| download: | research |
| Full analysis: | https://app.any.run/tasks/e10b2657-773f-4cc6-b558-5444d8991520 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 10:42:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | CC7BAD3A675AC76148B34F4DBE6E1607 |
| SHA1: | F777BF23DB32C2838DF933BD4499229BE60EDD1D |
| SHA256: | 834CD76239C0ABADDE82FD69416145B22D477EC5AC8D3036C2D55BE35995A536 |
| SSDEEP: | 1536:NzPxaERzpjT1/IcY75y5d5g5h5H50565mhNfBjRF1icQRQRdQp:NbxhRVjTBIcYlMXajZGUmh1BjPMCjQp |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1772)
- iexplore.exe (PID: 1936)
Reads internet explorer settings
- iexplore.exe (PID: 1936)
Reads settings of System Certificates
- iexplore.exe (PID: 1936)
- iexplore.exe (PID: 1772)
Reads Internet Cache Settings
- iexplore.exe (PID: 1772)
- iexplore.exe (PID: 2096)
Changes internet zones settings
- iexplore.exe (PID: 1772)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1936)
- iexplore.exe (PID: 1772)
Changes settings of System certificates
- iexplore.exe (PID: 1936)
- iexplore.exe (PID: 1772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| HTTPEquivXUaCompatible: | ie=edge |
|---|---|
| viewport: | width=device-width, initial-scale=1, shrink-to-fit=no |
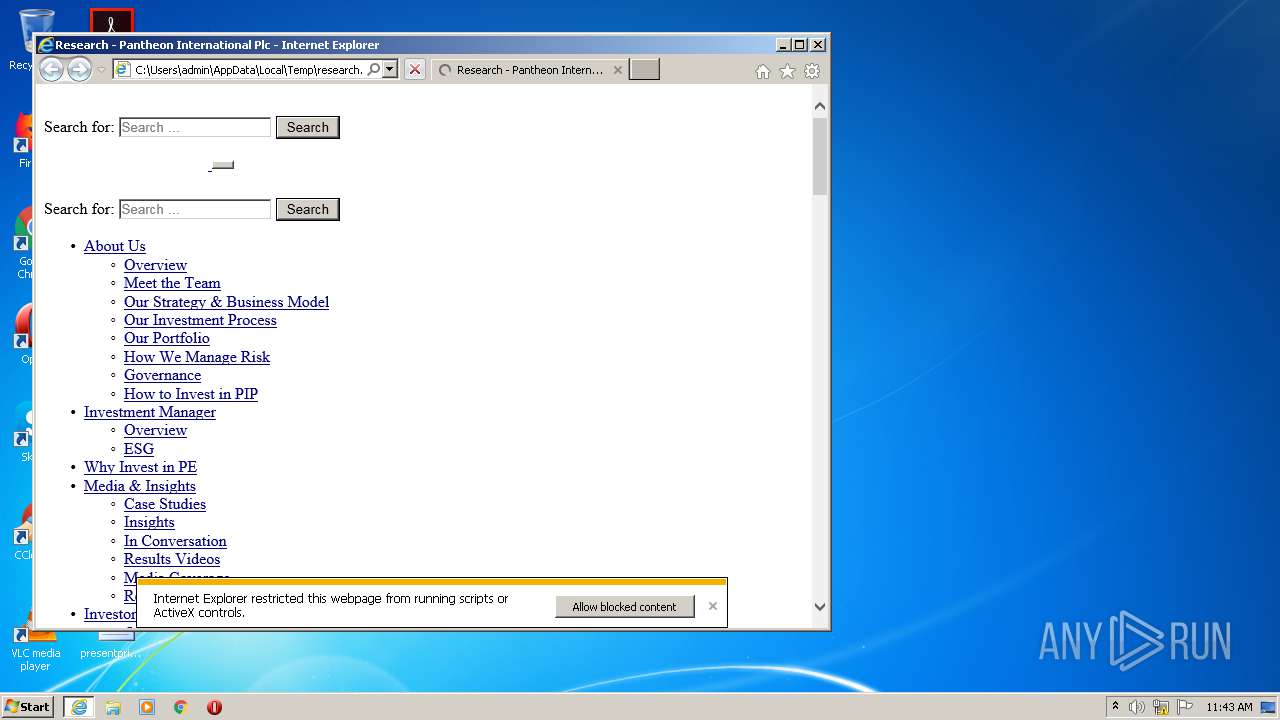
| Title: | Research - Pantheon International Plc |
| Robots: | max-snippet:-1, max-image-preview:large, max-video-preview:-1 |
| twitterCard: | summary_large_image |
| twitterTitle: | Research - Pantheon International Plc |
| msapplicationTileImage: | https://cdn.piplc.com/pip/app/uploads/2020/07/08155215/cropped-PIP_logo_navy-270x270.jpg |
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1772 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\research.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1772 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1772 CREDAT:398593 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 206
Read events
2 095
Write events
104
Delete events
7
Modification events
| (PID) Process: | (1772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3773111434 | |||
| (PID) Process: | (1772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844621 | |||
| (PID) Process: | (1772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
88
Text files
19
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1936 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab5019.tmp | — | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar501A.tmp | — | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0DA515F703BB9B49479E8697ADB0B955_7DC3E633EDFAEFC3AA3C99552548EC2F | binary | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_324D9D55FDD76ED80477DAE17E3A2DBB | binary | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0DA515F703BB9B49479E8697ADB0B955_7DC3E633EDFAEFC3AA3C99552548EC2F | der | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_324D9D55FDD76ED80477DAE17E3A2DBB | der | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
71
DNS requests
24
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1936 | iexplore.exe | GET | 200 | 13.35.253.170:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 13.35.253.170:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEB3oRgfjsJWUCAAAAABbLrQ%3D | US | der | 471 b | whitelisted |
1936 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 13.35.253.170:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 13.35.253.170:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 13.35.253.170:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 13.35.253.148:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 13.35.253.170:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1936 | iexplore.exe | 99.86.7.33:443 | cdn.piplc.com | AT&T Services, Inc. | US | suspicious |
1936 | iexplore.exe | 172.64.137.25:443 | ipmeta.io | Cloudflare Inc | US | unknown |
— | — | 99.86.7.33:443 | cdn.piplc.com | AT&T Services, Inc. | US | suspicious |
1936 | iexplore.exe | 3.218.236.32:443 | pin.ir-data.com | — | US | suspicious |
1936 | iexplore.exe | 172.217.23.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1936 | iexplore.exe | 13.35.253.170:80 | o.ss2.us | — | US | unknown |
1936 | iexplore.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
— | — | 13.35.253.148:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
1936 | iexplore.exe | 52.210.110.2:443 | www.piplc.com | Amazon.com, Inc. | IE | unknown |
— | — | 151.101.66.109:443 | polyfill.io | Fastly | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.piplc.com |
| suspicious |
www.piplc.com |
| unknown |
polyfill.io |
| whitelisted |
ipmeta.io |
| whitelisted |
pin.ir-data.com |
| suspicious |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1936 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1936 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1936 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1936 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1936 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1936 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |