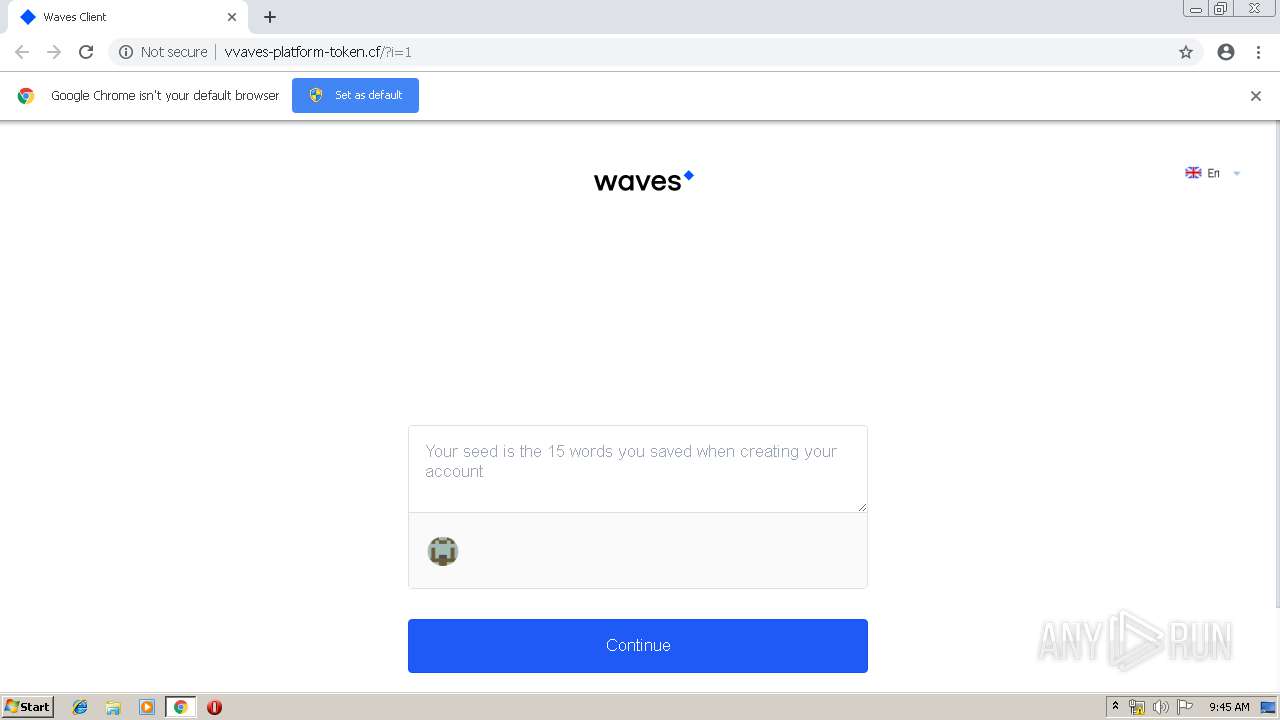
| URL: | http://vvaves-platform-token.cf |
| Full analysis: | https://app.any.run/tasks/6e21777b-6828-440c-a05c-112ab608e1dd |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 08:44:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CEB4E68743E9C85B5869556519DD6CF6 |
| SHA1: | C41B056955C1029447E2ADC031BDDC2B2F1FC7B2 |
| SHA256: | 839436DA89AE038036F7C2B2BE63177B3C14293B7661F4D096E25942F9ED4131 |
| SSDEEP: | 3:N1KI8KvALLUn:CIfvALLU |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2140)
INFO
Application launched itself
- chrome.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13935878691234937599 --mojo-platform-channel-handle=4128 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11327663617446382040 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11327663617446382040 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --service-pipe-token=927289249614774528 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=927289249614774528 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14068968182231203952 --mojo-platform-channel-handle=4220 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://vvaves-platform-token.cf | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15486281259383358646 --mojo-platform-channel-handle=2908 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6368398680746360677 --mojo-platform-channel-handle=4140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13742517874643176665 --mojo-platform-channel-handle=4092 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1621072883780344037 --mojo-platform-channel-handle=4164 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --service-pipe-token=13326005839914048453 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13326005839914048453 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
550
Read events
464
Write events
81
Delete events
5
Modification events
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2140-13205407496860000 |
Value: 259 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
10
Text files
164
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c1a2eefa-3fde-41cf-b3d9-571036810192.tmp | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
20
DNS requests
11
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2140 | chrome.exe | GET | 301 | 31.22.4.13:80 | http://thefreecpanel.com/ | GB | — | — | unknown |
2140 | chrome.exe | GET | 200 | 185.27.134.111:80 | http://vvaves-platform-token.cf/Waves%20Client_files/waves-client-styles-1.0.0-beta.13.css | GB | text | 71.2 Kb | malicious |
2140 | chrome.exe | GET | 302 | 185.27.134.111:80 | http://vvaves-platform-token.cf/img/icons/arrow-select.svg | GB | html | 208 b | malicious |
2140 | chrome.exe | GET | 200 | 185.27.134.111:80 | http://vvaves-platform-token.cf/ | GB | html | 561 b | malicious |
2140 | chrome.exe | GET | 200 | 185.27.134.111:80 | http://vvaves-platform-token.cf/?i=1 | GB | html | 1.75 Kb | malicious |
2140 | chrome.exe | GET | 200 | 185.27.134.111:80 | http://vvaves-platform-token.cf/bb.png | GB | image | 451 b | malicious |
2140 | chrome.exe | GET | 200 | 185.27.134.111:80 | http://vvaves-platform-token.cf/data.png | GB | image | 1.25 Kb | malicious |
2140 | chrome.exe | GET | 302 | 185.27.134.111:80 | http://vvaves-platform-token.cf/img/icons/flags/en.svg | GB | html | 208 b | malicious |
2140 | chrome.exe | GET | 302 | 185.27.134.111:80 | http://vvaves-platform-token.cf/img/icons/waves_logo.svg | GB | html | 208 b | malicious |
2140 | chrome.exe | GET | 302 | 185.27.134.111:80 | http://vvaves-platform-token.cf/fonts/roboto7.woff2 | GB | html | 208 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2140 | chrome.exe | 31.22.4.13:80 | thefreecpanel.com | Wildcard UK Limited | GB | unknown |
2140 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 31.22.4.13:443 | thefreecpanel.com | Wildcard UK Limited | GB | unknown |
2140 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 172.217.23.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 87.245.198.16:80 | r5---sn-gxuog0-axqe.gvt1.com | RETN Limited | RU | whitelisted |
2140 | chrome.exe | 185.27.134.111:80 | vvaves-platform-token.cf | Wildcard UK Limited | GB | malicious |
2140 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 172.217.16.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 172.217.22.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
vvaves-platform-token.cf |
| malicious |
clients1.google.com |
| whitelisted |
thefreecpanel.com |
| unknown |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-gxuog0-axqe.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |
2140 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Encryptor aes.js script (seen PedCont ransomware) |
2140 | chrome.exe | Potentially Bad Traffic | ET INFO Possible Phish - Saved Website Comment Observed |