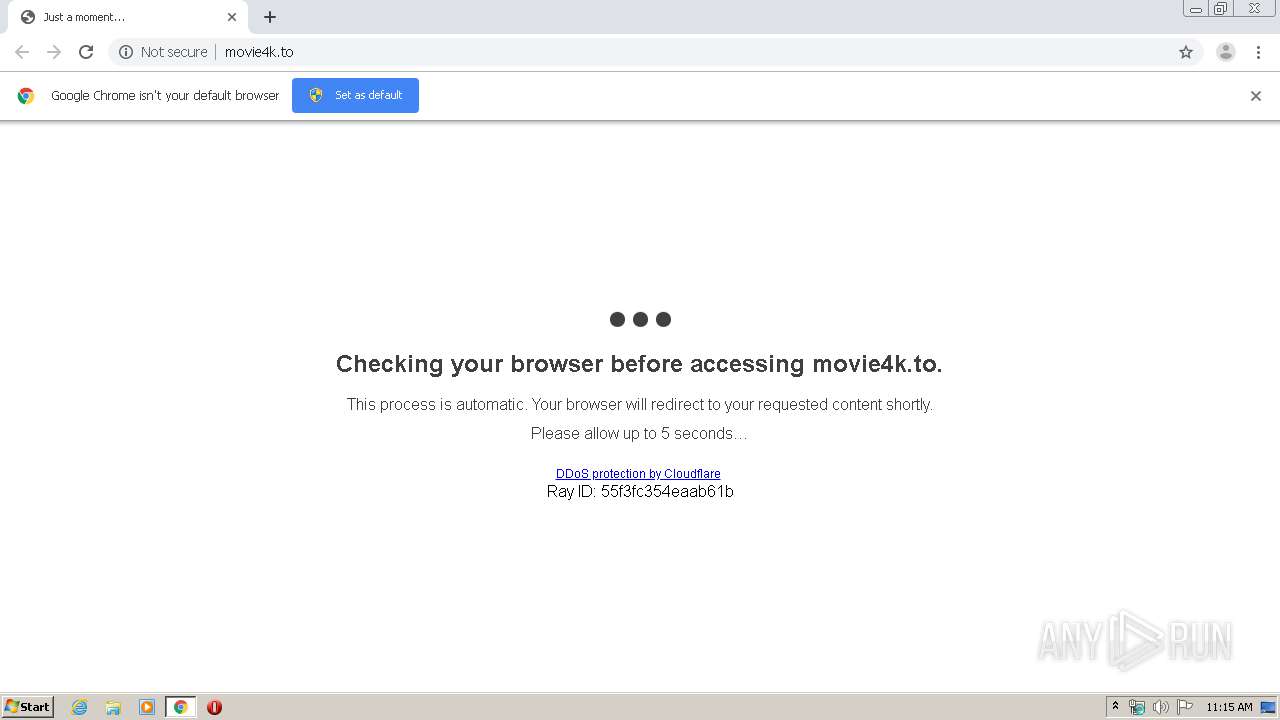
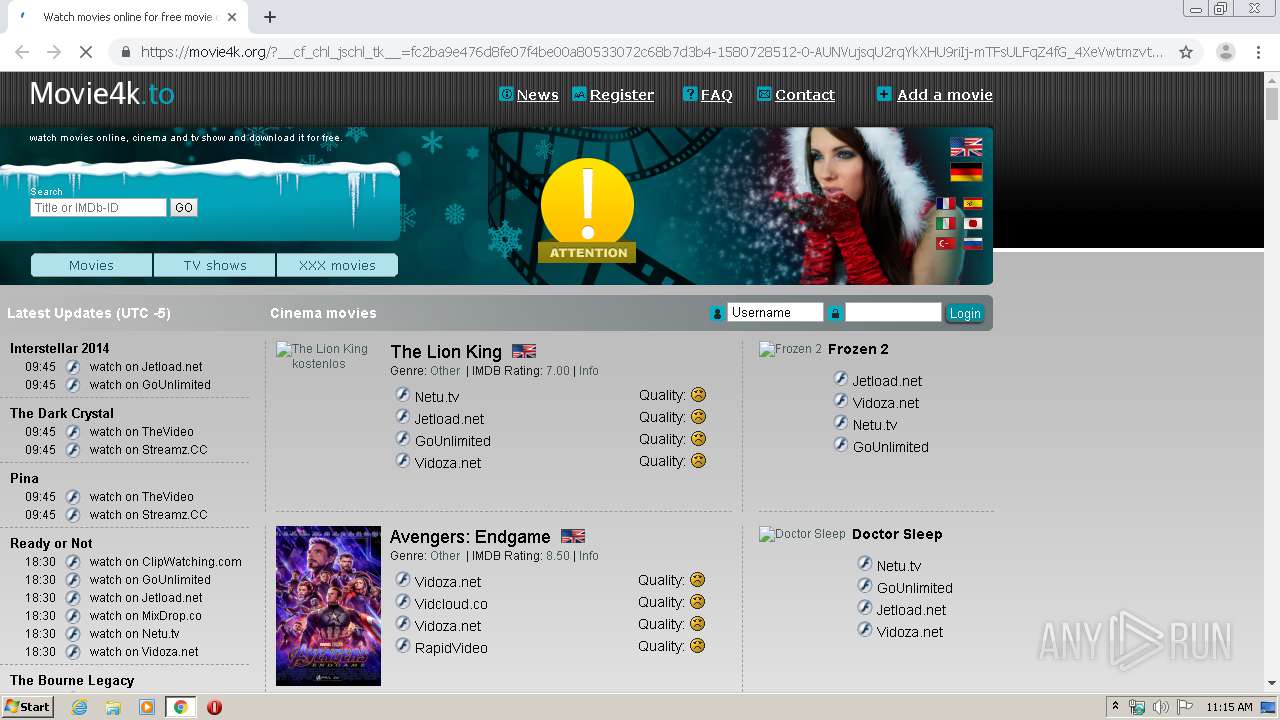
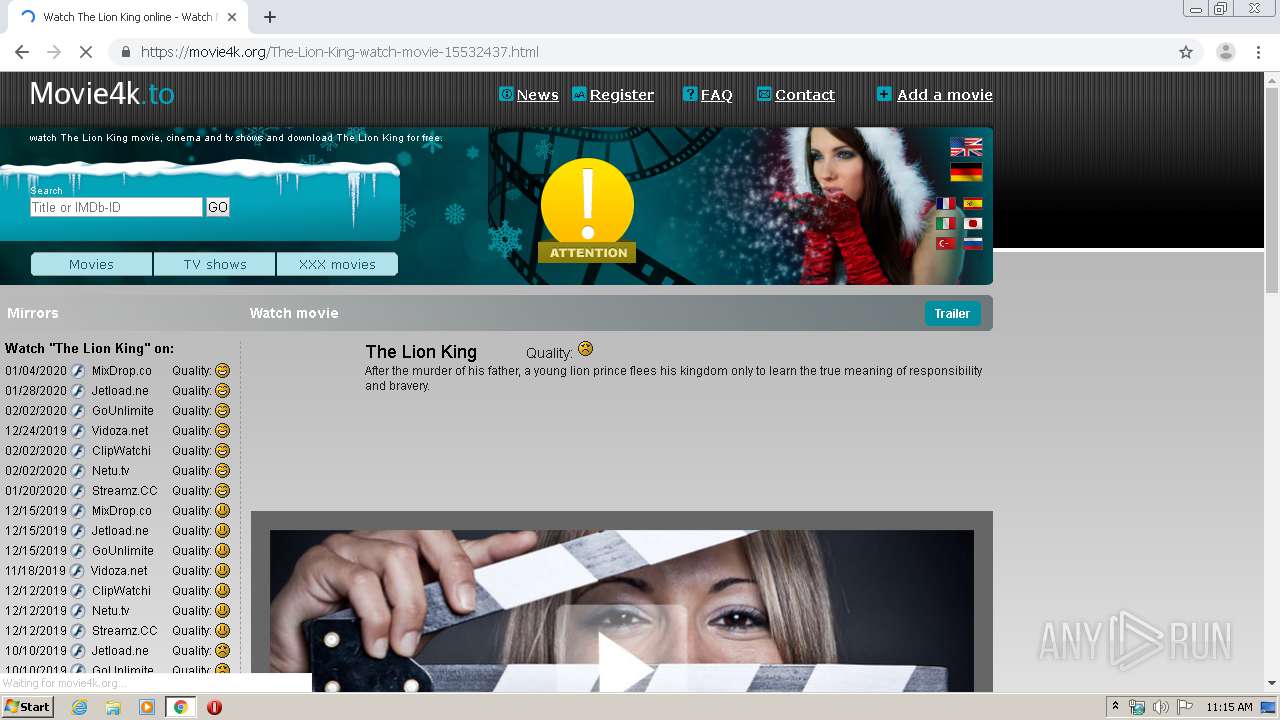
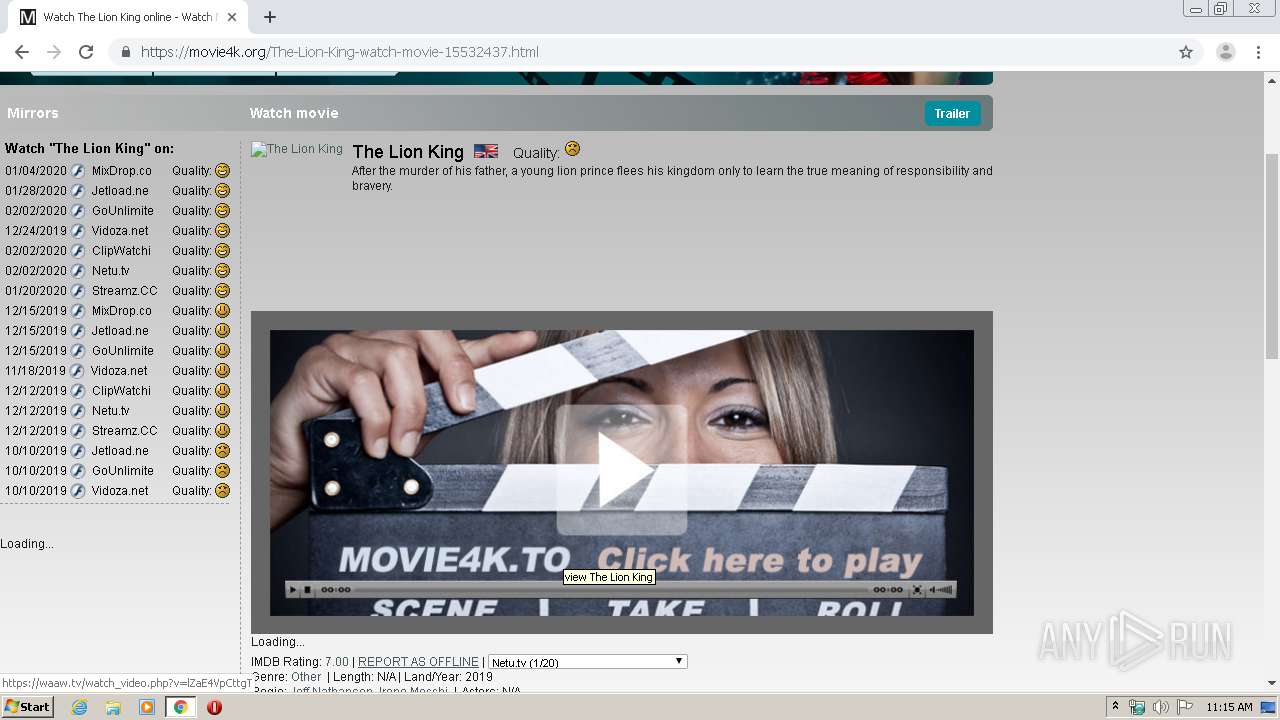
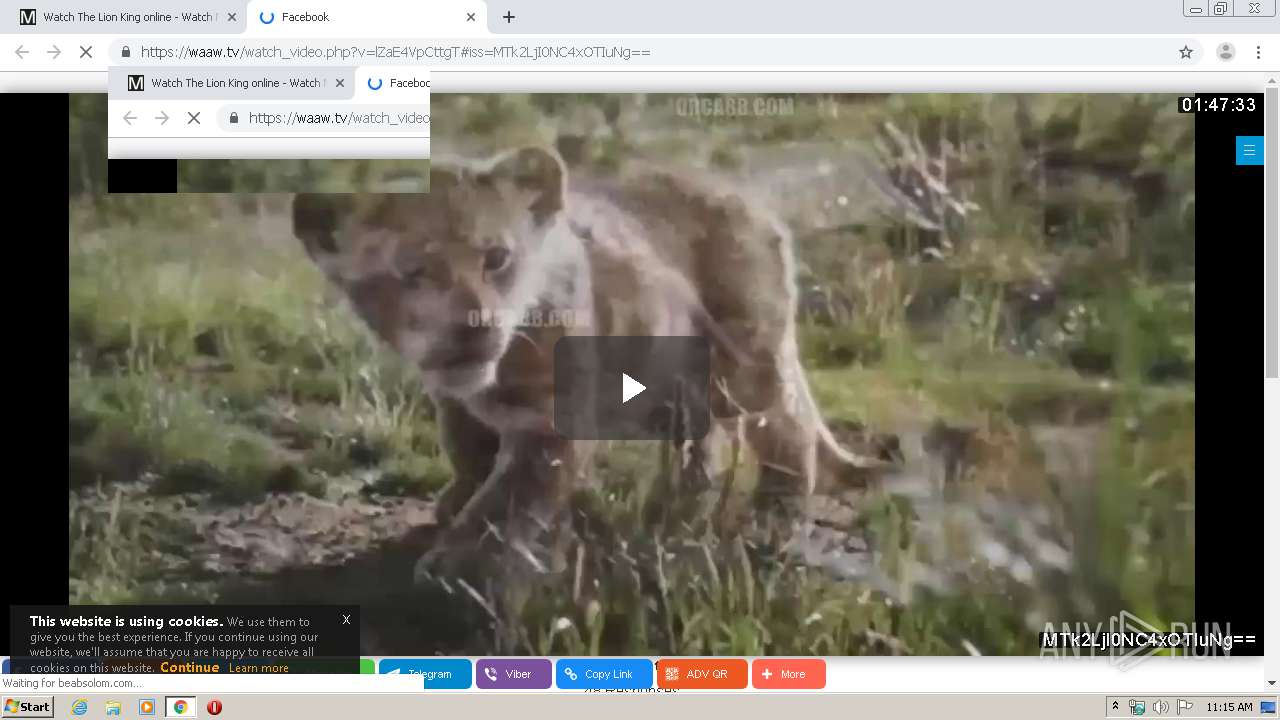
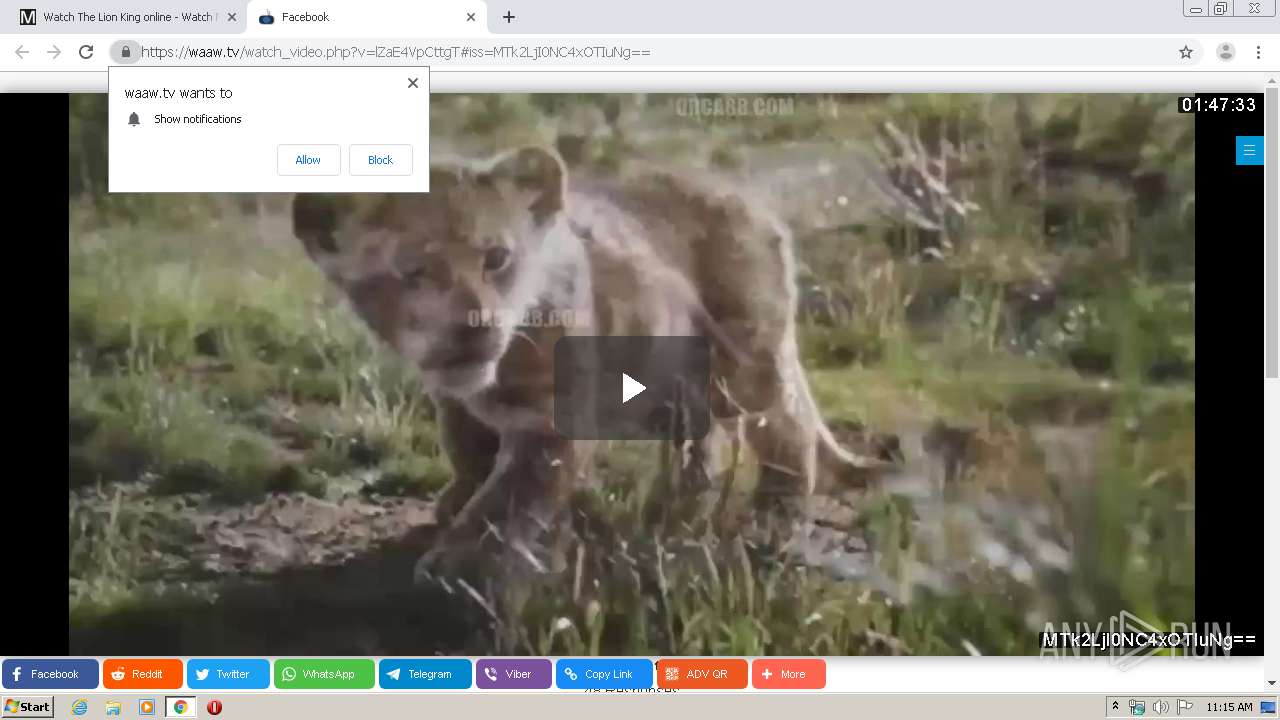
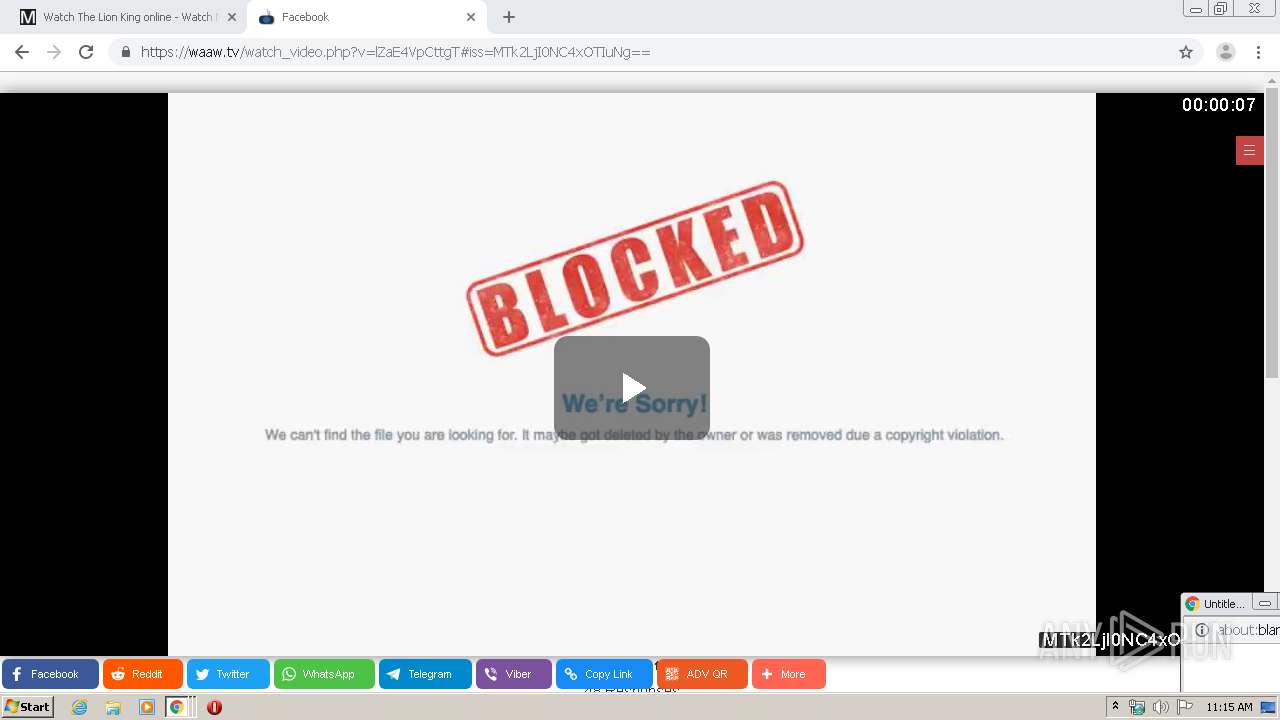
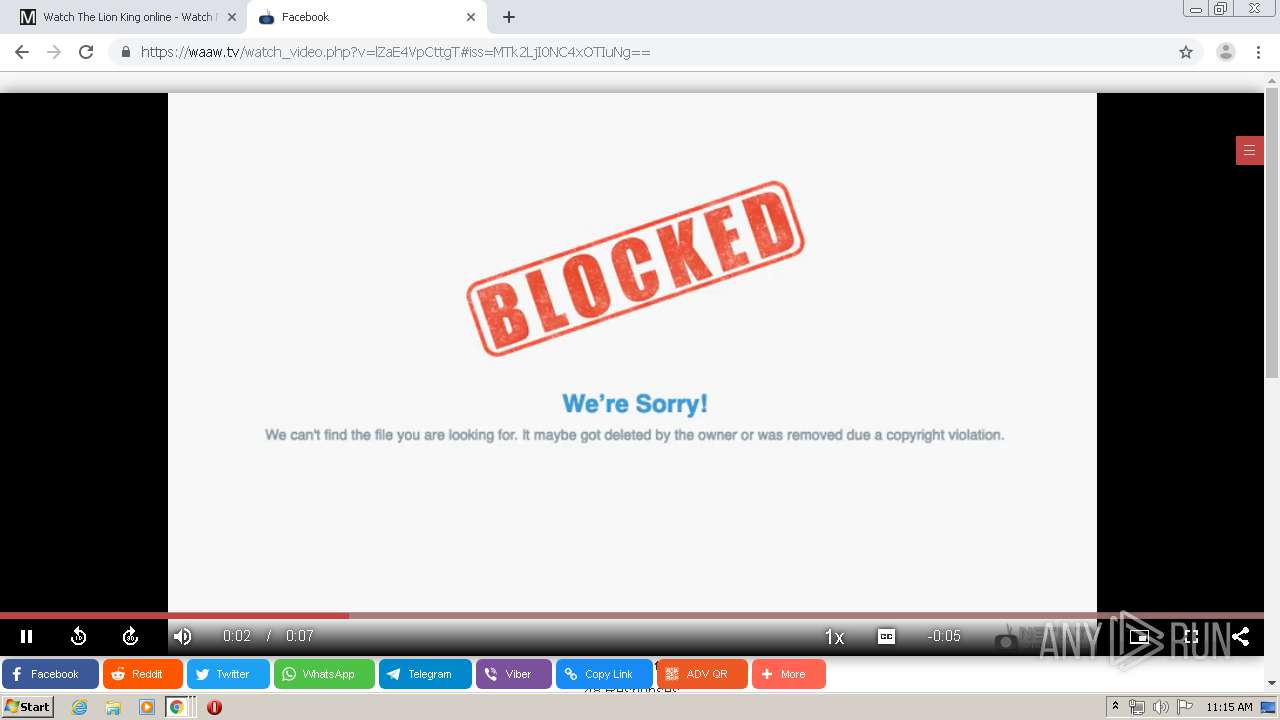
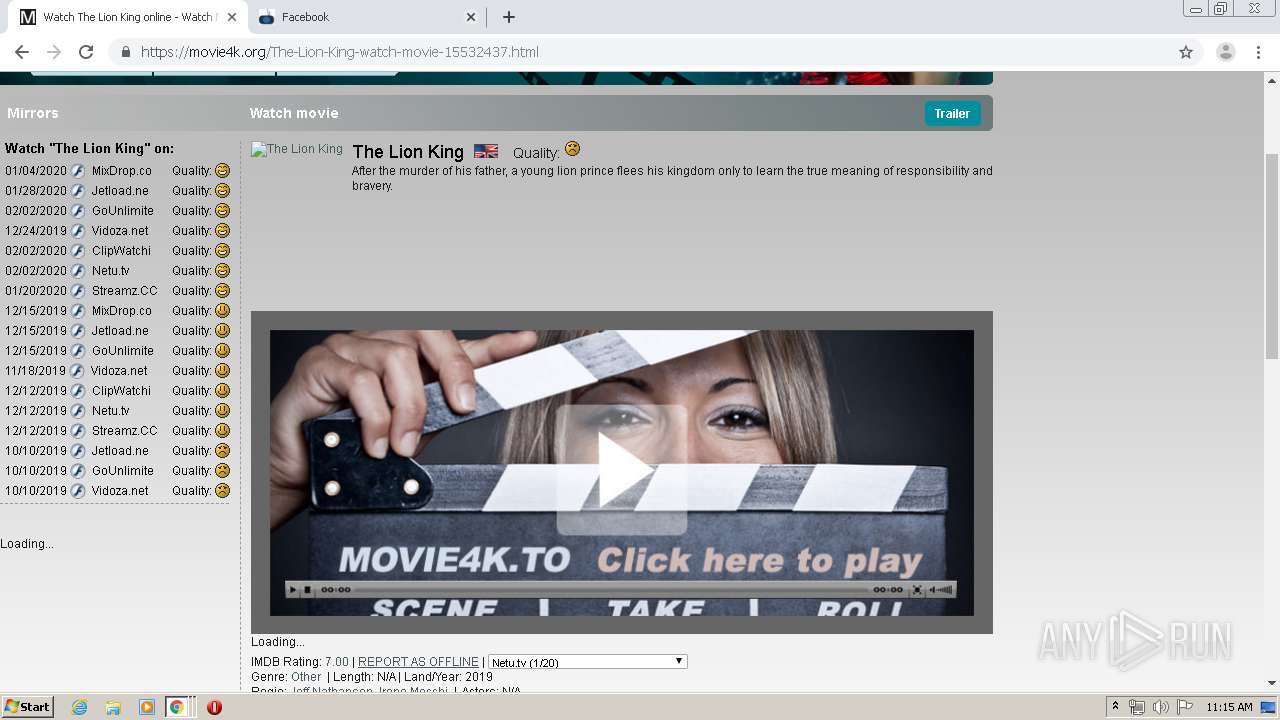
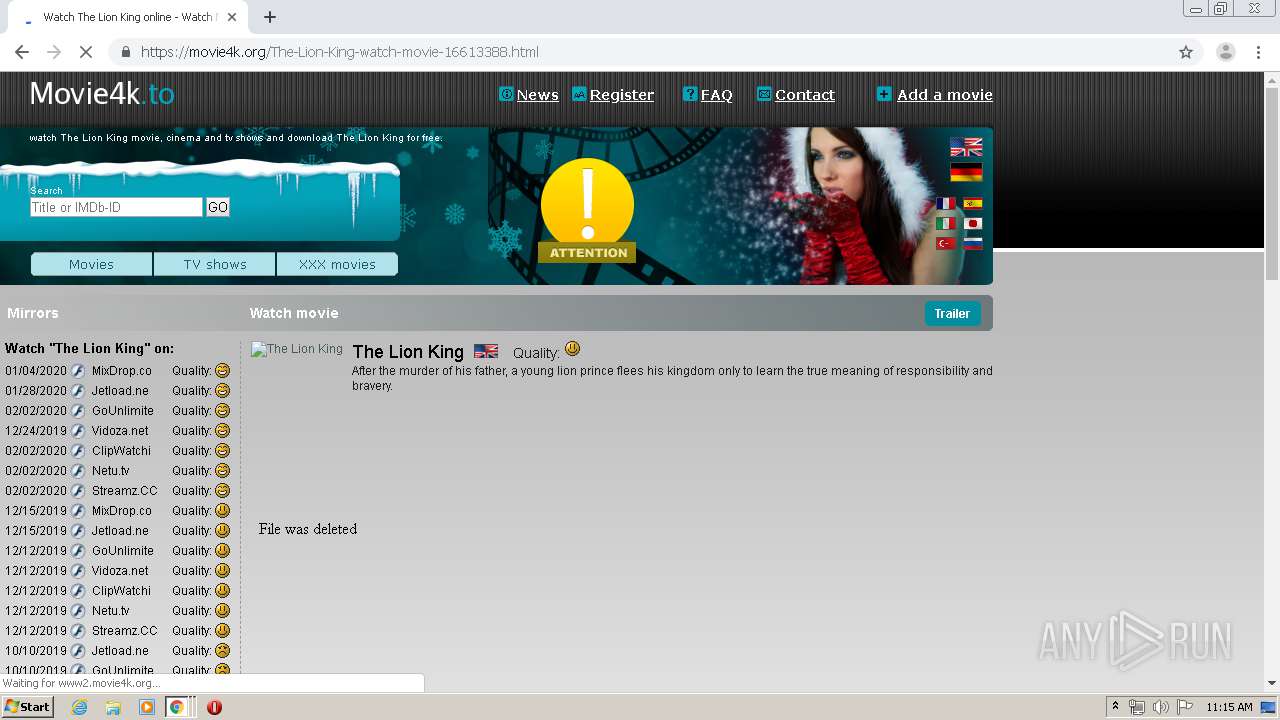
| URL: | http://movie4k.to |
| Full analysis: | https://app.any.run/tasks/5034c866-f1bd-46b4-a0de-3e3da713b0cc |
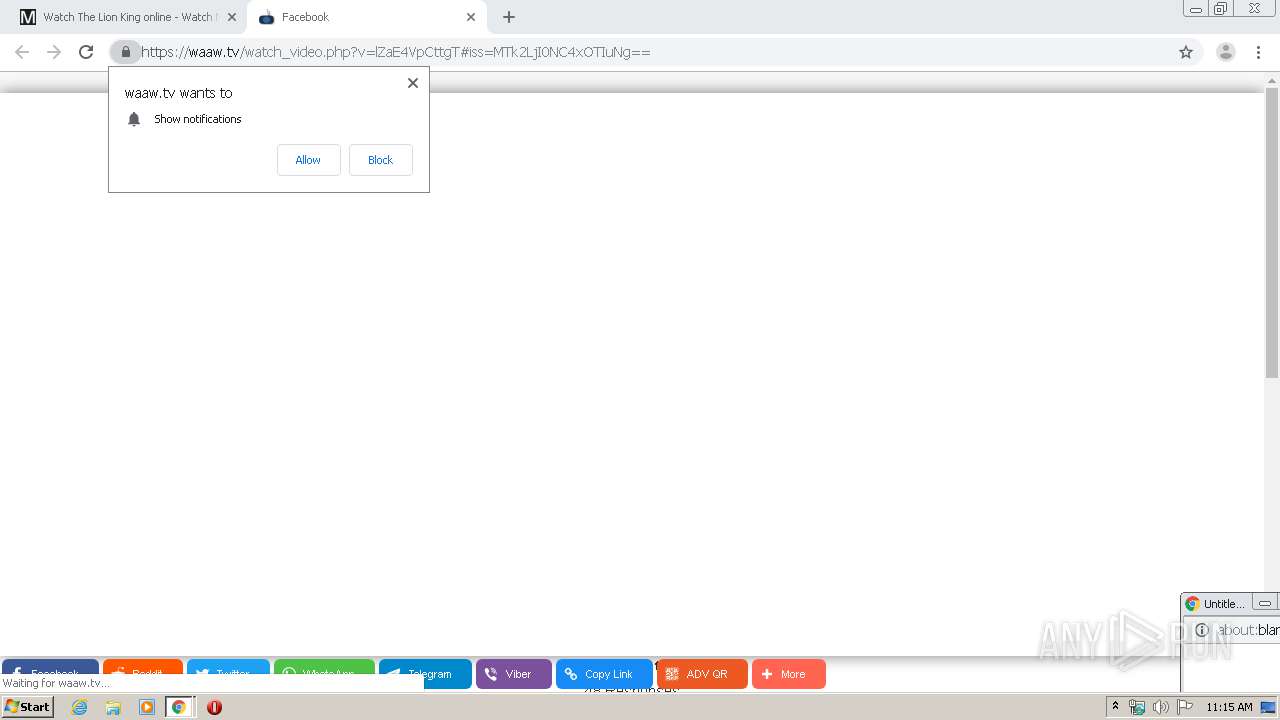
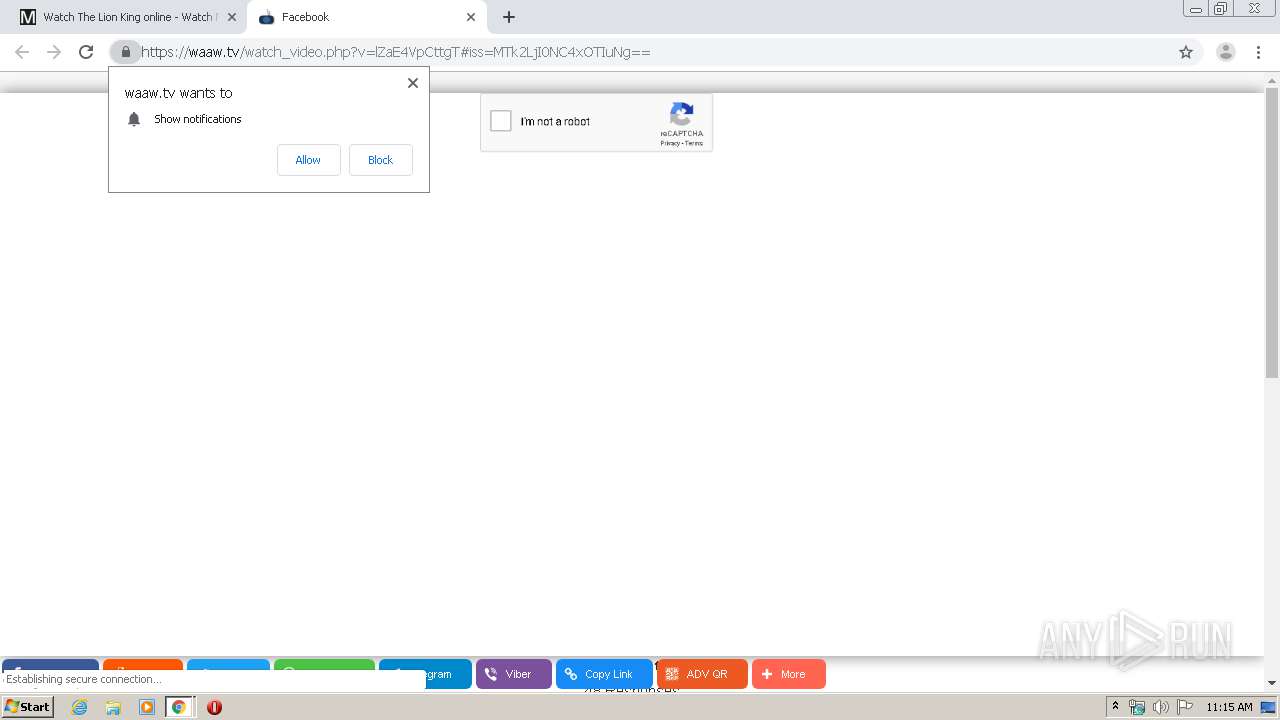
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2020, 11:14:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6E6B81AFB556C49E03607EE485AE20DA |
| SHA1: | 9DAD01995D235B1CF6053B16069C84AD38030D13 |
| SHA256: | 8336F54C151AD8545C9CA3E0C7732E6E9FC100DDC8510B78D73FCEF2432FC047 |
| SSDEEP: | 3:N1KTGWsn:Can |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2644)
INFO
Reads the hosts file
- chrome.exe (PID: 2644)
- chrome.exe (PID: 2496)
Application launched itself
- chrome.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
106
Monitored processes
70
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8869531842958416384 --renderer-client-id=54 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10380600514749259153 --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9773008247934733612 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3685082860636169679 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5712 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15287222577838839298 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8749052652262914363 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4332 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17993773230509943540 --mojo-platform-channel-handle=4316 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17808010946927930073 --mojo-platform-channel-handle=992 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6208394417636283598 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13008382472811860335 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
719
Read events
588
Write events
126
Delete events
5
Modification events
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2644-13225202106180875 |
Value: 259 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
211
Text files
225
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E3800BA-A54.pma | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ae956baa-28b2-417c-8687-71a54bb50628.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66bf1.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:AC43135B8C9FED46A92448C4E711F45C | SHA256:D840BA7CEBACF86DDBAD75BFB61A53449AA7AE3DE6B8ADC97FE45624626A6F09 | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66d87.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
204
DNS requests
112
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2496 | chrome.exe | GET | — | 104.18.32.63:80 | http://movie4k.to/ | US | — | — | whitelisted |
2496 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
2496 | chrome.exe | GET | 200 | 185.38.0.12:80 | http://r1---sn-4ox-ixae.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=196.244.192.6&mm=28&mn=sn-4ox-ixae&ms=nvh&mt=1580727957&mv=u&mvi=0&pl=24&shardbypass=yes | FI | crx | 862 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 185.38.0.12:80 | http://r1---sn-4ox-ixae.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=196.244.192.6&mm=28&mn=sn-4ox-ixae&ms=nvh&mt=1580727957&mv=u&mvi=0&pl=24&shardbypass=yes | FI | crx | 293 Kb | whitelisted |
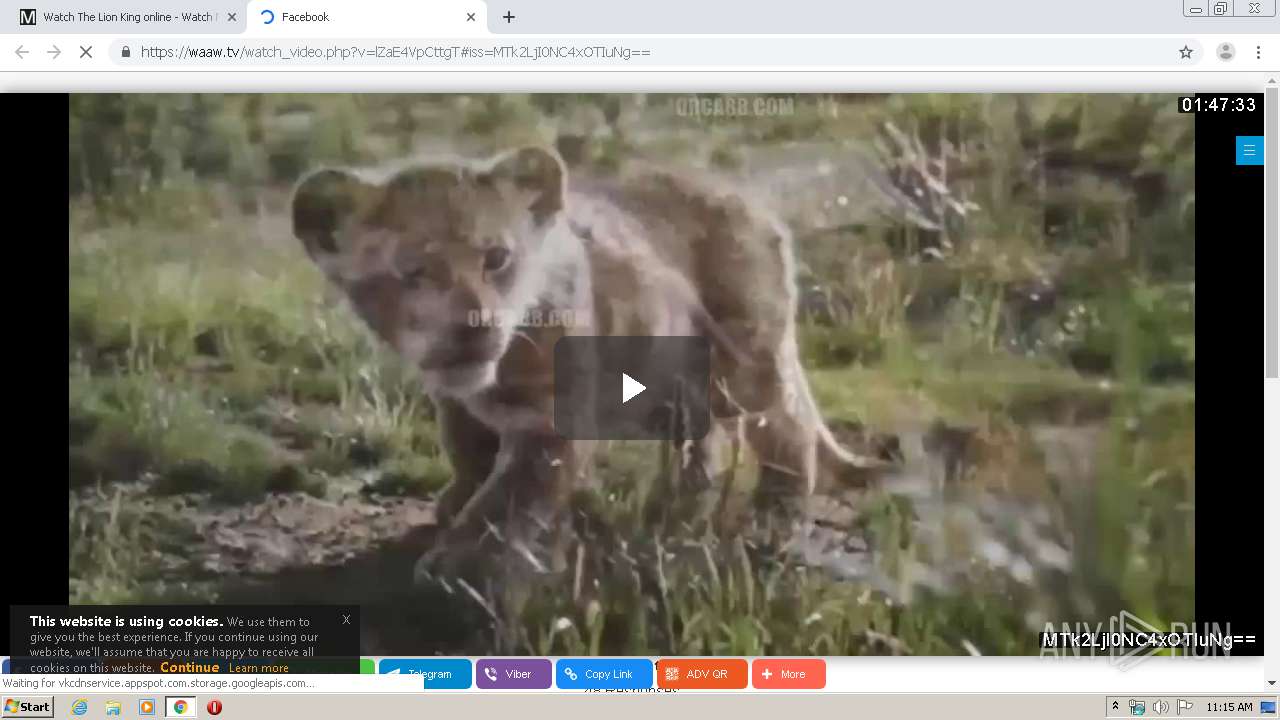
2496 | chrome.exe | GET | 200 | 198.143.165.222:80 | http://click.fasttrack.mobi/?utm_medium=119307414763139db150184789c1e9cdd2f6024c&utm_campaign=TB&1=87&cid=970e63zhqb4p26o57d | US | html | 1.25 Kb | suspicious |
2496 | chrome.exe | GET | 200 | 109.123.118.67:80 | http://track.bruceleadx2.com/ck.php?kp=lFI20CASF090dec0000RS002MZ0T3ZP03DSRR104UC03DSR00000000&line_item_id=19117&subid_spx=157851-bVfFnTCRr_pzatDj83hx | GB | html | 1.14 Kb | unknown |
2496 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2496 | chrome.exe | GET | 200 | 198.143.165.222:80 | http://click.fasttrack.mobi/?utm_term=6789177366024290471&clickverify=1&utm_content=fdc2c69a9cafac9c909b90a1909e96a589bbcdb9cbbfbc8c808482b1808482b5ba8bb9be8e8fbd8d8283ece0e8e3f7e6fbebfdb4eeedf5f0f3e1e991a797d3fa858c848ccea6828ecce3d2d5e6d5d0e5fafb9e98928c99fdf2c2f0c0c4cfc4f5fdf9f8c9cecfa8 | US | html | 2.95 Kb | suspicious |
2496 | chrome.exe | GET | 302 | 198.143.165.222:80 | http://click.fasttrack.mobi/proc.php?6b5d7ed92cd1ebe96b680039904e6925117d4a14 | US | compressed | 2.95 Kb | suspicious |
2496 | chrome.exe | GET | 200 | 35.208.56.33:80 | http://adexchangegate.com/script/s2iurl.php?csid=2663739&s1=222650_6gZ1Gv&md=0&stamat=m%7C%2C%2CAjPmojdvoGU3BU4GH0dEdHP3xP.ddc%2CbCXtBjQ7F1scyQbLRk11WsE0sBs6Ys_RQ7s-ER-5cfAVlSjcoPzoFI-LOiuK3mBV2ZwhZIMYlexEyGrA2P3Dj43TK-PG5FPbx51ophSyGIrOPOxzZLr-KbRjmm6aL-F1mwgfLcejhkBcTLmKvWE2_QQlnF1RqwAWM3_rLPbCfqIg39pPXrWJYp2lUw2G-DpZw1A8UmzCY_X3BiJTiw5F9SouRpP-tt2F7Cc22OV3r3HKlg33QfwR2GflAbOkDW8RpY6pJS89BhnXcO20FvSJduRhgbst0NZYvDV2KSce1hlY0rEmtK2Yg2VvVqfEhdokev6N8NZj5h8r0pb9EwWhELRoiKz9Y9G4SQC-V9Uss2teFCcVlwPAdXOZqjcDG7kNPdxRyBtWPyqT11cubVu08hU7ZuO74BsrQ_IAMzfApp4l9aWF_Hc8IgOCoG7fkfqK-xhIkjdQTckktIaK9LkMnK1A8ene9kQiW4Px7E6Og5ECVqX5hpH1wd5-figSgbKEiCbjlnGNiLo7CWzmg9LOFdrTmZQvkF--ipYVlSX1LOfc4PlMuLSwgdIK5bAX7V8w1LGNDF0WGhE1LmEN4jZeYudm6G9Uf_Y3JRBOs4ZBmxI9Vimmy5TAhXguoZ0LcbEiTsyAW_9Fs1Qq3Et5pT8UQRFQIOgE2LGBJY0zl4g2wt6UrnAqxIm4nMt2sj3RQSx0l_Apfw_OFZGHcZMWRacV_mna_L6aRH64FcdYOWS6-7k2dp9RhqVFnK1KBjE6QfawQLADsPIH0A2PLE6c08TKbjCaXmaNx-UX24K3wynl2nRgdw3P79TGBnujpEr-S8uT2ZM_LBwNwsMlyGbvYMWeQht8RPIue08V3J0kl9nWCW6moabWz8bC9PMlS5Is8M3cd_05-zjqS8ucsg4uz11-IWRjw9tHcA61m5mUiGhnYSlhP-jcyBaXsL0ODsU8dU5Q4K98PDA5wkSKltwdS3qo0DX6g5IwMtvDNlHSQ8VEgv85U1_UqkBiBMR-CkOfbrSsF8_Bc_VX2S-mGGU04klYf5-H3ygq4KdKeL3g2CIMNLNoQPFTpVF5AqlfAWzPraYadcoZH-7Xc0a5h-hq74jtobXxDFhHYt4hnC_Izj5vrow3muuDMUy5VjK3yA_Vx-4Yng8wnni2HjR6Qzm2yt77RZy9GlWEgl-lEzZI-SfWWaNB9TqIFThls0Lzuan-eo7F6kYFa2VRTOym9ljc6FVyuFDtv5Ek4fcUC_eViz2XyUo%2C | US | — | 2.45 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2496 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
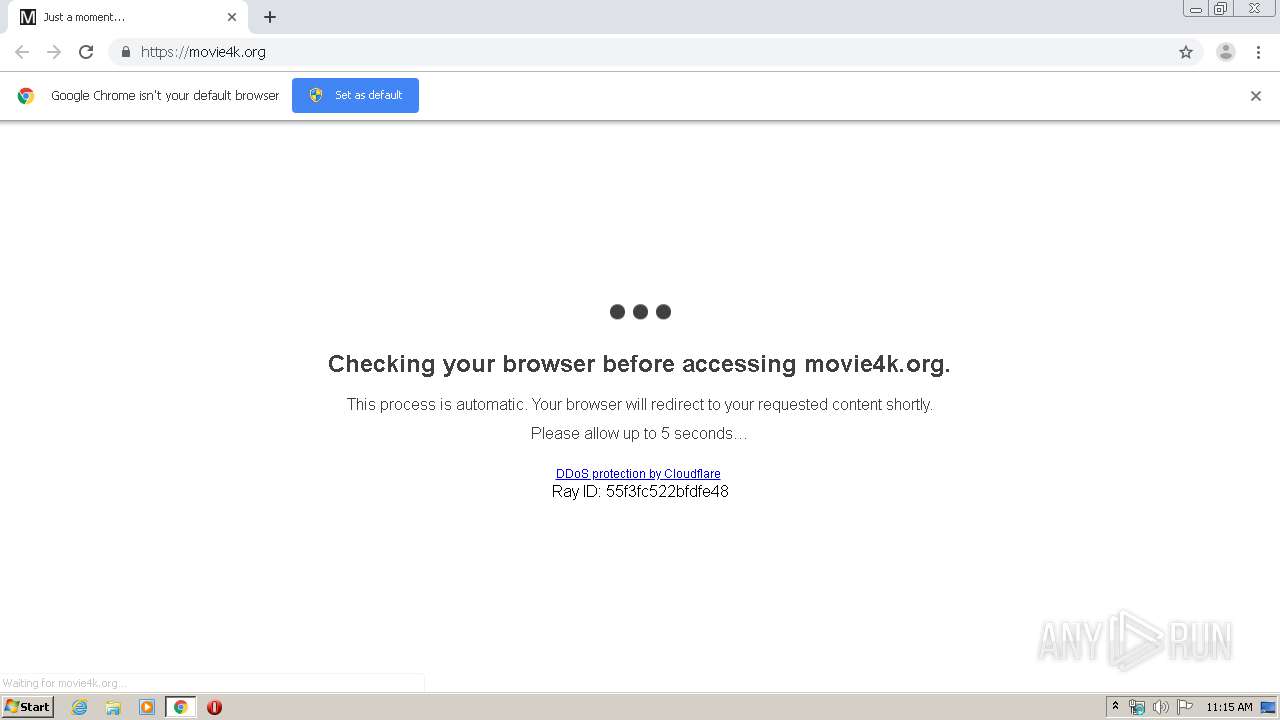
2496 | chrome.exe | 104.31.16.3:443 | movie4k.org | Cloudflare Inc | US | shared |
2496 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.21.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 216.58.210.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 185.38.0.12:80 | r1---sn-4ox-ixae.gvt1.com | FNE-Finland Ltd | FI | whitelisted |
2496 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.22.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 213.174.153.229:443 | fadsecz.com | DataWeb Global Group B.V. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
movie4k.to |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
derfueller.com |
| suspicious |
www.cloudflare.com |
| whitelisted |
movie4k.org |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-4ox-ixae.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
2496 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2496 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2496 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2496 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2496 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2496 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2496 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2496 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2496 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |