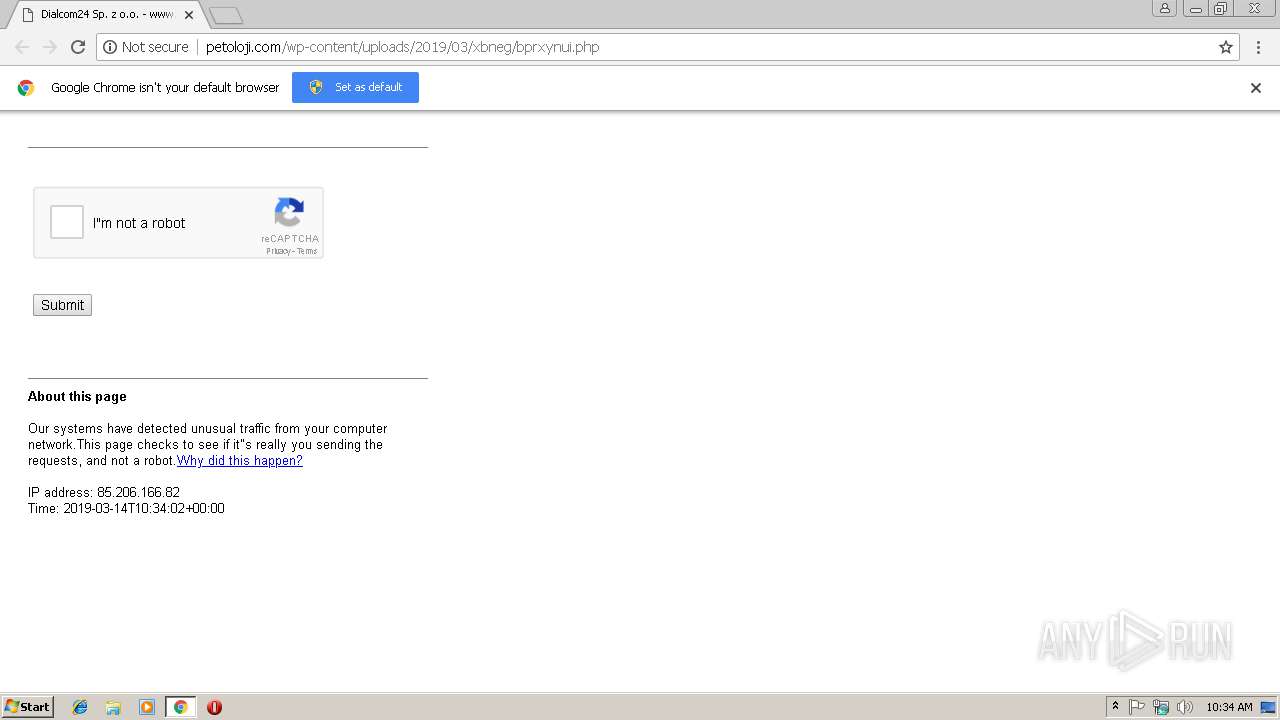
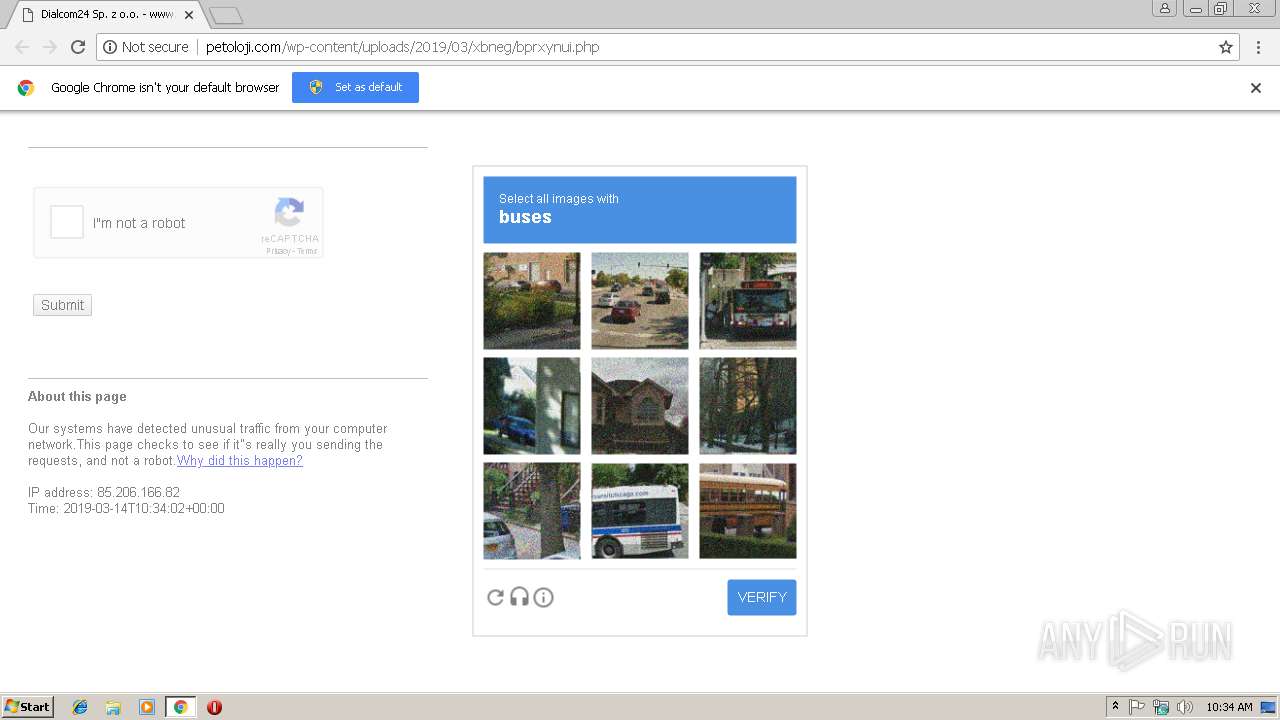
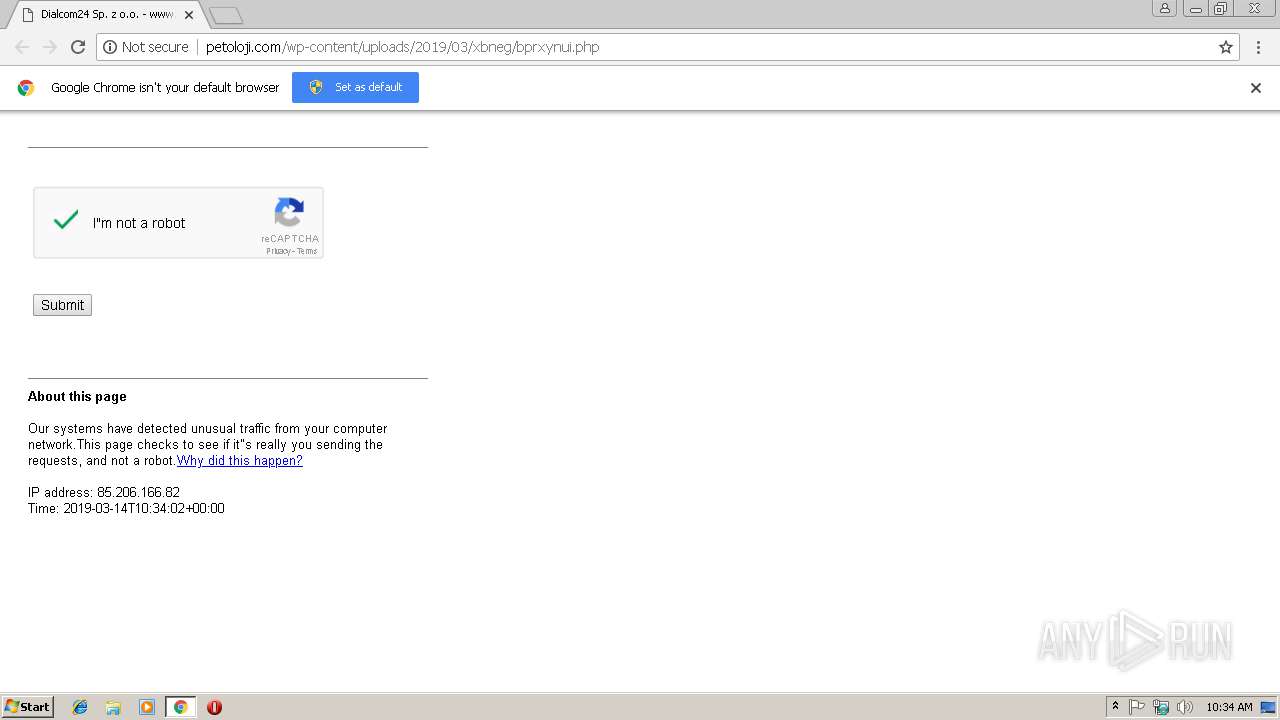
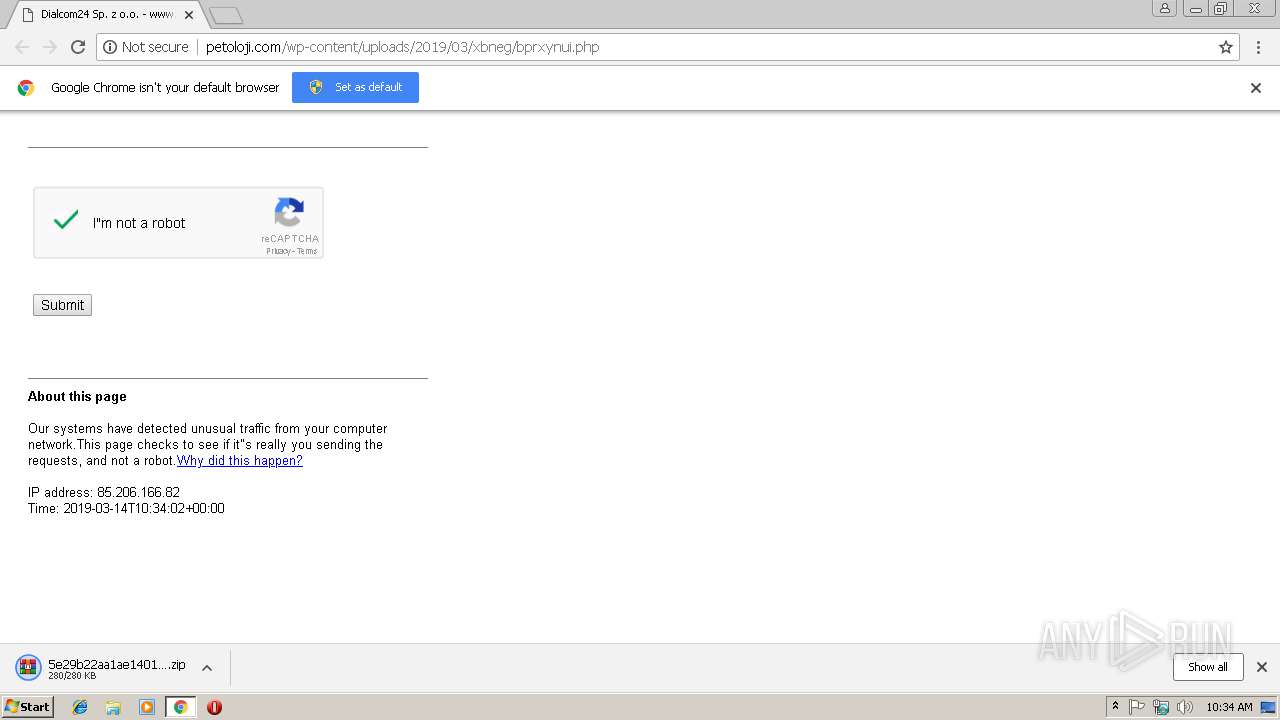
| URL: | http://petoloji.com/wp-content/uploads/2019/03/xbneg/bprxynui.php |
| Full analysis: | https://app.any.run/tasks/65fb9829-aaa0-490c-98c3-16d926247dd1 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 10:33:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E4A47F9F3F28EF05FA267DD43F64CC29 |
| SHA1: | FA88AE28F92A6AB2781B0C0F8E69D346E70C86DD |
| SHA256: | 83DF849A4CC798696D1104F67A707278069C23921F3F952FA95C8A47639255CC |
| SSDEEP: | 3:N1KOARSVtmOlAQyX28KGCc9UfHn:COlVQOlAZGZjPn |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- WScript.exe (PID: 4008)
Loads dropped or rewritten executable
- rundll32.exe (PID: 4004)
- regsvr32.exe (PID: 2452)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 3724)
Executes scripts
- WinRAR.exe (PID: 560)
Uses RUNDLL32.EXE to load library
- regsvr32.exe (PID: 2452)
Executable content was dropped or overwritten
- WScript.exe (PID: 4008)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3376)
Application launched itself
- chrome.exe (PID: 3376)
Reads Internet Cache Settings
- chrome.exe (PID: 3376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
15
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
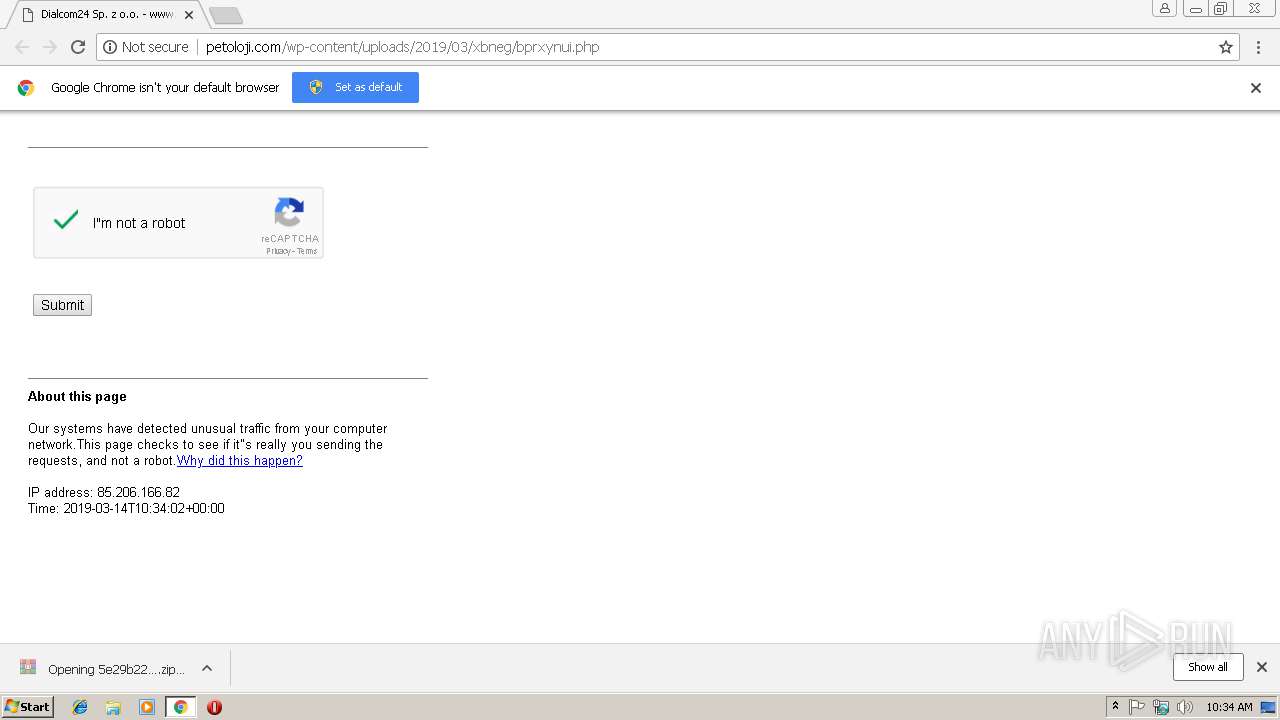
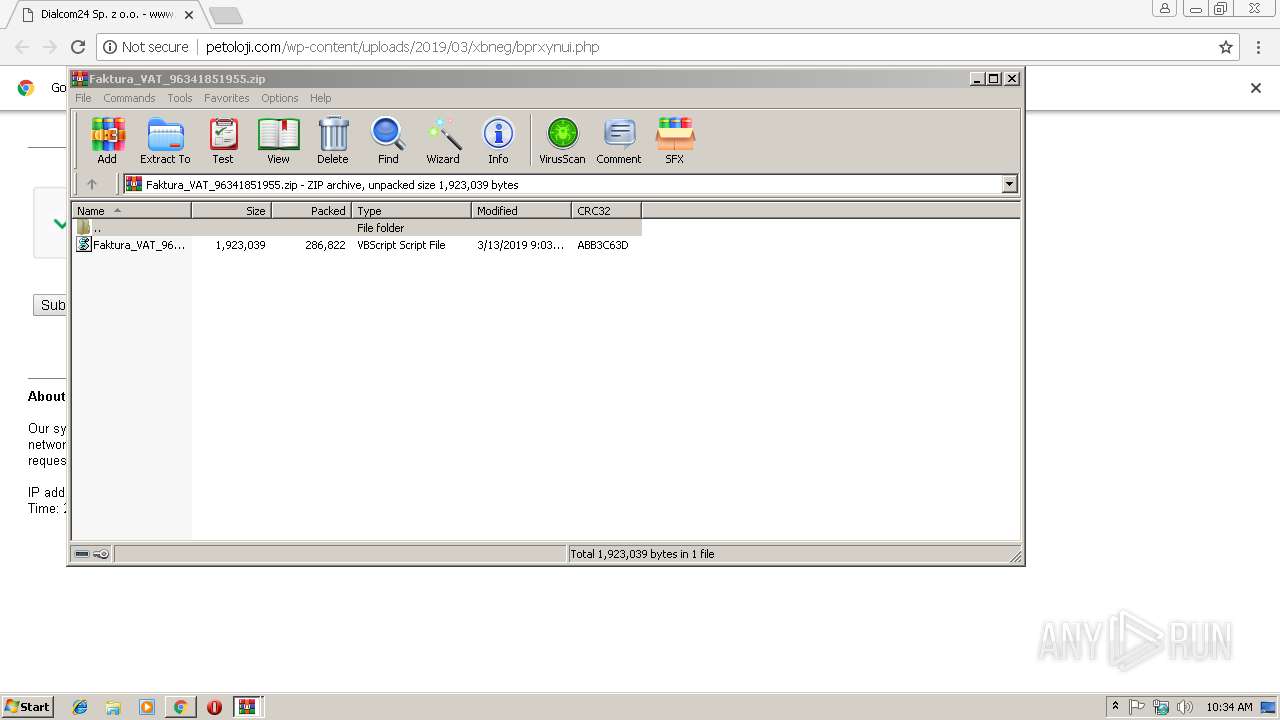
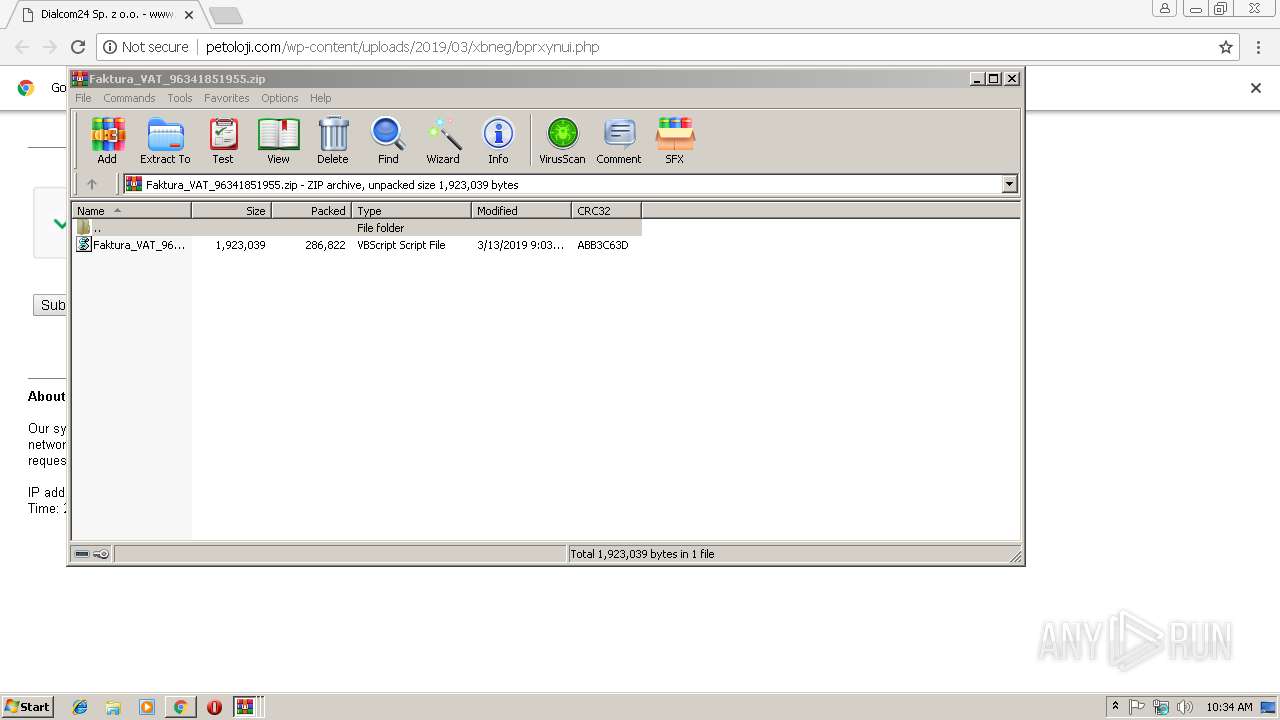
| 560 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa3724.16186\Faktura_VAT_96341851955.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6000b0,0x6f6000c0,0x6f6000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2452 | "C:\Windows\System32\regsvr32.exe" -s C:\Users\admin\AppData\Local\Temp/ofoM.dll | C:\Windows\System32\regsvr32.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=33FF2C0AC3CCF2B4F5A9F9DE1C426F58 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=A6F42A75E5BF78C261F41D79EEB9127E --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A6F42A75E5BF78C261F41D79EEB9127E --renderer-client-id=4 --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://petoloji.com/wp-content/uploads/2019/03/xbneg/bprxynui.php | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4404ACA4B48737E517F93BF55ECC0473 --mojo-platform-channel-handle=3908 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3380 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
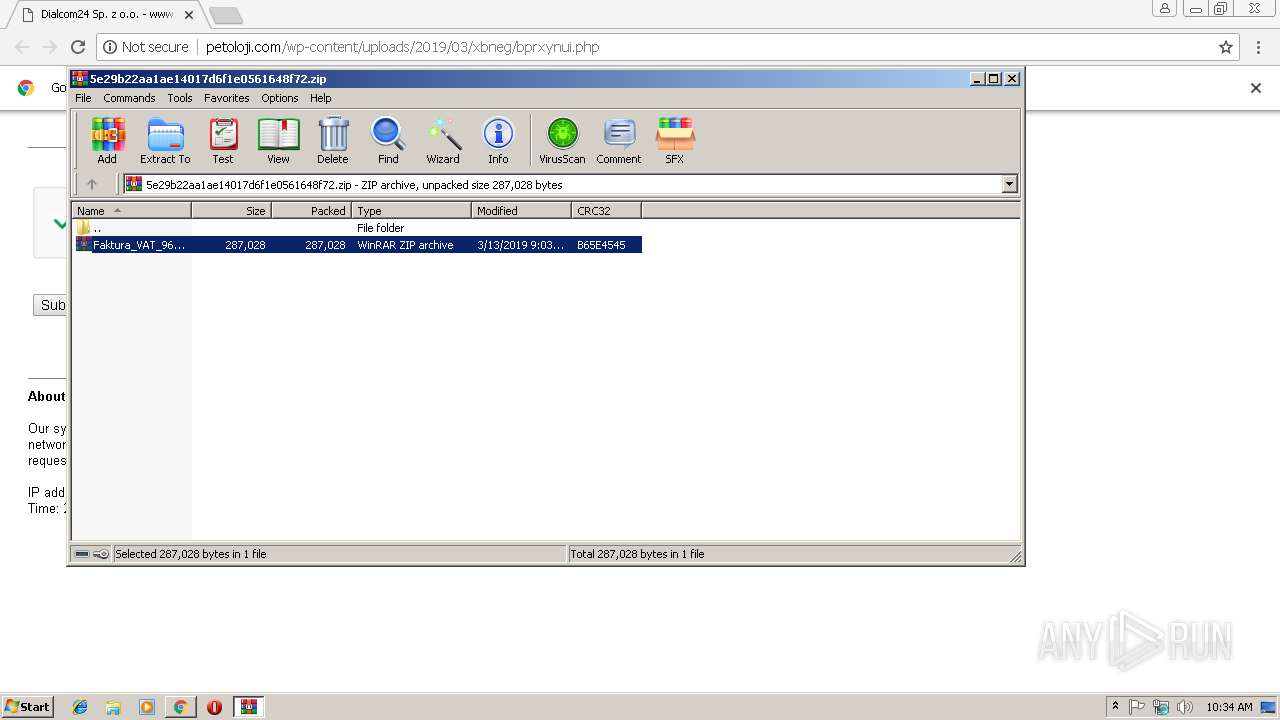
| 3696 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa3724.16721\Faktura_VAT_96341851955.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
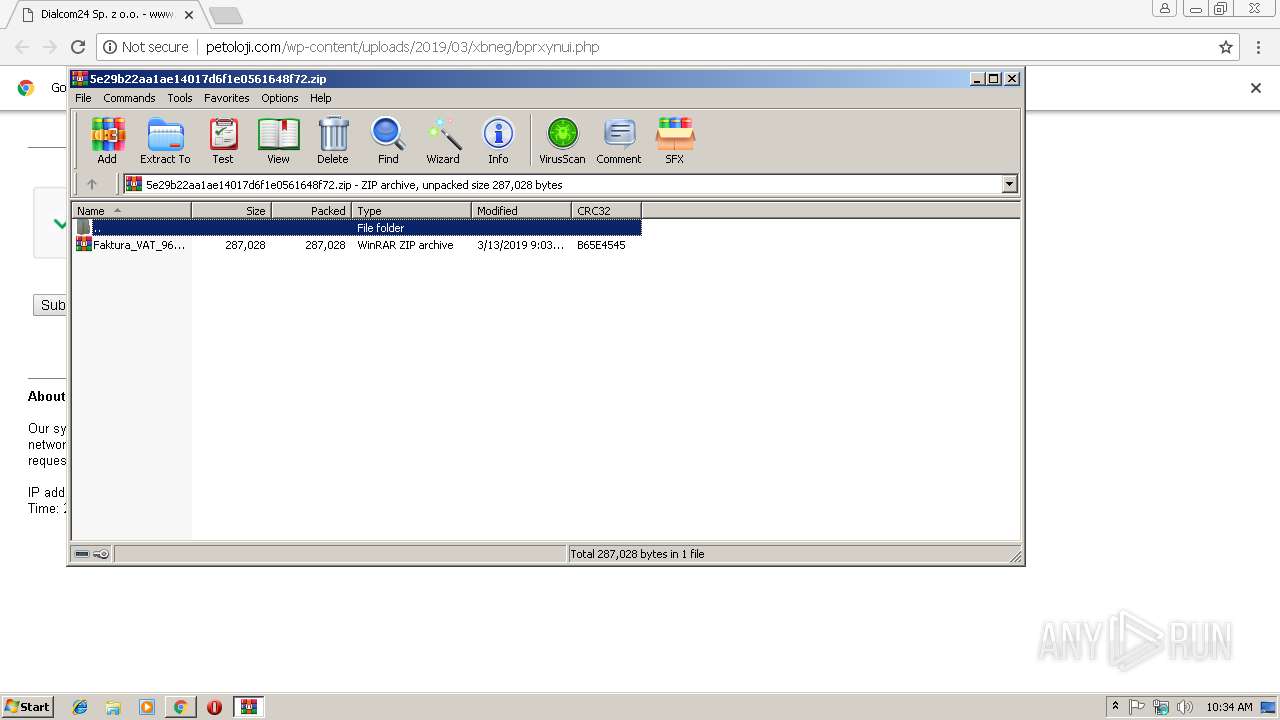
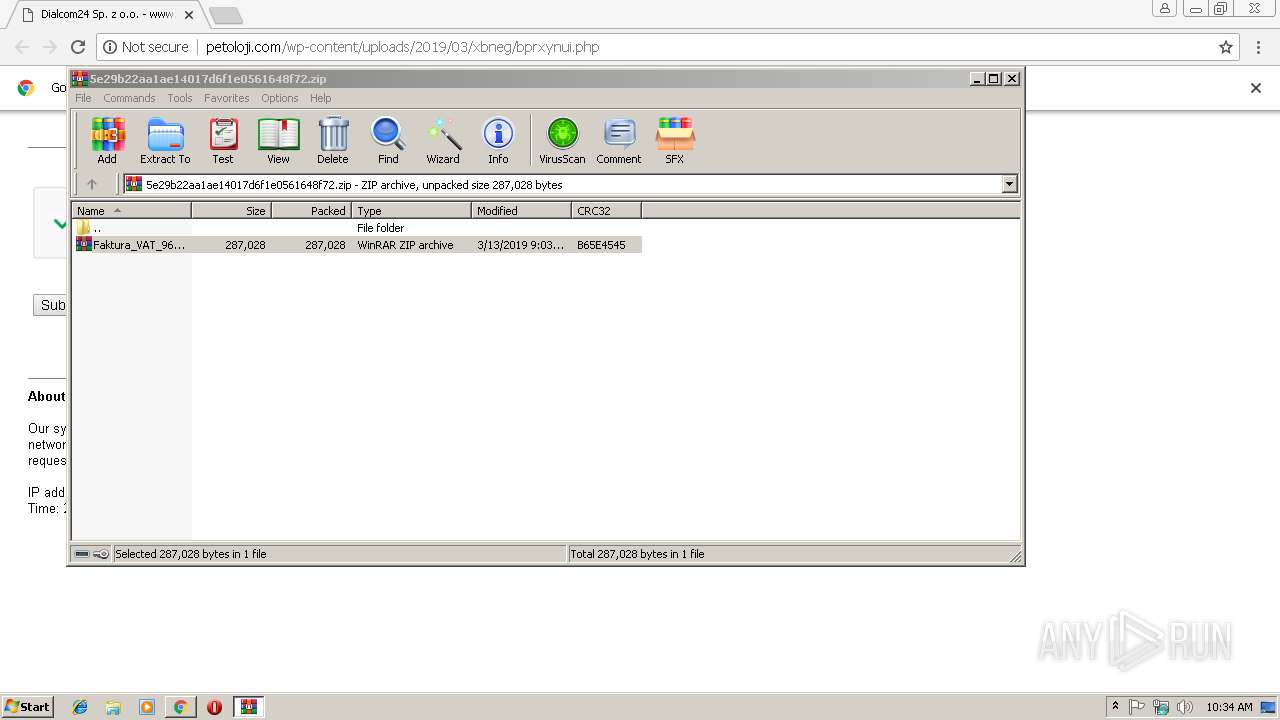
| 3724 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\5e29b22aa1ae14017d6f1e0561648f72.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 217
Read events
2 124
Write events
90
Delete events
3
Modification events
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3376-13197033239841750 |
Value: 259 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3376-13197033239841750 |
Value: 259 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
6
Suspicious files
19
Text files
52
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6b01bbe3-bb4f-42c5-b8c7-1875e44c0003.tmp | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\39465315-f9db-4af8-86ea-7c6663d50cd2.tmp | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF198870.TMP | text | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF198785.TMP | text | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF198795.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
13
DNS requests
7
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3376 | chrome.exe | GET | 200 | 89.252.130.228:80 | http://petoloji.com/wp-content/uploads/2019/03/xbneg/bprxynui.php | TR | html | 123 Kb | unknown |
3376 | chrome.exe | GET | 200 | 89.252.130.228:80 | http://petoloji.com/favicon.ico | TR | html | 141 b | unknown |
3376 | chrome.exe | GET | 200 | 89.252.130.228:80 | http://petoloji.com/wp-content/uploads/2019/03/xbneg/bprxynui.php?down9cf2906742e439c7cd529c4941b6344c | TR | compressed | 280 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3376 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 216.58.206.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 216.58.205.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
4004 | rundll32.exe | 153.182.78.20:443 | — | NTT Communications Corporation | JP | malicious |
3376 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4004 | rundll32.exe | 185.92.222.238:443 | — | Choopa, LLC | NL | malicious |
4004 | rundll32.exe | 214.161.108.156:443 | — | DoD Network Information Center | US | malicious |
3376 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 89.252.130.228:80 | petoloji.com | Netinternet Bilisim Teknolojileri AS | TR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
petoloji.com |
| unknown |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4004 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
4004 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
4004 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
4004 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |