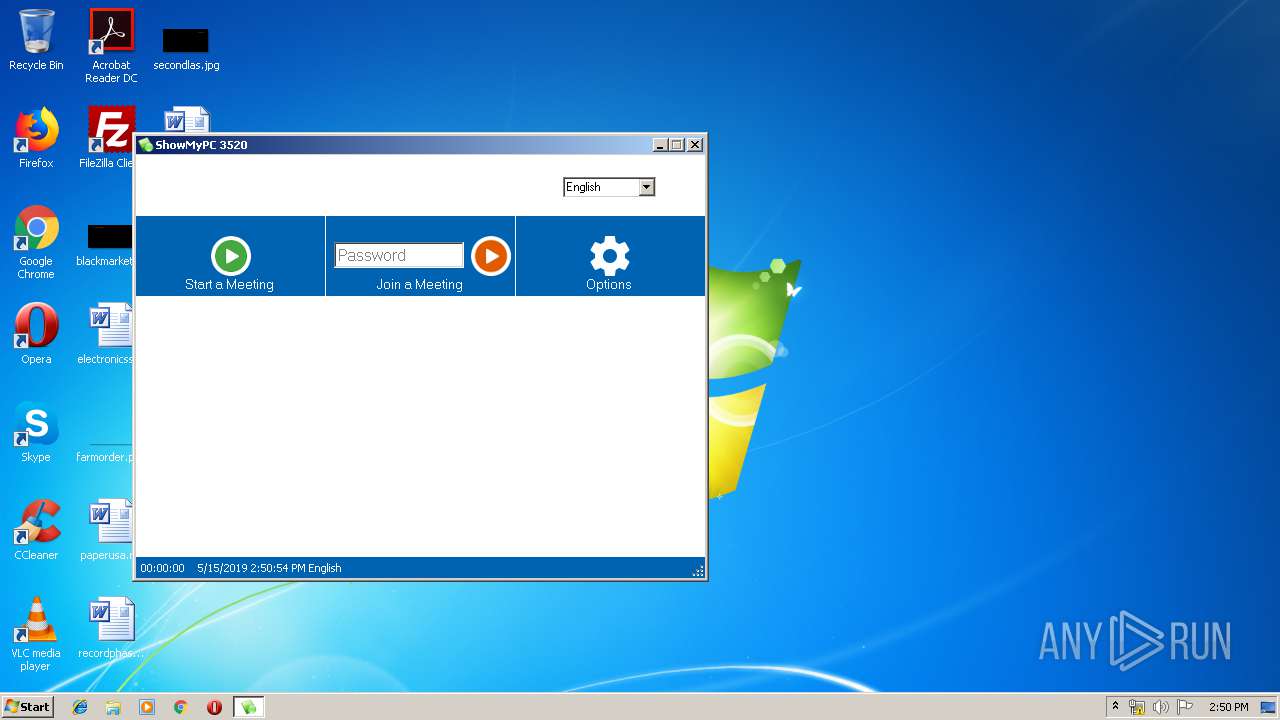
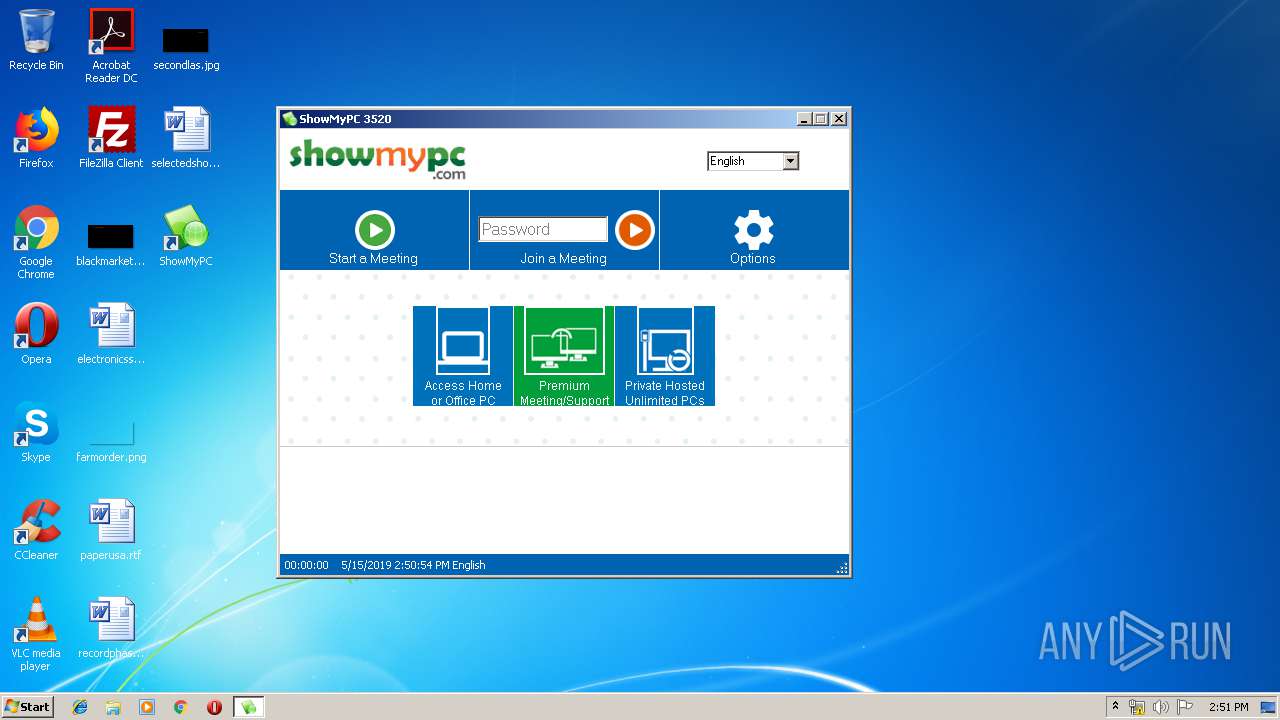
| URL: | https://download3.showmypc.com/ShowMyPC3520.exe |
| Full analysis: | https://app.any.run/tasks/38c27271-5b10-47f9-9d3f-5a51256177a9 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 13:50:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3D417341C3AB73E4EBE46DCF437F0881 |
| SHA1: | 2426FABE902DD9240BB3360151B3FBDCDEBFC9FD |
| SHA256: | 8346A7938DA54F82B6337C21317A216FFD1AEFF022EFB18CC36073670F2A0BA9 |
| SSDEEP: | 3:N8SE4LKJIquSB1Gb:2SeoTb |
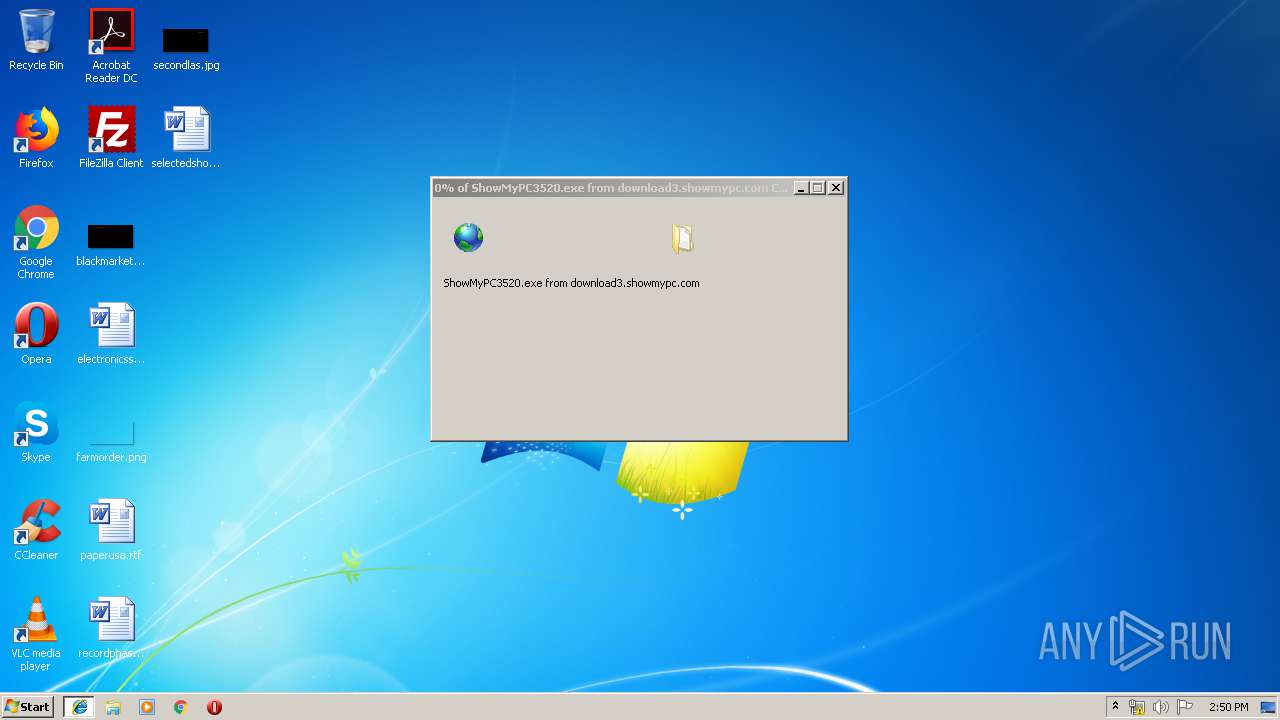
MALICIOUS
Application was dropped or rewritten from another process
- ShowMyPC3520[1].exe (PID: 3044)
- SMPCSetup.exe (PID: 3036)
- SMPCSetup.exe (PID: 3820)
Loads dropped or rewritten executable
- ShowMyPC3520[1].exe (PID: 3044)
- SMPCSetup.exe (PID: 3036)
- SMPCSetup.exe (PID: 3820)
- regsvr32.exe (PID: 760)
Starts NET.EXE for service management
- SMPCSetup.exe (PID: 3036)
Changes settings of System certificates
- SMPCSetup.exe (PID: 3820)
Registers / Runs the DLL via REGSVR32.EXE
- SMPCSetup.exe (PID: 3820)
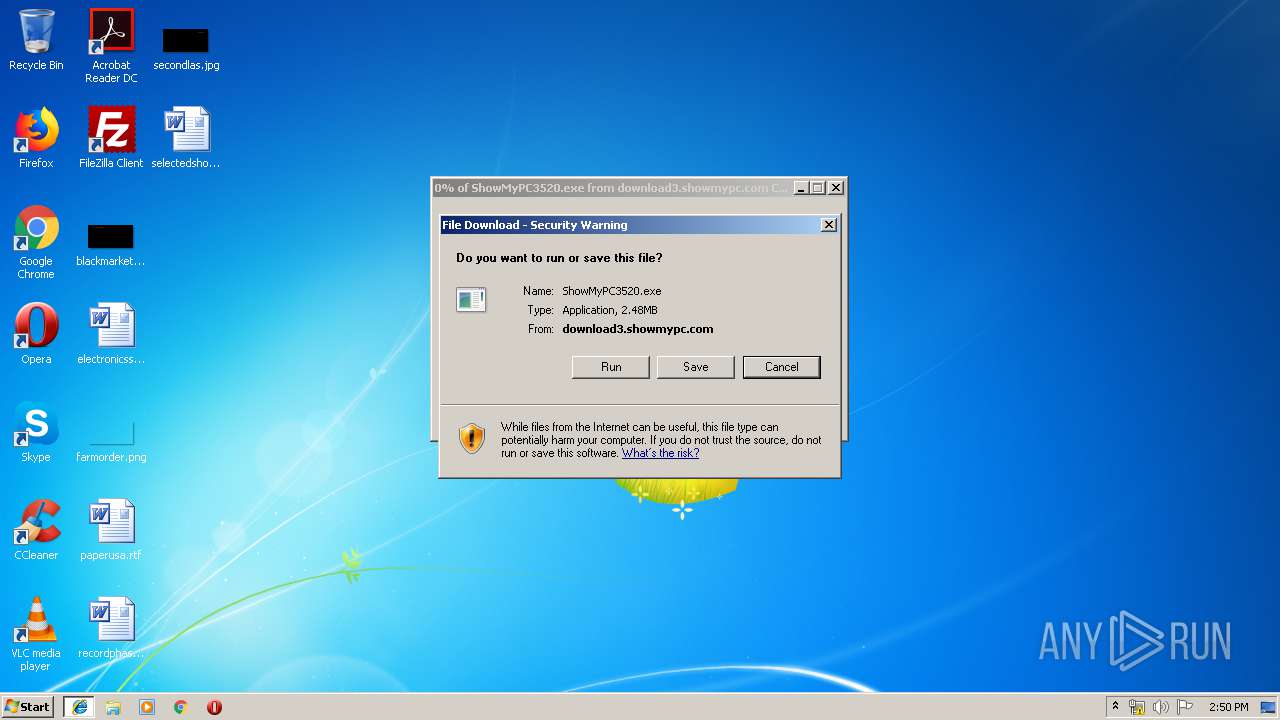
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 3272)
- ShowMyPC3520[1].exe (PID: 3044)
Reads internet explorer settings
- SMPCSetup.exe (PID: 3036)
- SMPCSetup.exe (PID: 3820)
Application launched itself
- SMPCSetup.exe (PID: 3036)
Reads Environment values
- SMPCSetup.exe (PID: 3036)
- SMPCSetup.exe (PID: 3820)
Uses NETSH.EXE for network configuration
- SMPCSetup.exe (PID: 3036)
- SMPCSetup.exe (PID: 3820)
Creates COM task schedule object
- regsvr32.exe (PID: 760)
Creates files in the user directory
- SMPCSetup.exe (PID: 3820)
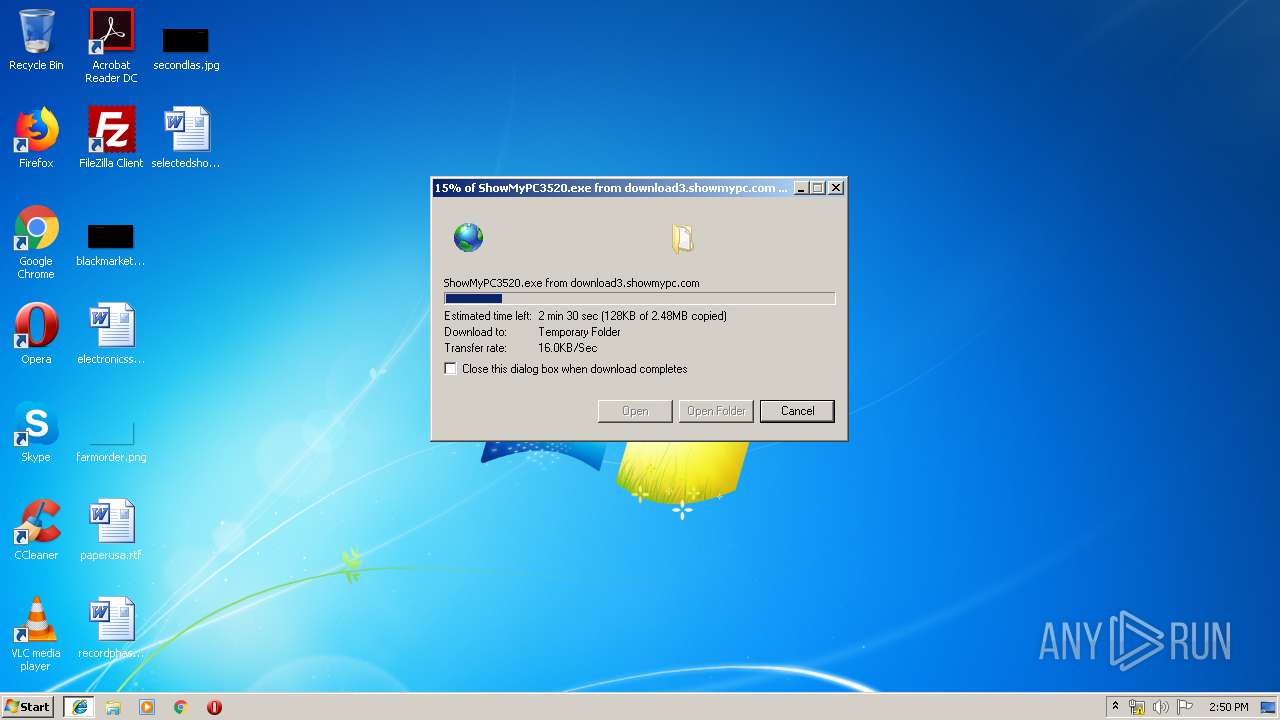
INFO
Creates files in the user directory
- iexplore.exe (PID: 3096)
Application launched itself
- iexplore.exe (PID: 3272)
Changes internet zones settings
- iexplore.exe (PID: 3272)
Reads Internet Cache Settings
- iexplore.exe (PID: 3096)
Reads settings of System Certificates
- SMPCSetup.exe (PID: 3036)
- SMPCSetup.exe (PID: 3820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
28
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Windows\System32\net.exe" stop tvnserver | C:\Windows\System32\net.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | "C:\Windows\System32\netsh.exe" advfirewall firewall add rule name="ShowMyPCAuto" dir=in action=allow program="C:\Users\admin\AppData\Local\Temp\ShowMyPC\-ShowMyPC3520[1]\SMPCSetup.exe" enable=yes | C:\Windows\System32\netsh.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 760 | "C:\Windows\System32\regsvr32.exe" "C:\Users\admin\AppData\Local\Temp\ShowMyPC\-ShowMyPC3520[1]\wodVPN.dll" /s | C:\Windows\System32\regsvr32.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | "C:\Windows\System32\netsh.exe" firewall add allowedprogram "C:\Users\admin\AppData\Local\Temp\ShowMyPC\-ShowMyPC3520[1]\SMPCSetup.exe" "ShowMyPCAuto" ENABLE | C:\Windows\System32\netsh.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Windows\System32\netsh.exe" firewall add allowedprogram "C:\Users\admin\AppData\Local\Temp\ShowMyPC\-ShowMyPC3520[1]\SMPCSetup.exe" "ShowMyPCAuto" ENABLE | C:\Windows\System32\netsh.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | C:\Windows\system32\net1 stop tvnserver | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2336 | "C:\Windows\System32\netsh.exe" firewall delete allowedprogram "C:\Users\admin\AppData\Local\Temp\ShowMyPC\-ShowMyPC3520[1]\SMPCSetup.exe" | C:\Windows\System32\netsh.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | "C:\Windows\System32\net.exe" stop uvnc_service | C:\Windows\System32\net.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2636 | "C:\Windows\System32\netsh.exe" advfirewall firewall delete rule name="ShowMyPCAuto" program="C:\Users\admin\AppData\Local\Temp\ShowMyPC\-ShowMyPC3520[1]\SMPCSetup.exe" | C:\Windows\System32\netsh.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2708 | "C:\Windows\System32\netsh.exe" advfirewall firewall add rule name="ShowMyPCtvnservertemp" dir=in action=allow program="C:\Users\admin\AppData\Local\Temp\ShowMyPC\-ShowMyPC3520[1]\tvnserver.exe" enable=yes | C:\Windows\System32\netsh.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 680
Read events
1 726
Write events
952
Delete events
2
Modification events
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {6283C3D9-7718-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307050003000F000D00320018007200 | |||
Executable files
18
Suspicious files
8
Text files
49
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC4492A1A12EBCFB8.TMP | — | |
MD5:— | SHA256:— | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019051520190516\index.dat | dat | |
MD5:A101FE7BBEA191C36002A6862BB90DE2 | SHA256:91E0C6E07A31E60E0A44A6A4988C54703FEE142E0AE5383C1B935C0109768A57 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\00G3HUBI\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RHNMSH6I\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3044 | ShowMyPC3520[1].exe | C:\Users\admin\AppData\Local\Temp\ShowMyPC\-ShowMyPC3520[1]\settings.ini | text | |
MD5:64D3A6D1366F2864599D904E01C6CC9D | SHA256:ADC989A4AB444C8153C1647FF8DC25CCCB73B0AD554951350FBAA5B67BD12495 | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\ShowMyPC3520[1].exe | executable | |
MD5:CBD6AFBA01E715B15FCEDD953F24A286 | SHA256:EA6AC32A9E4674B205D0F952848D72830E082E81CD9A811E93366FE4AC3C2040 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RHNMSH6I\ShowMyPC3520[1].exe | executable | |
MD5:CBD6AFBA01E715B15FCEDD953F24A286 | SHA256:EA6AC32A9E4674B205D0F952848D72830E082E81CD9A811E93366FE4AC3C2040 | |||
| 3044 | ShowMyPC3520[1].exe | C:\Users\admin\AppData\Local\Temp\ShowMyPC\-ShowMyPC3520[1]\SMPCSetup.exe | executable | |
MD5:885DE0364B125E3AA85005EA8222B06C | SHA256:30C4485C4ECA05E41EADF0C3E49DBF8EA8441F1334B7B8C7AD644B3C63824E4D | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\4D1WAOBG\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
13
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3036 | SMPCSetup.exe | GET | — | 35.239.221.136:80 | http://showmypc.com/app/about-us1.html?pv=3520 | US | — | — | malicious |
3820 | SMPCSetup.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSACodeSigningCA.crt | GB | der | 1.47 Kb | whitelisted |
3820 | SMPCSetup.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
3820 | SMPCSetup.exe | GET | 200 | 35.239.221.136:80 | http://showmypc.com/app/about-us1.html?pv=3520 | US | html | 4.92 Kb | malicious |
3820 | SMPCSetup.exe | GET | 200 | 52.216.176.61:80 | http://s3.showmypc.com/js/jquery-1.11.2.min.js | US | text | 93.6 Kb | shared |
3820 | SMPCSetup.exe | GET | 200 | 52.216.176.61:80 | http://s3.showmypc.com/js/ui/ui.core.js | US | text | 13.6 Kb | shared |
3820 | SMPCSetup.exe | GET | 200 | 52.216.176.61:80 | http://s3.showmypc.com/js/ui/ui.tabs.js | US | text | 18.6 Kb | shared |
3820 | SMPCSetup.exe | GET | 200 | 52.216.176.61:80 | http://s3.showmypc.com/js/themes/base/ui.theme.css | US | text | 17.5 Kb | shared |
3820 | SMPCSetup.exe | GET | 200 | 52.216.176.61:80 | http://s3.showmypc.com/js/themes/base/ui.base.css | US | text | 257 b | shared |
3820 | SMPCSetup.exe | GET | 200 | 52.216.176.61:80 | http://s3.showmypc.com/js/themes/base/ui.core.css | US | text | 1.35 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3096 | iexplore.exe | 35.239.221.136:443 | download3.showmypc.com | — | US | suspicious |
3272 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3036 | SMPCSetup.exe | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
3036 | SMPCSetup.exe | 67.27.234.126:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
— | — | 35.239.221.136:80 | download3.showmypc.com | — | US | suspicious |
3036 | SMPCSetup.exe | 35.239.221.136:443 | download3.showmypc.com | — | US | suspicious |
3820 | SMPCSetup.exe | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
3820 | SMPCSetup.exe | 35.239.221.136:443 | download3.showmypc.com | — | US | suspicious |
3820 | SMPCSetup.exe | 35.239.221.136:80 | download3.showmypc.com | — | US | suspicious |
3820 | SMPCSetup.exe | 52.216.176.61:80 | s3.showmypc.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download3.showmypc.com |
| malicious |
www.bing.com |
| whitelisted |
crt.comodoca.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
showmypc.com |
| malicious |
s3.showmypc.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |