| URL: | http://news.creaders.net/china/2020/04/14/big5/2214004.html |
| Full analysis: | https://app.any.run/tasks/1886ca6c-ae1e-460f-819f-745265a65cde |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2020, 13:34:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C0E11B09978DF327C6B903CDE041594E |
| SHA1: | F87CE4FF313B7B64798EC017539D63814A3E1EEF |
| SHA256: | 837843F723865A8823A20343010AC50F76F8086733E3990814A61418CF5426C0 |
| SSDEEP: | 3:N1KQ3WLfc0NMtUmrURVVR5G:CQ3WLfc0NMSzVu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3500)
INFO
Reads the hosts file
- chrome.exe (PID: 3500)
- chrome.exe (PID: 2580)
Application launched itself
- chrome.exe (PID: 3500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
112
Monitored processes
75
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17390724210346539111 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15641578004984461173 --renderer-client-id=56 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6787399429572454621 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12700513027478740522 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7993527614000489132 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4664 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6021308991618256757 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16681091035667419214 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8840484815949139638 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6982579208386276448 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
650
Read events
535
Write events
111
Delete events
4
Modification events
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3500-13231517688473875 |
Value: 259 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
226
Text files
293
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E985EF8-DAC.pma | — | |
MD5:— | SHA256:— | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3fdb726b-d5f3-49d9-99fd-b1e006c19c1b.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:FC9FFE77348619CC285333DFF5E1D5D1 | SHA256:7CB9B3575330B3D776A21EB7A7407E34F013A0975B7418DA11B5C85DEC91D1F3 | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa6e20b.TMP | text | |
MD5:FC9FFE77348619CC285333DFF5E1D5D1 | SHA256:7CB9B3575330B3D776A21EB7A7407E34F013A0975B7418DA11B5C85DEC91D1F3 | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa6e1ae.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e334.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
101
TCP/UDP connections
366
DNS requests
204
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2580 | chrome.exe | GET | — | 67.228.102.72:80 | http://news.creaders.net/breaking/css/content2015.css | US | — | — | unknown |
2580 | chrome.exe | GET | 200 | 13.225.73.34:80 | http://w.sharethis.com/button/buttons.js | US | text | 15.4 Kb | shared |
2580 | chrome.exe | GET | — | 67.228.102.72:80 | http://www.creaders.net/js/jquery-1.7.2.min.js | US | — | — | unknown |
2580 | chrome.exe | GET | 200 | 104.22.23.88:80 | http://services.bilsyndication.com/adv1/?d=357 | US | text | 248 b | suspicious |
2580 | chrome.exe | GET | — | 67.228.102.72:80 | http://pub.creaders.net/images/ww_03.gif | US | — | — | unknown |
2580 | chrome.exe | GET | — | 67.228.102.72:80 | http://pub.creaders.net/images/n103.gif | US | — | — | unknown |
2580 | chrome.exe | POST | 200 | 37.252.172.249:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | text | 138 b | whitelisted |
2580 | chrome.exe | GET | 301 | 13.225.78.76:80 | http://dsh7ky7308k4b.cloudfront.net/publishers/creadersnet.min.js | US | html | 183 b | whitelisted |
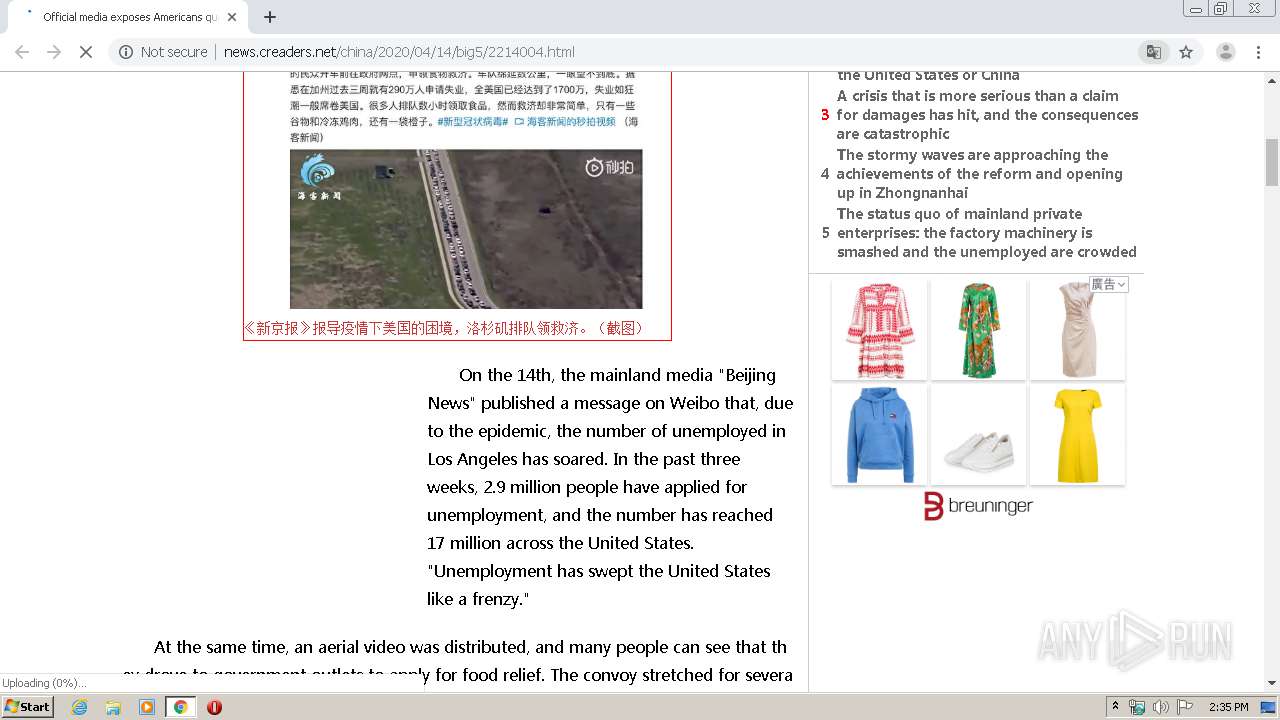
2580 | chrome.exe | GET | — | 67.228.102.72:80 | http://news.creaders.net/china/2020/04/14/big5/2214004.html | US | — | — | unknown |
2580 | chrome.exe | GET | 200 | 67.228.102.72:80 | http://www.creaders.net/js/ad_func.js | US | html | 3.05 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | chrome.exe | 23.213.15.82:443 | as-sec.casalemedia.com | Time Warner Cable Internet LLC | US | unknown |
2580 | chrome.exe | 23.213.164.135:443 | s7.addthis.com | Akamai Technologies, Inc. | US | unknown |
2580 | chrome.exe | 178.250.0.165:443 | bidder.criteo.com | Criteo SA | FR | unknown |
2580 | chrome.exe | 172.217.16.206:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 13.225.73.116:443 | c.sharethis.mgr.consensu.org | — | US | unknown |
2580 | chrome.exe | 3.124.133.106:443 | l.sharethis.com | — | US | unknown |
2580 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 67.228.102.72:80 | news.creaders.net | SoftLayer Technologies Inc. | US | unknown |
2580 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2580 | chrome.exe | 13.225.73.34:80 | w.sharethis.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
news.creaders.net |
| unknown |
accounts.google.com |
| shared |
www.creaders.net |
| unknown |
w.sharethis.com |
| shared |
dsh7ky7308k4b.cloudfront.net |
| whitelisted |
services.bilsyndication.com |
| suspicious |
pub.creaders.net |
| unknown |
s7.addthis.com |
| whitelisted |
pa.rxthdr.com |
| whitelisted |