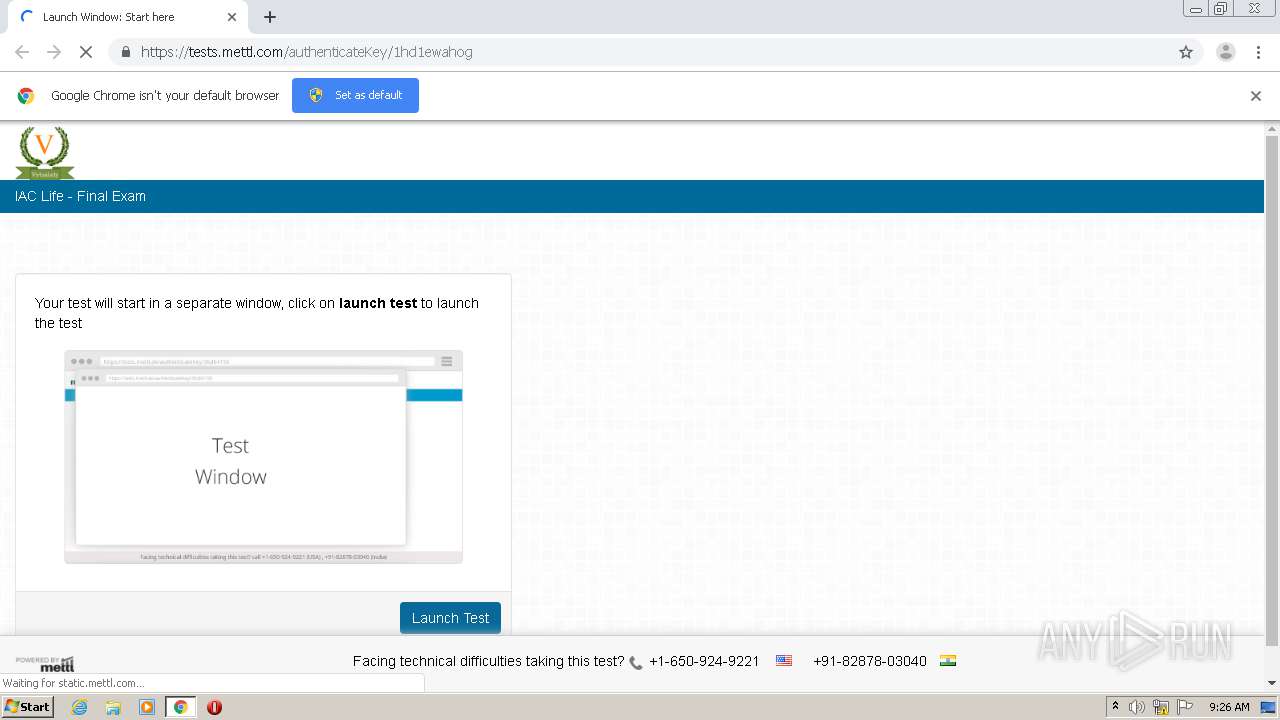
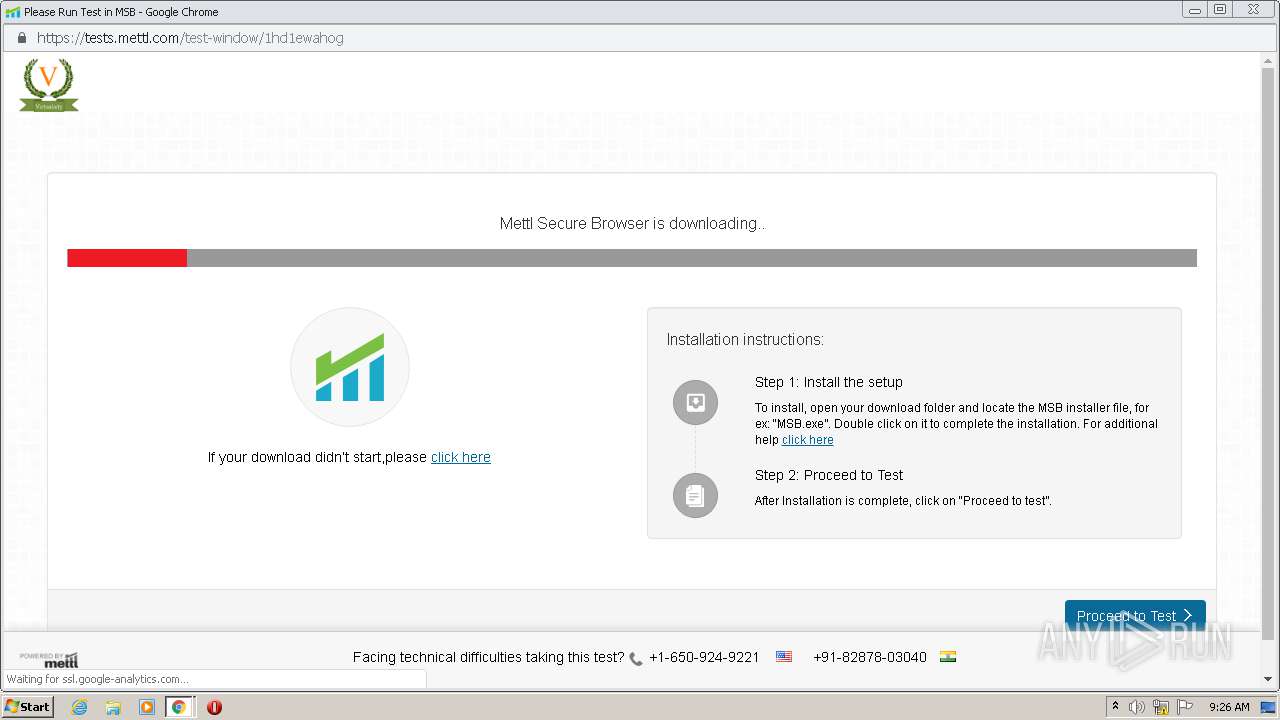
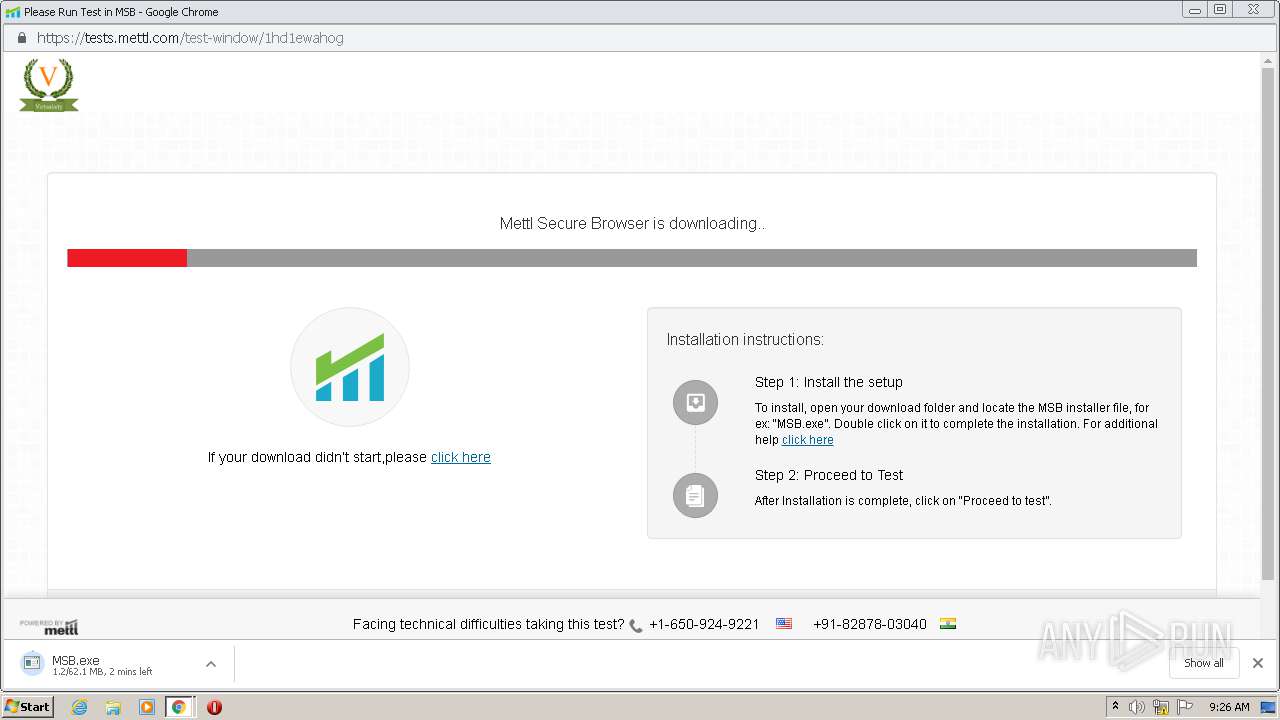
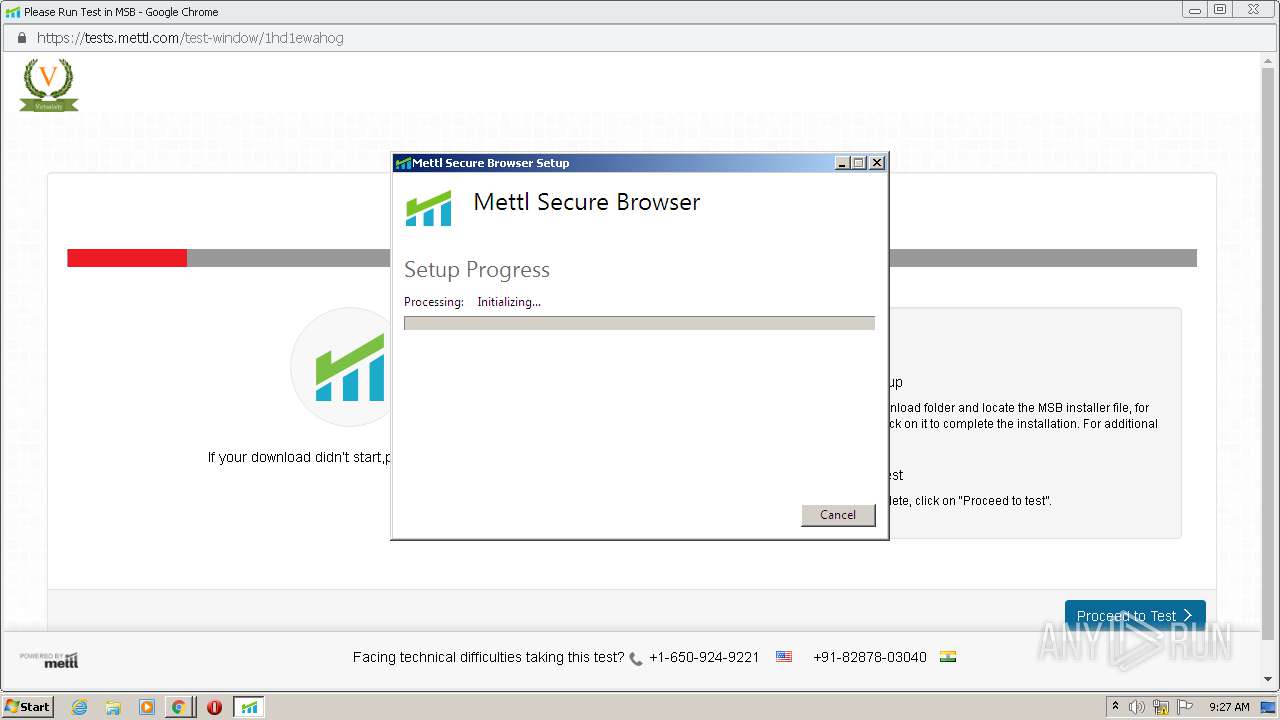
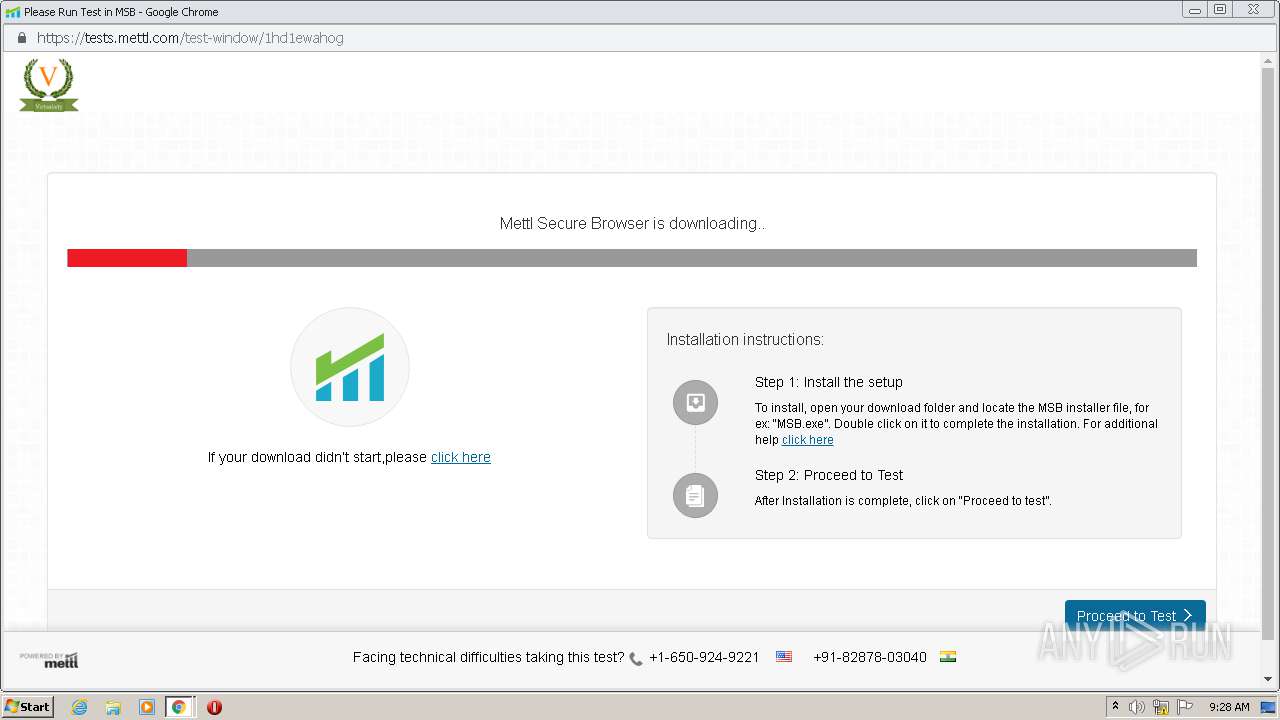
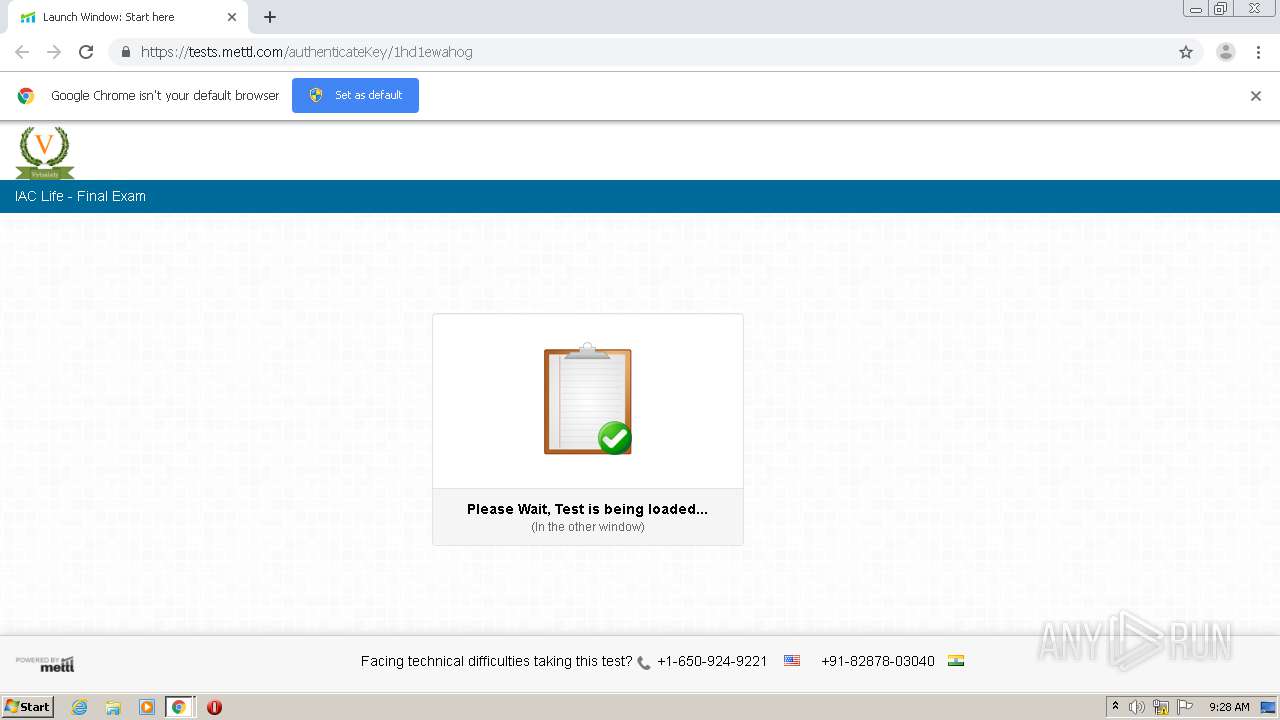
| URL: | https://tests.mettl.com/authenticateKey/1hd1ewahog |
| Full analysis: | https://app.any.run/tasks/e4403b6e-f6f5-40b2-9a41-c1b5c740b9b1 |
| Verdict: | Malicious activity |
| Analysis date: | October 30, 2020, 09:25:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 659428795425F3CBDCE1105484BBE2E5 |
| SHA1: | CC253B2030AA6604627AAD7A857B16945E8133CB |
| SHA256: | 837E0589ED1FF014CB6AEE509B5ED432E7DE121C4F354051A2ABFE08C2B8DC50 |
| SSDEEP: | 3:N8I6AsK0r8U50Z:2Ikd5u |
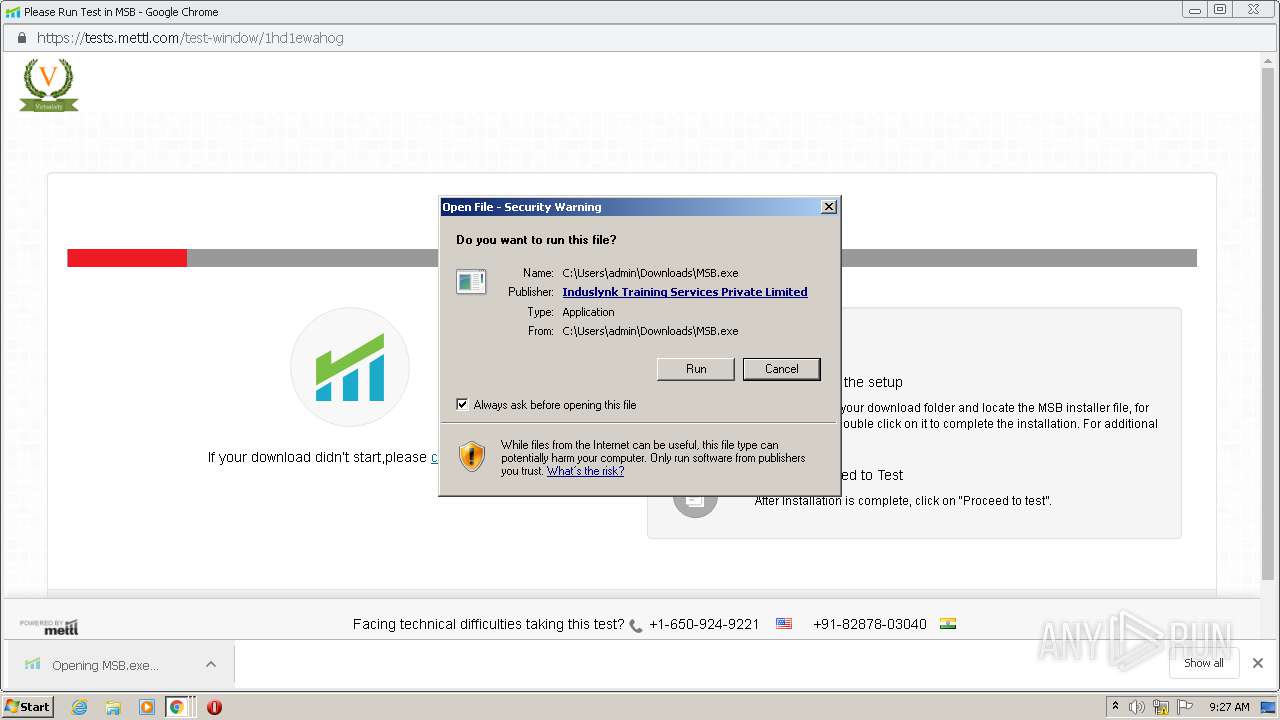
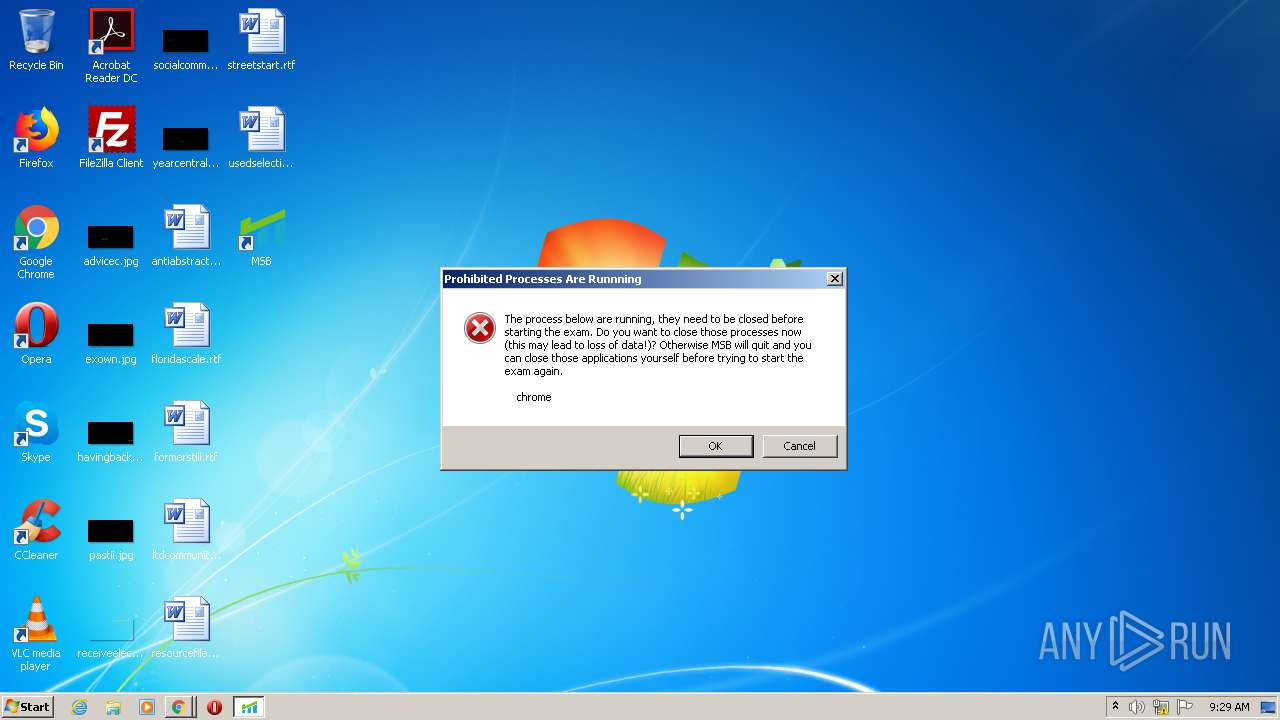
MALICIOUS
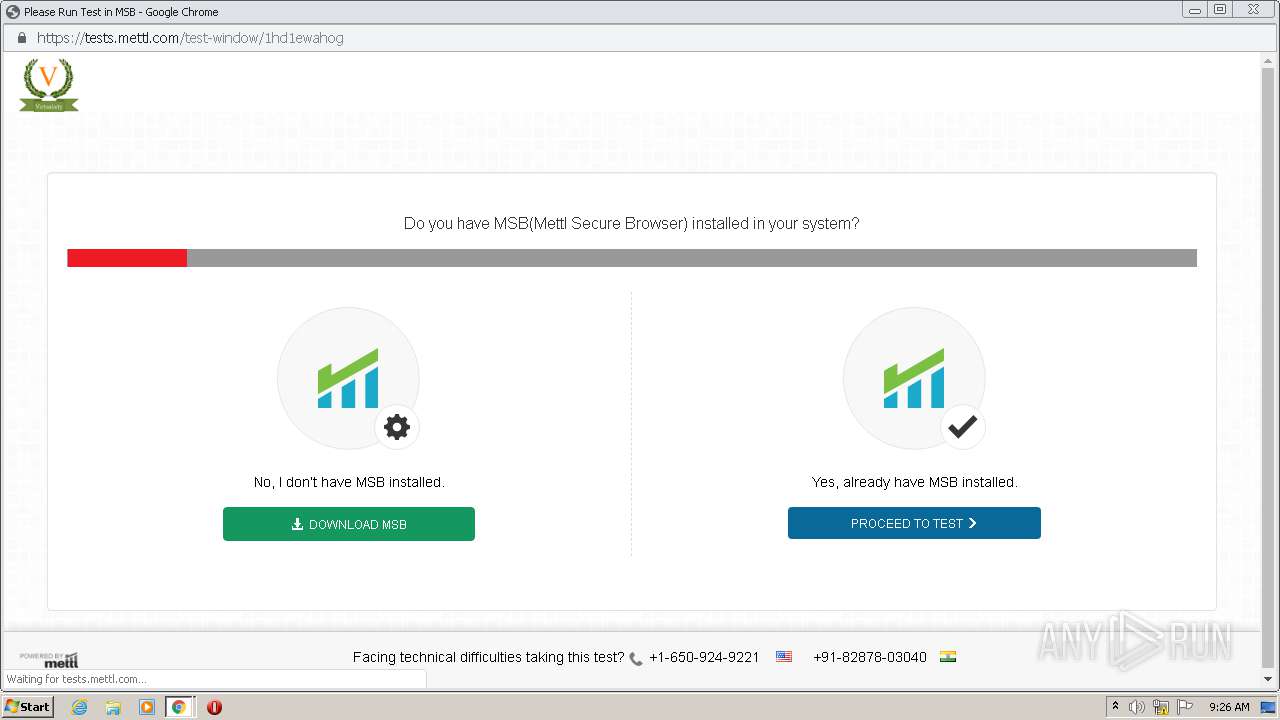
Application was dropped or rewritten from another process
- MSB.exe (PID: 548)
- MettlSecureBrowserInstaller.exe (PID: 352)
- MSB.exe (PID: 1332)
- SebWindowsServiceWCF.exe (PID: 2100)
- MSB.exe (PID: 2764)
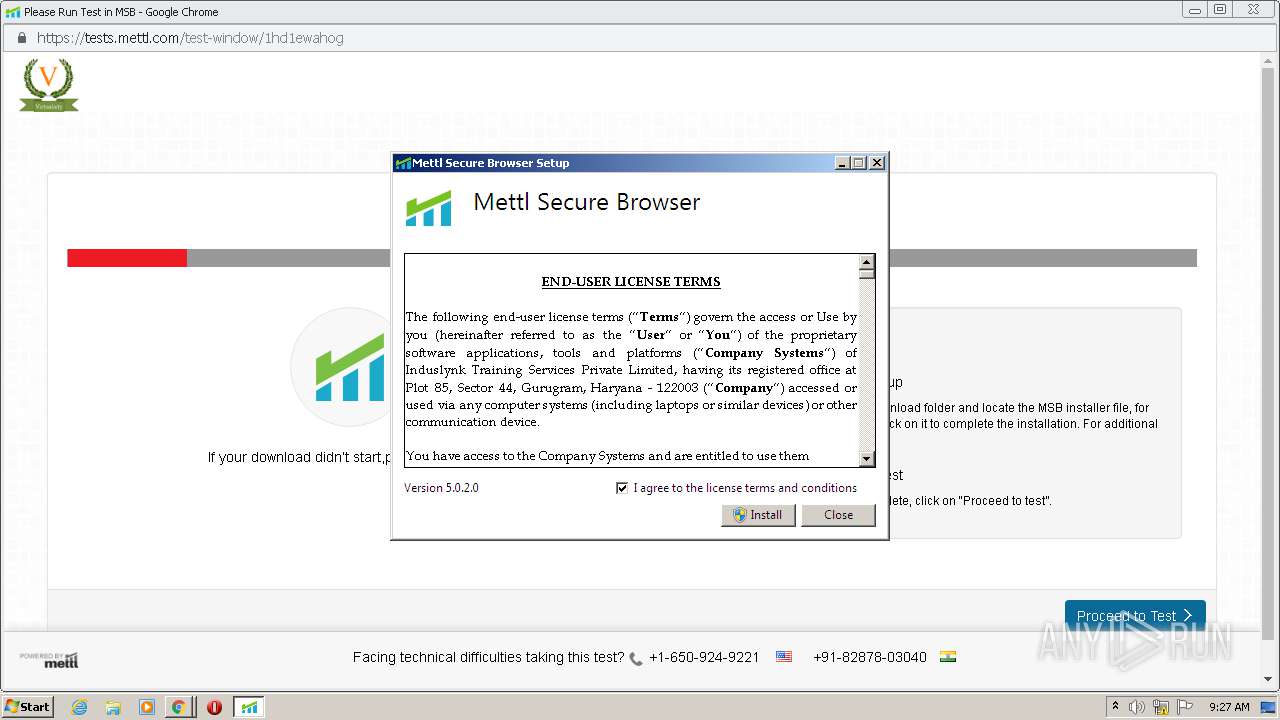
Changes the autorun value in the registry
- MettlSecureBrowserInstaller.exe (PID: 352)
Changes settings of System certificates
- msiexec.exe (PID: 3188)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2492)
Executable content was dropped or overwritten
- MSB.exe (PID: 1332)
- MSB.exe (PID: 548)
- chrome.exe (PID: 2492)
- MettlSecureBrowserInstaller.exe (PID: 352)
- msiexec.exe (PID: 3188)
Searches for installed software
- MettlSecureBrowserInstaller.exe (PID: 352)
Creates files in the program directory
- MettlSecureBrowserInstaller.exe (PID: 352)
- SebWindowsServiceWCF.exe (PID: 2100)
Starts itself from another location
- MSB.exe (PID: 548)
Executed as Windows Service
- vssvc.exe (PID: 2816)
- SebWindowsServiceWCF.exe (PID: 2100)
Creates a software uninstall entry
- MettlSecureBrowserInstaller.exe (PID: 352)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3188)
Creates COM task schedule object
- msiexec.exe (PID: 3188)
Modifies the open verb of a shell class
- msiexec.exe (PID: 3188)
Reads Environment values
- MSB.exe (PID: 2764)
Creates files in the user directory
- MSB.exe (PID: 2764)
INFO
Application launched itself
- chrome.exe (PID: 2492)
Reads the hosts file
- chrome.exe (PID: 2492)
- chrome.exe (PID: 1700)
Reads Internet Cache Settings
- chrome.exe (PID: 2492)
Changes settings of System certificates
- chrome.exe (PID: 1700)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2816)
Reads settings of System Certificates
- msiexec.exe (PID: 3188)
Manual execution by user
- MSB.exe (PID: 2764)
Creates a software uninstall entry
- msiexec.exe (PID: 3188)
Creates files in the program directory
- msiexec.exe (PID: 3188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
32
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
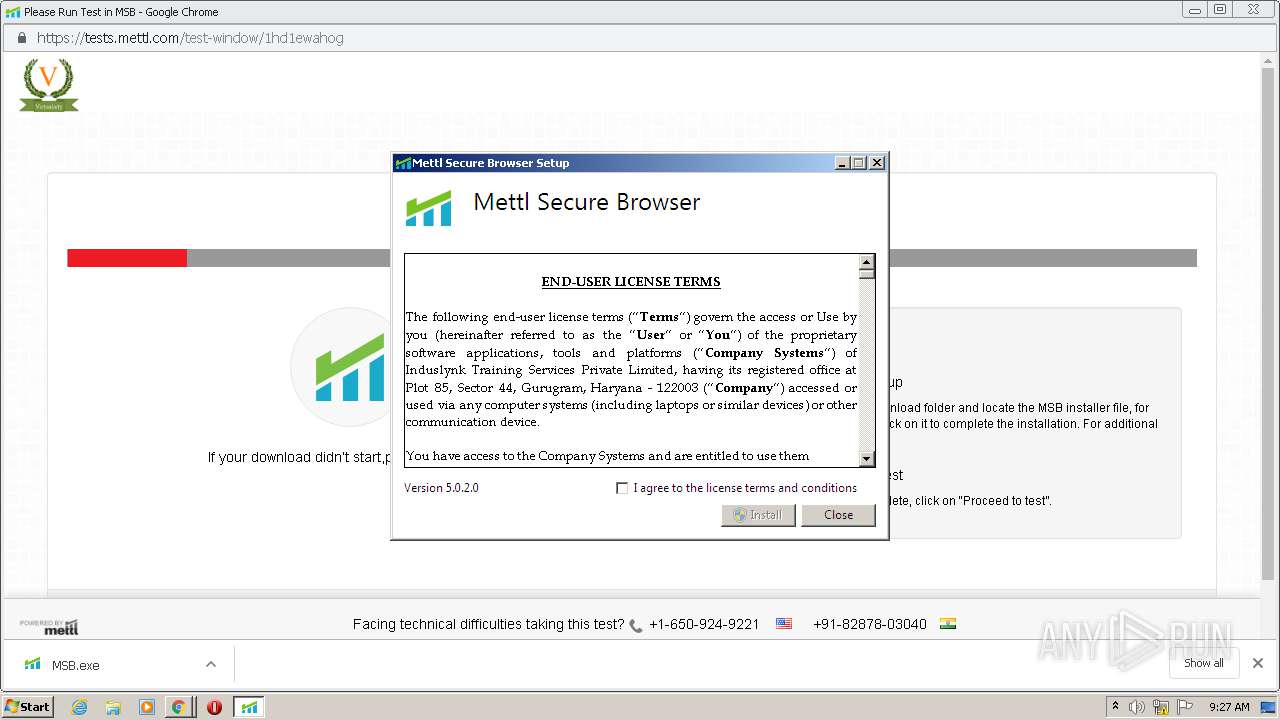
| 352 | "C:\Users\admin\AppData\Local\Temp\{F235AA81-850A-4625-B520-43E50E63C5C2}\.be\MettlSecureBrowserInstaller.exe" -q -burn.elevated BurnPipe.{BA459BD0-C879-4AA4-BB43-C630E3913905} {AA902444-21B3-41A0-8FE3-1AF9A1EB9272} 548 | C:\Users\admin\AppData\Local\Temp\{F235AA81-850A-4625-B520-43E50E63C5C2}\.be\MettlSecureBrowserInstaller.exe | MSB.exe | ||||||||||||
User: admin Company: Mettl Integrity Level: HIGH Description: Mettl Secure Browser Exit code: 0 Version: 5.0.2.0 Modules
| |||||||||||||||
| 548 | "C:\Users\admin\AppData\Local\Temp\{D0825FD5-FA6D-43D3-884A-FBB2FE07CB11}\.cr\MSB.exe" -burn.clean.room="C:\Users\admin\Downloads\MSB.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{D0825FD5-FA6D-43D3-884A-FBB2FE07CB11}\.cr\MSB.exe | MSB.exe | ||||||||||||
User: admin Company: Mettl Integrity Level: MEDIUM Description: Mettl Secure Browser Exit code: 0 Version: 5.0.2.0 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,13865762441141904785,7353893225699798192,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17432411809337568915 --mojo-platform-channel-handle=2804 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
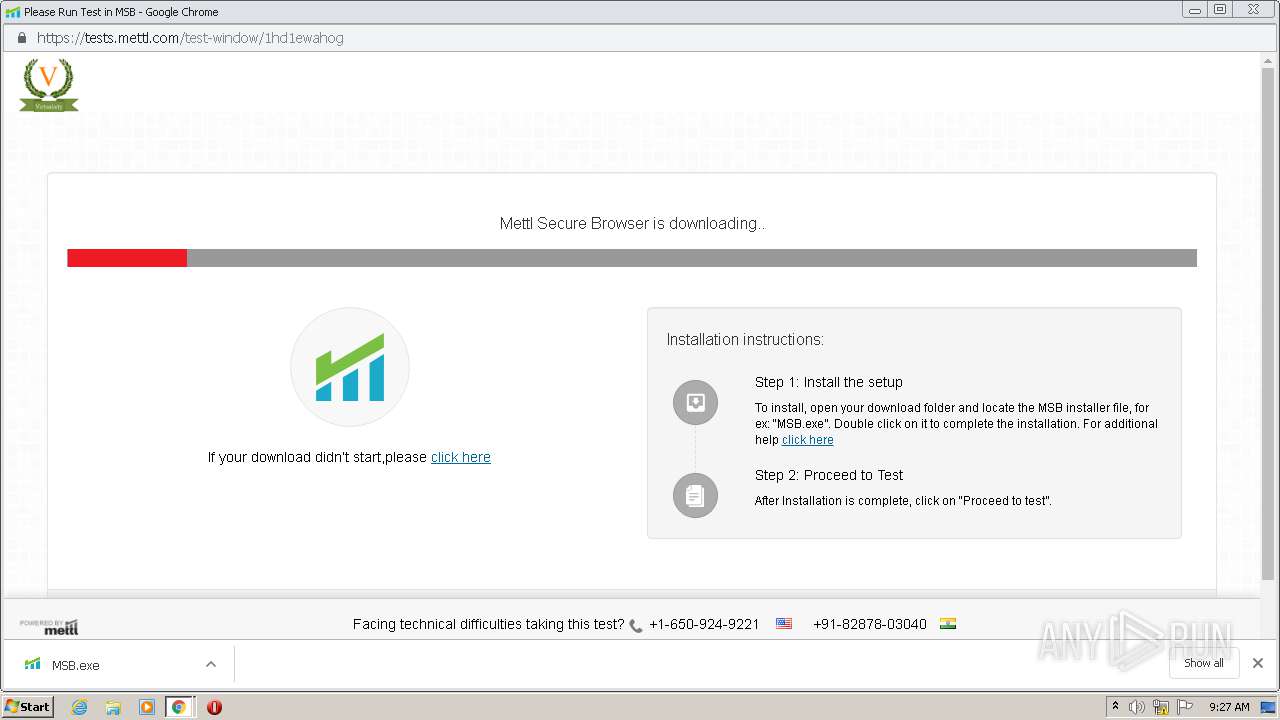
| 1332 | "C:\Users\admin\Downloads\MSB.exe" | C:\Users\admin\Downloads\MSB.exe | chrome.exe | ||||||||||||
User: admin Company: Mettl Integrity Level: MEDIUM Description: Mettl Secure Browser Exit code: 0 Version: 5.0.2.0 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,13865762441141904785,7353893225699798192,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16907586695305156512 --mojo-platform-channel-handle=3376 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,13865762441141904785,7353893225699798192,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6903296373436224062 --mojo-platform-channel-handle=1656 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2308 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,13865762441141904785,7353893225699798192,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1403575394928878039 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,13865762441141904785,7353893225699798192,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8053207909787091520 --mojo-platform-channel-handle=3516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1060,13865762441141904785,7353893225699798192,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2698220792034438763 --mojo-platform-channel-handle=4272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 110
Read events
1 914
Write events
1 178
Delete events
18
Modification events
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2492-13248523564191625 |
Value: 259 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
88
Suspicious files
227
Text files
637
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F9BDC2D-9BC.pma | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6b08e72a-63fd-46eb-86e2-889c7aa4e0f9.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF124e66.TMP | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF124dca.TMP | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF124de9.TMP | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1250c8.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
33
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1700 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZDM4QUFXaVZ5bThYeHlpdXd5bzU1RzRQUQ/8220.313.1.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 542 b | whitelisted |
1700 | chrome.exe | GET | 200 | 84.15.65.14:80 | http://r3---sn-cpux-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZDM4QUFXaVZ5bThYeHlpdXd5bzU1RzRQUQ/8220.313.1.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=i8&mip=85.206.166.82&mm=28&mn=sn-cpux-gpme&ms=nvh&mt=1604049921&mv=m&mvi=3&pcm2cms=yes&pl=23&shardbypass=yes | LT | crx | 839 Kb | whitelisted |
1700 | chrome.exe | GET | 200 | 192.124.249.31:80 | http://certificates.godaddy.com/repository/gdig2.crt | US | der | 1.21 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1700 | chrome.exe | 172.217.22.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 84.15.65.14:80 | r3---sn-cpux-gpme.gvt1.com | UAB Bite Lietuva | LT | whitelisted |
1700 | chrome.exe | 15.206.238.108:443 | tests.mettl.com | Hewlett-Packard Company | US | unknown |
1700 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 13.234.125.85:443 | tests.mettl.com | Amazon.com, Inc. | IN | unknown |
1700 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 172.217.20.4:443 | www.google.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 13.232.101.62:443 | static.mettl.com | Amazon.com, Inc. | IN | unknown |
1700 | chrome.exe | 13.127.35.35:443 | media.mettl.com | Amazon.com, Inc. | IN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
tests.mettl.com |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| malicious |
static.mettl.com |
| suspicious |
media.mettl.com |
| unknown |
certificates.godaddy.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |