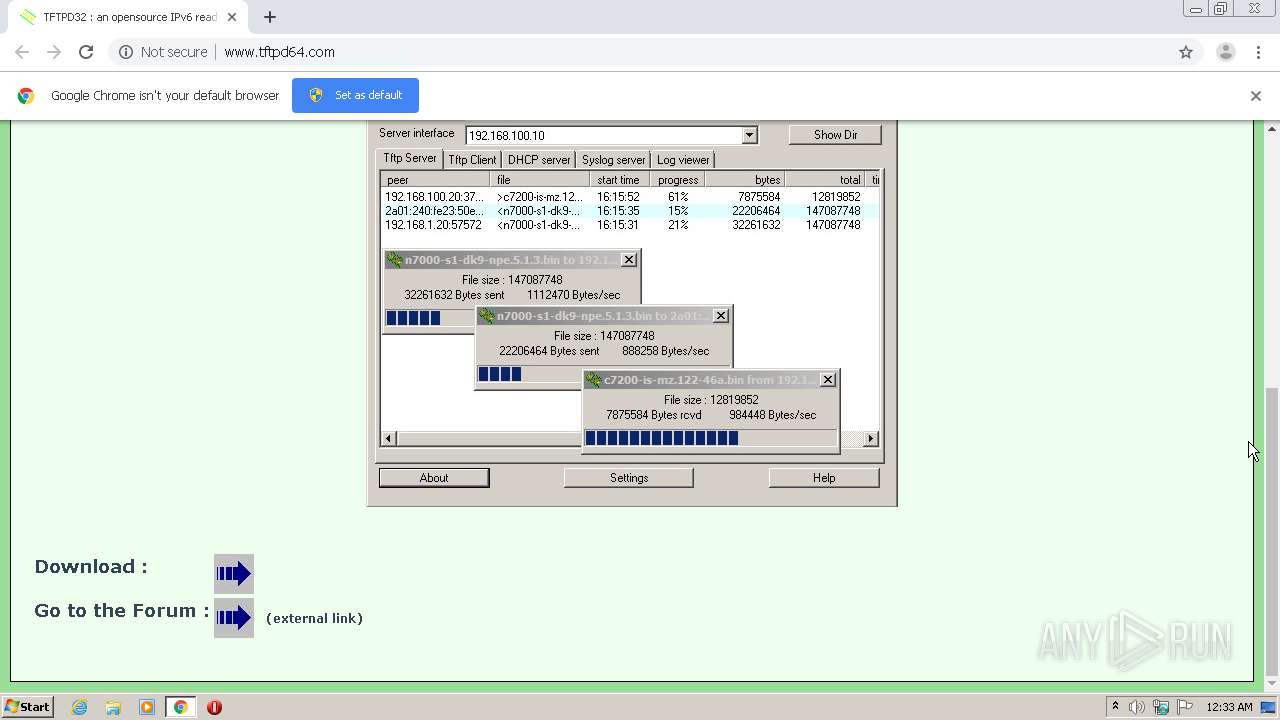
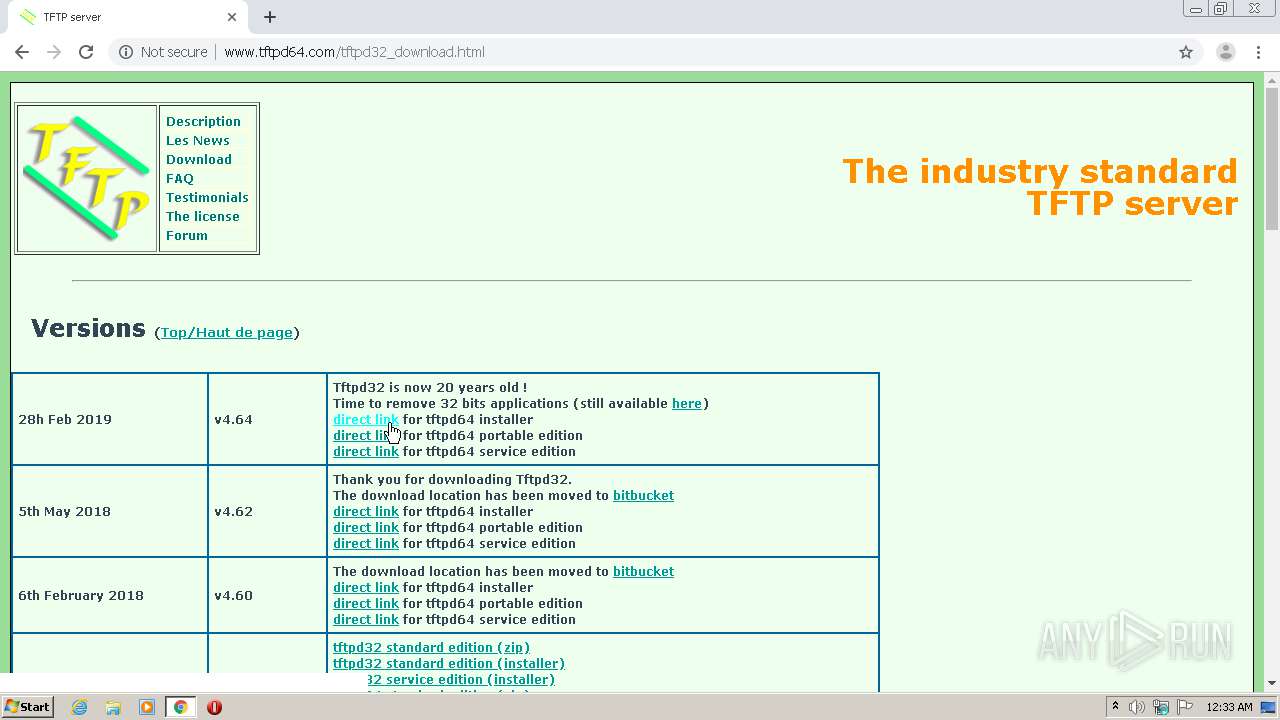
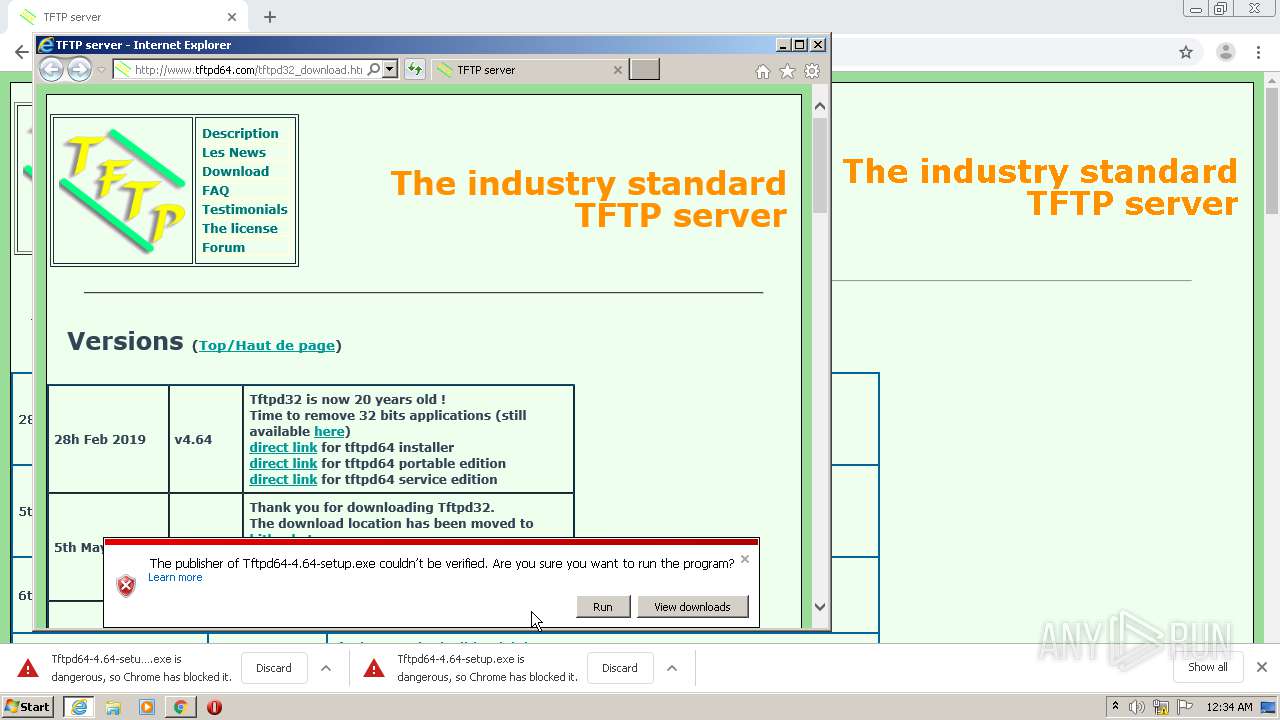
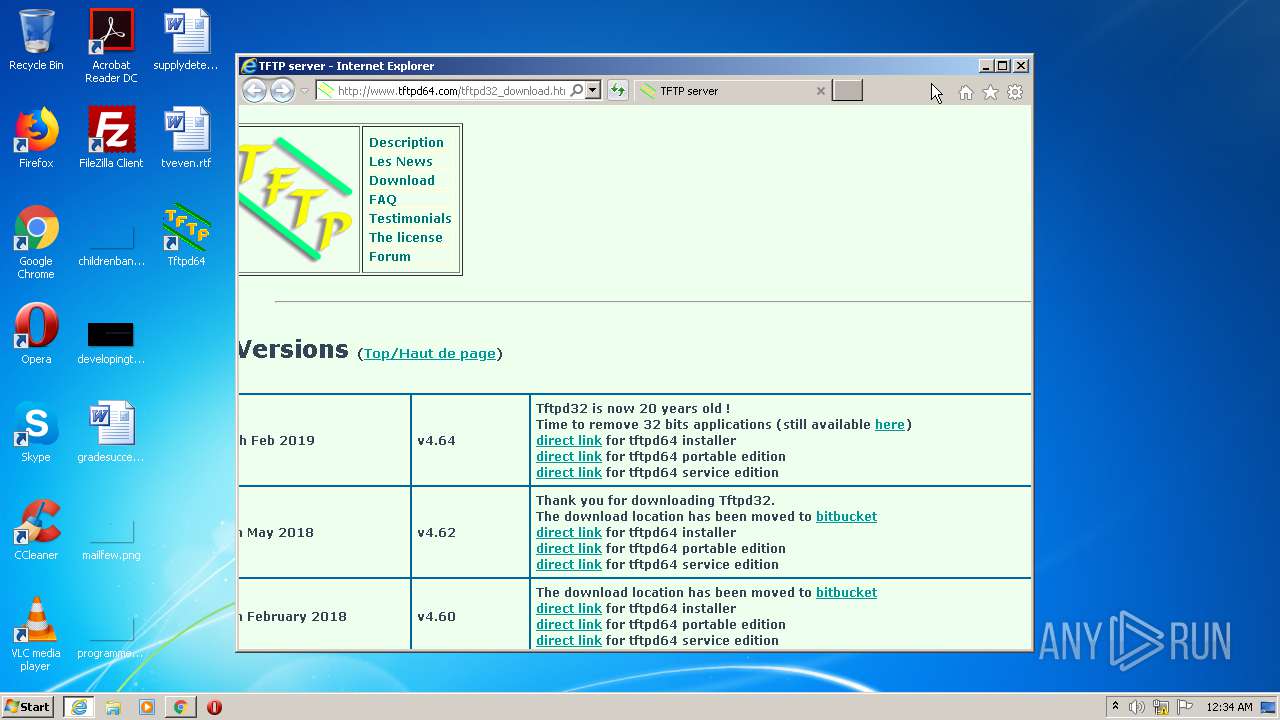
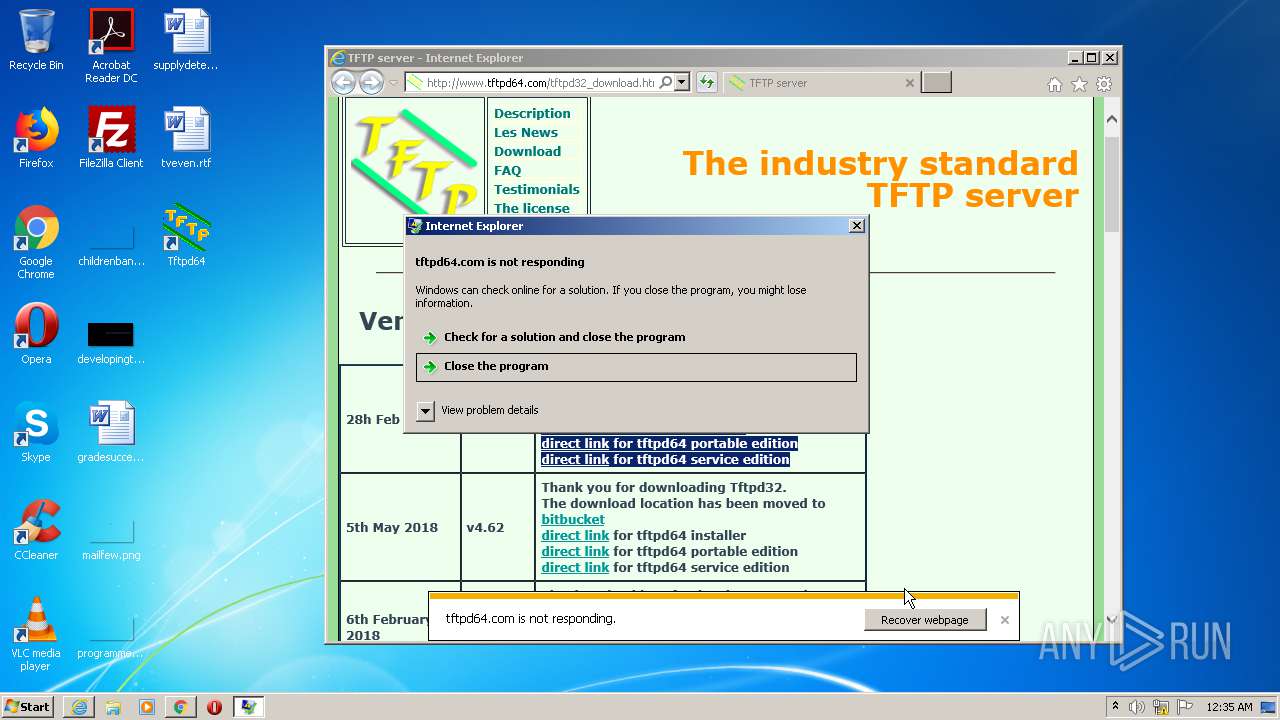
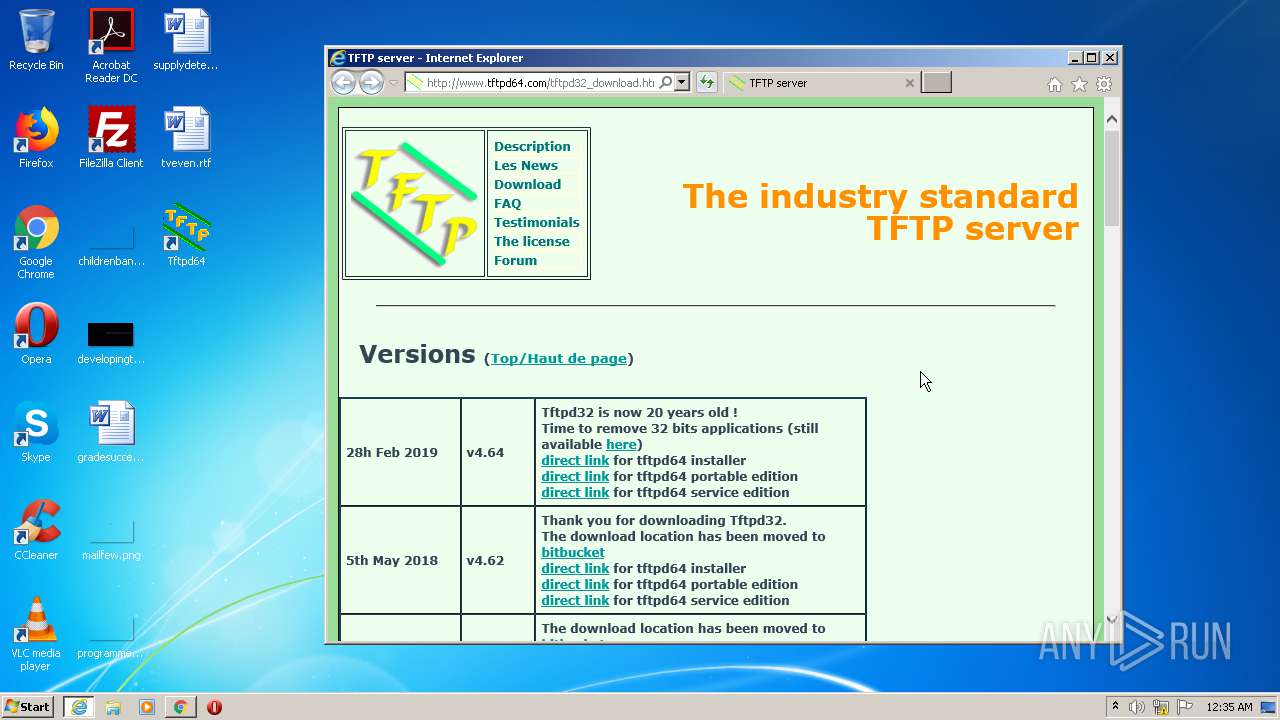
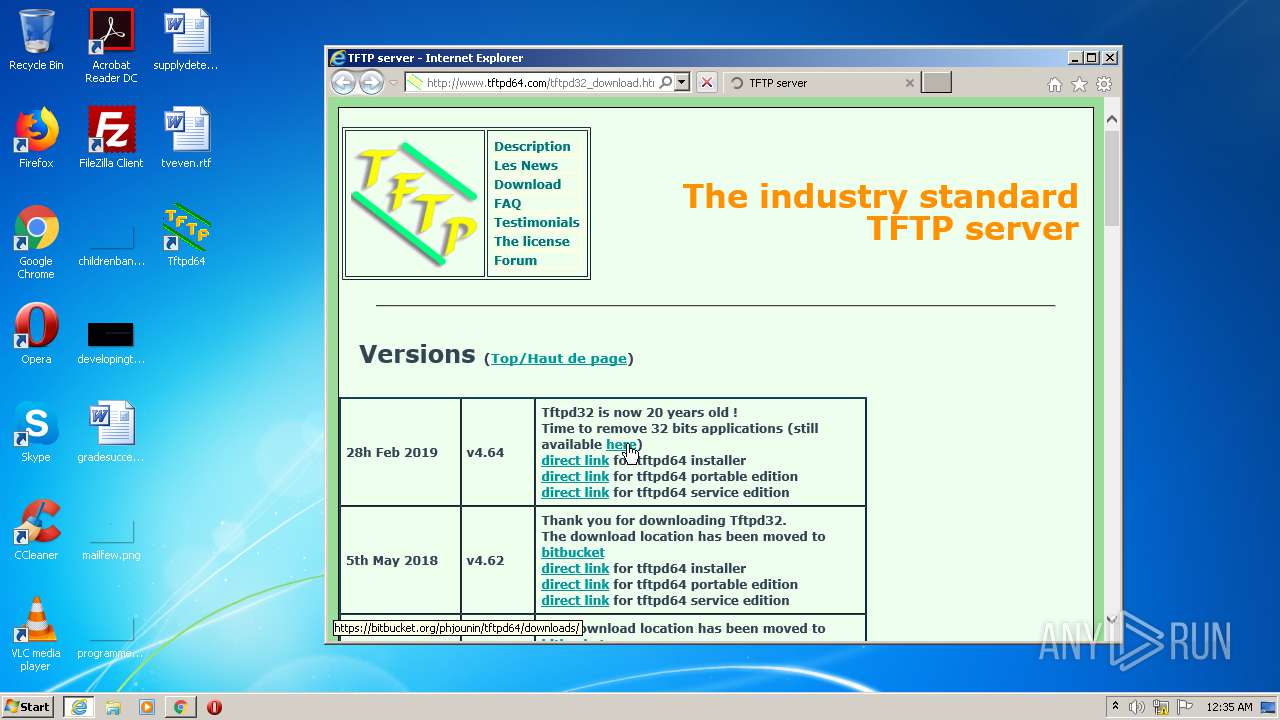
| URL: | http://www.tftpd64.com |
| Full analysis: | https://app.any.run/tasks/d8f73c60-e83f-4eed-a670-21ab906d3fd7 |
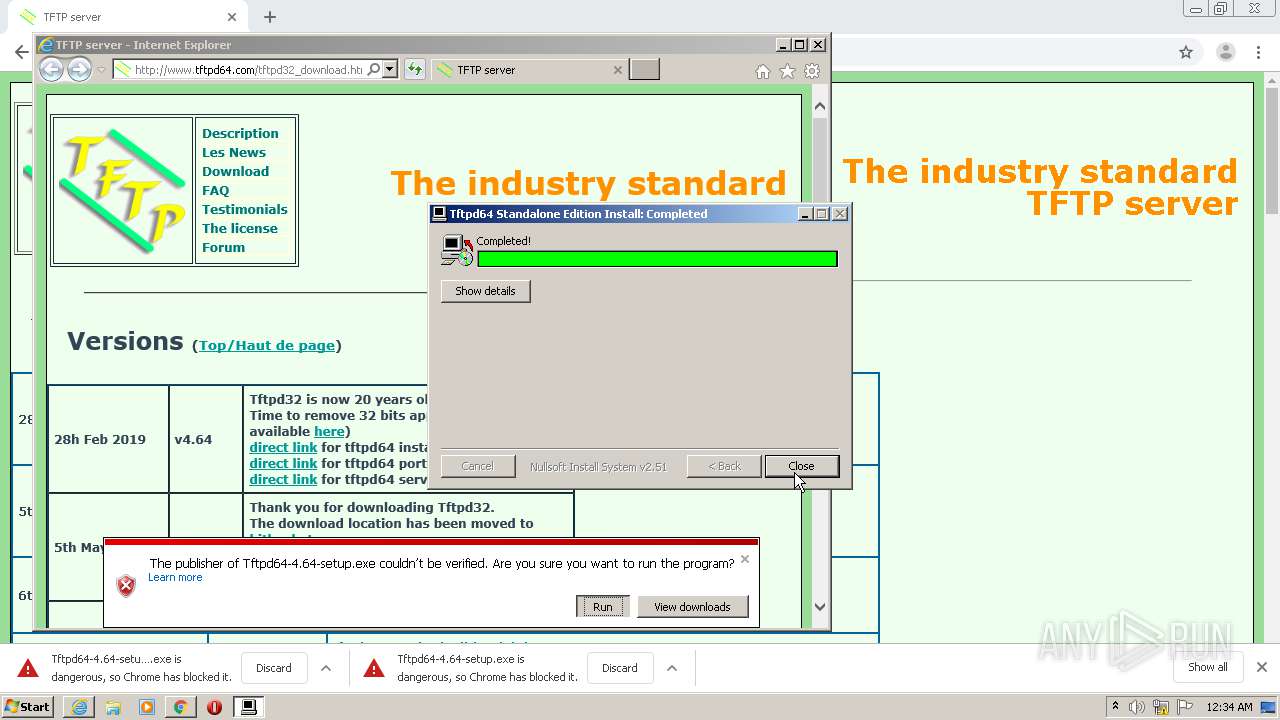
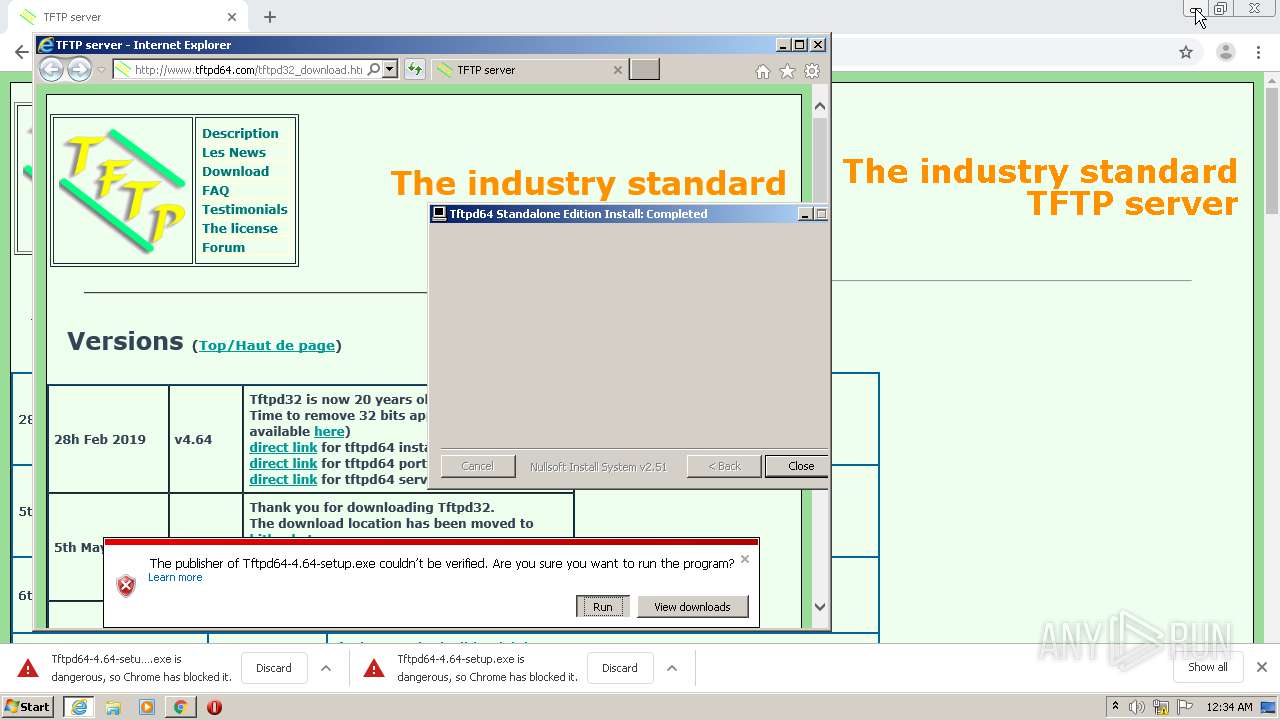
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2020, 23:32:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 21BAE55D87B1DC4BF900FB64E88BFA93 |
| SHA1: | 01562C6D988AC46D8558F8002F1DF57548C04522 |
| SHA256: | 831B496D0929B4C64EB6EE310048337BF593FB05C582A2528C580309D0399BAC |
| SSDEEP: | 3:N1KJS4NLdI:Cc4o |
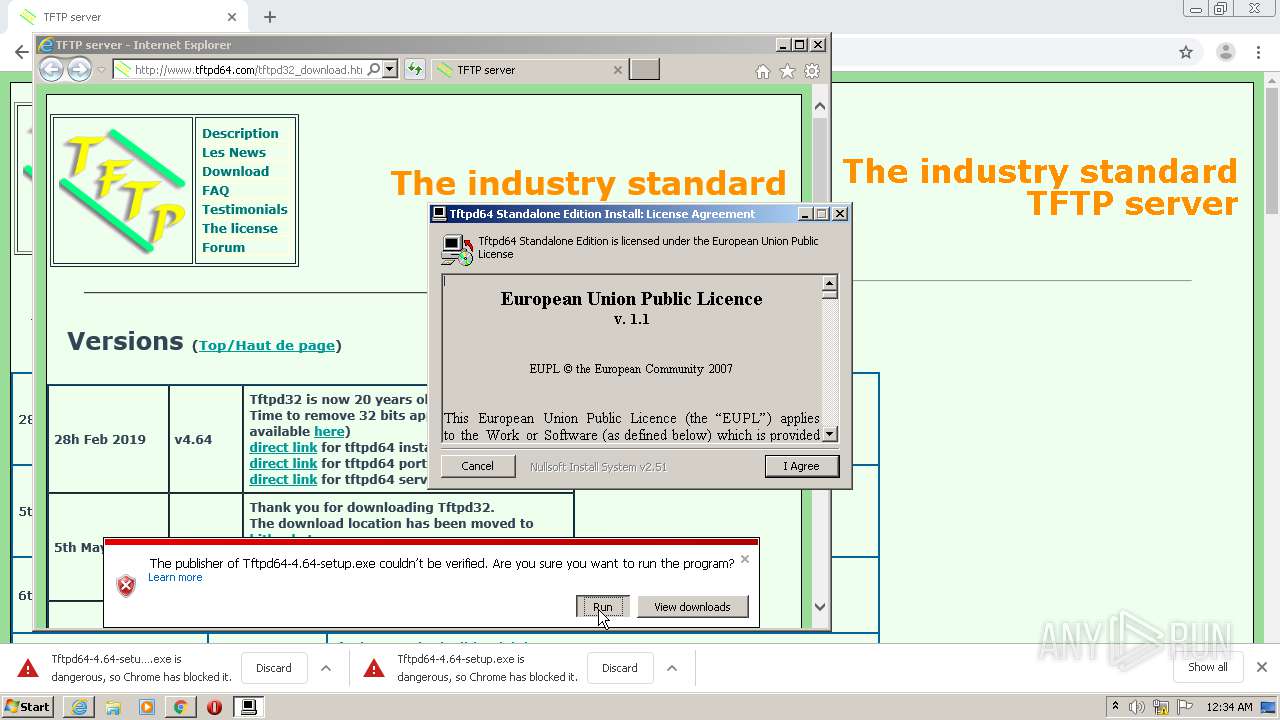
MALICIOUS
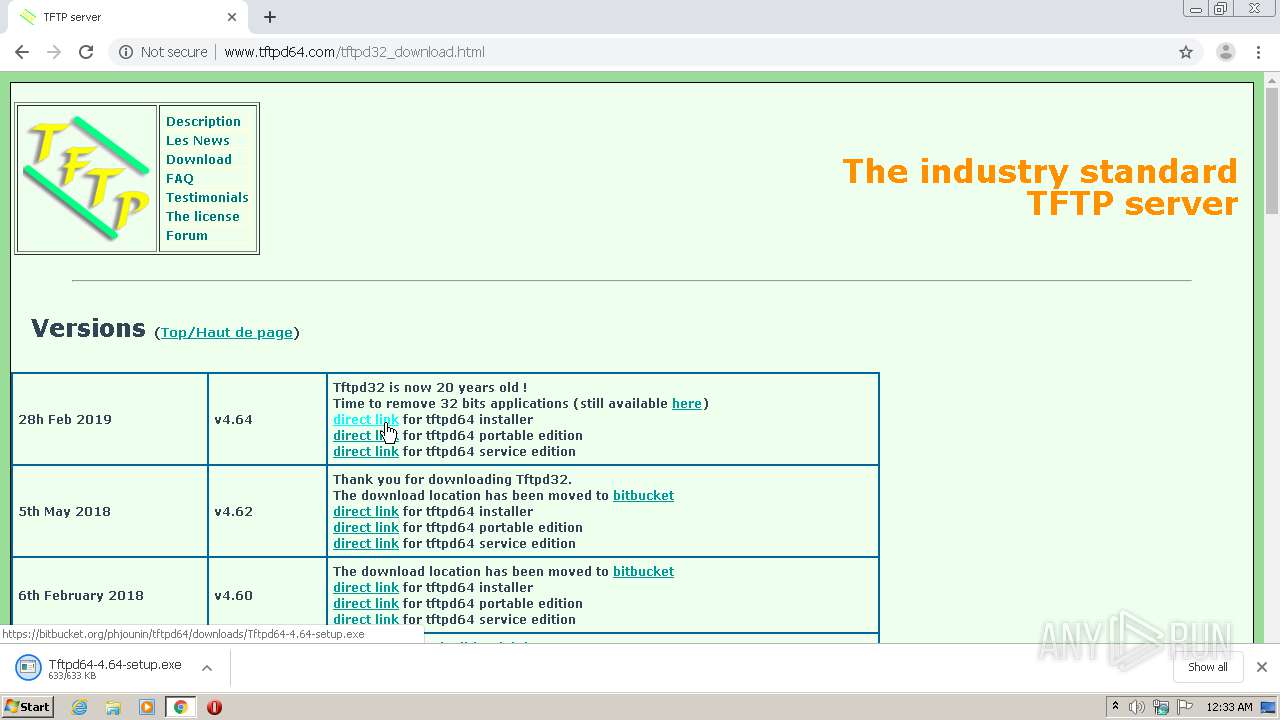
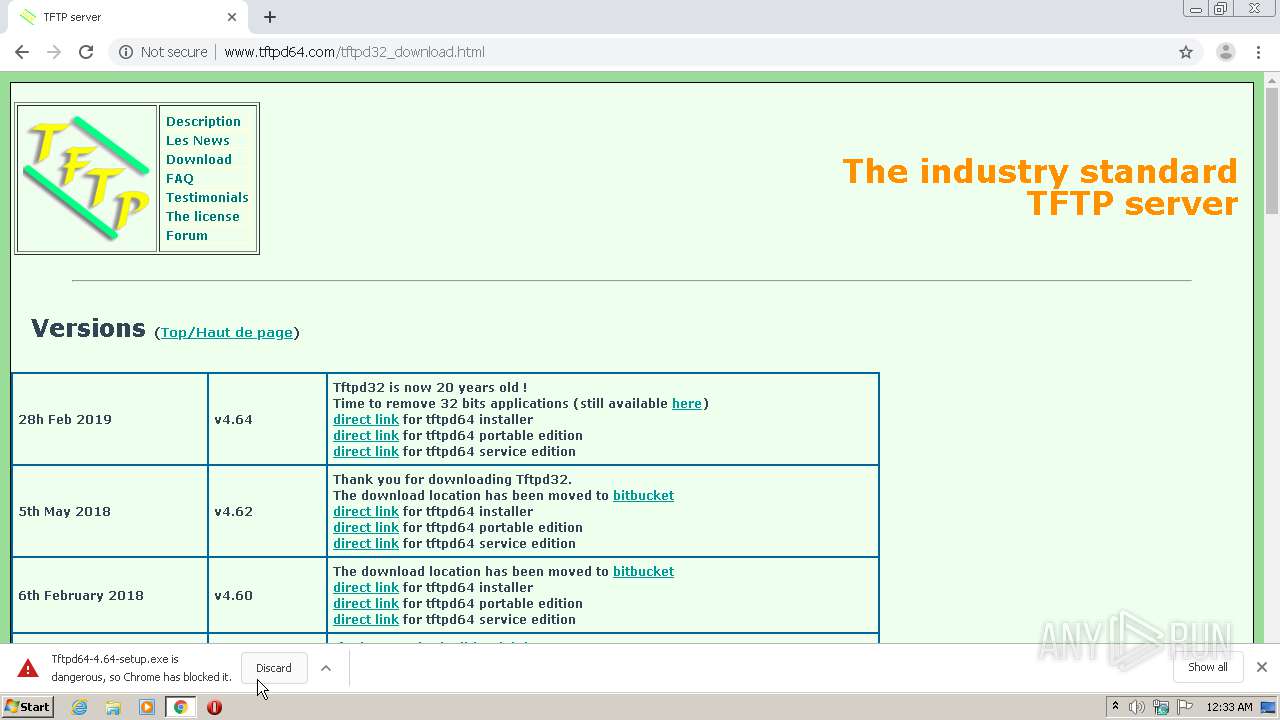
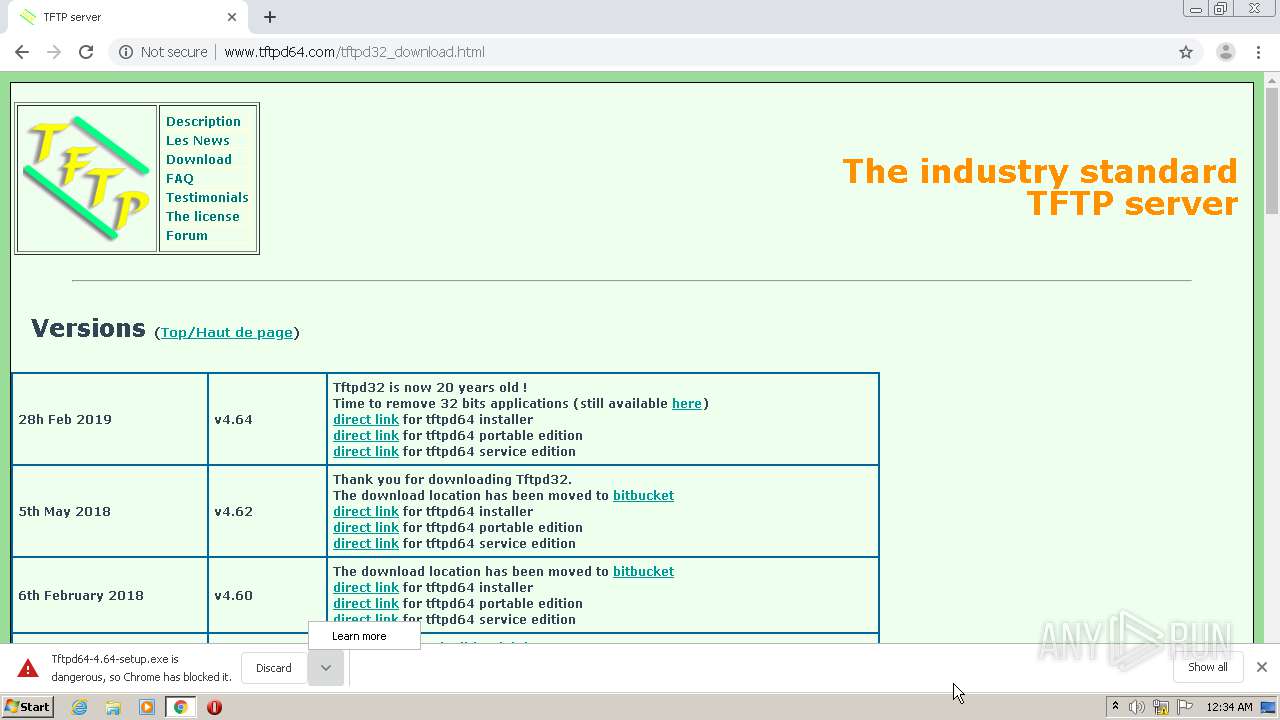
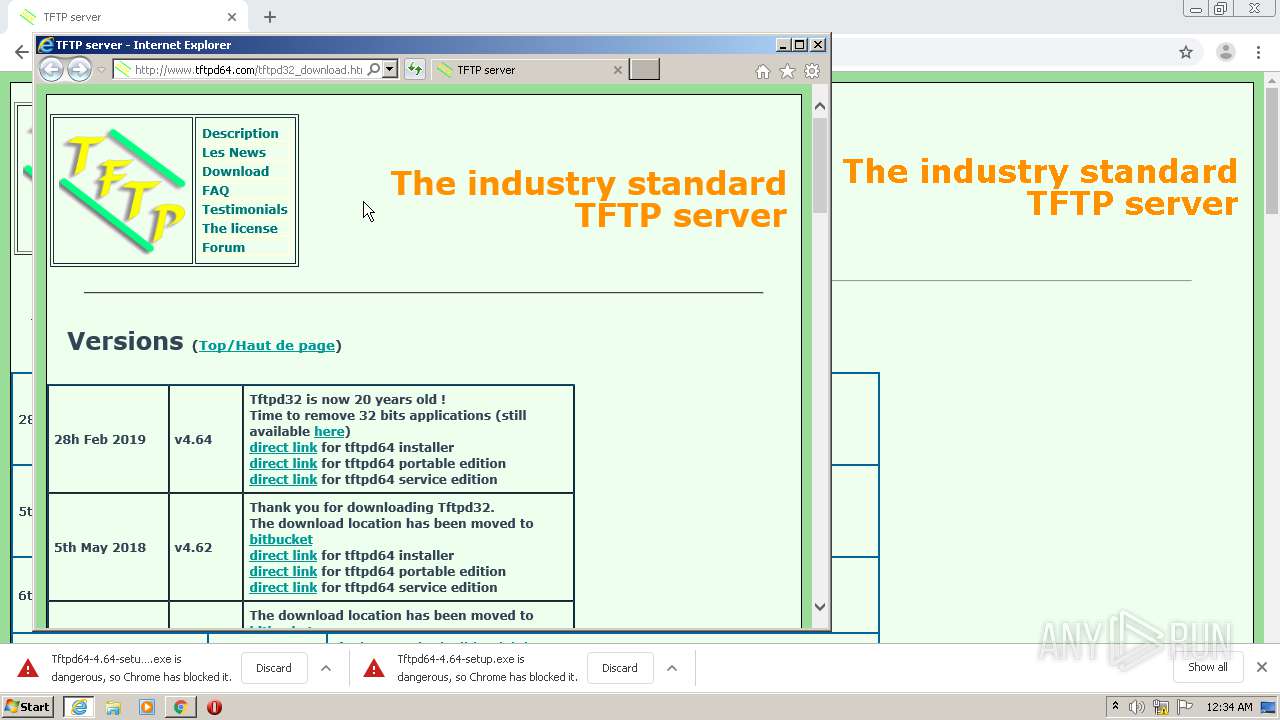
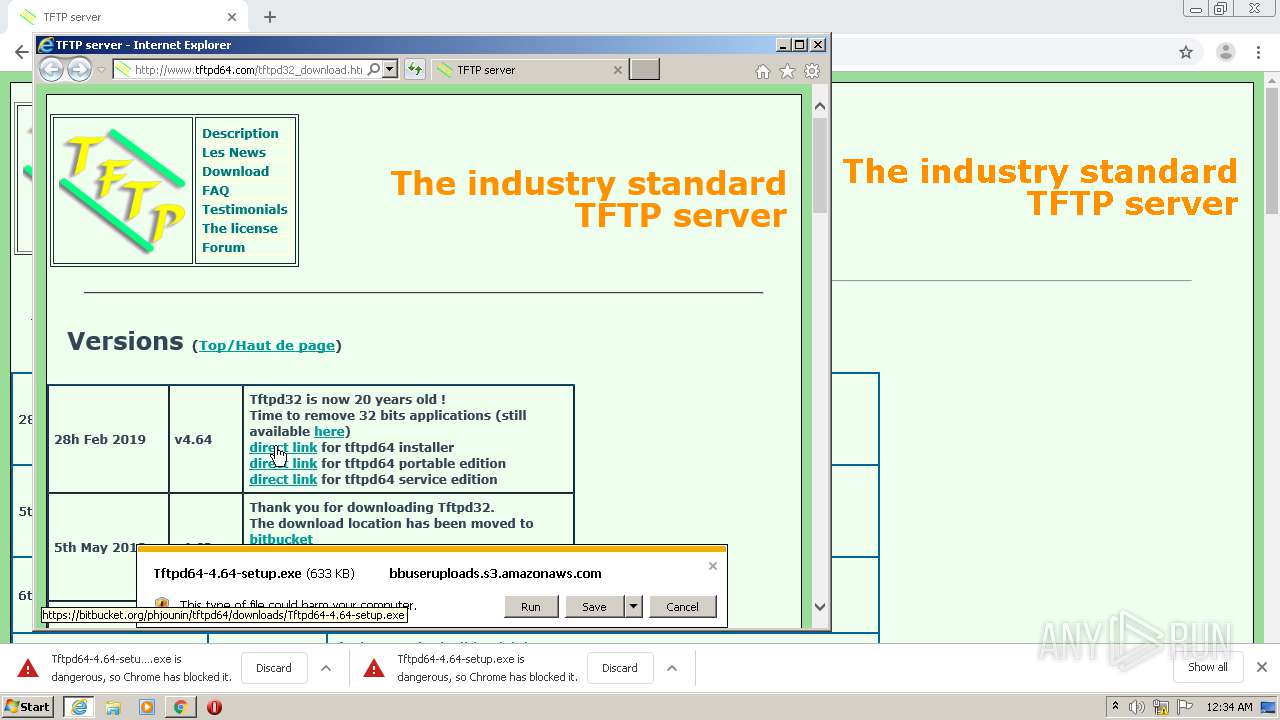
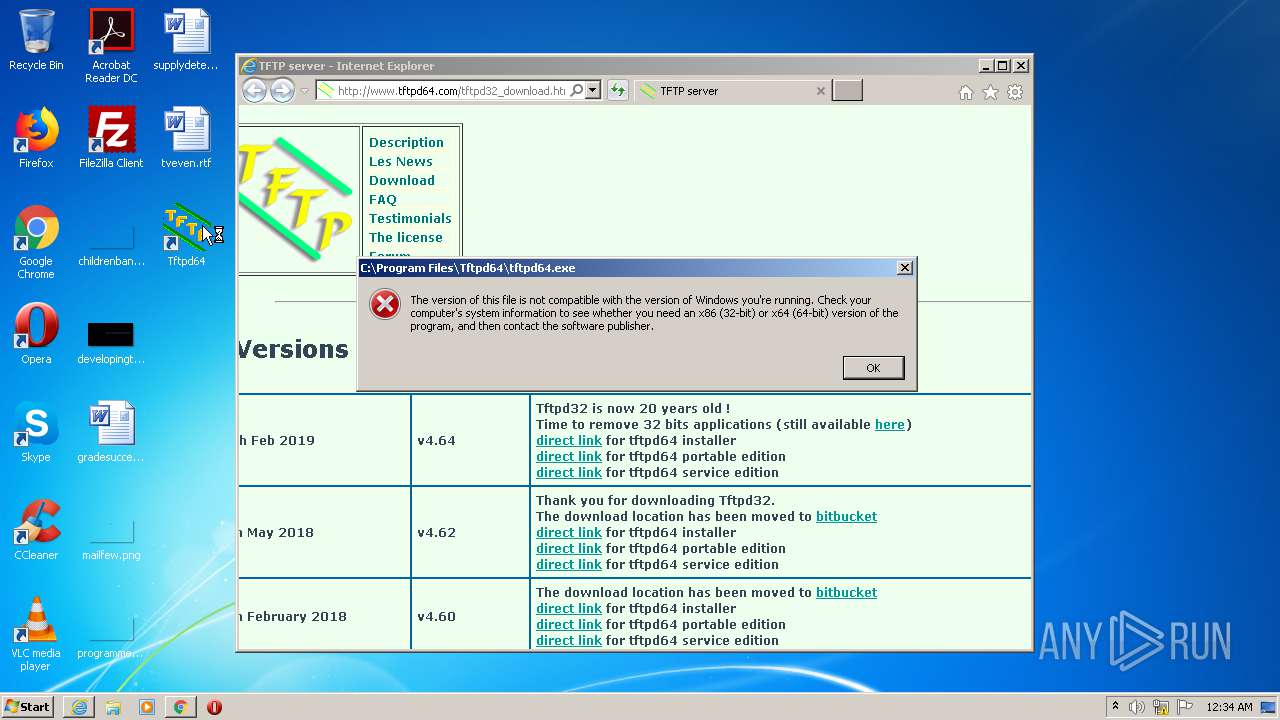
Application was dropped or rewritten from another process
- Tftpd64-4.64-setup.exe (PID: 576)
- Tftpd64-4.64-setup.exe (PID: 3432)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 712)
- chrome.exe (PID: 2468)
- iexplore.exe (PID: 2796)
- iexplore.exe (PID: 2168)
- Tftpd64-4.64-setup.exe (PID: 3432)
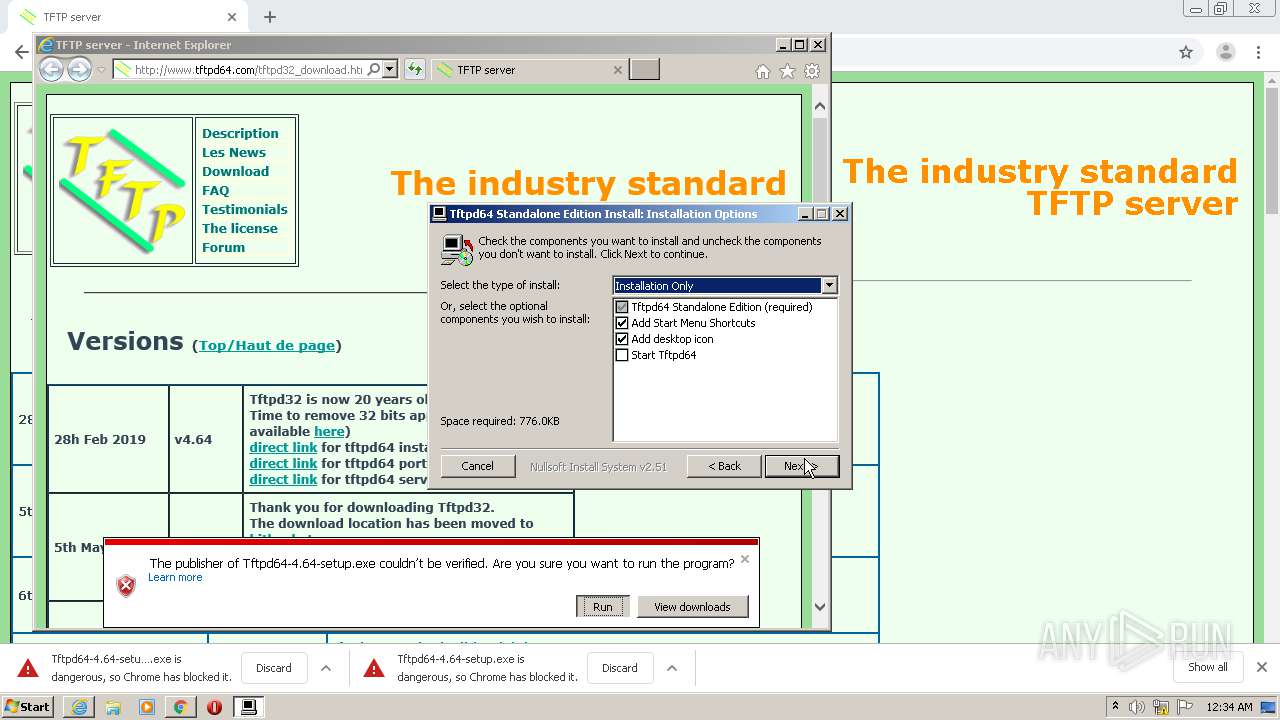
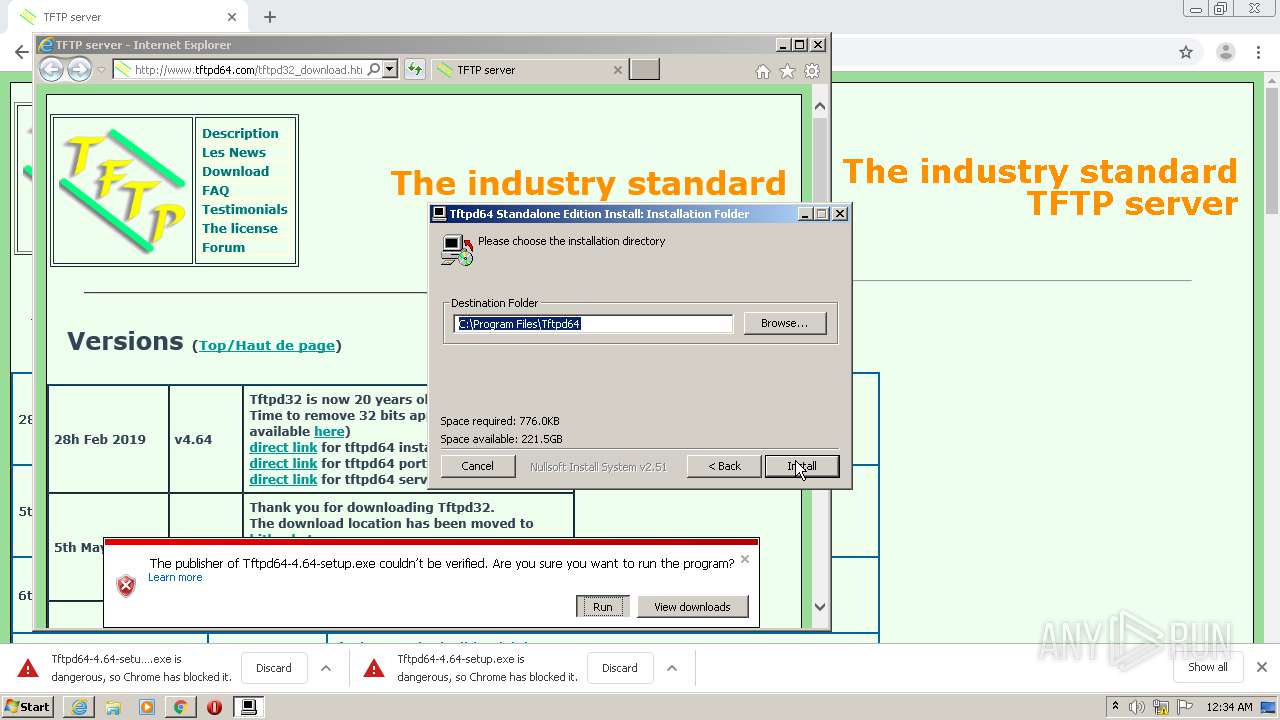
Creates a software uninstall entry
- Tftpd64-4.64-setup.exe (PID: 3432)
Creates files in the program directory
- Tftpd64-4.64-setup.exe (PID: 3432)
Creates files in the user directory
- Tftpd64-4.64-setup.exe (PID: 3432)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 712)
- iexplore.exe (PID: 2796)
- iexplore.exe (PID: 2168)
- iexplore.exe (PID: 3812)
Reads the hosts file
- chrome.exe (PID: 2468)
- chrome.exe (PID: 712)
Reads Internet Cache Settings
- iexplore.exe (PID: 2168)
- iexplore.exe (PID: 2796)
- iexplore.exe (PID: 3812)
- iexplore.exe (PID: 1924)
Changes internet zones settings
- iexplore.exe (PID: 2168)
Application launched itself
- chrome.exe (PID: 2468)
- iexplore.exe (PID: 2168)
Manual execution by user
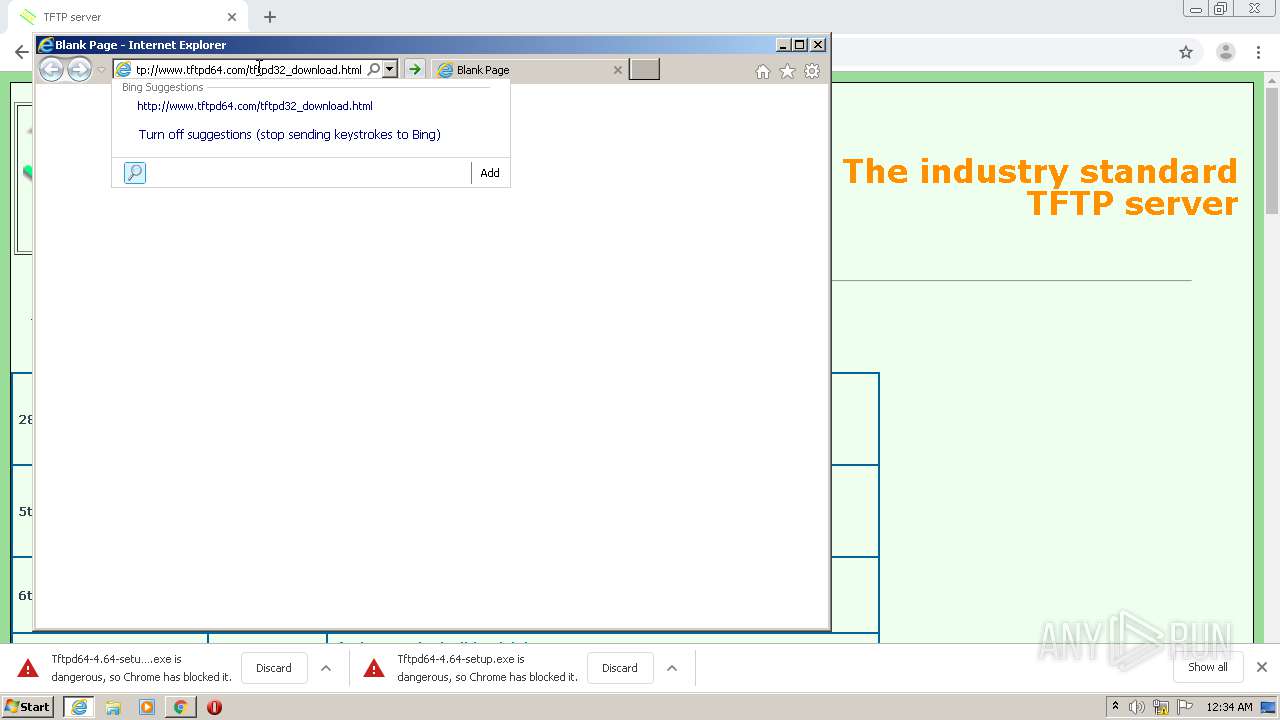
- iexplore.exe (PID: 2168)
Creates files in the user directory
- iexplore.exe (PID: 2796)
- iexplore.exe (PID: 2168)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2168)
Reads internet explorer settings
- iexplore.exe (PID: 2796)
- iexplore.exe (PID: 3812)
- iexplore.exe (PID: 1924)
Dropped object may contain Bitcoin addresses
- Tftpd64-4.64-setup.exe (PID: 3432)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2168)
Changes settings of System certificates
- iexplore.exe (PID: 2168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
22
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,10693027915585049062,10463374581693198966,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10832635424967569800 --mojo-platform-channel-handle=3572 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Tftpd64-4.64-setup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Tftpd64-4.64-setup.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,10693027915585049062,10463374581693198966,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2870031998782924262 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,10693027915585049062,10463374581693198966,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=855606953271532626 --mojo-platform-channel-handle=1056 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10693027915585049062,10463374581693198966,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10482853070135821857 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,10693027915585049062,10463374581693198966,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1375033929380126495 --mojo-platform-channel-handle=1316 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2168 CREDAT:3937548 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.tftpd64.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,10693027915585049062,10463374581693198966,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10810426490929792528 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 866
Read events
2 596
Write events
261
Delete events
9
Modification events
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2468-13241230389727125 |
Value: 259 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
10
Suspicious files
60
Text files
116
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b2643729-77e5-4763-8df9-f556bc301033.tmp | — | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFde753.TMP | text | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFde7d0.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
75
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
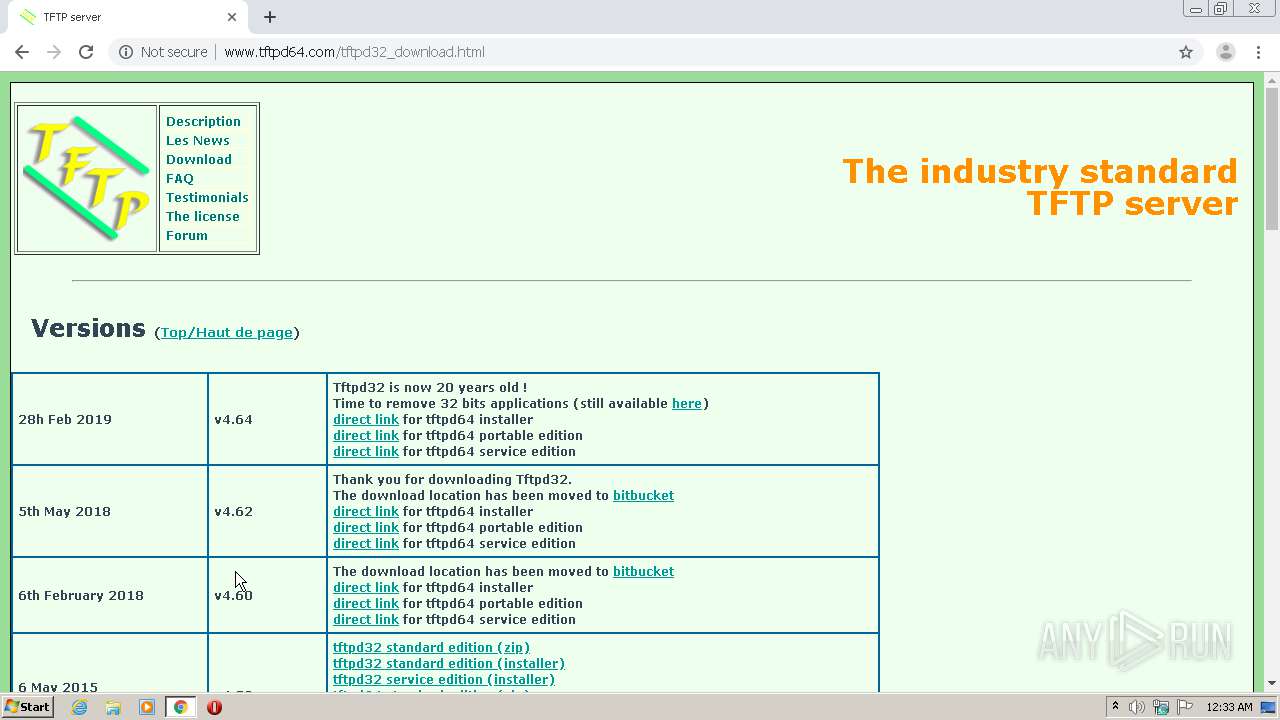
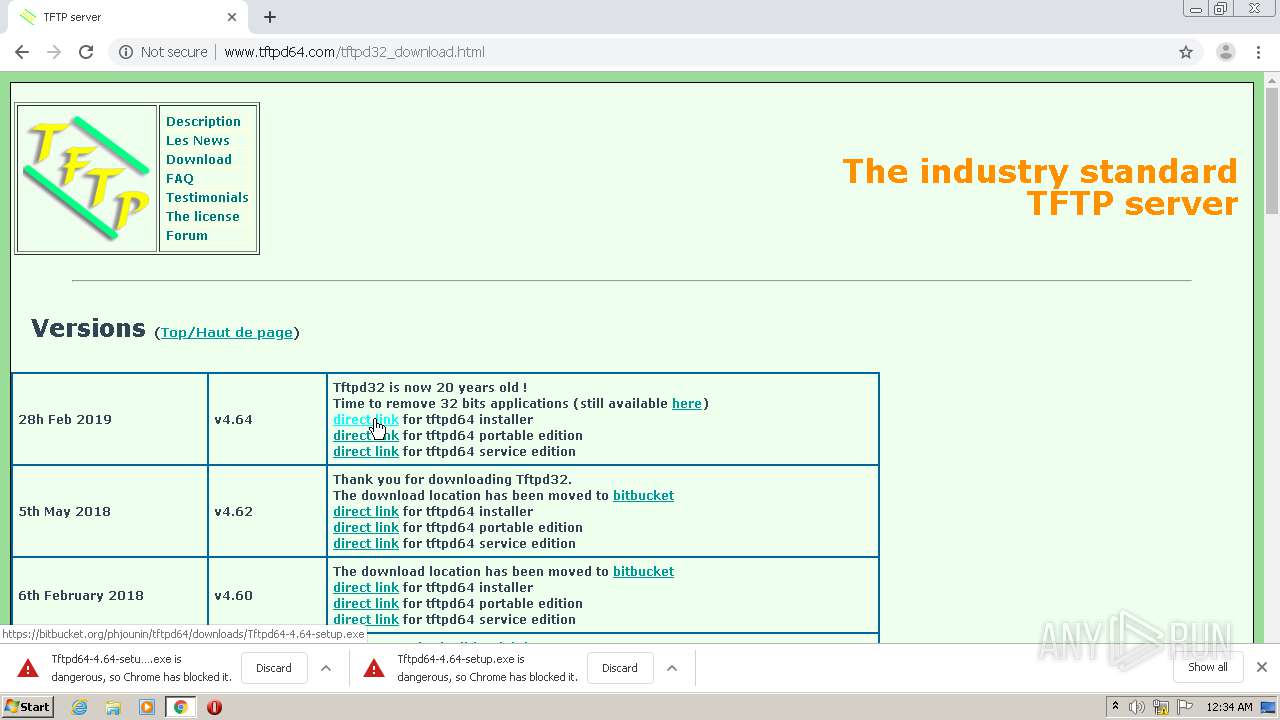
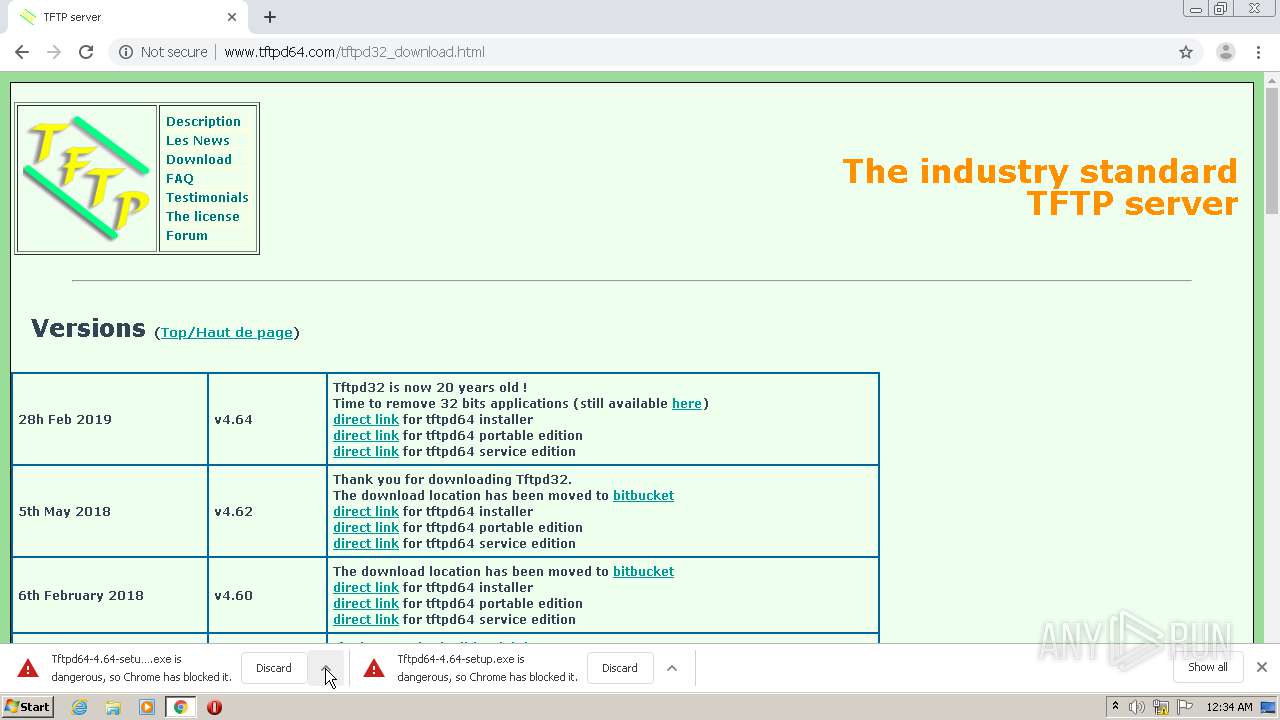
712 | chrome.exe | GET | — | 54.149.64.10:80 | http://www.tftpd64.com/tftpd32_download.html | US | — | — | suspicious |
2796 | iexplore.exe | GET | — | 54.149.64.10:80 | http://www.tftpd64.com/champagne.css | US | — | — | suspicious |
712 | chrome.exe | GET | — | 54.149.64.10:80 | http://www.tftpd64.com/images/r-arrow.jpg | US | — | — | suspicious |
2796 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=about%3Ablankhttp%3A%2F%2Fwww.tftpd64.com%2Ftftpd32_download.html&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 198 b | whitelisted |
2796 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=about%3Ablankhttp%3A%2F%2Fwww.tftpd64.com%2Ftftpd32_download.html&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 198 b | whitelisted |
2796 | iexplore.exe | GET | 200 | 54.149.64.10:80 | http://www.tftpd64.com/tftpd32_download.html | US | html | 17.6 Kb | suspicious |
2796 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAGC%2BAmOouYmuRo7J4Qfua8%3D | US | der | 1.47 Kb | whitelisted |
3812 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
3812 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
2796 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fwww.tftpd64.com%2Ftftpd32_download.html&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 207 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
712 | chrome.exe | 52.216.16.144:443 | bbuseruploads.s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
712 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
712 | chrome.exe | 216.58.212.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
712 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
2168 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2796 | iexplore.exe | 54.149.64.10:80 | www.tftpd64.com | Amazon.com, Inc. | US | suspicious |
2168 | iexplore.exe | 54.149.64.10:80 | www.tftpd64.com | Amazon.com, Inc. | US | suspicious |
2796 | iexplore.exe | 18.205.93.1:443 | bitbucket.org | — | US | malicious |
712 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
712 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.tftpd64.com |
| suspicious |
accounts.google.com |
| shared |
reboot.pro |
| unknown |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
bitbucket.org |
| shared |
ocsp.digicert.com |
| whitelisted |
bbuseruploads.s3.amazonaws.com |
| shared |
sb-ssl.google.com |
| whitelisted |