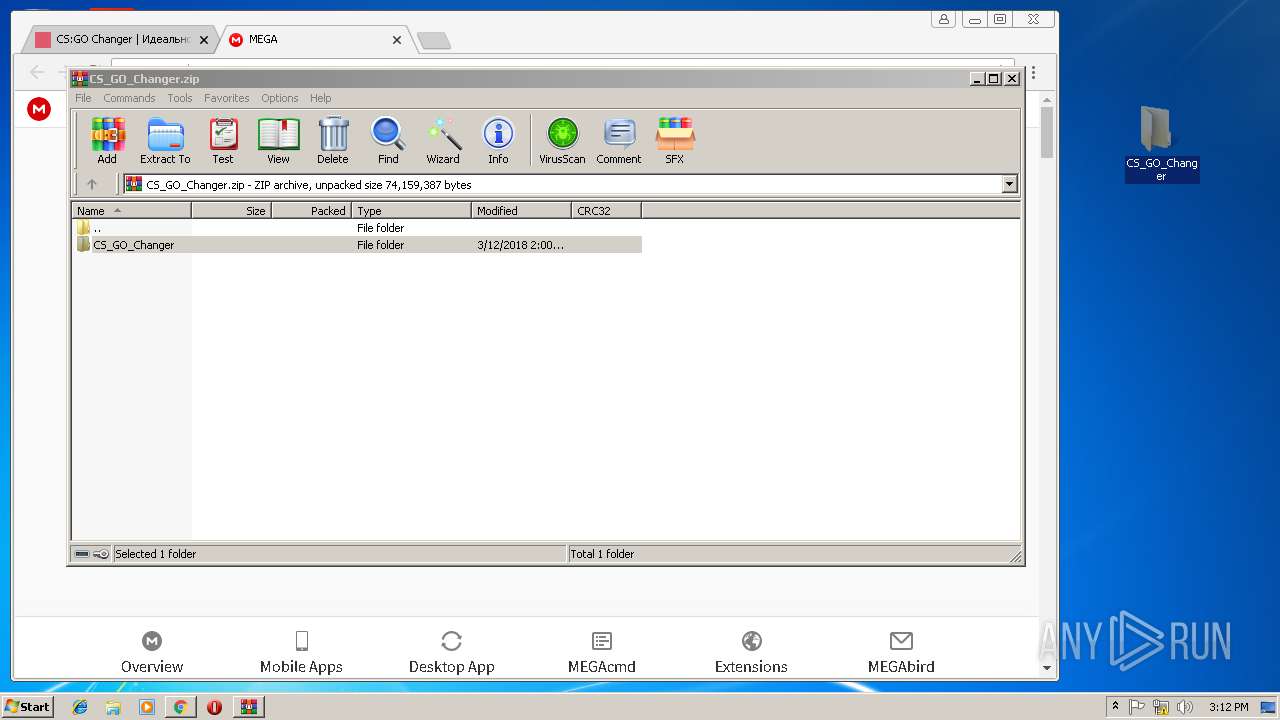
| download: | index.html |
| Full analysis: | https://app.any.run/tasks/ef5e0a25-67b0-46ad-bd9a-eafc6b5366a8 |
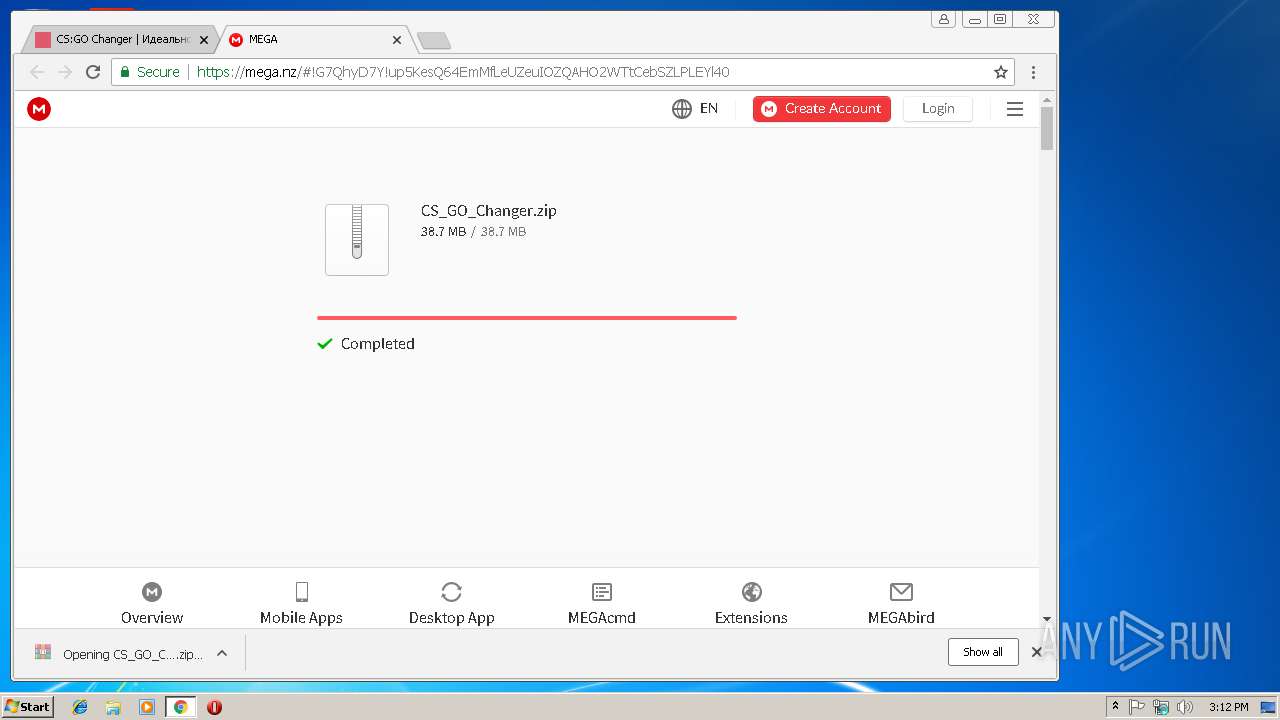
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 15:11:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with no line terminators |
| MD5: | C532DAFD2C687AB2A20C0F4AC0839772 |
| SHA1: | 3B11088B5A60F059EF340D99AE93A0EF7717B92B |
| SHA256: | 835A0D973EF675ED107FCC0CAE20F3994709A04212B387FAE465725E6AEE309C |
| SSDEEP: | 192:MRH5mGARJt+3aSA1GMd3tm6EKt97c0mzv8BMrN3NeUX+6kaJpbwUZvwV:emTRJsZ2tEK/70nrNqaJ6UI |
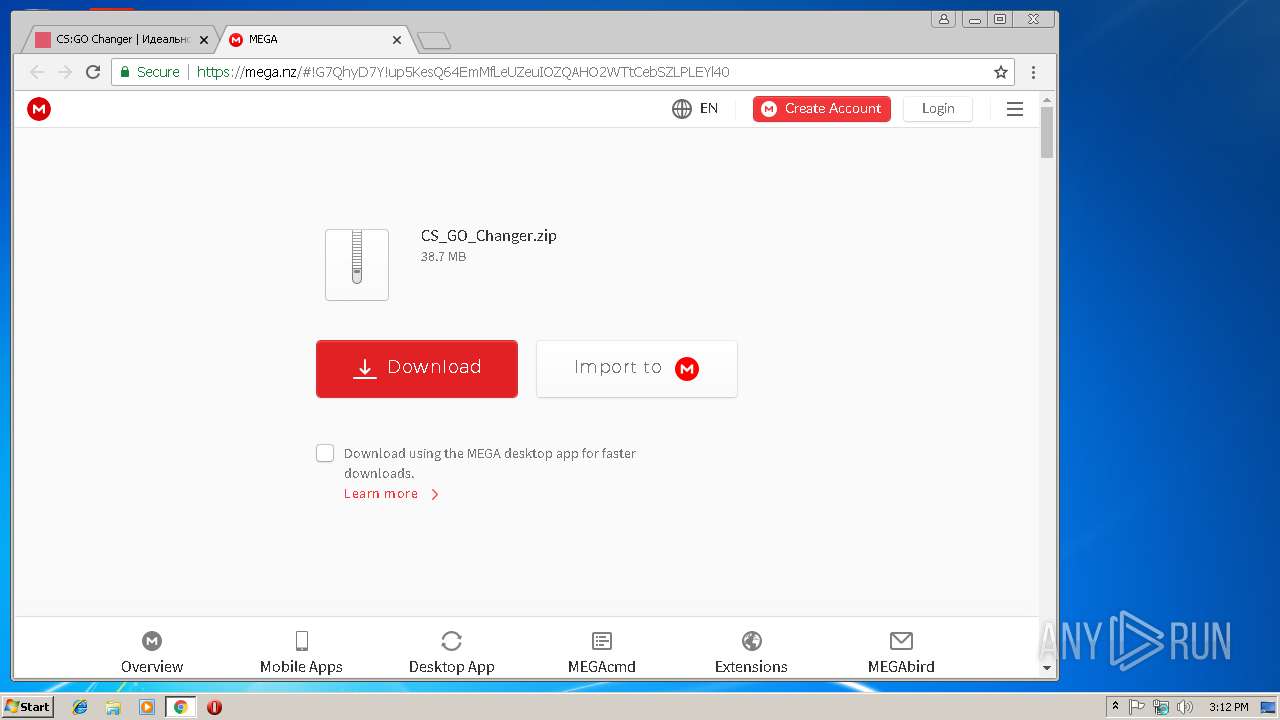
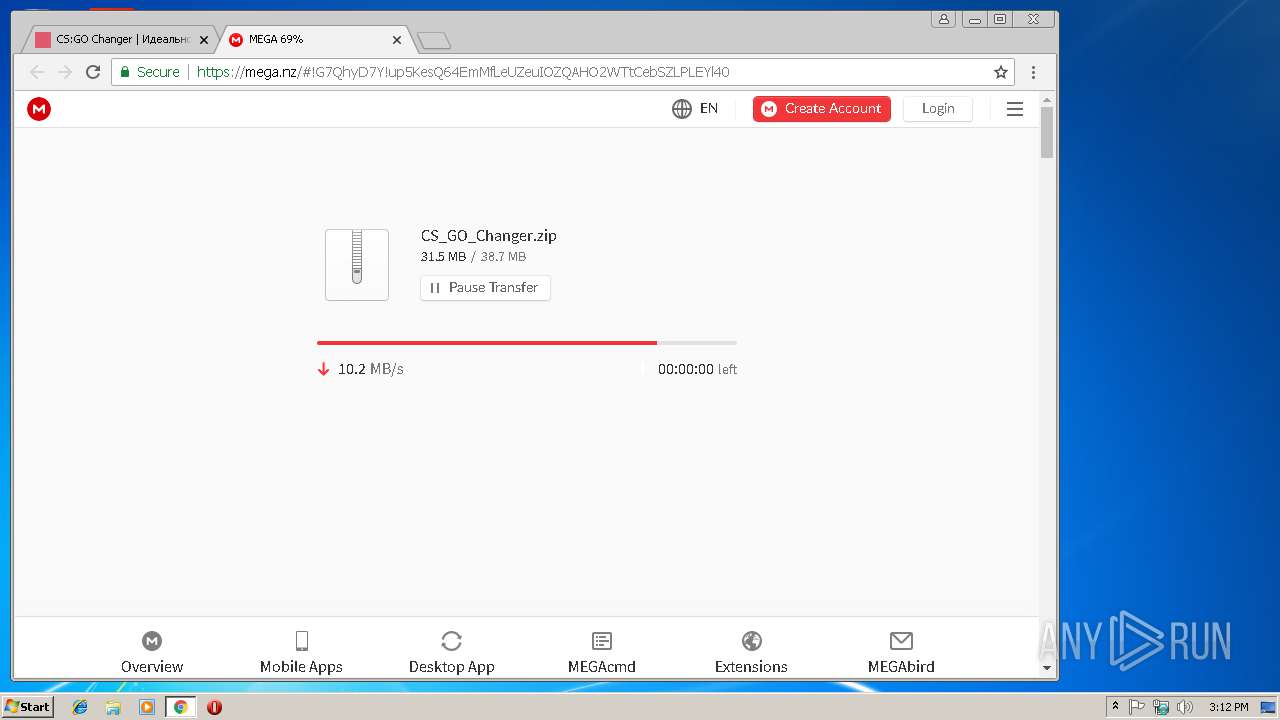
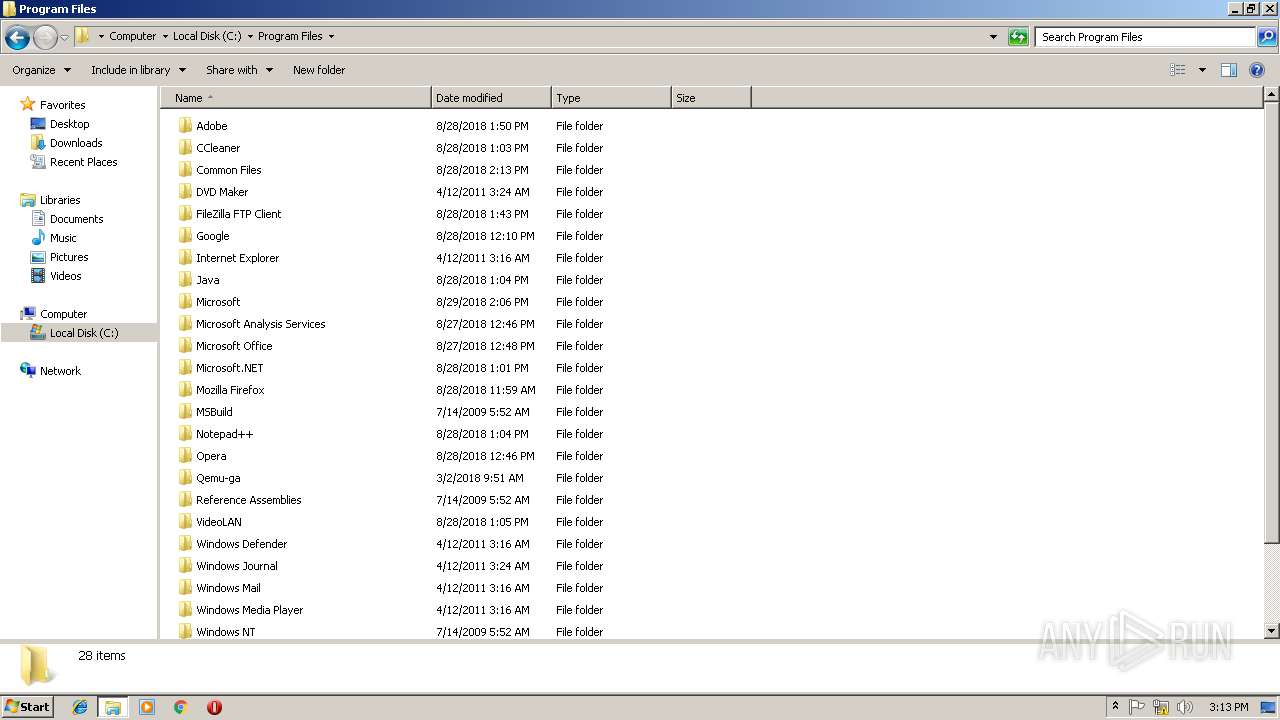
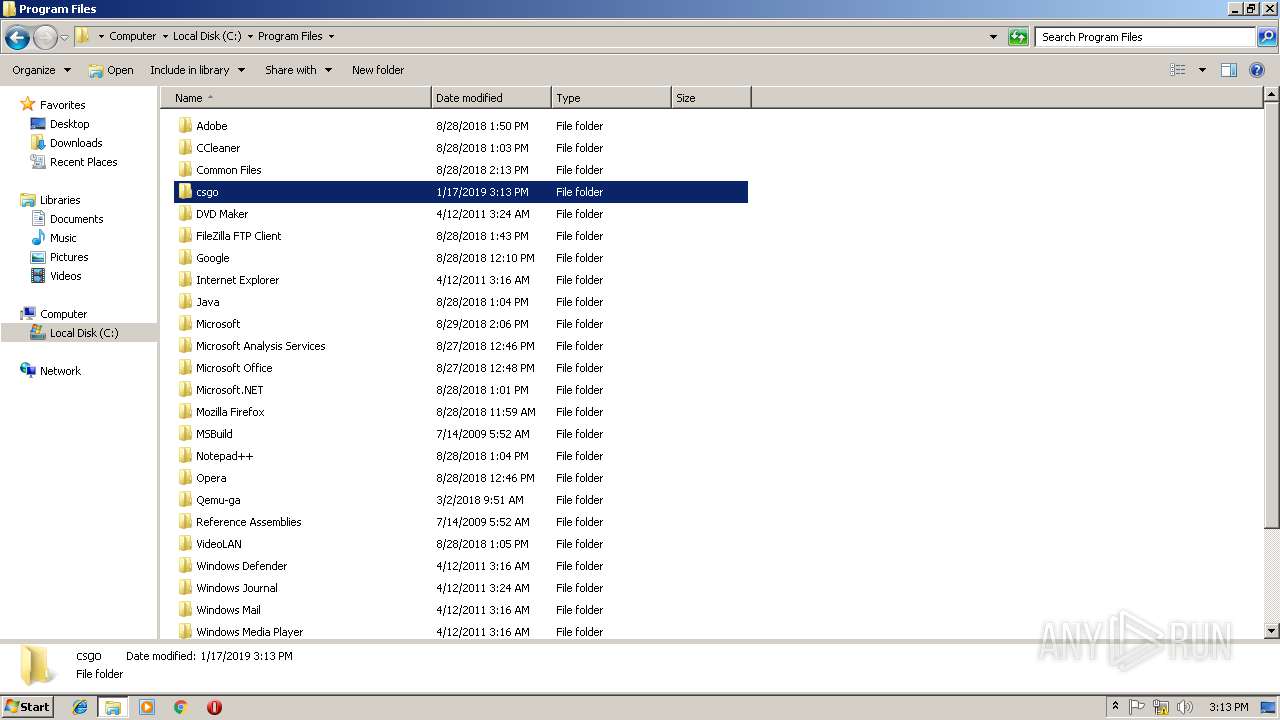
MALICIOUS
Application was dropped or rewritten from another process
- csc.exe (PID: 3556)
- csc.exe (PID: 3936)
- pcnsl.exe (PID: 3368)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1832)
- csc.exe (PID: 3936)
Changes settings of System certificates
- csc.exe (PID: 3936)
SUSPICIOUS
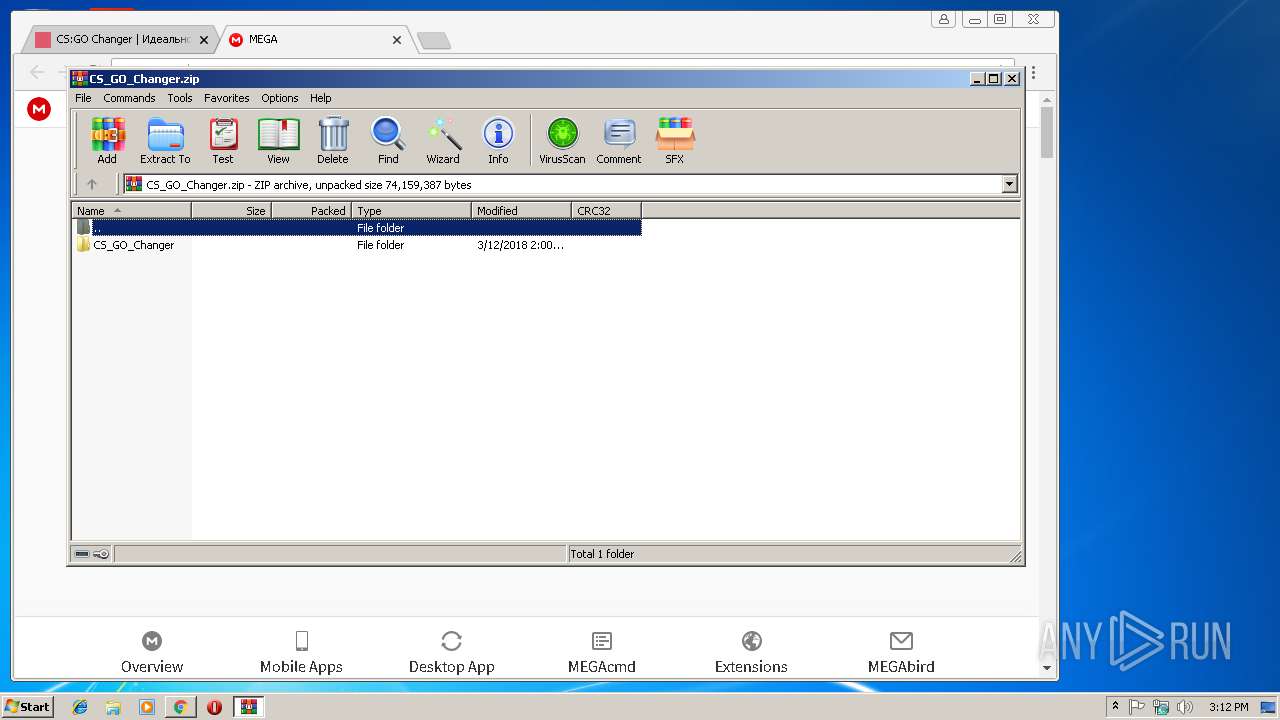
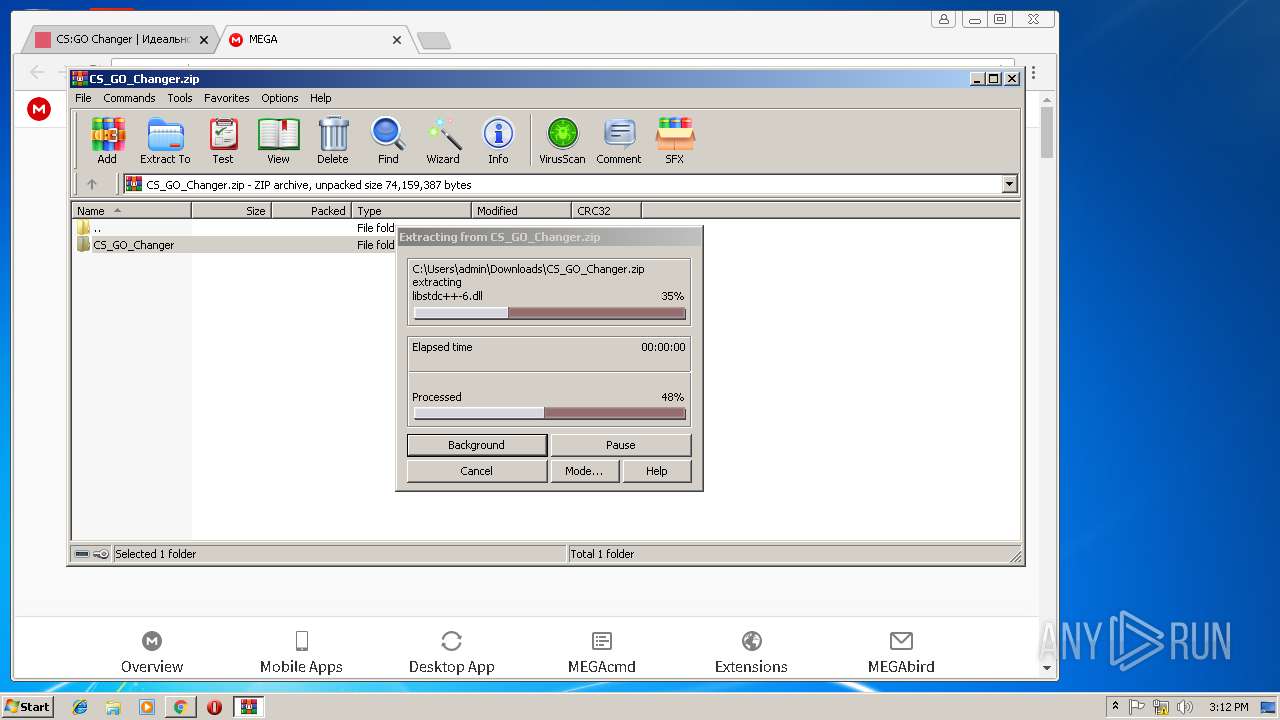
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3588)
Creates files in the user directory
- csc.exe (PID: 3936)
Reads internet explorer settings
- csc.exe (PID: 3936)
Reads Environment values
- csc.exe (PID: 3936)
Adds / modifies Windows certificates
- csc.exe (PID: 3936)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2844)
Application launched itself
- iexplore.exe (PID: 2844)
- chrome.exe (PID: 3124)
Reads internet explorer settings
- iexplore.exe (PID: 3168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
56
Monitored processes
21
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1832 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,3238475376321933939,1515638116460801673,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=26FB11FC1066BC57D8CFD2ED6E3AC59A --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=26FB11FC1066BC57D8CFD2ED6E3AC59A --renderer-client-id=6 --mojo-platform-channel-handle=3544 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,3238475376321933939,1515638116460801673,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5018F9673FF33E2EF4B54FFBCFDA61D4 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5018F9673FF33E2EF4B54FFBCFDA61D4 --renderer-client-id=8 --mojo-platform-channel-handle=3460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=908,3238475376321933939,1515638116460801673,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AAE0A623F61E2AC180E74602510A2A17 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2844 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
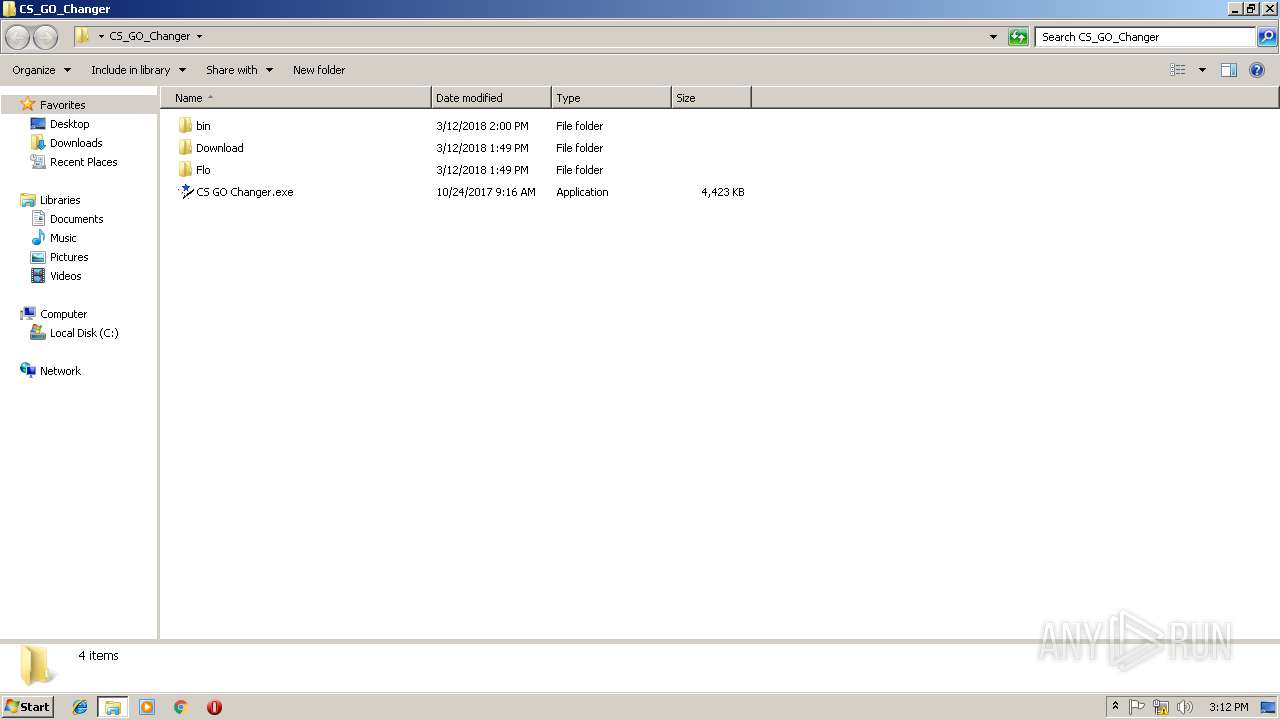
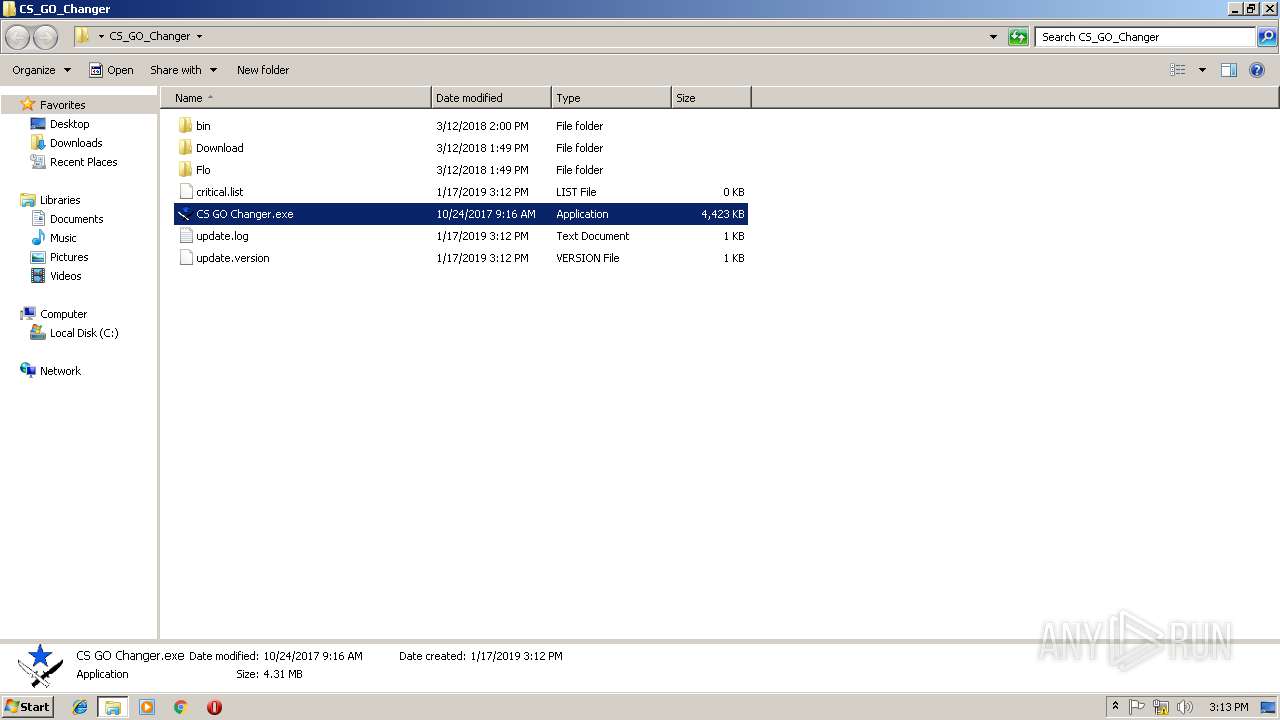
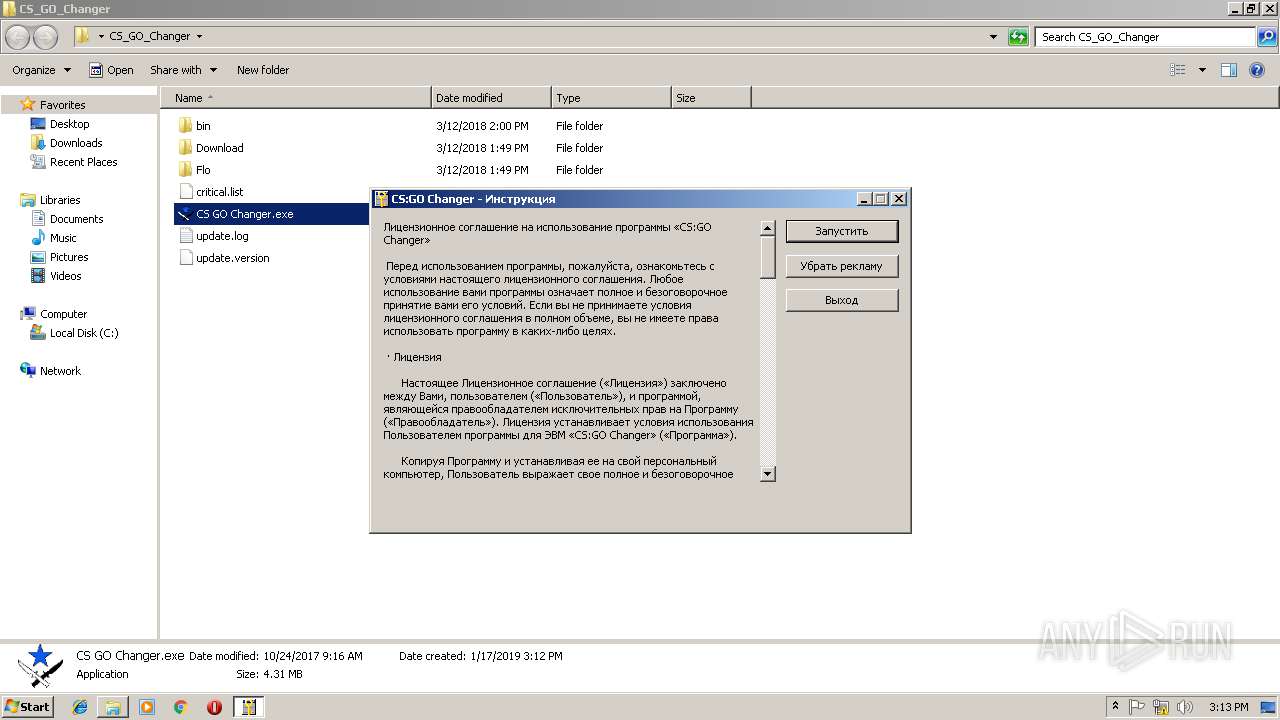
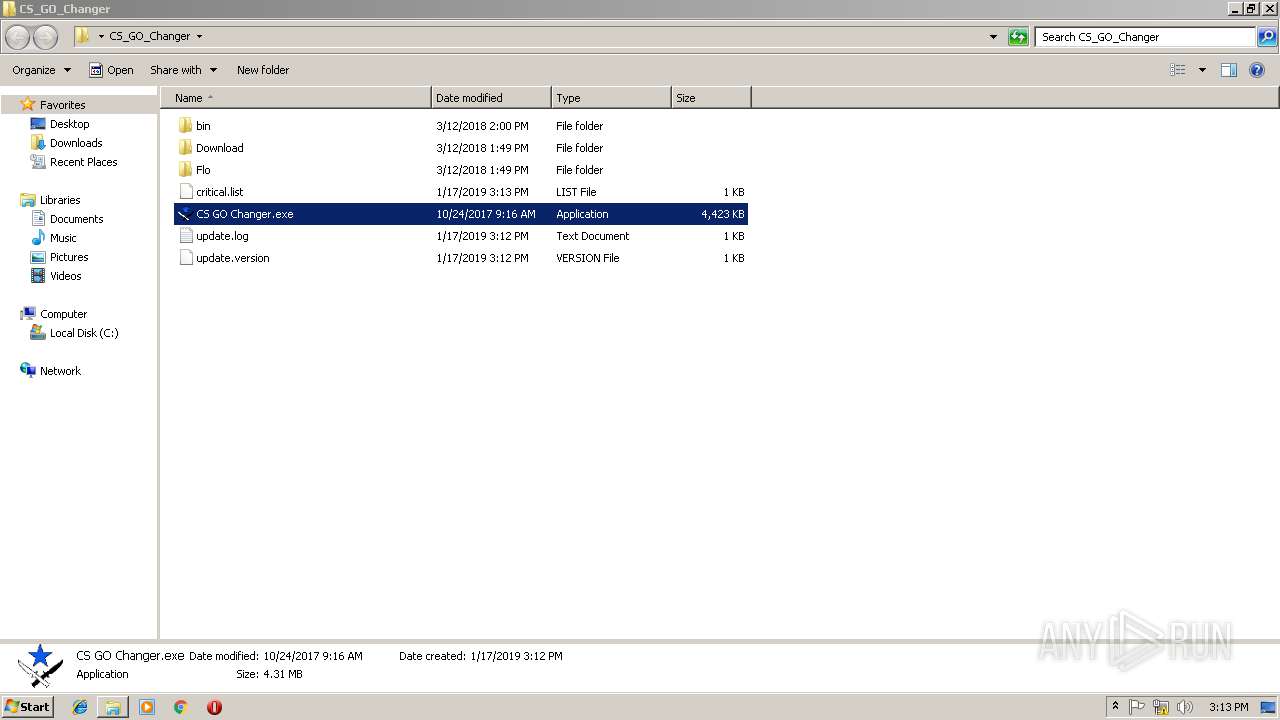
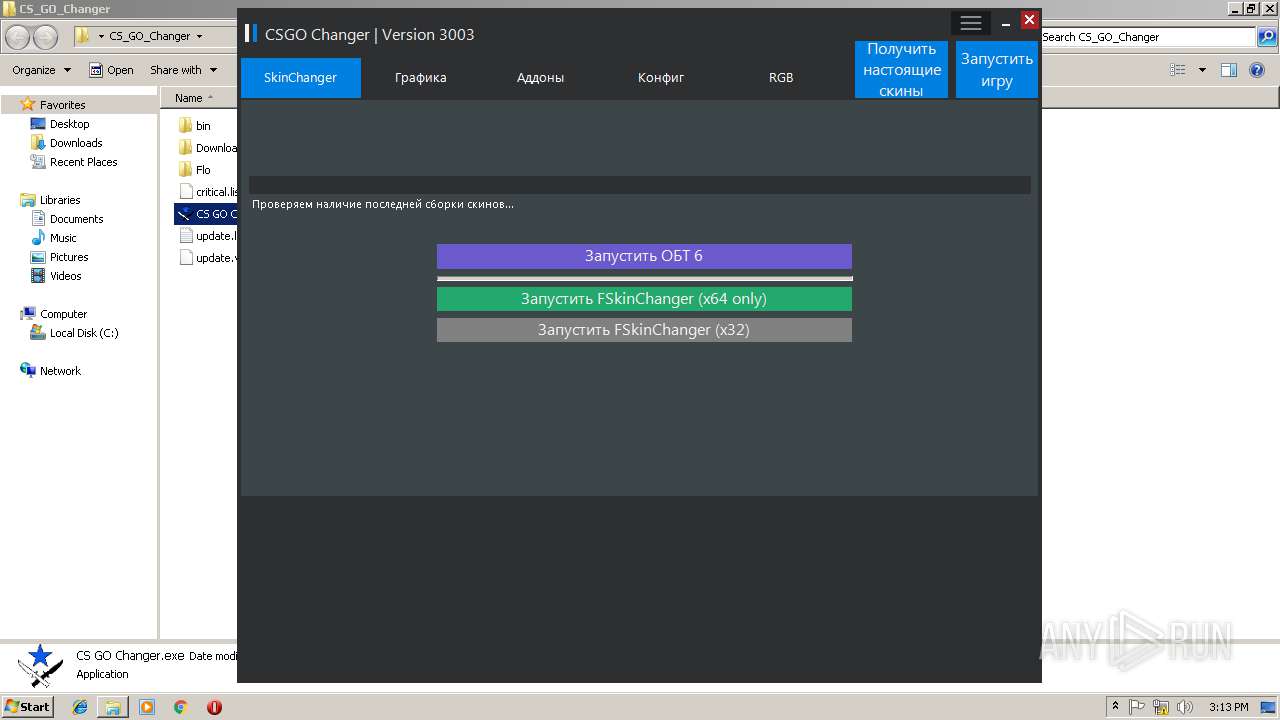
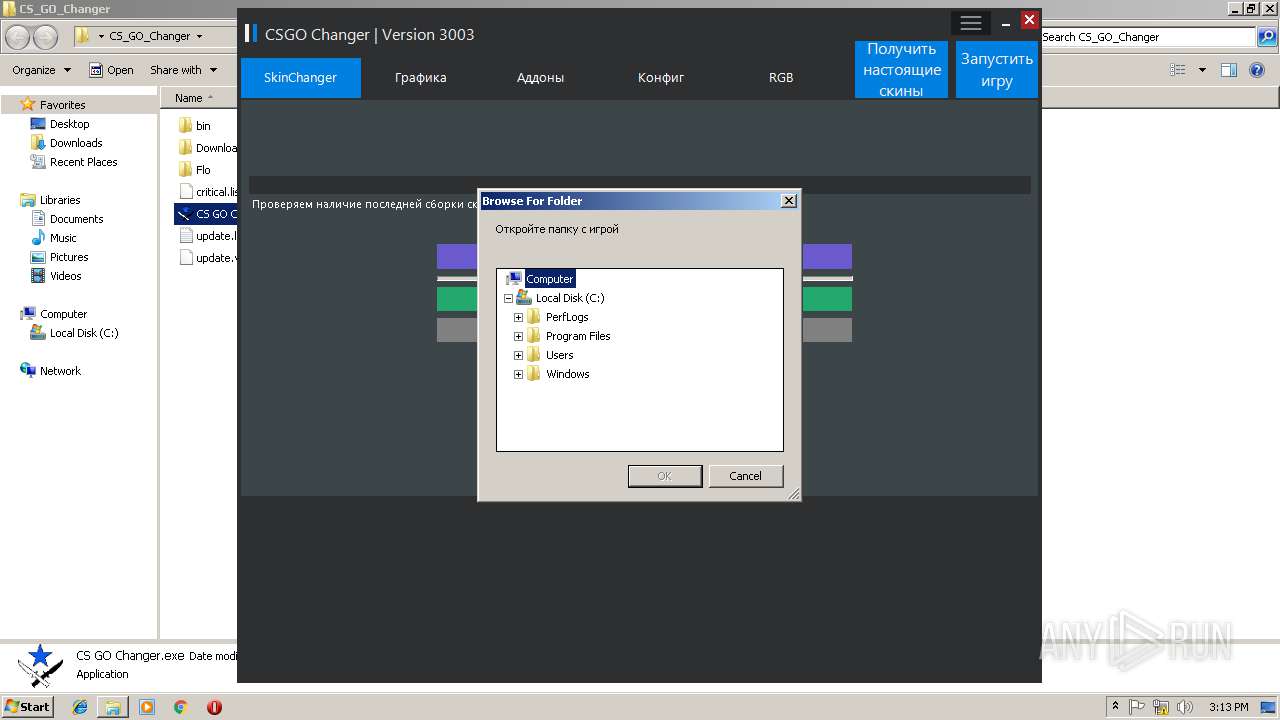
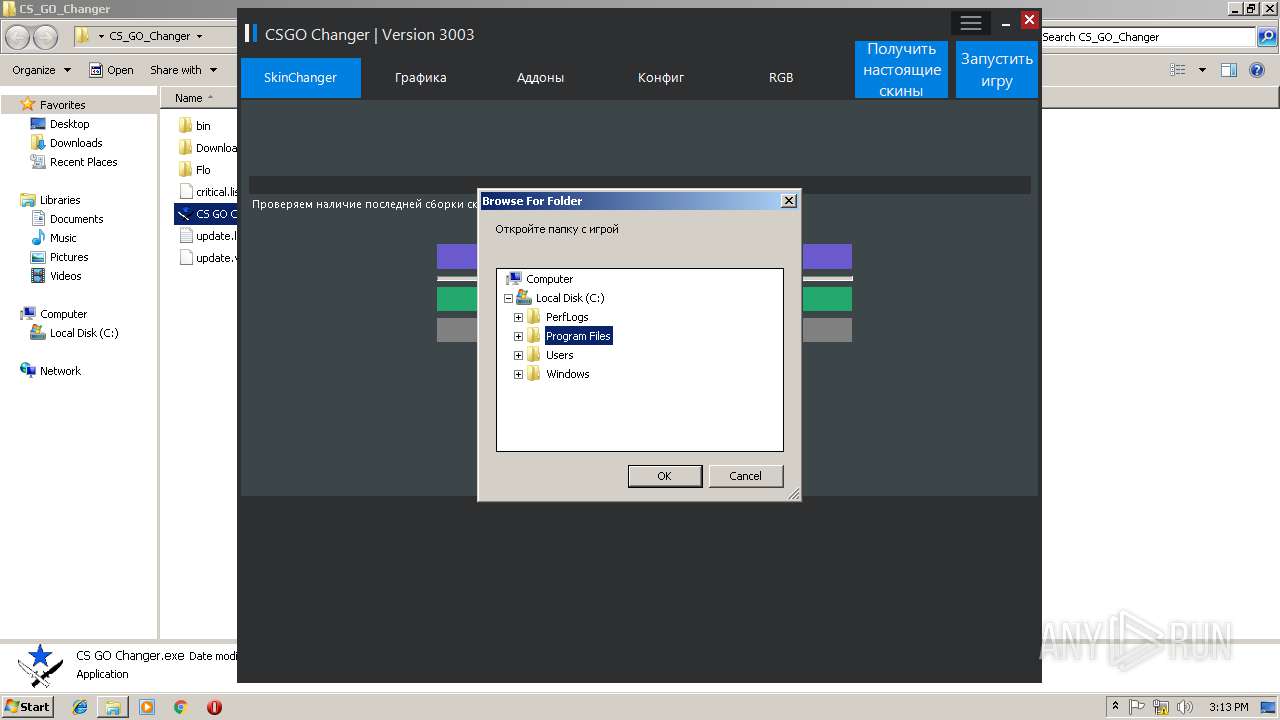
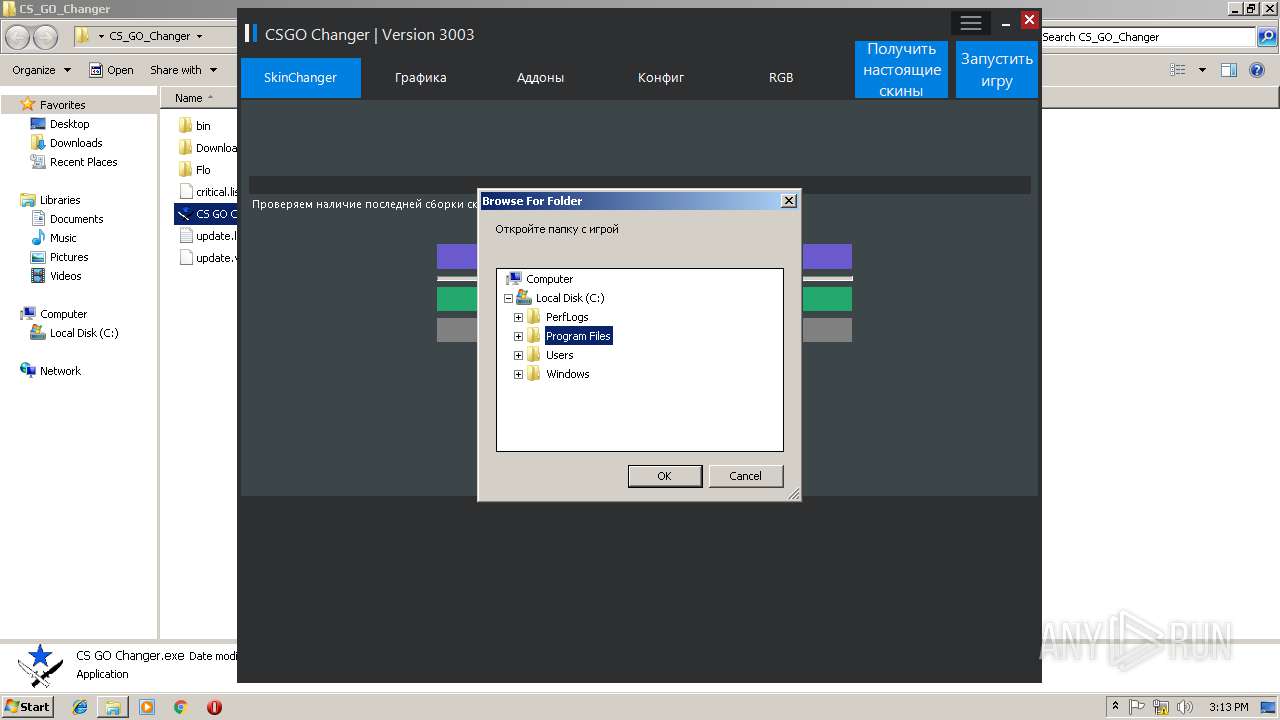
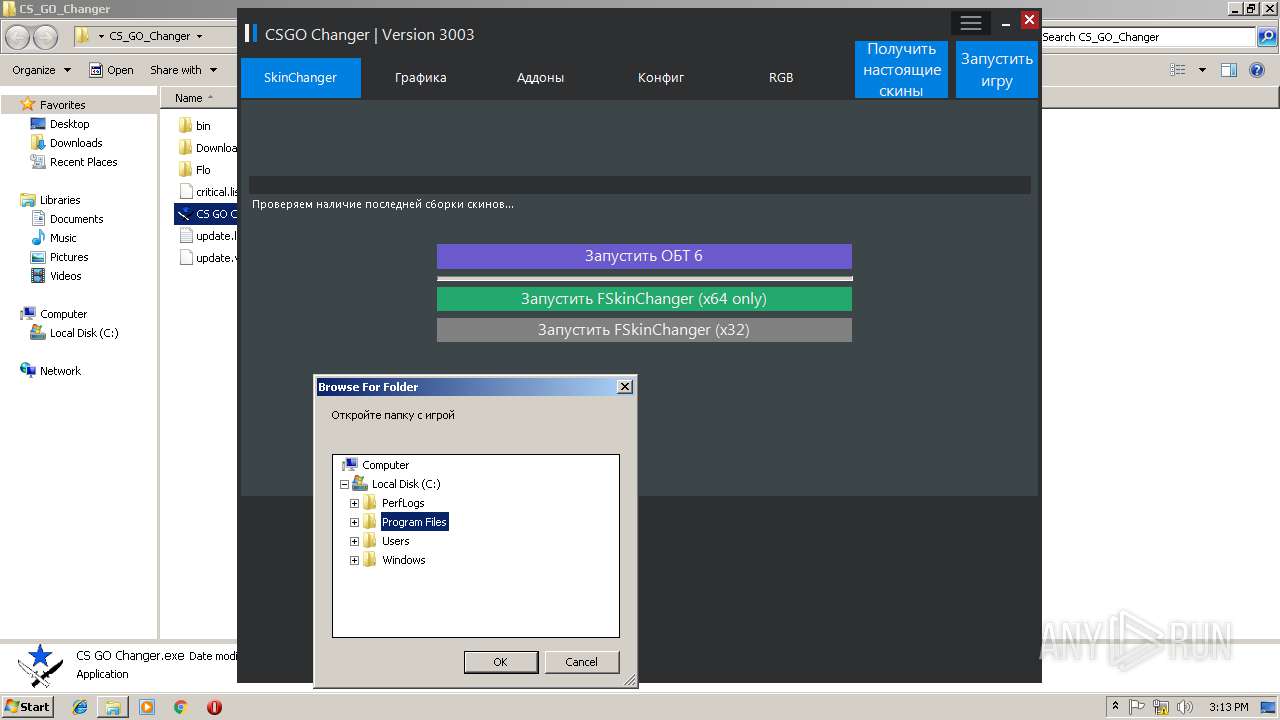
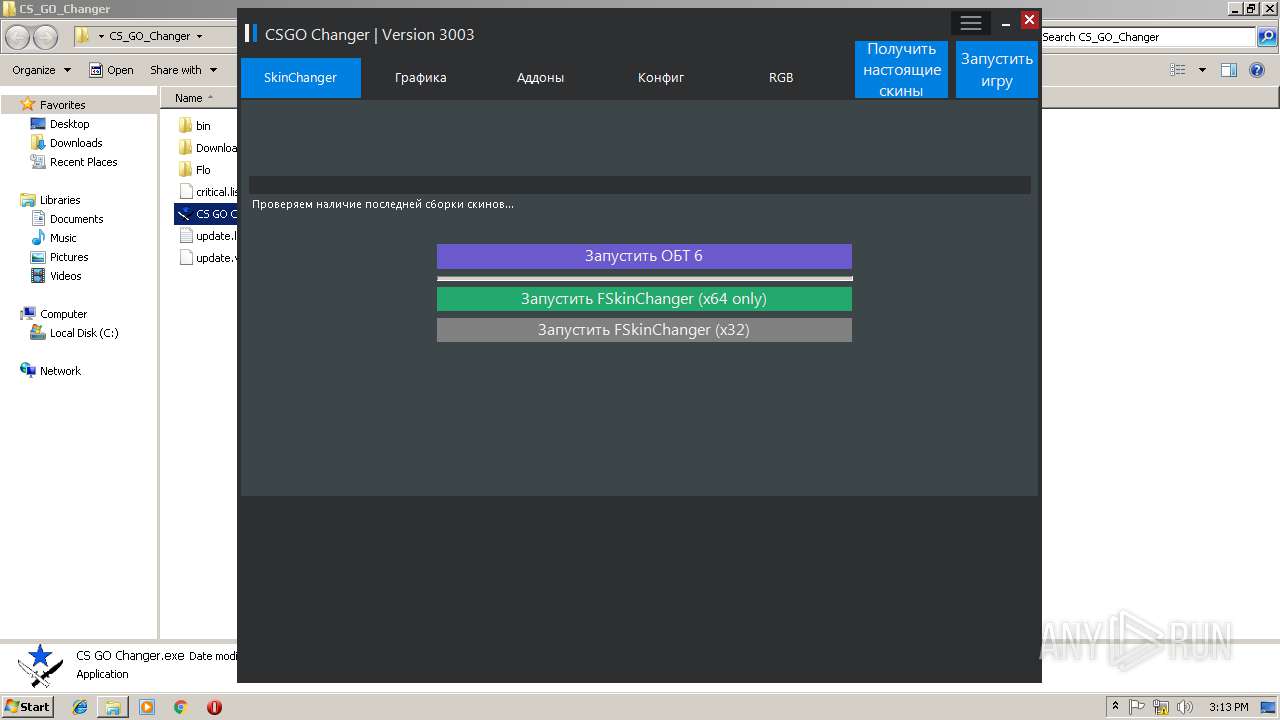
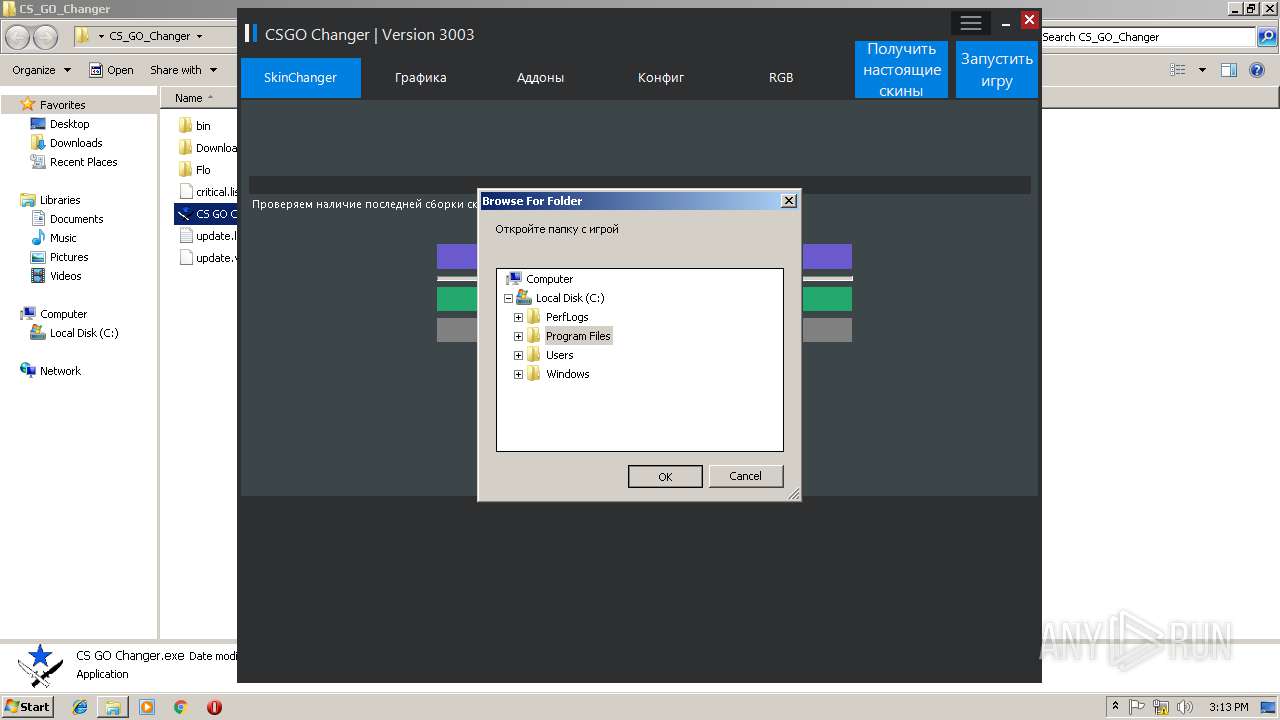
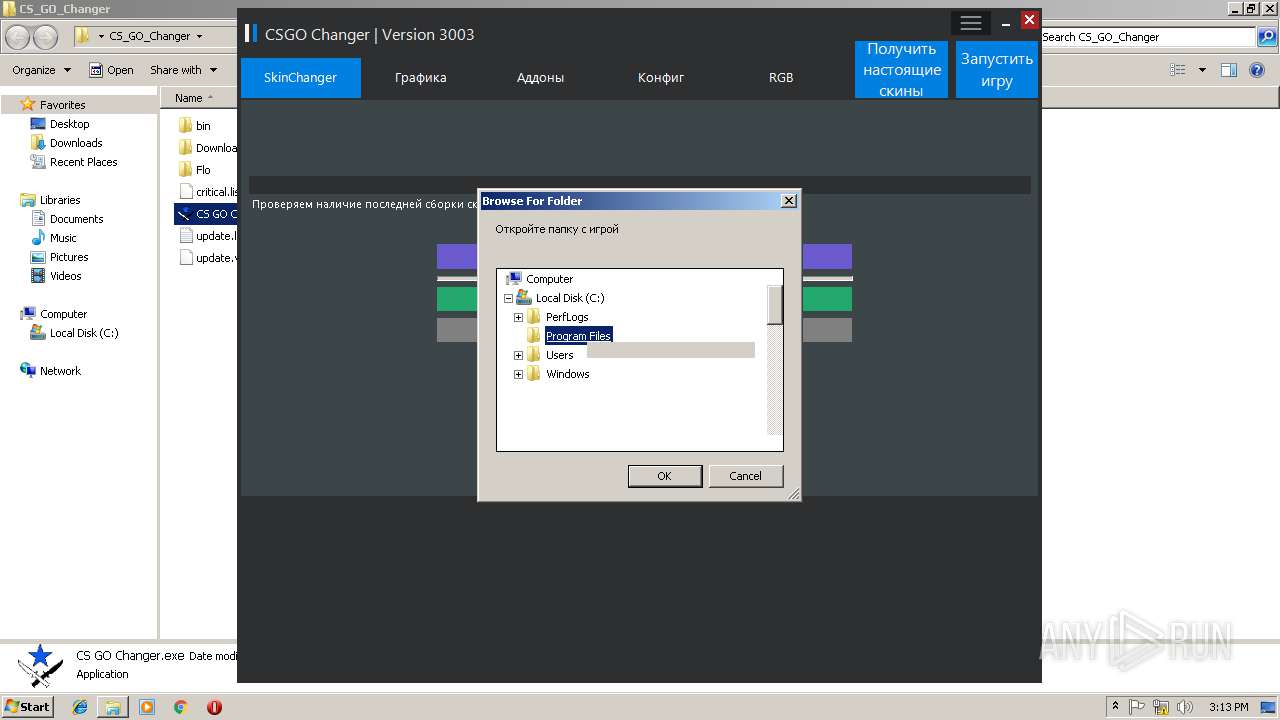
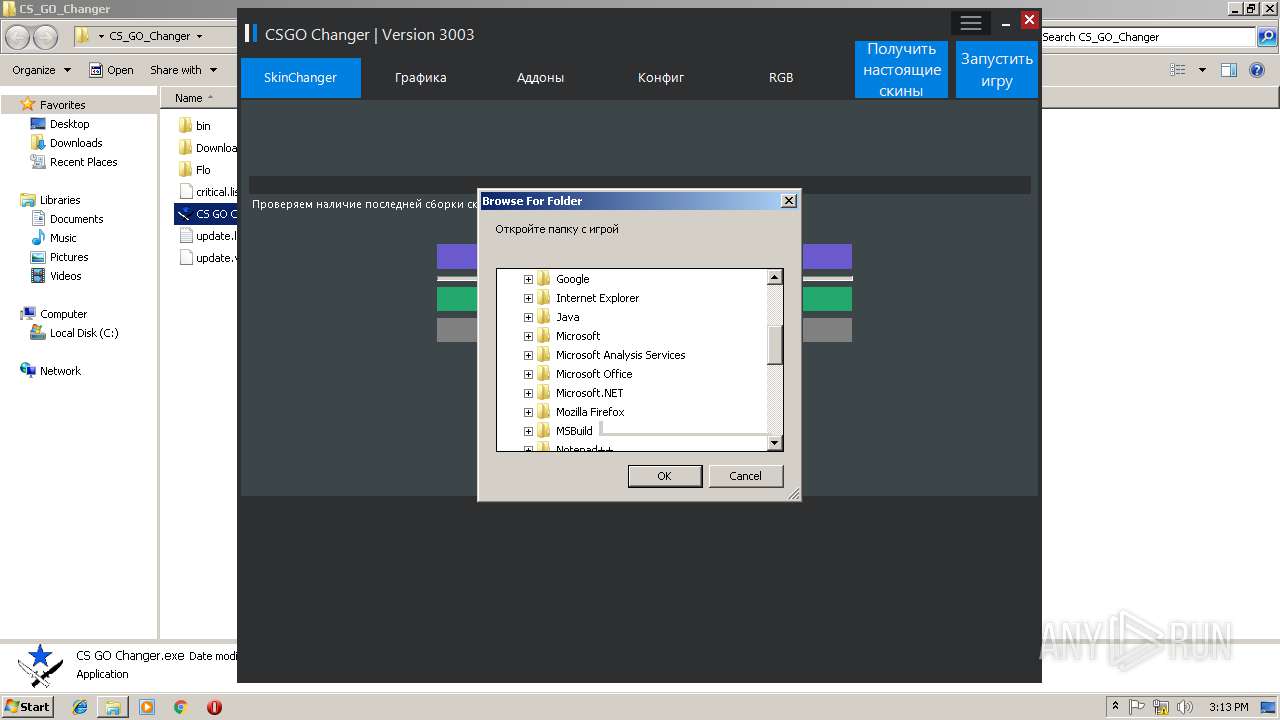
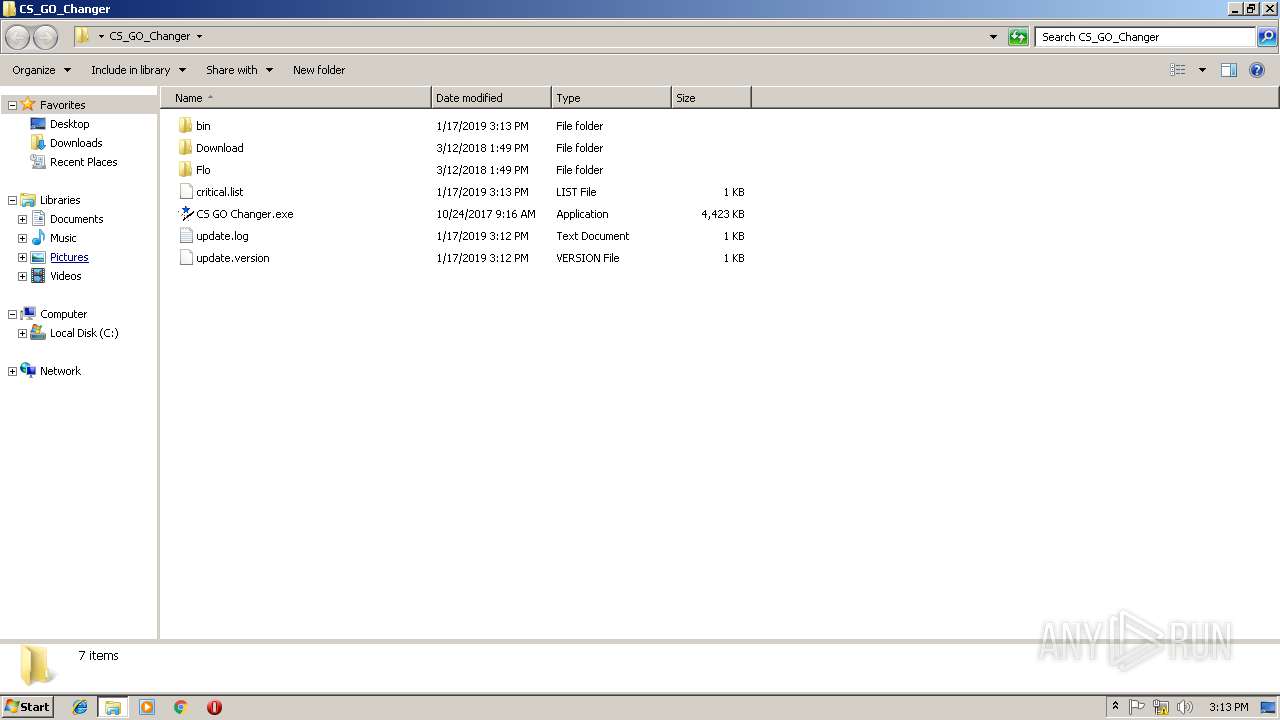
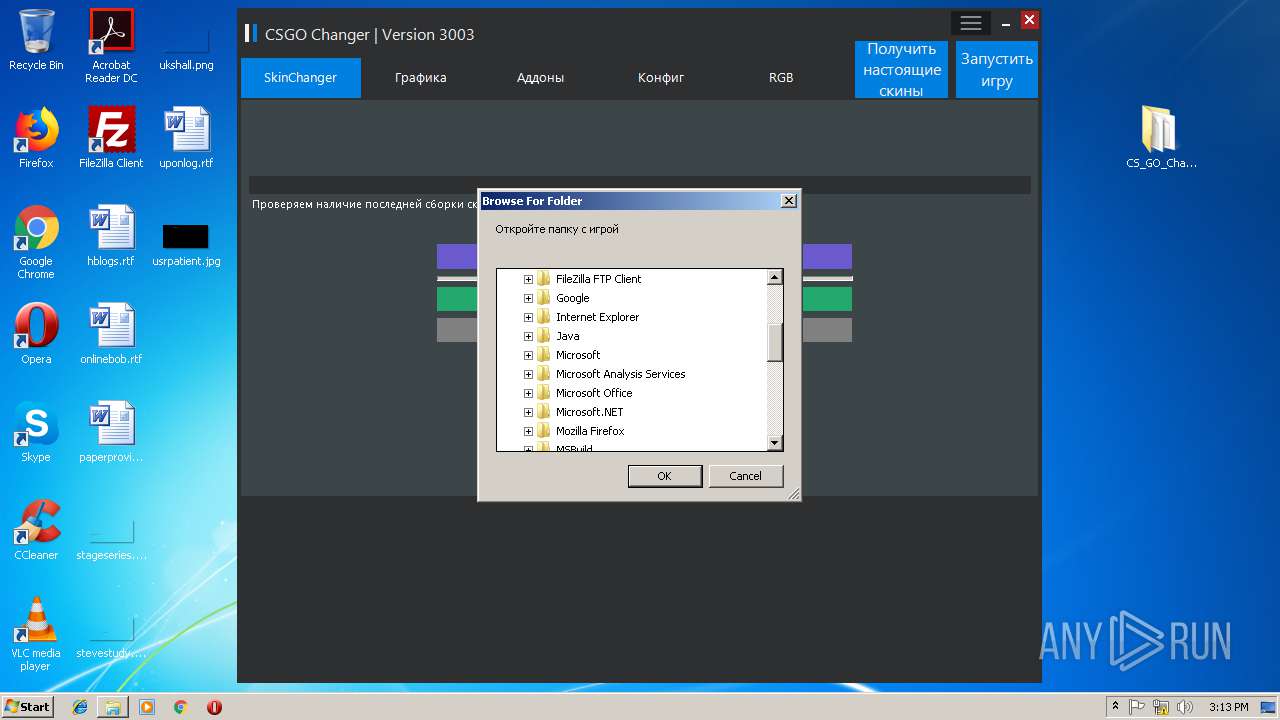
| 3136 | "C:\Users\admin\Desktop\CS_GO_Changer\CS GO Changer.exe" | C:\Users\admin\Desktop\CS_GO_Changer\CS GO Changer.exe | explorer.exe | ||||||||||||
User: admin Company: CS GO Changer Integrity Level: MEDIUM Description: CS GO Changer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3168 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2844 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3172 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=908,3238475376321933939,1515638116460801673,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=6444A8DBEC81B4B0C340A8CEACBF560C --mojo-platform-channel-handle=3852 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 813
Read events
2 626
Write events
183
Delete events
4
Modification events
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {3900F393-1A6A-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070100040011000F000B0037000A01 | |||
Executable files
56
Suspicious files
102
Text files
134
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB7B87DEE21E6AC14.TMP | — | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF84FE0B850977812B.TMP | — | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7FFA20499BDD19A7.TMP | — | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4E8EA764601D3130.TMP | — | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEE88D1CB15B3161C.TMP | — | |
MD5:— | SHA256:— | |||
| 3124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fb1b6b5b-1810-4082-8a7f-df30f8e84e59.tmp | — | |
MD5:— | SHA256:— | |||
| 3124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{4BBB6F4B-AC5C-11E8-969E-5254004AAD11}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
75
DNS requests
37
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
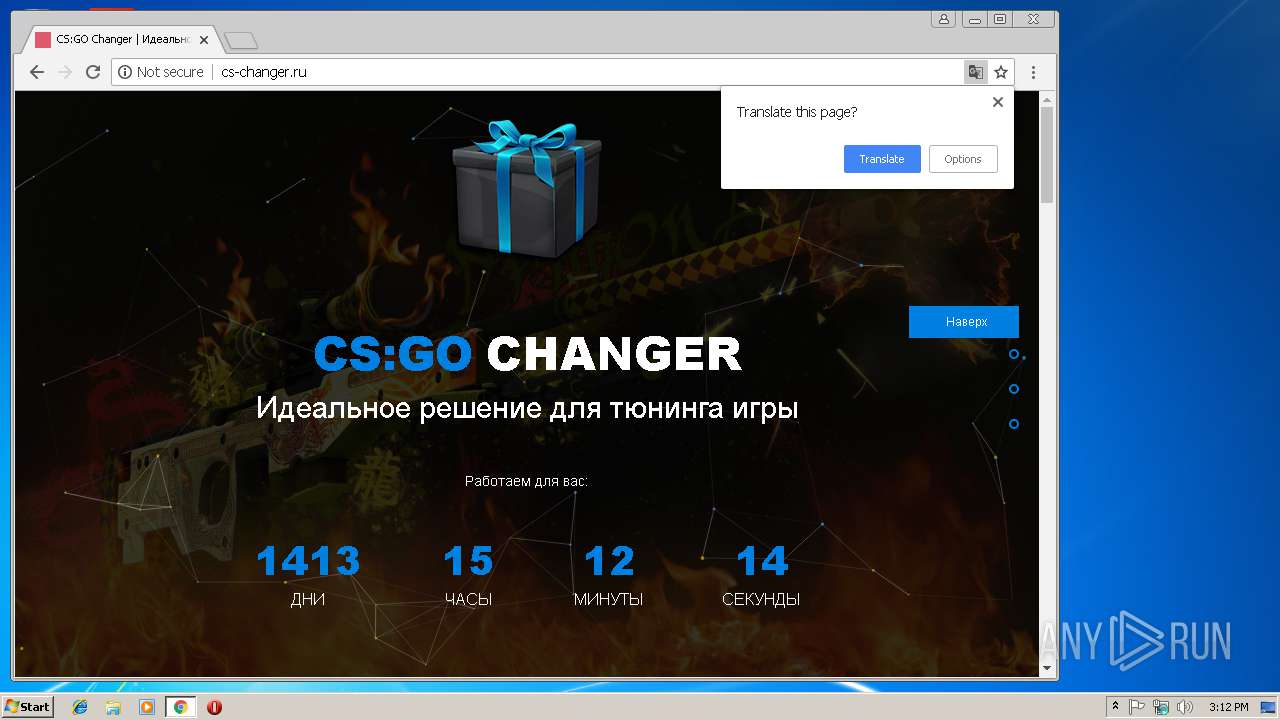
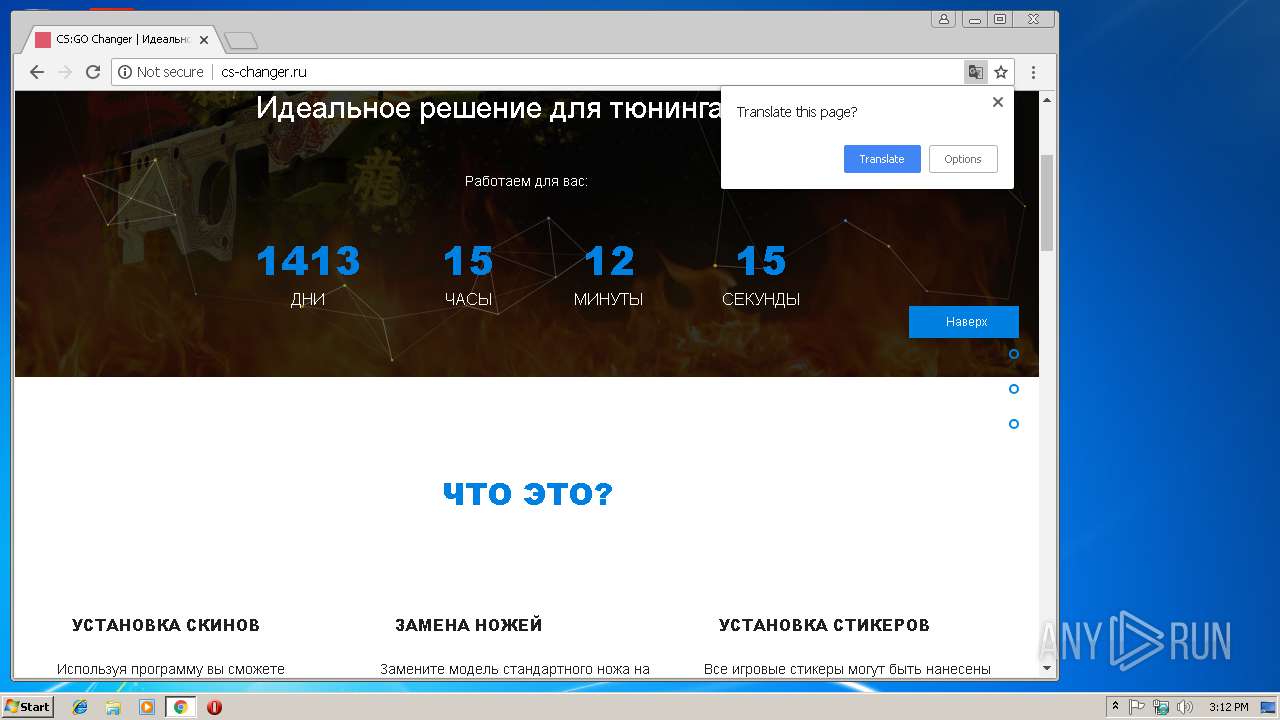
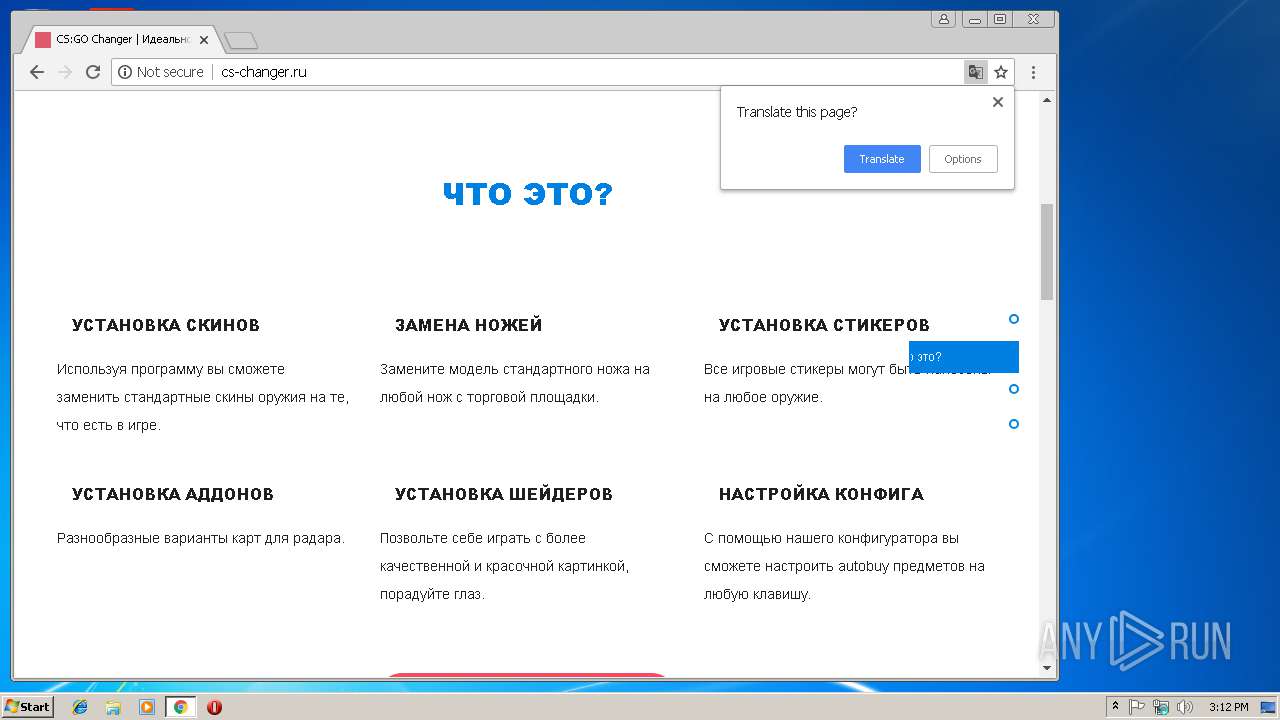
3124 | chrome.exe | GET | 200 | 91.218.229.13:80 | http://cs-changer.ru/css-family=Open+Sans-300italic,400italic,400,300,600,700,800.css | RU | text | 241 b | whitelisted |
3124 | chrome.exe | GET | 200 | 91.218.229.13:80 | http://cs-changer.ru/ | RU | html | 3.91 Kb | whitelisted |
3124 | chrome.exe | GET | 200 | 91.218.229.13:80 | http://cs-changer.ru/bootstrap.min.css | RU | text | 18.8 Kb | whitelisted |
3124 | chrome.exe | GET | 200 | 91.218.229.13:80 | http://cs-changer.ru/font-awesome.min.css | RU | text | 5.37 Kb | whitelisted |
3124 | chrome.exe | GET | 200 | 91.218.229.13:80 | http://cs-changer.ru/style.css | RU | text | 3.03 Kb | whitelisted |
3124 | chrome.exe | GET | 200 | 91.218.229.13:80 | http://cs-changer.ru/responsive.css | RU | text | 490 b | whitelisted |
3124 | chrome.exe | GET | 200 | 91.218.229.13:80 | http://cs-changer.ru/bootstrap.min.js | RU | text | 9.24 Kb | whitelisted |
3124 | chrome.exe | GET | 200 | 91.218.229.13:80 | http://cs-changer.ru/scripts.js | RU | text | 2.11 Kb | whitelisted |
3124 | chrome.exe | GET | 200 | 91.218.229.13:80 | http://cs-changer.ru/banner_prize.png | RU | image | 39.3 Kb | whitelisted |
3124 | chrome.exe | GET | 200 | 91.218.229.13:80 | http://cs-changer.ru/particles.min.js | RU | text | 5.84 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3124 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4 | System | 178.154.131.217:445 | yastatic.net | YANDEX LLC | RU | whitelisted |
2844 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 178.154.131.216:445 | yastatic.net | YANDEX LLC | RU | whitelisted |
4 | System | 178.154.131.215:445 | yastatic.net | YANDEX LLC | RU | whitelisted |
— | — | 178.154.131.215:137 | yastatic.net | YANDEX LLC | RU | whitelisted |
3124 | chrome.exe | 172.217.16.131:443 | www.google.de | Google Inc. | US | whitelisted |
3124 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3124 | chrome.exe | 91.218.229.13:80 | cs-changer.ru | Internet-Hosting Ltd | RU | malicious |
3124 | chrome.exe | 88.212.201.199:80 | counter.yadro.ru | United Network LLC | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yastatic.net |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3936 | csc.exe | A Network Trojan was detected | MALWARE [PTsecurity] PowerShell.Downloader httpHeader |
3936 | csc.exe | A Network Trojan was detected | MALWARE [PTsecurity] PowerShell.Downloader httpHeader |
3936 | csc.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
3936 | csc.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
1 ETPRO signatures available at the full report