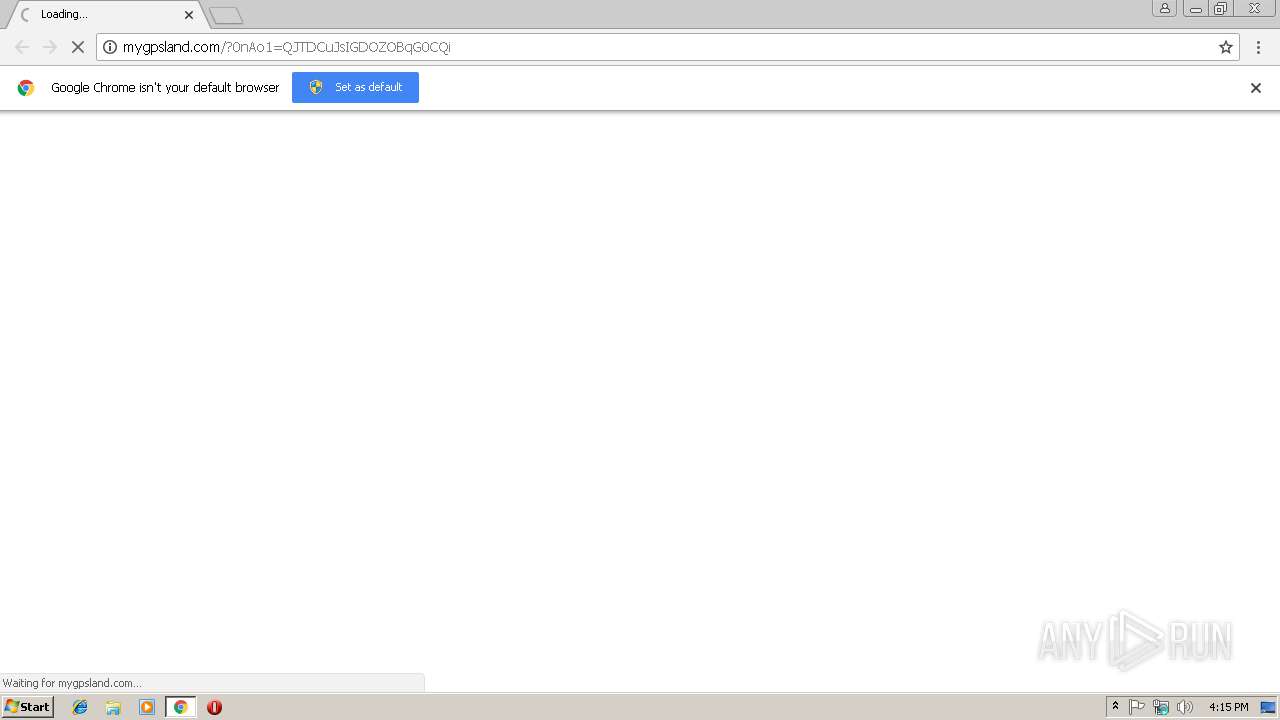
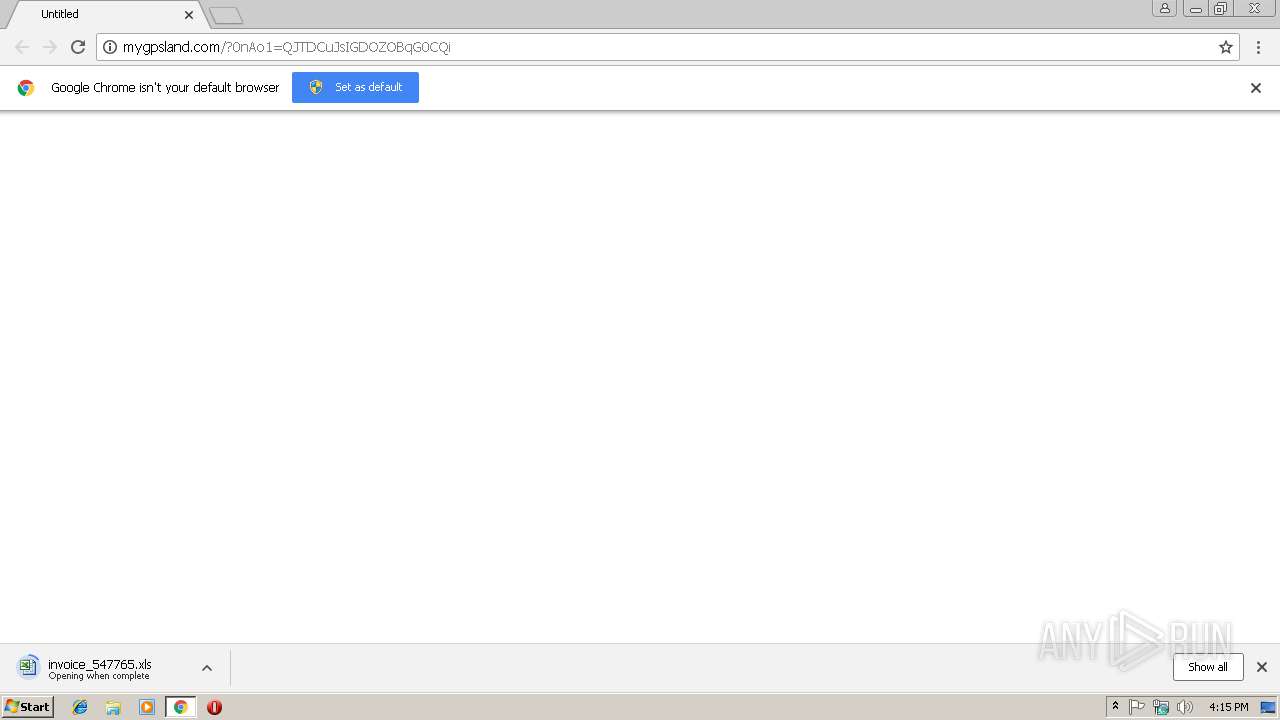
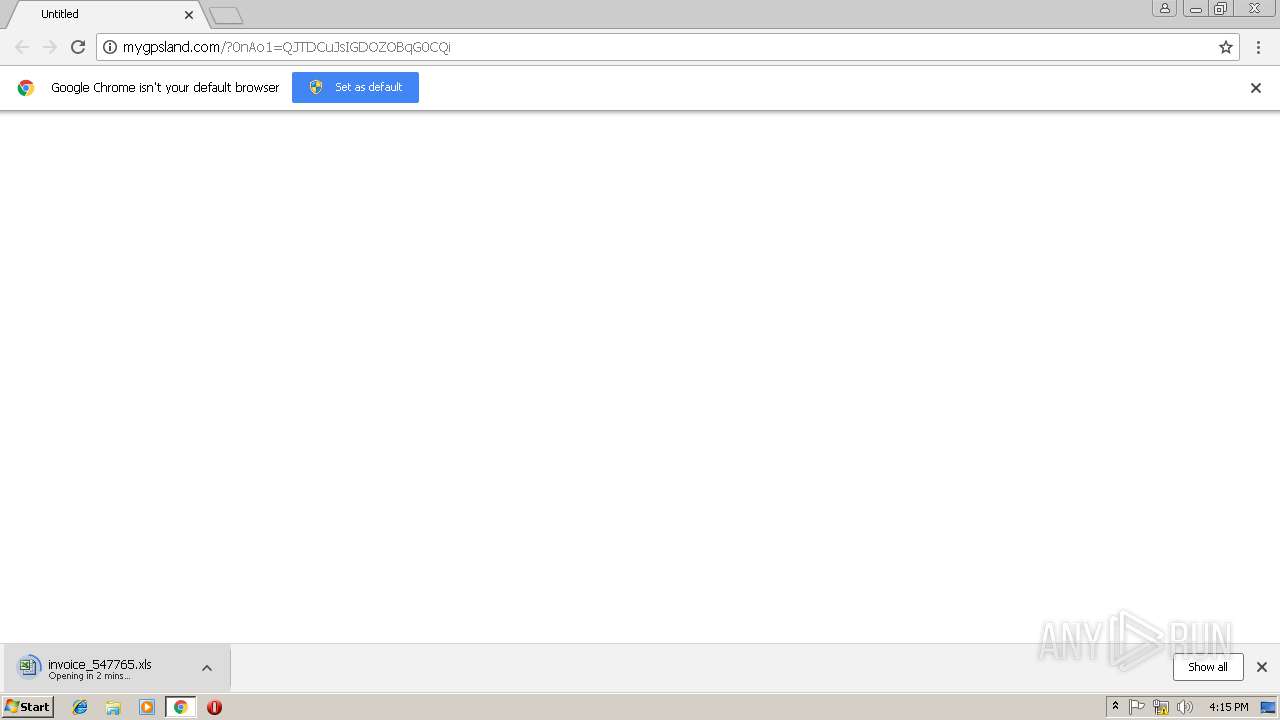
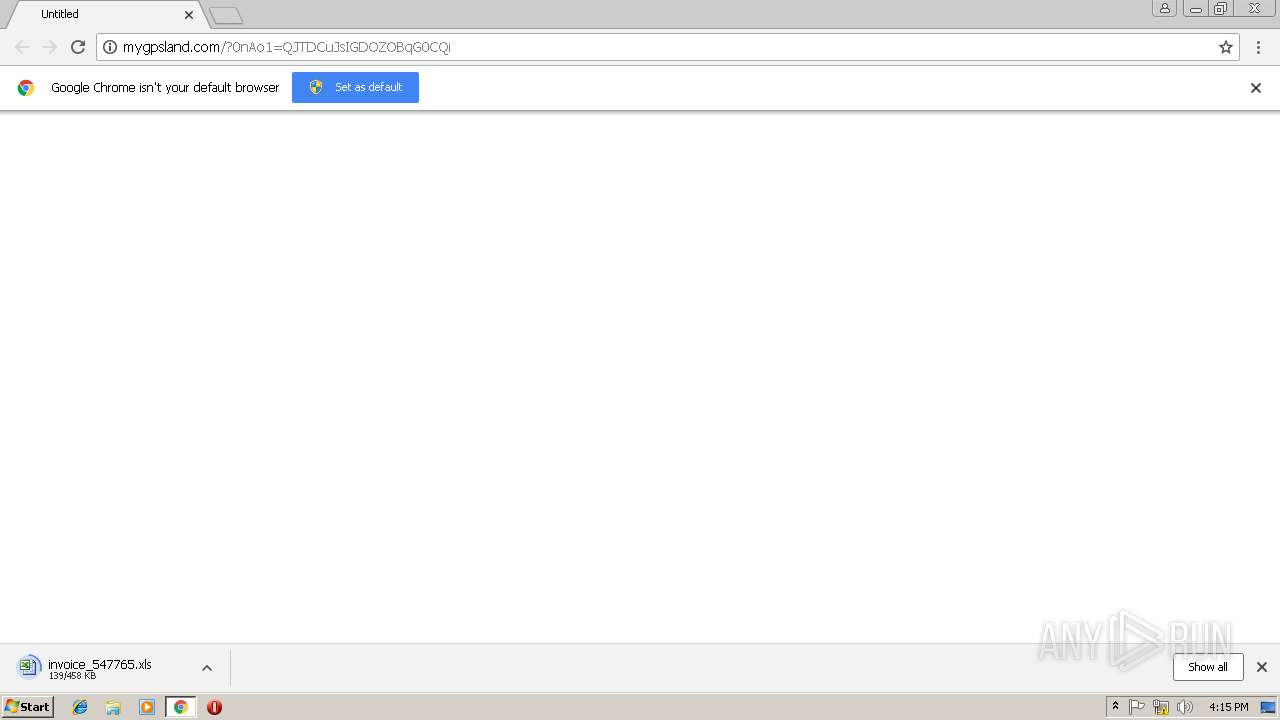
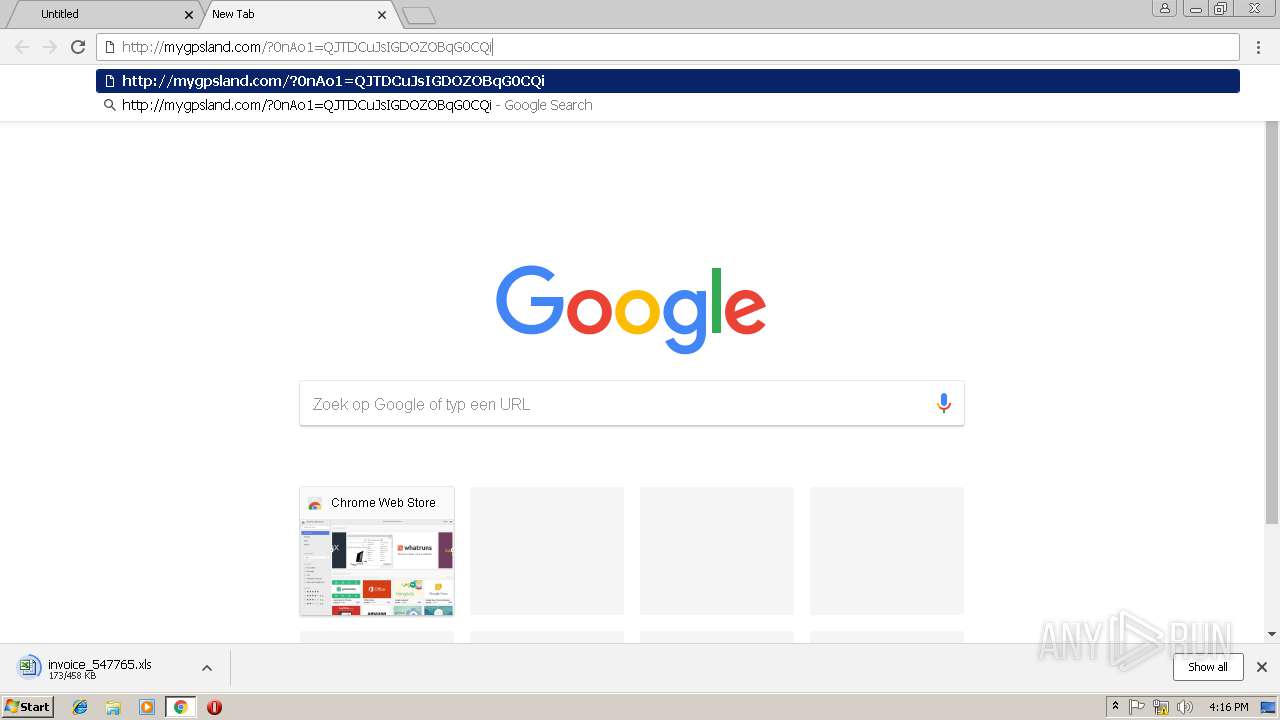
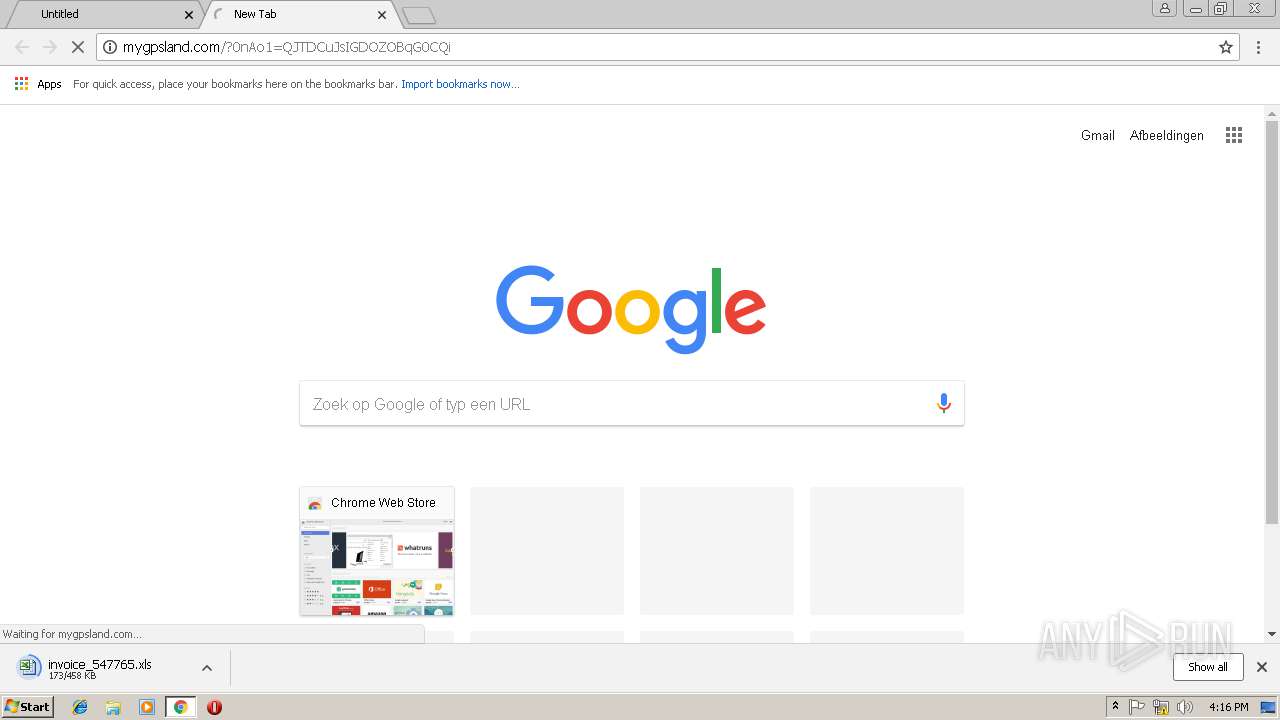
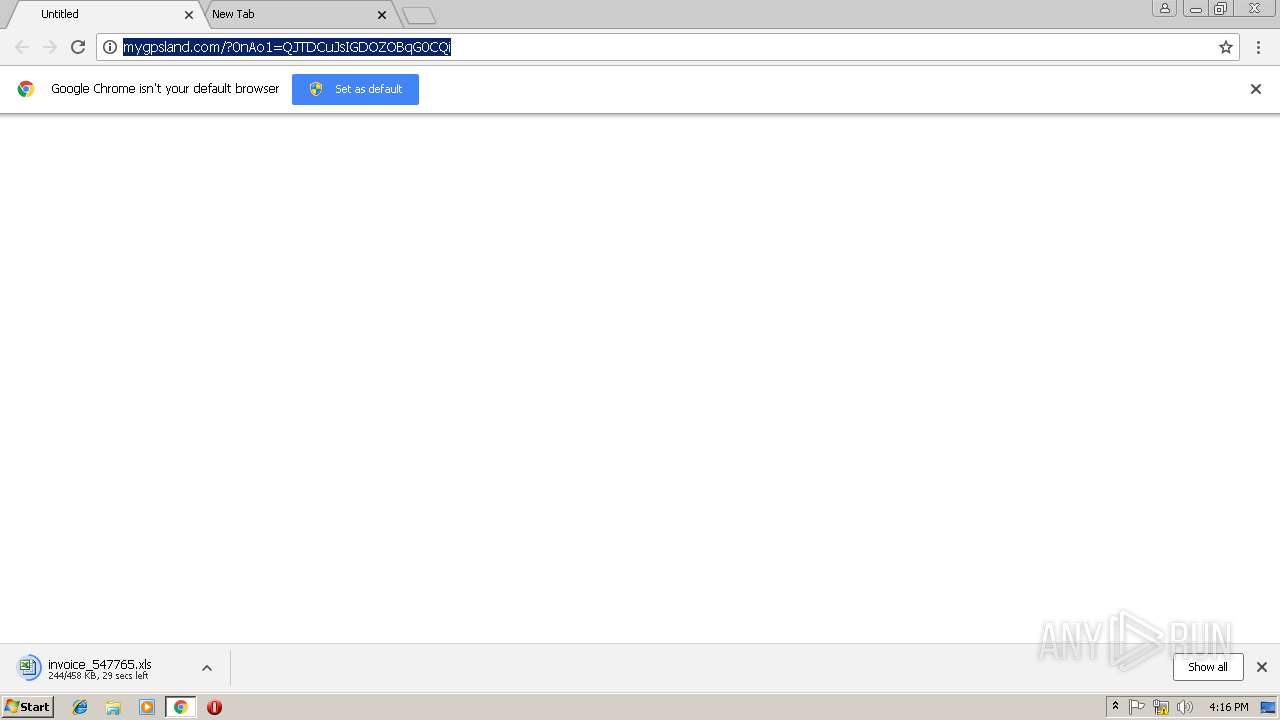
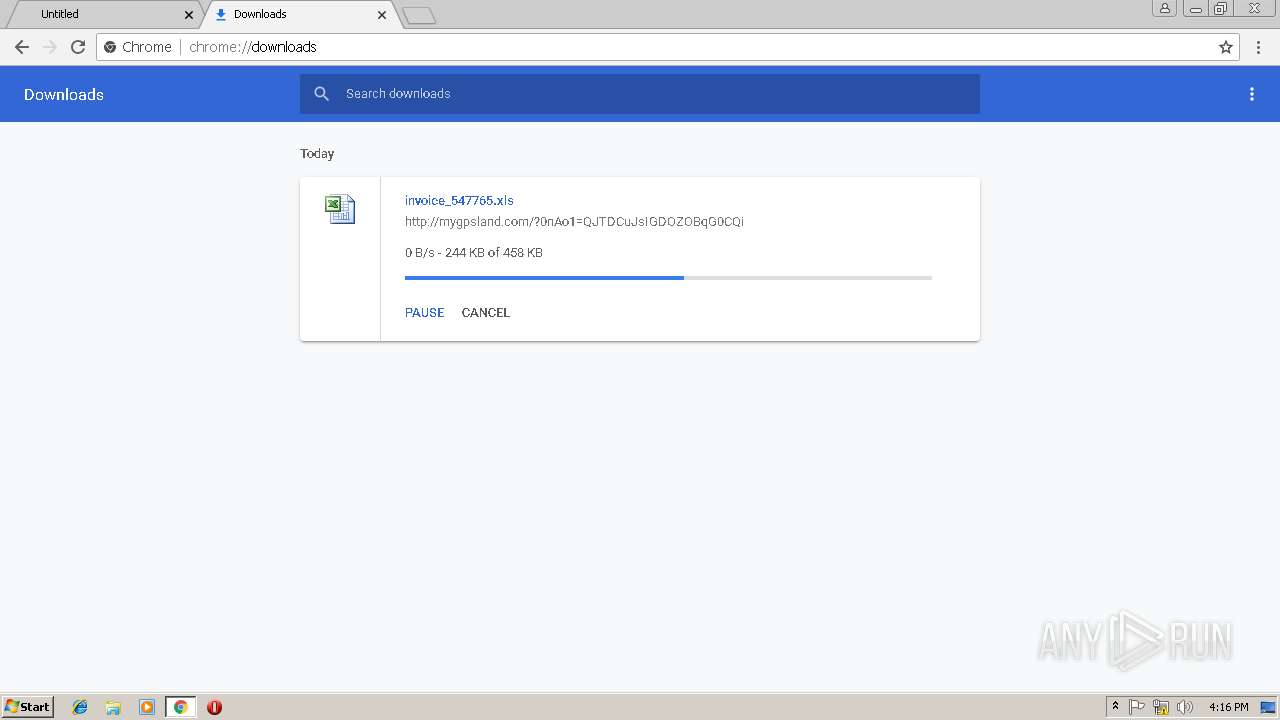
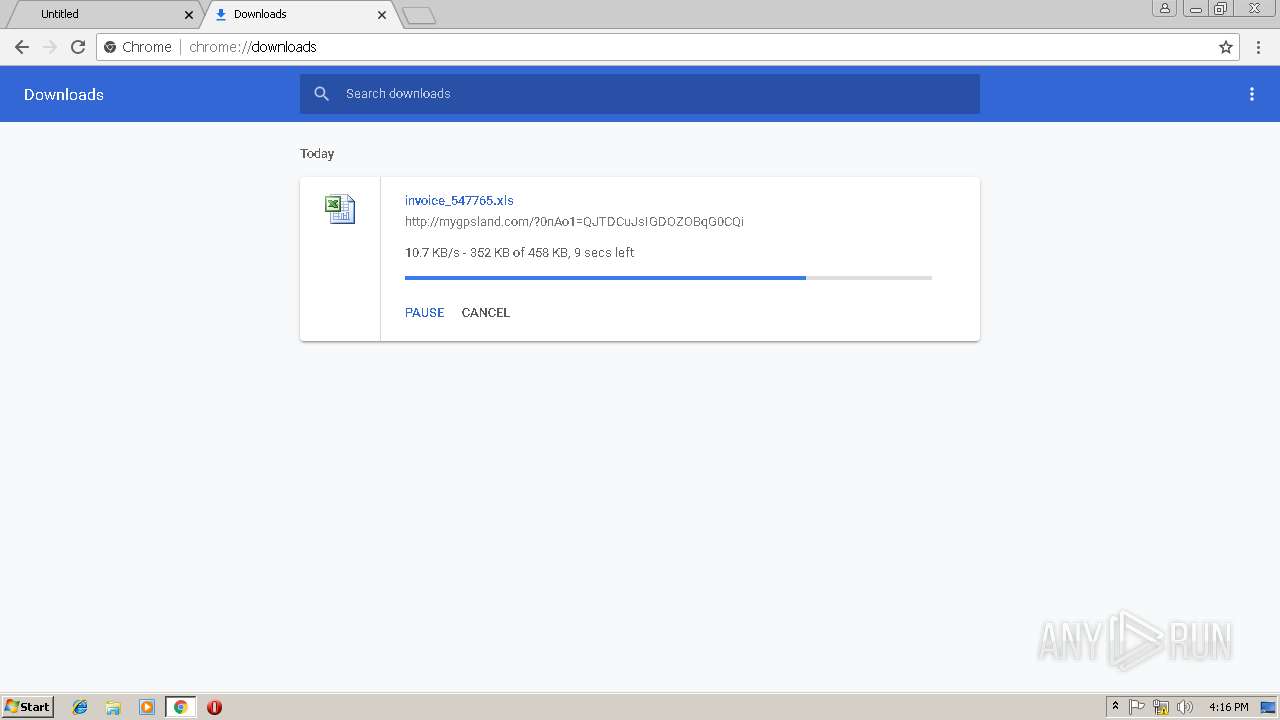
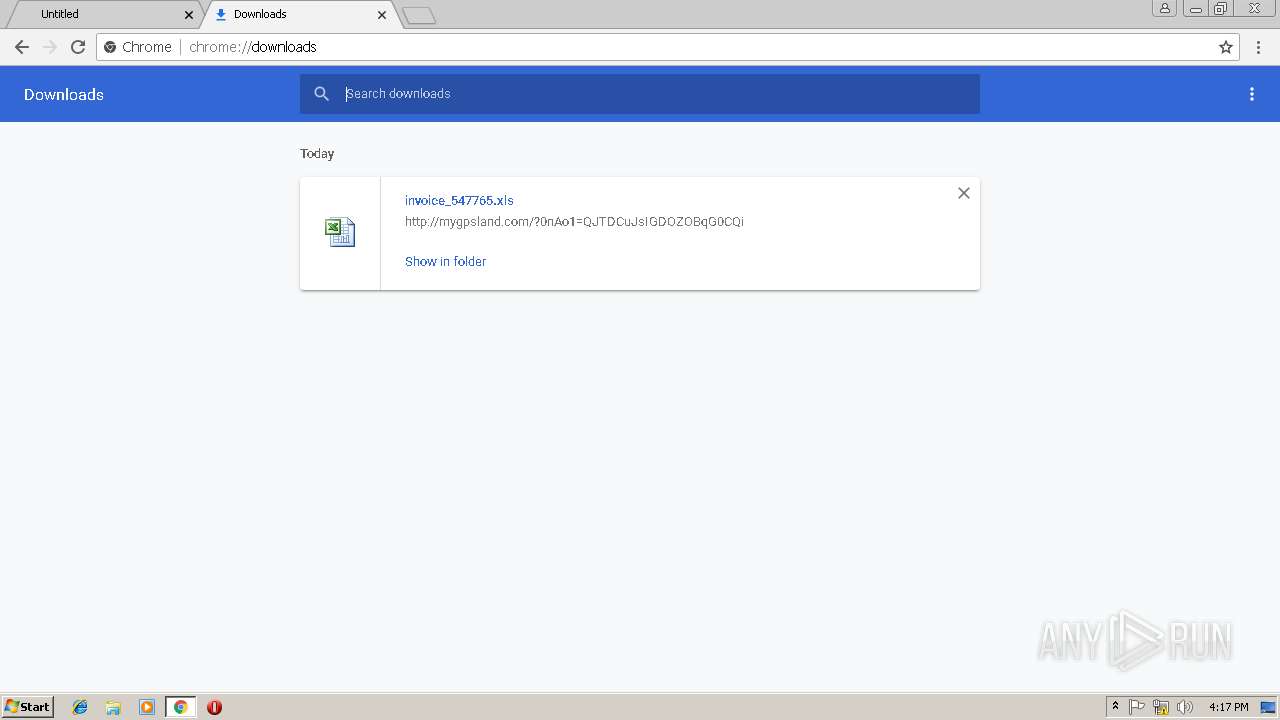
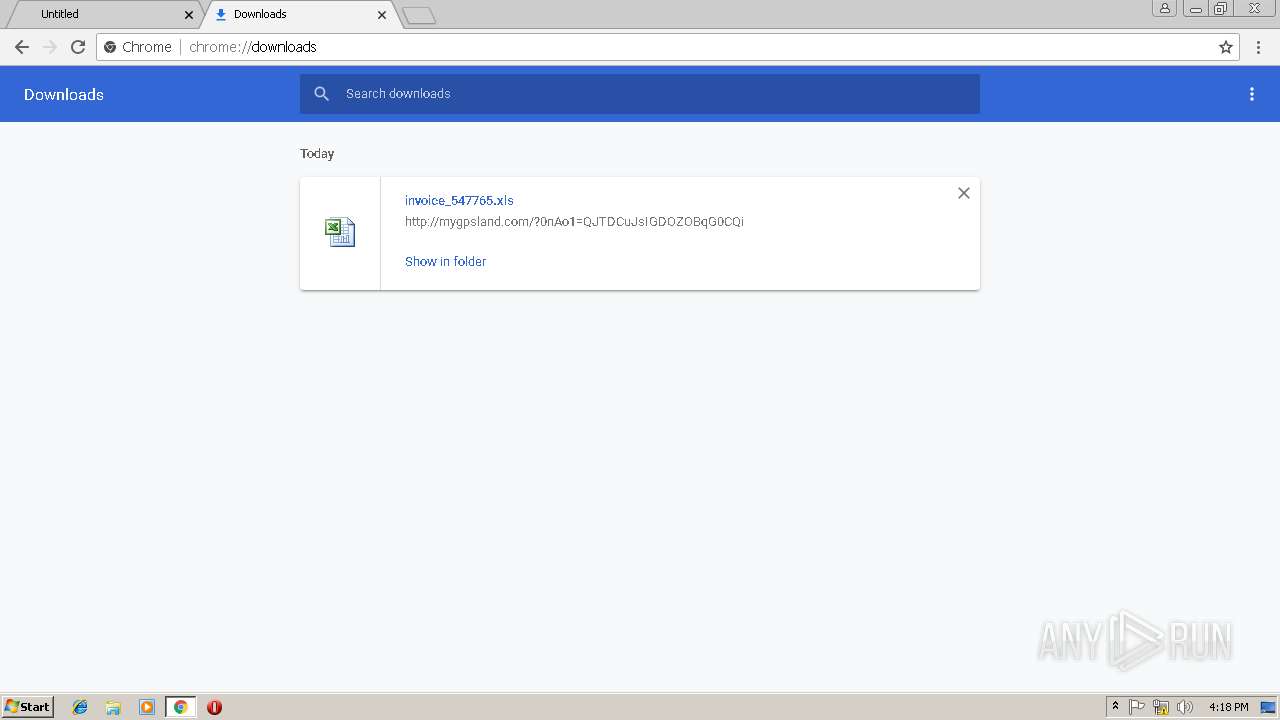
| URL: | http://mygpsland.com/?0nAo1=QJTDCuJsIGDOZOBqG0CQi |
| Full analysis: | https://app.any.run/tasks/d53e8069-d407-45f7-a371-7d7a924a0309 |
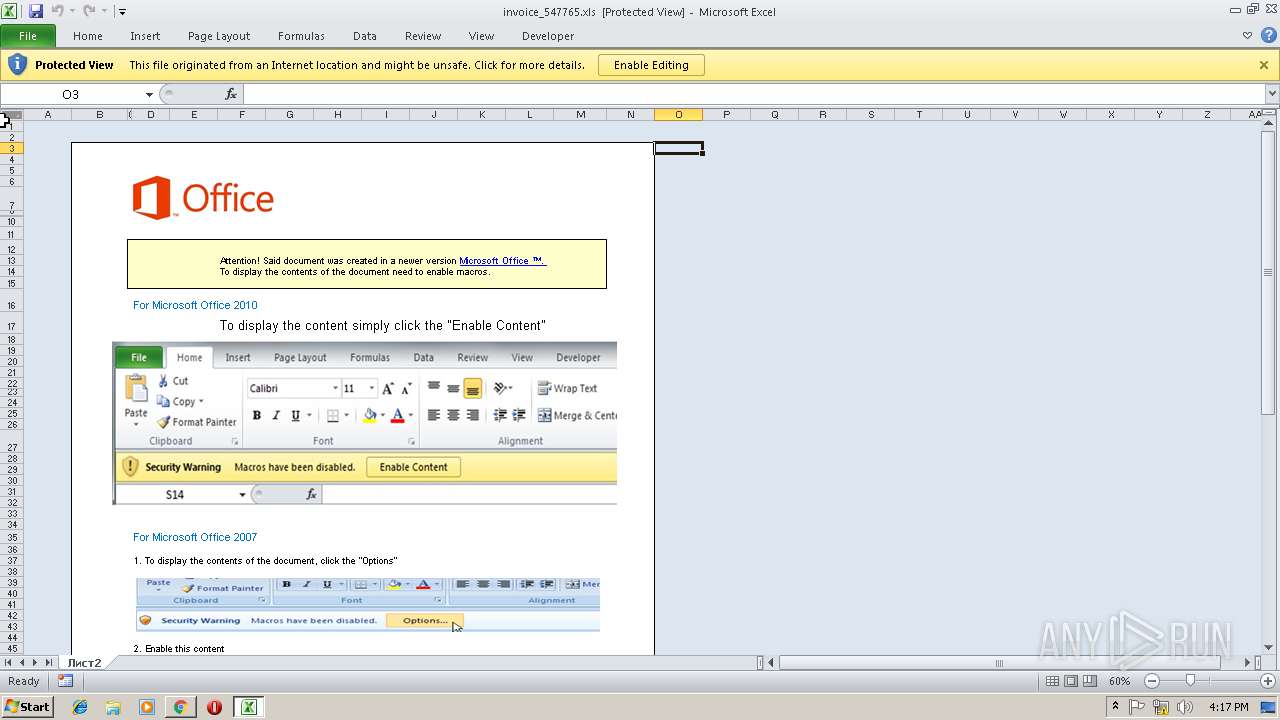
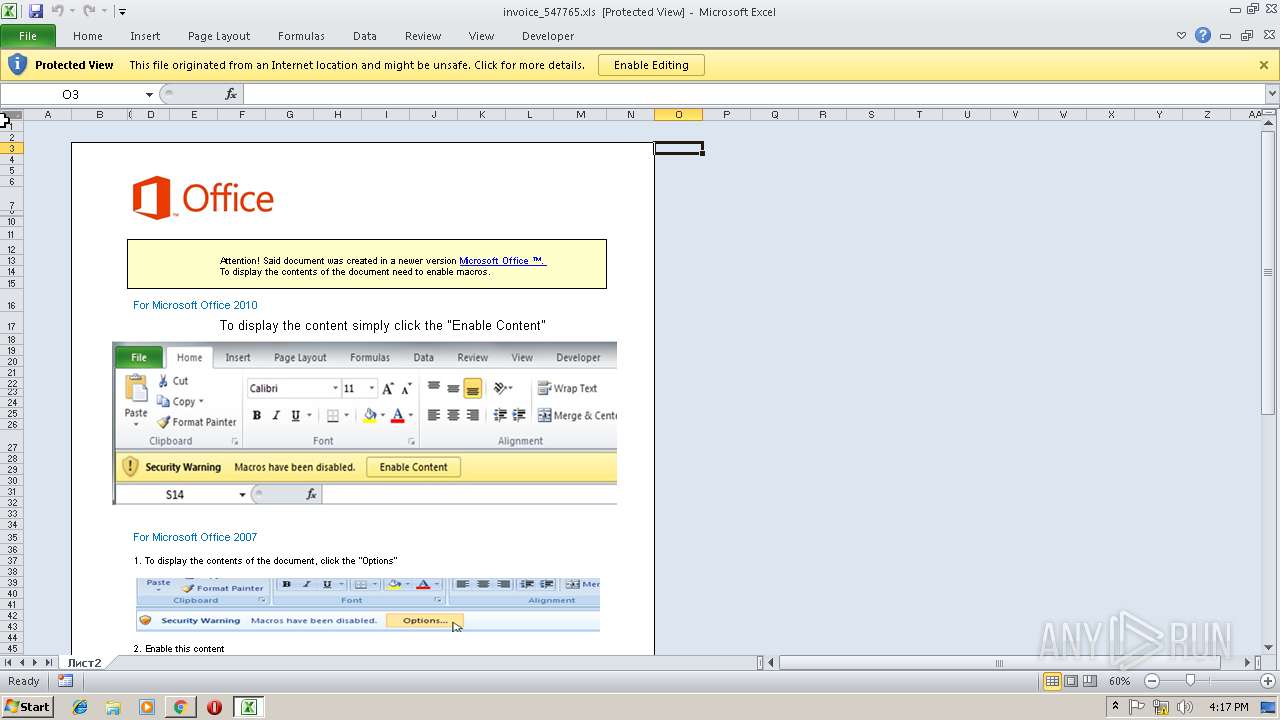
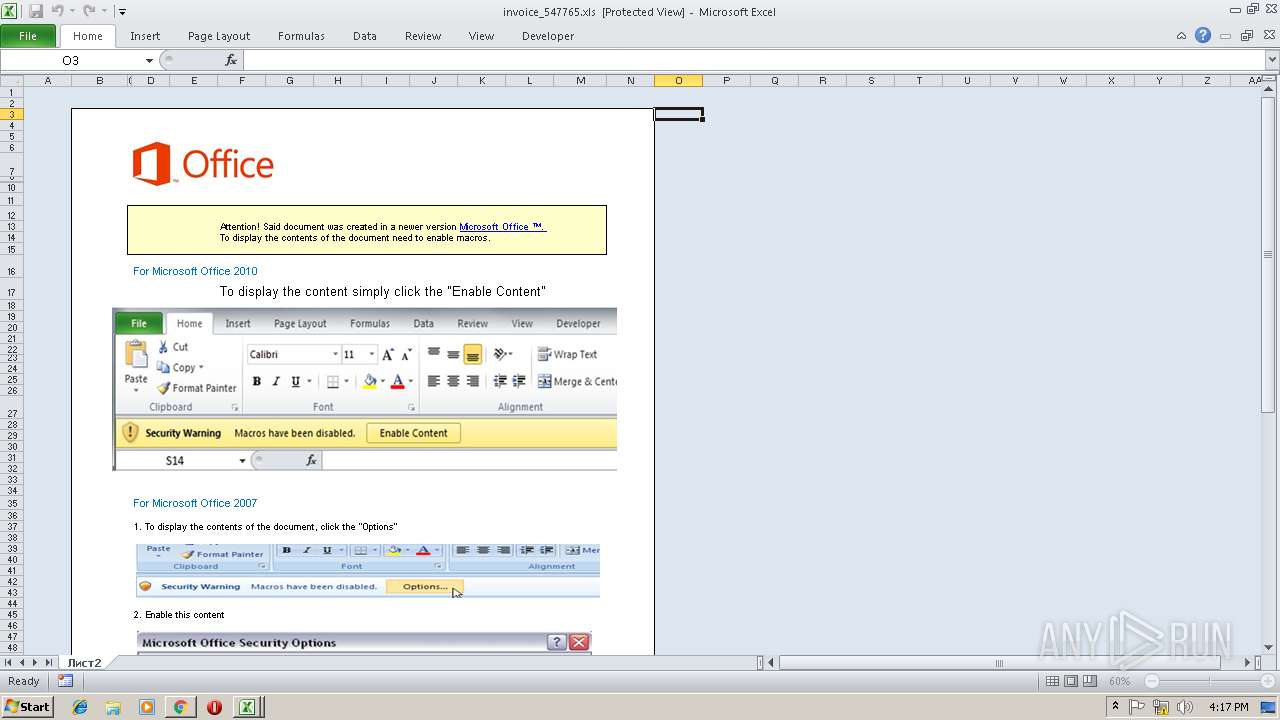
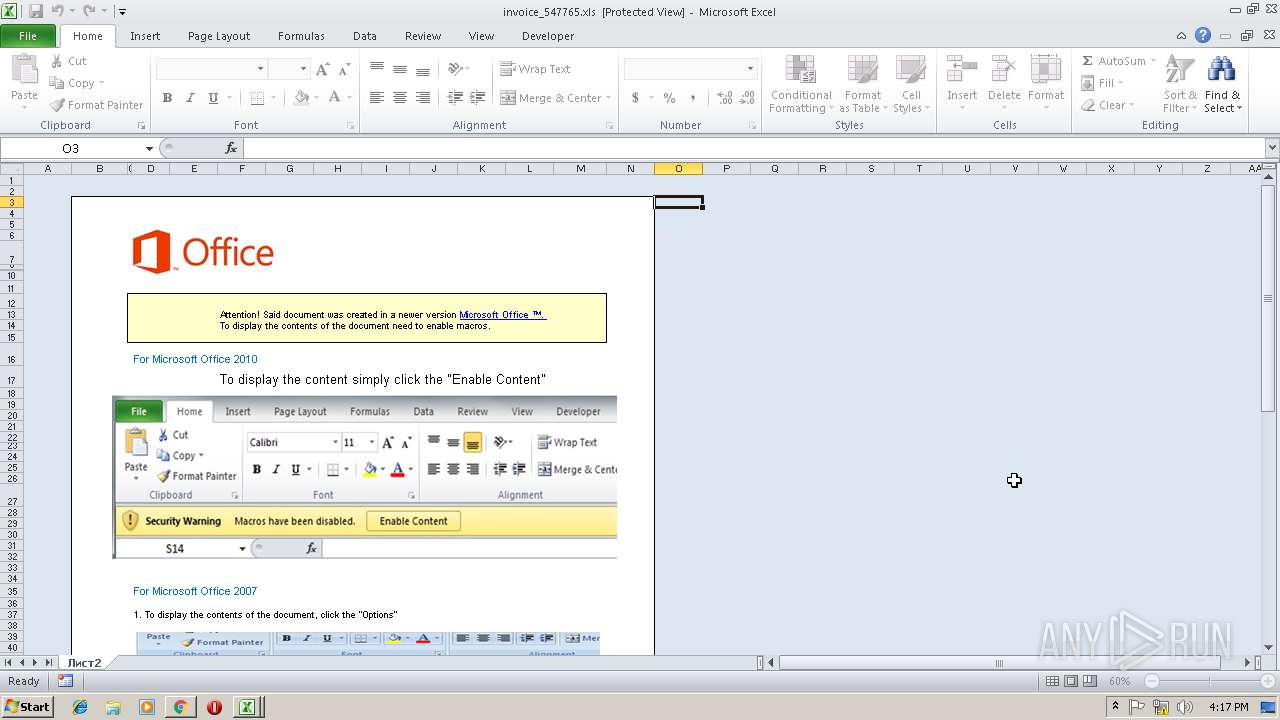
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 16:14:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F7E7CA18117CAED68EF6AB3652FF9B6D |
| SHA1: | 9D19F9F4997505F9A4565F6C3EF3CA5206EA1DB5 |
| SHA256: | 83805E59EC3ABAFEA9417842E32FAB74CD1998BF124EE75153D54DF4502D2B5B |
| SSDEEP: | 3:N1KTp9duLDB0PnOsmRm0M:C1DufB0PDmRm0M |
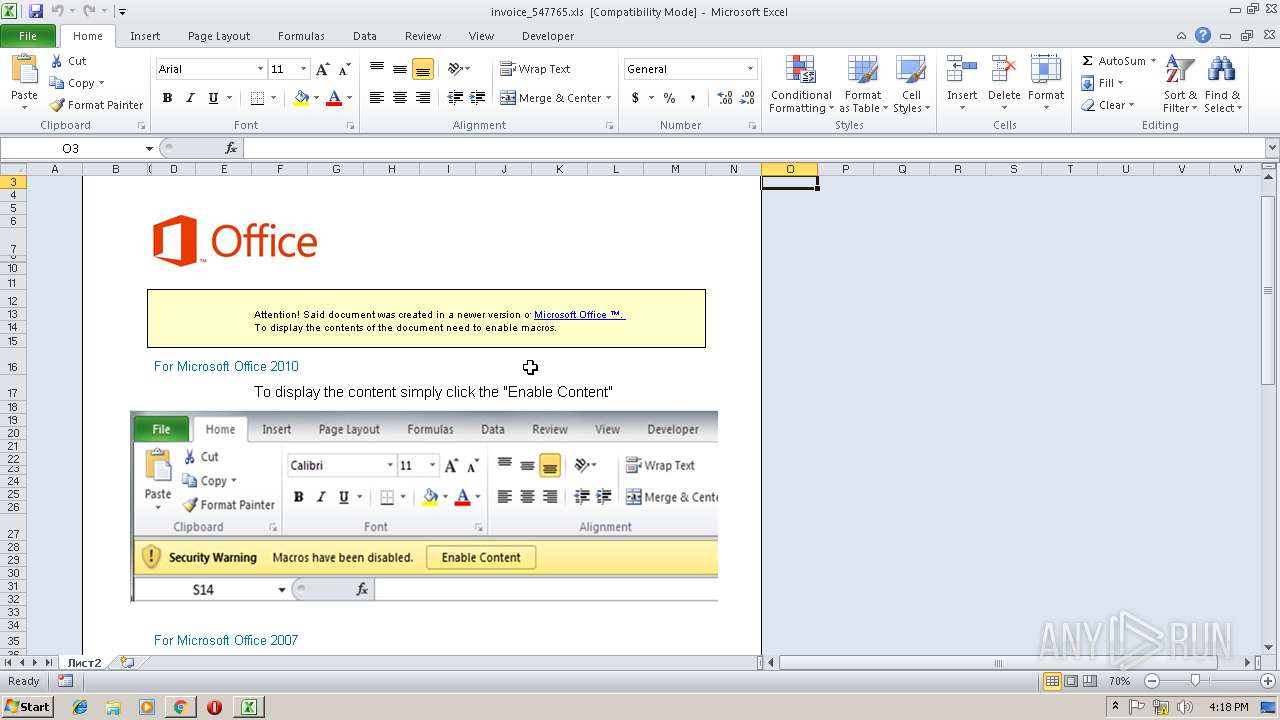
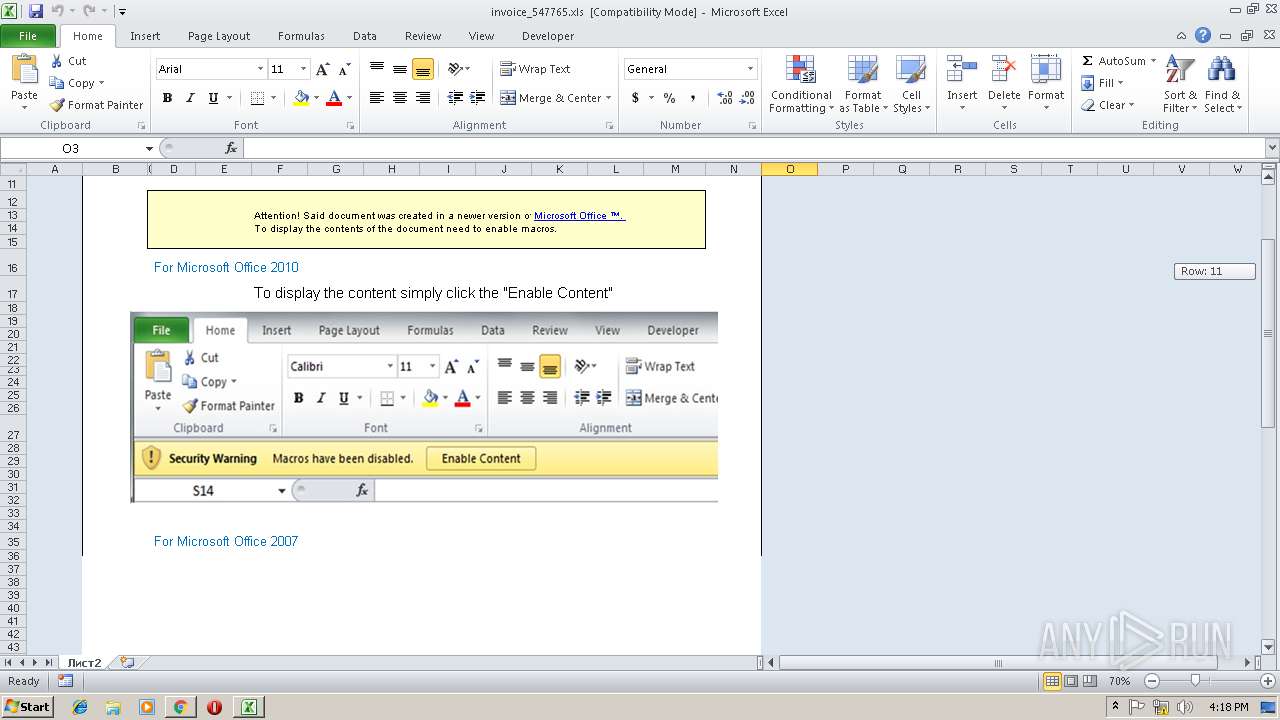
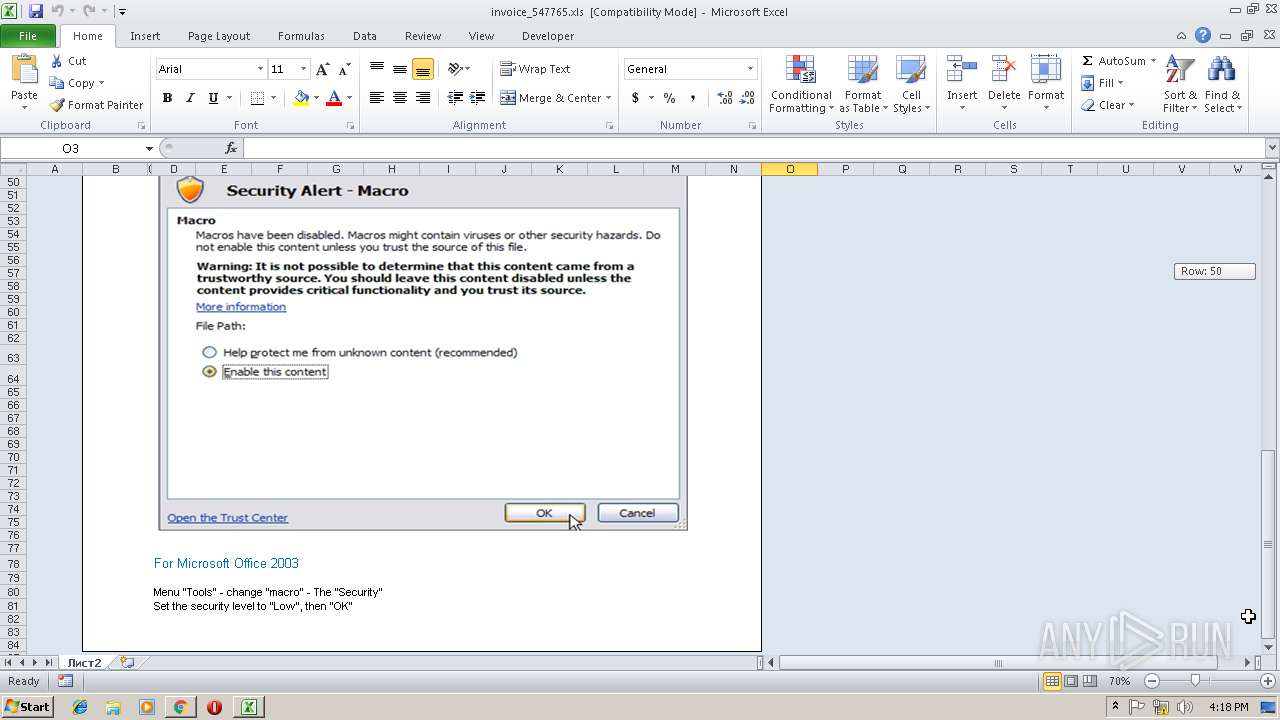
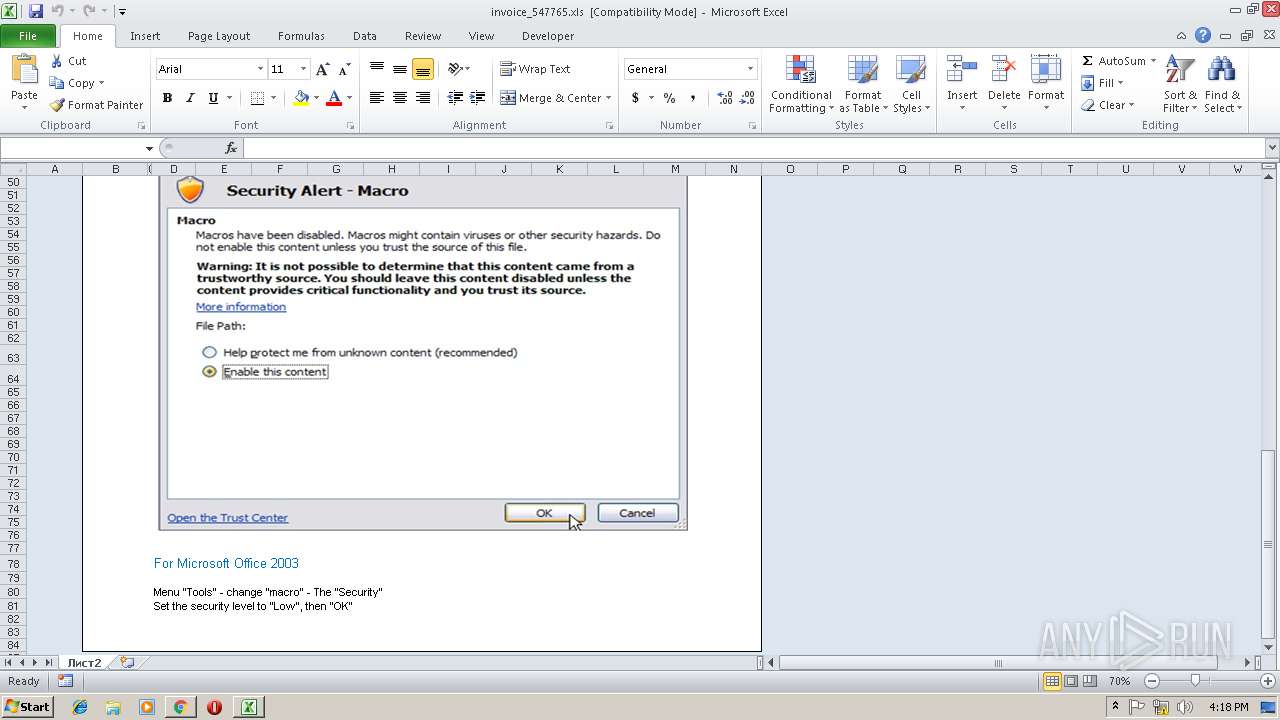
MALICIOUS
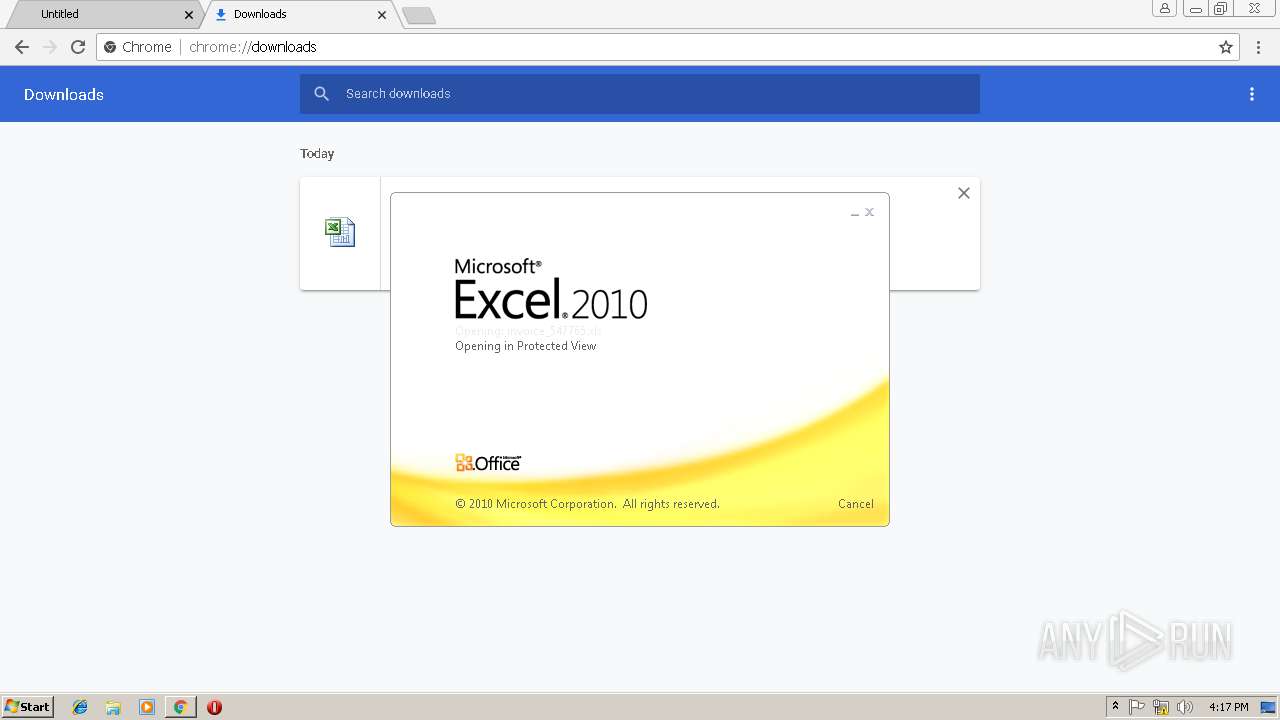
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2684)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2684)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2308)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2684)
SUSPICIOUS
Starts Microsoft Office Application
- chrome.exe (PID: 3004)
- EXCEL.EXE (PID: 2684)
Application launched itself
- EXCEL.EXE (PID: 2684)
INFO
Application launched itself
- chrome.exe (PID: 3004)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3004)
- EXCEL.EXE (PID: 2684)
Reads Internet Cache Settings
- chrome.exe (PID: 3004)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2684)
- EXCEL.EXE (PID: 3776)
Creates files in the user directory
- EXCEL.EXE (PID: 2684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
19
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0468A2C08C7541DBF96399226B1CECB2 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0468A2C08C7541DBF96399226B1CECB2 --renderer-client-id=10 --mojo-platform-channel-handle=3592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=888,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=11BFF5CE3237868FC9DA1CE0606B0AEB --mojo-platform-channel-handle=940 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5DC9EF60672513B5ED2F550C8E44C07E --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5DC9EF60672513B5ED2F550C8E44C07E --renderer-client-id=11 --mojo-platform-channel-handle=3792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=888,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=D1899B509D7046D8634E3EEBEAC3BF50 --mojo-platform-channel-handle=776 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2308 | cmd.exe /c ping localhost -n 100 && C:\Users\admin\AppData\Local\Temp\6.pif | C:\Windows\system32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=89352D8F8AEE9C50B07652926B79F0A2 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=89352D8F8AEE9C50B07652926B79F0A2 --renderer-client-id=13 --mojo-platform-channel-handle=2356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=888,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=F93FAA201181C84E3DABD4738120A6BE --mojo-platform-channel-handle=3860 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=888,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=3868224996D07D05A7B169286AB6D60A --mojo-platform-channel-handle=3508 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 178
Read events
1 975
Write events
180
Delete events
23
Modification events
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3004-13192647298351875 |
Value: 259 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3004-13192647298351875 |
Value: 259 | |||
Executable files
2
Suspicious files
66
Text files
95
Unknown types
3
Dropped files
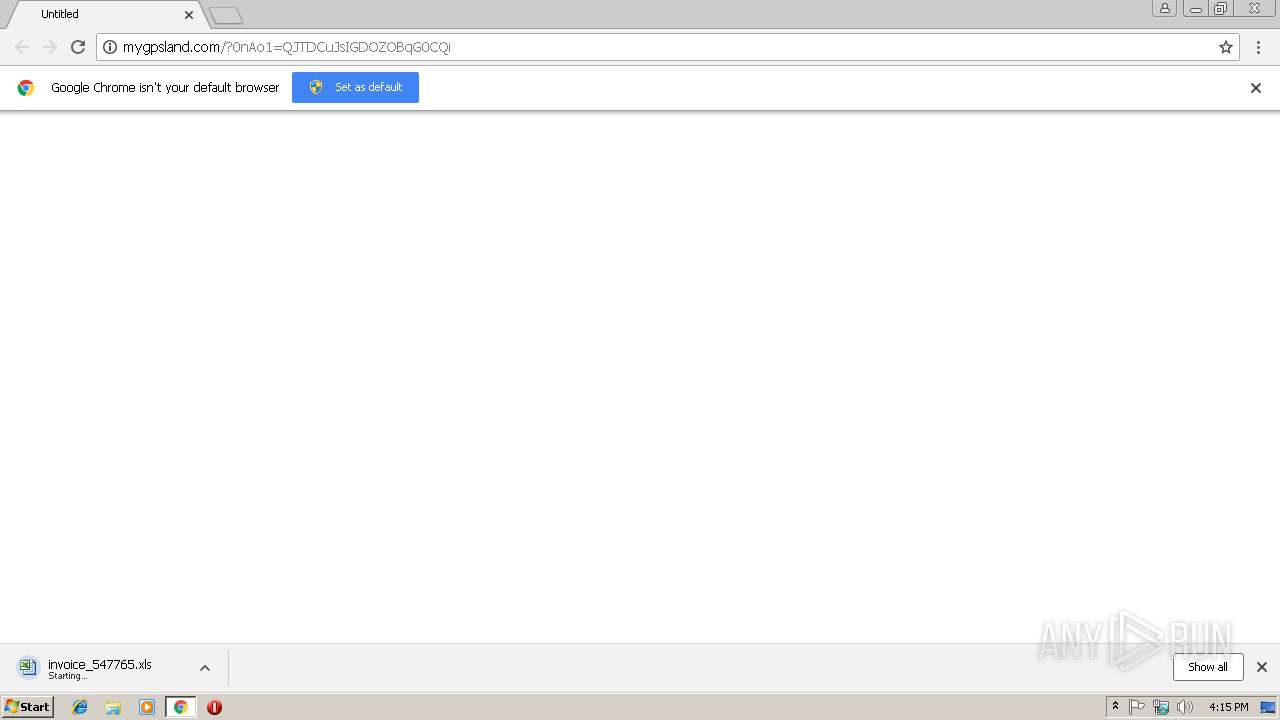
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2a827339-de6d-40f6-a953-c35b45ecefc8.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f9b3d373-d1ed-436b-a48f-9462361be6f8.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF20e737.TMP | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e737.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
21
DNS requests
13
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3004 | chrome.exe | GET | — | 47.74.24.76:80 | http://mygpsland.com/?0nAo1=QJTDCuJsIGDOZOBqG0CQi | JP | — | — | suspicious |
3004 | chrome.exe | GET | 200 | 47.74.24.76:80 | http://mygpsland.com/?0nAo1=QJTDCuJsIGDOZOBqG0CQi | JP | document | 458 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3004 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3004 | chrome.exe | 47.74.24.76:80 | mygpsland.com | Alibaba (China) Technology Co., Ltd. | JP | suspicious |
3004 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 172.217.16.163:443 | www.google.de | Google Inc. | US | whitelisted |
3004 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 172.217.18.3:443 | www.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mygpsland.com |
| suspicious |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.nl |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3004 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3004 | chrome.exe | Potentially Bad Traffic | SUSPICIOUS [PTsecurity] cmd.exe Command Inbound Detected |
3004 | chrome.exe | Potentially Bad Traffic | SUSPICIOUS [PTsecurity] cmd.exe Command Inbound Detected |
2 ETPRO signatures available at the full report