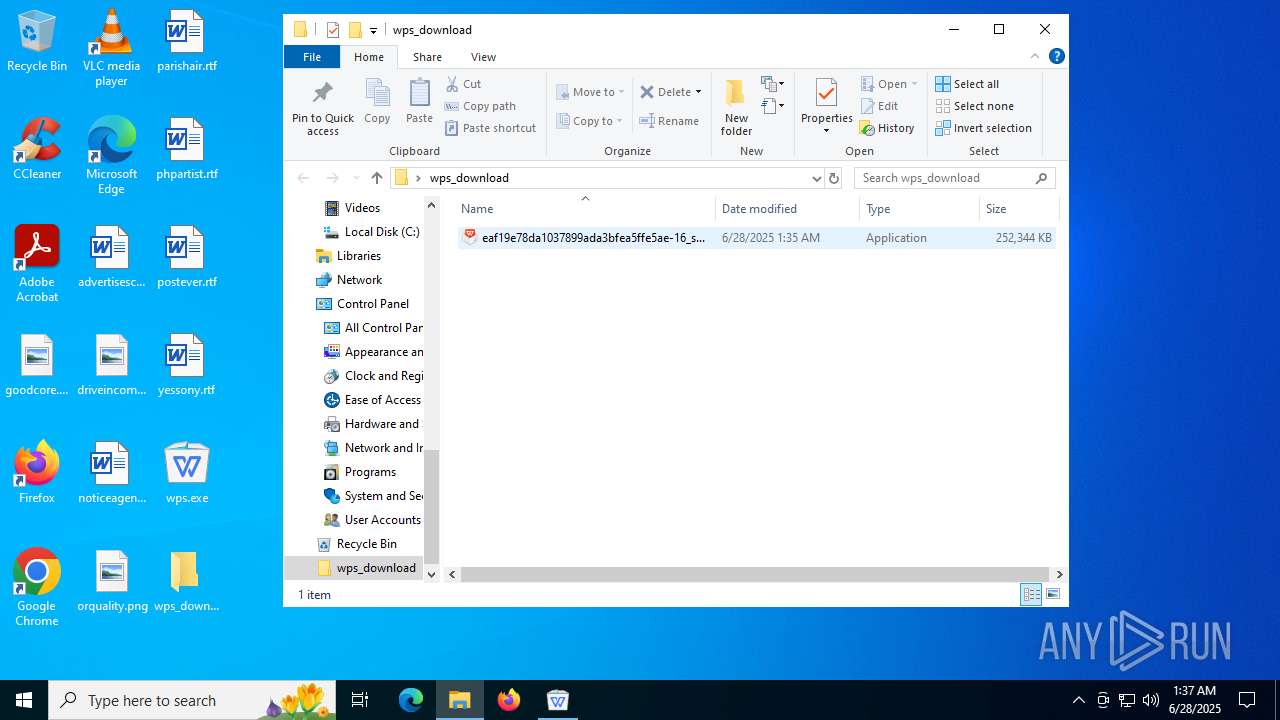
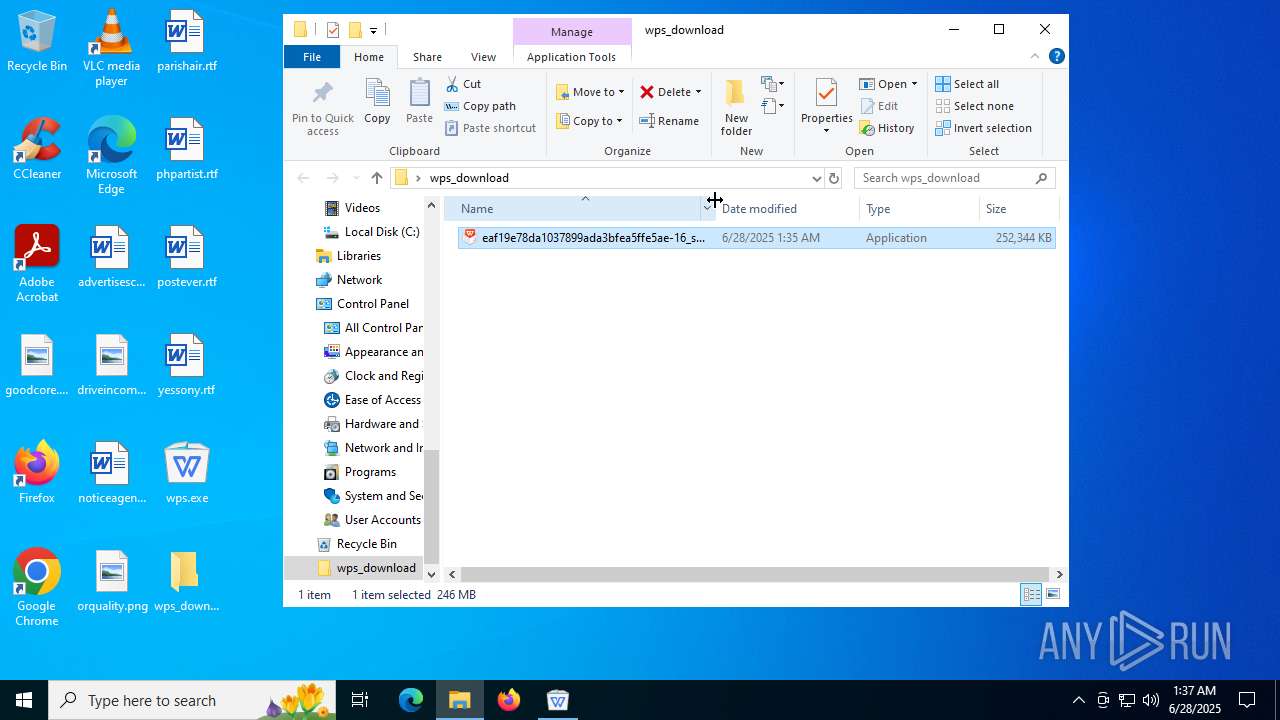
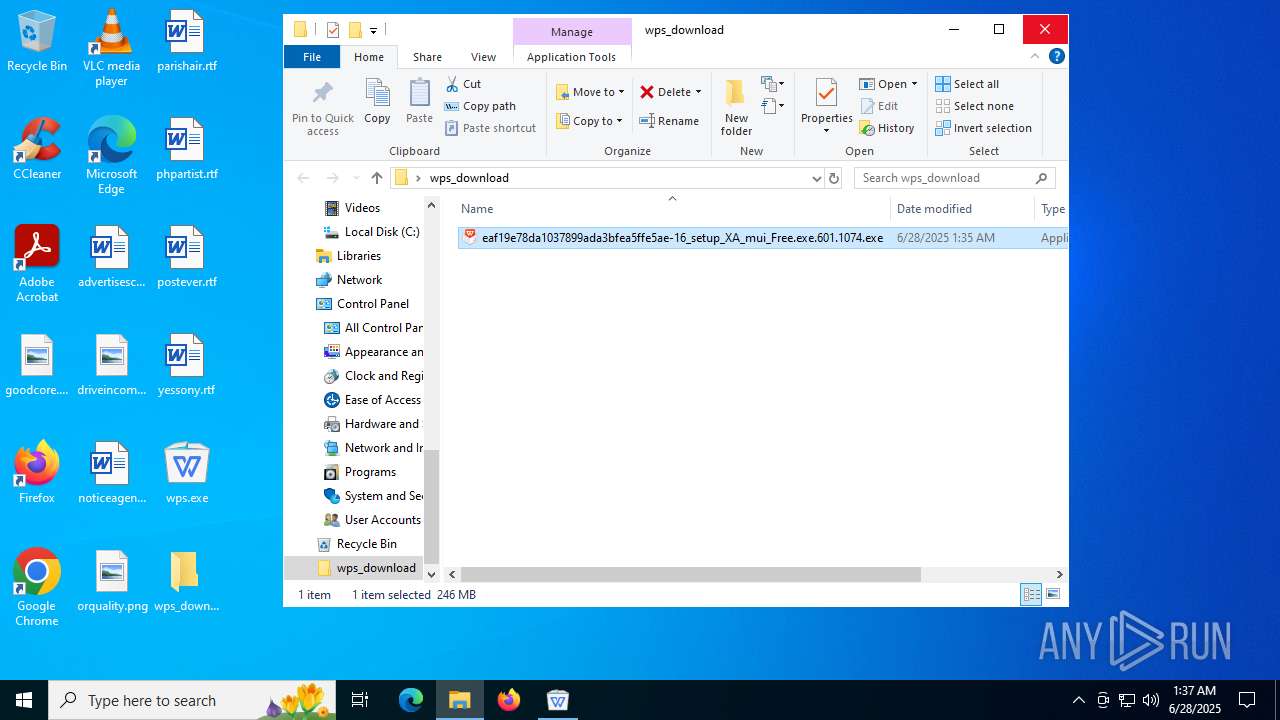
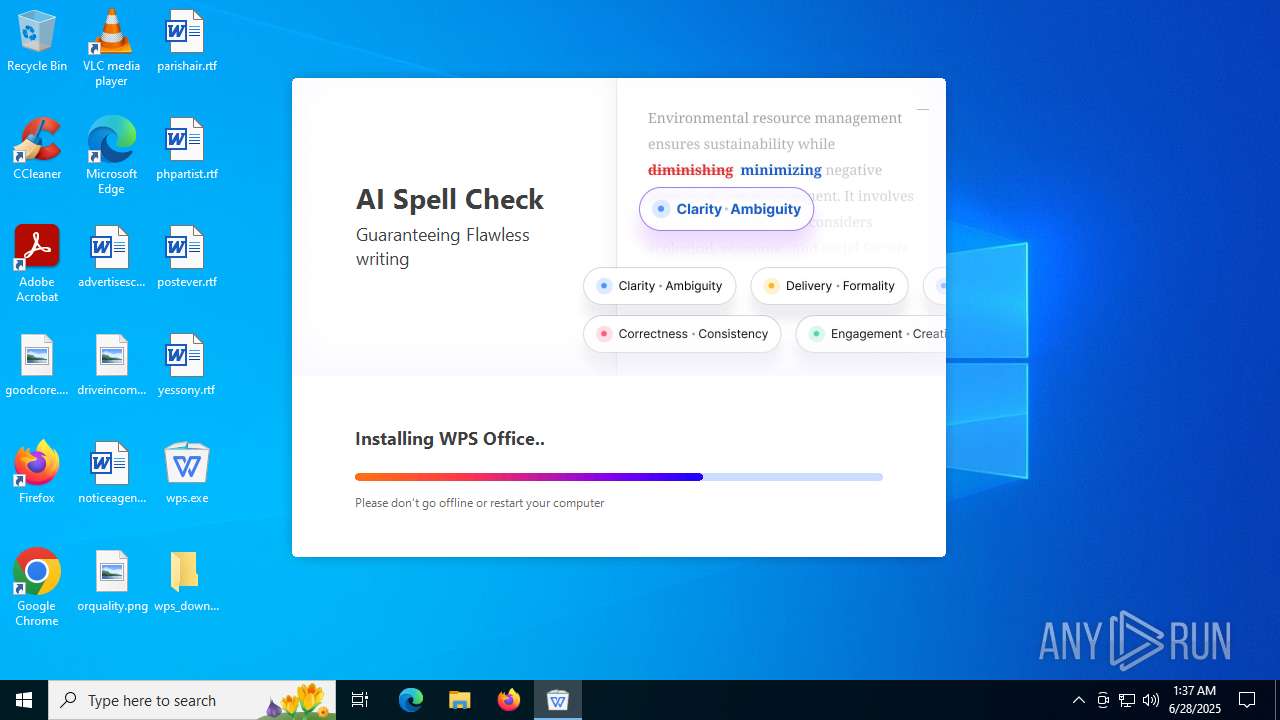
Drops known malicious document
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
Registers / Runs the DLL via REGSVR32.EXE
- ksomisc.exe (PID: 3944)
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
- ksomisc.exe (PID: 6336)
SUSPICIOUS
WPS mutex has been found
- wps.exe (PID: 1128)
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
- wpsupdate.exe (PID: 7156)
Process drops legitimate windows executable
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
Executable content was dropped or overwritten
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
The process drops C-runtime libraries
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
Reads security settings of Internet Explorer
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
- ksomisc.exe (PID: 3688)
- ksomisc.exe (PID: 3108)
- ksomisc.exe (PID: 7084)
- ksomisc.exe (PID: 4684)
- ksomisc.exe (PID: 3944)
- ksomisc.exe (PID: 4948)
- ksomisc.exe (PID: 3924)
- wpscloudsvr.exe (PID: 6828)
- ksomisc.exe (PID: 6320)
- ksomisc.exe (PID: 1984)
- wpscloudsvr.exe (PID: 4800)
- ksomisc.exe (PID: 1944)
- wpscloudsvr.exe (PID: 6420)
- ksomisc.exe (PID: 4520)
- wpscloudsvr.exe (PID: 5764)
- ksomisc.exe (PID: 3800)
- ksomisc.exe (PID: 2212)
- ksomisc.exe (PID: 6244)
- ksomisc.exe (PID: 7000)
- ksomisc.exe (PID: 3872)
- ksomisc.exe (PID: 3636)
- wps.exe (PID: 7152)
- ksomisc.exe (PID: 5124)
- ksomisc.exe (PID: 536)
- ksomisc.exe (PID: 1468)
- ksomisc.exe (PID: 1868)
- ksomisc.exe (PID: 6240)
- ksomisc.exe (PID: 6736)
- ksomisc.exe (PID: 3584)
- ksomisc.exe (PID: 6068)
- ksomisc.exe (PID: 6336)
- ksomisc.exe (PID: 544)
- wpscloudsvr.exe (PID: 4104)
- ksomisc.exe (PID: 2280)
The process checks if it is being run in the virtual environment
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
There is functionality for taking screenshot (YARA)
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
Creates a software uninstall entry
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
The process creates files with name similar to system file names
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
Process drops SQLite DLL files
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
Write to the desktop.ini file (may be used to cloak folders)
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
Creates file in the systems drive root
- ksomisc.exe (PID: 3688)
- ksomisc.exe (PID: 3108)
- ksomisc.exe (PID: 7084)
- ksomisc.exe (PID: 4684)
- ksomisc.exe (PID: 3944)
- ksomisc.exe (PID: 3924)
- ksomisc.exe (PID: 4948)
- ksomisc.exe (PID: 6320)
- ksomisc.exe (PID: 1984)
- ksomisc.exe (PID: 1944)
- ksomisc.exe (PID: 4520)
- ksomisc.exe (PID: 3800)
- ksomisc.exe (PID: 2212)
- ksomisc.exe (PID: 7000)
- ksomisc.exe (PID: 3872)
- ksomisc.exe (PID: 6244)
- ksomisc.exe (PID: 3636)
- wps.exe (PID: 7152)
- wps.exe (PID: 4880)
- ksomisc.exe (PID: 536)
- ksomisc.exe (PID: 5124)
- ksomisc.exe (PID: 1468)
- ksomisc.exe (PID: 6240)
- ksomisc.exe (PID: 1868)
- ksomisc.exe (PID: 6736)
- ksomisc.exe (PID: 3584)
- ksomisc.exe (PID: 6068)
- ksomisc.exe (PID: 6336)
- ksomisc.exe (PID: 544)
Creates/Modifies COM task schedule object
- ksomisc.exe (PID: 3944)
- regsvr32.exe (PID: 4500)
The process verifies whether the antivirus software is installed
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
Application launched itself
- wps.exe (PID: 7152)
INFO
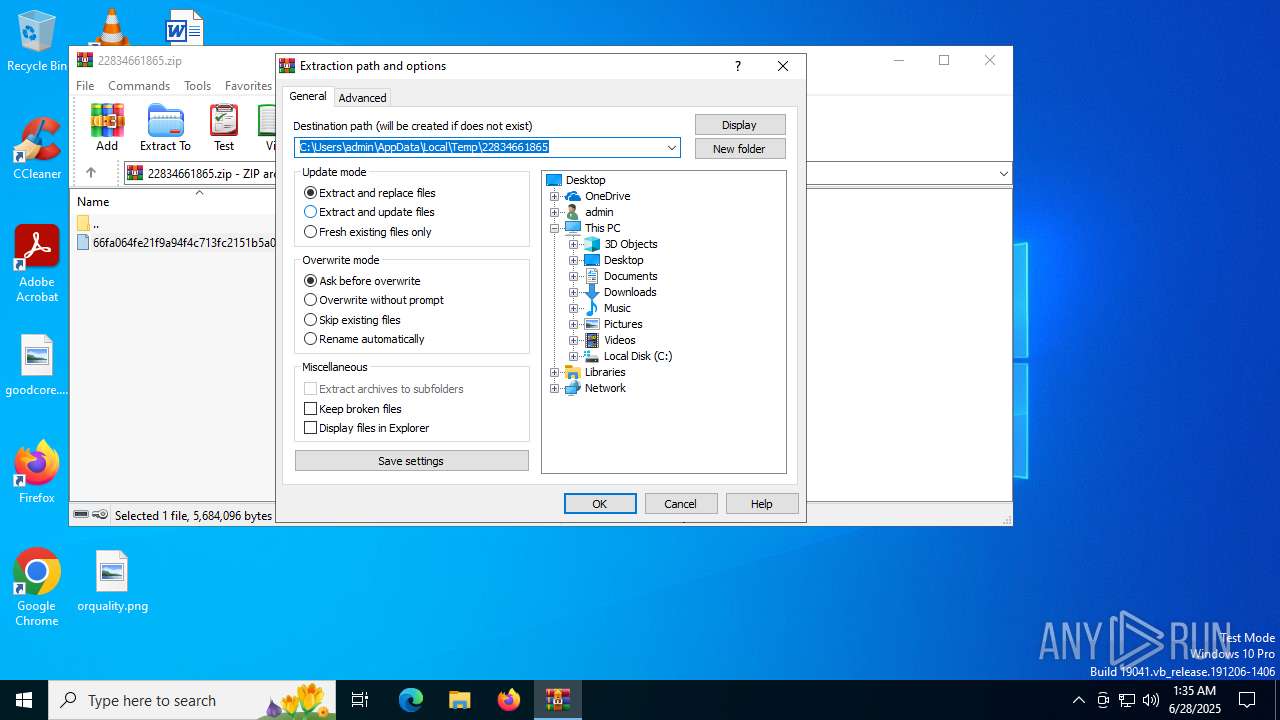
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5808)
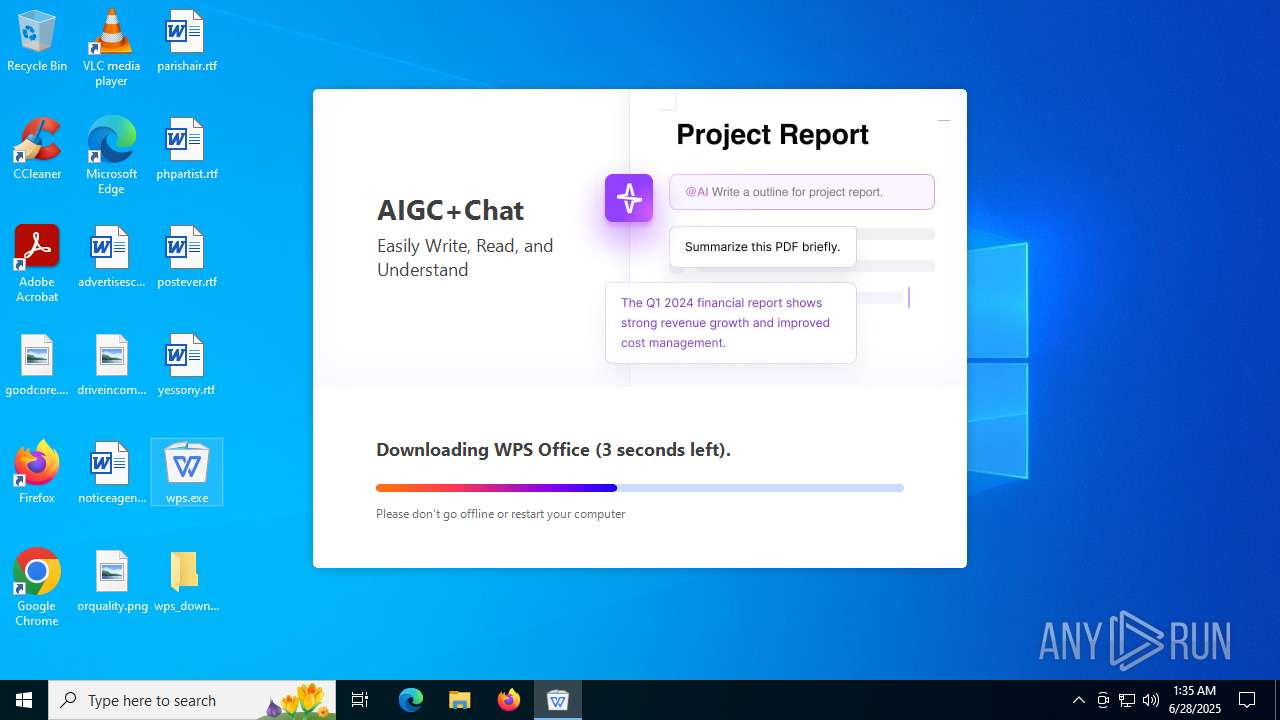
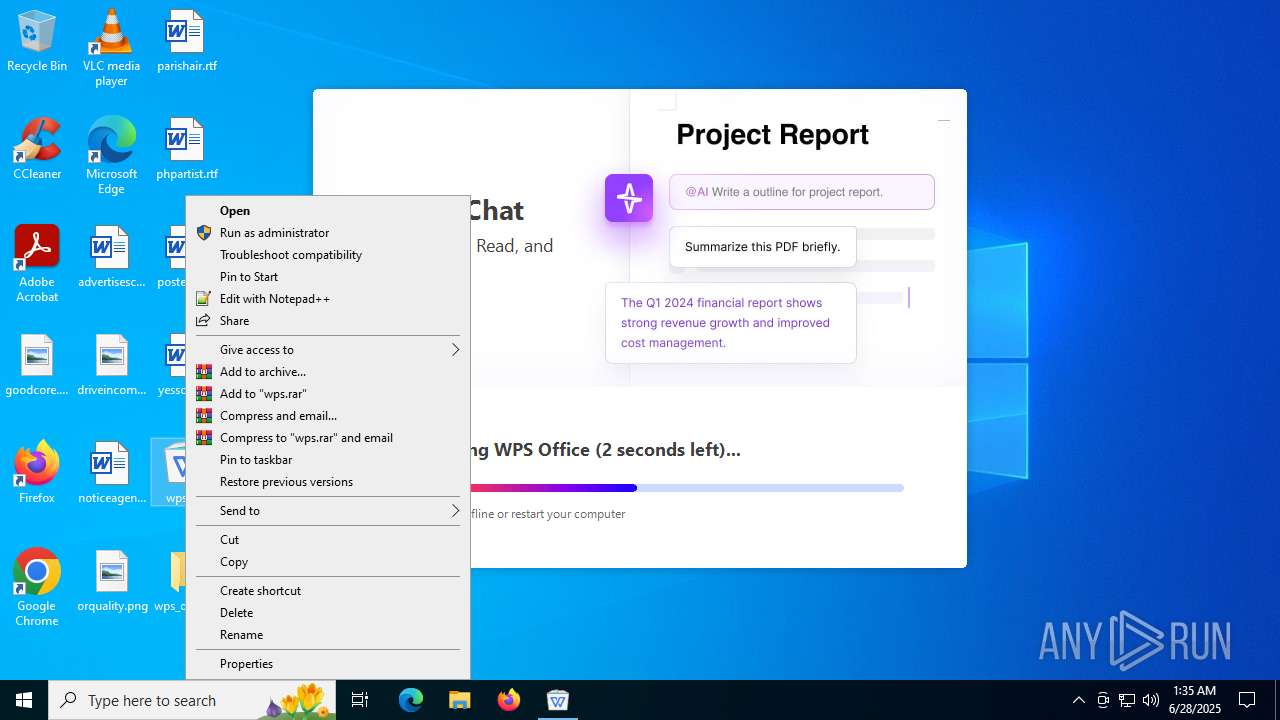
Manual execution by a user
- wps.exe (PID: 1128)
Reads the machine GUID from the registry
- wps.exe (PID: 1128)
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
- ksomisc.exe (PID: 7084)
- ksomisc.exe (PID: 3688)
- ksomisc.exe (PID: 3108)
- ksomisc.exe (PID: 4684)
- ksomisc.exe (PID: 3944)
- ksomisc.exe (PID: 3924)
- ksomisc.exe (PID: 4948)
- wpscloudsvr.exe (PID: 6828)
- ksomisc.exe (PID: 6320)
- ksomisc.exe (PID: 1984)
- wpscloudsvr.exe (PID: 4800)
- ksomisc.exe (PID: 1944)
- wpscloudsvr.exe (PID: 6420)
- wpscloudsvr.exe (PID: 5764)
- ksomisc.exe (PID: 4520)
- ksomisc.exe (PID: 2212)
- ksomisc.exe (PID: 3800)
- ksomisc.exe (PID: 6244)
- ksomisc.exe (PID: 3872)
- ksomisc.exe (PID: 7000)
- ksomisc.exe (PID: 3636)
- wps.exe (PID: 7152)
- ksomisc.exe (PID: 536)
- ksomisc.exe (PID: 5124)
- ksomisc.exe (PID: 1468)
- ksomisc.exe (PID: 1868)
- ksomisc.exe (PID: 6240)
- ksomisc.exe (PID: 3584)
- ksomisc.exe (PID: 6736)
- ksomisc.exe (PID: 6068)
- wpsupdate.exe (PID: 7156)
- wpsupdate.exe (PID: 5028)
- ksomisc.exe (PID: 544)
- ksomisc.exe (PID: 6336)
- wpscloudsvr.exe (PID: 4104)
- ksomisc.exe (PID: 2280)
Checks supported languages
- wps.exe (PID: 1128)
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
- ksomisc.exe (PID: 7084)
- ksomisc.exe (PID: 3688)
- ksomisc.exe (PID: 3108)
- ksomisc.exe (PID: 3944)
- ksomisc.exe (PID: 4684)
- ksomisc.exe (PID: 4948)
- ksomisc.exe (PID: 3924)
- ksomisc.exe (PID: 6320)
- wpscloudsvr.exe (PID: 6828)
- ksomisc.exe (PID: 1984)
- wpscloudsvr.exe (PID: 4800)
- ksomisc.exe (PID: 1944)
- wpscloudsvr.exe (PID: 6420)
- ksomisc.exe (PID: 4520)
- wpscloudsvr.exe (PID: 5764)
- ksomisc.exe (PID: 2212)
- ksomisc.exe (PID: 6244)
- ksomisc.exe (PID: 3800)
- ksomisc.exe (PID: 3872)
- ksomisc.exe (PID: 7000)
- pintaskbar.exe (PID: 6860)
- ksomisc.exe (PID: 3636)
- wps.exe (PID: 7152)
- wps.exe (PID: 4880)
- ksomisc.exe (PID: 536)
- ksomisc.exe (PID: 5124)
- ksomisc.exe (PID: 1468)
- ksomisc.exe (PID: 1868)
- ksomisc.exe (PID: 6240)
- ksomisc.exe (PID: 3584)
- ksomisc.exe (PID: 6736)
- wpsupdate.exe (PID: 7156)
- wpsupdate.exe (PID: 5028)
- ksomisc.exe (PID: 6068)
- ksomisc.exe (PID: 544)
- ksomisc.exe (PID: 6336)
- ksomisc.exe (PID: 2280)
- wpscloudsvr.exe (PID: 4104)
Reads the computer name
- wps.exe (PID: 1128)
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
- ksomisc.exe (PID: 3688)
- ksomisc.exe (PID: 3108)
- ksomisc.exe (PID: 7084)
- ksomisc.exe (PID: 4684)
- ksomisc.exe (PID: 3944)
- ksomisc.exe (PID: 3924)
- ksomisc.exe (PID: 4948)
- ksomisc.exe (PID: 6320)
- wpscloudsvr.exe (PID: 6828)
- ksomisc.exe (PID: 1984)
- wpscloudsvr.exe (PID: 4800)
- ksomisc.exe (PID: 1944)
- wpscloudsvr.exe (PID: 6420)
- ksomisc.exe (PID: 4520)
- wpscloudsvr.exe (PID: 5764)
- ksomisc.exe (PID: 3800)
- ksomisc.exe (PID: 2212)
- ksomisc.exe (PID: 3872)
- ksomisc.exe (PID: 7000)
- ksomisc.exe (PID: 6244)
- ksomisc.exe (PID: 3636)
- wps.exe (PID: 7152)
- wps.exe (PID: 4880)
- ksomisc.exe (PID: 536)
- ksomisc.exe (PID: 5124)
- ksomisc.exe (PID: 1468)
- ksomisc.exe (PID: 1868)
- ksomisc.exe (PID: 6240)
- ksomisc.exe (PID: 3584)
- ksomisc.exe (PID: 6736)
- ksomisc.exe (PID: 6068)
- wpsupdate.exe (PID: 7156)
- wpsupdate.exe (PID: 5028)
- ksomisc.exe (PID: 6336)
- ksomisc.exe (PID: 544)
- wpscloudsvr.exe (PID: 4104)
Process checks computer location settings
- wps.exe (PID: 1128)
- ksomisc.exe (PID: 3944)
- ksomisc.exe (PID: 6320)
- ksomisc.exe (PID: 1984)
- ksomisc.exe (PID: 4520)
- ksomisc.exe (PID: 1944)
- ksomisc.exe (PID: 3872)
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
- ksomisc.exe (PID: 3584)
- ksomisc.exe (PID: 6336)
- ksomisc.exe (PID: 544)
Reads the software policy settings
- wps.exe (PID: 1128)
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
- explorer.exe (PID: 4772)
- slui.exe (PID: 6376)
- ksomisc.exe (PID: 3688)
- ksomisc.exe (PID: 3108)
- ksomisc.exe (PID: 7084)
- ksomisc.exe (PID: 3944)
- ksomisc.exe (PID: 4684)
- ksomisc.exe (PID: 4948)
- ksomisc.exe (PID: 3924)
- wpscloudsvr.exe (PID: 6828)
- ksomisc.exe (PID: 6320)
- ksomisc.exe (PID: 1984)
- wpscloudsvr.exe (PID: 4800)
- ksomisc.exe (PID: 1944)
- wpscloudsvr.exe (PID: 6420)
- wpscloudsvr.exe (PID: 5764)
- ksomisc.exe (PID: 4520)
- ksomisc.exe (PID: 3800)
- ksomisc.exe (PID: 2212)
- ksomisc.exe (PID: 3872)
- ksomisc.exe (PID: 7000)
- ksomisc.exe (PID: 6244)
- ksomisc.exe (PID: 3636)
- wps.exe (PID: 7152)
- ksomisc.exe (PID: 536)
- ksomisc.exe (PID: 5124)
- ksomisc.exe (PID: 6240)
- ksomisc.exe (PID: 1468)
- ksomisc.exe (PID: 1868)
- ksomisc.exe (PID: 3584)
- OpenWith.exe (PID: 4320)
- ksomisc.exe (PID: 6736)
- wpsupdate.exe (PID: 7156)
- ksomisc.exe (PID: 6068)
- ksomisc.exe (PID: 6336)
- ksomisc.exe (PID: 544)
- wpscloudsvr.exe (PID: 4104)
- ksomisc.exe (PID: 2280)
Creates files or folders in the user directory
- wps.exe (PID: 1128)
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
- explorer.exe (PID: 4772)
- ksomisc.exe (PID: 7084)
- ksomisc.exe (PID: 3688)
- ksomisc.exe (PID: 3108)
- ksomisc.exe (PID: 4684)
- ksomisc.exe (PID: 3944)
- ksomisc.exe (PID: 4948)
- ksomisc.exe (PID: 3924)
- ksomisc.exe (PID: 6320)
- ksomisc.exe (PID: 1984)
- ksomisc.exe (PID: 1944)
- ksomisc.exe (PID: 4520)
- ksomisc.exe (PID: 3800)
- ksomisc.exe (PID: 2212)
- ksomisc.exe (PID: 7000)
- ksomisc.exe (PID: 6244)
- ksomisc.exe (PID: 3872)
- ksomisc.exe (PID: 3636)
- wps.exe (PID: 7152)
- ksomisc.exe (PID: 536)
- ksomisc.exe (PID: 5124)
- ksomisc.exe (PID: 1468)
- ksomisc.exe (PID: 1868)
- ksomisc.exe (PID: 6240)
- OpenWith.exe (PID: 4320)
- ksomisc.exe (PID: 6736)
- ksomisc.exe (PID: 3584)
- wpsupdate.exe (PID: 7156)
- wpsupdate.exe (PID: 5028)
- ksomisc.exe (PID: 6068)
- ksomisc.exe (PID: 6336)
- ksomisc.exe (PID: 544)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4772)
- OpenWith.exe (PID: 4320)
Create files in a temporary directory
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
- ksomisc.exe (PID: 3872)
The sample compiled with english language support
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
Checks proxy server information
- slui.exe (PID: 6376)
- explorer.exe (PID: 4772)
- OpenWith.exe (PID: 4320)
- wpsupdate.exe (PID: 7156)
- wpsupdate.exe (PID: 5028)
The sample compiled with chinese language support
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
The sample compiled with japanese language support
- eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe (PID: 1052)
Creates files in the program directory
- ksomisc.exe (PID: 7000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x7cdc4683 |
| ZipCompressedSize: | 3068804 |
| ZipUncompressedSize: | 5684096 |
| ZipFileName: | 66fa064fe21f9a94f4c713fc2151b5a0dc8058c8a352328f0d74bd4a74fcea66 |
Total processes
198
Monitored processes
54
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\ksomisc.exe" -createsubmodulelink startmenu prometheus | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\ksomisc.exe | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | ||||||||||||
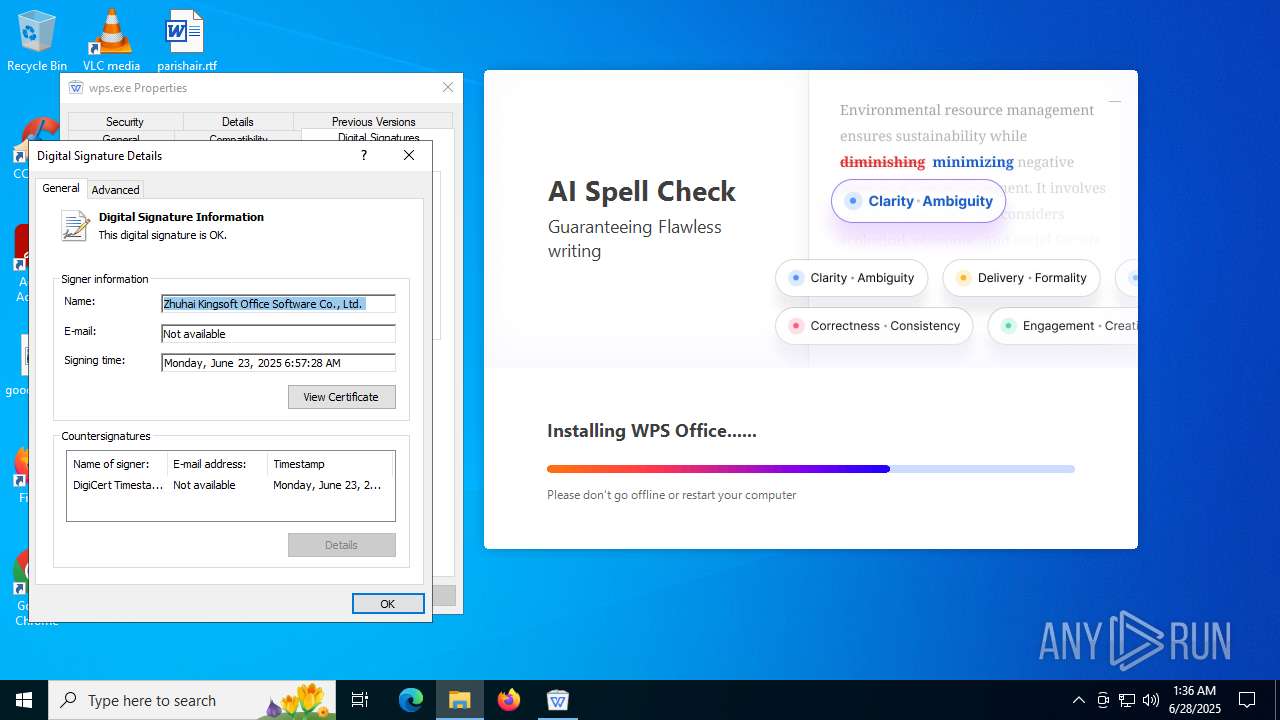
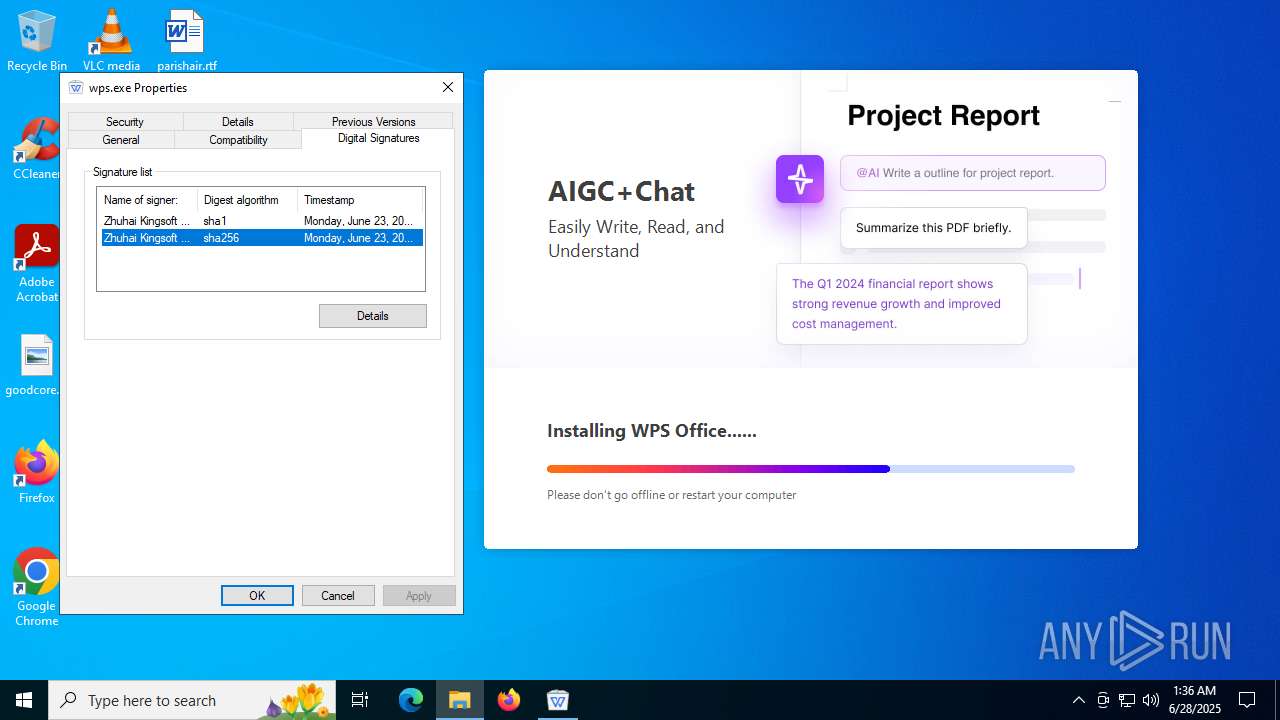
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Module Exit code: 0 Version: 12,2,0,21546 Modules
| |||||||||||||||
| 544 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\ksomisc.exe" -regPreviewHandler | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\ksomisc.exe | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Module Exit code: 0 Version: 12,2,0,21546 Modules
| |||||||||||||||
| 868 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
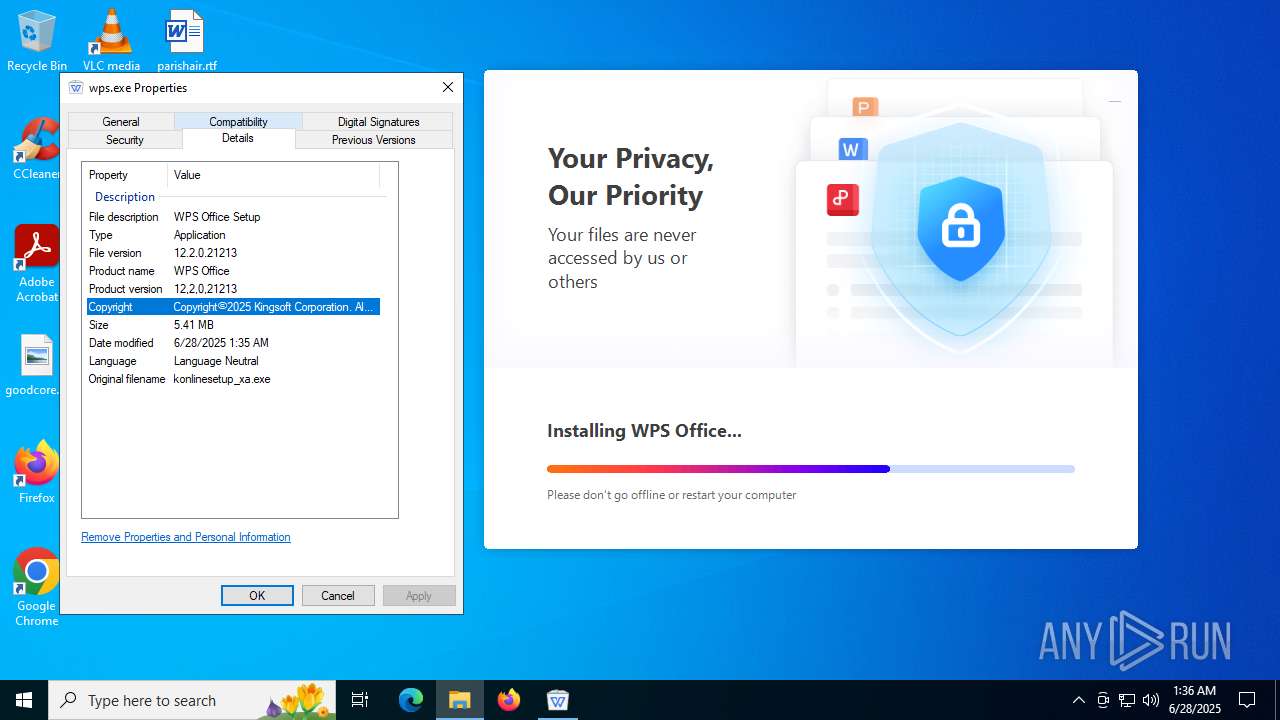
| 1052 | "C:\Users\admin\Desktop\wps_download\eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe" -installCallByOnlineSetup -defaultOpen -defaultOpenPdf -asso_pic_setup -createIcons -pinTaskbar -curlangofinstalledproduct=en_US -notElevateAndDirectlyInstall -D="C:\Users\admin\AppData\Local\Kingsoft\WPS Office" -notautostartwps -enableSetupMuiPkg -appdata="C:\Users\admin\AppData\Roaming" | C:\Users\admin\Desktop\wps_download\eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | wps.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Install Application Version: 12,2,0,21546 Modules
| |||||||||||||||
| 1096 | /s "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\kmso2pdfplugins64.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
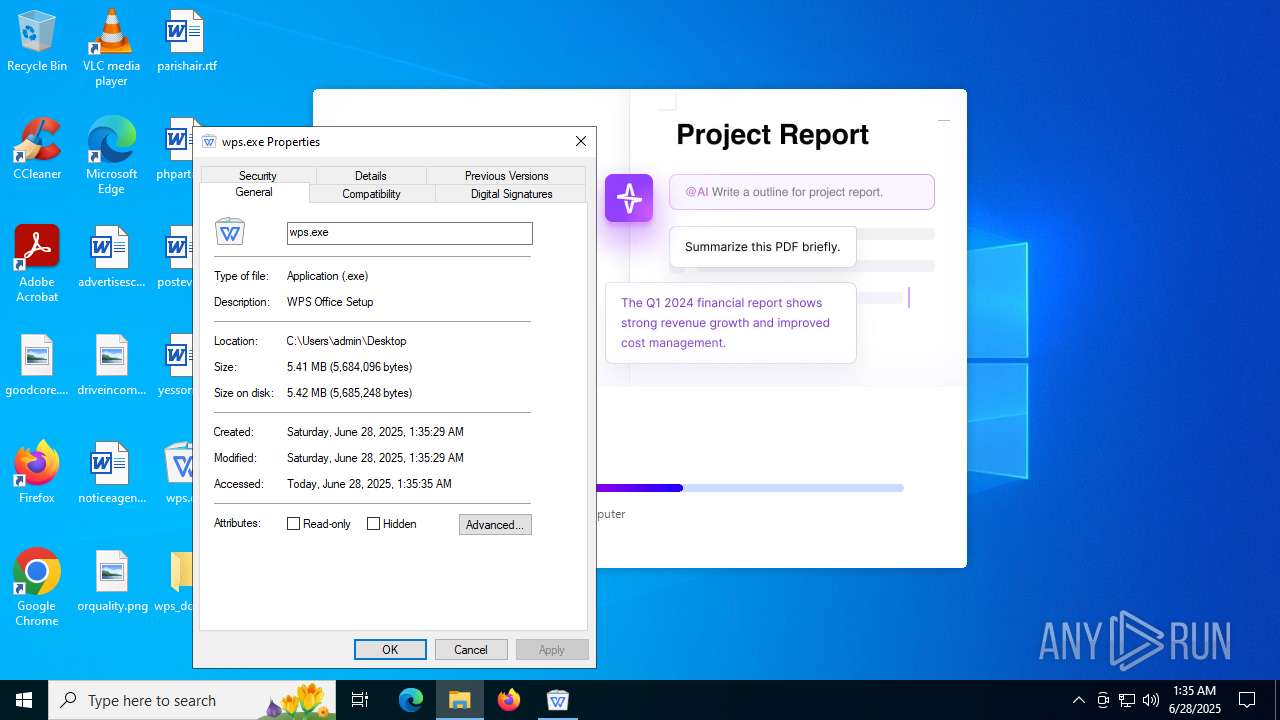
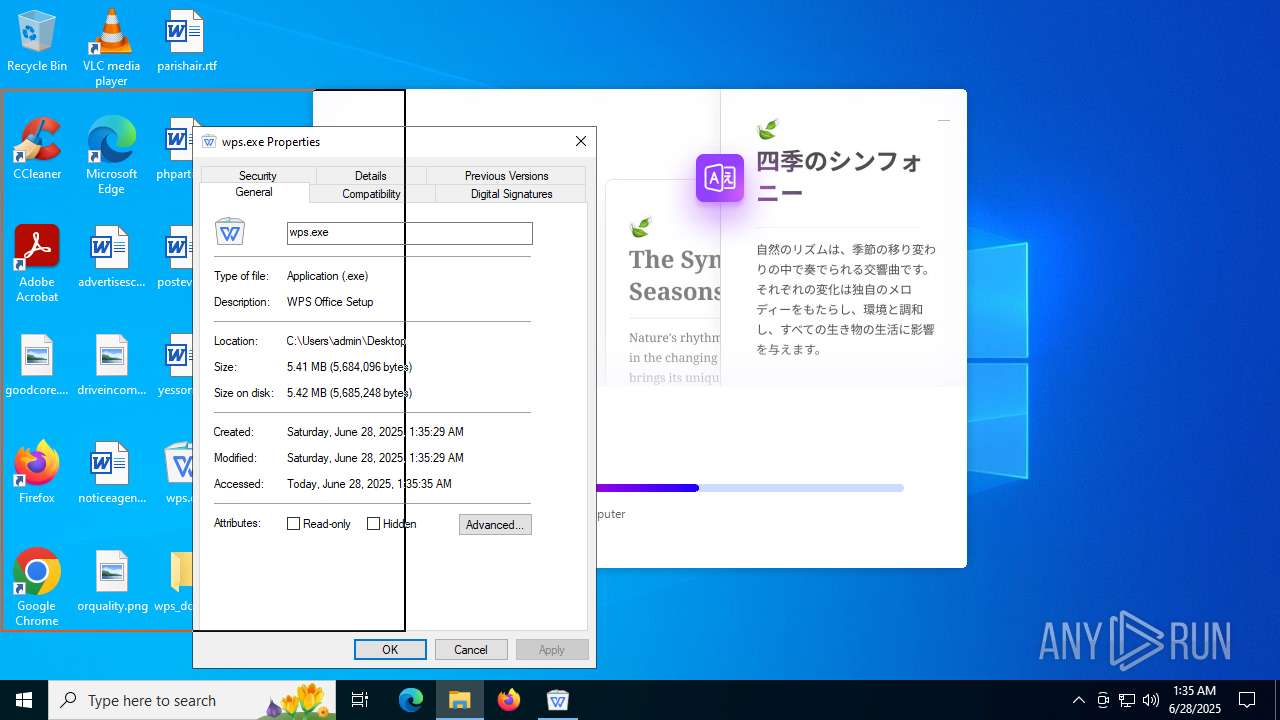
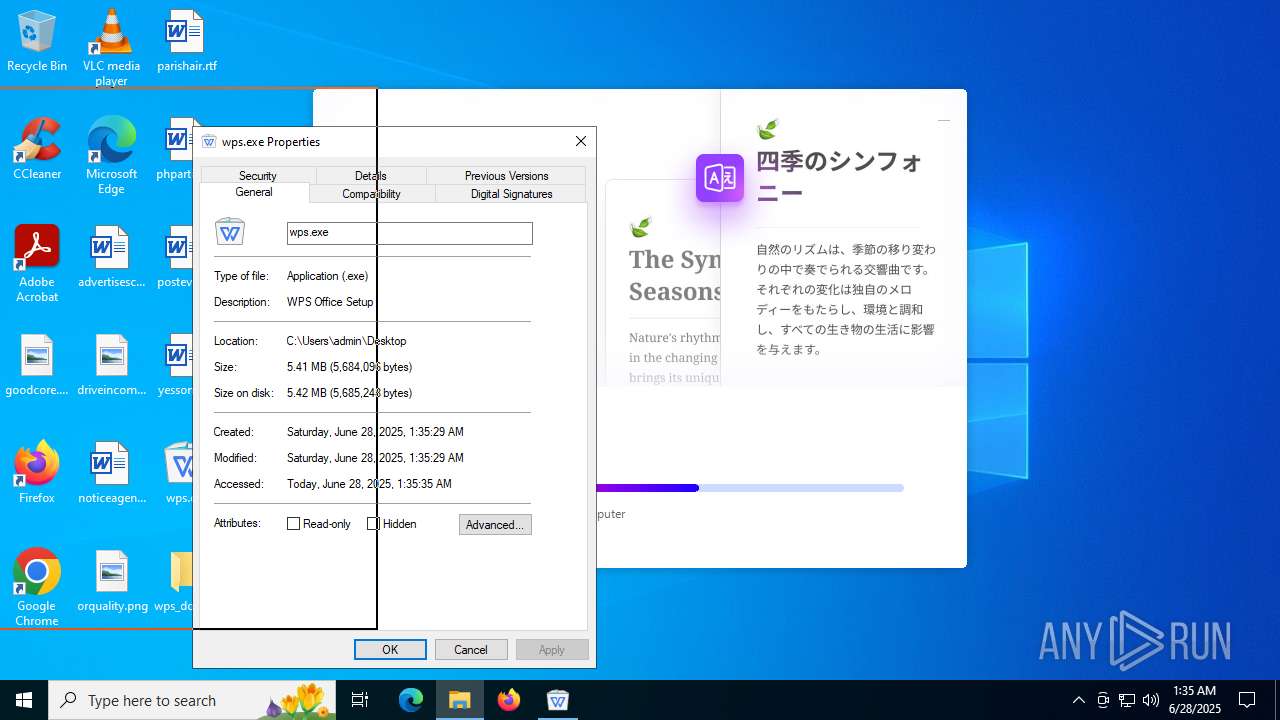
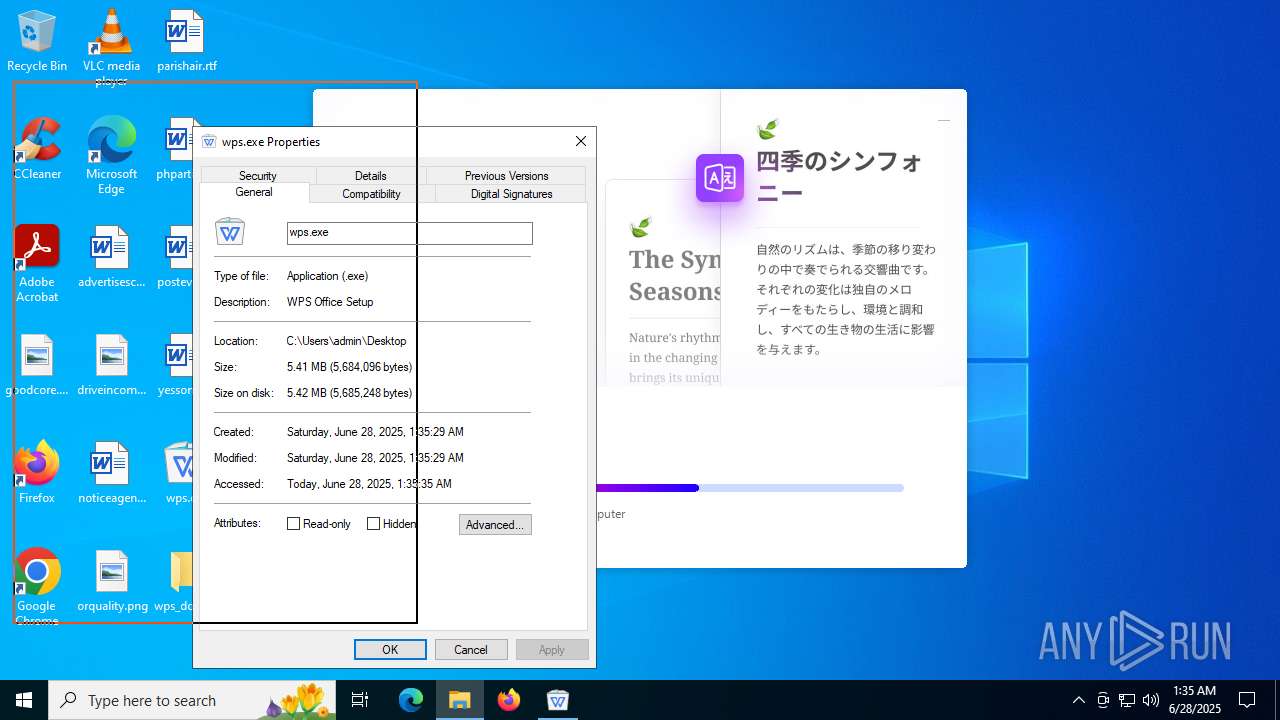
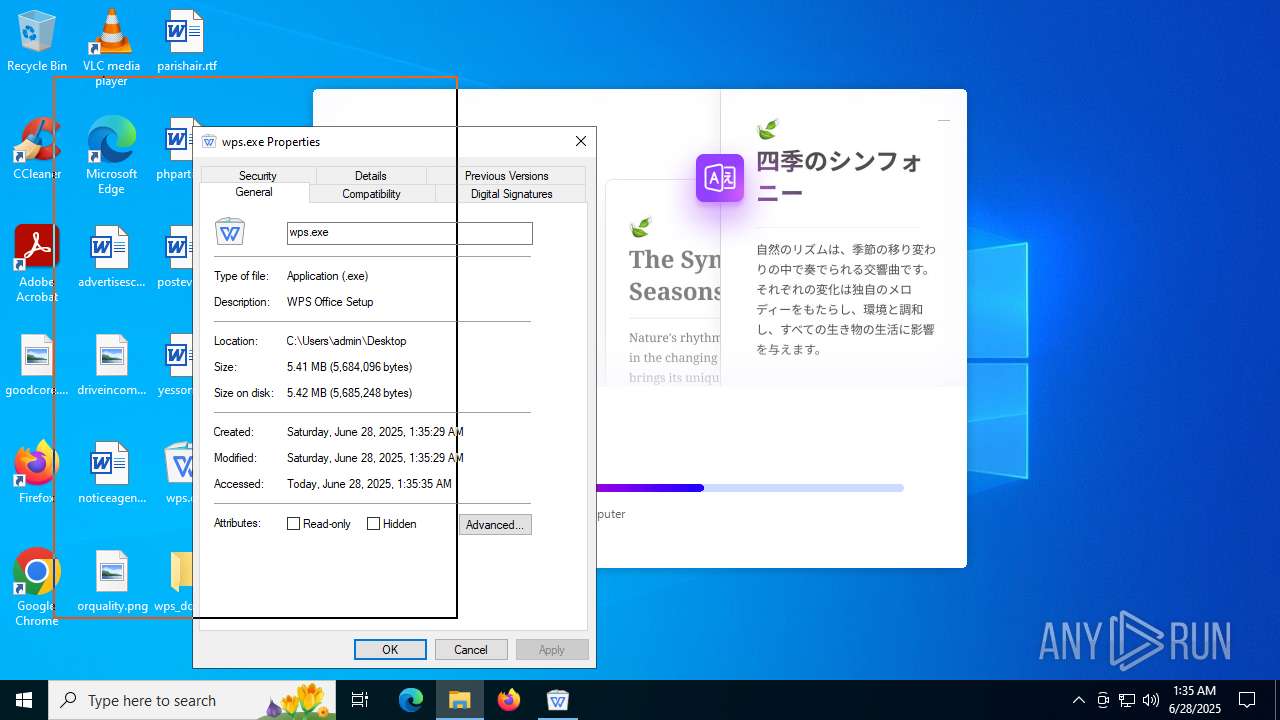
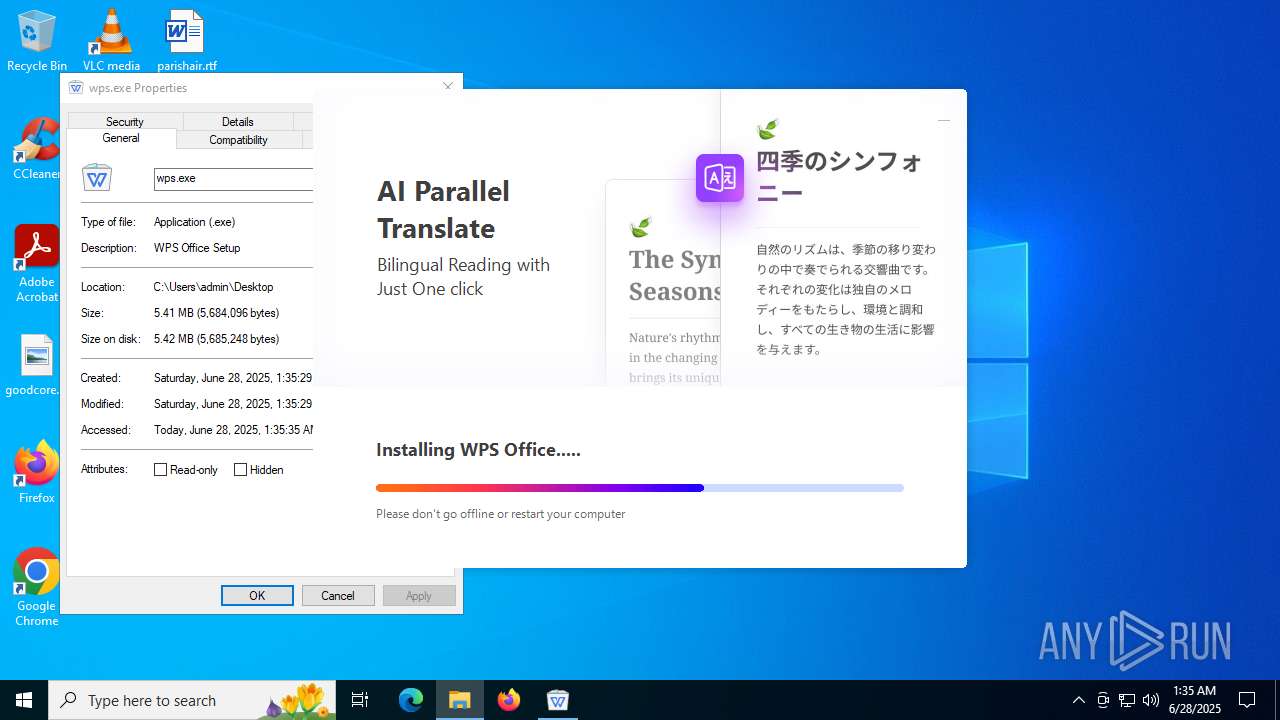
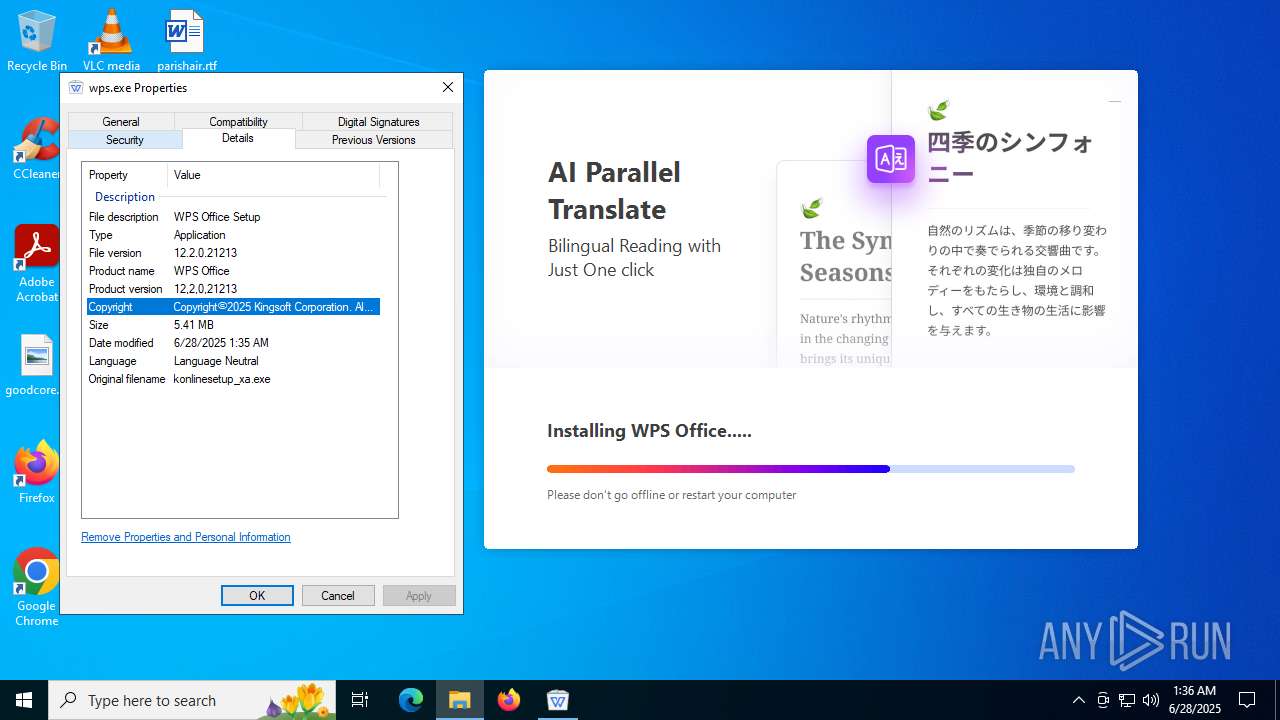
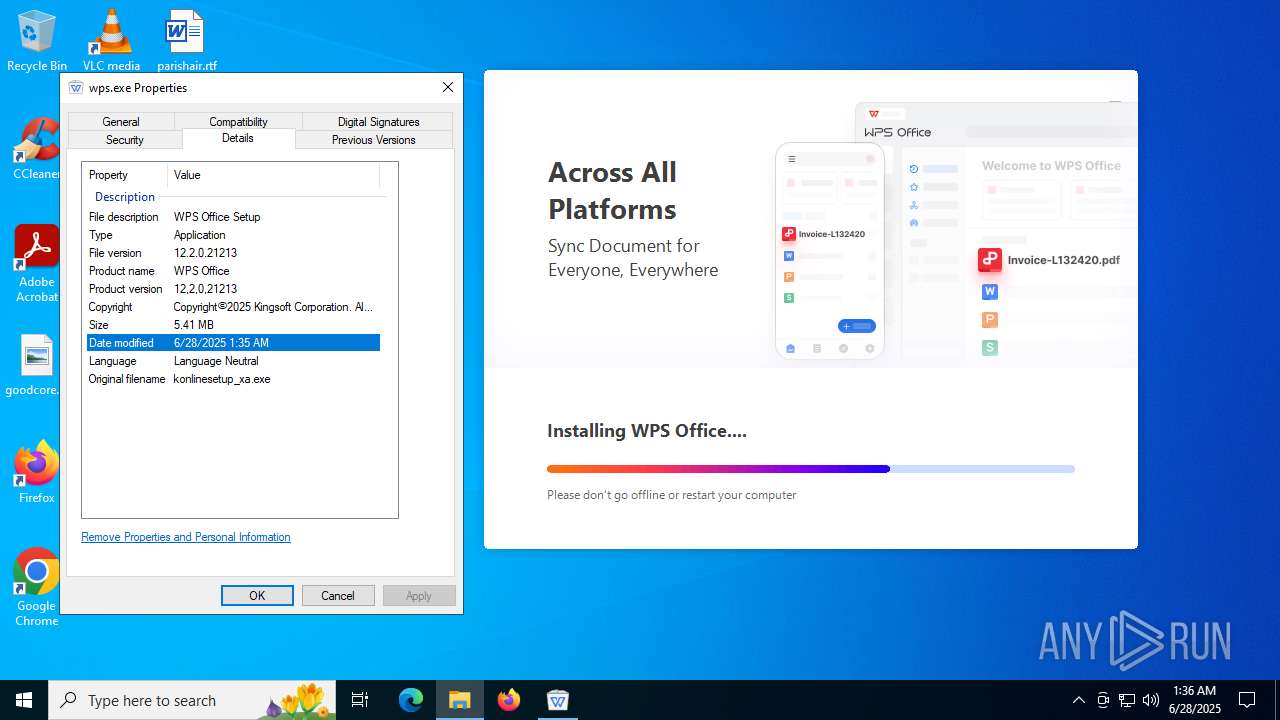
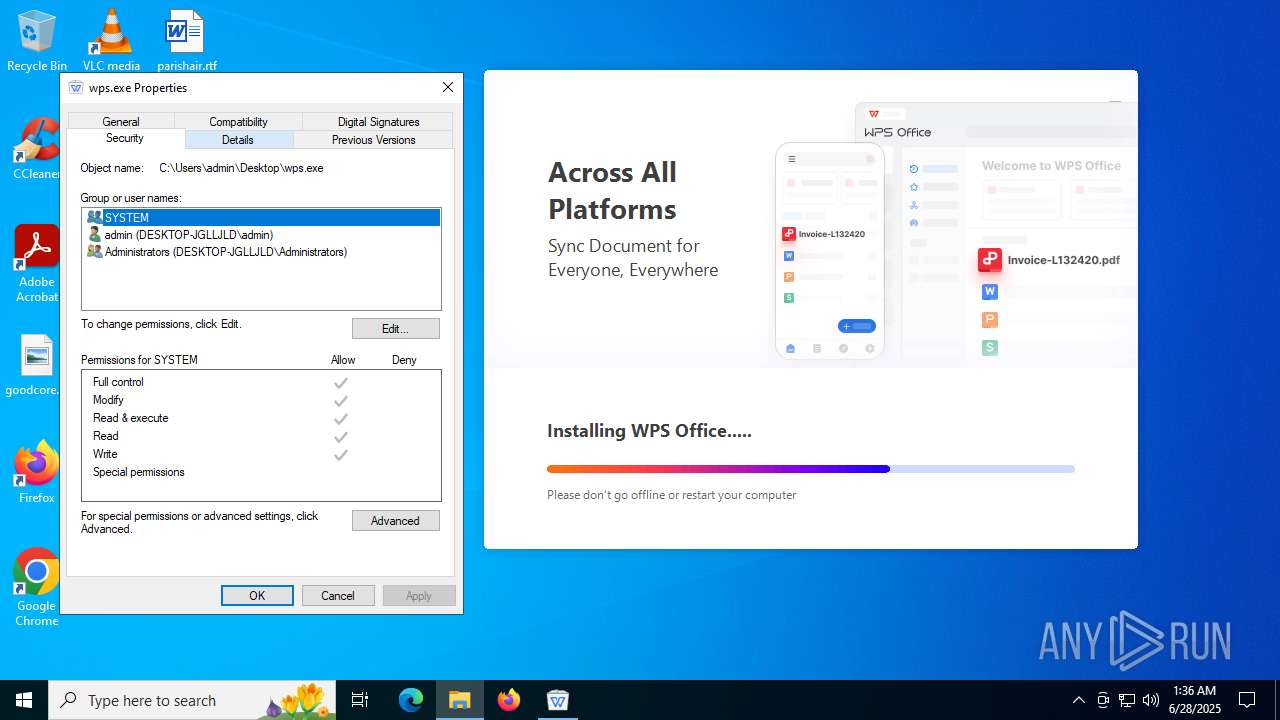
| 1128 | "C:\Users\admin\Desktop\wps.exe" | C:\Users\admin\Desktop\wps.exe | explorer.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Setup Version: 12,2,0,21213 Modules
| |||||||||||||||
| 1468 | /s "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\kmso2pdfplugins64.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\ksomisc.exe" -createsubmodulelink desktop pdf | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\ksomisc.exe | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Module Exit code: 0 Version: 12,2,0,21546 Modules
| |||||||||||||||
| 1868 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\ksomisc.exe" -createsubmodulelink desktop prometheus | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\ksomisc.exe | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Module Exit code: 0 Version: 12,2,0,21546 Modules
| |||||||||||||||
| 1944 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\ksomisc.exe" -assopowerpnt | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\12.2.0.21546\office6\ksomisc.exe | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Module Exit code: 0 Version: 12,2,0,21546 Modules
| |||||||||||||||
Total events
163 929
Read events
159 925
Write events
3 427
Delete events
577
Modification events
| (PID) Process: | (5808) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5808) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5808) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5808) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\22834661865.zip | |||
| (PID) Process: | (5808) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5808) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5808) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5808) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000050306 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (5808) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
Executable files
425
Suspicious files
1 174
Text files
2 451
Unknown types
0
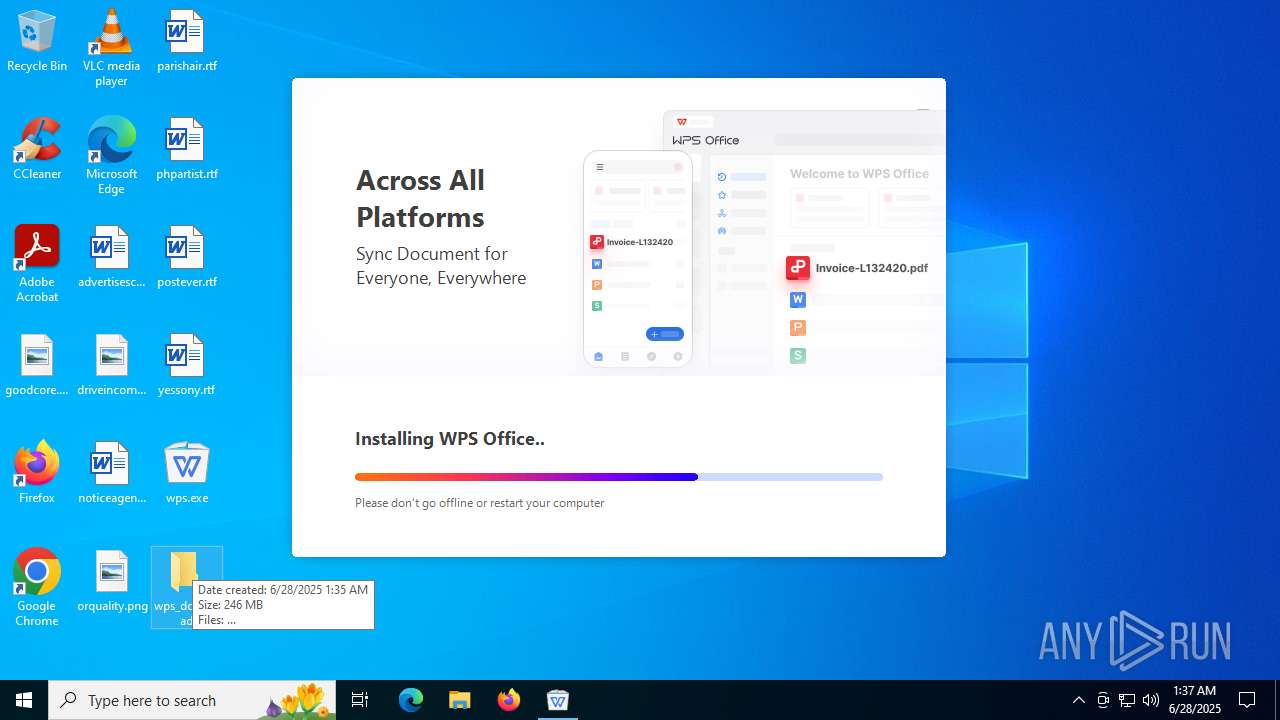
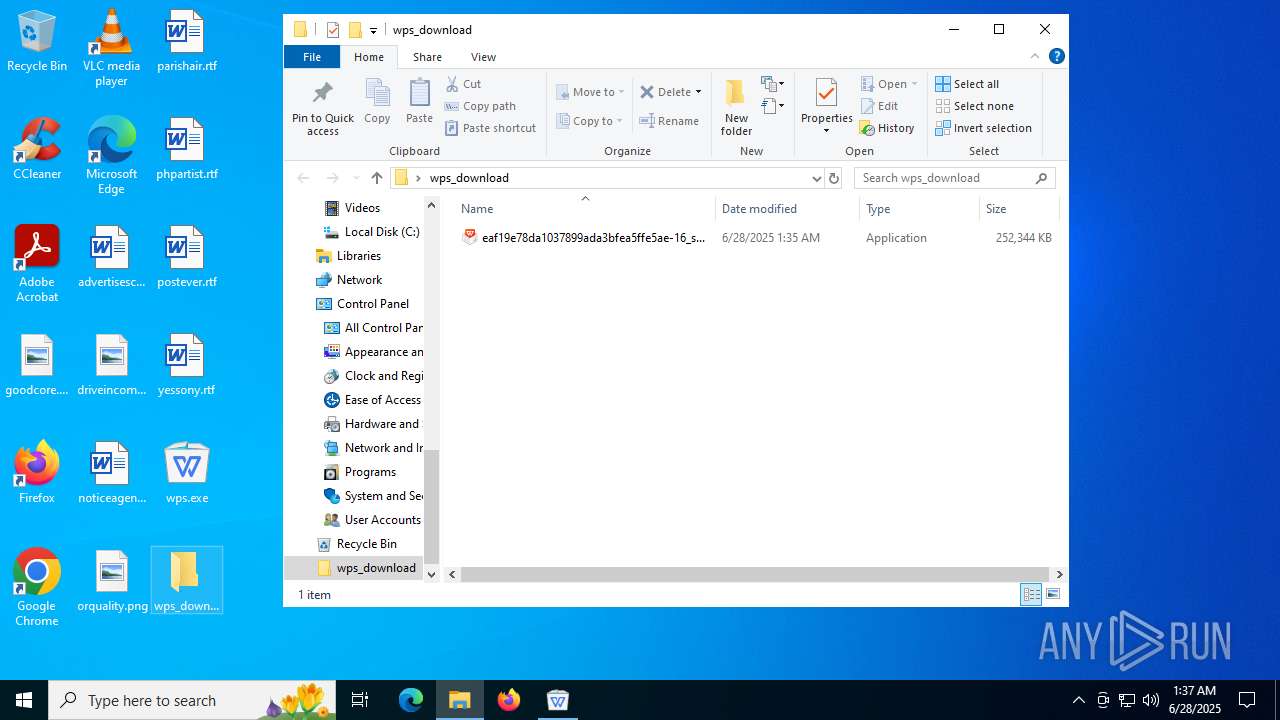
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1128 | wps.exe | C:\Users\admin\Desktop\wps_download\eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | — | |
MD5:— | SHA256:— | |||
| 1052 | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | C:\Users\admin\AppData\Local\Temp\wps\~17ee67\CONTROL\prereadimages_et.txt | — | |
MD5:— | SHA256:— | |||
| 1052 | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | C:\Users\admin\AppData\Local\Temp\wps\~17ee67\CONTROL\prereadimages_pdf.txt | — | |
MD5:— | SHA256:— | |||
| 1052 | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | C:\Users\admin\AppData\Local\Temp\wps\~17ee67\CONTROL\prereadimages_prometheus.txt | — | |
MD5:— | SHA256:— | |||
| 1052 | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | C:\Users\admin\AppData\Local\Temp\wps\~17ee67\CONTROL\prereadimages_prome_init.txt | — | |
MD5:— | SHA256:— | |||
| 1052 | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | C:\Users\admin\AppData\Local\Temp\wps\~17ee67\CONTROL\prereadimages_qing.txt | — | |
MD5:— | SHA256:— | |||
| 1052 | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | C:\Users\admin\AppData\Local\Temp\wps\~17ee67\CONTROL\prereadimages_wpp.txt | — | |
MD5:— | SHA256:— | |||
| 1052 | eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | C:\Users\admin\AppData\Local\Temp\wps\~17ee67\CONTROL\prereadimages_wps.txt | — | |
MD5:— | SHA256:— | |||
| 4772 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 4772 | explorer.exe | C:\Users\admin\Desktop\wps.exe | executable | |
MD5:A473D96E0AC7FC71424B71B47484672C | SHA256:66FA064FE21F9A94F4C713FC2151B5A0DC8058C8A352328F0D74BD4A74FCEA66 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
64
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
436 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
2996 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 420 b | whitelisted |
2996 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
4772 | explorer.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA9S8pUz7rrUEVA2eU7hB08%3D | DE | binary | 727 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | SE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
4772 | explorer.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | DE | binary | 727 b | whitelisted |
4772 | explorer.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | DE | binary | 471 b | whitelisted |
1028 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
6364 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | DE | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4372 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
436 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
wdl1.pcfg.cache.wpscdn.com |
| unknown |
Threats
Process | Message |
|---|---|
eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | [kscreen] isElide:0 switchRec:0 switchRecElide:1 |
eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | QLayout: Attempting to add QLayout "" to QWidget "", which already has a layout
|
eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | QLayout: Attempting to add QLayout "" to QWidget "m_BrandAreaWidget", which already has a layout
|
eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
eaf19e78da1037899ada3bfea5ffe5ae-16_setup_XA_mui_Free.exe.601.1074.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|