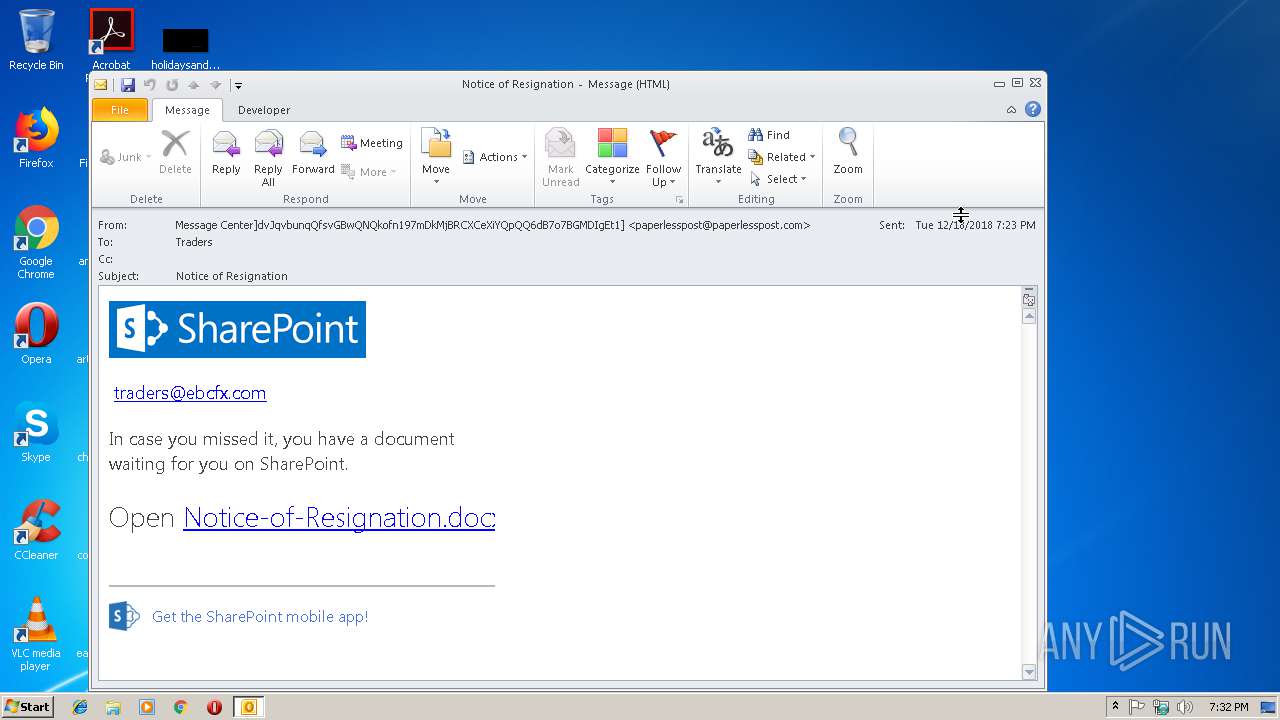
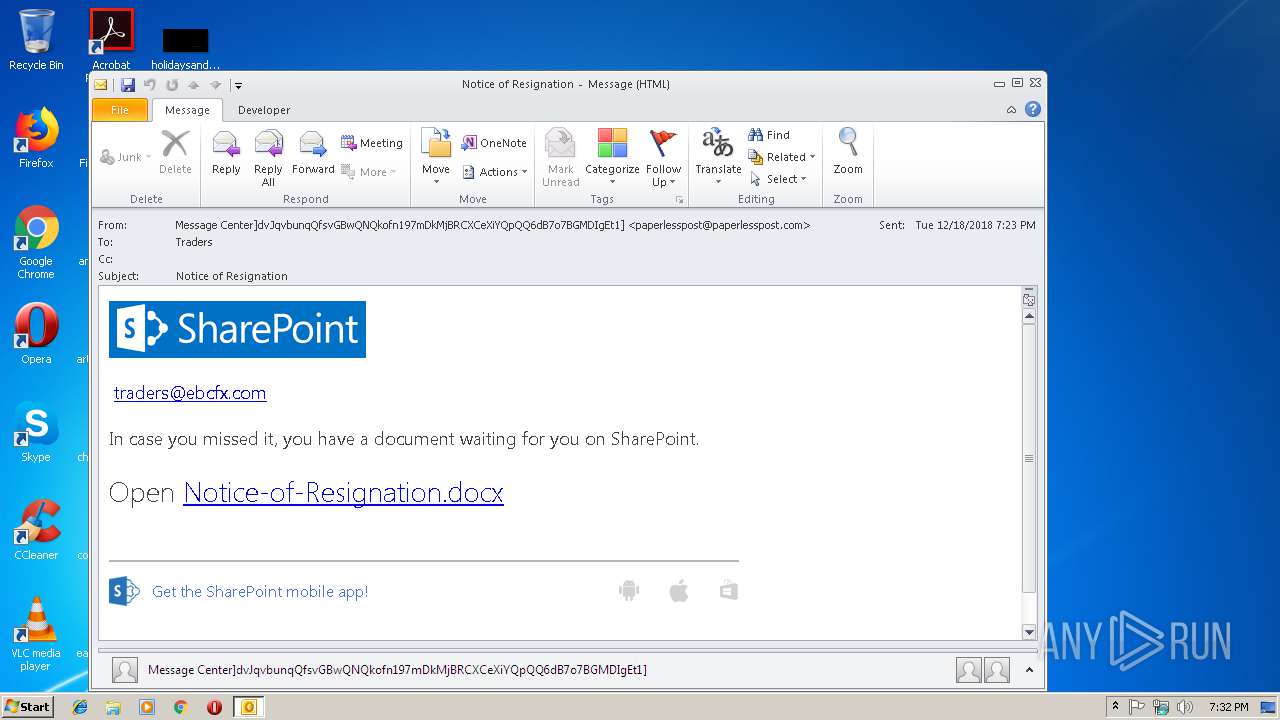
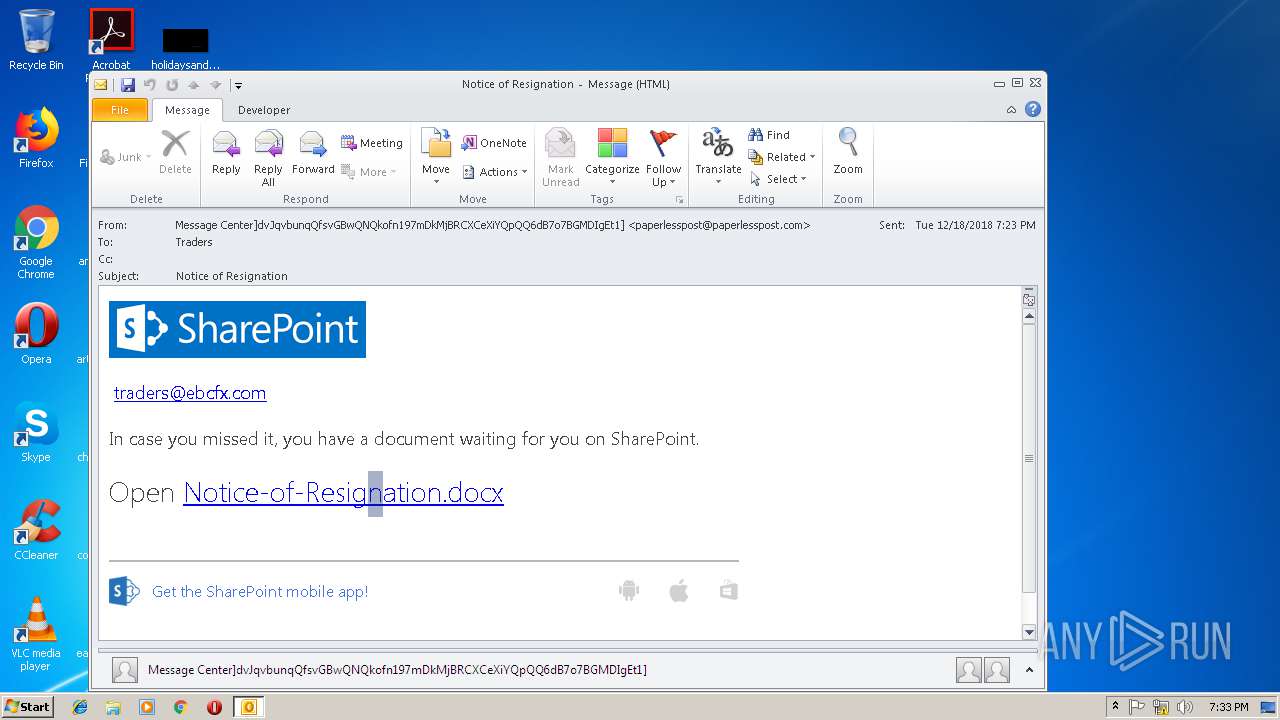
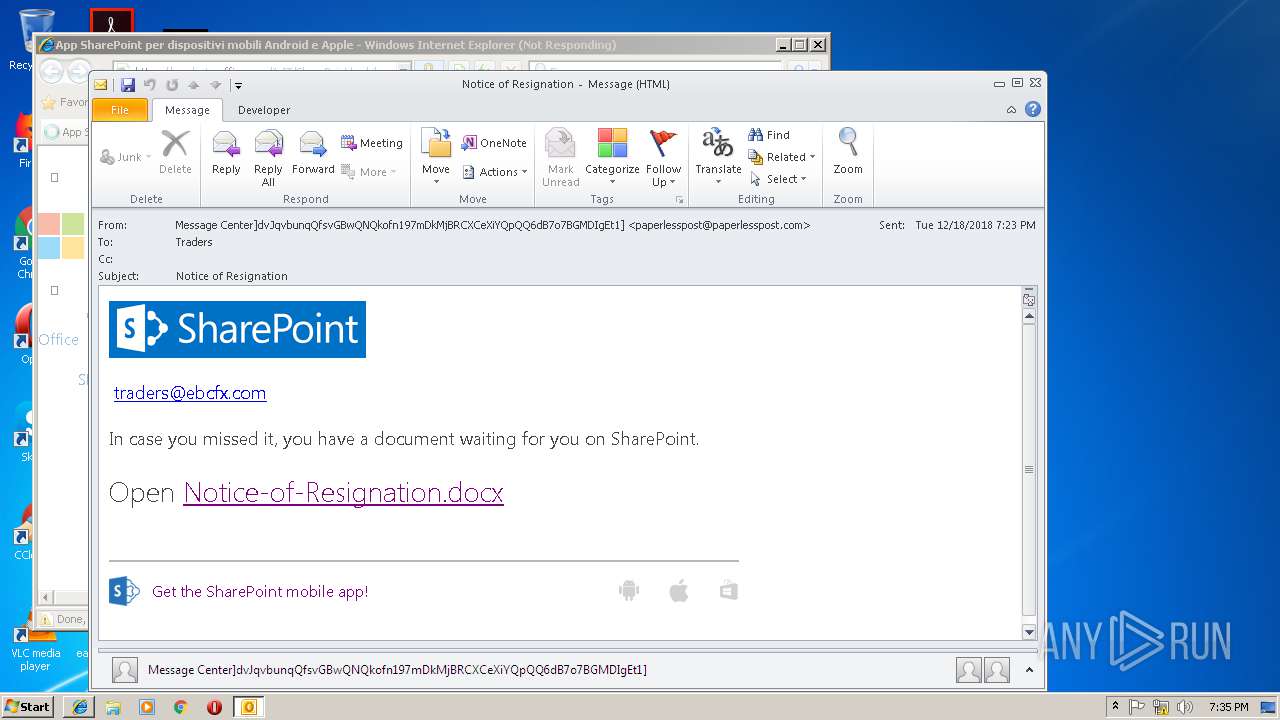
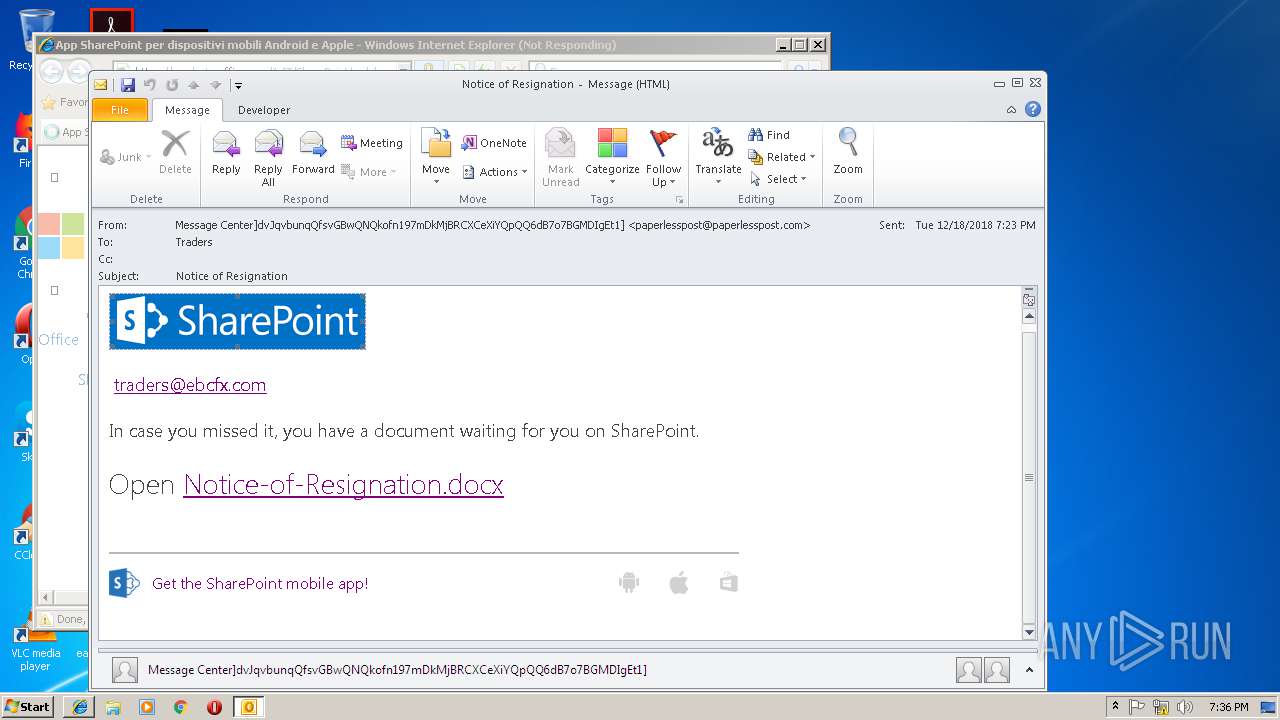
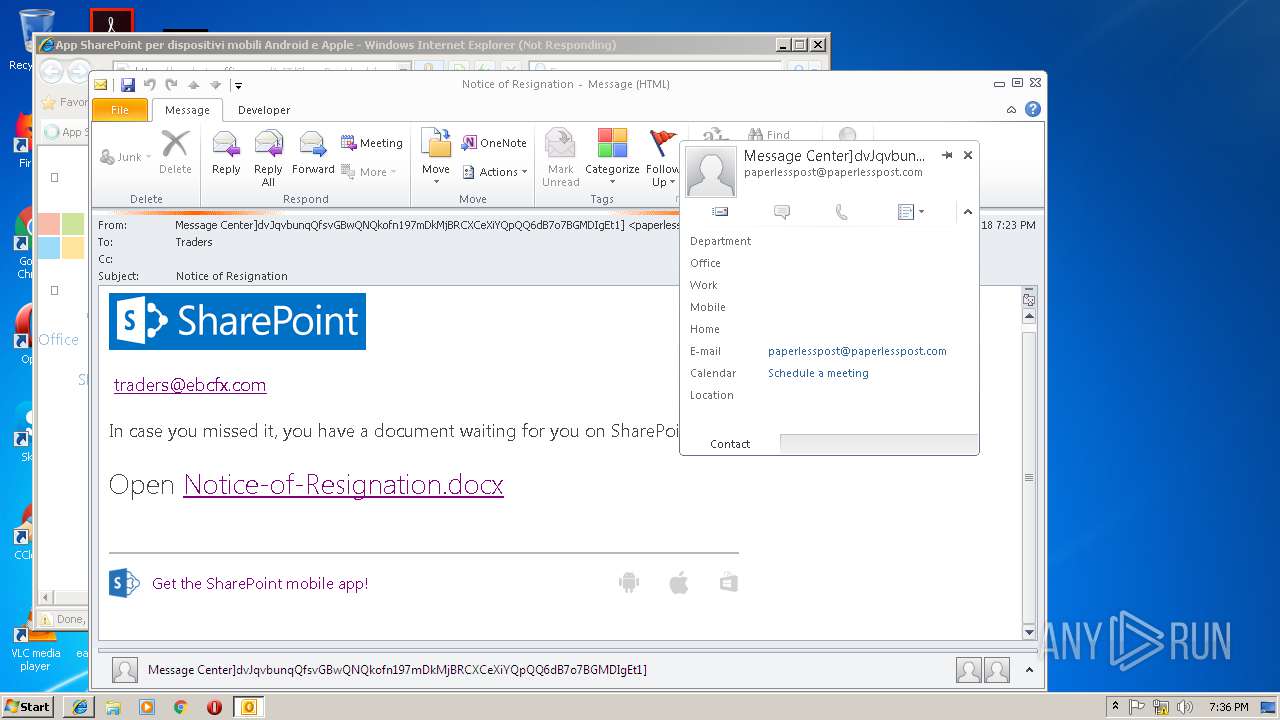
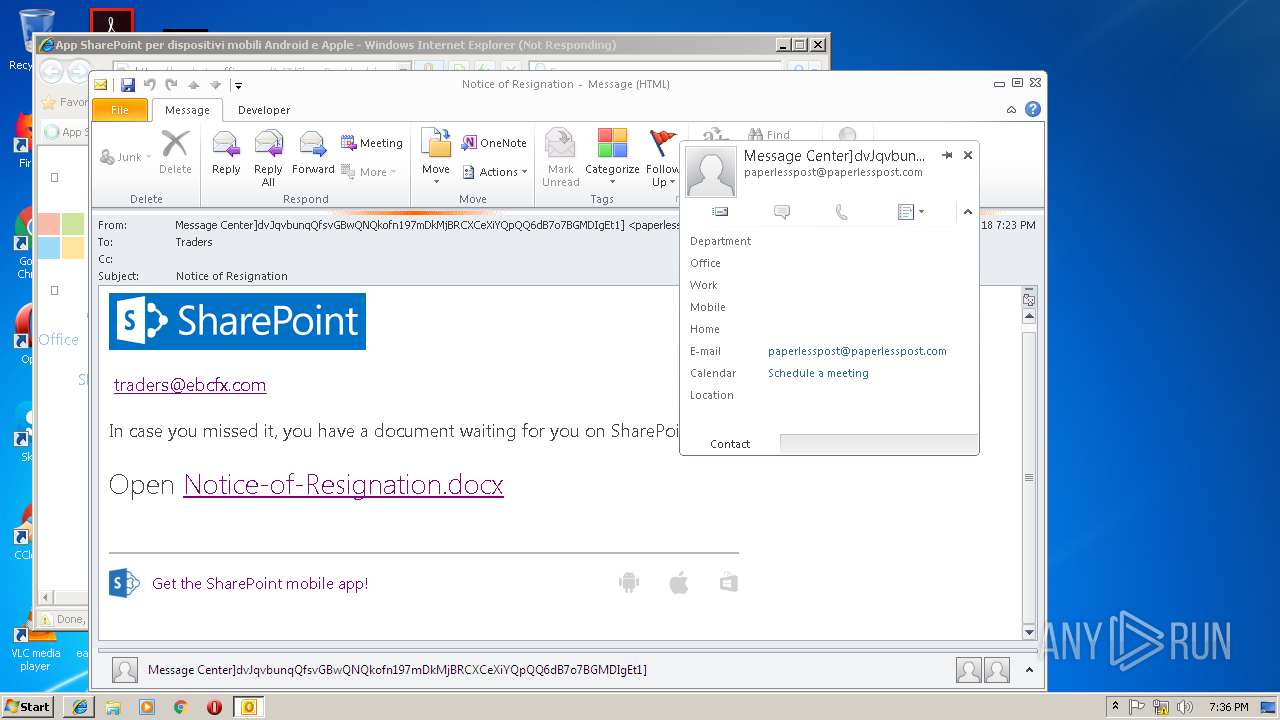
| File name: | Notice of Resignation (27.2 KB).msg |
| Full analysis: | https://app.any.run/tasks/a2834eb5-6dea-4a84-a227-6b45256665e2 |
| Verdict: | Malicious activity |
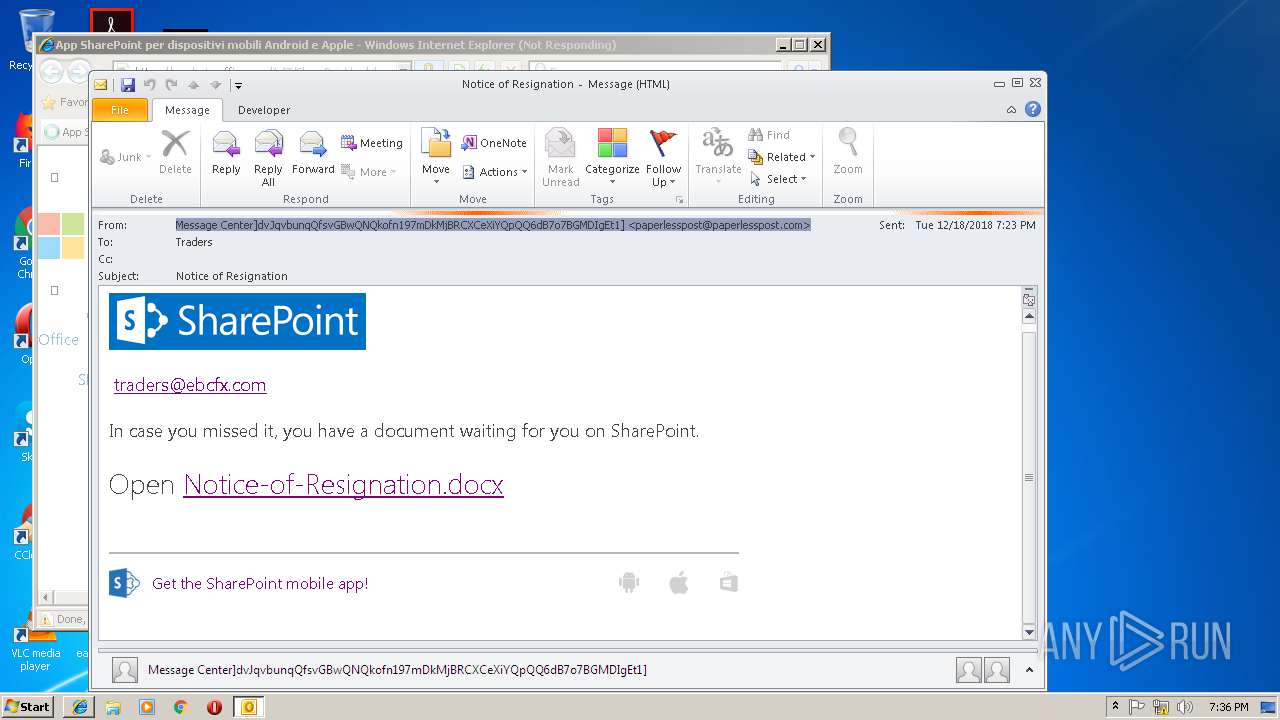
| Analysis date: | December 18, 2018, 19:32:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 7061D51CD470DA15BF44F5080D1F3AB7 |
| SHA1: | BBDC8E00C3CC9B10B564DDA0573737BCD8A89BFE |
| SHA256: | 839513F61048A68576F13F233773615EA74CD5515466D6C91823DA792A285AB8 |
| SSDEEP: | 768:fuguwr+t35jADEhJp+jdK9SETIQF3U+O6QUS+M7TK/dy/9b:f7S9ZfTIQFNrQr/ |
MALICIOUS
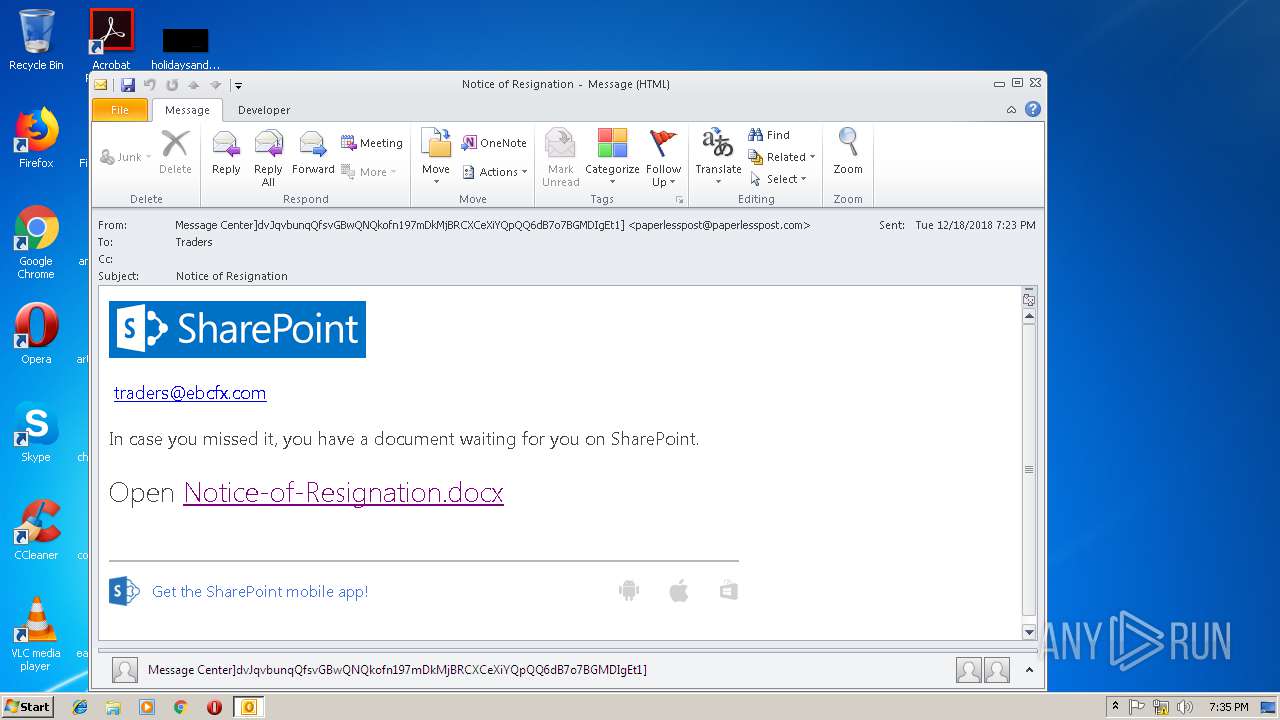
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2968)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2968)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2968)
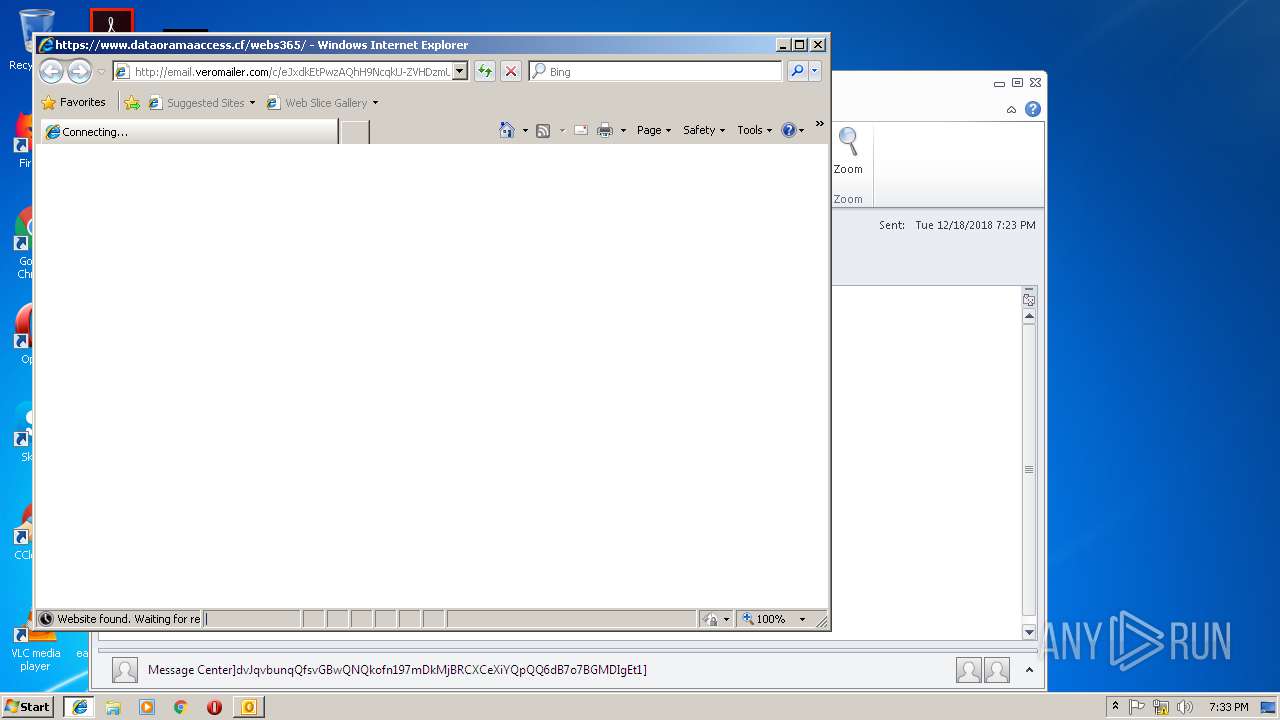
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2968)
Starts itself from another location
- OUTLOOK.EXE (PID: 2968)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2968)
- OUTLOOK.EXE (PID: 3696)
- OUTLOOK.EXE (PID: 2404)
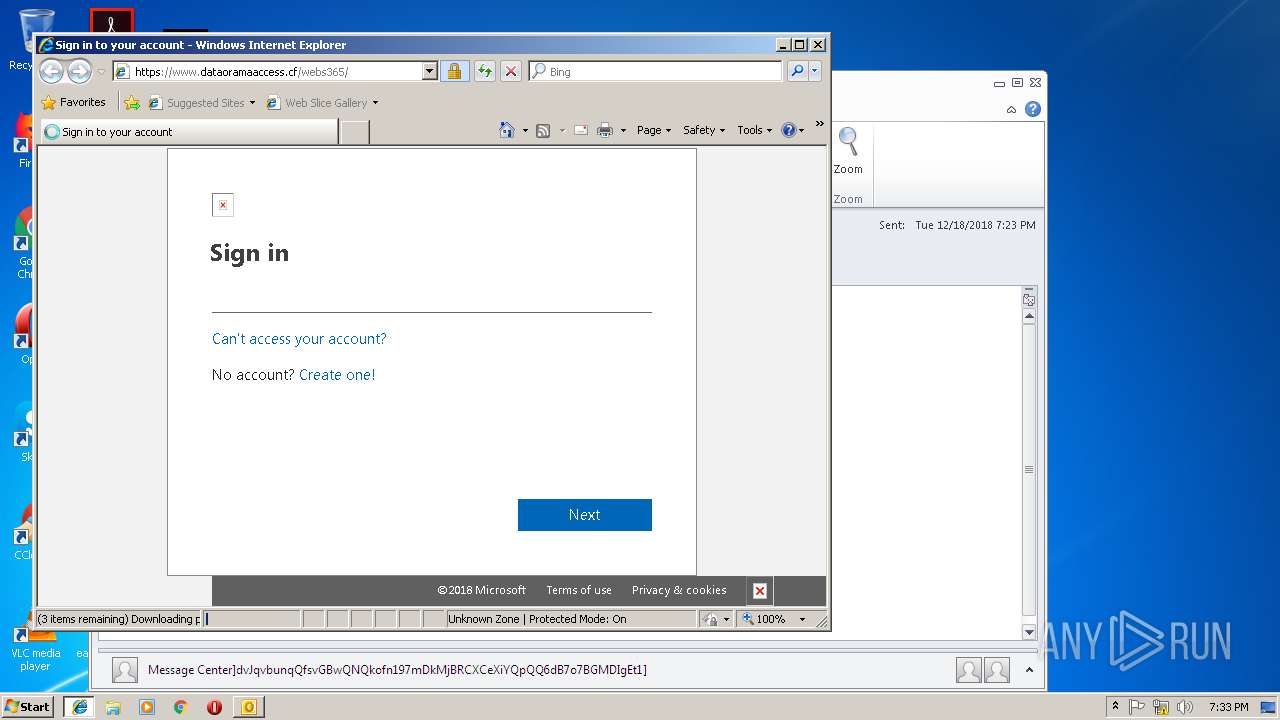
Changes internet zones settings
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 3980)
Application launched itself
- iexplore.exe (PID: 3000)
Reads Internet Cache Settings
- iexplore.exe (PID: 3732)
- iexplore.exe (PID: 2160)
Creates files in the user directory
- iexplore.exe (PID: 3732)
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 2160)
Reads internet explorer settings
- iexplore.exe (PID: 3732)
- iexplore.exe (PID: 2160)
Reads settings of System Certificates
- iexplore.exe (PID: 3000)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3000)
Changes settings of System certificates
- iexplore.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
42
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2160 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3980 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Notice of Resignation (27.2 KB).msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Internet Explorer\iexplore.exe" http://email.veromailer.com/c/eJxdkEtPwzAQhH9NcqkU-ZVHDzmURhVcECeu0dbZtkZ2HNkmgX-PnQoISLa02hnNN7YEM4G6jln54FCqSeEY-sEaUHHVtfepkNbk8teJcal7_35-QxmS7RG1tvnQAm_IfuucwSkIyq5hRzsGZ3WuWkZoQ1m8TVlSUdCiPnLKu1MlDoLQjtFMkBldgmt0K_7WMlpXDakGyRu4CMJFxc97ZBJZLRgA33I33TLWvDicFS4Z2-_uTXV7C2HyGT9k7BTPsizFAAGsAwMgJXpfyEsS8Ox5VeaudR_GhbXYNbX6_yWTswnYj2AwUSNyjIF696p8fP7uaZRbe_icVtszLl5jCOj-qGgmDQF_0rbi99irIUkloYRXX6MElhk | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
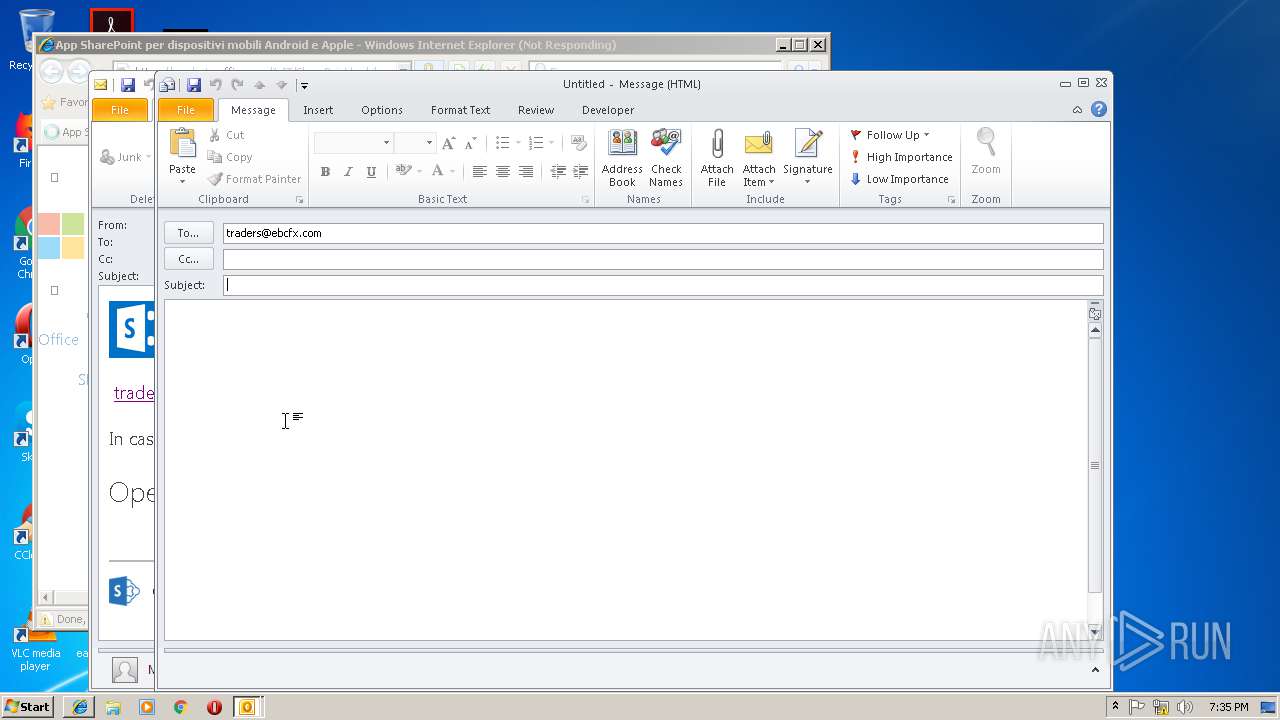
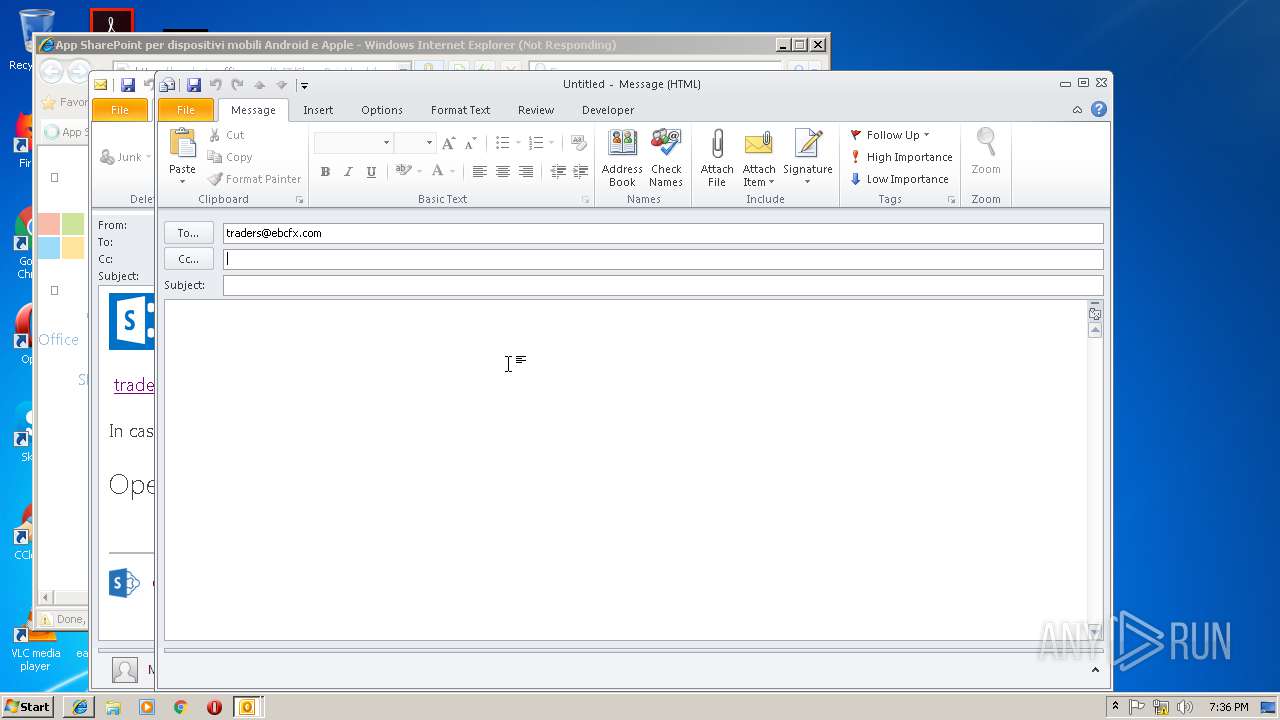
| 3696 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:traders@ebcfx.com" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3732 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3000 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3980 | "C:\Program Files\Internet Explorer\iexplore.exe" https://aka.ms/getspmobile | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 311
Read events
1 710
Write events
568
Delete events
33
Modification events
| (PID) Process: | (2968) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2968) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2968) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | ha? |
Value: 68613F00980B0000010000000000000000000000 | |||
| (PID) Process: | (2968) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 980B0000641ED6680897D40100000000 | |||
| (PID) Process: | (2968) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2968) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219826080 | |||
| (PID) Process: | (2968) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2968) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2968) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2968) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1301413909 | |||
Executable files
0
Suspicious files
8
Text files
80
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA5E8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3732 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\webs365[1].txt | — | |
MD5:— | SHA256:— | |||
| 2968 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2968 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3E1302DA.dat | image | |
MD5:— | SHA256:— | |||
| 2968 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CCA8EF99.dat | image | |
MD5:— | SHA256:— | |||
| 2968 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\55C9FF8.dat | image | |
MD5:— | SHA256:— | |||
| 2968 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1640113.dat | image | |
MD5:— | SHA256:— | |||
| 2968 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\19FC20C6.dat | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
60
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2968 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3732 | iexplore.exe | GET | 302 | 52.72.252.15:80 | http://email.veromailer.com/c/eJxdkEtPwzAQhH9NcqkU-ZVHDzmURhVcECeu0dbZtkZ2HNkmgX-PnQoISLa02hnNN7YEM4G6jln54FCqSeEY-sEaUHHVtfepkNbk8teJcal7_35-QxmS7RG1tvnQAm_IfuucwSkIyq5hRzsGZ3WuWkZoQ1m8TVlSUdCiPnLKu1MlDoLQjtFMkBldgmt0K_7WMlpXDakGyRu4CMJFxc97ZBJZLRgA33I33TLWvDicFS4Z2-_uTXV7C2HyGT9k7BTPsizFAAGsAwMgJXpfyEsS8Ox5VeaudR_GhbXYNbX6_yWTswnYj2AwUSNyjIF696p8fP7uaZRbe_icVtszLl5jCOj-qGgmDQF_0rbi99irIUkloYRXX6MElhk | US | html | 283 b | whitelisted |
3980 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3000 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3732 | iexplore.exe | 52.72.252.15:80 | email.veromailer.com | Amazon.com, Inc. | US | unknown |
3000 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
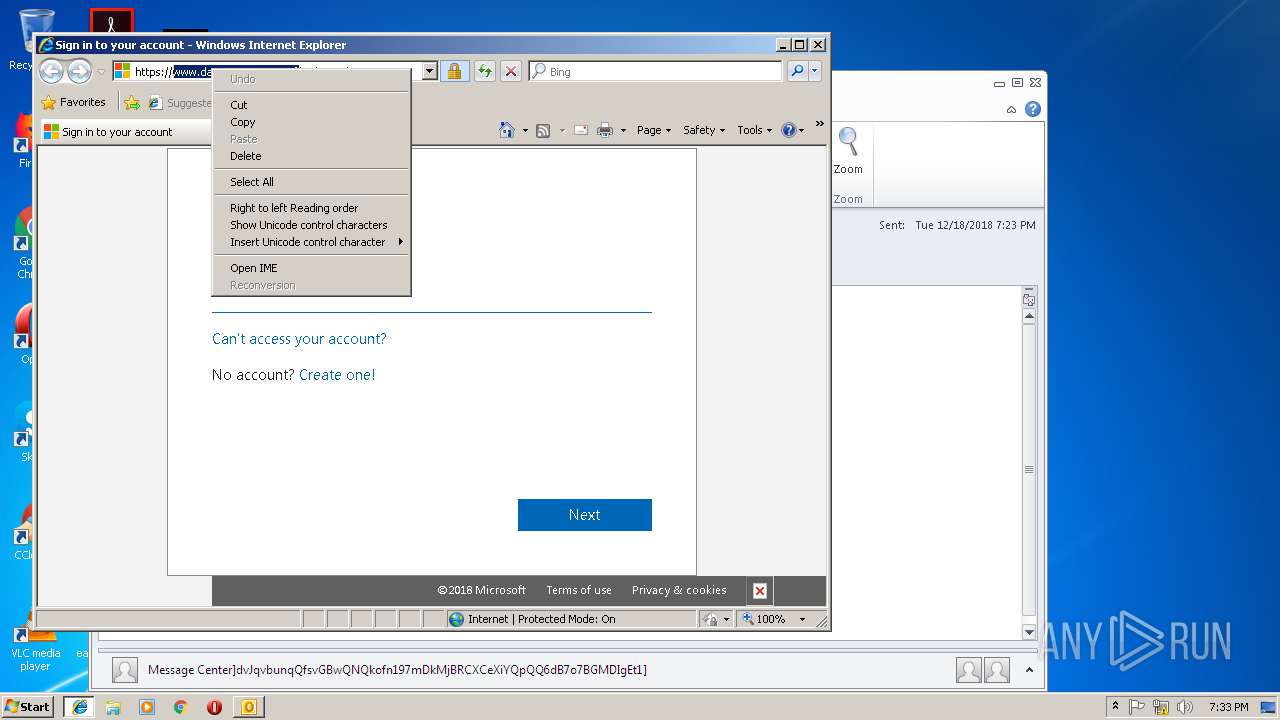
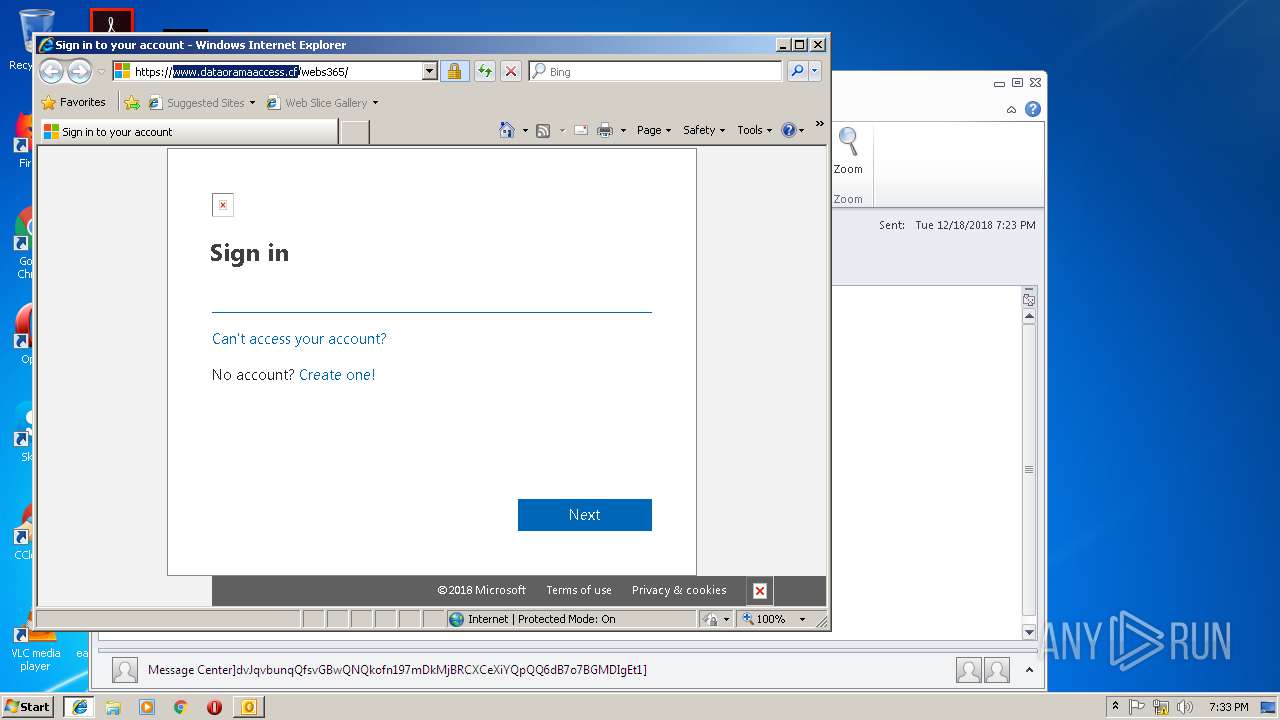
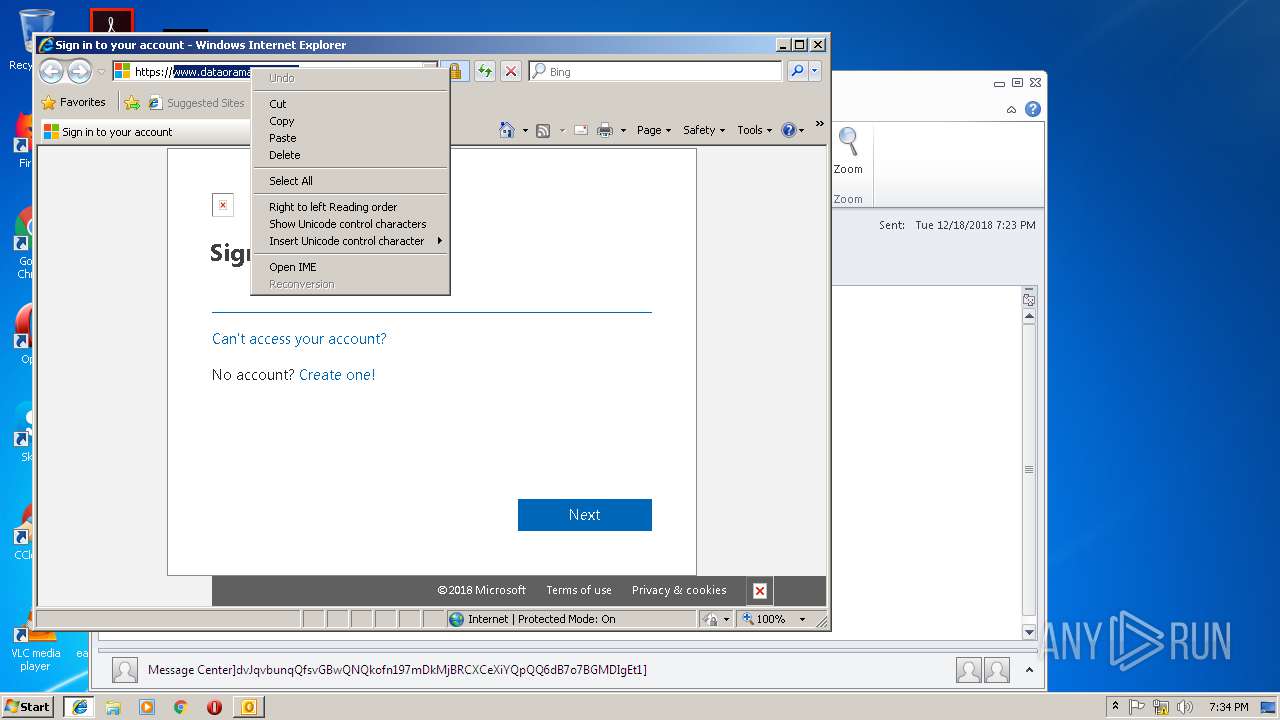
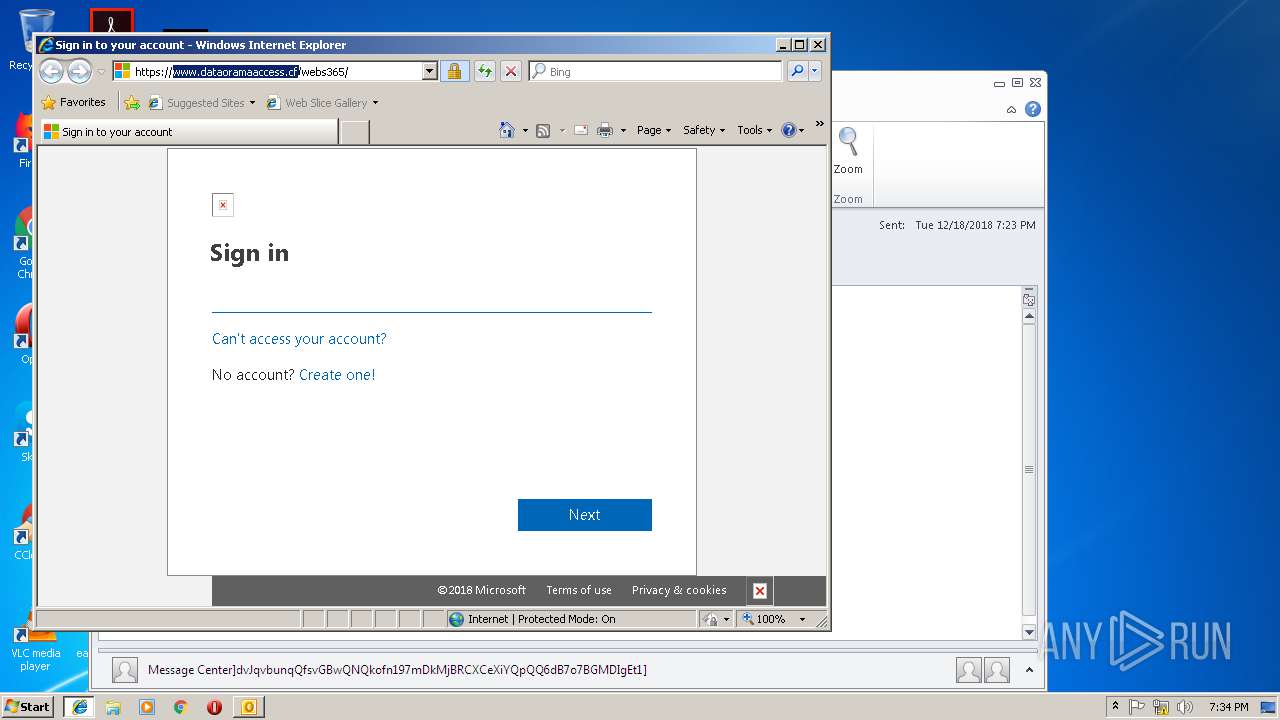
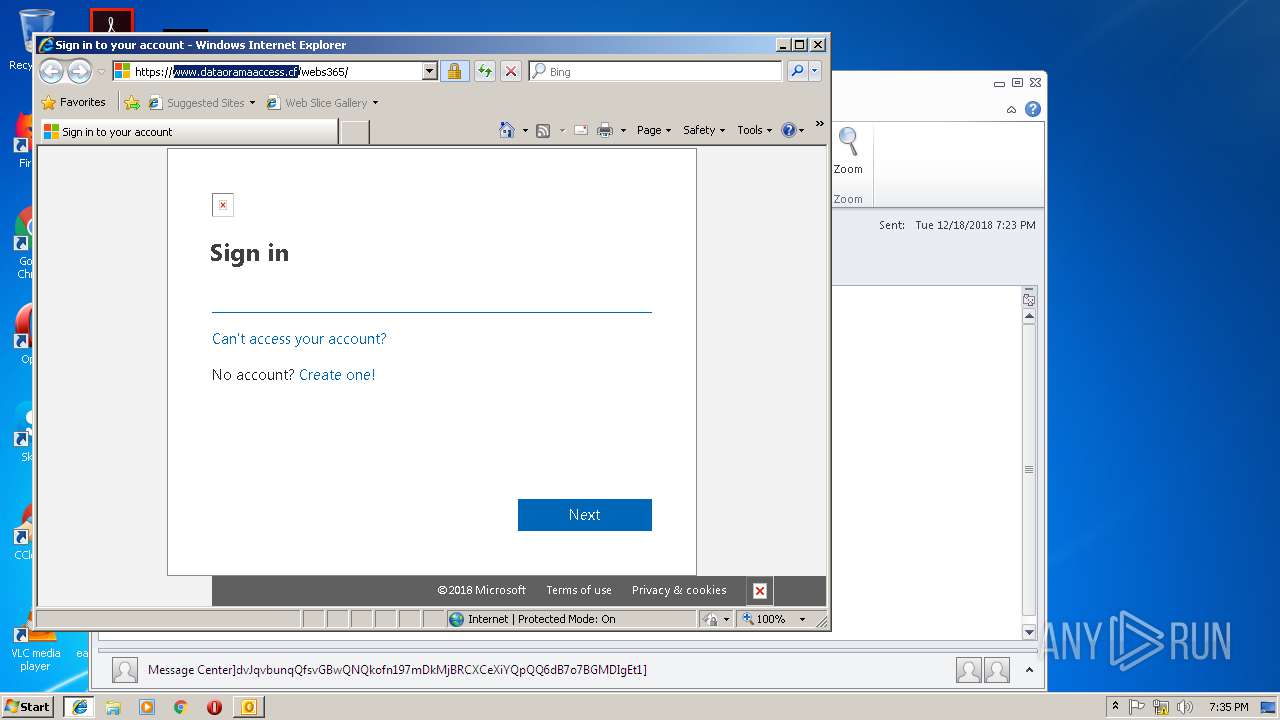
3732 | iexplore.exe | 64.137.233.115:443 | www.dataoramaaccess.cf | 2267921 ONTARIO LTD | CA | suspicious |
3000 | iexplore.exe | 64.137.233.115:443 | www.dataoramaaccess.cf | 2267921 ONTARIO LTD | CA | suspicious |
2160 | iexplore.exe | 23.66.21.99:443 | aka.ms | Akamai Technologies, Inc. | NL | whitelisted |
2160 | iexplore.exe | 2.21.37.228:443 | query.prod.cms.rt.microsoft.com | GTT Communications Inc. | FR | unknown |
2160 | iexplore.exe | 152.199.19.160:443 | ajax.aspnetcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2160 | iexplore.exe | 2.18.233.62:443 | c.s-microsoft.com | Akamai International B.V. | — | whitelisted |
2160 | iexplore.exe | 23.8.8.86:443 | mem.gfx.ms | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
email.veromailer.com |
| whitelisted |
www.dataoramaaccess.cf |
| suspicious |
www.bing.com |
| whitelisted |
aka.ms |
| whitelisted |
products.office.com |
| whitelisted |
ajax.aspnetcdn.com |
| whitelisted |
statics-uhf-eus.akamaized.net |
| whitelisted |
mem.gfx.ms |
| whitelisted |
query.prod.cms.rt.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |