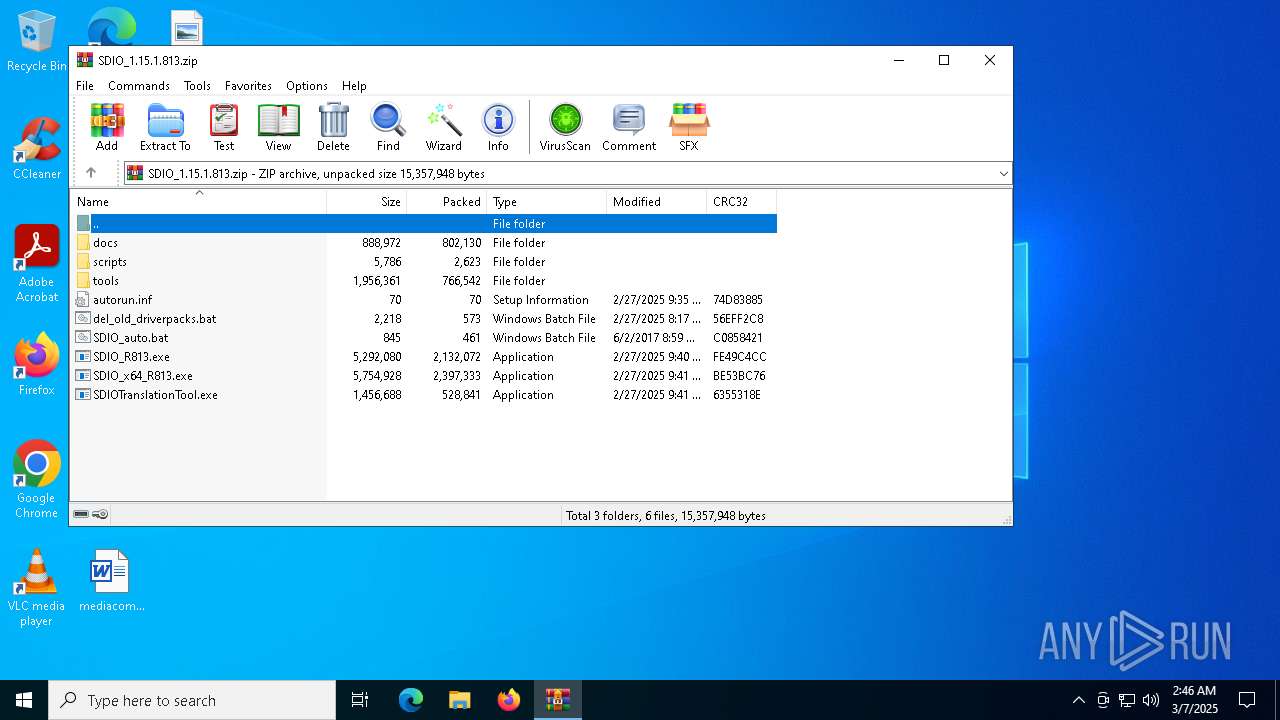
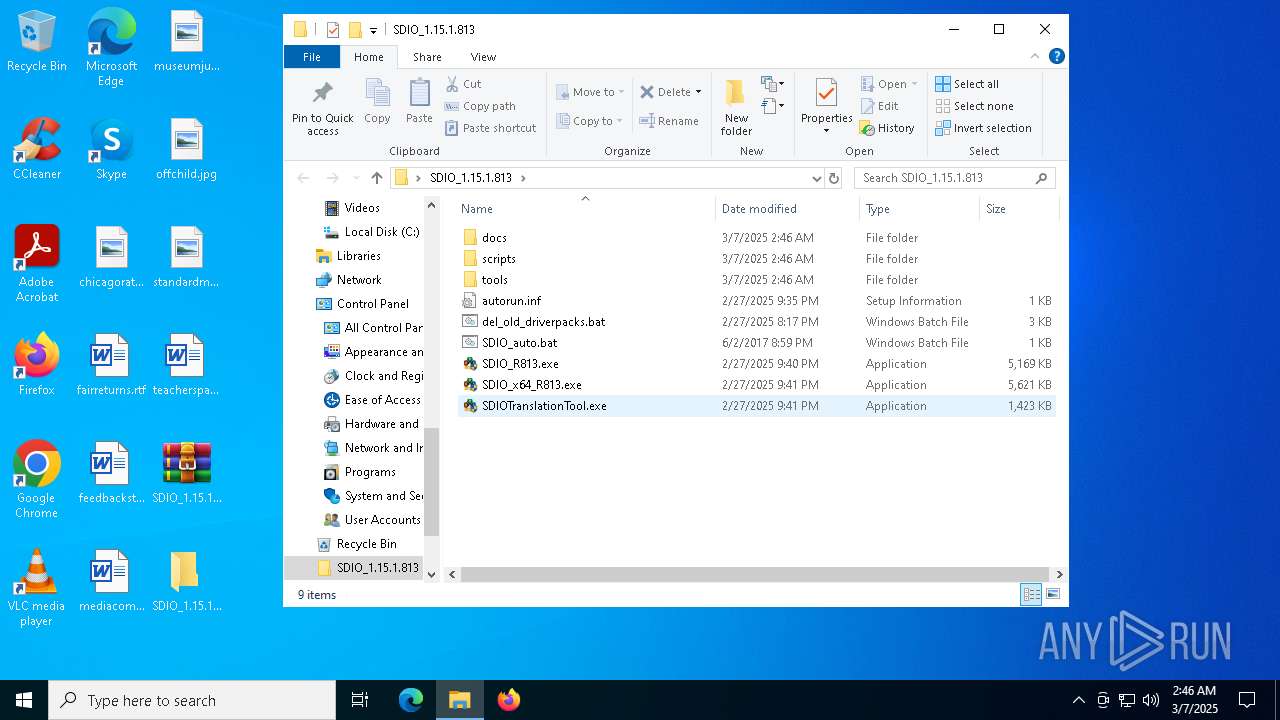
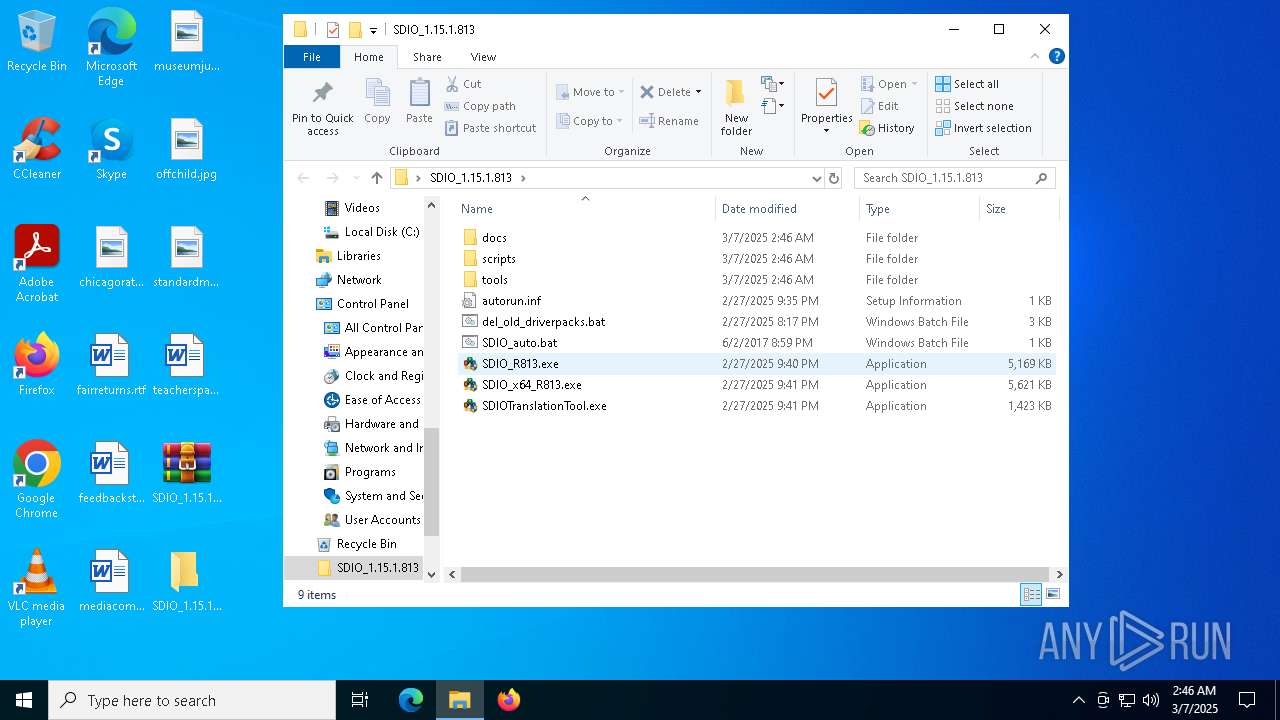
| File name: | SDIO_1.15.1.813.zip |
| Full analysis: | https://app.any.run/tasks/d5a554e7-2a43-4b3c-af27-481b37f48a2b |
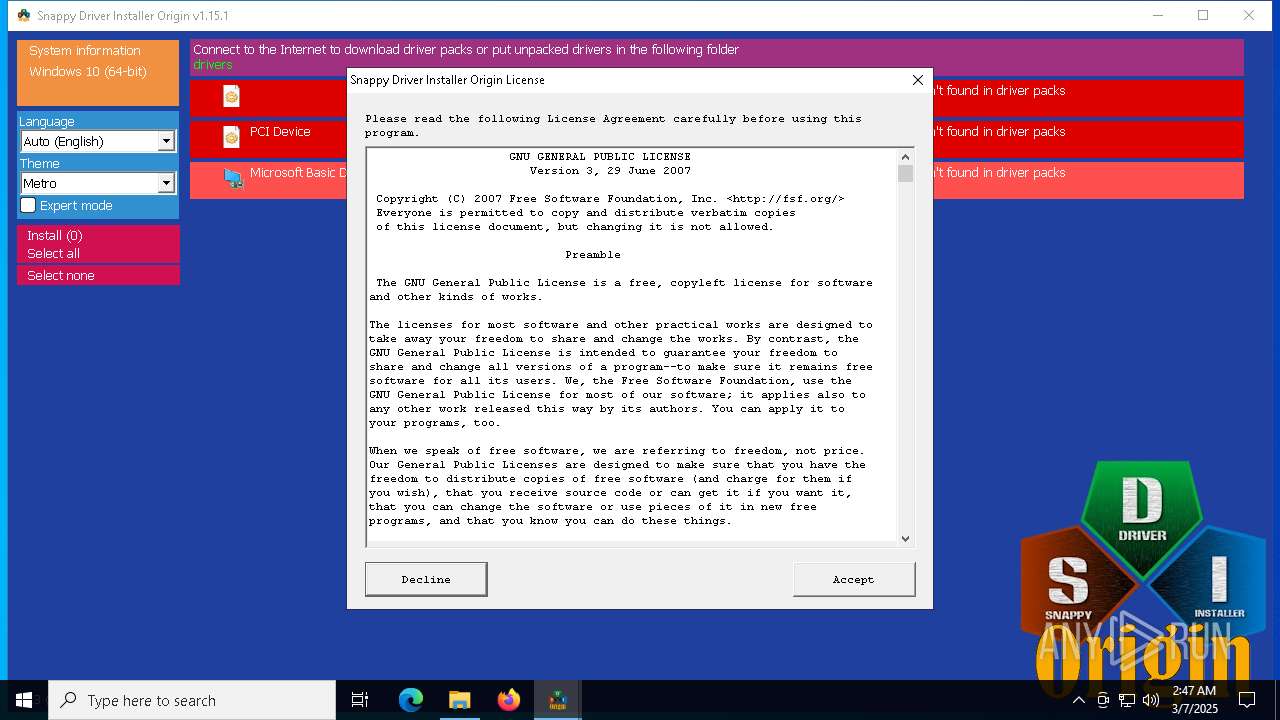
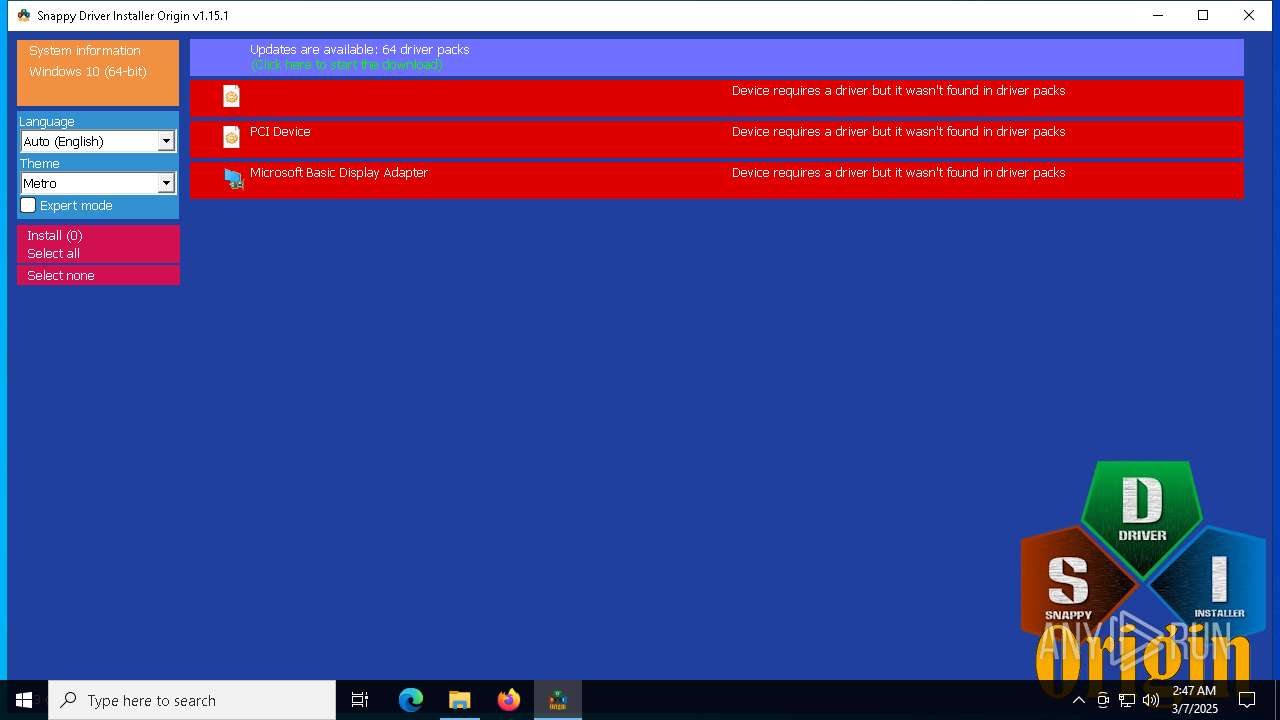
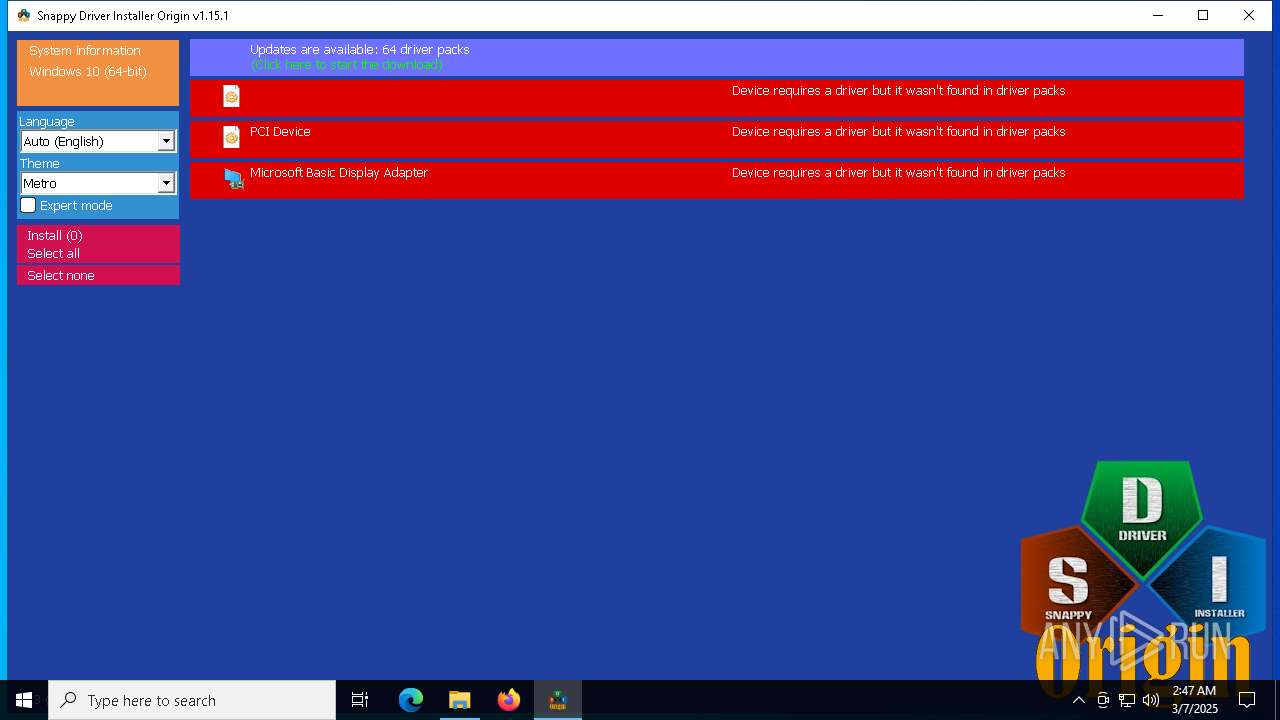
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2025, 02:46:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 2AD065D9CA39BB390EDAC96EBFB7AF33 |
| SHA1: | C844E3E3E5102175560C56058BBDAE814F0A67E5 |
| SHA256: | 83F65065DE223C3F2AA371B0AE14C8DAA2C6AE42E28F8ACD54A919E44CE4FC55 |
| SSDEEP: | 98304:5E4Wo6DFJlFn7Mtw5AFSG4MkCsvbF/77ysglMFU+FpKvZkY2iFTCWlfCK4YH+yfB:6fgzL0qF6026nXiI |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7408)
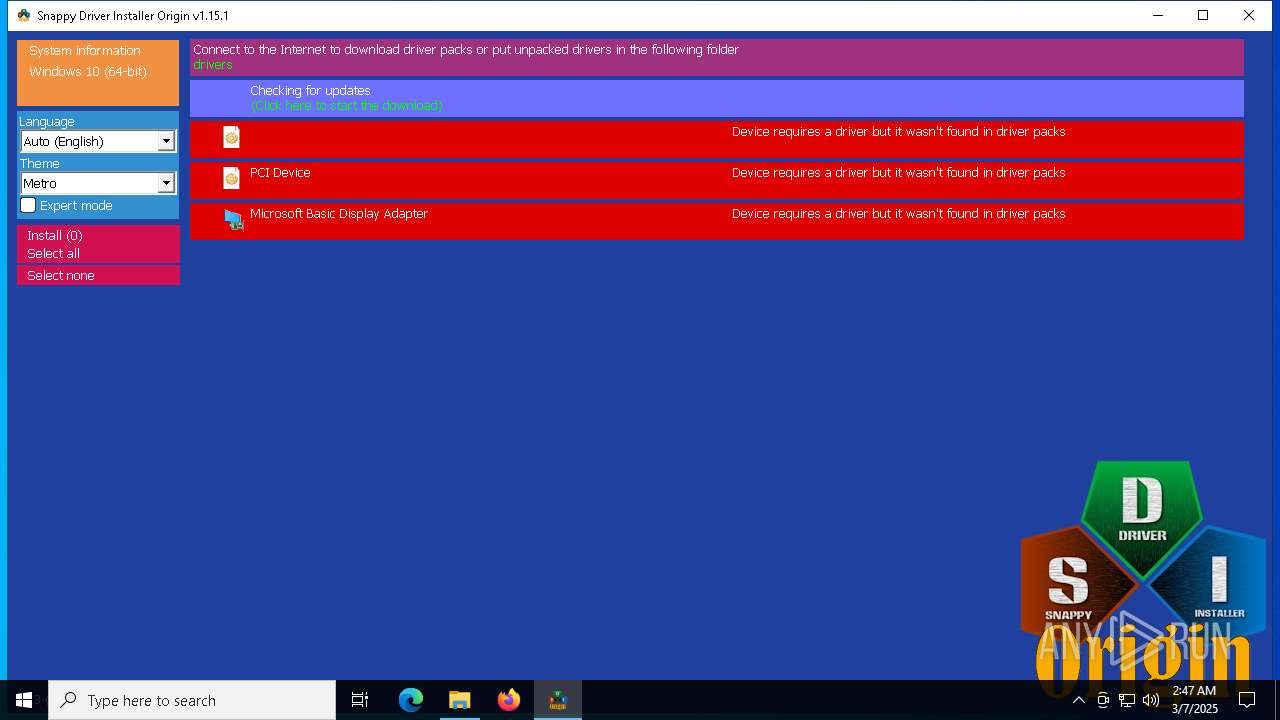
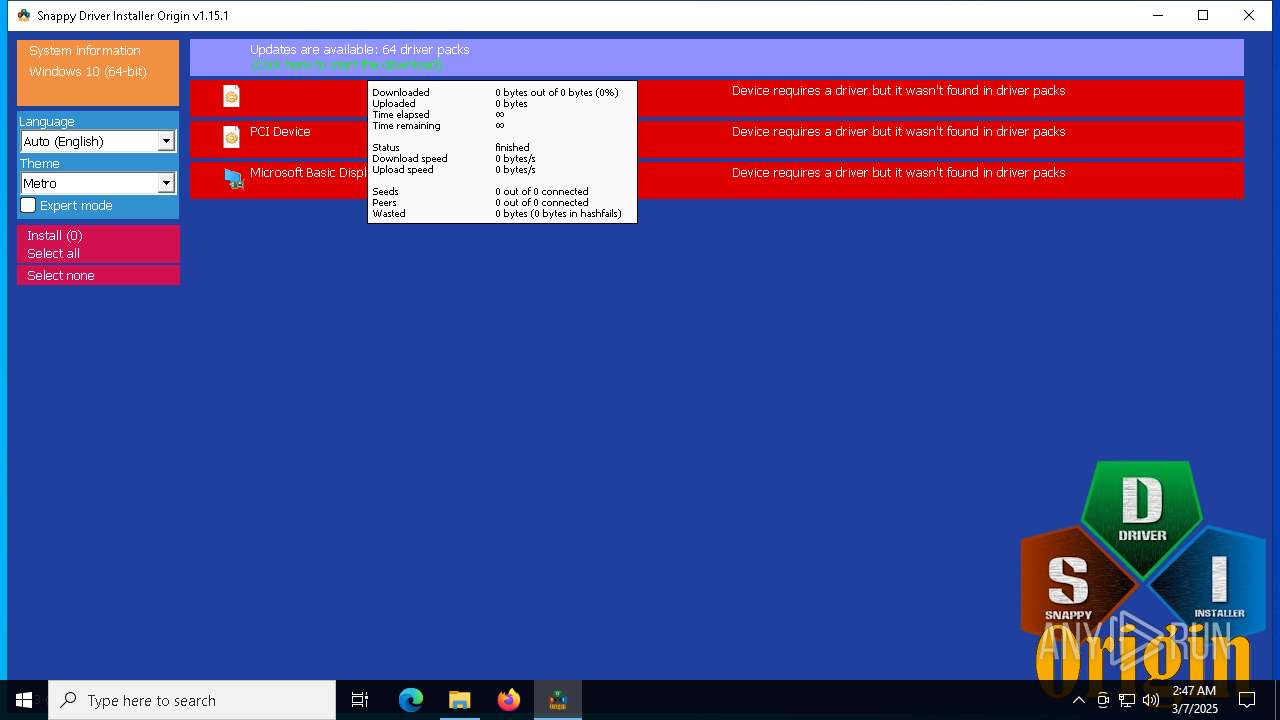
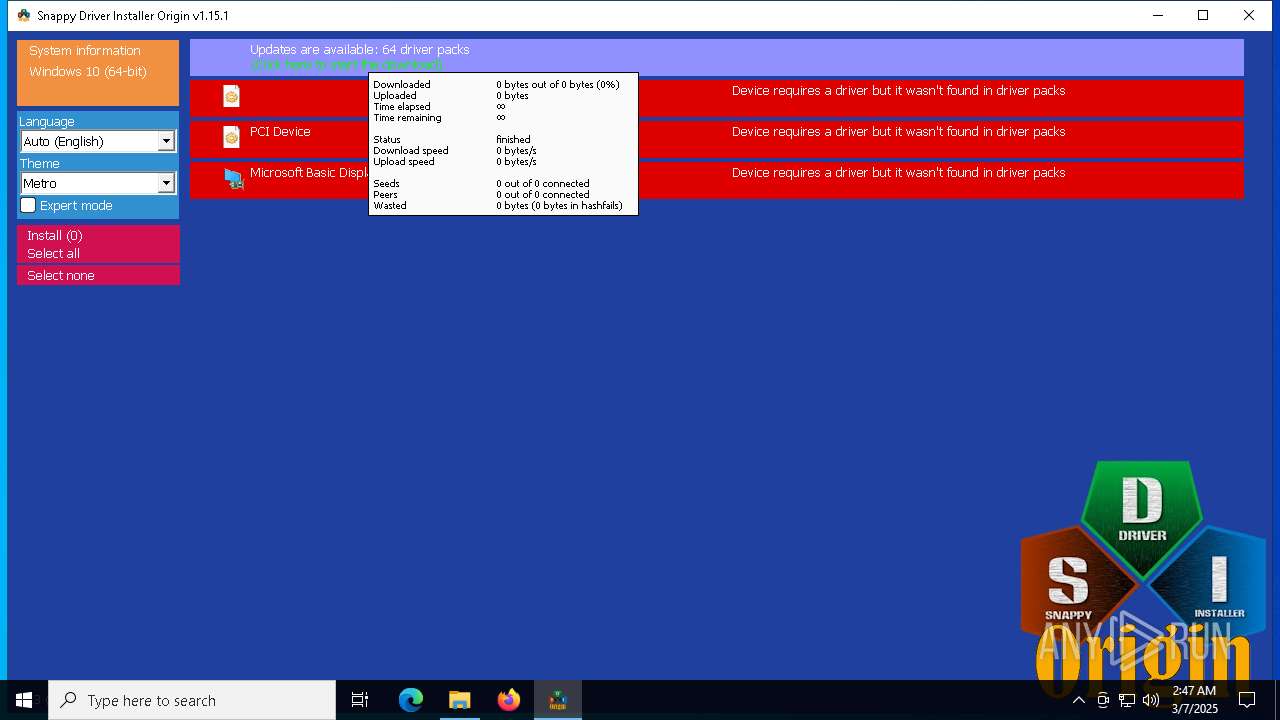
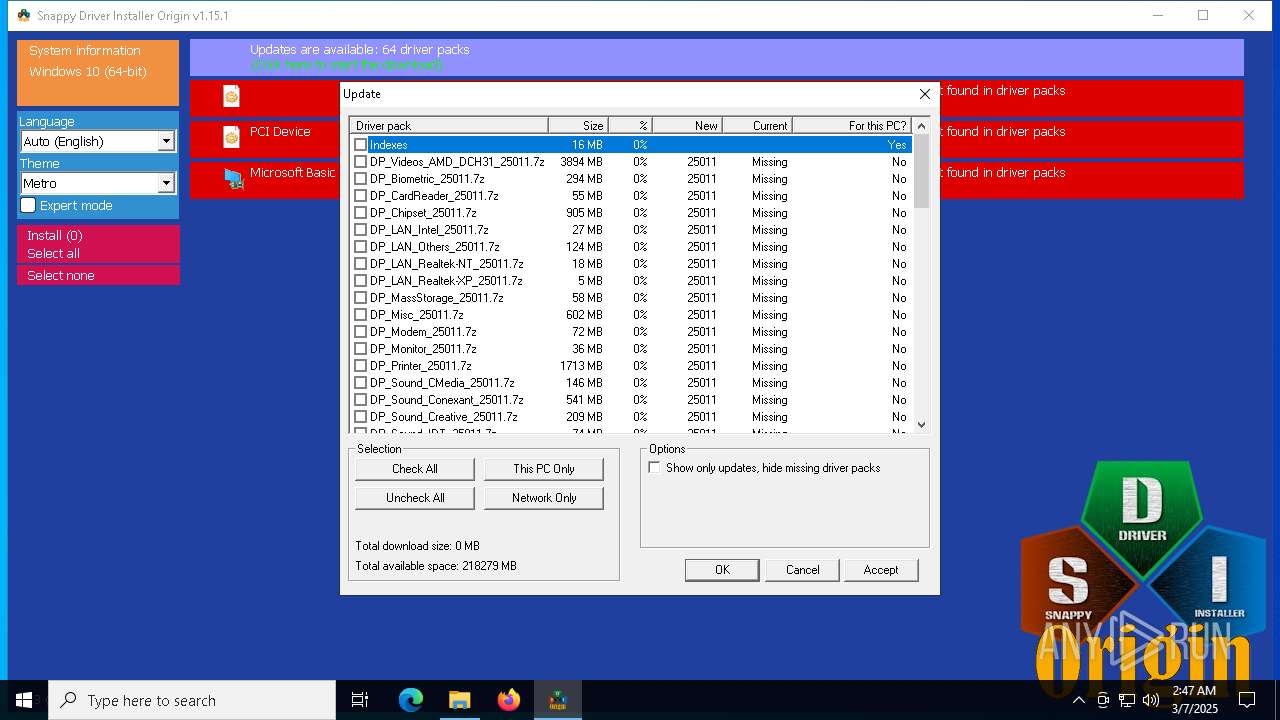
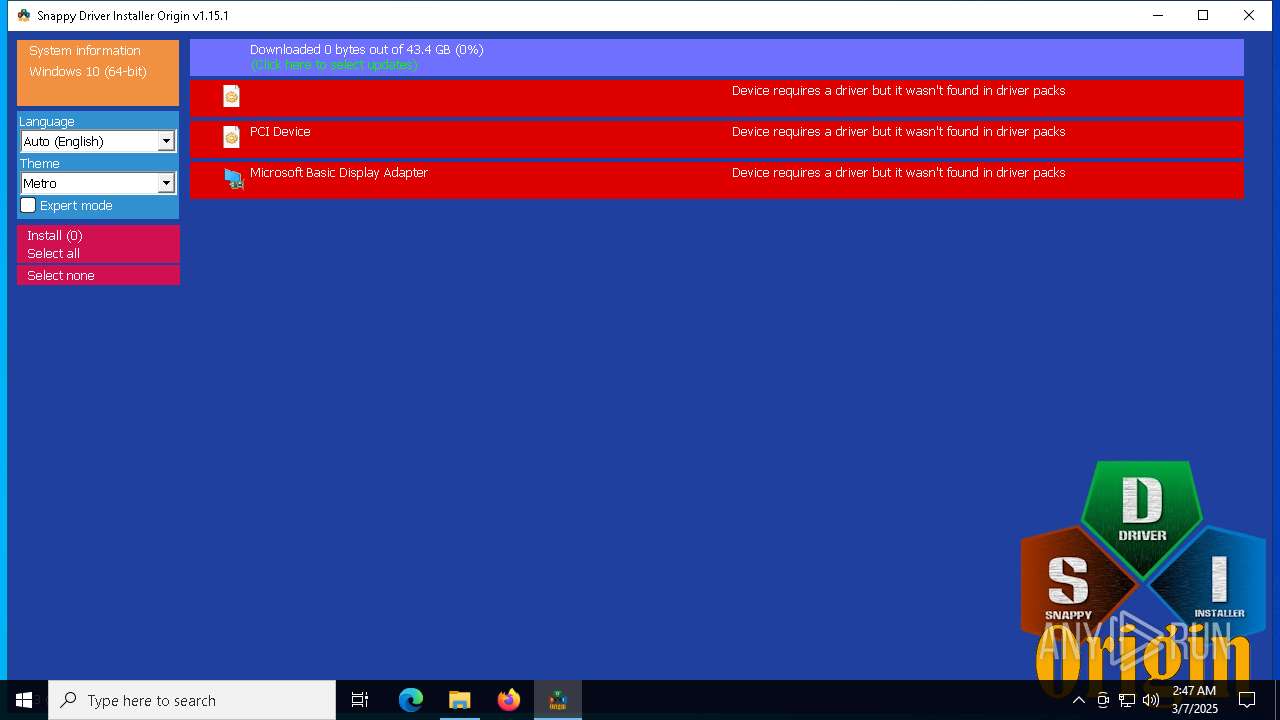
BITTORRENT has been detected (SURICATA)
- SDIO_x64_R813.exe (PID: 6028)
SUSPICIOUS
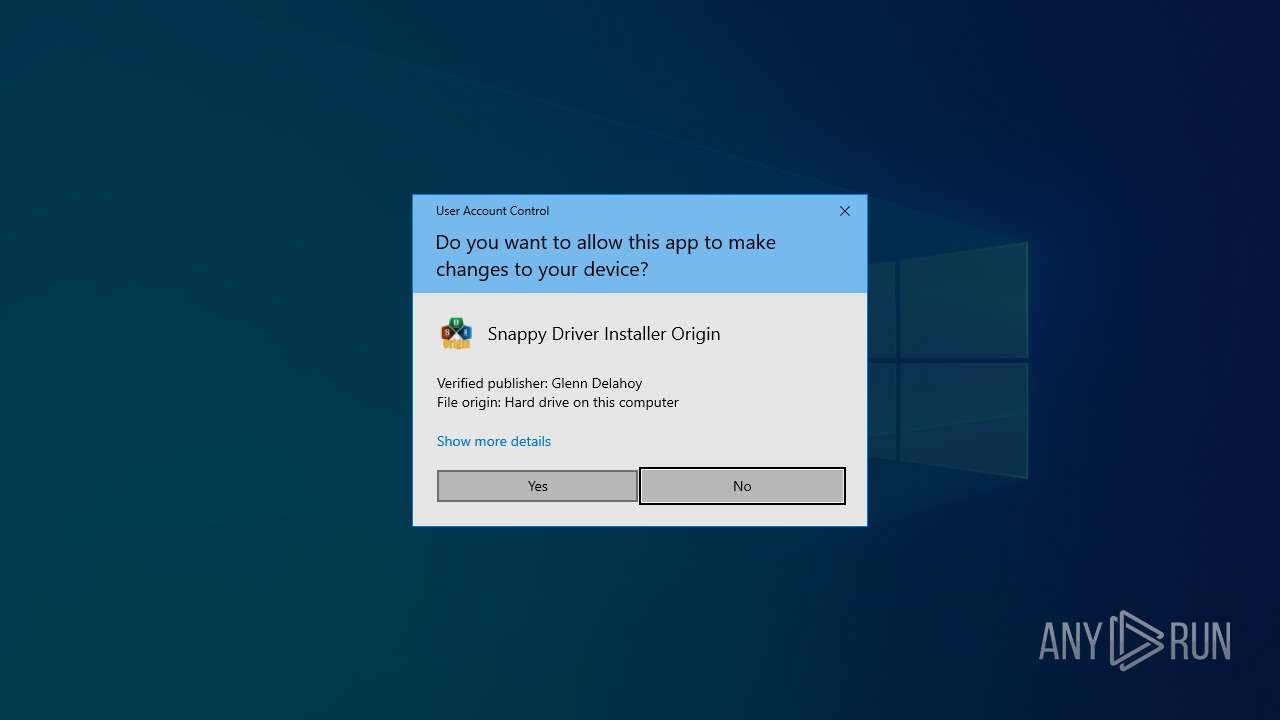
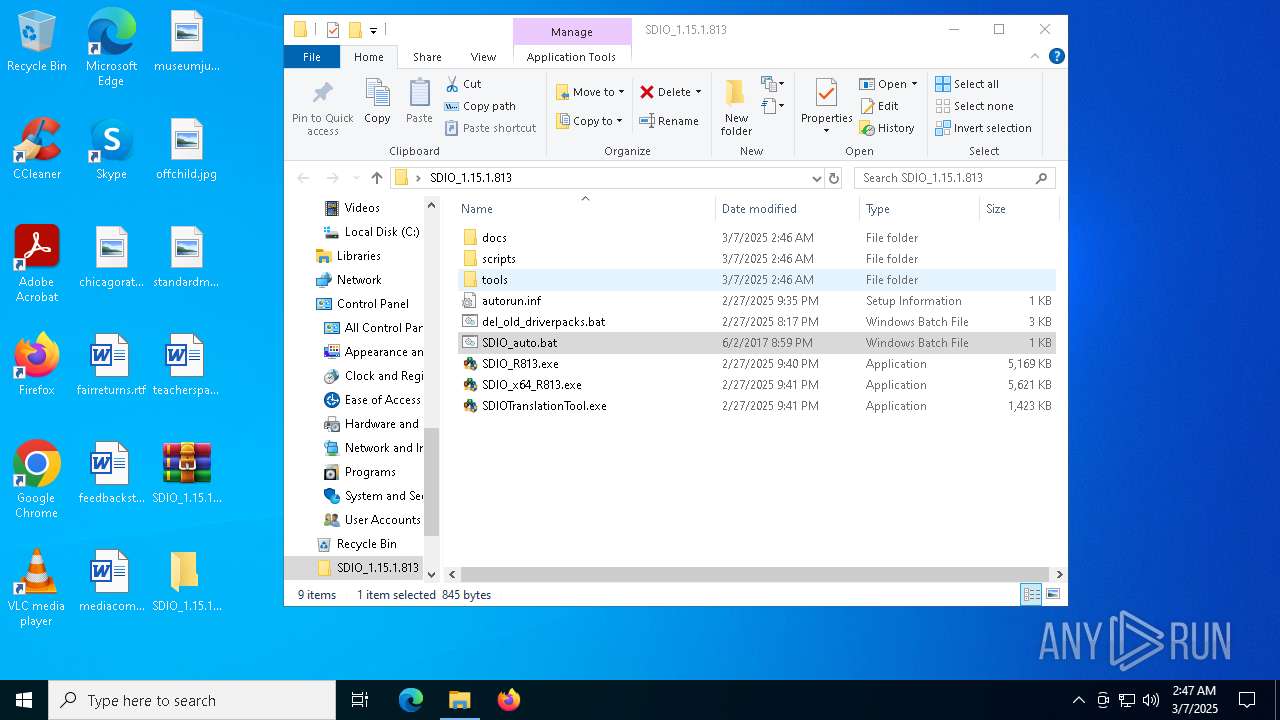
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4436)
- SDIO_x64_R813.exe (PID: 6028)
Application launched itself
- cmd.exe (PID: 4436)
Potential Corporate Privacy Violation
- SDIO_x64_R813.exe (PID: 6028)
Connects to unusual port
- SDIO_x64_R813.exe (PID: 6028)
Reads security settings of Internet Explorer
- SDIO_x64_R813.exe (PID: 6028)
INFO
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 6436)
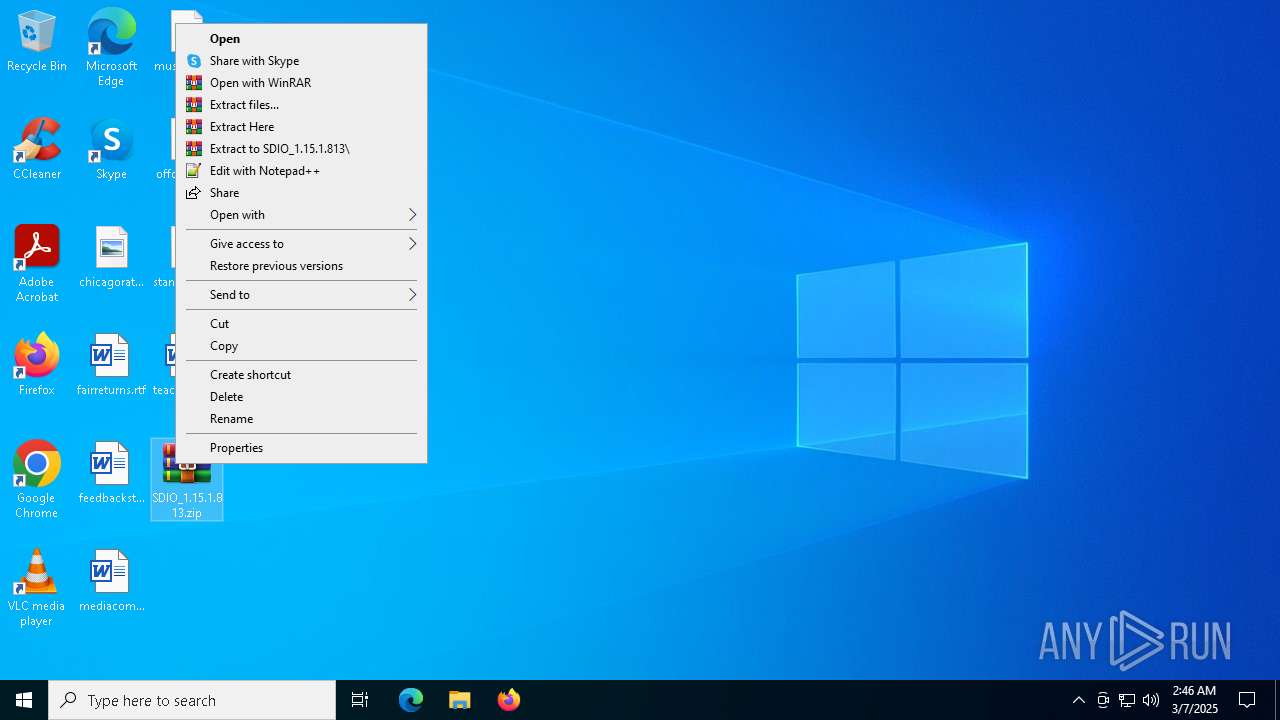
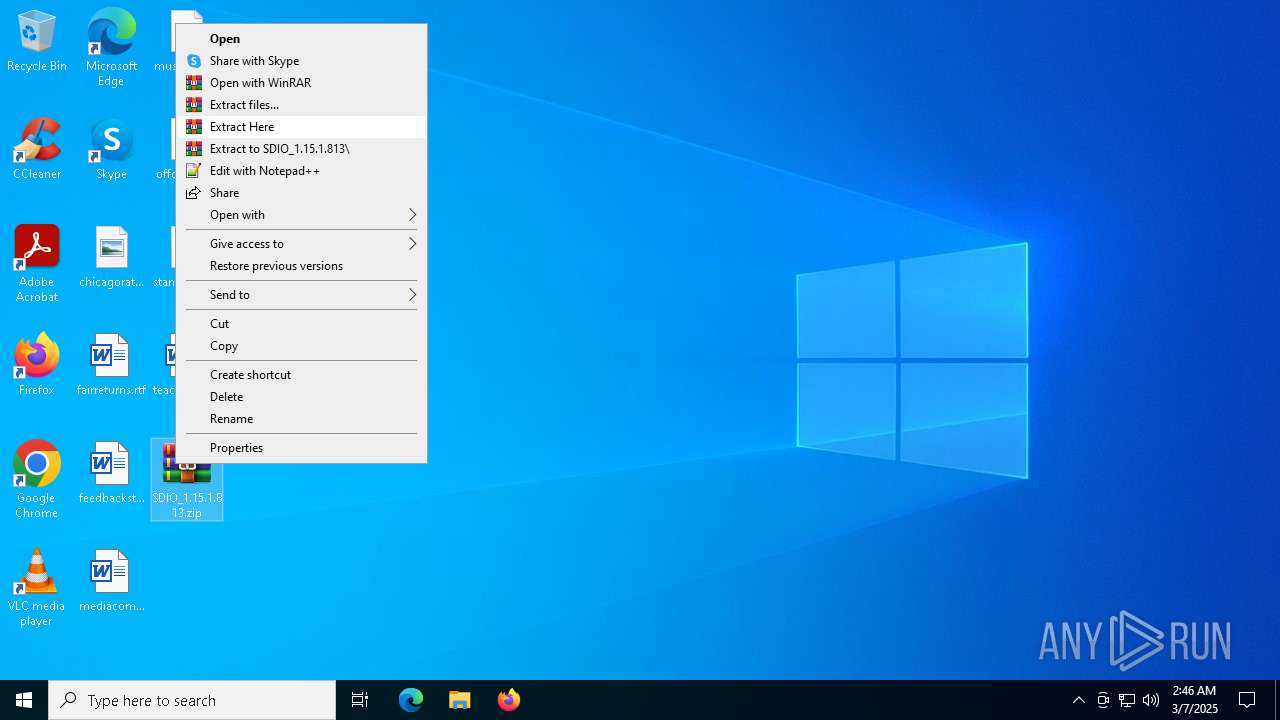
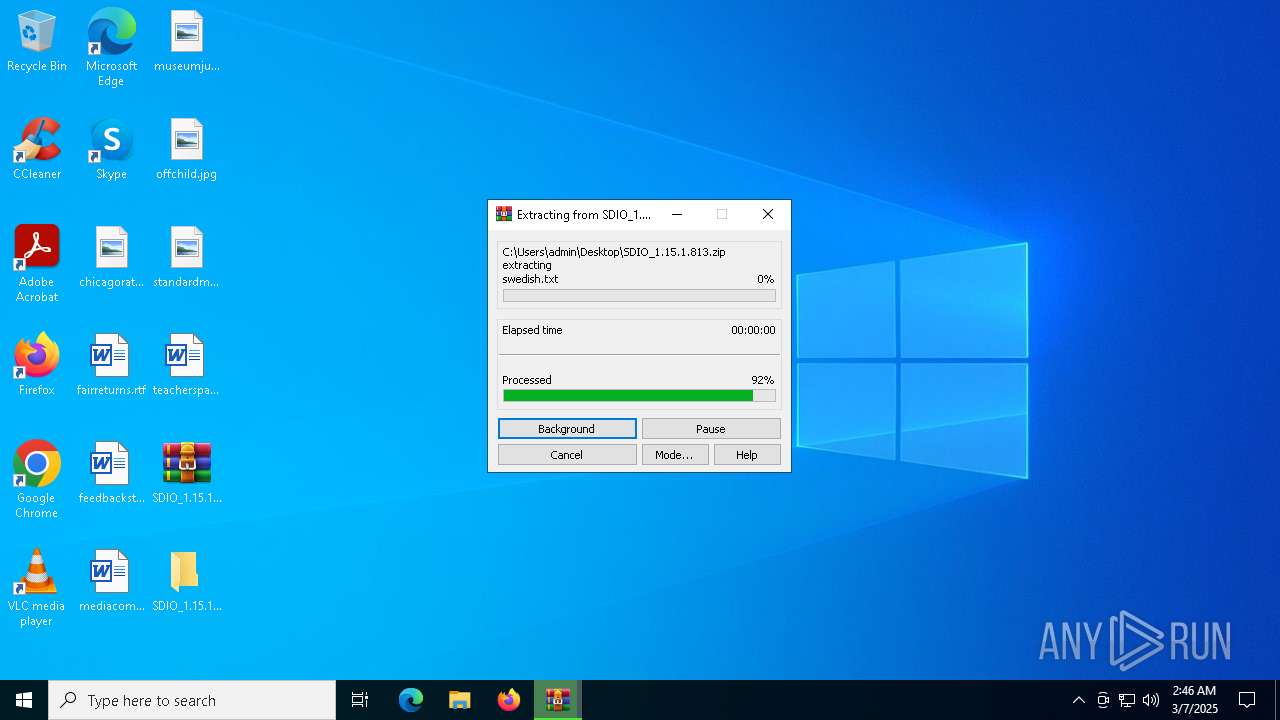
Manual execution by a user
- WinRAR.exe (PID: 7660)
- cmd.exe (PID: 4436)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 3100)
- BackgroundTransferHost.exe (PID: 7992)
- BackgroundTransferHost.exe (PID: 4220)
- BackgroundTransferHost.exe (PID: 6436)
- BackgroundTransferHost.exe (PID: 7224)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 6436)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 6436)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7660)
The sample compiled with english language support
- WinRAR.exe (PID: 7660)
Checks supported languages
- SDIO_x64_R813.exe (PID: 6028)
Reads Environment values
- SDIO_x64_R813.exe (PID: 6028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:02:28 08:35:06 |
| ZipCRC: | 0x74d83885 |
| ZipCompressedSize: | 70 |
| ZipUncompressedSize: | 70 |
| ZipFileName: | autorun.inf |
Total processes
154
Monitored processes
21
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3100 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3100 | "C:\Windows\System32\cmd.exe" /c rd /s /q update | C:\Windows\System32\cmd.exe | — | SDIO_x64_R813.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4112 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4220 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4436 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\SDIO_1.15.1.813\SDIO_auto.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5164 | "C:\Users\admin\Desktop\SDIO_1.15.1.813\SDIO_x64_R813.exe" | C:\Users\admin\Desktop\SDIO_1.15.1.813\SDIO_x64_R813.exe | — | cmd.exe | |||||||||||
User: admin Company: Glenn Delahoy Integrity Level: MEDIUM Description: Snappy Driver Installer Origin Exit code: 3221226540 Version: 1.15.1.813 Modules
| |||||||||||||||
| 5380 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SDIO_x64_R813.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6028 | "C:\Users\admin\Desktop\SDIO_1.15.1.813\SDIO_x64_R813.exe" | C:\Users\admin\Desktop\SDIO_1.15.1.813\SDIO_x64_R813.exe | cmd.exe | ||||||||||||
User: admin Company: Glenn Delahoy Integrity Level: HIGH Description: Snappy Driver Installer Origin Version: 1.15.1.813 Modules
| |||||||||||||||
| 6436 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 623
Read events
5 586
Write events
37
Delete events
0
Modification events
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SDIO_1.15.1.813.zip | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
3
Suspicious files
17
Text files
155
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6436 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\6d6321bc-15ff-4587-ac52-44099661608e.down_data | — | |
MD5:— | SHA256:— | |||
| 6436 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:38989CDC9B939CBF439472EC8FEBE5D7 | SHA256:0188CCDAB61284075618619F99DBB9FC9BA066DF5B1FF02EC5684476CABA0732 | |||
| 7660 | WinRAR.exe | C:\Users\admin\Desktop\SDIO_1.15.1.813\autorun.inf | binary | |
MD5:016671EEC700B2D556A0996FD9232A11 | SHA256:A18059537BF72A077B8252BFA8DF9EFB168FC1F83C0686559858AC0EE2DEE258 | |||
| 7660 | WinRAR.exe | C:\Users\admin\Desktop\SDIO_1.15.1.813\scripts\scan_driver_packs.bat | text | |
MD5:2DBC6FD7355358866C8FACE4168A18AC | SHA256:7C78826B30C054D407037D41368A40FABEF133F1C83348290F0D756E05141E16 | |||
| 7660 | WinRAR.exe | C:\Users\admin\Desktop\SDIO_1.15.1.813\scripts\remote.bat | text | |
MD5:CDC25C410A2B6EB4E7E8C90294C2146E | SHA256:C6DE4403113E0586CBA59FDFC2CB20C68F2C690636692D03C9A4CCE09CA61287 | |||
| 7660 | WinRAR.exe | C:\Users\admin\Desktop\SDIO_1.15.1.813\scripts\prep_unpacked.bat | text | |
MD5:00BDB244439526A613B23F1EA831D926 | SHA256:671C3B573A7A0A617E5A1156EC2C6496846A3A256B64A5AD1CE92FD179904954 | |||
| 6436 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\c7978982-6407-4068-b9cf-f02292cc1bf7.up_meta_secure | binary | |
MD5:70314611C355F80F1B7ED14E911F7F9B | SHA256:1CD02877355446B2425DE29F331230B59BEB86F22B66840357DA7342653310E7 | |||
| 6436 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\c7978982-6407-4068-b9cf-f02292cc1bf7.88286087-bf66-4322-beda-66855a8c77f2.down_meta | binary | |
MD5:ACC77E9A629AFE11BE6F7A68E14C323A | SHA256:5ED3BA9C578DA46971A6E12B92A5F223C99378BD5FCE88C1710BEB37D55C10E7 | |||
| 6436 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\6d6321bc-15ff-4587-ac52-44099661608e.88286087-bf66-4322-beda-66855a8c77f2.down_meta | binary | |
MD5:ACC77E9A629AFE11BE6F7A68E14C323A | SHA256:5ED3BA9C578DA46971A6E12B92A5F223C99378BD5FCE88C1710BEB37D55C10E7 | |||
| 7660 | WinRAR.exe | C:\Users\admin\Desktop\SDIO_1.15.1.813\scripts\autoupdate.bat | text | |
MD5:3342F57D5527BDE4740984AA492223F9 | SHA256:3A5EDFAA2CDAACB452D7F09EC7D3BD9A374D335A46173F8E0D2D678FB63FB245 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
333
DNS requests
18
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7768 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6436 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
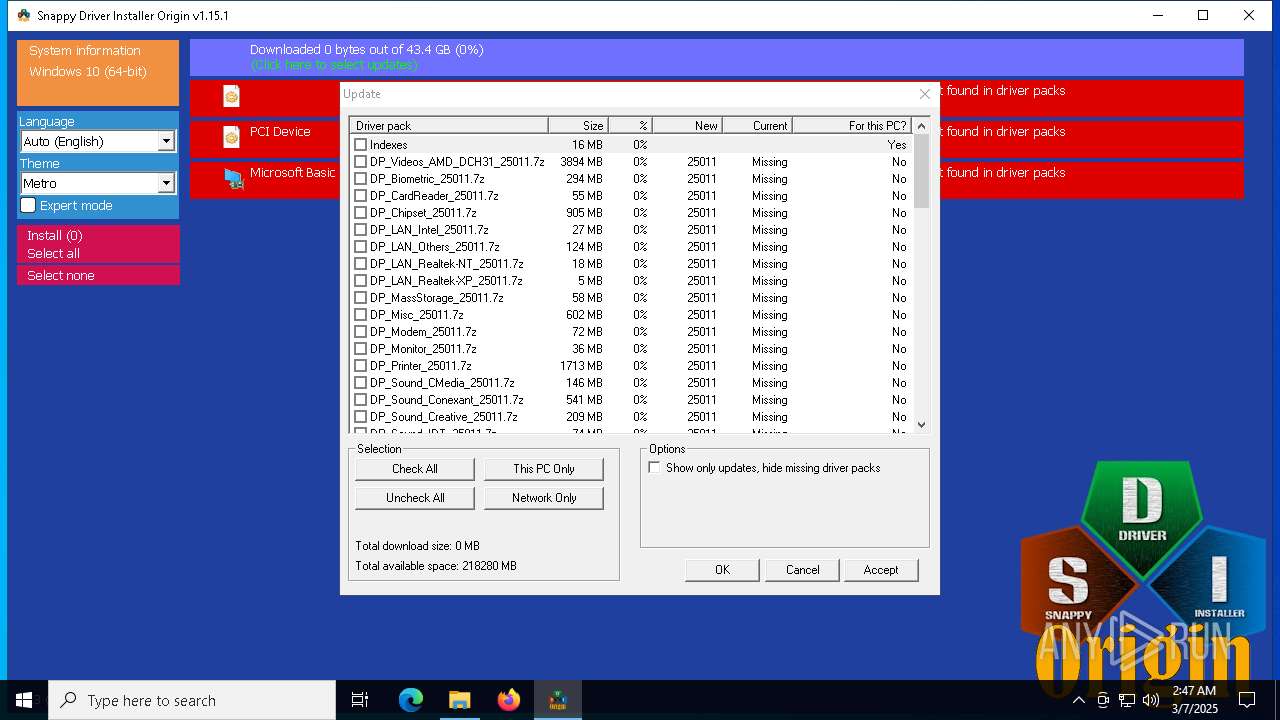
6028 | SDIO_x64_R813.exe | GET | 200 | 110.232.143.85:80 | http://www.snappy-driver-installer.org/downloads/SDIO_Update.torrent | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7768 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7768 | backgroundTaskHost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6436 | BackgroundTransferHost.exe | 104.126.37.178:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
router.bittorrent.com |
| whitelisted |
router.utorrent.com |
| whitelisted |
router.bitcomet.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6028 | SDIO_x64_R813.exe | Potential Corporate Privacy Violation | ET P2P Possible Torrent Download via HTTP Request |
6028 | SDIO_x64_R813.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent - Torrent File Downloaded |
6028 | SDIO_x64_R813.exe | Potential Corporate Privacy Violation | ET P2P Vuze BT UDP Connection (5) |
6028 | SDIO_x64_R813.exe | Misc activity | INFO [ANY.RUN] P2P BitTorrent Protocol |
6028 | SDIO_x64_R813.exe | Misc activity | INFO [ANY.RUN] P2P BitTorrent Protocol |