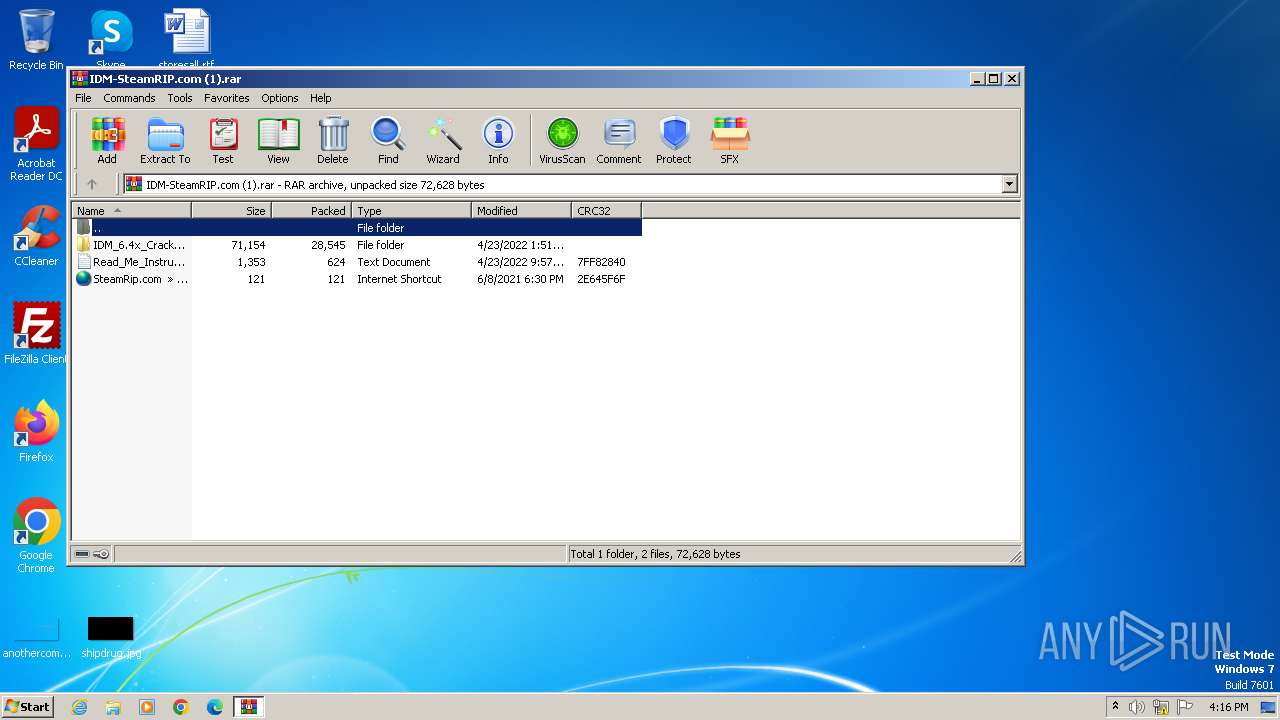
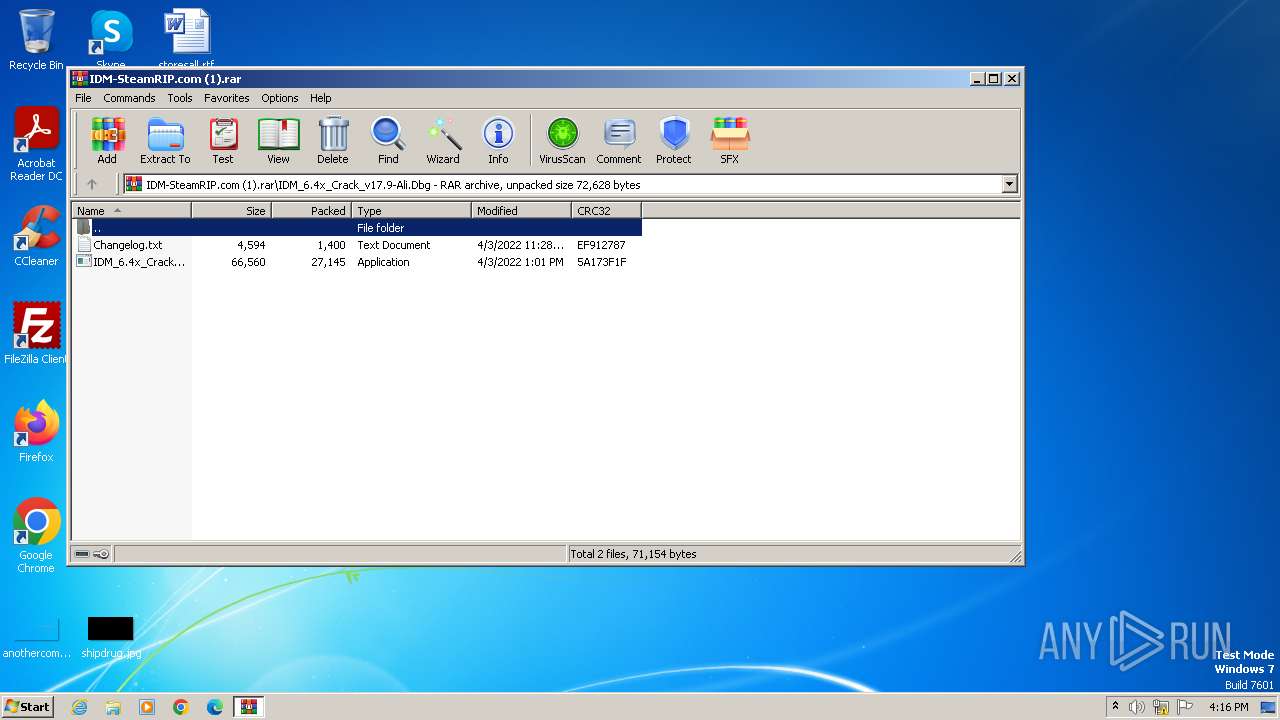
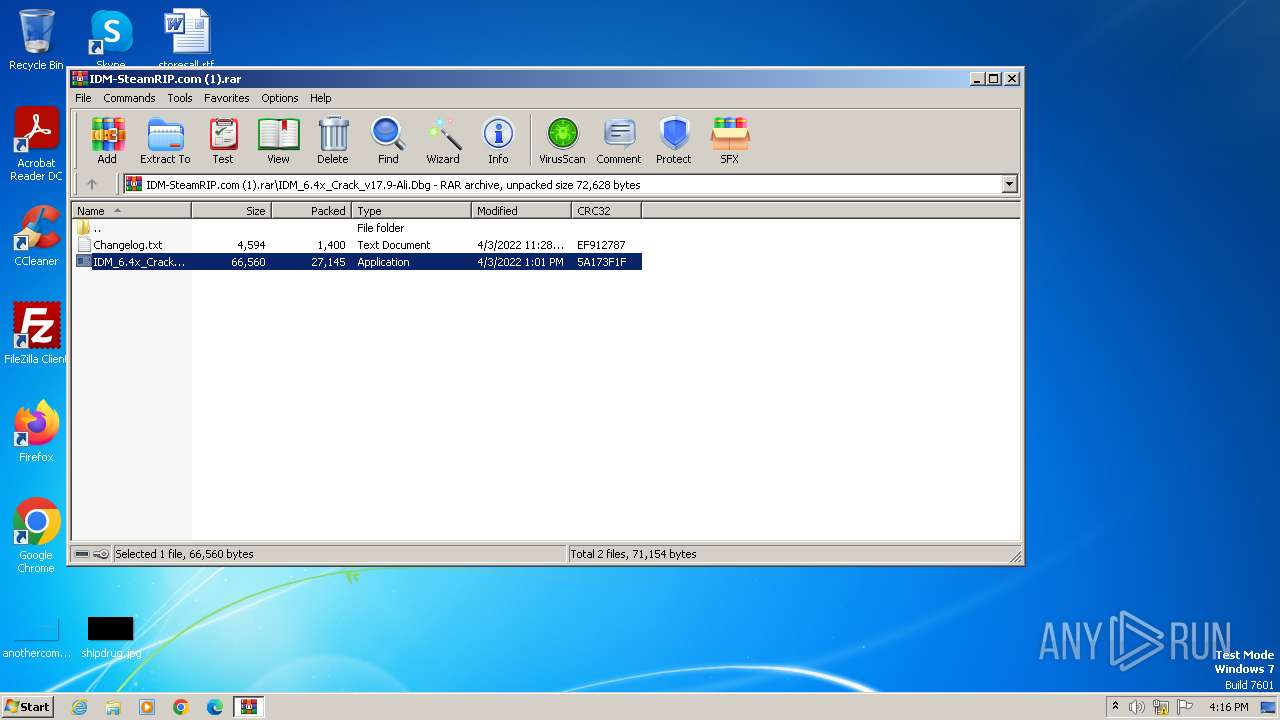
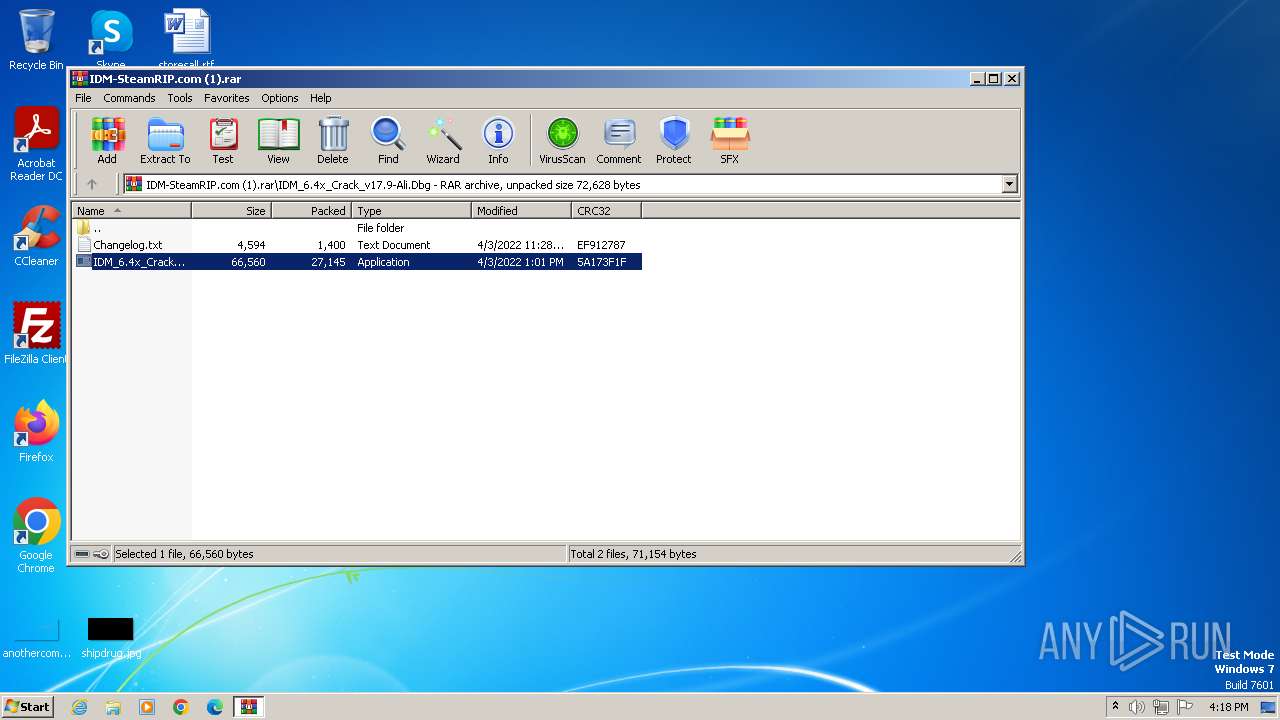
| File name: | IDM-SteamRIP.com (1).rar |
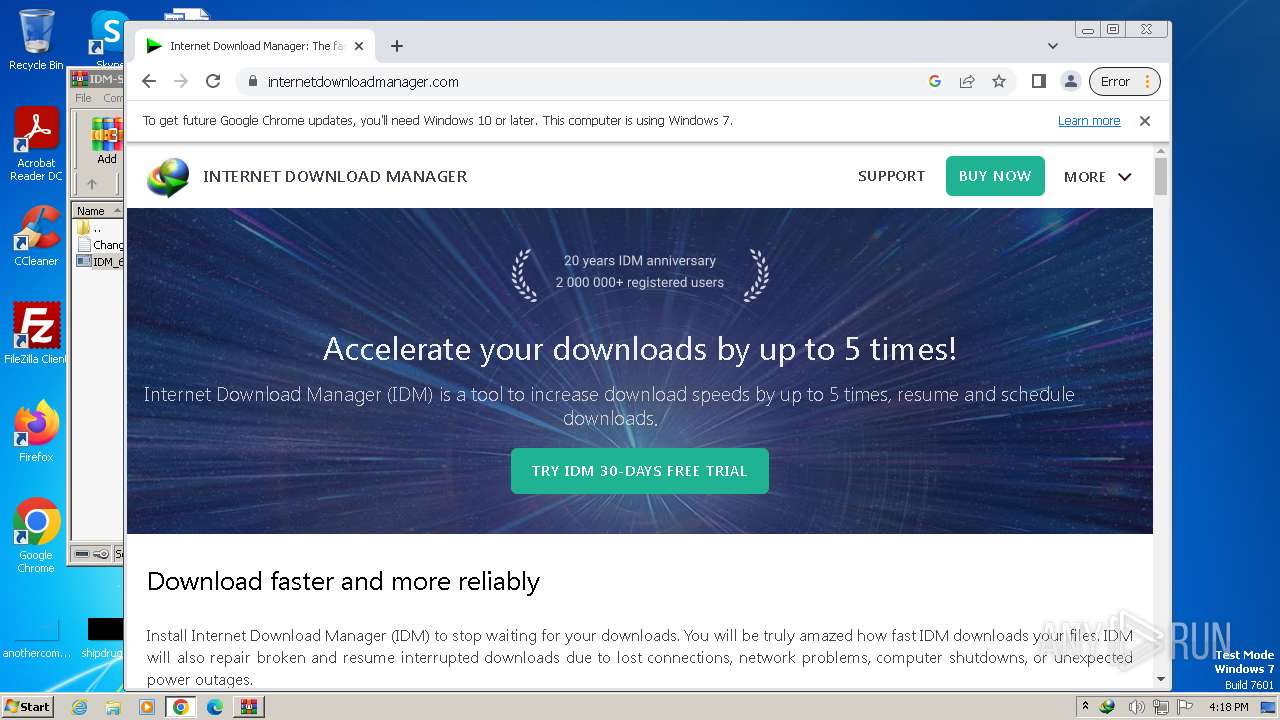
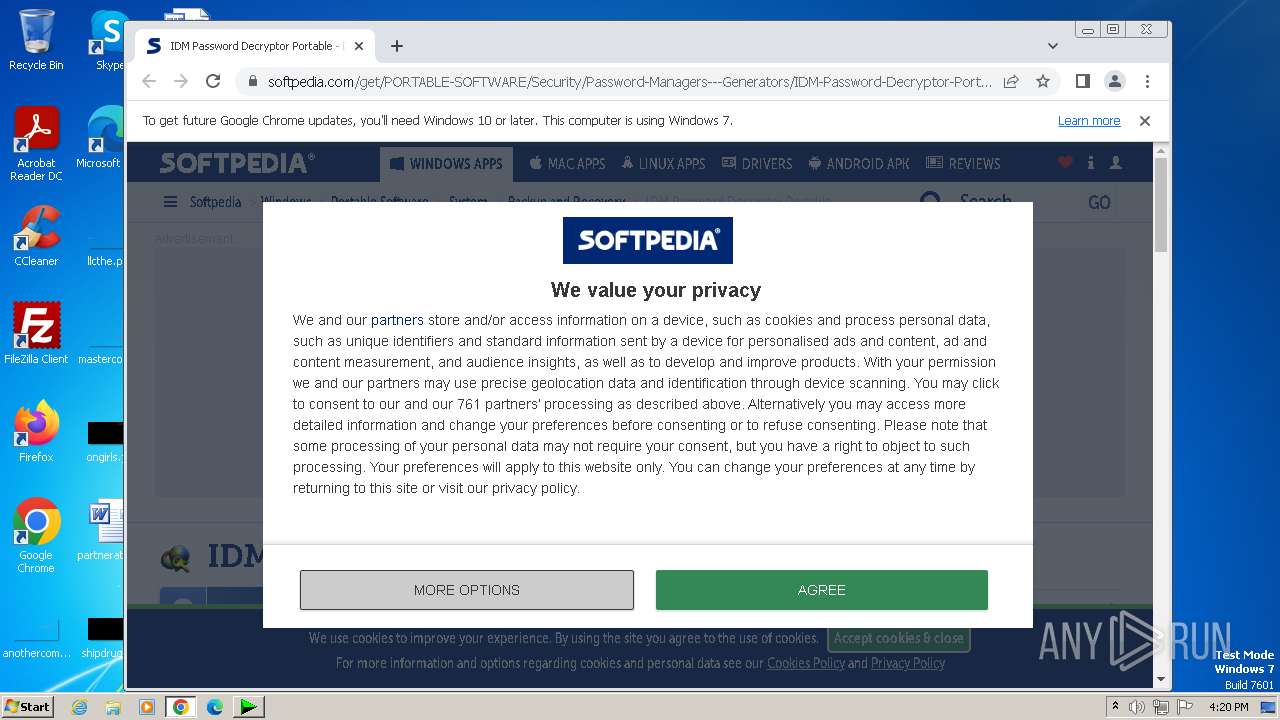
| Full analysis: | https://app.any.run/tasks/f81a1d08-4cae-4bd4-8571-c986bb76311c |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2023, 16:16:30 |
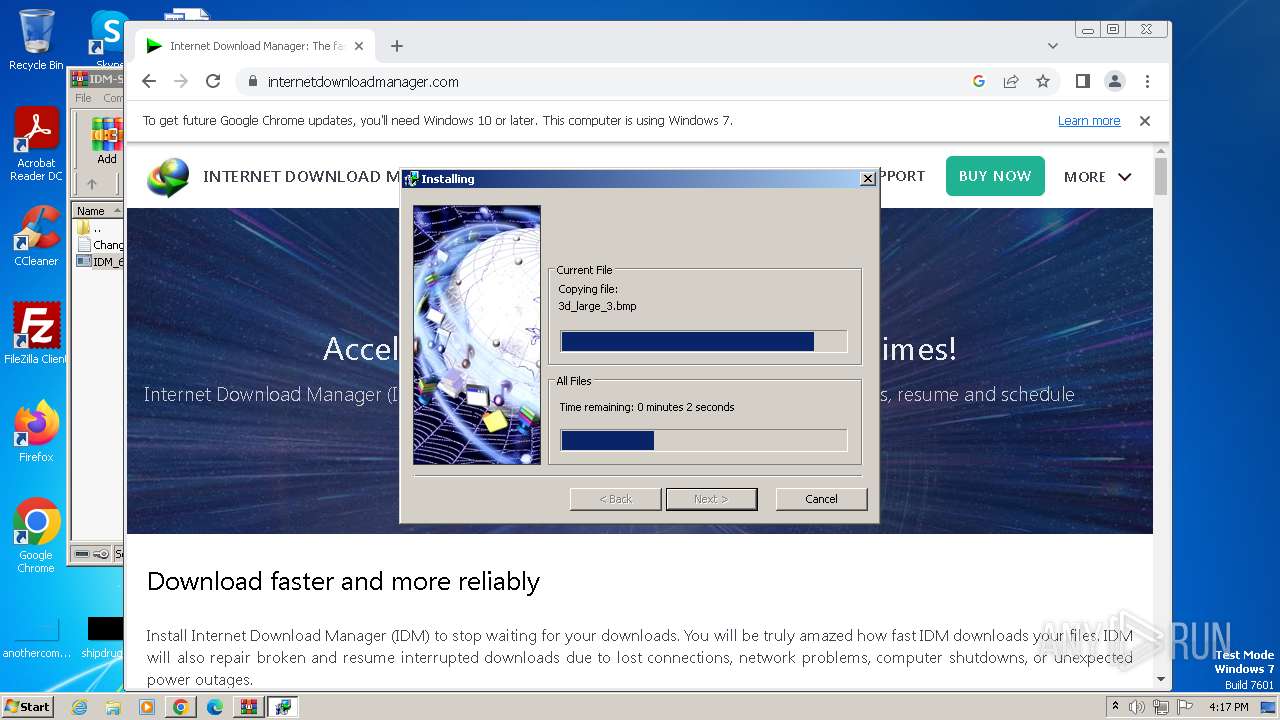
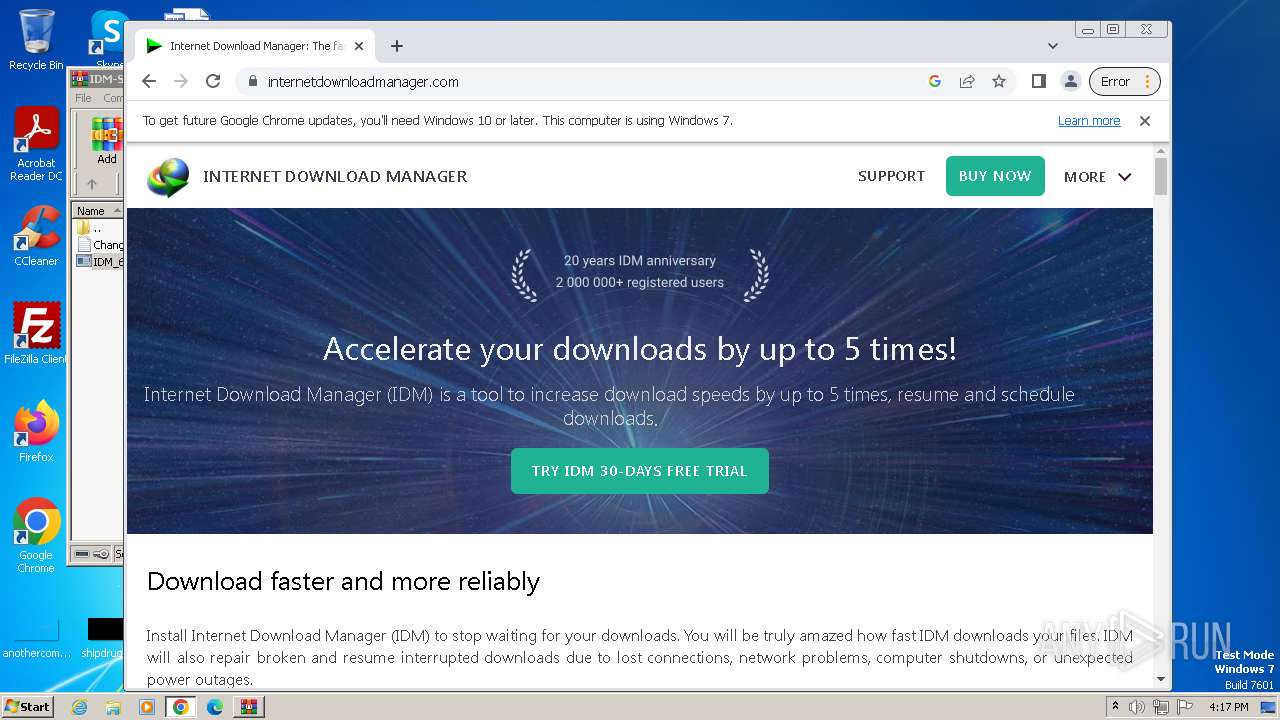
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
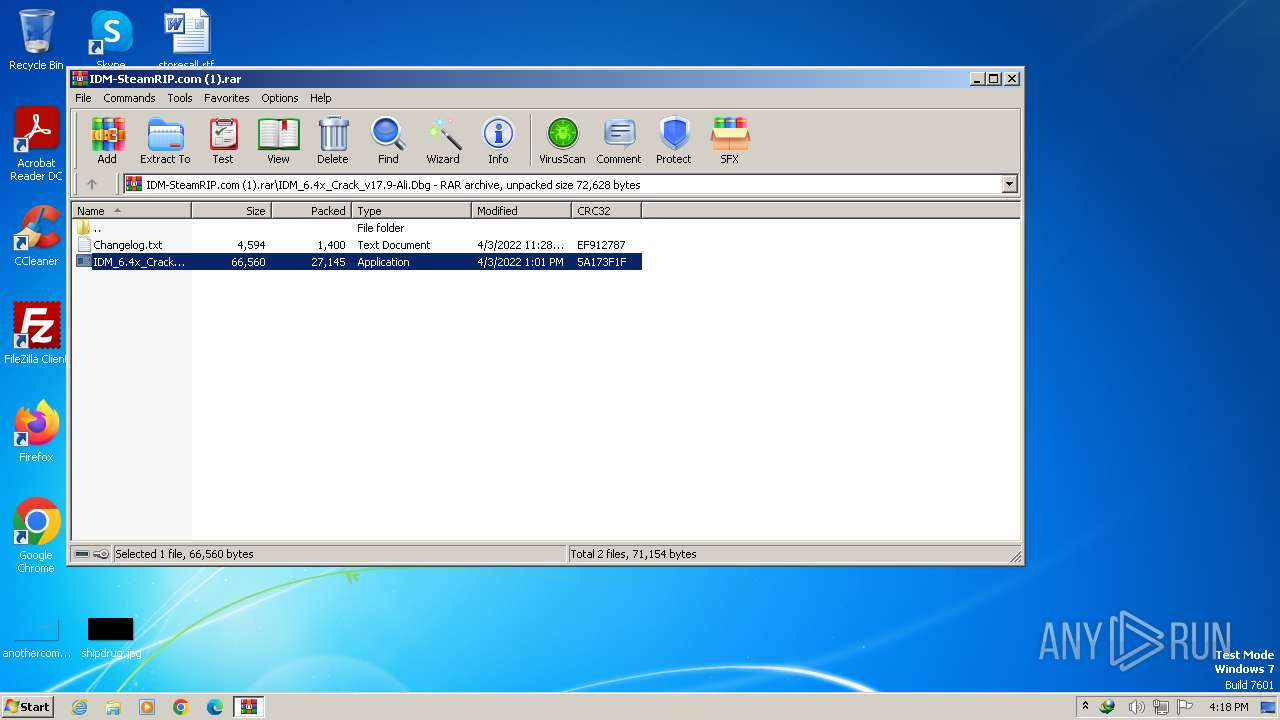
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 3FA47F957836610C818220FE018CBC75 |
| SHA1: | 69AFCB980B7CAC7C1F067C3DC72406F716E28763 |
| SHA256: | 8325DBAD7CF07A439F94B57C2A871B1D73754DE03A17604166AC9D56589FEB9D |
| SSDEEP: | 1536:n+e159Jb0/52C4HXfNfSXWcSOysjXS7r2L+:v15jQAC4HXdSmYysjiW+ |
MALICIOUS
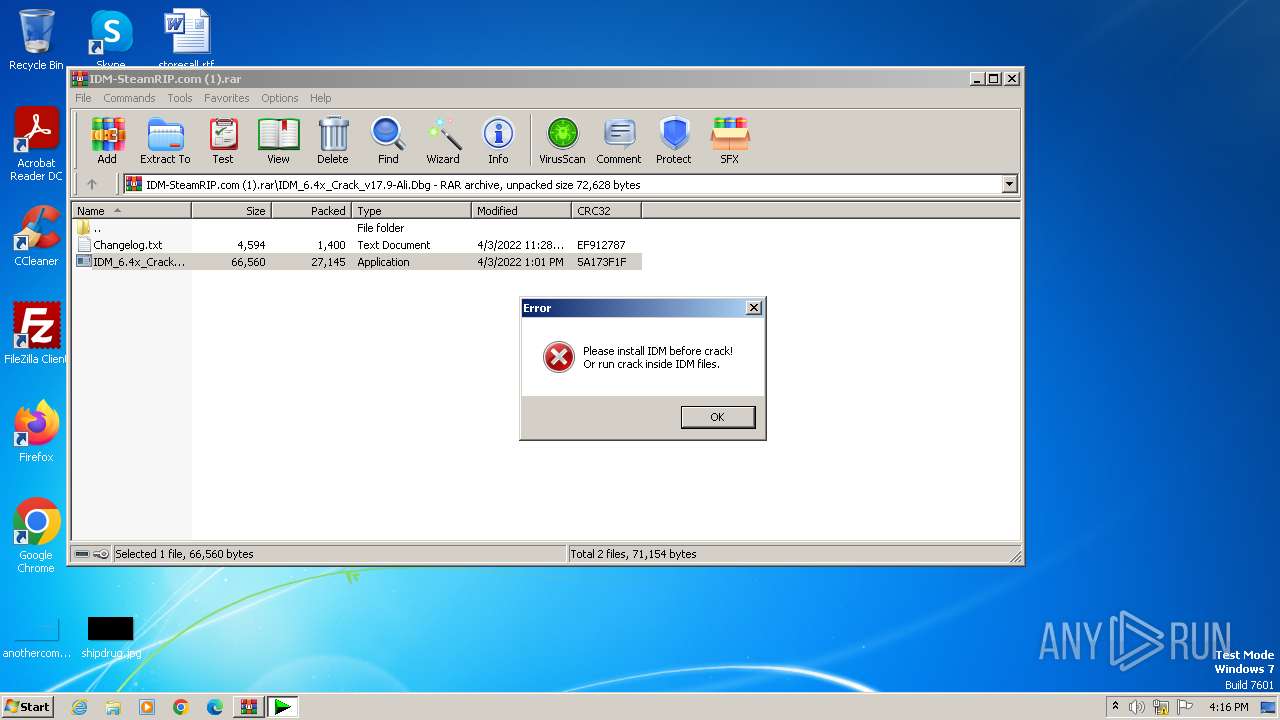
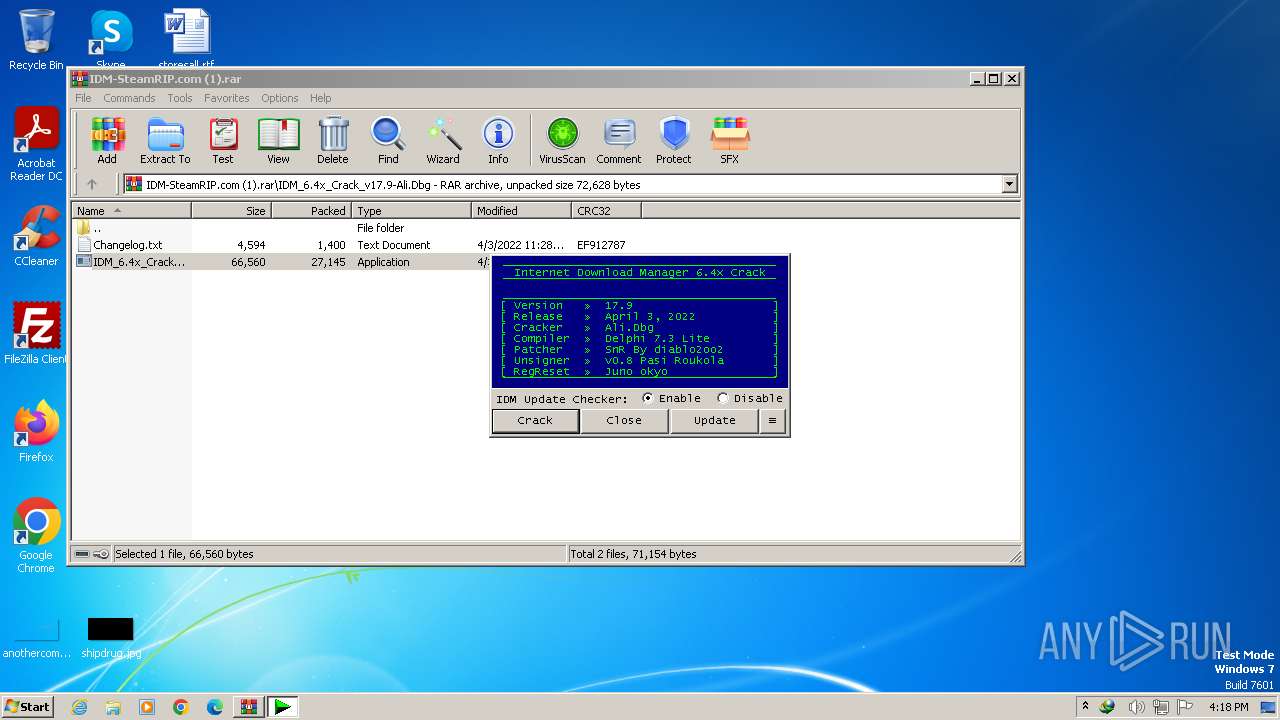
Drops the executable file immediately after the start
- IDMan.exe (PID: 3236)
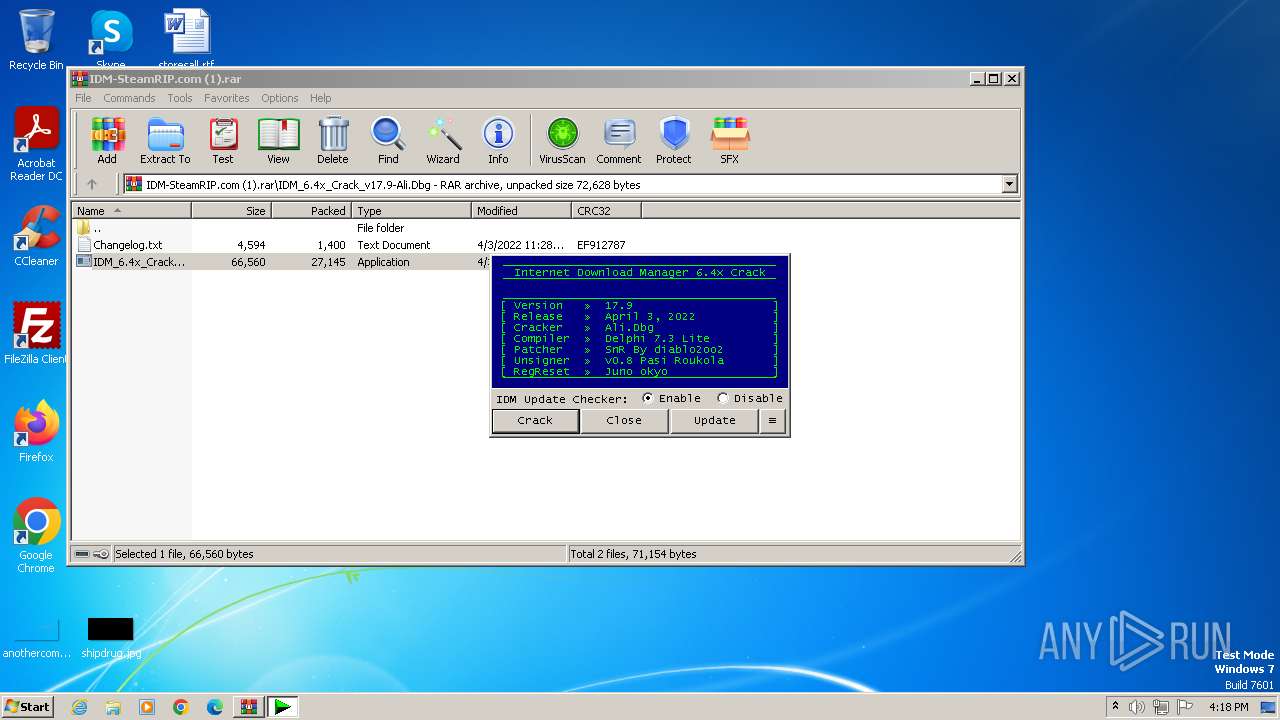
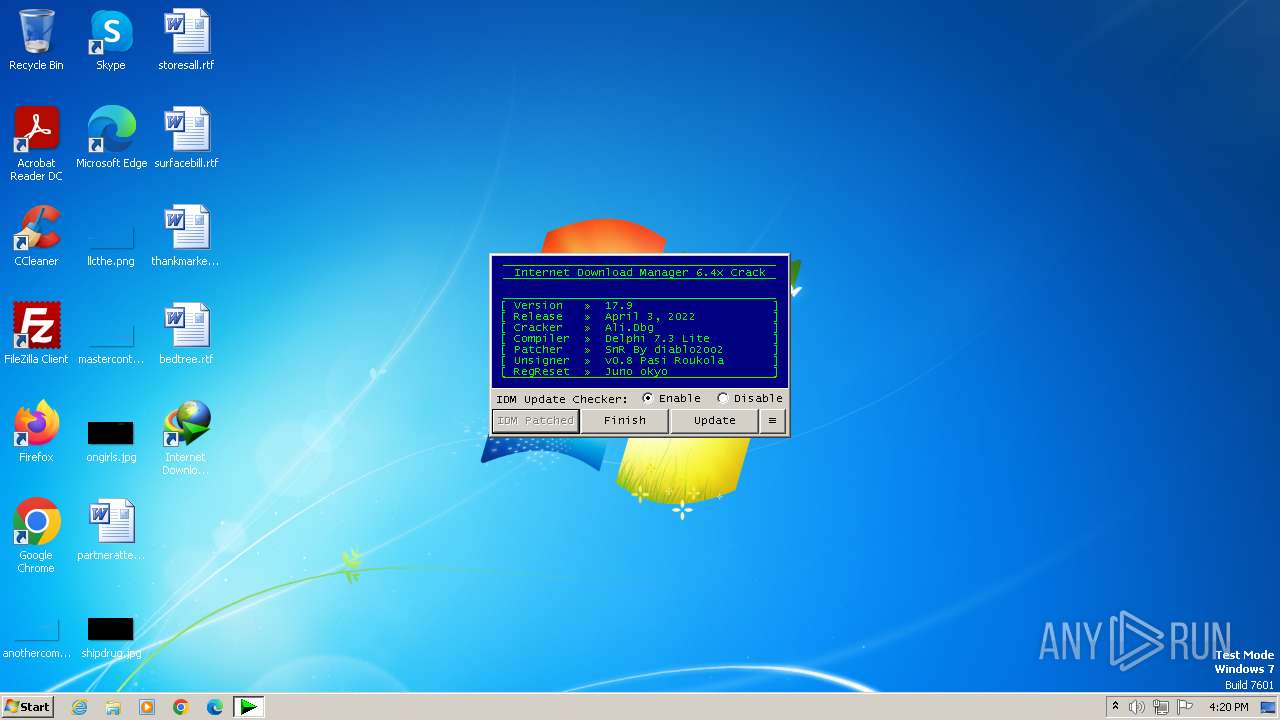
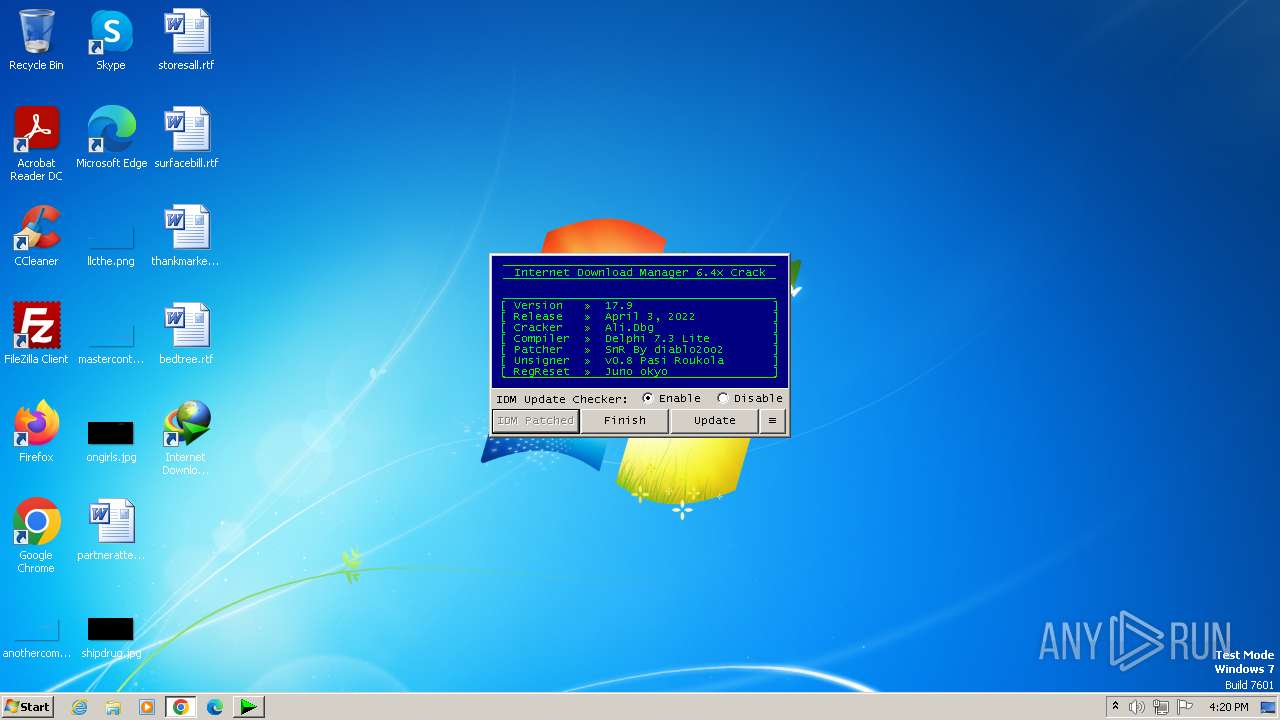
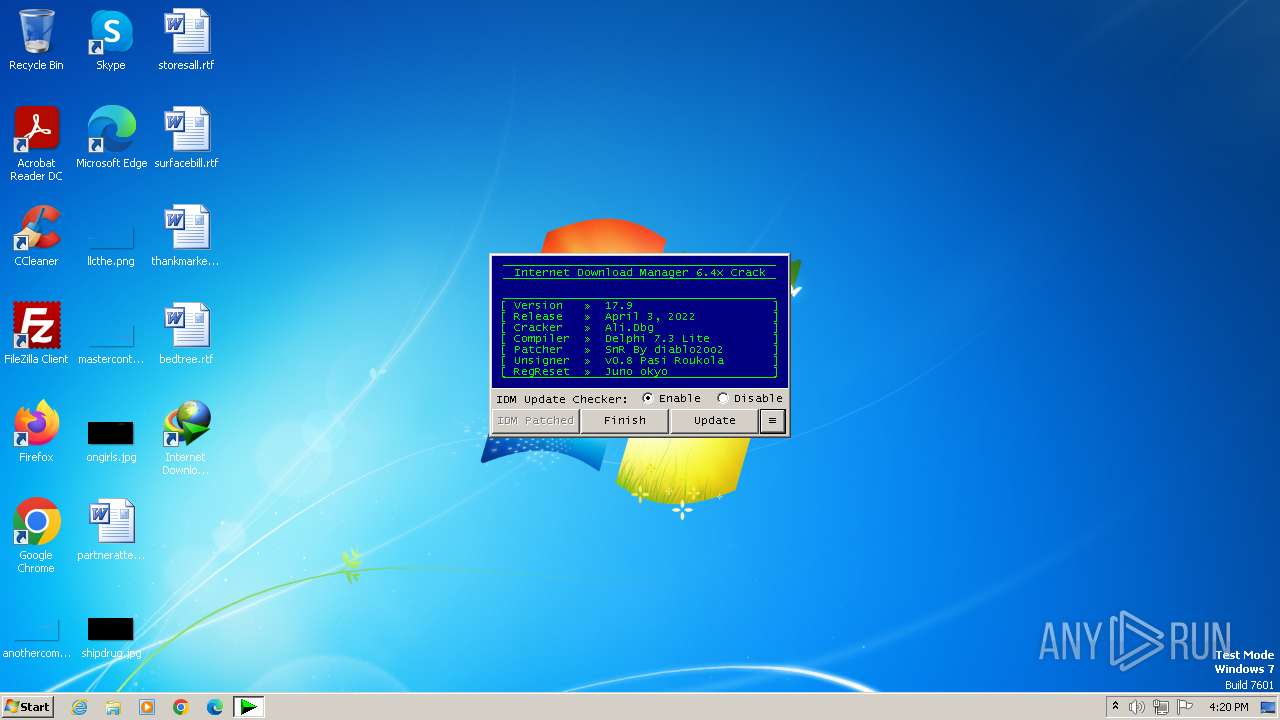
- IDM_6.4x_Crack_v17.9.exe (PID: 3592)
- wscript.exe (PID: 2864)
- UnSigner.exe (PID: 3196)
Creates a writable file in the system directory
- rundll32.exe (PID: 3988)
Starts NET.EXE for service management
- Uninstall.exe (PID: 2132)
- net.exe (PID: 1856)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 2864)
- wscript.exe (PID: 3516)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 2864)
- wscript.exe (PID: 3516)
- wscript.exe (PID: 3776)
Deletes a file (SCRIPT)
- wscript.exe (PID: 2864)
- wscript.exe (PID: 3516)
- wscript.exe (PID: 3776)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 2864)
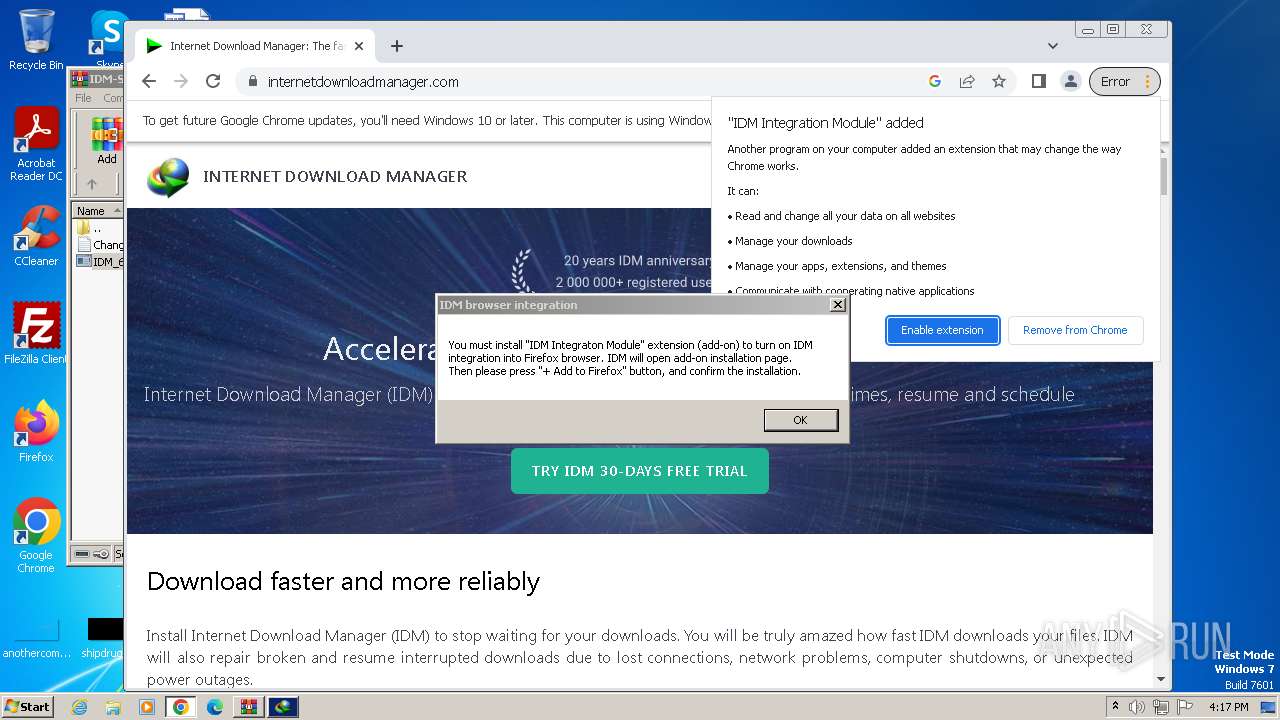
Actions looks like stealing of personal data
- IDMan.exe (PID: 3192)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3776)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3776)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3776)
Unusual connection from system programs
- wscript.exe (PID: 3776)
SUSPICIOUS
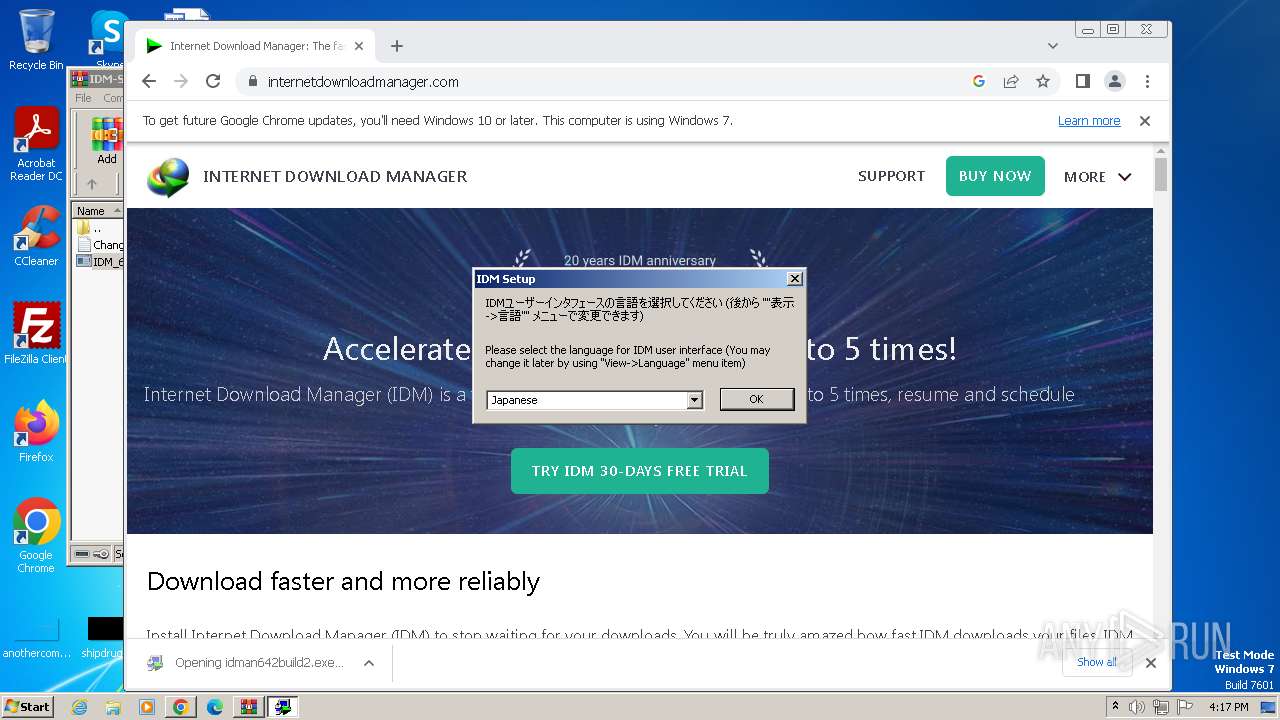
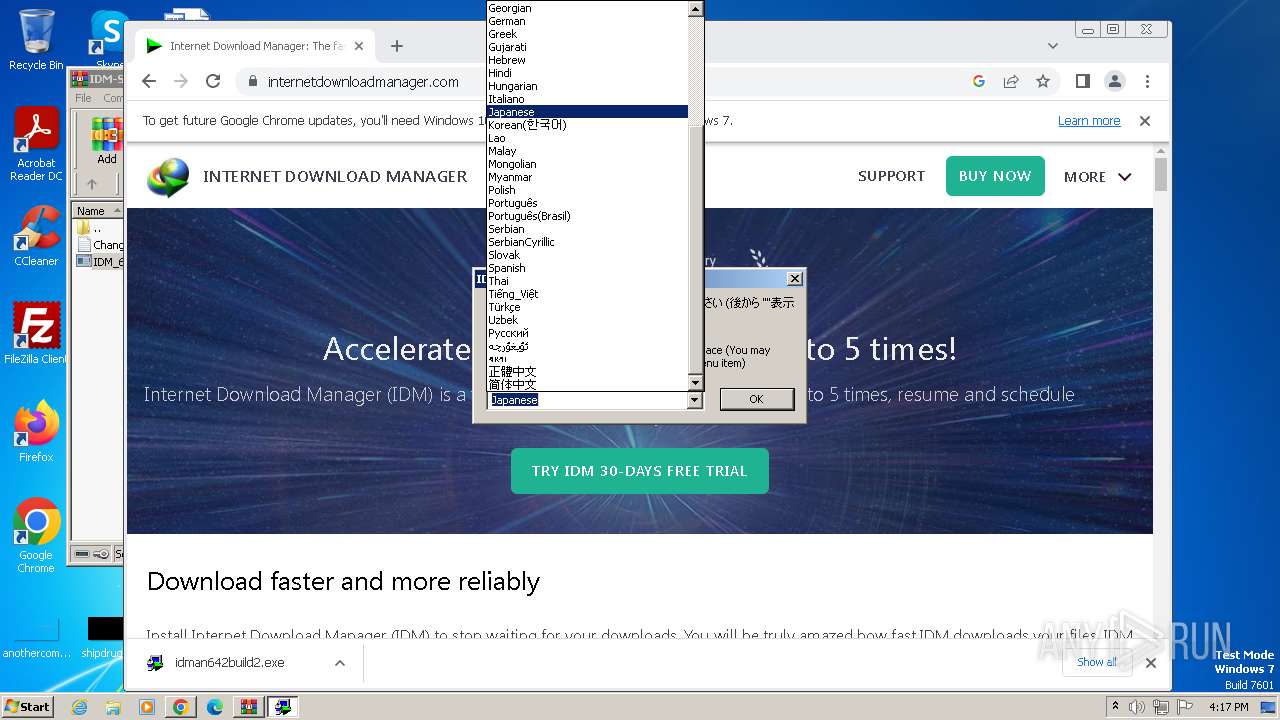
Starts application with an unusual extension
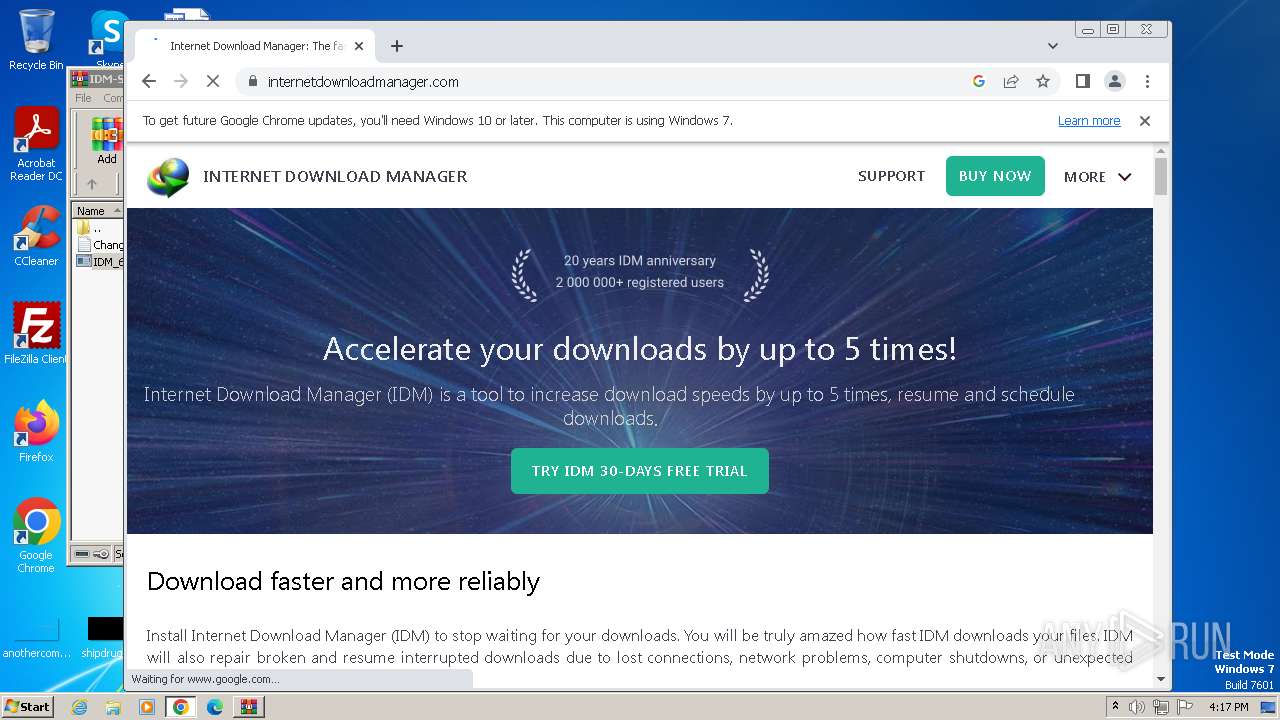
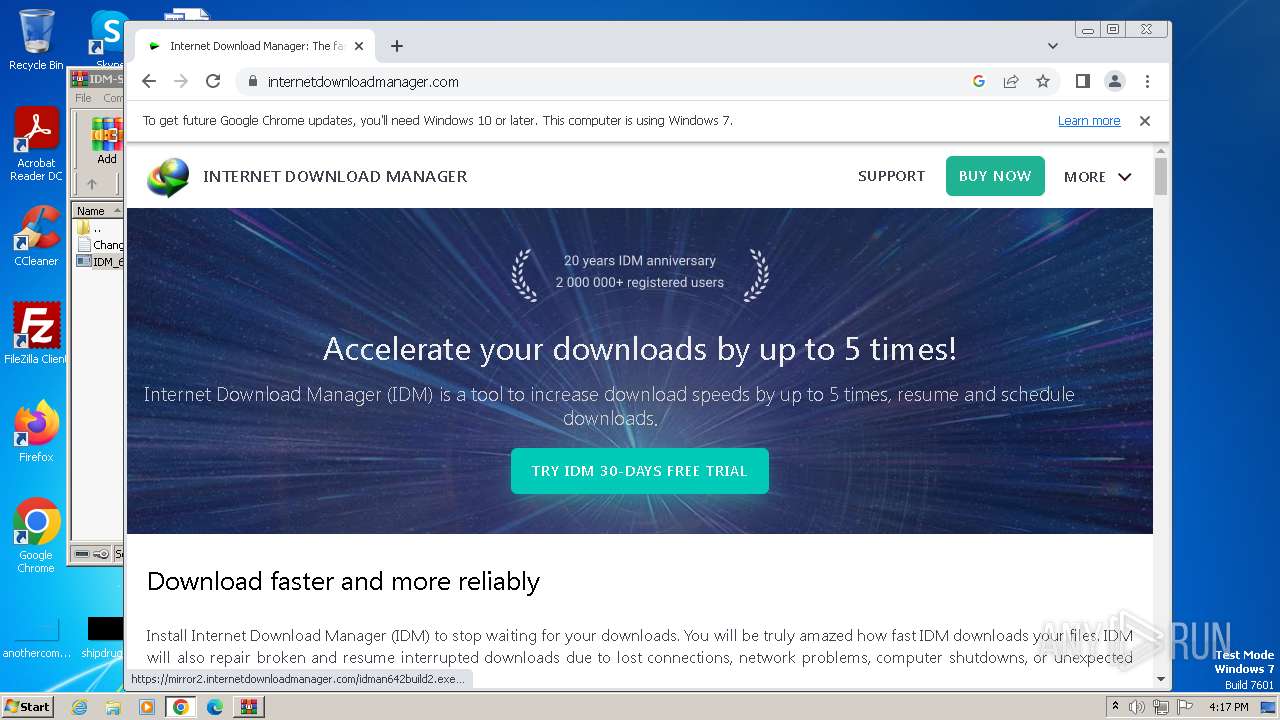
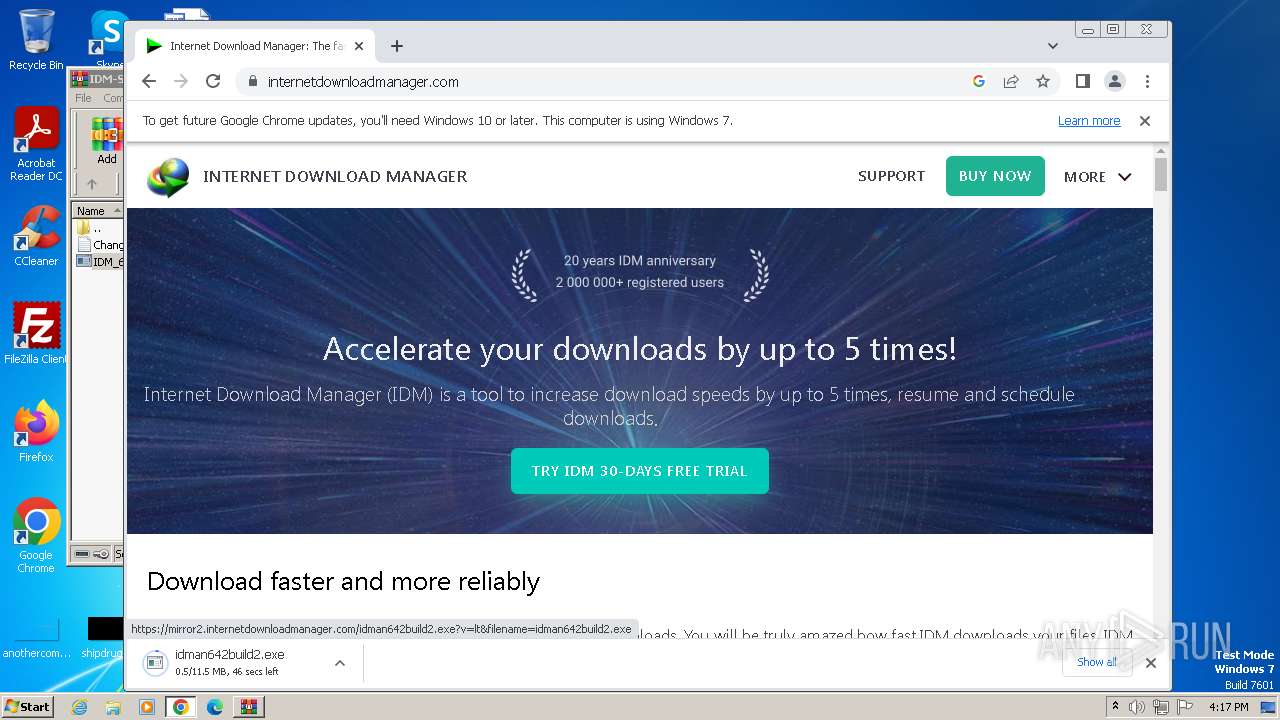
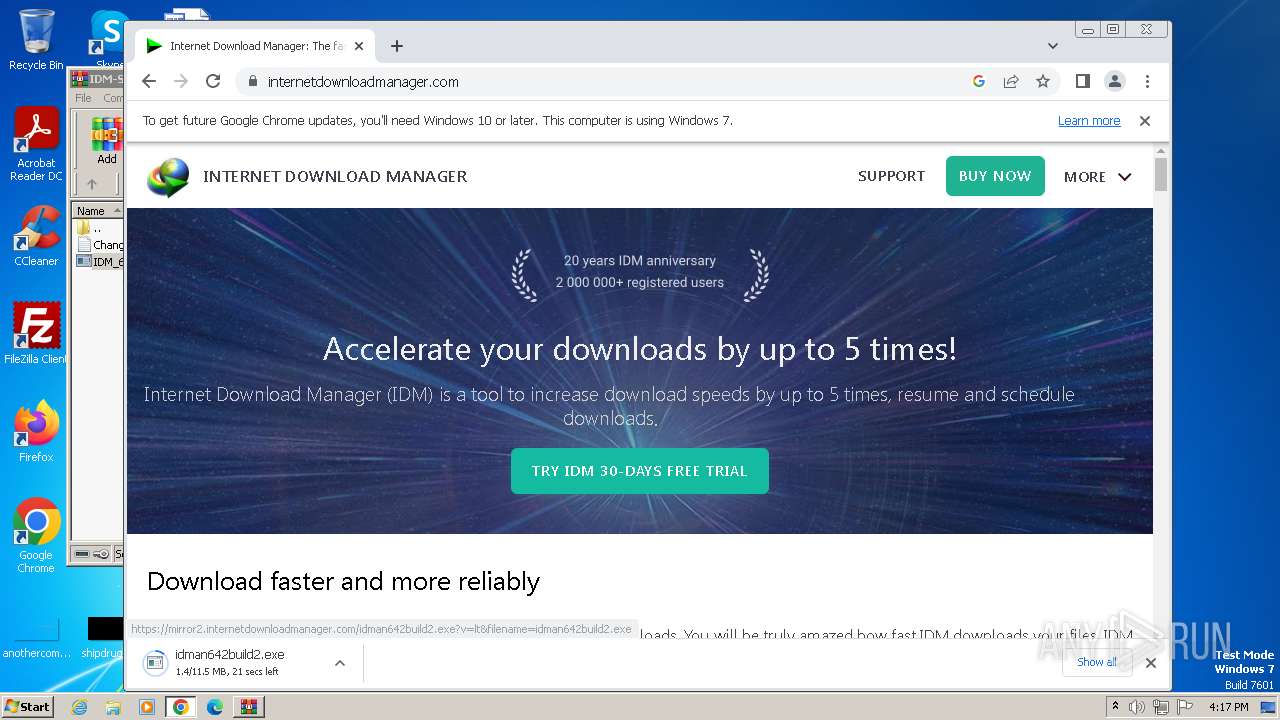
- idman642build2.exe (PID: 3912)
The process creates files with name similar to system file names
- IDM1.tmp (PID: 2900)
Reads the Internet Settings
- IDM1.tmp (PID: 2900)
- IDMan.exe (PID: 3236)
- Uninstall.exe (PID: 2132)
- runonce.exe (PID: 3320)
- IDMan.exe (PID: 3192)
- IDM_6.4x_Crack_v17.9.exe (PID: 3572)
- wscript.exe (PID: 3776)
Checks Windows Trust Settings
- IDMan.exe (PID: 3236)
- IDMan.exe (PID: 3192)
Reads security settings of Internet Explorer
- IDMan.exe (PID: 3236)
- IDMan.exe (PID: 3192)
Reads settings of System Certificates
- IDMan.exe (PID: 3236)
- IDMan.exe (PID: 3192)
Creates/Modifies COM task schedule object
- IDMan.exe (PID: 3236)
- Uninstall.exe (PID: 2132)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 2132)
Drops a system driver (possible attempt to evade defenses)
- rundll32.exe (PID: 3988)
Creates or modifies Windows services
- Uninstall.exe (PID: 2132)
Searches for installed software
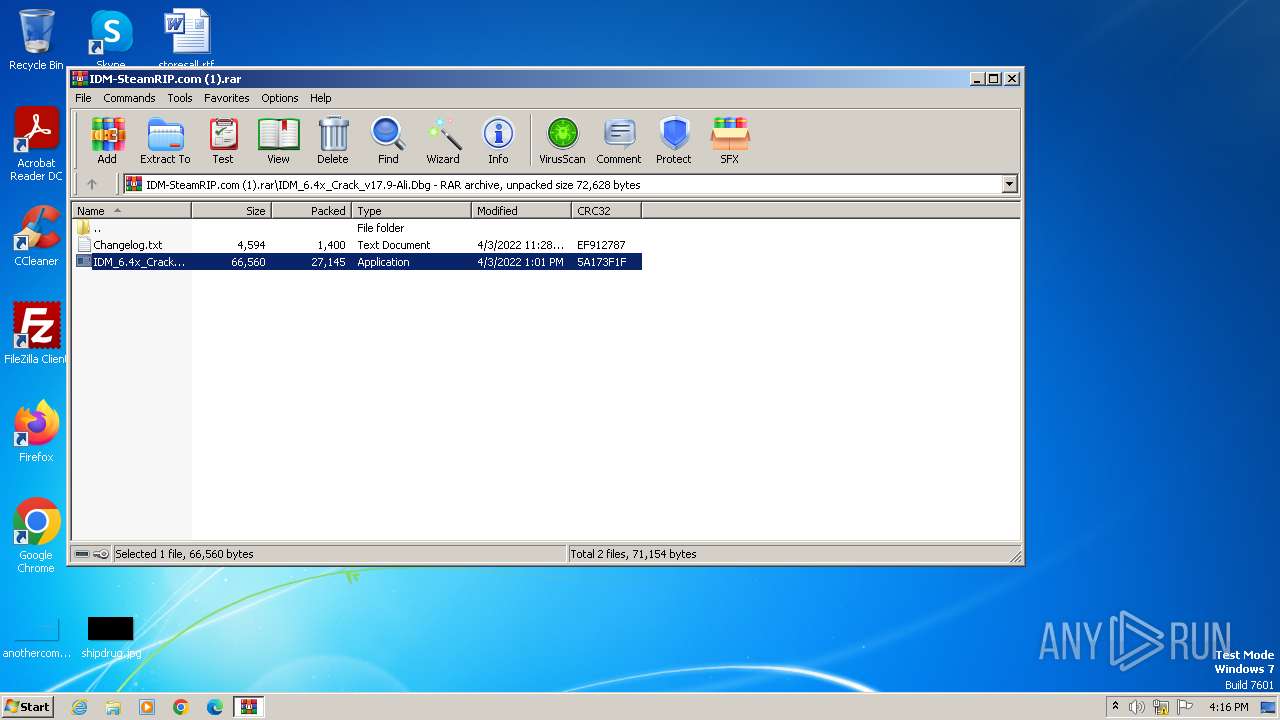
- IDM_6.4x_Crack_v17.9.exe (PID: 3592)
- IDM_6.4x_Crack_v17.9.exe (PID: 3572)
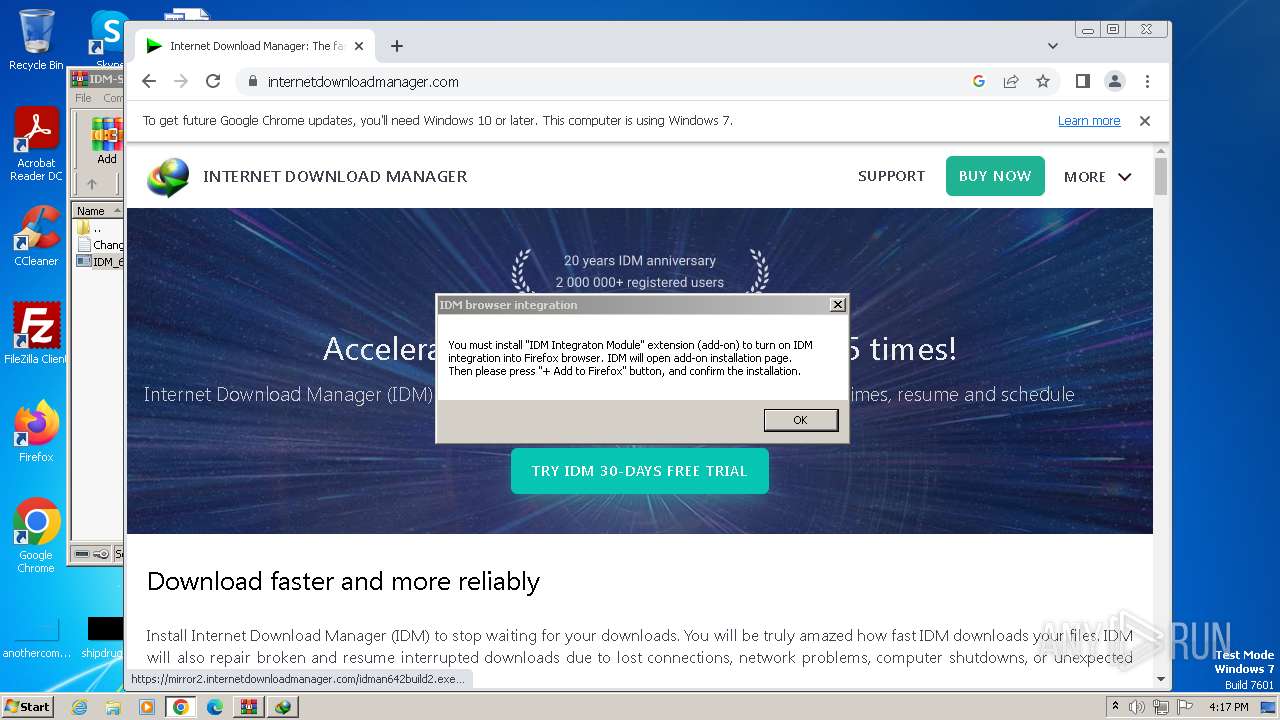
The process executes VB scripts
- IDM_6.4x_Crack_v17.9.exe (PID: 3592)
- IDM_6.4x_Crack_v17.9.exe (PID: 3572)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2864)
- wscript.exe (PID: 3516)
- wscript.exe (PID: 3776)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 2864)
- wscript.exe (PID: 3516)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2864)
- wscript.exe (PID: 3516)
- wscript.exe (PID: 3776)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v17.9.exe (PID: 3572)
Uses TASKKILL.EXE to kill process
- IDM_6.4x_Crack_v17.9.exe (PID: 3572)
Requests information from PasteBin
- wscript.exe (PID: 3776)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 3776)
INFO
Drops the executable file immediately after the start
- WinRAR.exe (PID: 888)
- chrome.exe (PID: 924)
- chrome.exe (PID: 3380)
- rundll32.exe (PID: 3988)
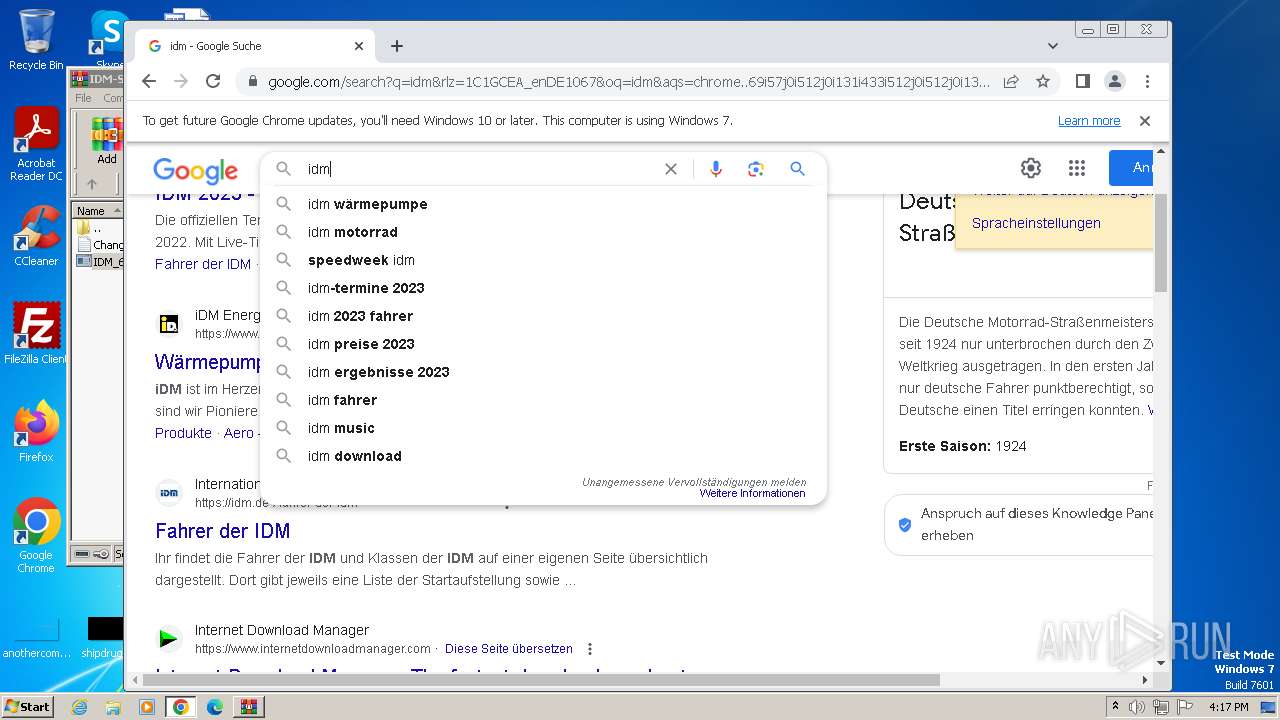
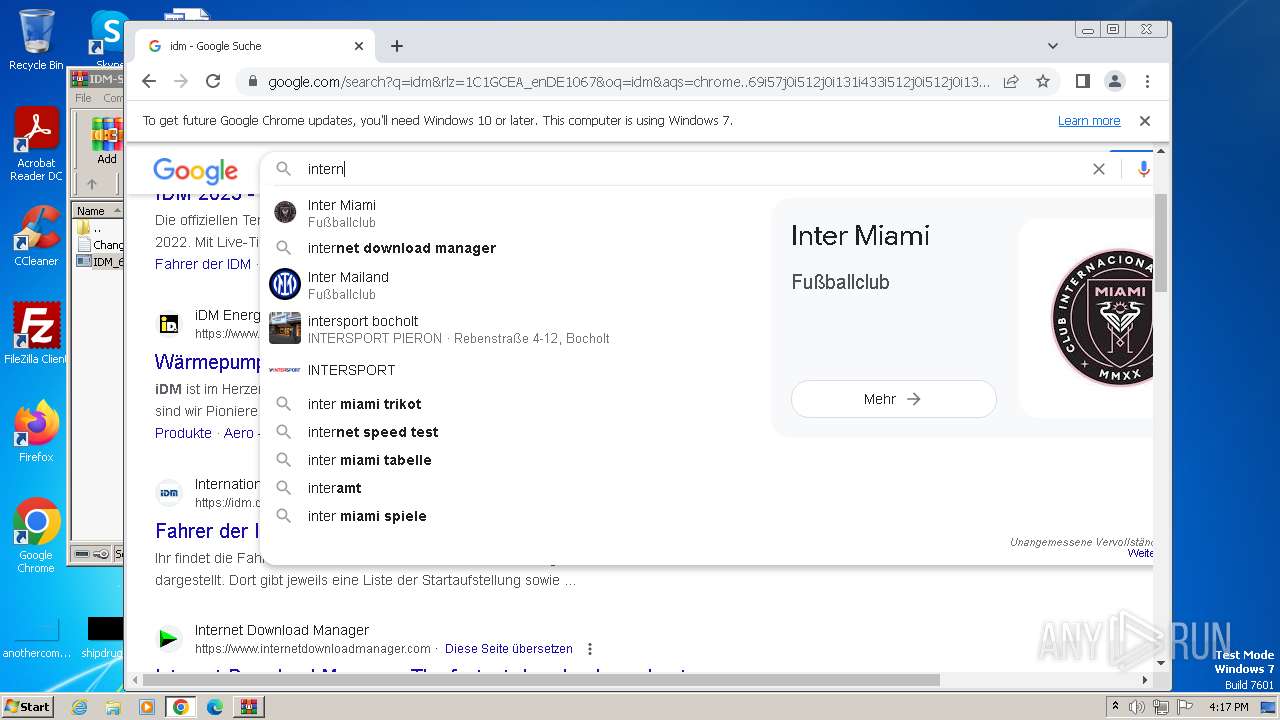
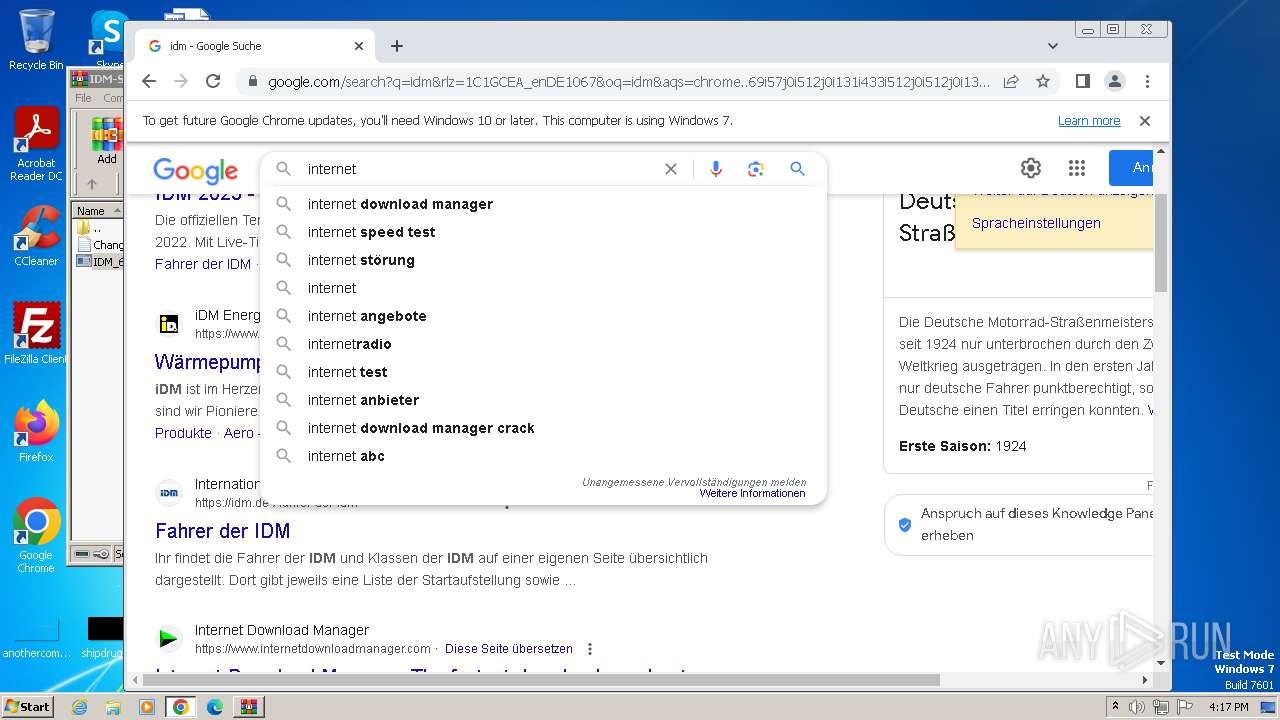
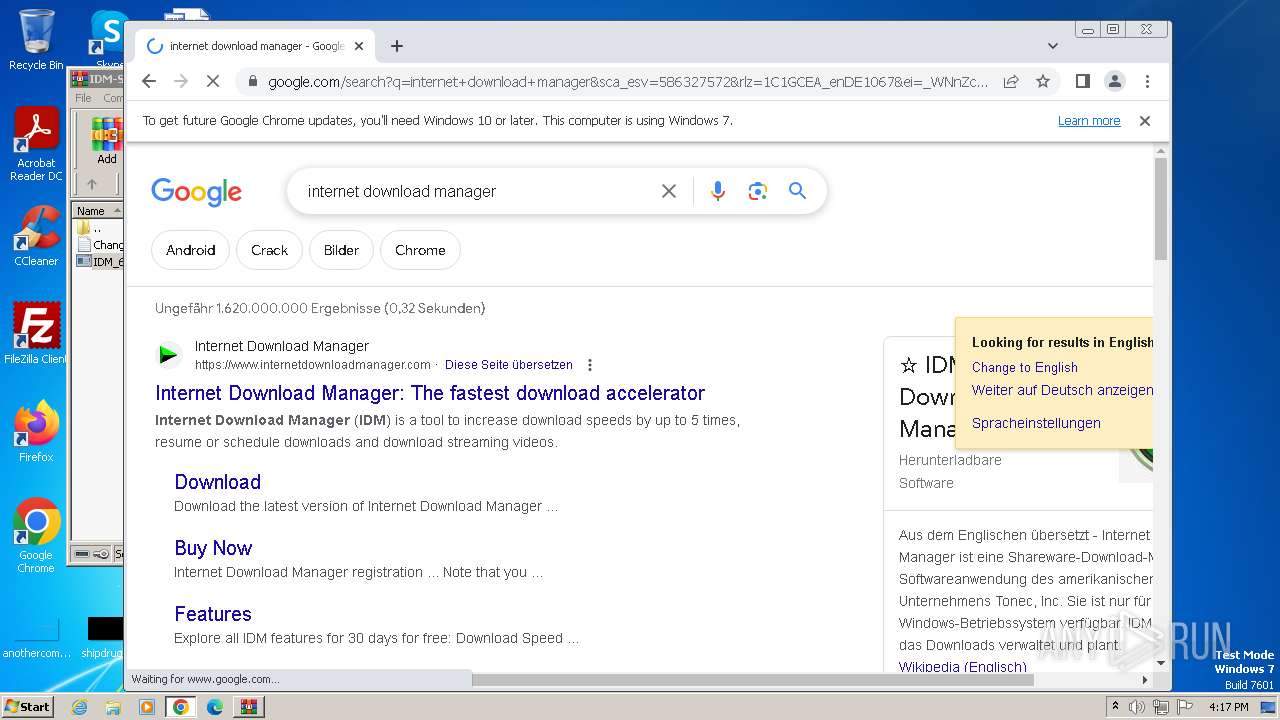
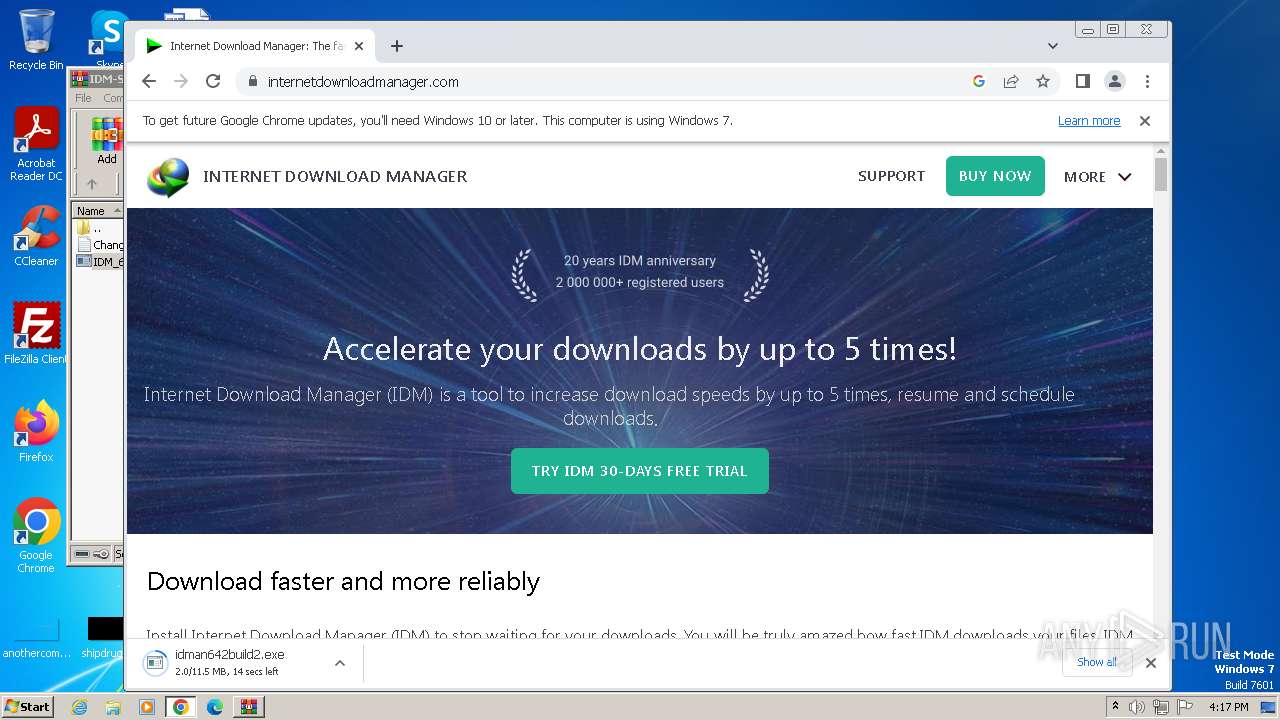
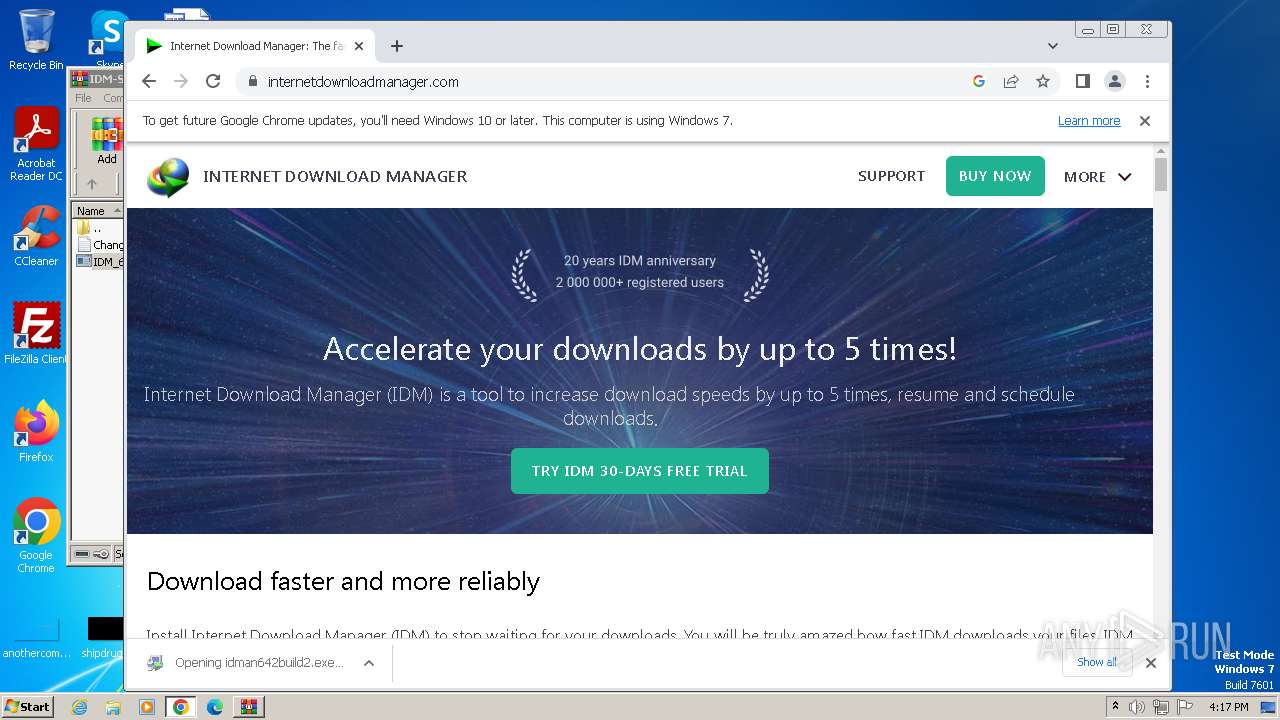
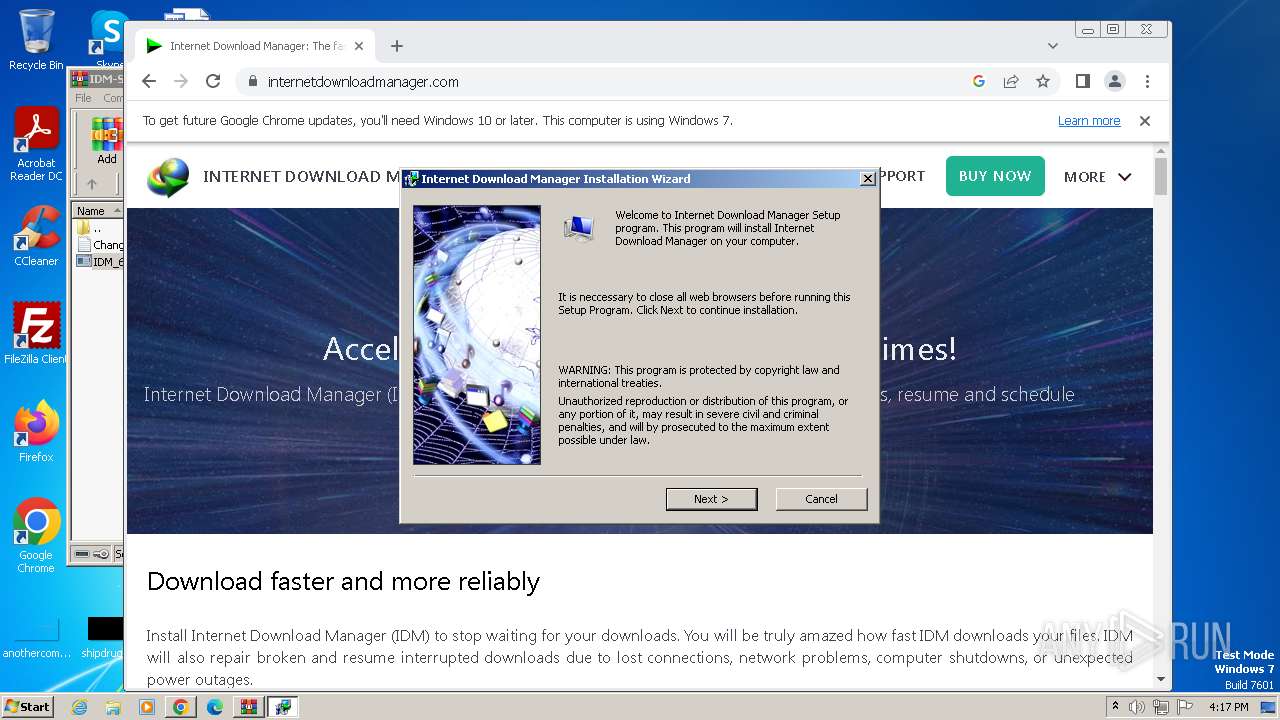
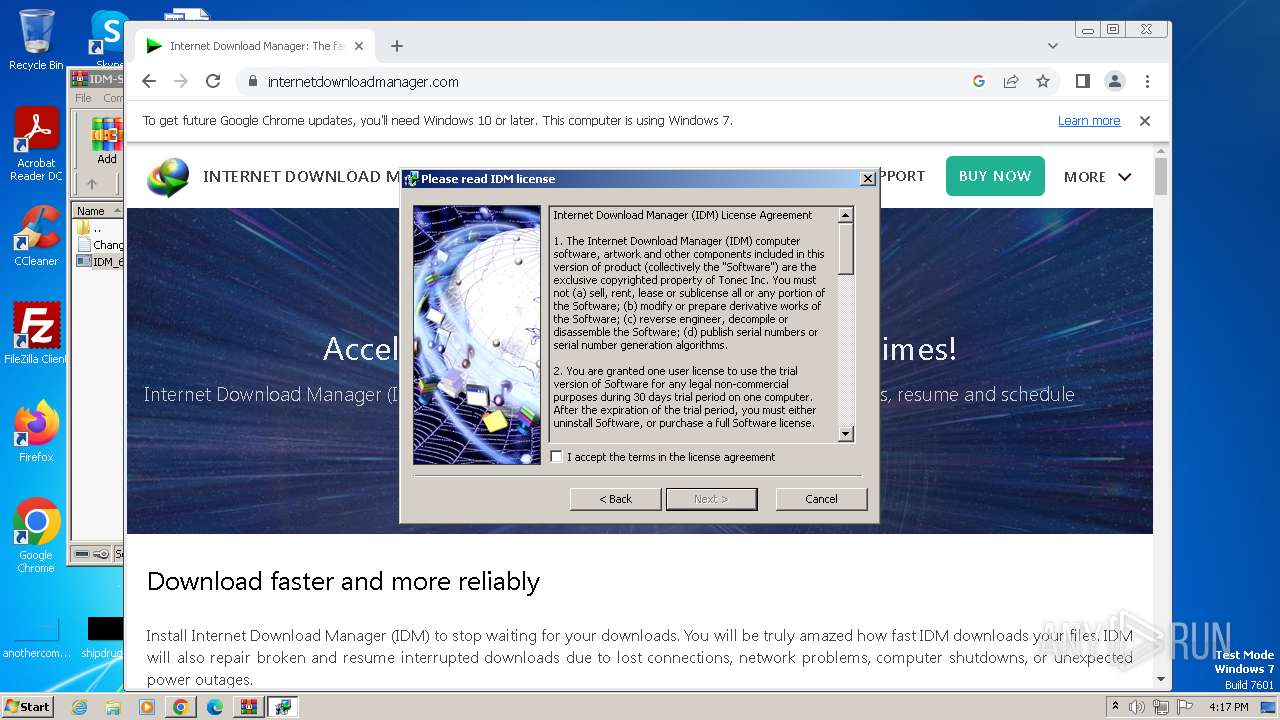
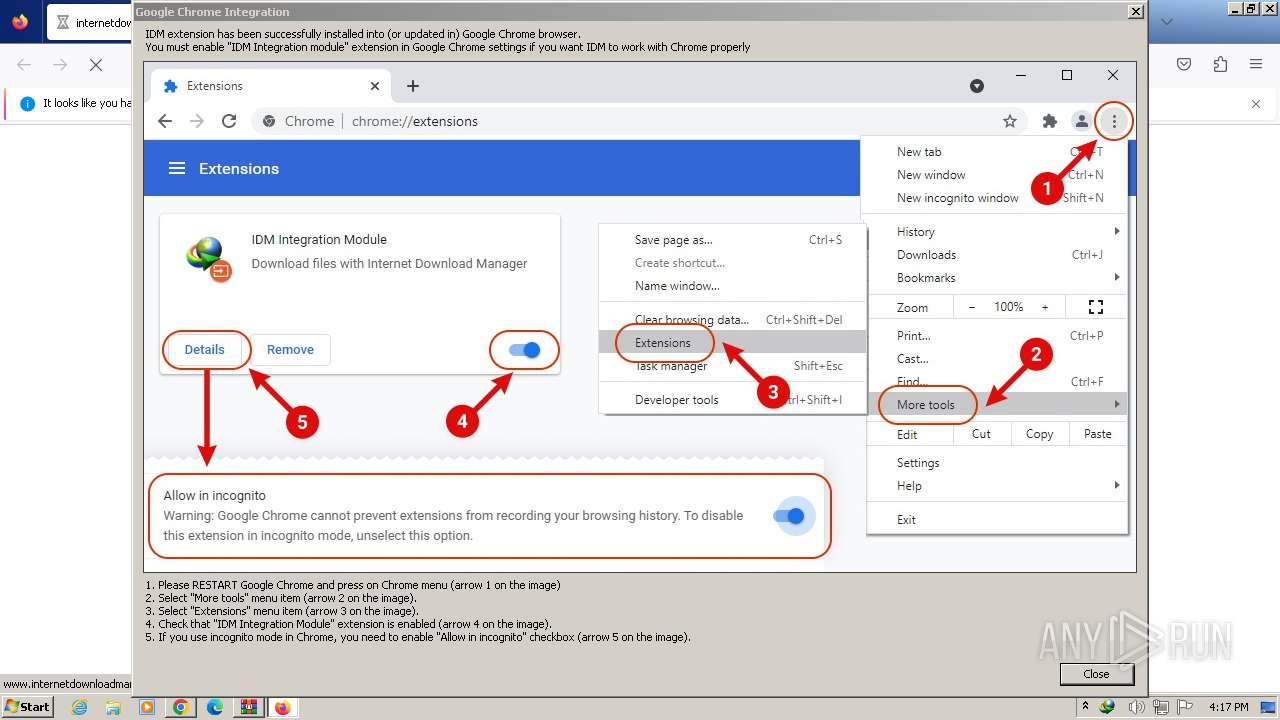
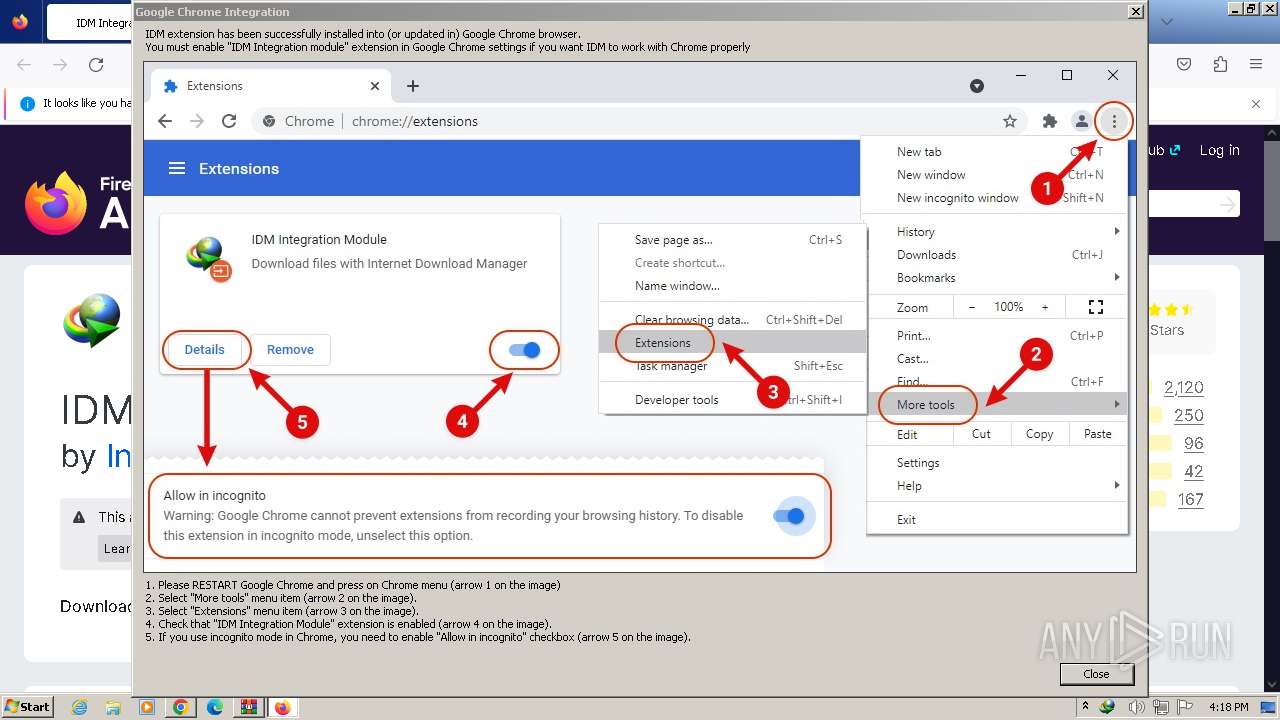
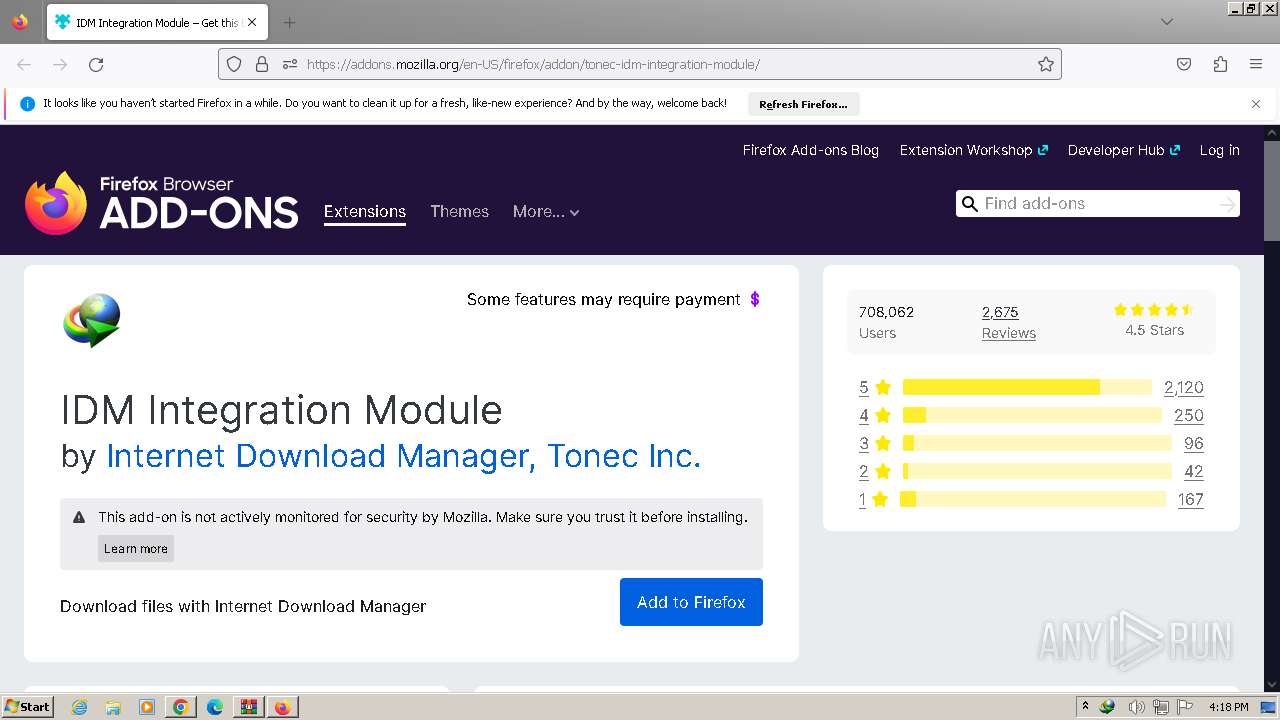
Manual execution by a user
- chrome.exe (PID: 924)
- wmpnscfg.exe (PID: 3312)
- firefox.exe (PID: 3128)
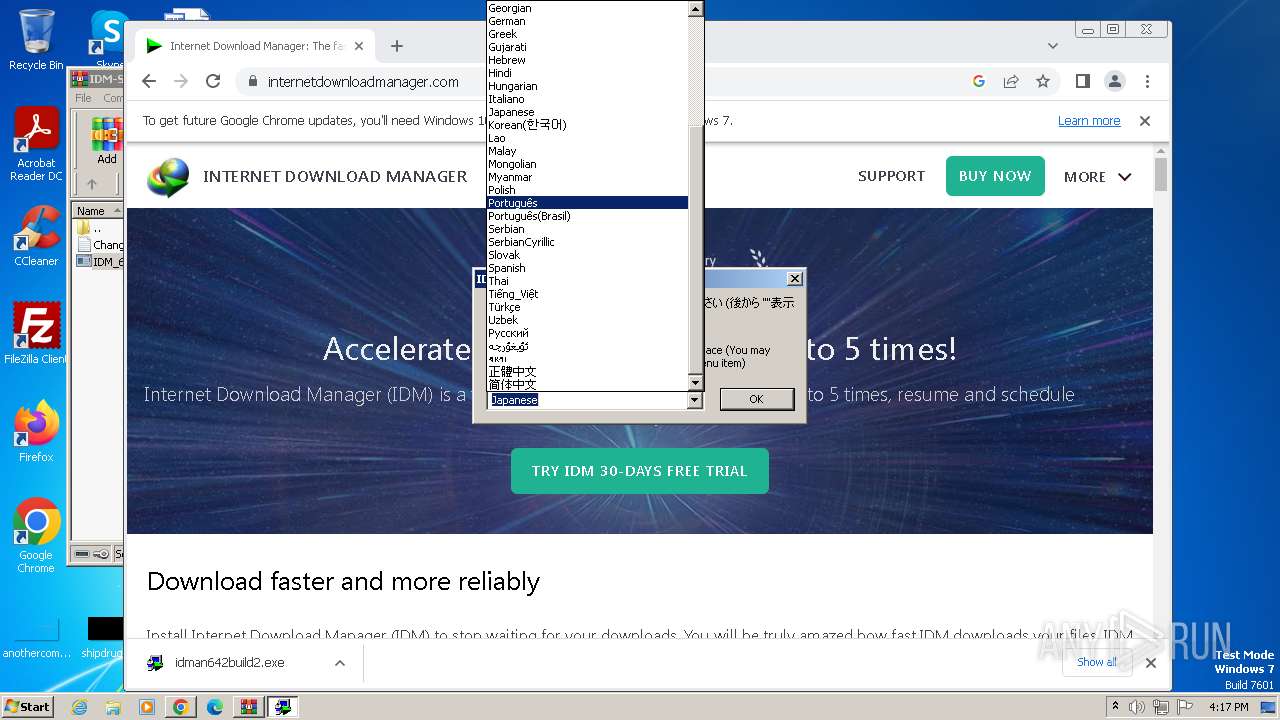
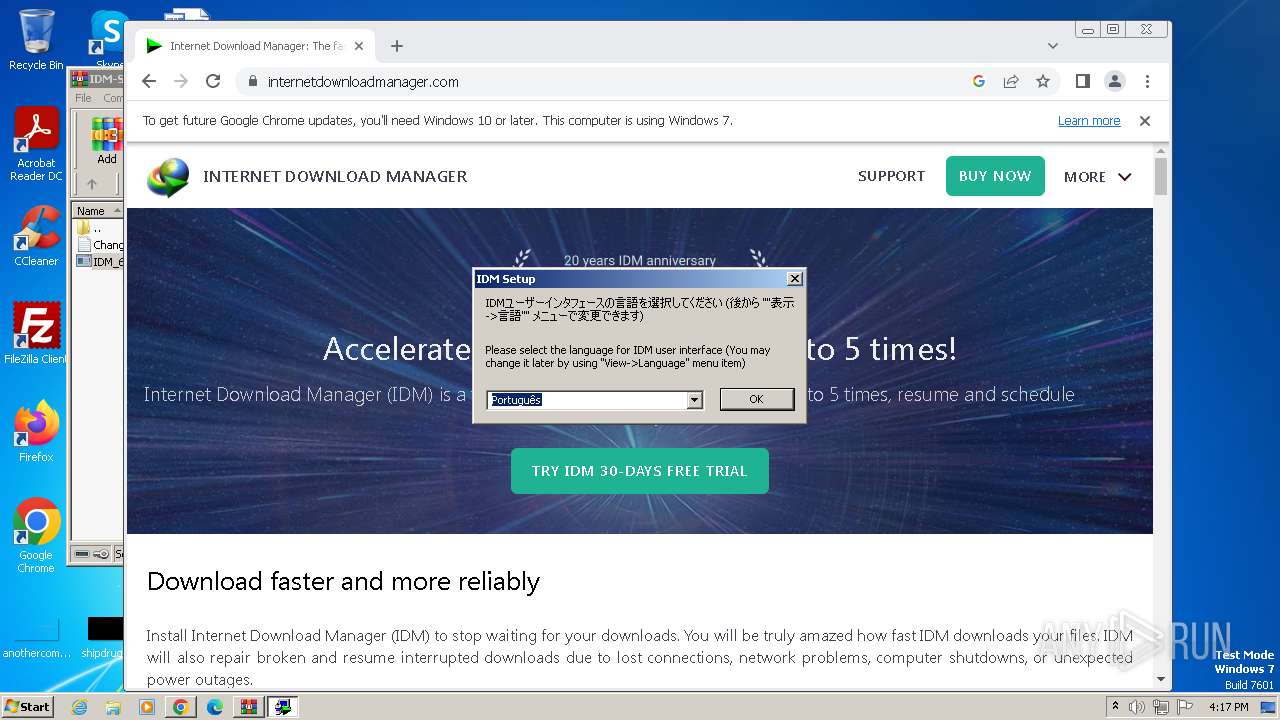
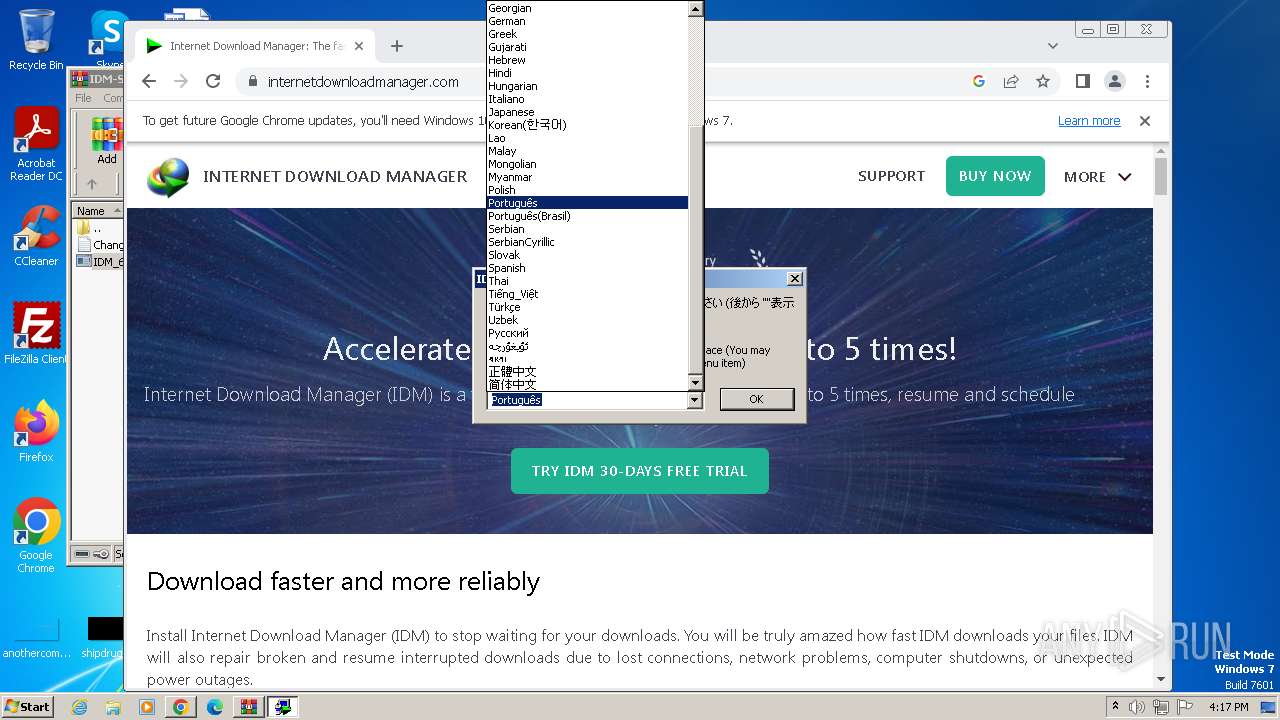
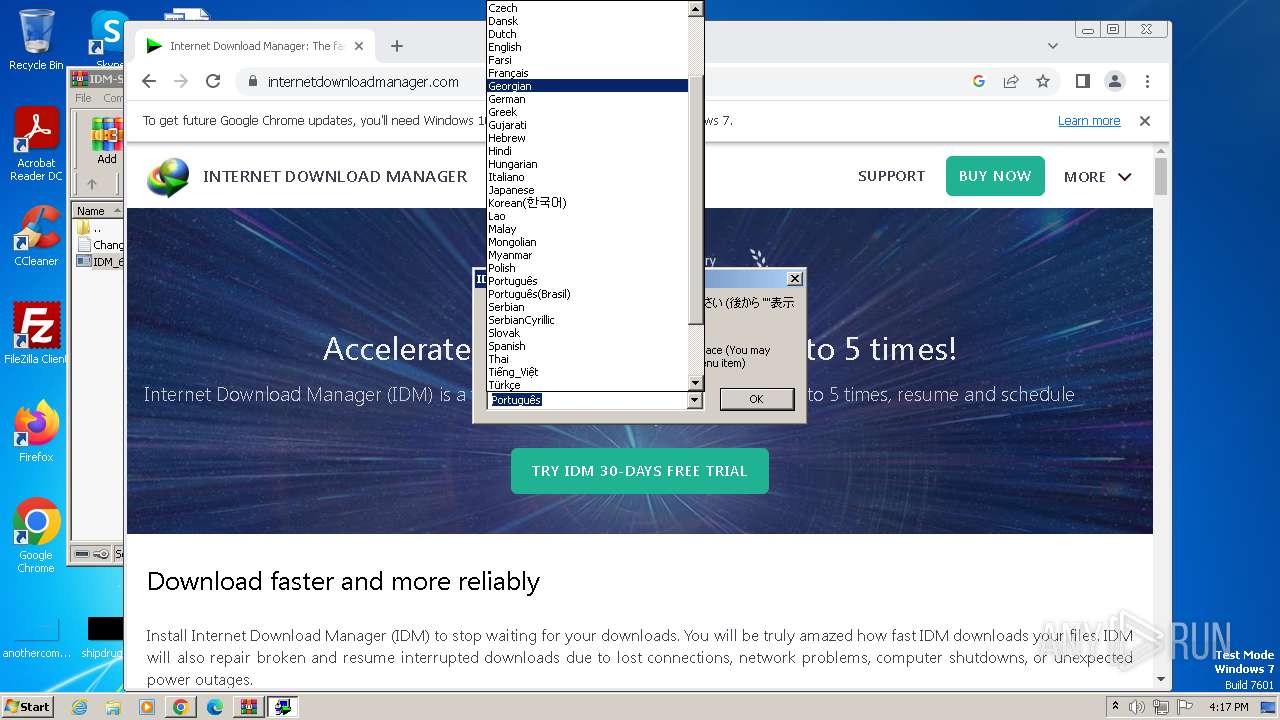
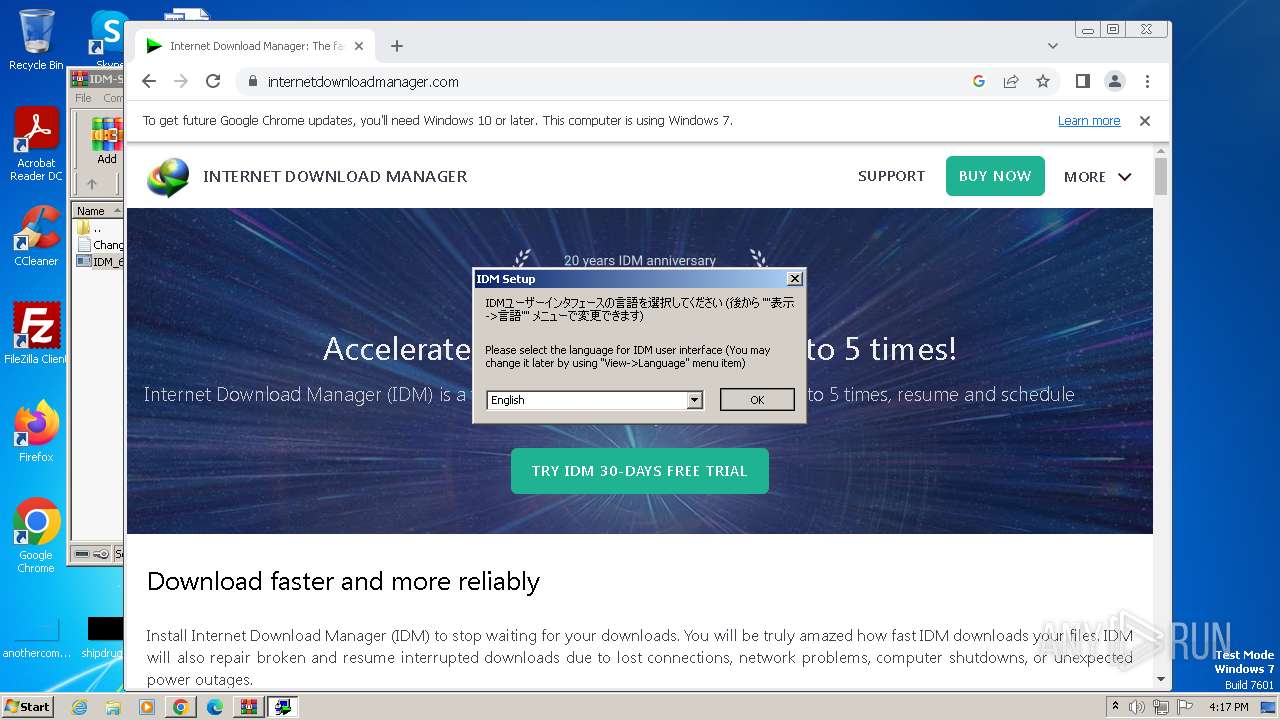
Checks supported languages
- IDM_6.4x_Crack_v17.9.exe (PID: 2460)
- wmpnscfg.exe (PID: 3312)
- IDM1.tmp (PID: 2900)
- idman642build2.exe (PID: 3912)
- idmBroker.exe (PID: 316)
- IDMan.exe (PID: 3236)
- Uninstall.exe (PID: 2132)
- MediumILStart.exe (PID: 2680)
- IDMan.exe (PID: 3192)
- IEMonitor.exe (PID: 3636)
- IDM_6.4x_Crack_v17.9.exe (PID: 3592)
- IDM_6.4x_Crack_v17.9.exe (PID: 3572)
- UnSigner.exe (PID: 3196)
Application launched itself
- chrome.exe (PID: 924)
- firefox.exe (PID: 3128)
- firefox.exe (PID: 2960)
- chrome.exe (PID: 2536)
Reads the computer name
- wmpnscfg.exe (PID: 3312)
- IDM1.tmp (PID: 2900)
- IDMan.exe (PID: 3236)
- Uninstall.exe (PID: 2132)
- MediumILStart.exe (PID: 2680)
- IDMan.exe (PID: 3192)
- IEMonitor.exe (PID: 3636)
- IDM_6.4x_Crack_v17.9.exe (PID: 3572)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3312)
- IDM1.tmp (PID: 2900)
- IDMan.exe (PID: 3236)
- MediumILStart.exe (PID: 2680)
- IDMan.exe (PID: 3192)
The process uses the downloaded file
- chrome.exe (PID: 1628)
- chrome.exe (PID: 2396)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 924)
Create files in a temporary directory
- idman642build2.exe (PID: 3912)
- IDM1.tmp (PID: 2900)
- IDMan.exe (PID: 3236)
- IDMan.exe (PID: 3192)
- IDM_6.4x_Crack_v17.9.exe (PID: 3592)
- IDM_6.4x_Crack_v17.9.exe (PID: 3572)
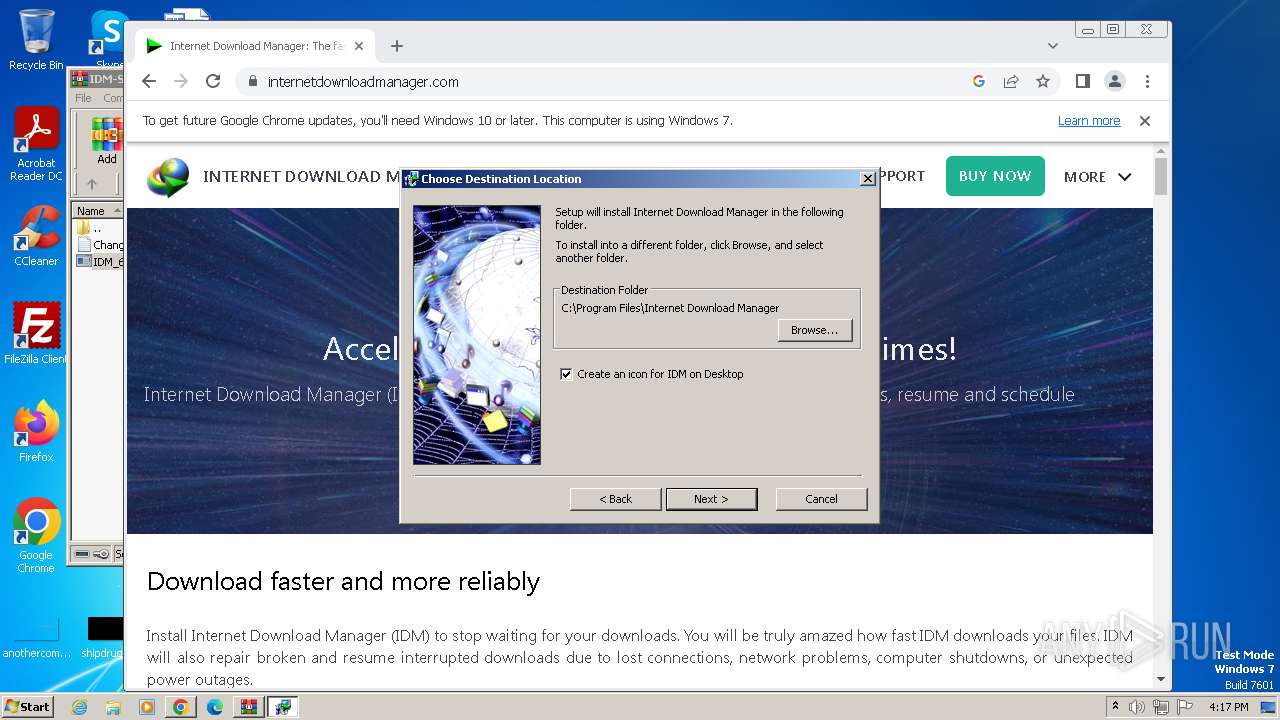
Creates files in the program directory
- IDM1.tmp (PID: 2900)
- IDMan.exe (PID: 3236)
- wscript.exe (PID: 2864)
- chrome.exe (PID: 2536)
Creates files or folders in the user directory
- IDM1.tmp (PID: 2900)
- IDMan.exe (PID: 3236)
- IDMan.exe (PID: 3192)
Creates files in the driver directory
- rundll32.exe (PID: 3988)
Reads the time zone
- runonce.exe (PID: 3320)
Checks proxy server information
- IDMan.exe (PID: 3192)
- wscript.exe (PID: 3776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
145
Monitored processes
88
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4328 --field-trial-handle=1104,i,15026613883206119356,12593706806305304904,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4560 --field-trial-handle=1104,i,15026613883206119356,12593706806305304904,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2128 --field-trial-handle=1104,i,15026613883206119356,12593706806305304904,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Internet Download Manager\idmBroker.exe" -RegServer | C:\Program Files\Internet Download Manager\idmBroker.exe | — | IDM1.tmp | |||||||||||
User: admin Company: Internet Download Manager, Tonec Inc. Integrity Level: HIGH Description: Broker for reading of IDM settings Exit code: 0 Version: 6, 35, 9, 1 Modules
| |||||||||||||||
| 448 | C:\Windows\system32\net1 start IDMWFP | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4720 --field-trial-handle=1104,i,15026613883206119356,12593706806305304904,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\IDM-SteamRIP.com (1).rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4092 --field-trial-handle=1104,i,15026613883206119356,12593706806305304904,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2264 --field-trial-handle=1104,i,15026613883206119356,12593706806305304904,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
36 523
Read events
35 959
Write events
455
Delete events
109
Modification events
| (PID) Process: | (888) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
23
Suspicious files
384
Text files
146
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1c2032.TMP | — | |
MD5:— | SHA256:— | |||
| 924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 888 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa888.8413\Read_Me_Instructions.txt | text | |
MD5:9B9759ED16E93B0C7A12D823E14003FE | SHA256:7A49FE18C047FFA0E5AF8B9A108079A1F8512D08A62E90EE44FA26CB6AF21638 | |||
| 924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 888 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa888.8413\IDM_6.4x_Crack_v17.9-Ali.Dbg\Changelog.txt | text | |
MD5:7C169566C85442A049E525AA6E400F04 | SHA256:6AB0219B76159D0C6BBBF103DD349E2B9B8BCA5ADE06098AA1DB271011EA0BBC | |||
| 924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF1c21a9.TMP | text | |
MD5:7C1C23F006788D107F8A01B852CC6701 | SHA256:9FA4E627077EDCBEC8AAA1ED2DD5538E630790893F88F02F1E9CC863E6A27848 | |||
| 924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1c2245.TMP | — | |
MD5:— | SHA256:— | |||
| 924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
109
DNS requests
179
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2960 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | text | 90 b | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
3236 | IDMan.exe | GET | 200 | 23.53.42.26:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e4ff40690fdde035 | unknown | compressed | 65.2 Kb | unknown |
2960 | firefox.exe | POST | — | 184.24.77.61:80 | http://r3.o.lencr.org/ | unknown | — | — | unknown |
2960 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | text | 8 b | unknown |
2960 | firefox.exe | POST | — | 184.24.77.61:80 | http://r3.o.lencr.org/ | unknown | — | — | unknown |
2960 | firefox.exe | POST | — | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | unknown |
2960 | firefox.exe | POST | — | 18.245.65.219:80 | http://ocsp.r2m02.amazontrust.com/ | unknown | — | — | unknown |
2960 | firefox.exe | POST | — | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | unknown |
2960 | firefox.exe | POST | — | 184.24.77.61:80 | http://r3.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3380 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
924 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3380 | chrome.exe | 142.250.184.237:443 | accounts.google.com | GOOGLE | US | unknown |
3380 | chrome.exe | 142.250.181.228:443 | www.google.com | GOOGLE | US | whitelisted |
3380 | chrome.exe | 142.250.185.131:443 | update.googleapis.com | GOOGLE | US | whitelisted |
3380 | chrome.exe | 142.250.181.238:443 | encrypted-tbn0.gstatic.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
consent.google.com |
| shared |