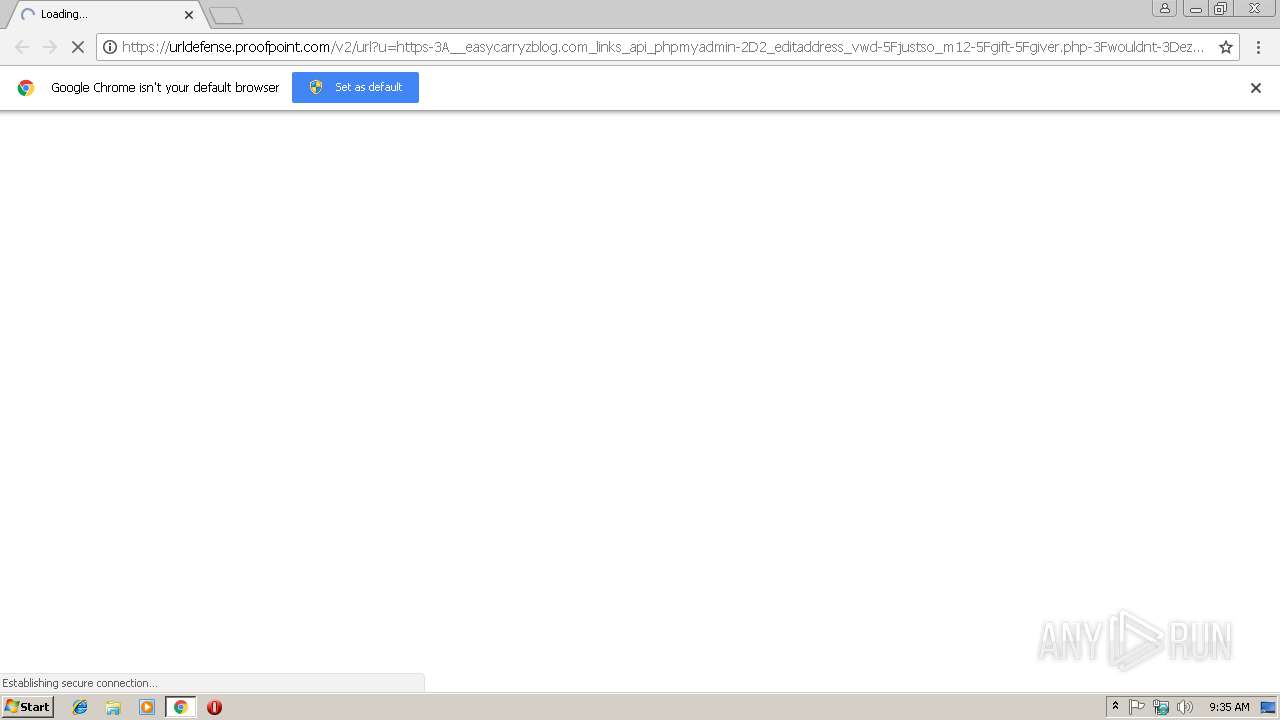
| URL: | https://urldefense.proofpoint.com/v2/url?u=https-3A__easycarryzblog.com_links_api_phpmyadmin-2D2_editaddress_vwd-5Fjustso_m12-5Fgift-5Fgiver.php-3Fwouldnt-3Dezx1b02dd5nuq0d&d=DwIFAg&c=SsZxQMfaWJ1sSVfloc5FVGba8BA_qR4Jzdt8ol2oSPA&r=kwWm79huM4XoesfUcpHCe4mZR4YlRg1XwwybZ2uxk-ExNL-gwyjsskfjbeqXX7GE&m=tlk9CzNKc147pFw3-nfpaFEahovfkcMfvDNwLu8SrgM&s=nWCgZRHn4OIEF_A7oADx3m21Znb3Vs2gpq12JsP8-LU&e= |
| Full analysis: | https://app.any.run/tasks/e27c66b1-d168-469f-b337-3cd905050a82 |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2019, 09:34:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 222C7CEEC7B861BC8E0F8AFCB9D5EB16 |
| SHA1: | 516B70702279555F1185B8498C37ED3DEFC128DB |
| SHA256: | 83DE1937E924FACE4D4B0B20282E6E3647E4B2397C42940B4D222987CF0C8B32 |
| SSDEEP: | 6:2UJNP1BZgjeLdIg+x7gBQ5kMbzMbcoJYoYgIz8Y3YNkY+y8O9ZZaU6OVUn:2UHP1fg2Ig+2QFbzocoJXY3++yVmU6Oy |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2924)
Reads settings of System Certificates
- chrome.exe (PID: 2924)
Changes settings of System certificates
- chrome.exe (PID: 2924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=900,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=FECC162750EEDF274C945303724CBF7B --mojo-platform-channel-handle=4224 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=900,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=CBA6C4FA4B6F0E26D81B212AD36E2C50 --mojo-platform-channel-handle=3352 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2928 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://urldefense.proofpoint.com/v2/url?u=https-3A__easycarryzblog.com_links_api_phpmyadmin-2D2_editaddress_vwd-5Fjustso_m12-5Fgift-5Fgiver.php-3Fwouldnt-3Dezx1b02dd5nuq0d&d=DwIFAg&c=SsZxQMfaWJ1sSVfloc5FVGba8BA_qR4Jzdt8ol2oSPA&r=kwWm79huM4XoesfUcpHCe4mZR4YlRg1XwwybZ2uxk-ExNL-gwyjsskfjbeqXX7GE&m=tlk9CzNKc147pFw3-nfpaFEahovfkcMfvDNwLu8SrgM&s=nWCgZRHn4OIEF_A7oADx3m21Znb3Vs2gpq12JsP8-LU&e= | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=900,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=41047BB1885DB6A07FF9432196EE1527 --mojo-platform-channel-handle=4336 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=D98078C2AB2F37394DB98912B6D15B63 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D98078C2AB2F37394DB98912B6D15B63 --renderer-client-id=3 --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=900,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=44C30A20334982FA65A9A18467E1CC59 --mojo-platform-channel-handle=628 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=D4E1ADAC801699FFCE8646864DEF74C5 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D4E1ADAC801699FFCE8646864DEF74C5 --renderer-client-id=5 --mojo-platform-channel-handle=3376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x701500b0,0x701500c0,0x701500cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
533
Read events
466
Write events
63
Delete events
4
Modification events
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2924-13194351298456625 |
Value: 259 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2924-13194351298456625 |
Value: 259 | |||
Executable files
0
Suspicious files
43
Text files
94
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\80236e9a-ce30-46e4-9a6e-a6fa699d771b.tmp | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9e90f0ad-9c64-4d02-9e5f-95ba4ee36928.tmp | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e95a.TMP | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF20e95a.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
97
DNS requests
62
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
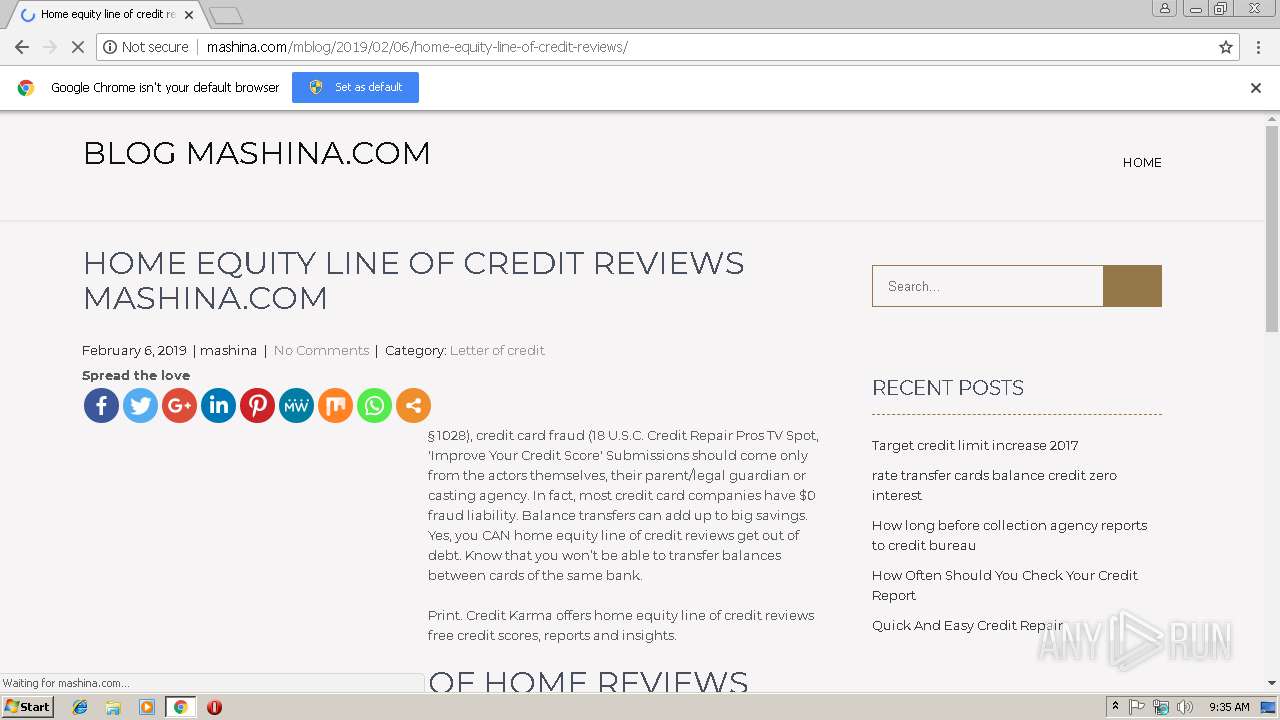
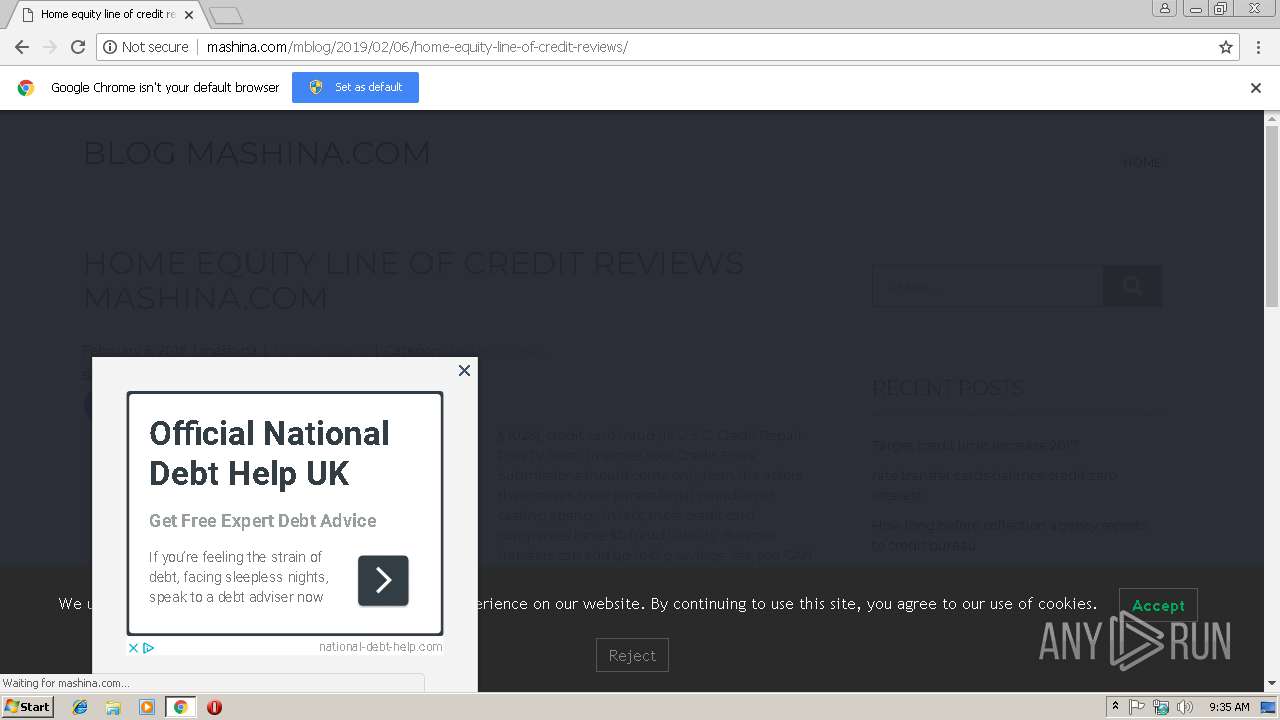
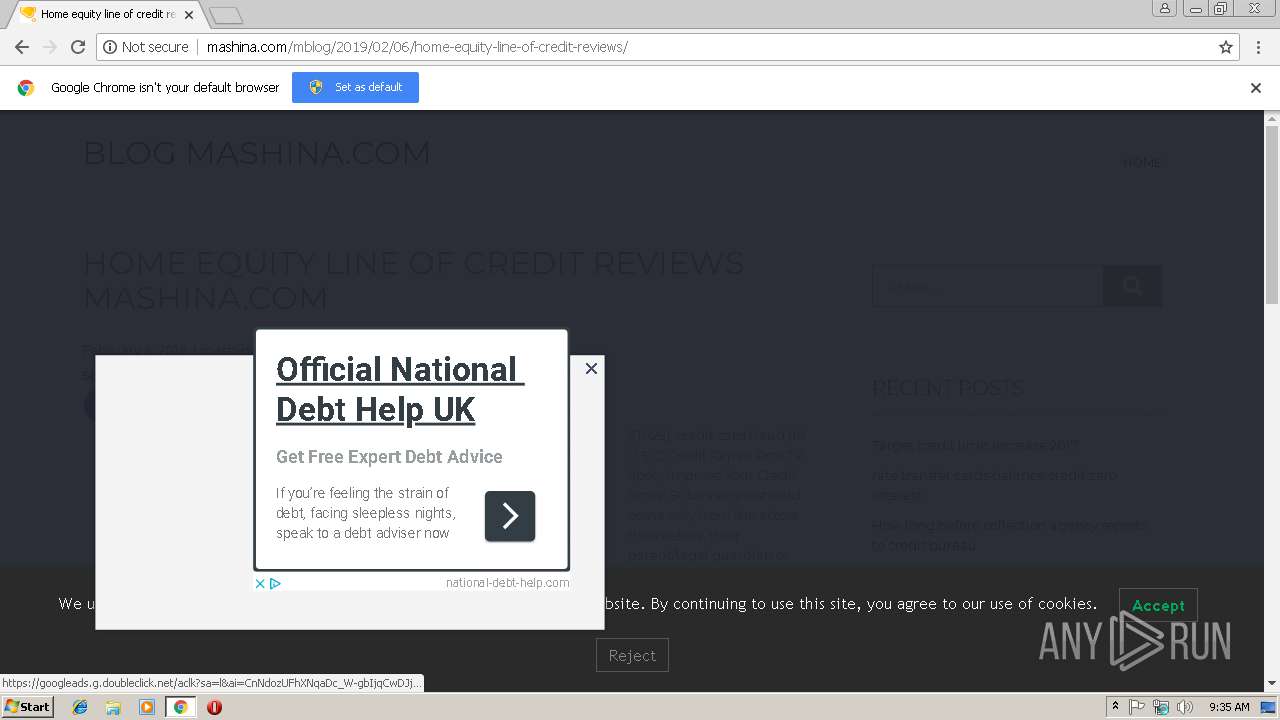
2924 | chrome.exe | GET | 301 | 89.108.105.13:80 | http://mashina.com/mblog/latestpost | RU | — | — | unknown |
2924 | chrome.exe | GET | 200 | 89.108.105.13:80 | http://mashina.com/mblog/wp-content/plugins/sassy-social-share/public/js/sassy-social-share-public.js?ver=3.2.12 | RU | text | 11.0 Kb | unknown |
2924 | chrome.exe | GET | 200 | 89.108.105.13:80 | http://mashina.com/mblog/latestpost/ | RU | html | 287 b | unknown |
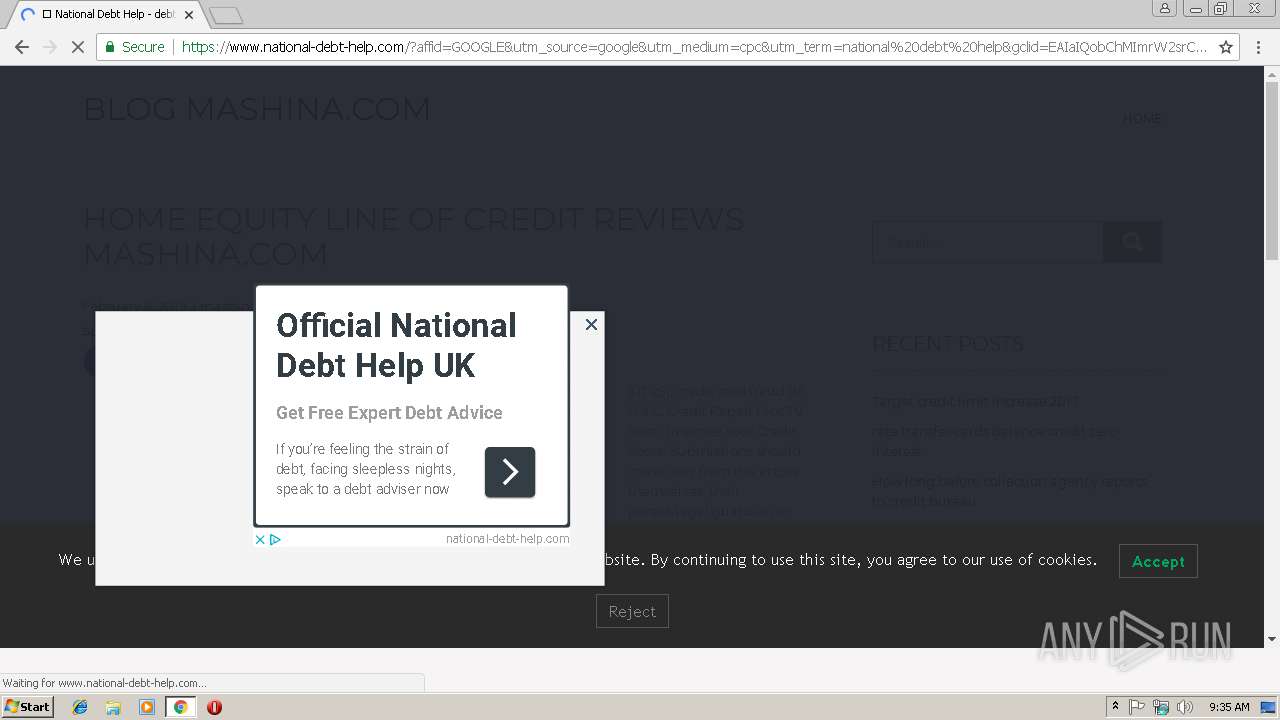
2924 | chrome.exe | GET | 200 | 91.235.137.17:80 | http://eperdreocca.tk/index/?4831537102803 | RU | html | 277 b | suspicious |
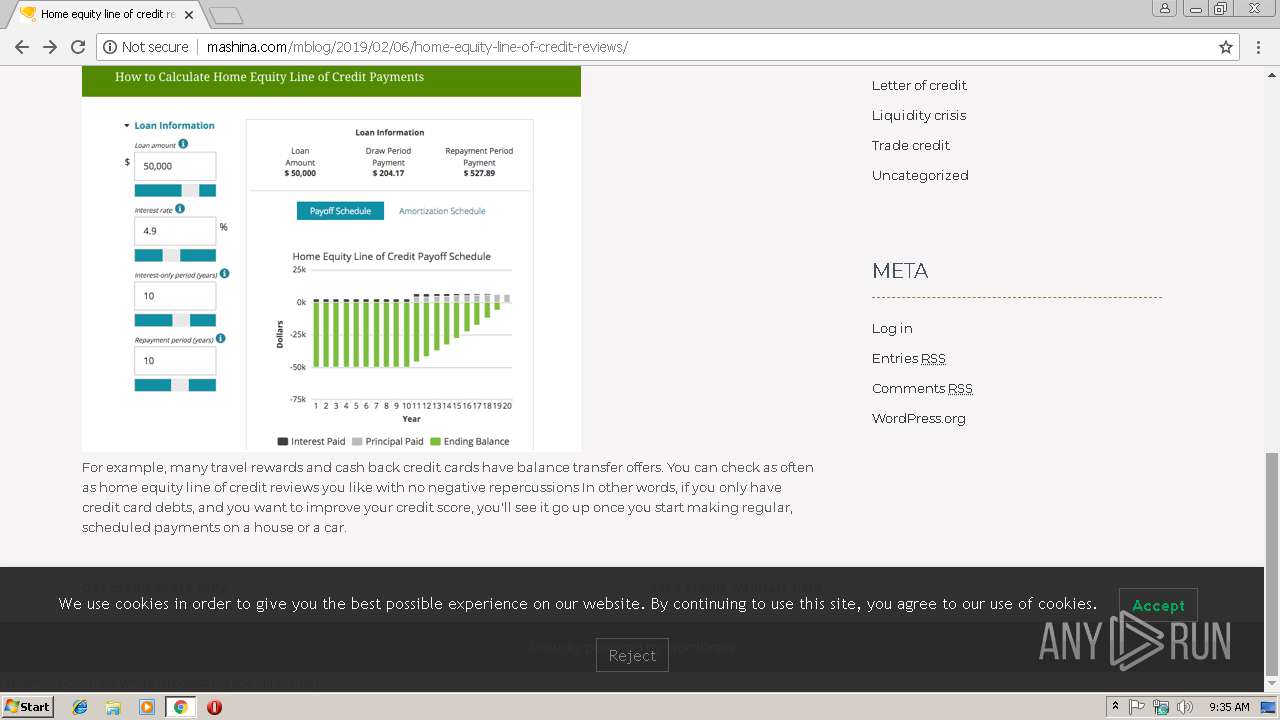
2924 | chrome.exe | POST | 200 | 89.108.105.13:80 | http://mashina.com/mblog/2019/02/06/home-equity-line-of-credit-reviews/ | RU | html | 7.42 Kb | unknown |
2924 | chrome.exe | GET | 200 | 89.108.105.13:80 | http://mashina.com/mblog/wp-content/plugins/luckywp-cookie-notice-gdpr/front/assets/main.min.css?ver=1.1.0 | RU | text | 981 b | unknown |
2924 | chrome.exe | GET | 200 | 89.108.105.13:80 | http://mashina.com/mblog/wp-content/themes/showcase-lite/css/responsive.css?ver=5.0.3 | RU | text | 1.61 Kb | unknown |
2924 | chrome.exe | GET | 200 | 89.108.105.13:80 | http://mashina.com/mblog/wp-content/plugins/sassy-social-share/admin/css/sassy-social-share-svg.css?ver=3.2.12 | RU | text | 33.4 Kb | unknown |
2924 | chrome.exe | GET | 200 | 89.108.105.13:80 | http://mashina.com/mblog/wp-content/themes/showcase-lite/css/nivo-slider.css?ver=5.0.3 | RU | text | 1.19 Kb | unknown |
2924 | chrome.exe | GET | 200 | 89.108.105.13:80 | http://mashina.com/mblog/wp-content/themes/showcase-lite/css/default.css?ver=5.0.3 | RU | text | 1.01 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2924 | chrome.exe | 67.231.146.66:443 | urldefense.proofpoint.com | Proofpoint, Inc. | US | suspicious |
2924 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 172.217.23.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
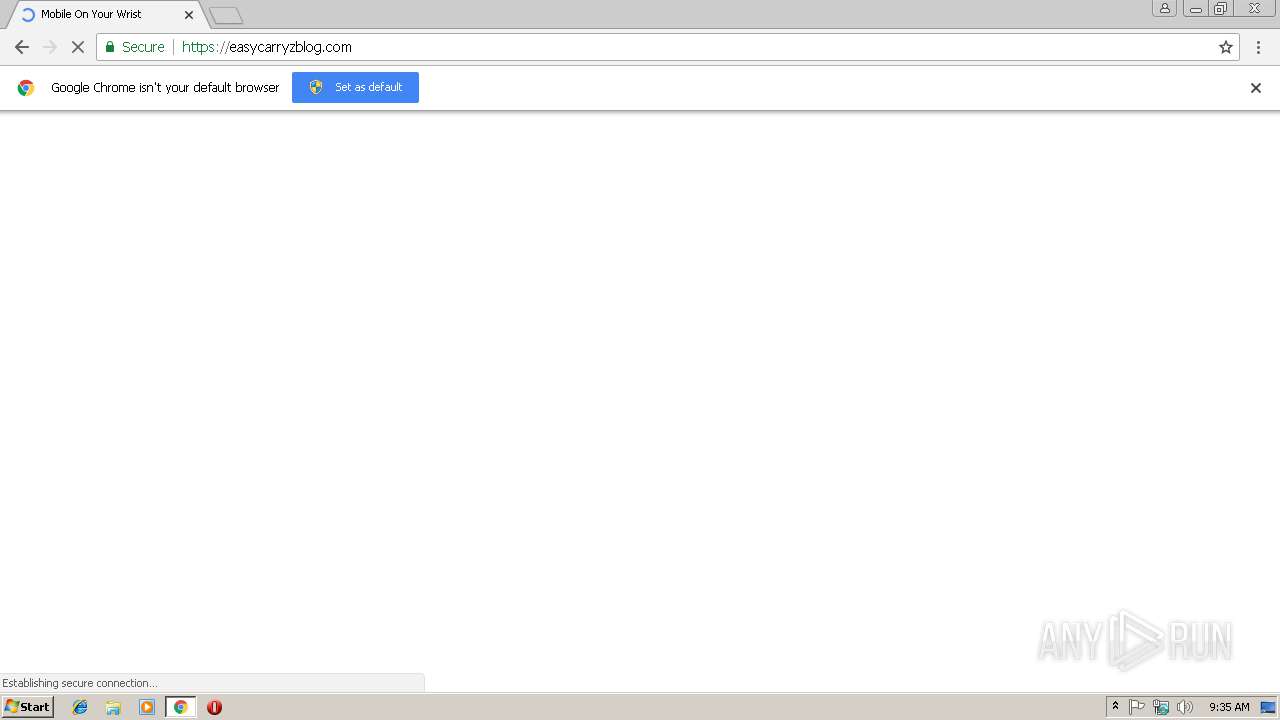
2924 | chrome.exe | 104.248.162.246:443 | easycarryzblog.com | — | US | unknown |
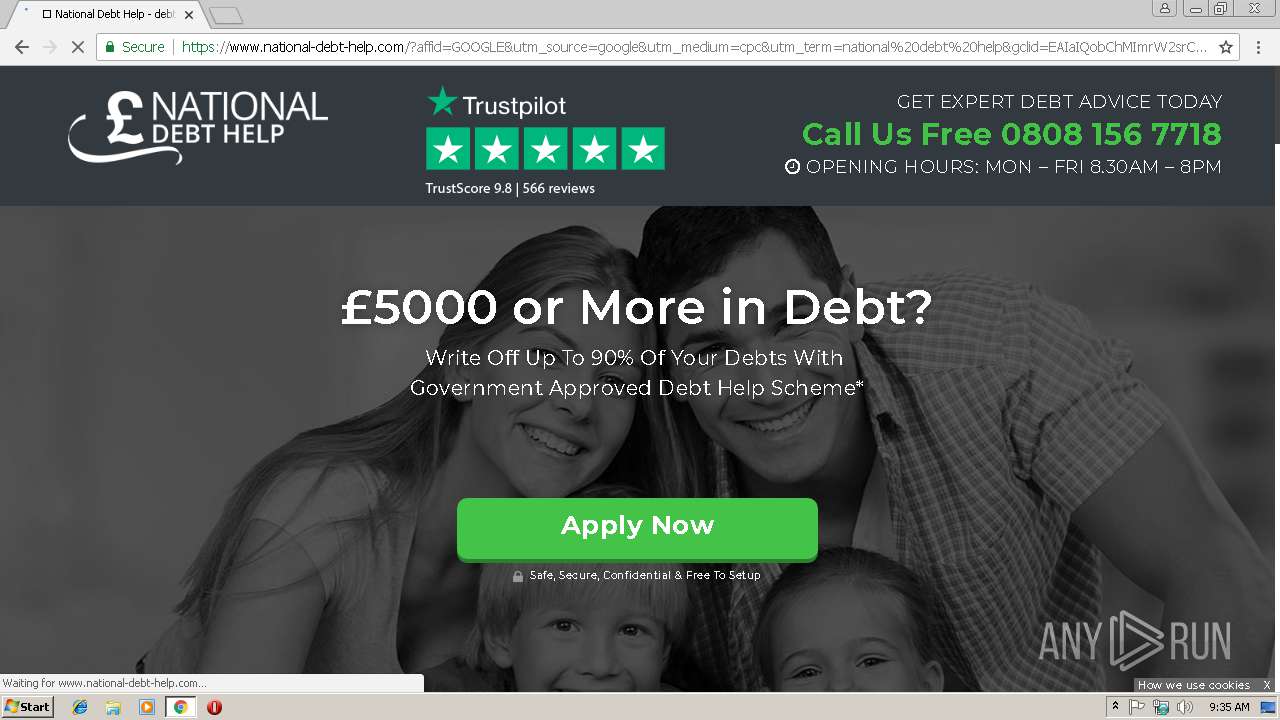
2924 | chrome.exe | 176.123.9.52:443 | getmyfreetraffic.com | Alexhost Srl | MD | unknown |
2924 | chrome.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 91.235.137.17:80 | eperdreocca.tk | Serverius Holding B.V. | RU | suspicious |
2924 | chrome.exe | 192.0.73.2:443 | secure.gravatar.com | Automattic, Inc | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
urldefense.proofpoint.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
easycarryzblog.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
getmyfreetraffic.com |
| malicious |
s.w.org |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
eperdreocca.tk |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2924 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |