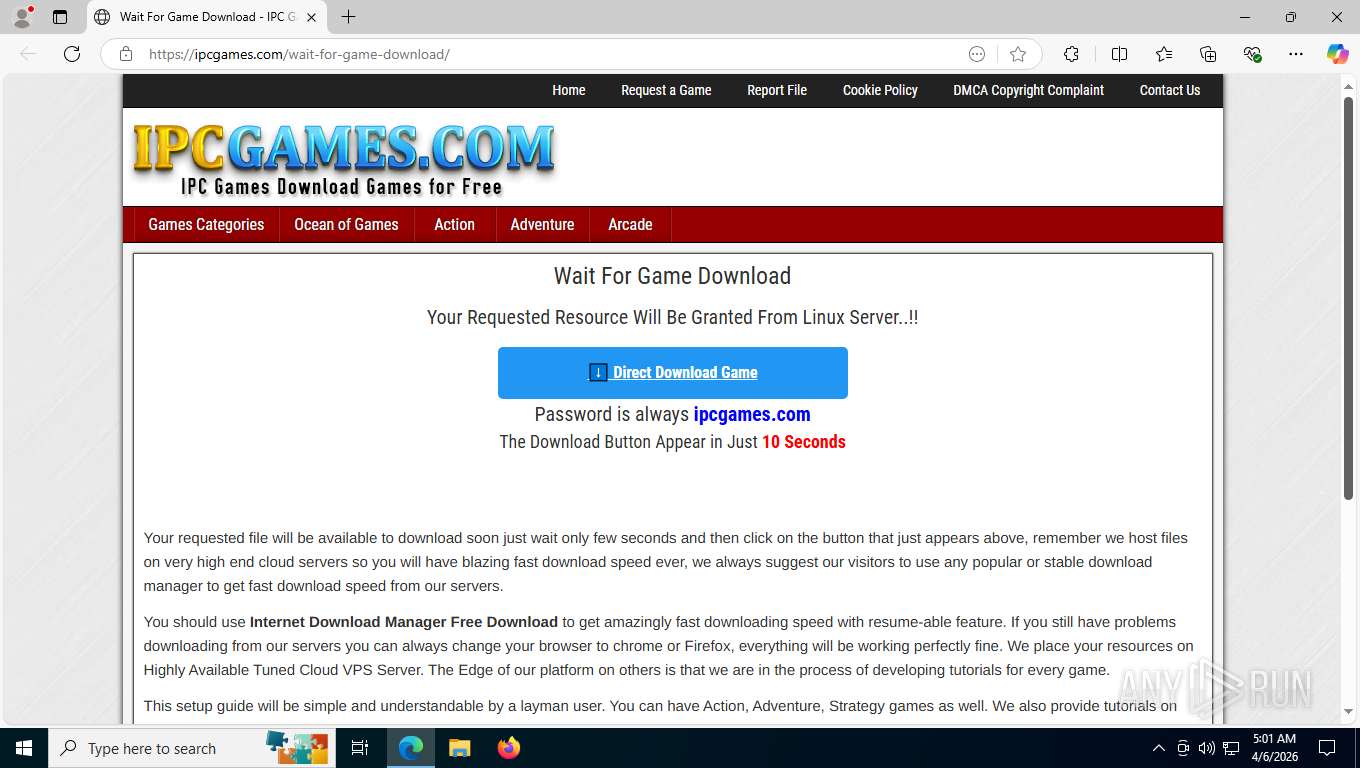
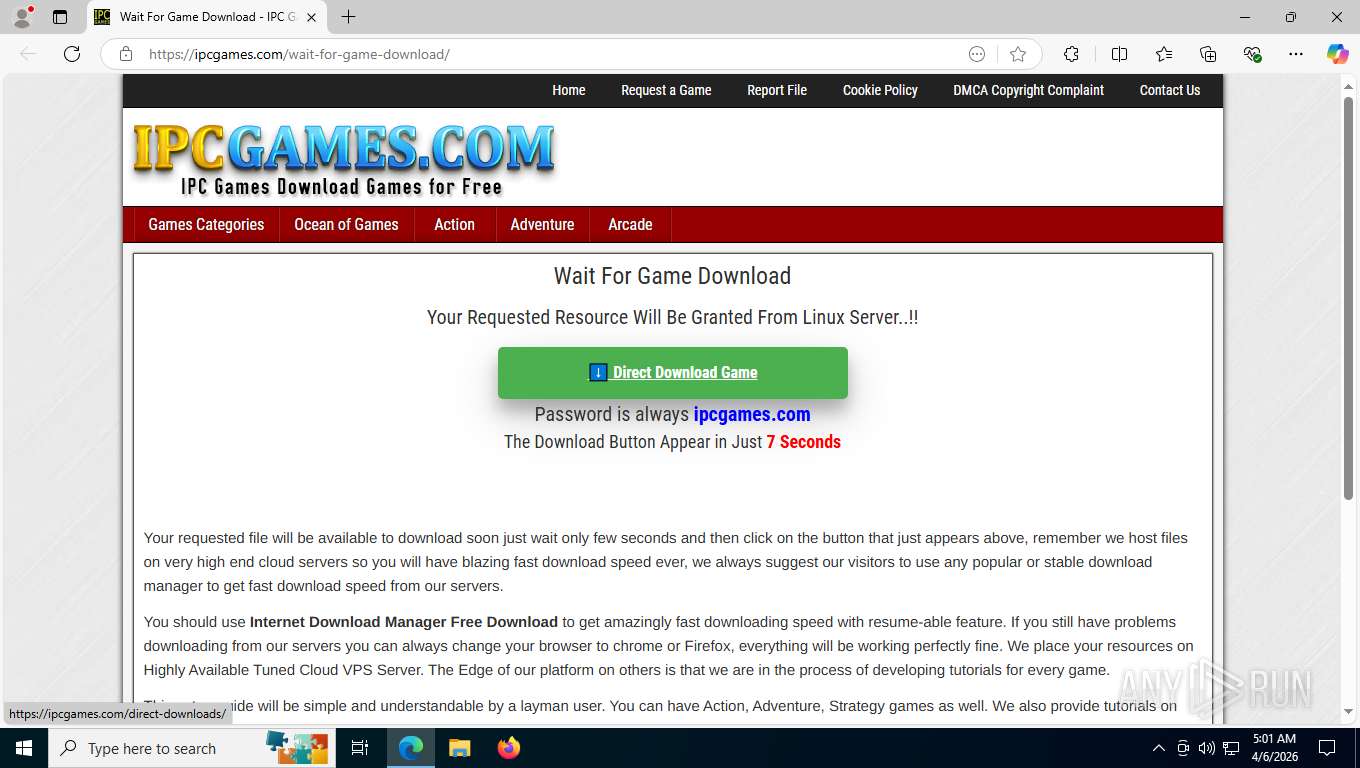
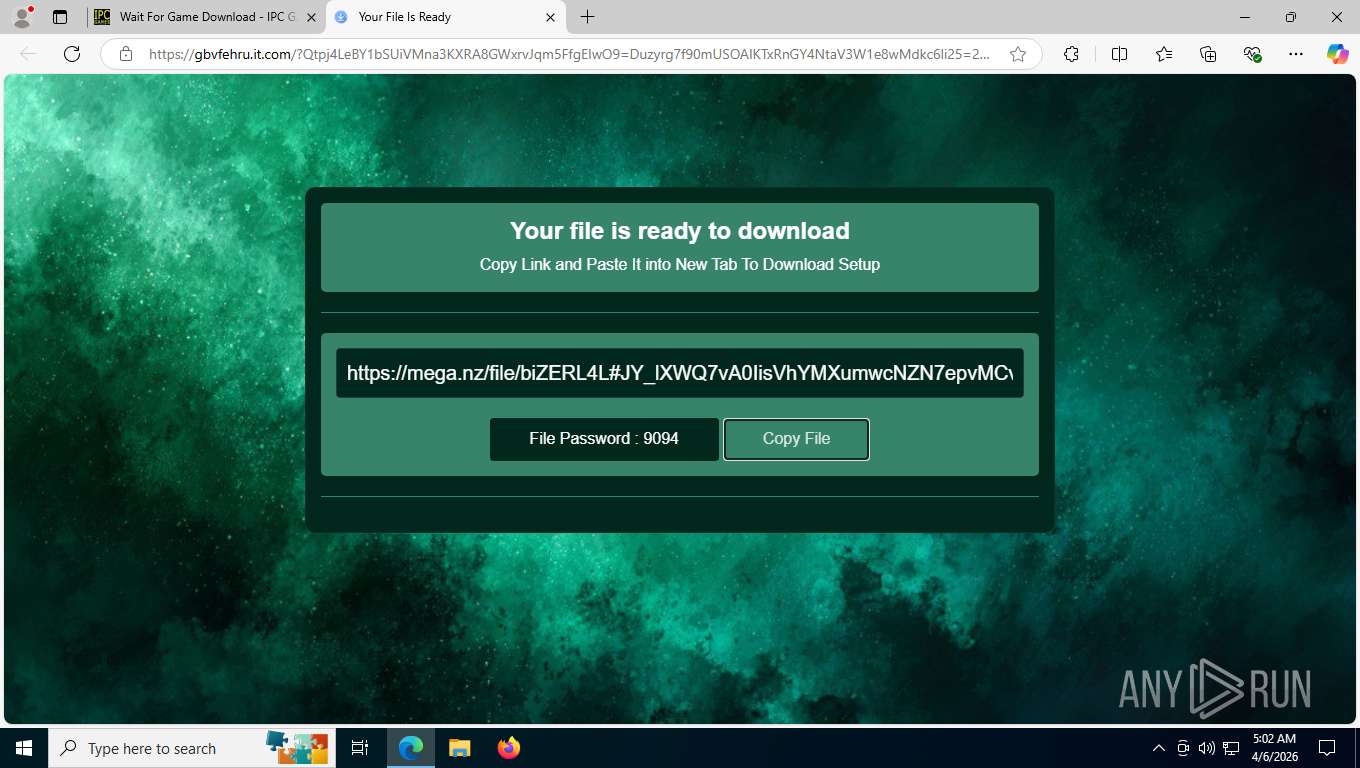
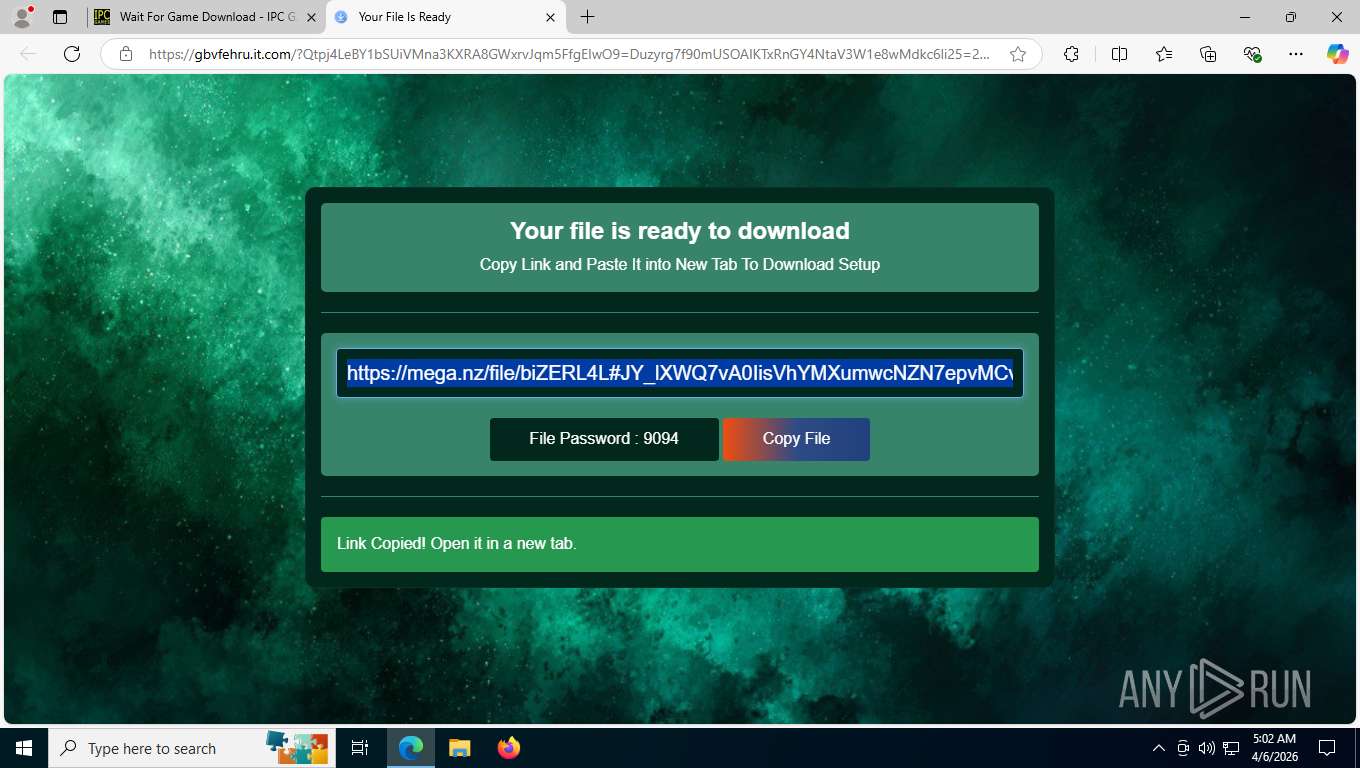
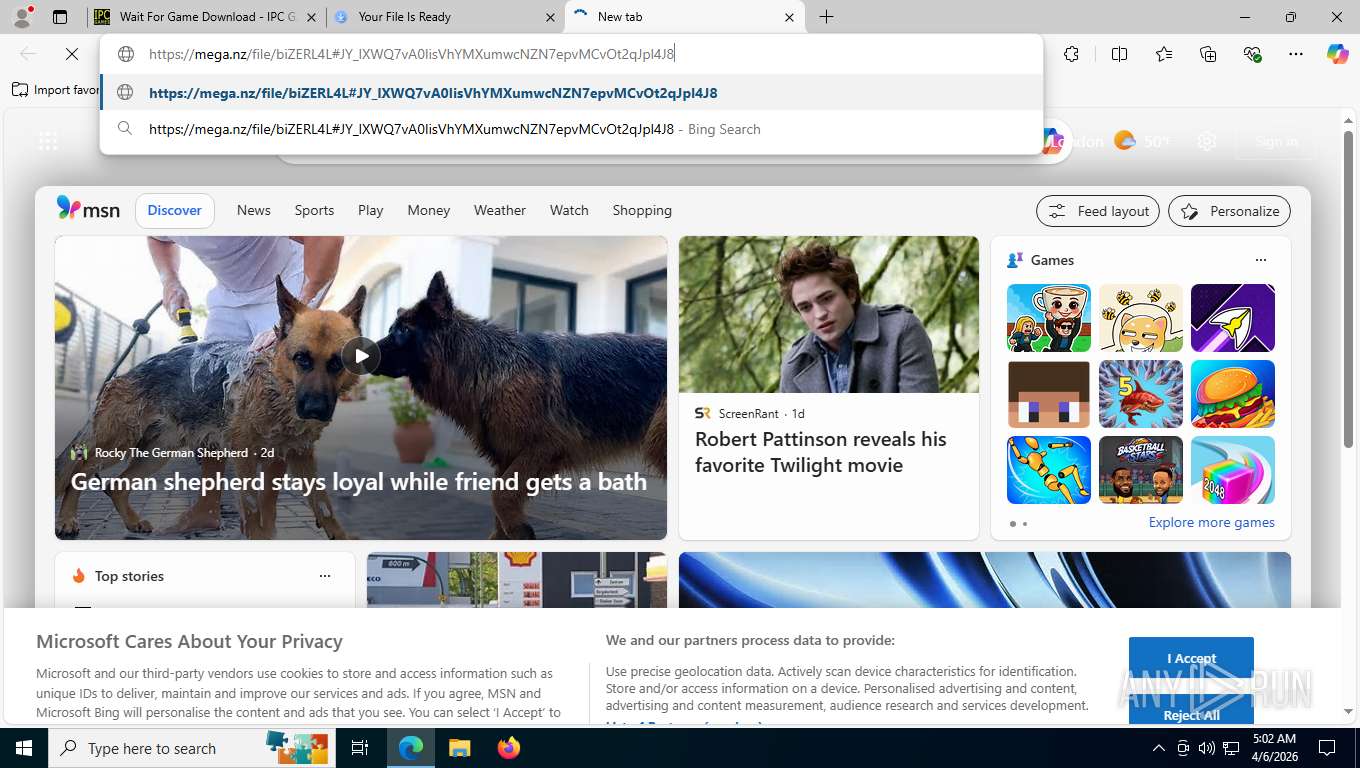
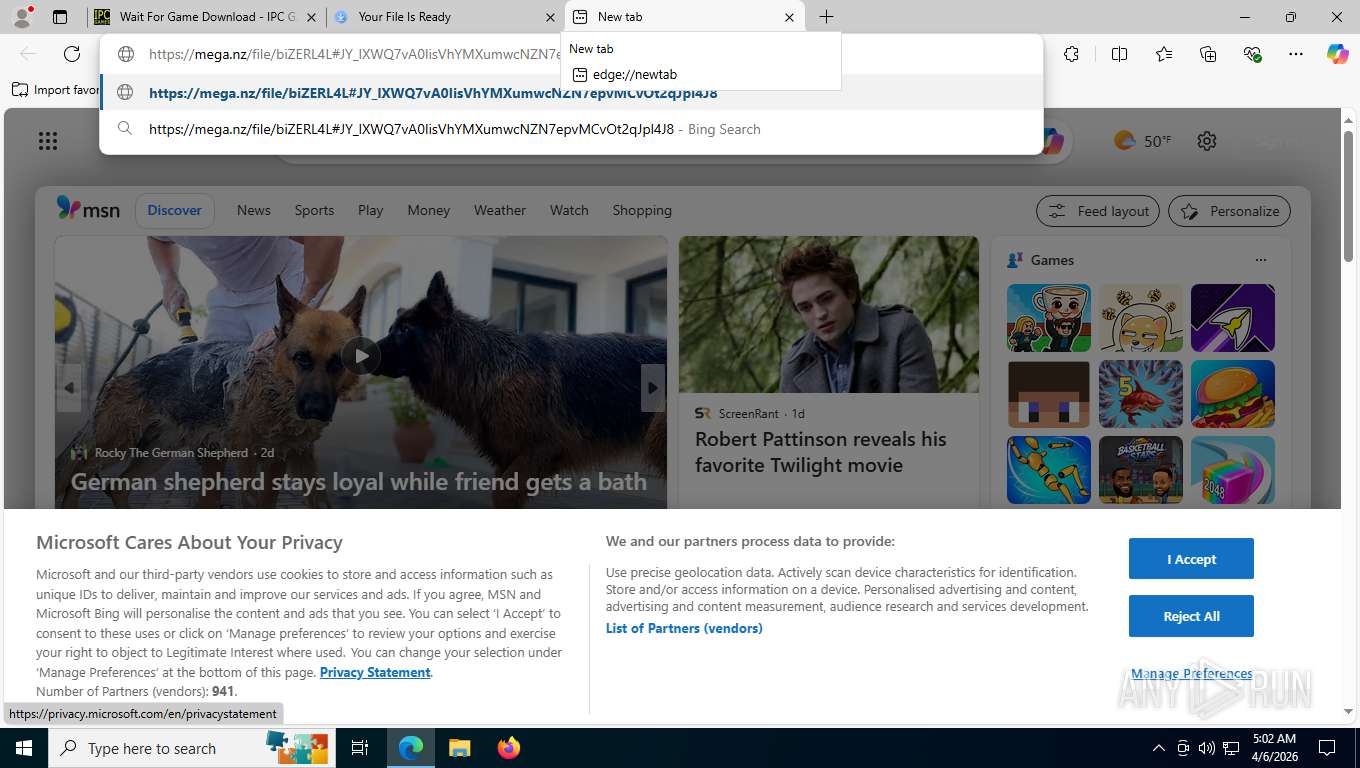
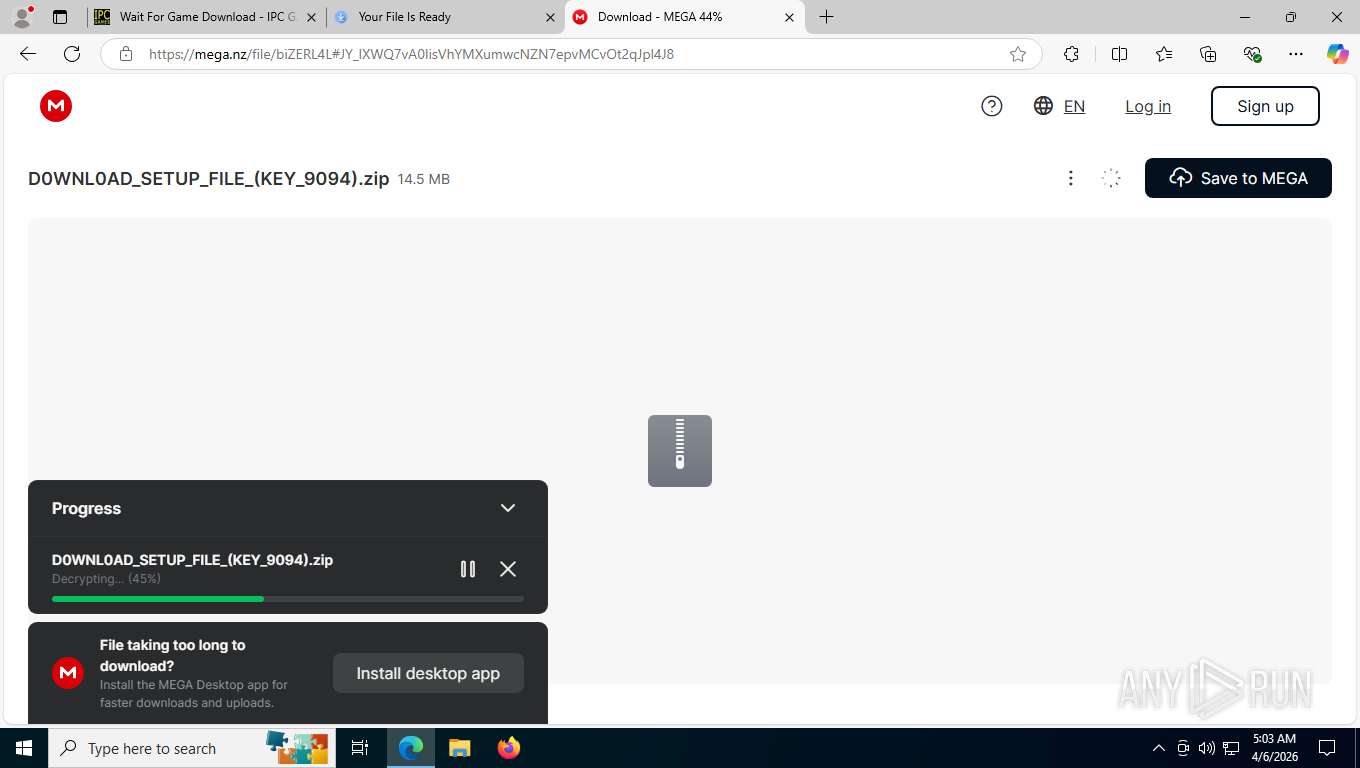
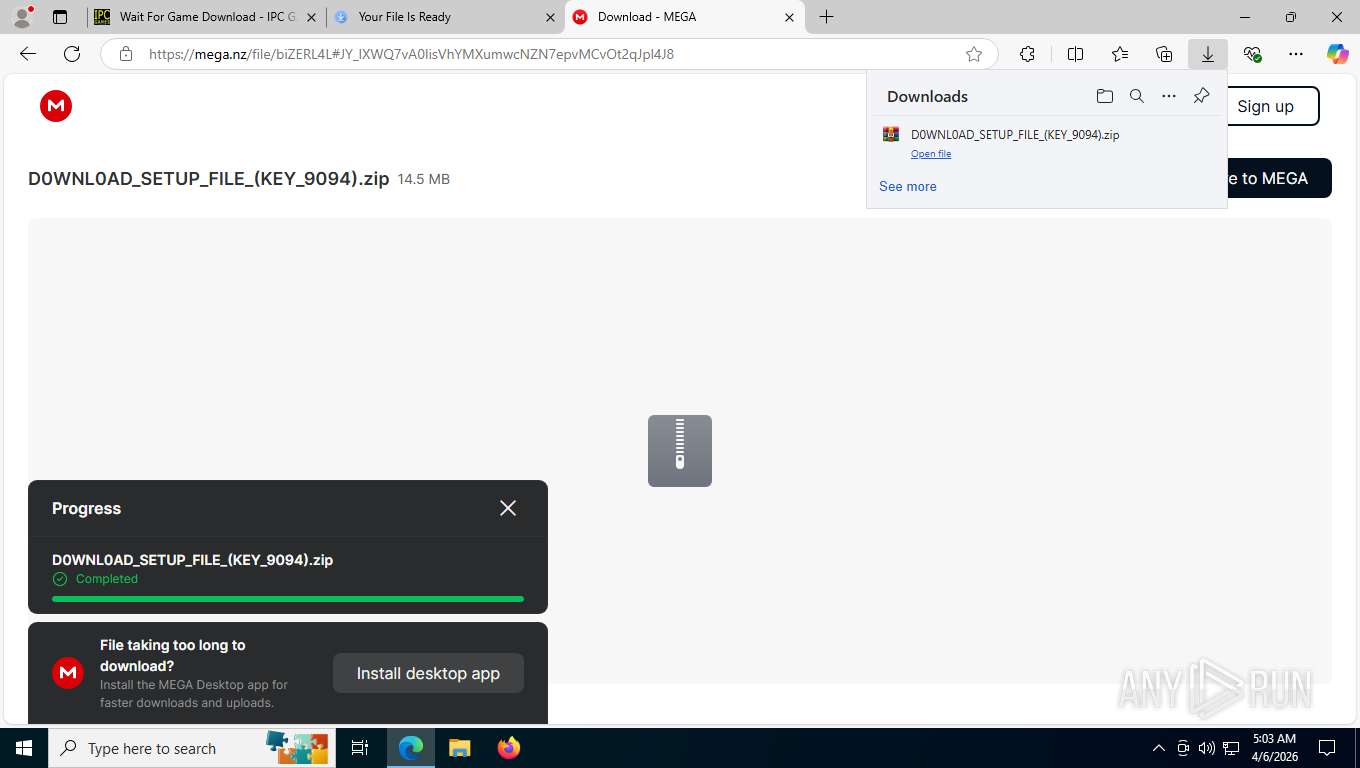
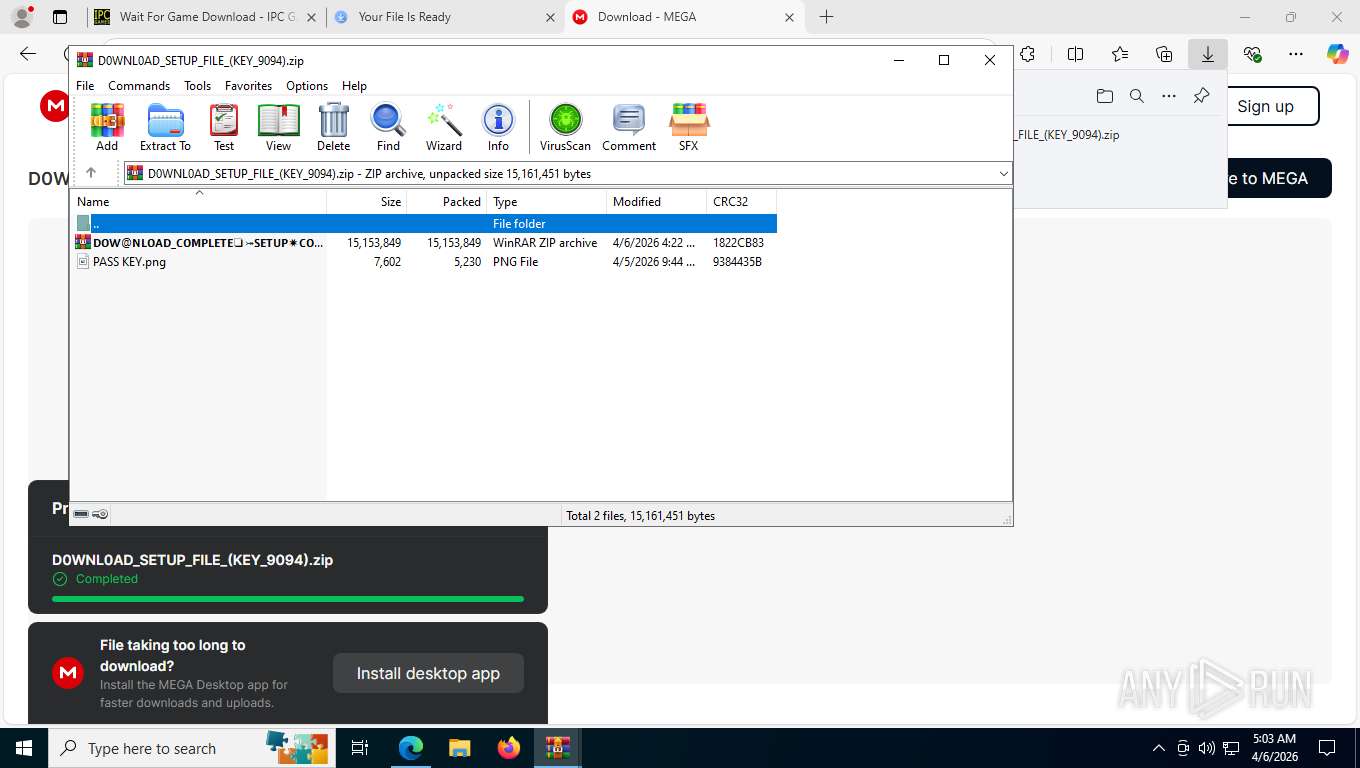
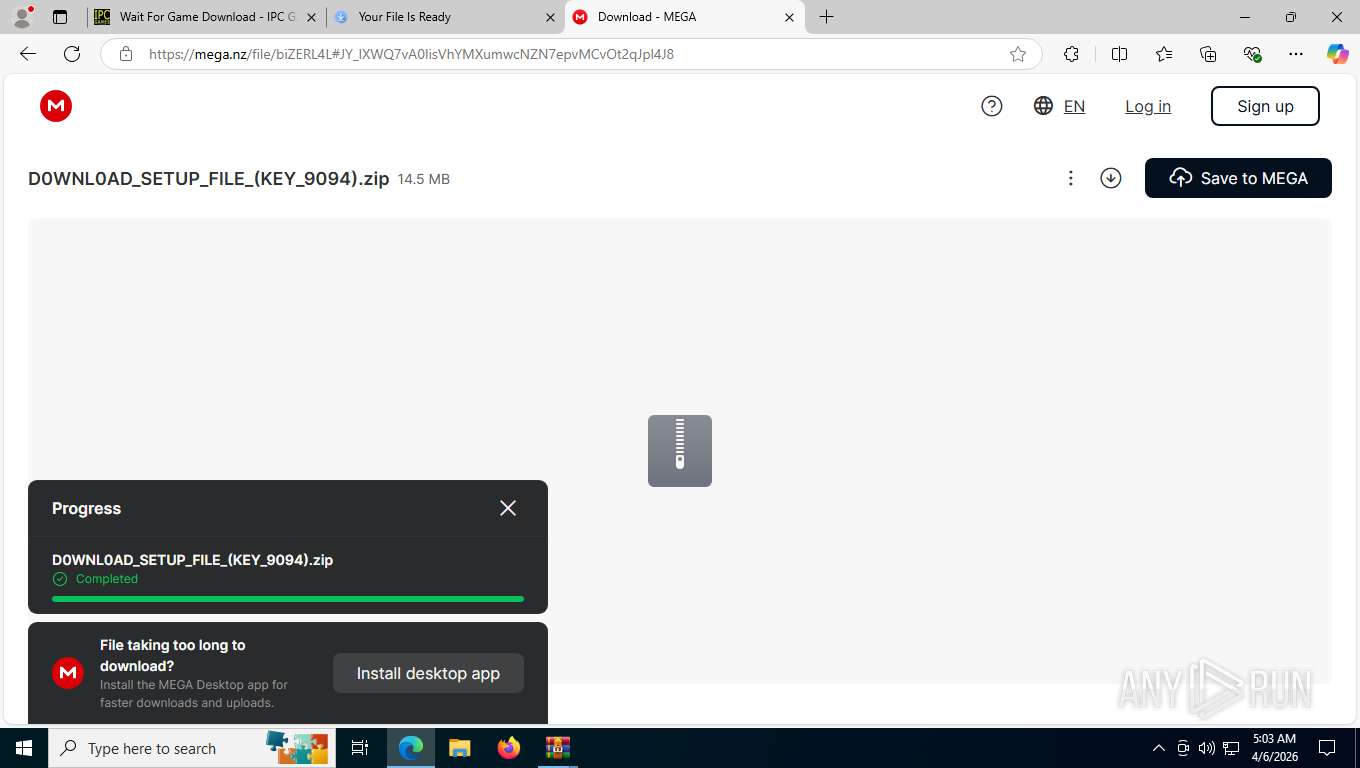
| URL: | https://ipcgames.com/wait-for-game-download/ |
| Full analysis: | https://app.any.run/tasks/0dfea91f-3594-4062-aa3f-0685b6705eb1 |
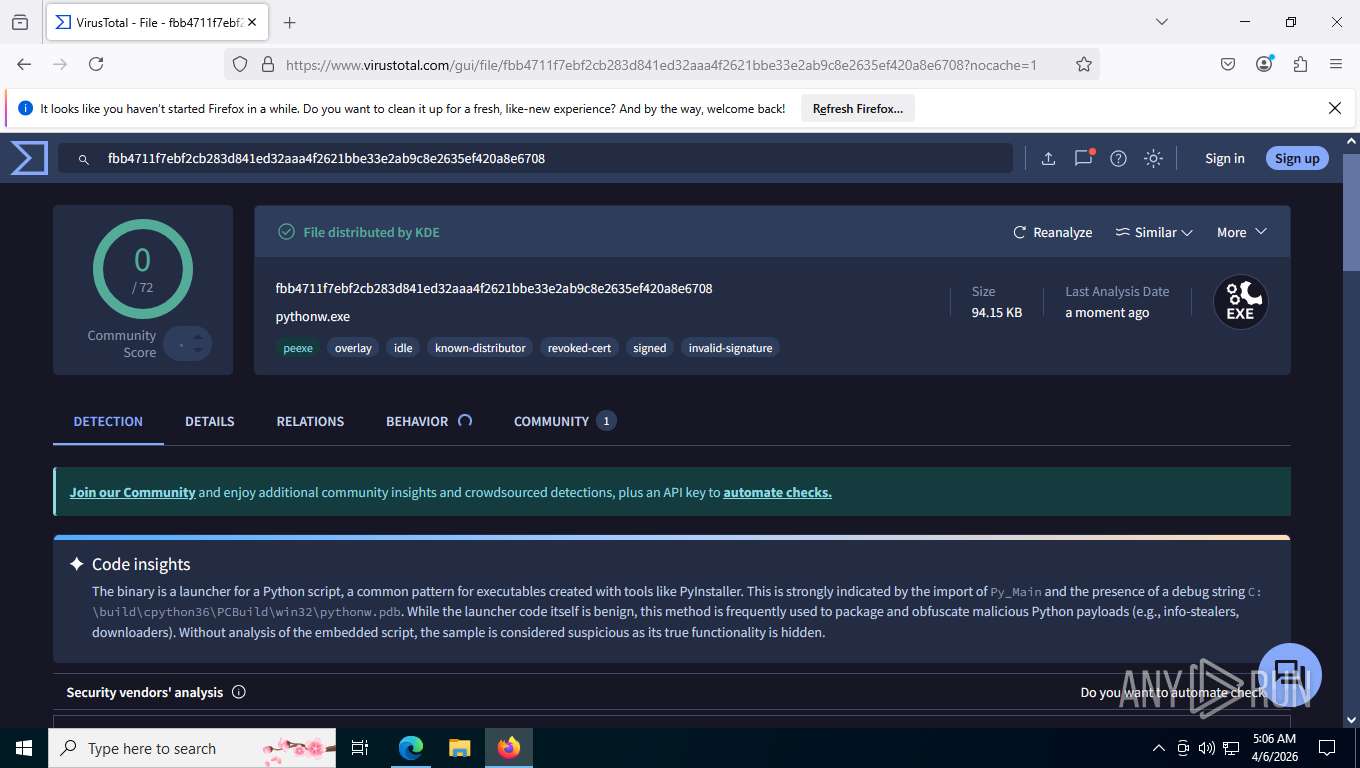
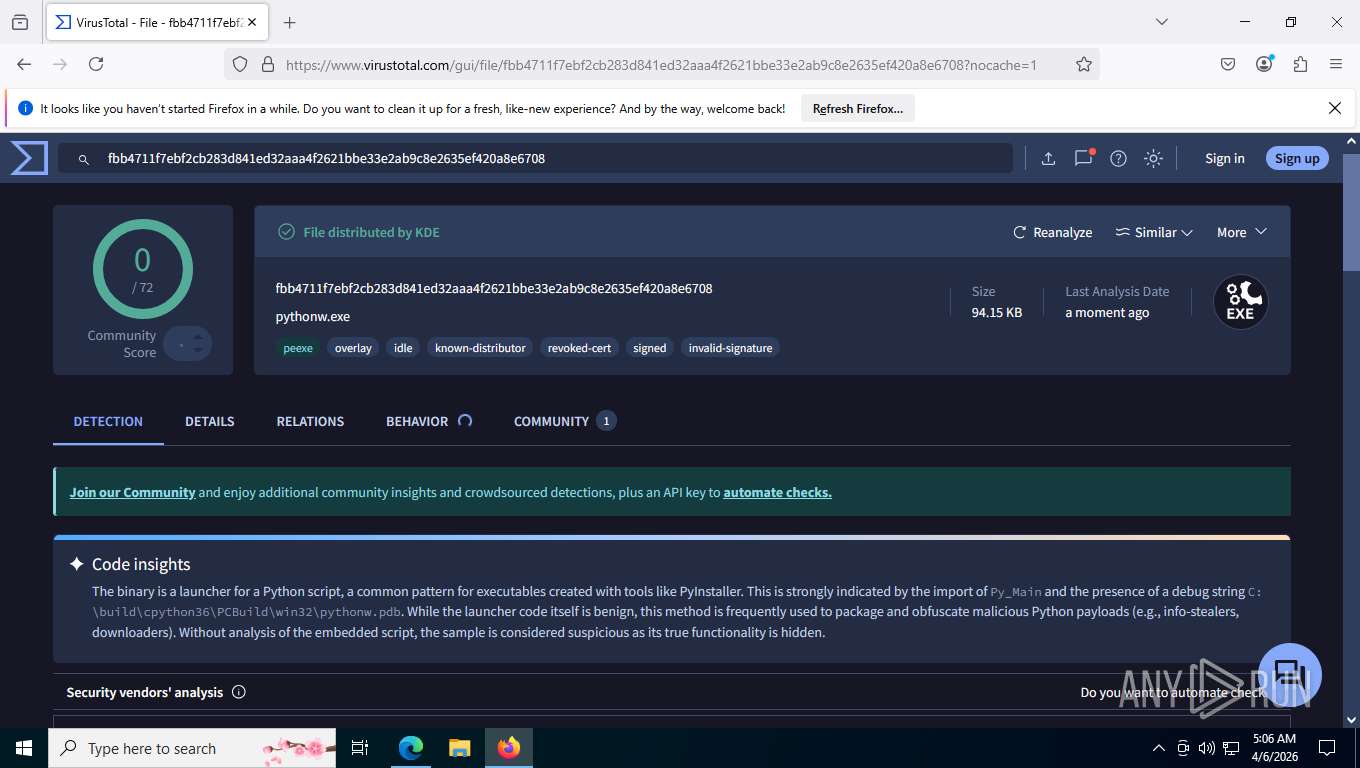
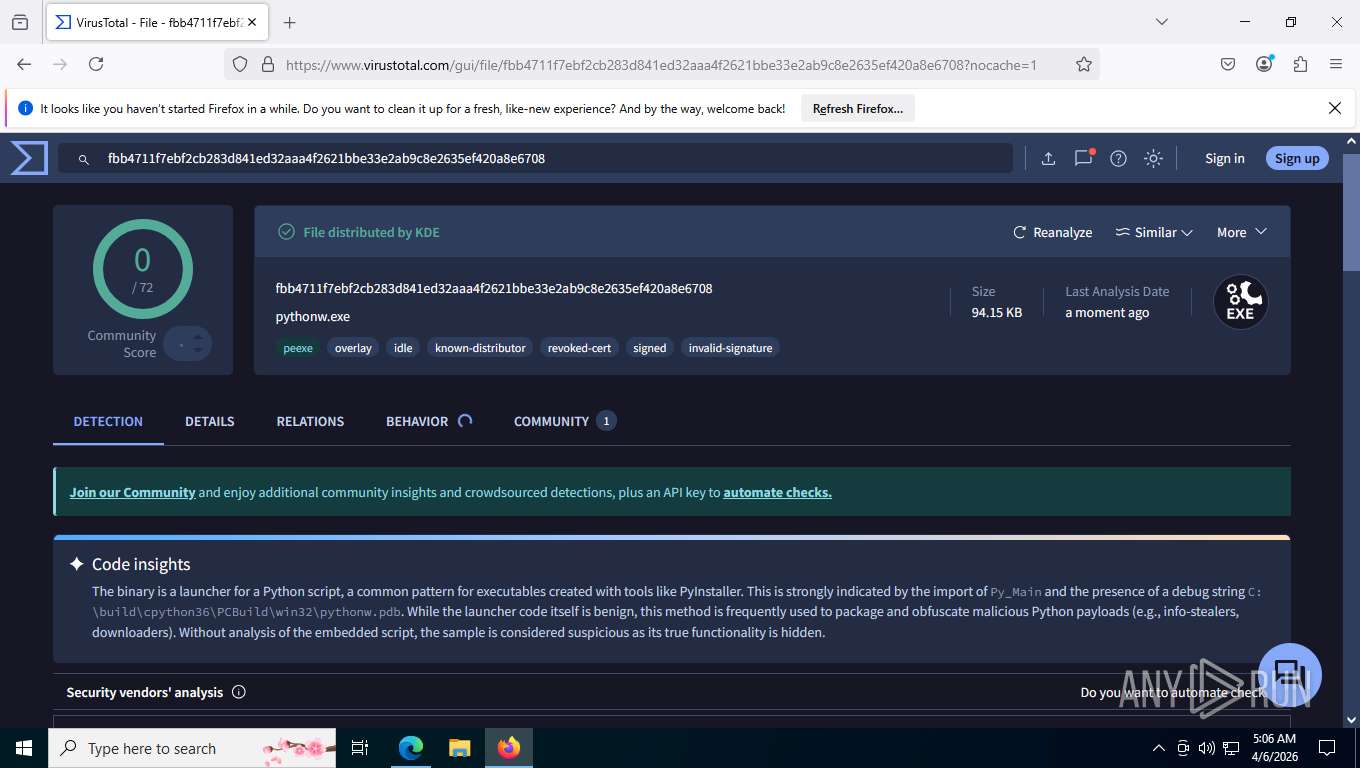
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | April 06, 2026, 09:01:44 |
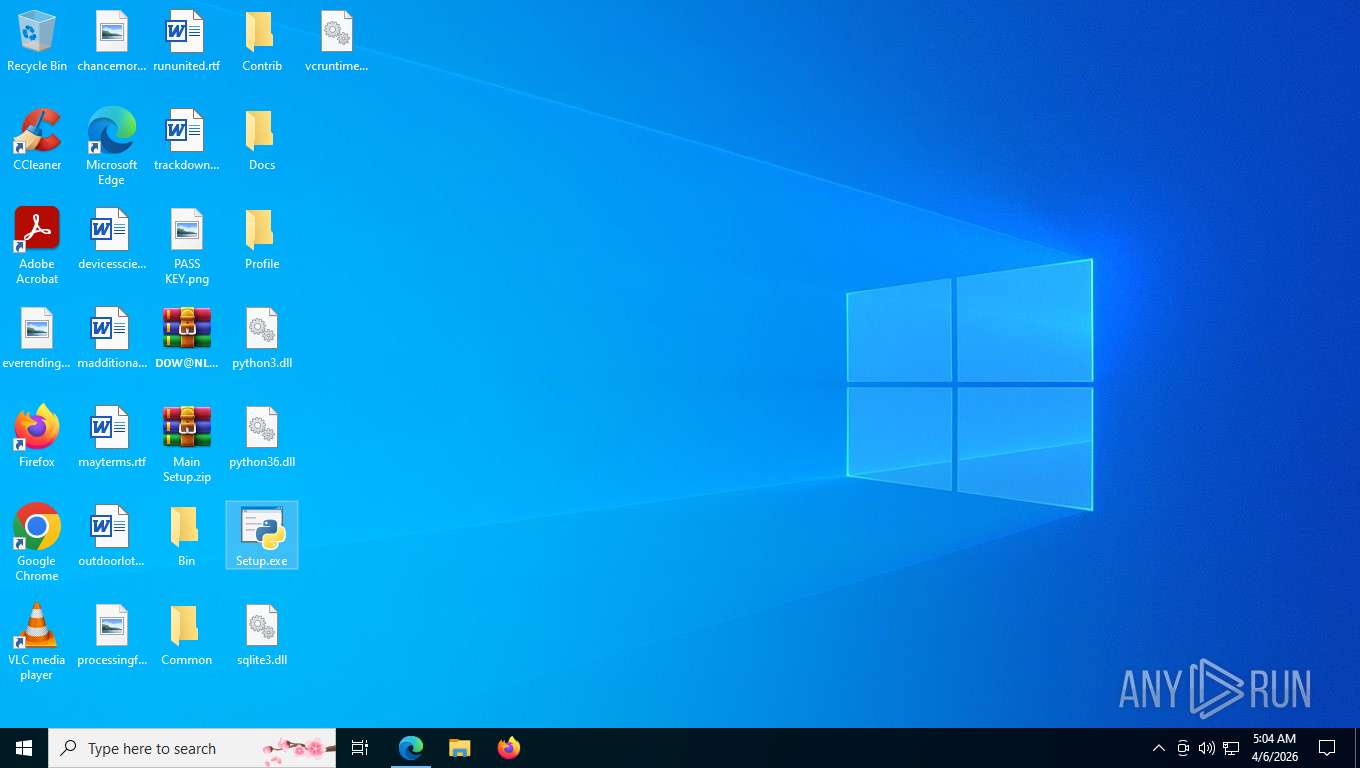
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
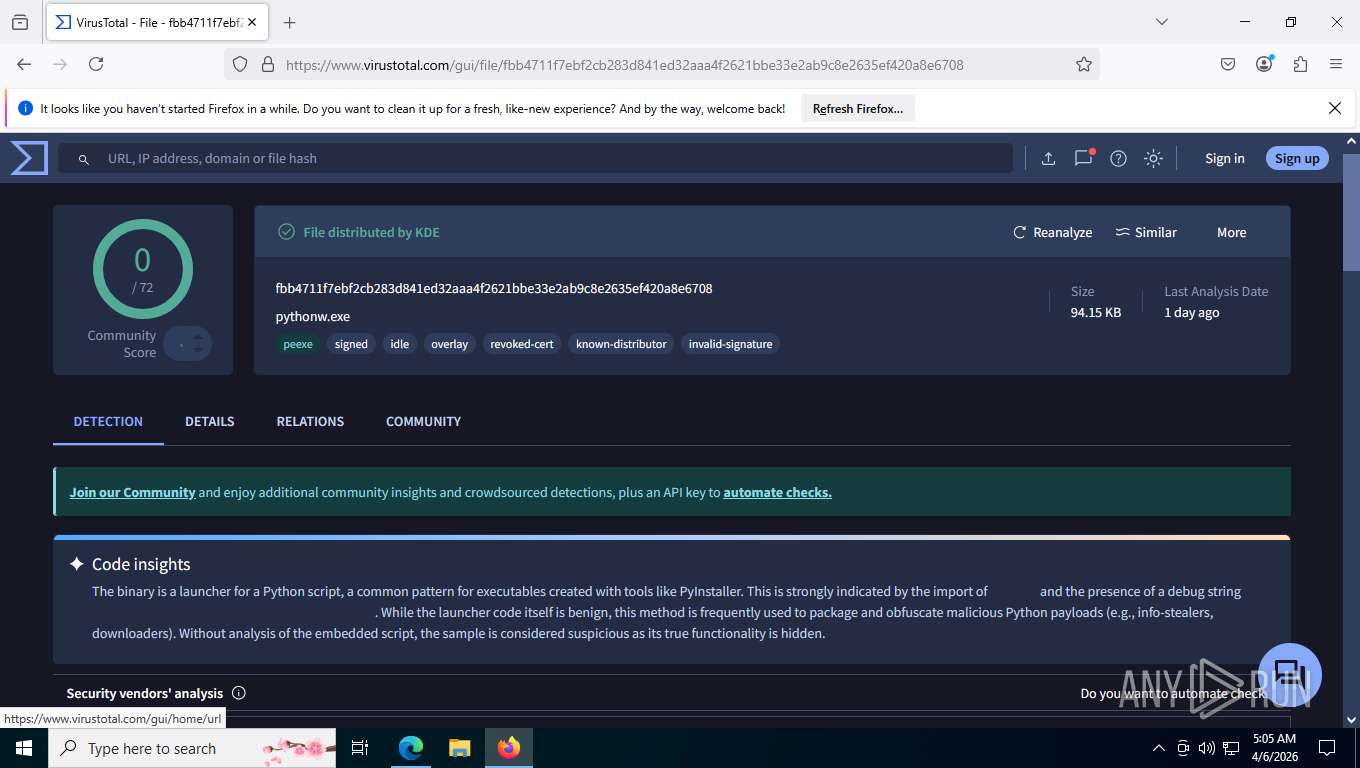
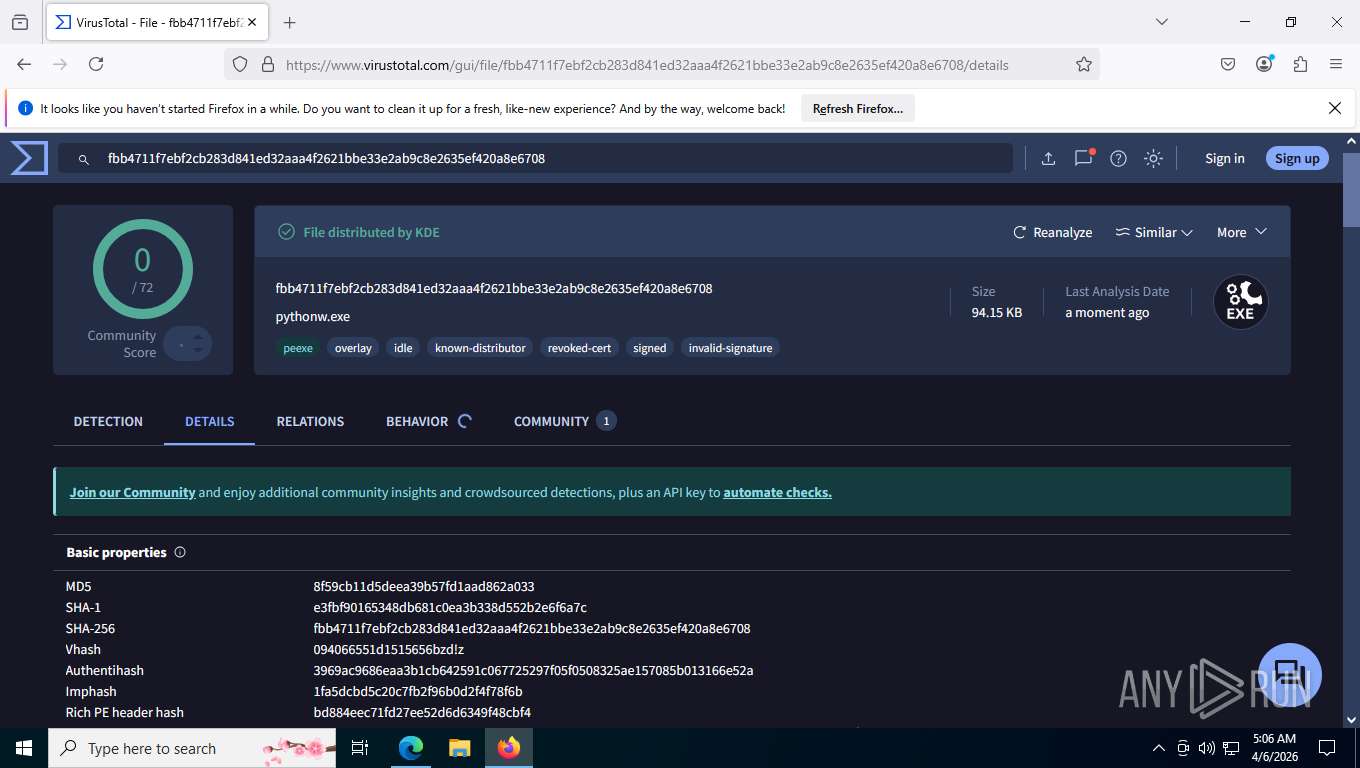
| MD5: | 848C8A892A247547D057BB89B3BE9F14 |
| SHA1: | 9F792D335F1212D16EA110D65043E1A4ED50F776 |
| SHA256: | 836D6A17C7C34619EA22D7799BF4B19C2022815C2ABB43F809CFFCC8899037A2 |
| SSDEEP: | 3:N8UEIzgEQ+MIBLn:2d/L+MIBL |
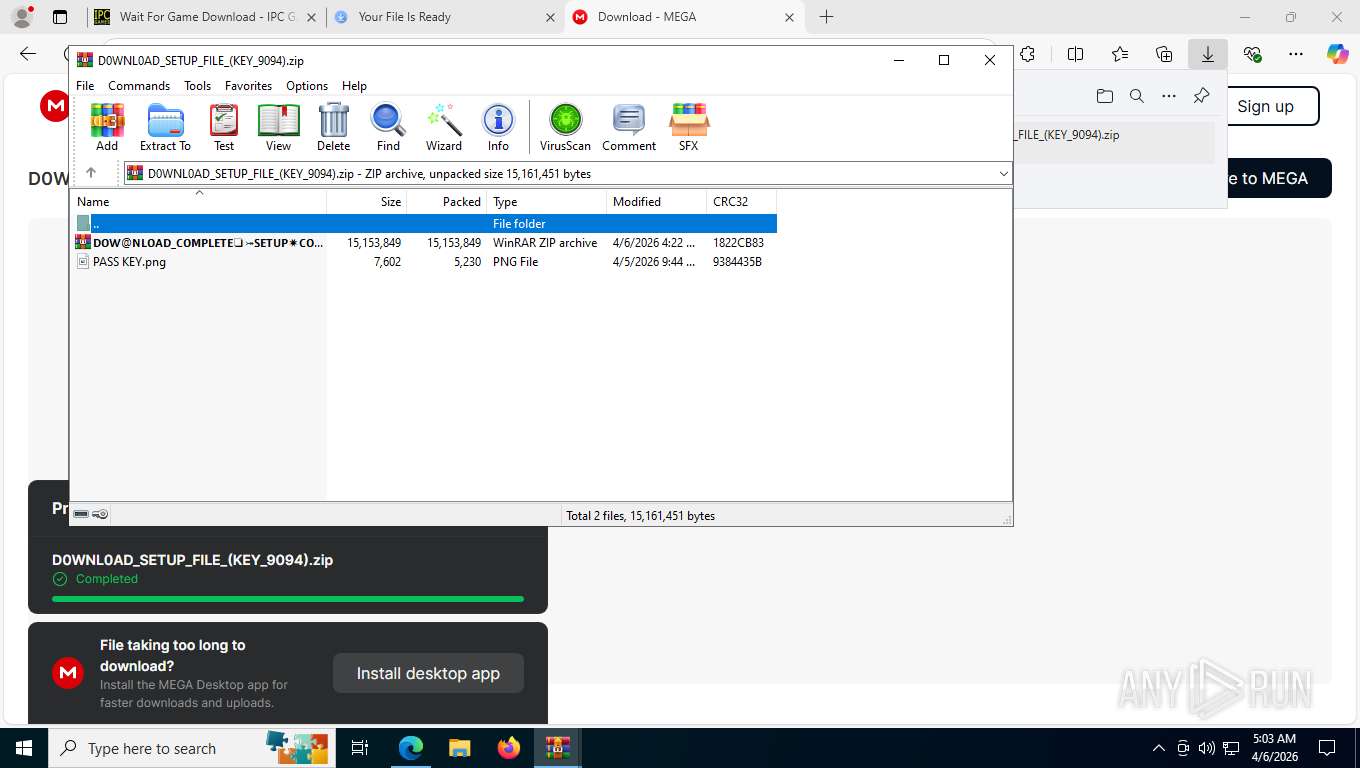
MALICIOUS
Executing a file with an untrusted certificate
- Setup.exe (PID: 7784)
Steals credentials from Web Browsers
- Setup.exe (PID: 7784)
SUSPICIOUS
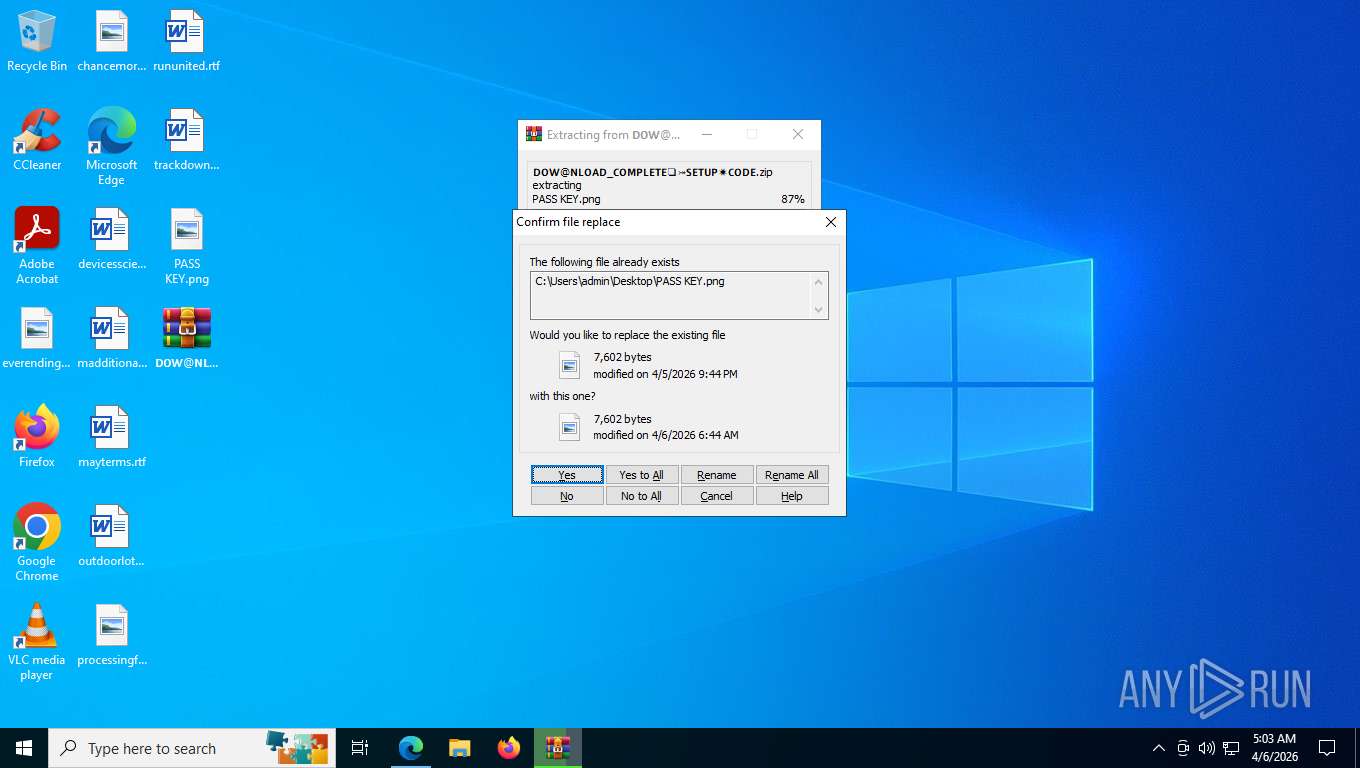
The process creates files with name similar to system file names
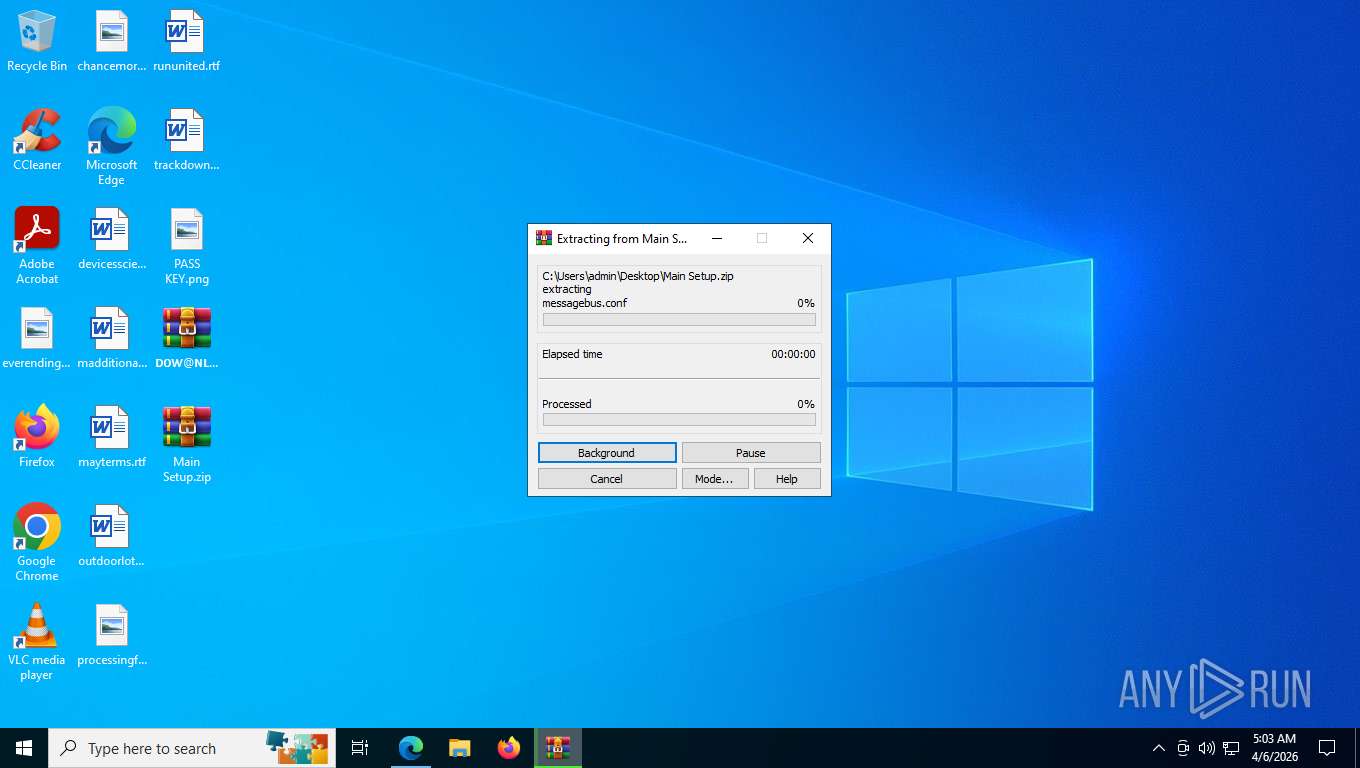
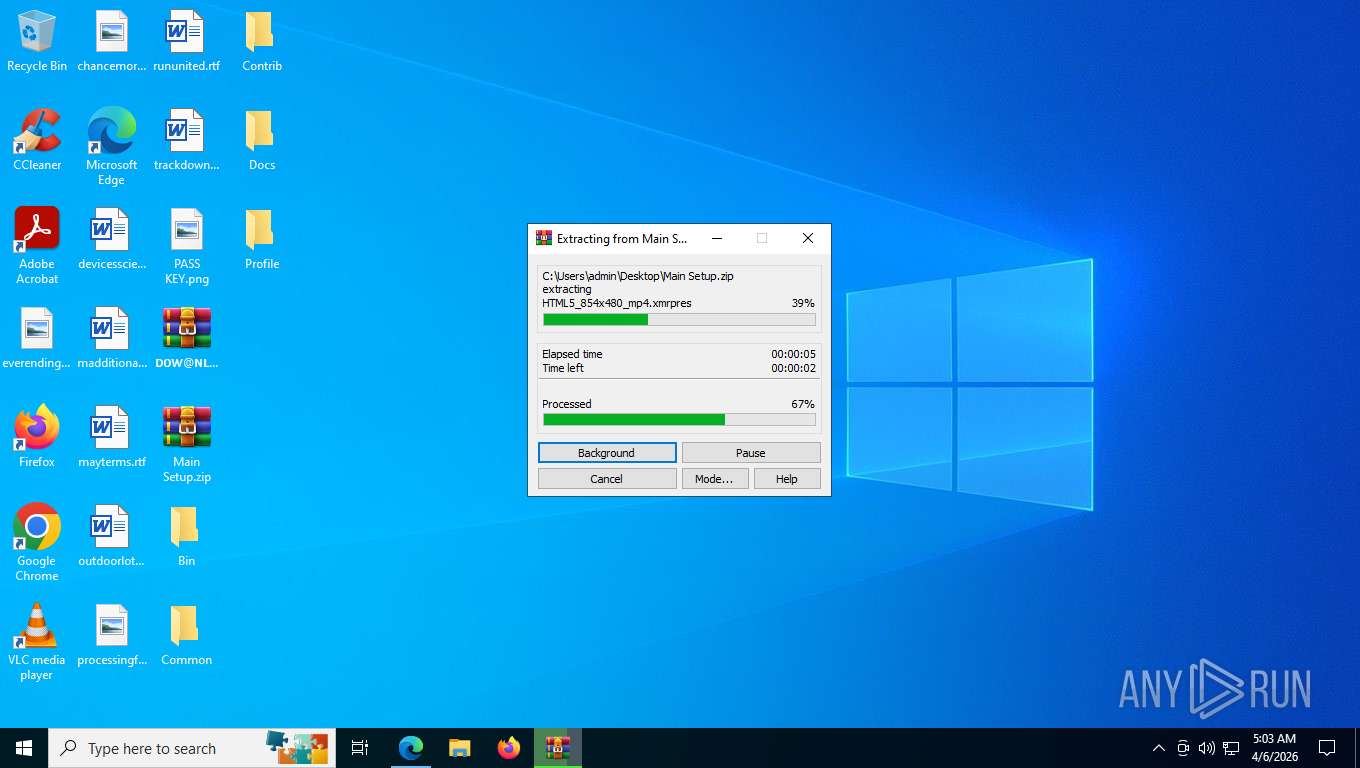
- WinRAR.exe (PID: 7636)
Potential Corporate Privacy Violation
- msedge.exe (PID: 5760)
Possible stealing from crypto wallets
- Setup.exe (PID: 7784)
Searches for installed software
- Setup.exe (PID: 7784)
Browser launch with unusual user-data-dir
- chrome.exe (PID: 2736)
- chrome.exe (PID: 10356)
Browser headless start
- chrome.exe (PID: 8708)
- chrome.exe (PID: 10540)
Browser sandbox disabling
- chrome.exe (PID: 8708)
- chrome.exe (PID: 2300)
- chrome.exe (PID: 8716)
- chrome.exe (PID: 2952)
- chrome.exe (PID: 3168)
- chrome.exe (PID: 7500)
- chrome.exe (PID: 8680)
- chrome.exe (PID: 7856)
- chrome.exe (PID: 5392)
- chrome.exe (PID: 8972)
- chrome.exe (PID: 4176)
- chrome.exe (PID: 8744)
- chrome.exe (PID: 8760)
- chrome.exe (PID: 8928)
- chrome.exe (PID: 1284)
- chrome.exe (PID: 8732)
- chrome.exe (PID: 1116)
- chrome.exe (PID: 552)
- chrome.exe (PID: 8844)
- chrome.exe (PID: 7960)
- chrome.exe (PID: 4328)
- chrome.exe (PID: 7572)
- chrome.exe (PID: 8024)
- chrome.exe (PID: 7924)
- chrome.exe (PID: 800)
- chrome.exe (PID: 4548)
- chrome.exe (PID: 7288)
- chrome.exe (PID: 5400)
- chrome.exe (PID: 7096)
- chrome.exe (PID: 1164)
- chrome.exe (PID: 5420)
- chrome.exe (PID: 8024)
- chrome.exe (PID: 9284)
- chrome.exe (PID: 9468)
- chrome.exe (PID: 9548)
- chrome.exe (PID: 9648)
- chrome.exe (PID: 9556)
- chrome.exe (PID: 9712)
- chrome.exe (PID: 9724)
- chrome.exe (PID: 9792)
- chrome.exe (PID: 9936)
- chrome.exe (PID: 9928)
- chrome.exe (PID: 9828)
- chrome.exe (PID: 9944)
- chrome.exe (PID: 10100)
- chrome.exe (PID: 10060)
- chrome.exe (PID: 10172)
- chrome.exe (PID: 10200)
- chrome.exe (PID: 9248)
- chrome.exe (PID: 5664)
- chrome.exe (PID: 800)
- chrome.exe (PID: 9088)
- chrome.exe (PID: 10540)
- chrome.exe (PID: 8912)
- chrome.exe (PID: 9872)
- chrome.exe (PID: 10304)
- chrome.exe (PID: 10564)
- chrome.exe (PID: 10552)
- chrome.exe (PID: 10776)
- chrome.exe (PID: 10620)
- chrome.exe (PID: 10612)
- chrome.exe (PID: 10704)
- chrome.exe (PID: 10712)
- chrome.exe (PID: 10764)
- chrome.exe (PID: 10860)
- chrome.exe (PID: 11080)
- chrome.exe (PID: 11184)
- chrome.exe (PID: 11208)
- chrome.exe (PID: 11192)
- chrome.exe (PID: 11200)
- chrome.exe (PID: 11216)
- chrome.exe (PID: 6792)
- chrome.exe (PID: 8080)
- chrome.exe (PID: 1180)
- chrome.exe (PID: 8876)
- chrome.exe (PID: 8724)
- chrome.exe (PID: 9000)
- chrome.exe (PID: 9756)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 1400)
- chrome.exe (PID: 7612)
- chrome.exe (PID: 552)
- chrome.exe (PID: 10772)
- chrome.exe (PID: 10348)
- chrome.exe (PID: 11140)
- chrome.exe (PID: 11136)
- chrome.exe (PID: 10304)
- chrome.exe (PID: 8680)
- chrome.exe (PID: 8376)
- chrome.exe (PID: 9756)
- chrome.exe (PID: 11156)
- chrome.exe (PID: 11256)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 4336)
- chrome.exe (PID: 9008)
- chrome.exe (PID: 3100)
- chrome.exe (PID: 11092)
- chrome.exe (PID: 1528)
- chrome.exe (PID: 9924)
- chrome.exe (PID: 10344)
- chrome.exe (PID: 10376)
- chrome.exe (PID: 11236)
- chrome.exe (PID: 11196)
- chrome.exe (PID: 10924)
- chrome.exe (PID: 11136)
- chrome.exe (PID: 11200)
- chrome.exe (PID: 5696)
- chrome.exe (PID: 11128)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 8956)
Possible stealing from browsers
- Setup.exe (PID: 7784)
Possible stealing of messenger data
- Setup.exe (PID: 7784)
Possible stealing of FTP data
- Setup.exe (PID: 7784)
Possible stealing of email data
- Setup.exe (PID: 7784)
Possible stealing from 2fa
- Setup.exe (PID: 7784)
Possible stealing of VPN data
- Setup.exe (PID: 7784)
Possible stealing from password managers
- Setup.exe (PID: 7784)
INFO
Context menu (right-click) prevention is present
- msedge.exe (PID: 2452)
Reads the computer name
- identity_helper.exe (PID: 7392)
- Setup.exe (PID: 7784)
Checks supported languages
- identity_helper.exe (PID: 7392)
- Setup.exe (PID: 7784)
Reads Environment values
- identity_helper.exe (PID: 7392)
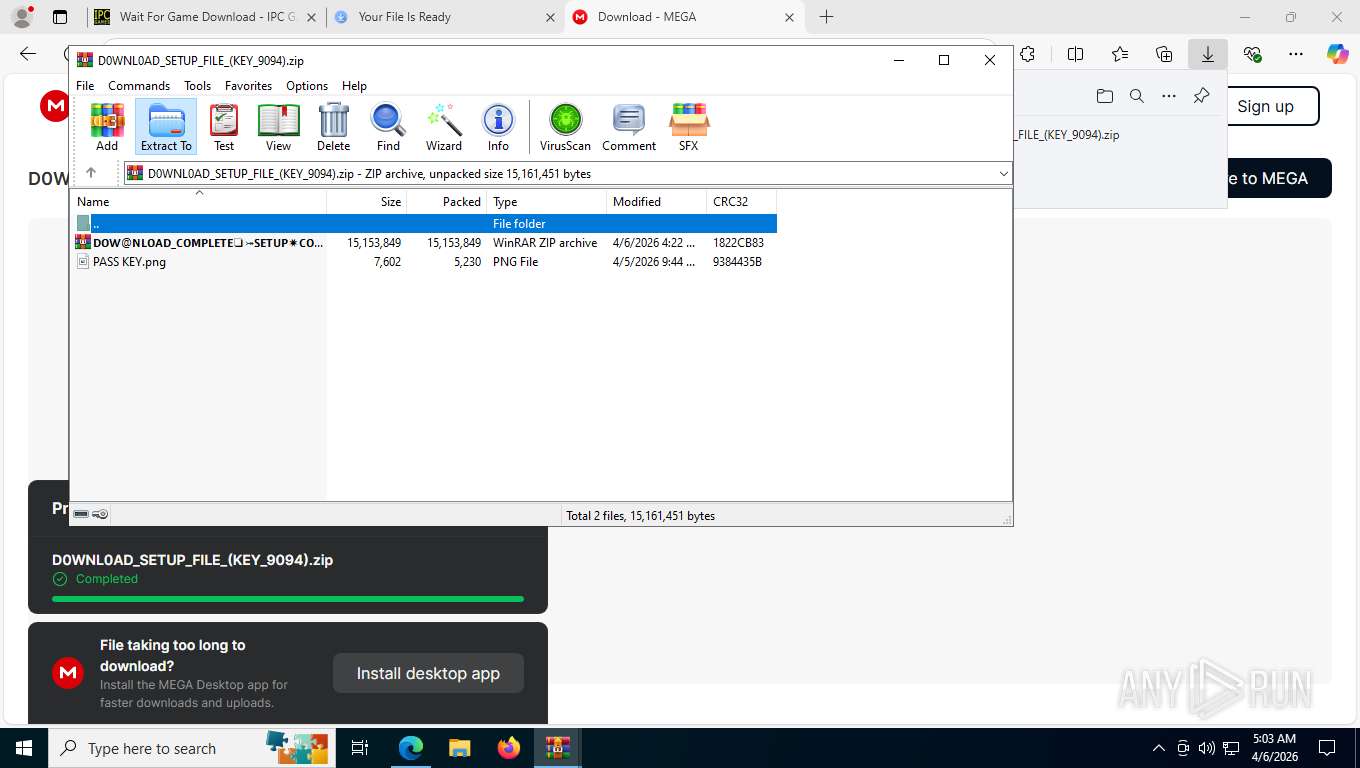
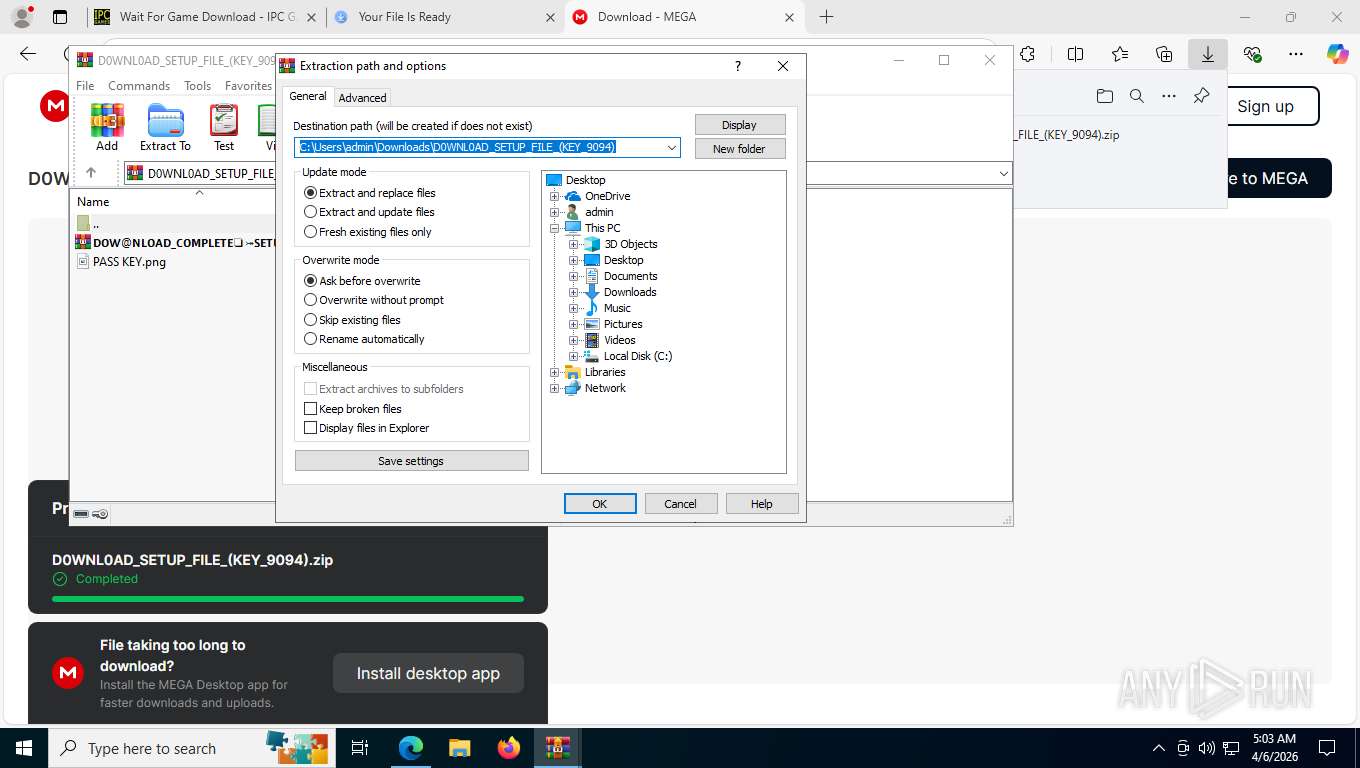
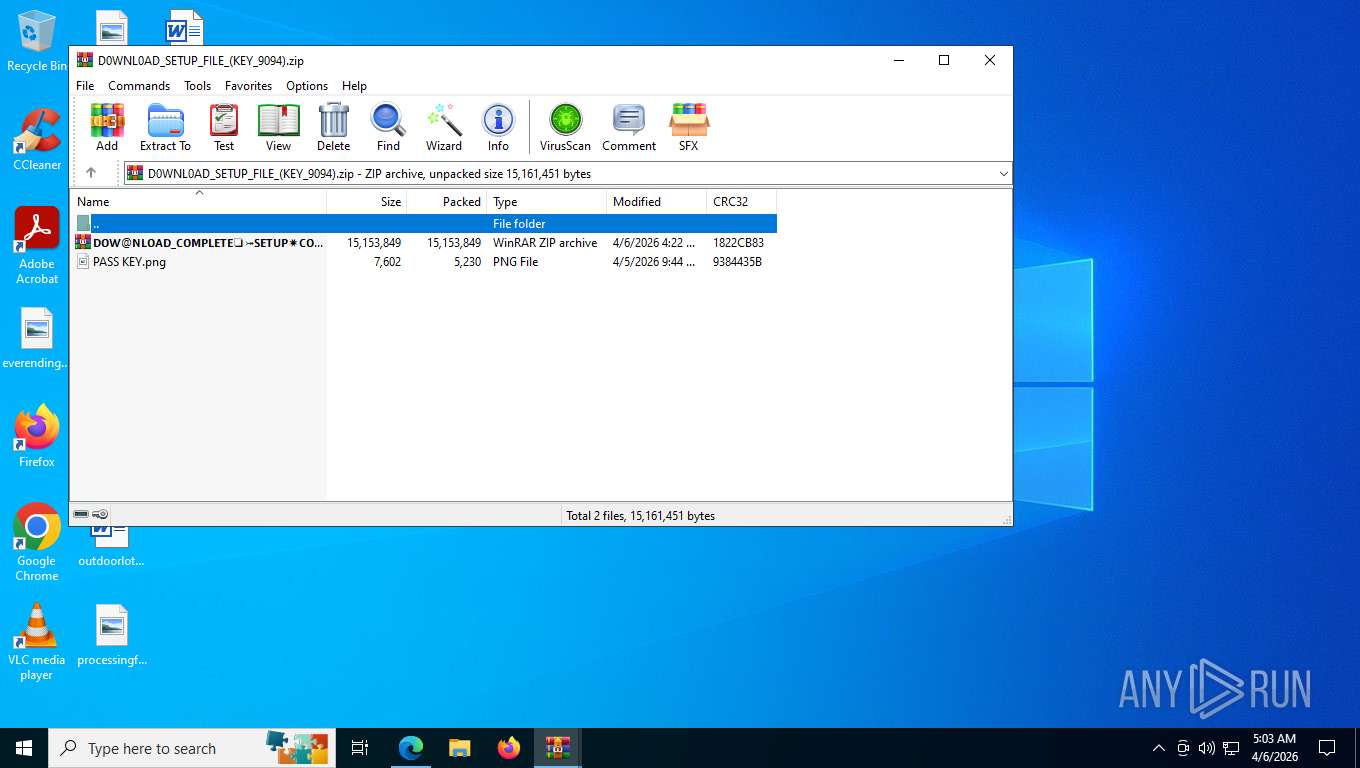
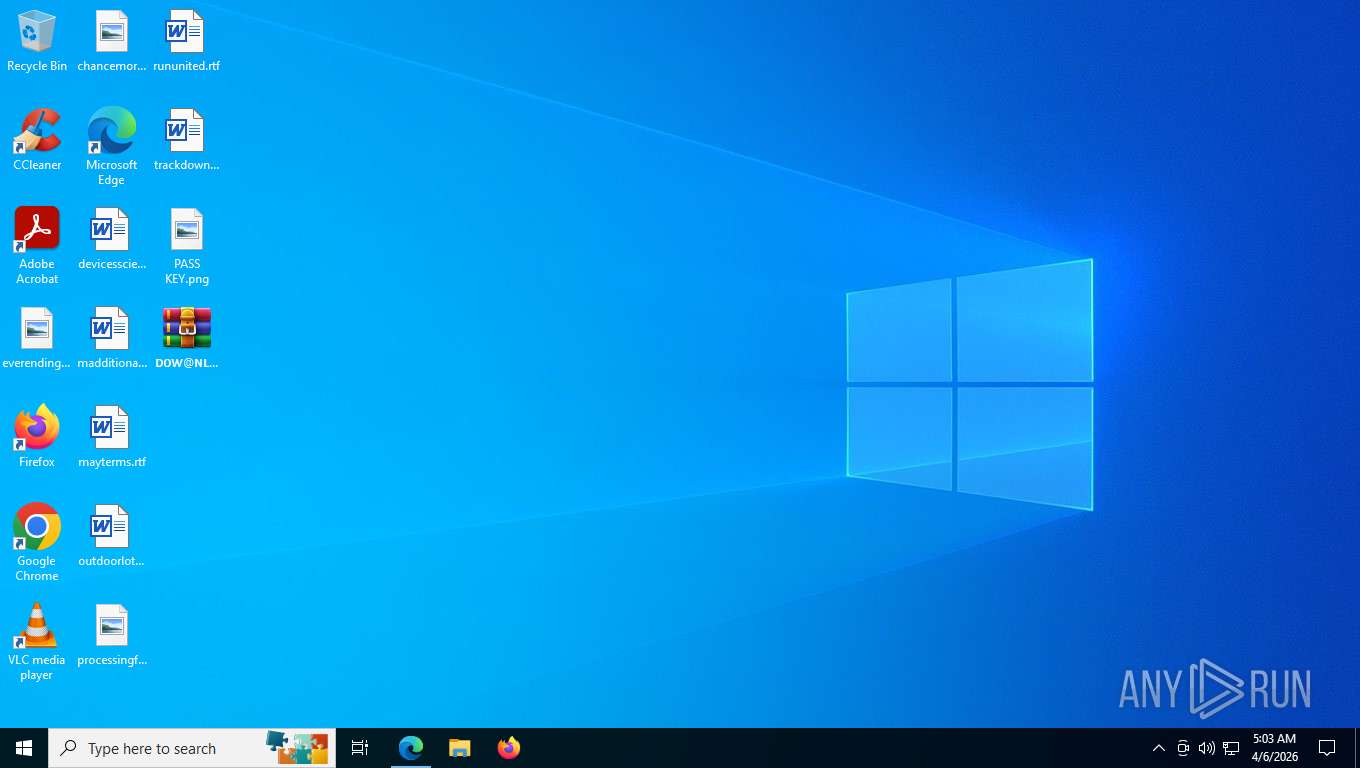
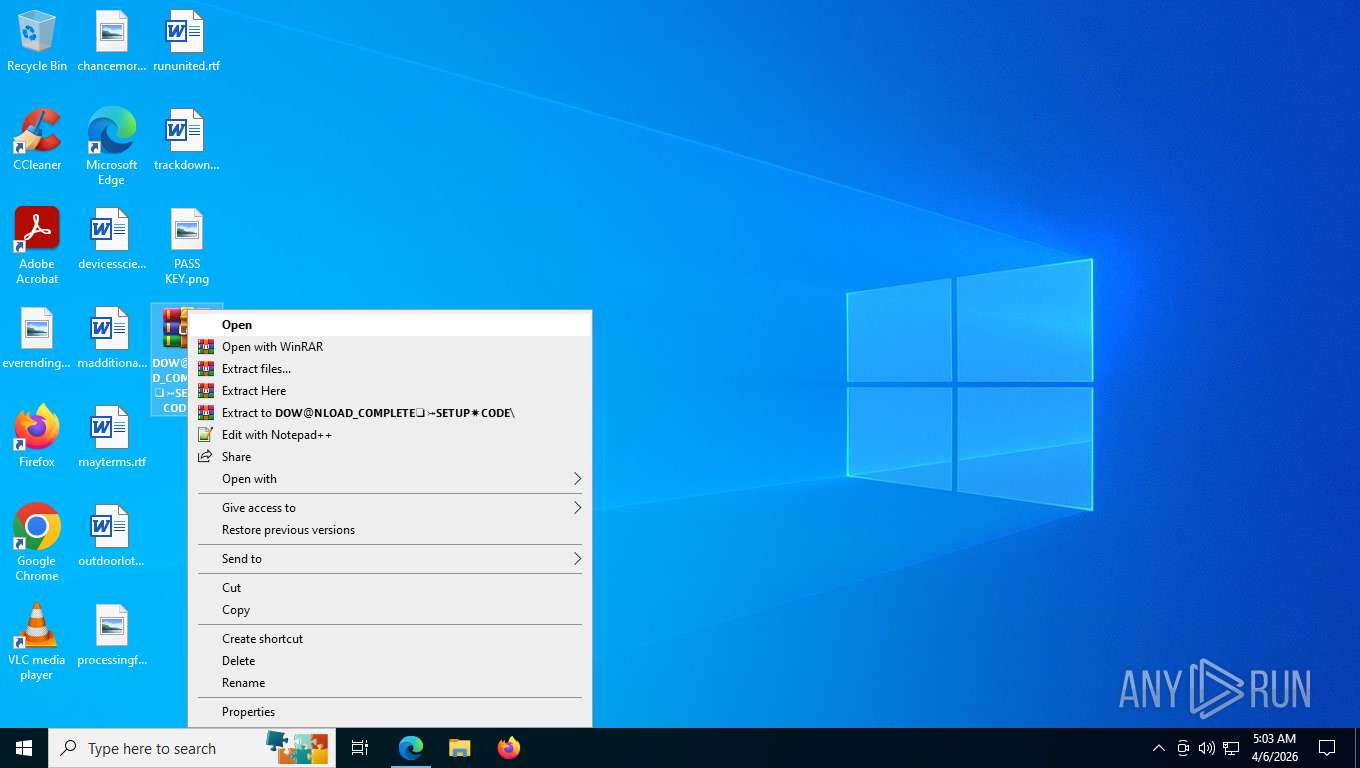
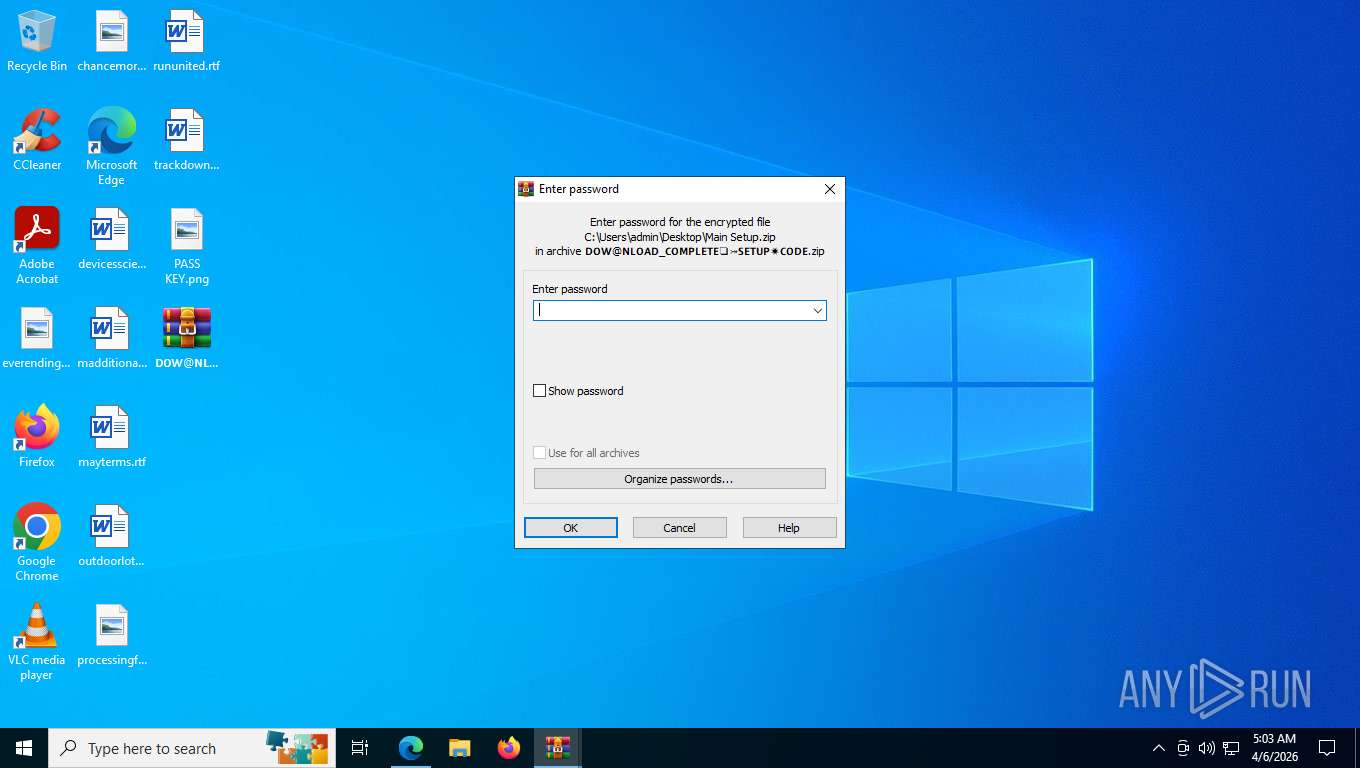
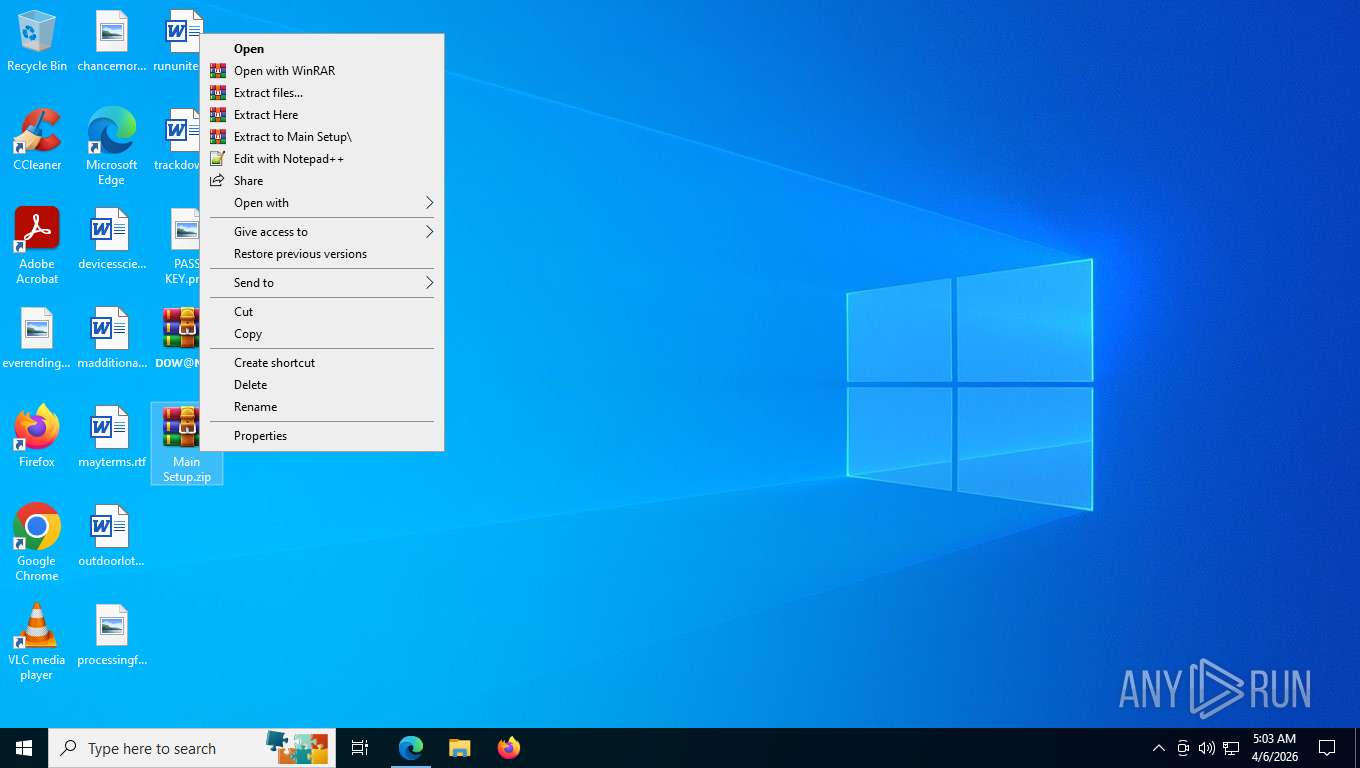
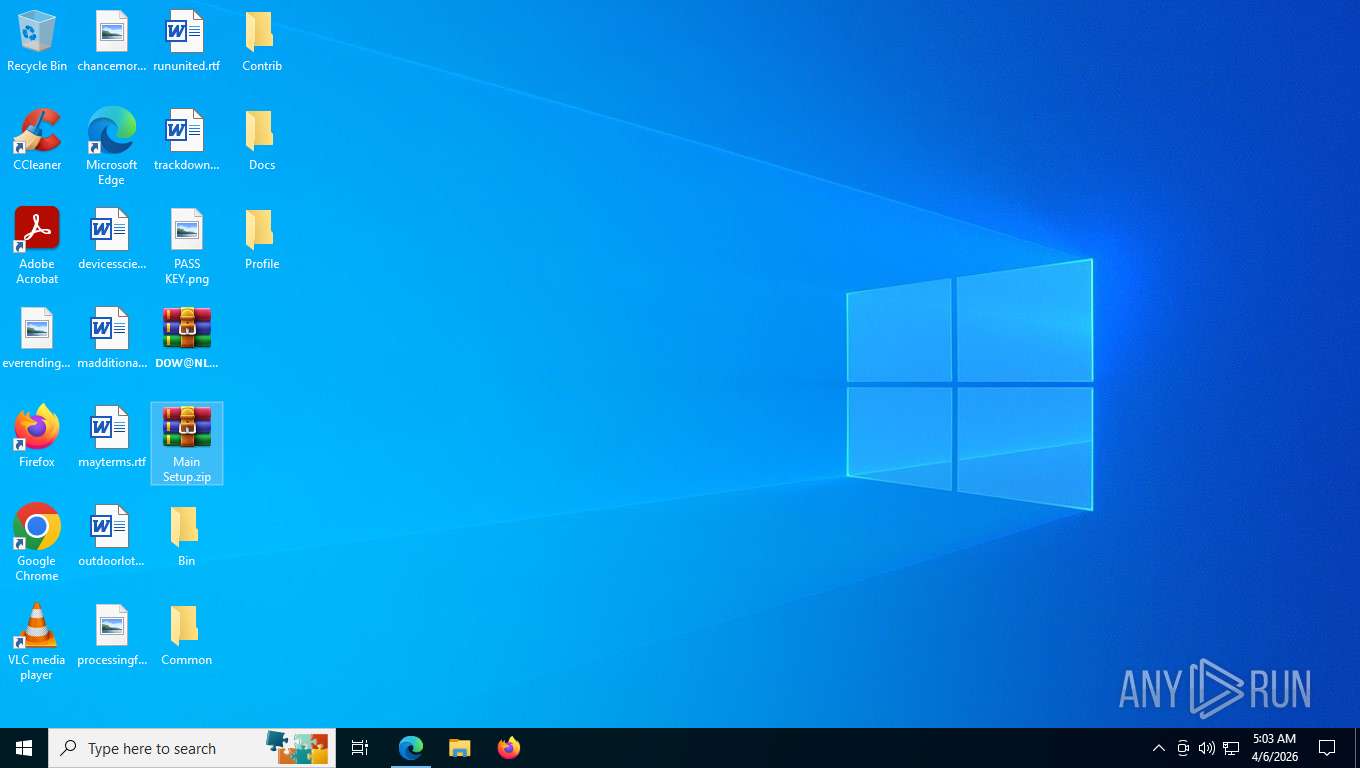
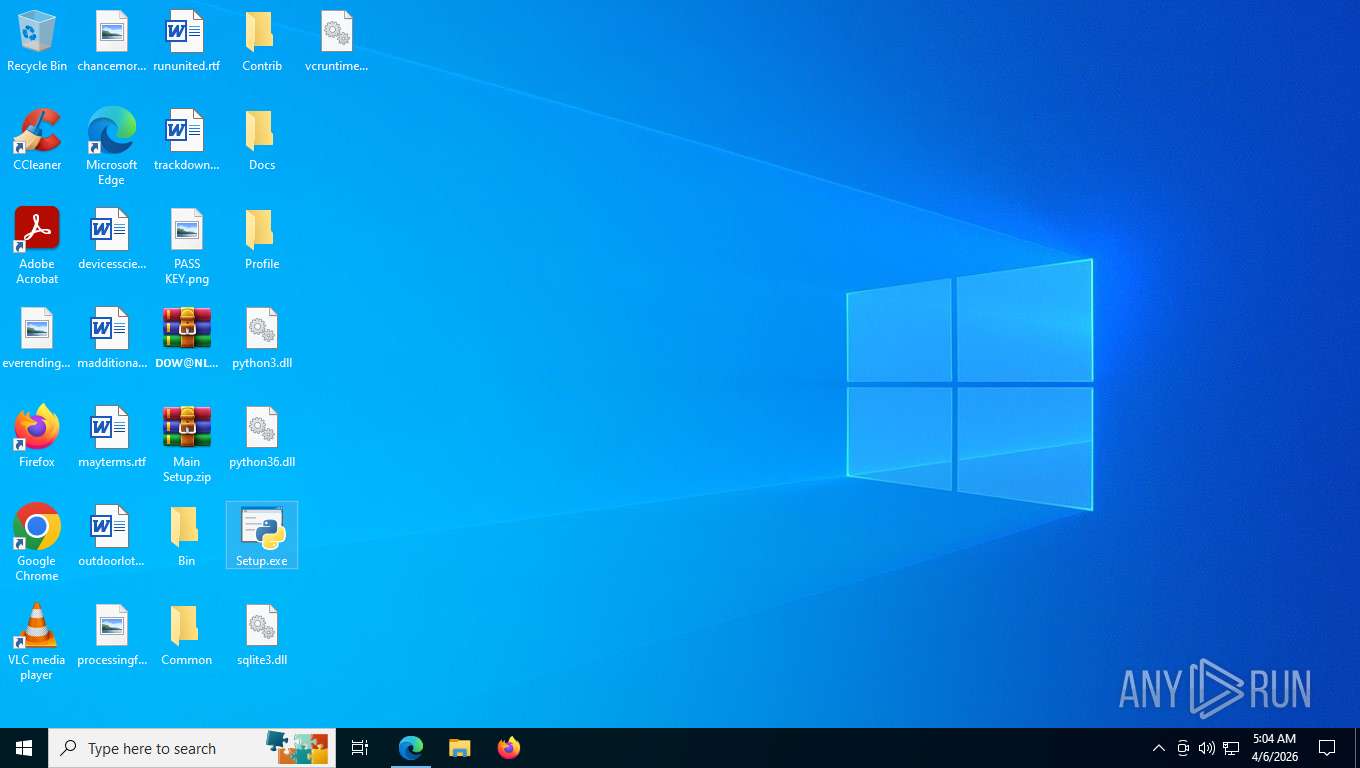
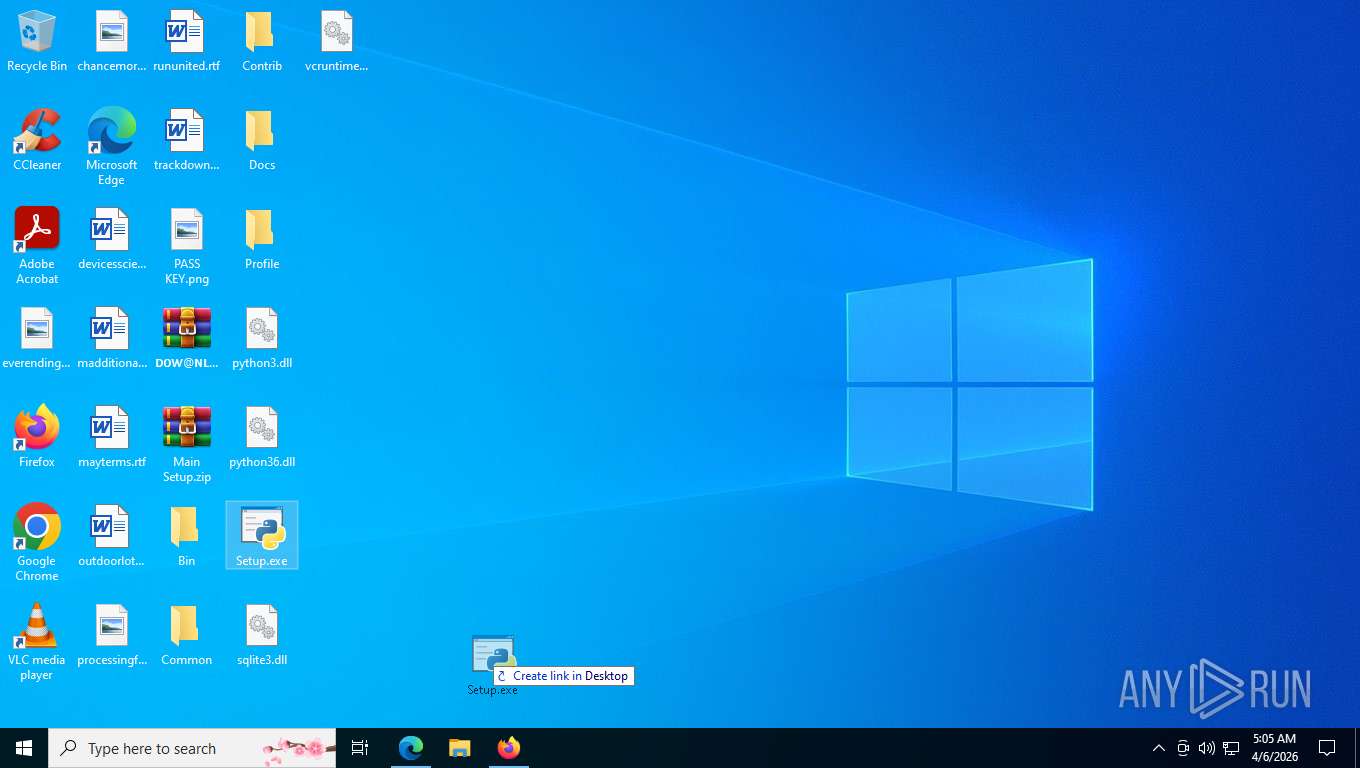
Manual execution by a user
- WinRAR.exe (PID: 1528)
- WinRAR.exe (PID: 7636)
- Setup.exe (PID: 7784)
- firefox.exe (PID: 9964)
Application launched itself
- msedge.exe (PID: 2452)
- chrome.exe (PID: 2736)
- firefox.exe (PID: 9964)
- firefox.exe (PID: 10048)
- chrome.exe (PID: 10356)
Launching a file from the Downloads directory
- msedge.exe (PID: 2452)
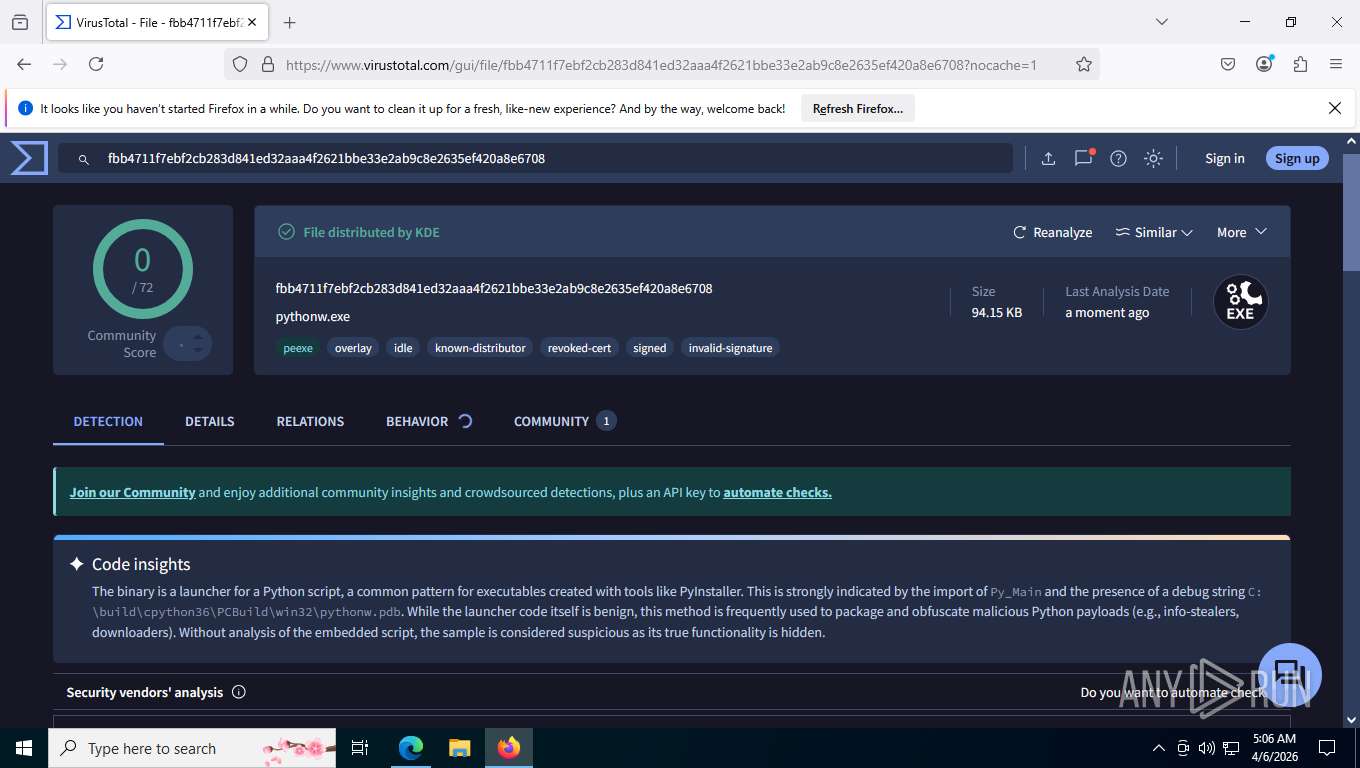
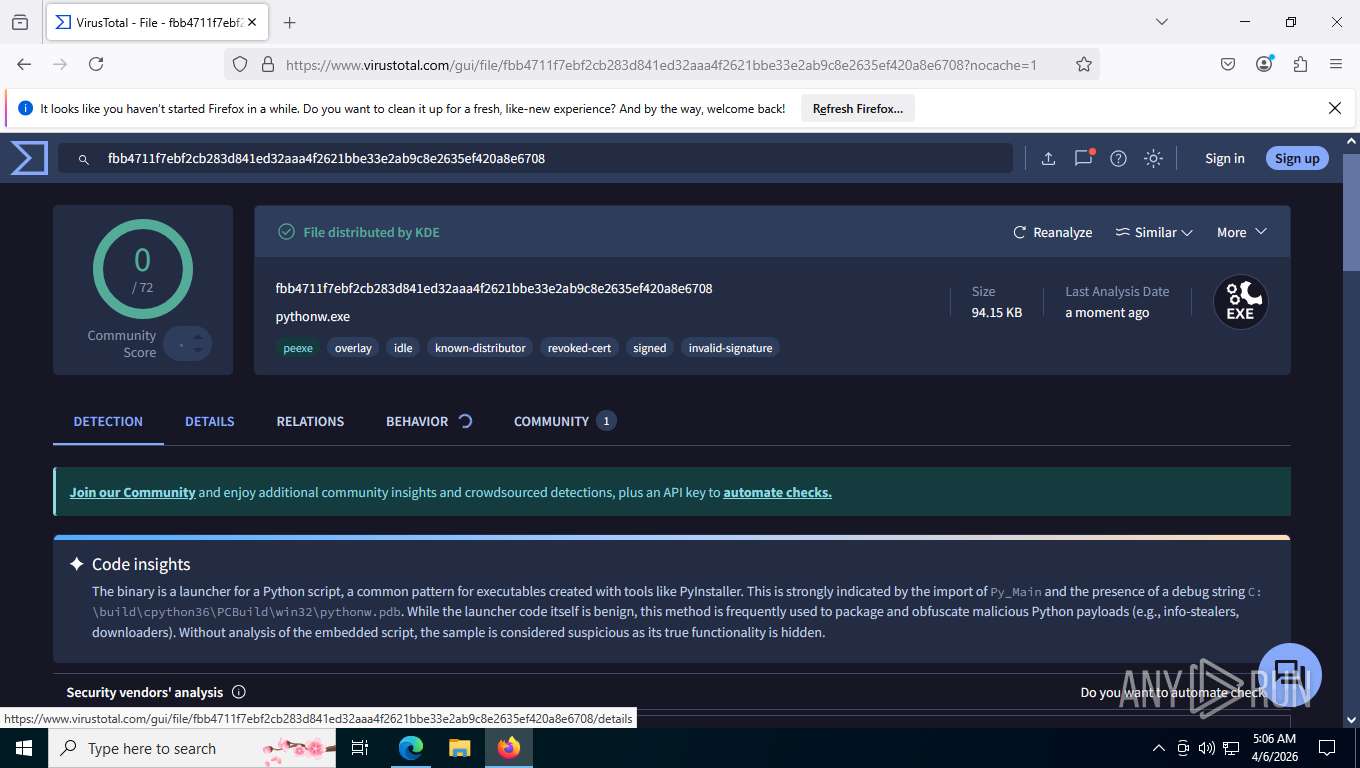
Python executable
- Setup.exe (PID: 7784)
Reads the machine GUID from the registry
- Setup.exe (PID: 7784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
317
Monitored processes
175
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-sandbox --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome27361074390" --field-trial-handle=4892,i,12856977942747740327,17608893042398543388,262144 --disable-features=PaintHolding --variations-seed-version --mojo-platform-channel-handle=4888 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-sandbox --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome103561149718" --field-trial-handle=5136,i,13201153997512487868,11111755131498254015,262144 --disable-features=PaintHolding --variations-seed-version --mojo-platform-channel-handle=5212 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-sandbox --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome27361074390" --field-trial-handle=5000,i,12856977942747740327,17608893042398543388,262144 --disable-features=PaintHolding --variations-seed-version --mojo-platform-channel-handle=5052 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-sandbox --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome27361074390" --field-trial-handle=5268,i,12856977942747740327,17608893042398543388,262144 --disable-features=PaintHolding --variations-seed-version --mojo-platform-channel-handle=3944 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 800 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 3548 -prefsLen 37299 -prefMapHandle 3552 -prefMapSize 273045 -ipcHandle 3560 -initialChannelId {3a6c3215-351a-4702-a812-5c737d03c2fd} -parentPid 10048 -crashReporter "\\.\pipe\gecko-crash-server-pipe.10048" -appDir "C:\Program Files\Mozilla Firefox\browser" - 4 rdd | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-sandbox --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome27361074390" --field-trial-handle=4844,i,12856977942747740327,17608893042398543388,262144 --disable-features=PaintHolding --variations-seed-version --mojo-platform-channel-handle=4840 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-sandbox --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome27361074390" --field-trial-handle=4196,i,12856977942747740327,17608893042398543388,262144 --disable-features=PaintHolding --variations-seed-version --mojo-platform-channel-handle=4216 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome103561149718" --enable-dinosaur-easter-egg-alt-images --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=22 --field-trial-handle=3136,i,13201153997512487868,11111755131498254015,262144 --disable-features=PaintHolding --variations-seed-version --mojo-platform-channel-handle=4524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome27361074390" --enable-dinosaur-easter-egg-alt-images --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=16 --field-trial-handle=4676,i,12856977942747740327,17608893042398543388,262144 --disable-features=PaintHolding --variations-seed-version --mojo-platform-channel-handle=4664 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-sandbox --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome103561149718" --field-trial-handle=5108,i,13201153997512487868,11111755131498254015,262144 --disable-features=PaintHolding --variations-seed-version --mojo-platform-channel-handle=5172 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
4 854
Read events
4 796
Write events
45
Delete events
13
Modification events
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
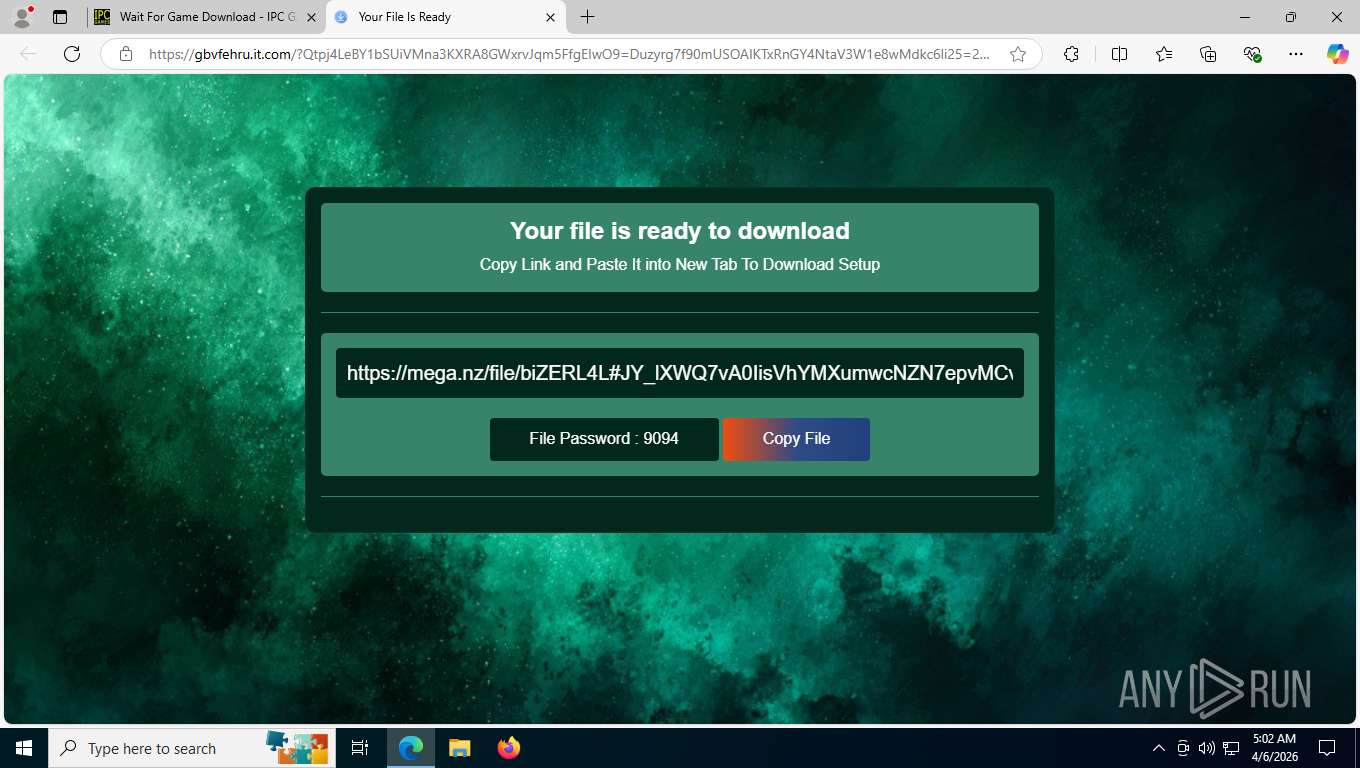
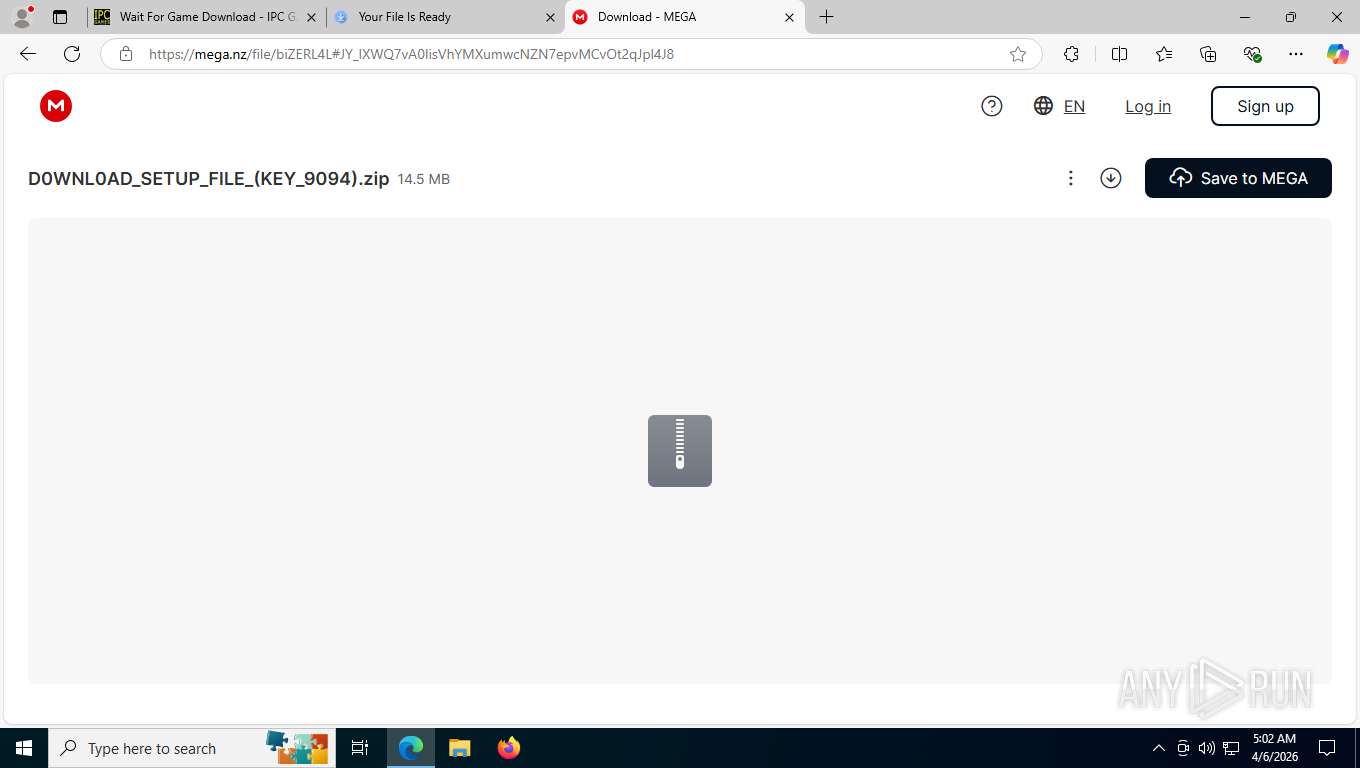
Value: C:\Users\admin\Downloads\D0WNL0AD_SETUP_FILE_(KEY_9094).zip | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5196) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\D0WNL0AD_SETUP_FILE_(KEY_9094).zip | |||
| (PID) Process: | (5196) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
5
Suspicious files
203
Text files
629
Unknown types
2 127
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2452 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFe0153.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2452 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe0163.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe0163.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2452 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFe0163.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe0163.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2452 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe0163.TMP | — | |
MD5:— | SHA256:— | |||
| 2452 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 051
TCP/UDP connections
256
DNS requests
347
Threats
59
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5760 | msedge.exe | GET | 404 | 172.67.216.57:443 | https://ipcgames.com/wp-content/plugins/contextual-related-posts/css/default-style.css?ver=1.0 | US | — | — | unknown |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5760 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:ZrI9-SHetp0oqdQTPVAKb9rCDPV9dOax-LzTkLeonLo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | binary | 101 b | whitelisted |
5760 | msedge.exe | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=IhSFONKMxbe8OVTbklviN45kKA0vh580GHE3ISQ6Vp39kEFGBRh2RJkjSOdOamBQl1%2FNmGamsRL6vXQ6aurv4IgwLpOWkd0C7Qyhj2AVftxJZZwKUanlBDhhC%2BaBHRk%3D | US | — | — | unknown |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
5760 | msedge.exe | GET | 200 | 172.67.216.57:443 | https://ipcgames.com/wait-for-game-download/ | US | binary | 28.5 Kb | unknown |
5760 | msedge.exe | GET | 404 | 172.67.216.57:443 | https://ipcgames.com/wp-content/plugins/uk-cookie-consent/assets/css/style.css?ver=5.2.1 | US | binary | 51.3 Kb | unknown |
5760 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 314 b | whitelisted |
5760 | msedge.exe | GET | 200 | 172.67.216.57:443 | https://ipcgames.com/wp-content/plugins/wp-pagenavi/pagenavi-css.css?ver=2.70 | US | — | 374 b | unknown |
5760 | msedge.exe | GET | 200 | 172.67.216.57:443 | https://ipcgames.com/wp-content/uploads/2019/05/ipcgameslogoe.png | US | — | 40.7 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4212 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.216.77.20:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5760 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5760 | msedge.exe | 52.123.243.213:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ipcgames.com |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5760 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5760 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5760 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5760 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5760 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5760 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
5760 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
5760 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
5760 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
5760 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome27361074390 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome103561149718 directory exists )
|