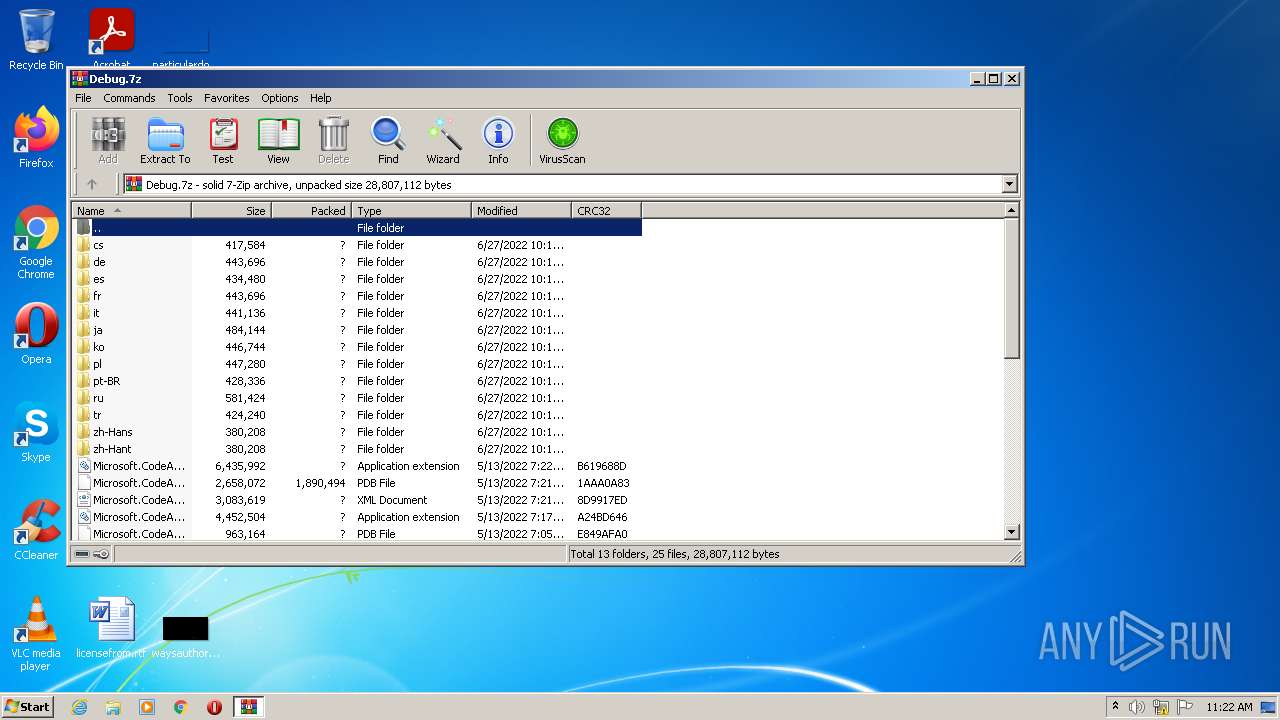
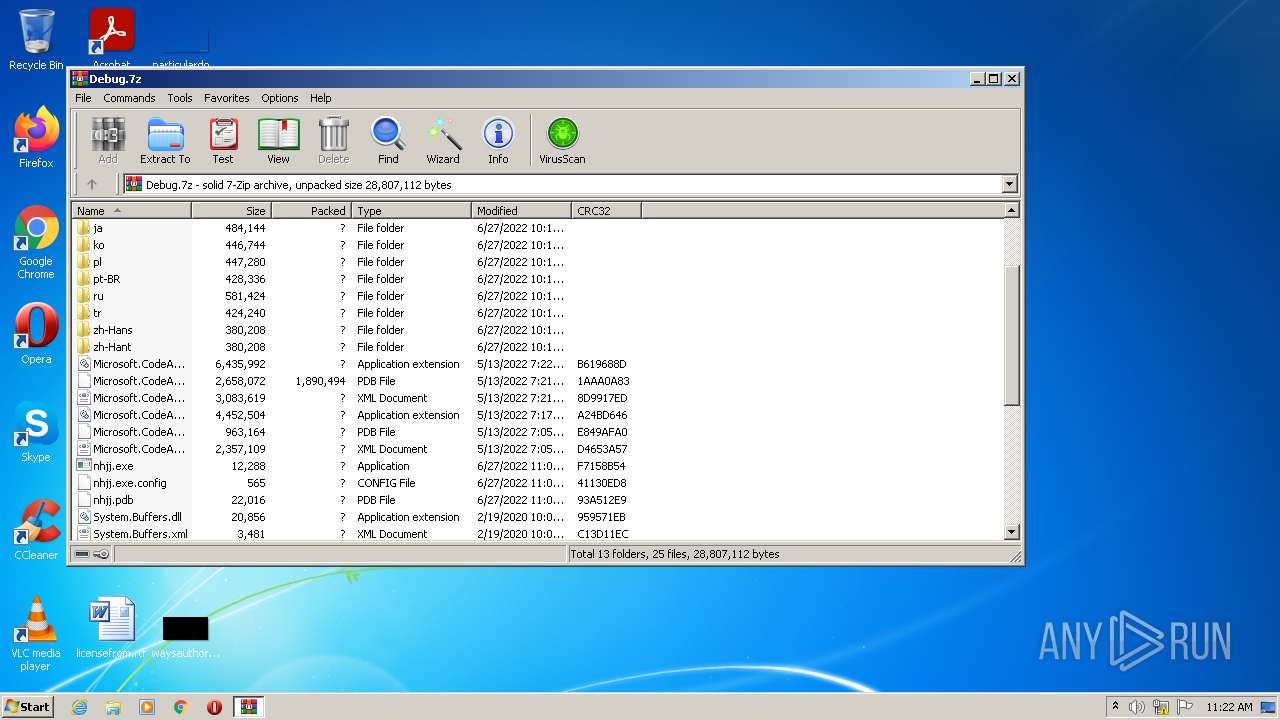
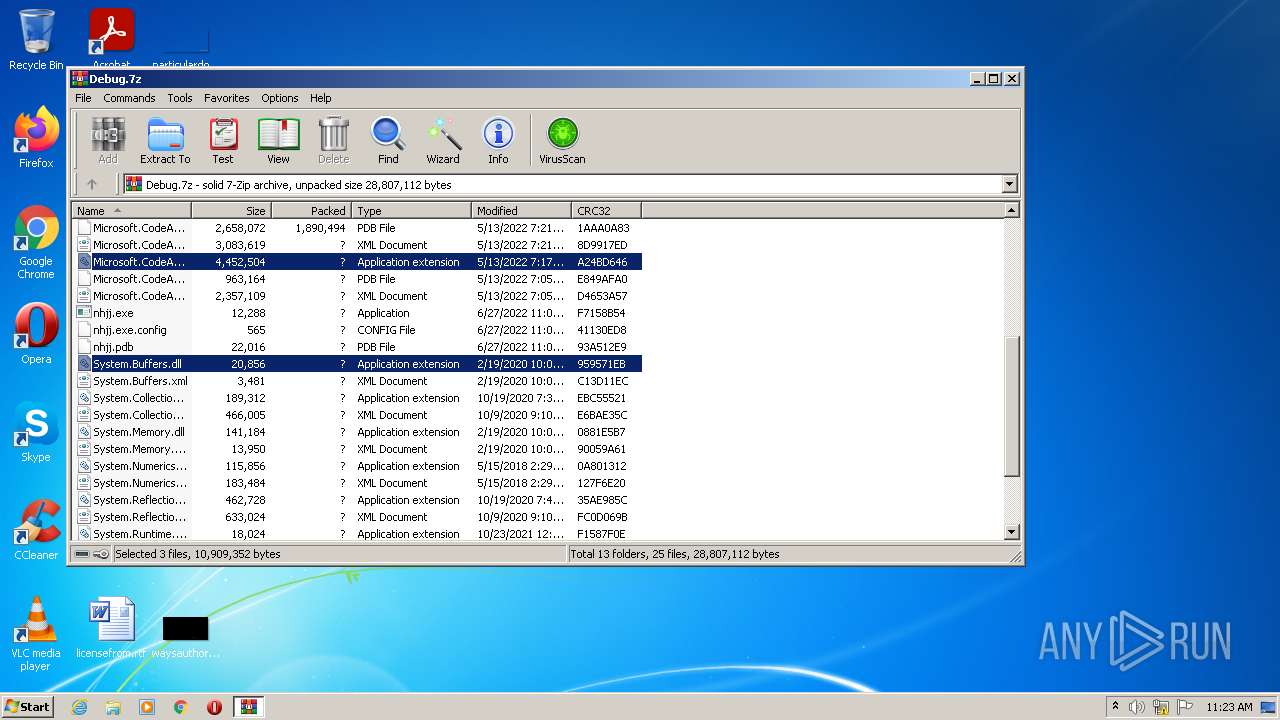
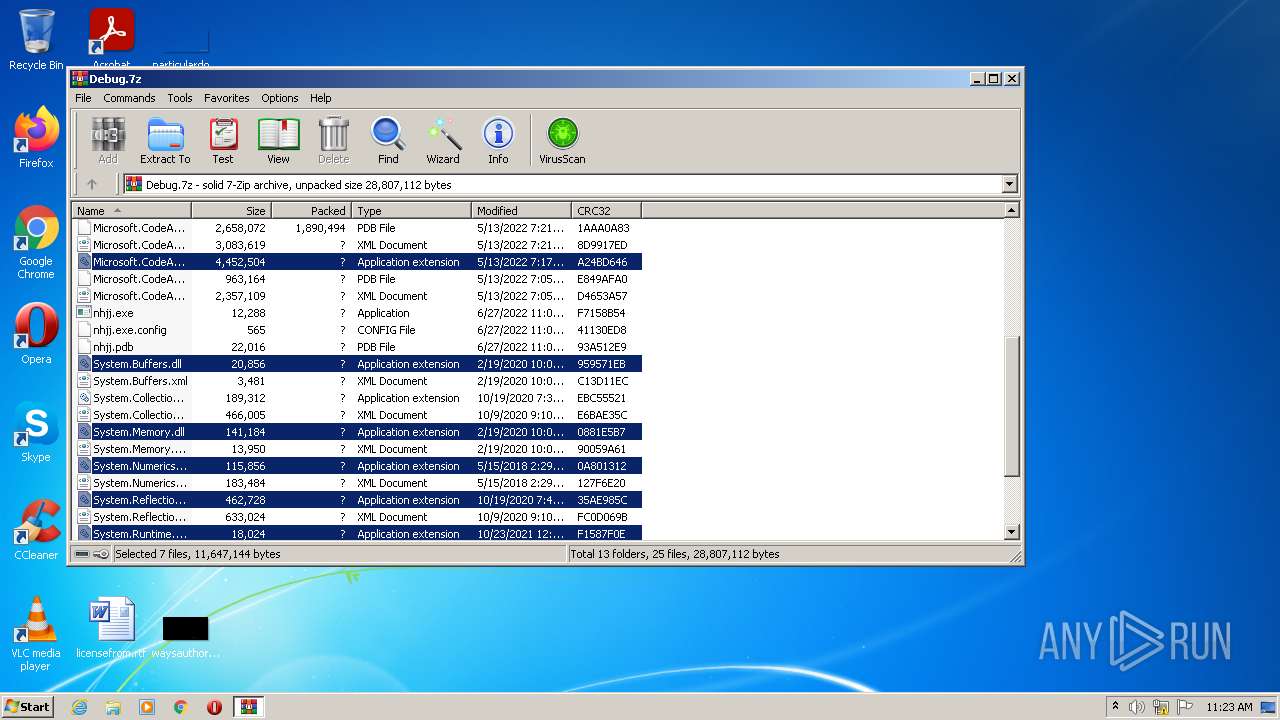
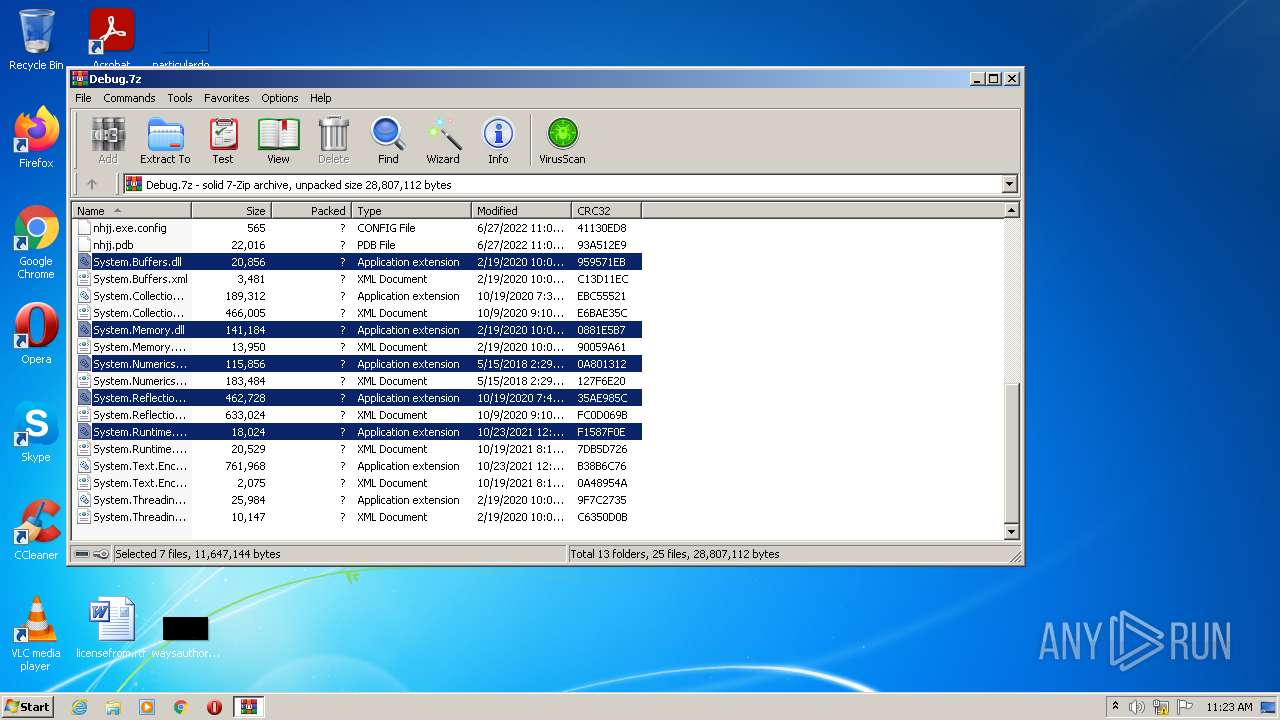
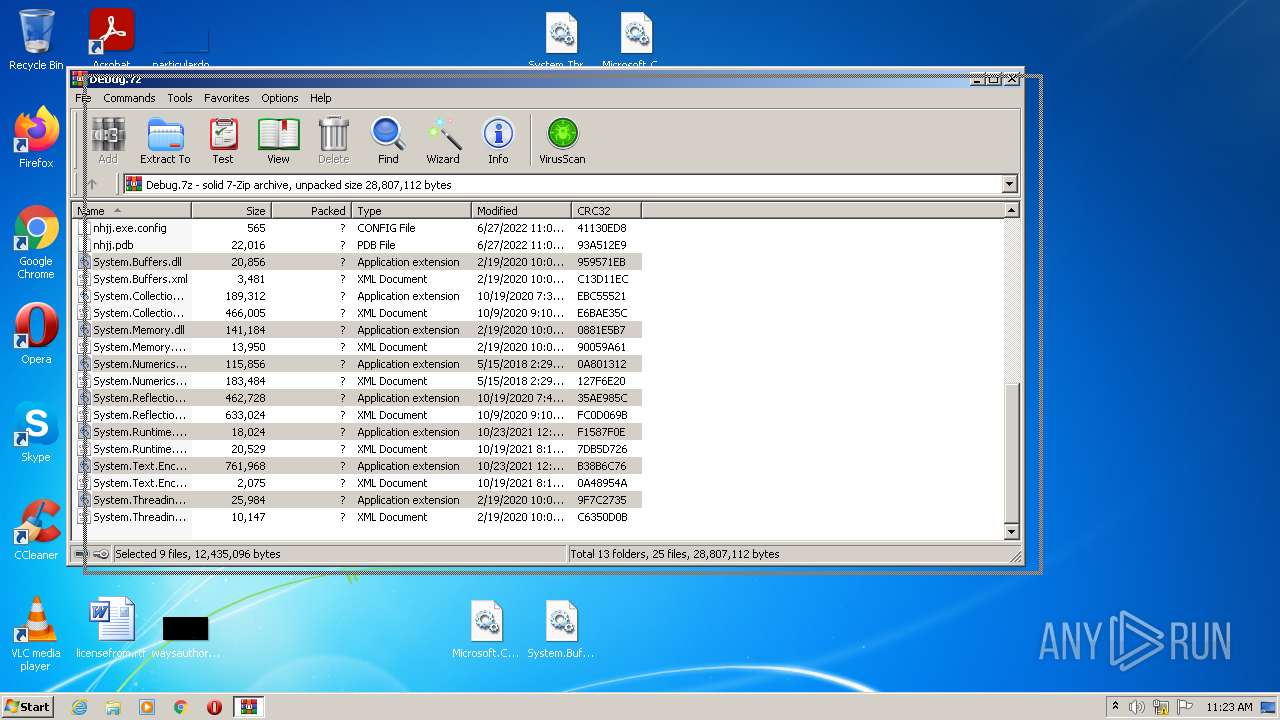
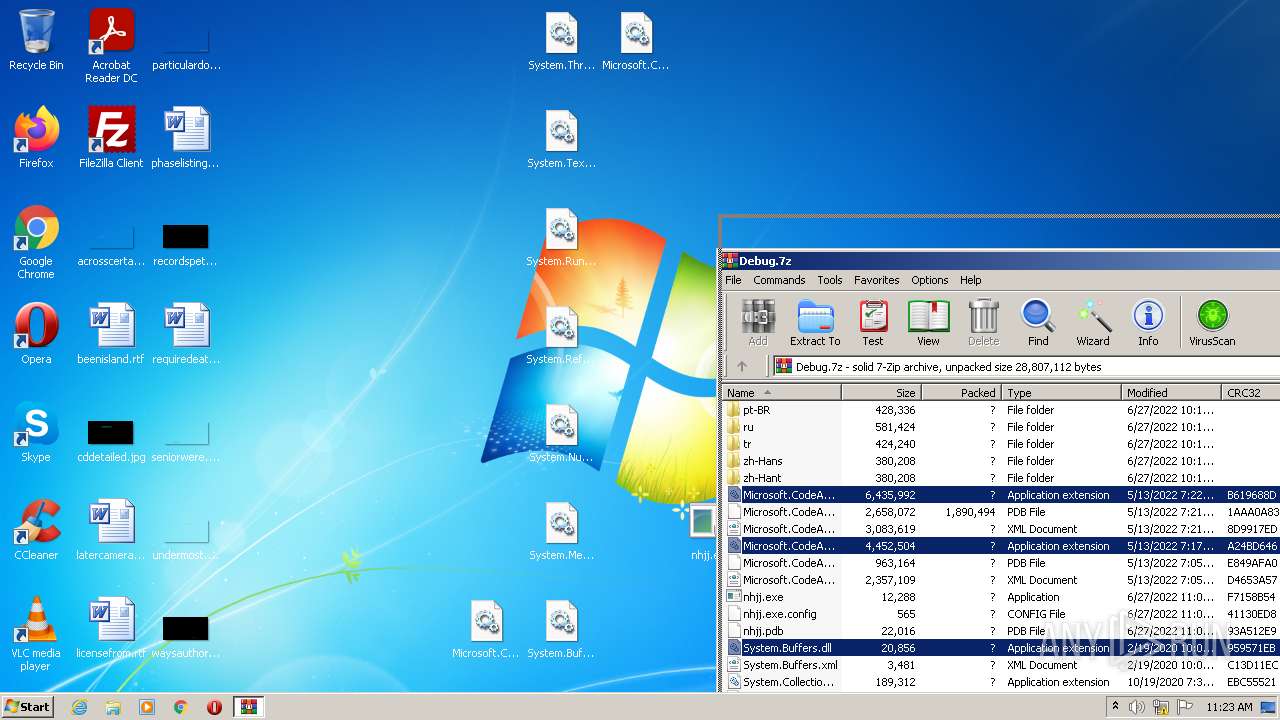
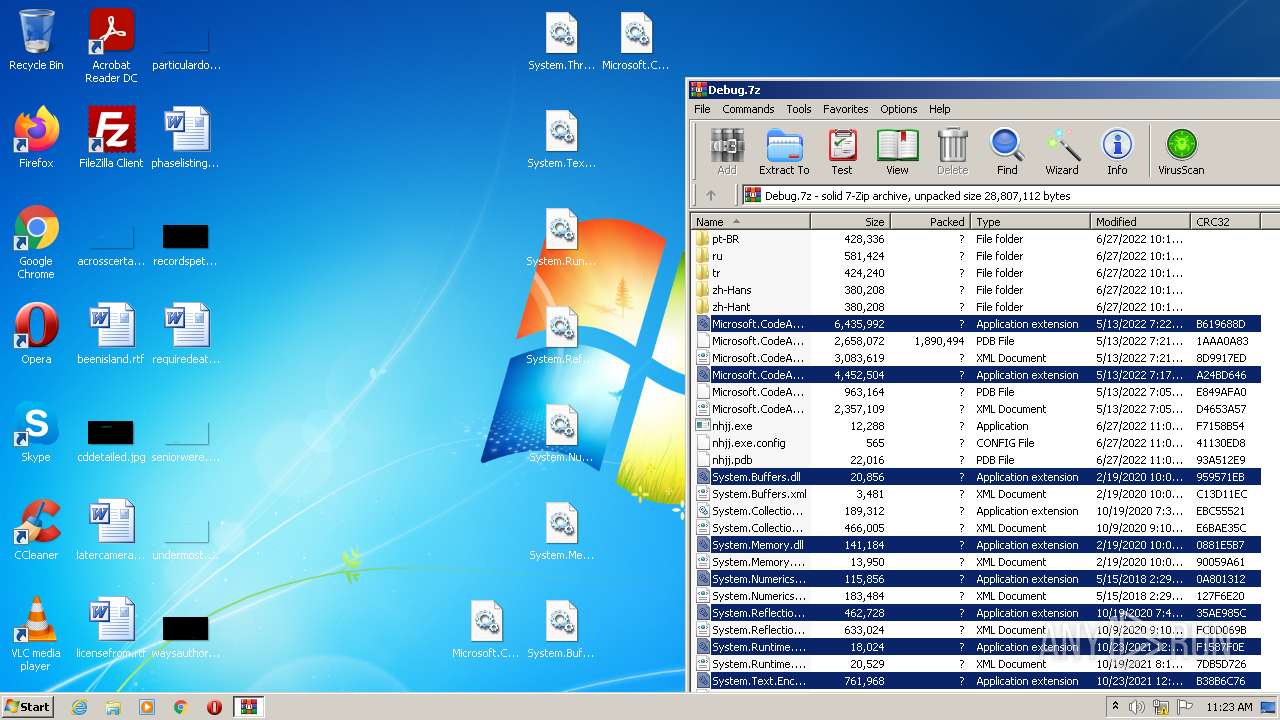
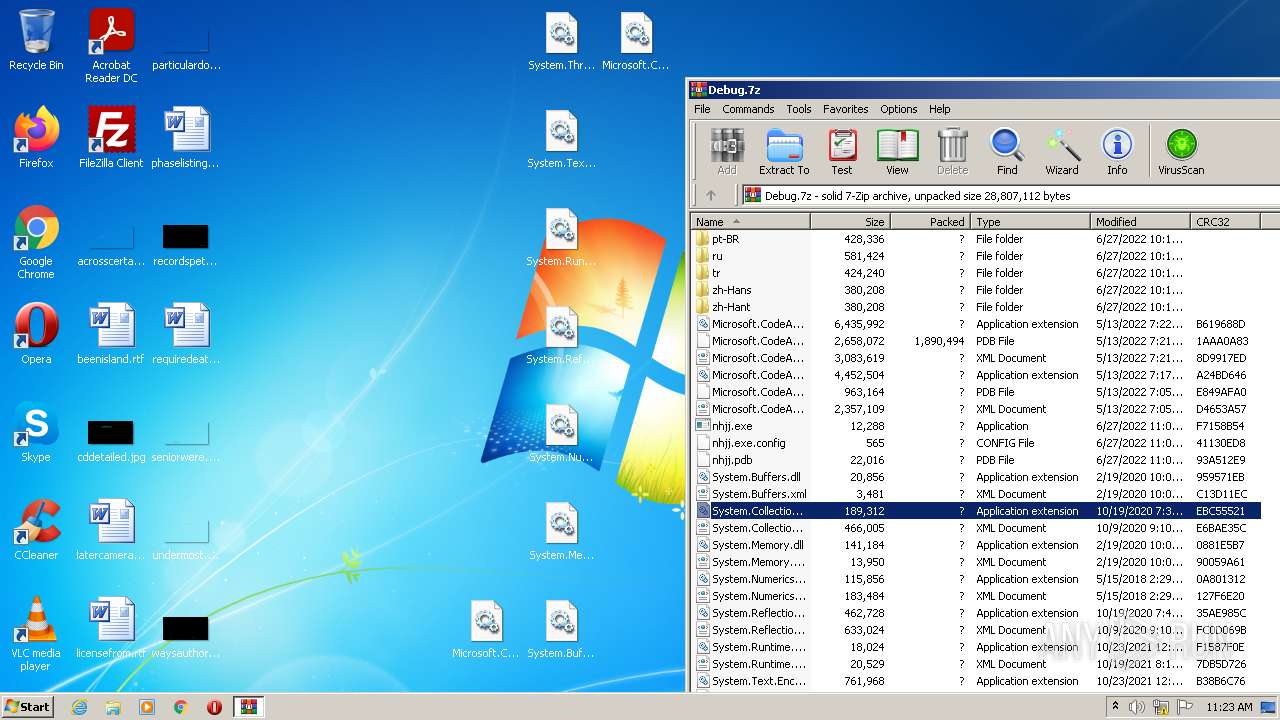
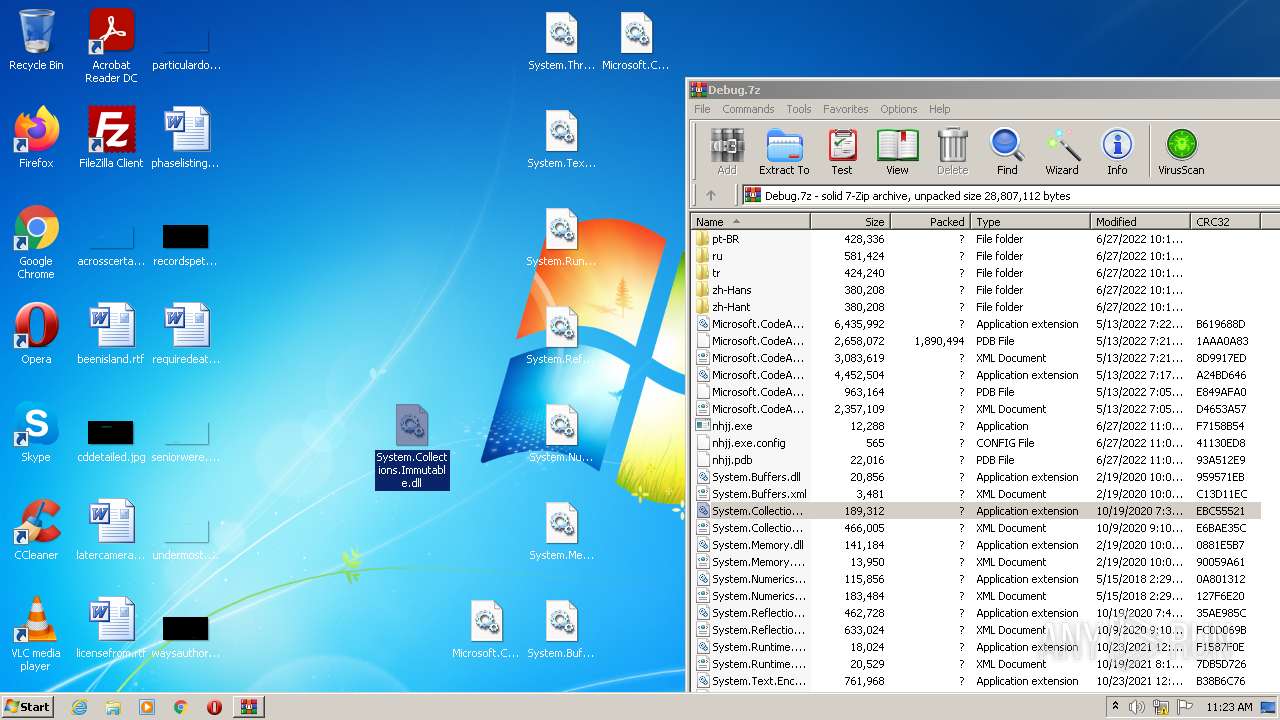
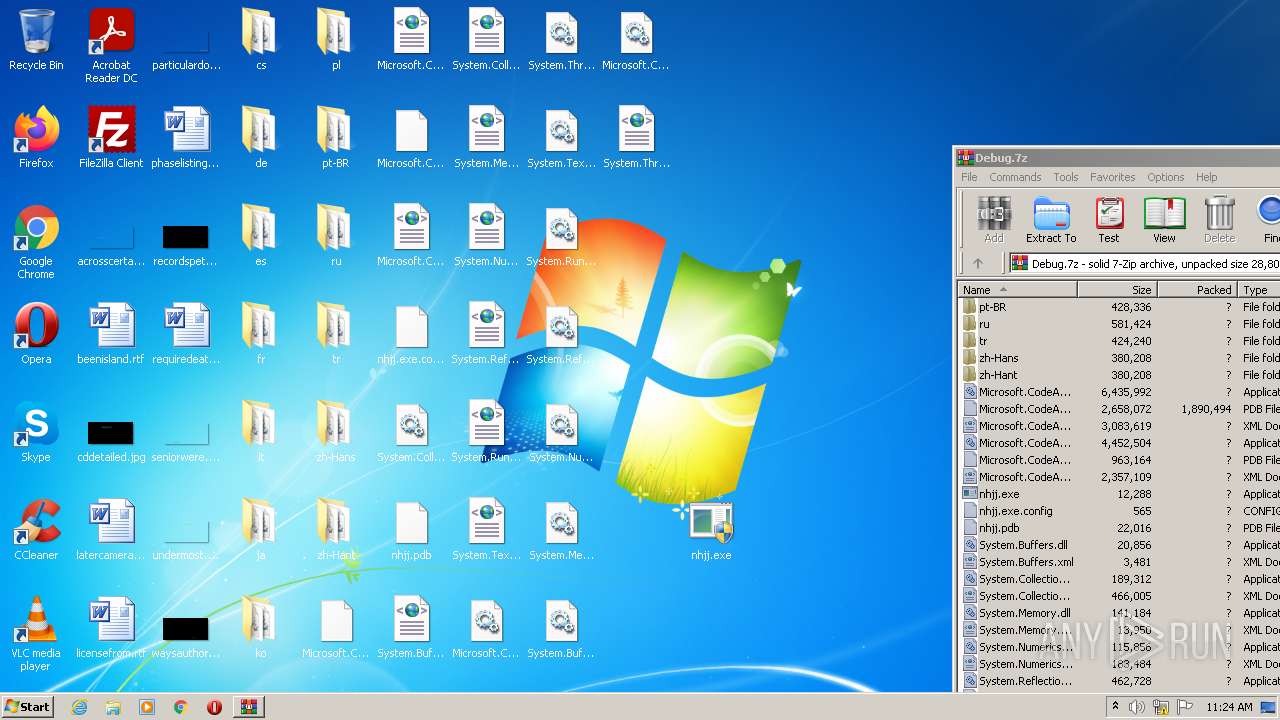
| File name: | Debug.7z |
| Full analysis: | https://app.any.run/tasks/4e2041de-c8c3-4664-8cfe-8e80ae1320f5 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 10:22:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 6D4FA8AB3B7C2D9433C92141D1897608 |
| SHA1: | 88DA8EE0C7E27DF69103B0719BDE71804A6714FB |
| SHA256: | 83DFA333E40CAFC2C7E62FECDDC9F66A3441498C1EB5D5E36B31C469BC6E8506 |
| SSDEEP: | 98304:LuLx3GvI4FtQJIgtVAu02ZBzJE66S3AEO9J+wSAq0iujUvR4bEQP+mM2y8CIHr:sx3GvI4F2JIsAUL6wAEMAzADiuo2V+X4 |
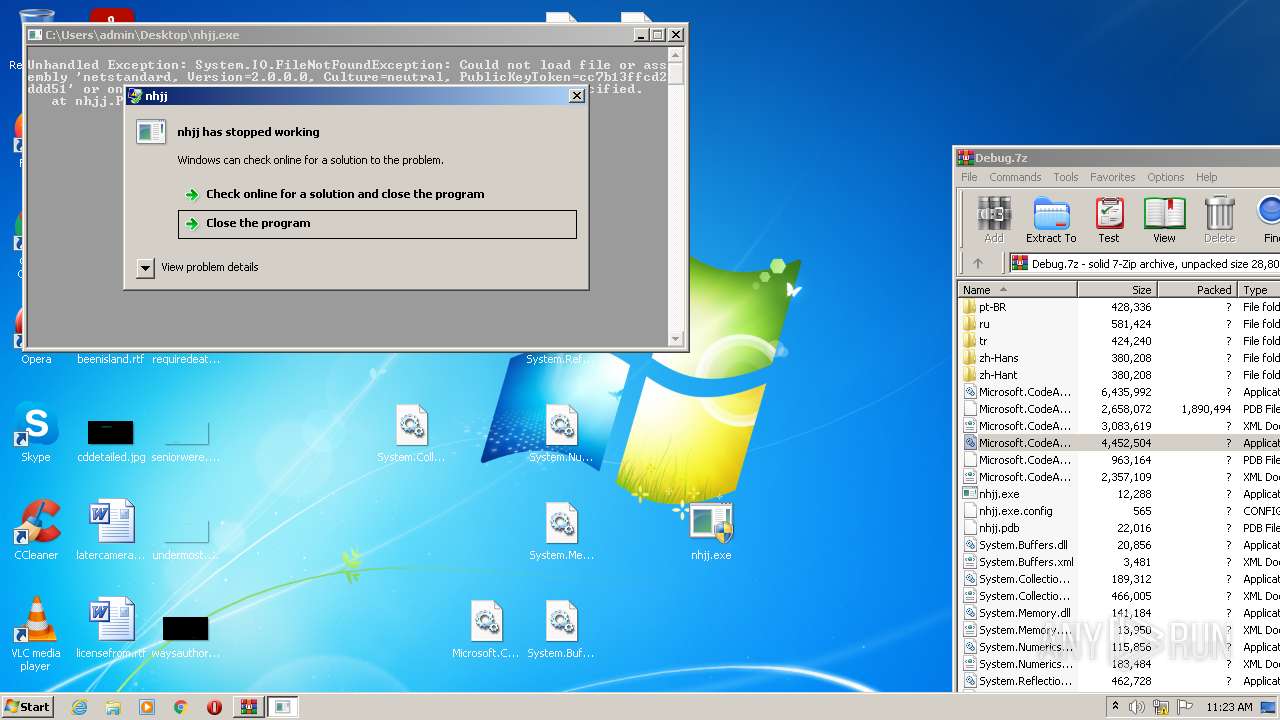
MALICIOUS
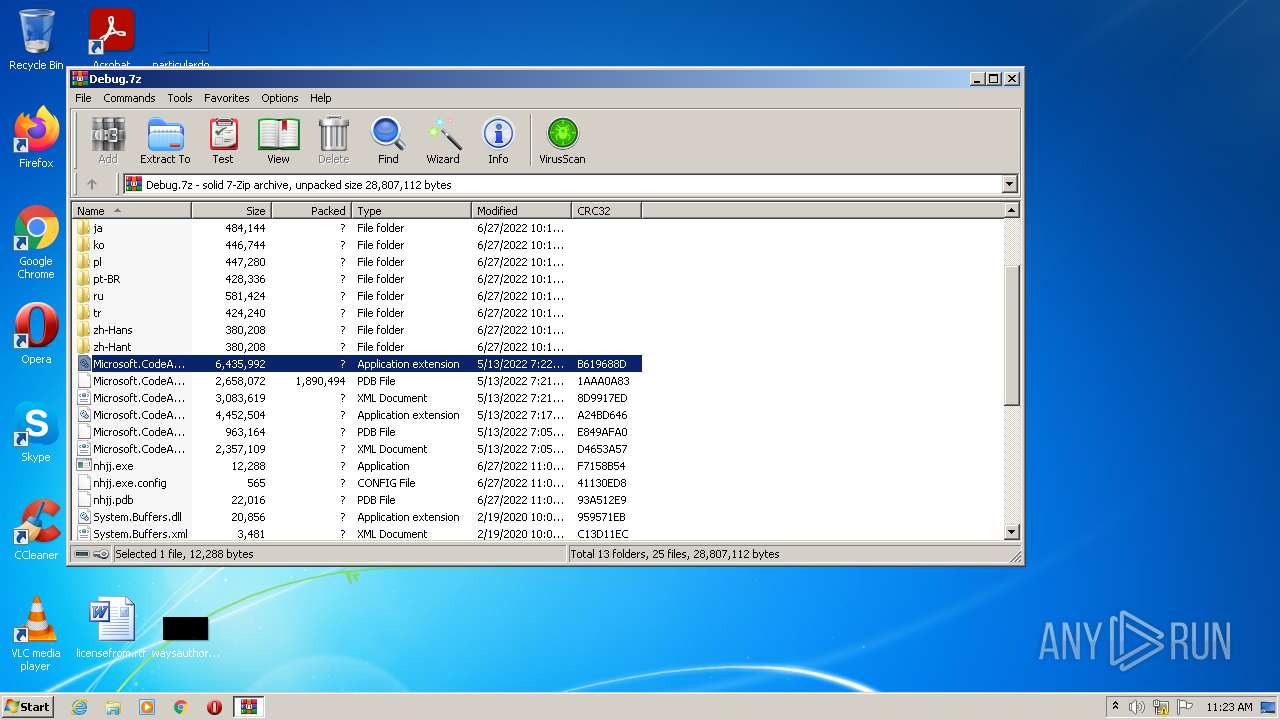
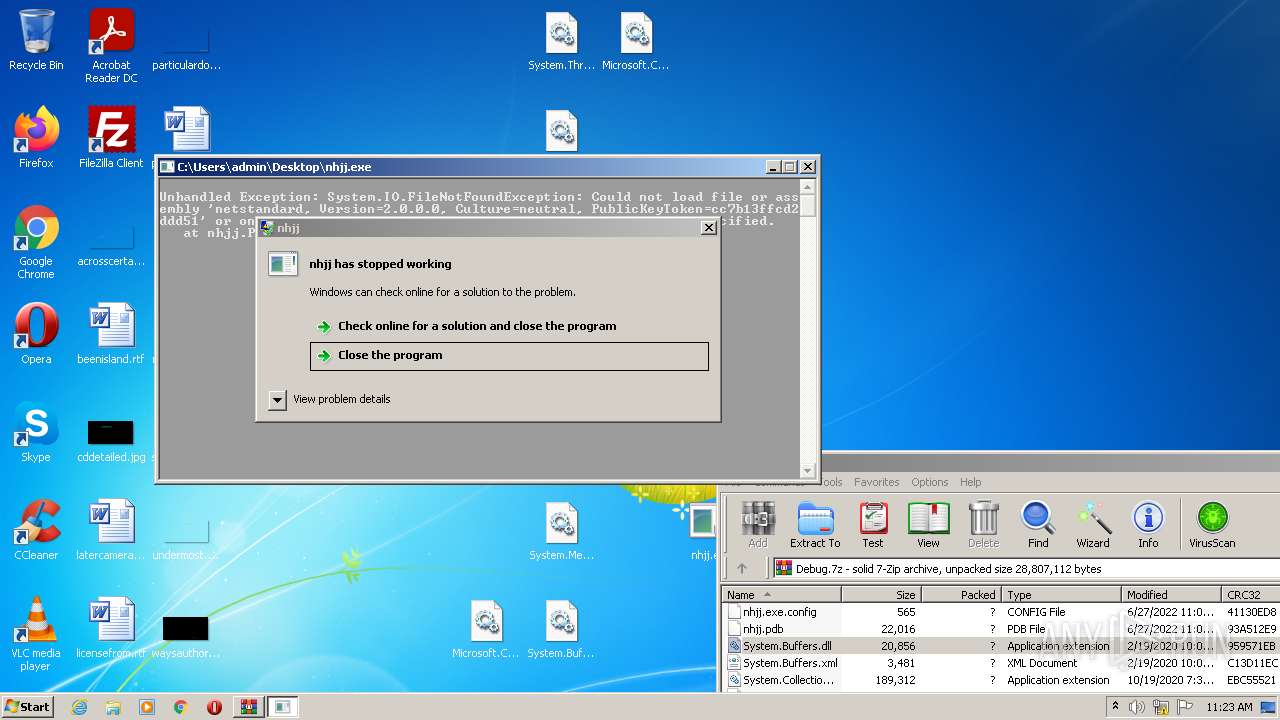
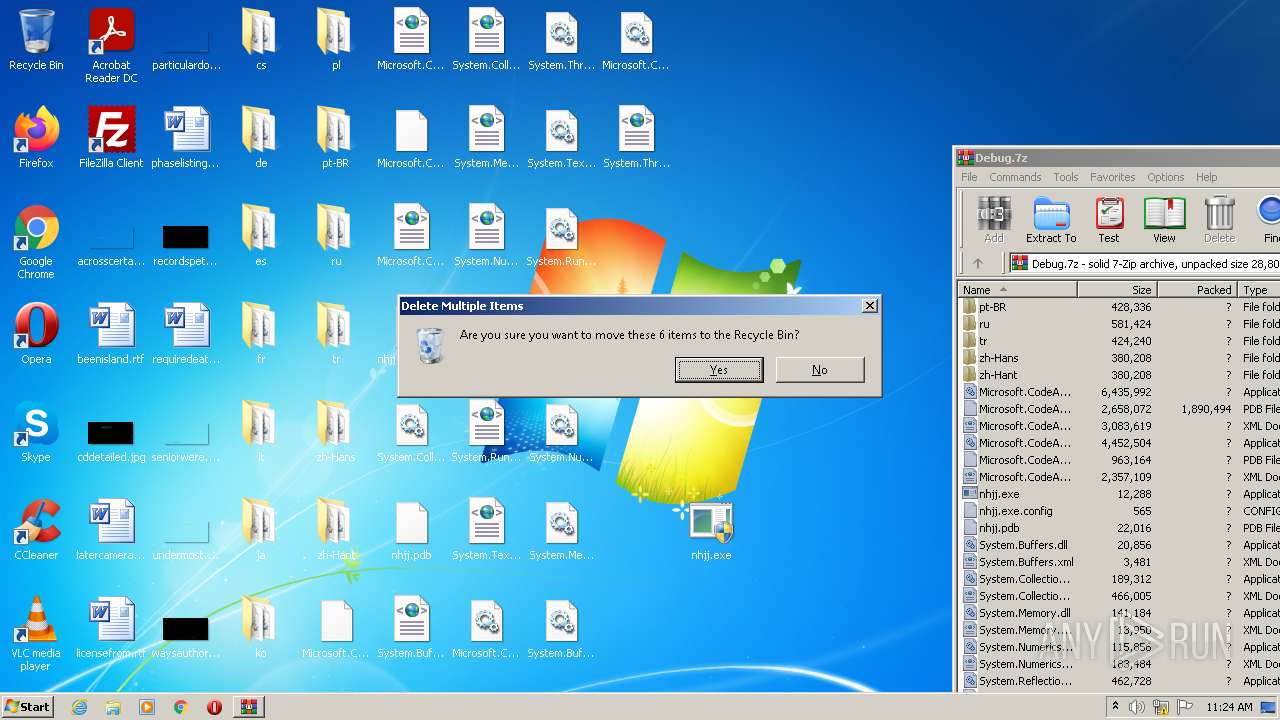
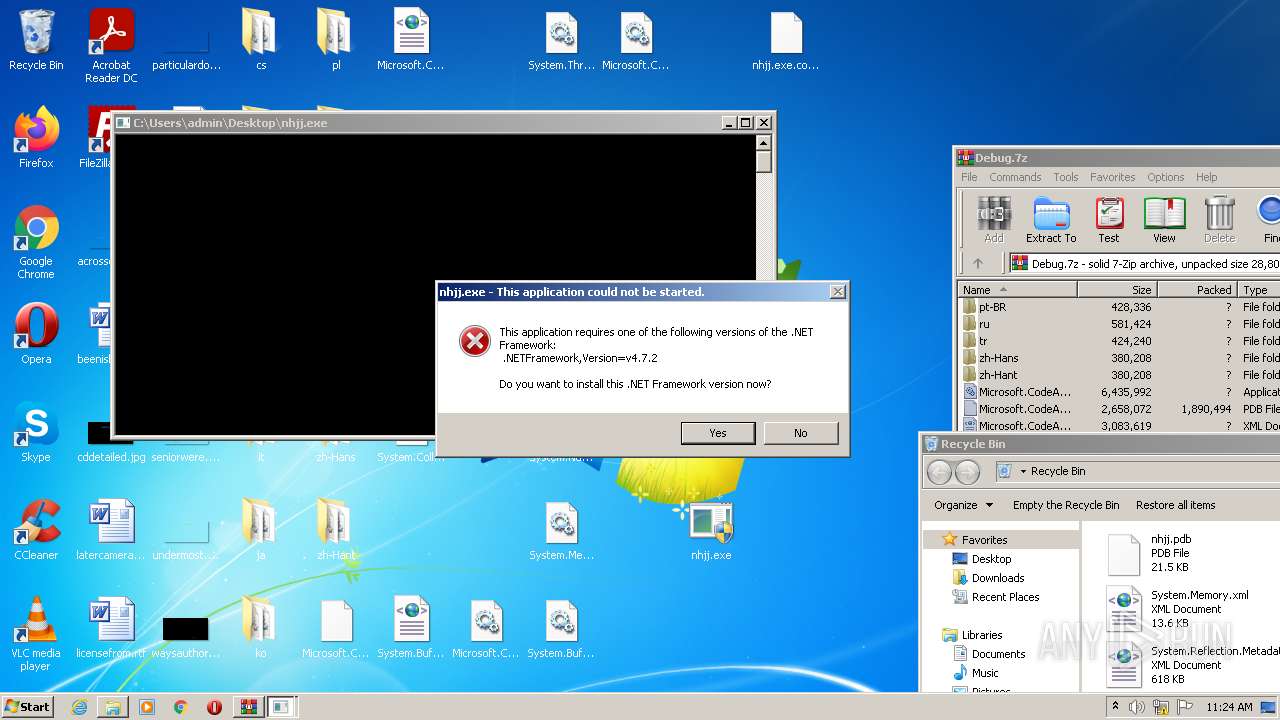
Drops executable file immediately after starts
- WinRAR.exe (PID: 2544)
- Explorer.EXE (PID: 528)
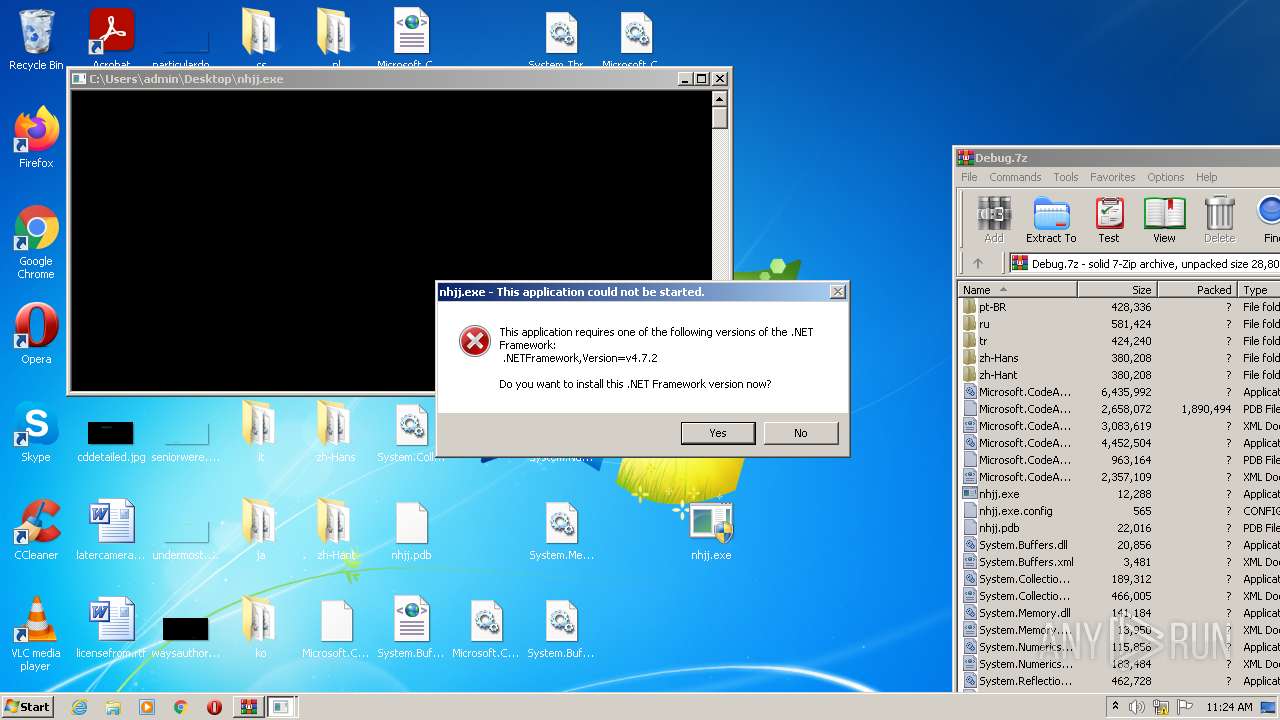
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2804)
- nhjj.exe (PID: 3016)
- nhjj.exe (PID: 4068)
- Explorer.EXE (PID: 528)
- nhjj.exe (PID: 2052)
Application was dropped or rewritten from another process
- nhjj.exe (PID: 1468)
- nhjj.exe (PID: 3016)
- nhjj.exe (PID: 2140)
- nhjj.exe (PID: 4068)
- nhjj.exe (PID: 3176)
- nhjj.exe (PID: 1052)
- nhjj.exe (PID: 2756)
- nhjj.exe (PID: 356)
- nhjj.exe (PID: 1116)
- nhjj.exe (PID: 2052)
- nhjj.exe (PID: 2492)
- nhjj.exe (PID: 2108)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2544)
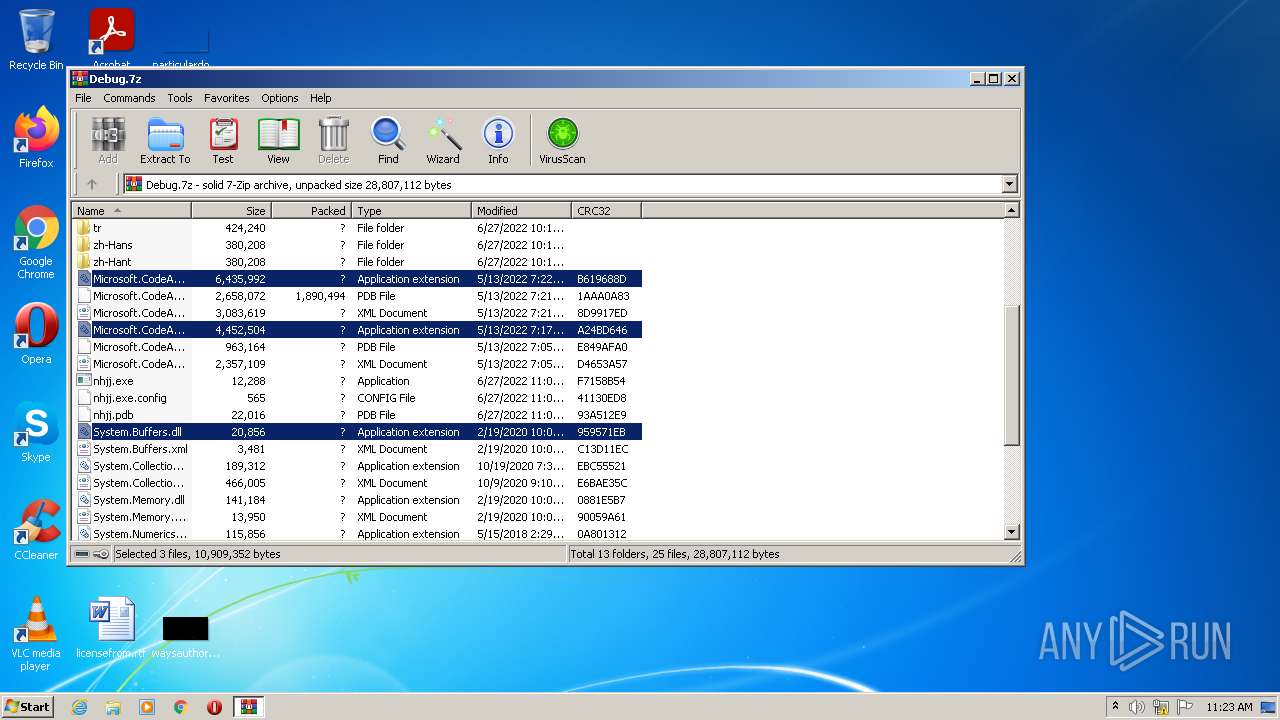
Checks supported languages
- WinRAR.exe (PID: 2544)
- nhjj.exe (PID: 3016)
- nhjj.exe (PID: 4068)
- nhjj.exe (PID: 1052)
- nhjj.exe (PID: 2756)
- nhjj.exe (PID: 2052)
- nhjj.exe (PID: 2108)
Reads the computer name
- WinRAR.exe (PID: 2544)
- nhjj.exe (PID: 3016)
- nhjj.exe (PID: 4068)
- nhjj.exe (PID: 2052)
Drops a file with a compile date too recent
- Explorer.EXE (PID: 528)
- WinRAR.exe (PID: 2544)
INFO
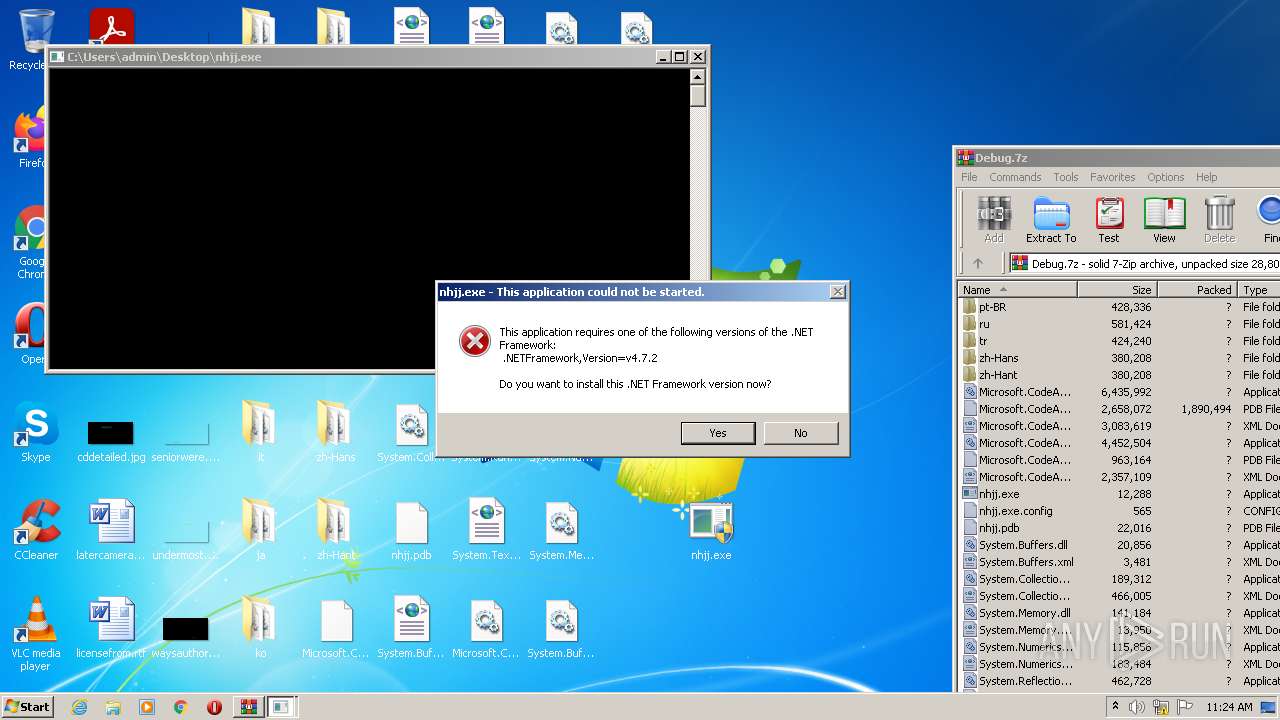
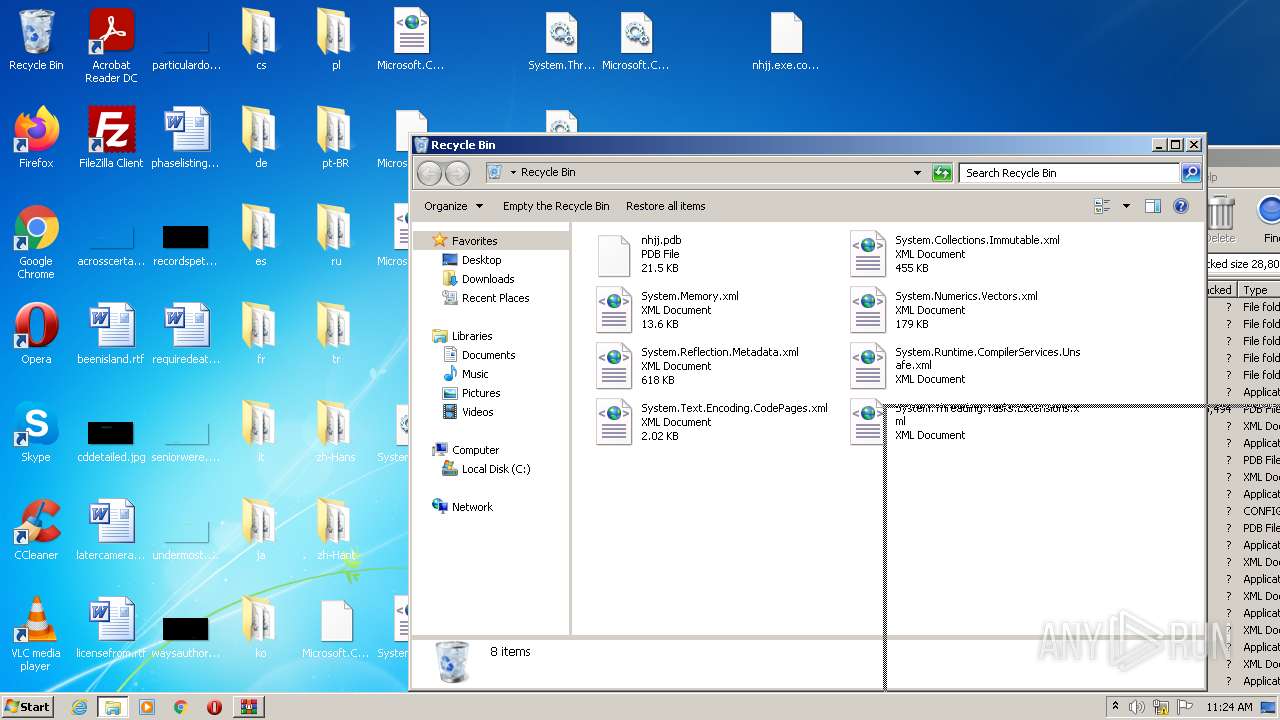
Manual execution by user
- nhjj.exe (PID: 1468)
- nhjj.exe (PID: 3016)
- nhjj.exe (PID: 2140)
- nhjj.exe (PID: 4068)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
78
Monitored processes
15
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Users\admin\Desktop\nhjj.exe" | C:\Users\admin\Desktop\nhjj.exe | — | Explorer.EXE | |||||||||||
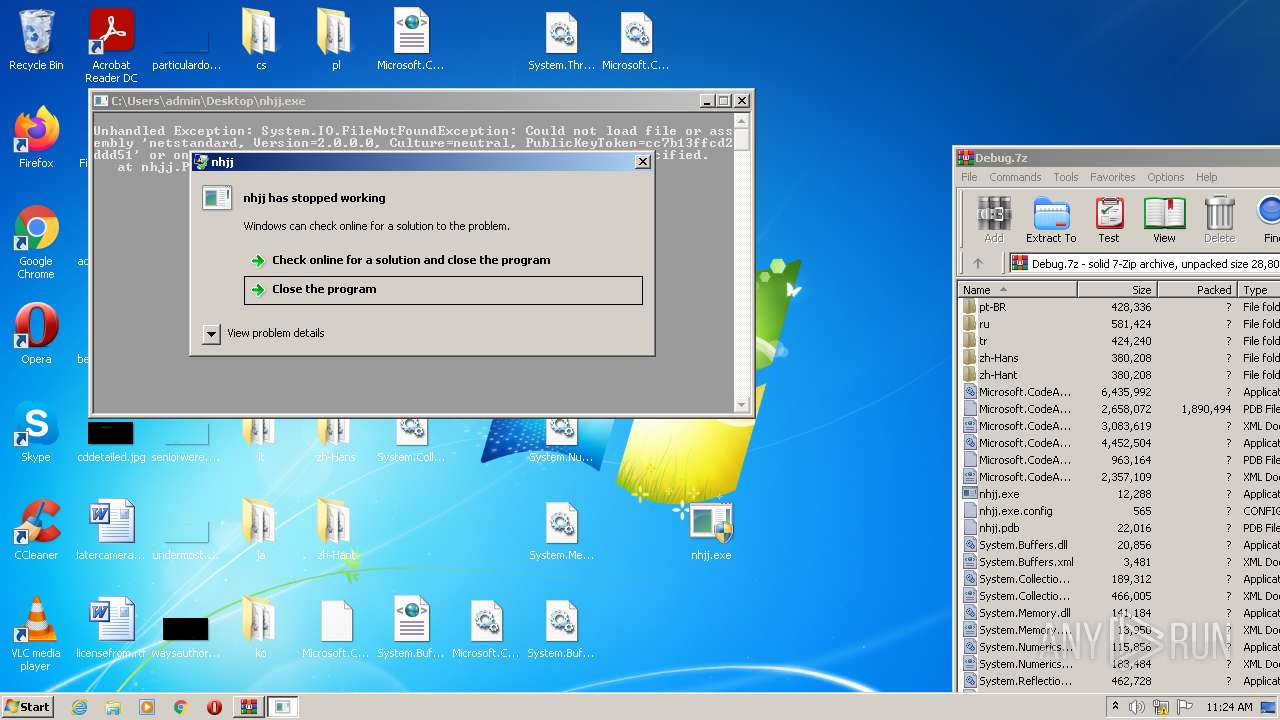
User: admin Integrity Level: MEDIUM Description: nhjj Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 528 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1052 | "C:\Users\admin\Desktop\nhjj.exe" | C:\Users\admin\Desktop\nhjj.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: nhjj Exit code: 2148734720 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1116 | "C:\Users\admin\Desktop\nhjj.exe" | C:\Users\admin\Desktop\nhjj.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: nhjj Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\Desktop\nhjj.exe" | C:\Users\admin\Desktop\nhjj.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: nhjj Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2052 | "C:\Users\admin\Desktop\nhjj.exe" | C:\Users\admin\Desktop\nhjj.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: nhjj Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2108 | "C:\Users\admin\Desktop\nhjj.exe" | C:\Users\admin\Desktop\nhjj.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: nhjj Exit code: 2148734720 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\Desktop\nhjj.exe" | C:\Users\admin\Desktop\nhjj.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: nhjj Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2492 | "C:\Users\admin\Desktop\nhjj.exe" | C:\Users\admin\Desktop\nhjj.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: nhjj Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
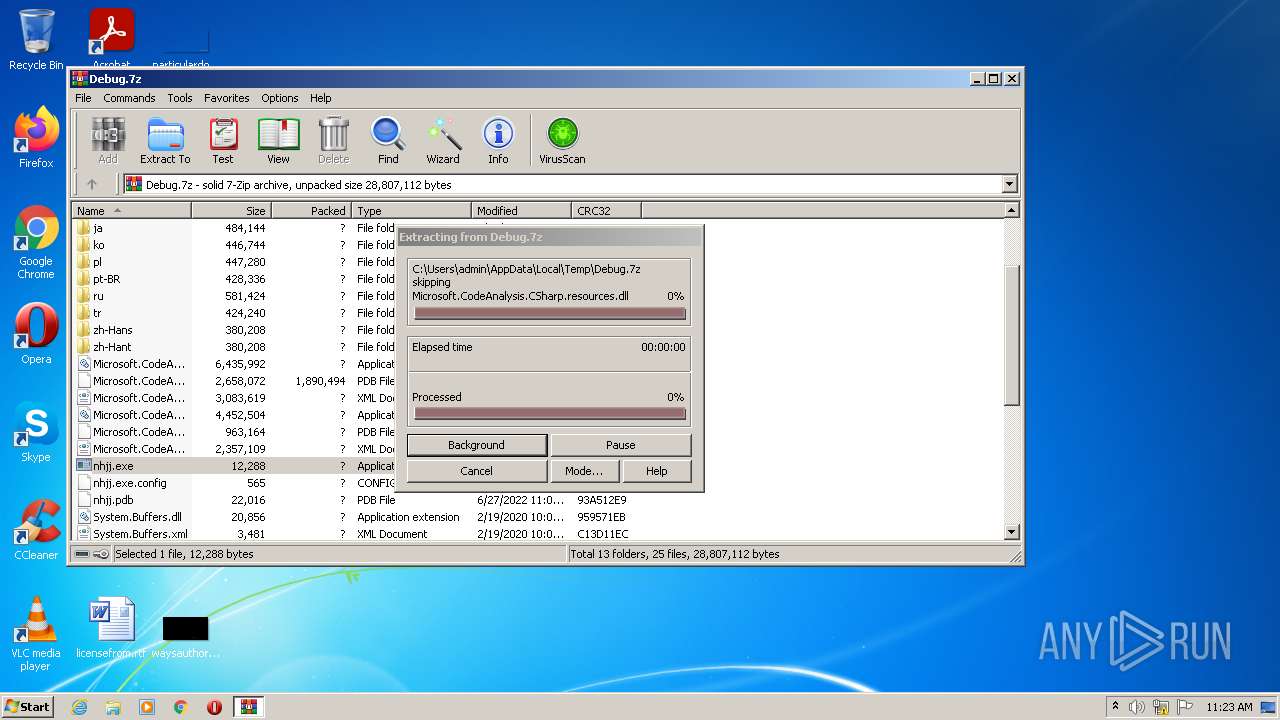
| 2544 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Debug.7z" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
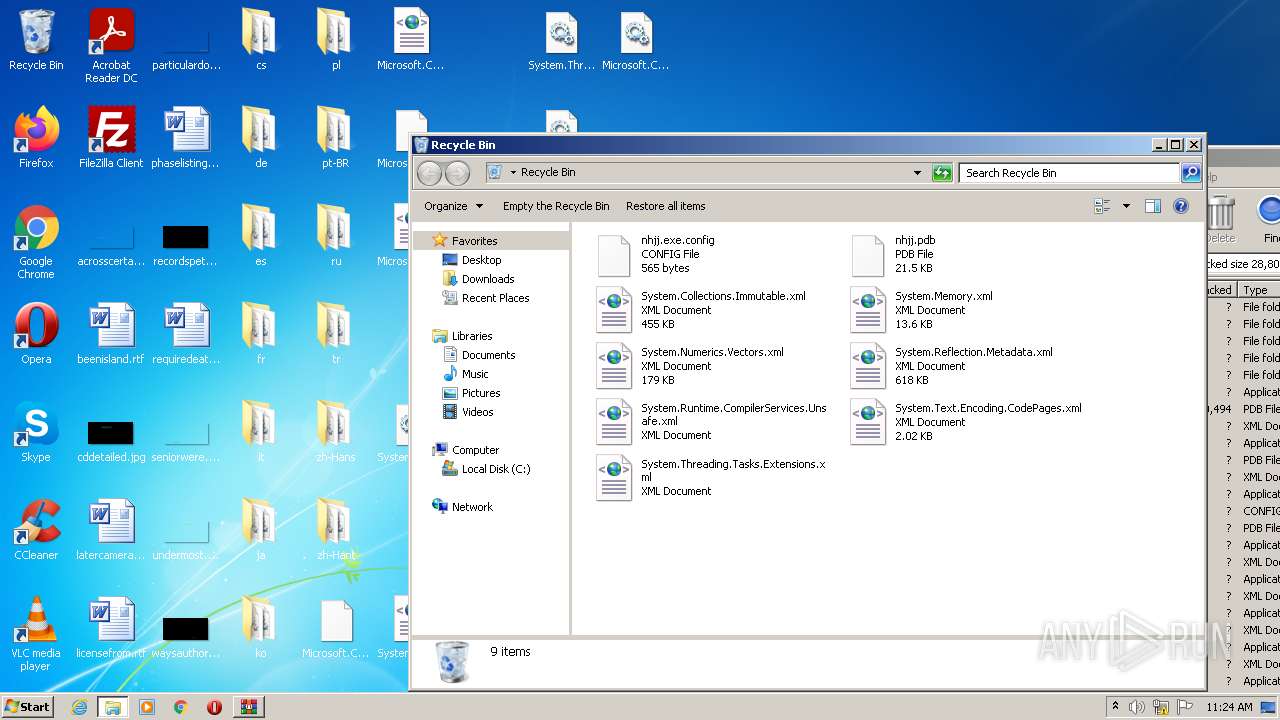
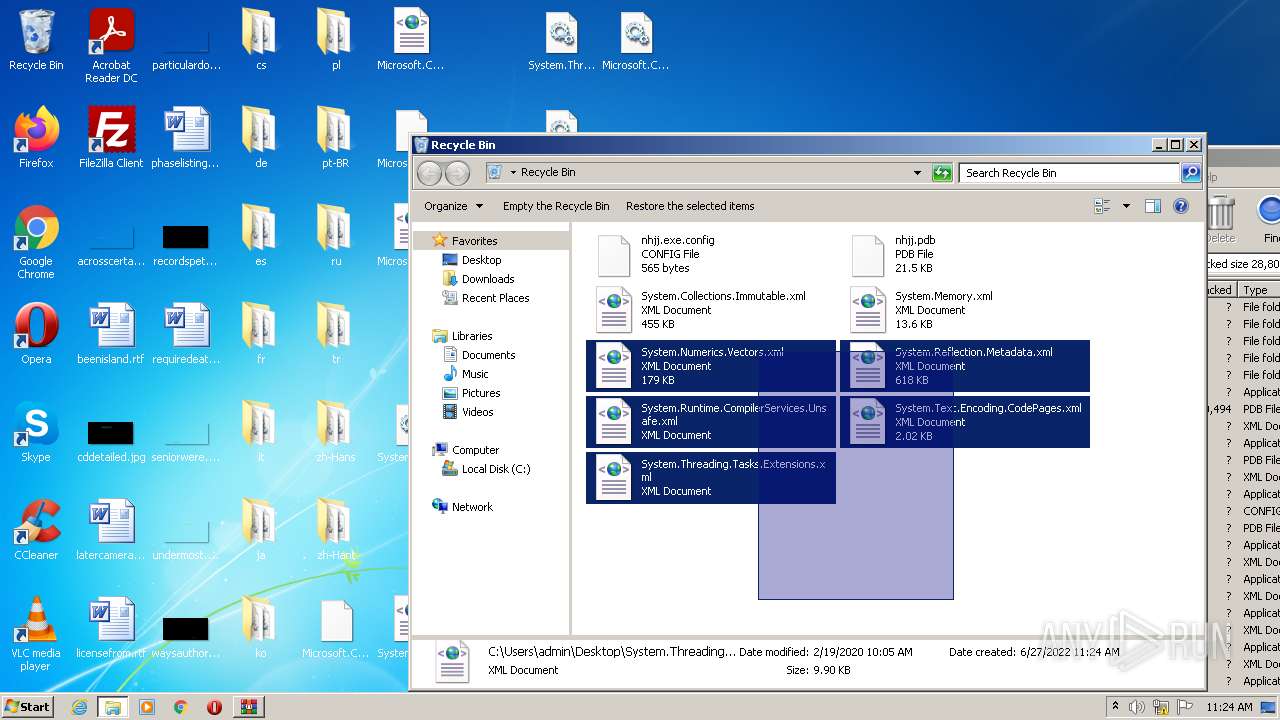
Total events
13 965
Read events
13 728
Write events
232
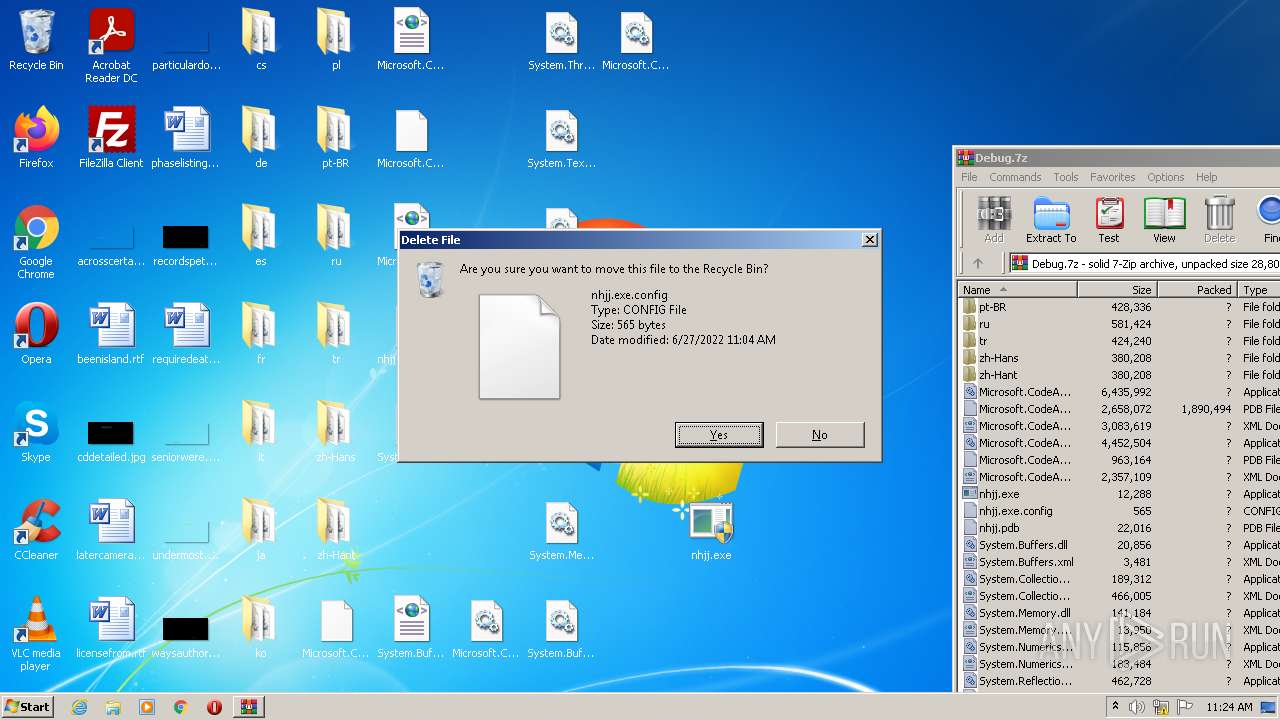
Delete events
5
Modification events
| (PID) Process: | (2544) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2544) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2544) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2544) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2544) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2544) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Debug.7z | |||
| (PID) Process: | (2544) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2544) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2544) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2544) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
59
Suspicious files
15
Text files
30
Unknown types
3
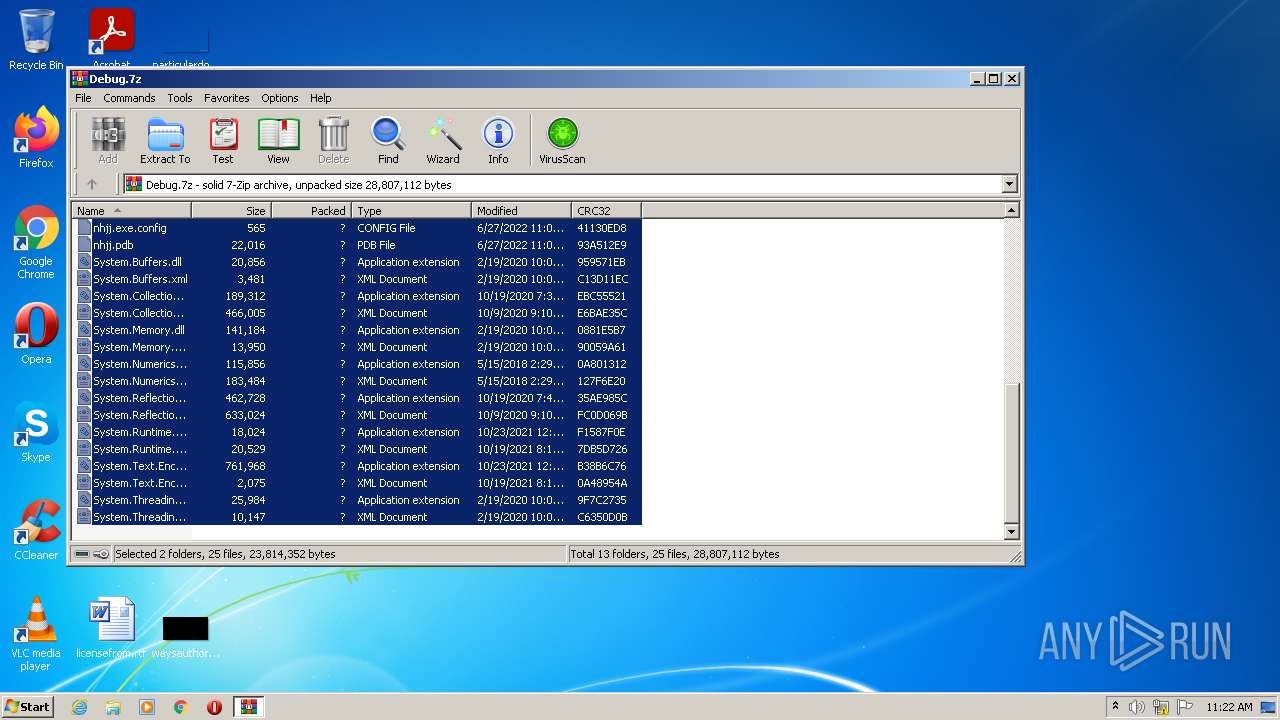
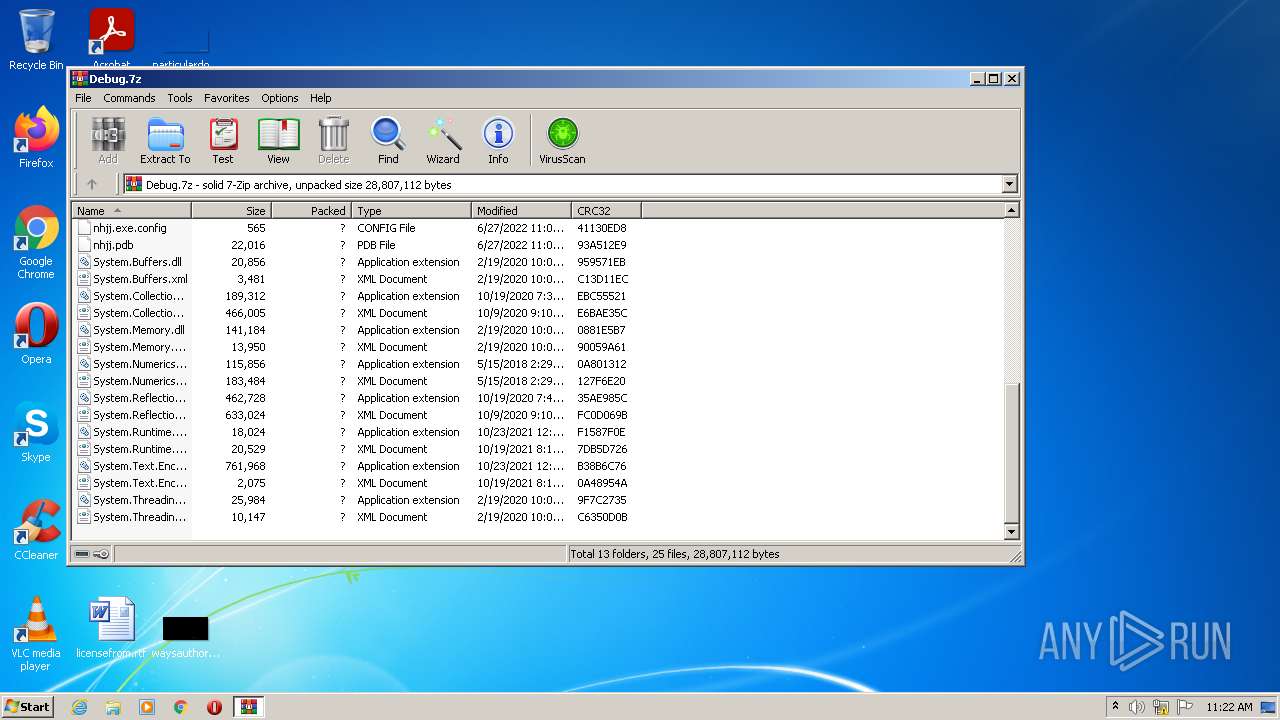
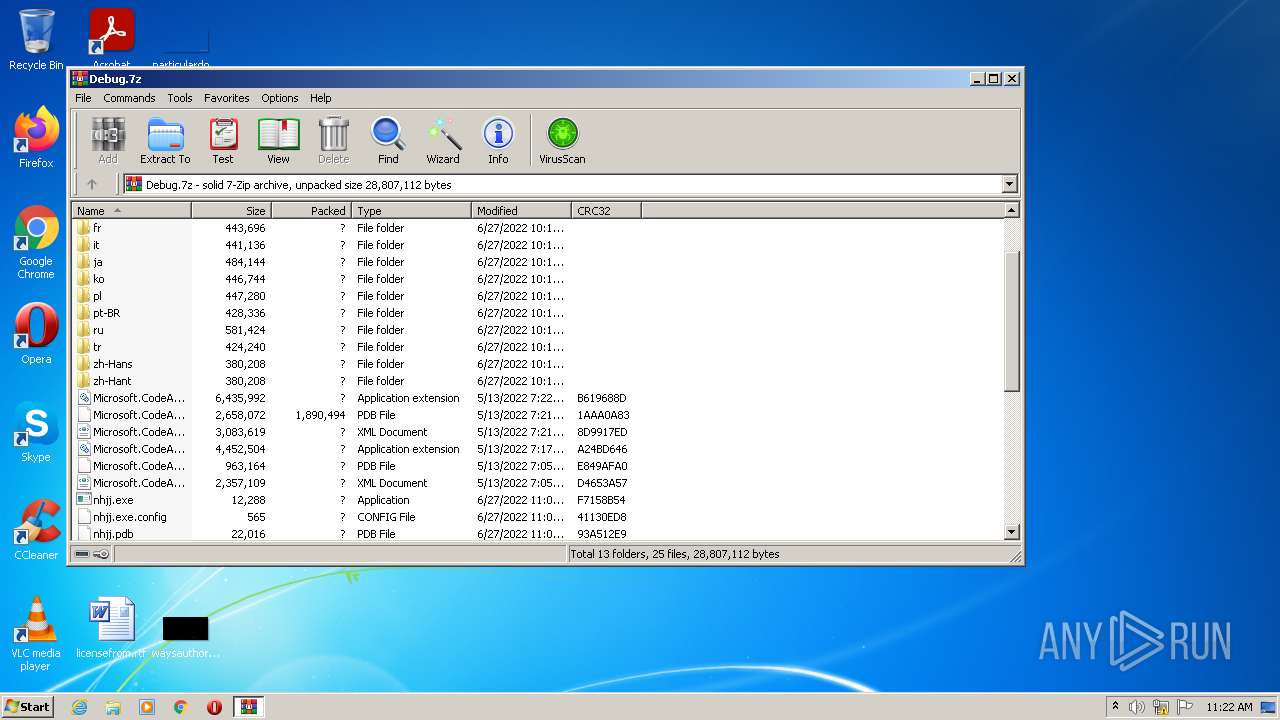
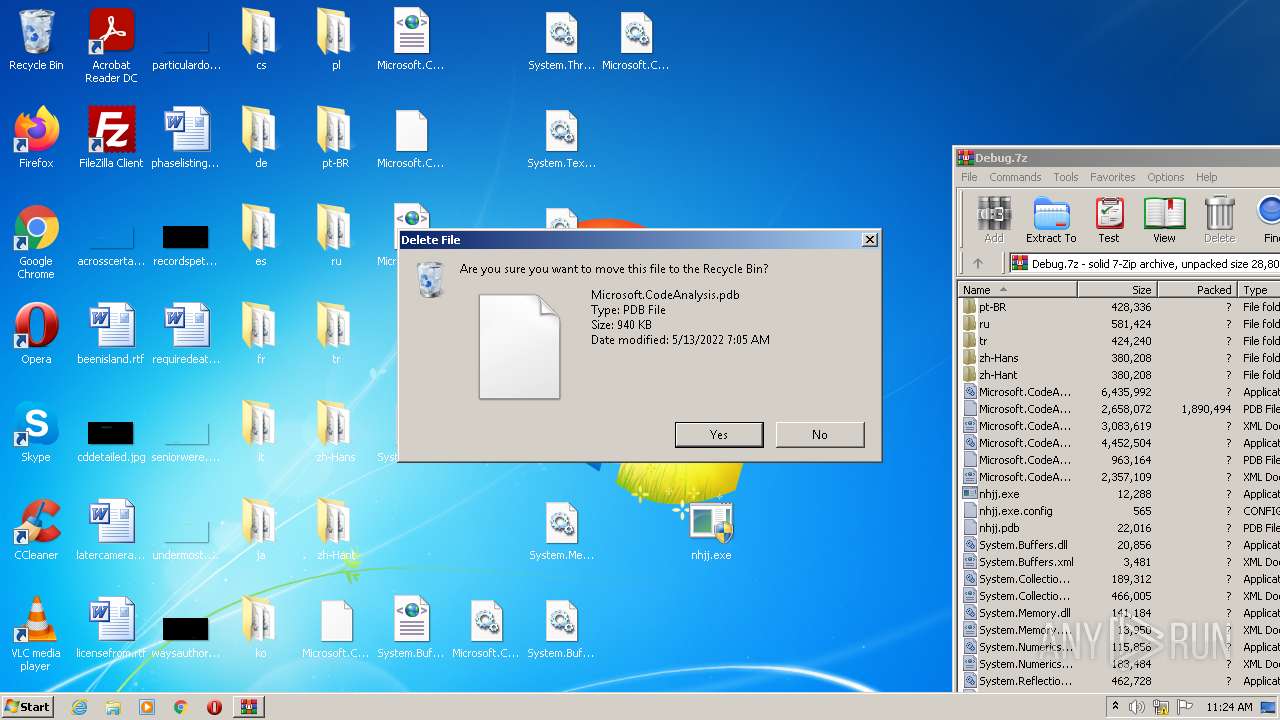
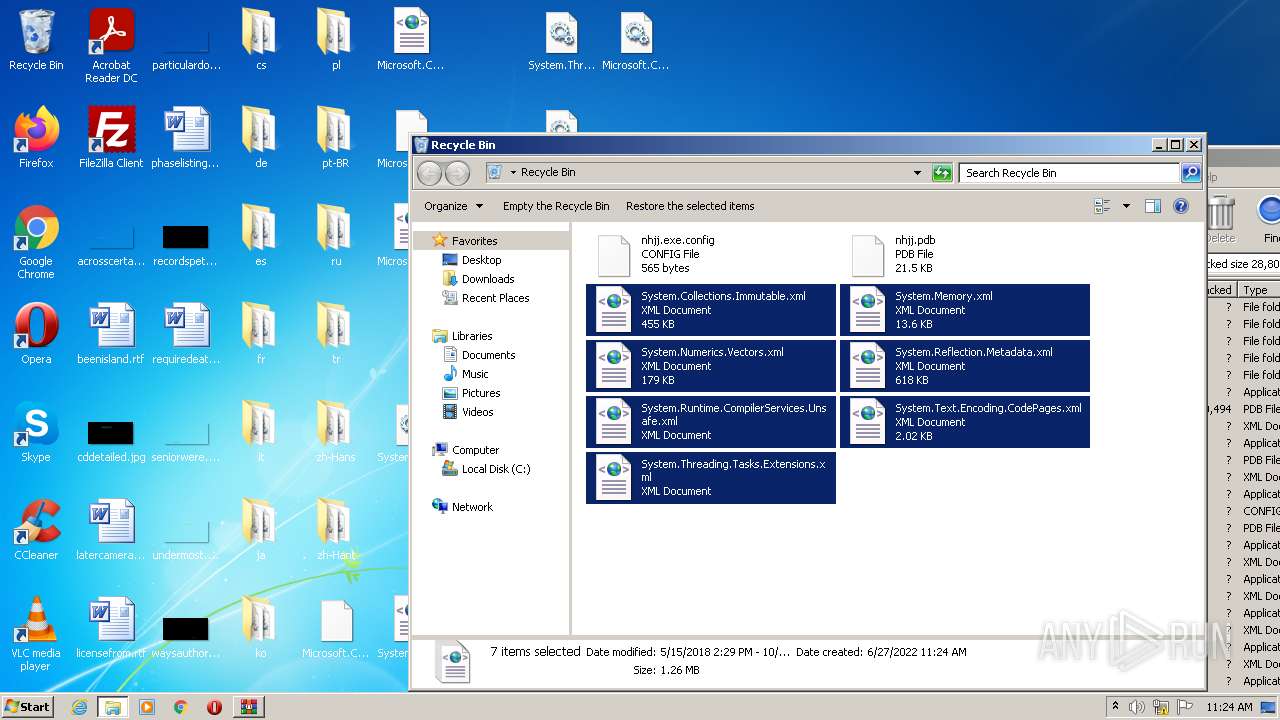
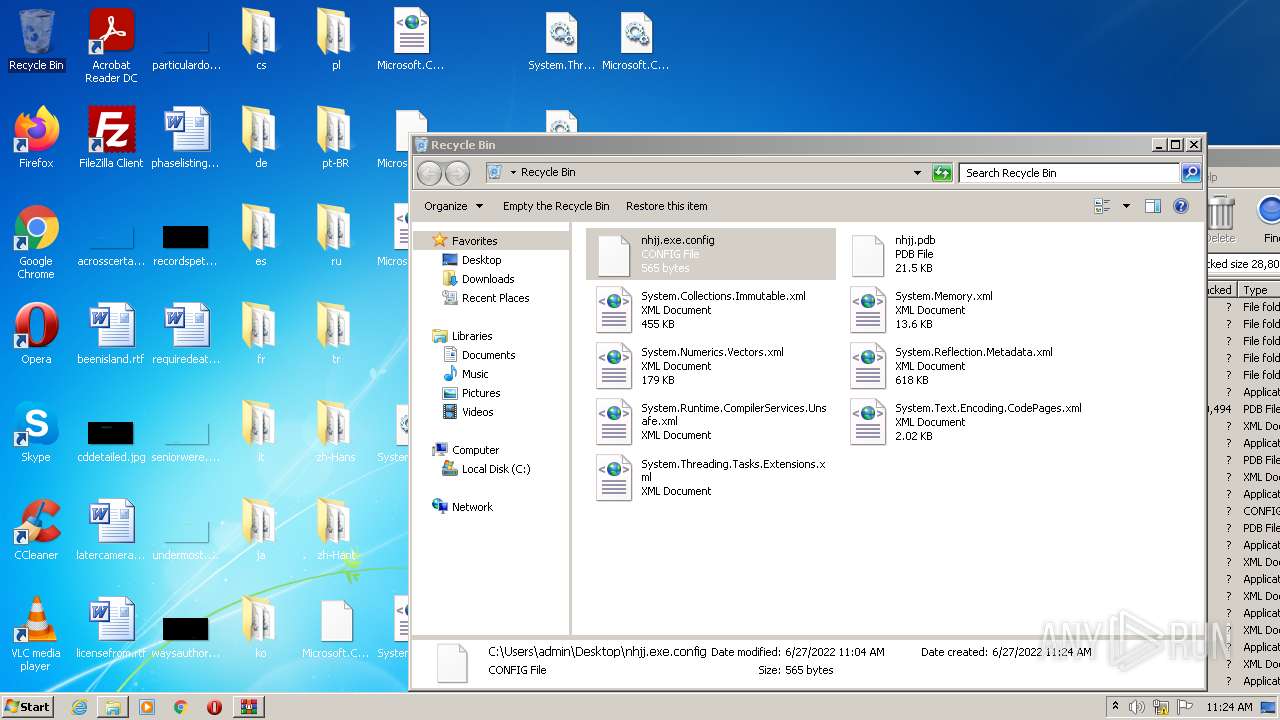
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
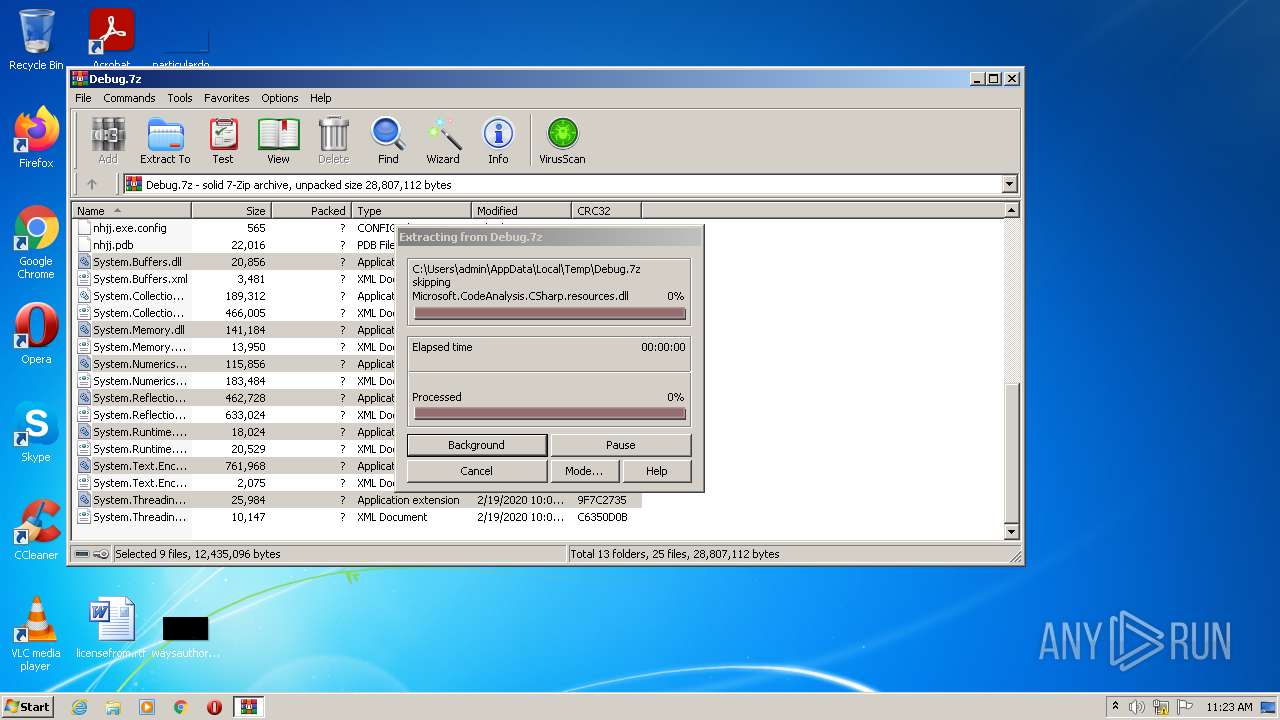
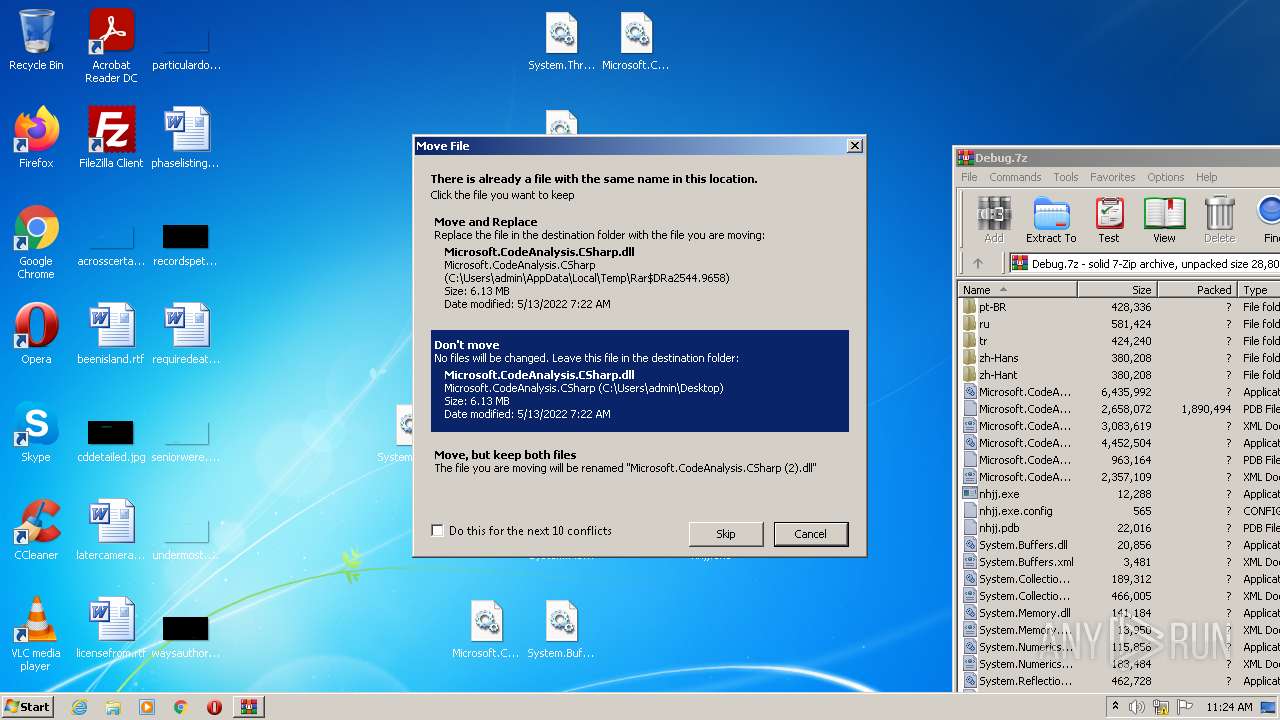
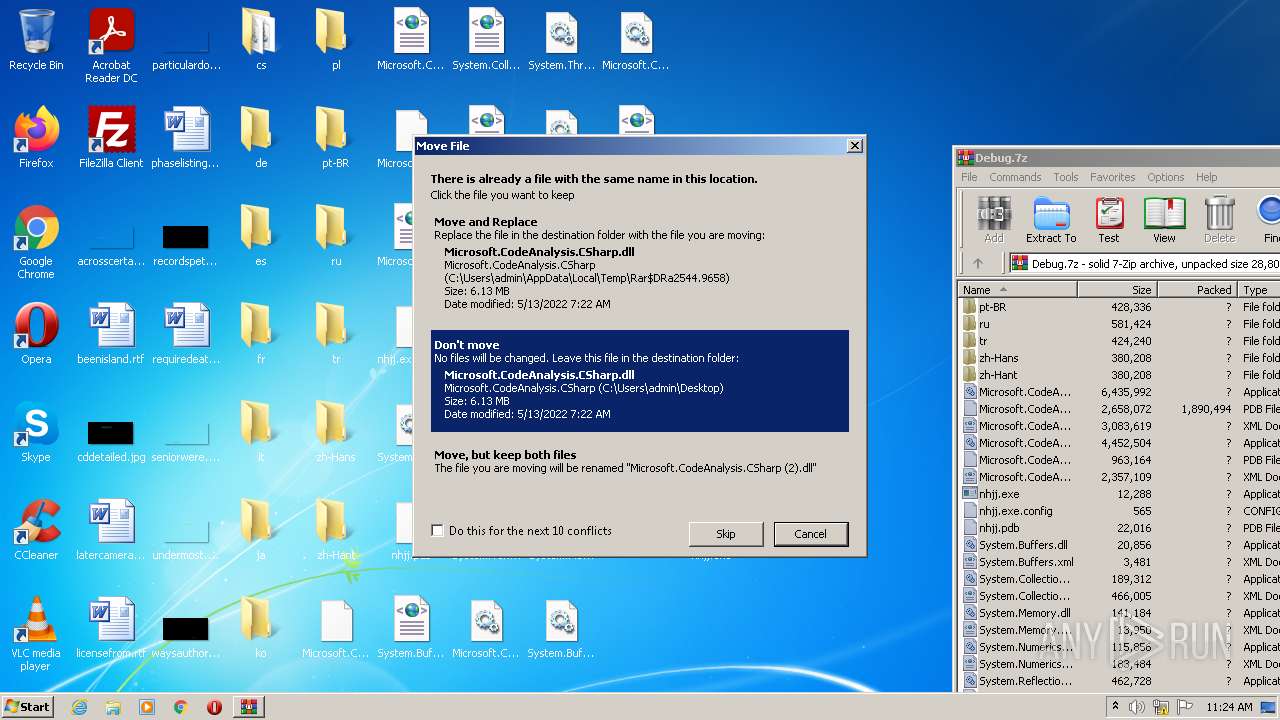
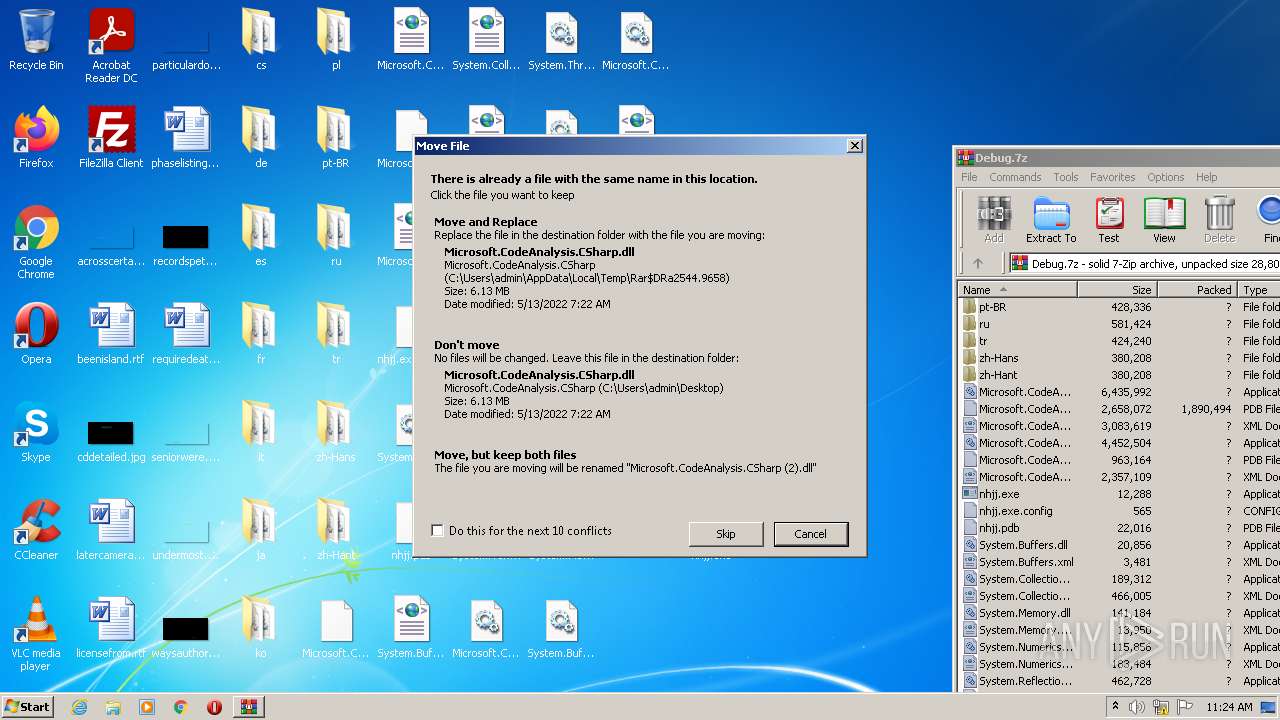
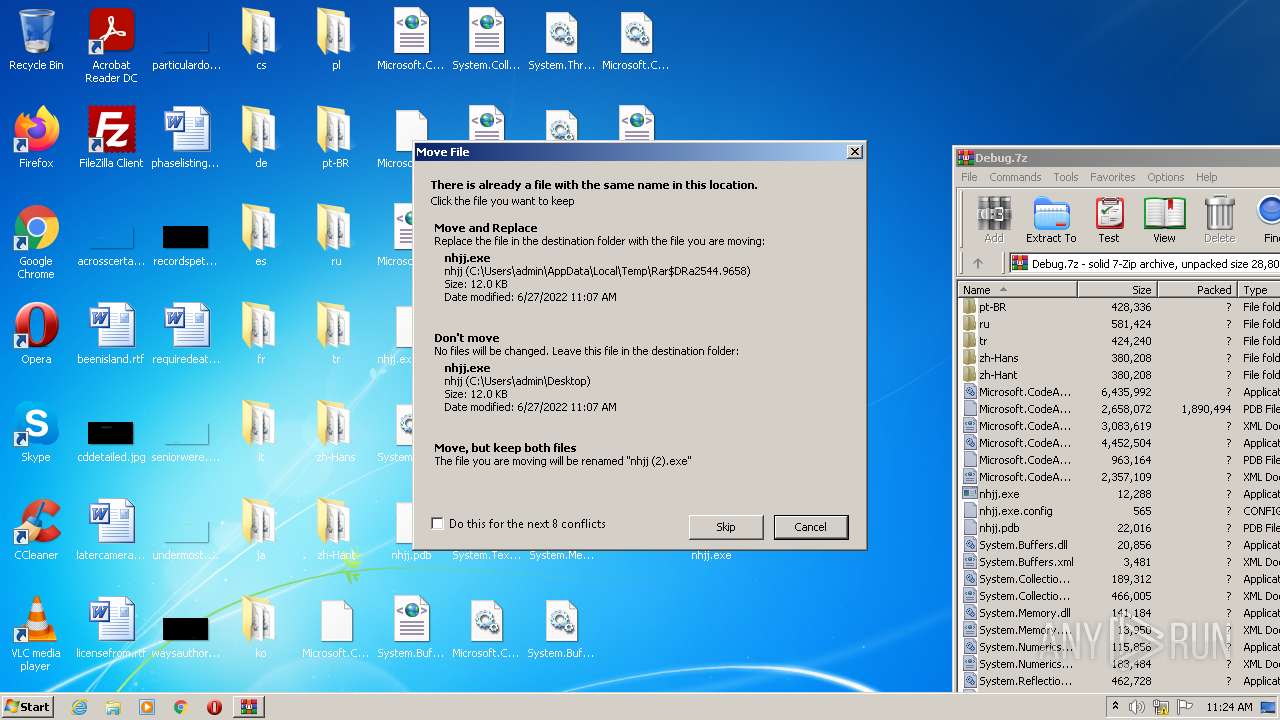
| 2544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2544.3703\nhjj.exe | executable | |
MD5:— | SHA256:— | |||
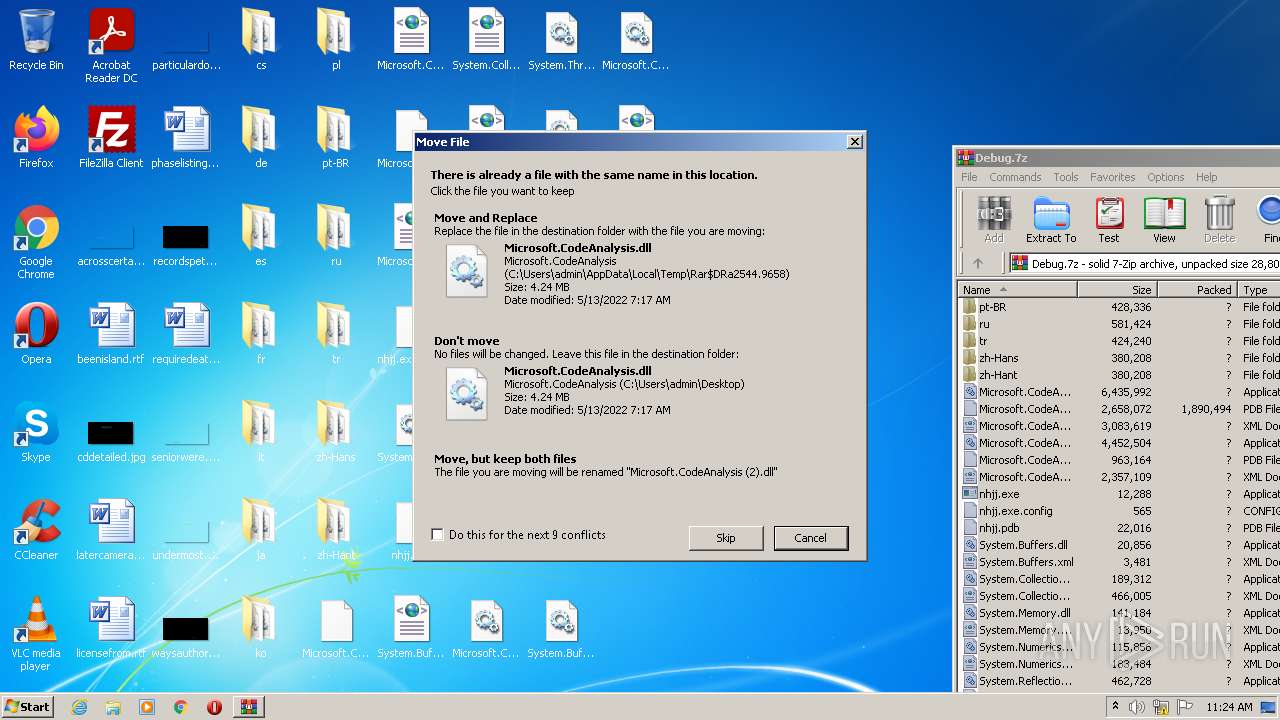
| 2544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2544.6133\Microsoft.CodeAnalysis.dll | executable | |
MD5:— | SHA256:— | |||
| 528 | Explorer.EXE | C:\Users\admin\Desktop\Microsoft.CodeAnalysis.CSharp.dll | executable | |
MD5:— | SHA256:— | |||
| 2544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2544.6133\Microsoft.CodeAnalysis.CSharp.dll | executable | |
MD5:— | SHA256:— | |||
| 528 | Explorer.EXE | C:\Users\admin\Desktop\nhjj.exe | executable | |
MD5:— | SHA256:— | |||
| 528 | Explorer.EXE | C:\Users\admin\Desktop\Microsoft.CodeAnalysis.dll | executable | |
MD5:— | SHA256:— | |||
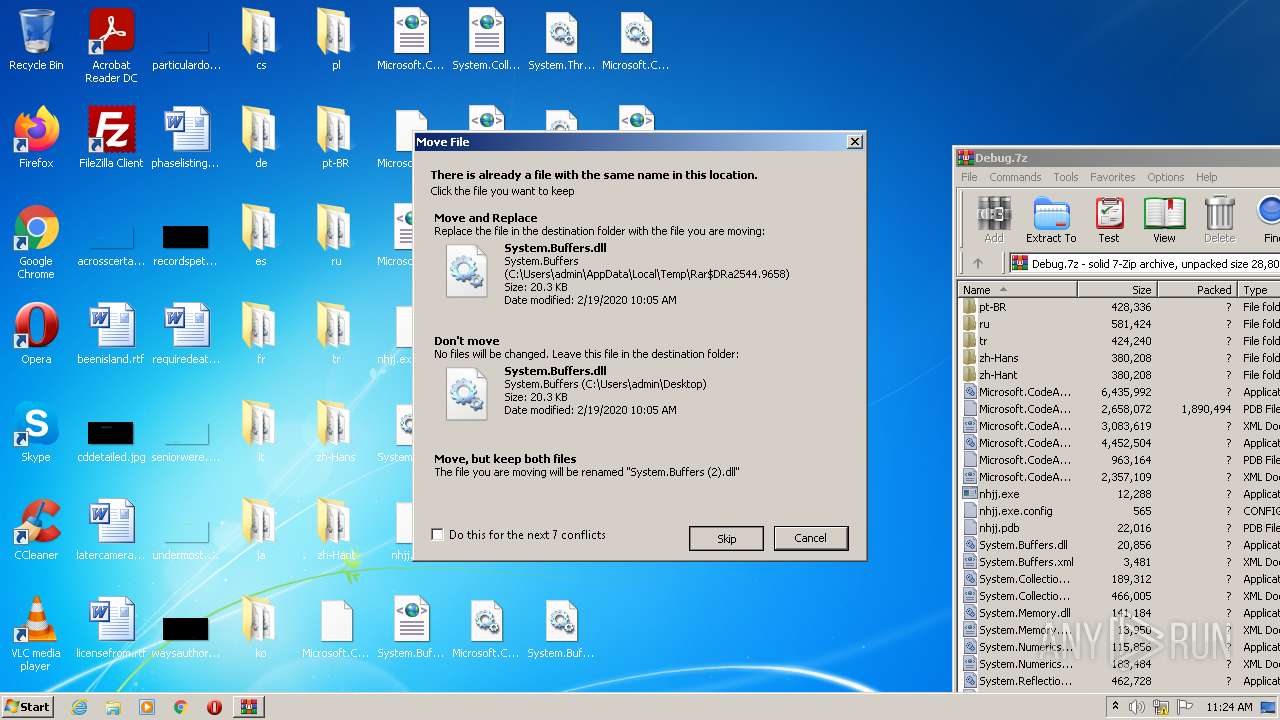
| 2544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2544.6133\System.Runtime.CompilerServices.Unsafe.dll | executable | |
MD5:C610E828B54001574D86DD2ED730E392 | SHA256:37768488E8EF45729BC7D9A2677633C6450042975BB96516E186DA6CB9CD0DCF | |||
| 528 | Explorer.EXE | C:\Users\admin\Desktop\System.Memory.dll | executable | |
MD5:6FB95A357A3F7E88ADE5C1629E2801F8 | SHA256:8E76318E8B06692ABF7DAB1169D27D15557F7F0A34D36AF6463EFF0FE21213C7 | |||
| 2544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2544.6133\System.Numerics.Vectors.dll | executable | |
MD5:AAA2CBF14E06E9D3586D8A4ED455DB33 | SHA256:1D3EF8698281E7CF7371D1554AFEF5872B39F96C26DA772210A33DA041BA1183 | |||
| 2544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2544.6133\System.Text.Encoding.CodePages.dll | executable | |
MD5:4C12C76415A3D8AF9C3CBCF0A3CB52DD | SHA256:87F7F43626CAC445A9CBACDA4068C51C0B17B6AF6E6B752FF613668C21E49412 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report