| File name: | e621ca05.exe |
| Full analysis: | https://app.any.run/tasks/f22057e8-b9c6-43f1-80ba-c078ba0a3ae7 |
| Verdict: | Malicious activity |
| Analysis date: | August 11, 2023, 13:42:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BEB5D494D98FD8ED82C6D5ABB9DC6F36 |
| SHA1: | A60BBB81E73ACCE35C769110D7CF28BCE78AFAF9 |
| SHA256: | 83B3DDB35DBC64E9A3584B5CBAD78D96DA138250493C8BE0BFCEA275A5C6D921 |
| SSDEEP: | 3072:8s0iMCjOY1lN5WOzM7UfBtuLJnKyA7N8R4YcyUL/faYJa+bS:8RY1drOiuLJnKyA7N8R4YULHaWa |
MALICIOUS
UxCryptor is detected
- explorer.exe (PID: 1024)
Application was injected by another process
- ctfmon.exe (PID: 1480)
- taskeng.exe (PID: 284)
- dwm.exe (PID: 304)
- explorer.exe (PID: 1024)
Changes the autorun value in the registry
- explorer.exe (PID: 1024)
Runs injected code in another process
- e621ca05.exe (PID: 2528)
Connects to the CnC server
- explorer.exe (PID: 1024)
SUSPICIOUS
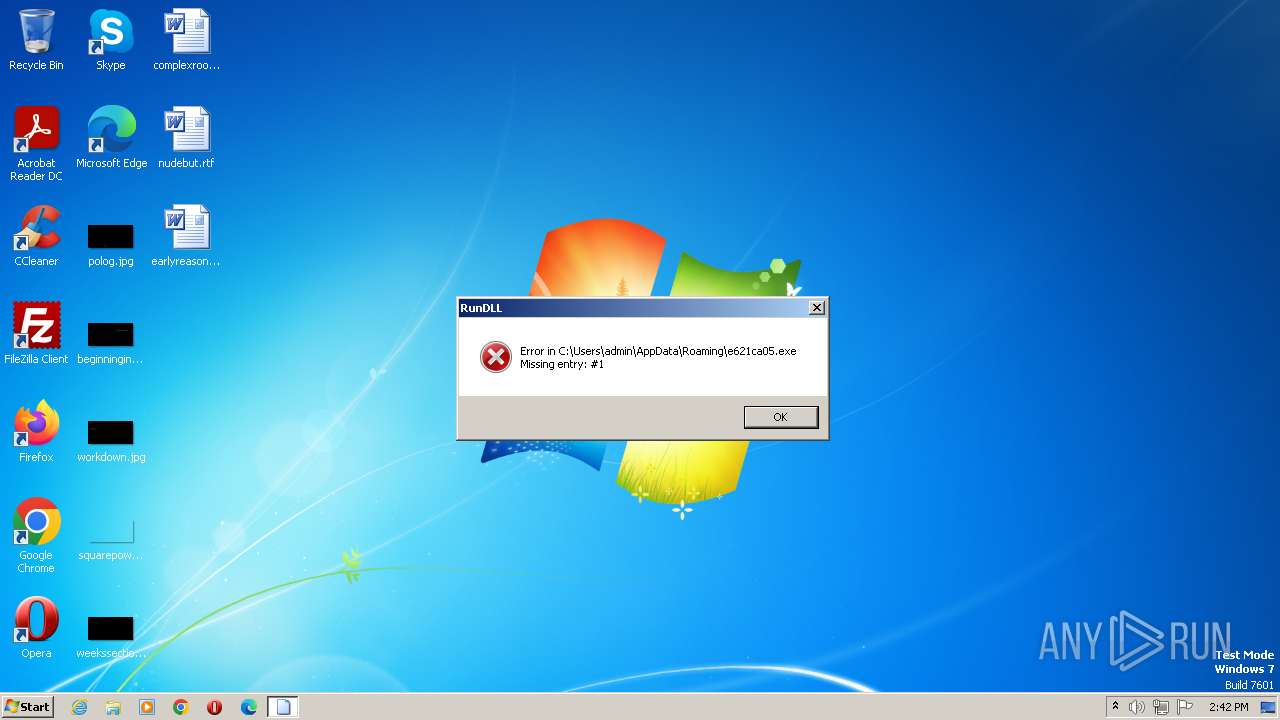
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 1024)
Application launched itself
- e621ca05.exe (PID: 2712)
Executable content was dropped or overwritten
- explorer.exe (PID: 1024)
Connects to unusual port
- explorer.exe (PID: 1024)
INFO
Checks supported languages
- e621ca05.exe (PID: 2712)
- e621ca05.exe (PID: 2528)
Reads the computer name
- e621ca05.exe (PID: 2528)
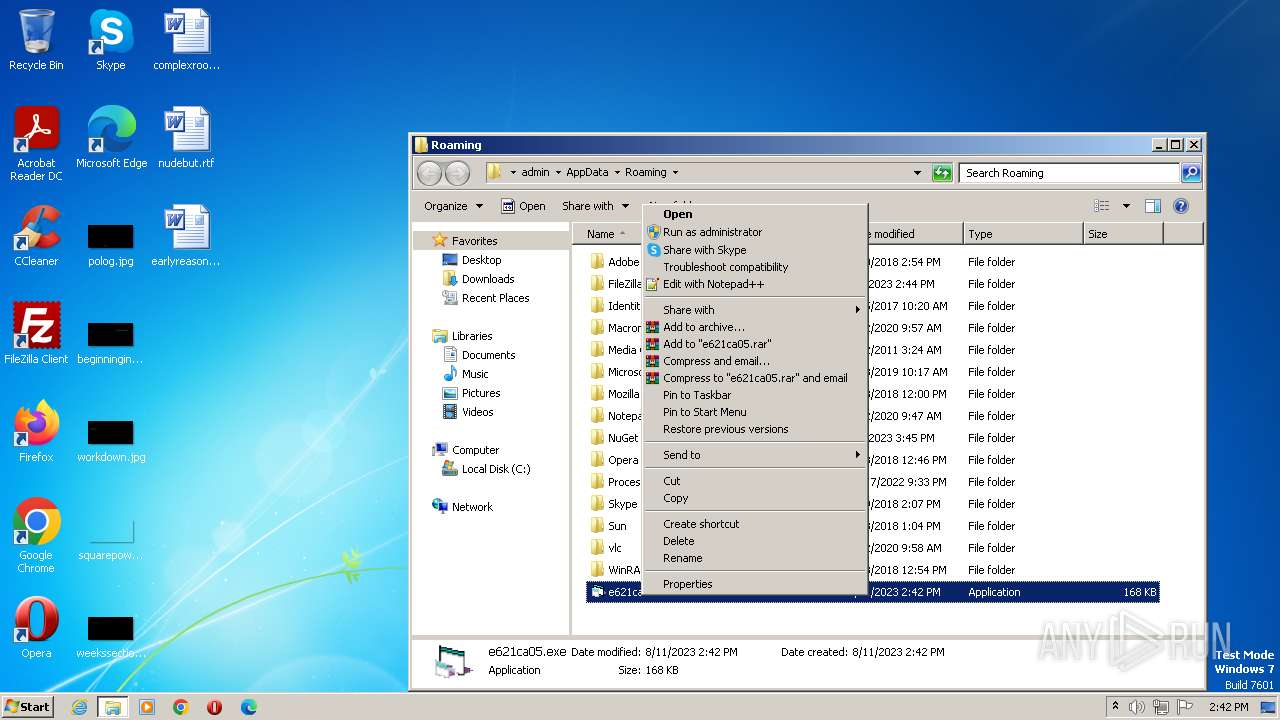
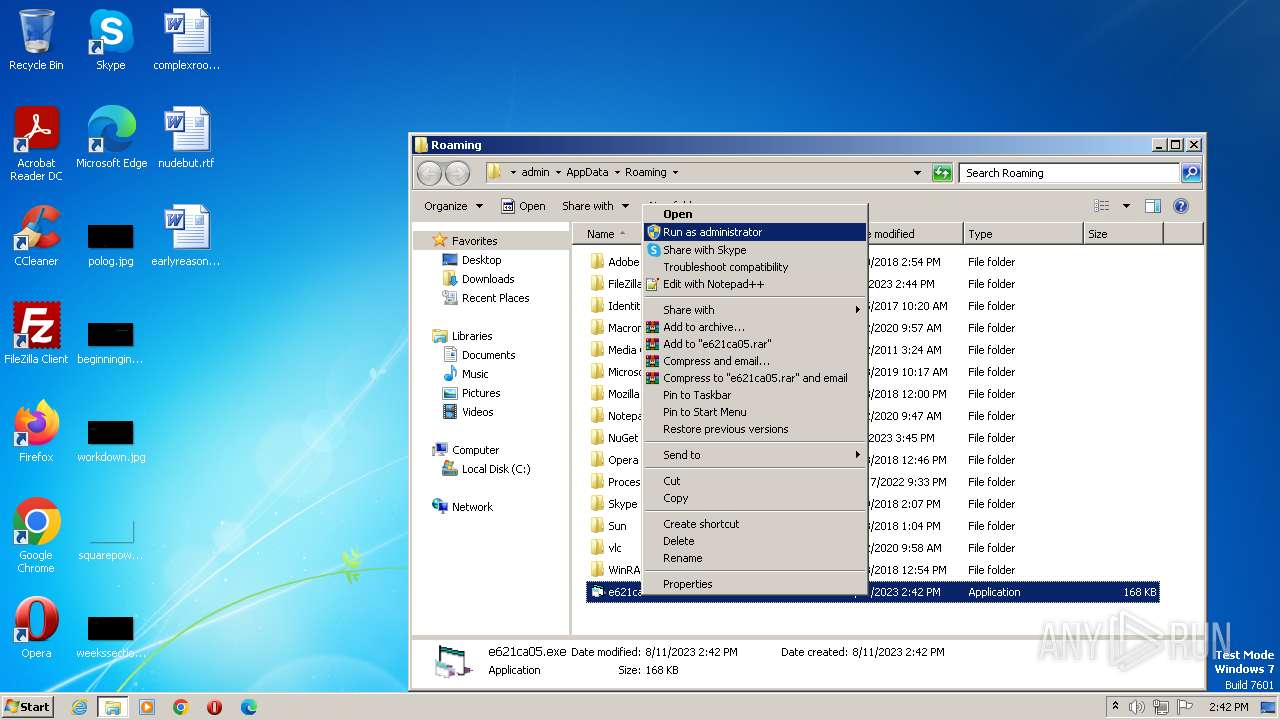
Manual execution by a user
- verclsid.exe (PID: 2748)
- e621ca05.exe (PID: 2712)
Creates files or folders in the user directory
- explorer.exe (PID: 1024)
Checks proxy server information
- explorer.exe (PID: 1024)
Reads the Internet Settings
- explorer.exe (PID: 1024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 50.5 |
| OSVersion: | 4 |
| EntryPoint: | 0x1834 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 16384 |
| CodeSize: | 61440 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2011:05:10 22:31:50+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-May-2011 22:31:50 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-May-2011 22:31:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000E980 | 0x0000F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.85589 |
.data | 0x00010000 | 0x0000262C | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE, IMAGE_SCN_TYPE_GROUP | 0 |
.rsrc | 0x00013000 | 0x00018934 | 0x00019000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.95913 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.97836 | 48 | Unicode (UTF 16LE) | UNKNOWN | RT_GROUP_ICON |
30001 | 2.22226 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 0 | 838861104 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 2.49166 | 296 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
39
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | taskeng.exe {CFFDAB72-A1D3-422E-87FF-2F067303F51C} | C:\Windows\System32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1480 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
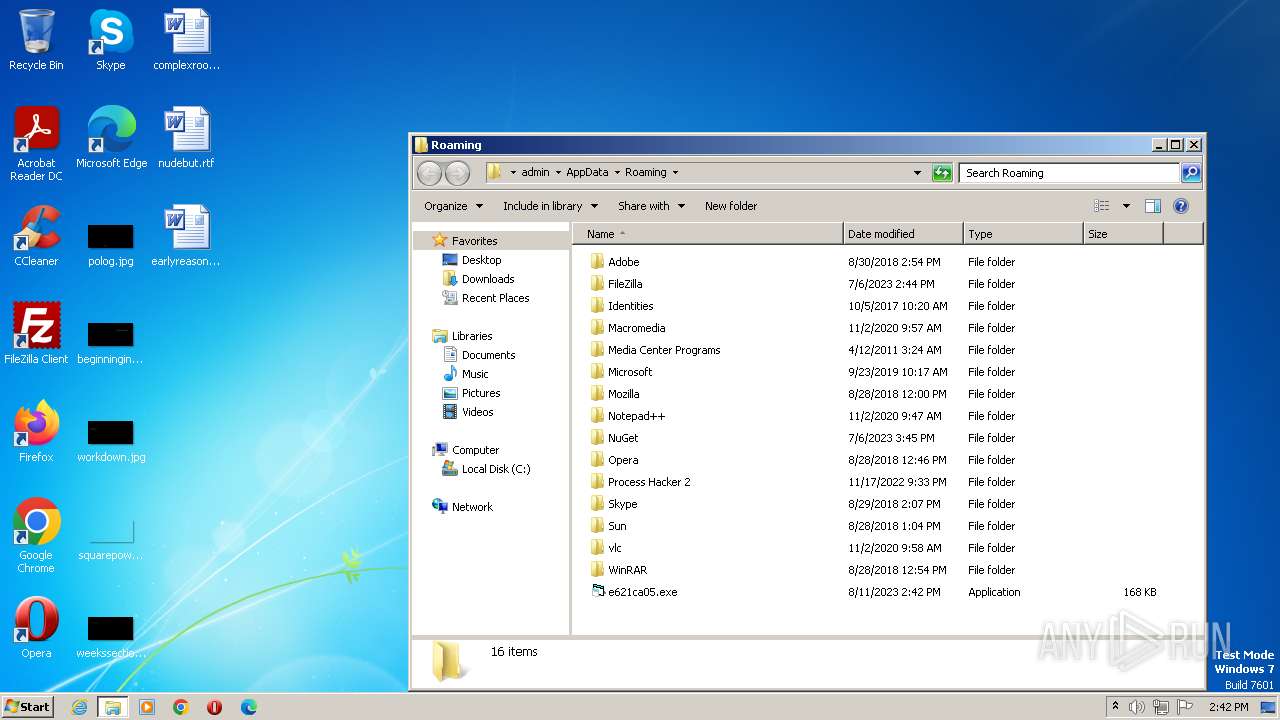
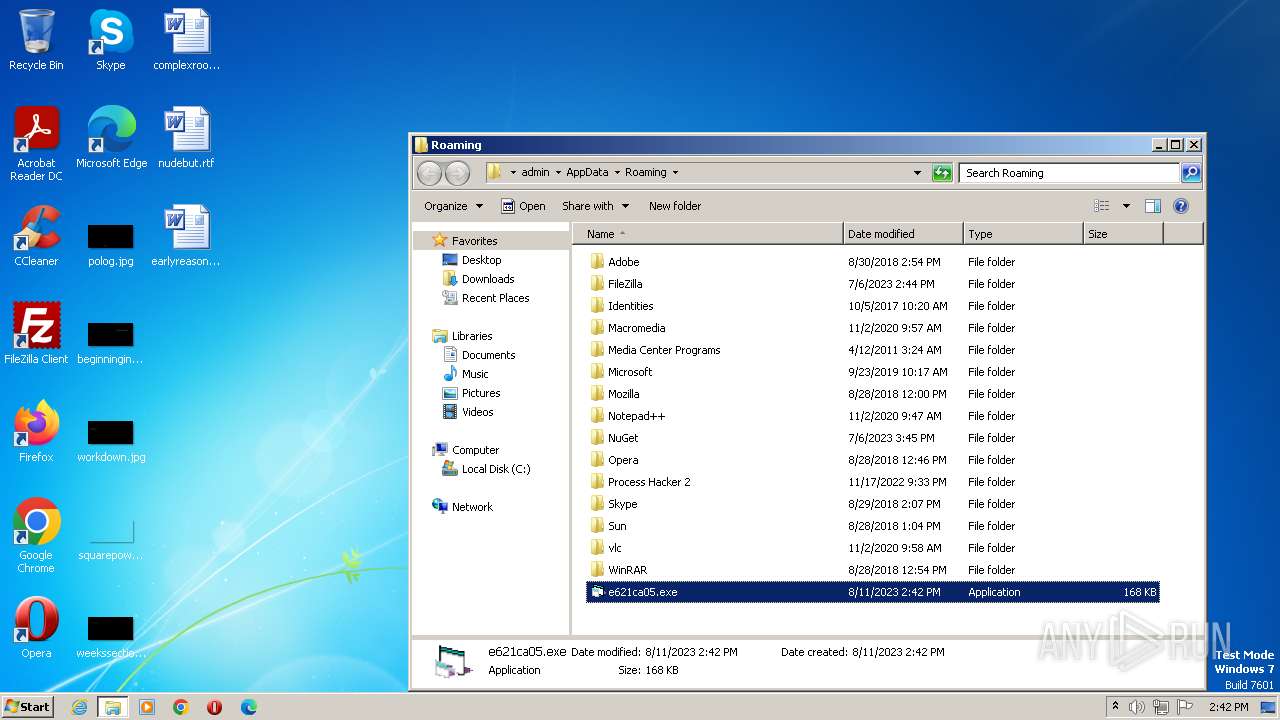
| 2528 | "C:\Users\admin\AppData\Roaming\e621ca05.exe" | C:\Users\admin\AppData\Roaming\e621ca05.exe | — | e621ca05.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2712 | "C:\Users\admin\AppData\Roaming\e621ca05.exe" | C:\Users\admin\AppData\Roaming\e621ca05.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2748 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\System32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3628 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\e621ca05.exe, #1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 810
Read events
6 883
Write events
926
Delete events
1
Modification events
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000F6D6788197A75D498472ACE88906AC8D0000000002000000000010660000000100002000000075B0D7E28E2E17B576E141128F731FE5320CCA30C35292A435B65D5E91F3150B000000000E80000000020000200000000C791686155A322F498D360901A0BC88A787D4ADF186758AE2D9BB16BE317ECD30000000E07A76BA5A881A8B5FF9F7A7FE5833EB2B96D7A240E8CDC394ED7C494DEC5BF8E13DB07B279185F24F9C8B497FA4E70A400000008D71222A7DB9FE2EAB90303DA35140A5A9A6780343B0FFB0C4B233499C2F0735FA041306AFACB24F5B397960A2D4CBA893F7FF12508B7C84A5AE9013C2C0A092 | |||
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 07000000020000000000000006000000010000000C0000000B0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | MRUList |
Value: eabdc | |||
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\194\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000091010000D9020000F53561013F0000004A0000008E0F0D004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000028003E004000A4E75102B8E651020000000000000000000000000000080274E45102000008026CE25102000000000000D26CFFFFFFFF705911750000000000000000A4E251027C900D75000400000000000008E35102FFFFFFFF38EA7000FFFFFFFF080A7400D80E740030EA7000D4E25102F7AF3D7680D0707614F05102081D3E76E4613E766820700008E351020000000071000000BBF2CB00E8E25102A1693E766820700008E351020000000014E551023F613E766820700008E3510200000400000000800400000026E4510298E351025DA5147726E45102D26E147779A51477D6794D7526E4510210E65102000100006400610072E3510226E451026F0061006D0069006E0067005C006D006900630072006F0073006F0066007400CCE351023400000080E35102DE70310033003300350033003800310030003000F8E551025A000000A0E351021DA71477D6610E02D4E351025A00000010E651025C00000011000000104F7000084F7000F8E55102C4E3510220E40000D7F3CB00D0E351025E903E7620E45102D4E3510203943E760000000064561802FCE35102A9933E7664561802A8E45102D8511802BD933E7600000000D8511802A8E4510204E45102010000007F000000130B63004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C000000000001000000514F1D7621D9E2138202000088D9FE010000000000000000000000002CE33A02C0E33A0298E53A02136822762575C567FEFFFFFF514F1D7662001B74880005008202000001000000000000000000000088D9FE018CFF1A748800050001000000FFFFFFFFFFFFFFFFE0C31D7691C41D764E00000000000000000000000000000064E33A02A8C01A74B8E73A021368227625FEC567BCD9FE014EC41D76FE501D760000000088F41A7488000500C11000000000000000000000E454F70001000000FFFFFFFFC11000000C00000088F41A748800050030281D0020E43A02EA531D76D054F7002051F7000000000020E43A0224CE1D76088000007D2F1D7650441A740880000088000500FCFFFFFF0D000000780CFD011100000048512100405121000C00000030C4E71378E43A02C0E40000F3DFE21374E43A025E903376C0E43A0264570000DFDFE21388E43A02929B337668570B024C060000A0E43A02D8520B02ACE43A02110000004851210040512100A0E43A02F8520B0210E5000007DFE213C0E43A025E90337610E53A02C4E43A02039433760000000064570B02ECE43A02A993337664570B0298E53A02D8520B02BD93337600000000D8520B0298E53A02F4E43A02010000007F000000130B63004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C000000000001000000514F1D7621D9E2138202000088D9FE010000000000000000000000002CE33A02C0E33A0298E53A02136822762575C567FEFFFFFF514F1D7662001B74880005008202000001000000000000000000000088D9FE018CFF1A748800050001000000FFFFFFFFFFFFFFFFE0C31D7691C41D764E00000000000000000000000000000064E33A02A8C01A74B8E73A021368227625FEC567BCD9FE014EC41D76FE501D760000000088F41A7488000500C11000000000000000000000E454F70001000000FFFFFFFFC11000000C00000088F41A748800050030281D0020E43A02EA531D76D054F7002051F7000000000020E43A0224CE1D76088000007D2F1D7650441A740880000088000500FCFFFFFF0D000000780CFD011100000048512100405121000C00000030C4E71378E43A02C0E40000F3DFE21374E43A025E903376C0E43A0264570000DFDFE21388E43A02929B337668570B024C060000A0E43A02D8520B02ACE43A02110000004851210040512100A0E43A02F8520B0210E5000007DFE213C0E43A025E90337610E53A02C4E43A02039433760000000064570B02ECE43A02A993337664570B0298E53A02D8520B02BD93337600000000D8520B0298E53A02F4E43A02 | |||
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage\NewShortcuts |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\Shell |
| Operation: | write | Name: | WFlags |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1024 | explorer.exe | C:\Users\admin\AppData\Roaming\Zeeoen.exe | executable | |
MD5:BEB5D494D98FD8ED82C6D5ABB9DC6F36 | SHA256:83B3DDB35DBC64E9A3584B5CBAD78D96DA138250493C8BE0BFCEA275A5C6D921 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
12
DNS requests
13
Threats
66
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1024 | explorer.exe | 199.2.137.21:7777 | xxxd2.com | MICROSOFT-CORP-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.wipmania.com |
| unknown |
xxxd2.com |
| malicious |
xxxd1.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1024 | explorer.exe | A Network Trojan was detected | ET MALWARE Likely Bot Nick in IRC (USA +..) |
1024 | explorer.exe | A Network Trojan was detected | ET MALWARE Likely Bot Nick in IRC (Country Code ISO 3166-1 alpha-3) |
1024 | explorer.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS IRC - NICK and 3 Letter Country Code |
1024 | explorer.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS IRC - NICK and Possible Windows XP/7 |
1024 | explorer.exe | Misc activity | ET INFO IRC Nick change on non-standard port |
1024 | explorer.exe | A Network Trojan was detected | ET MALWARE Likely Bot Nick in IRC (USA +..) |
1024 | explorer.exe | A Network Trojan was detected | ET MALWARE Likely Bot Nick in IRC (Country Code ISO 3166-1 alpha-3) |
1024 | explorer.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS IRC - NICK and 3 Letter Country Code |
1024 | explorer.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS IRC - NICK and Possible Windows XP/7 |
1024 | explorer.exe | Misc activity | ET INFO IRC Nick change on non-standard port |
13 ETPRO signatures available at the full report