| File name: | 36w1djuloejycqul.exe |
| Full analysis: | https://app.any.run/tasks/5073a325-8b34-47af-939c-1b8561973e75 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2026, 13:53:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 3086F21F7370FB091DA5344EA2EE5691 |
| SHA1: | 4CA5258BFB1E344F571818B76F2E9BD89B12BCA5 |
| SHA256: | 83E0149FE826086FF93E7BD950CC8F74CED1974B05362BB0D475935ED8A1B426 |
| SSDEEP: | 12288:CxTyx0OvujKllh/ZJOJY5mpUHBroE6/ZznbhhRt8:CJyb9/rOwr9N |
MALICIOUS
Runs injected code in another process
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
Application was injected by another process
- MoUsoCoreWorker.exe (PID: 6768)
- winrshost.exe (PID: 3528)
- svchost.exe (PID: 7480)
- svchost.exe (PID: 2556)
- explorer.exe (PID: 4972)
- conhost.exe (PID: 9060)
- MusNotification.exe (PID: 4804)
- winrshost.exe (PID: 4656)
- conhost.exe (PID: 6528)
- svchost.exe (PID: 3140)
- svchost.exe (PID: 4316)
- winrshost.exe (PID: 7352)
- svchost.exe (PID: 568)
- svchost.exe (PID: 9040)
- fontdrvhost.exe (PID: 960)
- svchost.exe (PID: 4900)
- svchost.exe (PID: 1548)
- svchost.exe (PID: 3320)
- svchost.exe (PID: 2728)
- svchost.exe (PID: 924)
- fontdrvhost.exe (PID: 952)
- svchost.exe (PID: 1936)
- svchost.exe (PID: 1540)
- svchost.exe (PID: 4888)
- ShellExperienceHost.exe (PID: 972)
- svchost.exe (PID: 356)
- OfficeClickToRun.exe (PID: 3308)
- svchost.exe (PID: 3504)
- svchost.exe (PID: 4488)
- svchost.exe (PID: 2320)
- svchost.exe (PID: 1248)
- StartMenuExperienceHost.exe (PID: 5384)
- ctfmon.exe (PID: 4980)
- winrshost.exe (PID: 4108)
- UserOOBEBroker.exe (PID: 6840)
- svchost.exe (PID: 4672)
- RuntimeBroker.exe (PID: 5668)
- svchost.exe (PID: 2884)
- RUXIMICS.exe (PID: 9088)
- svchost.exe (PID: 3676)
- svchost.exe (PID: 3280)
- svchost.exe (PID: 1500)
- svchost.exe (PID: 2292)
- firefox.exe (PID: 4936)
- svchost.exe (PID: 3468)
- RuntimeBroker.exe (PID: 512)
- WmiPrvSE.exe (PID: 8108)
- svchost.exe (PID: 8516)
- svchost.exe (PID: 3292)
- svchost.exe (PID: 1712)
- conhost.exe (PID: 9000)
- svchost.exe (PID: 2104)
- RuntimeBroker.exe (PID: 5452)
- svchost.exe (PID: 3284)
- RuntimeBroker.exe (PID: 6160)
- svchost.exe (PID: 7092)
- svchost.exe (PID: 2072)
- svchost.exe (PID: 3452)
- svchost.exe (PID: 2660)
- TextInputHost.exe (PID: 3444)
- svchost.exe (PID: 2928)
- dllhost.exe (PID: 8560)
- slui.exe (PID: 6396)
- svchost.exe (PID: 2064)
- PLUGScheduler.exe (PID: 8564)
- svchost.exe (PID: 1272)
- svchost.exe (PID: 7008)
- svchost.exe (PID: 2472)
- svchost.exe (PID: 500)
- svchost.exe (PID: 2648)
- SearchApp.exe (PID: 5568)
- svchost.exe (PID: 2440)
- svchost.exe (PID: 6680)
- svchost.exe (PID: 3424)
- svchost.exe (PID: 1256)
- svchost.exe (PID: 772)
- svchost.exe (PID: 1072)
- svchost.exe (PID: 2644)
- svchost.exe (PID: 1264)
- slui.exe (PID: 6956)
- svchost.exe (PID: 1828)
- dasHost.exe (PID: 3024)
- svchost.exe (PID: 1444)
- spoolsv.exe (PID: 2828)
- firefox.exe (PID: 8400)
- svchost.exe (PID: 2992)
- svchost.exe (PID: 7160)
- svchost.exe (PID: 5188)
- svchost.exe (PID: 3412)
- svchost.exe (PID: 3012)
- RuntimeBroker.exe (PID: 7732)
- dwm.exe (PID: 840)
- svchost.exe (PID: 1532)
- slui.exe (PID: 6568)
- svchost.exe (PID: 1224)
- svchost.exe (PID: 2724)
- svchost.exe (PID: 1812)
- svchost.exe (PID: 1804)
- slui.exe (PID: 2868)
- winrshost.exe (PID: 816)
- uhssvc.exe (PID: 4716)
- svchost.exe (PID: 2588)
- svchost.exe (PID: 6168)
- SppExtComObj.Exe (PID: 3168)
- svchost.exe (PID: 1796)
- default-browser-agent.exe (PID: 1908)
- dllhost.exe (PID: 1476)
- ApplicationFrameHost.exe (PID: 6520)
- dllhost.exe (PID: 5744)
- lsass.exe (PID: 804)
- svchost.exe (PID: 6712)
- taskhostw.exe (PID: 7296)
- svchost.exe (PID: 3360)
- sihost.exe (PID: 4460)
- svchost.exe (PID: 1216)
- svchost.exe (PID: 1032)
- conhost.exe (PID: 6532)
- svchost.exe (PID: 4532)
- svchost.exe (PID: 5644)
- conhost.exe (PID: 6556)
- svchost.exe (PID: 7376)
- audiodg.exe (PID: 5404)
- conhost.exe (PID: 8824)
- TrustedInstaller.exe (PID: 476)
- WaaSMedicAgent.exe (PID: 7964)
Disables Windows Defender
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
Changes the login/logoff helper path in the registry
- 36w1djuloejycqul.exe (PID: 8396)
Creates or modifies Windows services
- 36w1djuloejycqul.exe (PID: 8396)
Starts NET.EXE for service management
- cmd.exe (PID: 416)
- net.exe (PID: 1400)
- cmd.exe (PID: 2256)
- net.exe (PID: 3652)
- cmd.exe (PID: 6284)
- net.exe (PID: 2496)
- net.exe (PID: 5896)
- cmd.exe (PID: 6804)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 4312)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7748)
SUSPICIOUS
Executable content was dropped or overwritten
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6852)
- cmd.exe (PID: 8784)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 416)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 4312)
- cmd.exe (PID: 2256)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 6796)
- cmd.exe (PID: 756)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 3348)
- cmd.exe (PID: 8268)
- cmd.exe (PID: 288)
- cmd.exe (PID: 8760)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 2416)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 9032)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 5636)
- cmd.exe (PID: 6284)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 6804)
- cmd.exe (PID: 8892)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 2228)
- cmd.exe (PID: 1232)
- cmd.exe (PID: 4216)
- cmd.exe (PID: 8576)
- cmd.exe (PID: 1520)
- cmd.exe (PID: 2256)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 752)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 2872)
- cmd.exe (PID: 7740)
- cmd.exe (PID: 1424)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 664)
Stops a currently running service
- sc.exe (PID: 6796)
- sc.exe (PID: 3332)
- sc.exe (PID: 1856)
The process creates files with name similar to system file names
- 36w1djuloejycqul.exe (PID: 8396)
Windows service management via SC.EXE
- sc.exe (PID: 7476)
- sc.exe (PID: 5356)
- sc.exe (PID: 7024)
- sc.exe (PID: 4940)
Checks for external IP
- svchost.exe (PID: 2292)
Creates scheduled task with ONLOGON parameter
- cmd.exe (PID: 4312)
- 36w1djuloejycqul.exe (PID: 8396)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 1656)
- schtasks.exe (PID: 3544)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 5964)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 9032)
- cmd.exe (PID: 3348)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 8268)
- cmd.exe (PID: 288)
- cmd.exe (PID: 8760)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 2256)
- cmd.exe (PID: 1232)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 2228)
- cmd.exe (PID: 8892)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 664)
- cmd.exe (PID: 752)
- cmd.exe (PID: 2872)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 7740)
- cmd.exe (PID: 4216)
Creates files in the driver directory
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
Drops a system driver (possible attempt to evade defenses)
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
Possibly patching Antimalware Scan Interface function (YARA)
- RuntimeBroker.exe (PID: 7732)
Creates scheduled task with highest privileges
- cmd.exe (PID: 7748)
- schtasks.exe (PID: 8324)
Reads the date of Windows installation
- 36w1djuloejycqul.exe (PID: 8396)
Starts itself from another location
- 36w1djuloejycqul.exe (PID: 8396)
The process executes files with name similar to system file names
- 36w1djuloejycqul.exe (PID: 8396)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 4972)
- 36w1djuloejycqul.exe (PID: 8396)
Disables trace logs
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
Reads Windows Product ID
- WmiPrvSE.exe (PID: 8108)
Reads Environment values
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
Reads the computer name
- 36w1djuloejycqul.exe (PID: 8396)
- TrustedInstaller.exe (PID: 476)
- AntiMalware Services.exe (PID: 6400)
- PLUGScheduler.exe (PID: 8564)
Reads the machine GUID from the registry
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
- SearchApp.exe (PID: 5568)
Checks supported languages
- 36w1djuloejycqul.exe (PID: 8396)
- TrustedInstaller.exe (PID: 476)
- PLUGScheduler.exe (PID: 8564)
- default-browser-agent.exe (PID: 1908)
- AntiMalware Services.exe (PID: 6400)
- SearchApp.exe (PID: 5568)
- StartMenuExperienceHost.exe (PID: 5384)
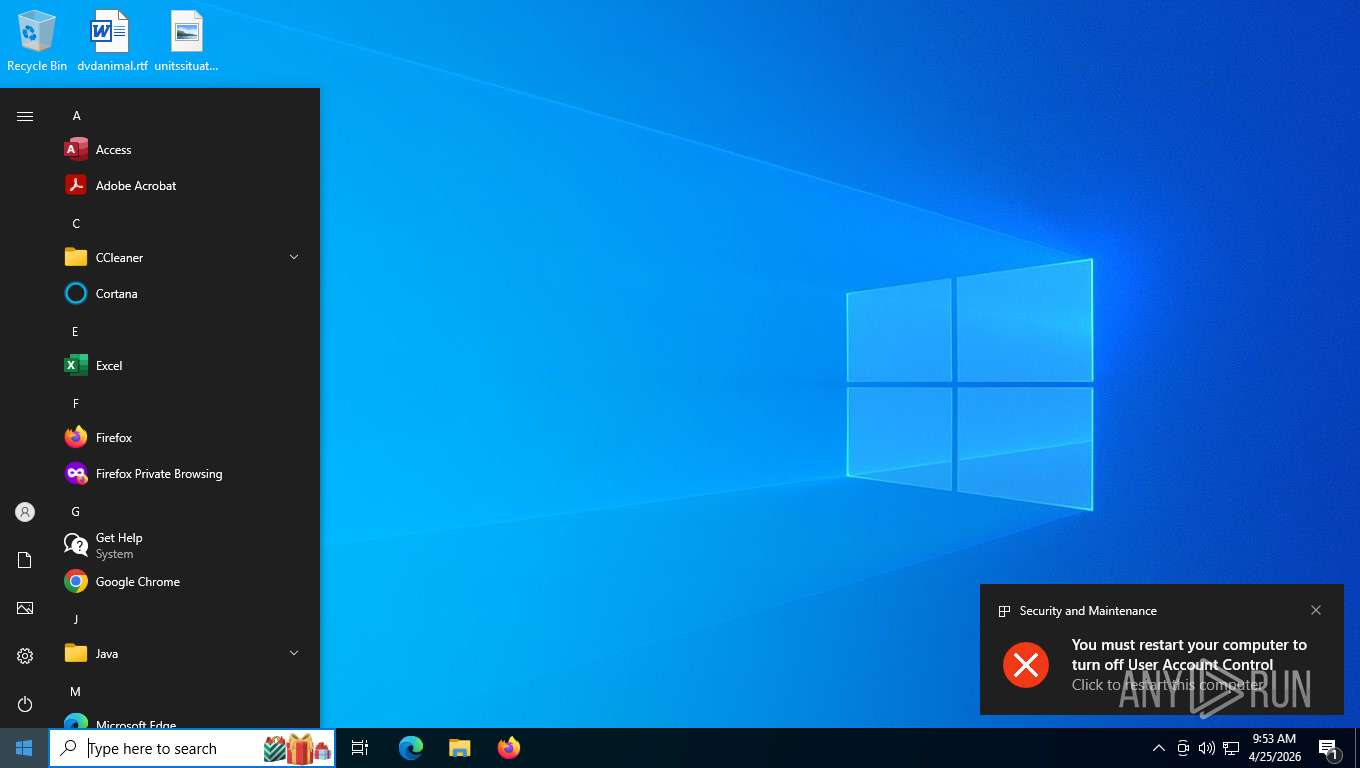
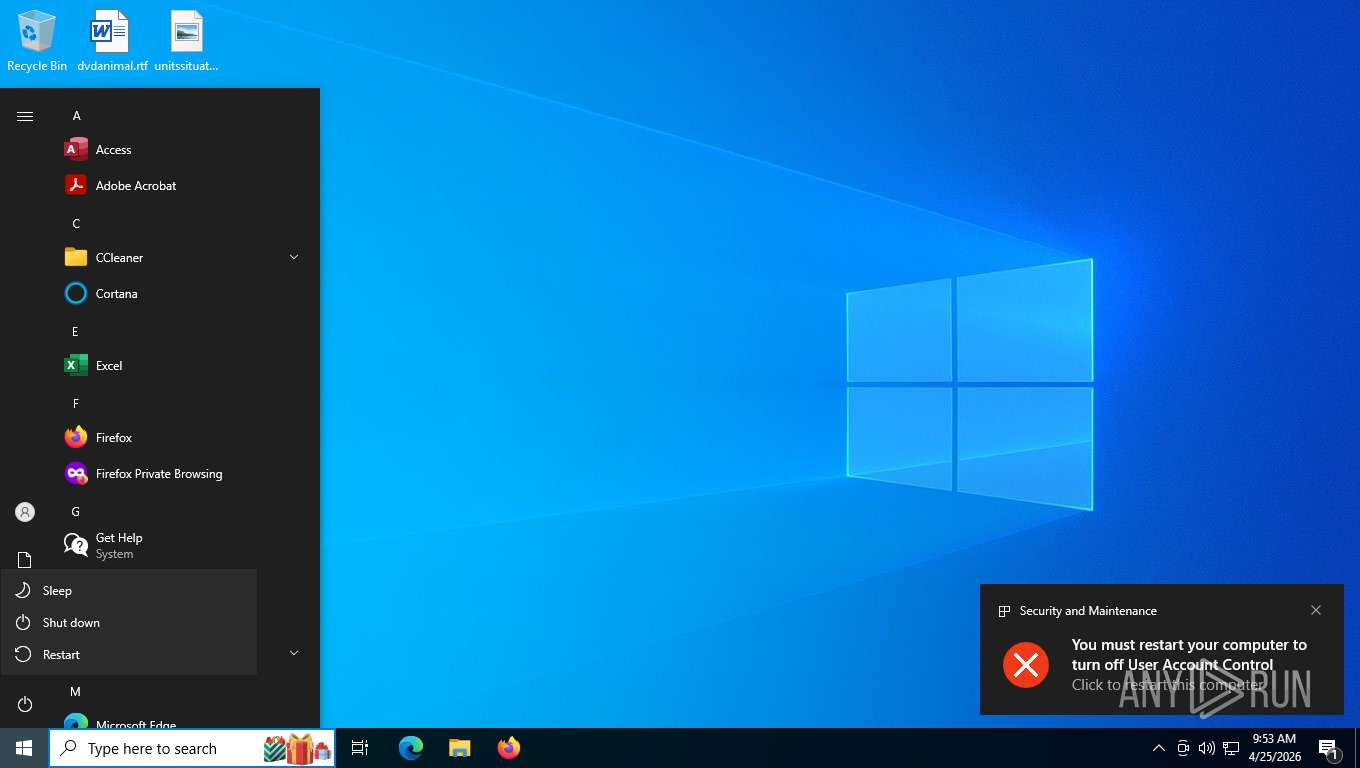
Process checks whether UAC notifications are on
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
Create files in a temporary directory
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
Creates files or folders in the user directory
- 36w1djuloejycqul.exe (PID: 8396)
- lsass.exe (PID: 804)
Creating file in SysWOW64
- 36w1djuloejycqul.exe (PID: 8396)
Drops encrypted JS script (Microsoft Script Encoder)
- svchost.exe (PID: 1224)
The sample compiled with english language support
- 36w1djuloejycqul.exe (PID: 8396)
- AntiMalware Services.exe (PID: 6400)
Launching a file from Task Scheduler
- cmd.exe (PID: 7748)
Process checks computer location settings
- 36w1djuloejycqul.exe (PID: 8396)
- SearchApp.exe (PID: 5568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2026:03:15 13:00:37+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 381952 |
| InitializedDataSize: | 13824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Client |
| FileVersion: | 1.0.0.0 |
| InternalName: | Client.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | Client.exe |
| ProductName: | Client |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
298
Monitored processes
275
Malicious processes
5
Suspicious processes
78
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | "cmd.exe" /c icacls "C:\WINDOWS\system32\drivers\serenum.sys" /grant administrators:F /t /c | C:\Windows\System32\cmd.exe | 36w1djuloejycqul.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 356 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s wlidsvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 416 | "cmd.exe" /c net stop WinDefend | C:\Windows\System32\cmd.exe | 36w1djuloejycqul.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 476 | C:\WINDOWS\servicing\TrustedInstaller.exe | C:\Windows\servicing\TrustedInstaller.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 500 | C:\WINDOWS\system32\svchost.exe -k RPCSS -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 568 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p -s LSM | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "cmd.exe" /c icacls "C:\WINDOWS\system32\drivers\parport.sys.bak" /grant administrators:F | C:\Windows\System32\cmd.exe | AntiMalware Services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "cmd.exe" /c icacls "C:\WINDOWS\system32\drivers\parport.sys" /grant administrators:F /t /c | C:\Windows\System32\cmd.exe | AntiMalware Services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | "cmd.exe" /c mountvol E: /D | C:\Windows\System32\cmd.exe | — | 36w1djuloejycqul.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
48 688
Read events
47 807
Write events
552
Delete events
329
Modification events
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{83ca2343-c25b-d824-0294-11f78b25391a}\Root\InventoryDevicePnp |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{83ca2343-c25b-d824-0294-11f78b25391a}\Root\InventoryDevicePnp\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{83ca2343-c25b-d824-0294-11f78b25391a}\Root\InventoryDeviceContainer |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{83ca2343-c25b-d824-0294-11f78b25391a}\Root\InventoryDeviceContainer\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{83ca2343-c25b-d824-0294-11f78b25391a}\Root\InventoryDriverBinary |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{83ca2343-c25b-d824-0294-11f78b25391a}\Root\InventoryDriverBinary\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{83ca2343-c25b-d824-0294-11f78b25391a}\Root\InventoryDeviceMediaClass |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{83ca2343-c25b-d824-0294-11f78b25391a}\Root\InventoryDeviceMediaClass\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{83ca2343-c25b-d824-0294-11f78b25391a}\Root\DriverPackageExtended |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (7092) svchost.exe | Key: | \REGISTRY\A\{83ca2343-c25b-d824-0294-11f78b25391a}\Root\DriverPackageExtended\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
289
Suspicious files
62
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1796 | svchost.exe | C:\Windows\Prefetch\CONSENT.EXE-531BD9EA.pf | binary | |
MD5:C3027082305F803B8E0FD66DC3F9AD83 | SHA256:1B22A83518D4135E33C9E80100969C61DA71AD3EE2D059751A94FCBB1F7275D4 | |||
| 1796 | svchost.exe | C:\Windows\Prefetch\SPPEXTCOMOBJ.EXE-BB03B3D6.pf | binary | |
MD5:6E65764439EC2F2962AB9342DB38F2B1 | SHA256:D4B352C63FBAFAA4B3B8F75175C9D583E2FAECE386AC3F0DA7E95AC6299377A1 | |||
| 7092 | svchost.exe | C:\Windows\appcompat\Programs\Amcache.hve | binary | |
MD5:92FCA268C228701FA54B911023E985C7 | SHA256:382C288A9AE8DE83B7D3520800F09F77D931D6B2ED00036225A51FF32326D236 | |||
| 1796 | svchost.exe | C:\Windows\Prefetch\SLUI.EXE-724E99D9.pf | binary | |
MD5:BC448B0E877D0236B978DDF47AEE2646 | SHA256:E0969CFCAA9D80528A755D1A6289D72B7CAFDD64F8BB9E37C9A7DFA1AAC0F4D6 | |||
| 1796 | svchost.exe | C:\Windows\Prefetch\SPPSVC.EXE-B0F8131B.pf | binary | |
MD5:4D3DEDF3ED7DD1B2F1365D4D9A60F41B | SHA256:D261FC725999735AD3F76BC78475F38D01EAAF7057526E9F8262EC5EBB4E12F9 | |||
| 1796 | svchost.exe | C:\Windows\Prefetch\HOST.EXE-1AA3DD74.pf | binary | |
MD5:857592984FEB3D856DFC31E211882B03 | SHA256:70399E6DD74E6E386F97833E901F54DC8011FE9E552AB7F854F9B60D6B83FBF3 | |||
| 8396 | 36w1djuloejycqul.exe | C:\Users\admin\AppData\Local\Temp\$77temp\484a70a6-bacf-4591-be6f-f75311c03fb8.dll | executable | |
MD5:6295C384C45EF898B40608F7AF8155DB | SHA256:FF95571A4B3880BE2807CAD8875EE6CCD0B2B705CAF0D4D0D0F56950DD78EE5A | |||
| 8396 | 36w1djuloejycqul.exe | C:\Users\admin\Desktop\driver_infector.log | text | |
MD5:8E8FD651588B9E0BBF87974862425997 | SHA256:67137B2818C62A548E9FCDCAAF58E6477E5C0D1C62CA6C0521BB4C7328638387 | |||
| 8396 | 36w1djuloejycqul.exe | C:\Users\admin\AppData\Local\Temp\$77temp\732ac554-b80b-4ce9-9e3c-da0d0c3d0753.dll | executable | |
MD5:6295C384C45EF898B40608F7AF8155DB | SHA256:FF95571A4B3880BE2807CAD8875EE6CCD0B2B705CAF0D4D0D0F56950DD78EE5A | |||
| 8396 | 36w1djuloejycqul.exe | C:\Users\admin\AppData\Local\Temp\$77temp\ff49466a-8363-49bb-b413-68d0d8714004.dll | executable | |
MD5:6295C384C45EF898B40608F7AF8155DB | SHA256:FF95571A4B3880BE2807CAD8875EE6CCD0B2B705CAF0D4D0D0F56950DD78EE5A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
21
DNS requests
15
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | text | 7.04 Kb | whitelisted |
8396 | 36w1djuloejycqul.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=query,country,countryCode | US | text | 28 b | unknown |
356 | svchost.exe | POST | 200 | 40.126.31.129:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
356 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
7004 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
7004 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | Not routed | — | whitelisted |
9088 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7004 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8396 | 36w1djuloejycqul.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
356 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
7004 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ip-api.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Misc activity | INFO [ANY.RUN] External IP Check (ip-api .com) |
2292 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7004 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6400 | AntiMalware Services.exe | Misc activity | HUNTING [ANY.RUN] TLS cert too long-lived (>2029-12-31) |