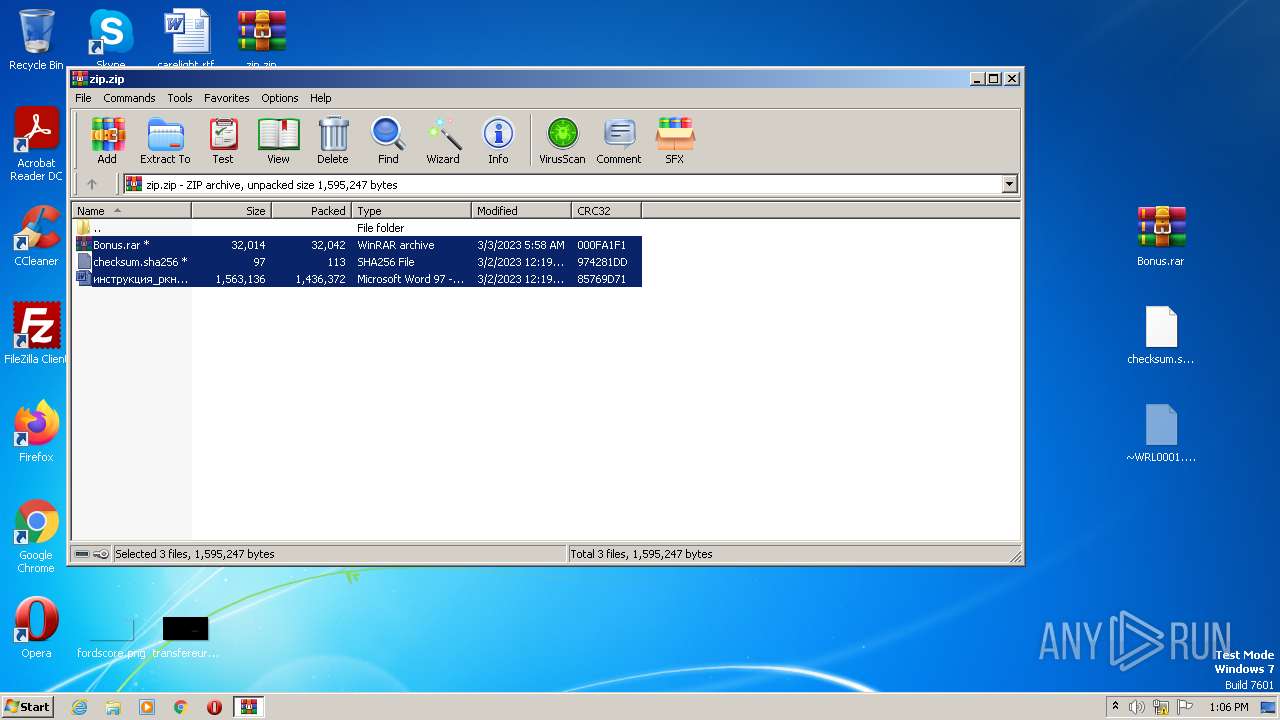
| download: | zip |
| Full analysis: | https://app.any.run/tasks/499d0818-d4f0-4289-93ab-597a26f6d254 |
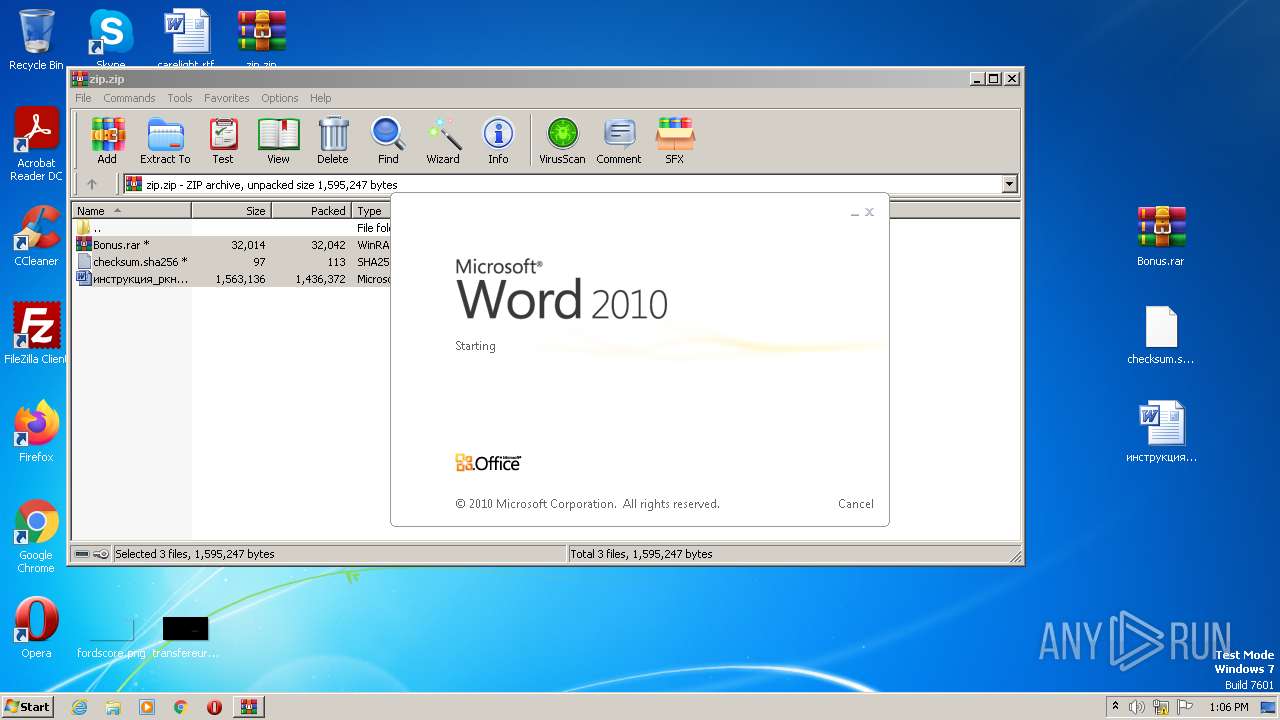
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 12:05:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7F7BA3D6DA851D654037FE94E5442ACE |
| SHA1: | 72ED47050B07CB27603F9CE2DCA7F5204A35D2F9 |
| SHA256: | 83D5AD1F70CBE68C591E97E5AB7491D4E308A8BC931263CC4B937A433F02A2A4 |
| SSDEEP: | 24576:cJYtjyYU1juGMC72LHa+UdEnL6bc3hRAwLdhN4e0M/uWKrz8SZWep5nysp2bT1vO:ltjyZZue7J+UanLzvhD/ut0vep5ysQFm |
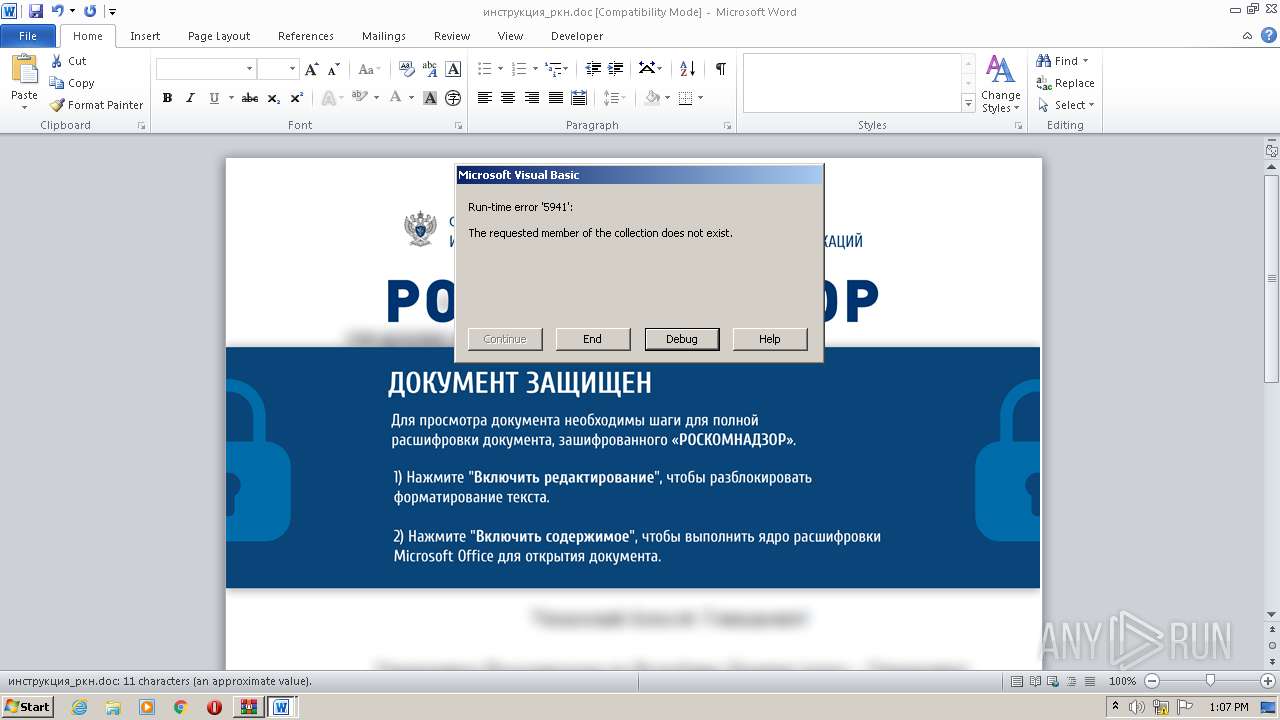
MALICIOUS
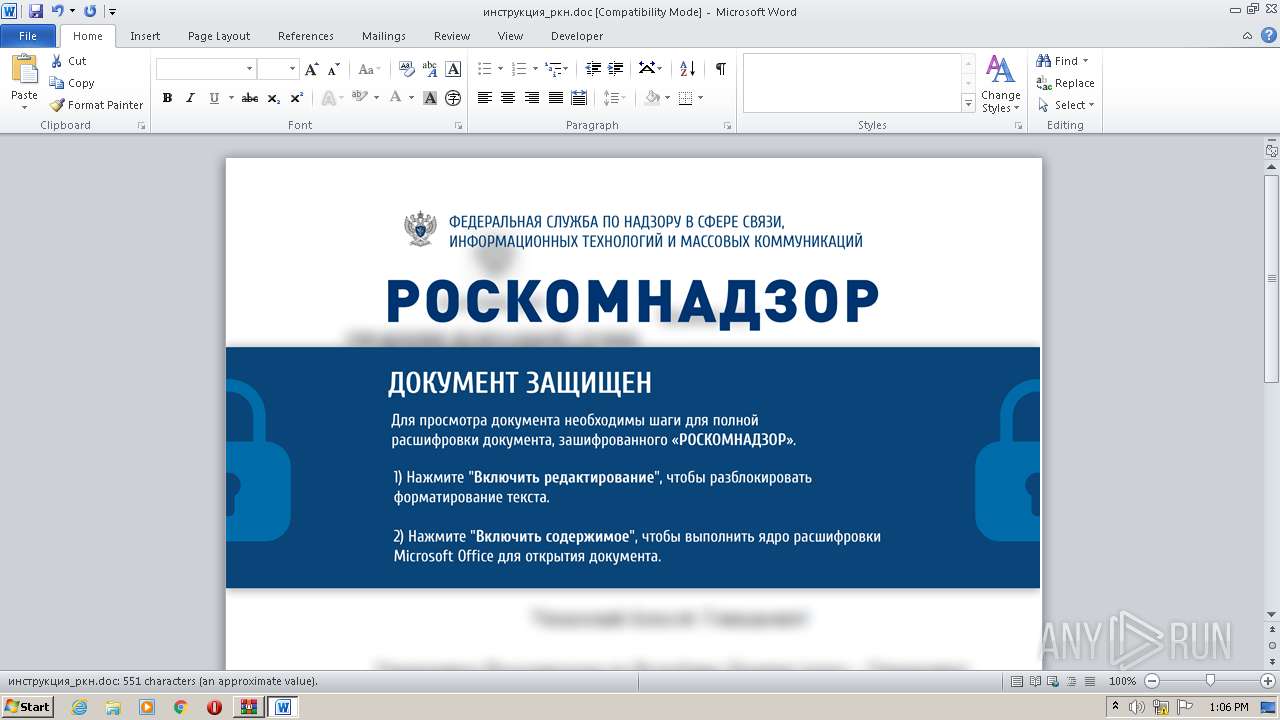
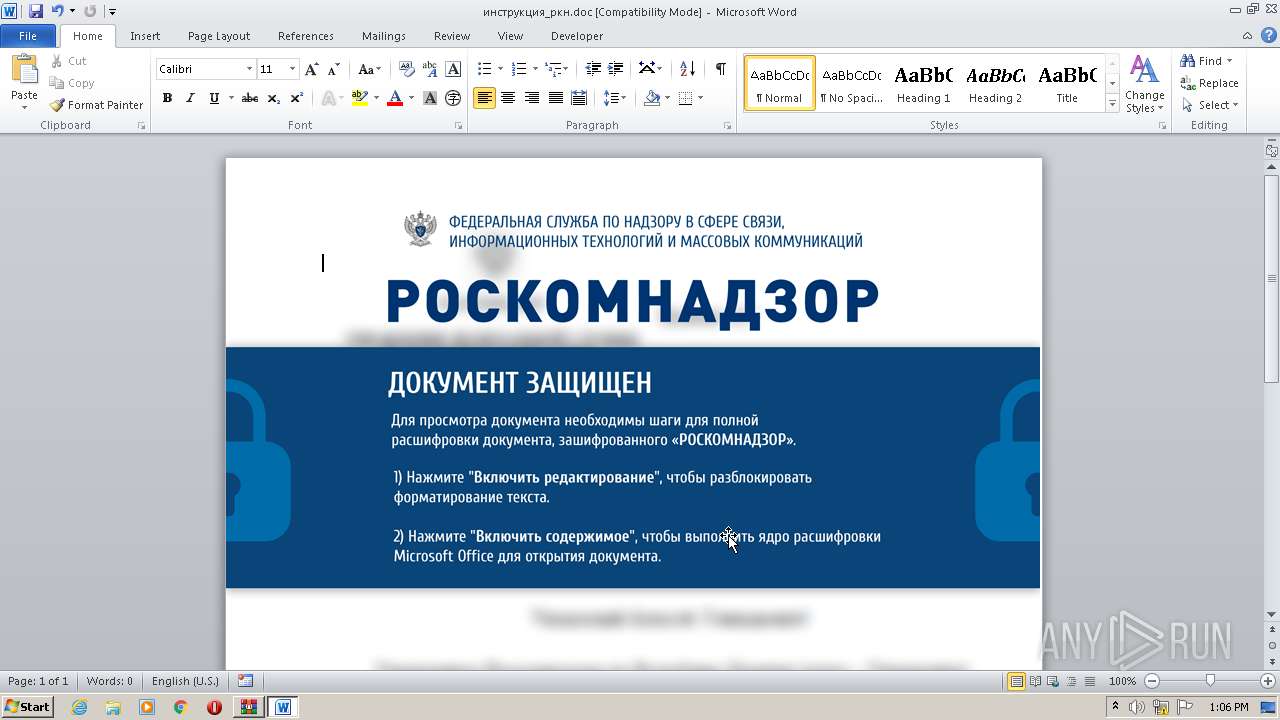
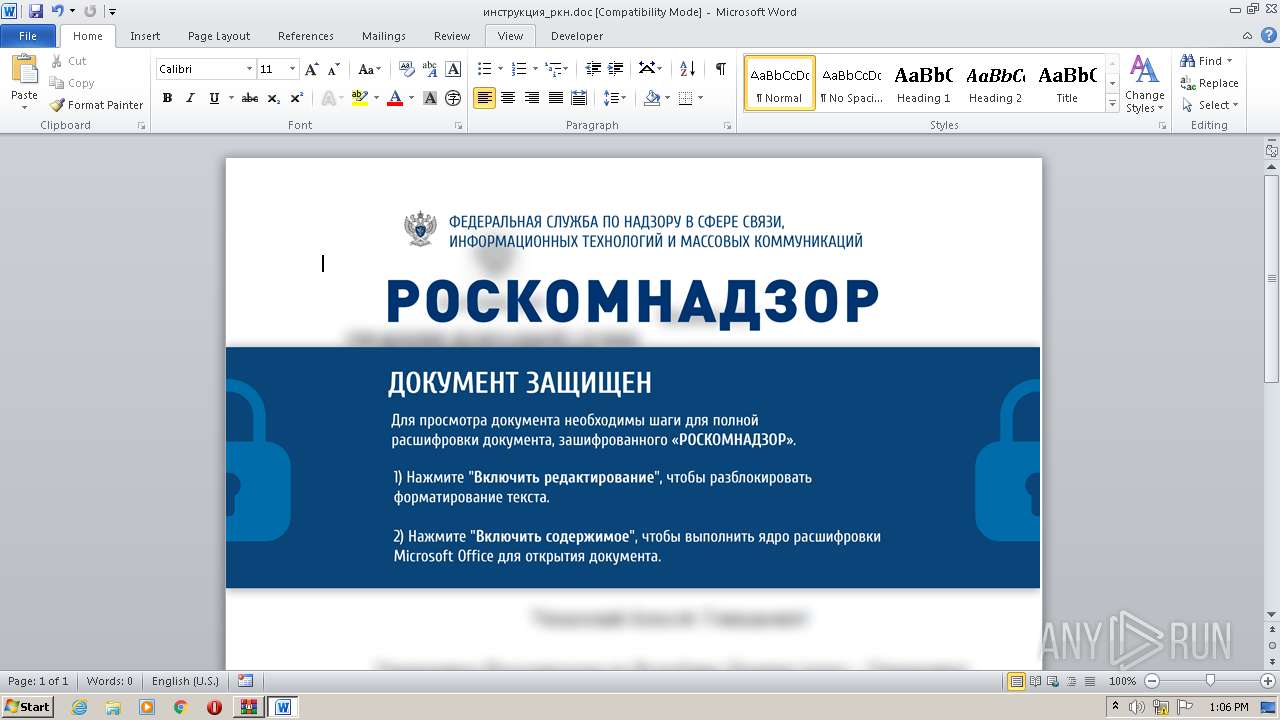
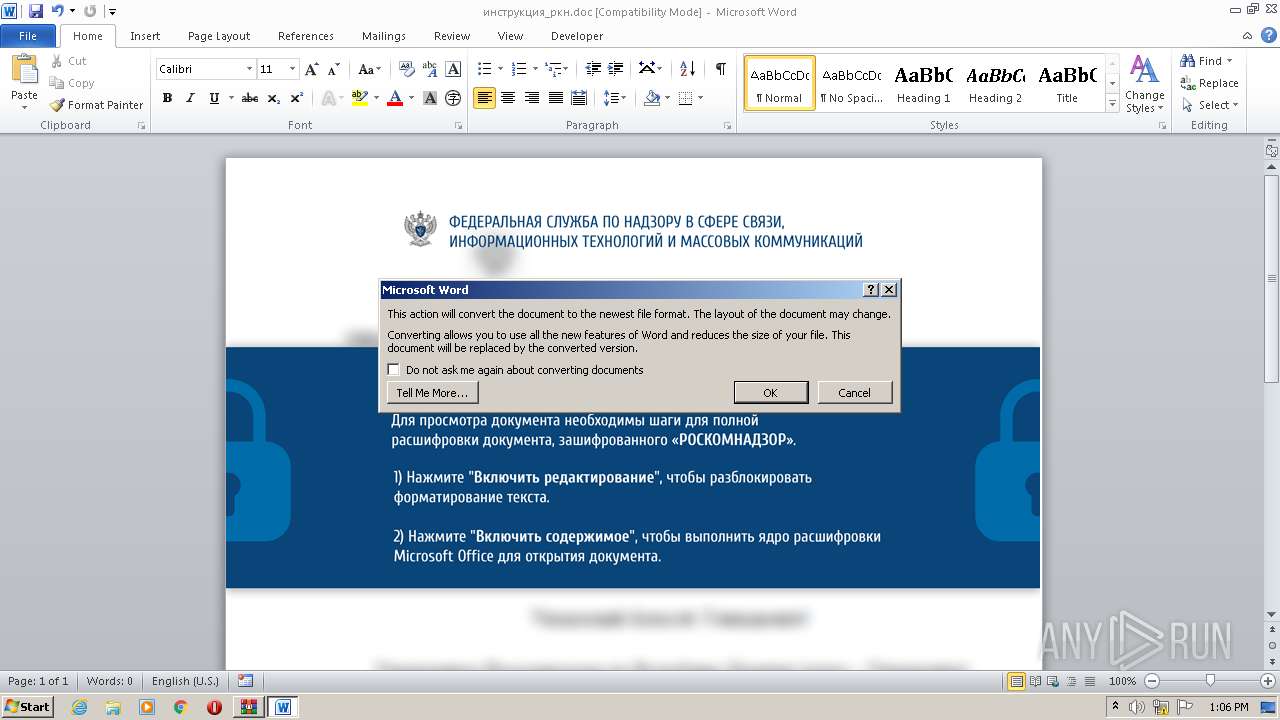
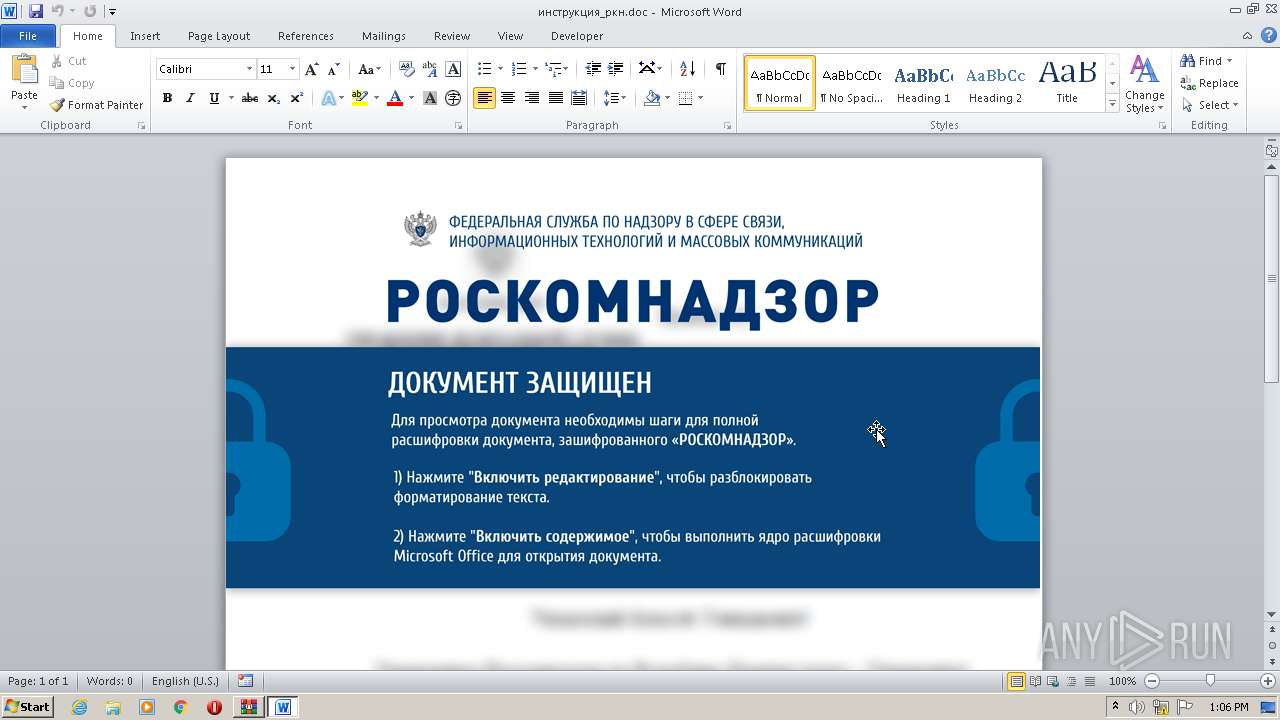
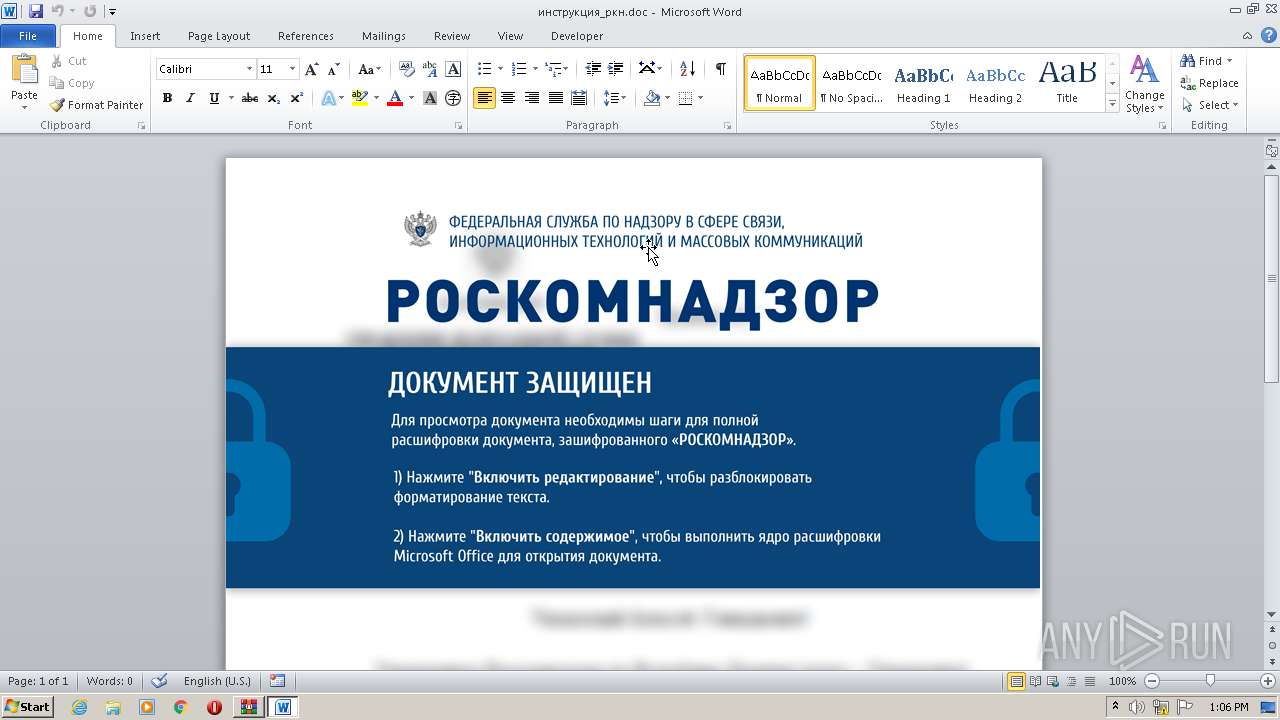
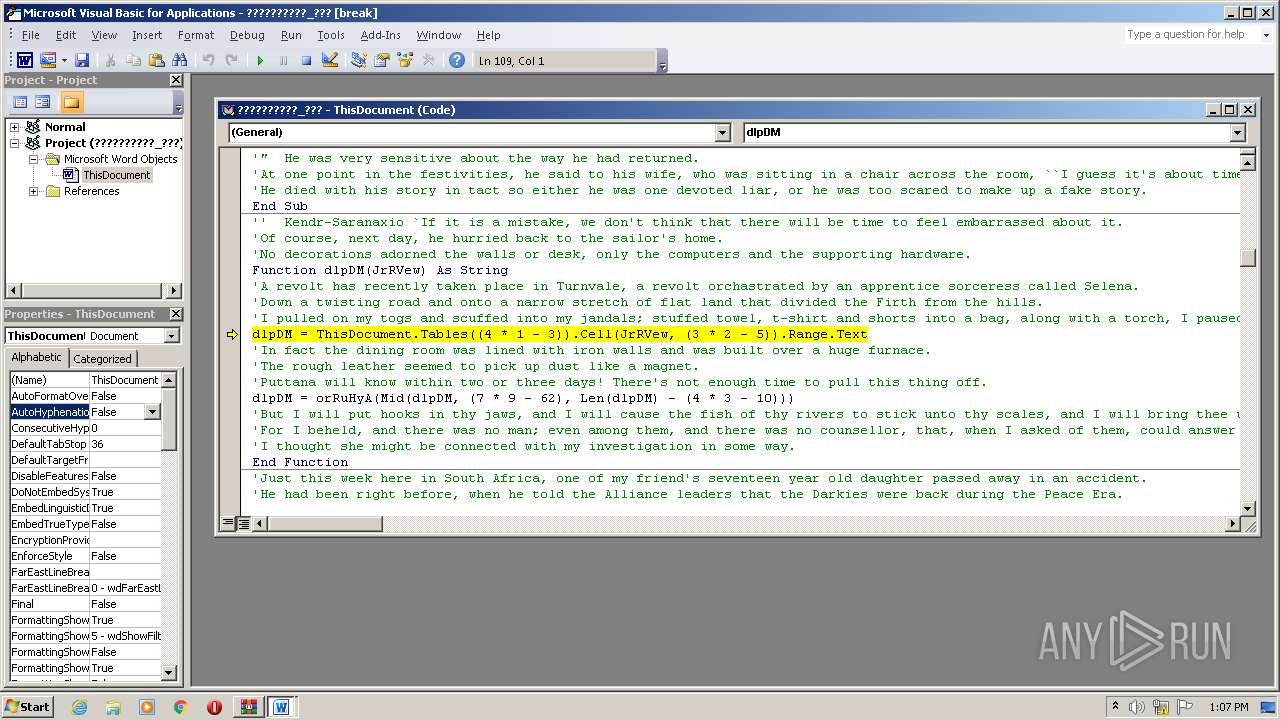
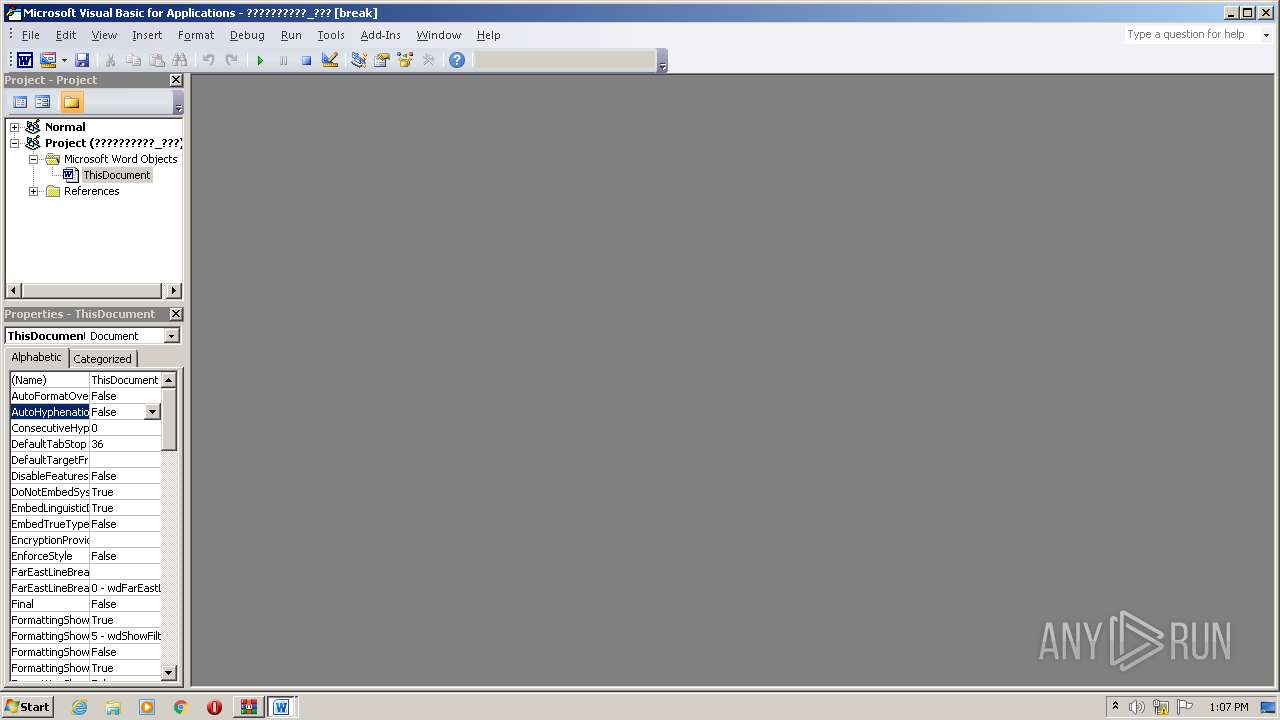
Microsoft Office executes commands via PowerShell or Cmd
- WINWORD.EXE (PID: 3956)
Unusual execution from MS Office
- WINWORD.EXE (PID: 3956)
Bypass execution policy to execute commands
- powershell.exe (PID: 1964)
Run PowerShell with an invisible window
- powershell.exe (PID: 1964)
Starts POWERSHELL.EXE for commands execution
- WINWORD.EXE (PID: 3956)
SUSPICIOUS
The process hide an interactive prompt from the user
- WINWORD.EXE (PID: 3956)
Reads the Internet Settings
- powershell.exe (PID: 1964)
The process executes Powershell scripts
- WINWORD.EXE (PID: 3956)
Unusual connection from system programs
- powershell.exe (PID: 1964)
The process hides Powershell's copyright startup banner
- WINWORD.EXE (PID: 3956)
INFO
Create files in a temporary directory
- powershell.exe (PID: 1964)
Manual execution by a user
- WINWORD.EXE (PID: 3956)
- WINWORD.EXE (PID: 2096)
Reads security settings of Internet Explorer
- powershell.exe (PID: 1964)
The process uses the downloaded file
- WINWORD.EXE (PID: 3956)
The process checks LSA protection
- powershell.exe (PID: 1964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
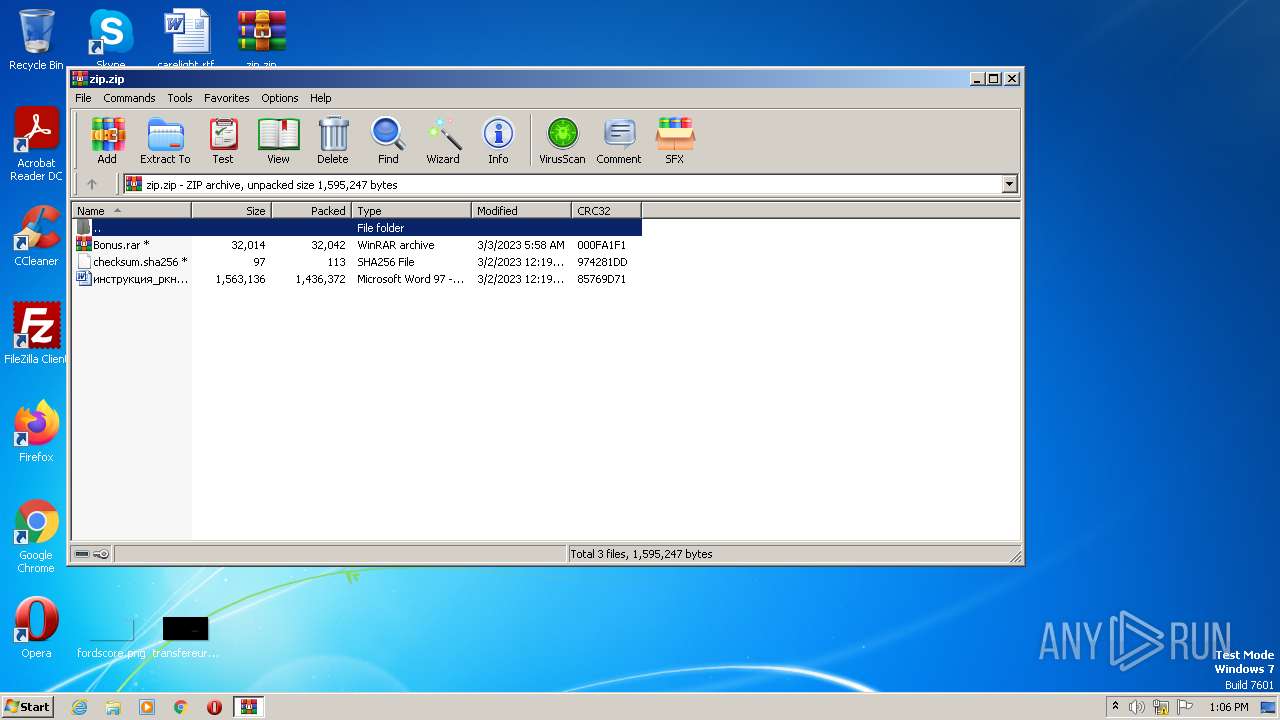
| ZipFileName: | - |
|---|---|
| ZipUncompressedSize: | 1563136 |
| ZipCompressedSize: | 1436372 |
| ZipCRC: | 0x85769d71 |
| ZipModifyDate: | 2023:03:02 12:19:00 |
| ZipCompression: | Unknown (99) |
| ZipBitFlag: | 0x0809 |
| ZipRequiredVersion: | 20 |
Total processes
44
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1964 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ex bypass -NoLogo -WindowStyle Hidden -NonInteractive -f c:\users\admin\appdata\roaming\microsoft\templates\HkvWahS6osjcp1g.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
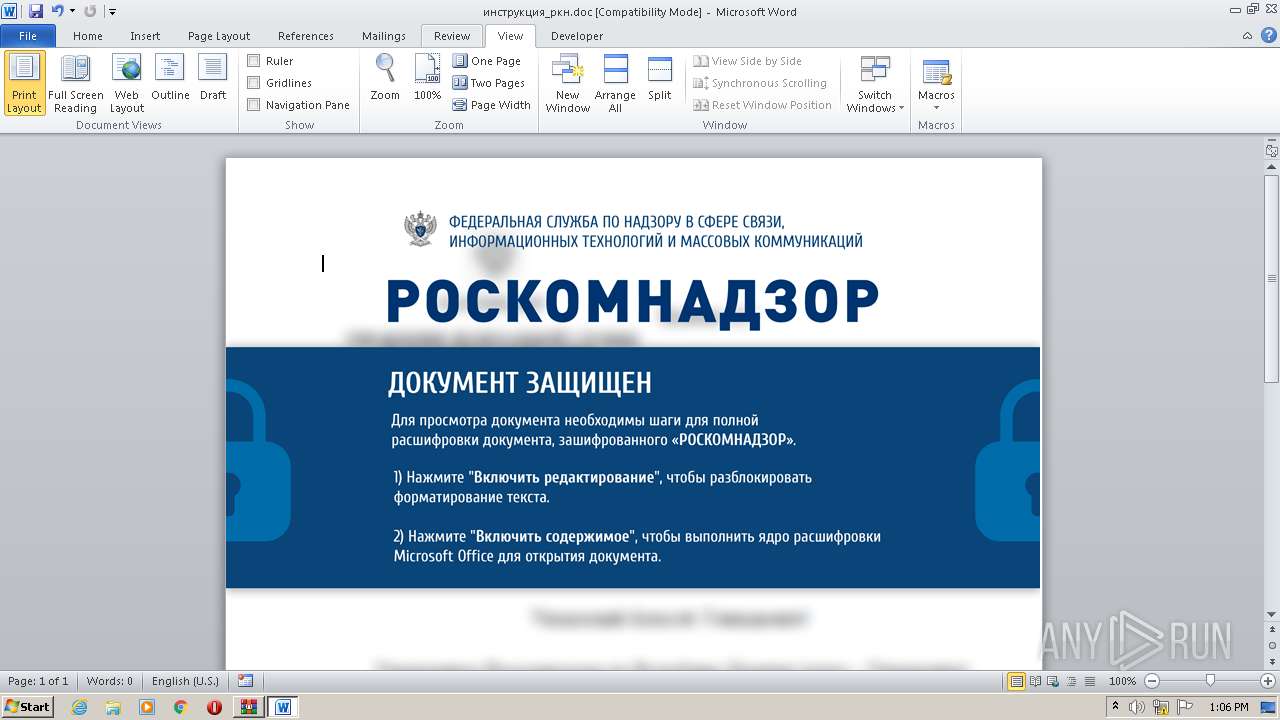
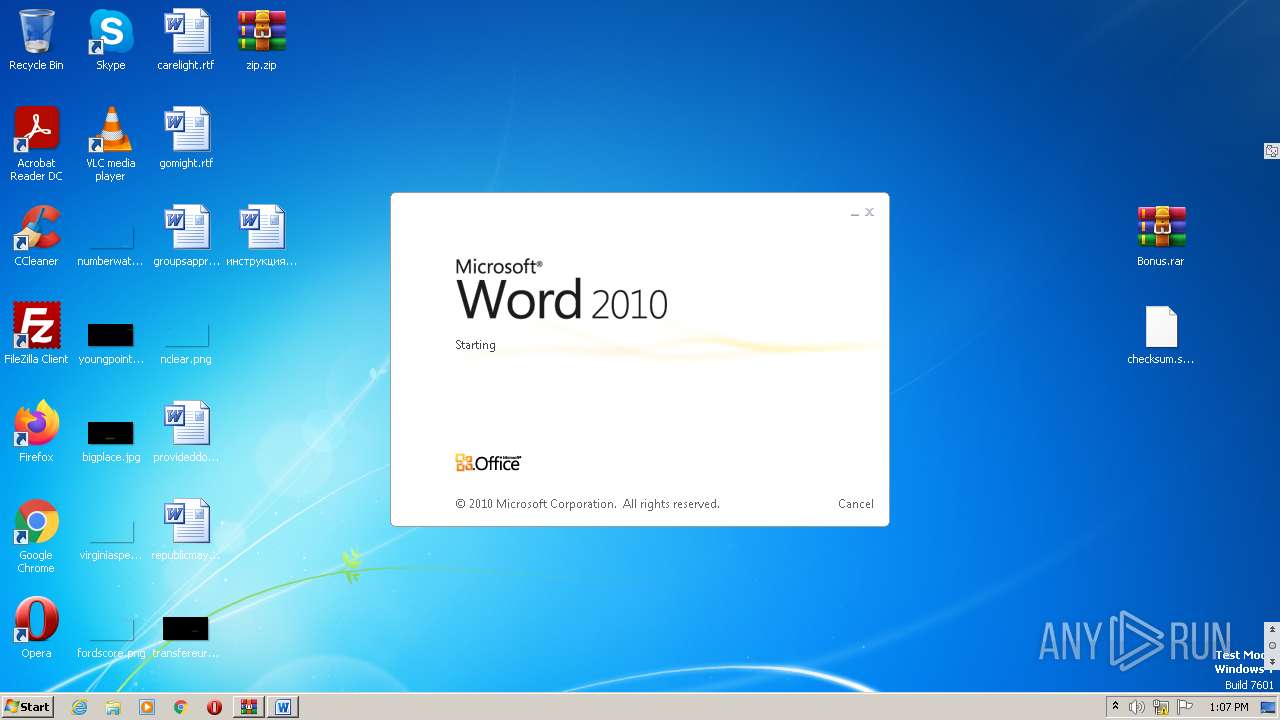
| 2096 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\инструкция_ркн.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\zip.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3956 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\инструкция_ркн.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
16 416
Read events
15 184
Write events
718
Delete events
514
Modification events
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
Executable files
0
Suspicious files
32
Text files
12
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3544.tmp.cvr | — | |
MD5:— | SHA256:— | |||
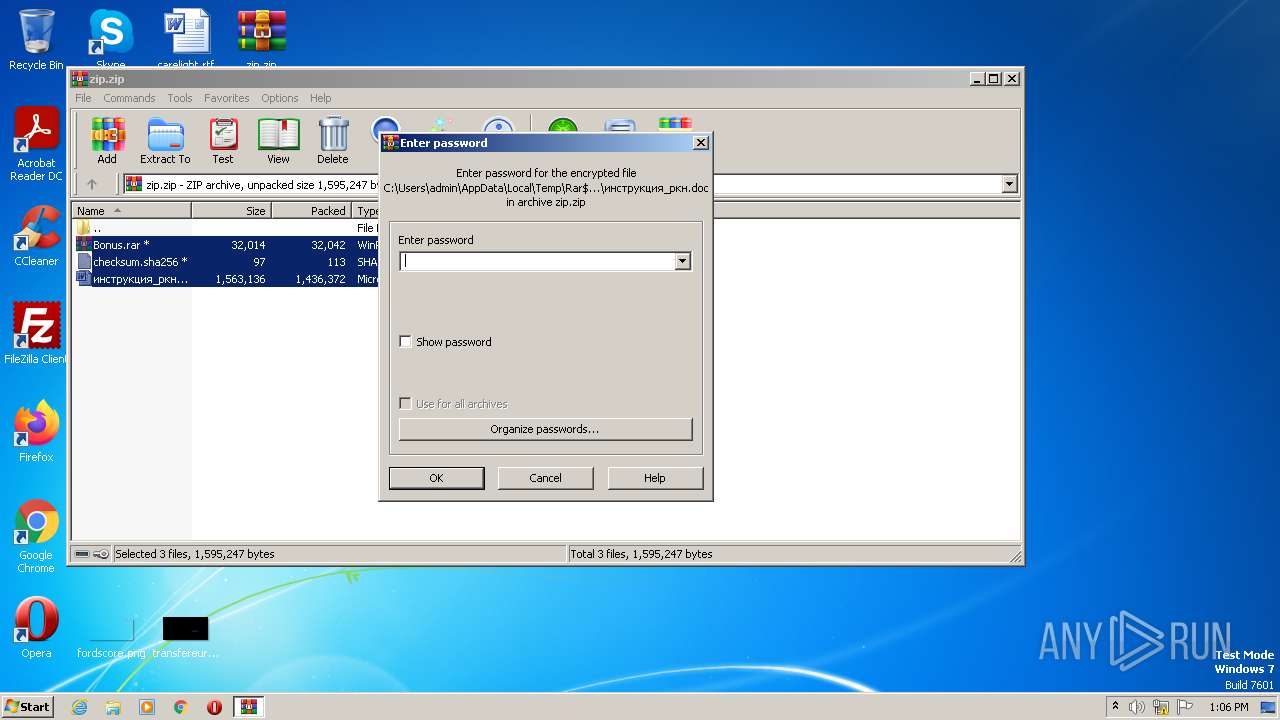
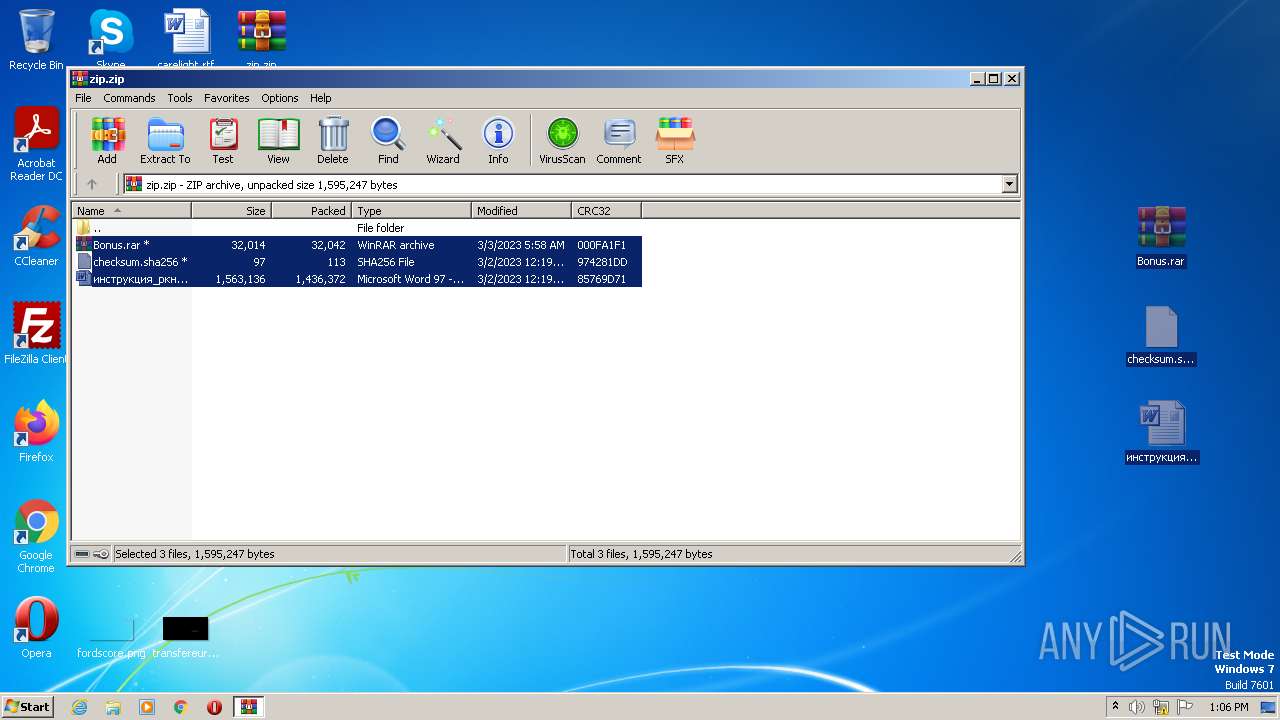
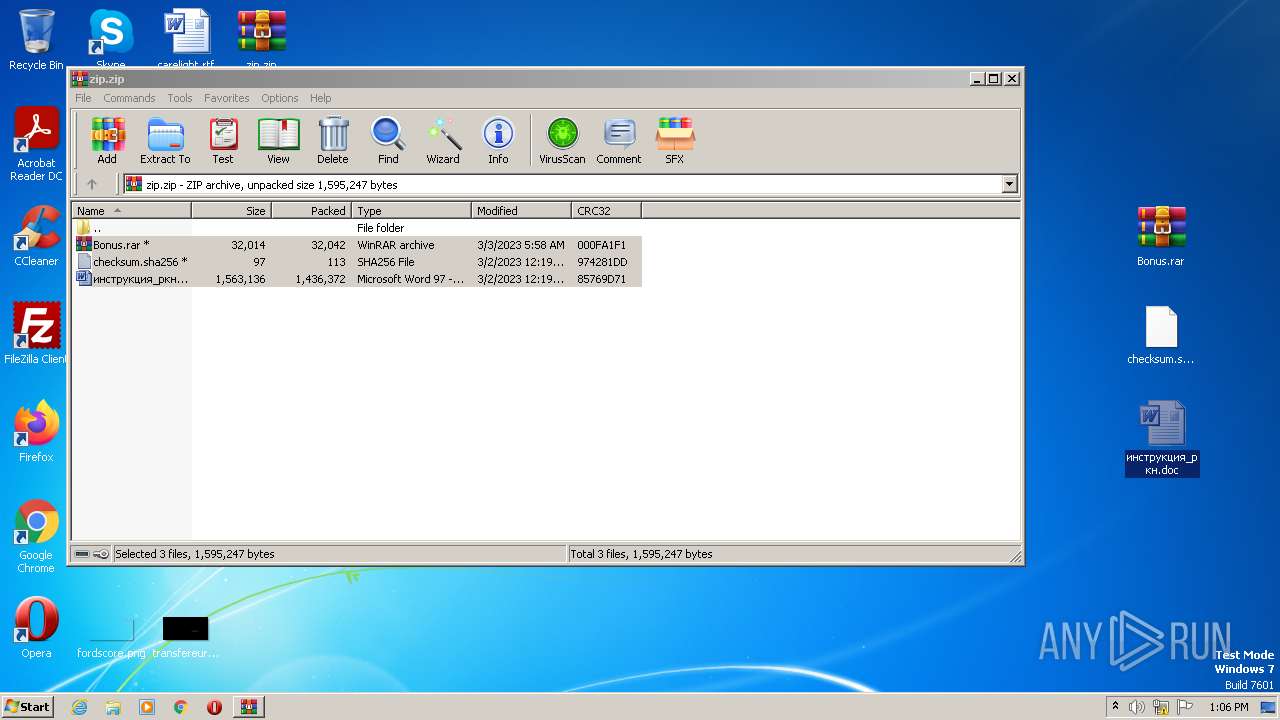
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2644.25535\инструкция_ркн.doc | document | |
MD5:— | SHA256:— | |||
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3956 | WINWORD.EXE | C:\Users\admin\Desktop\~$струкция_ркн.doc | pgc | |
MD5:— | SHA256:— | |||
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\9sIAWssbW73TcYG.W4x9LosInhvOjtI | text | |
MD5:— | SHA256:— | |||
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\HkvWahS6osjcp1g.ps1 | text | |
MD5:— | SHA256:— | |||
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\инструкция_ркн.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2644.25535\checksum.sha256 | text | |
MD5:— | SHA256:— | |||
| 2644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2644.25535\Bonus.rar | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
58
DNS requests
1
Threats
60
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 99.83.154.118:443 | swordoke.com | AMAZON-02 | US | malicious |
1964 | powershell.exe | 99.83.154.118:443 | swordoke.com | AMAZON-02 | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
swordoke.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Domain Observed Used for C2 Detected | ET MALWARE Win32/Backdoor Related Domain in DNS Lookup (swordoke .com) |
1964 | powershell.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Backdoor Related Domain (swordoke .com in TLS SNI) |
1964 | powershell.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Backdoor Related Domain (swordoke .com in TLS SNI) |
1964 | powershell.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Backdoor Related Domain (swordoke .com in TLS SNI) |
1964 | powershell.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Backdoor Related Domain (swordoke .com in TLS SNI) |
1964 | powershell.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Backdoor Related Domain (swordoke .com in TLS SNI) |
1964 | powershell.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Backdoor Related Domain (swordoke .com in TLS SNI) |
1964 | powershell.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Backdoor Related Domain (swordoke .com in TLS SNI) |
1964 | powershell.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Backdoor Related Domain (swordoke .com in TLS SNI) |
1964 | powershell.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Backdoor Related Domain (swordoke .com in TLS SNI) |