| download: | setup.exe |
| Full analysis: | https://app.any.run/tasks/f6038639-6ff1-40d9-bc01-4b4db5237047 |
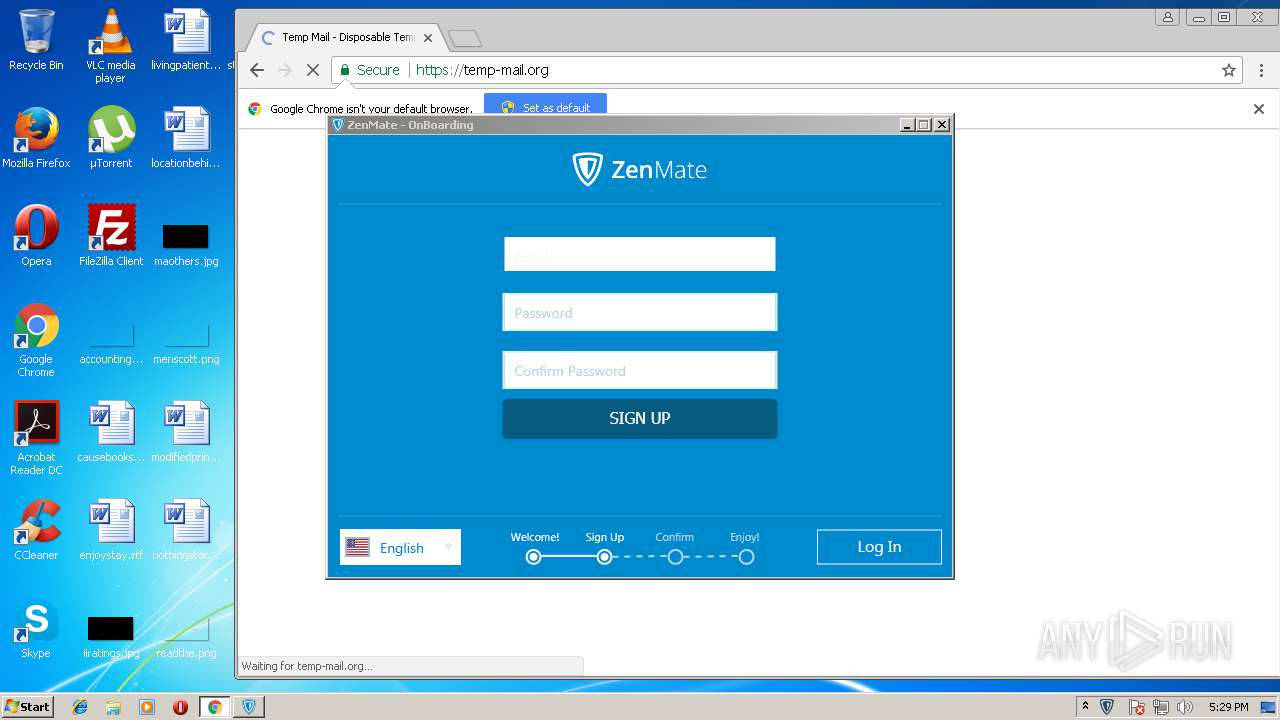
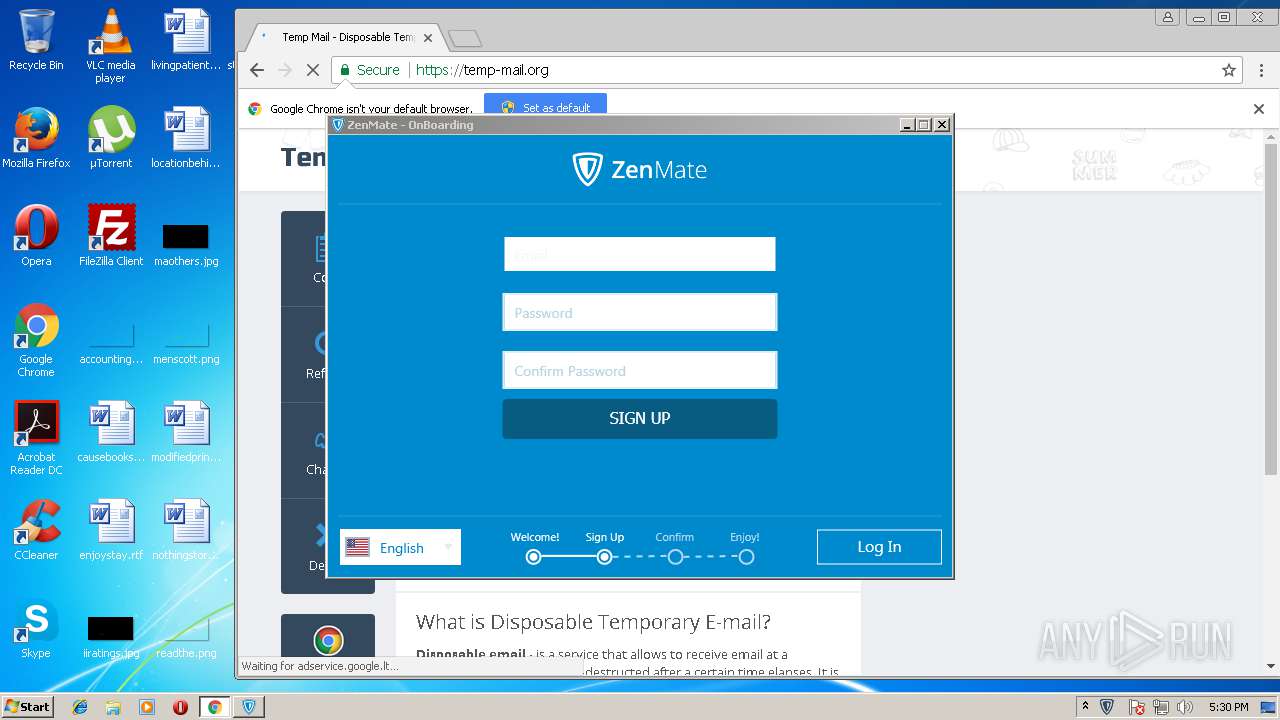
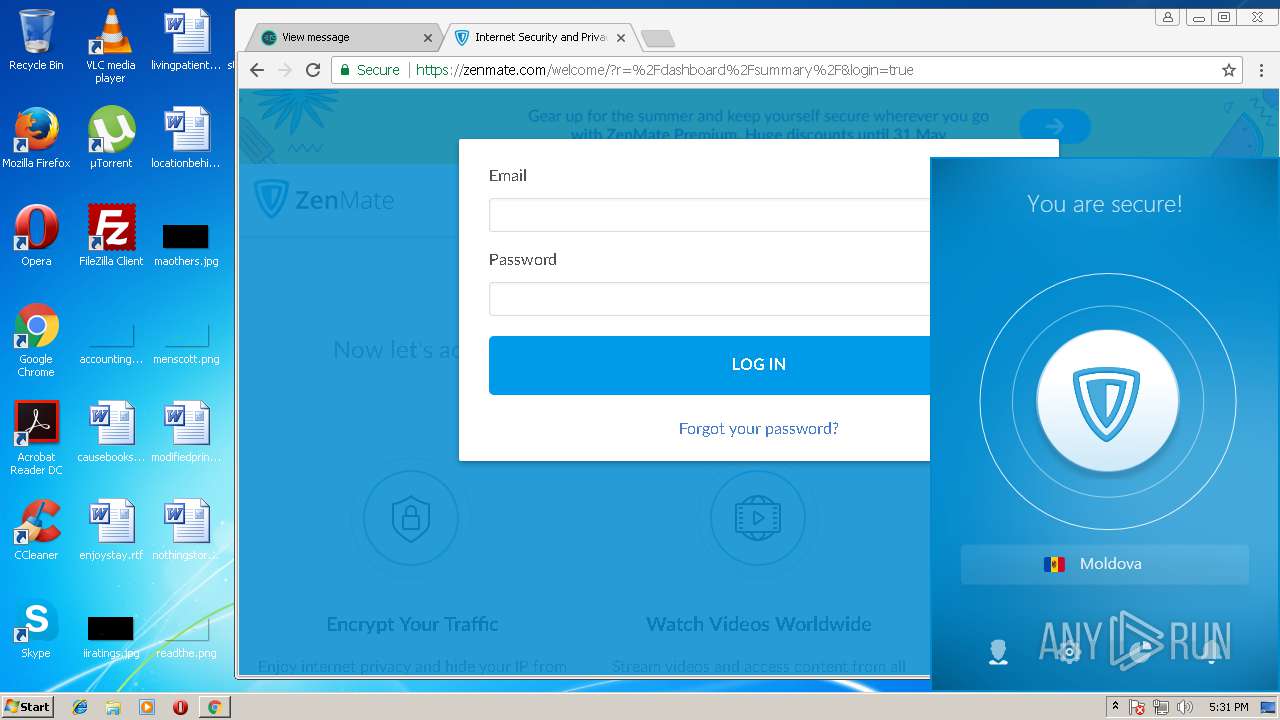
| Verdict: | Malicious activity |
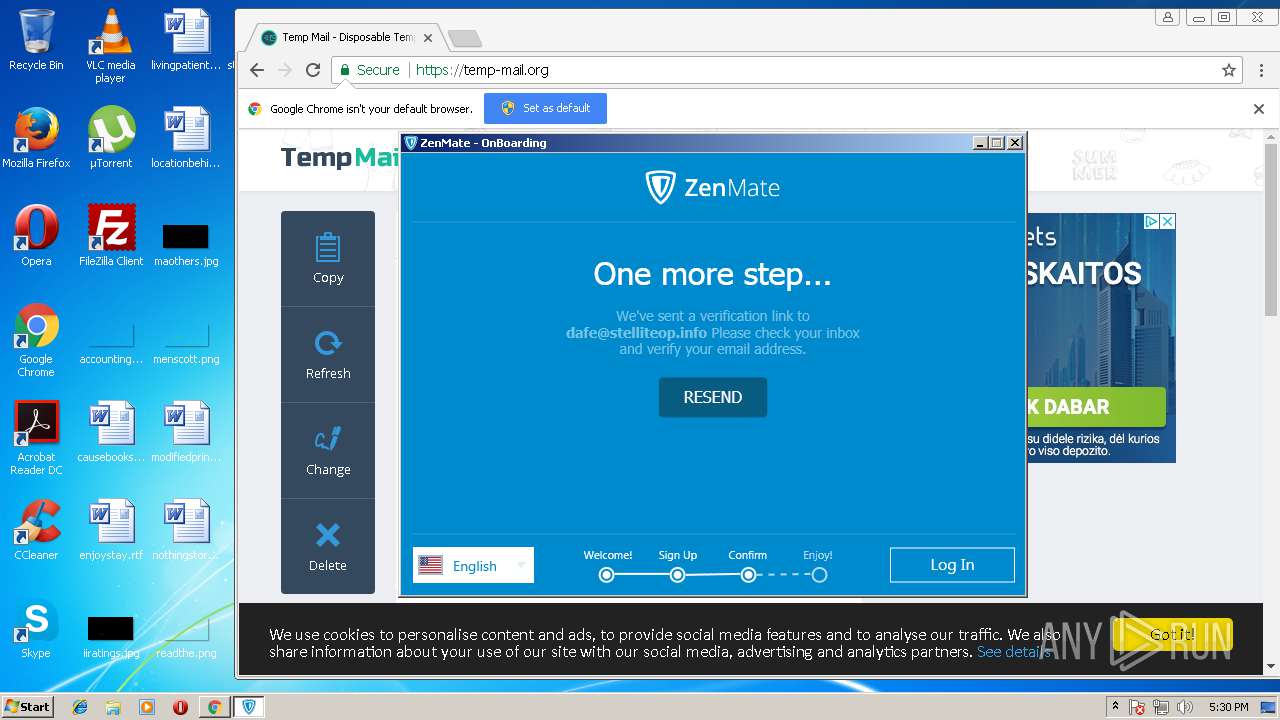
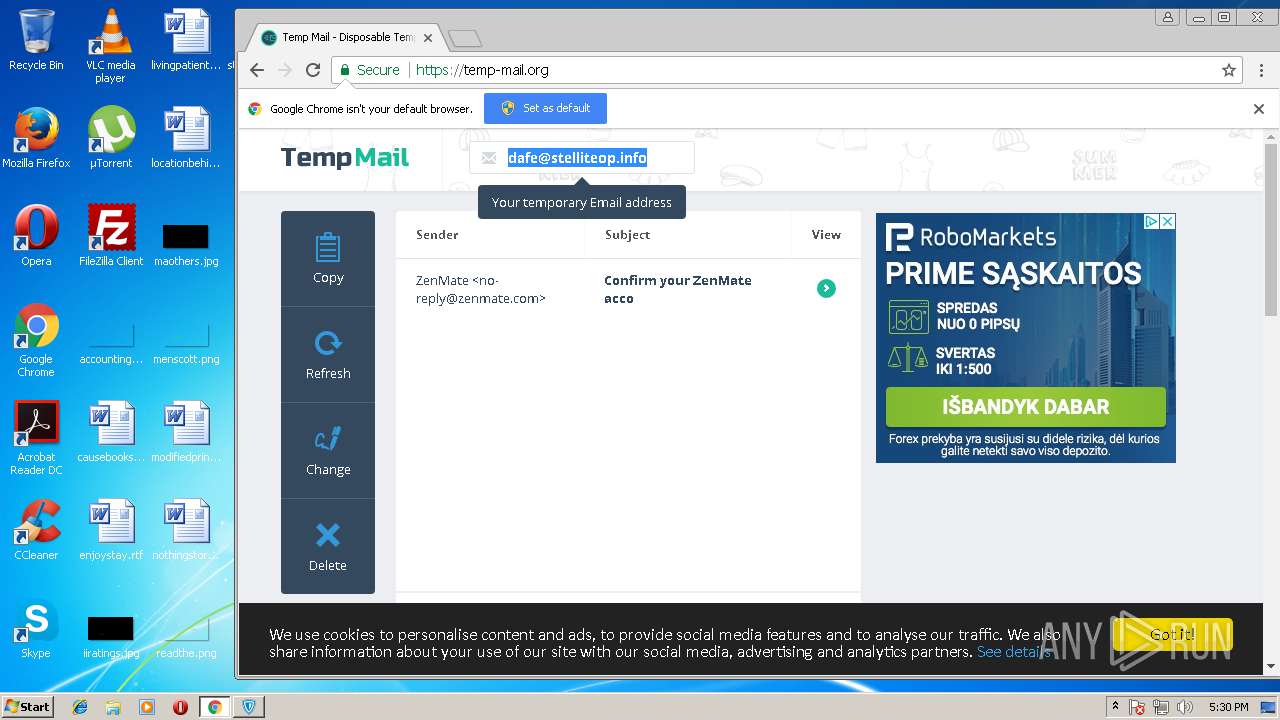
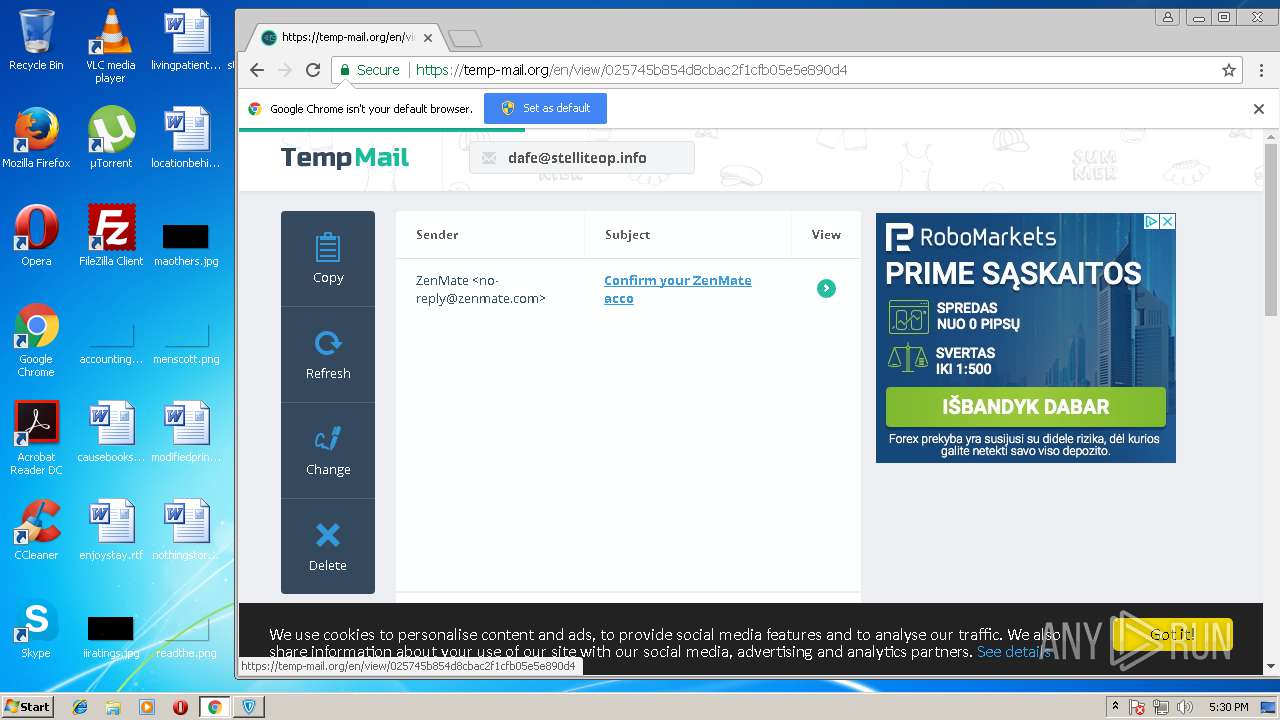
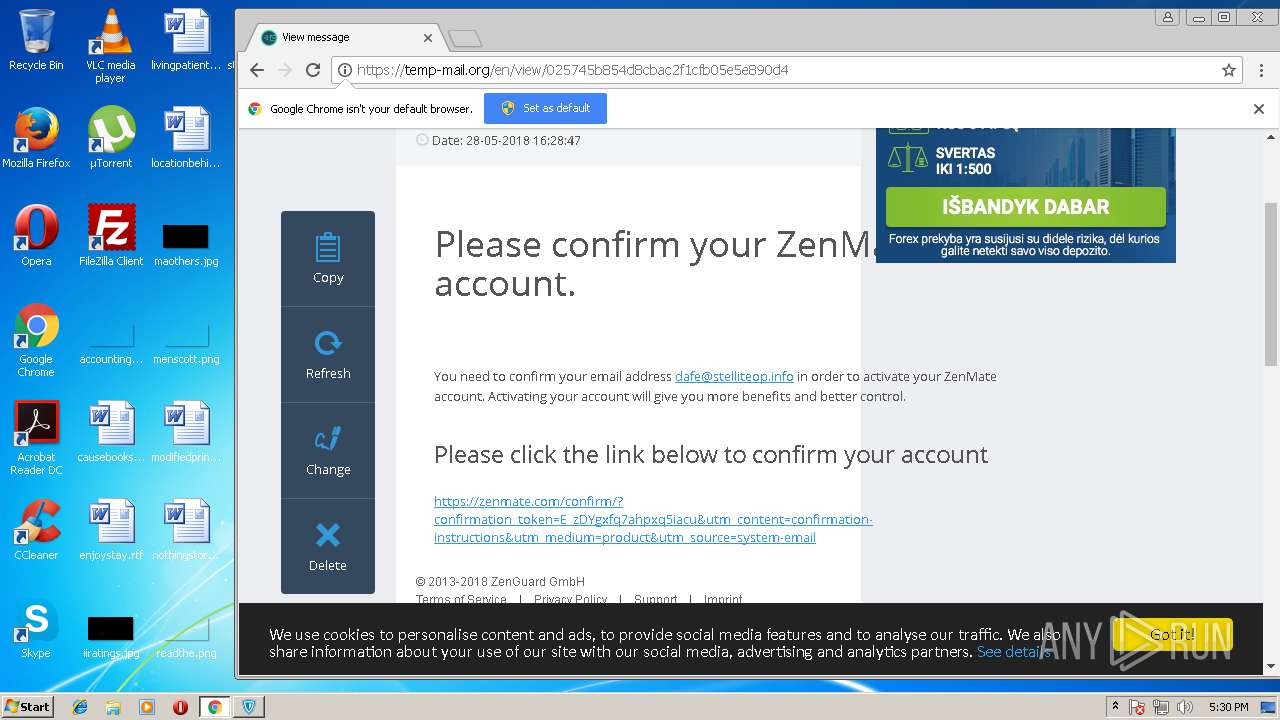
| Analysis date: | May 28, 2018, 16:28:56 |
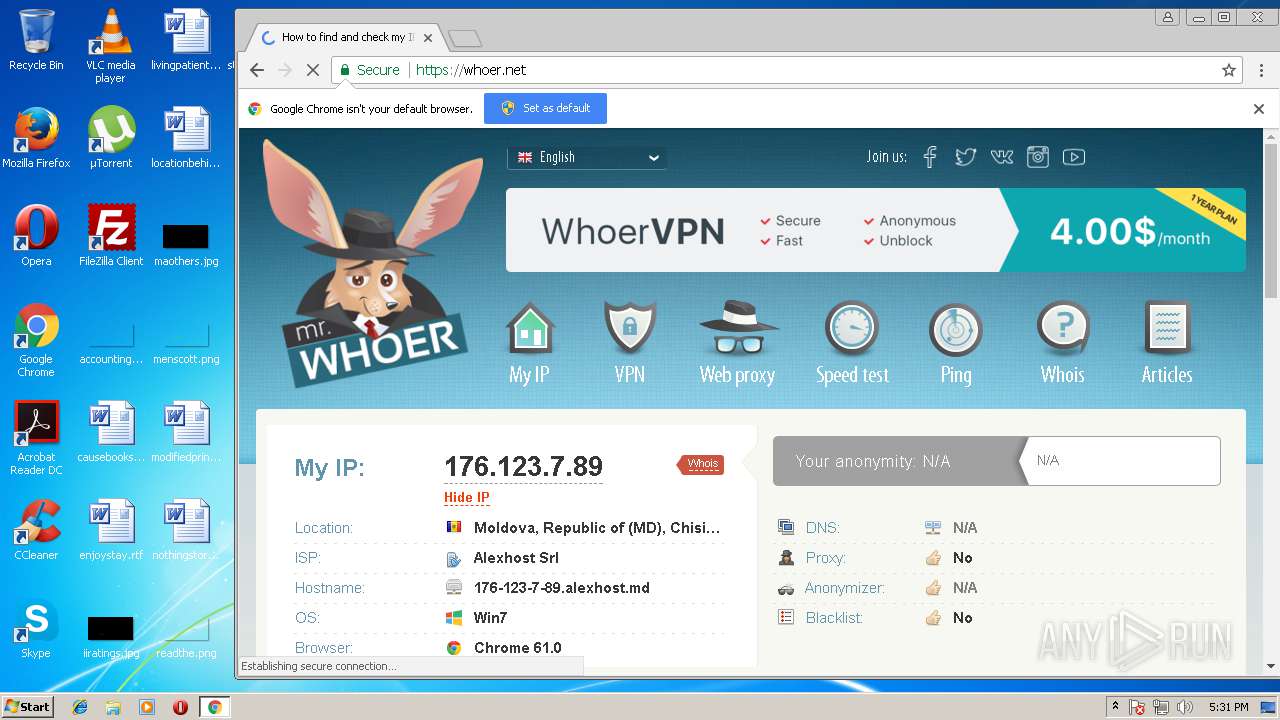
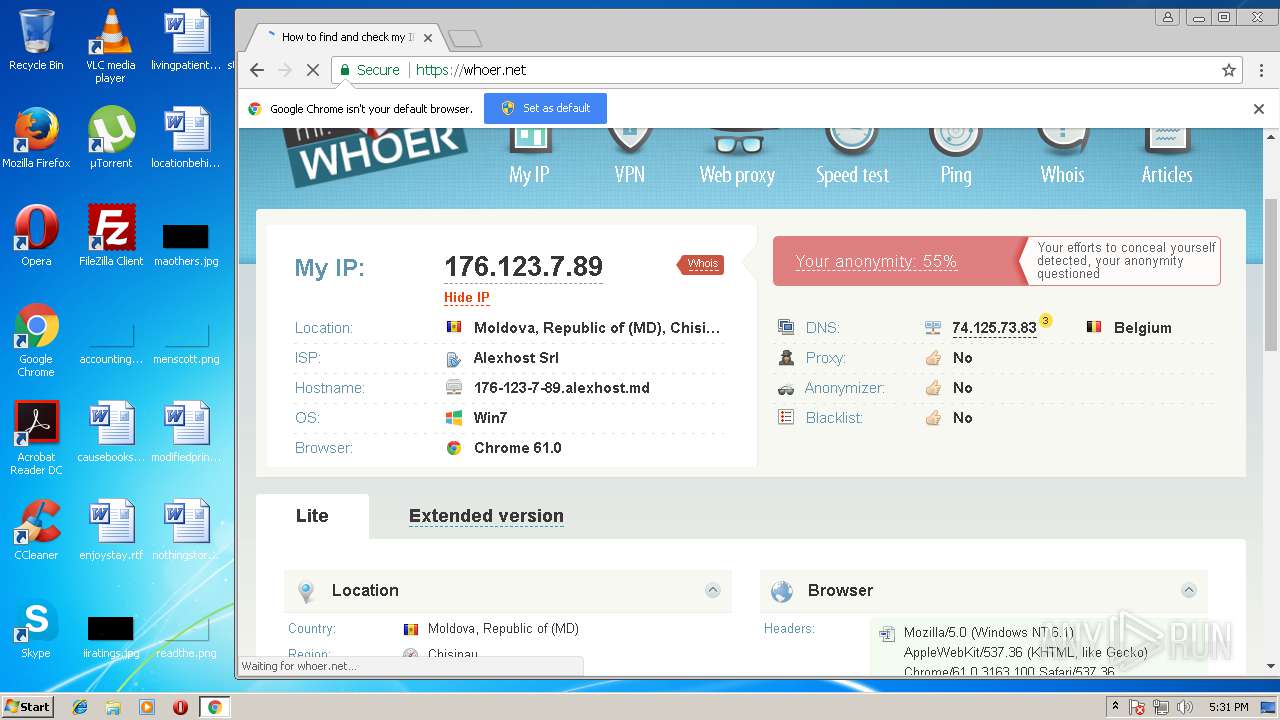
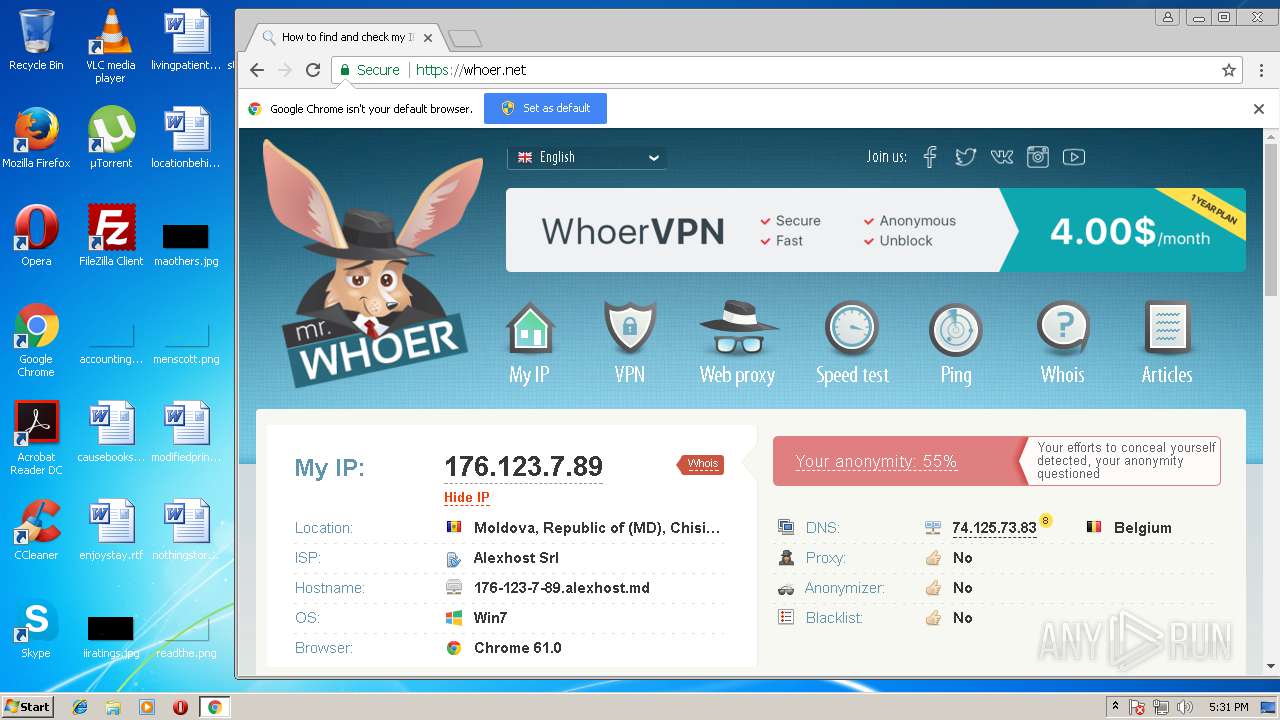
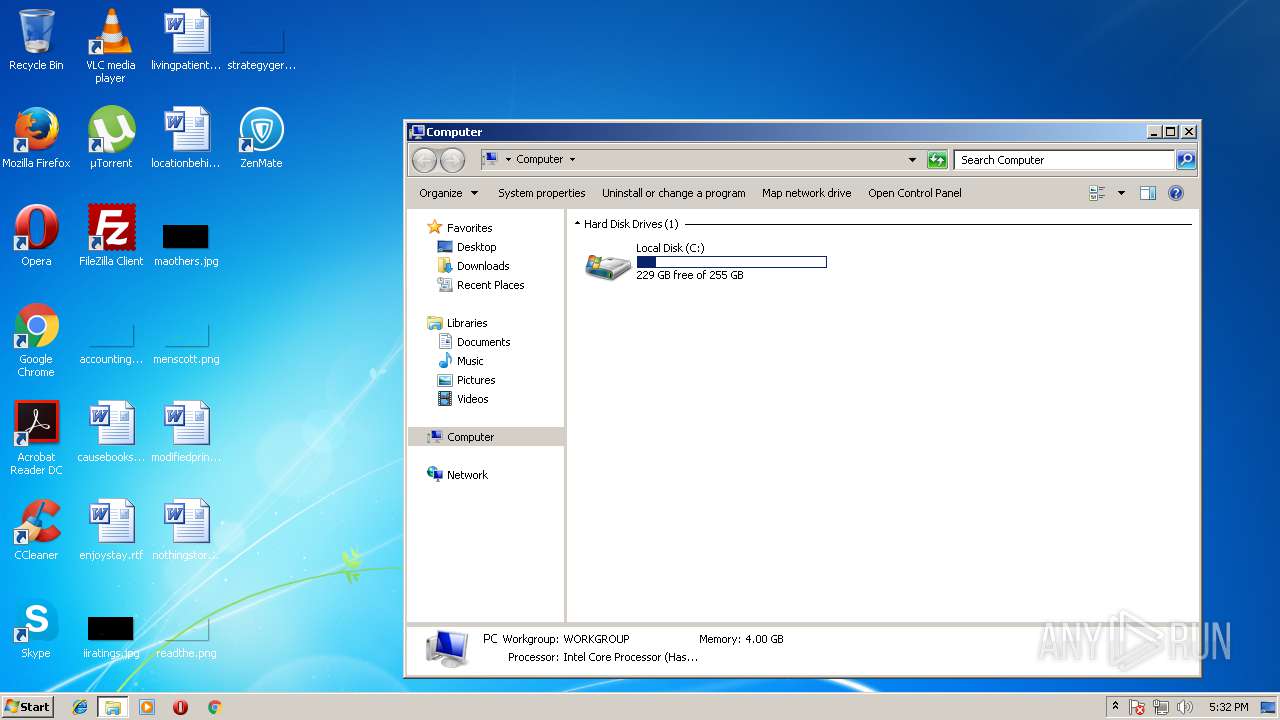
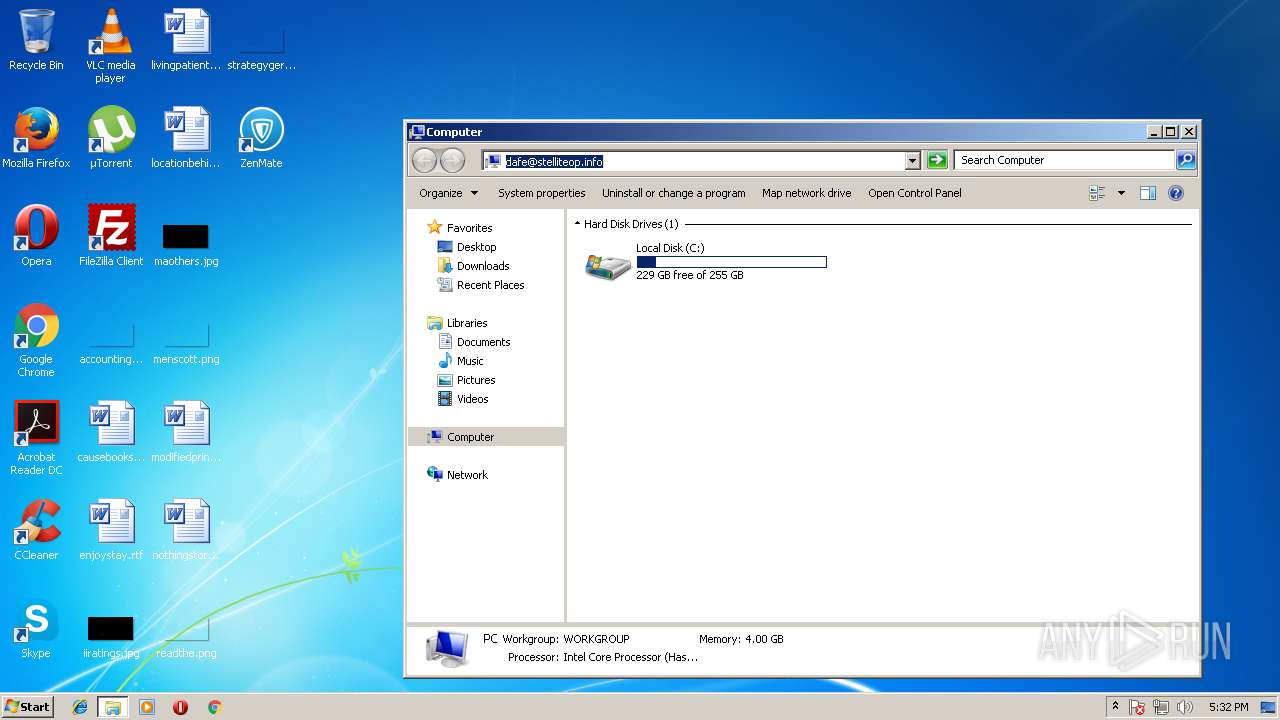
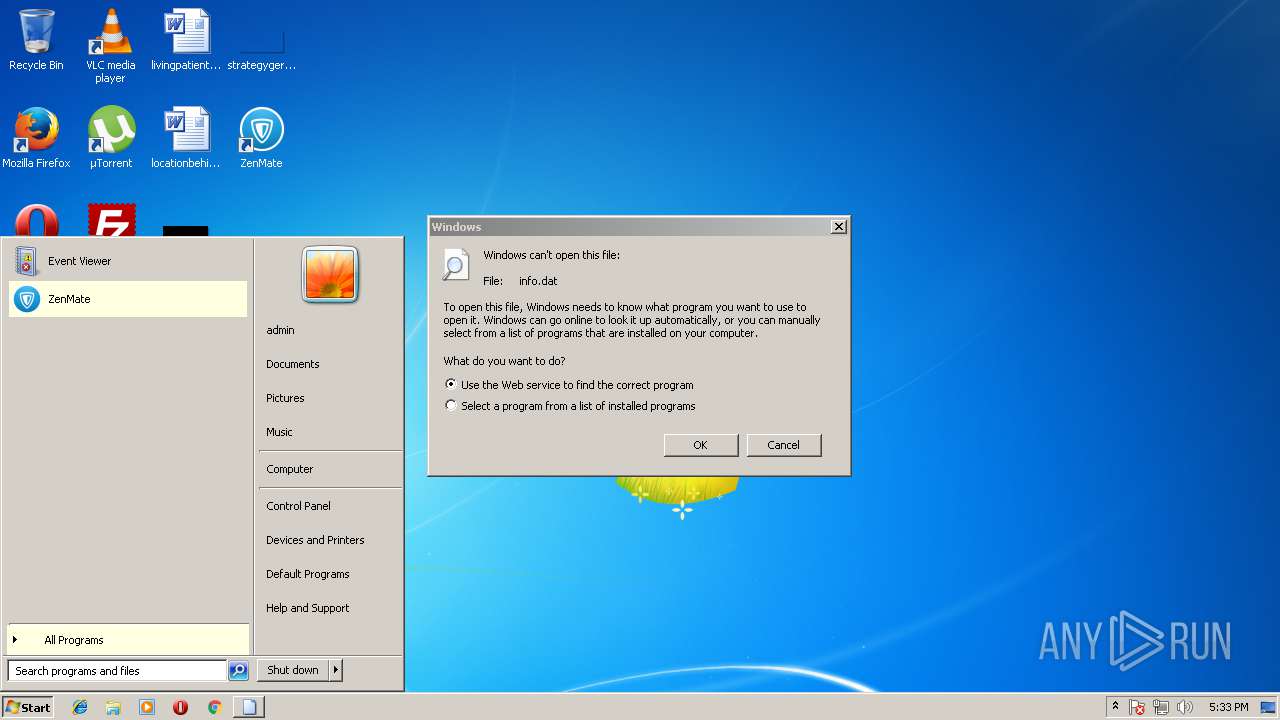
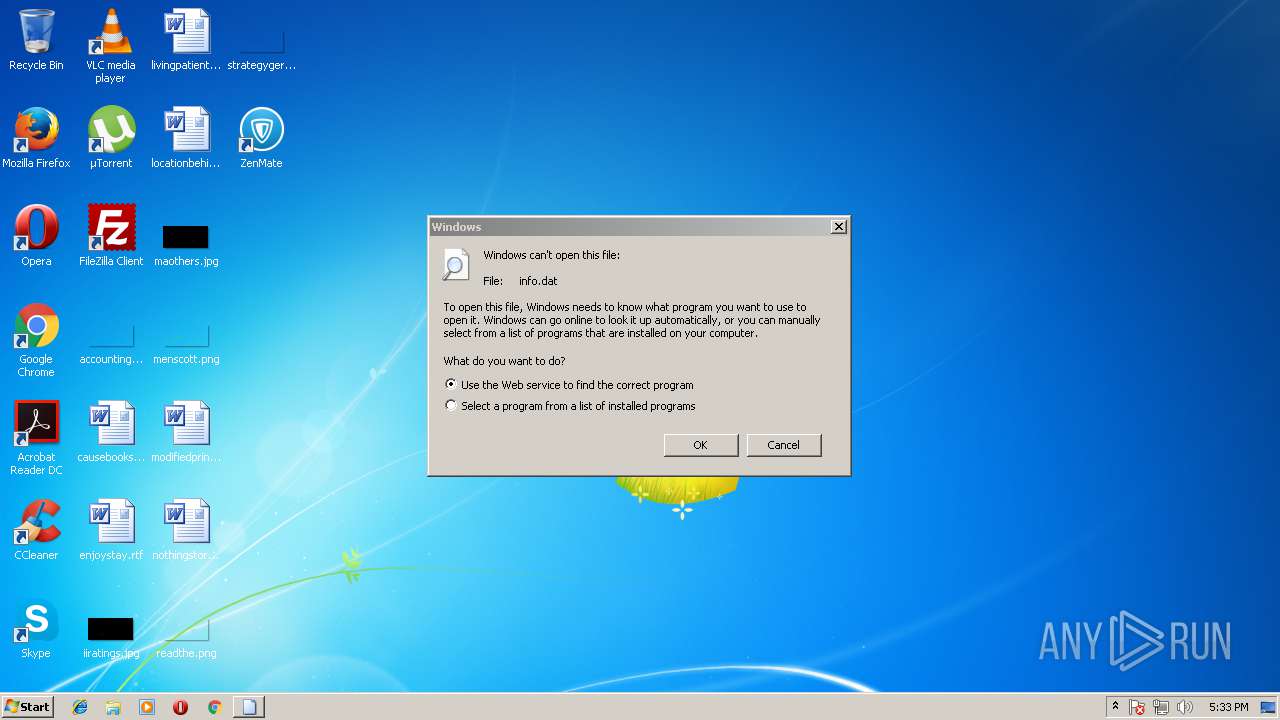
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DDB0AB2EFDFD596F2EAD0FF0CCA1EB6C |
| SHA1: | B11A80AF748E55425FDF9C46F57CE54E58B53F8E |
| SHA256: | 83D9F88576D089744903014E4C299EB84A94AABF1C641A7F7A5365002756E294 |
| SSDEEP: | 196608:1OKulZgfwMiujALcWW0PGZ14E/5iNgONwRo4A:UZIfCu0cgC53r |
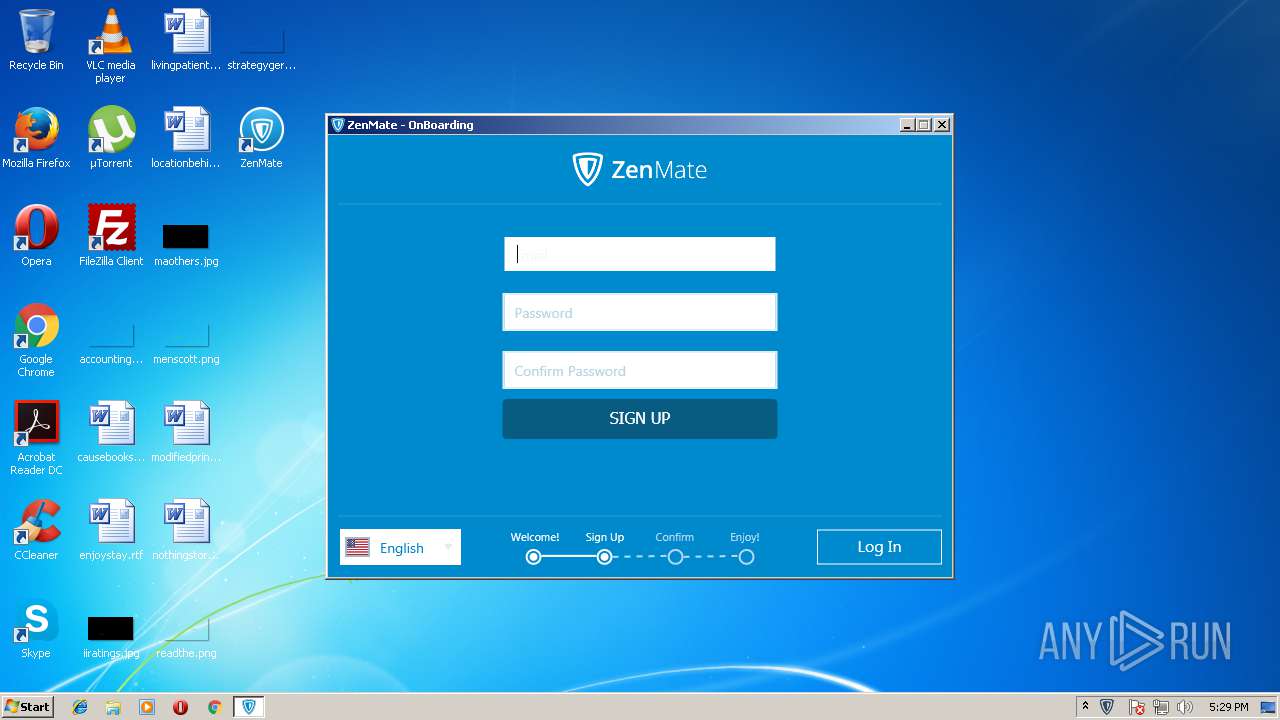
MALICIOUS
Application was dropped or rewritten from another process
- Update.exe (PID: 2748)
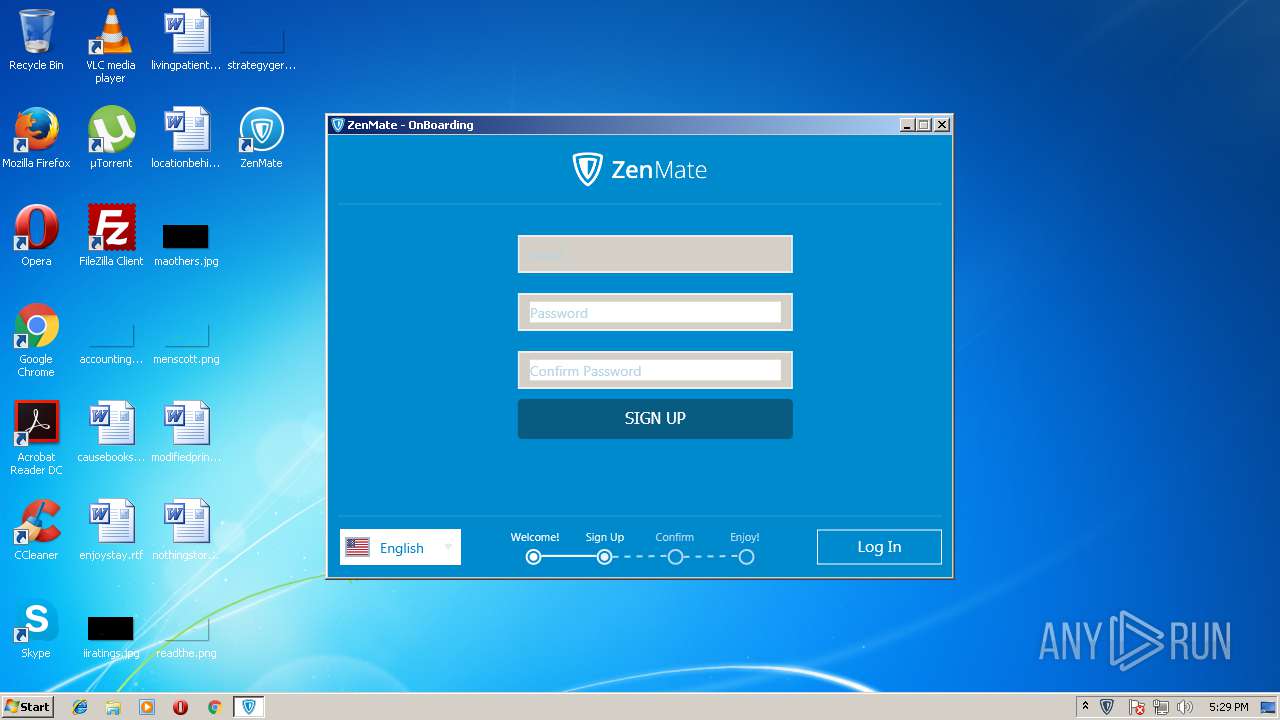
- ZenMate.exe (PID: 1400)
- ZenMate.exe (PID: 3100)
- ZenMate.exe (PID: 684)
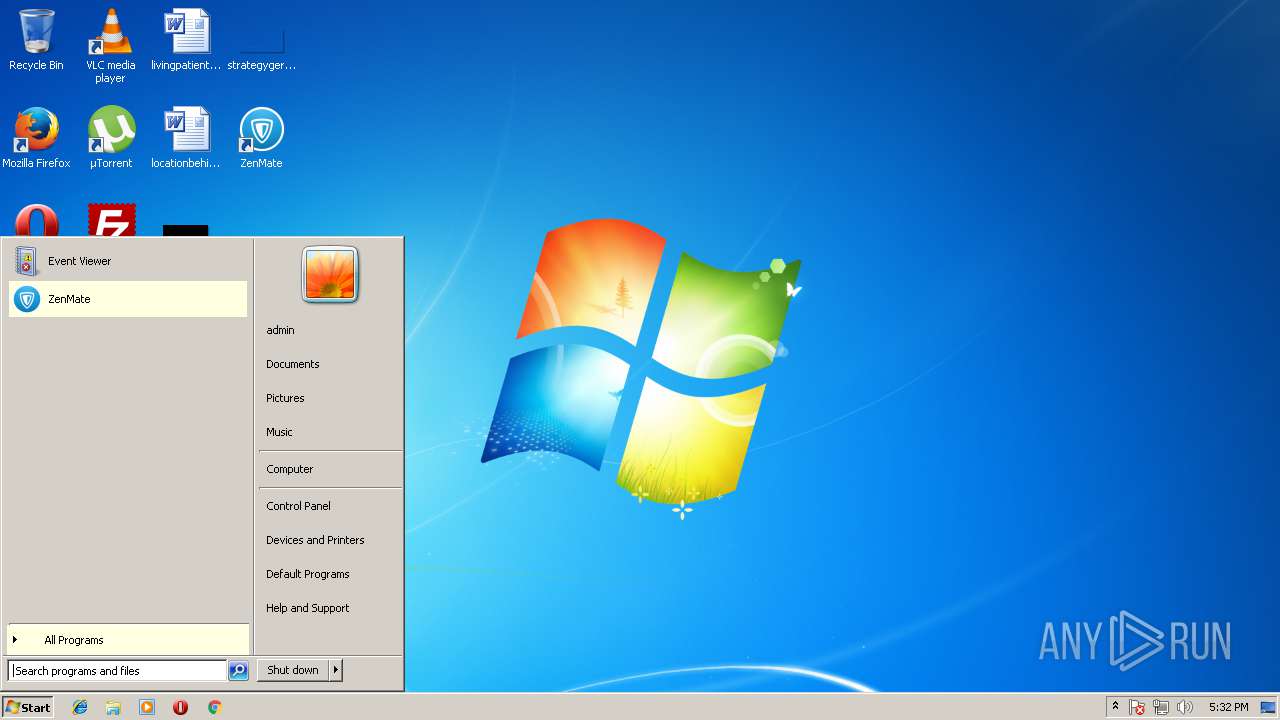
Writes to a start menu file
- ZenMate.exe (PID: 3100)
Loads dropped or rewritten executable
- ZenMate.exe (PID: 3100)
- ZenMate.exe (PID: 1400)
SUSPICIOUS
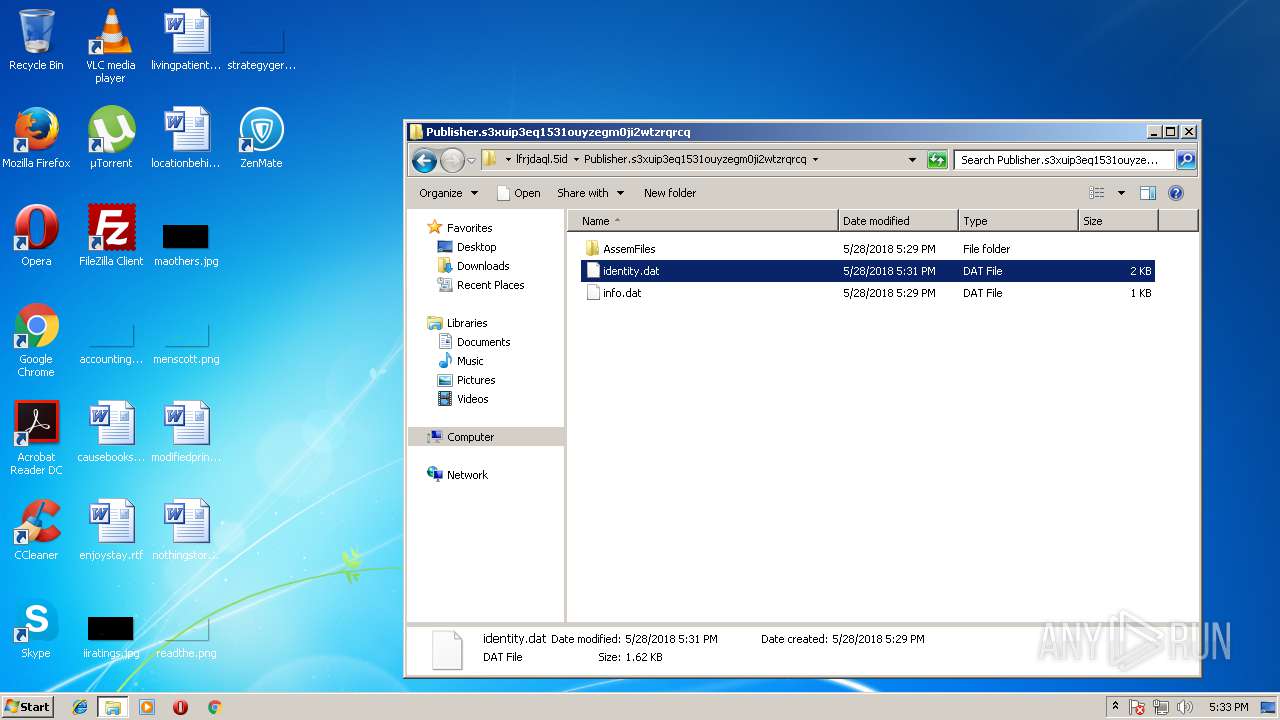
Executable content was dropped or overwritten
- setup.exe (PID: 3616)
- Update.exe (PID: 2748)
- ZenMate.exe (PID: 3100)
Creates files in the user directory
- ZenMate.exe (PID: 3100)
- ZenMate.exe (PID: 1400)
Searches for installed software
- ZenMate.exe (PID: 3100)
Creates a software uninstall entry
- Update.exe (PID: 2748)
- ZenMate.exe (PID: 3100)
Modifies the open verb of a shell class
- rundll32.exe (PID: 3316)
INFO
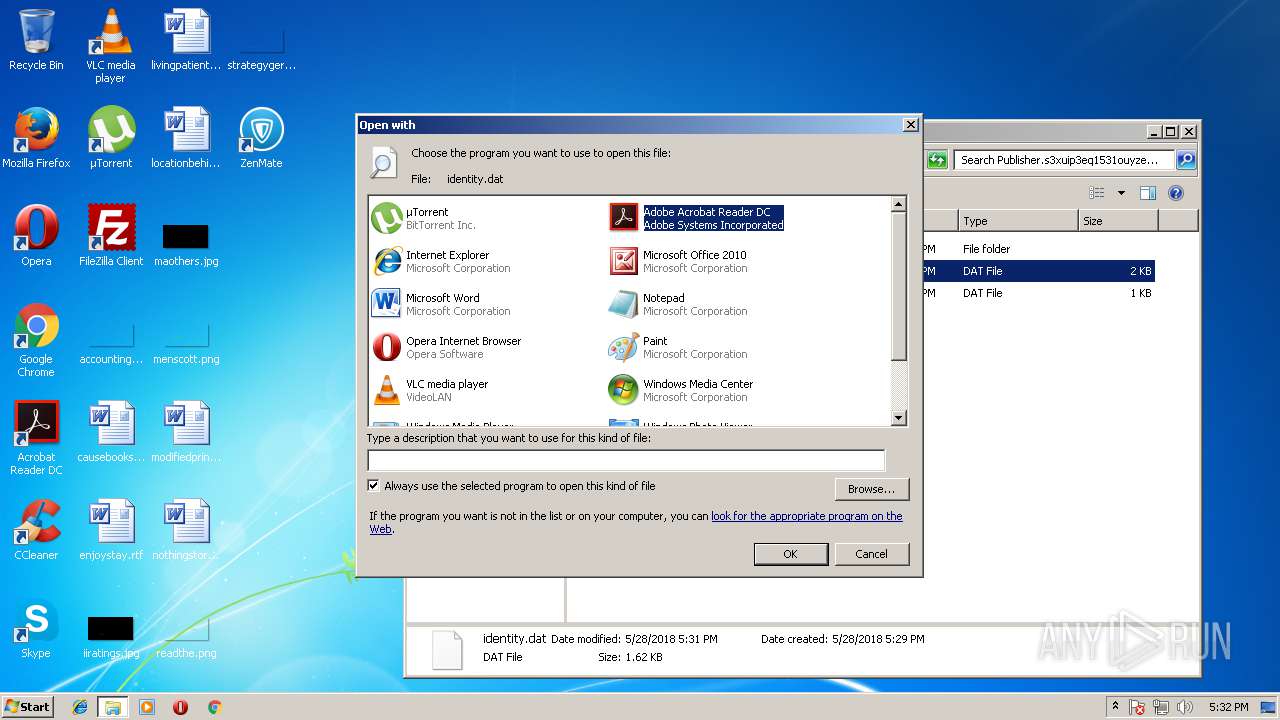
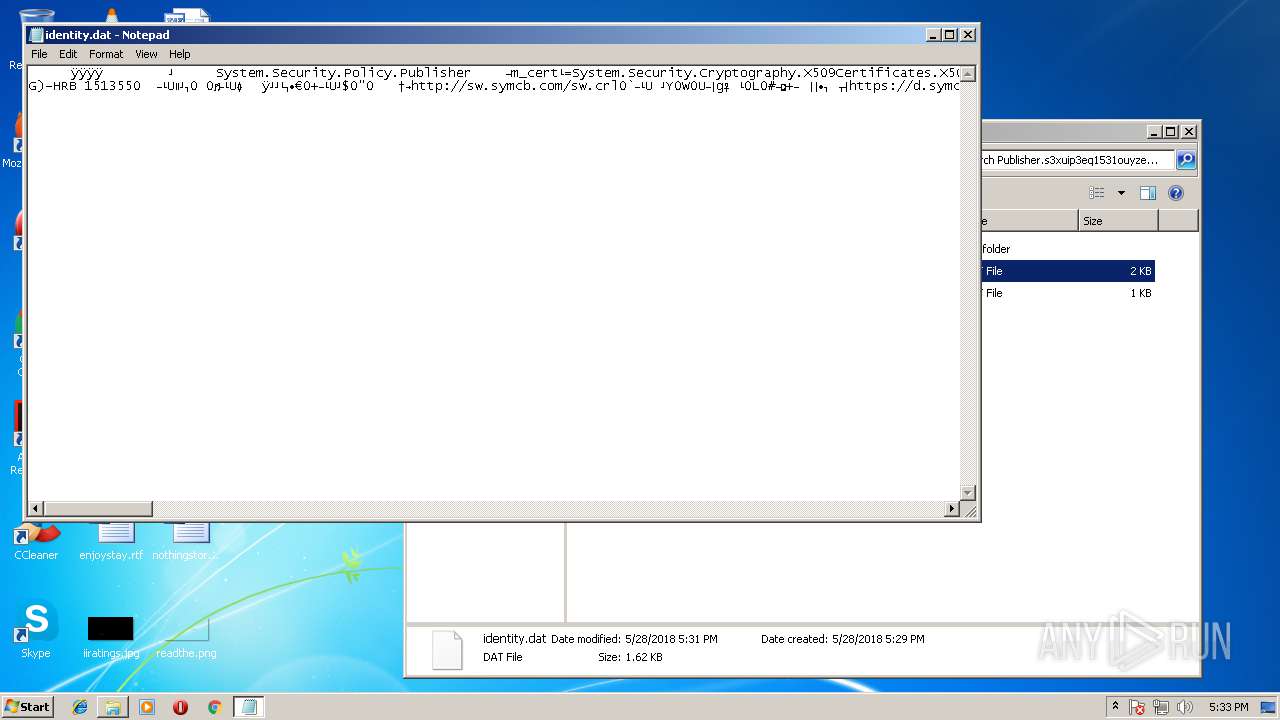
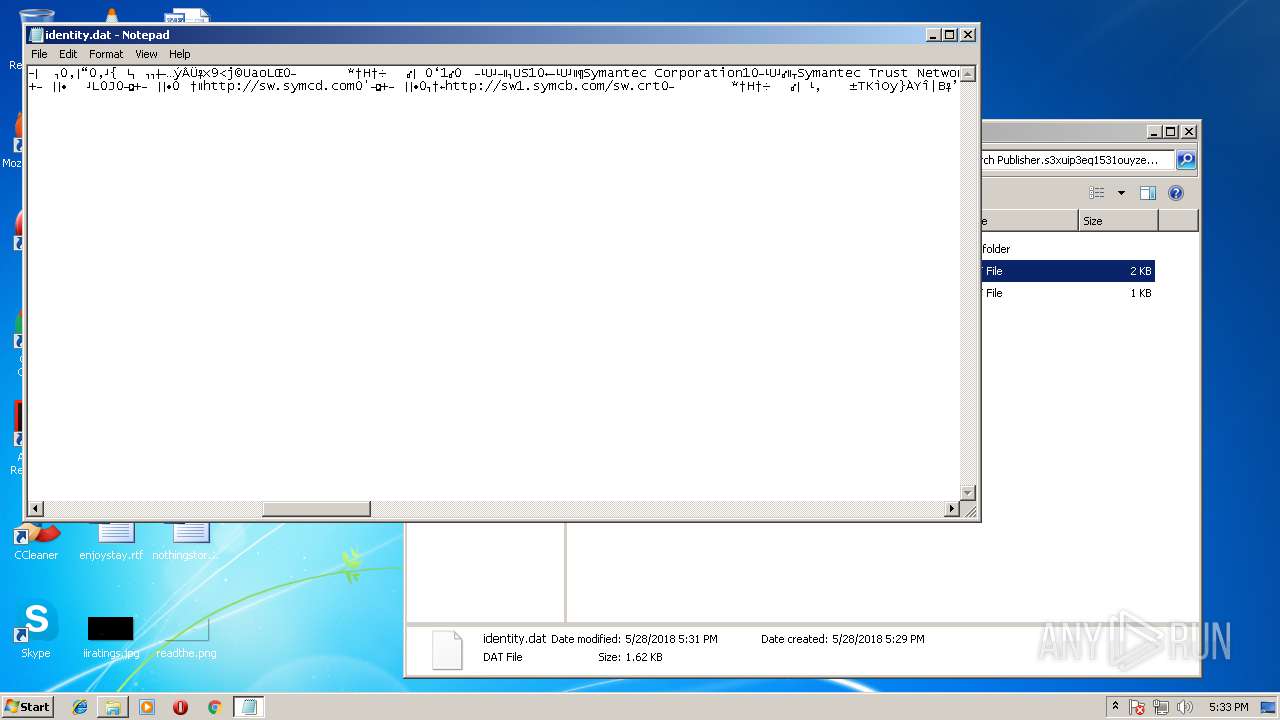
Dropped object may contain URL's
- Update.exe (PID: 2748)
- ZenMate.exe (PID: 1400)
- ZenMate.exe (PID: 684)
- ZenMate.exe (PID: 3100)
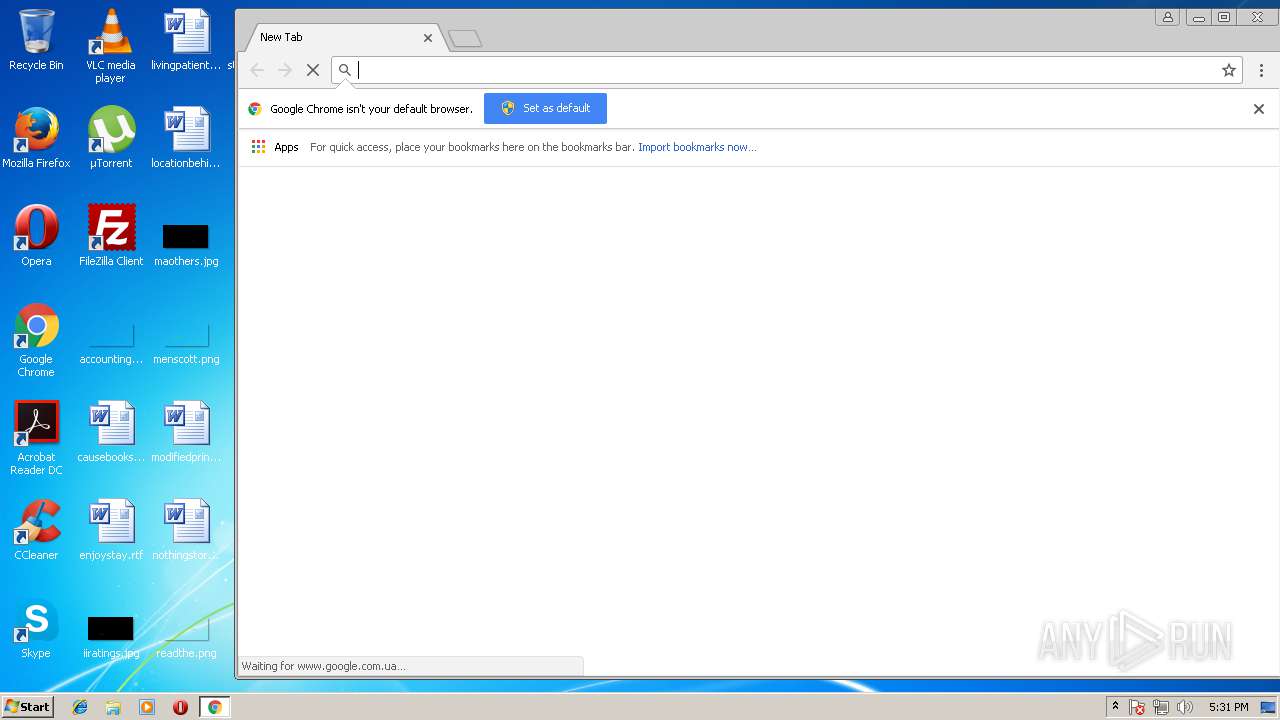
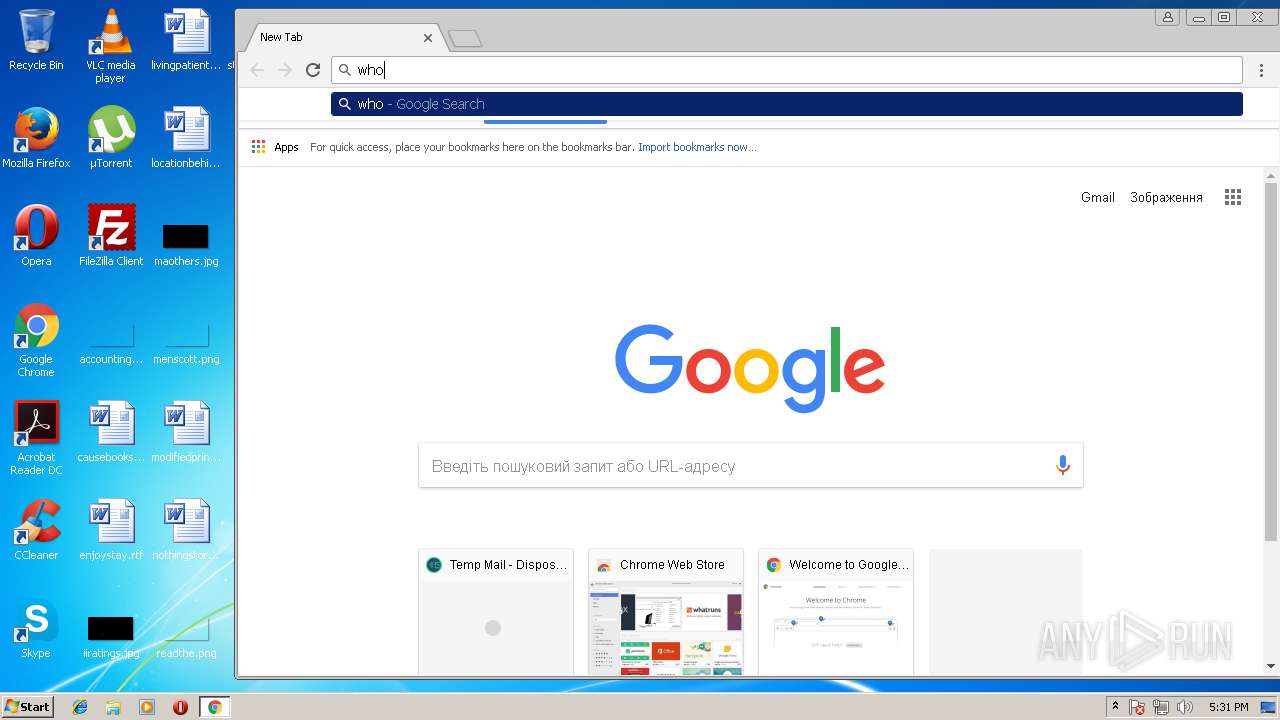
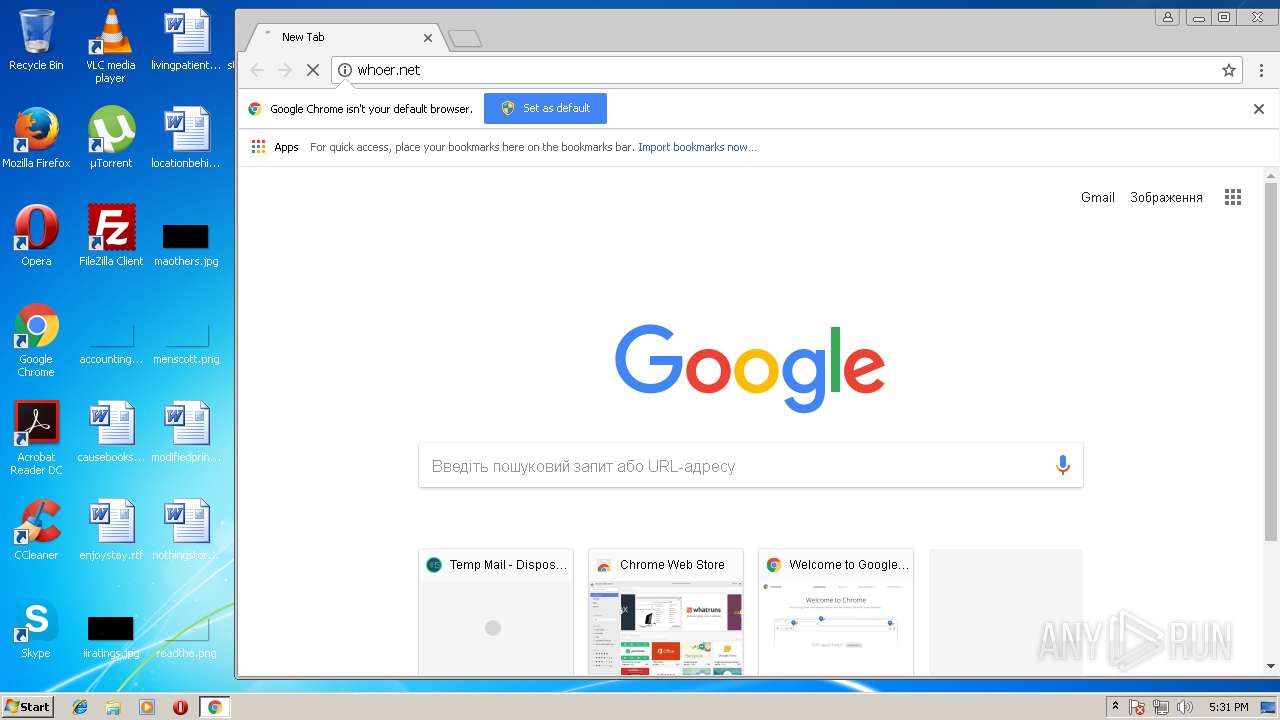
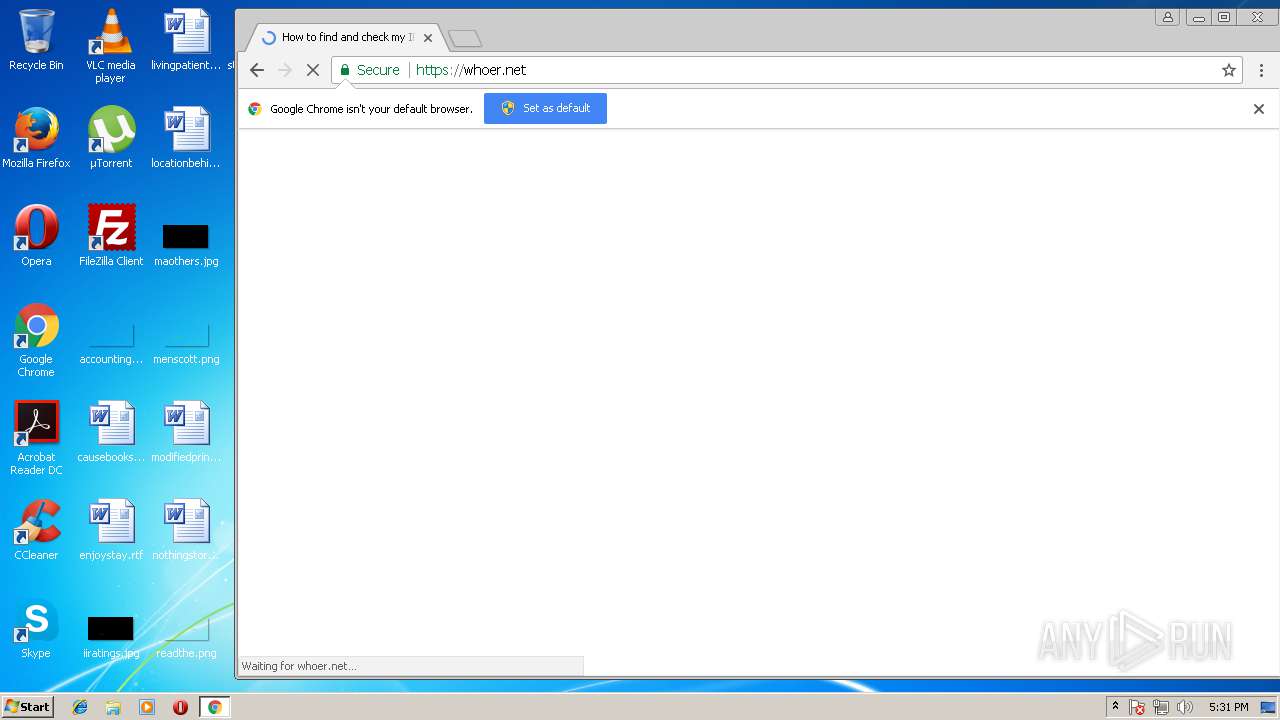
- chrome.exe (PID: 2348)
- chrome.exe (PID: 2220)
Application launched itself
- chrome.exe (PID: 2220)
- chrome.exe (PID: 2348)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2220)
- chrome.exe (PID: 2348)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 1920)
Reads settings of System Certificates
- chrome.exe (PID: 2220)
- chrome.exe (PID: 2348)
Changes settings of System certificates
- chrome.exe (PID: 2220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (54.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (34.8) |
| .exe | | | Win32 Executable (generic) (5.6) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:18 18:55:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 107008 |
| InitializedDataSize: | 8646144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.9.18 |
| ProductVersionNumber: | 3.4.9.18 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
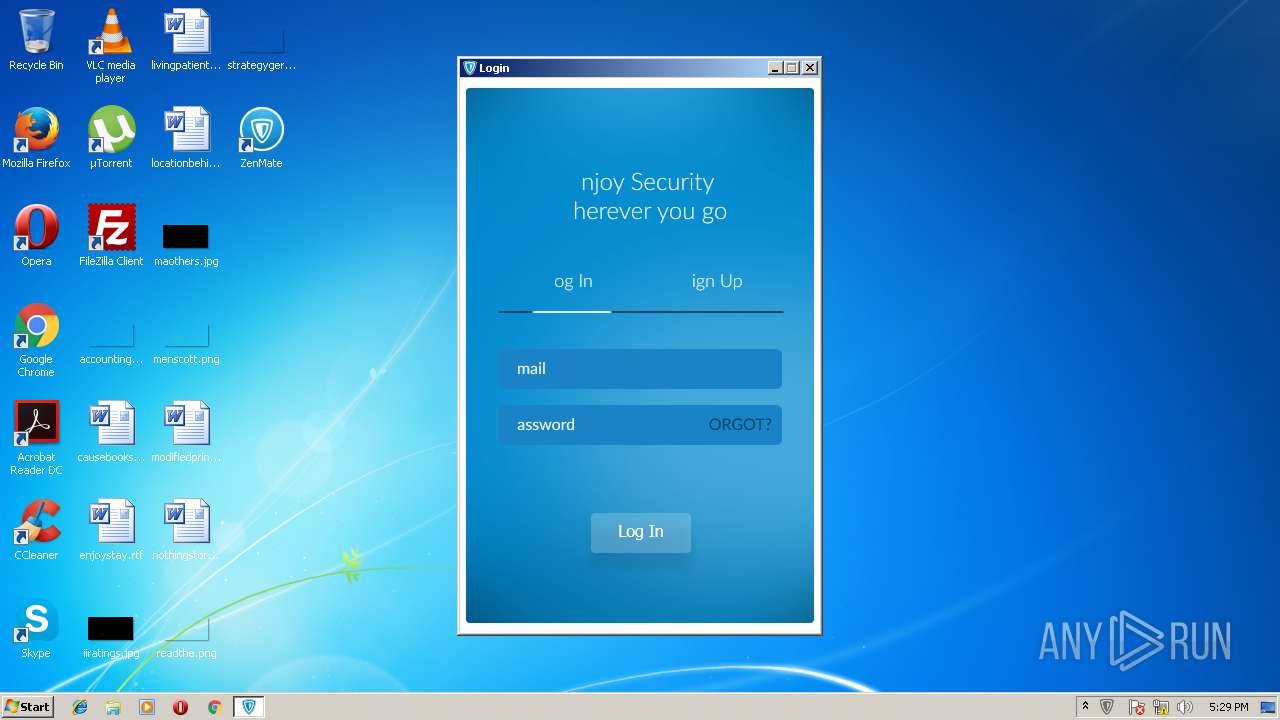
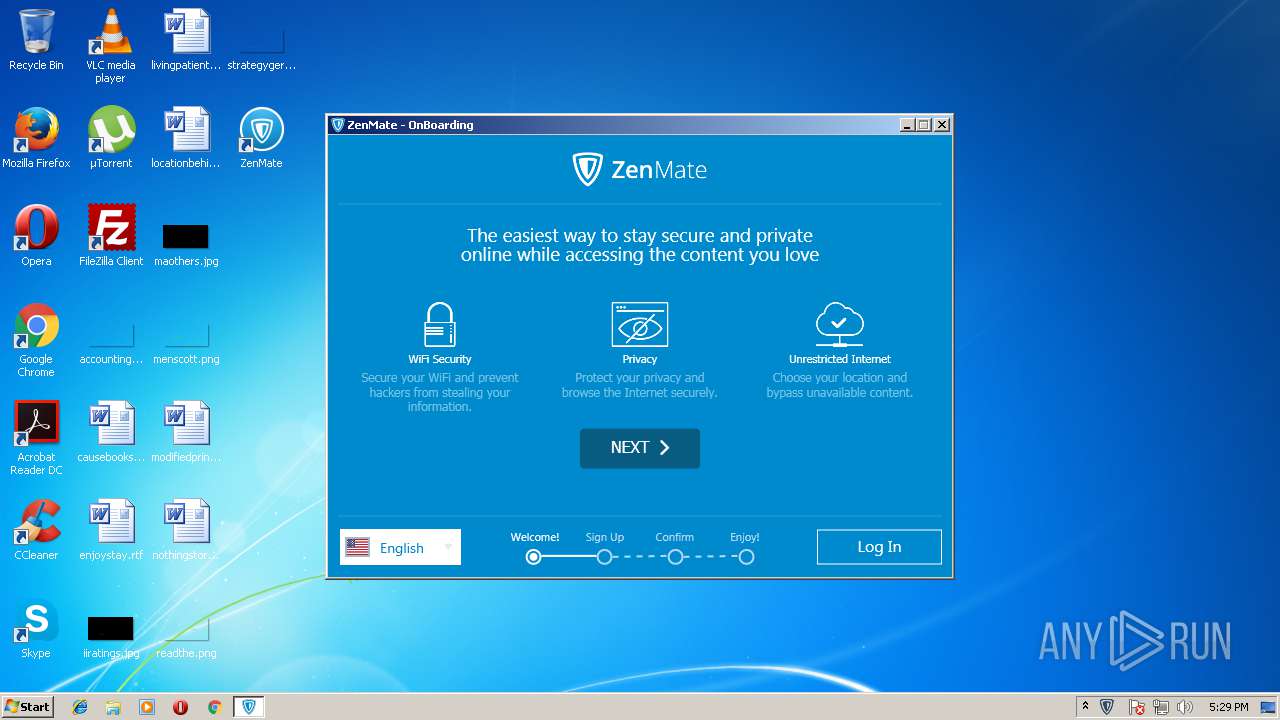
| FileDescription: | ZenMate is your Cyber Security solution |
| FileVersion: | 3.4.9.18 |
| InternalName: | Setup.exe |
| LegalCopyright: | Copyright 2016 |
| OriginalFileName: | Setup.exe |
| ProductName: | ZenMate is your Cyber Security solution |
| ProductVersion: | 3.4.9.18 |
| SquirrelAwareVersion: | 1 |
| CompanyName: | ZenGuard GmbH |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Apr-2016 16:55:56 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | ZenMate is your Cyber Security solution |
| FileVersion: | 3.4.9.18 |
| InternalName: | Setup.exe |
| LegalCopyright: | Copyright 2016 |
| OriginalFilename: | Setup.exe |
| ProductName: | ZenMate is your Cyber Security solution |
| ProductVersion: | 3.4.9.18 |
| SquirrelAwareVersion: | 1 |
| CompanyName: | ZenGuard GmbH |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Apr-2016 16:55:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001A18A | 0x0001A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64535 |
.rdata | 0x0001C000 | 0x0000A4BA | 0x0000A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.64076 |
.data | 0x00027000 | 0x00003648 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9676 |
.rsrc | 0x0002B000 | 0x00831754 | 0x00831800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.95478 |
.reloc | 0x0085D000 | 0x000019F8 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58822 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31968 | 999 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.24943 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.01025 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.66588 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.25535 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.04285 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.00563 | 142 | Latin 1 / Western European | English - United States | RT_STRING |
107 | 2.37447 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
108 | 2.49212 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
131 | 7.9982 | 8218261 | Latin 1 / Western European | English - United States | DATA |
Imports
ADVAPI32.dll |
COMCTL32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
urlmon.dll |
Total processes
69
Monitored processes
33
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1592,4343056263126564767,12908003600763806034,131072 --service-pipe-token=FCE4147890BB40F9584212502A6854C6 --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=FCE4147890BB40F9584212502A6854C6 --renderer-client-id=2 --mojo-platform-channel-handle=1760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 684 | "C:\Users\admin\AppData\Local\ZenMate\app-3.5.0.20\ZenMate.exe" --squirrel-updated 3.5.0.20 | C:\Users\admin\AppData\Local\ZenMate\app-3.5.0.20\ZenMate.exe | — | ZenMate.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ZenMate Exit code: 0 Version: 3.5.0.20 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=61.0.3163.100 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x66f37d7c,0x66f37da4,0x66f37d8c | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1400 | "C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\ZenMate.exe" --squirrel-install 3.4.9.18 | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\ZenMate.exe | — | Update.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ZenMate Exit code: 0 Version: 3.4.9.18 Modules
| |||||||||||||||
| 1408 | "c:\users\admin\appdata\local\google\chrome\user data\swreporter\23.129.0\software_reporter_tool.exe" --crash-handler "--database=c:\users\admin\appdata\local\Google\Software Reporter Tool" --url=https://clients2.google.com/cr/report --annotation=plat=Win32 --annotation=prod=ChromeFoil --annotation=ver=23.129.0 --initial-client-data=0xe4,0xec,0xf0,0xe8,0xf4,0x13ac42c,0x13ac43c,0x13ac44c | c:\users\admin\appdata\local\google\chrome\user data\swreporter\23.129.0\software_reporter_tool.exe | — | software_reporter_tool.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 0 Version: 23.129.0 Modules
| |||||||||||||||
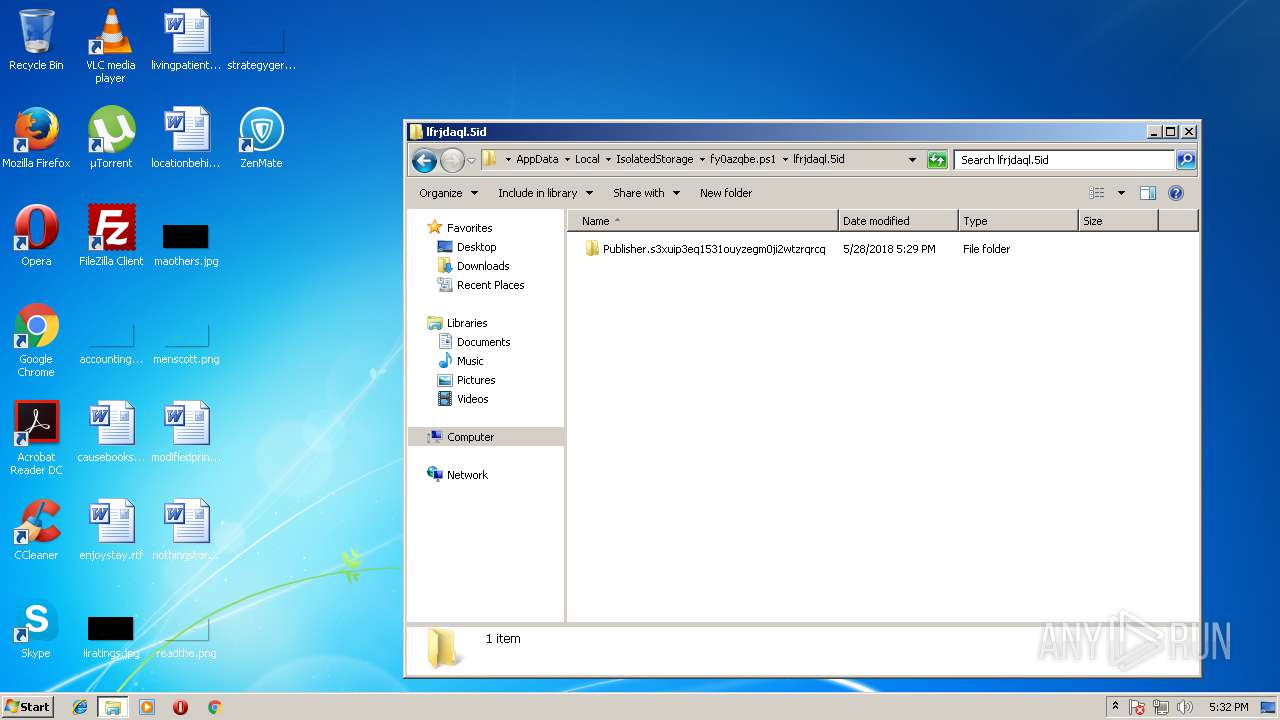
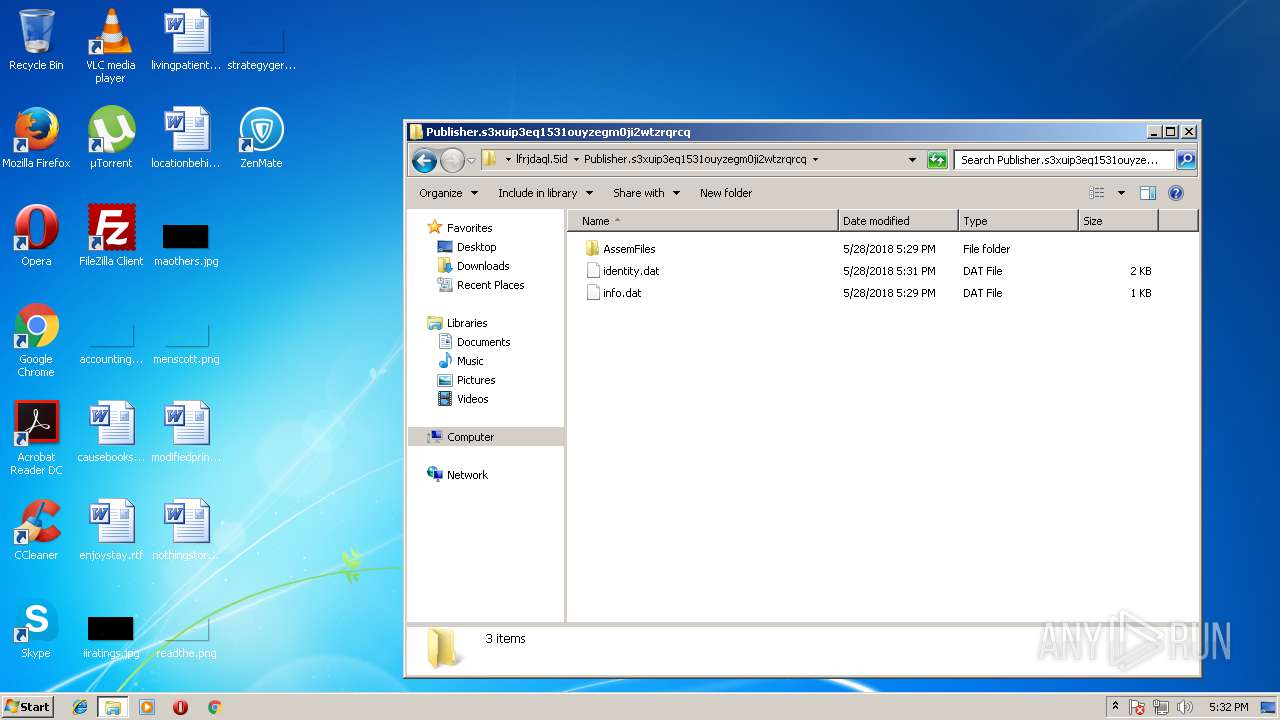
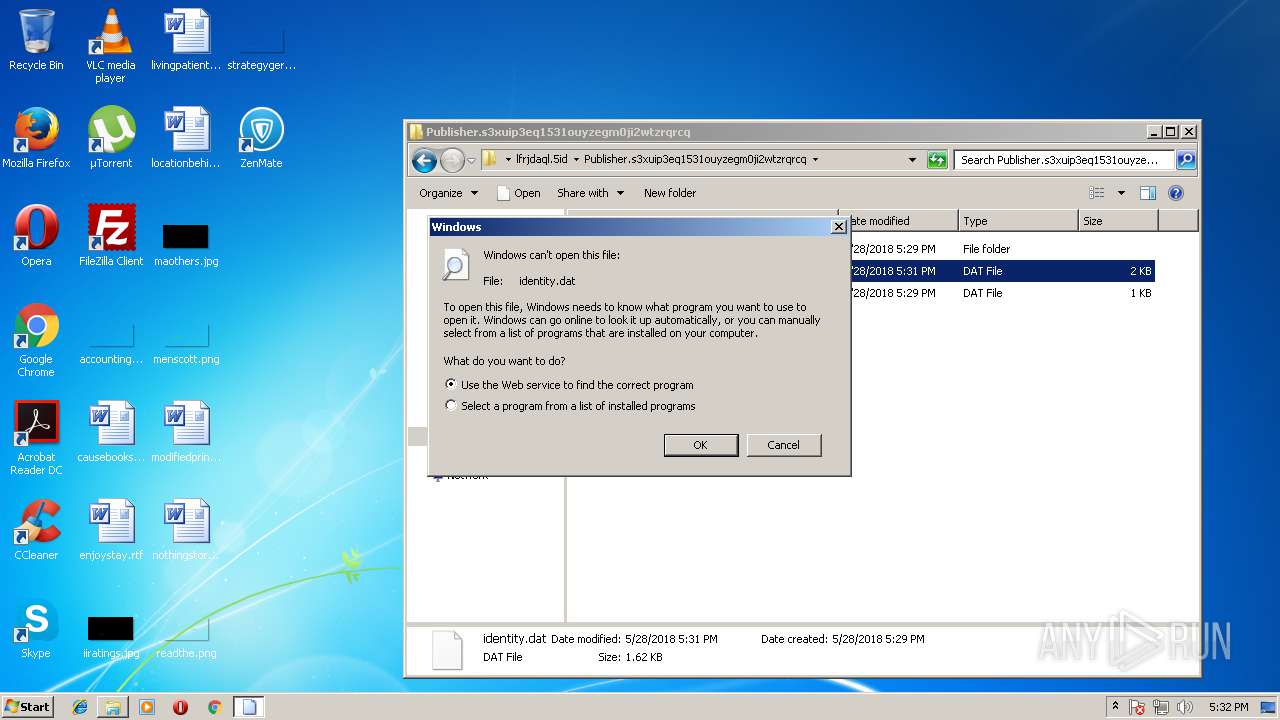
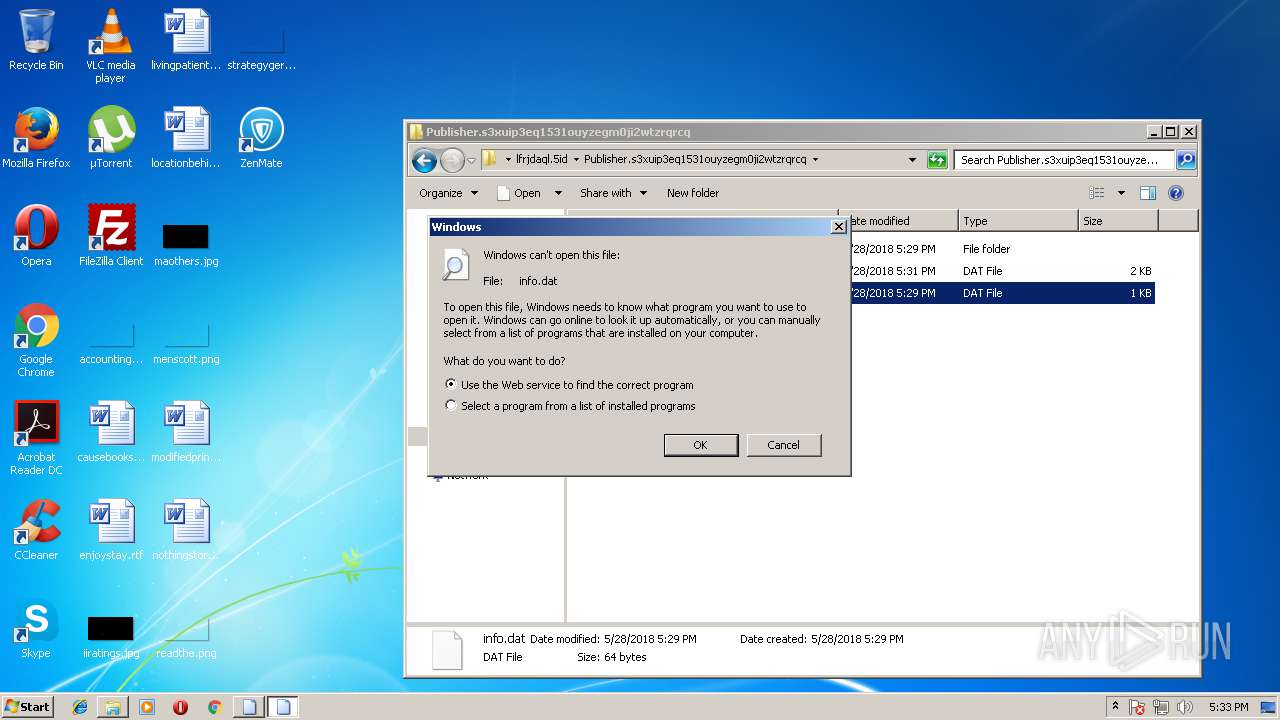
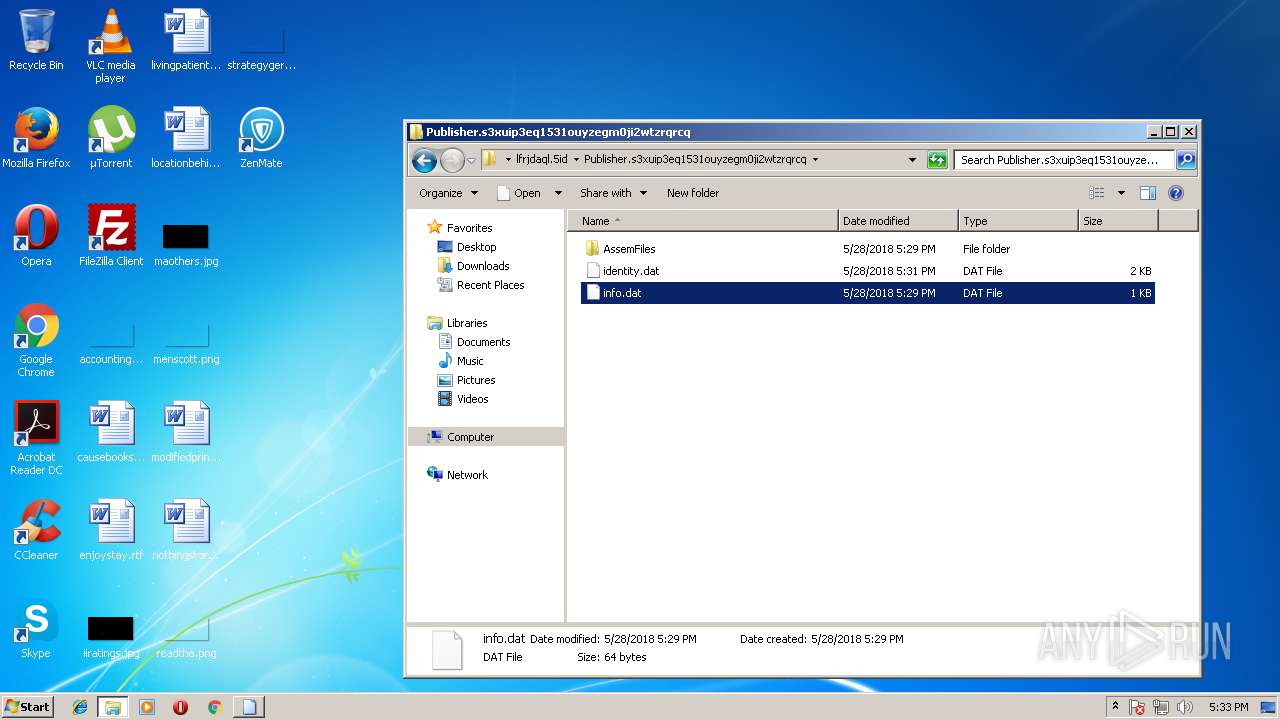
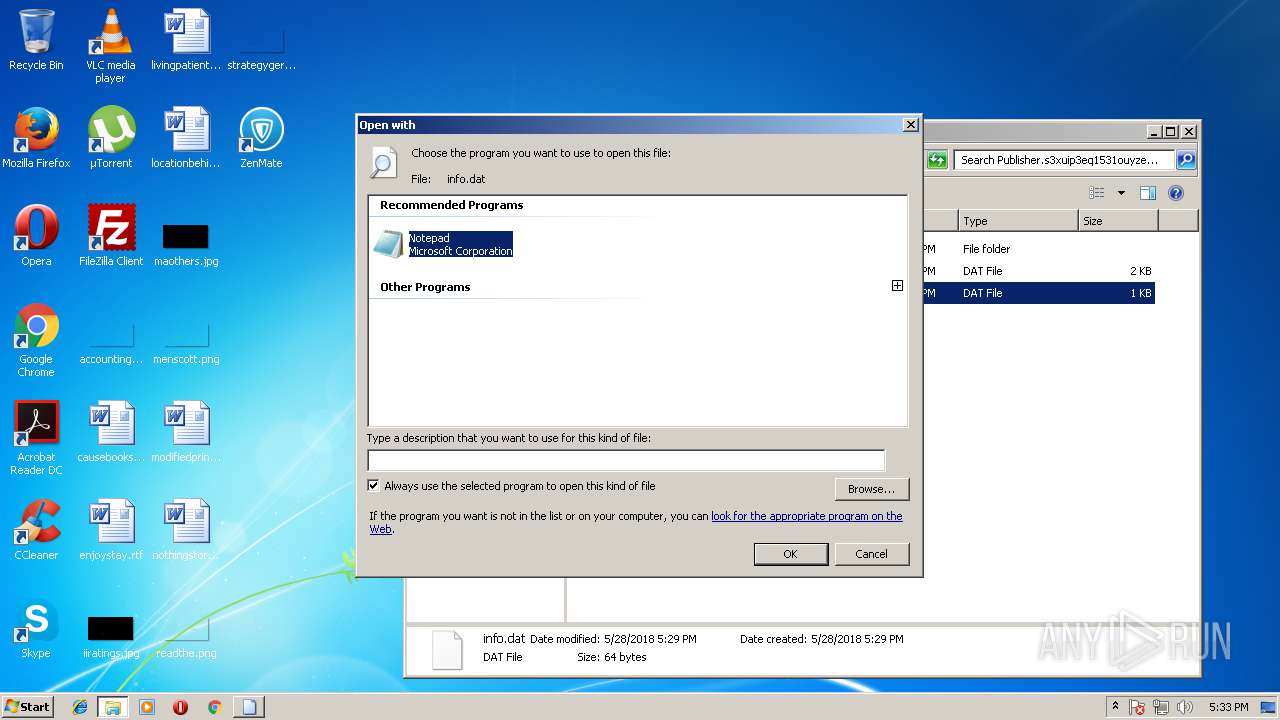
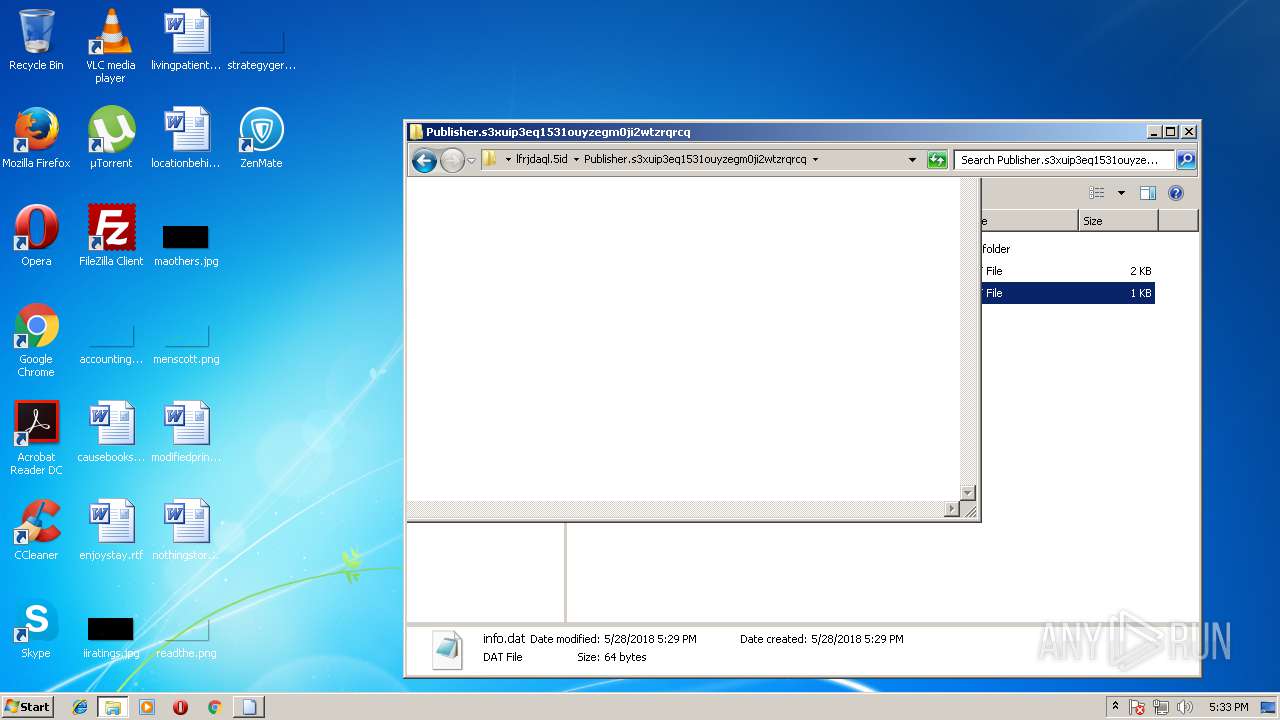
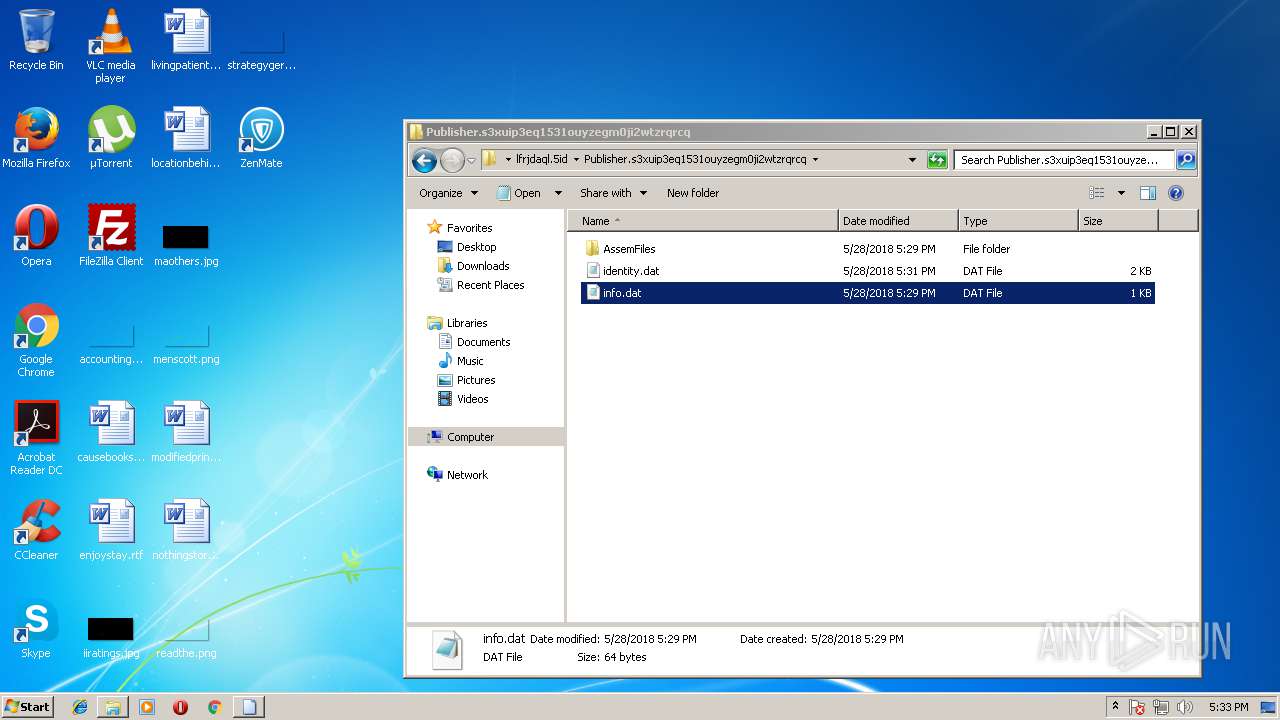
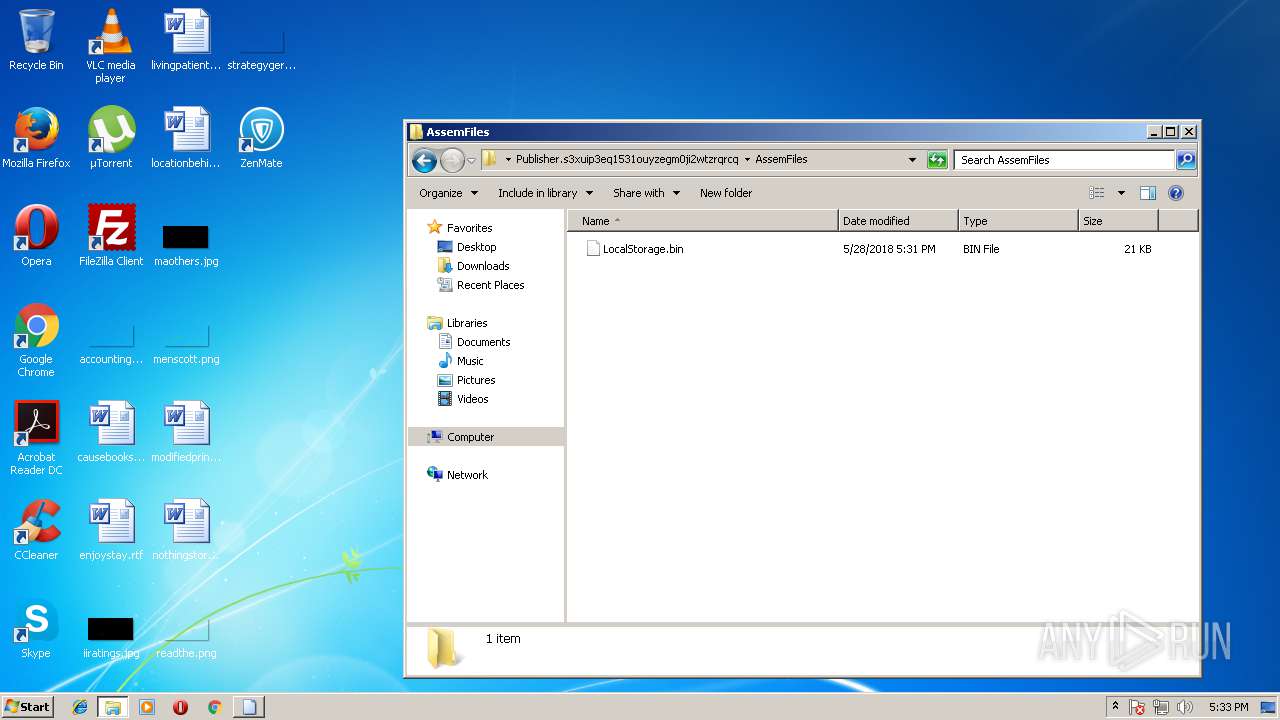
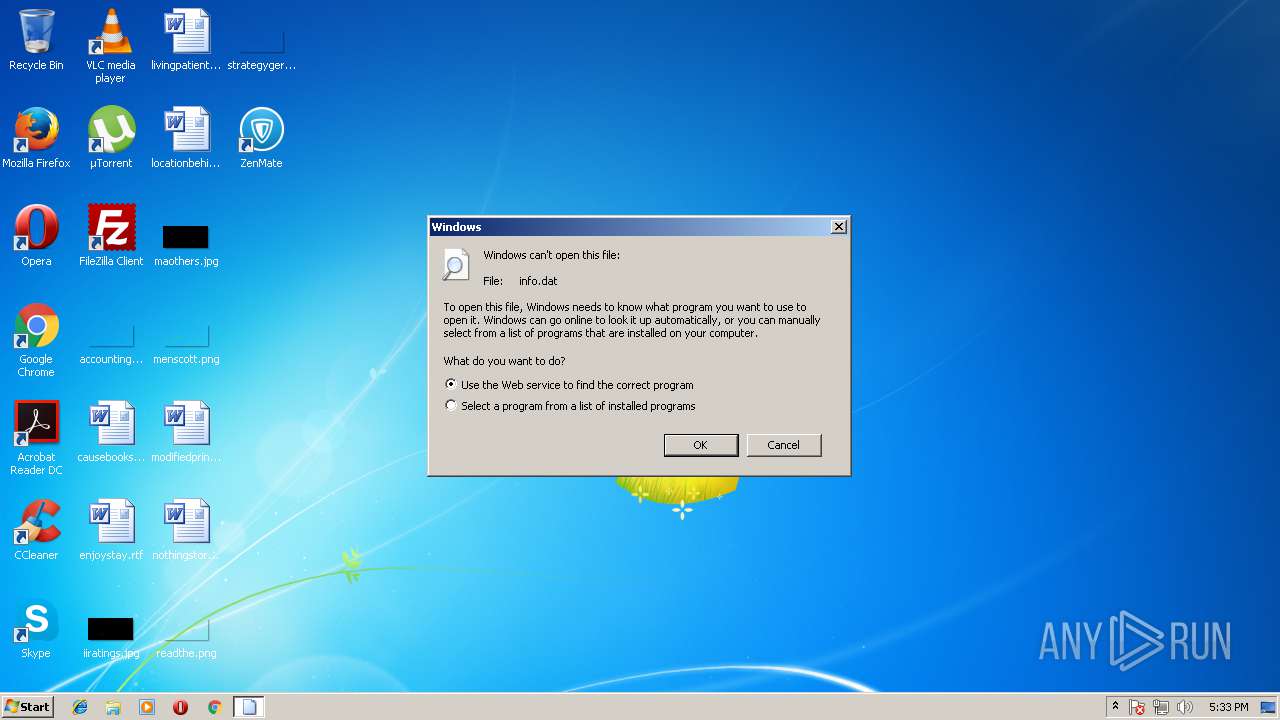
| 1504 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\IsolatedStorage\fy0azqbe.ps1\lfrjdaql.5id\Publisher.s3xuip3eq1531ouyzegm0ji2wtzrqrcq\info.dat | C:\Windows\system32\NOTEPAD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1592,4343056263126564767,12908003600763806034,131072 --service-pipe-token=08B03BA501130B6E23EE0657D6015162 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=08B03BA501130B6E23EE0657D6015162 --renderer-client-id=8 --mojo-platform-channel-handle=3460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1652,16891077783831694956,2567167130369840911,131072 --service-pipe-token=0105CA7524D2002557143A4F26F9A91A --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=0105CA7524D2002557143A4F26F9A91A --renderer-client-id=6 --mojo-platform-channel-handle=3596 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\AppData\Local\Google\Chrome\User Data\SwReporter\23.129.0\software_reporter_tool.exe" --session-id=oZ/kZ76uiWo3W5qFWK56VFspKVlXZdZHkde2LgEN | C:\Users\admin\AppData\Local\Google\Chrome\User Data\SwReporter\23.129.0\software_reporter_tool.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 2 Version: 23.129.0 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1592,4343056263126564767,12908003600763806034,131072 --lang=en-US --service-request-channel-token=80263ED8C5F1AB1F727106AFA969FC38 --mojo-platform-channel-handle=2108 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
Total events
3 300
Read events
2 581
Write events
703
Delete events
16
Modification events
| (PID) Process: | (1400) ZenMate.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1400) ZenMate.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1400) ZenMate.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2748) Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2748) Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2748) Update.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2748) Update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Update_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2748) Update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Update_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2748) Update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Update_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2748) Update.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Update_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
162
Suspicious files
186
Text files
216
Unknown types
69
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2748 | Update.exe | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\lib\net45\App.config | — | |
MD5:— | SHA256:— | |||
| 2748 | Update.exe | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\lib\net45\DeltaCompressionDotNet.dll | — | |
MD5:— | SHA256:— | |||
| 2748 | Update.exe | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\lib\net45\DeltaCompressionDotNet.MsDelta.dll | — | |
MD5:— | SHA256:— | |||
| 2748 | Update.exe | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\lib\net45\DeltaCompressionDotNet.PatchApi.dll | — | |
MD5:— | SHA256:— | |||
| 2748 | Update.exe | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\lib\net45\DotRas.dll | — | |
MD5:— | SHA256:— | |||
| 2748 | Update.exe | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\lib\net45\ICSharpCode.SharpZipLib.dll | — | |
MD5:— | SHA256:— | |||
| 2748 | Update.exe | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\lib\net45\Interop.NETWORKLIST.dll | — | |
MD5:— | SHA256:— | |||
| 2748 | Update.exe | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\lib\net45\Mono.Cecil.dll | — | |
MD5:— | SHA256:— | |||
| 2748 | Update.exe | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\lib\net45\Mono.Cecil.Mdb.dll | — | |
MD5:— | SHA256:— | |||
| 2748 | Update.exe | C:\Users\admin\AppData\Local\ZenMate\app-3.4.9.18\lib\net45\Mono.Cecil.Pdb.dll | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
185
DNS requests
169
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
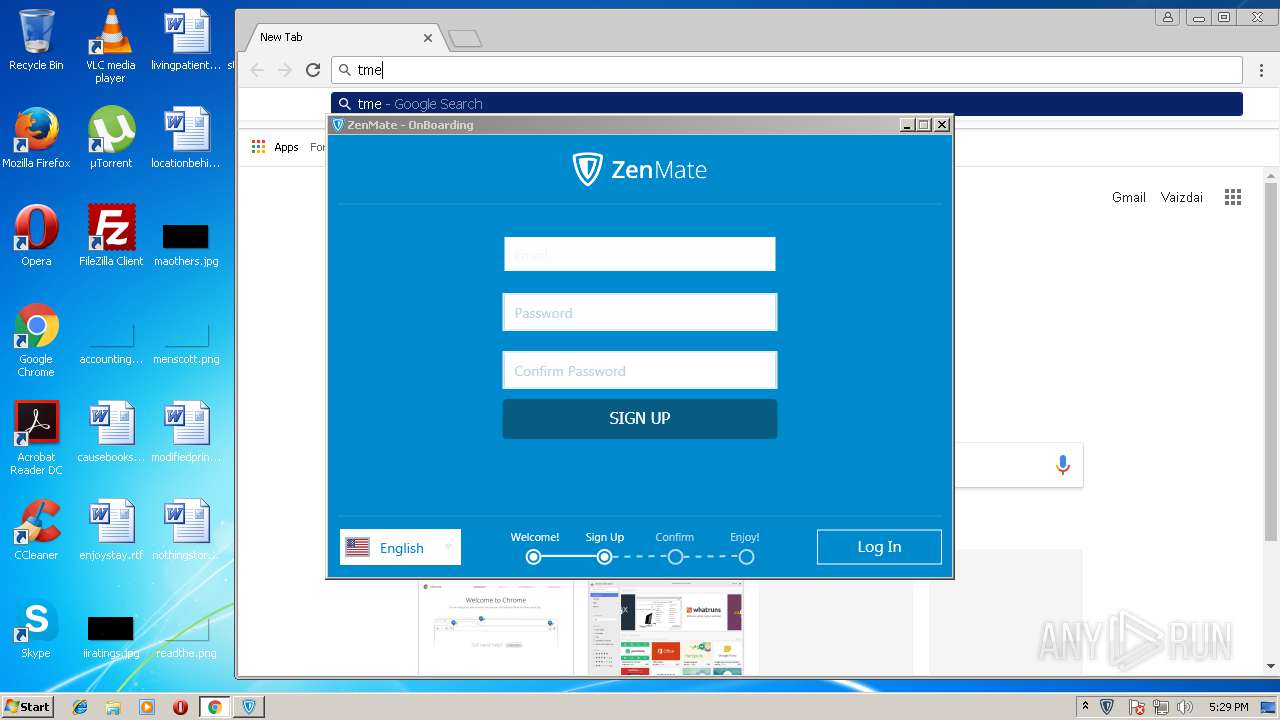
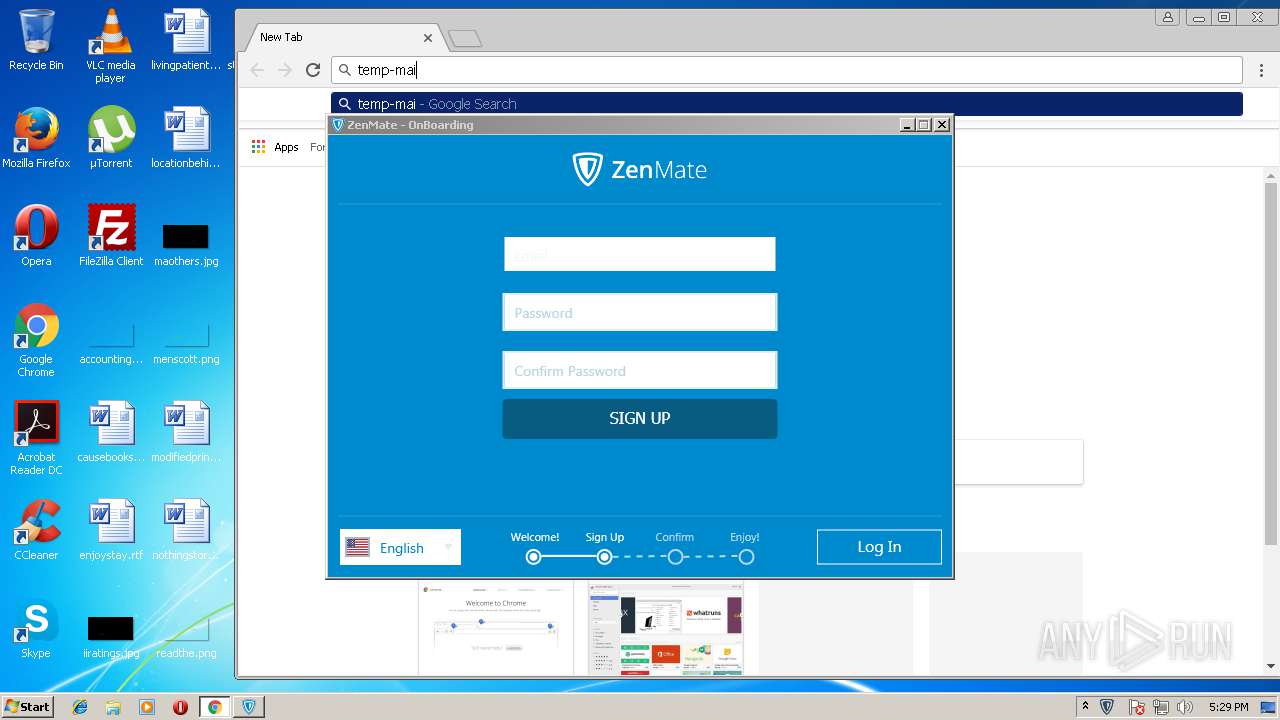
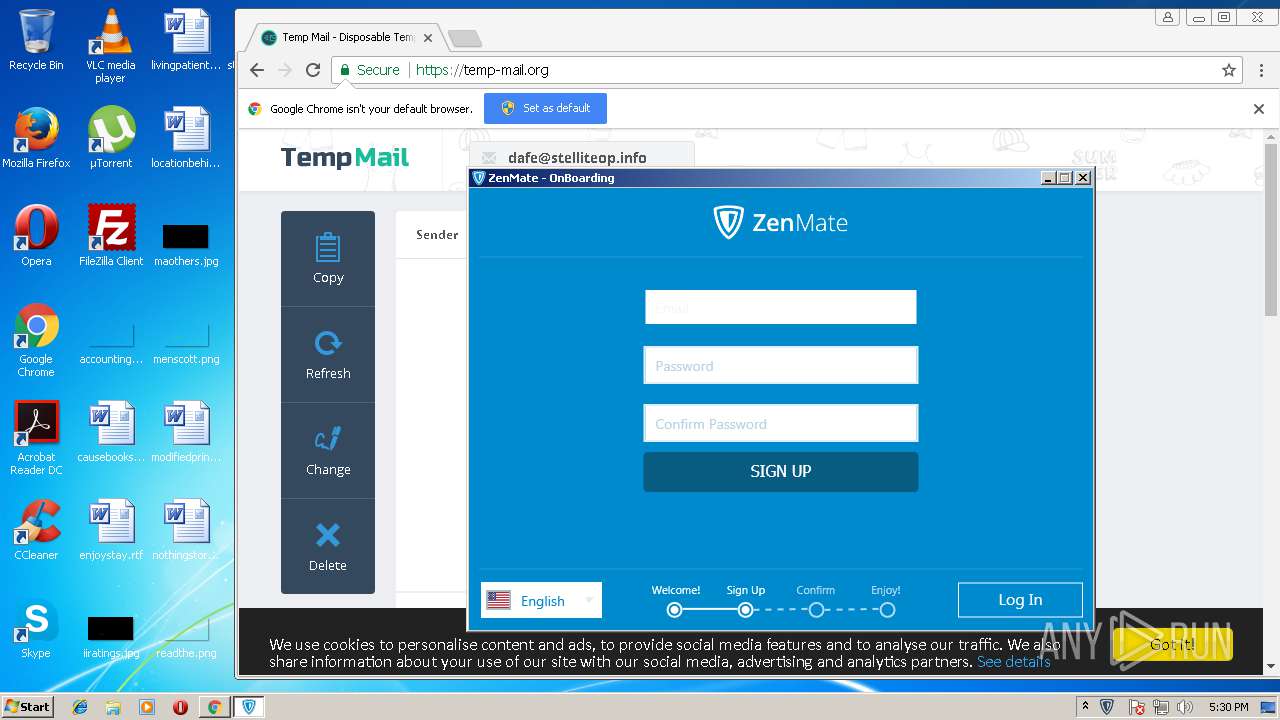
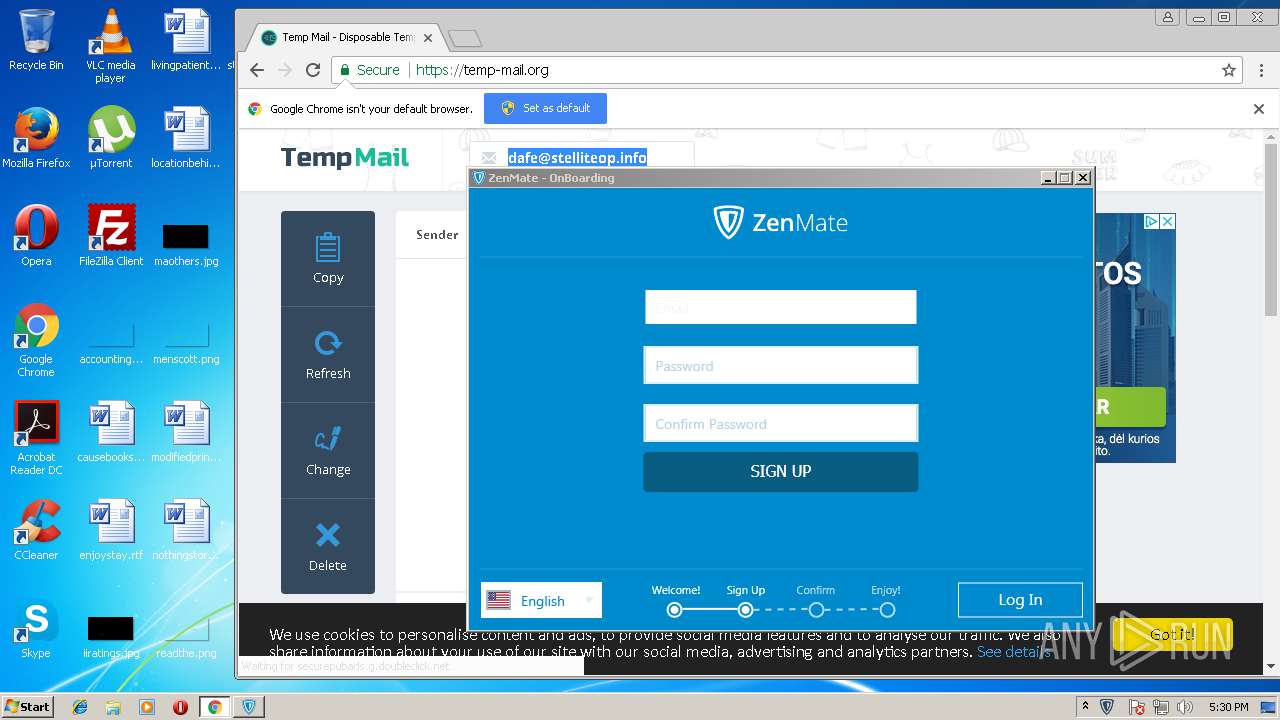
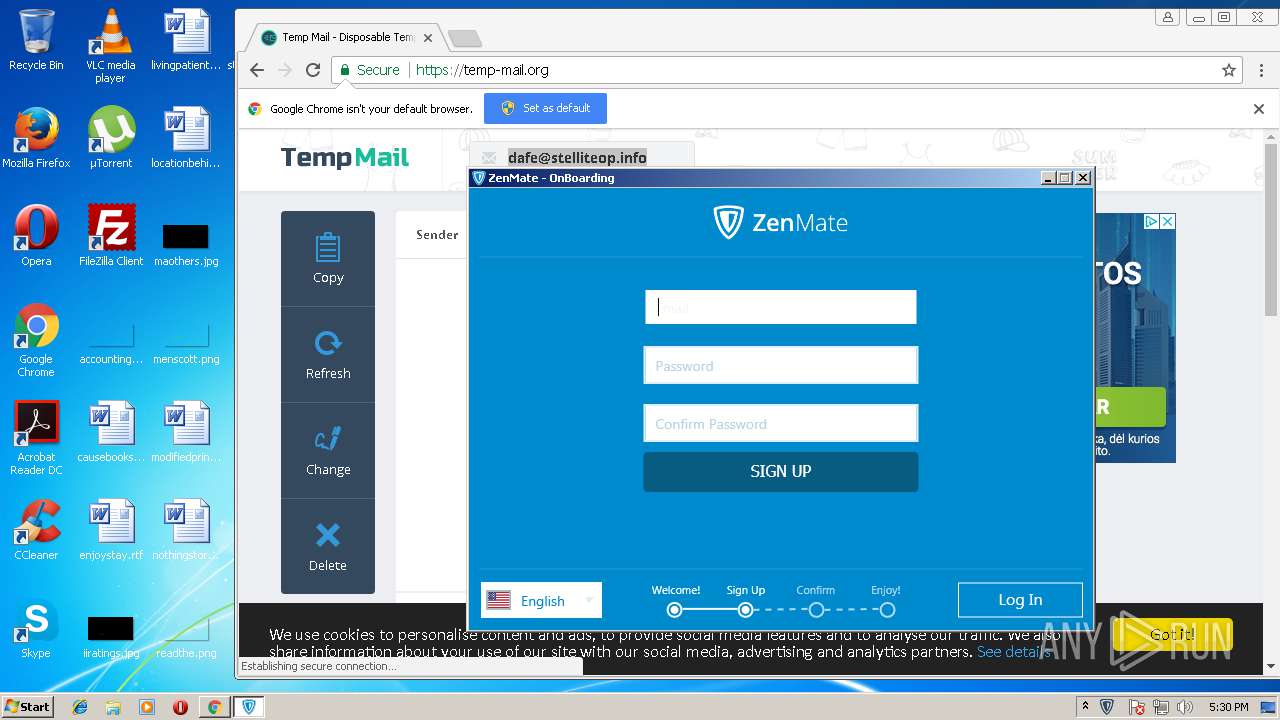
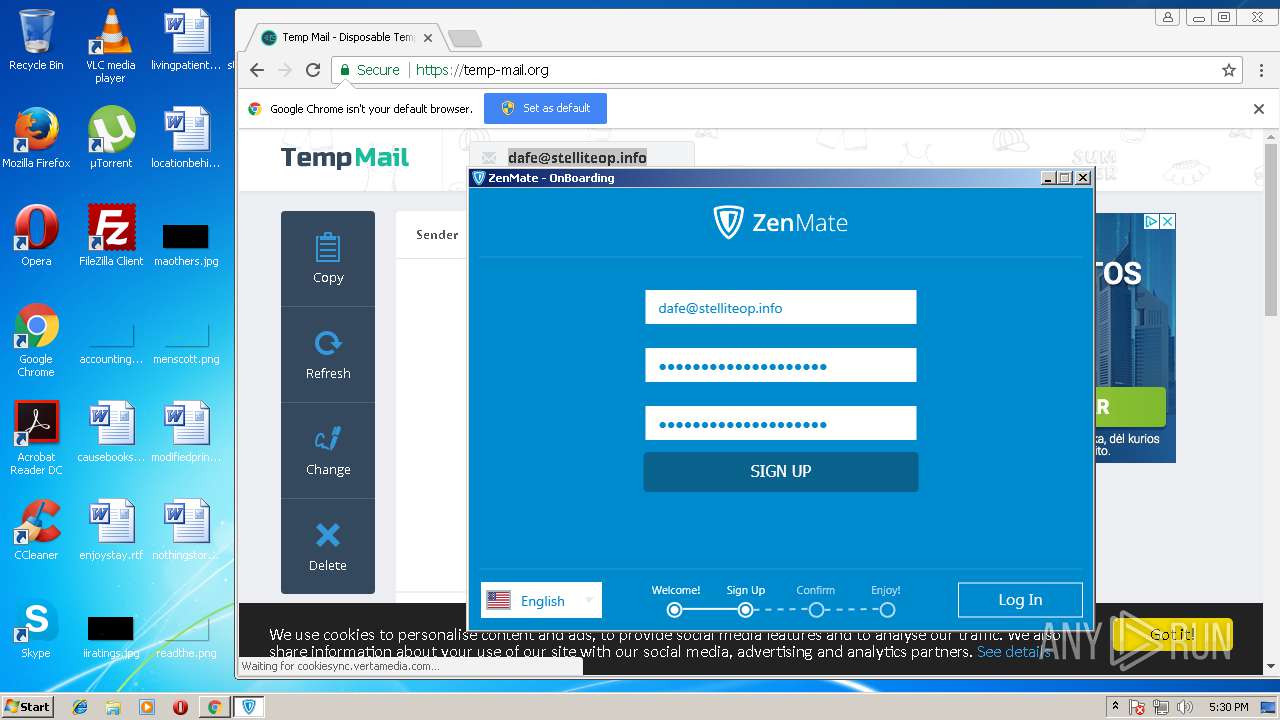
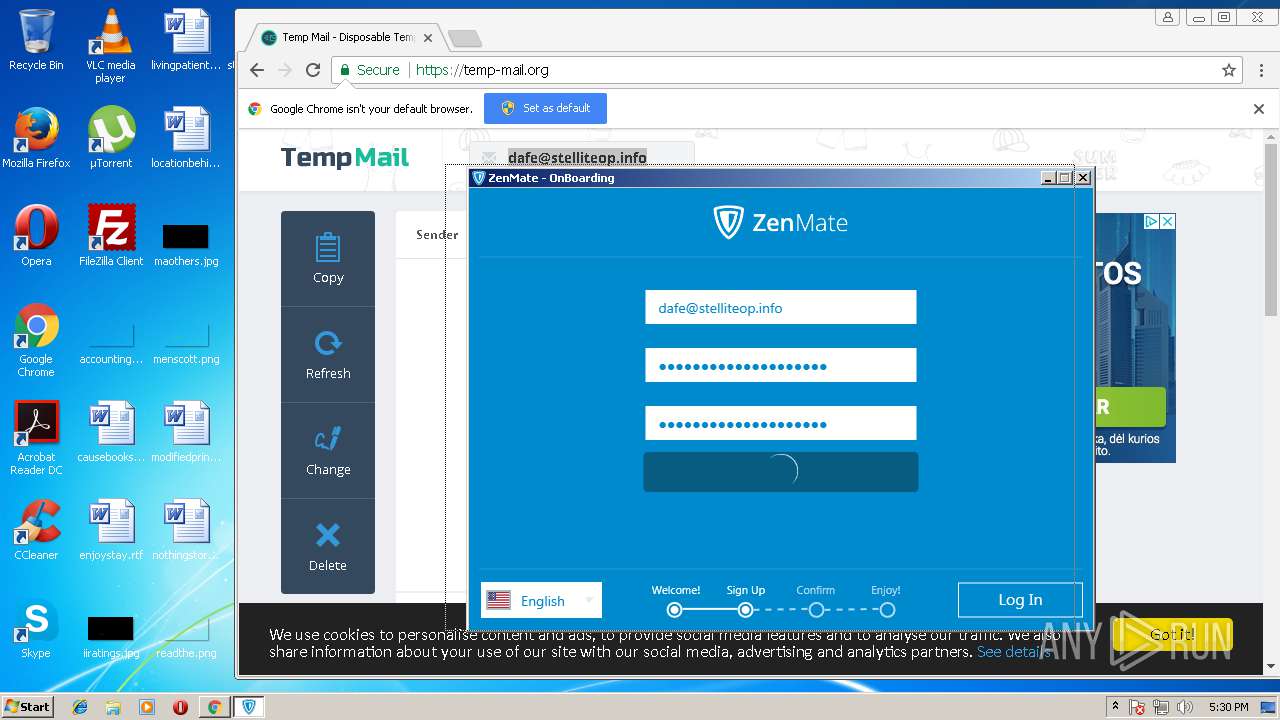
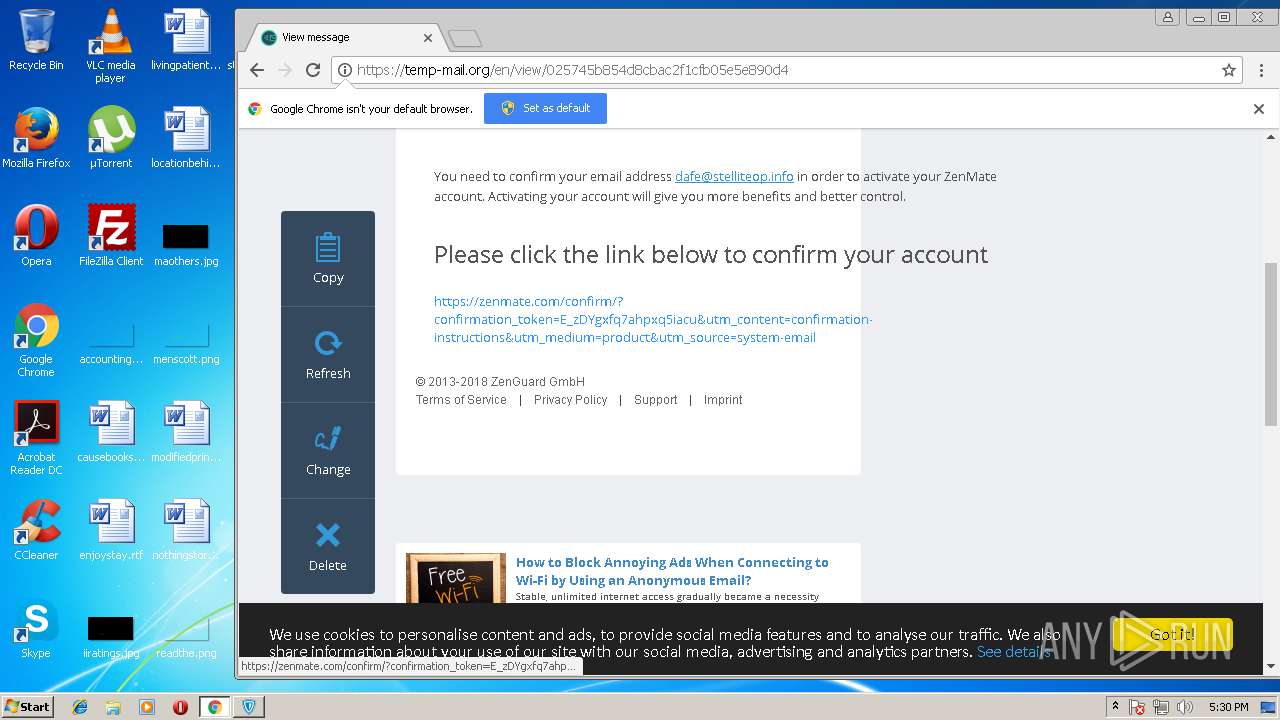
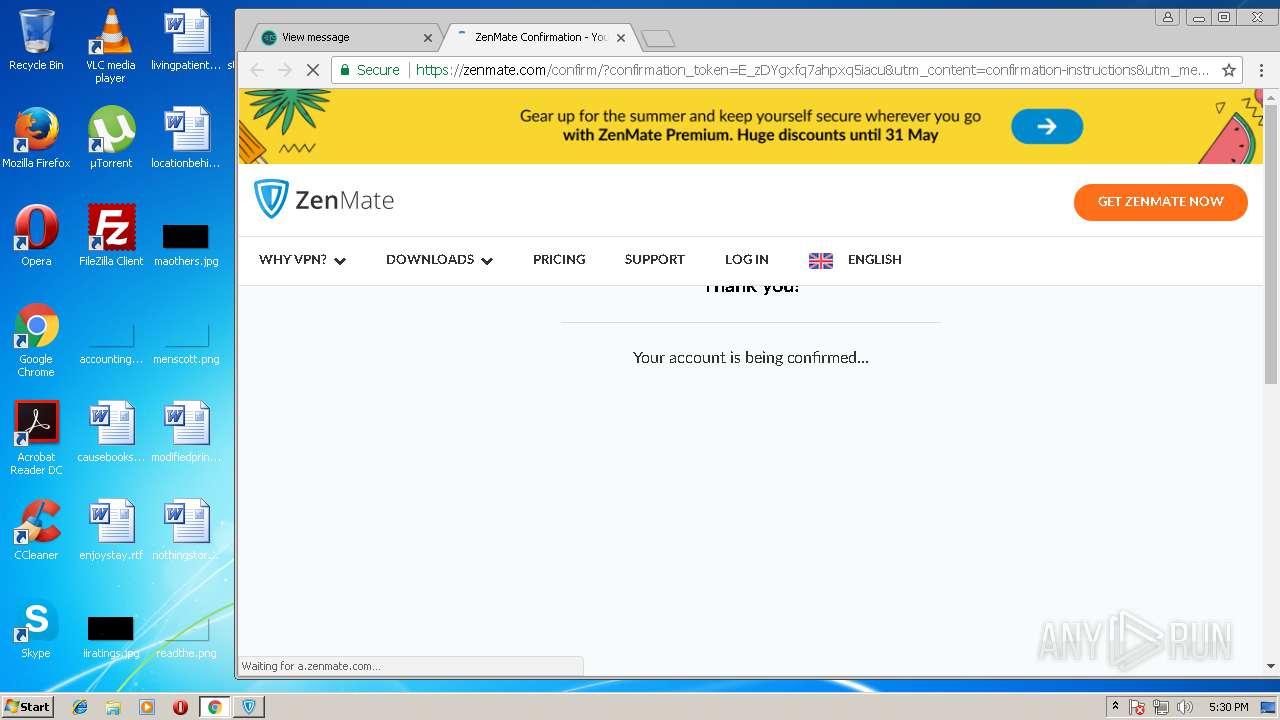
2220 | chrome.exe | GET | 301 | 104.27.153.38:80 | http://temp-mail.org/ | US | — | — | suspicious |
2220 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
2220 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
2220 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
2220 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
2220 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
2220 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
2220 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
2220 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
2220 | chrome.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3100 | ZenMate.exe | 104.24.31.106:443 | api.zcdn.de | Cloudflare Inc | US | shared |
2748 | Update.exe | 52.218.80.84:443 | s3-eu-west-1.amazonaws.com | Amazon.com, Inc. | IE | unknown |
2220 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 172.217.22.99:443 | www.google.ru | Google Inc. | US | whitelisted |
2220 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 172.217.16.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 178.250.0.74:443 | static.criteo.net | Criteo SA | FR | unknown |
2220 | chrome.exe | 172.217.18.162:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
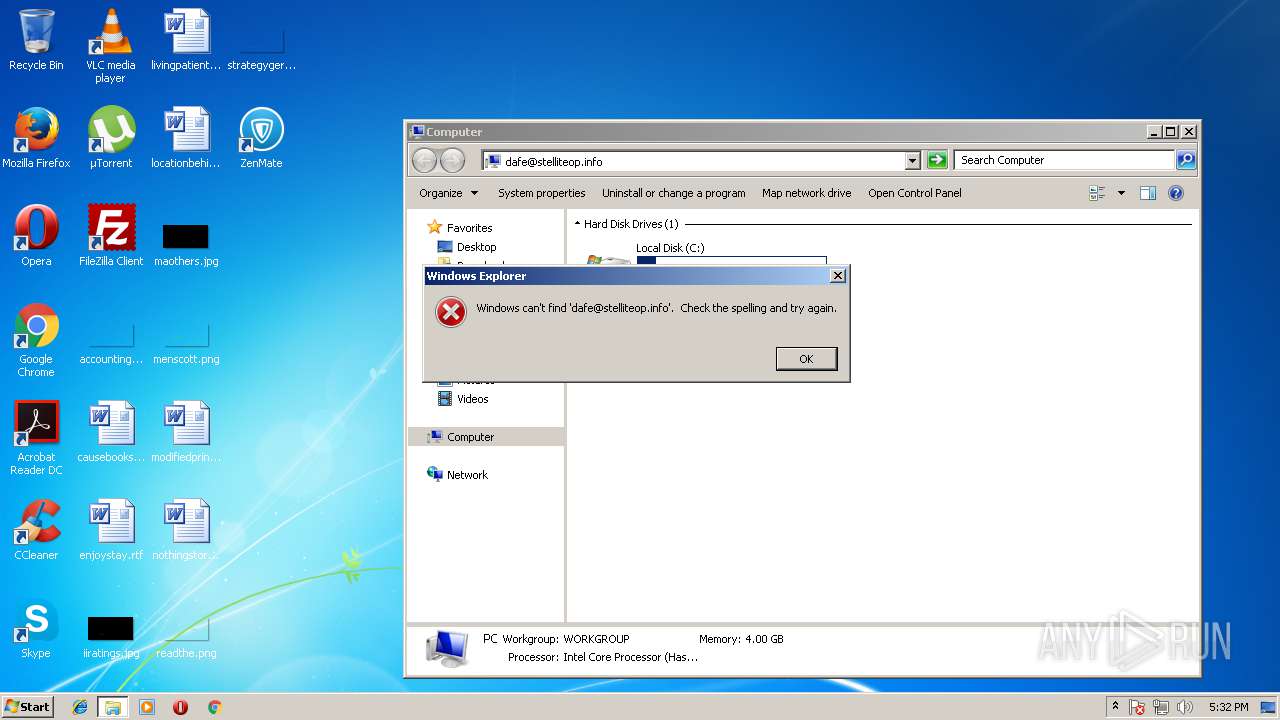
DNS requests
Domain | IP | Reputation |
|---|---|---|
s3-eu-west-1.amazonaws.com |
| shared |
api.zcdn.de |
| unknown |
zenmate-windows-update.s3.amazonaws.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
www.google.ru |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
temp-mail.org |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |