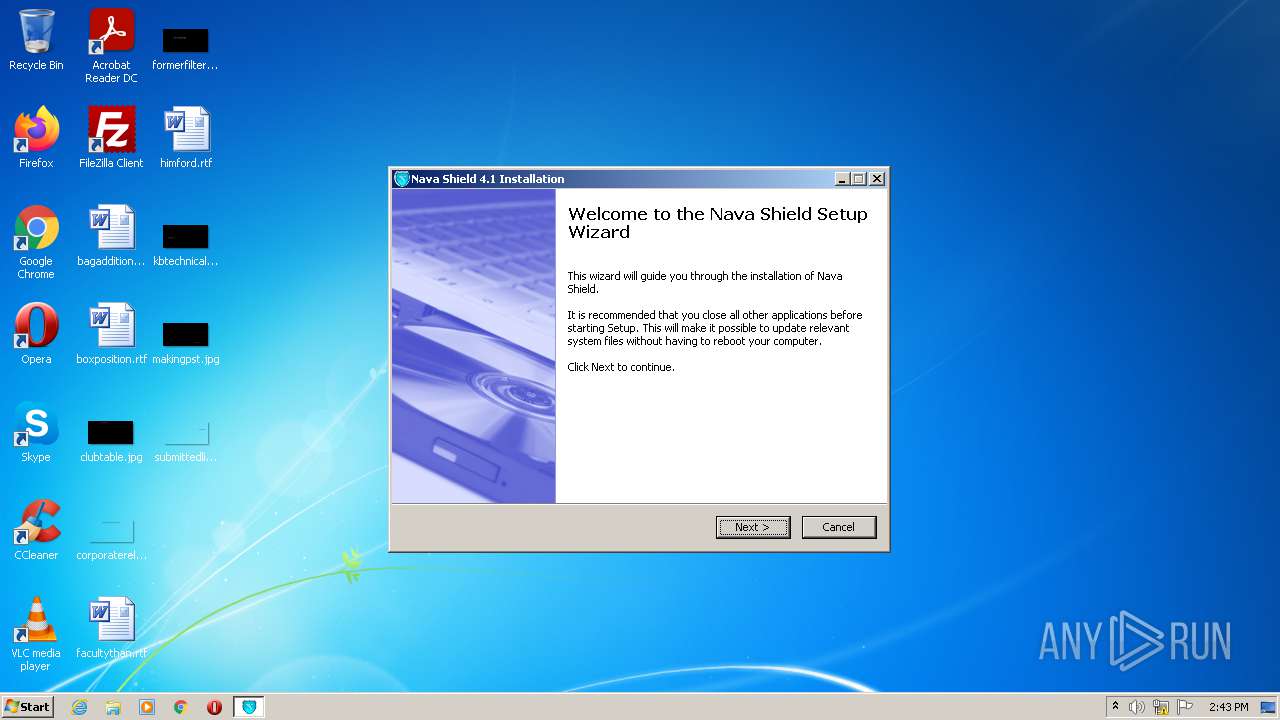
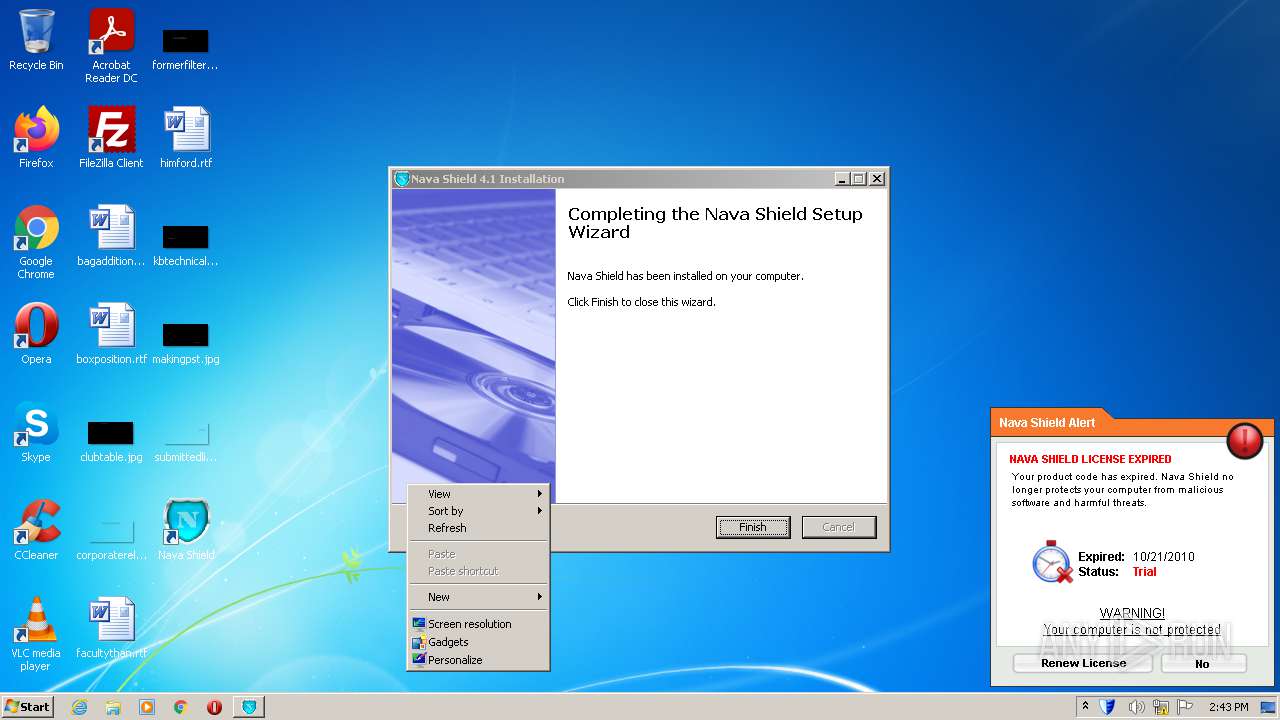
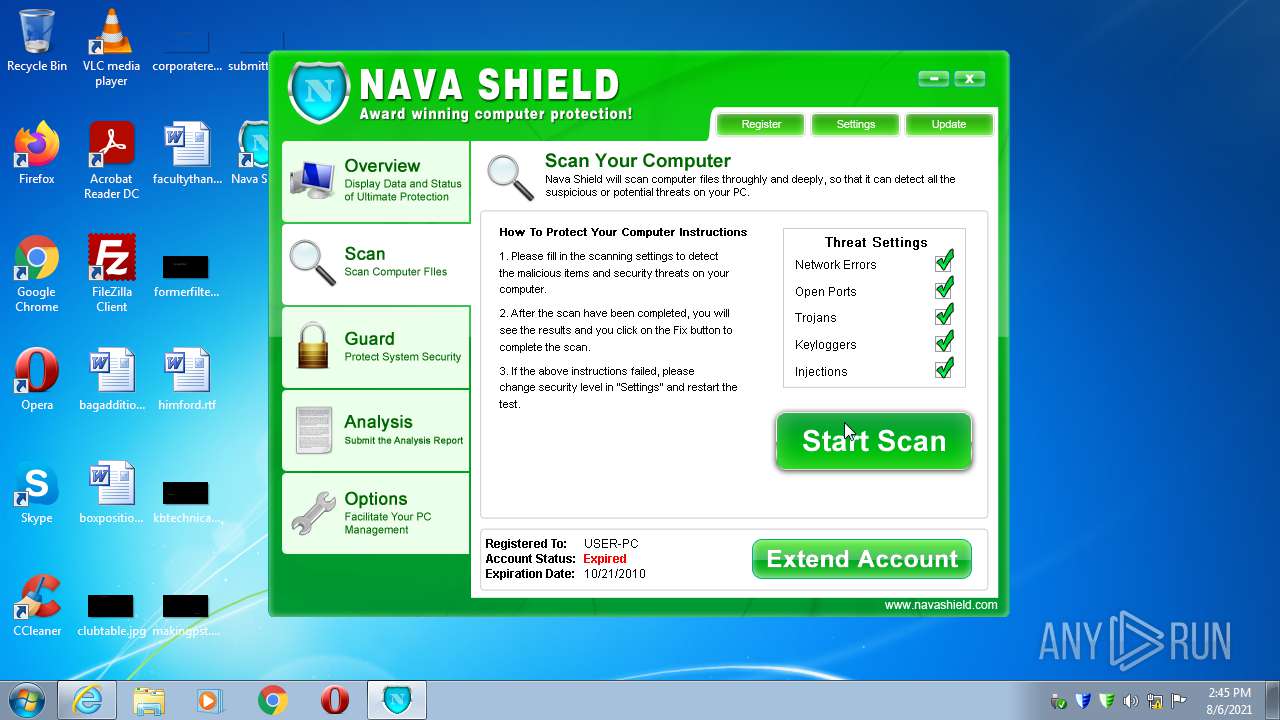
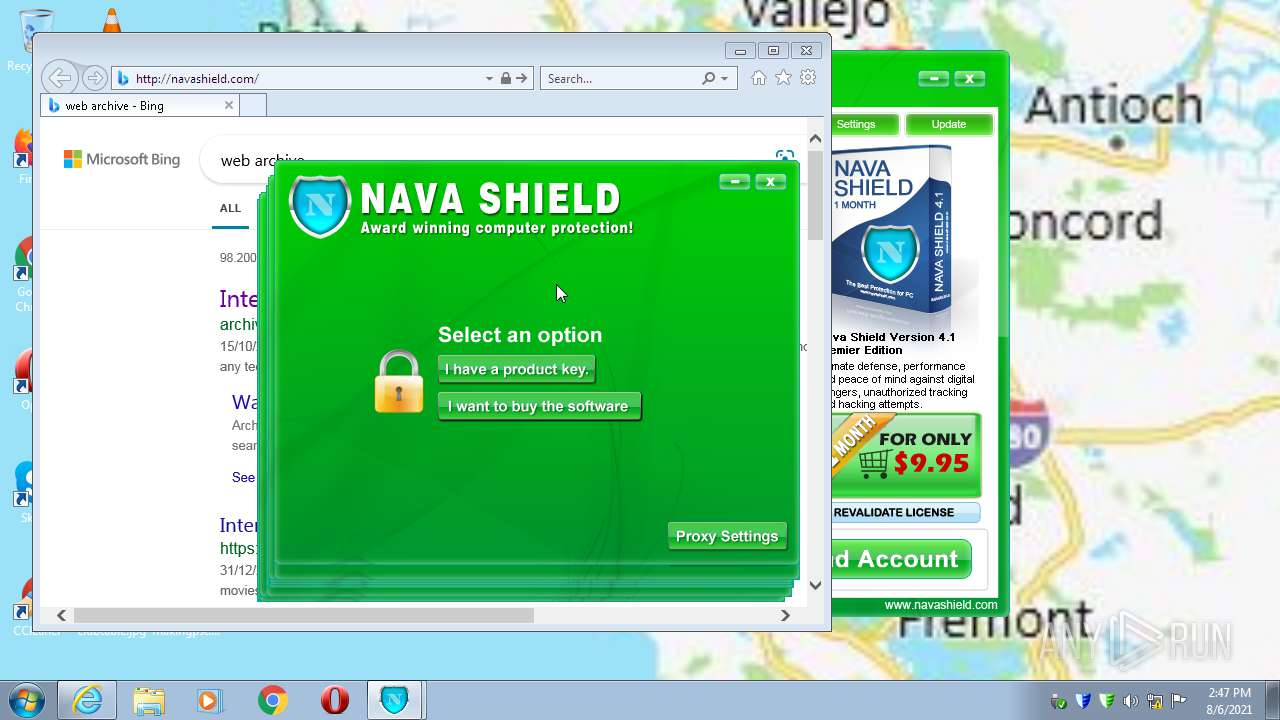
| File name: | Endermanch@NavaShield.exe |
| Full analysis: | https://app.any.run/tasks/09f2907a-6544-483c-84a4-feda7b18bc4b |
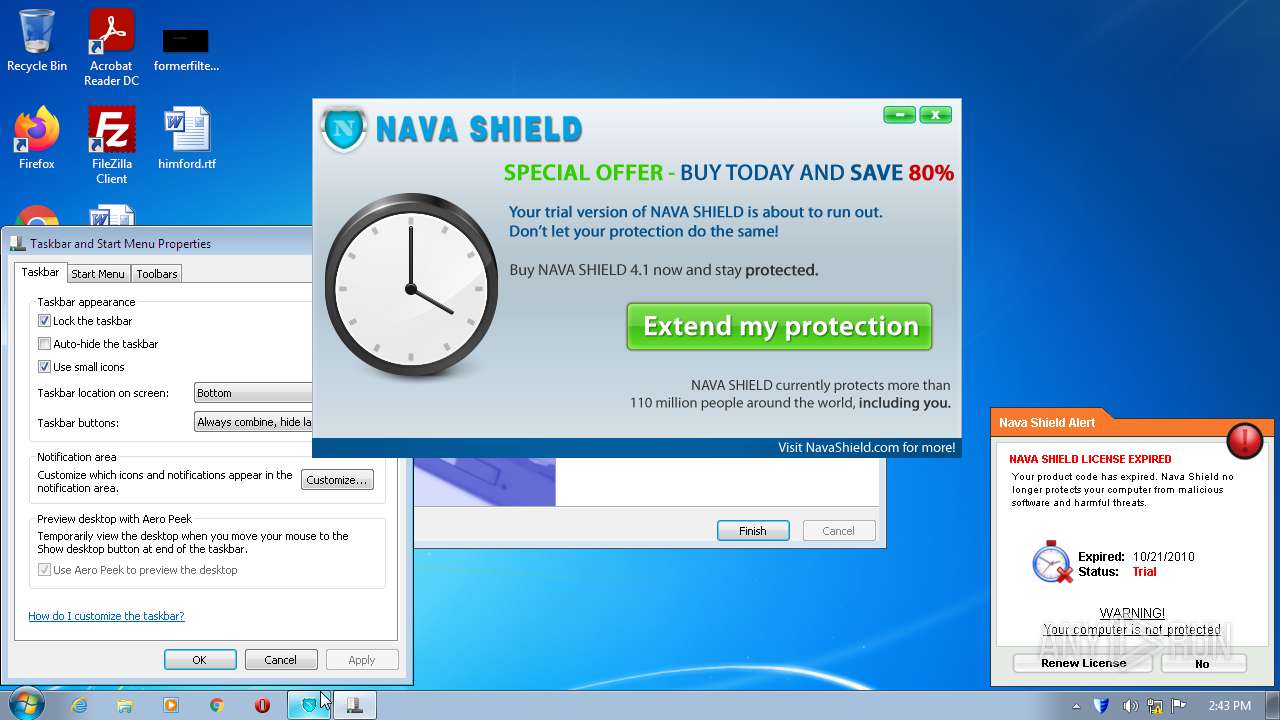
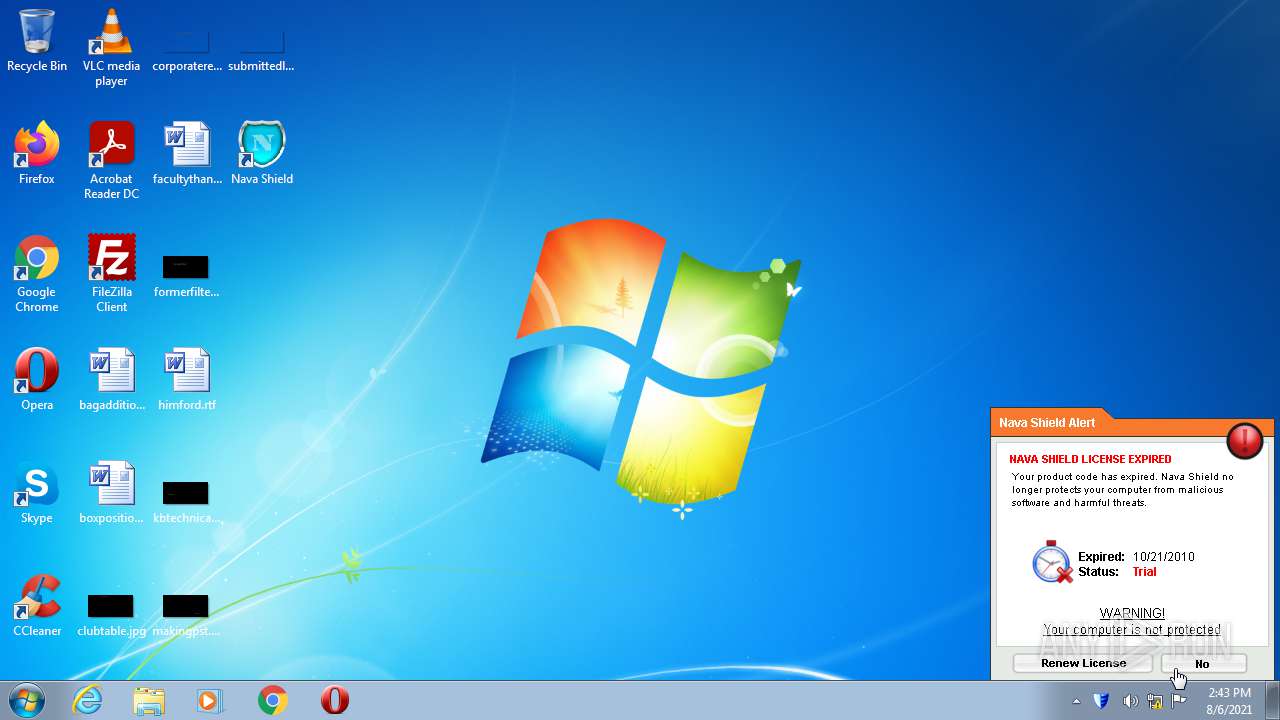
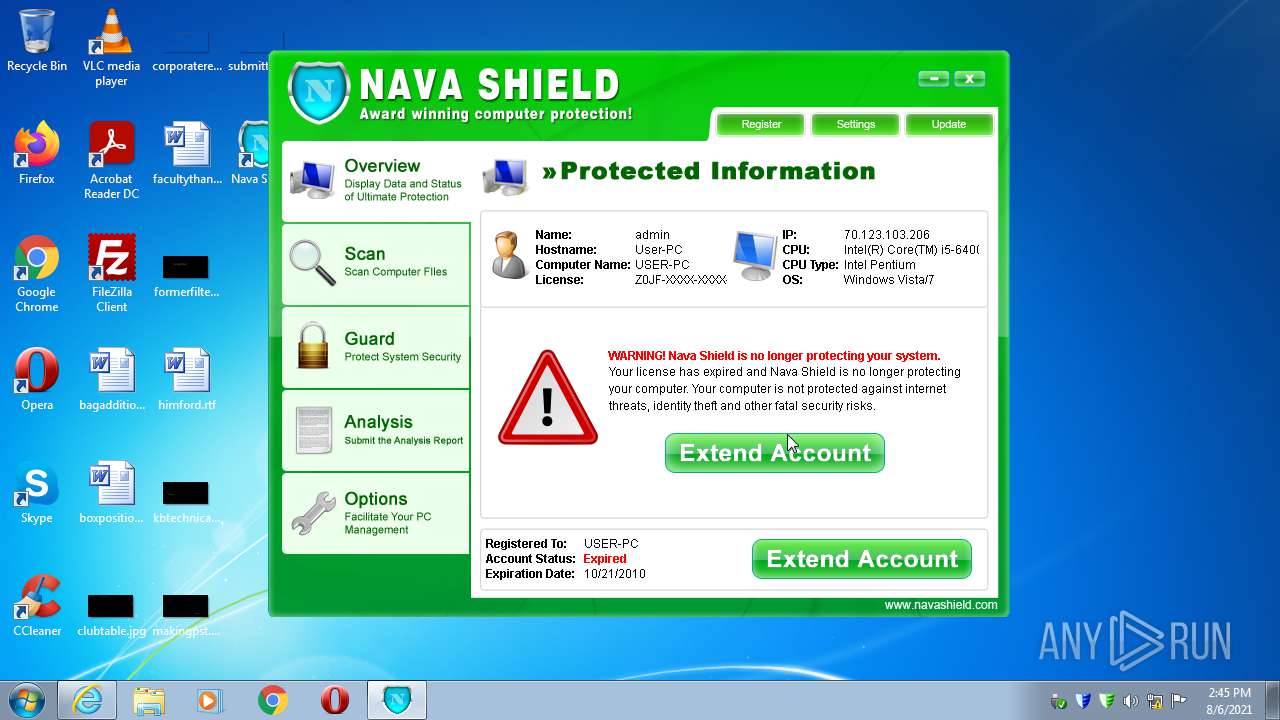
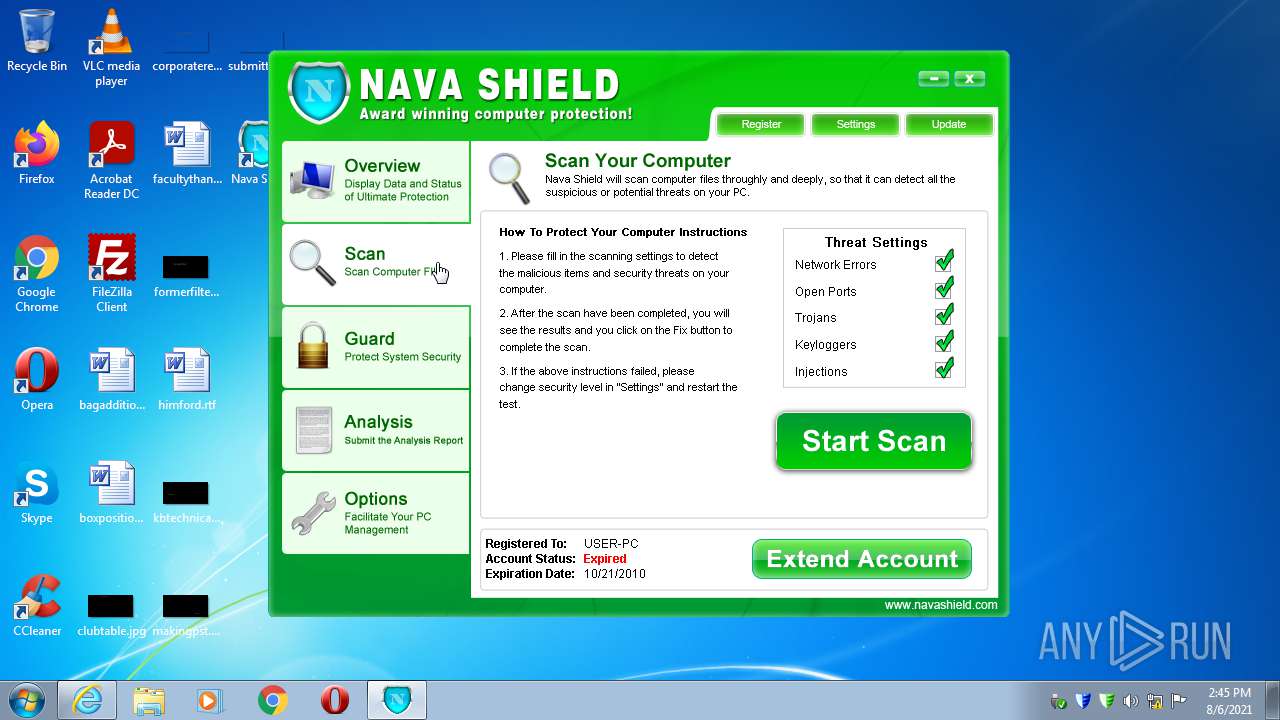
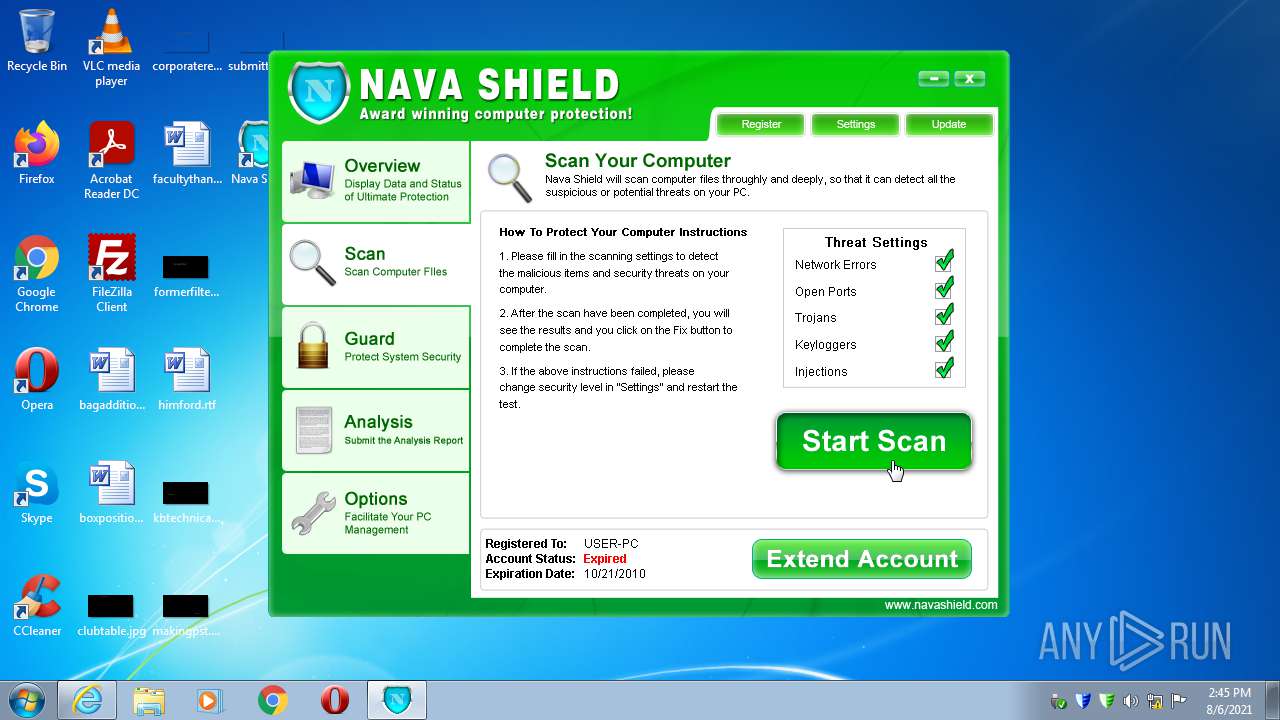
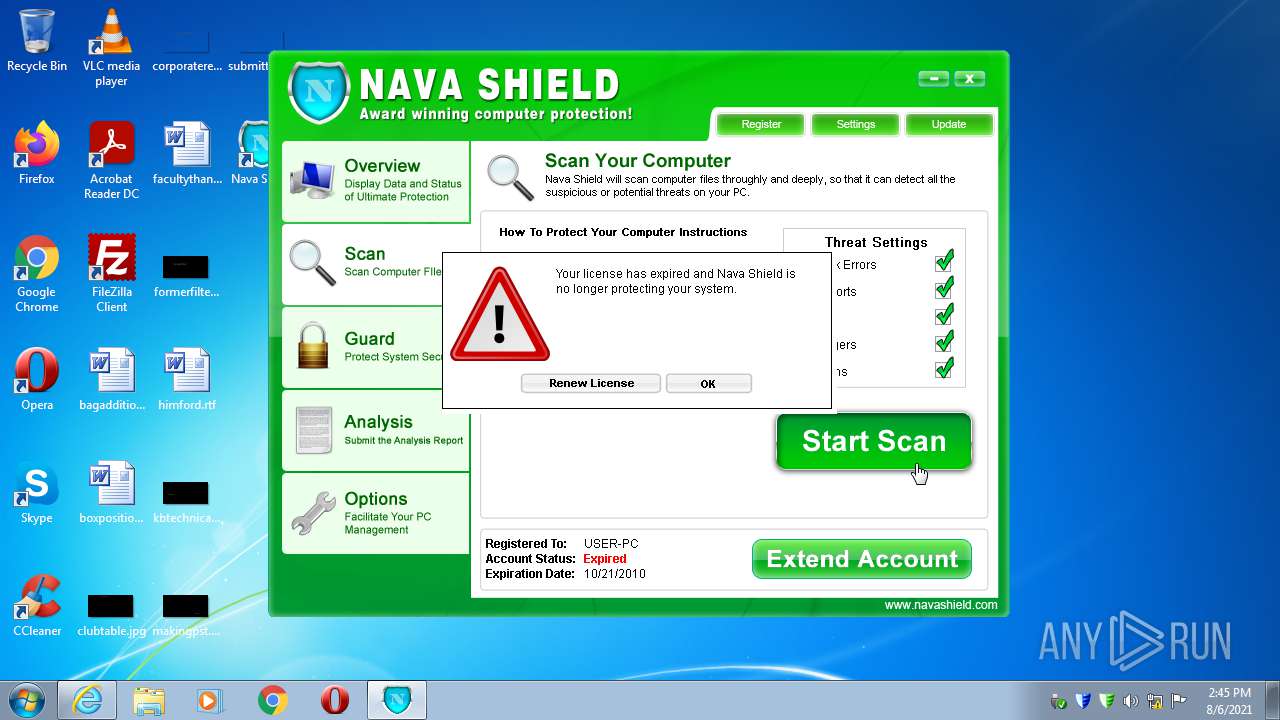
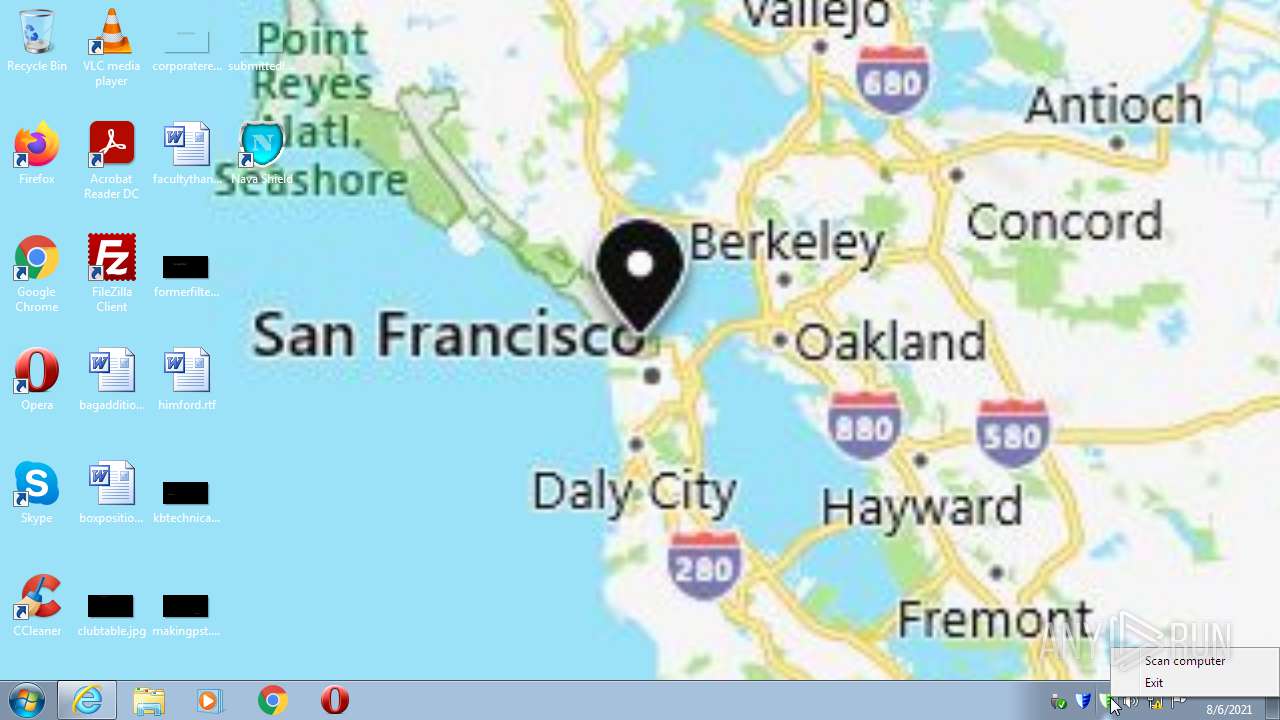
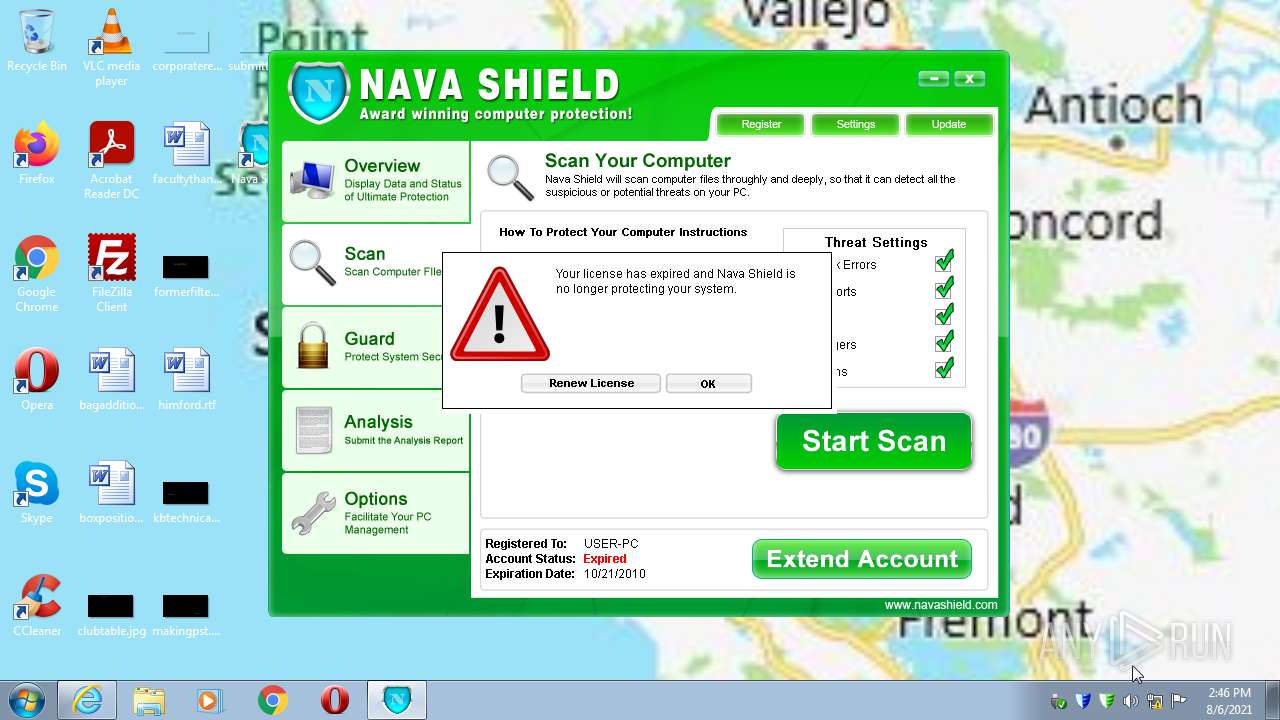
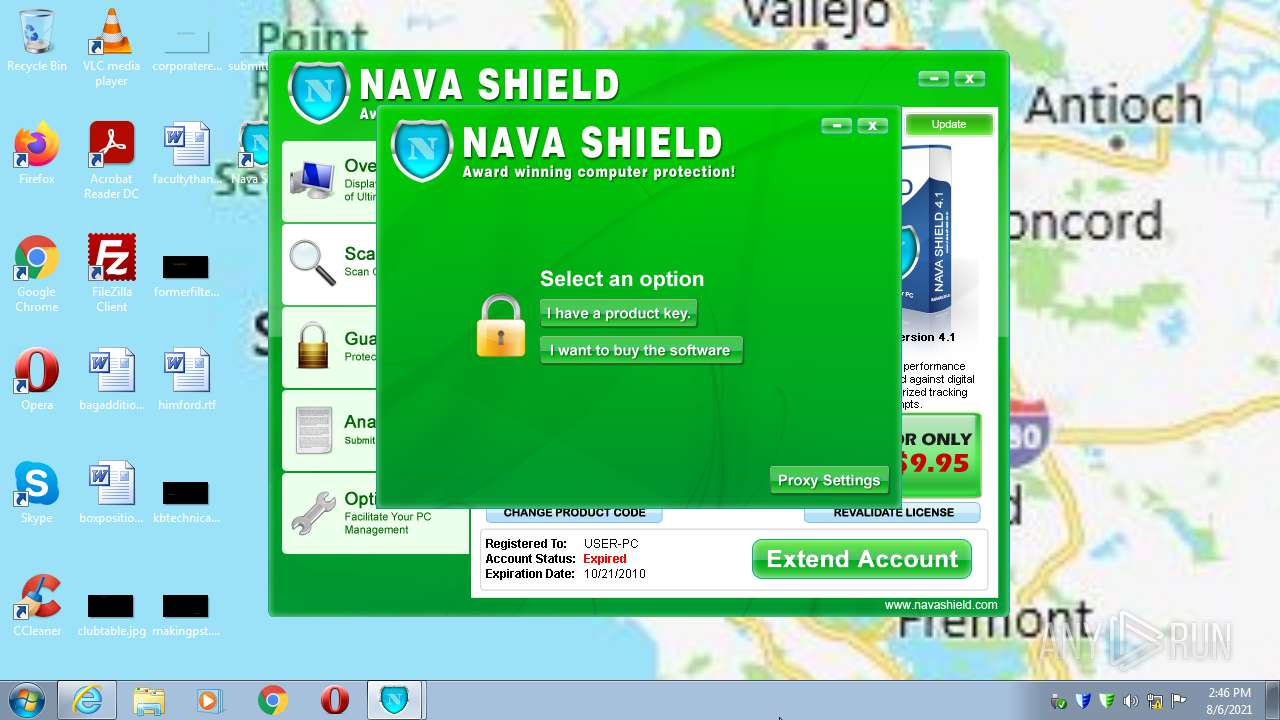
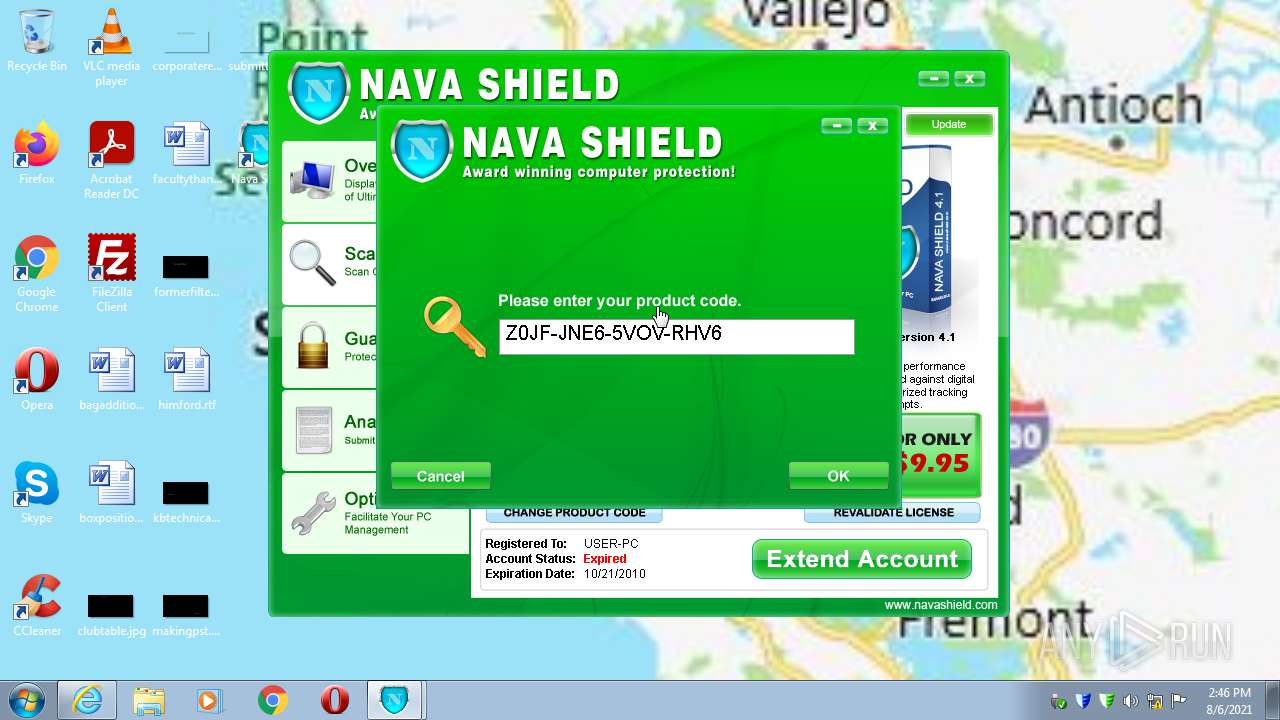
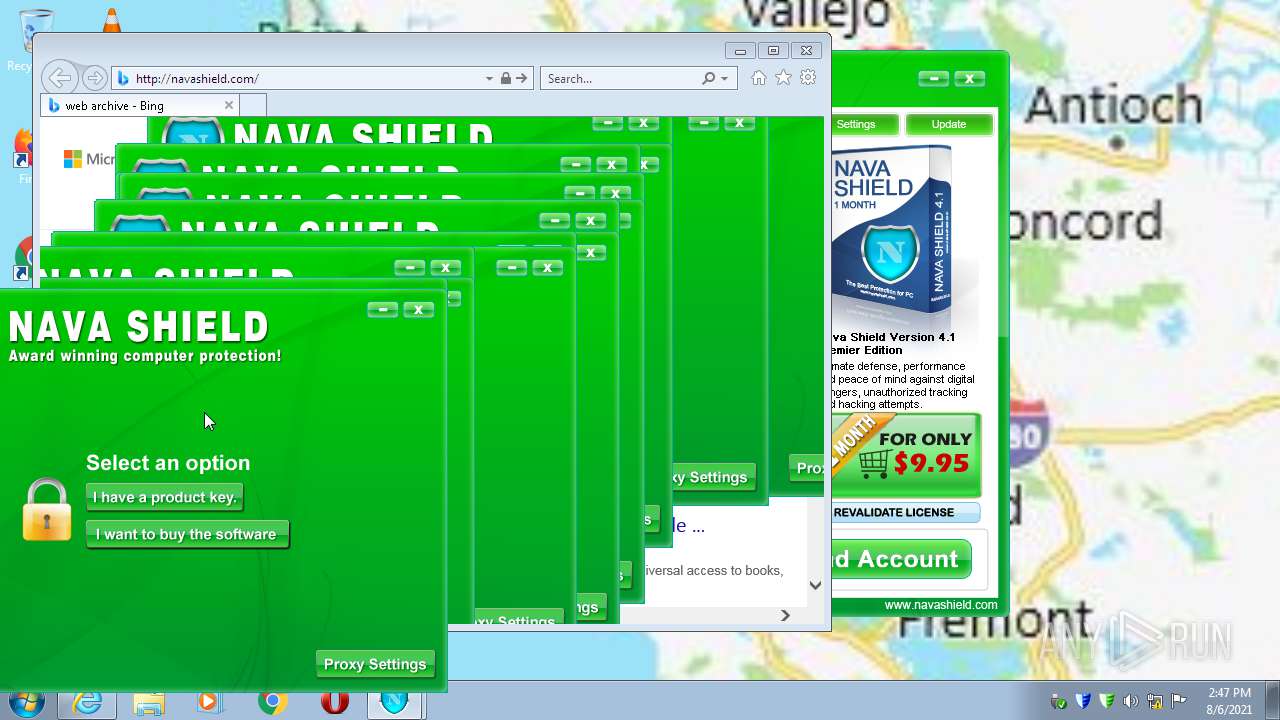
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2021, 13:42:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1F13396FA59D38EBE76CCC587CCB11BB |
| SHA1: | 867ADB3076C0D335B9BFA64594EF37A7E2C951FF |
| SHA256: | 83ECB875F87150A88F4C3D496EB3CB5388CD8BAFDFF4879884ECECDBD1896E1D |
| SSDEEP: | 196608:CtbTP1ErBwMQjd1YTHdmpCP2PVgP/acIE/xQ0zyZejVk+YzbRdTZ:C1E1+dYx6OP9hdyZwV4zd |
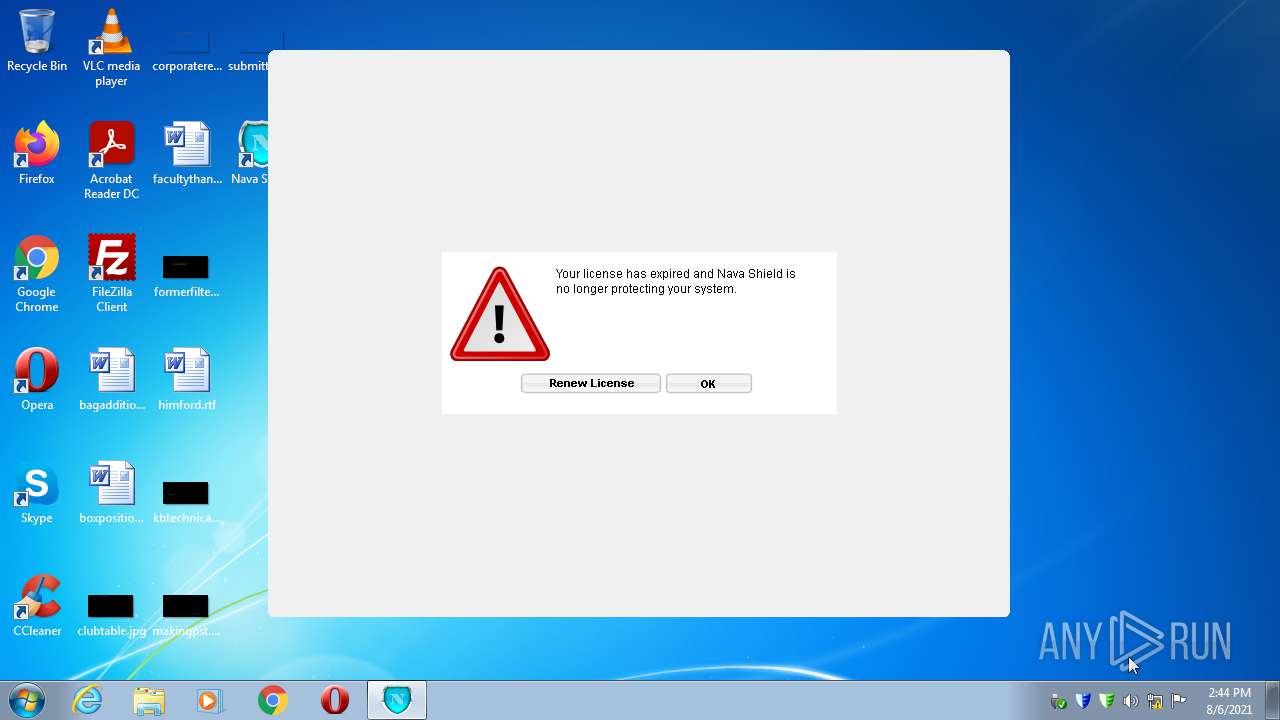
MALICIOUS
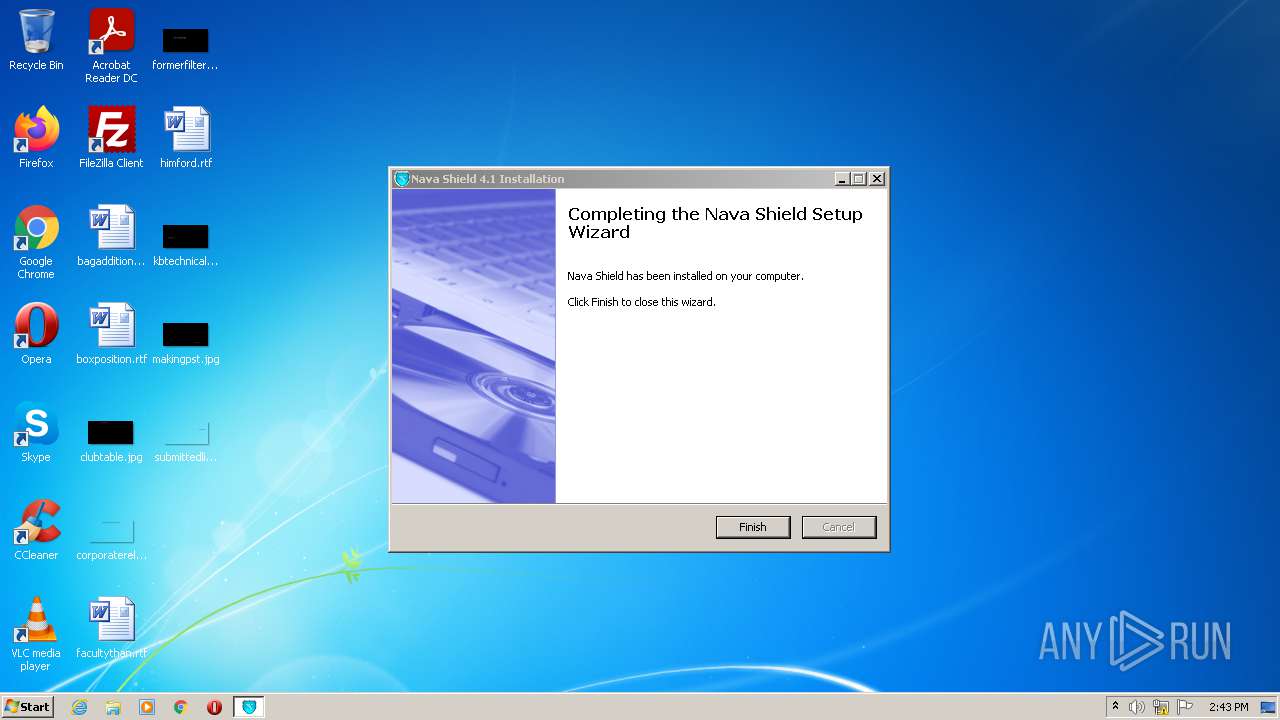
Changes the autorun value in the registry
- Endermanch@NavaShield.exe (PID: 3072)
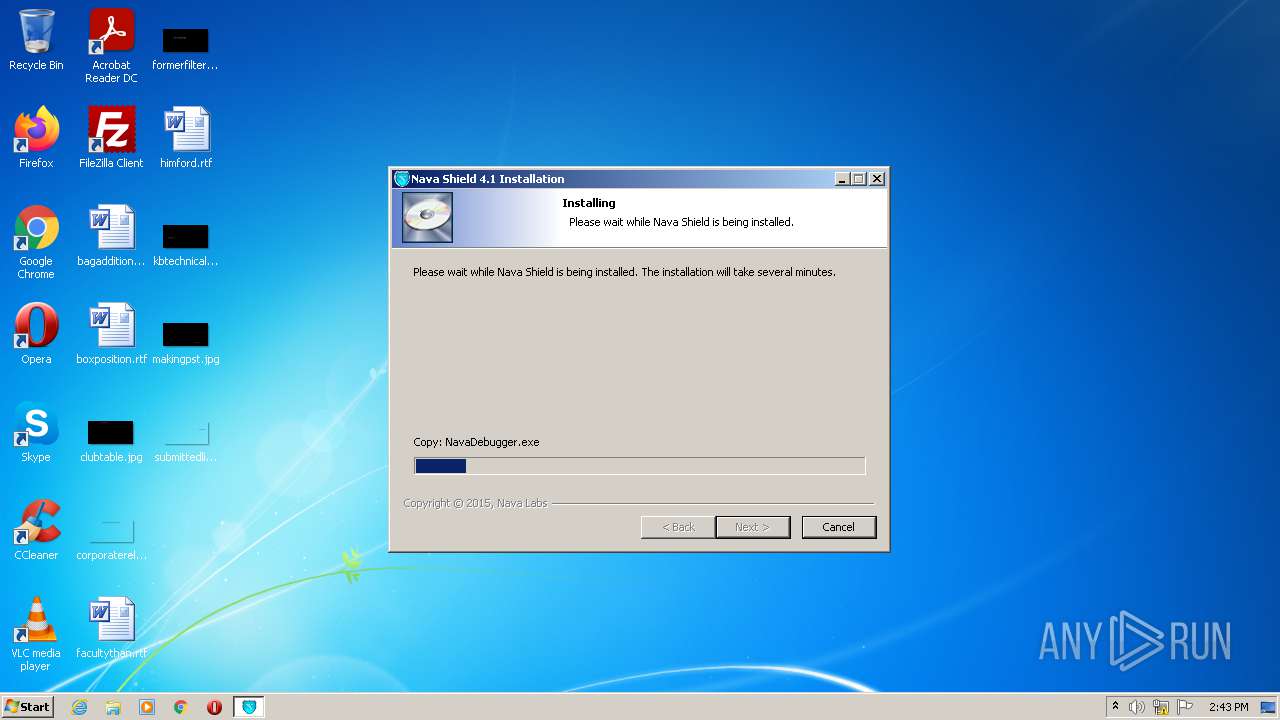
Application was dropped or rewritten from another process
- NavaShield.exe (PID: 3852)
- NavaBridge.exe (PID: 416)
- NavaDebugger.exe (PID: 3800)
- NavaShield.exe (PID: 3612)
- NavaShield.exe (PID: 520)
- NavaShield.exe (PID: 1140)
Loads dropped or rewritten executable
- NavaShield.exe (PID: 3852)
- NavaBridge.exe (PID: 416)
- NavaDebugger.exe (PID: 3800)
- NavaShield.exe (PID: 3612)
- NavaShield.exe (PID: 520)
- NavaShield.exe (PID: 1140)
SUSPICIOUS
Reads the computer name
- Endermanch@NavaShield.exe (PID: 3072)
- NavaShield.exe (PID: 3852)
- NavaBridge.exe (PID: 416)
- NavaDebugger.exe (PID: 3800)
Executable content was dropped or overwritten
- Endermanch@NavaShield.exe (PID: 3072)
Checks supported languages
- Endermanch@NavaShield.exe (PID: 3072)
- NavaShield.exe (PID: 3852)
- NavaBridge.exe (PID: 416)
- NavaDebugger.exe (PID: 3800)
- NavaShield.exe (PID: 3612)
- NavaShield.exe (PID: 520)
- NavaShield.exe (PID: 1140)
Creates files in the user directory
- Endermanch@NavaShield.exe (PID: 3072)
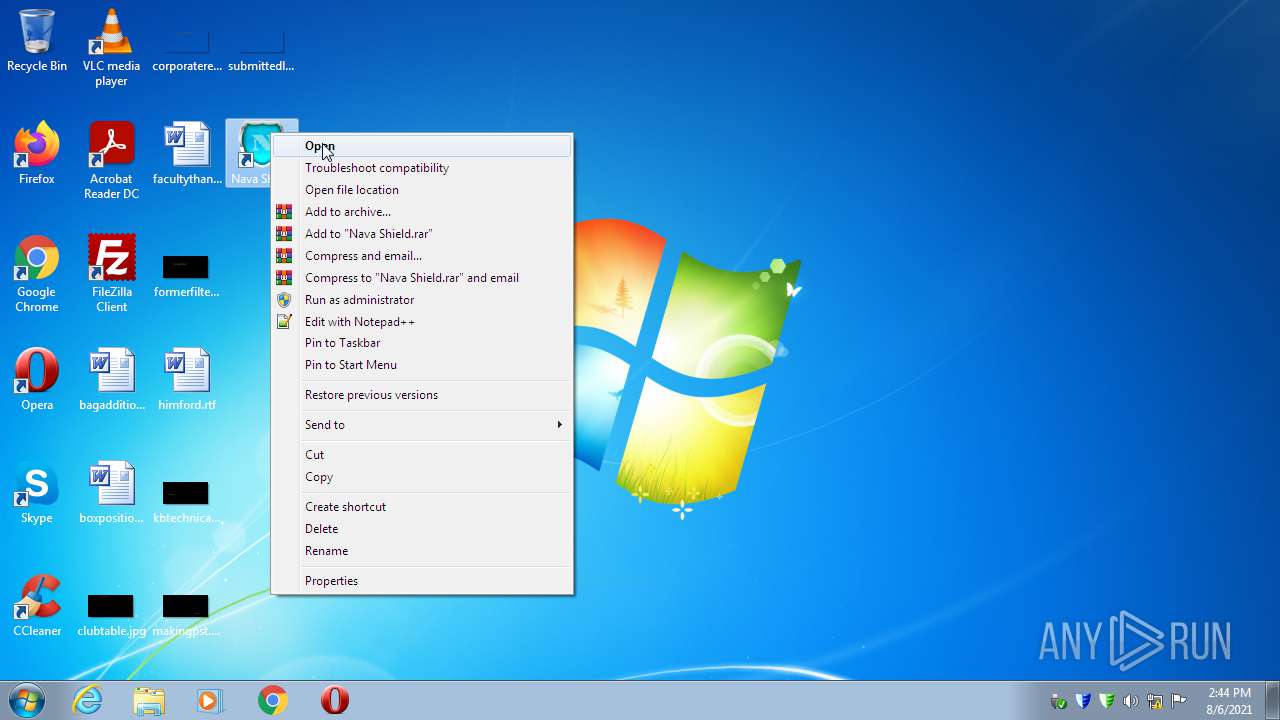
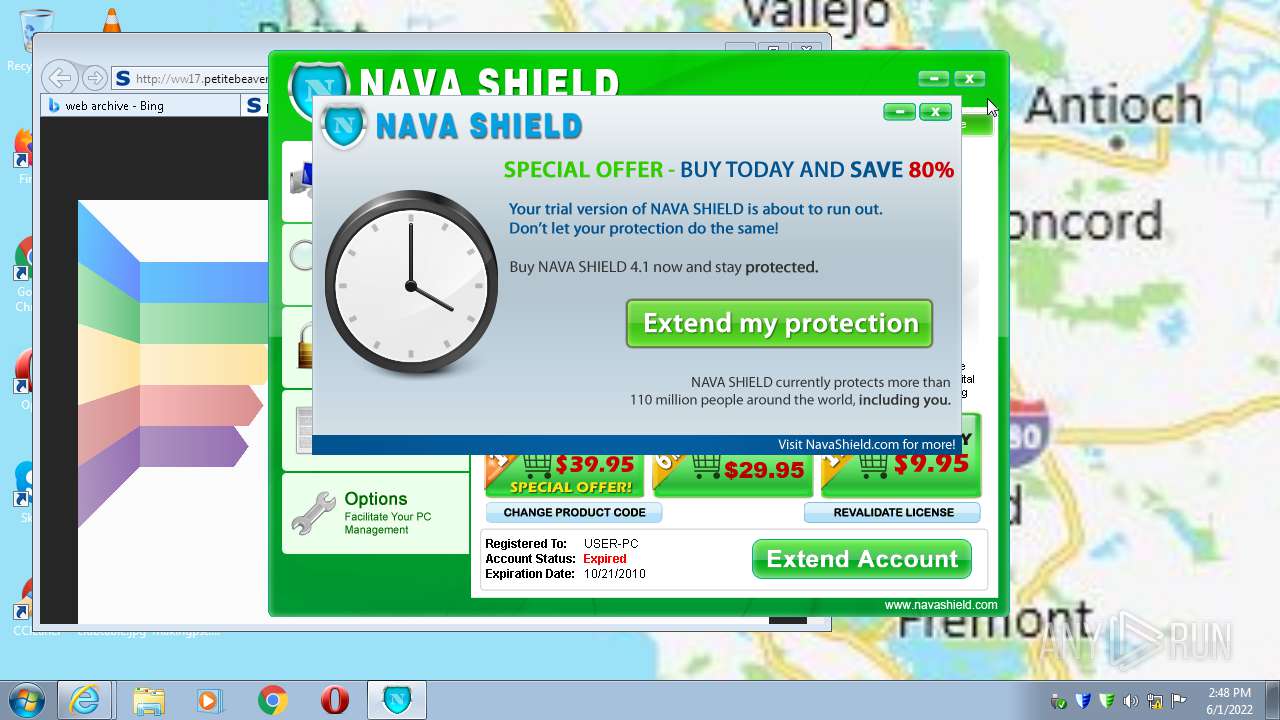
Creates a software uninstall entry
- Endermanch@NavaShield.exe (PID: 3072)
Drops a file that was compiled in debug mode
- Endermanch@NavaShield.exe (PID: 3072)
Drops a file with too old compile date
- Endermanch@NavaShield.exe (PID: 3072)
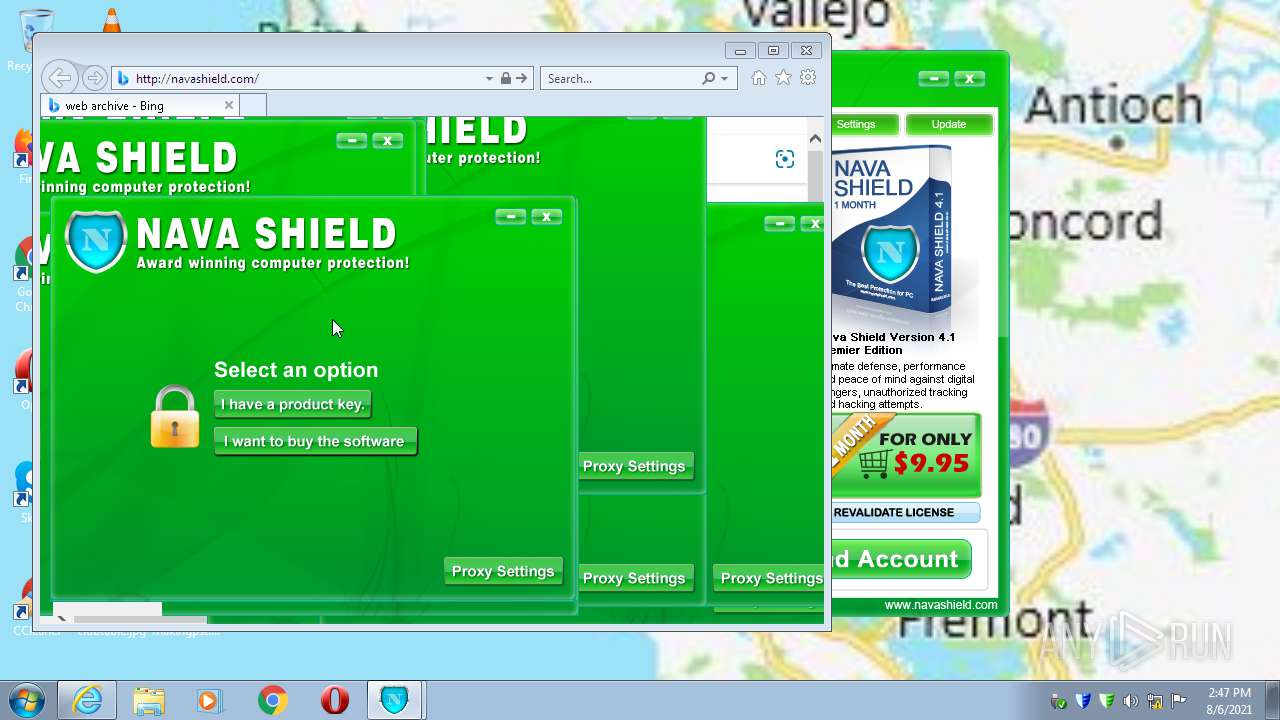
Starts itself from another location
- NavaShield.exe (PID: 3852)
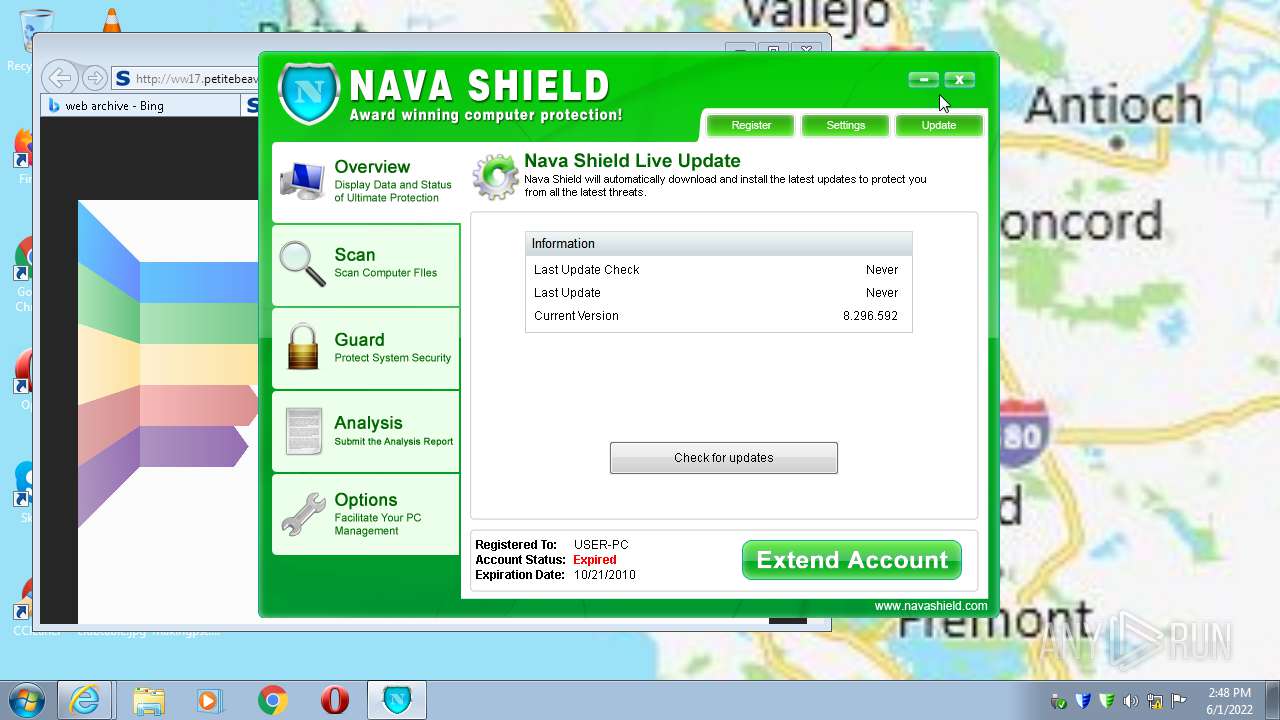
Reads CPU info
- NavaShield.exe (PID: 3852)
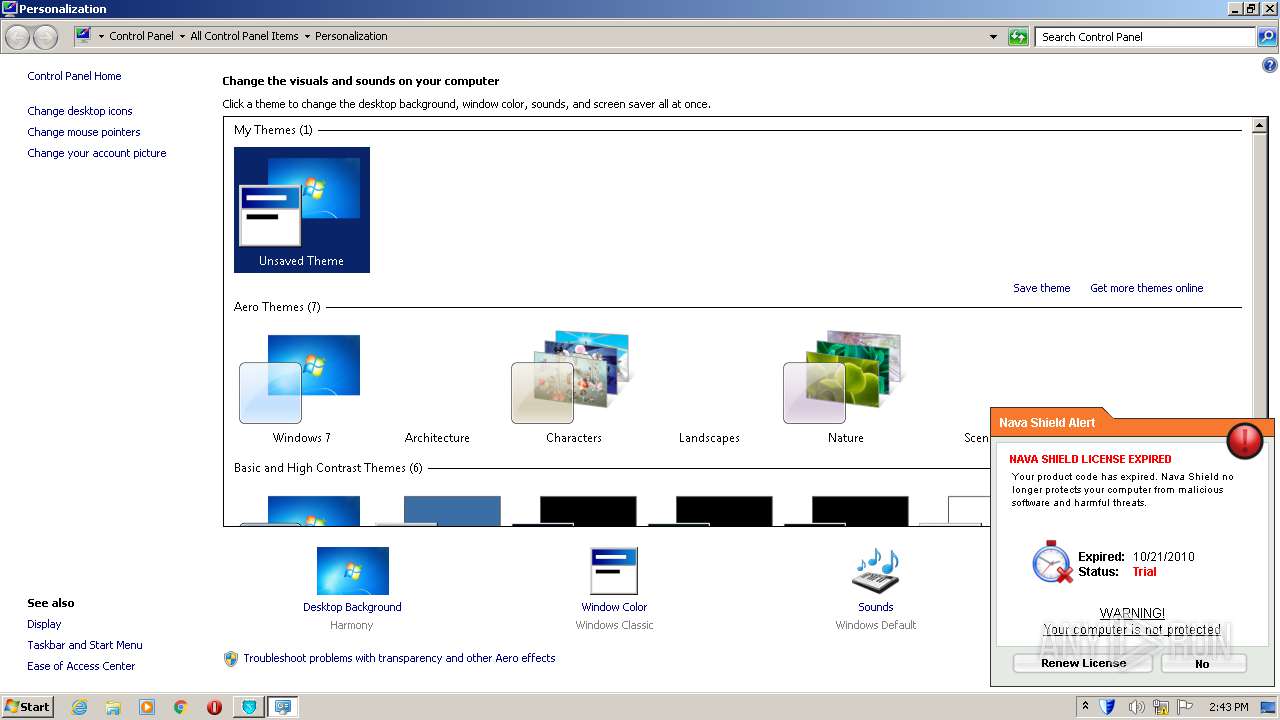
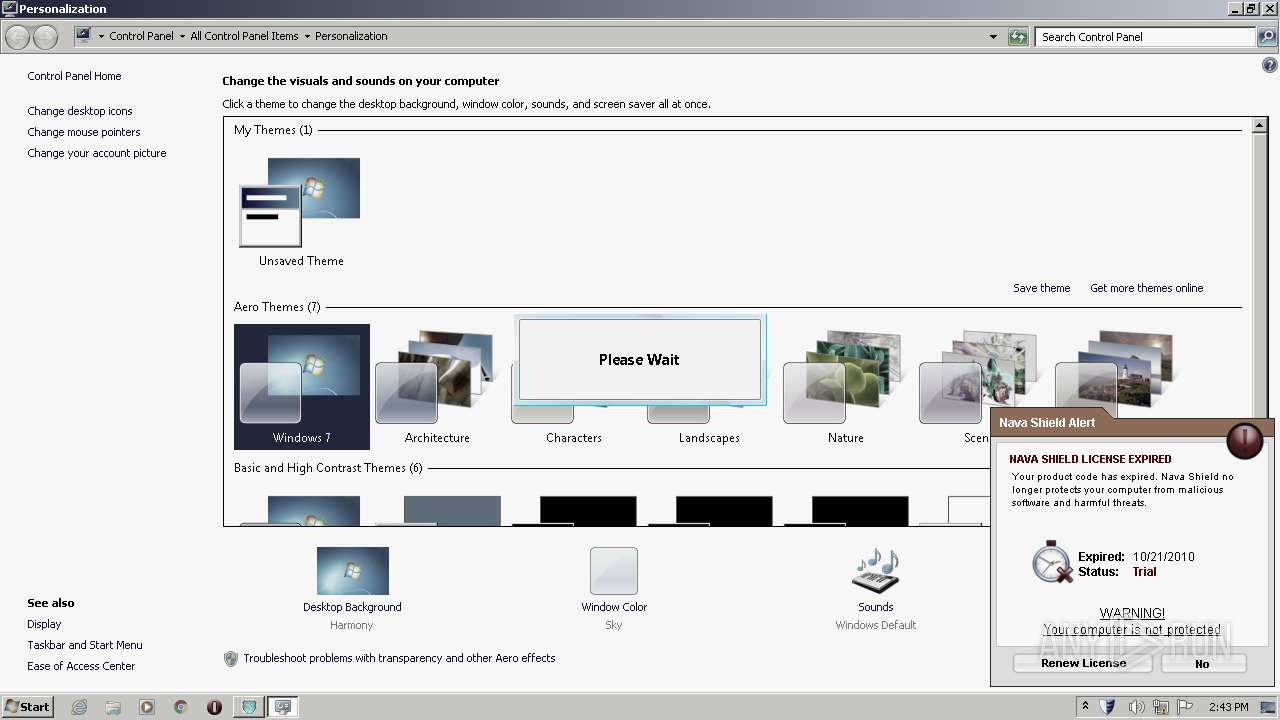
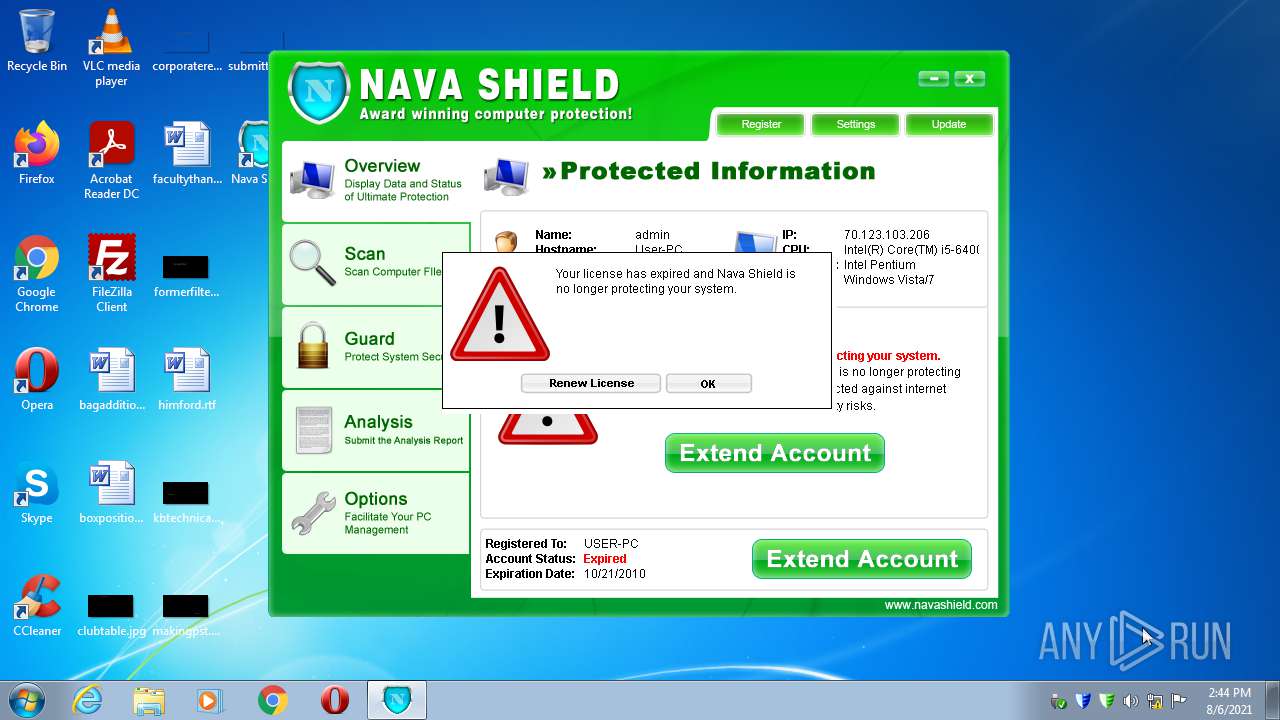
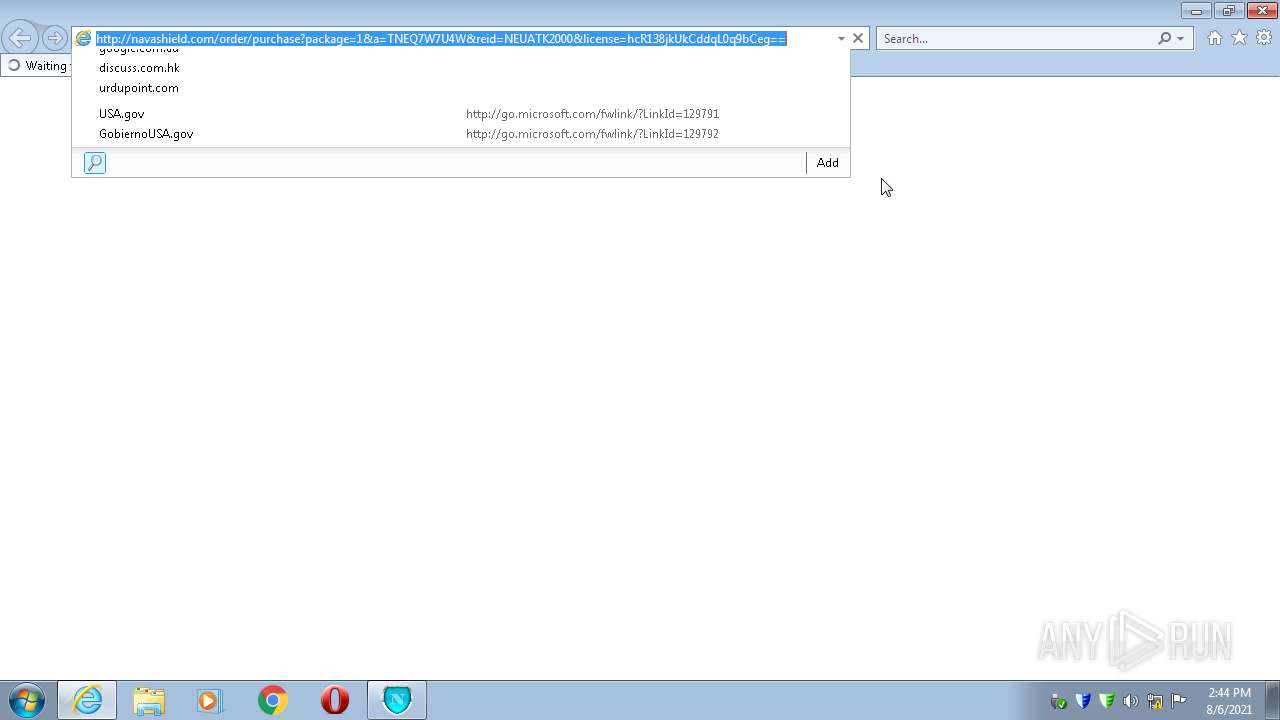
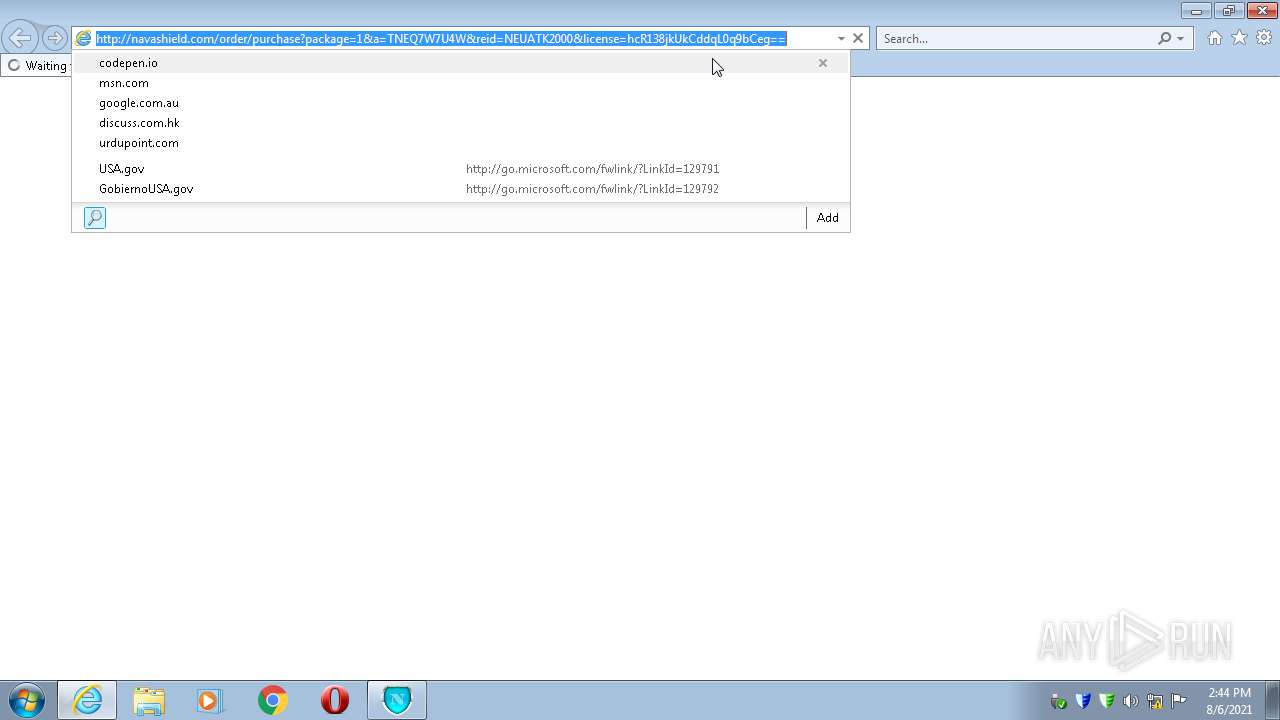
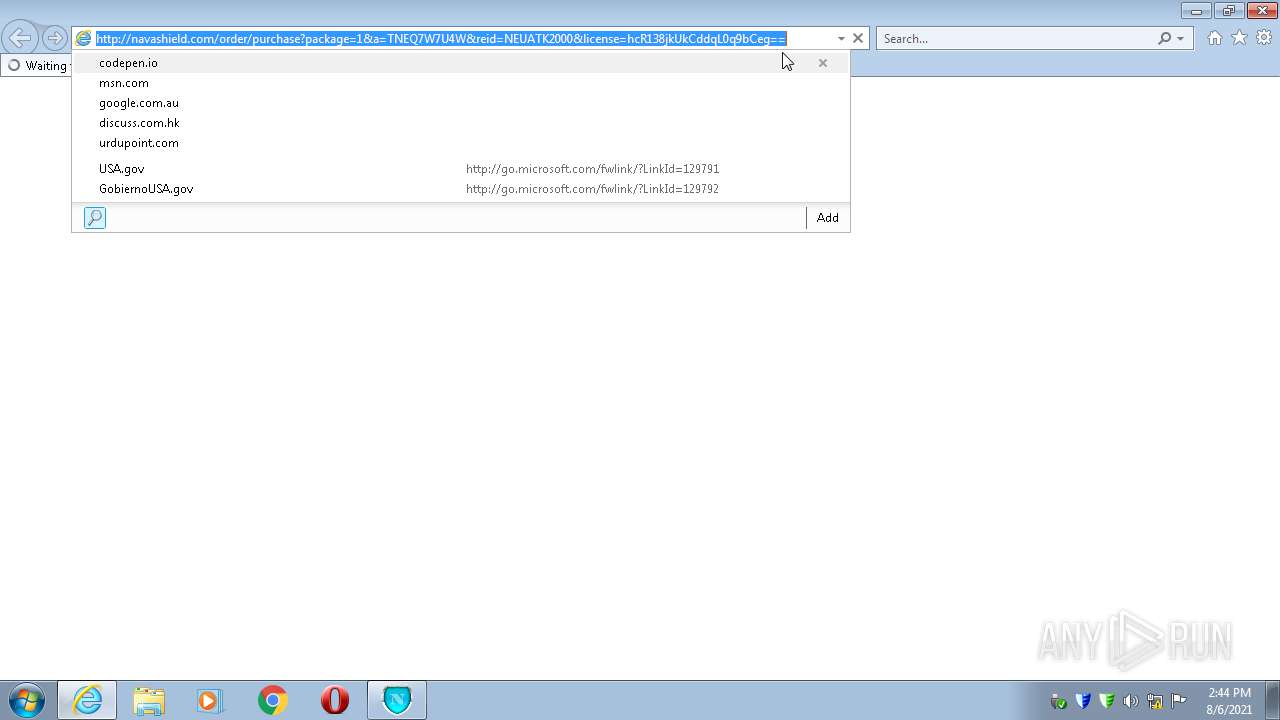
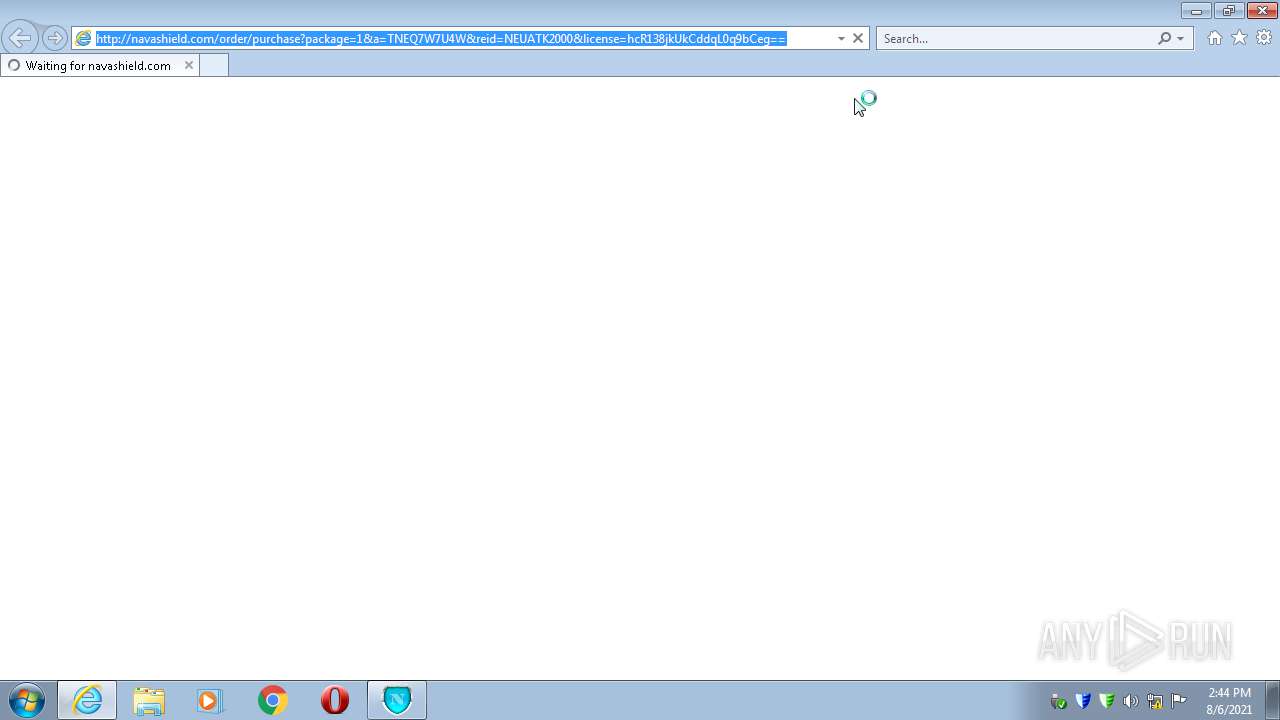
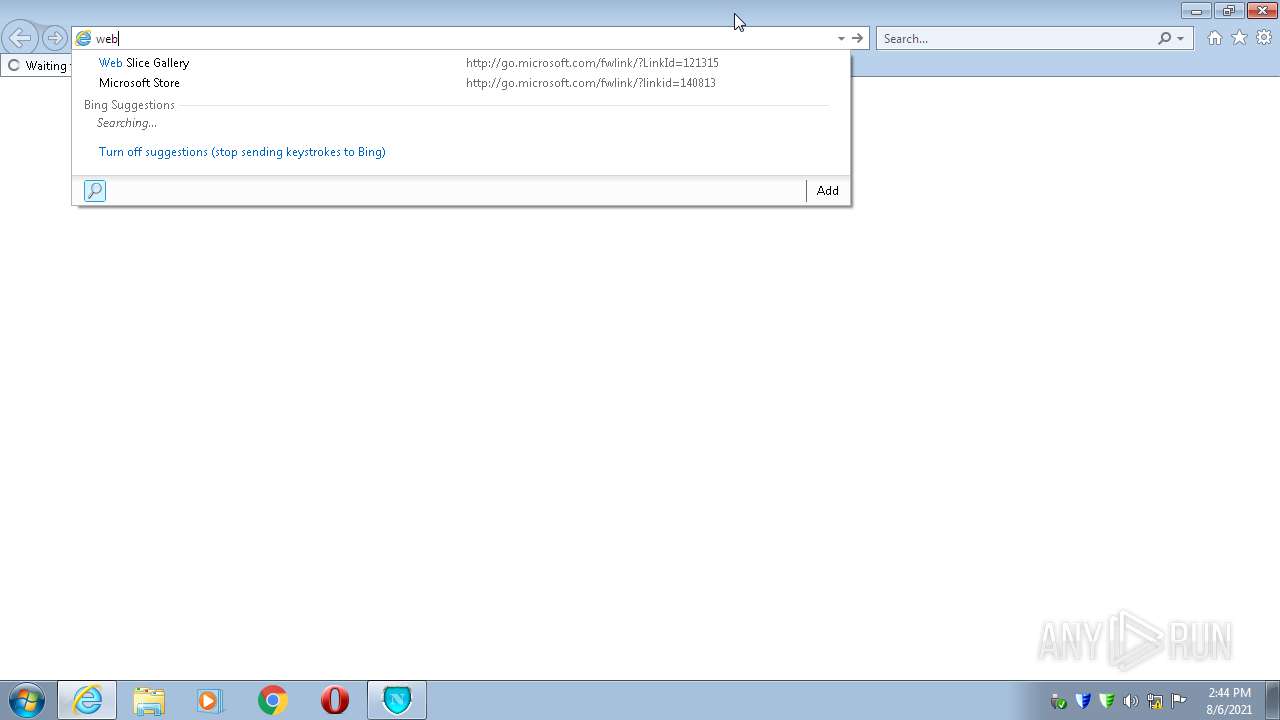
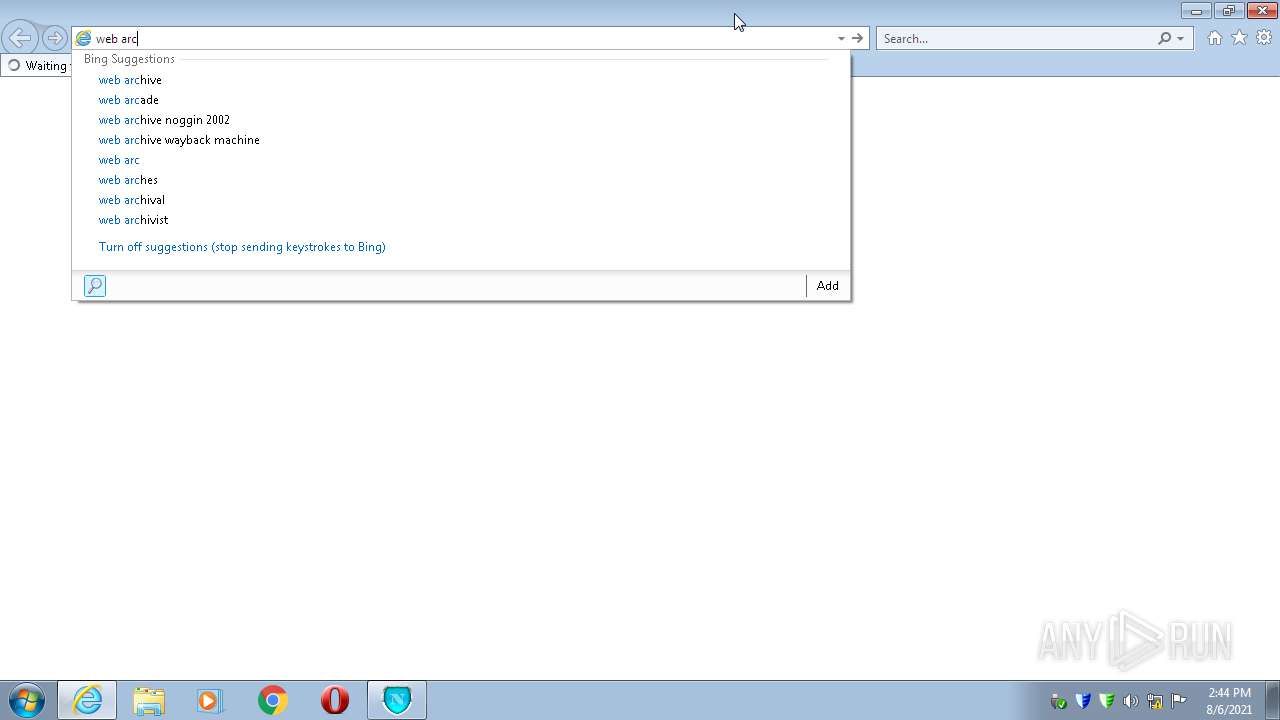
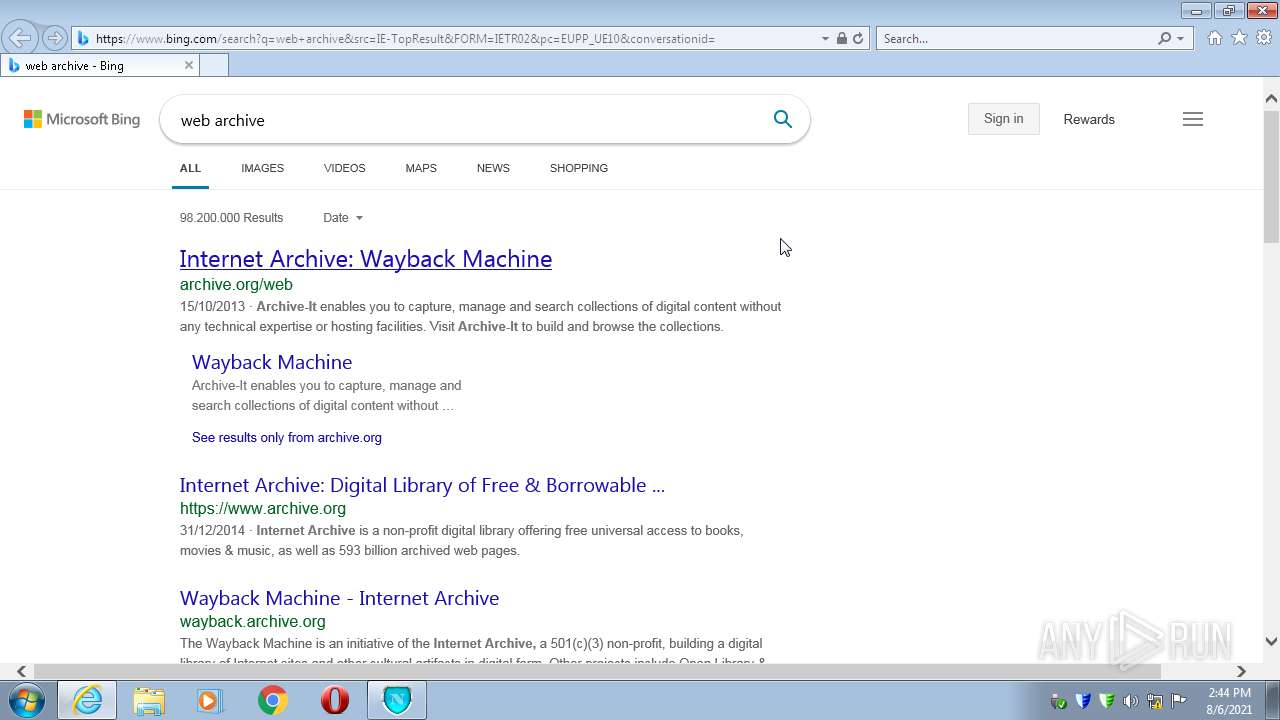
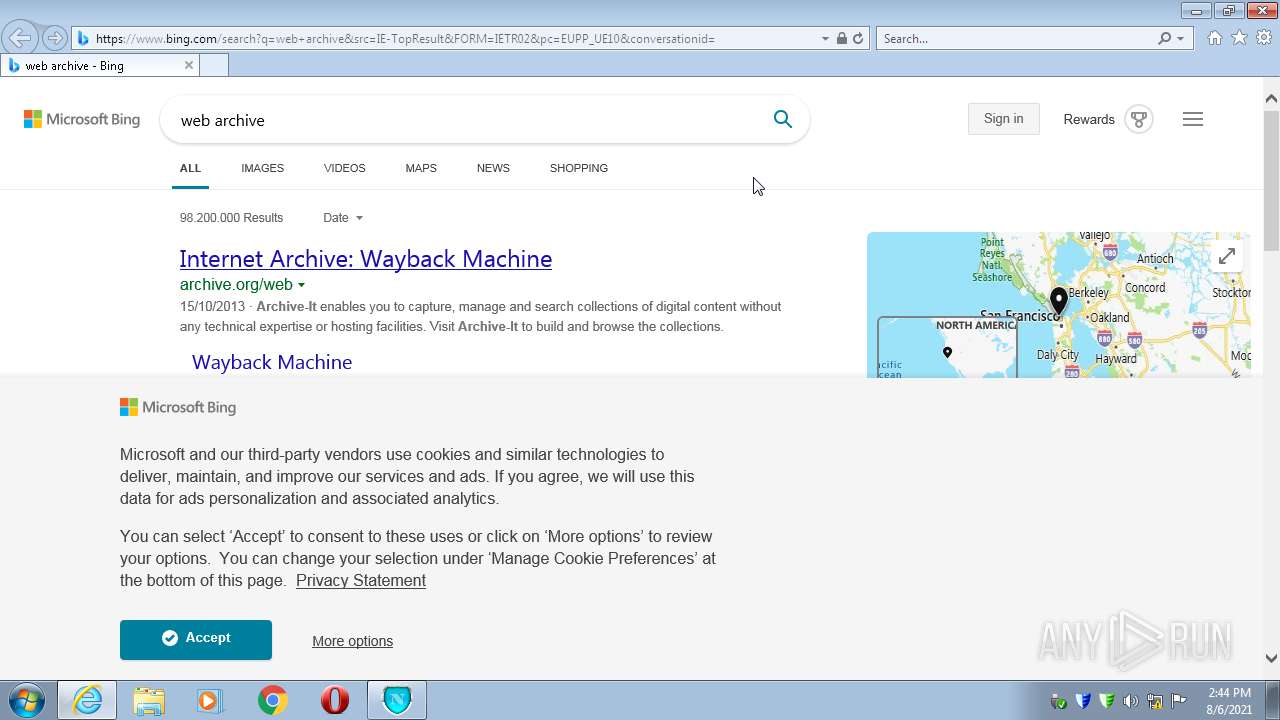
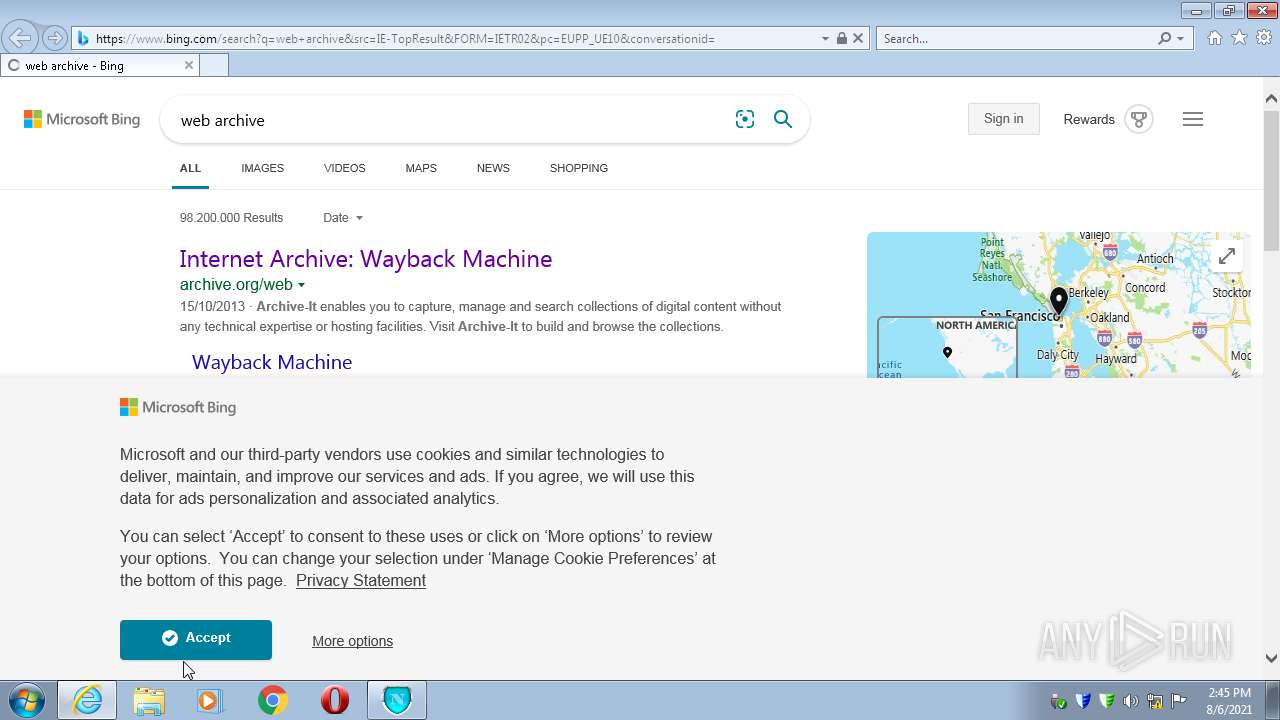
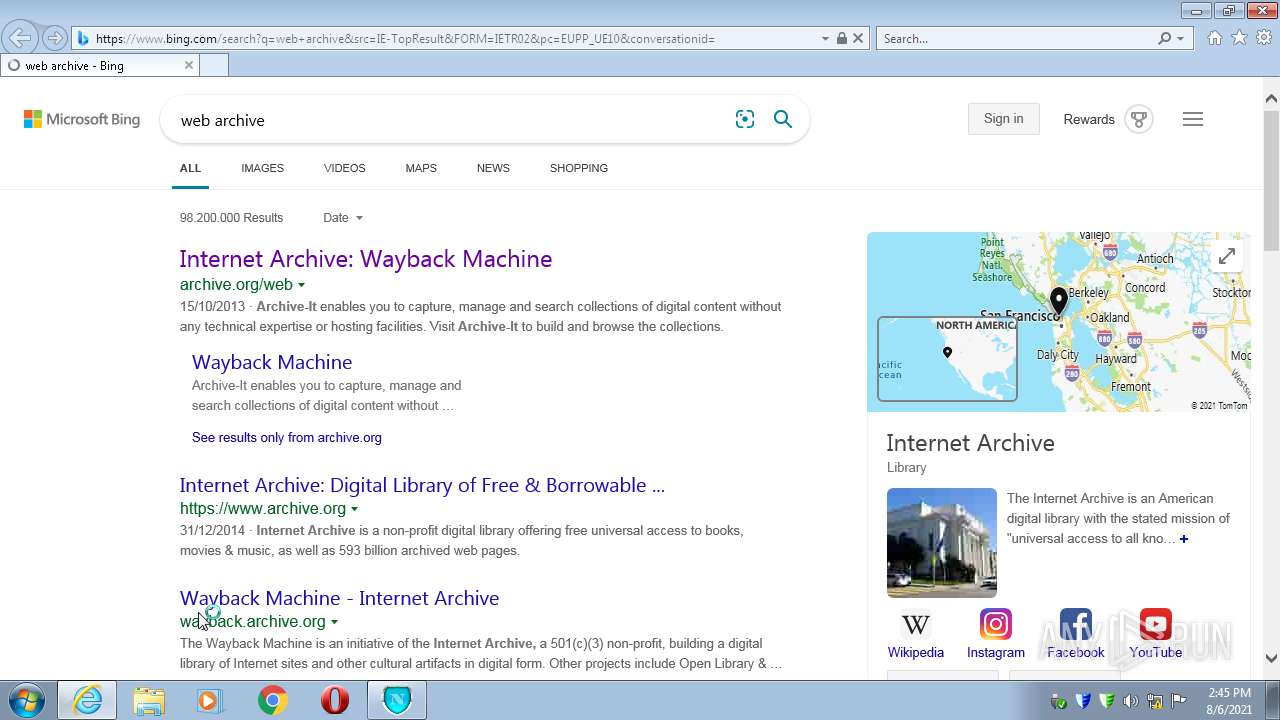
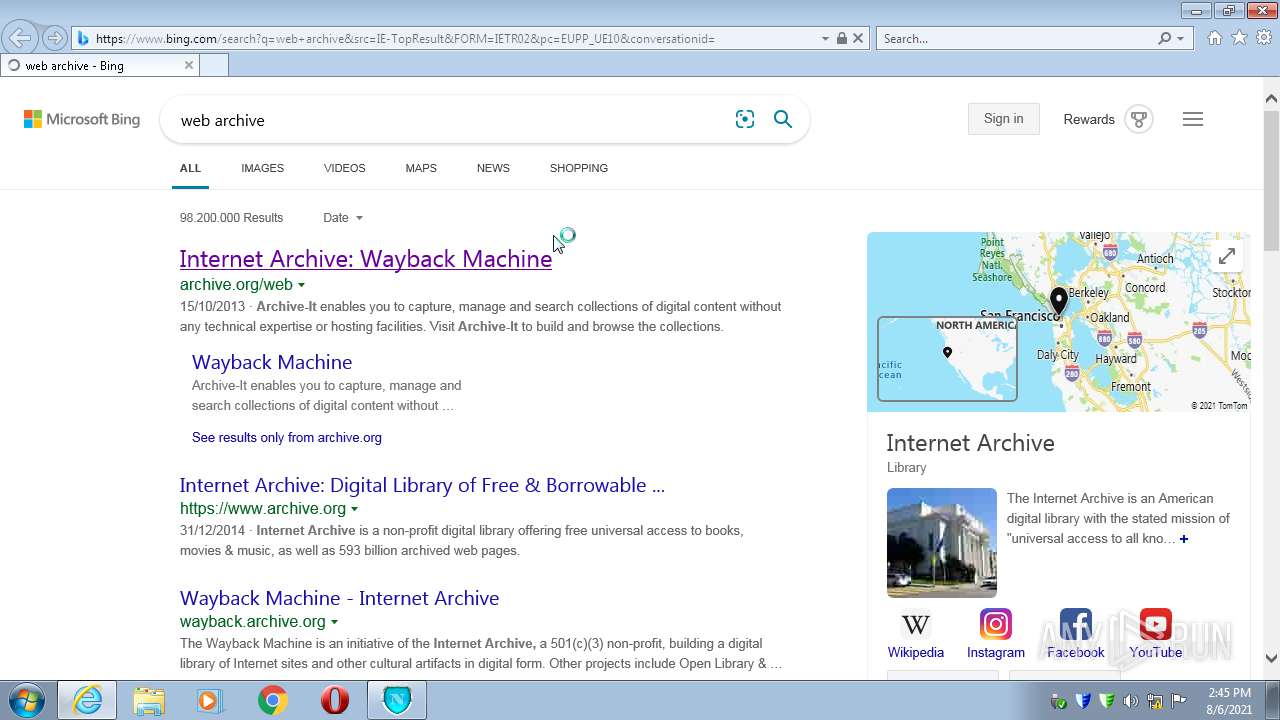
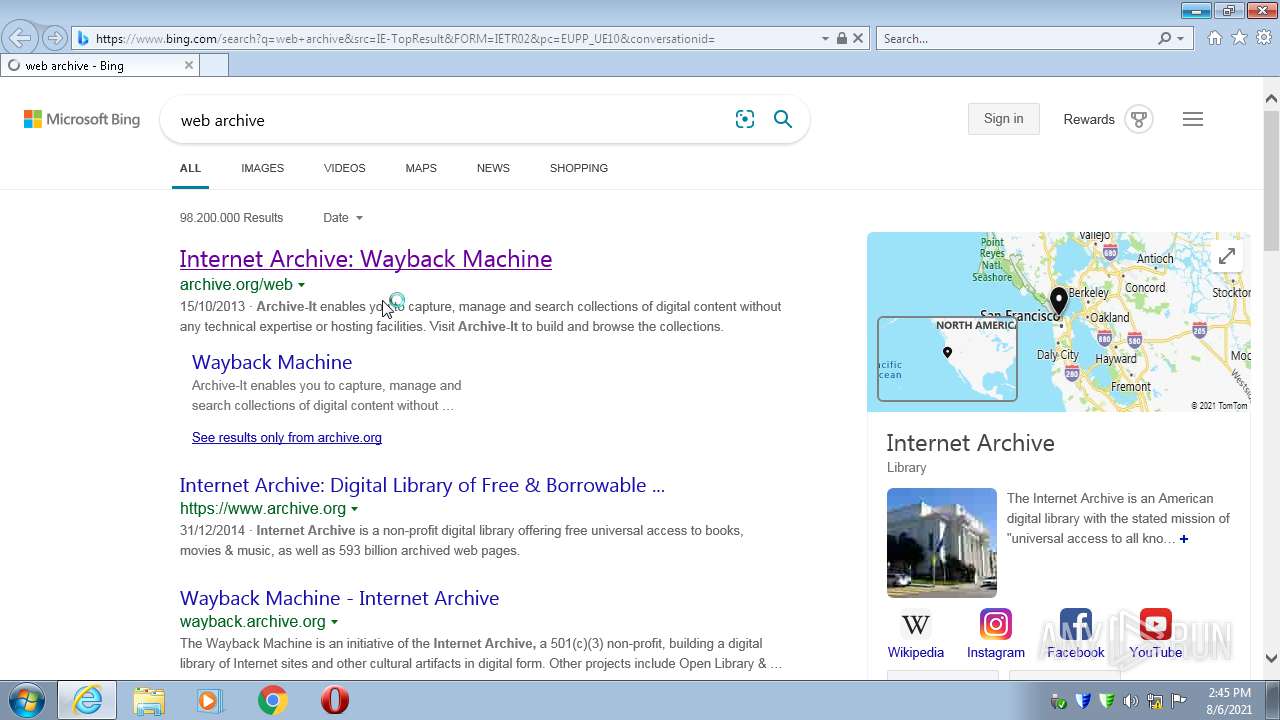
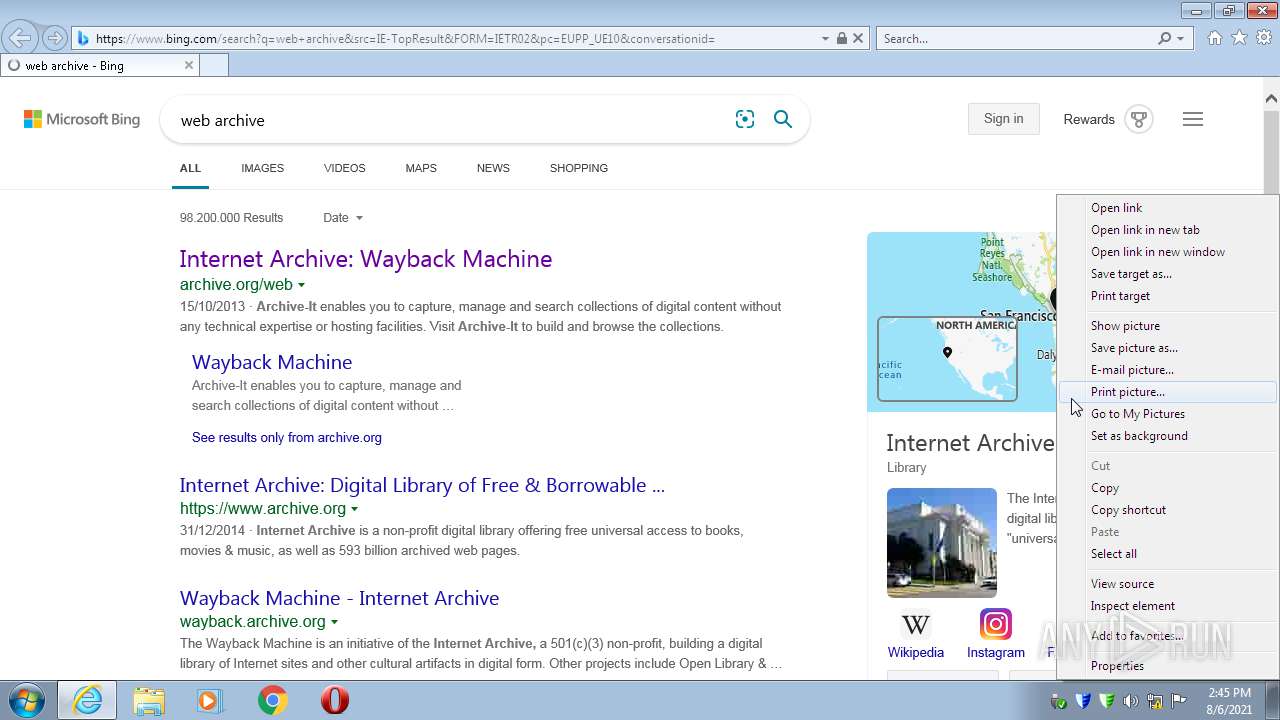
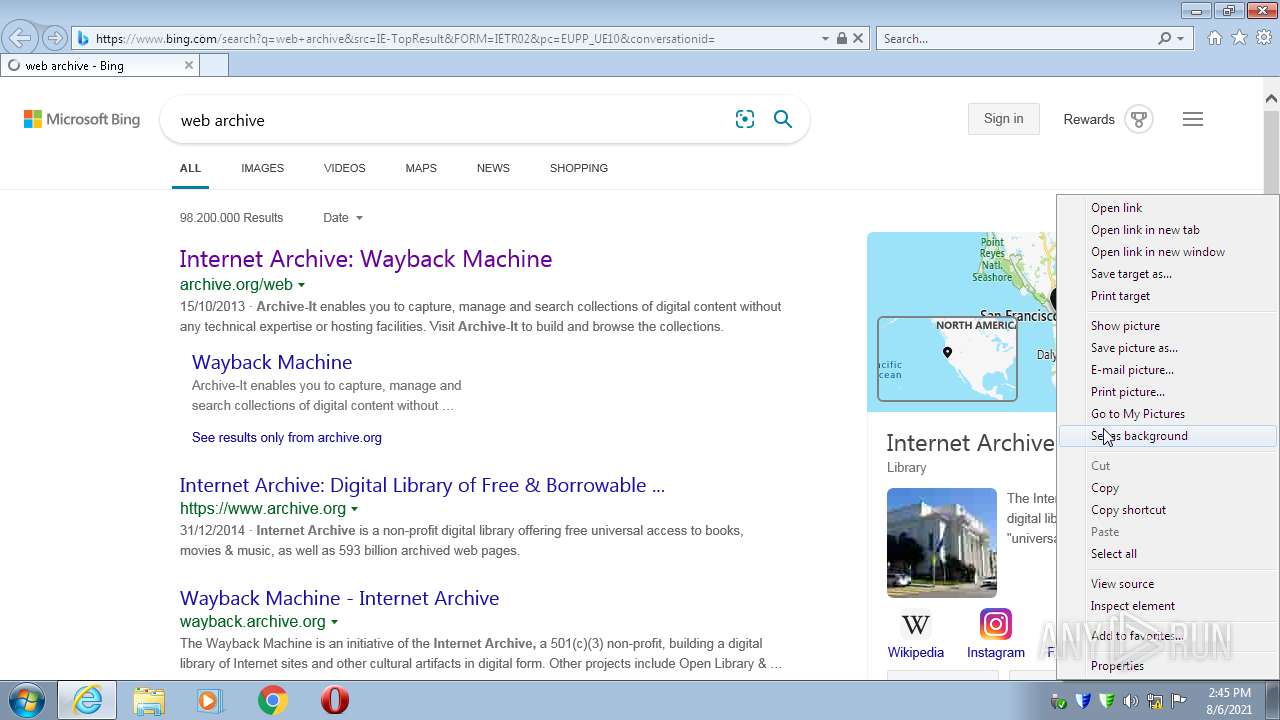
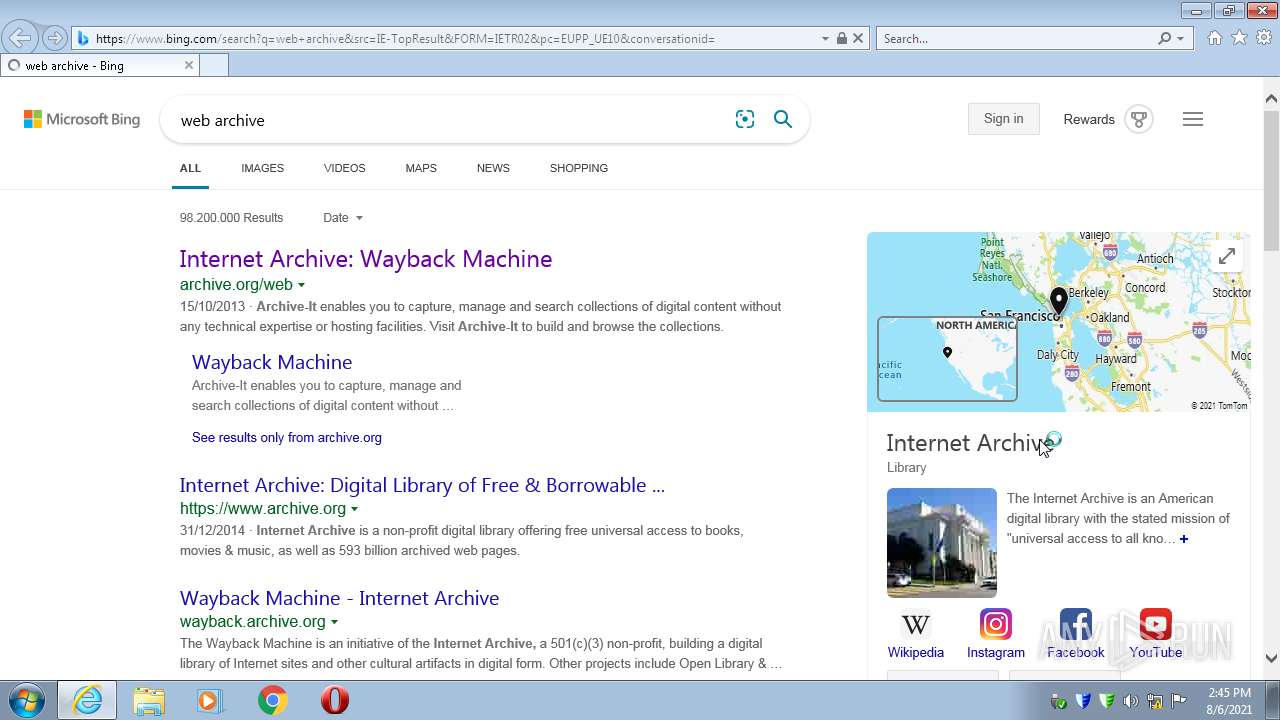
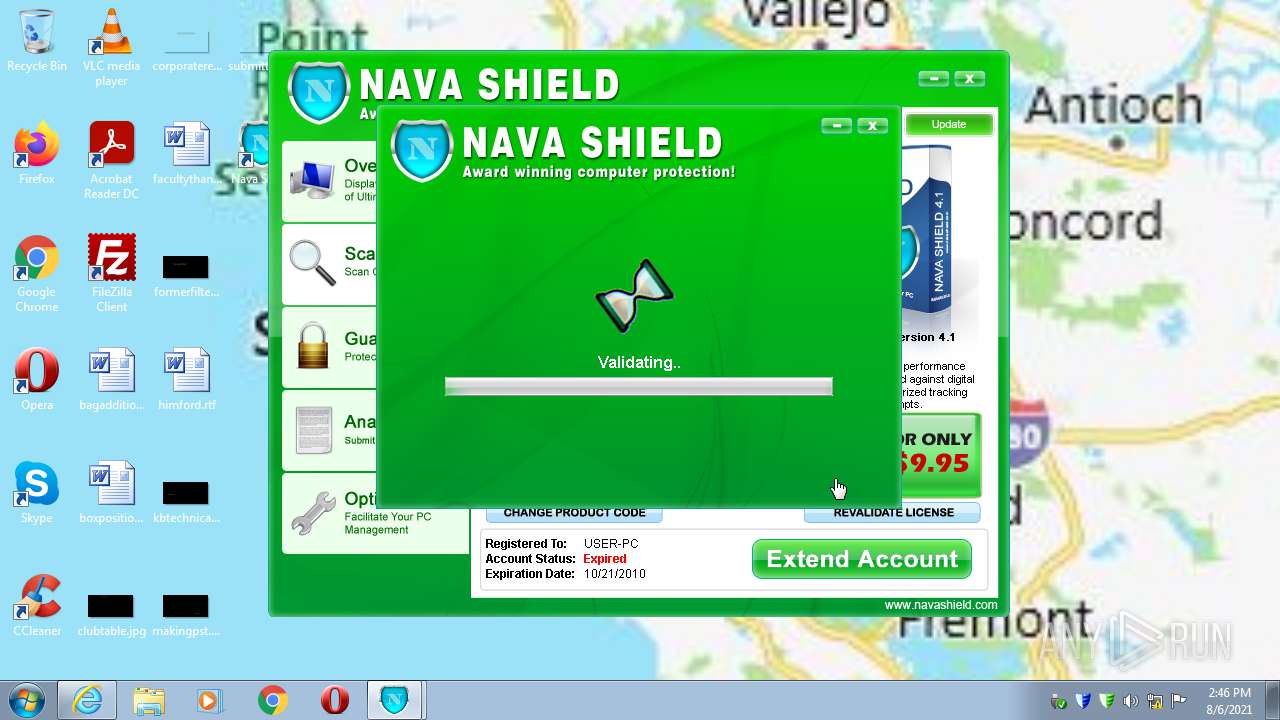
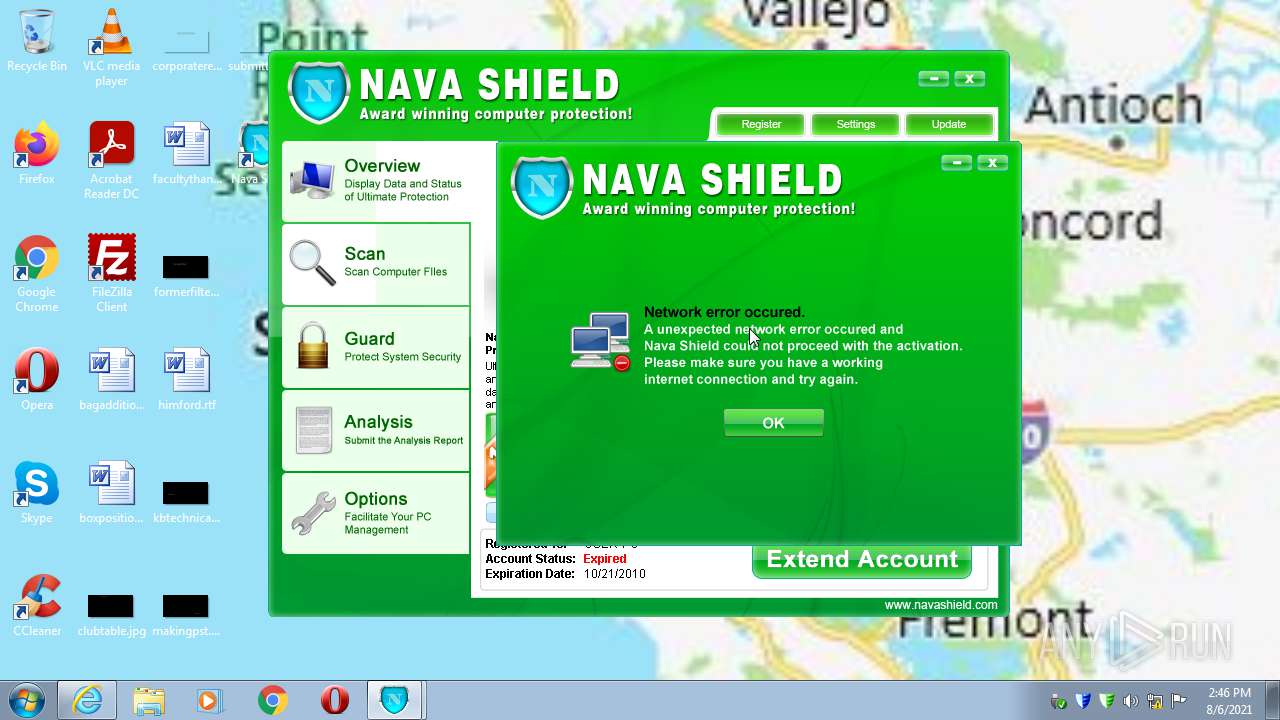
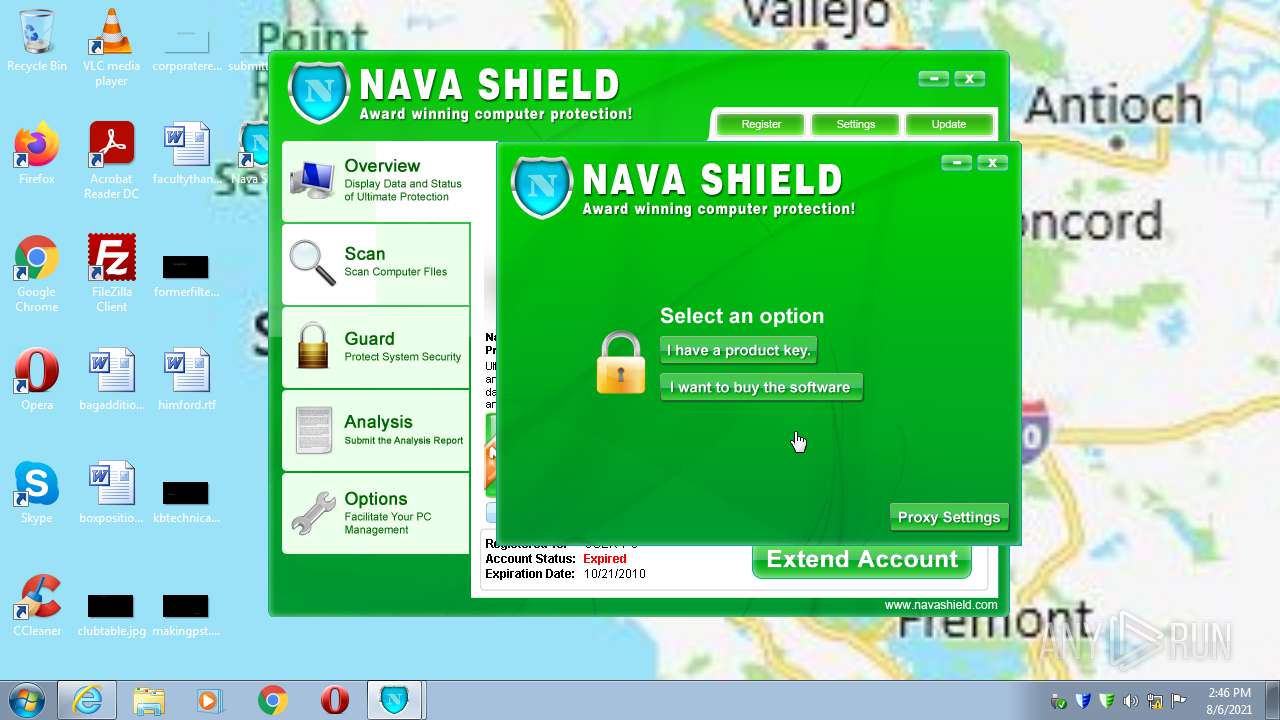
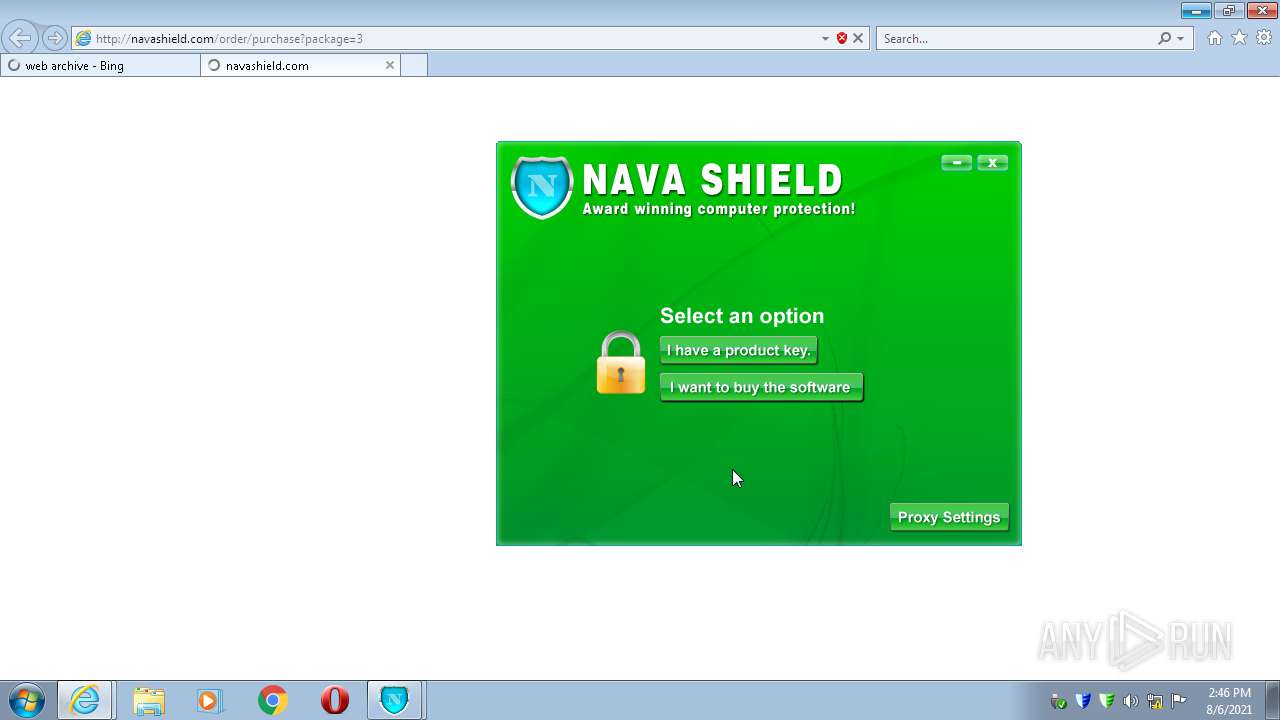
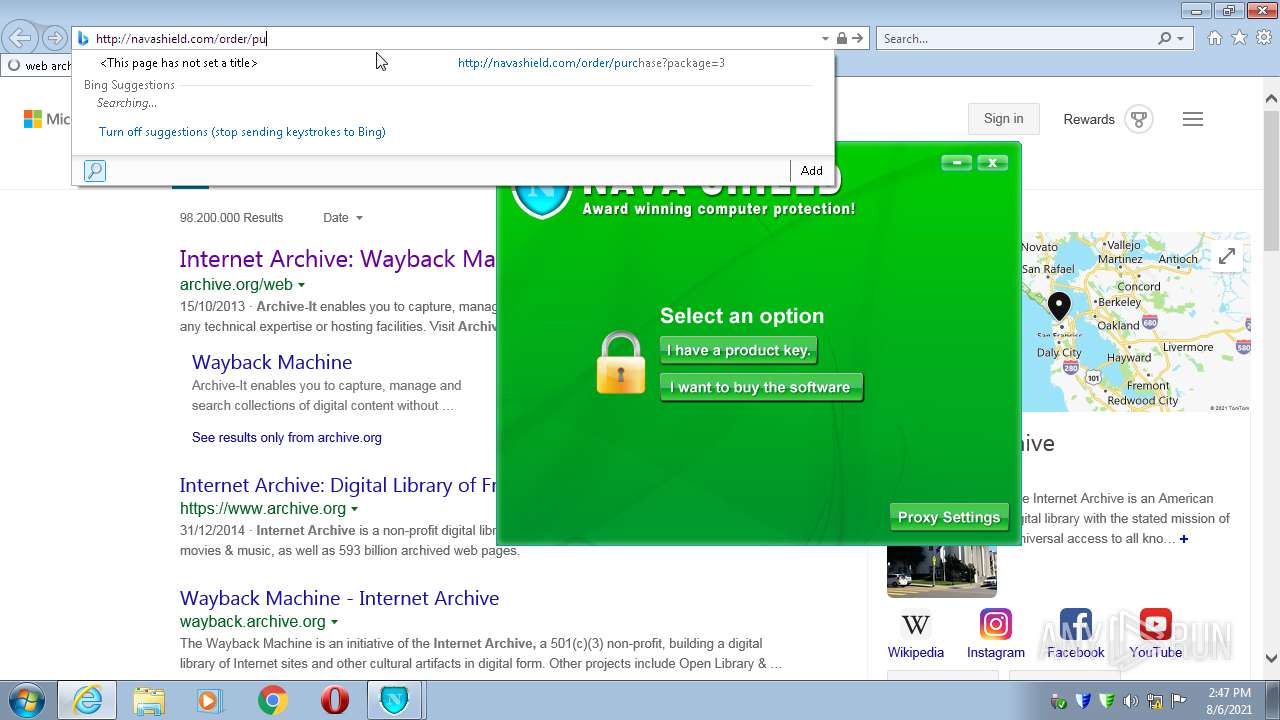
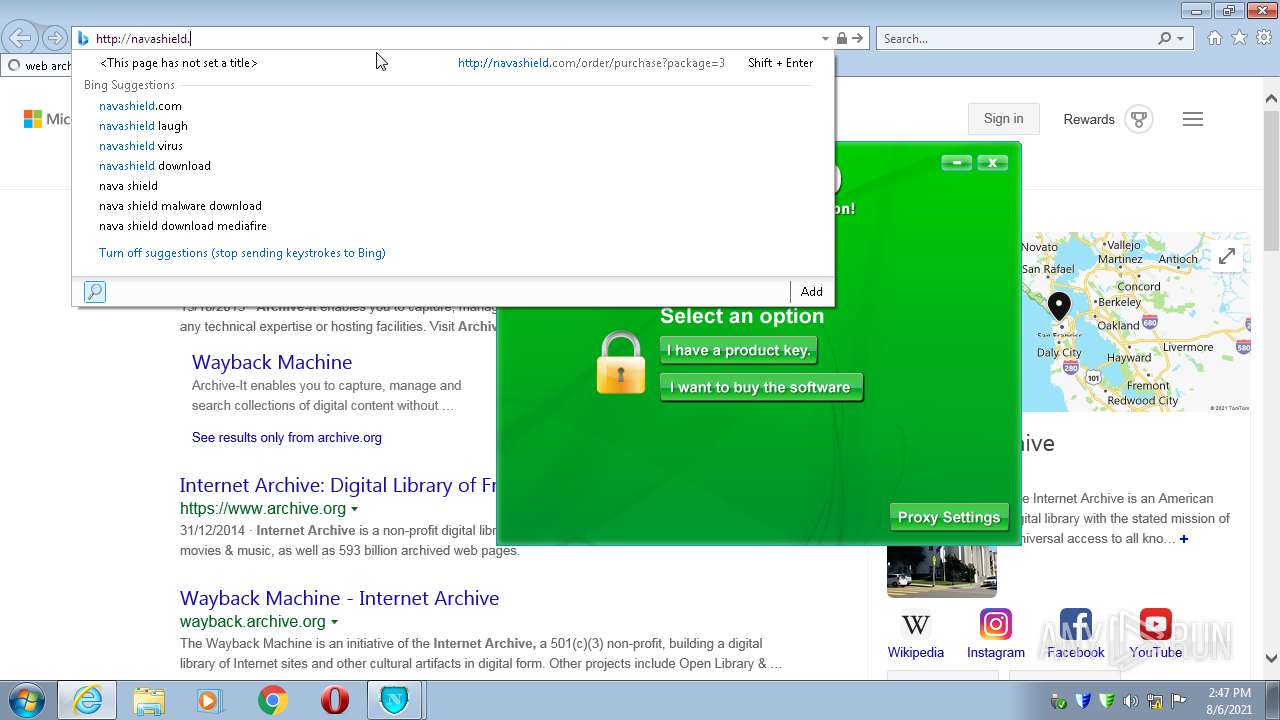
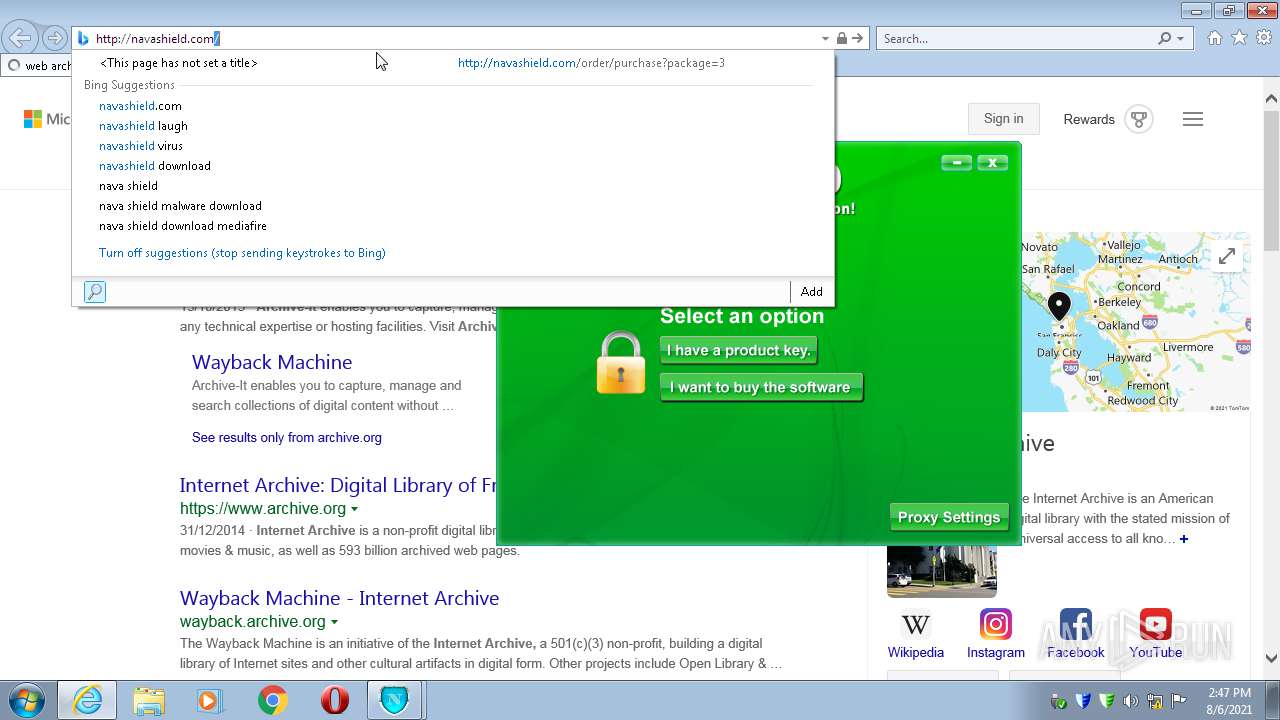
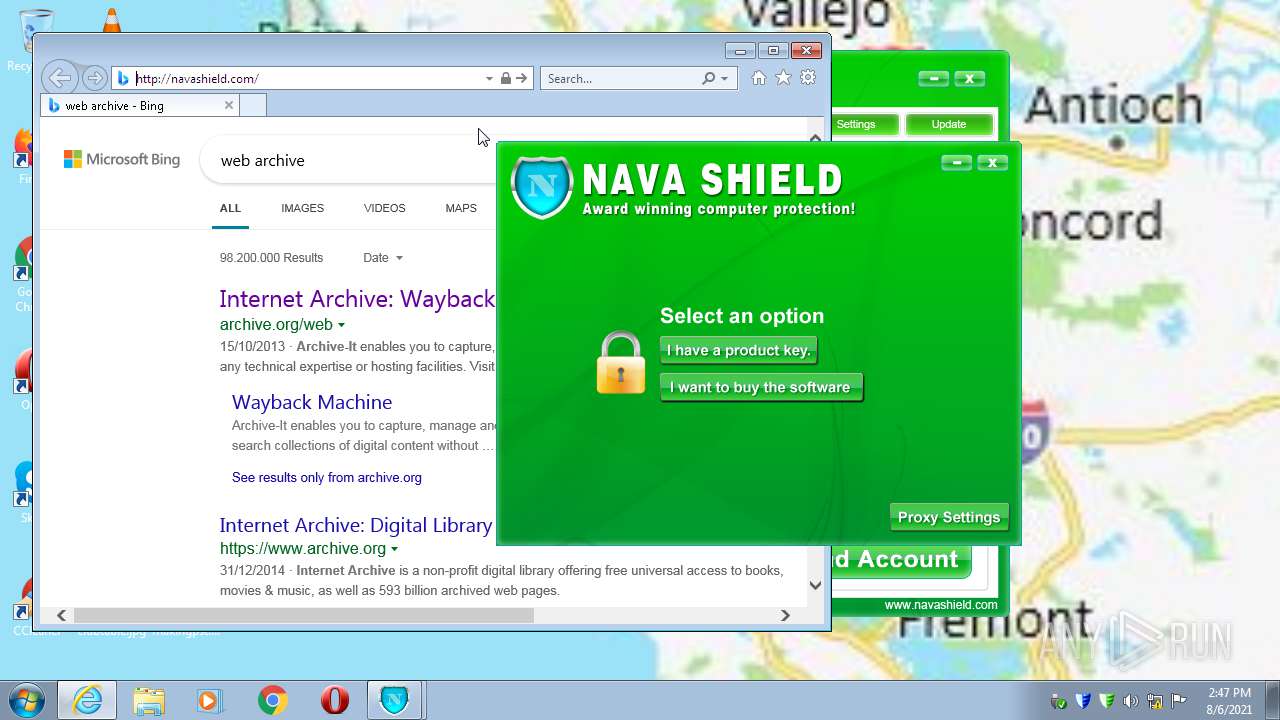
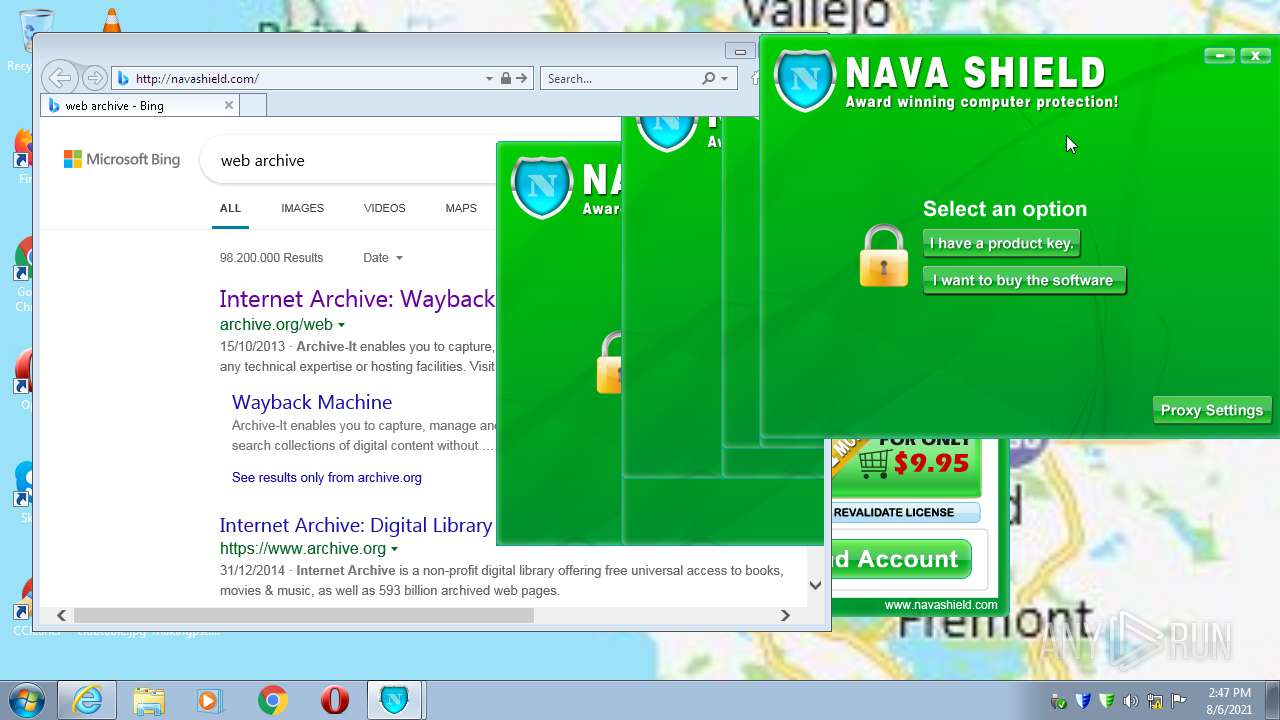
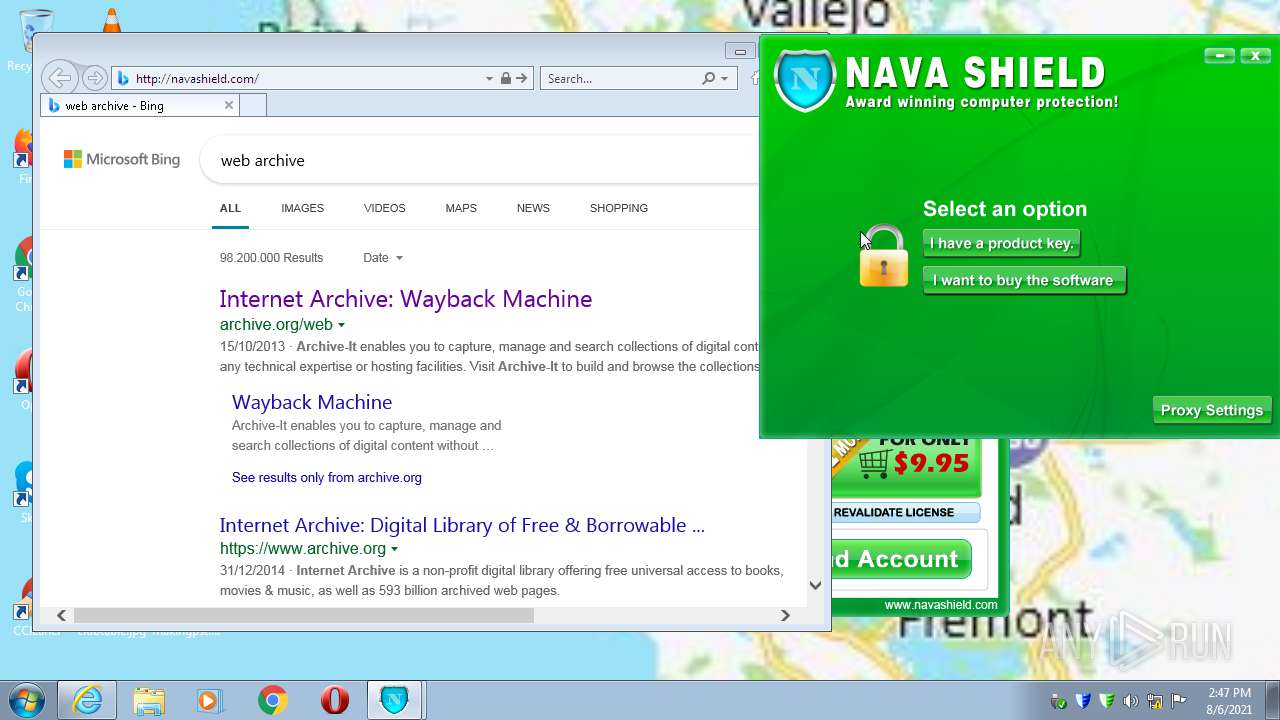
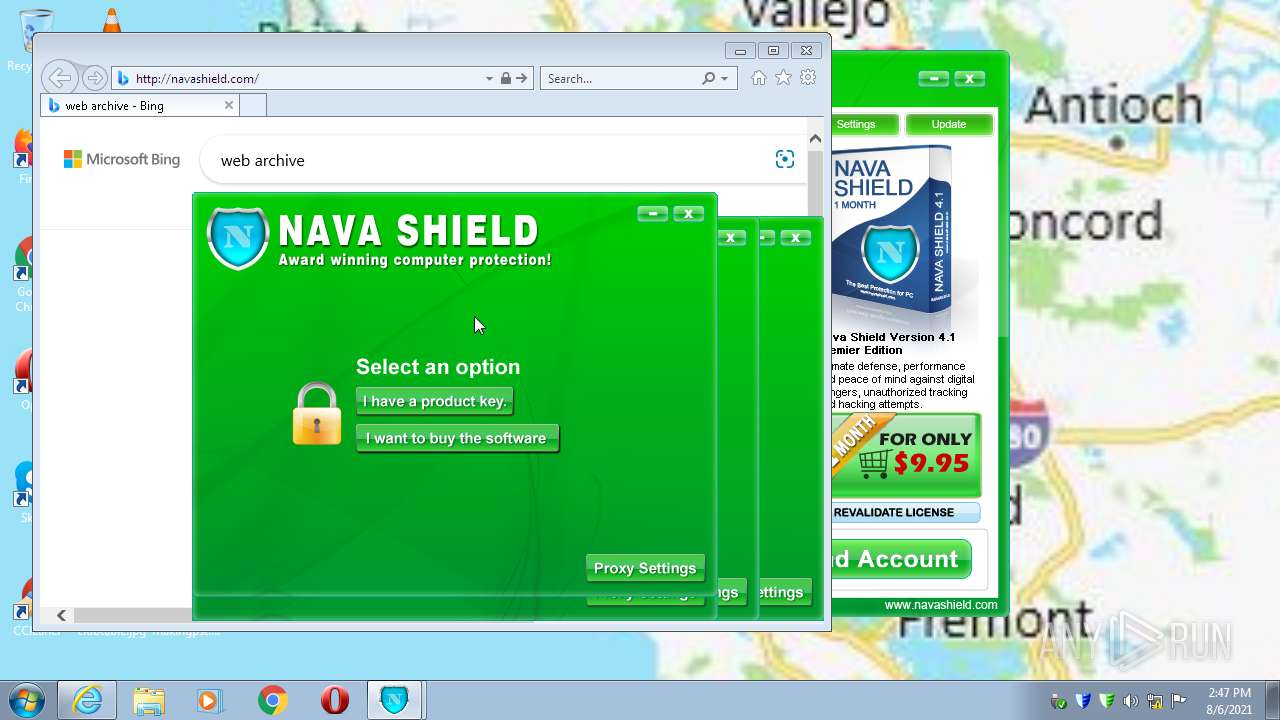
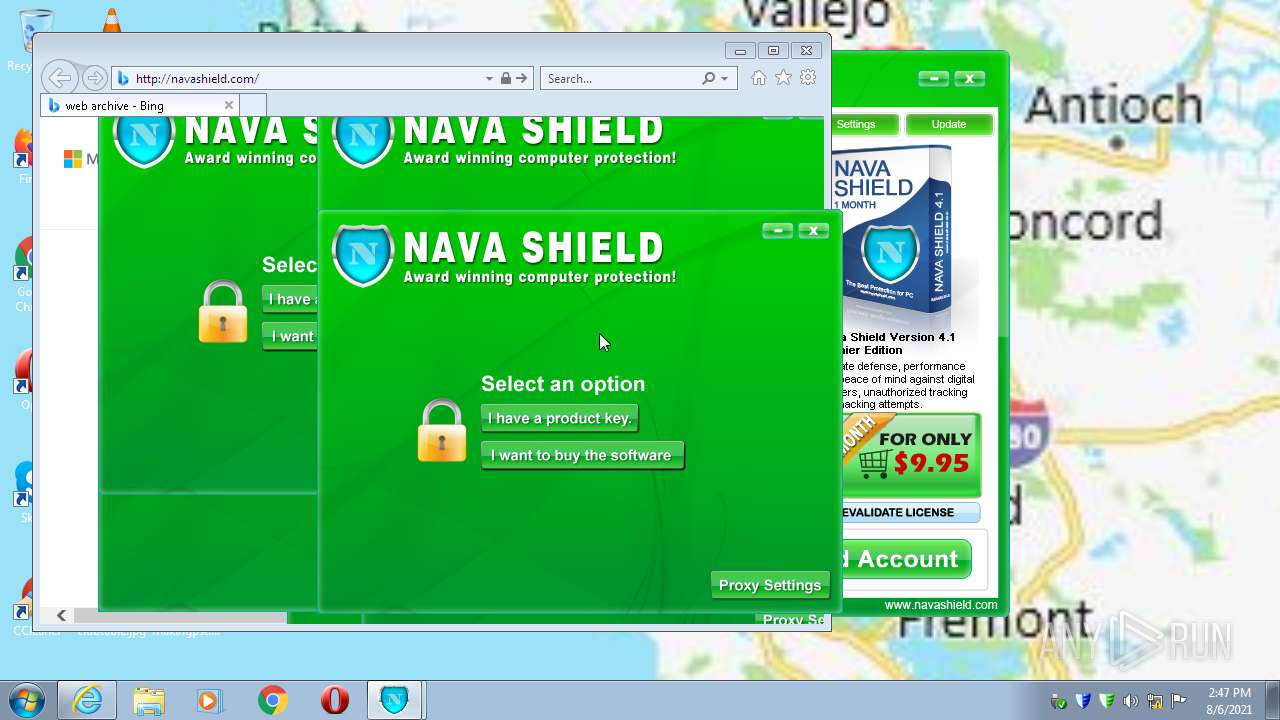
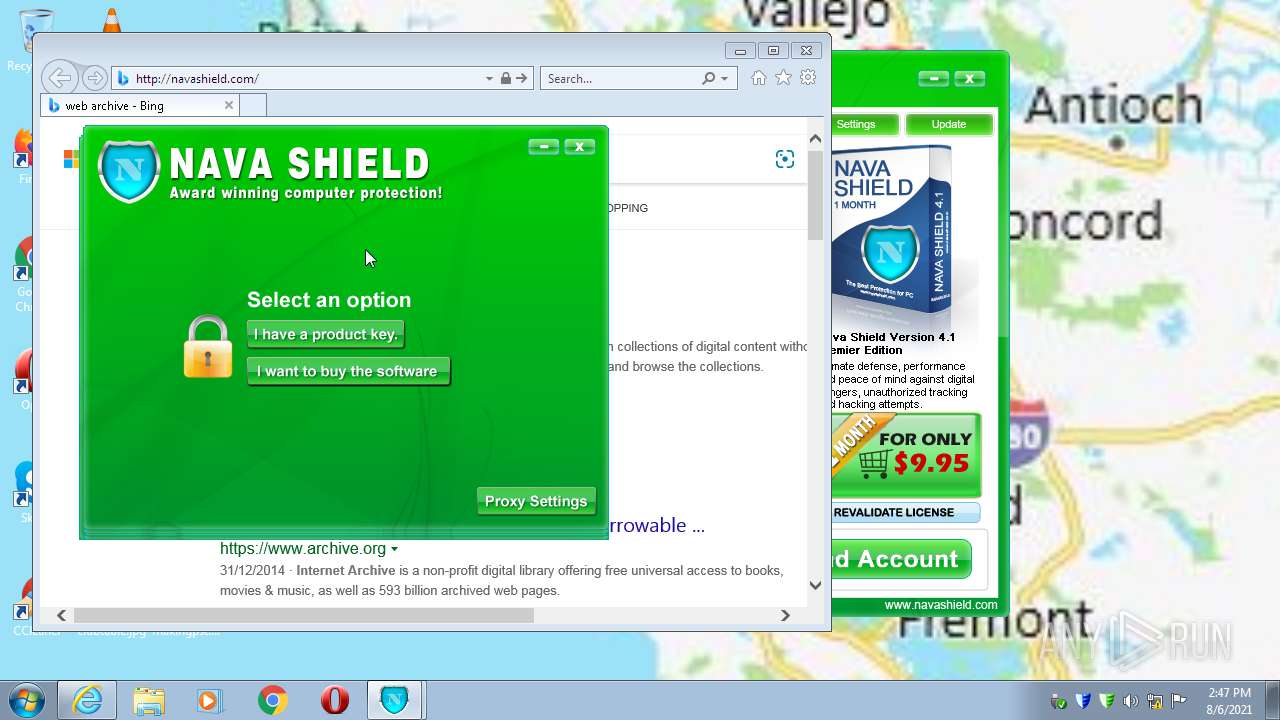
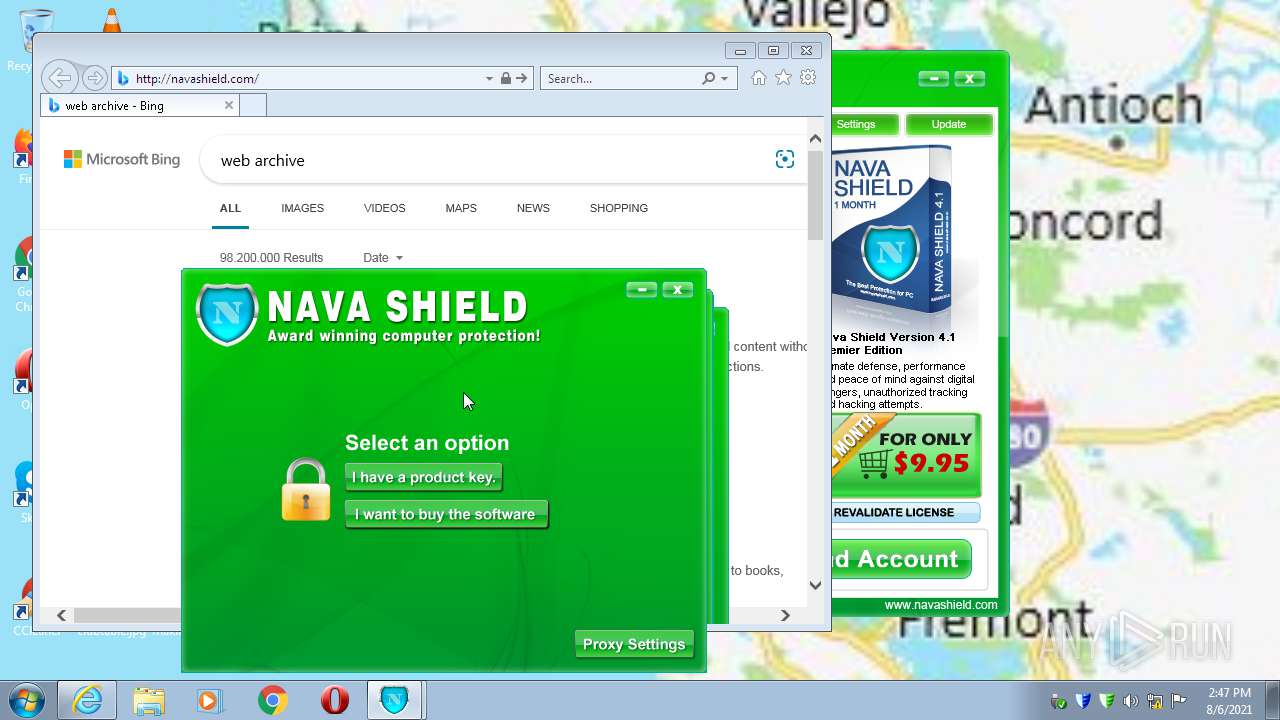
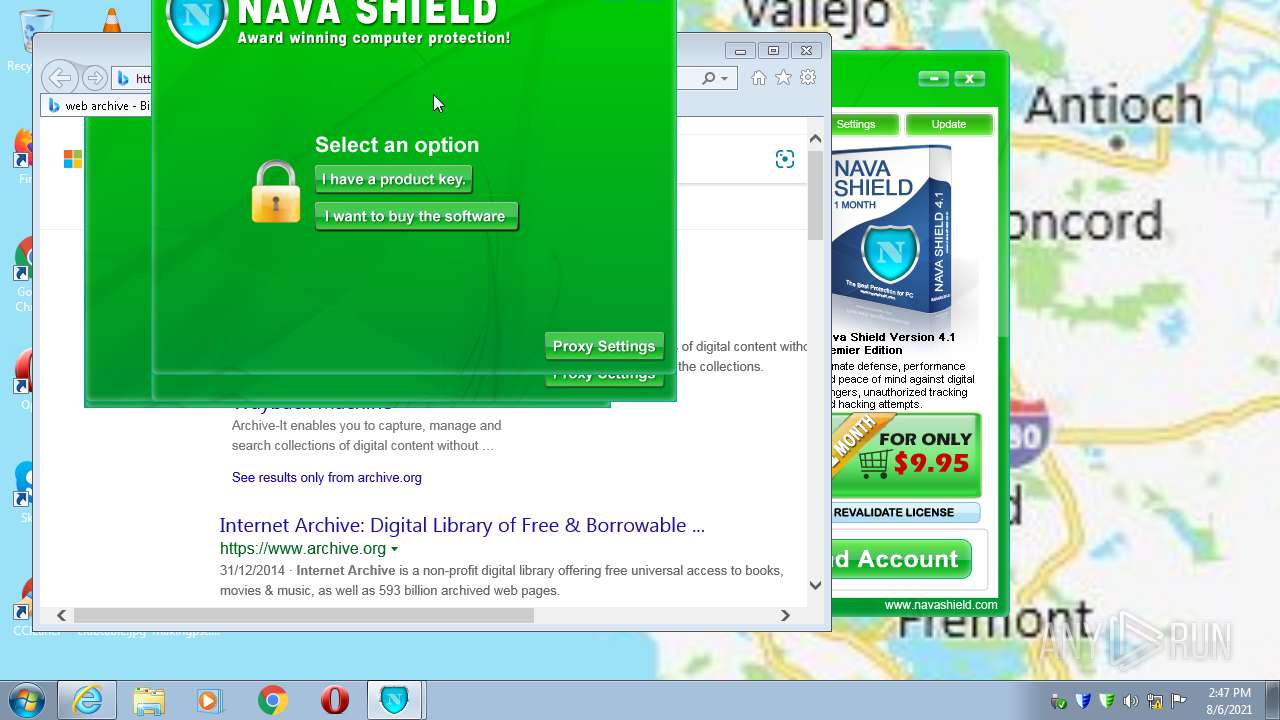
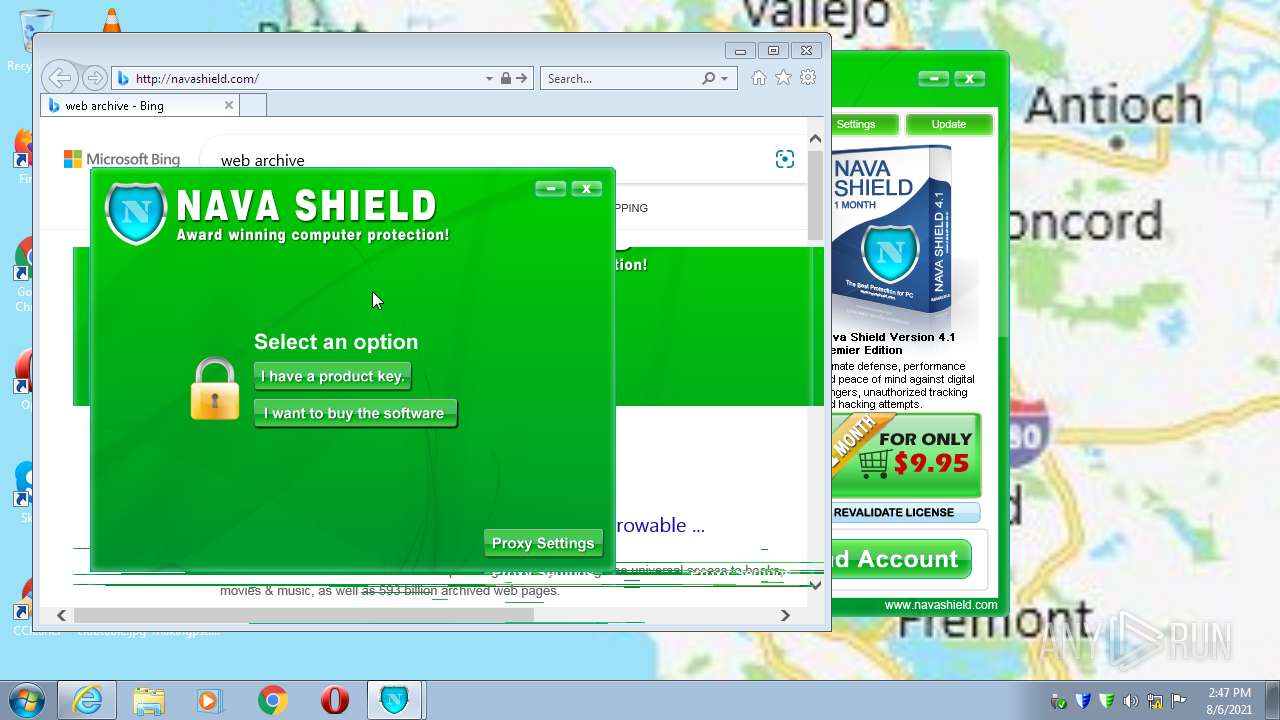
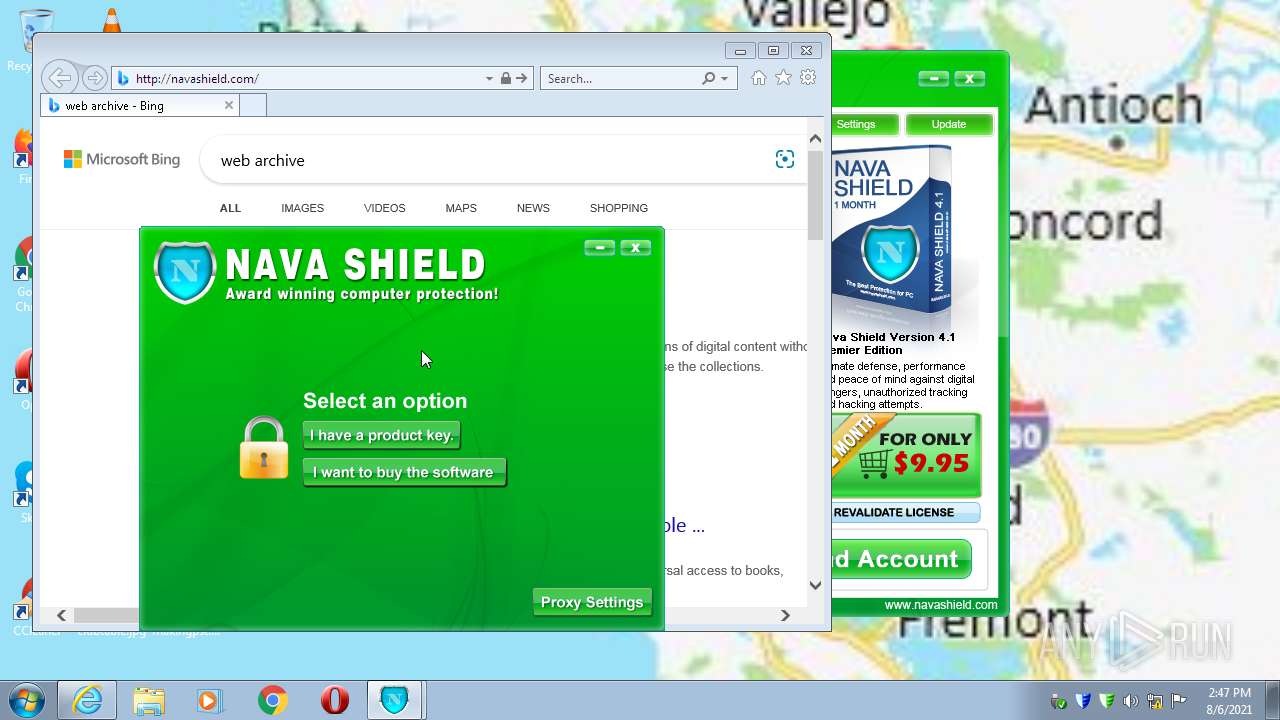
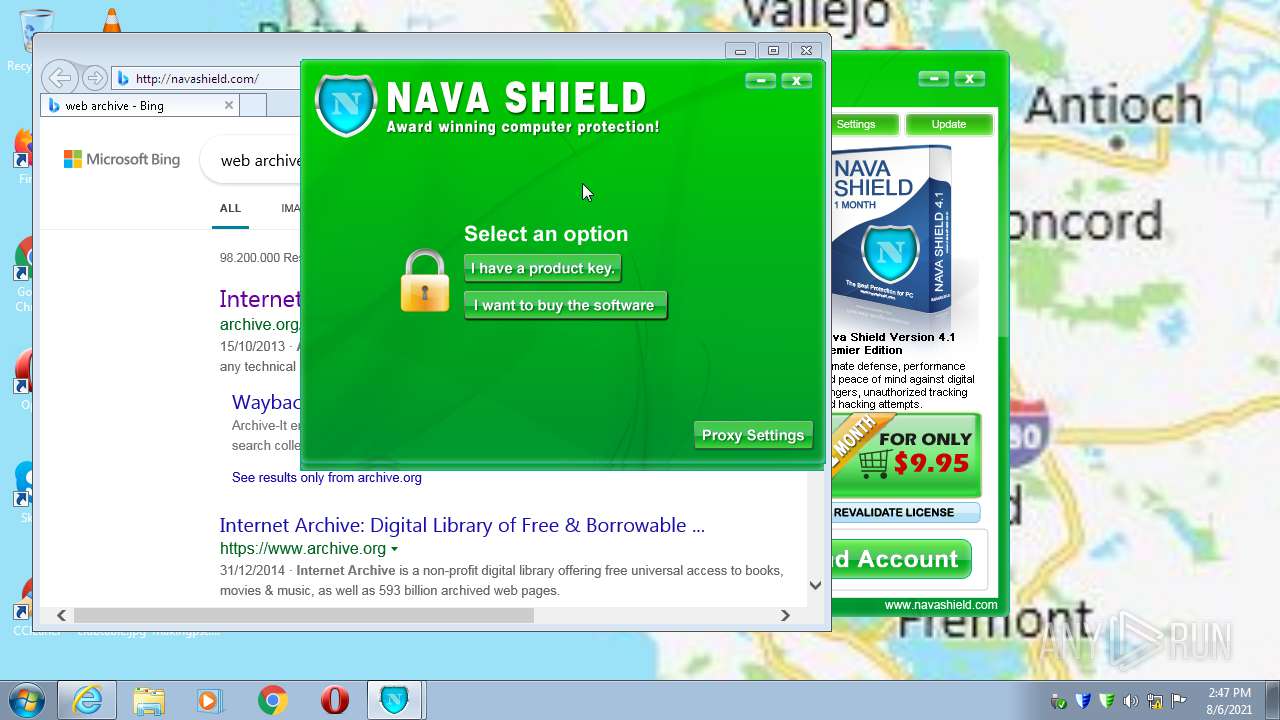
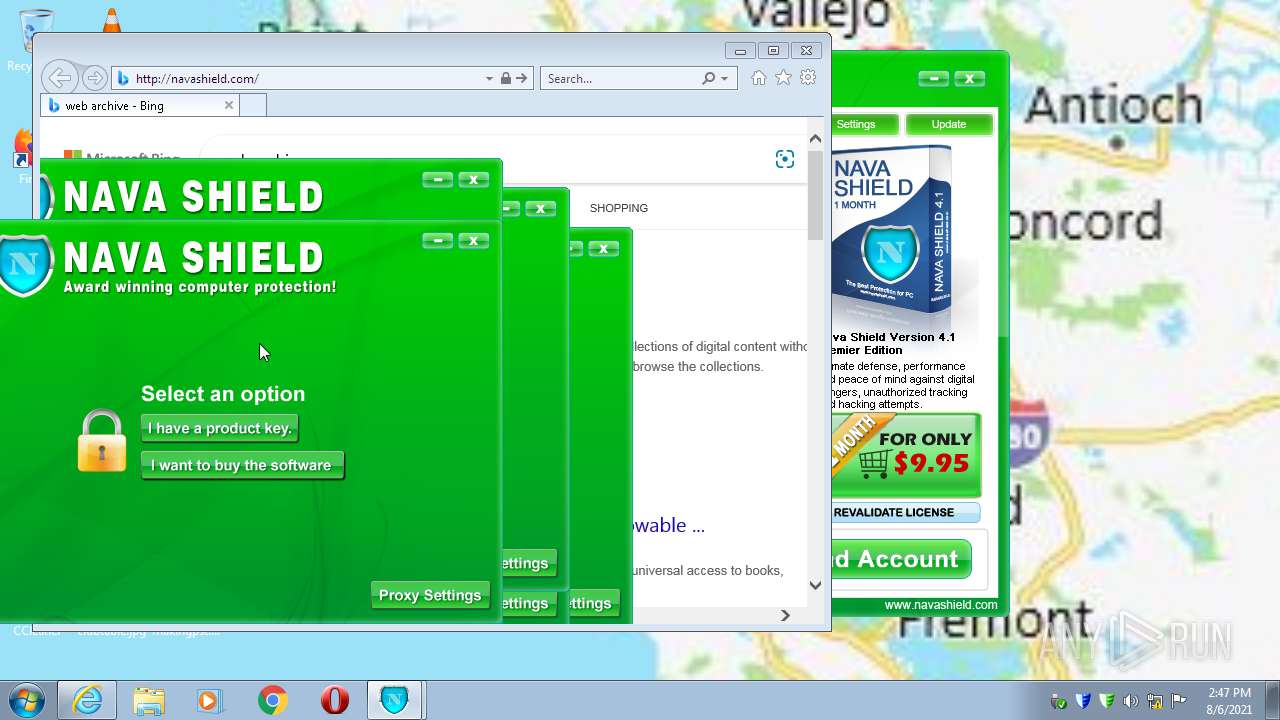
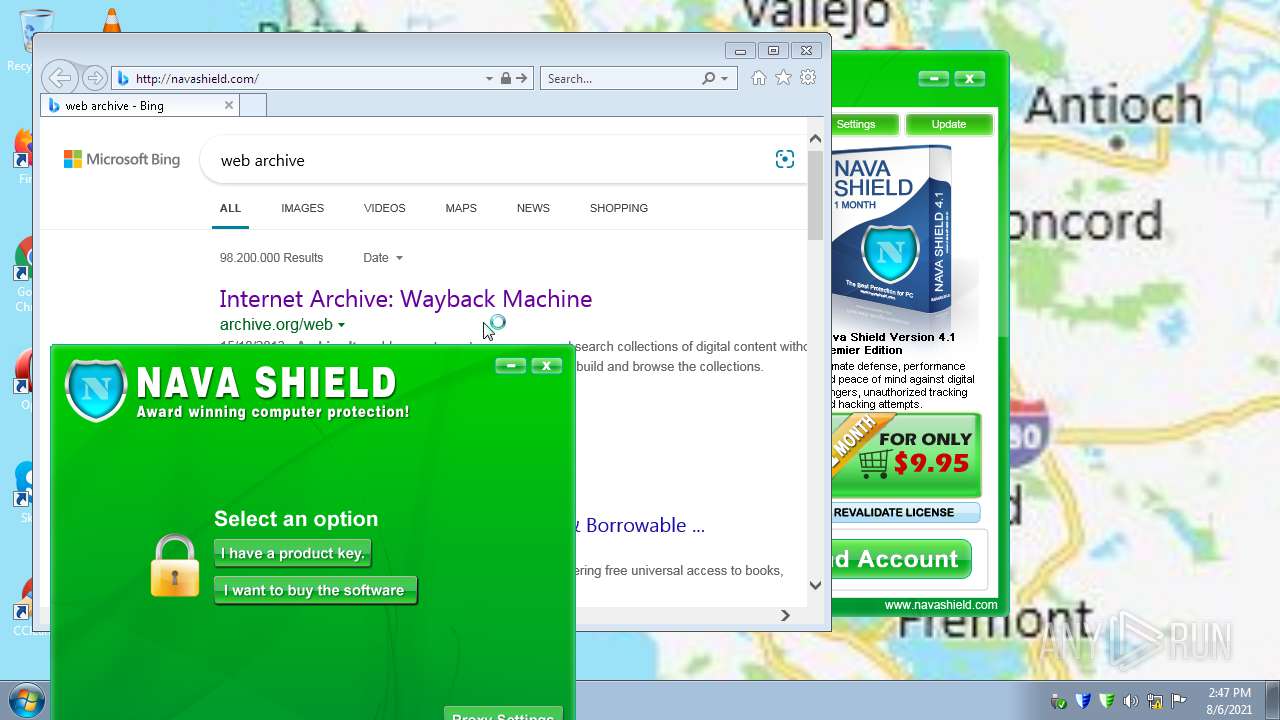
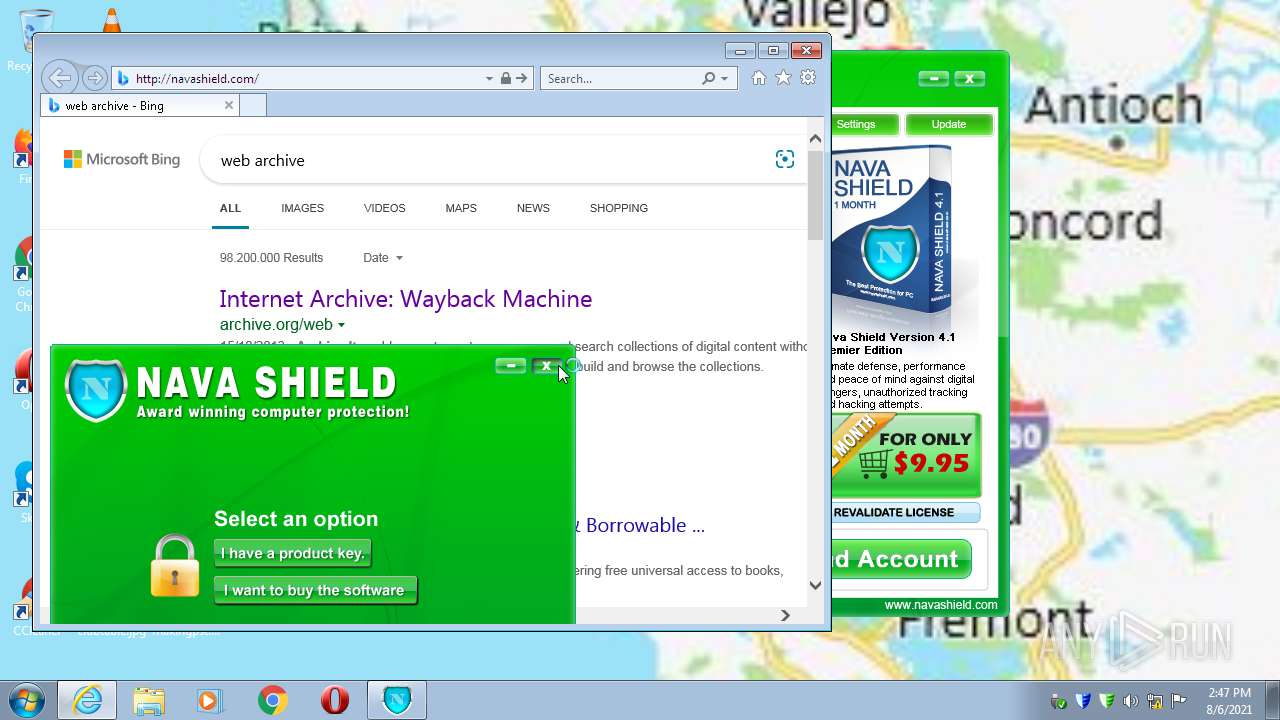
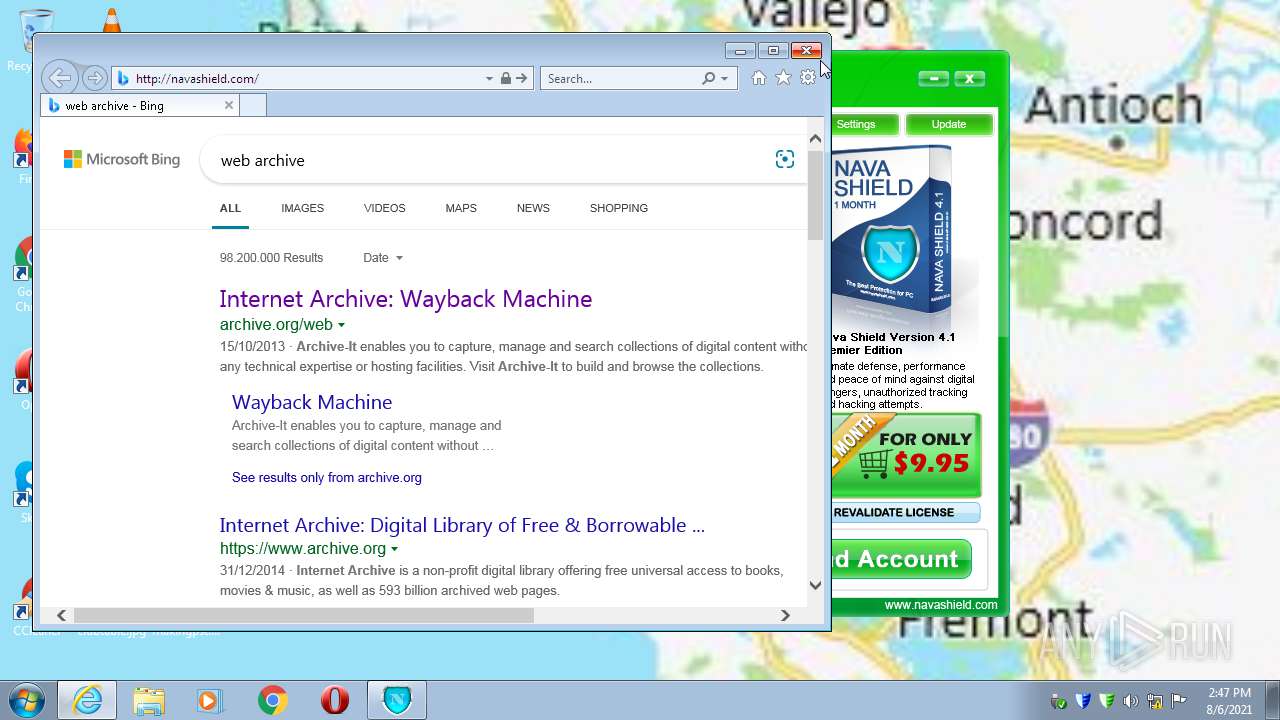
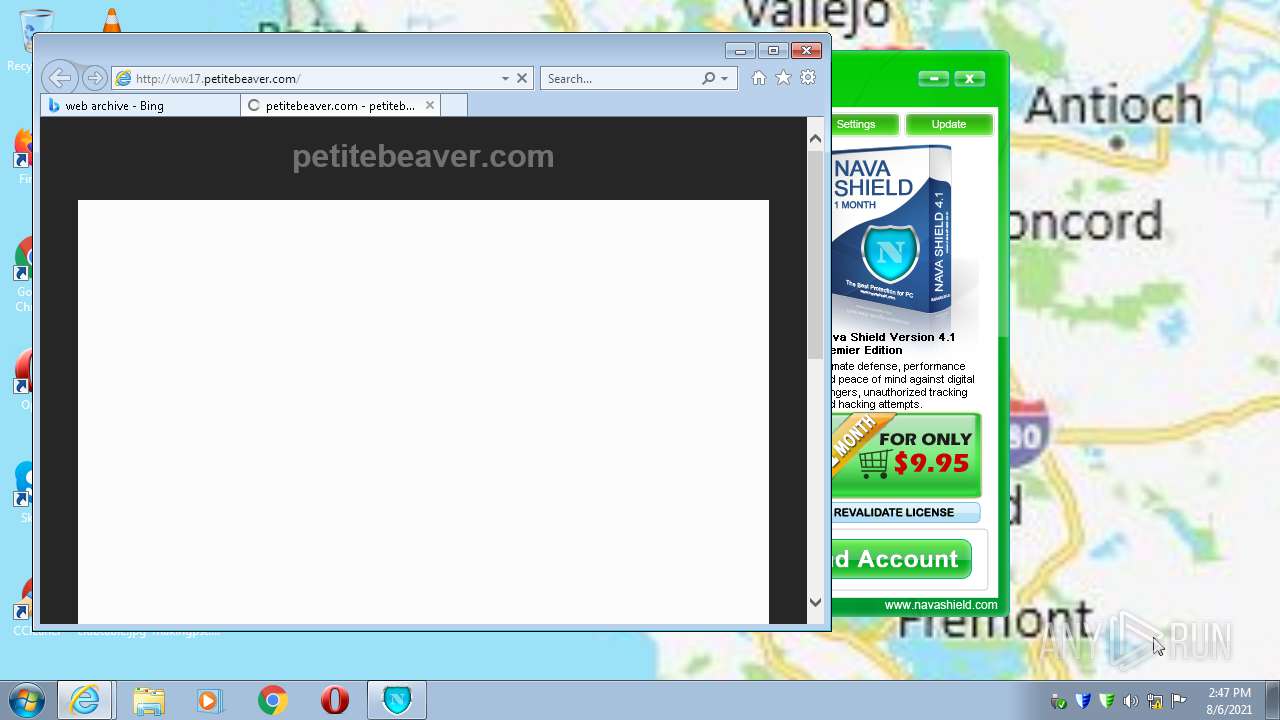
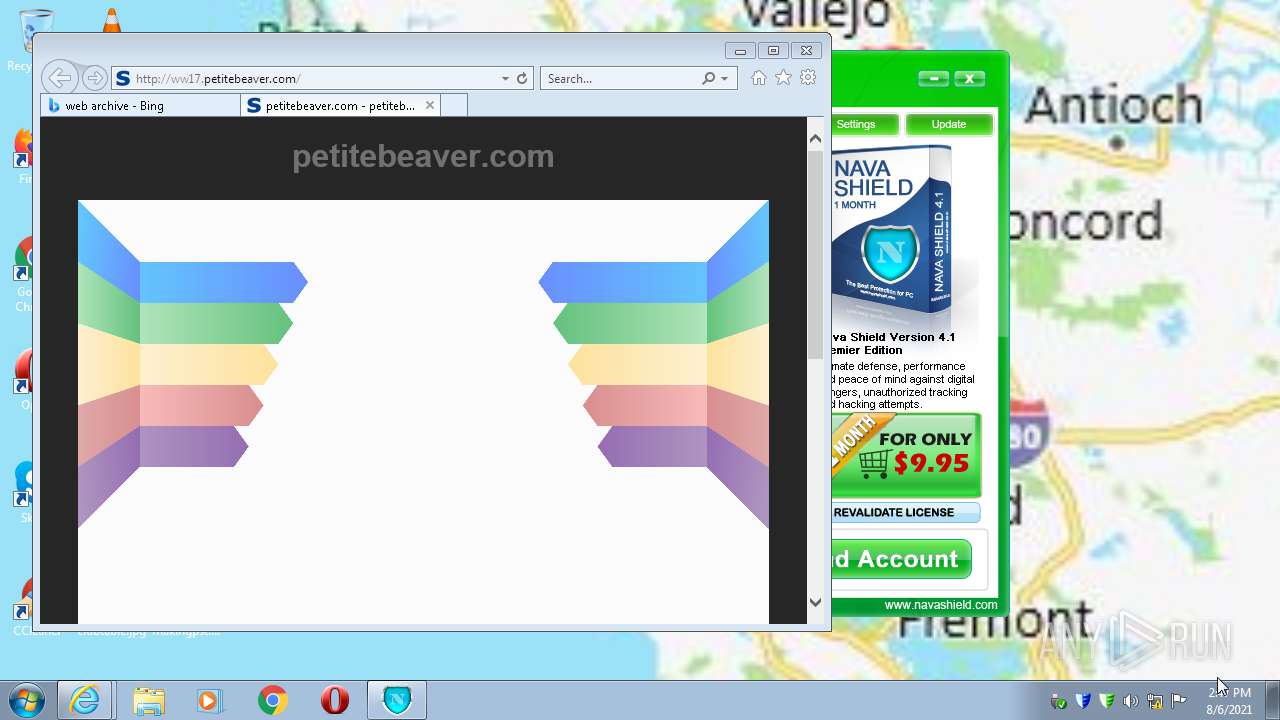
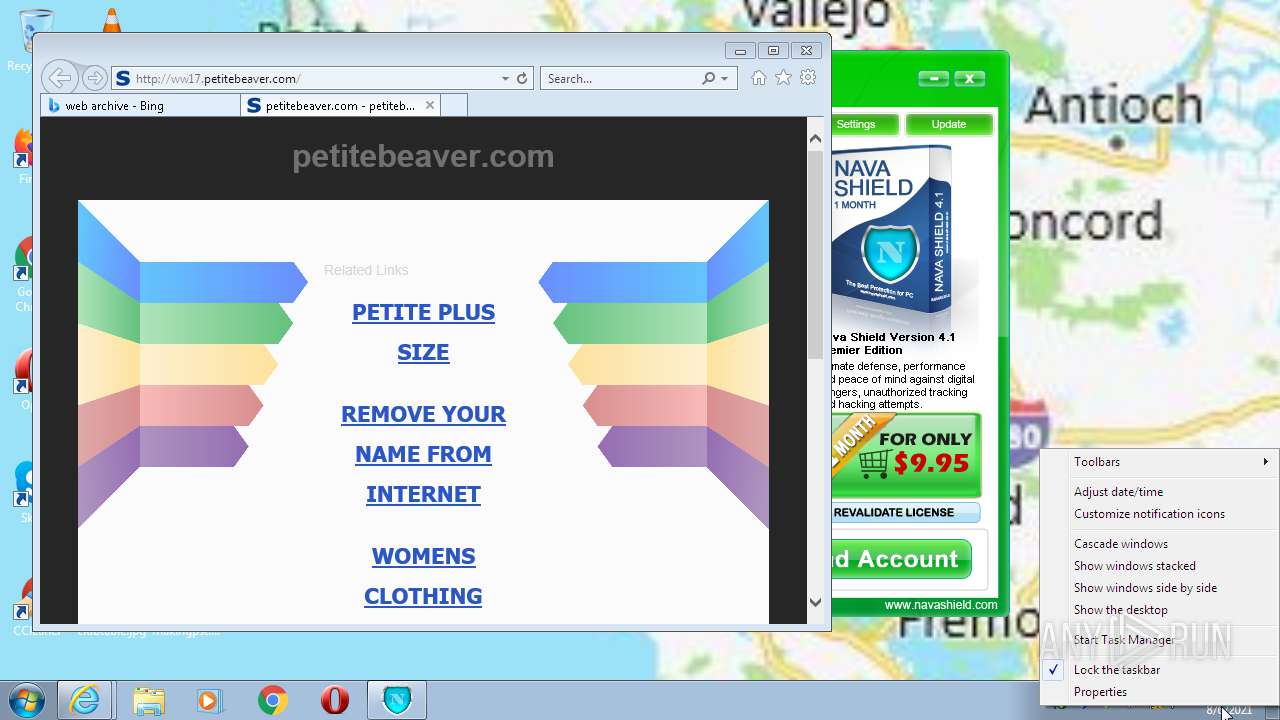
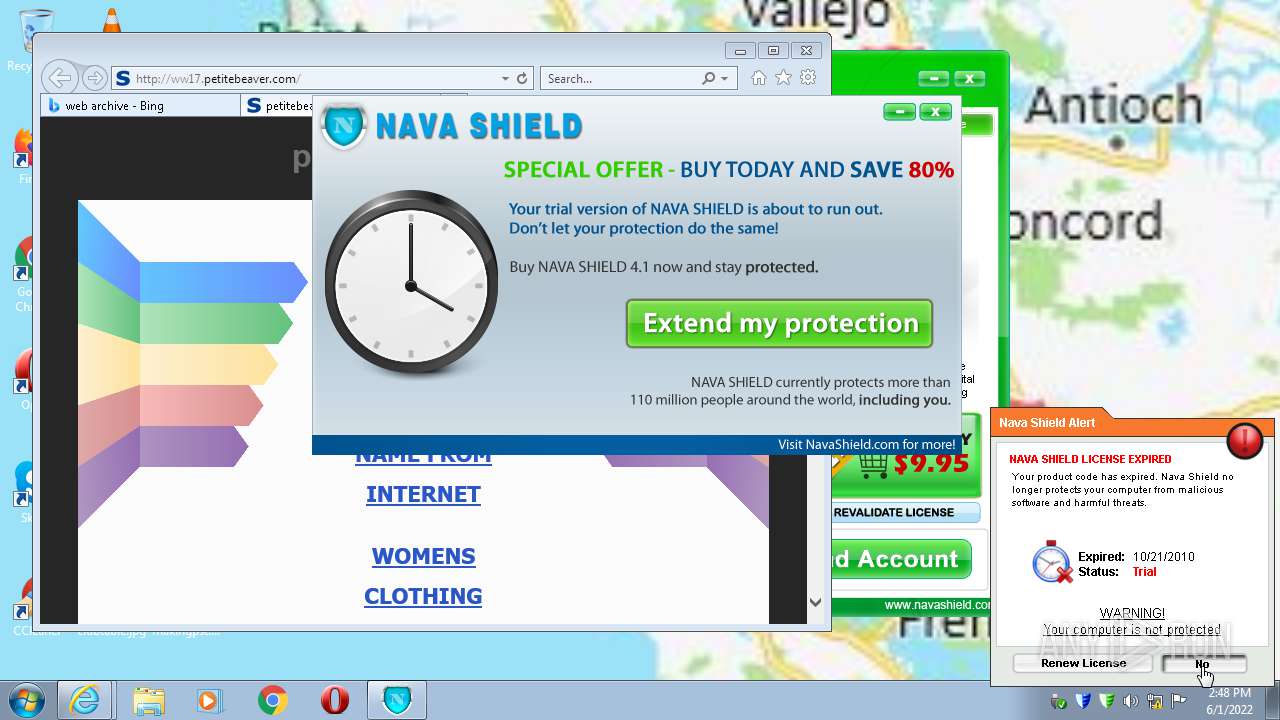
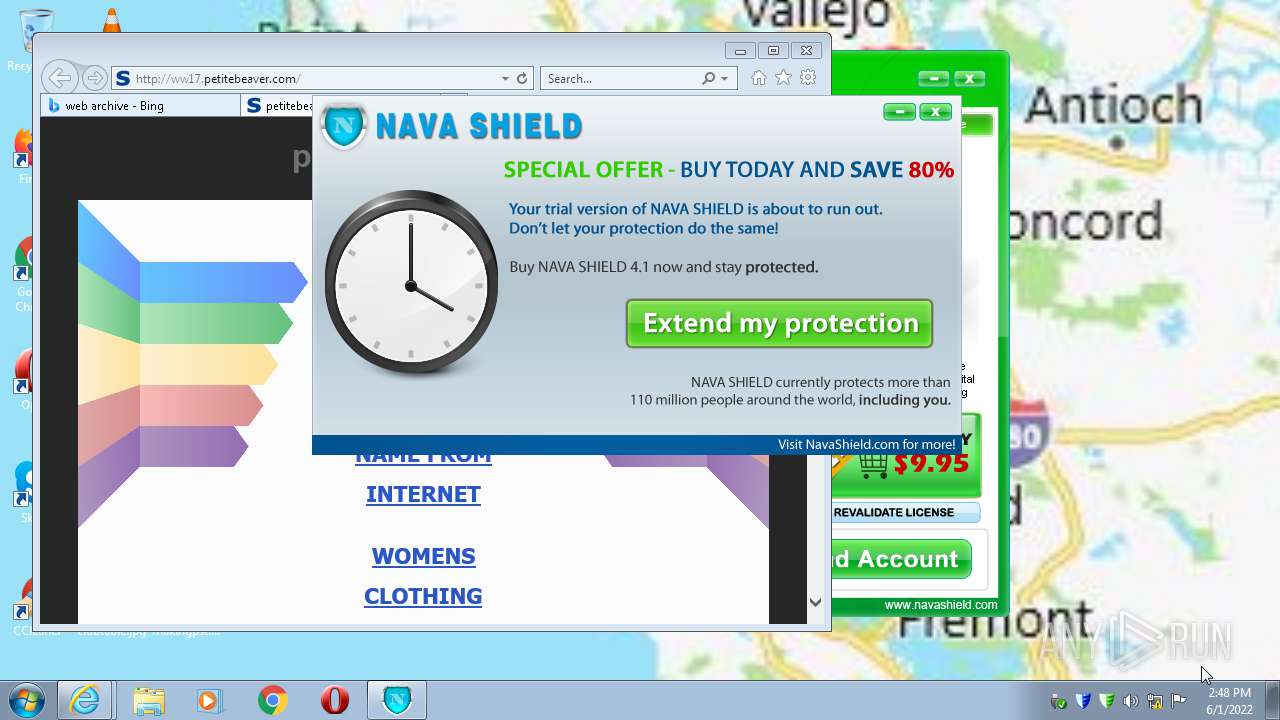
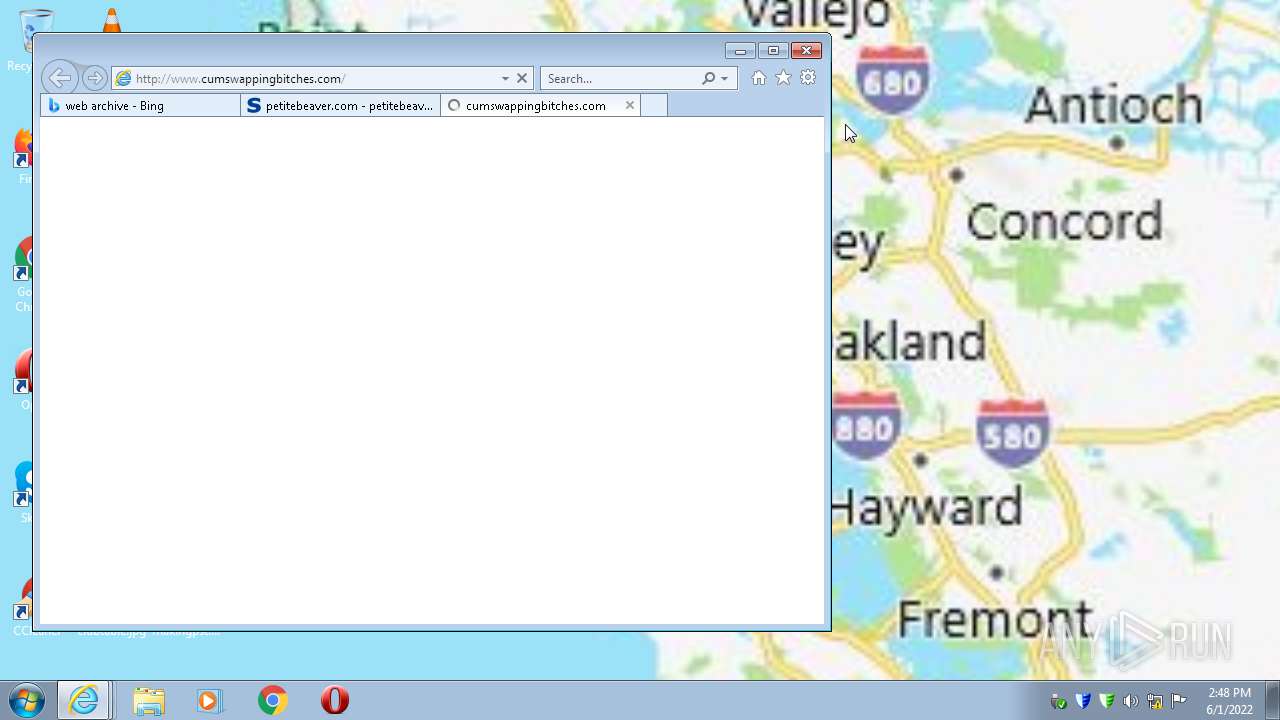
Starts Internet Explorer
- NavaShield.exe (PID: 3852)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1512)
- iexplore.exe (PID: 2068)
Executed via COM
- DllHost.exe (PID: 908)
- DllHost.exe (PID: 3896)
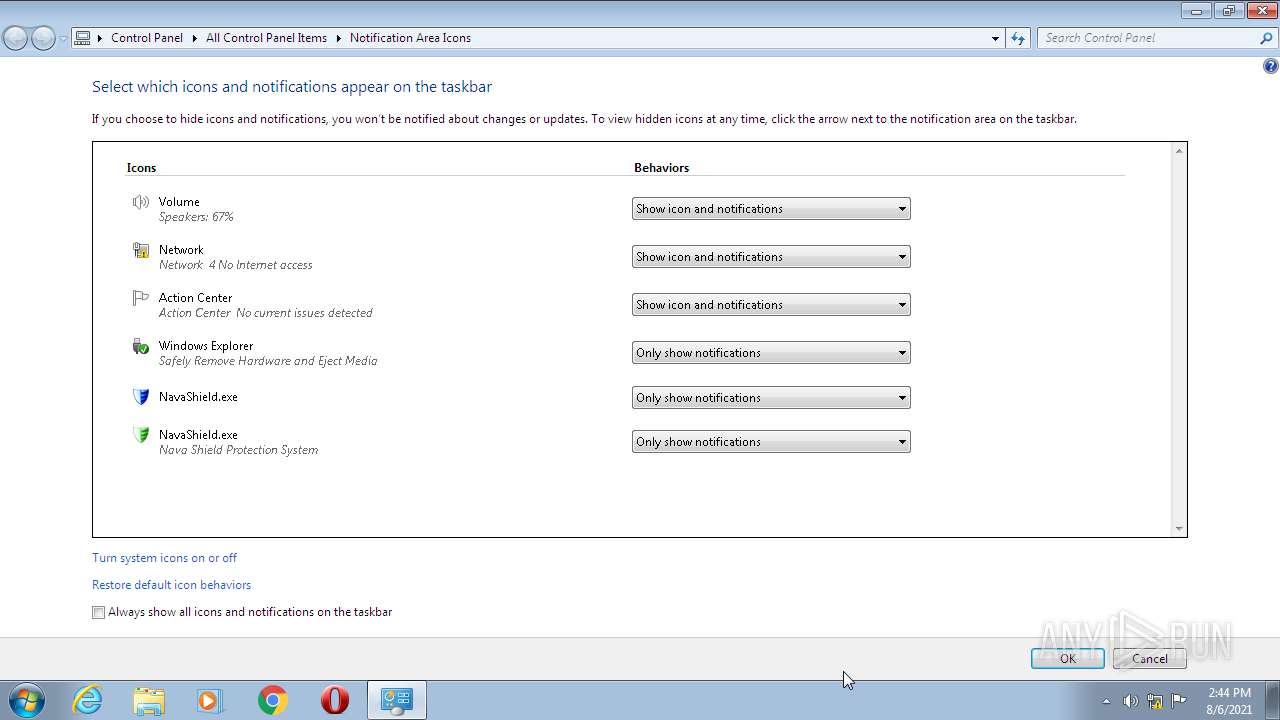
Uses RUNDLL32.EXE to load library
- control.exe (PID: 2284)
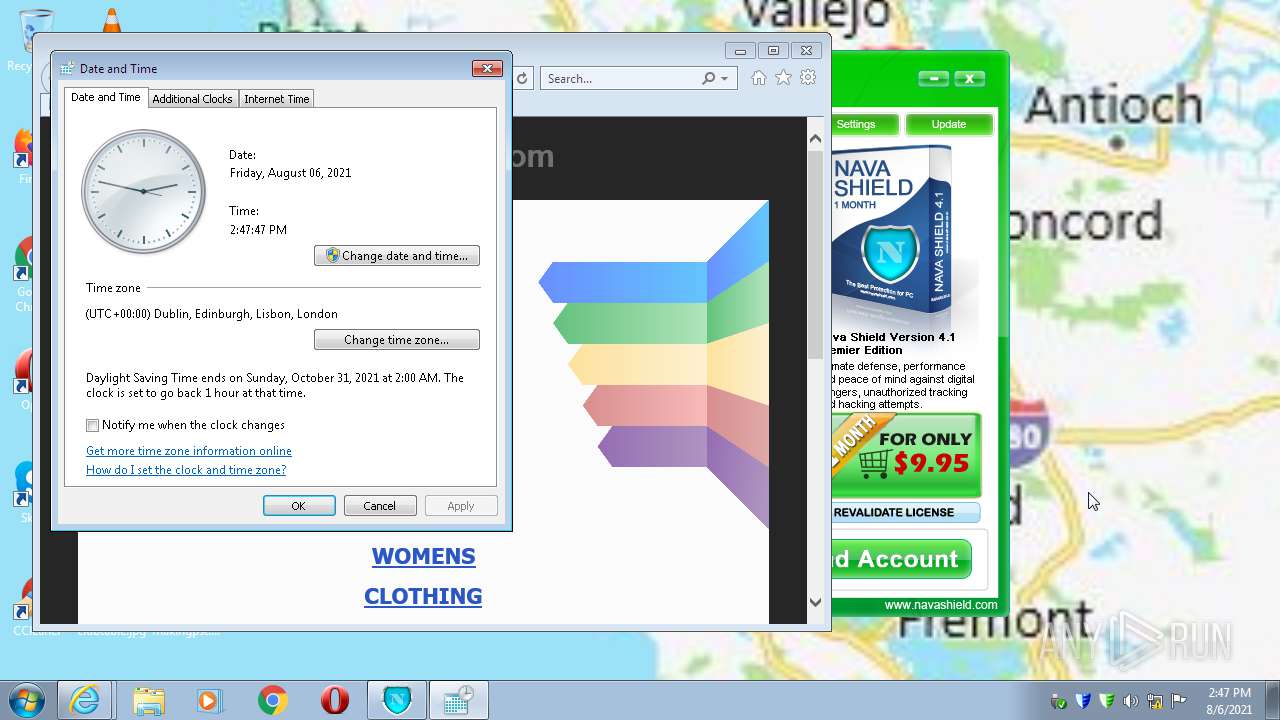
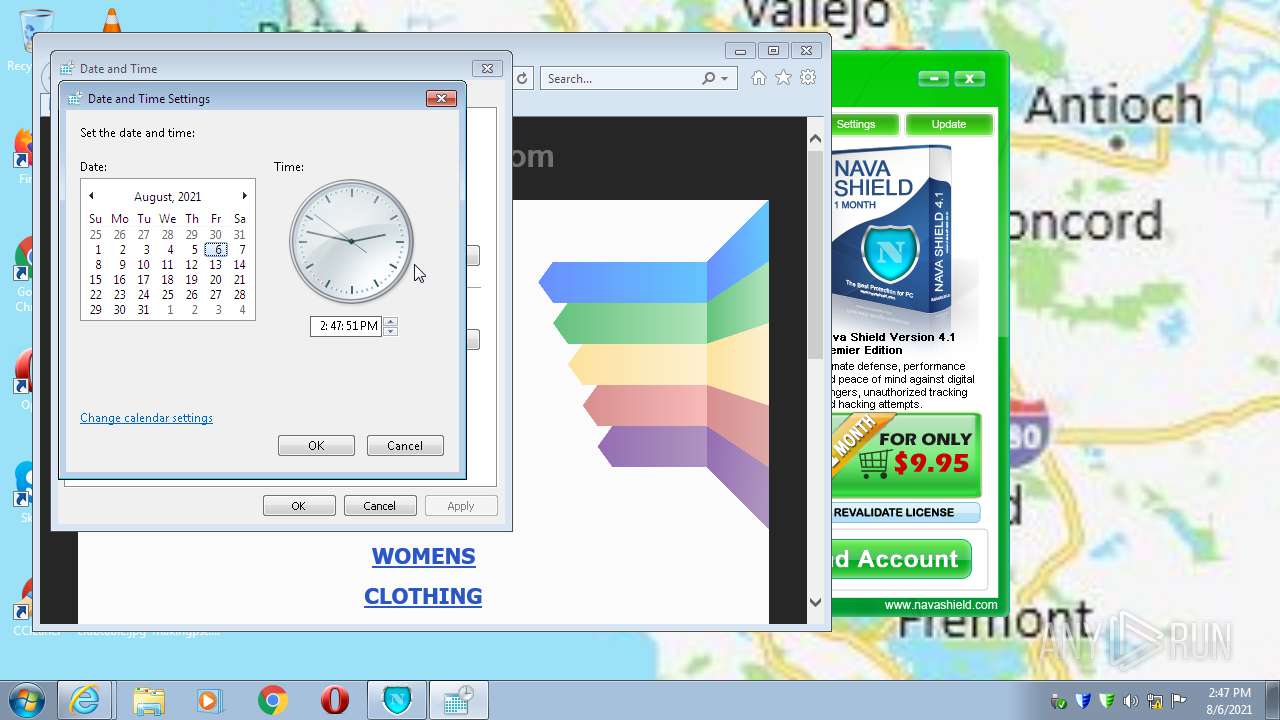
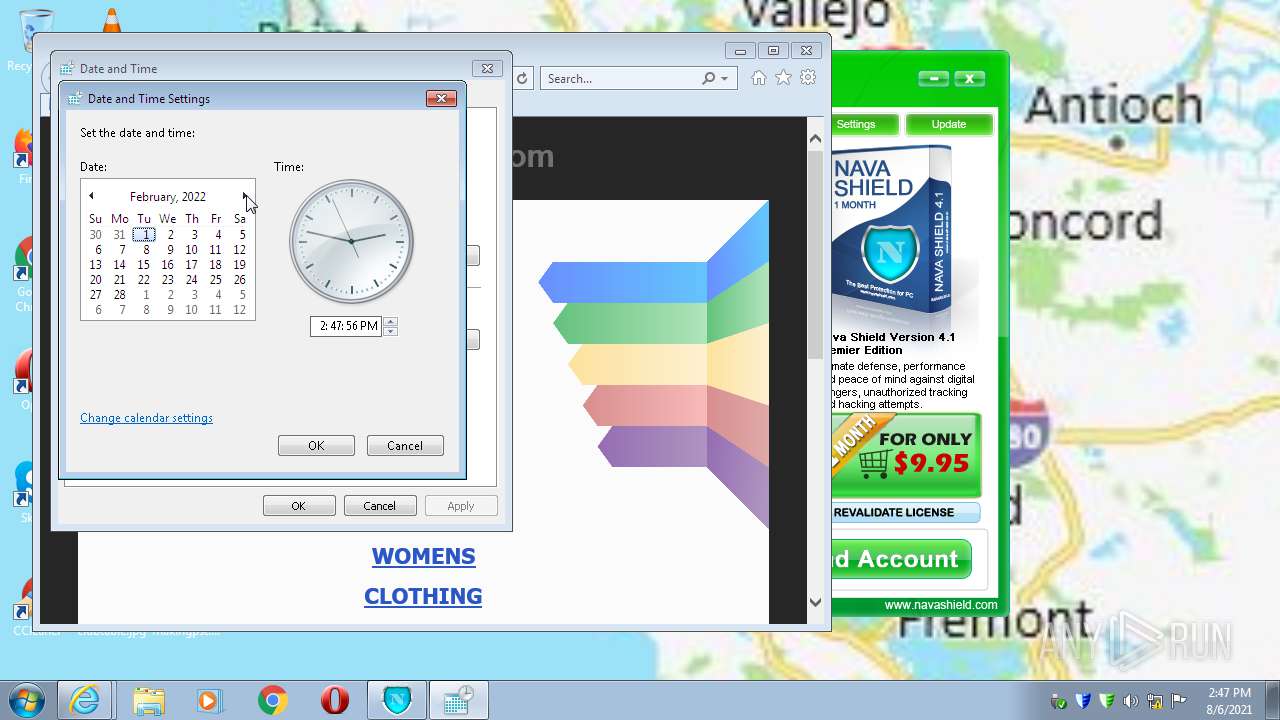
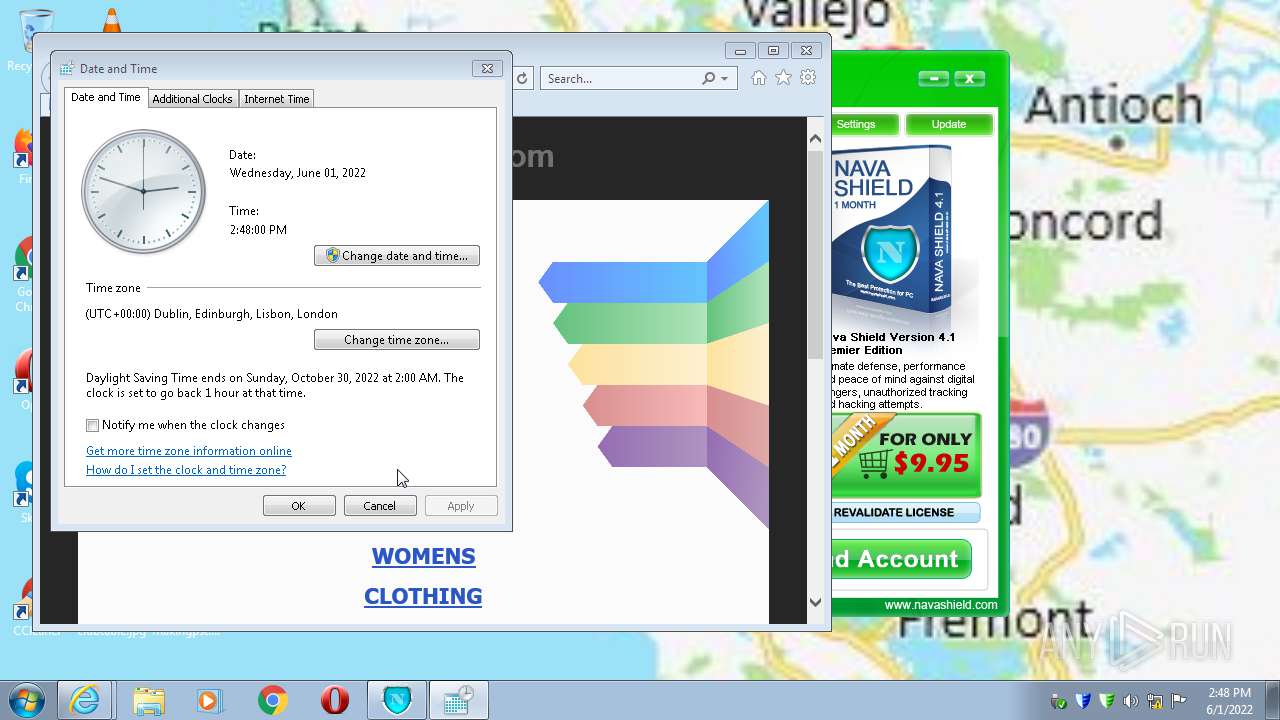
Reads the time zone
- rundll32.exe (PID: 3952)
INFO
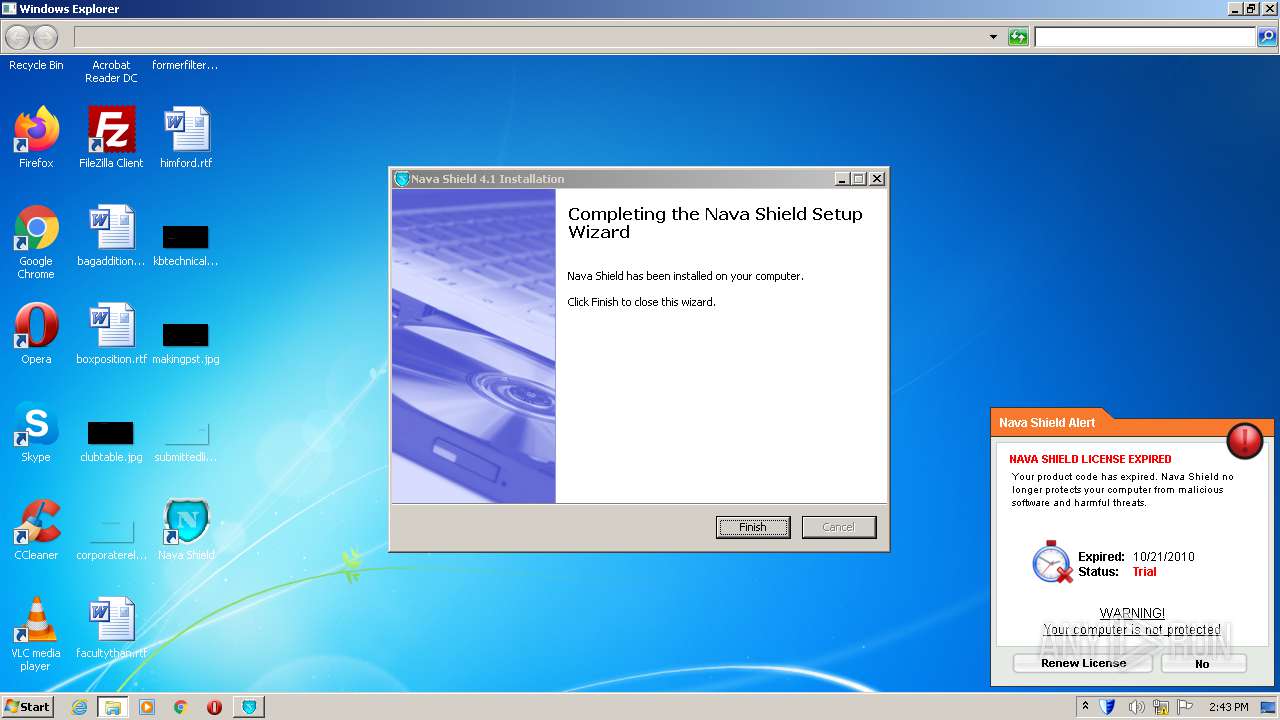
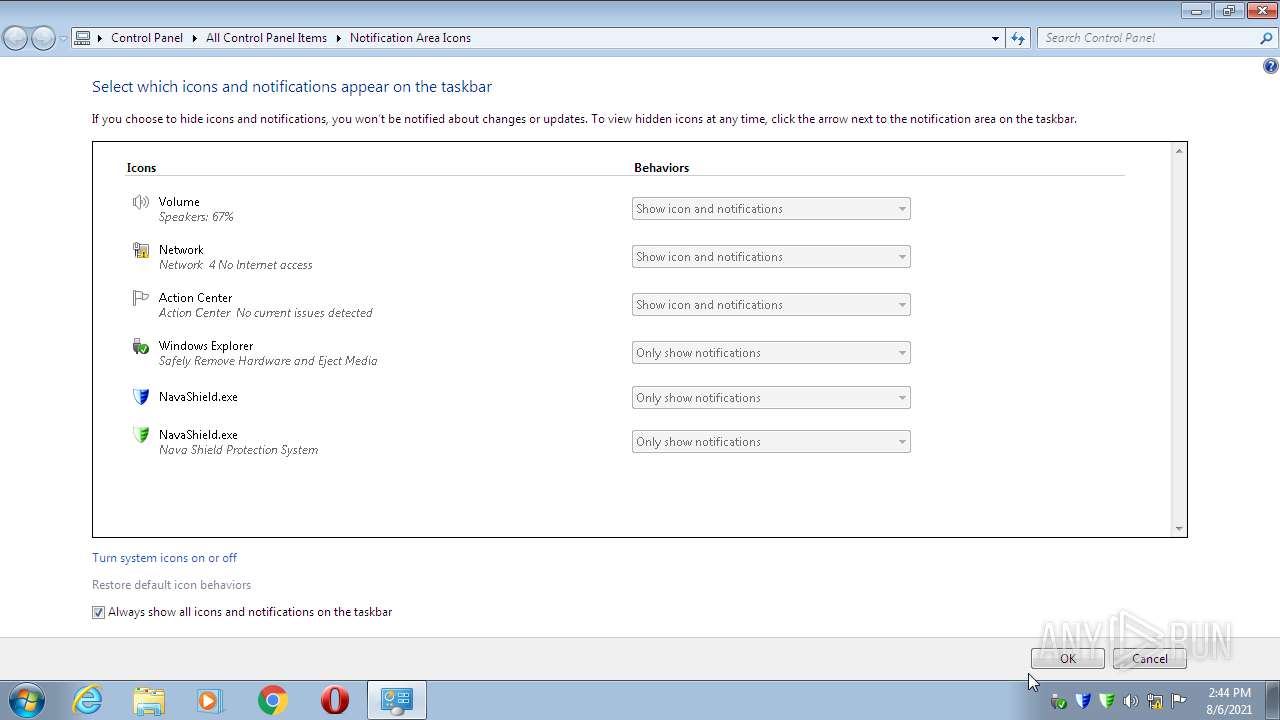
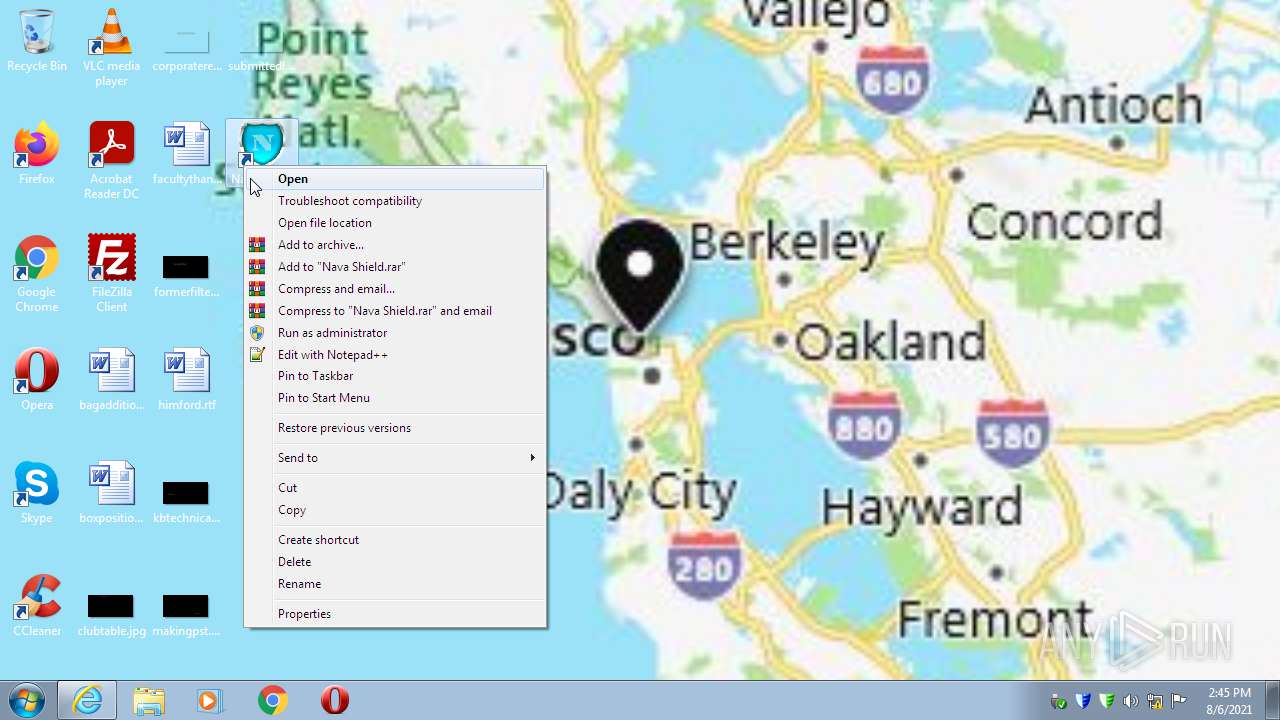
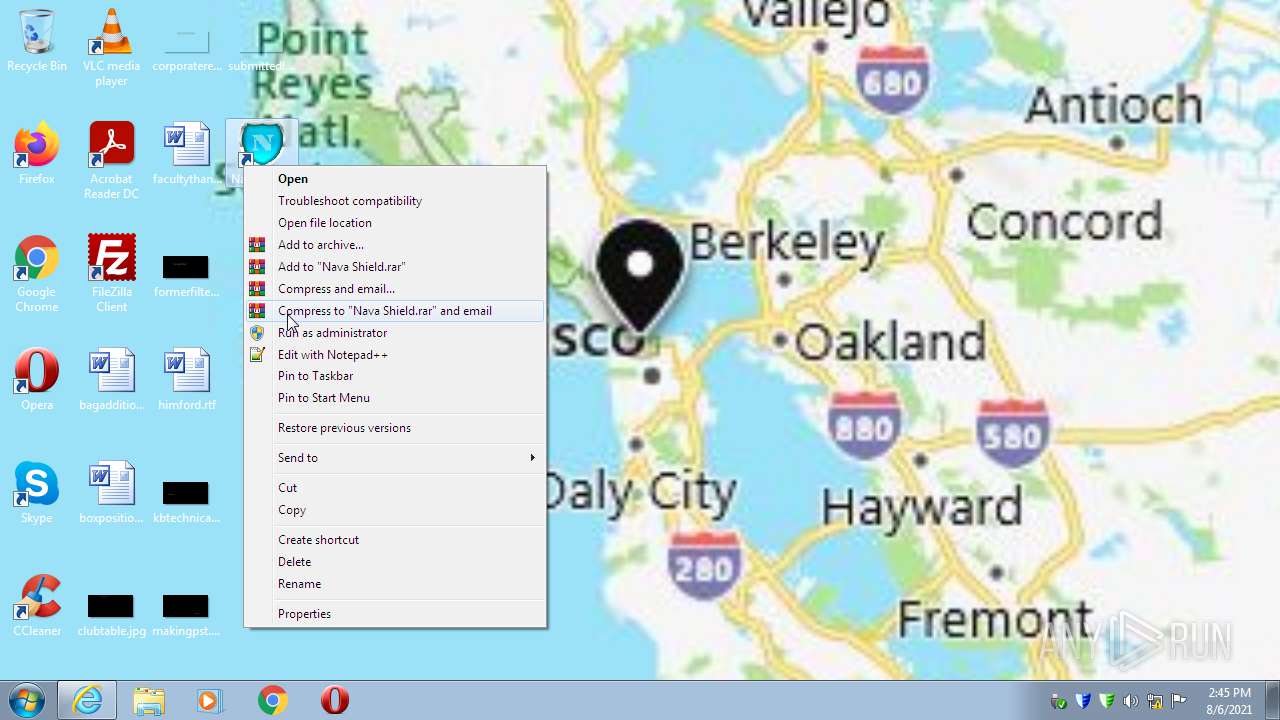
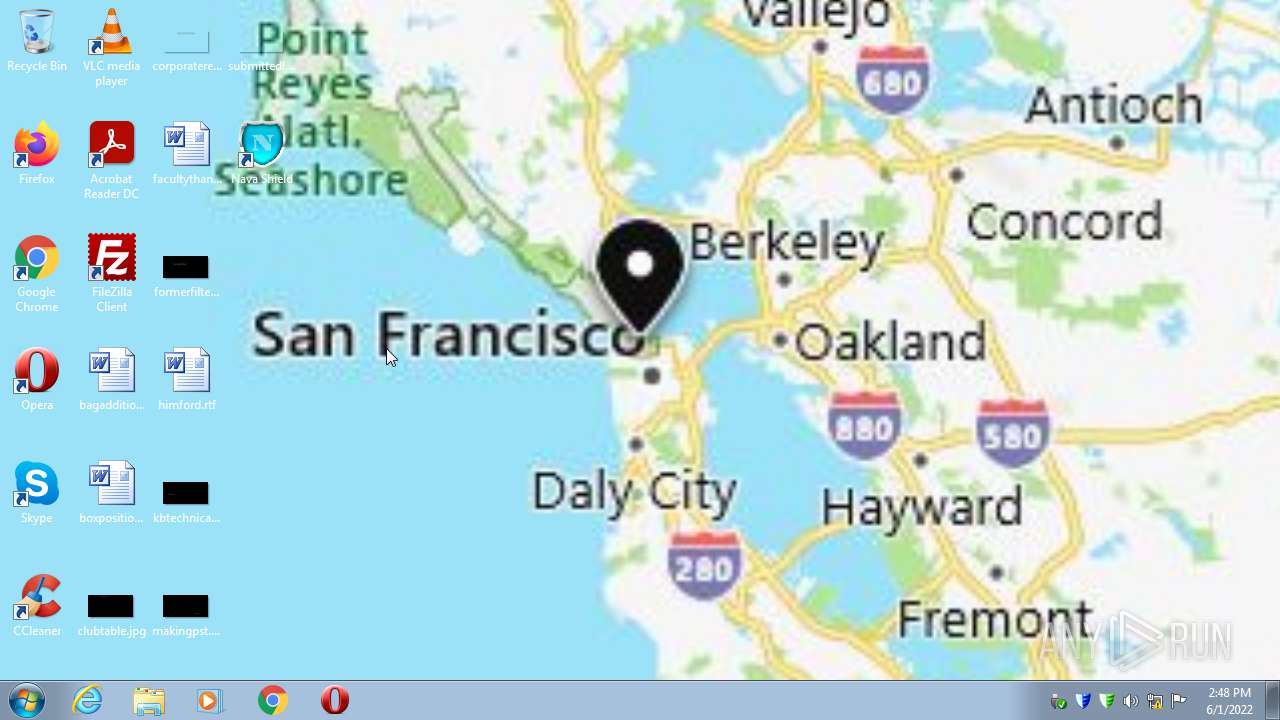
Manual execution by user
- NavaShield.exe (PID: 3612)
- NavaShield.exe (PID: 520)
- NavaShield.exe (PID: 1140)
- control.exe (PID: 2284)
Checks supported languages
- iexplore.exe (PID: 1512)
- iexplore.exe (PID: 3756)
- iexplore.exe (PID: 2068)
- DllHost.exe (PID: 908)
- control.exe (PID: 2284)
- rundll32.exe (PID: 3952)
- DllHost.exe (PID: 3896)
Application launched itself
- iexplore.exe (PID: 3756)
Changes internet zones settings
- iexplore.exe (PID: 3756)
Reads the computer name
- iexplore.exe (PID: 1512)
- iexplore.exe (PID: 3756)
- iexplore.exe (PID: 2068)
- DllHost.exe (PID: 908)
- control.exe (PID: 2284)
- rundll32.exe (PID: 3952)
- DllHost.exe (PID: 3896)
Creates files in the user directory
- iexplore.exe (PID: 1512)
- iexplore.exe (PID: 3756)
- iexplore.exe (PID: 2068)
Reads settings of System Certificates
- iexplore.exe (PID: 1512)
- iexplore.exe (PID: 3756)
- iexplore.exe (PID: 2068)
Reads internet explorer settings
- iexplore.exe (PID: 1512)
- iexplore.exe (PID: 2068)
Checks Windows Trust Settings
- iexplore.exe (PID: 3756)
- iexplore.exe (PID: 1512)
- iexplore.exe (PID: 2068)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3756)
- iexplore.exe (PID: 2068)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3756)
Changes settings of System certificates
- iexplore.exe (PID: 3756)
- iexplore.exe (PID: 2068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| LegalCopyright: | Nava Labs |
|---|---|
| FileVersion: | 4.1 |
| FileDescription: | Nava Shield 4.1 Installation |
| CompanyName: | Nava Labs |
| Comments: | - |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 4.1.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x25468 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 320000 |
| CodeSize: | 148992 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Nava Labs |
| FileDescription: | Nava Shield 4.1 Installation |
| FileVersion: | 4.1 |
| LegalCopyright: | Nava Labs |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x0004830C | 0x00048400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.02875 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 4.09909 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 4.03587 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 3.39783 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 4.95382 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
54 | 5.03612 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
55 | 4.99088 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
56 | 4.85001 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
66
Monitored processes
15
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 412 | "C:\Users\admin\AppData\Local\Temp\Endermanch@NavaShield.exe" | C:\Users\admin\AppData\Local\Temp\Endermanch@NavaShield.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Nava Labs Integrity Level: MEDIUM Description: Nava Shield 4.1 Installation Exit code: 3221226540 Version: 4.1 Modules
| |||||||||||||||
| 416 | "C:\Nava Labs\Nava Shield\NavaBridge.exe" | C:\Nava Labs\Nava Shield\NavaBridge.exe | NavaShield.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 520 | "C:\Nava Labs\Nava Shield\NavaShield.exe" | C:\Nava Labs\Nava Shield\NavaShield.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 908 | C:\Windows\system32\DllHost.exe /Processid:{3EB3C877-1F16-487C-9050-104DBCD66683} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1140 | "C:\Nava Labs\Nava Shield\NavaShield.exe" | C:\Nava Labs\Nava Shield\NavaShield.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3756 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3756 CREDAT:996364 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2284 | "C:\Windows\System32\control.exe" "C:\Windows\System32\timedate.cpl", | C:\Windows\System32\control.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3072 | "C:\Users\admin\AppData\Local\Temp\Endermanch@NavaShield.exe" | C:\Users\admin\AppData\Local\Temp\Endermanch@NavaShield.exe | Explorer.EXE | ||||||||||||
User: admin Company: Nava Labs Integrity Level: HIGH Description: Nava Shield 4.1 Installation Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 3612 | "C:\Nava Labs\Nava Shield\NavaShield.exe" | C:\Nava Labs\Nava Shield\NavaShield.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
29 854
Read events
29 454
Write events
398
Delete events
2
Modification events
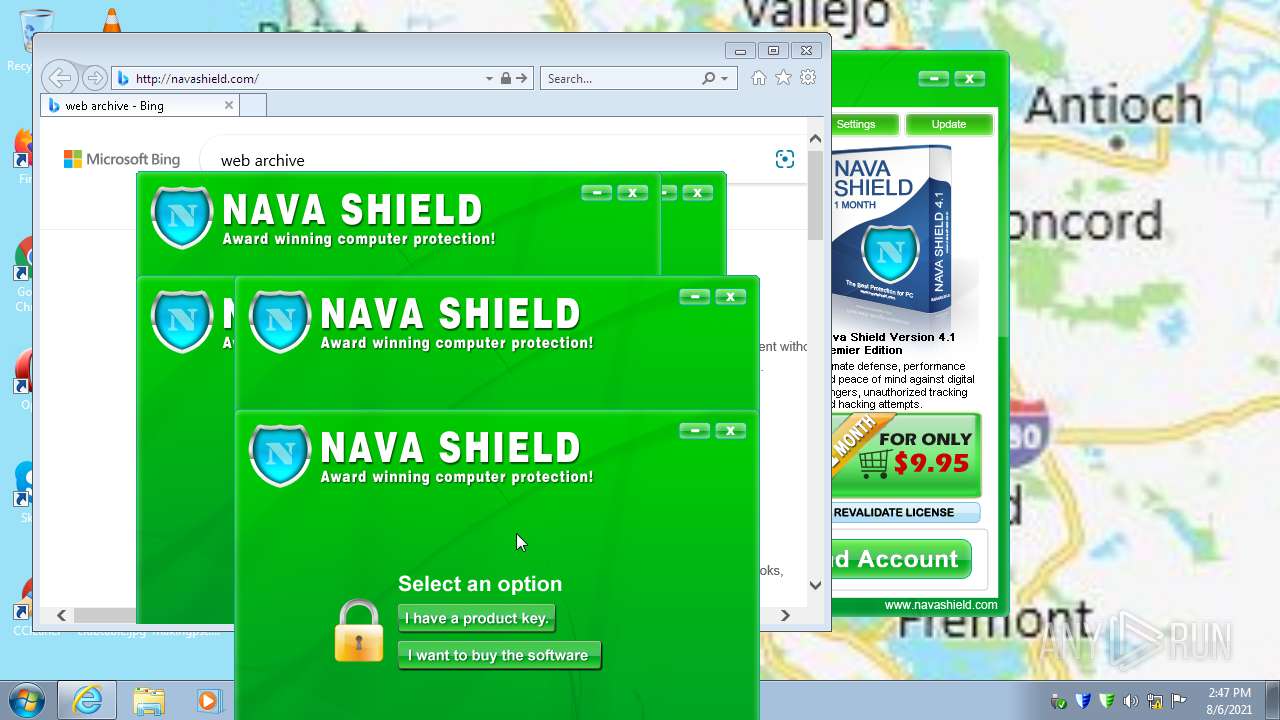
| (PID) Process: | (3072) Endermanch@NavaShield.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | NavaShield |
Value: c:\Nava Labs\Nava Shield\navashield.exe | |||
| (PID) Process: | (3072) Endermanch@NavaShield.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Nava Shield 4.1 |
| Operation: | write | Name: | DisplayName |
Value: Nava Shield 4.1 | |||
| (PID) Process: | (3072) Endermanch@NavaShield.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Nava Shield 4.1 |
| Operation: | write | Name: | DisplayVersion |
Value: 4.1 | |||
| (PID) Process: | (3072) Endermanch@NavaShield.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Nava Shield 4.1 |
| Operation: | write | Name: | VersionMajor |
Value: 4 | |||
| (PID) Process: | (3072) Endermanch@NavaShield.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Nava Shield 4.1 |
| Operation: | write | Name: | VersionMinor |
Value: 1 | |||
| (PID) Process: | (3072) Endermanch@NavaShield.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Nava Shield 4.1 |
| Operation: | write | Name: | Publisher |
Value: Nava Labs | |||
| (PID) Process: | (3072) Endermanch@NavaShield.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Nava Shield 4.1 |
| Operation: | write | Name: | DisplayIcon |
Value: c:\Nava Labs\Nava Shield\UninstallNava.exe | |||
| (PID) Process: | (3072) Endermanch@NavaShield.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Nava Shield 4.1 |
| Operation: | write | Name: | UninstallString |
Value: c:\Nava Labs\Nava Shield\UninstallNava.exe | |||
| (PID) Process: | (3072) Endermanch@NavaShield.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Nava Shield 4.1 |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.navashield.com/ | |||
| (PID) Process: | (3072) Endermanch@NavaShield.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Nava Shield 4.1 |
| Operation: | write | Name: | InstallLocation |
Value: c:\Nava Labs\Nava Shield\ | |||
Executable files
12
Suspicious files
21
Text files
227
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3072 | Endermanch@NavaShield.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 3072 | Endermanch@NavaShield.exe | C:\Nava Labs\Nava Shield\bridge.dat | binary | |
MD5:E66F1107F995D52BCD90421B3CDC0DDE | SHA256:45FA6EACEA58E682C2EF2BB9E888CB6BF396C37B957FD144CA73C95699AD3C74 | |||
| 3072 | Endermanch@NavaShield.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:37A639FC899D0C312AF607BE808B5E4D | SHA256:8ECAD2A44EBB53CEF96FDF4D6A695B729FC2027408421A194F290A31E28B9790 | |||
| 3072 | Endermanch@NavaShield.exe | C:\Nava Labs\Nava Shield\config.dat | binary | |
MD5:389BF6E15AE0A7250F454DA52AA7CED5 | SHA256:5993325ACFE309946C176737A019AA16E22B921FA6387B766BF8BC8A504E220D | |||
| 3072 | Endermanch@NavaShield.exe | C:\Nava Labs\Nava Shield\freeset.dat | text | |
MD5:2C66614915A2EDAC8BD5489C957A2879 | SHA256:FD242B6EAED612C71FF90B17D10D129FF9B4B4969291303458EE817FE2FB3F06 | |||
| 3072 | Endermanch@NavaShield.exe | C:\Nava Labs\Nava Shield\install.log | text | |
MD5:33836EF8621FC8D2E5F3302FD3BFBC8C | SHA256:FE219EB5CC7DA3F928E816D65DCEC5FD8A727F34B026F681810DFCC2B9F395DA | |||
| 3072 | Endermanch@NavaShield.exe | C:\Nava Labs\Nava Shield\NavaBridge Libs\MD5.dll | executable | |
MD5:831295342C47B770BF7CC591A6916FA7 | SHA256:8341ECC0938CA6D90B7E0F02AF2D7E6B571C948A03A99D54AF61C4557C78D656 | |||
| 3072 | Endermanch@NavaShield.exe | C:\Users\admin\AppData\Local\Temp\$inst\4.tmp | image | |
MD5:5252FE76395E49A85C435D3431EE3927 | SHA256:5CA7C69BA0AA28276A718706CAE4E61520CB45FB34F32DE9FAC019B0574B2C1C | |||
| 3072 | Endermanch@NavaShield.exe | C:\Nava Labs\Nava Shield\NavaBridge Libs\Internet Encodings.dll | executable | |
MD5:DE5EEFA1B686E3D32E3AE265392492BD | SHA256:A50E56DFB68410A7927ECD50F55044756B54868E920E462671162D1961BFE744 | |||
| 3072 | Endermanch@NavaShield.exe | C:\Nava Labs\Nava Shield\NavaBridge Libs\Browser Plugin.dll | executable | |
MD5:912924F628E277BE9CC28A5F2A990CB9 | SHA256:BD474C5AAFCAA12F20DA5ECB29E17555B953ECA46B4F56588A72672A36D4A8EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
163
DNS requests
43
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
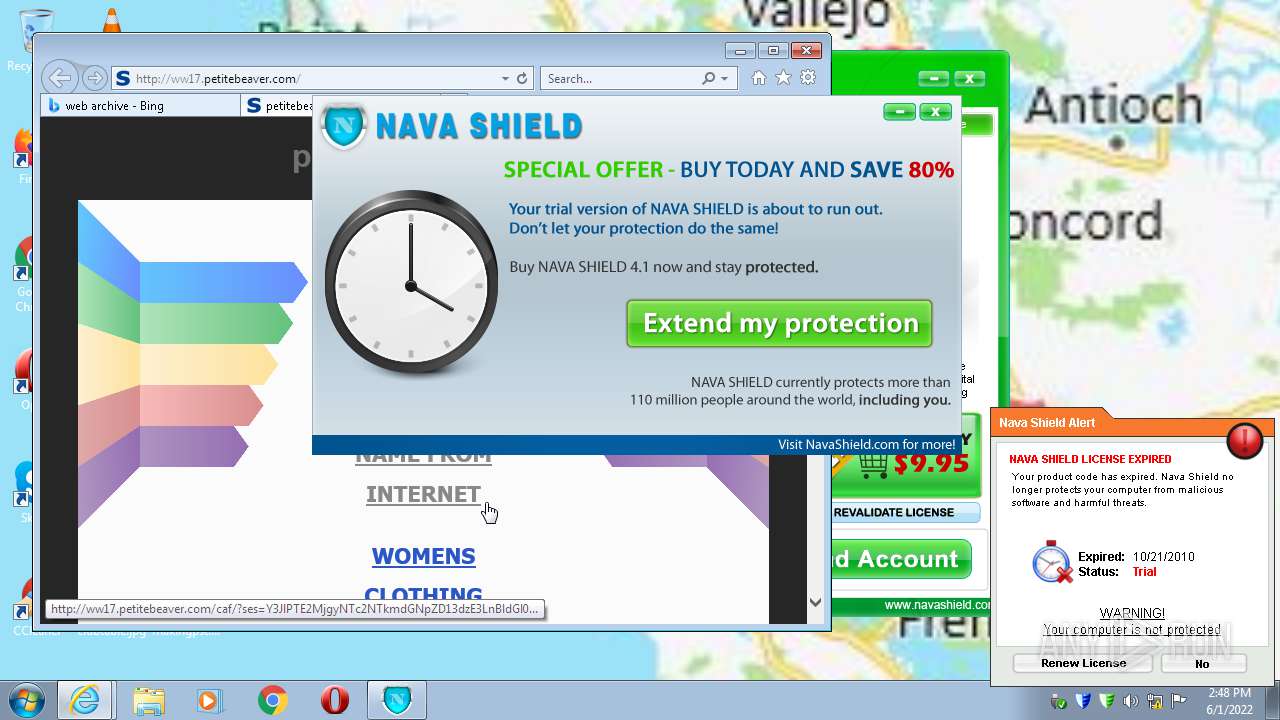
2068 | iexplore.exe | GET | 302 | 103.224.182.245:80 | http://www.petitebeaver.com/ | AU | — | — | malicious |
416 | NavaBridge.exe | GET | 200 | 208.91.196.74:80 | http://navashield.com/nava/offers?a=TNEQ7W7U4W&v=1&b=QLT0sgTt2oykpEhKnfDBwA== | VG | html | 272 b | malicious |
1512 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1512 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3852 | NavaShield.exe | POST | — | 208.91.196.74:80 | http://navashield.com/nava/license | VG | — | — | malicious |
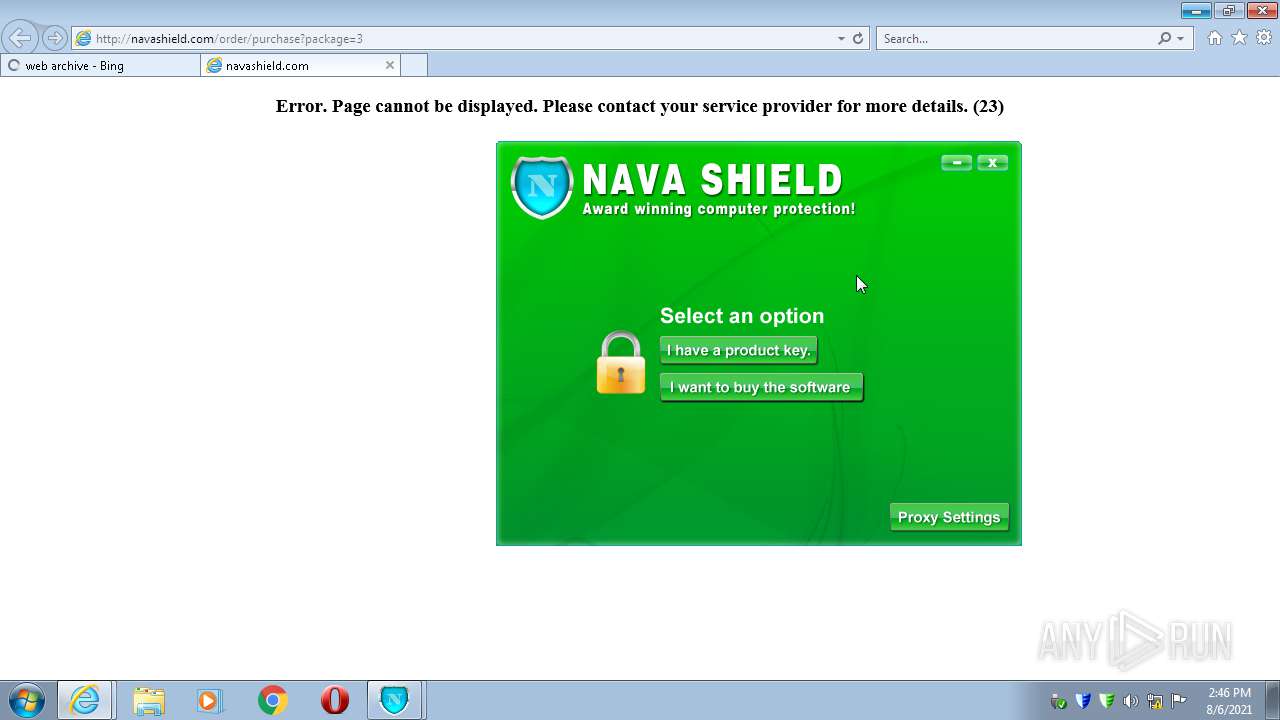
2068 | iexplore.exe | GET | 200 | 208.91.196.74:80 | http://navashield.com/order/purchase?package=3 | VG | html | 615 b | malicious |
1512 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA9bw6F2y3ieICDHiTyBZ7Q%3D | US | der | 1.47 Kb | whitelisted |
1512 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2068 | iexplore.exe | GET | 200 | 91.195.240.49:80 | http://ww17.petitebeaver.com/ | DE | html | 7.26 Kb | whitelisted |
2068 | iexplore.exe | GET | 200 | 216.58.212.164:80 | http://www.google.com/adsense/domains/caf.js | US | text | 56.0 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
416 | NavaBridge.exe | 208.91.196.74:80 | navashield.com | Confluence Networks Inc | VG | malicious |
1512 | iexplore.exe | 208.91.196.74:80 | navashield.com | Confluence Networks Inc | VG | malicious |
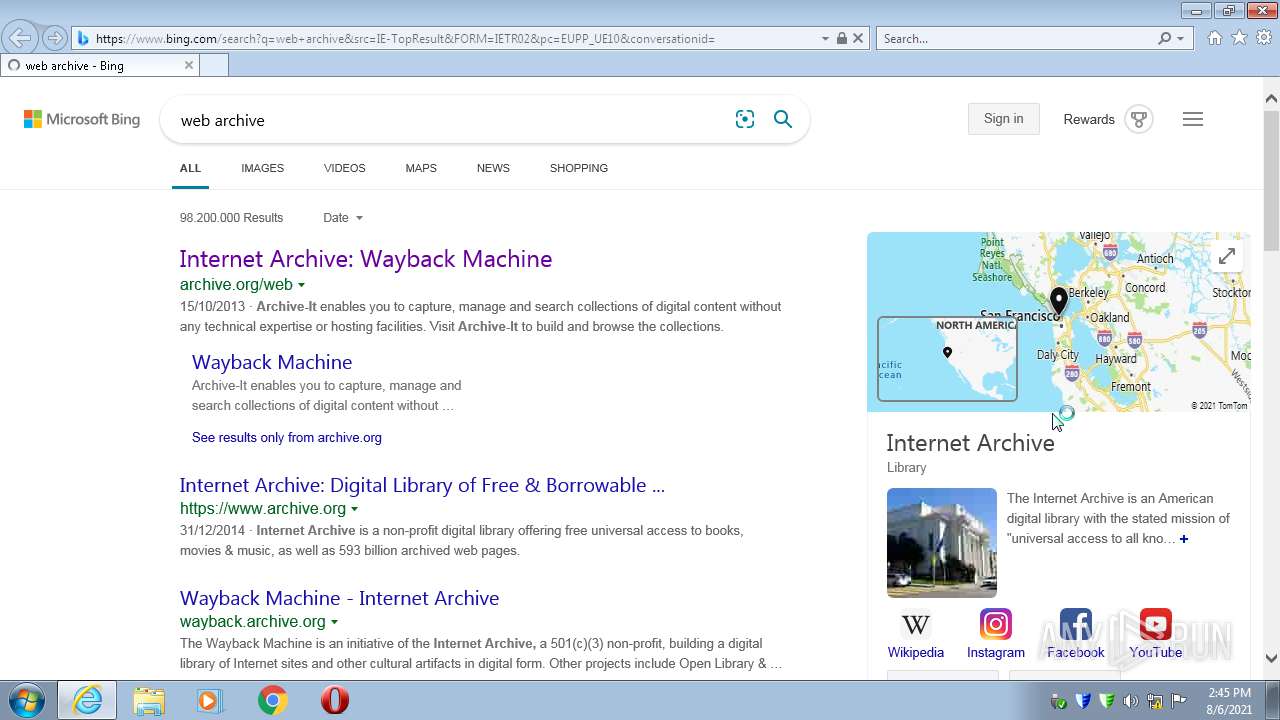
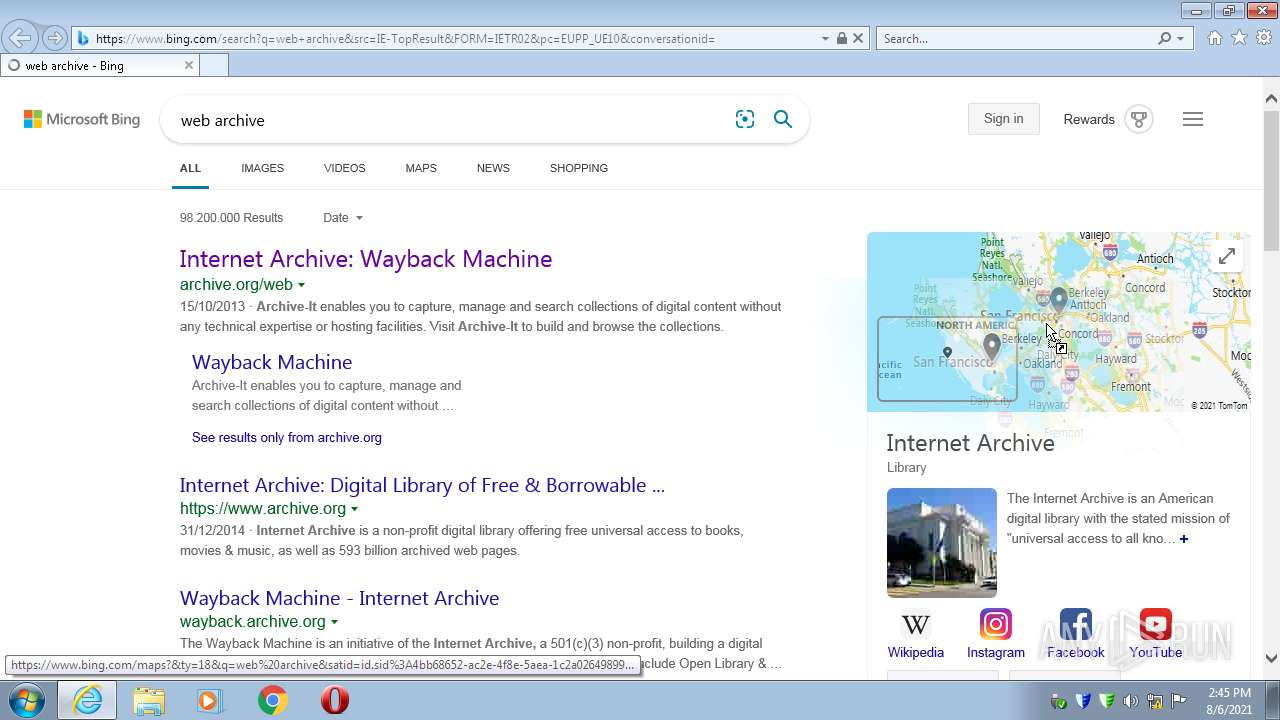
3756 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1512 | iexplore.exe | 13.107.5.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
1512 | iexplore.exe | 67.27.157.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1512 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1512 | iexplore.exe | 8.248.137.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1512 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1512 | iexplore.exe | 40.126.31.139:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
1512 | iexplore.exe | 207.241.224.2:80 | archive.org | Internet Archive | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
navashield.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
archive.org |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2068 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2068 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |