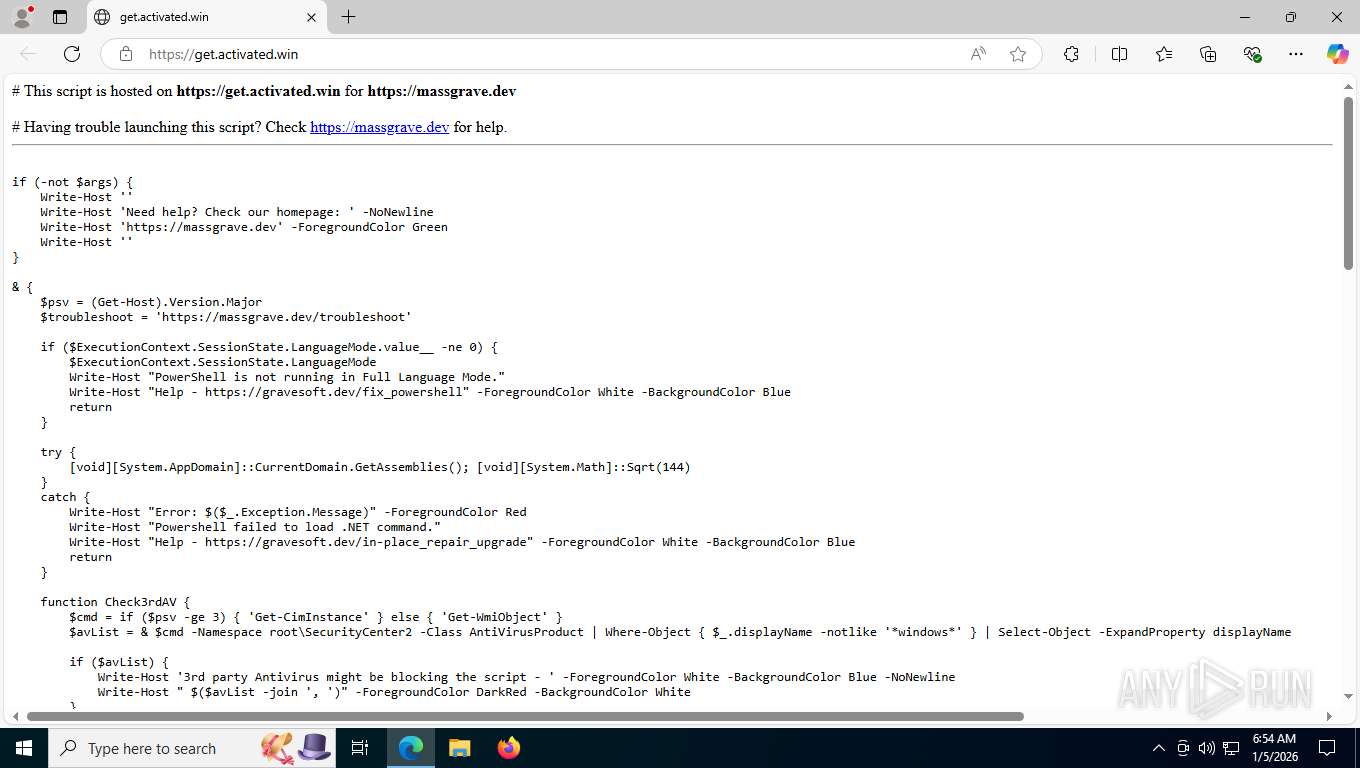
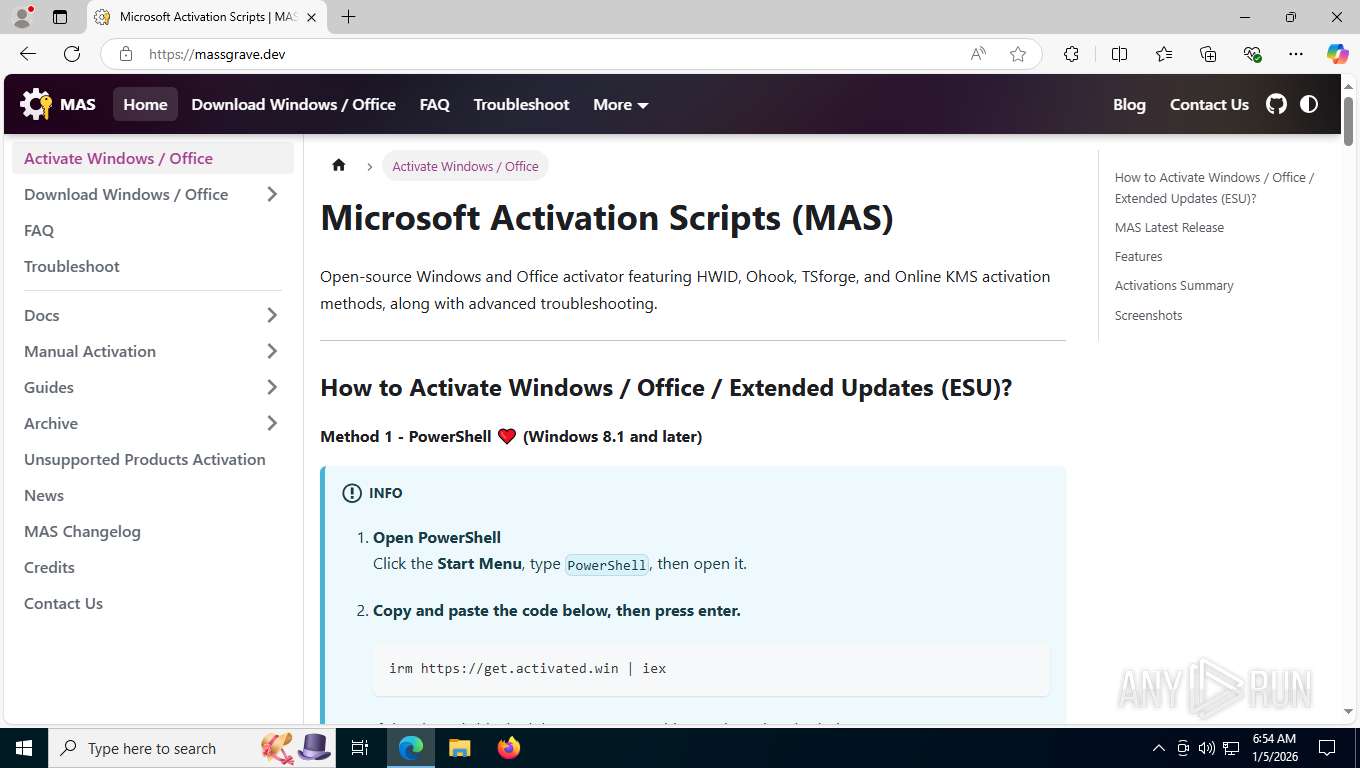
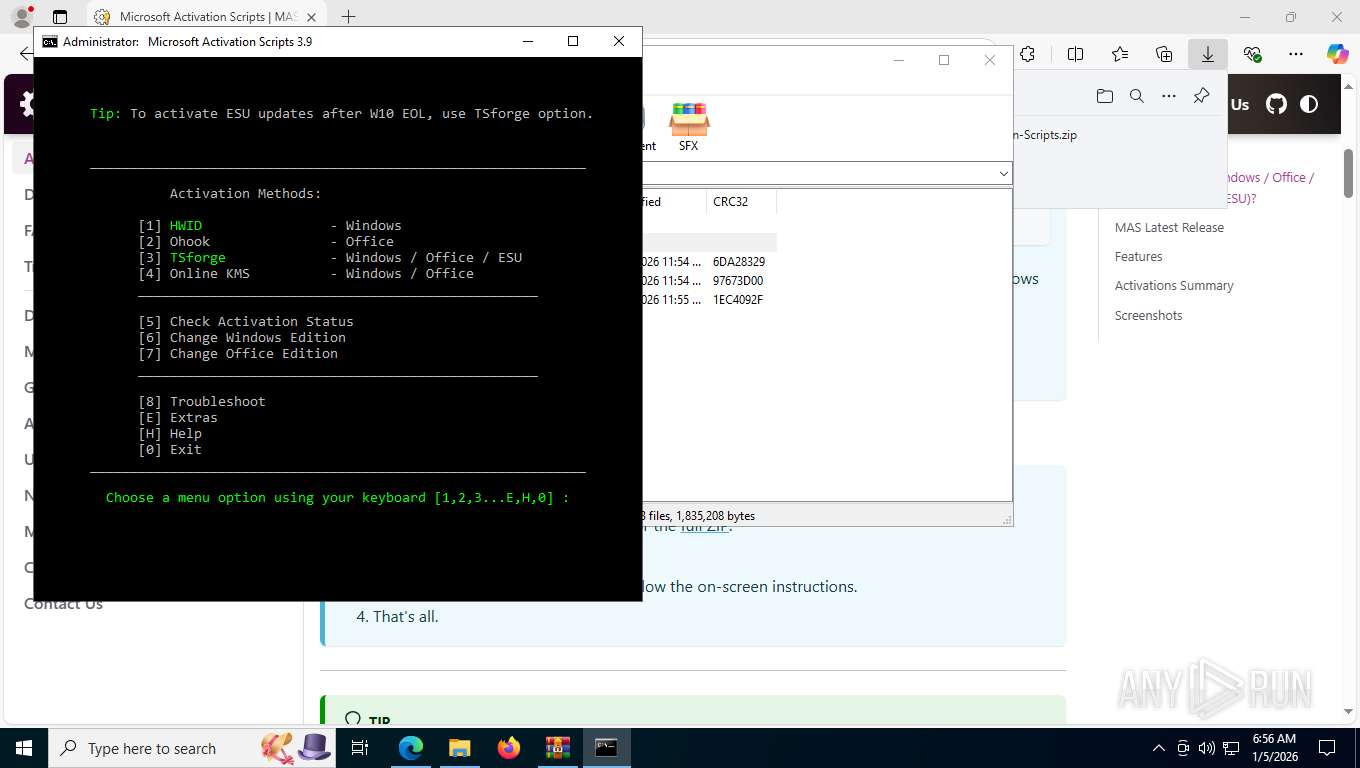
| URL: | https://get.activated.win/ |
| Full analysis: | https://app.any.run/tasks/5d3d7ea2-ee63-4e24-979c-817f103eff8e |
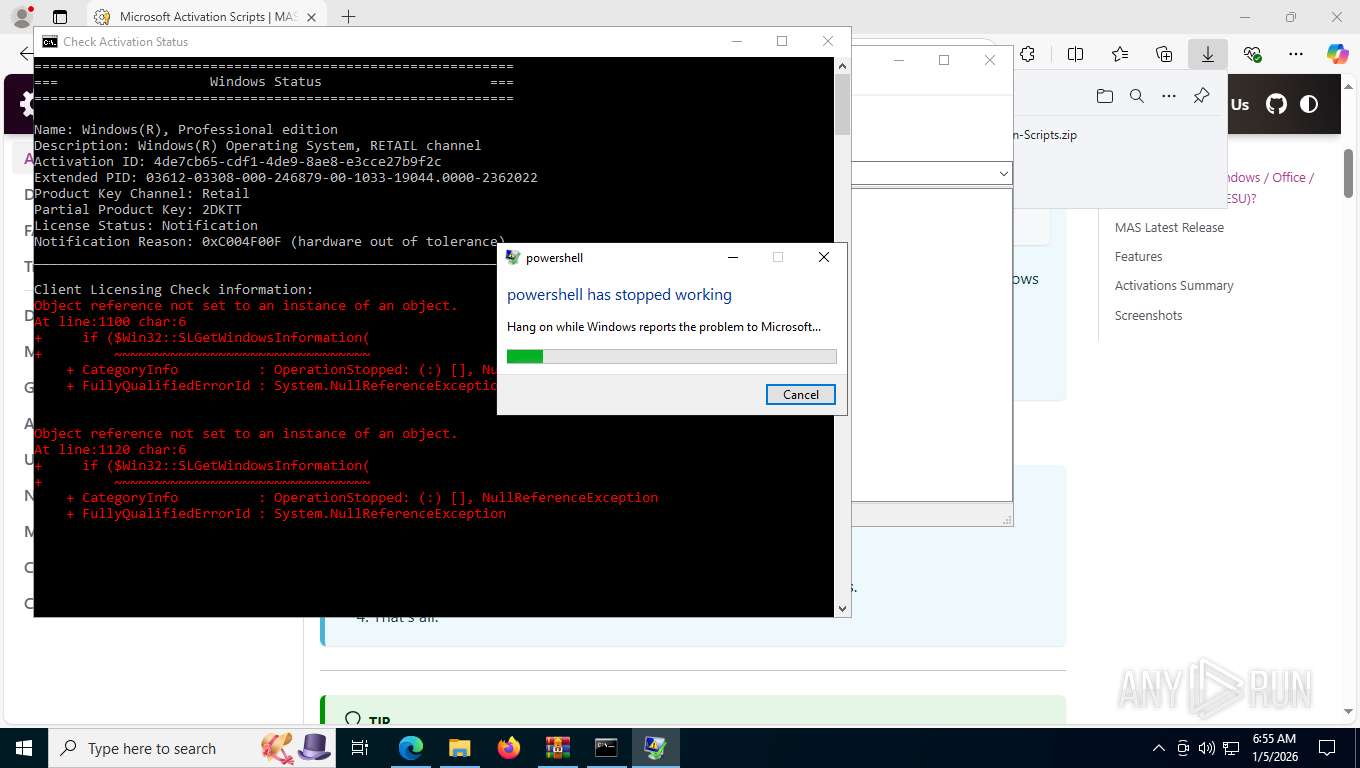
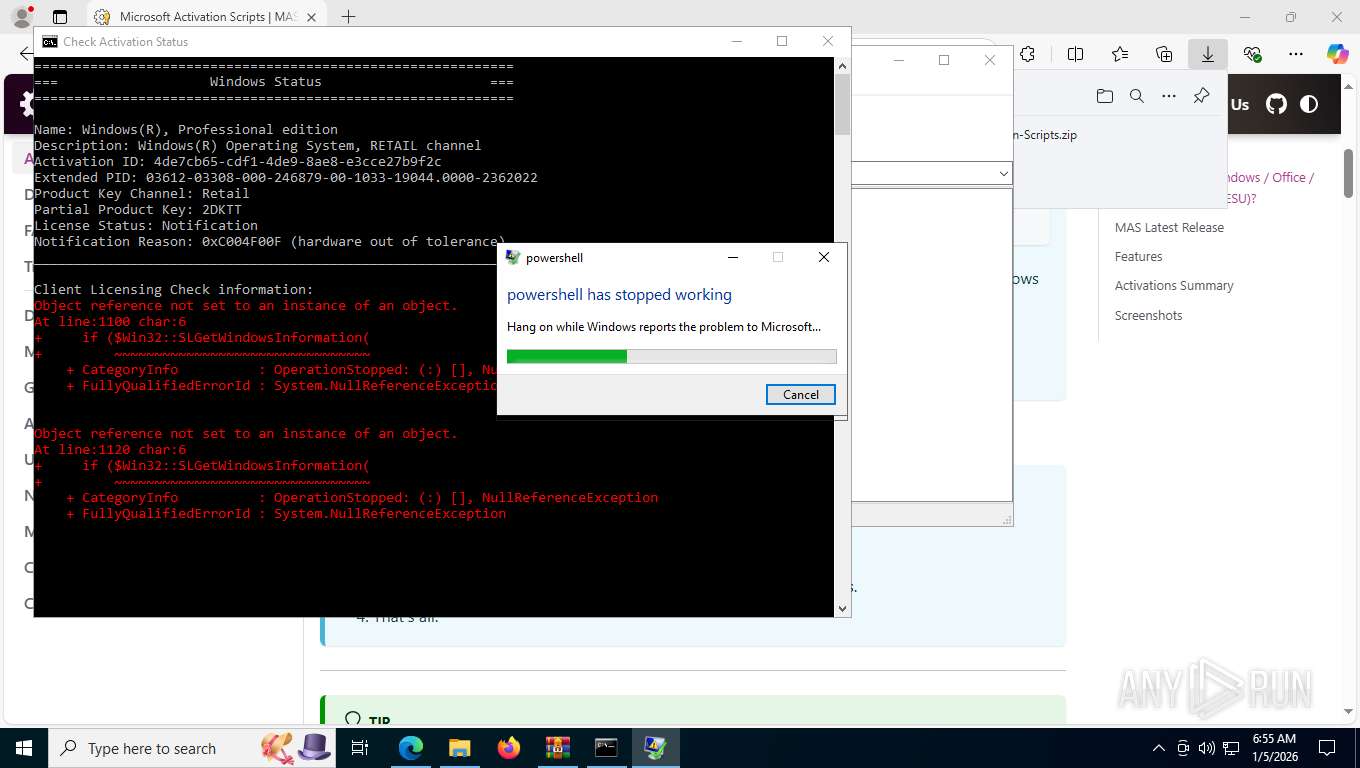
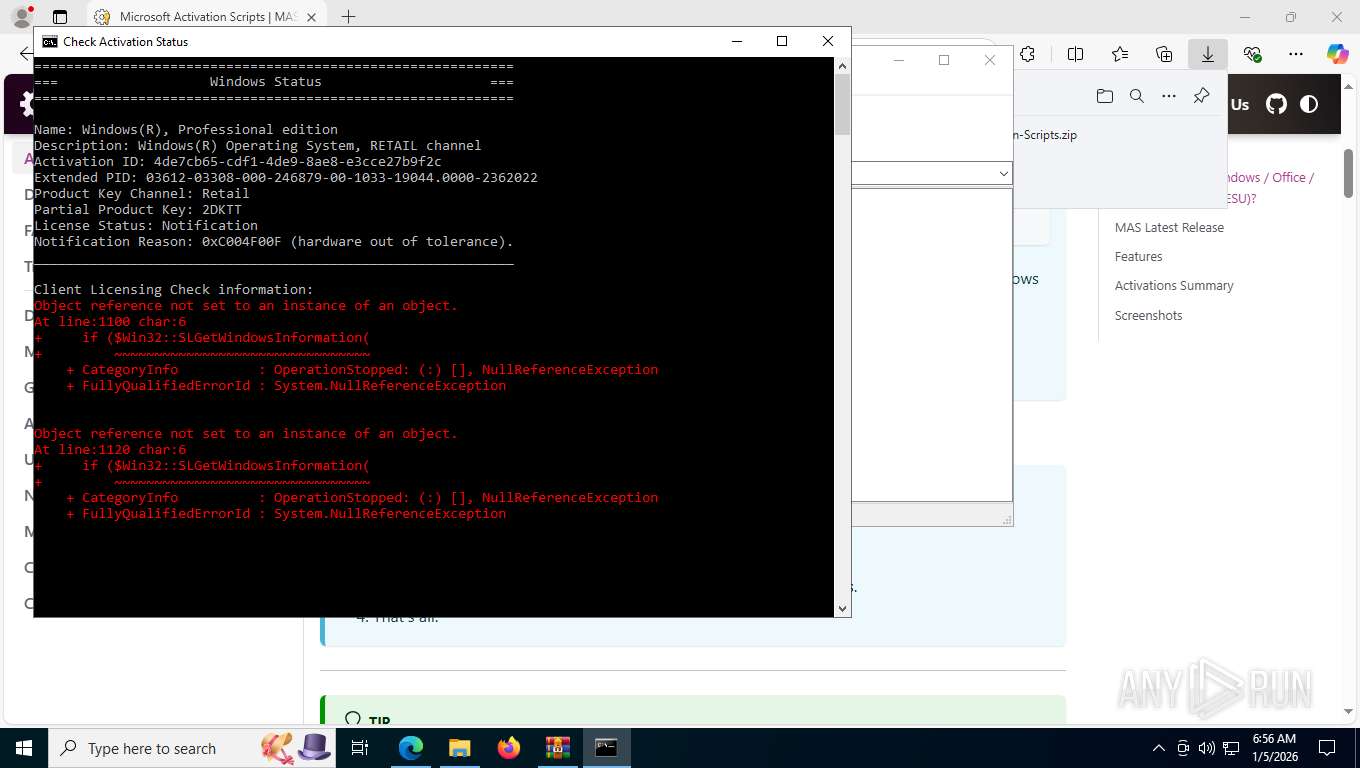
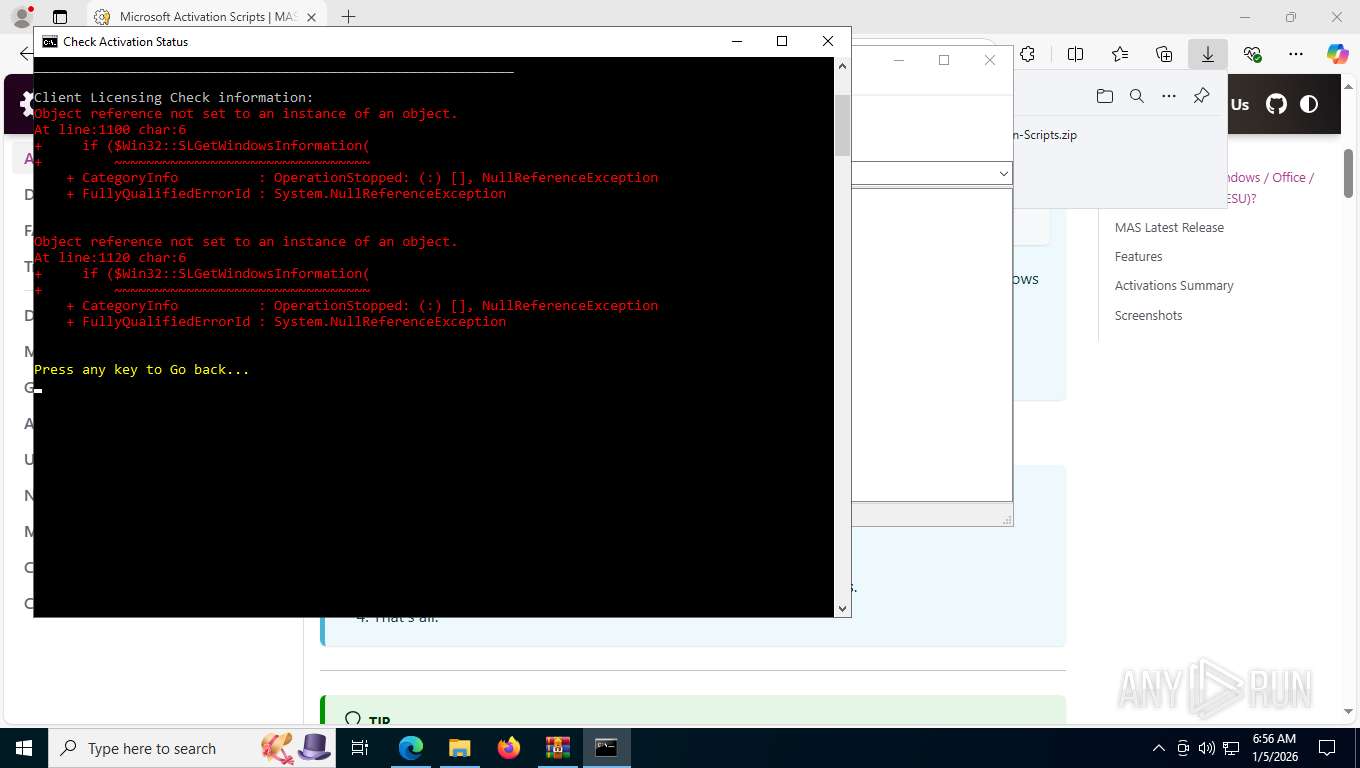
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2026, 11:54:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B1F8CA0B0615F4F5C94BCE2C1C7CA0B9 |
| SHA1: | AECABEC64ADC293026514AF34CD3872DFCC3F9BD |
| SHA256: | 83C654432A5089F2A7E339FEC4BABFBF040E4CA55A95B8A57ECE17FB23AC11D9 |
| SSDEEP: | 3:N8hsTE2mM+:2omR |
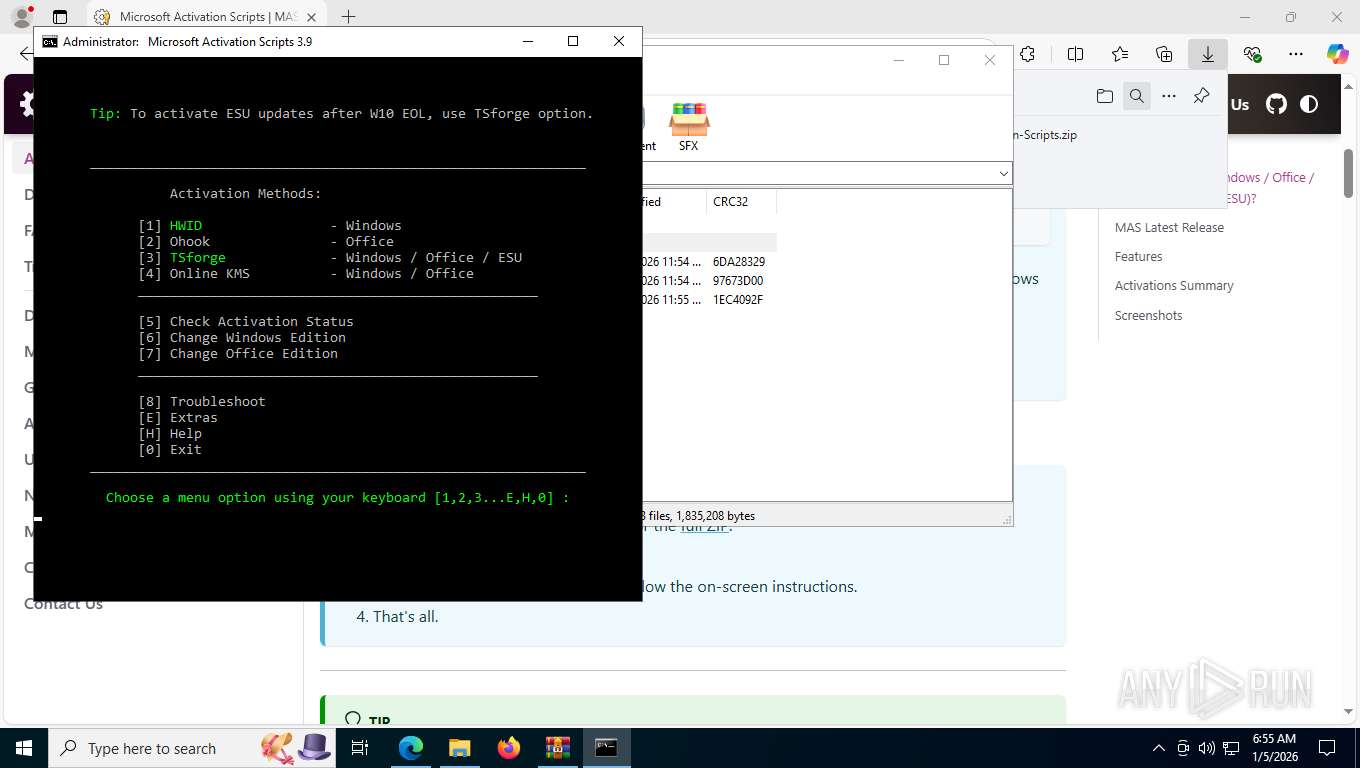
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts SC.EXE for service management
- cmd.exe (PID: 1172)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 1948)
Windows service management via SC.EXE
- sc.exe (PID: 4292)
- sc.exe (PID: 5436)
- sc.exe (PID: 3060)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1172)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 1948)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1172)
- powershell.exe (PID: 4292)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 5764)
- cmd.exe (PID: 1948)
- cmd.exe (PID: 6900)
Application launched itself
- cmd.exe (PID: 1172)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 5764)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 1948)
- cmd.exe (PID: 6900)
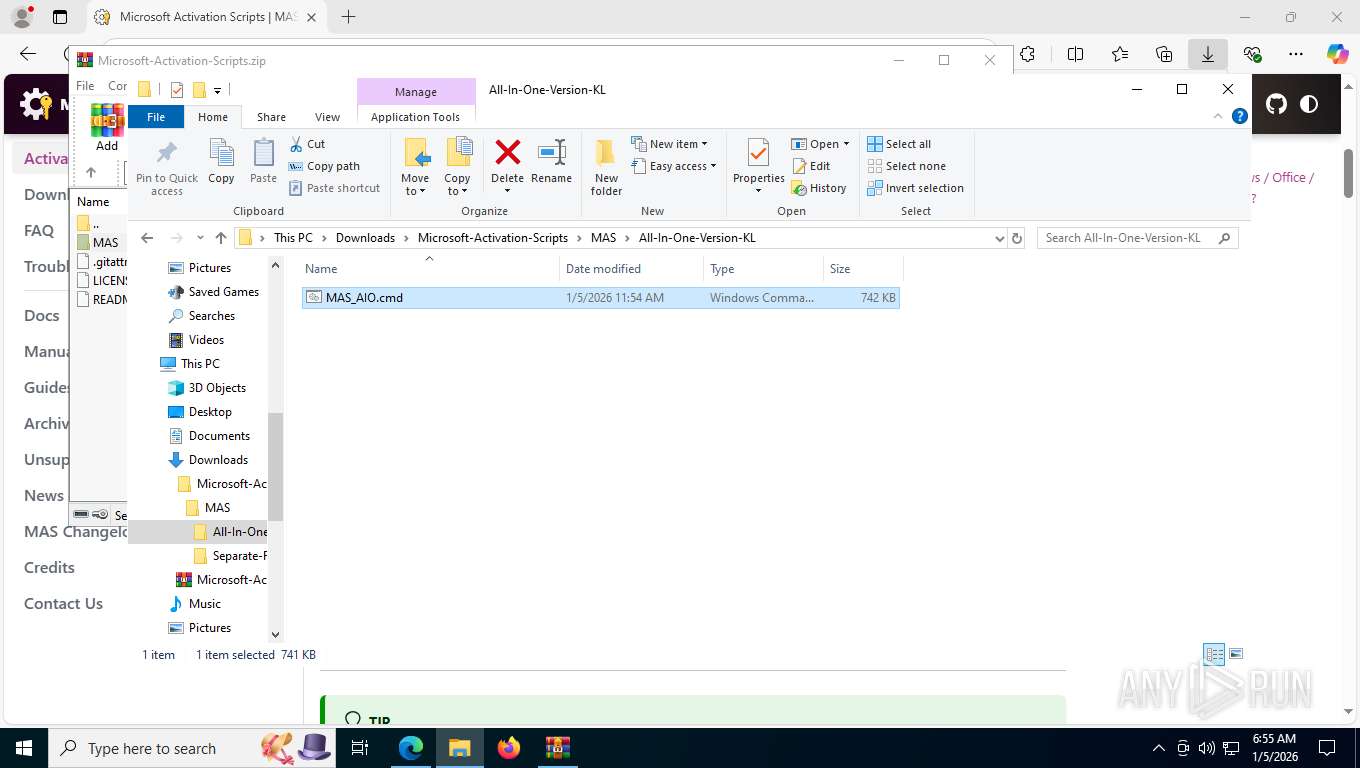
Executing commands from ".cmd" file
- cmd.exe (PID: 1172)
- powershell.exe (PID: 4292)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 1948)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1172)
- cmd.exe (PID: 2508)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 1948)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1172)
- cmd.exe (PID: 2508)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 1948)
Executes script without checking the security policy
- powershell.exe (PID: 4292)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 800)
- powershell.exe (PID: 1456)
Converts TXT file into a string
- powershell.exe (PID: 7388)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 1456)
Queries Computer System Information (Win32_ComputerSystem) (SCRIPT)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 1456)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 1456)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 1456)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 1456)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2252)
Hides command output
- cmd.exe (PID: 2508)
- cmd.exe (PID: 7920)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2508)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 1948)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 1456)
The process creates files with name similar to system file names
- wermgr.exe (PID: 5872)
INFO
Checks supported languages
- identity_helper.exe (PID: 7724)
- mode.com (PID: 7268)
- mode.com (PID: 6344)
- mode.com (PID: 7060)
- mode.com (PID: 3352)
- mode.com (PID: 2356)
Reads the computer name
- identity_helper.exe (PID: 7724)
Reads Environment values
- identity_helper.exe (PID: 7724)
Application launched itself
- msedge.exe (PID: 7768)
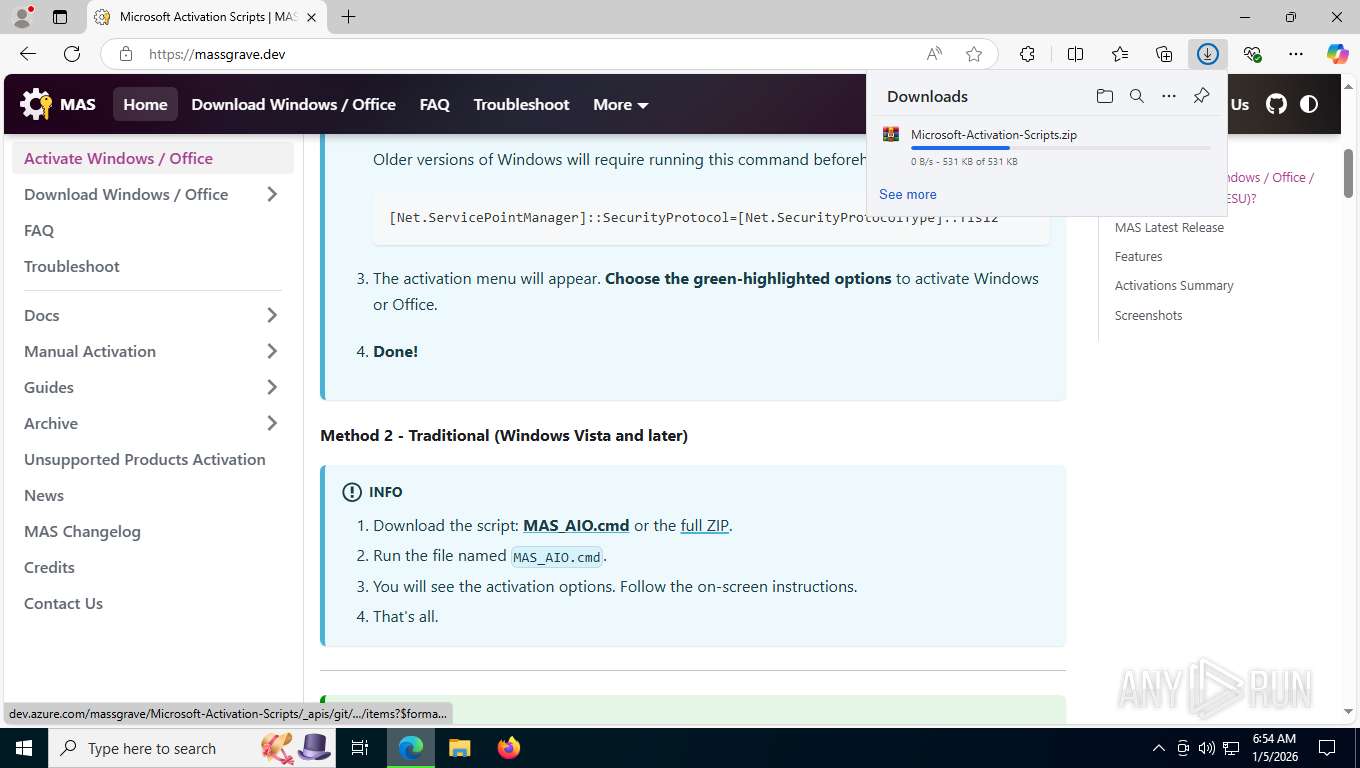
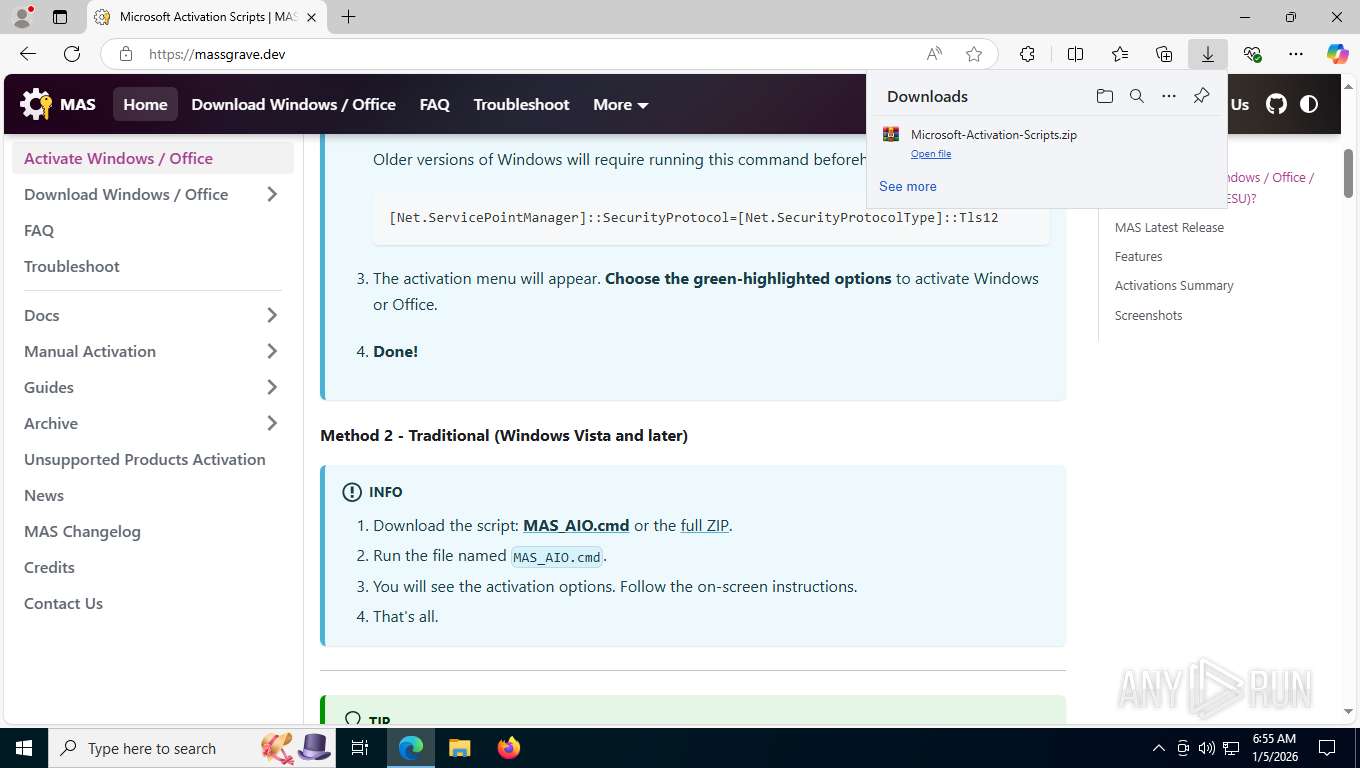
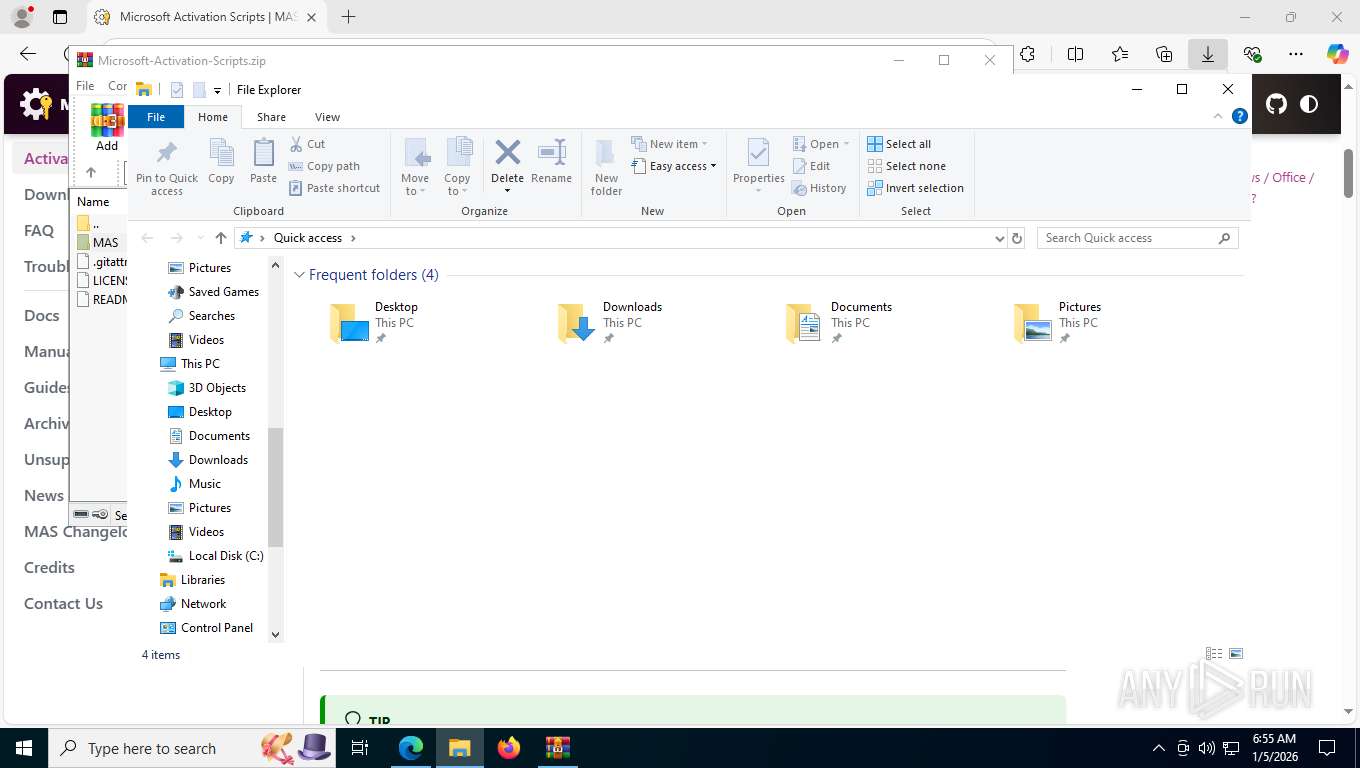
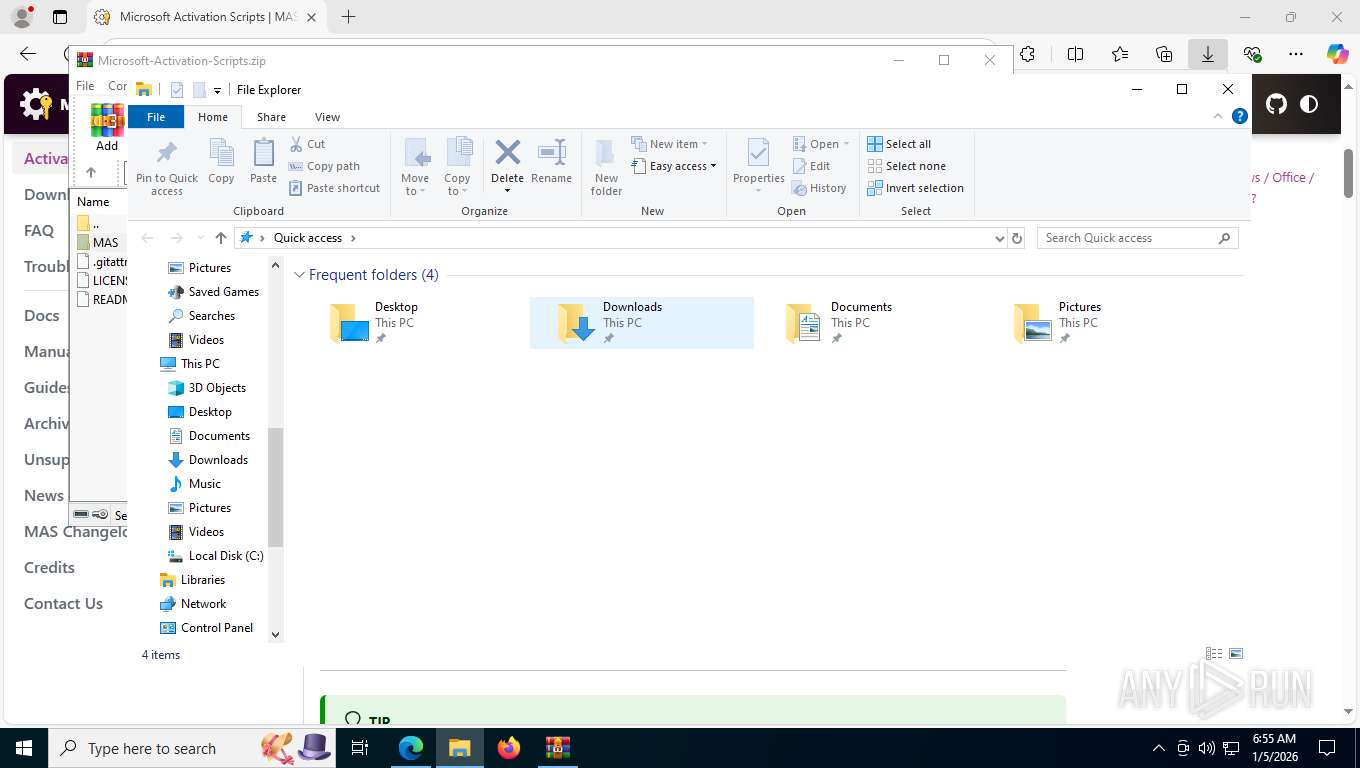
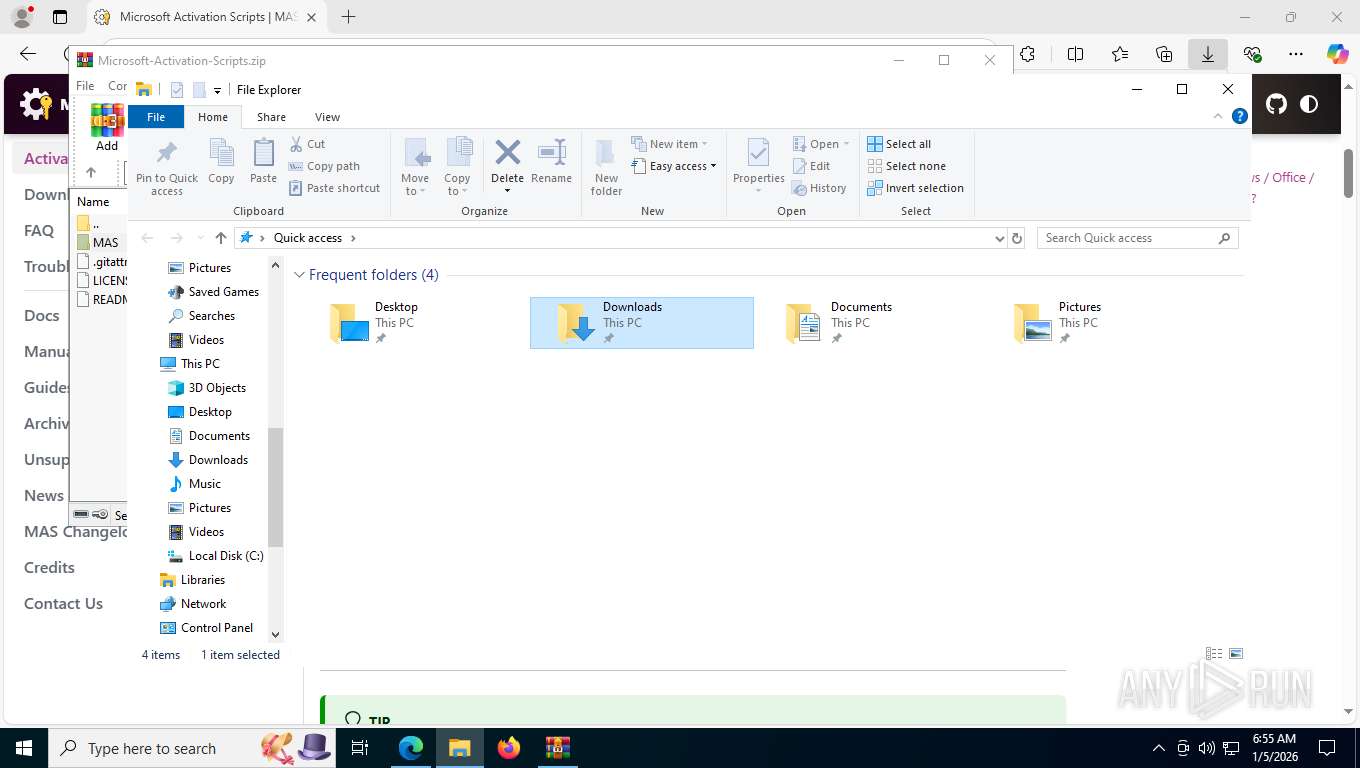
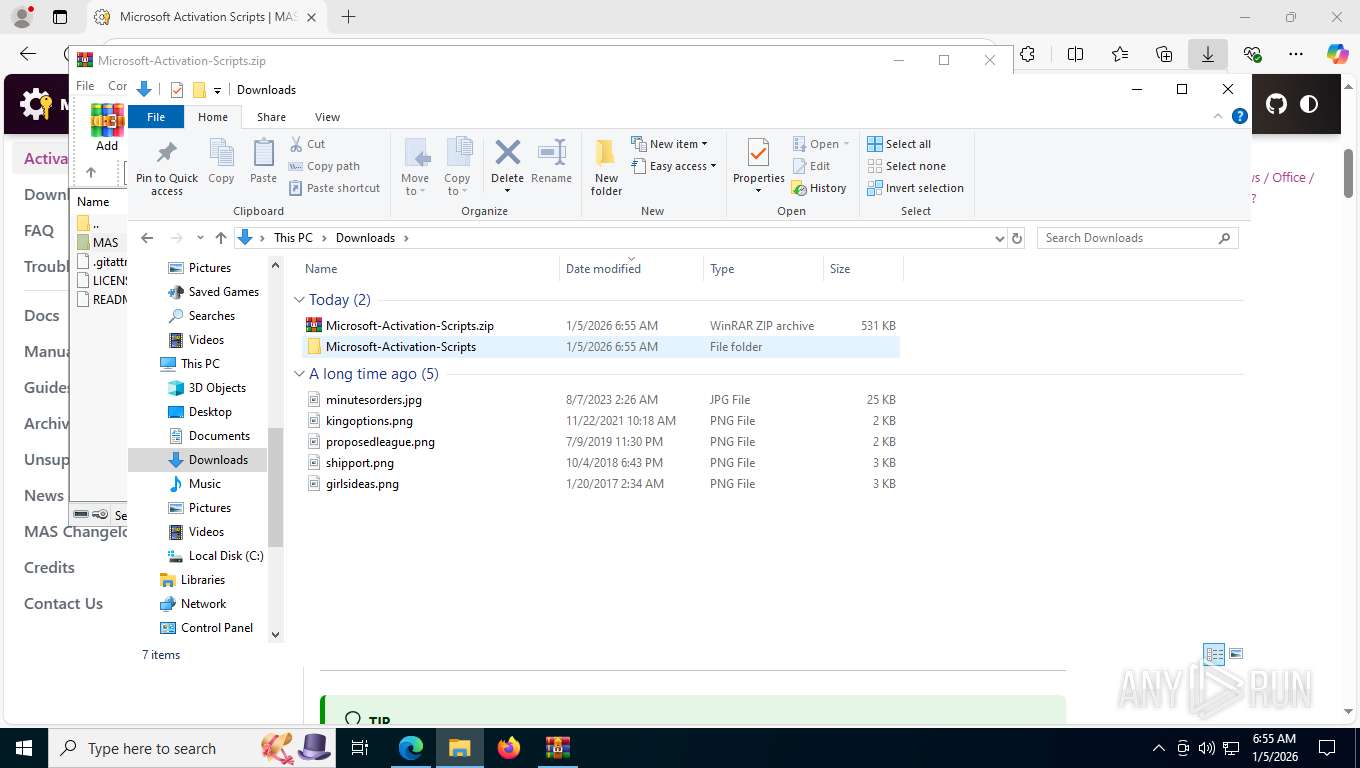
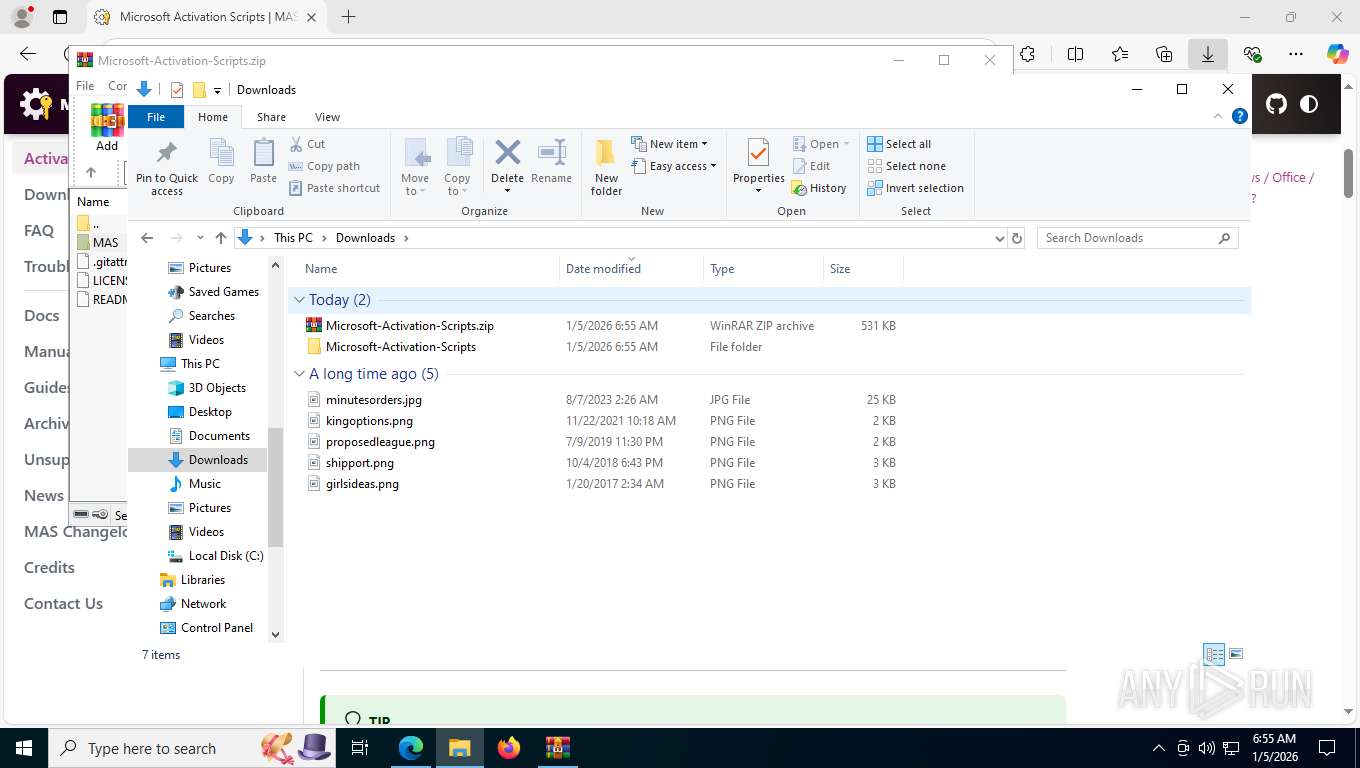
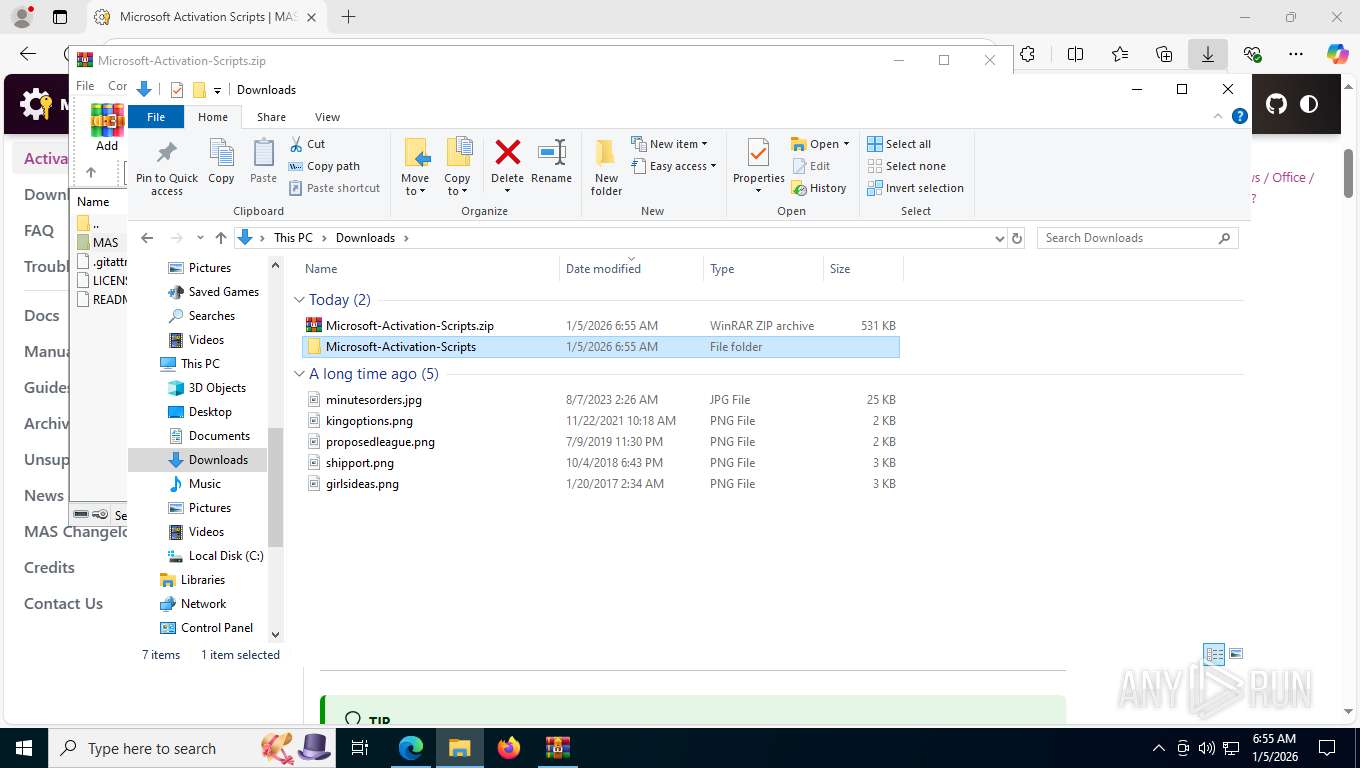
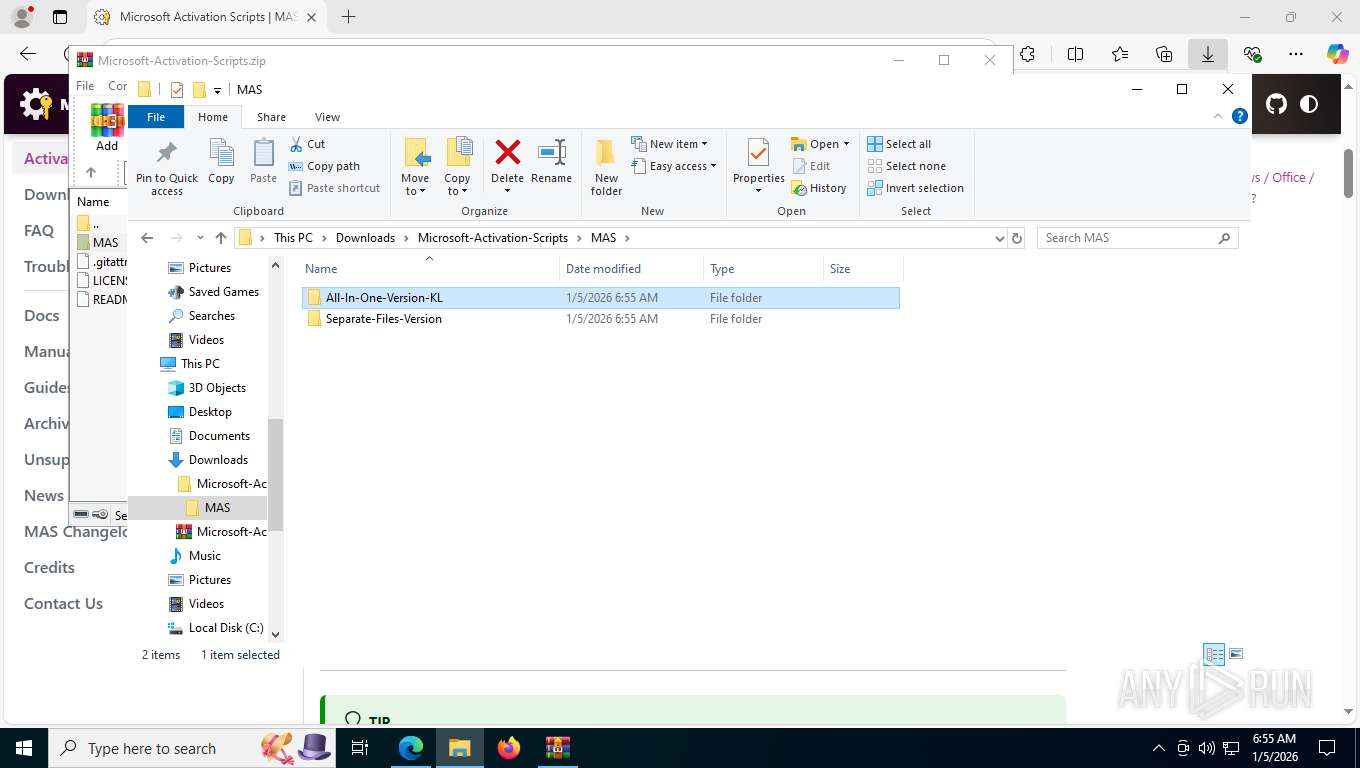
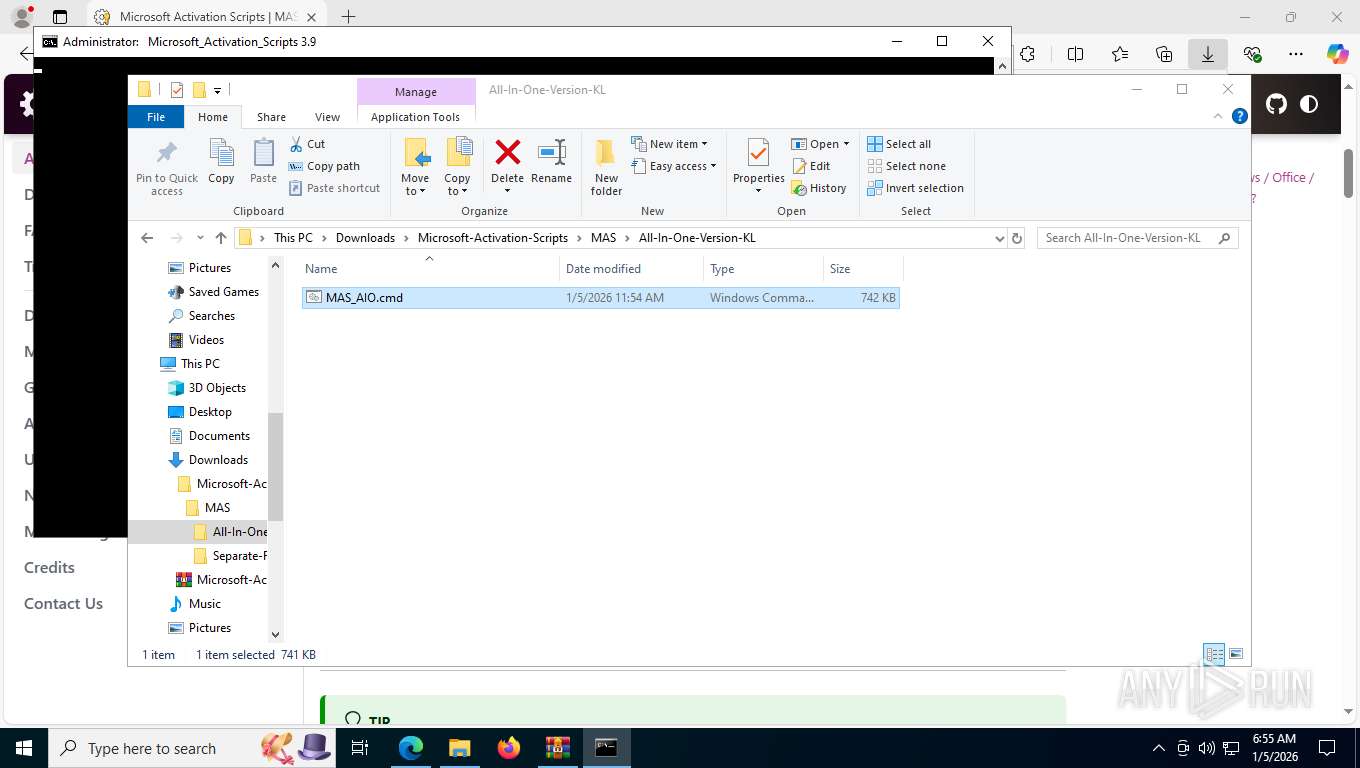
Launching a file from the Downloads directory
- msedge.exe (PID: 7768)
Manual execution by a user
- cmd.exe (PID: 1172)
Search a value from a registry key
- reg.exe (PID: 2140)
- reg.exe (PID: 5772)
- reg.exe (PID: 6852)
- reg.exe (PID: 7816)
- cmd.exe (PID: 5492)
- reg.exe (PID: 6440)
- reg.exe (PID: 4284)
- reg.exe (PID: 7492)
- reg.exe (PID: 5104)
- reg.exe (PID: 1112)
Checks operating system version
- cmd.exe (PID: 1172)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 1948)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 1456)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 1456)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 1456)
Starts MODE.COM to configure console settings
- mode.com (PID: 7268)
- mode.com (PID: 6344)
- mode.com (PID: 7060)
- mode.com (PID: 3352)
- mode.com (PID: 2356)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1456)
Creates files or folders in the user directory
- wermgr.exe (PID: 5872)
Creates files in the program directory
- powershell.exe (PID: 1456)
Checks proxy server information
- wermgr.exe (PID: 5872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
271
Monitored processes
125
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "-el -qedit" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 412 | find /i "O365" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 800 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "&{$W=$Host.UI.RawUI.WindowSize;$B=$Host.UI.RawUI.BufferSize;$W.Height=35;$B.Height=300;$Host.UI.RawUI.WindowSize=$W;$Host.UI.RawUI.BufferSize=$B;}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=16 --always-read-main-dll --field-trial-handle=7084,i,17267749398847214038,5166014067266207891,262144 --variations-seed-version --mojo-platform-channel-handle=6940 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1000 | findstr /v "f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "MAS_AIO.cmd" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1112 | reg query HKLM\SOFTWARE\Microsoft\Office\ClickToRun\Configuration /v ProductReleaseIds | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
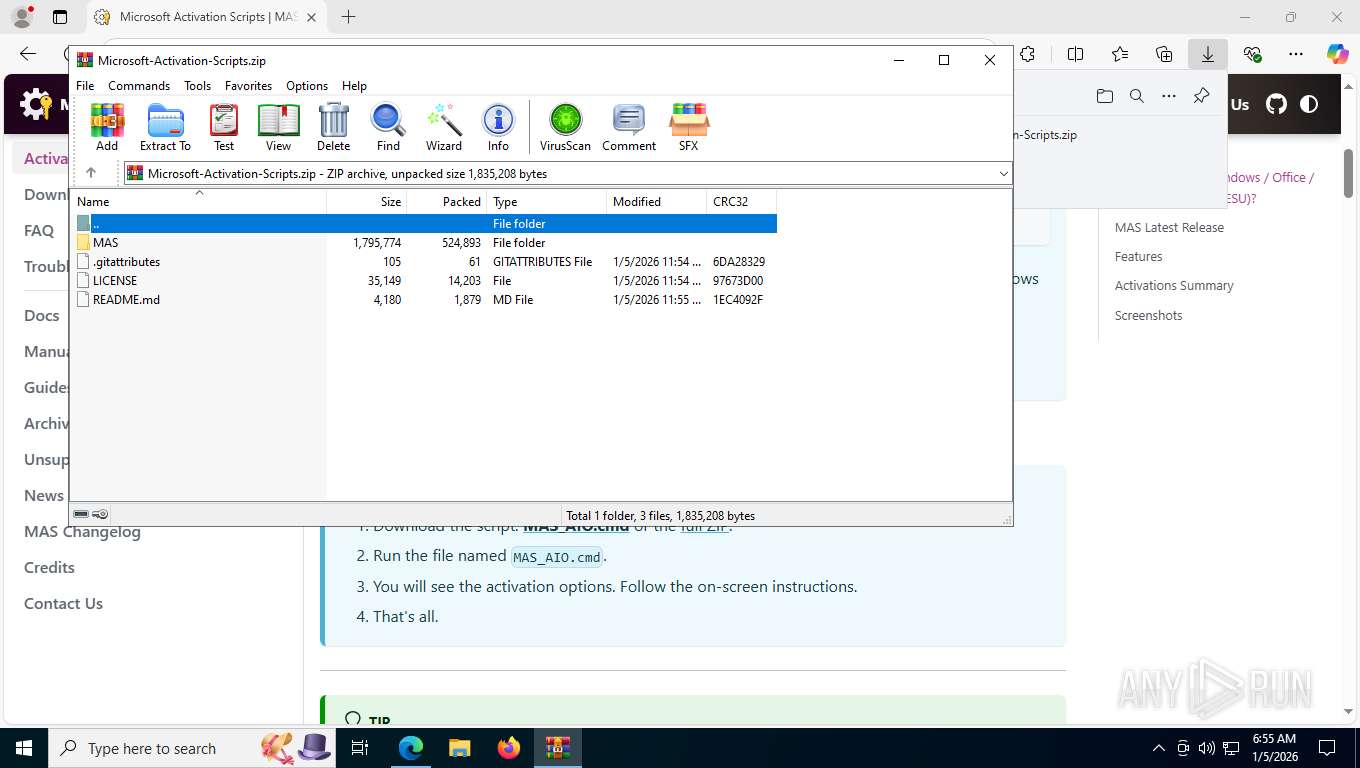
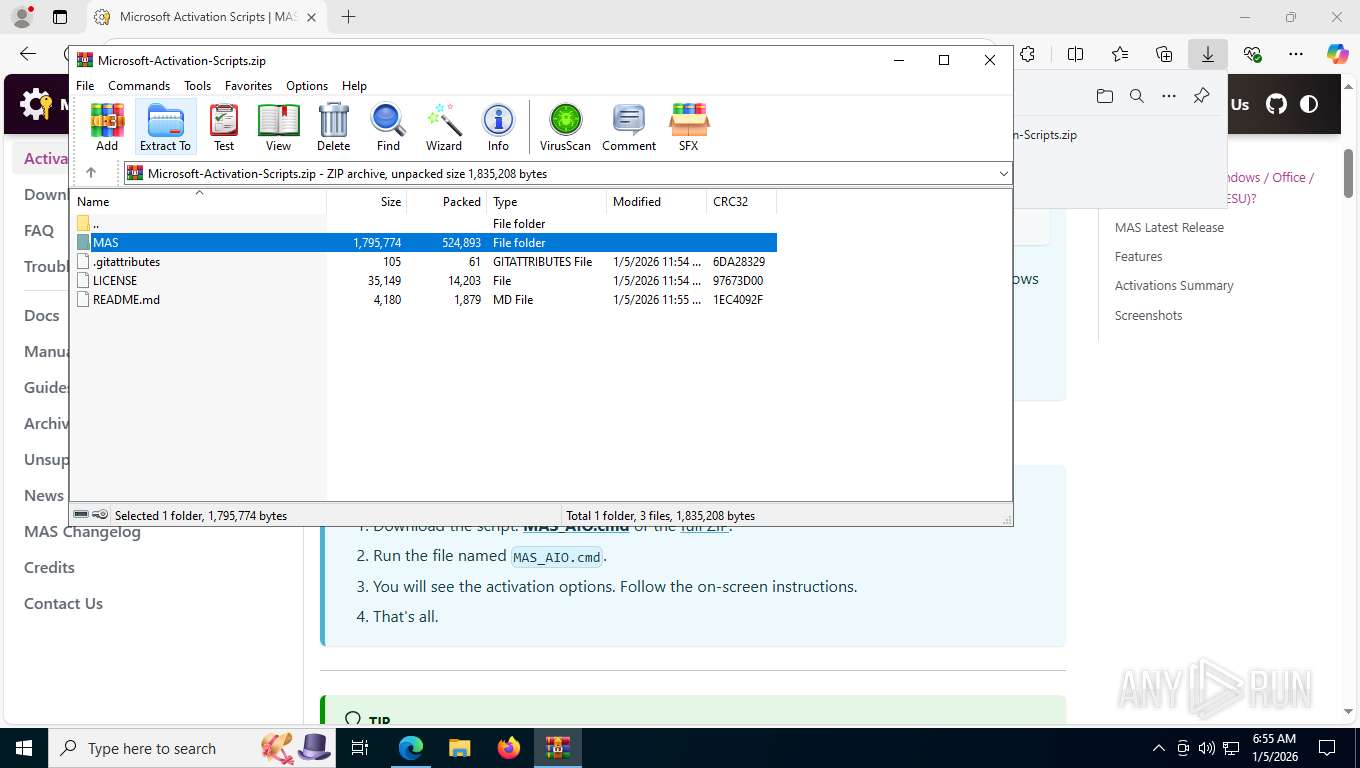
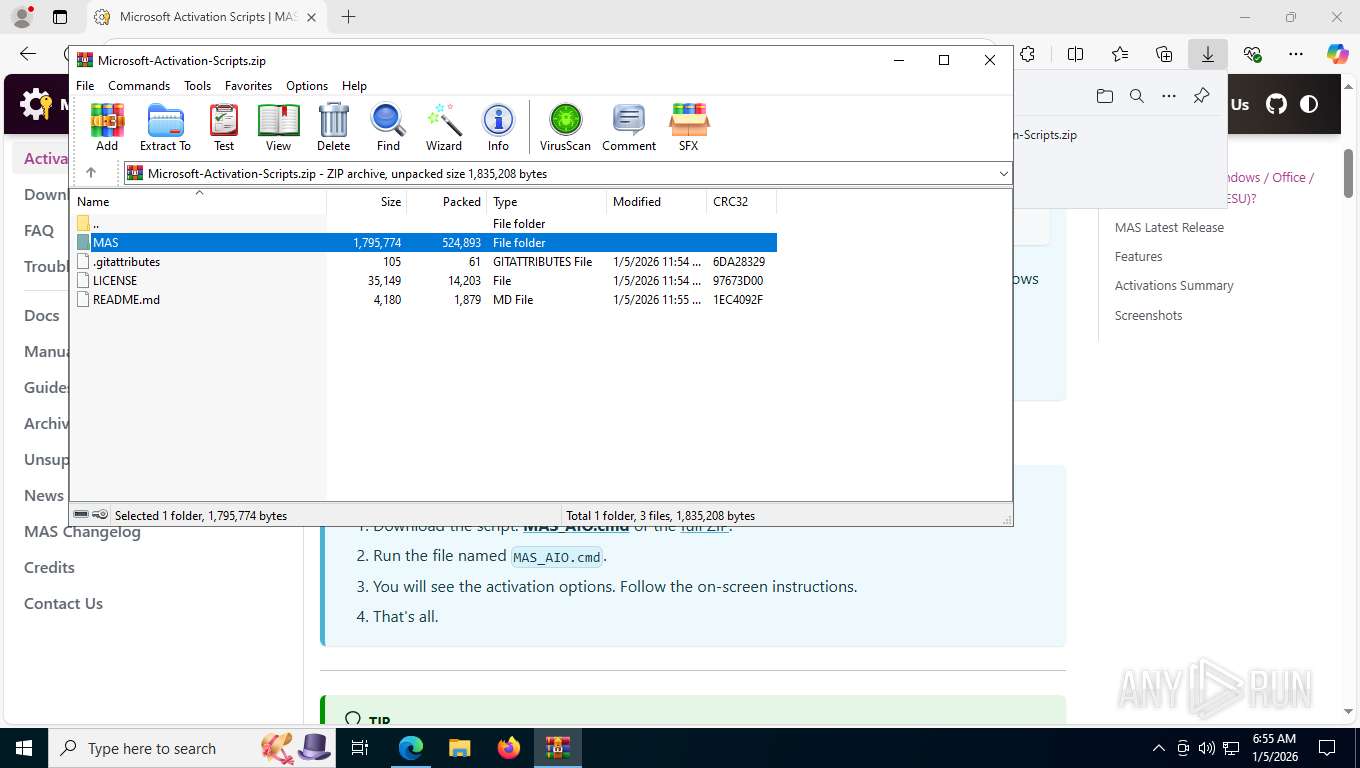
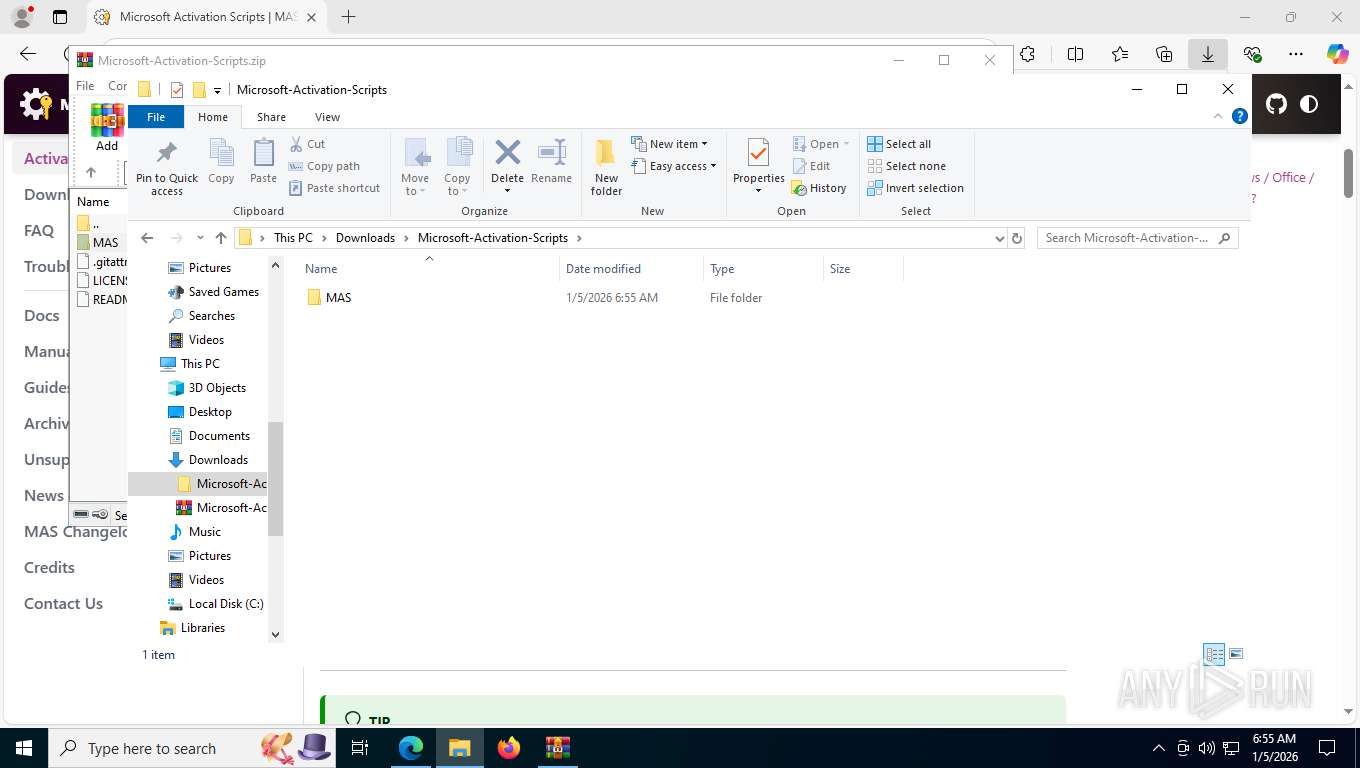
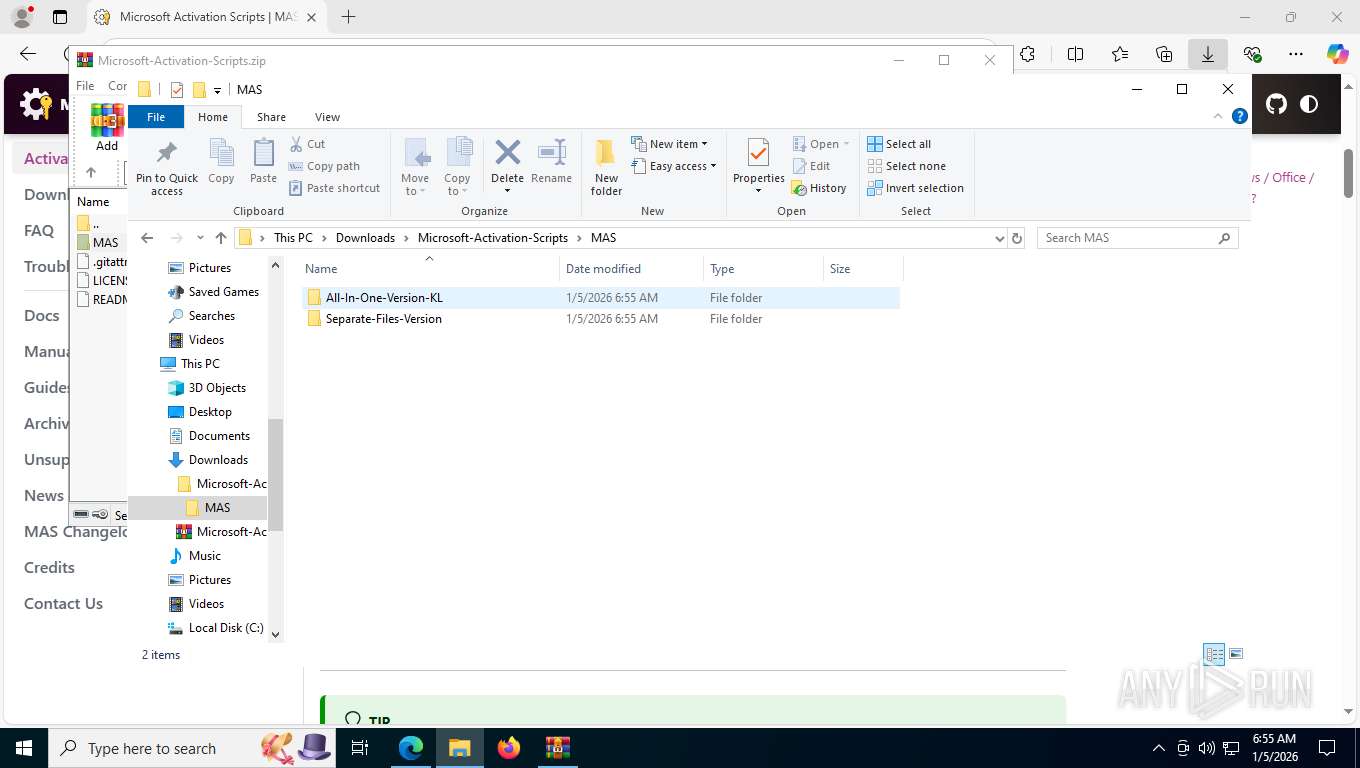
| 1172 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Downloads\Microsoft-Activation-Scripts\MAS\All-In-One-Version-KL\MAS_AIO.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | choice /C:12345678EH0 /N | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1456 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "$f=[System.IO.File]::ReadAllText('C:\Users\admin\Downloads\Microsoft-Activation-Scripts\MAS\All-In-One-Version-KL\MAS_AIO.cmd') -split ':sppmgr\:.*';. ([scriptblock]::Create($f[1]))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1848 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 702
Read events
28 674
Write events
13
Delete events
15
Modification events
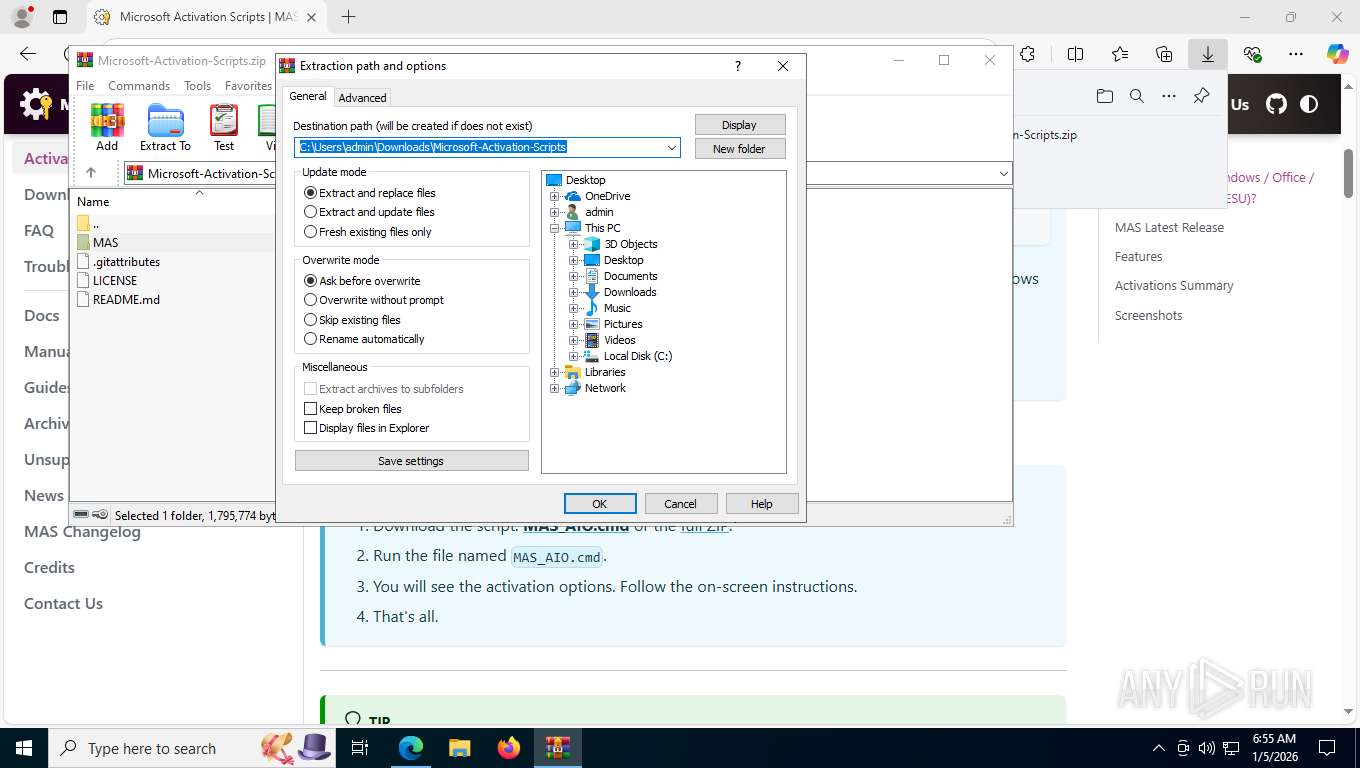
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Microsoft-Activation-Scripts.zip | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
1
Suspicious files
59
Text files
305
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7768 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfe323.TMP | — | |
MD5:— | SHA256:— | |||
| 7768 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfe323.TMP | — | |
MD5:— | SHA256:— | |||
| 7768 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7768 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfe333.TMP | — | |
MD5:— | SHA256:— | |||
| 7768 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7768 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7768 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfe342.TMP | — | |
MD5:— | SHA256:— | |||
| 7768 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7768 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFfe333.TMP | — | |
MD5:— | SHA256:— | |||
| 7768 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
122
TCP/UDP connections
72
DNS requests
71
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8004 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
8004 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:0GhiKyx5WsWbOSbEmZHJ8CDzxT1t5ZyfRxKL9ICzJZ4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
8004 | msedge.exe | GET | 200 | 2.16.204.142:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 128 Kb | whitelisted |
8004 | msedge.exe | GET | 200 | 185.199.109.153:443 | https://get.activated.win/ | US | html | 6.15 Kb | unknown |
8004 | msedge.exe | GET | 404 | 185.199.109.153:443 | https://get.activated.win/favicon.ico | US | html | 9.16 Kb | unknown |
8004 | msedge.exe | GET | 200 | 13.107.213.44:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v1/GetGlobalConfig?EdgeChannel=stable&EdgeVersion=133.0.3065.92&ConfigVersion=0 | US | text | 128 Kb | whitelisted |
8004 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1767614084&lafgdate=0 | US | text | 4.71 Kb | whitelisted |
8004 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=arbitration_priority_list&version=24.*.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | US | text | 271 b | whitelisted |
8004 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/extensionwebstorebase/v1/crx?os=win&arch=x64&os_arch=x86_64&nacl_arch=x86-64&prod=edgecrx&prodchannel=&prodversion=133.0.3065.92&lang=en-US&acceptformat=crx3,puff&x=id%3Djmjflgjpcpepeafmmgdpfkogkghcpiha%26v%3D1.2.1%26installedby%3Dother%26uc%26ping%3Dr%253D536%2526e%253D1 | US | xml | 413 b | whitelisted |
8004 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=edge_hub_apps_manifest_gz&version=4.11.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | US | text | 266 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6056 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1412 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8004 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8004 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8004 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8004 | msedge.exe | 185.199.109.153:443 | get.activated.win | FASTLY | US | whitelisted |
8004 | msedge.exe | 104.18.23.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
get.activated.win |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-WmiObject Cmdlet has been detected |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] The Principal.WindowsIdentity in PS.Script has been detected |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-CimInstance Cmdlet has been detected |
— | — | Potentially Bad Traffic | ET HUNTING PowerShell DownloadString Command Common In Powershell Stagers |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET HUNTING Powershell ScheduledTasks cmdlet Get-ScheduledTask command in HTTP Body Response |
— | — | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |