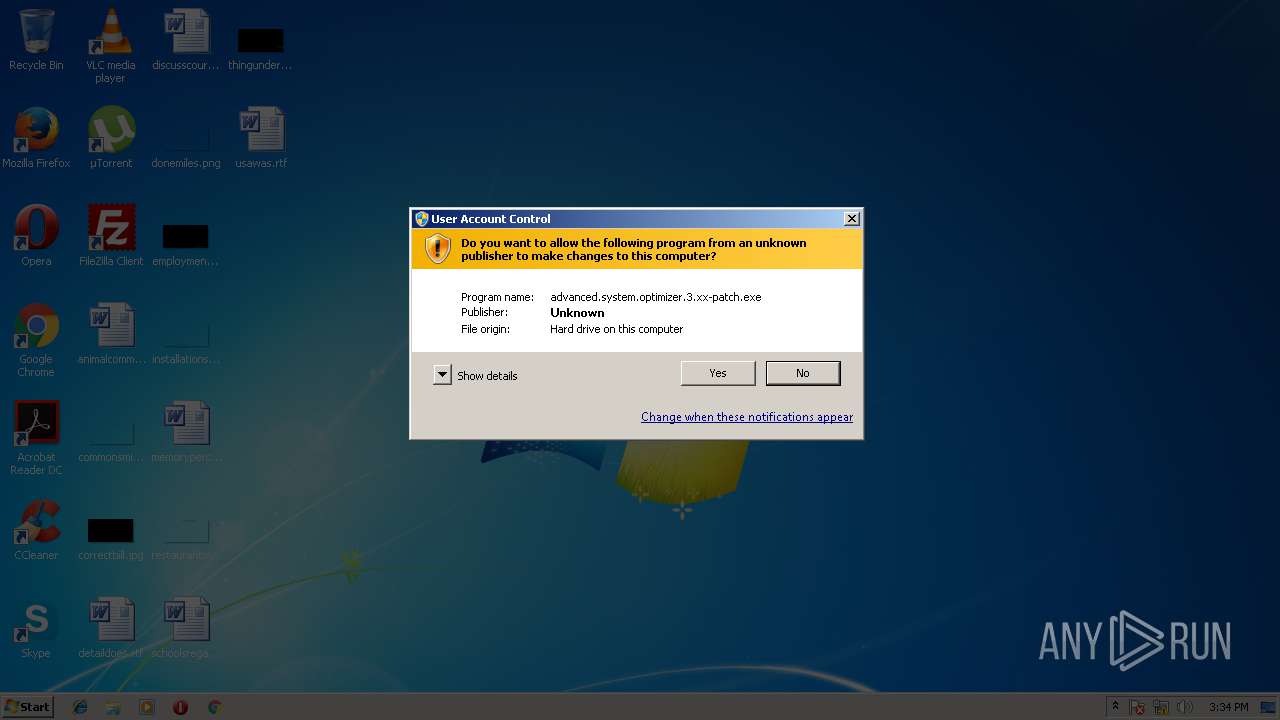
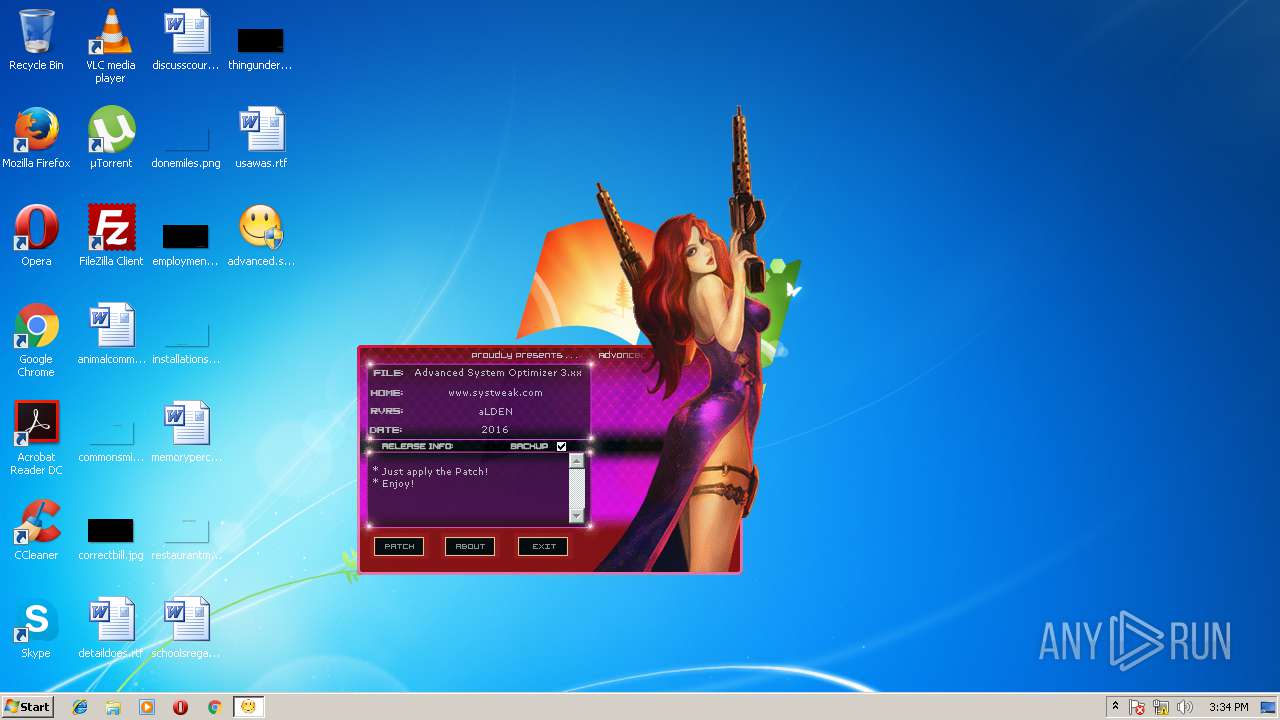
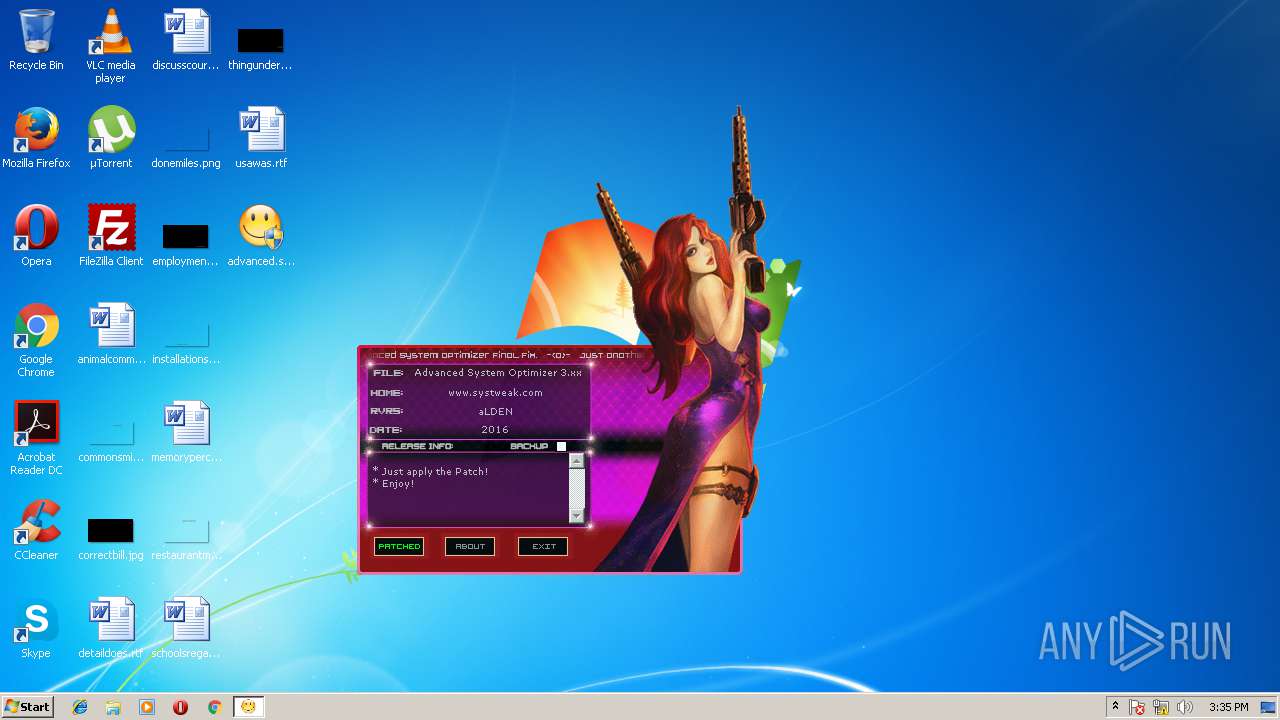
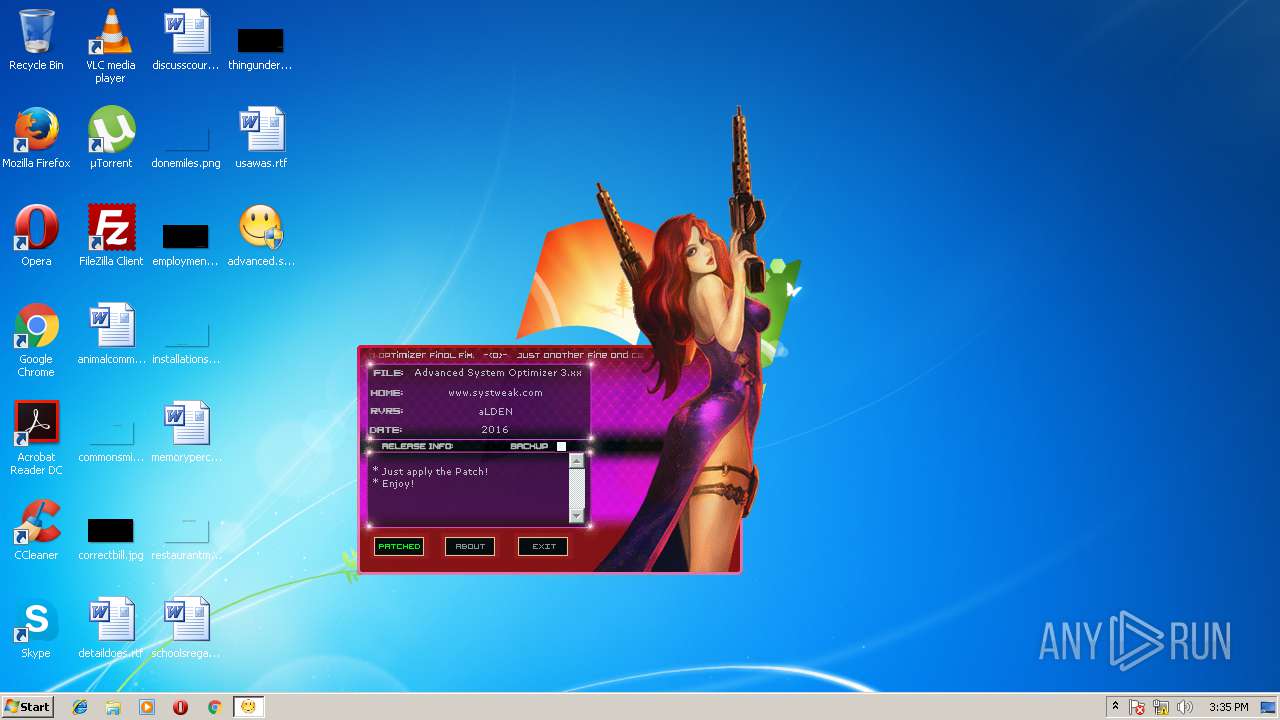
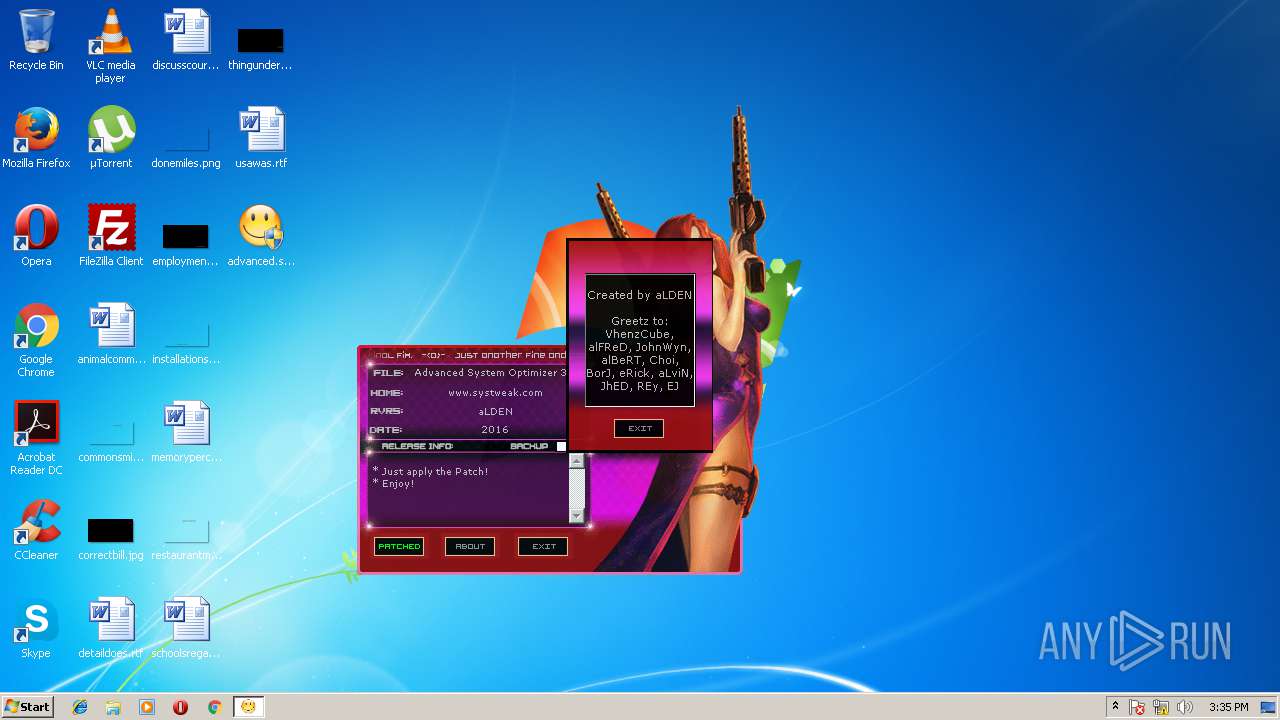
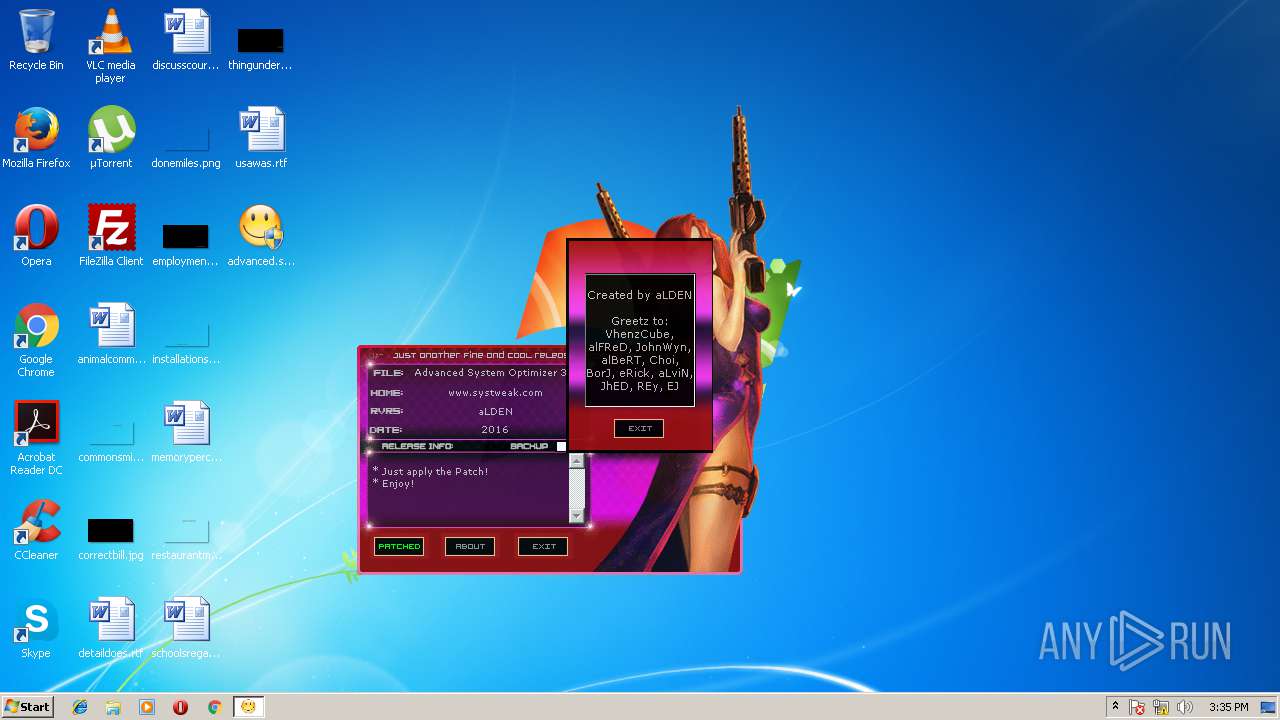
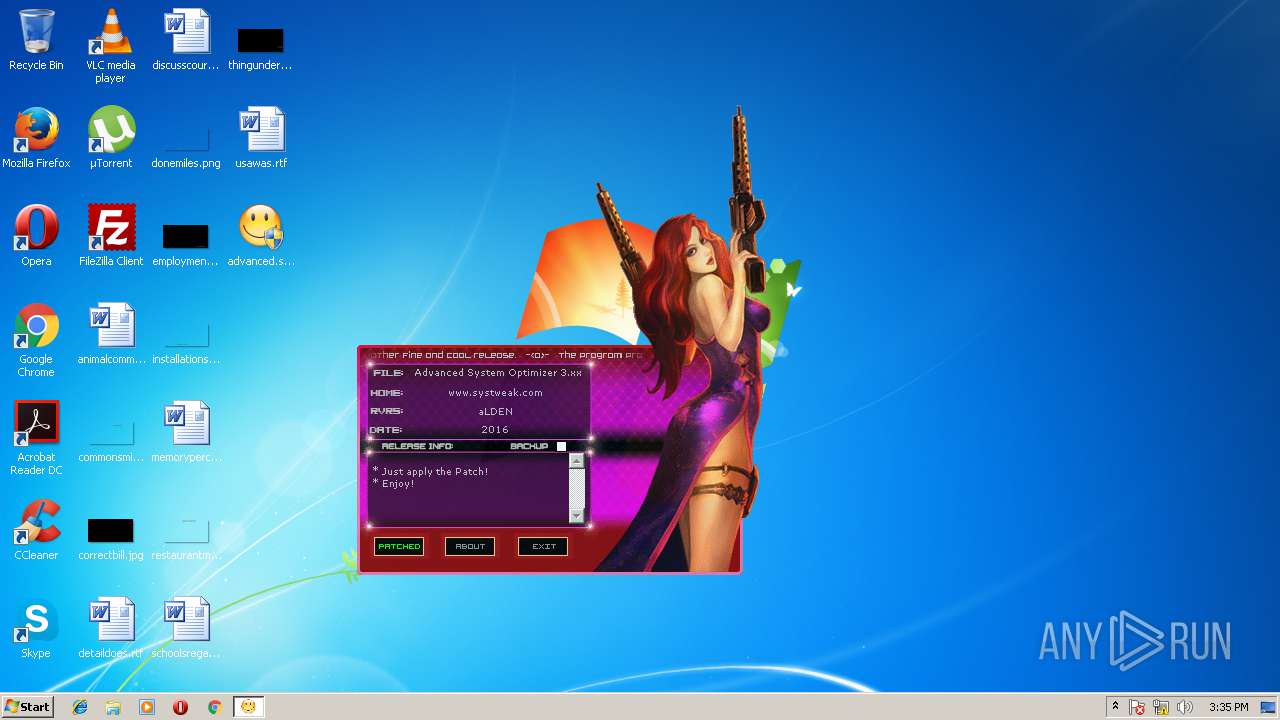
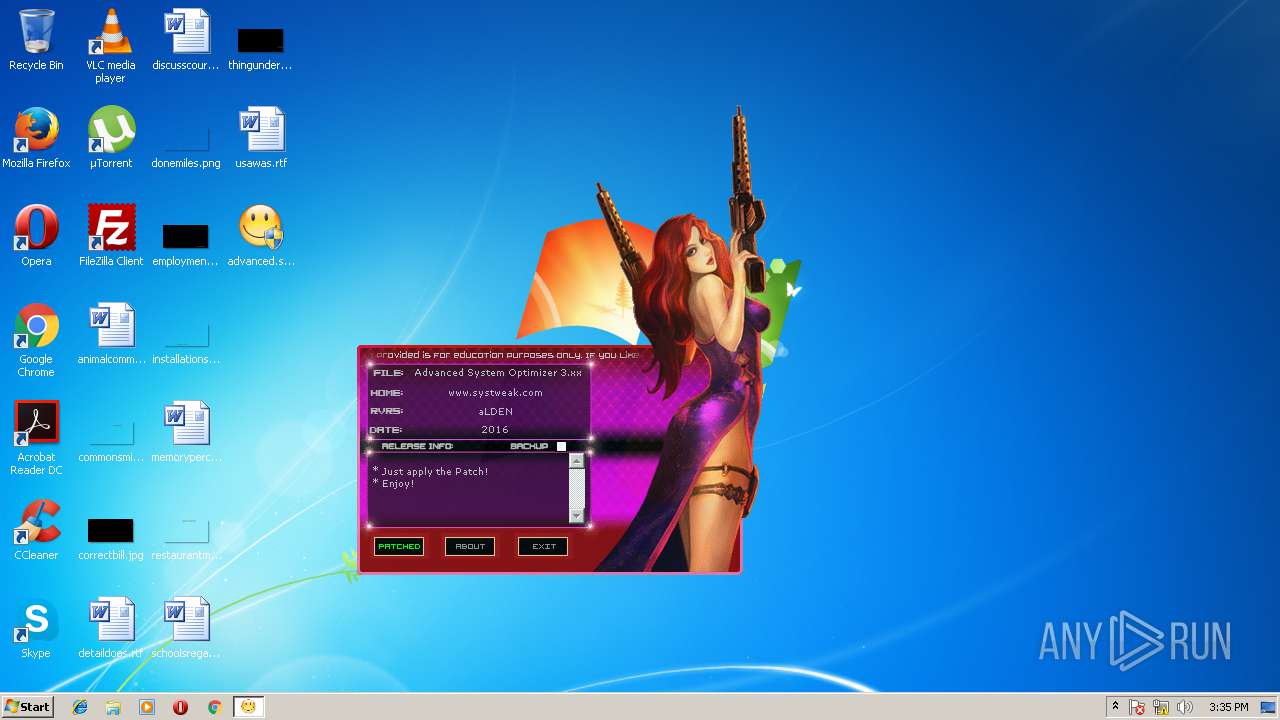
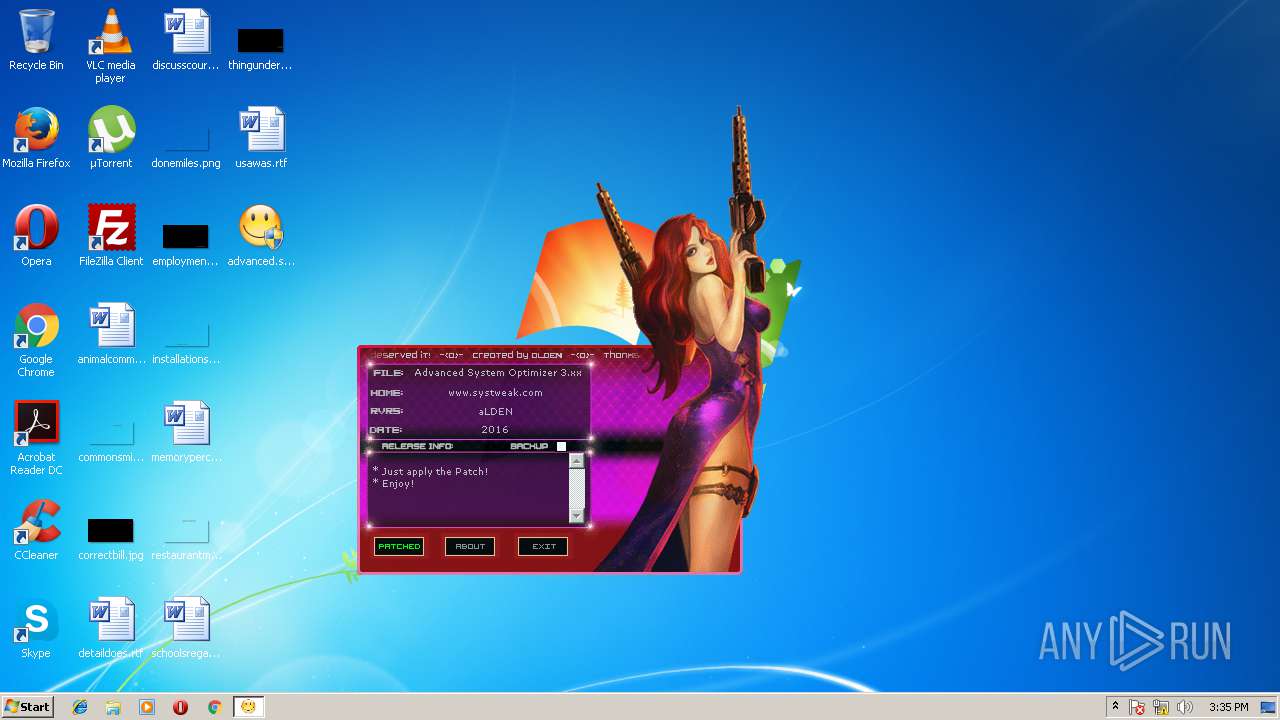
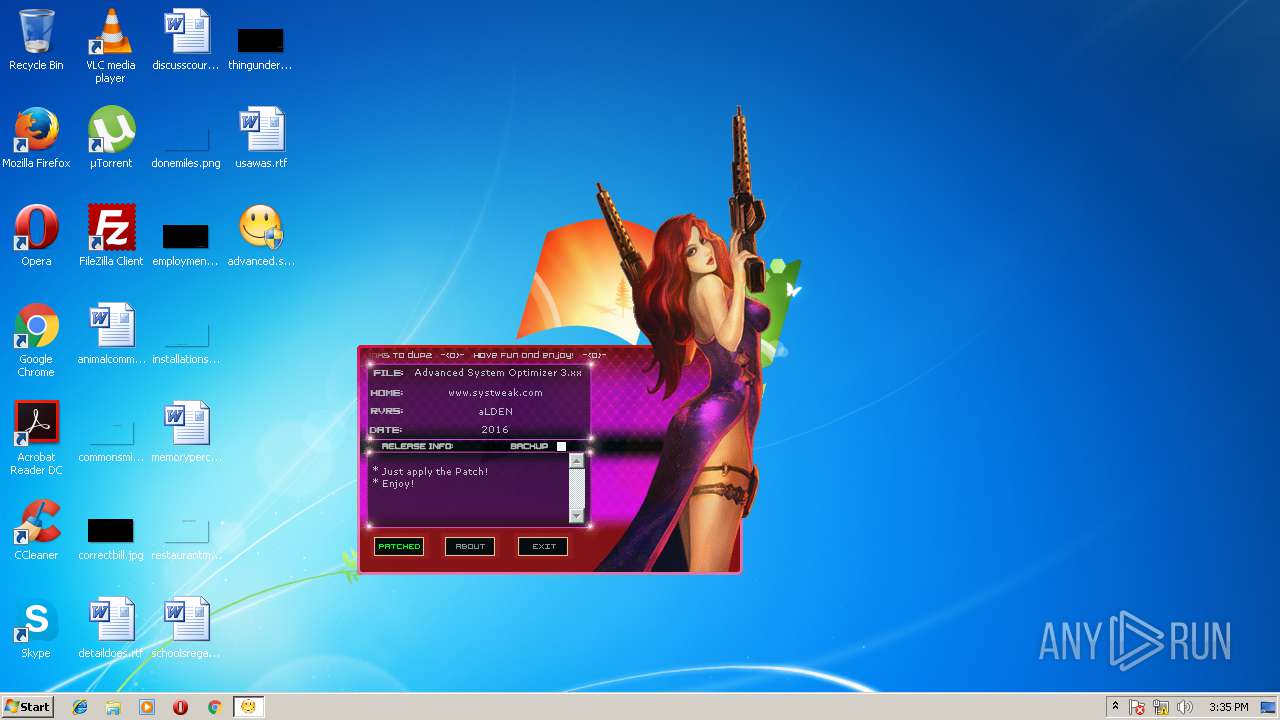
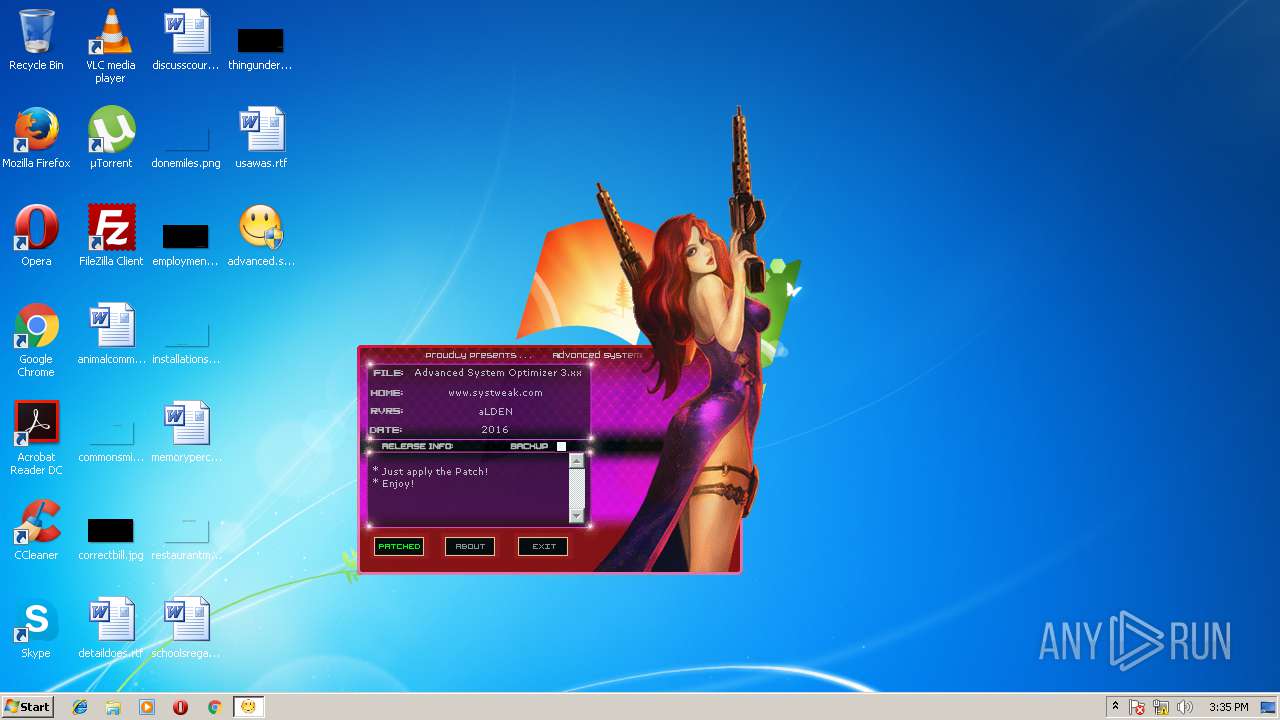
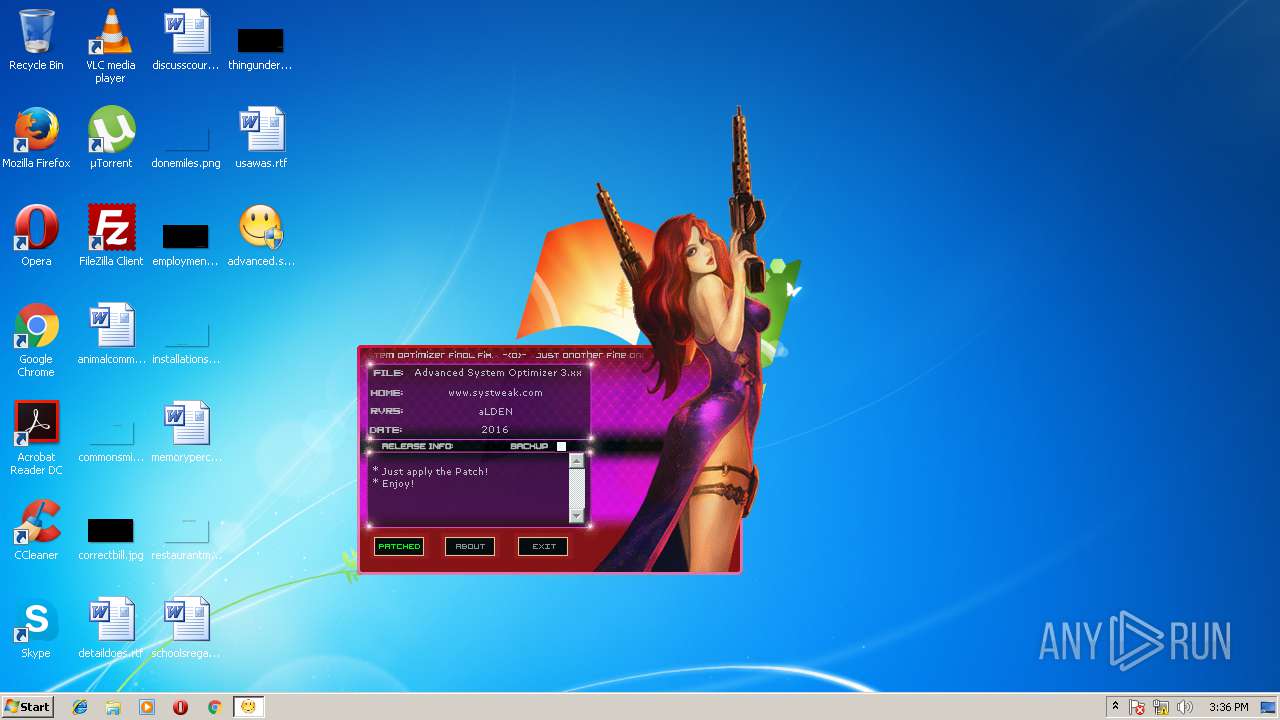
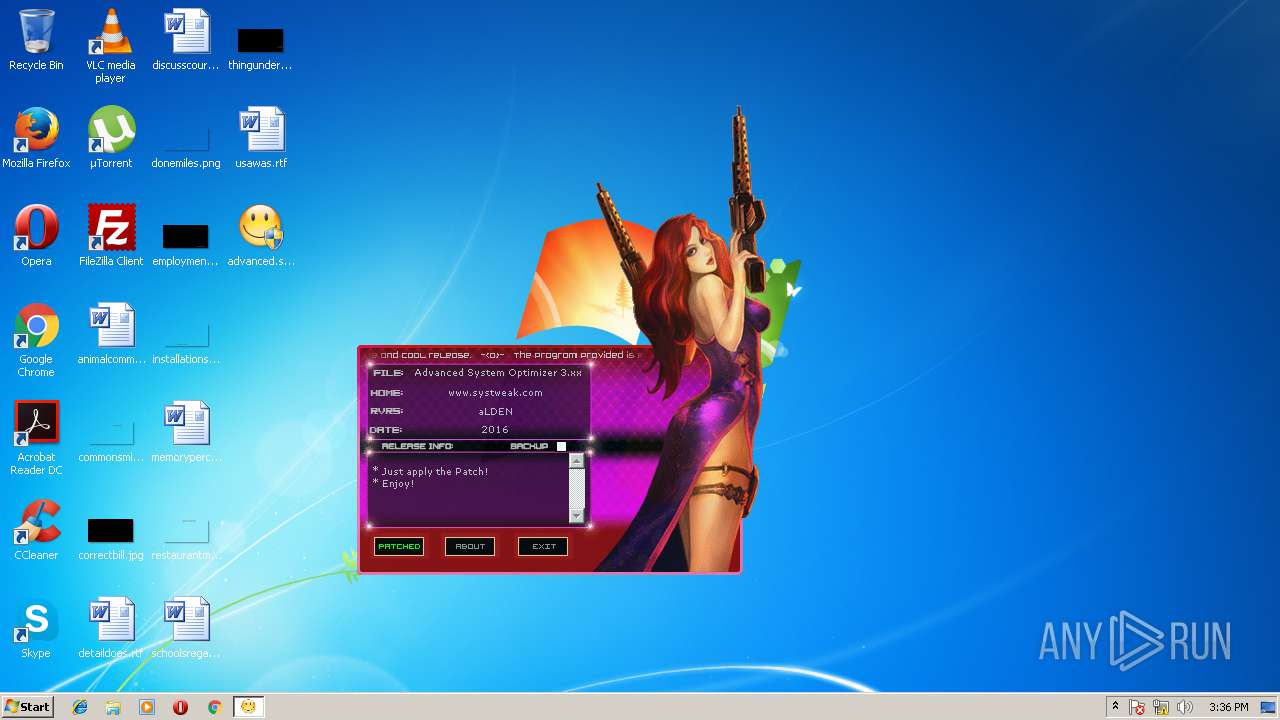
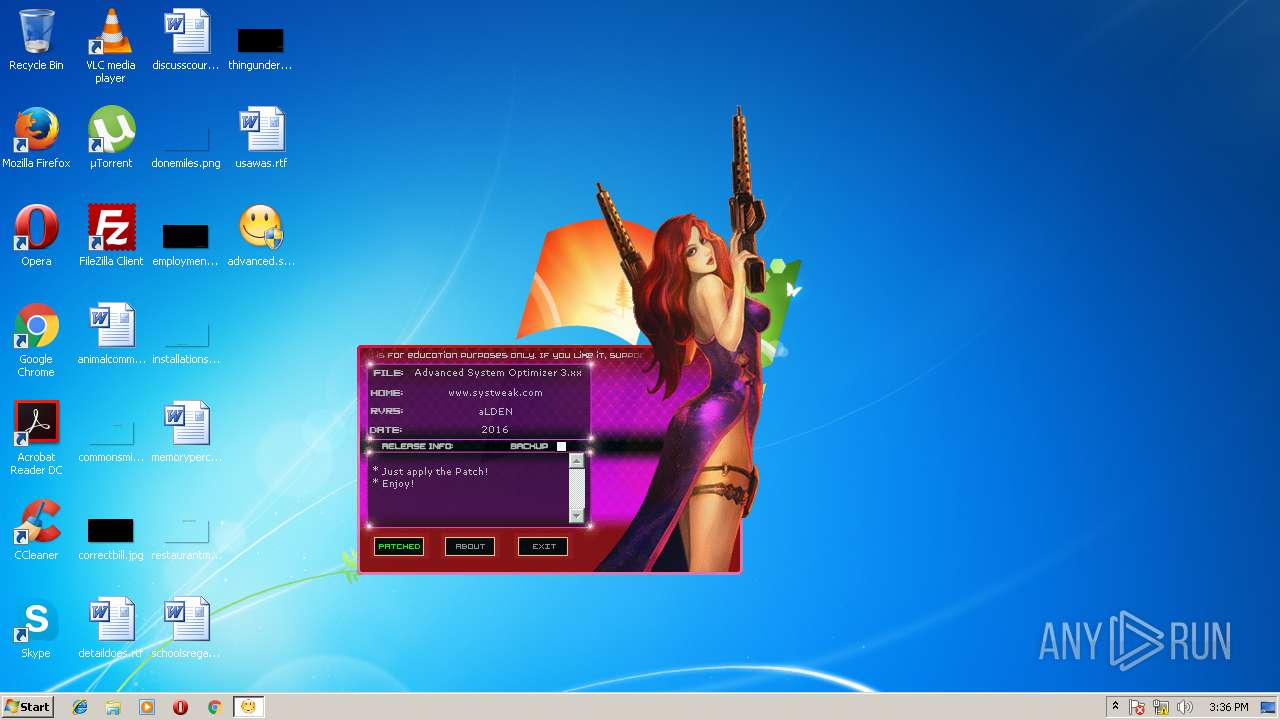
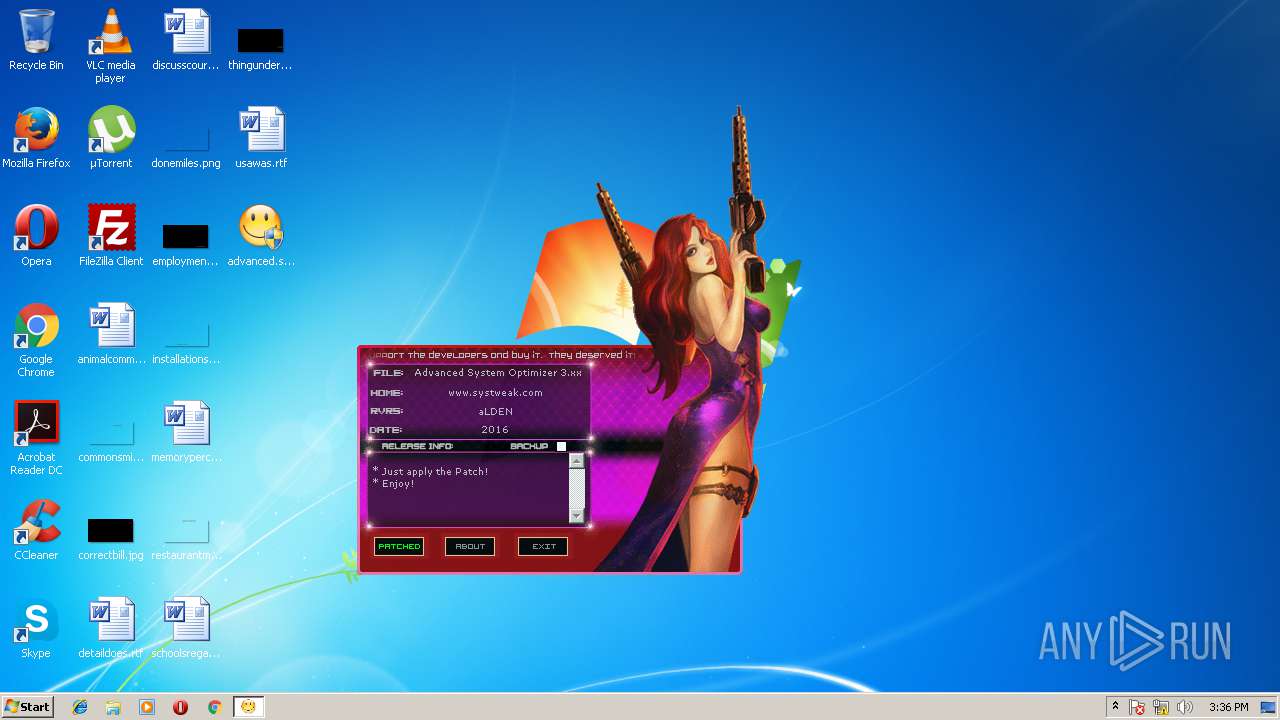
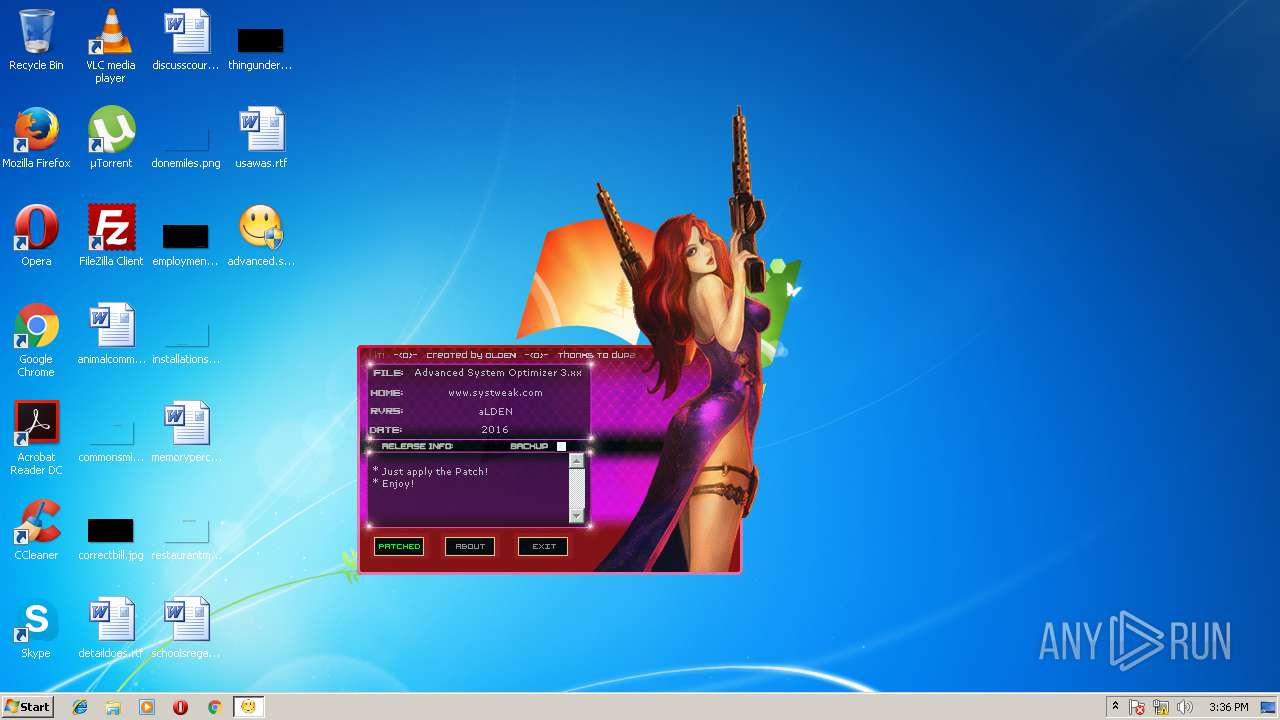
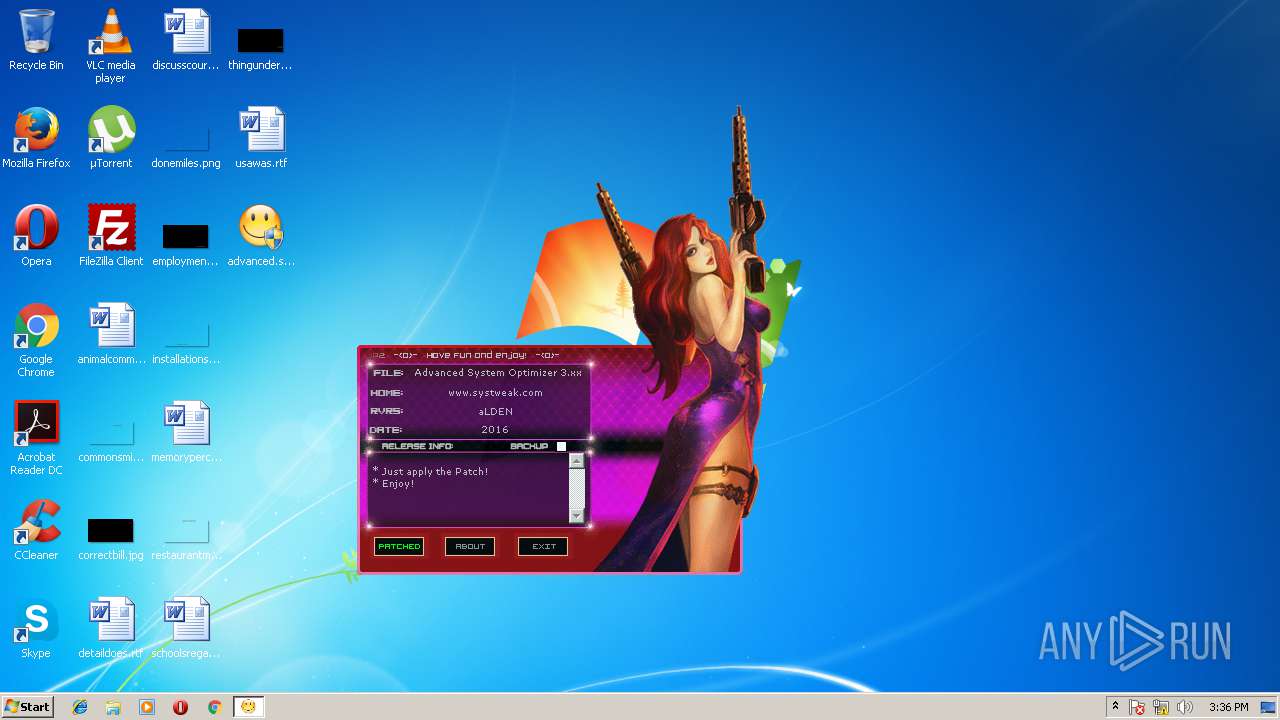
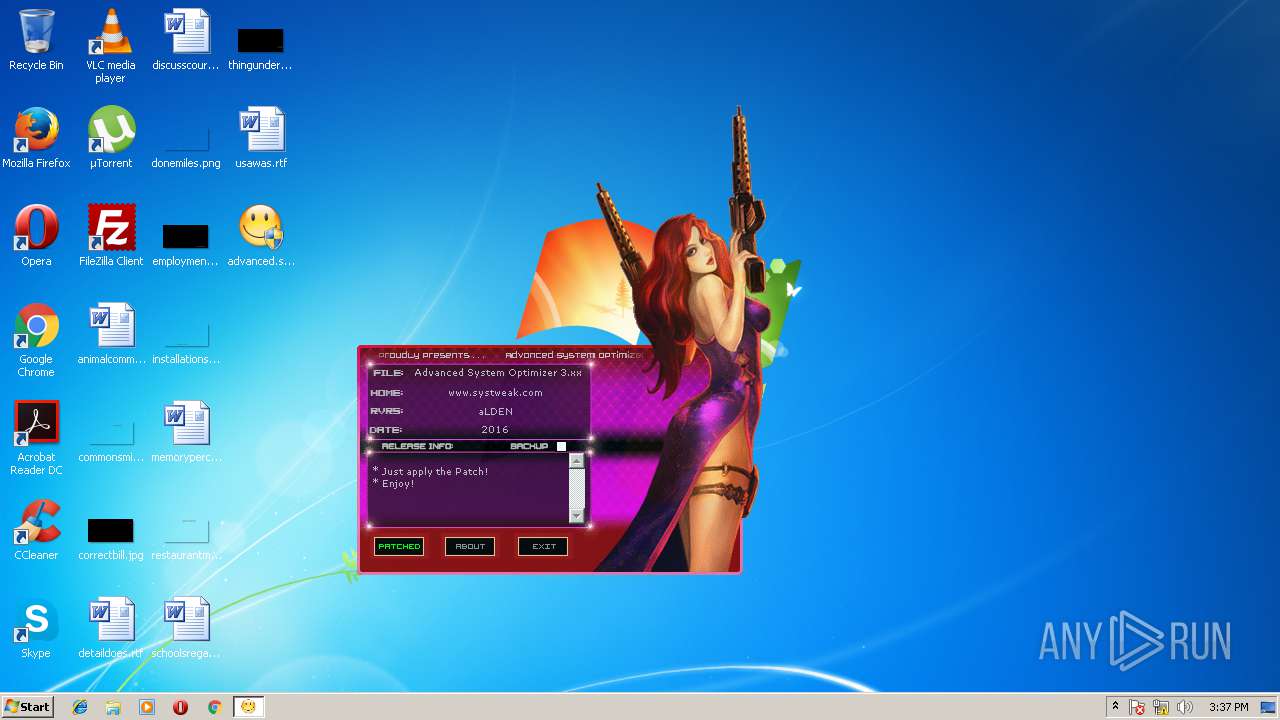
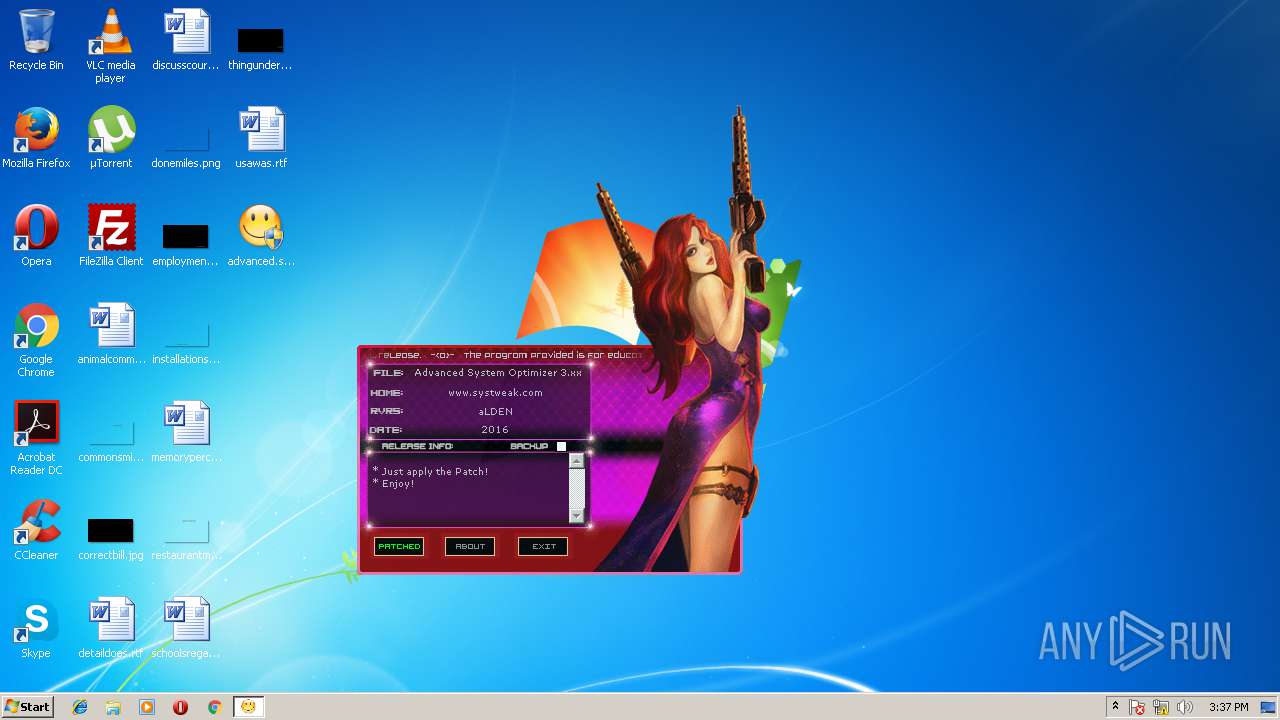
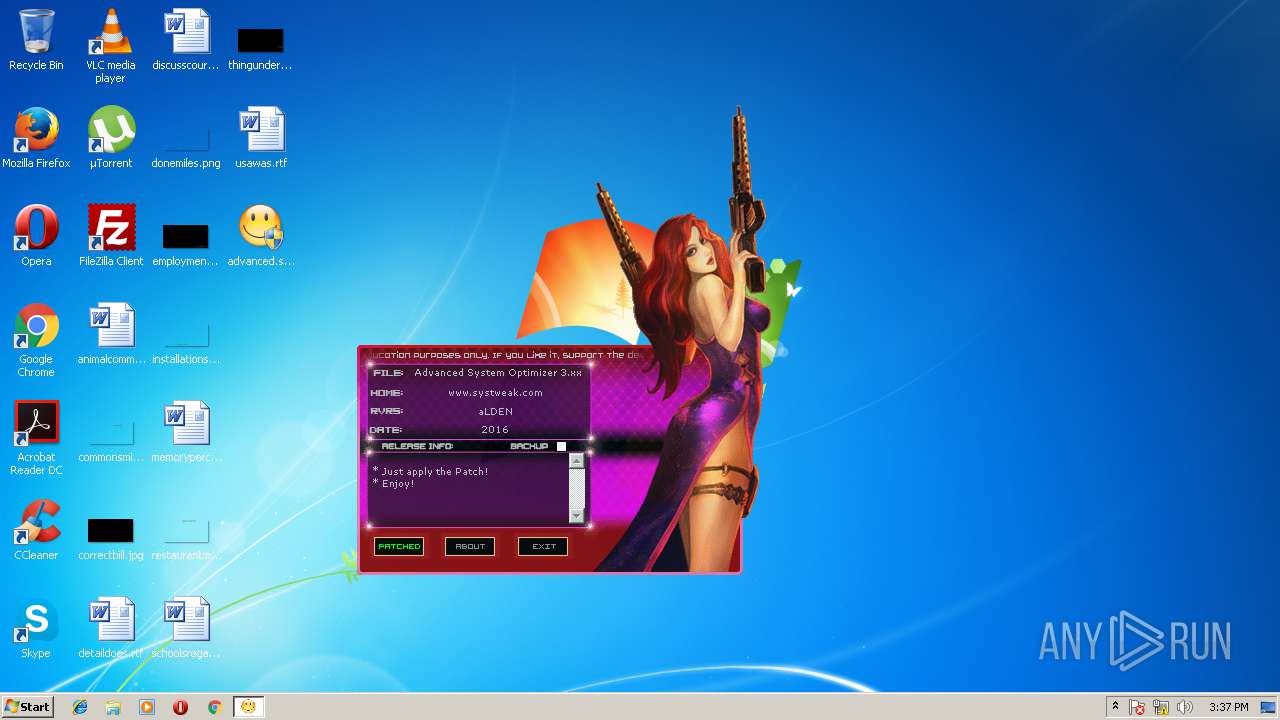
| File name: | advanced.system.optimizer.3.xx-patch.exe |
| Full analysis: | https://app.any.run/tasks/1c894f08-b0b4-475d-8169-57524ffad327 |
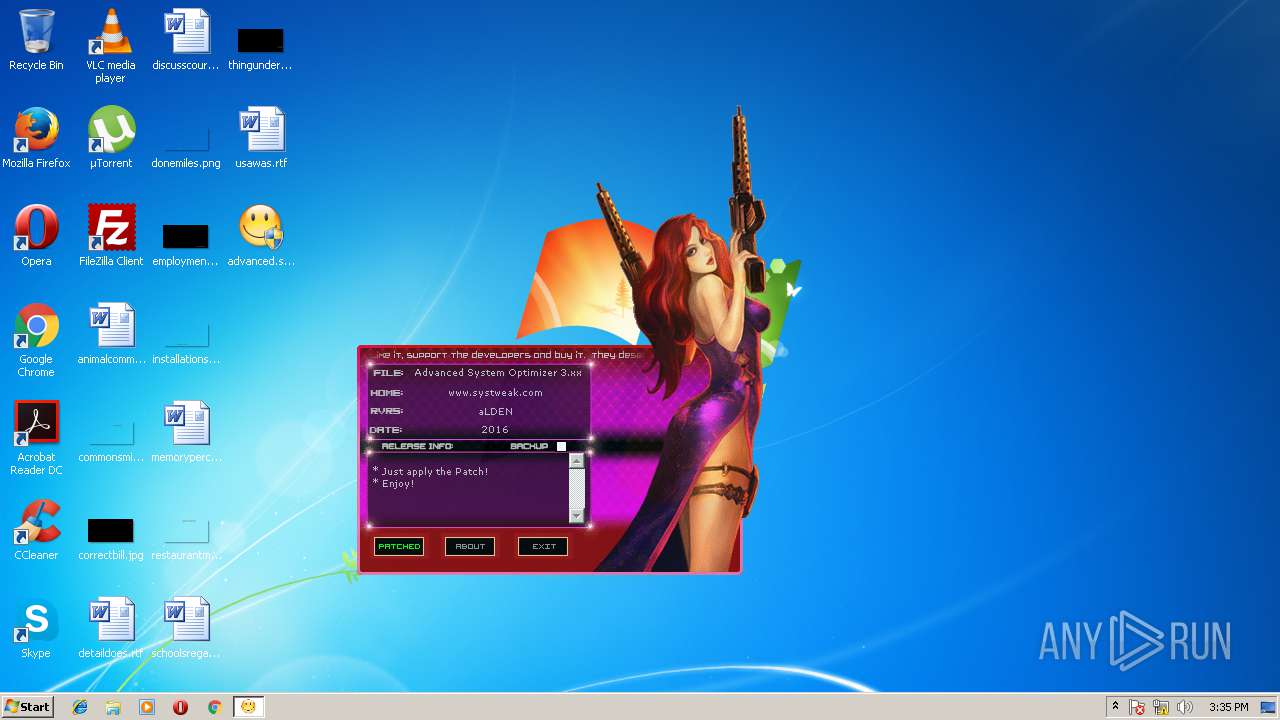
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2018, 15:34:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 93149F065474219D2320E51DED943ED9 |
| SHA1: | 8BF734C3848D21B3A018246B7202DABA4CB42494 |
| SHA256: | 83B9BB1F40F1F7D2335BC8BCA28158EBC9766699176DDF5A5EDBC19B73DB31C2 |
| SSDEEP: | 3072:1d1MVlYh6+wsAZXzrY5Db2lZWpIfHWoA5ve8CQQb:1diVlr+wsAZYUqIf2oApZCT |
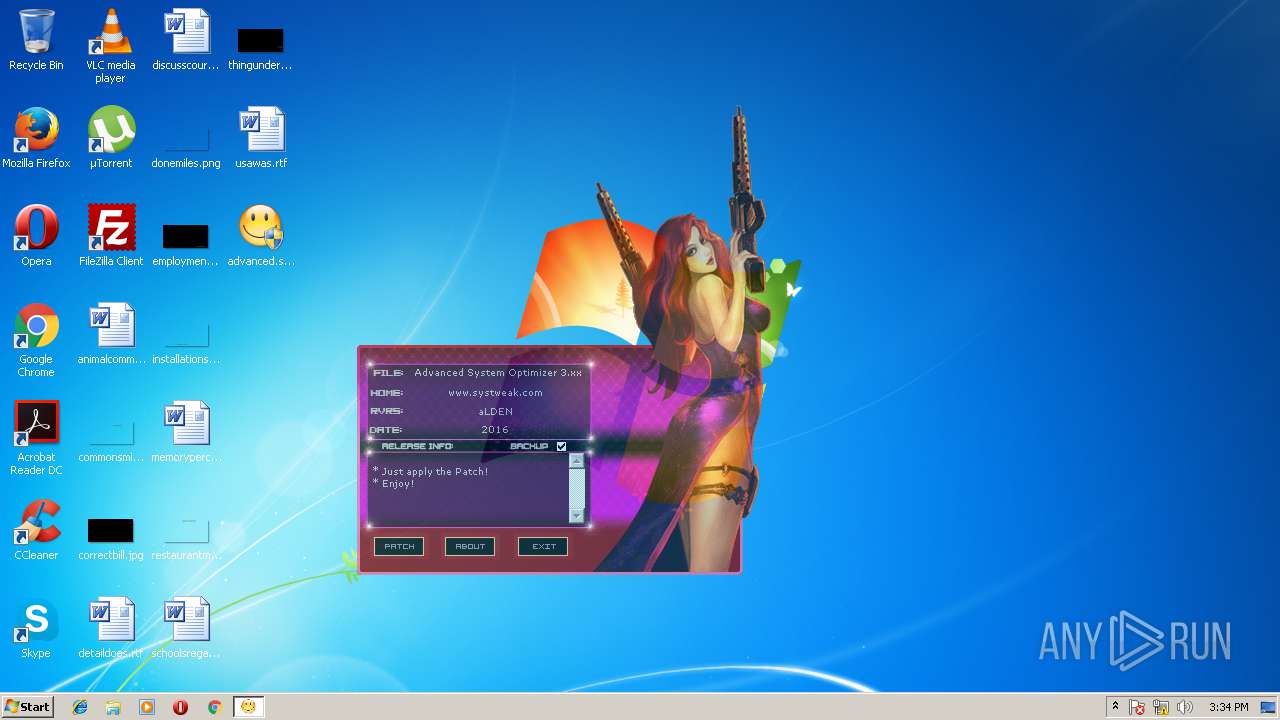
MALICIOUS
Application was dropped or rewritten from another process
- KillProc.exe (PID: 2164)
- Blocker.exe (PID: 2284)
Application loaded dropped or rewritten executable
- advanced.system.optimizer.3.xx-patch.exe (PID: 3740)
SUSPICIOUS
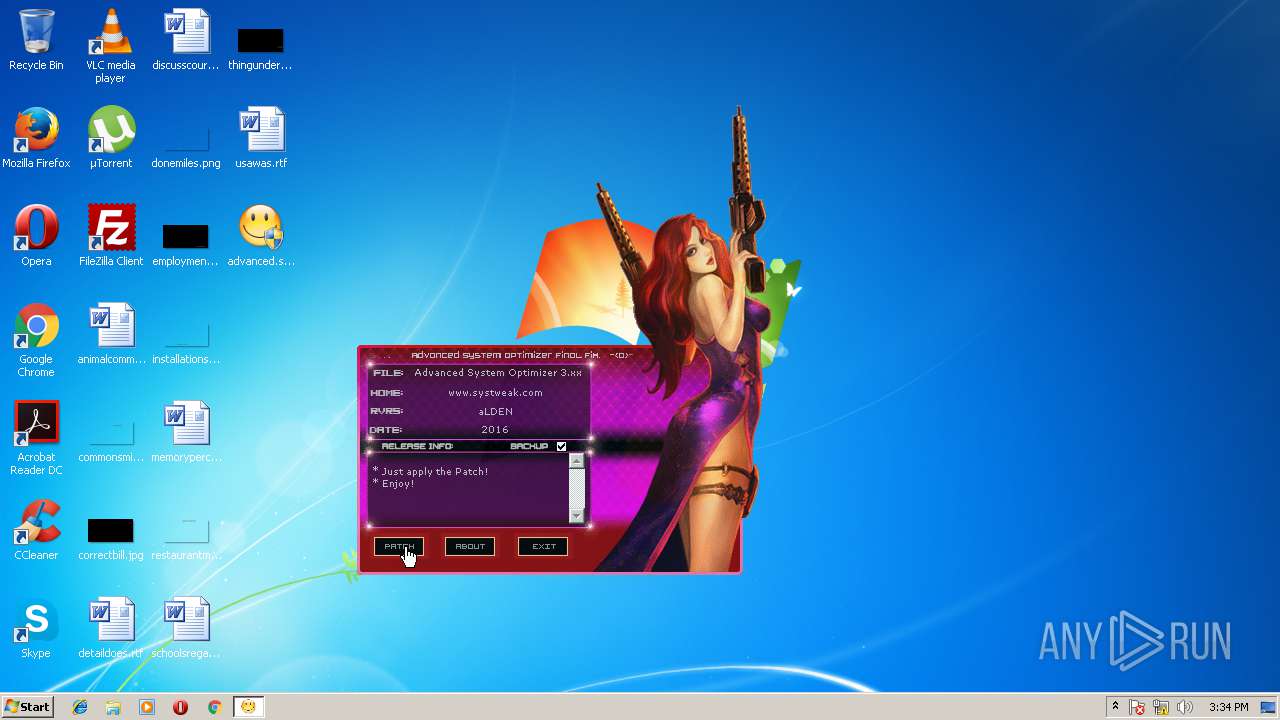
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3024)
Starts CMD.EXE for commands execution
- KillProc.exe (PID: 2164)
- Blocker.exe (PID: 2284)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3024)
- cmd.exe (PID: 3104)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 144896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x00022E78 | 0x00023000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.92816 |
.reloc | 0x00027000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
500 | 1.91924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
DLL | 7.99873 | 132096 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
Total processes
59
Monitored processes
21
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1804 | TASKKILL /F /IM ASO3.exe /T | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | "C:\Users\admin\AppData\Local\Temp\KillProc.exe" C:\Users\admin\AppData\Local\Temp\KillProc.exe | C:\Users\admin\AppData\Local\Temp\KillProc.exe | — | advanced.system.optimizer.3.xx-patch.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2264 | FIND /C /I "updateservice1.systweak.com" C:\Windows\SYSTEM32\DRIVERS\ETC\HOSTS | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Local\Temp\Blocker.exe" C:\Users\admin\AppData\Local\Temp\Blocker.exe | C:\Users\admin\AppData\Local\Temp\Blocker.exe | — | advanced.system.optimizer.3.xx-patch.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2324 | FIND /C /I "www.systweak.com" C:\Windows\SYSTEM32\DRIVERS\ETC\HOSTS | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Windows\regedit.exe" /s "C:\Users\admin\AppData\Local\Temp\\regpatch.reg" | C:\Windows\regedit.exe | — | advanced.system.optimizer.3.xx-patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | REG.EXE QUERY "HKU\S-1-5-19\ENVIRONMENT" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2636 | FIND /C /I "systweak.com/STCheckGenuineness" C:\Windows\SYSTEM32\DRIVERS\ETC\HOSTS | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2792 | FIND /C /I "systweak.com" C:\Windows\SYSTEM32\DRIVERS\ETC\HOSTS | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2880 | "C:\Users\admin\Desktop\advanced.system.optimizer.3.xx-patch.exe" | C:\Users\admin\Desktop\advanced.system.optimizer.3.xx-patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
179
Read events
144
Write events
34
Delete events
1
Modification events
| (PID) Process: | (2164) KillProc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2164) KillProc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3480) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\systweak\aso3 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3740) advanced.system.optimizer.3.xx-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3740) advanced.system.optimizer.3.xx-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2284) Blocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2284) Blocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2368) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\systweak\aso3 |
| Operation: | write | Name: | ASOBUILDFOR |
Value: systweak | |||
| (PID) Process: | (2368) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\systweak\aso3 |
| Operation: | write | Name: | ASO3CAM |
Value: website | |||
| (PID) Process: | (2368) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\systweak\aso3 |
| Operation: | write | Name: | ASO3AFFILIATE |
Value: | |||
Executable files
5
Suspicious files
0
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3740 | advanced.system.optimizer.3.xx-patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:— | SHA256:— | |||
| 3740 | advanced.system.optimizer.3.xx-patch.exe | C:\Users\admin\AppData\Local\Temp\Techno Funk.ttf | ttf | |
MD5:— | SHA256:— | |||
| 3740 | advanced.system.optimizer.3.xx-patch.exe | C:\Users\admin\AppData\Local\Temp\regpatch.reg | text | |
MD5:— | SHA256:— | |||
| 3740 | advanced.system.optimizer.3.xx-patch.exe | C:\Users\admin\AppData\Local\Temp\Blocker.exe | executable | |
MD5:— | SHA256:— | |||
| 2164 | KillProc.exe | C:\Users\admin\AppData\Local\Temp\2ED5.tmp\2ED6.bat | text | |
MD5:— | SHA256:— | |||
| 2284 | Blocker.exe | C:\Users\admin\AppData\Local\Temp\327E.tmp\327F.bat | text | |
MD5:— | SHA256:— | |||
| 3740 | advanced.system.optimizer.3.xx-patch.exe | C:\Users\admin\AppData\Local\Temp\KillProc.exe | executable | |
MD5:— | SHA256:— | |||
| 3104 | cmd.exe | C:\Windows\SYSTEM32\DRIVERS\ETC\HOSTS | text | |
MD5:— | SHA256:— | |||
| 3740 | advanced.system.optimizer.3.xx-patch.exe | C:\Users\admin\AppData\Local\Temp\A1D76FF97175BF79025AB7AA1DDF0A2A.dll | executable | |
MD5:70A3B98D4DCD9C7BF08D228334FBCAB4 | SHA256:08A0599B4CE4F8E963279FFD47642C82325A9C7B98E08DFA42CEC62B454C2BCB | |||
| 3740 | advanced.system.optimizer.3.xx-patch.exe | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:D55F25972291D5AF43940B4BCA124774 | SHA256:FFD0A2F5161E459FCF34EEECA9F777E8DCDEC11712B3ECEE4B4243D06FADC189 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
teredo.ipv6.microsoft.com |
| whitelisted |