| File name: | zip |
| Full analysis: | https://app.any.run/tasks/5fbaad6e-d8da-48ae-a853-c732d2a4f62e |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 12:17:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7F7BA3D6DA851D654037FE94E5442ACE |
| SHA1: | 72ED47050B07CB27603F9CE2DCA7F5204A35D2F9 |
| SHA256: | 83D5AD1F70CBE68C591E97E5AB7491D4E308A8BC931263CC4B937A433F02A2A4 |
| SSDEEP: | 24576:cJYtjyYU1juGMC72LHa+UdEnL6bc3hRAwLdhN4e0M/uWKrz8SZWep5nysp2bT1vO:ltjyZZue7J+UanLzvhD/ut0vep5ysQFm |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
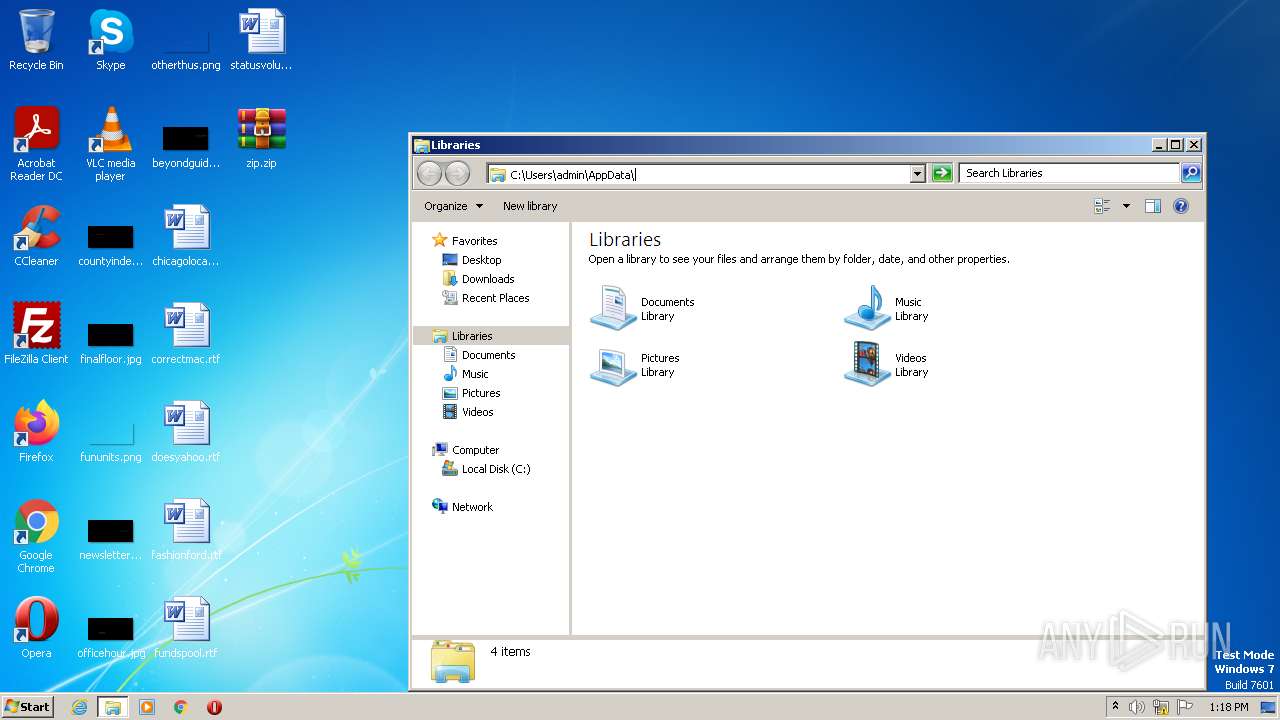
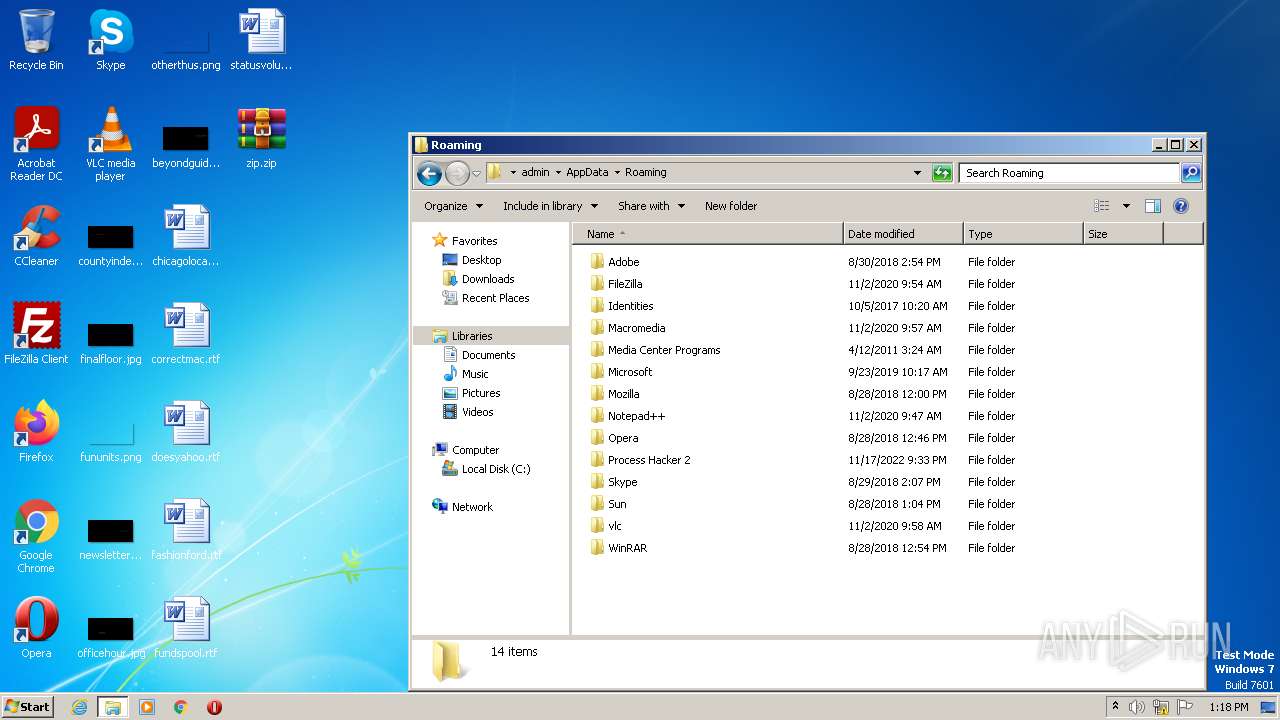
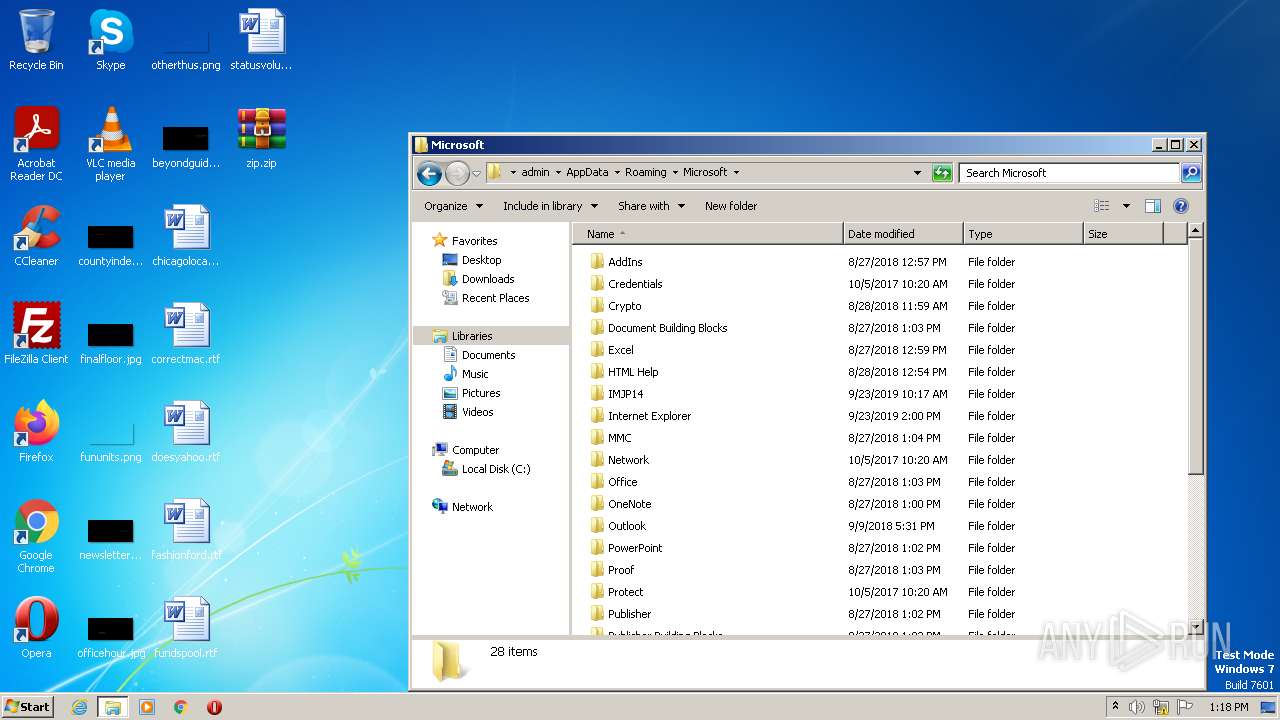
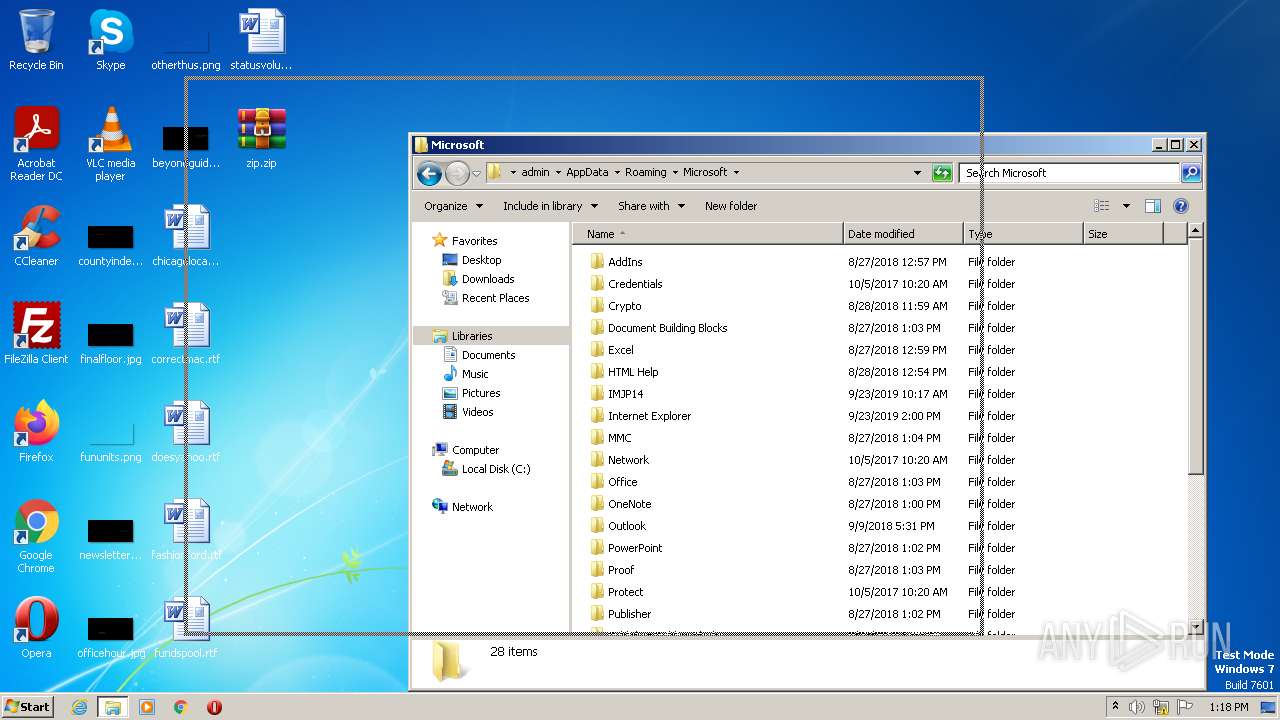
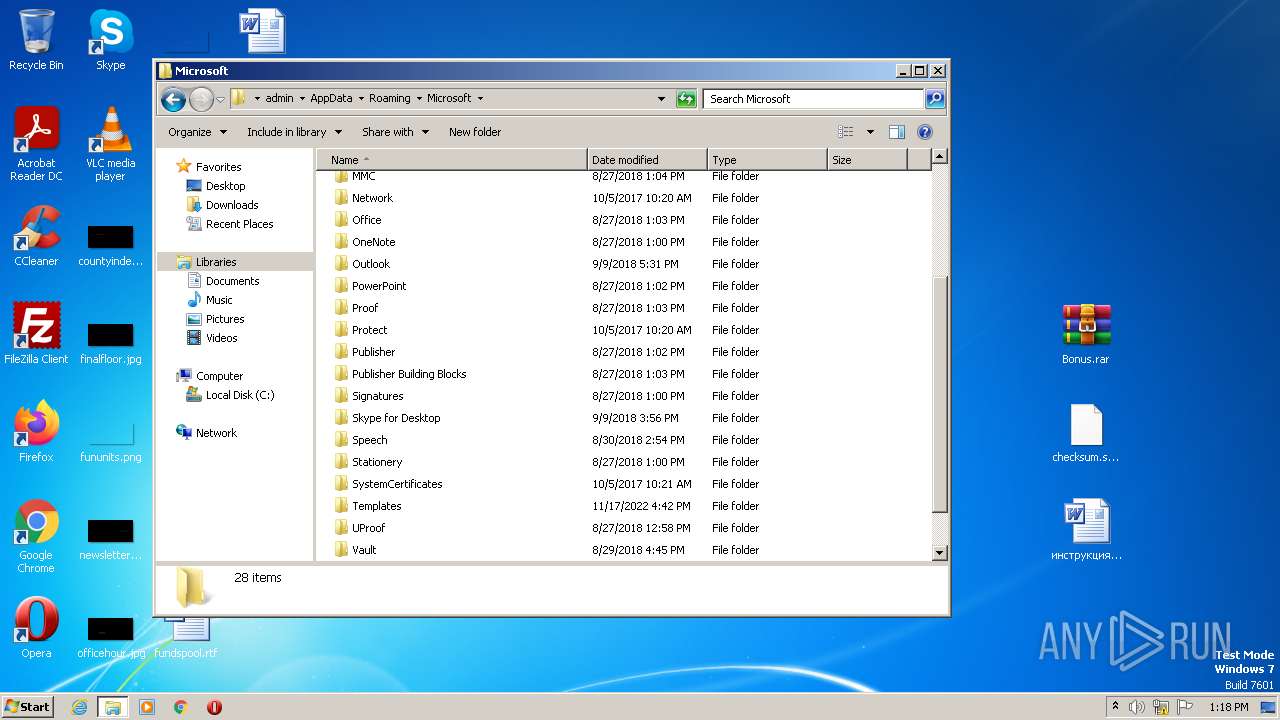
Manual execution by a user
- explorer.exe (PID: 3656)
- chrome.exe (PID: 3252)
The process checks LSA protection
- explorer.exe (PID: 3656)
Application launched itself
- chrome.exe (PID: 3252)
Create files in a temporary directory
- chrome.exe (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
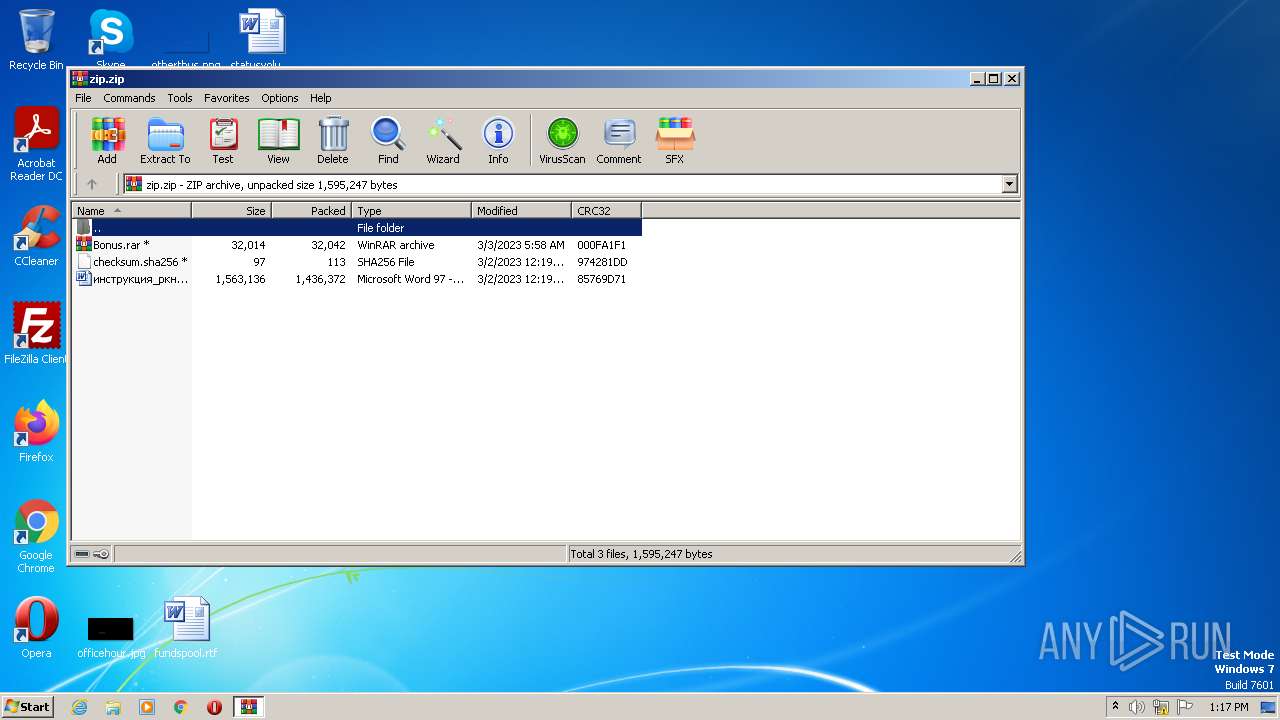
| ZipFileName: | - |
|---|---|
| ZipUncompressedSize: | 1563136 |
| ZipCompressedSize: | 1436372 |
| ZipCRC: | 0x85769d71 |
| ZipModifyDate: | 2023:03:02 12:19:00 |
| ZipCompression: | Unknown (99) |
| ZipBitFlag: | 0x0809 |
| ZipRequiredVersion: | 20 |
Total processes
62
Monitored processes
24
Malicious processes
0
Suspicious processes
0
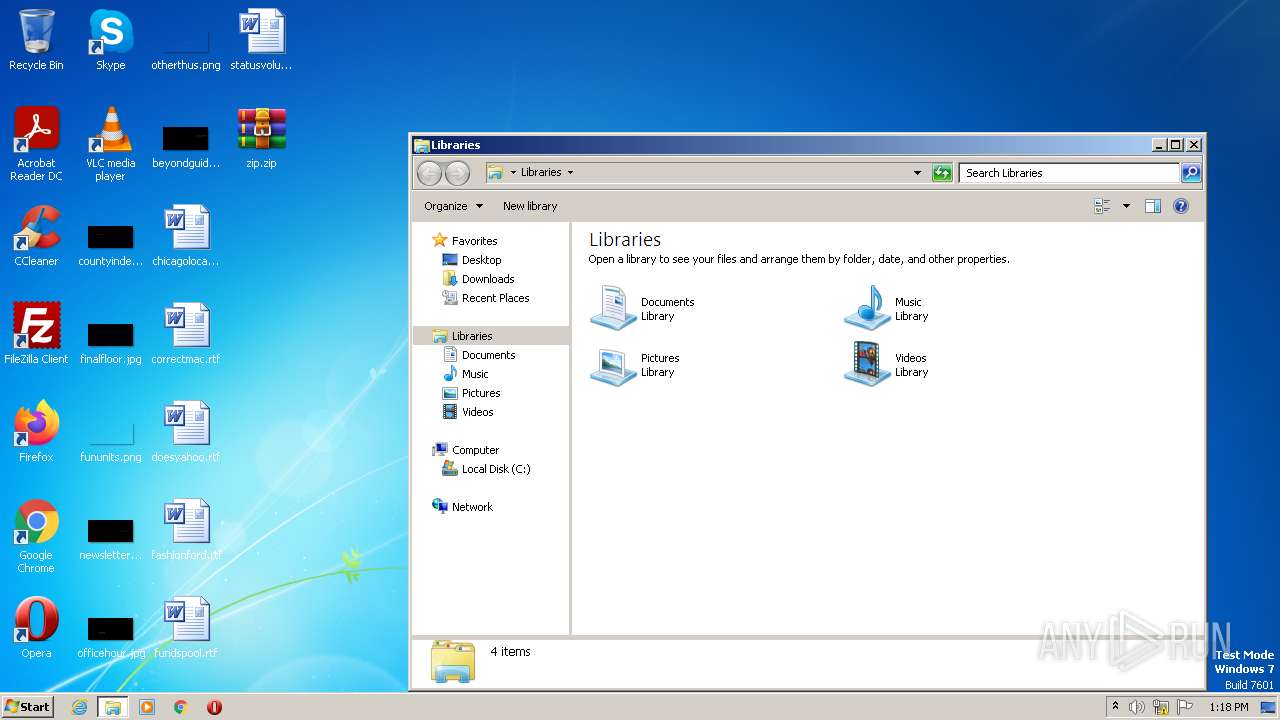
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1120,14526361997560081693,17613881429671850994,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3744 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1120,14526361997560081693,17613881429671850994,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2844 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1120,14526361997560081693,17613881429671850994,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1424 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
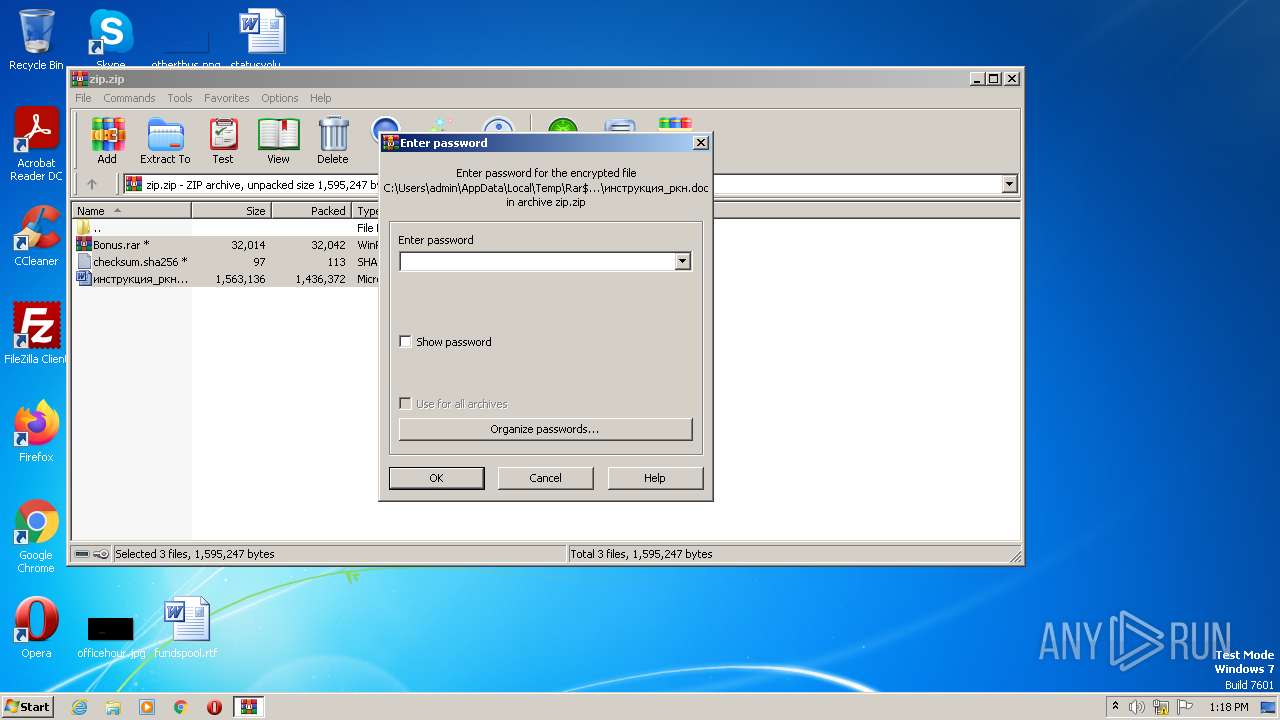
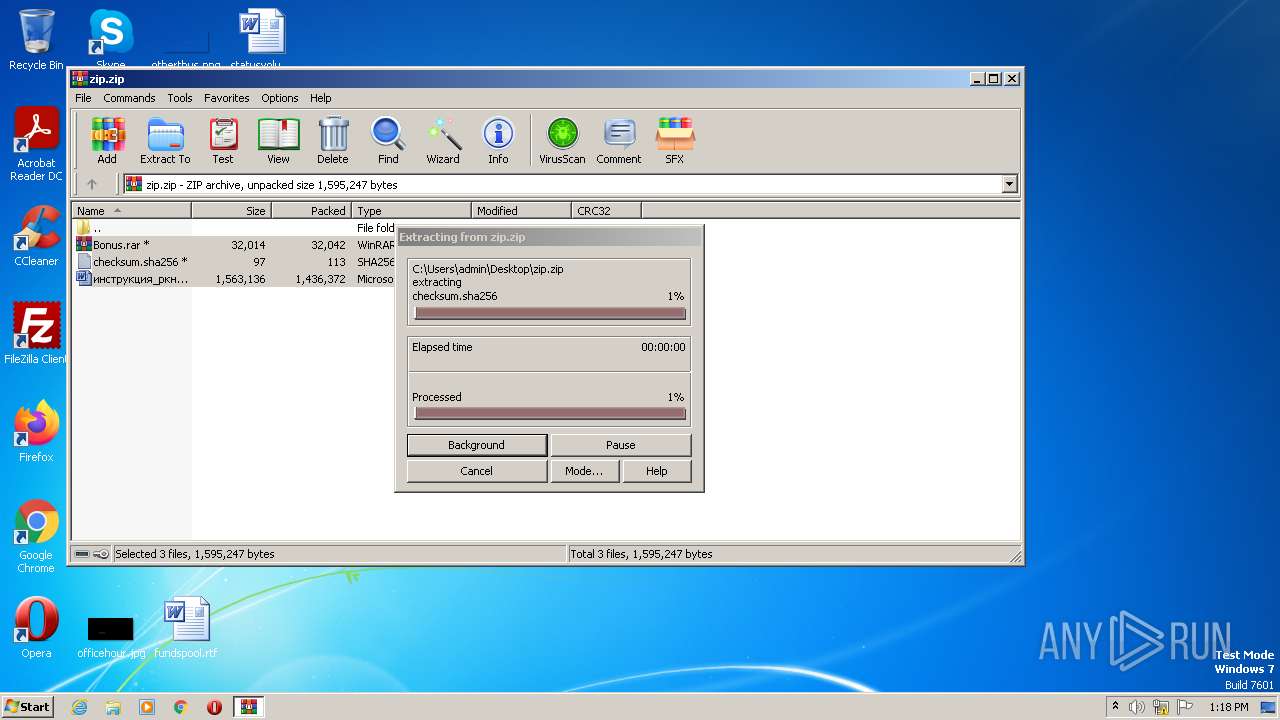
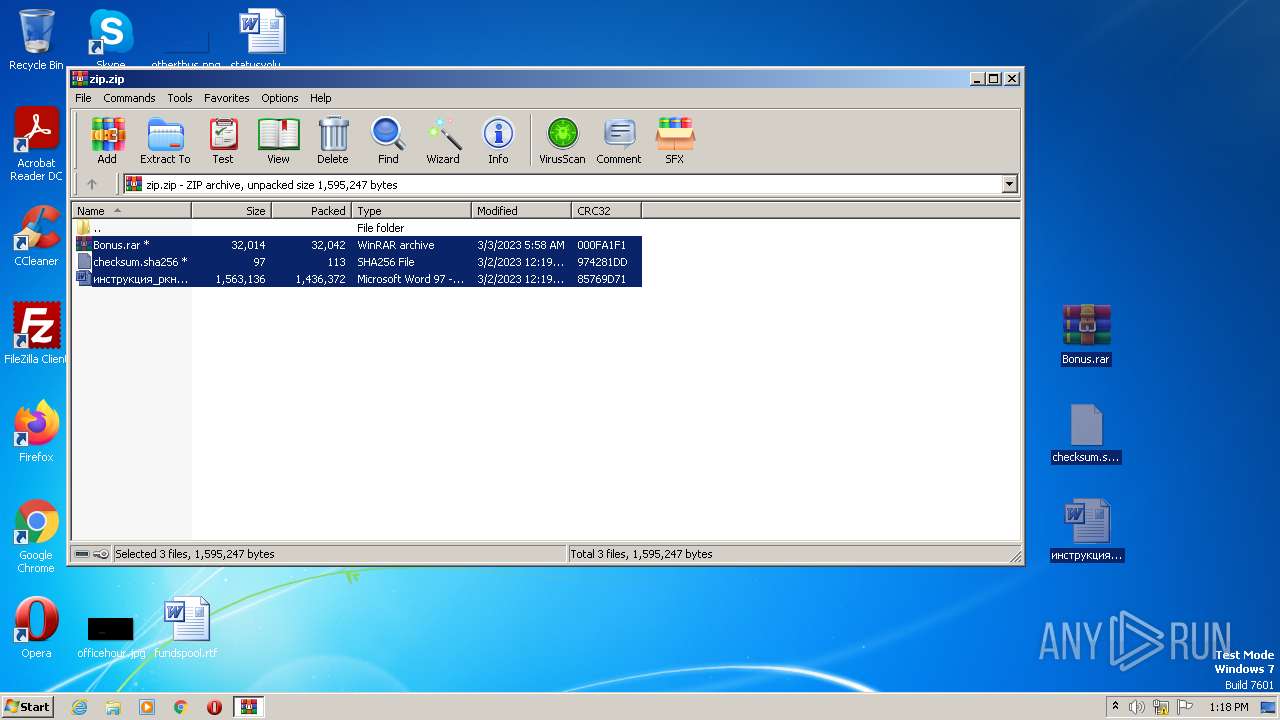
| 2644 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\zip.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1120,14526361997560081693,17613881429671850994,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1120,14526361997560081693,17613881429671850994,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3440 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1120,14526361997560081693,17613881429671850994,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1120,14526361997560081693,17613881429671850994,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3724 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1120,14526361997560081693,17613881429671850994,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1120,14526361997560081693,17613881429671850994,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
17 912
Read events
17 770
Write events
142
Delete events
0
Modification events
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
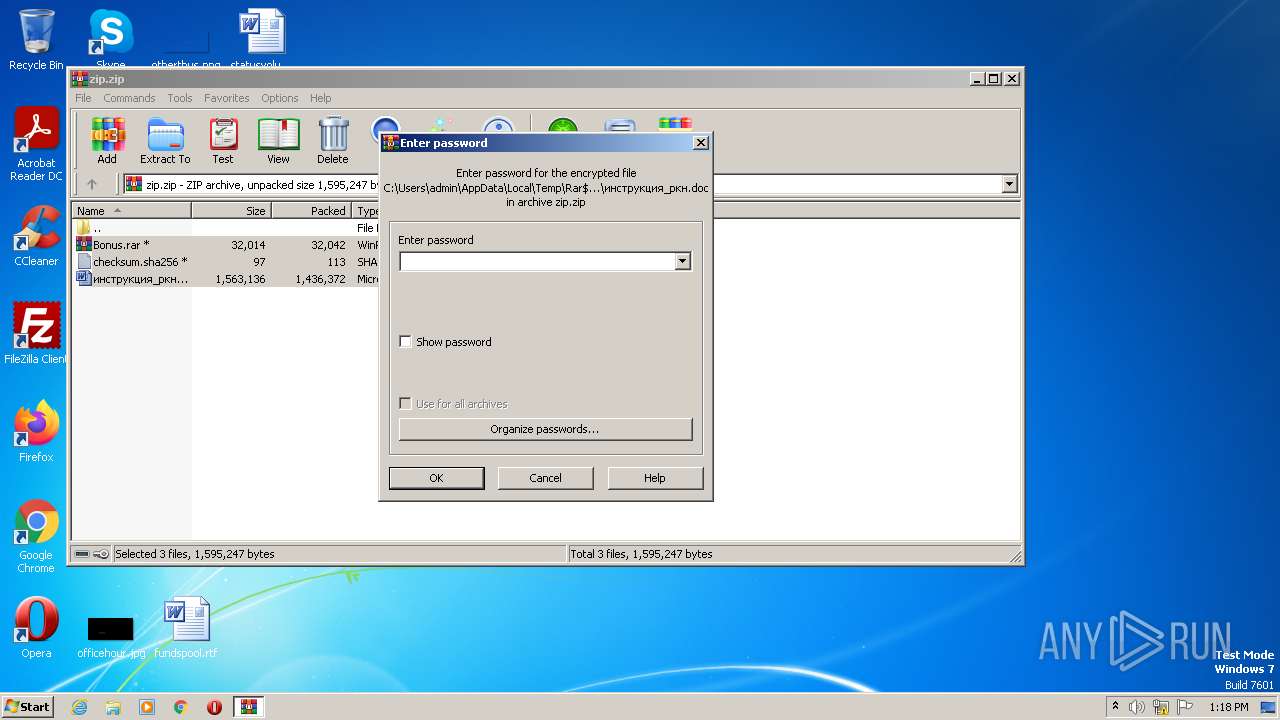
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
0
Suspicious files
242
Text files
170
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-64282111-CB4.pma | — | |
MD5:— | SHA256:— | |||
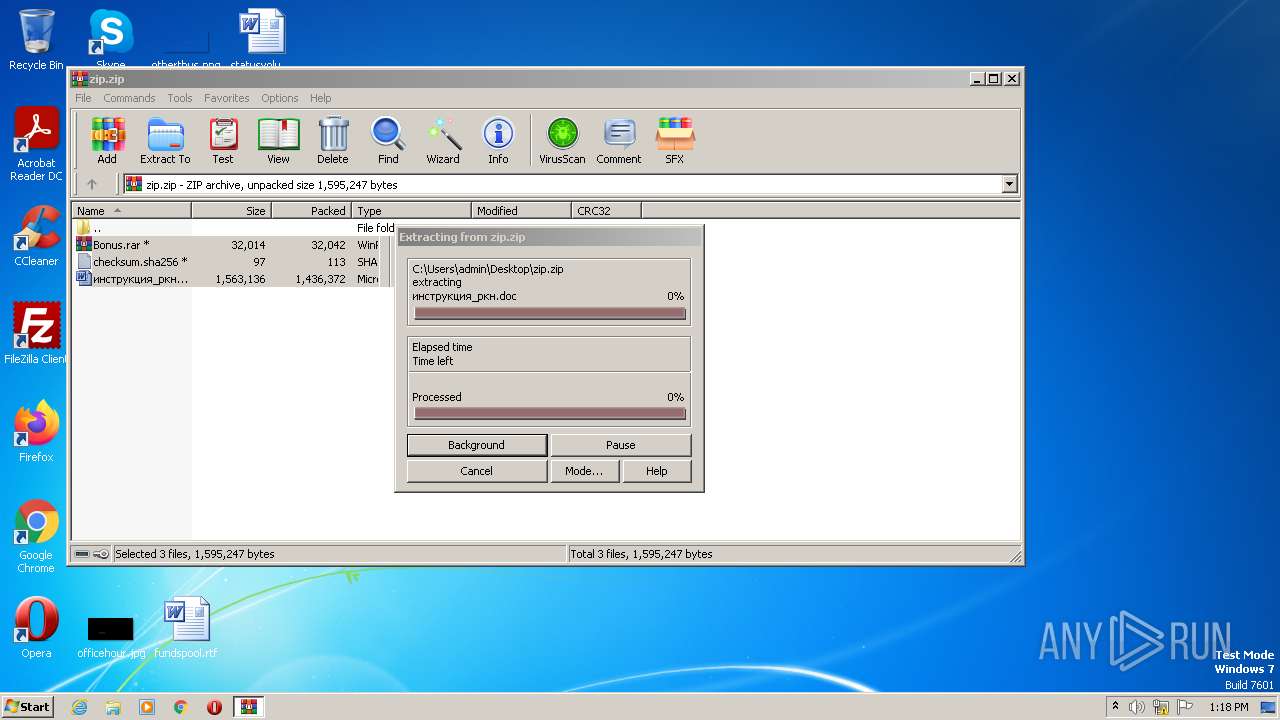
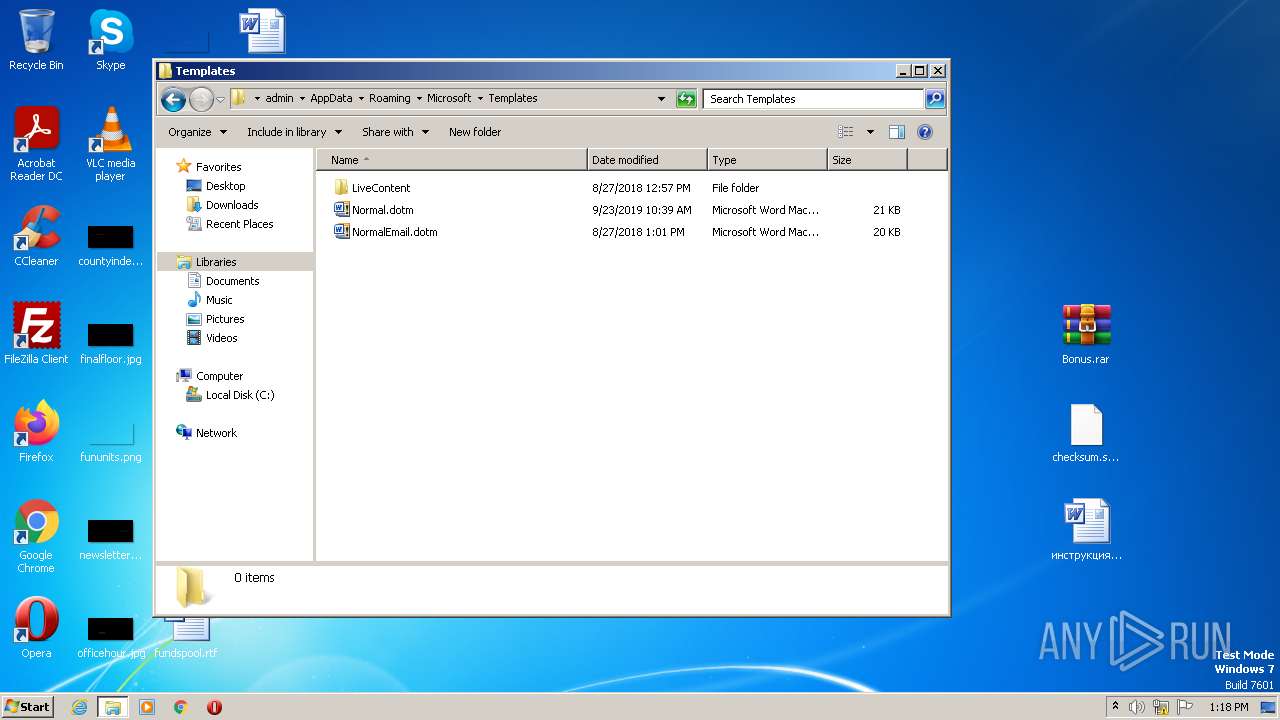
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2644.46483\checksum.sha256 | text | |
MD5:— | SHA256:— | |||
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2644.46483\инструкция_ркн.doc | document | |
MD5:— | SHA256:— | |||
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2644.46483\Bonus.rar | compressed | |
MD5:— | SHA256:— | |||
| 3252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b3fb0df5-2cd8-45a3-b60a-2239ff1de95f.tmp | text | |
MD5:— | SHA256:— | |||
| 3252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF256b1a.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
38
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
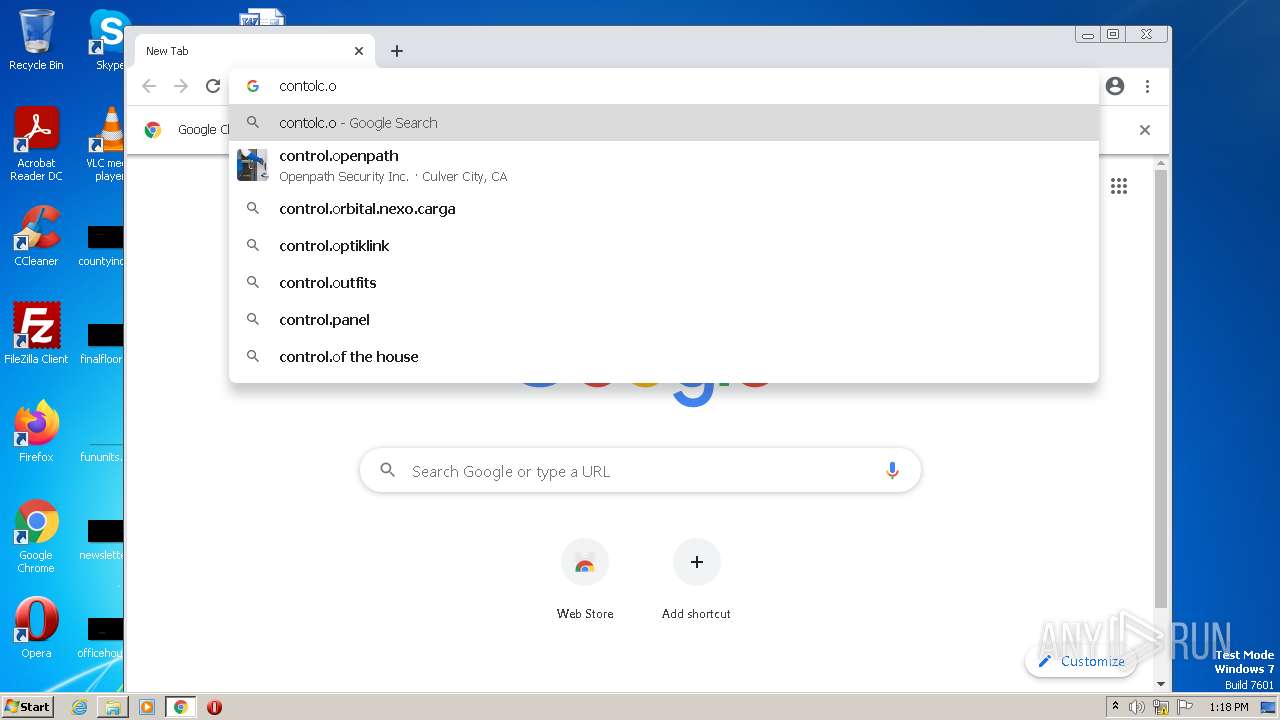
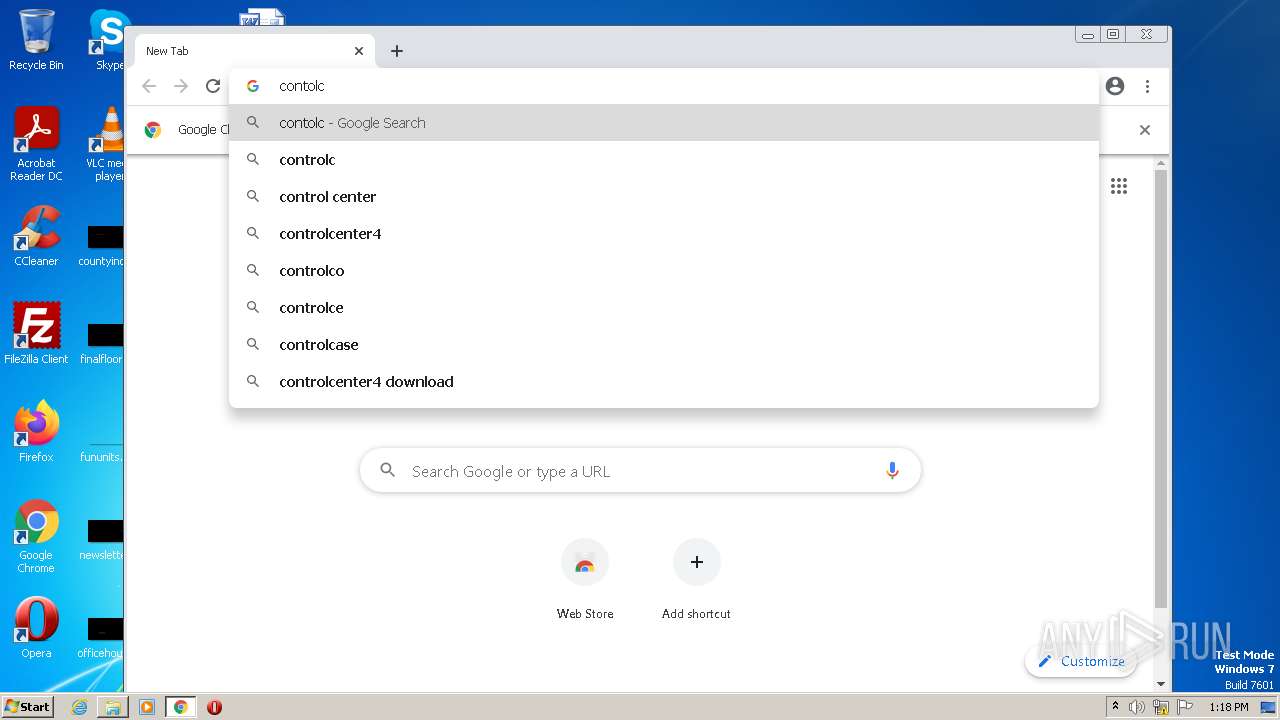
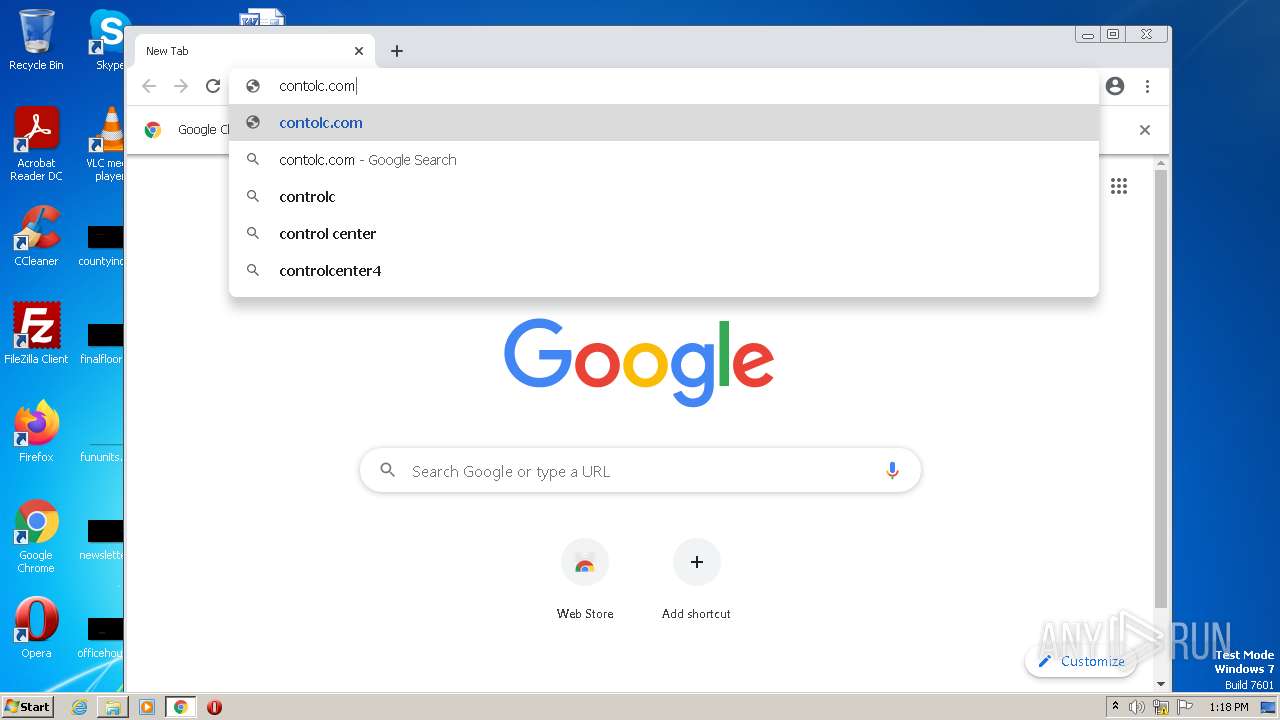
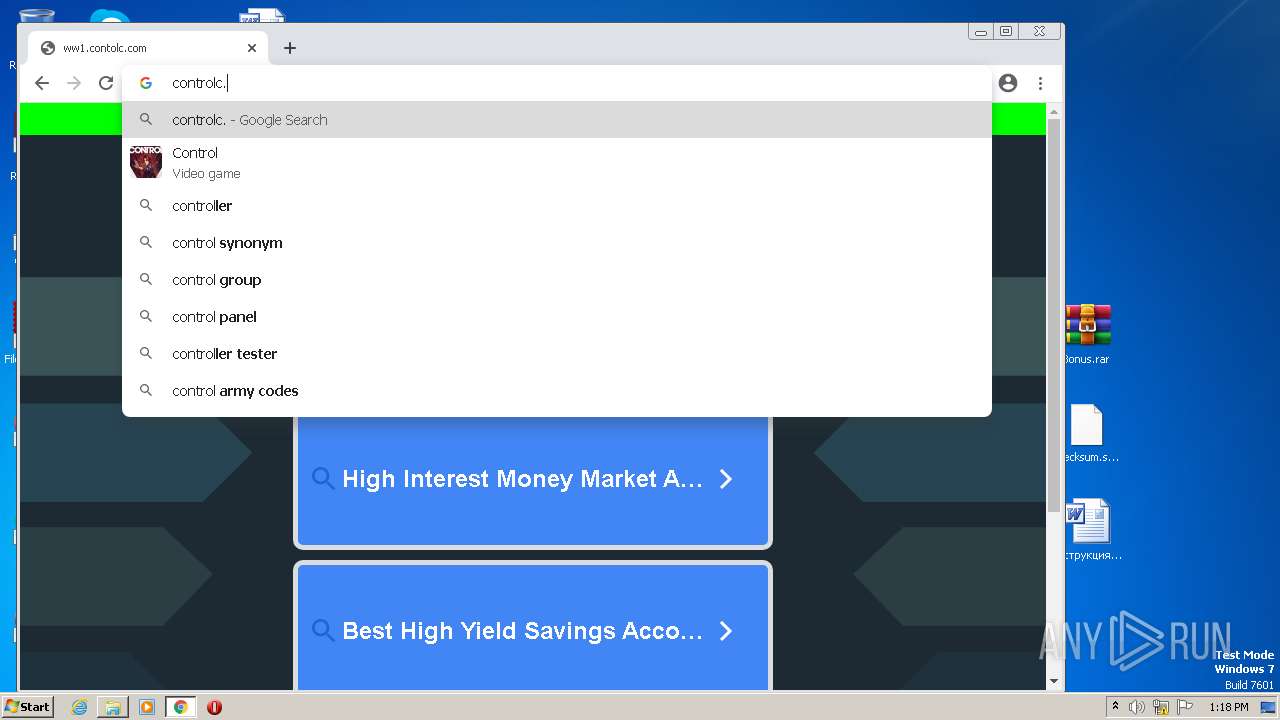
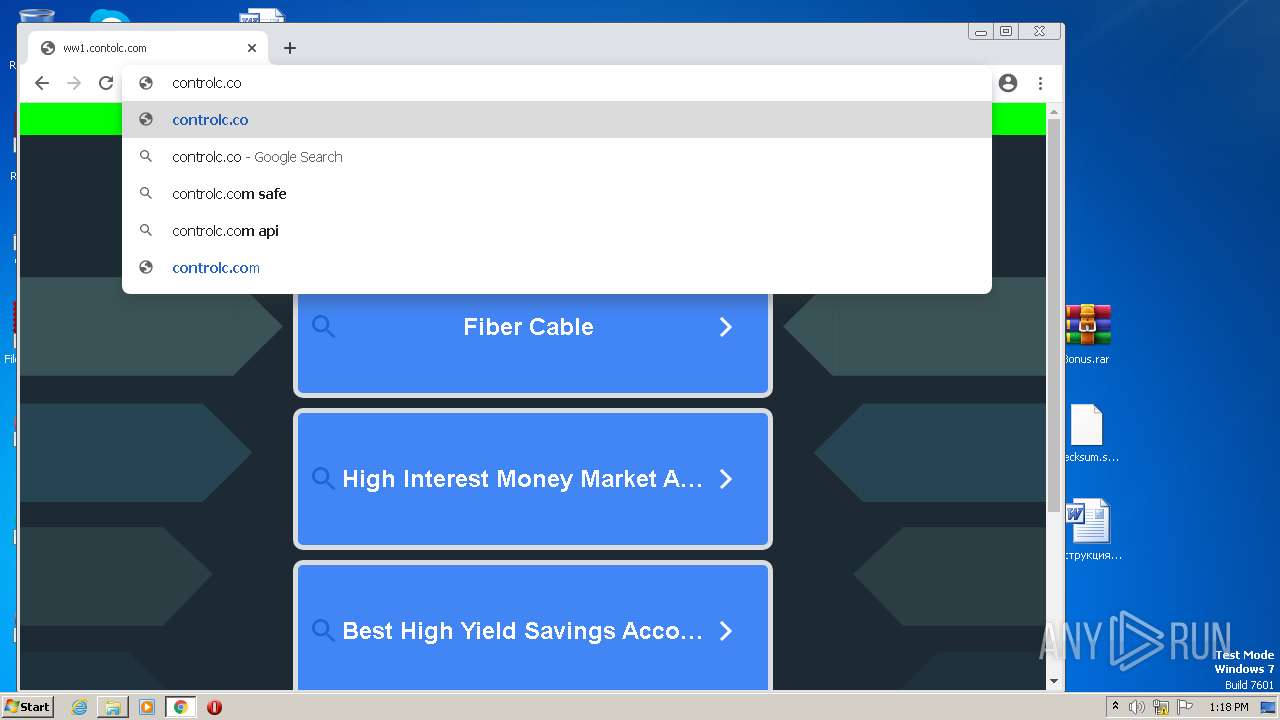
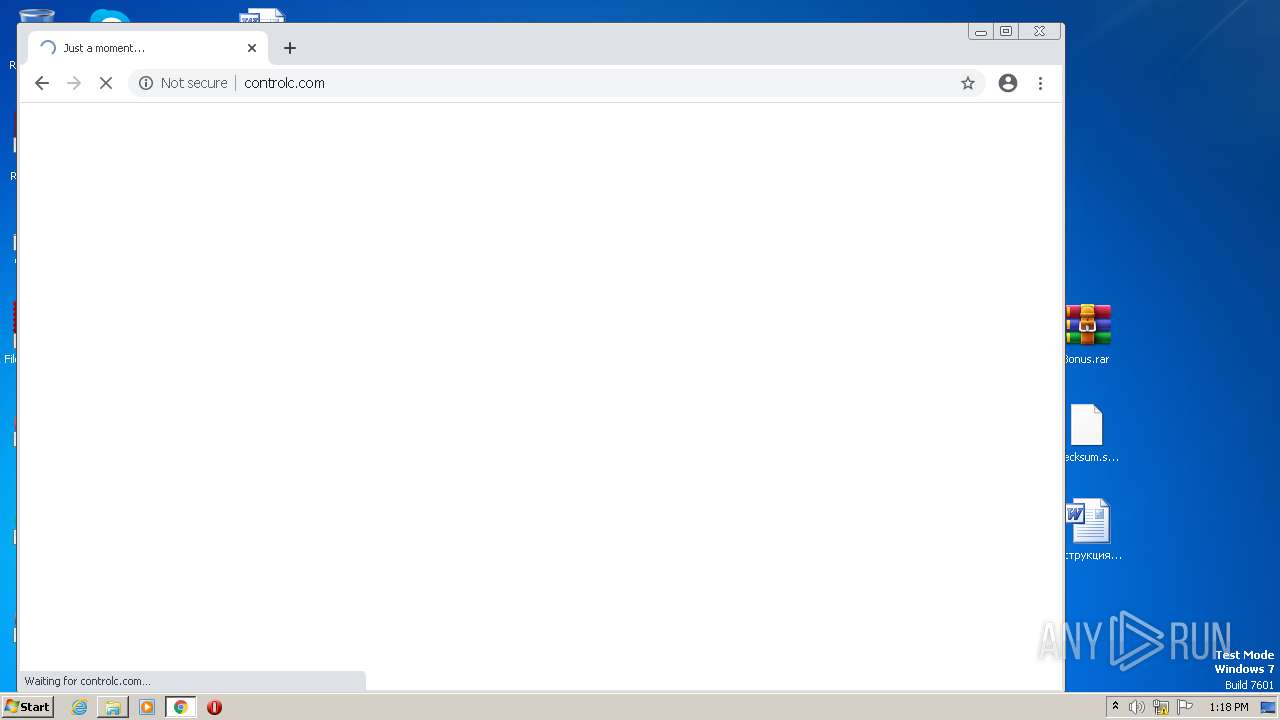
3804 | chrome.exe | POST | 200 | 172.67.131.19:80 | http://controlc.com/cdn-cgi/challenge-platform/h/b/flow/ov1/528124820:1680350901:X-oh1kCnXdZVwECI9End1M07F2s6og6DHDzU4BVYE-U/7b10c6dadcf73af9/a166c8a065dae7a | US | text | 3.80 Kb | malicious |
3804 | chrome.exe | POST | 200 | 172.67.131.19:80 | http://controlc.com/cdn-cgi/challenge-platform/h/b/flow/ov1/528124820:1680350901:X-oh1kCnXdZVwECI9End1M07F2s6og6DHDzU4BVYE-U/7b10c6dadcf73af9/a166c8a065dae7a | US | text | 49.1 Kb | malicious |
3804 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
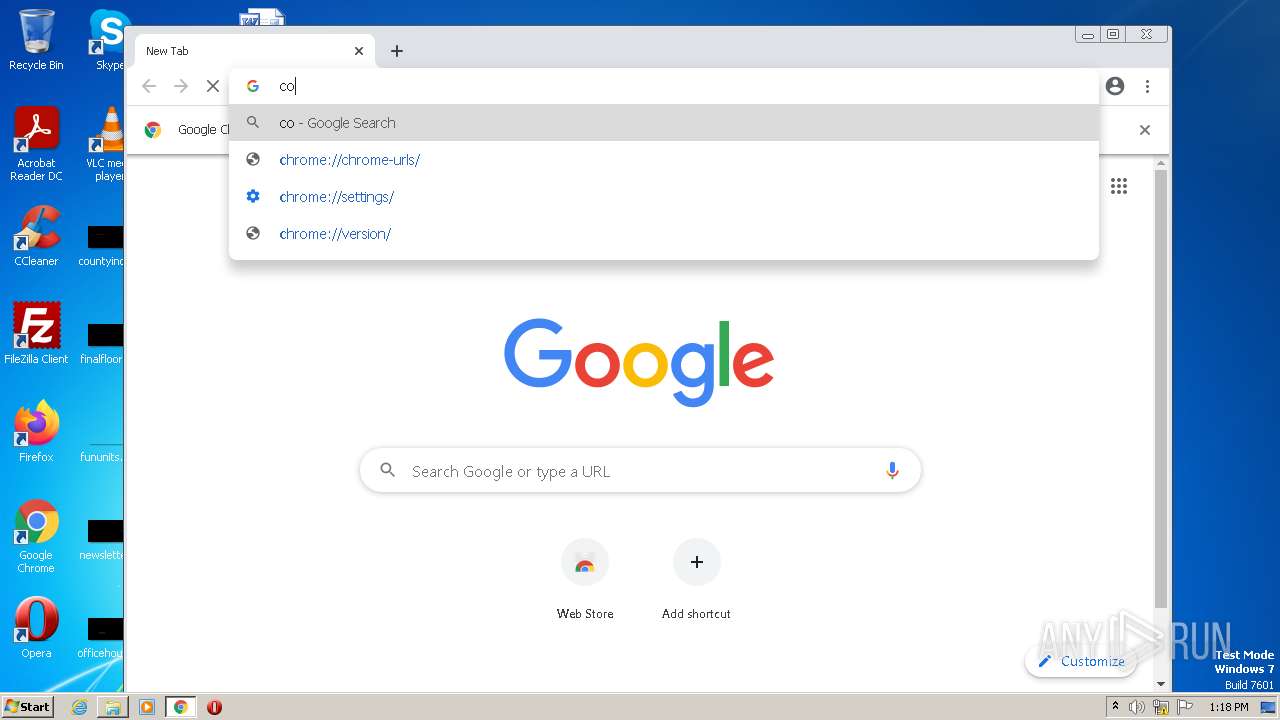
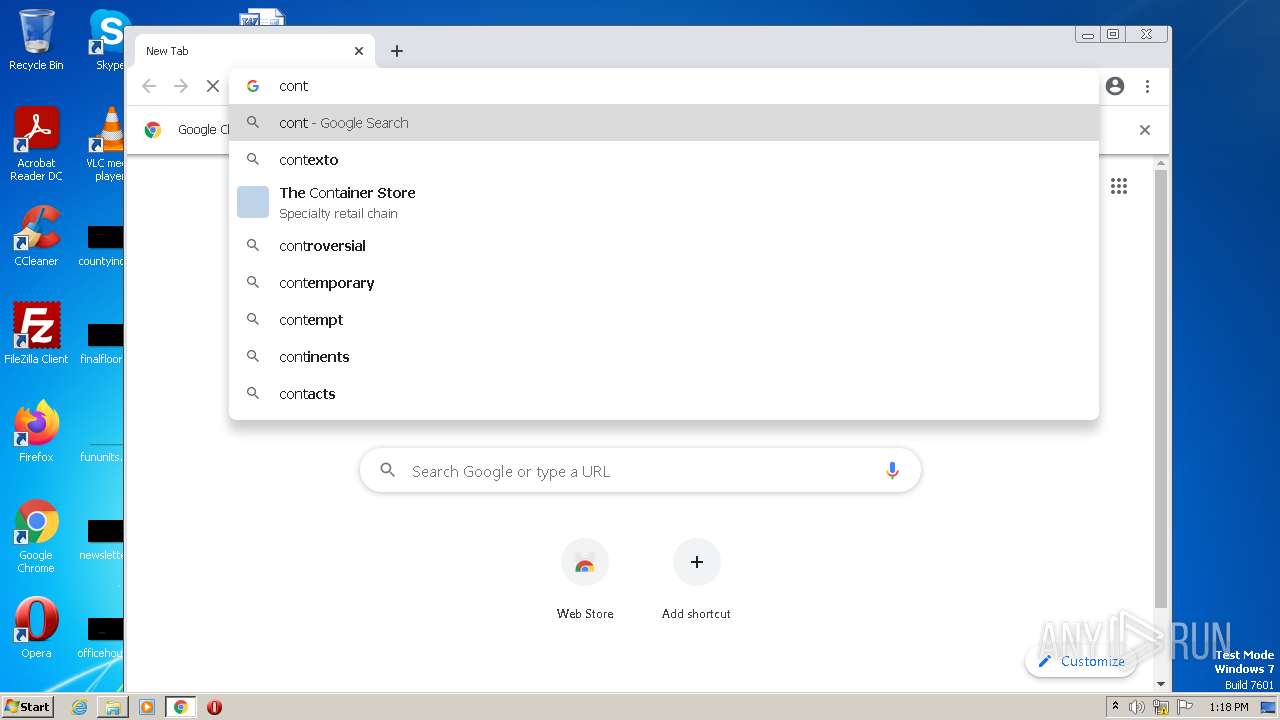
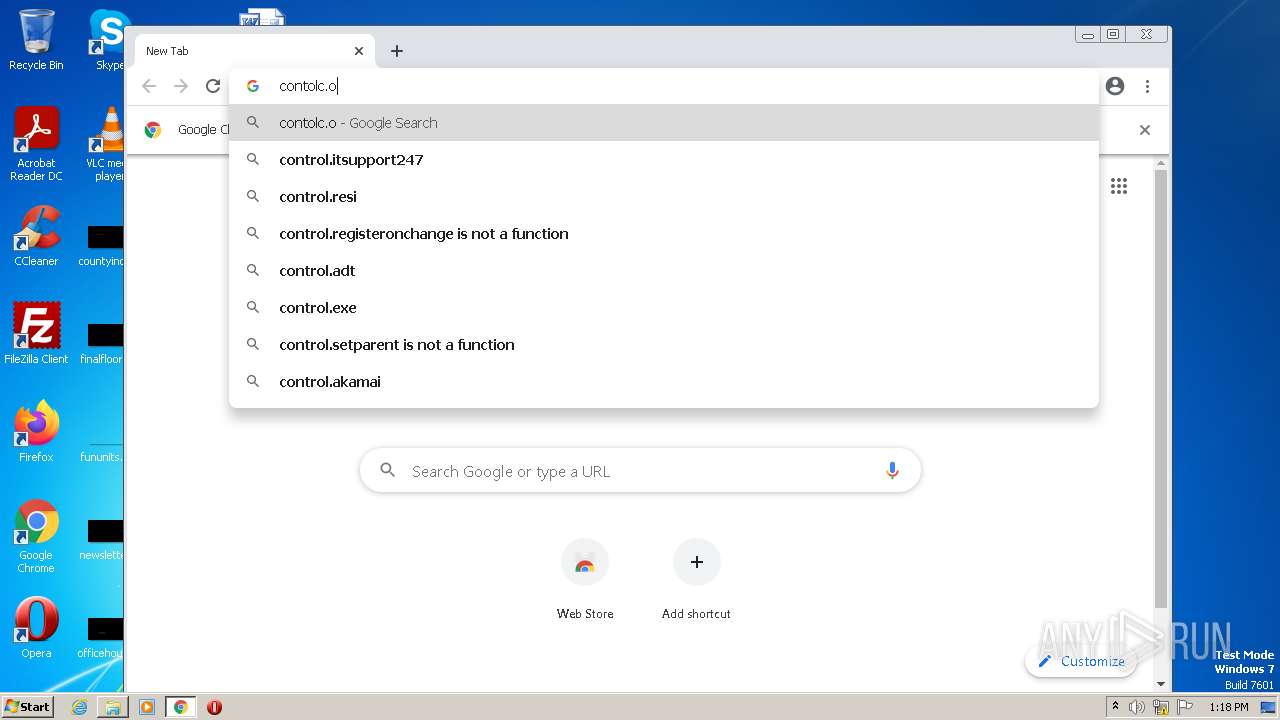
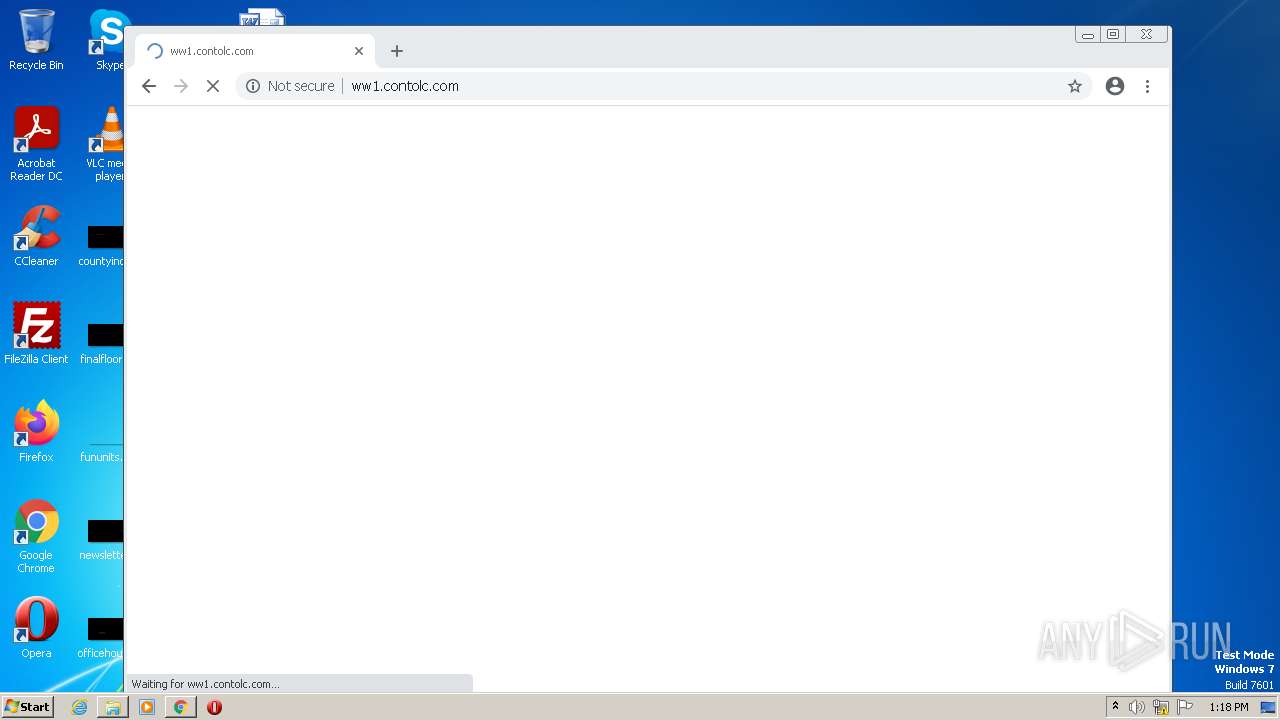
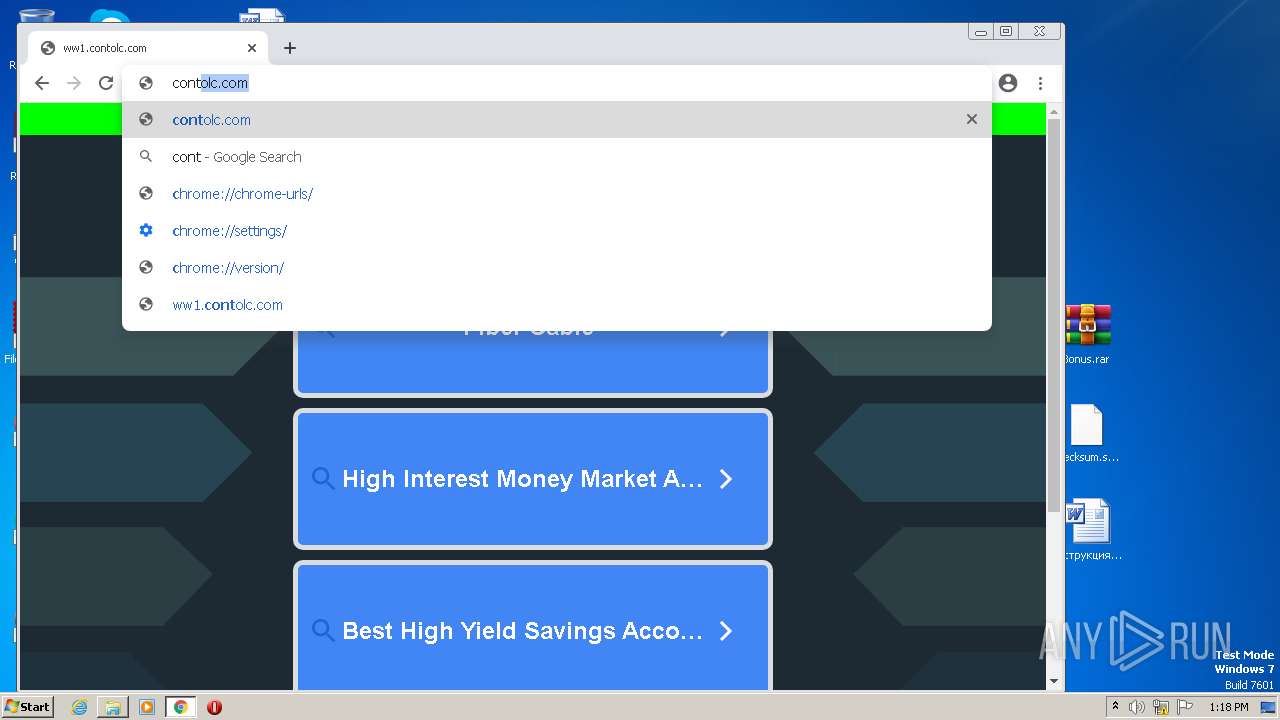
3804 | chrome.exe | GET | 200 | 35.186.238.101:80 | http://ww1.contolc.com/px.js?ch=2&abp=1 | US | text | 476 b | malicious |
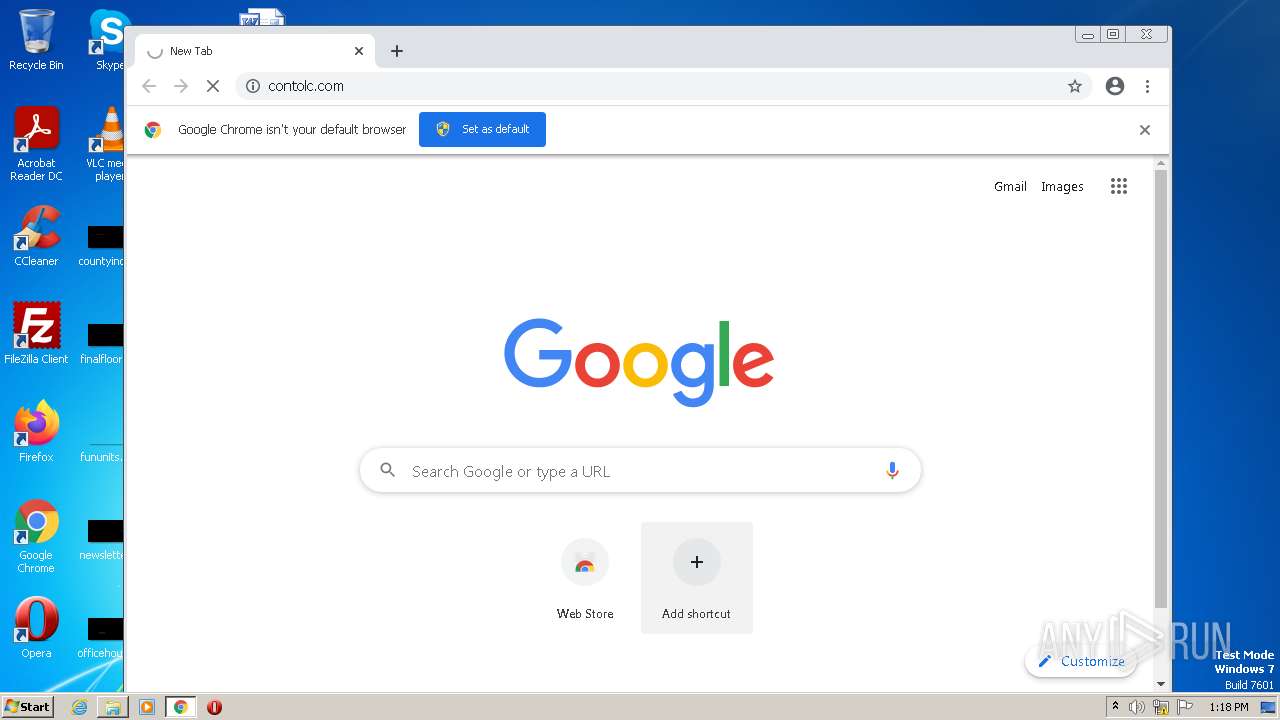
3804 | chrome.exe | GET | 302 | 77.247.183.148:80 | http://contolc.com/ | NL | text | 11 b | suspicious |
3804 | chrome.exe | GET | 200 | 35.186.238.101:80 | http://ww1.contolc.com/px.js?ch=1&abp=1 | US | text | 476 b | malicious |
3804 | chrome.exe | GET | 200 | 172.67.131.19:80 | http://controlc.com/favicon.ico | US | image | 691 b | malicious |
3804 | chrome.exe | GET | 403 | 172.67.131.19:80 | http://controlc.com/ | US | html | 3.27 Kb | malicious |
3804 | chrome.exe | GET | 200 | 172.67.131.19:80 | http://controlc.com/cdn-cgi/styles/challenges.css | US | text | 2.56 Kb | malicious |
3804 | chrome.exe | GET | 200 | 172.67.131.19:80 | http://controlc.com/cdn-cgi/images/trace/managed/js/transparent.gif?ray=7b10c6dadcf73af9 | US | image | 42 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3804 | chrome.exe | 142.250.186.33:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
3804 | chrome.exe | 142.250.181.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3804 | chrome.exe | 142.250.74.195:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3804 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3804 | chrome.exe | 142.250.186.67:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3804 | chrome.exe | 142.250.185.142:443 | apis.google.com | GOOGLE | US | whitelisted |
3804 | chrome.exe | 142.250.184.196:443 | www.google.com | GOOGLE | US | whitelisted |
3804 | chrome.exe | 142.250.184.237:443 | accounts.google.com | GOOGLE | US | suspicious |
3804 | chrome.exe | 142.250.185.78:443 | clients2.google.com | GOOGLE | US | whitelisted |
3804 | chrome.exe | 77.247.183.148:80 | contolc.com | NForce Entertainment B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |