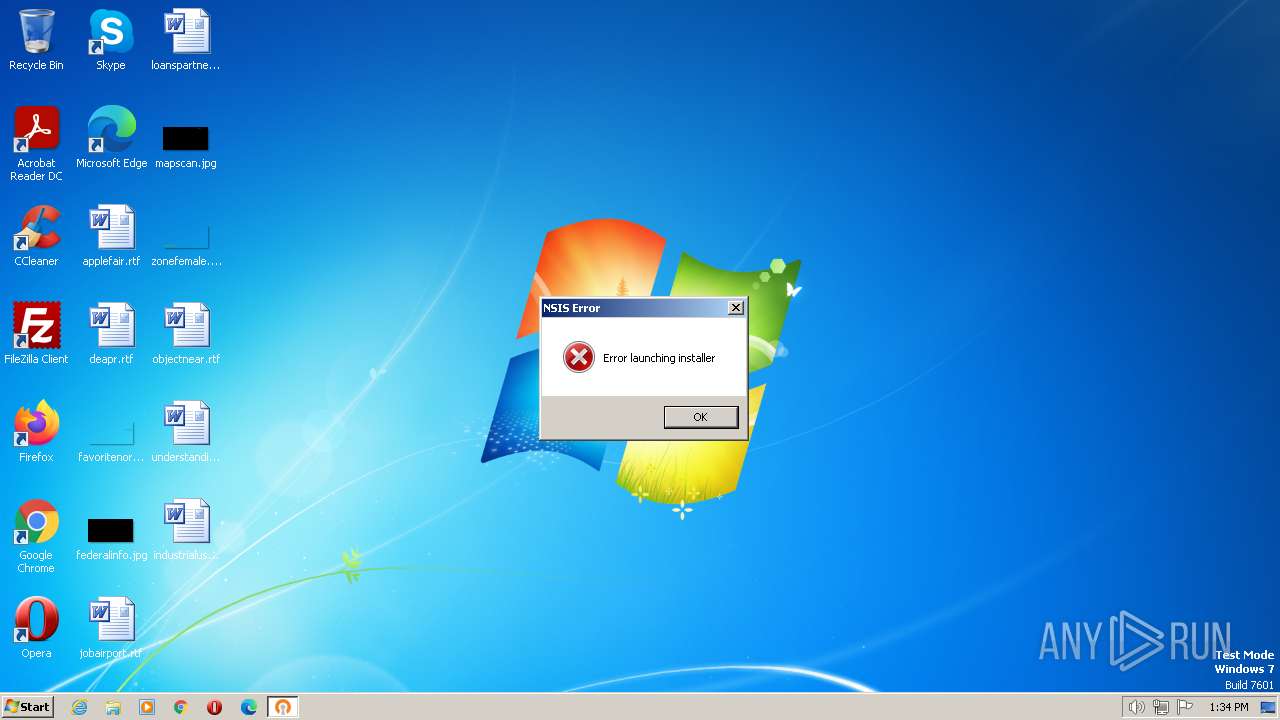
| File name: | VPN登录控件.exe.VIRUS |
| Full analysis: | https://app.any.run/tasks/5dd0a0e2-6d31-439b-ad0f-06fd51da41c5 |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2023, 12:34:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DA402EE030CA67FEE6C221FABF4AC8D1 |
| SHA1: | 01CFF98DCC7FB53D6F43688668032719F29D5BD9 |
| SHA256: | 8353D2AC6E05A4DF1FDC576D2AF8F86ACDA300A06B18F0BFA736CD43BC3516D4 |
| SSDEEP: | 98304:DuBGoYZGOTHpfWM/gZ1GxHTevOVr48OEyoome5n6F2ZHt:DCG98OTH1gMHdr4ZEyZtnn |
MALICIOUS
Application was dropped or rewritten from another process
- winIogon.exe (PID: 3892)
- VPN登录控件.exe (PID: 2988)
Connects to the CnC server
- winIogon.exe (PID: 3892)
SUSPICIOUS
Executable content was dropped or overwritten
- VPN登录控件.exe.VIRUS.exe (PID: 3612)
The process executes VB scripts
- VPN登录控件.exe.VIRUS.exe (PID: 3612)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1696)
Reads the Internet Settings
- wscript.exe (PID: 1696)
INFO
Create files in a temporary directory
- VPN登录控件.exe.VIRUS.exe (PID: 3612)
Checks supported languages
- VPN登录控件.exe.VIRUS.exe (PID: 3612)
- winIogon.exe (PID: 3892)
- VPN登录控件.exe (PID: 2988)
The process checks LSA protection
- VPN登录控件.exe (PID: 2988)
The executable file from the user directory is run by the CMD process
- VPN登录控件.exe (PID: 2988)
Reads the computer name
- VPN登录控件.exe (PID: 2988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| ProductVersion: | 19 |
|---|---|
| ProductName: | 7-Zip |
| OriginalFileName: | 7zS.sfx.exe |
| LegalCopyright: | Copyright (c) 1999-2018 Igor Pavlov |
| InternalName: | 7zS.sfx |
| FileVersion: | 19 |
| FileDescription: | 7z Setup SFX |
| CompanyName: | Igor Pavlov |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 19.0.0.0 |
| FileVersionNumber: | 19.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x1910c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 28160 |
| CodeSize: | 104448 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, 32-bit |
| TimeStamp: | 2019:02:21 16:00:00+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Feb-2019 16:00:00 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 19.00 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2018 Igor Pavlov |
| OriginalFilename: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 19.00 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Feb-2019 16:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00019745 | 0x00019800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63014 |
.rdata | 0x0001B000 | 0x00003A98 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39319 |
.data | 0x0001F000 | 0x000023F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.30023 |
.sxdata | 0x00022000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00023000 | 0x00000AB0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.32929 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.42782 | 700 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.18403 | 296 | UNKNOWN | English - United States | RT_ICON |
97 | 3.04857 | 184 | UNKNOWN | English - United States | RT_DIALOG |
188 | 2.17822 | 84 | UNKNOWN | English - United States | RT_STRING |
207 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
43
Monitored processes
6
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1696 | wscript.exe C:\Users\admin\AppData\Local\Temp\7zSC1E21632\install.vbs VPN登录控件.exe winIogon.exe | C:\Windows\System32\wscript.exe | — | VPN登录控件.exe.VIRUS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1820 | "C:\Users\admin\Downloads\VPN登录控件.exe.VIRUS.exe" | C:\Users\admin\Downloads\VPN登录控件.exe.VIRUS.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z Setup SFX Exit code: 3221226540 Version: 19.00 Modules
| |||||||||||||||
| 2084 | "C:\Windows\System32\cmd.exe" /K VPN登录控件.exe & exit | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2988 | VPN登录控件.exe | C:\Users\admin\AppData\Local\Temp\7zSC1E21632\VPN登录控件.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 3612 | "C:\Users\admin\Downloads\VPN登录控件.exe.VIRUS.exe" | C:\Users\admin\Downloads\VPN登录控件.exe.VIRUS.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Setup SFX Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 3892 | "C:\Users\admin\AppData\Local\Temp\7zSC1E21632\winIogon.exe" | C:\Users\admin\AppData\Local\Temp\7zSC1E21632\winIogon.exe | wscript.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 582
Read events
1 574
Write events
8
Delete events
0
Modification events
| (PID) Process: | (1696) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1696) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1696) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1696) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3612 | VPN登录控件.exe.VIRUS.exe | C:\Users\admin\AppData\Local\Temp\7zSC1E21632\VPN登录控件.exe | executable | |
MD5:73BCD5B6A0208D953A38ED74FDEF5FF1 | SHA256:16165E4505874E71C9FE732041274C3CE10E0881DFEEECE529E8B54C5B558296 | |||
| 3612 | VPN登录控件.exe.VIRUS.exe | C:\Users\admin\AppData\Local\Temp\7zSC1E21632\winIogon.exe | executable | |
MD5:18EA180AAE6E8639FABD2A86F35B5311 | SHA256:5760FCD7F963E71791770704D50A2C6C791D1742649412A829DCF3CABF431D6B | |||
| 3612 | VPN登录控件.exe.VIRUS.exe | C:\Users\admin\AppData\Local\Temp\7zSC1E21632\install.vbs | text | |
MD5:90A1BA69792DCB304A28A848A44C60B9 | SHA256:F1E4C02163E3E66F493C784D9B1301DE6E53BF4BCFFA02A84931F3682FCFDC20 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3388 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3892 | winIogon.exe | 47.100.65.182:8081 | — | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3892 | winIogon.exe | A Network Trojan was detected | ET MALWARE Win32/Corrempa/HZRAT CnC Checkin |
3892 | winIogon.exe | A Network Trojan was detected | ET MALWARE Win32/Corrempa/HZRAT CnC Checkin |