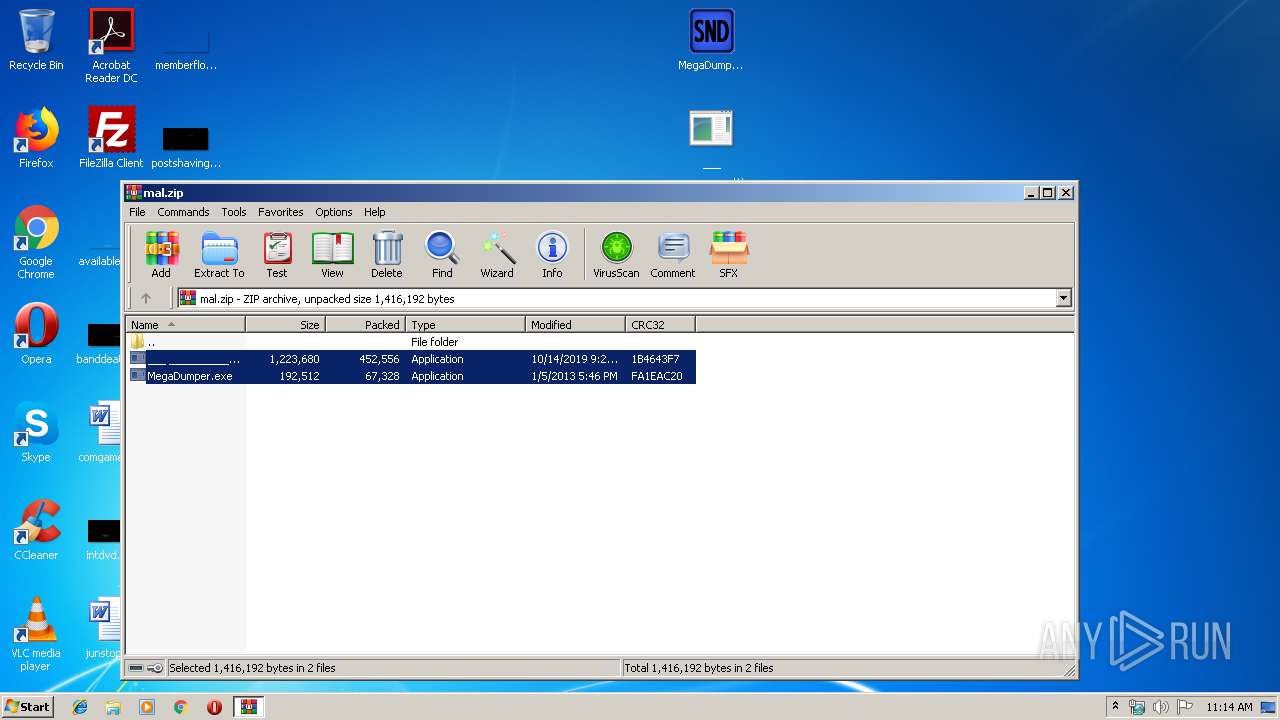
| File name: | mal.zip |
| Full analysis: | https://app.any.run/tasks/1337d779-0a2f-4f32-9931-ca4aadb5b909 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 10:14:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4D19ADFE1864FE3B7ADB77FD5BD4F847 |
| SHA1: | B305CBD1A848E912C21A2251281471FEA91E9449 |
| SHA256: | 83148438E5C977107F80EFA8D193CBA9D23172591593BD408F519EC88F8F1037 |
| SSDEEP: | 12288:JNFv3xGqPb7mZhFohWHdu5a5CEIfI7bVTSE8:rFv37mZnoMHI56CEbHVuE8 |
MALICIOUS
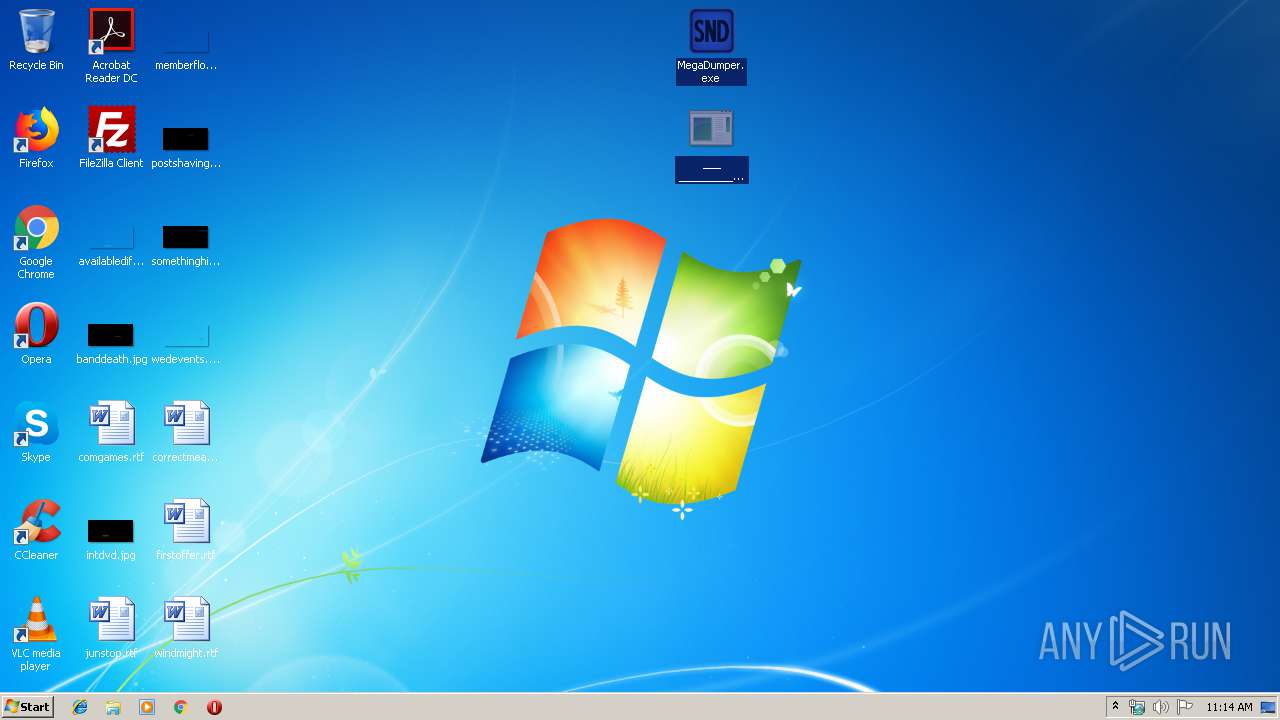
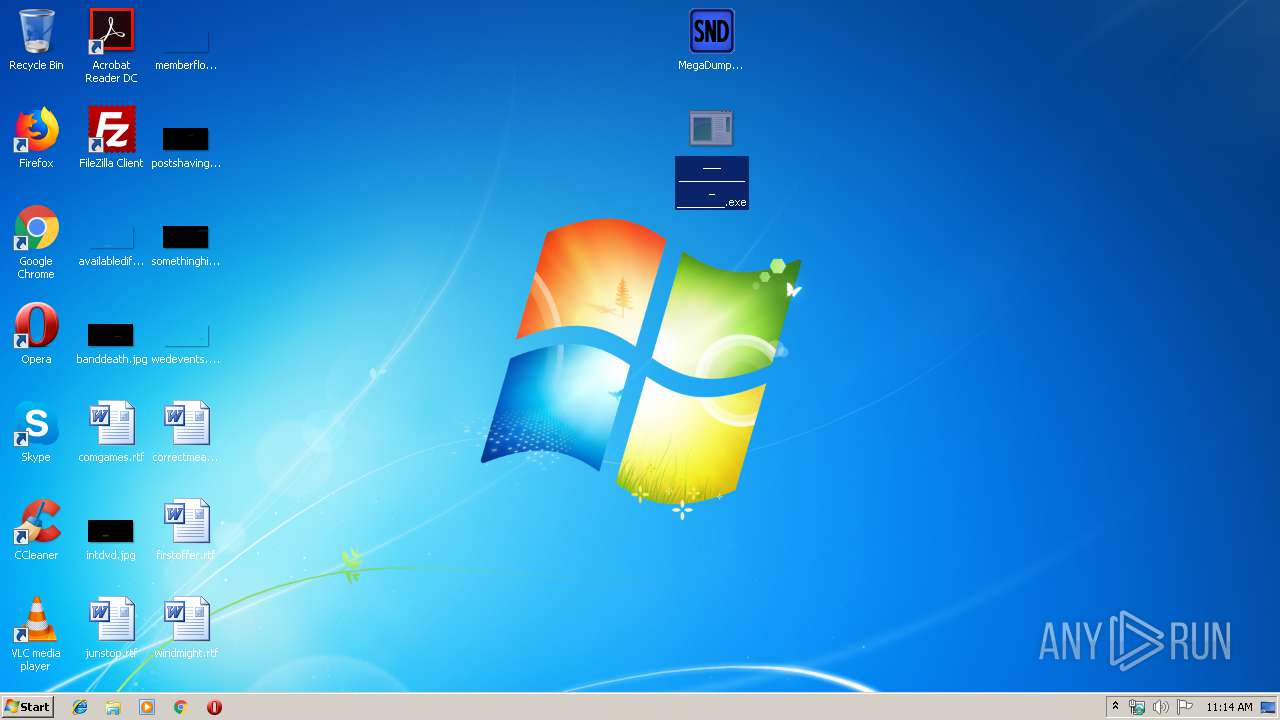
Application was dropped or rewritten from another process
- ___ ____________ ________.exe (PID: 2552)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 2444)
SUSPICIOUS
Loads DLL from Mozilla Firefox
- RegAsm.exe (PID: 2444)
Connects to SMTP port
- RegAsm.exe (PID: 2444)
INFO
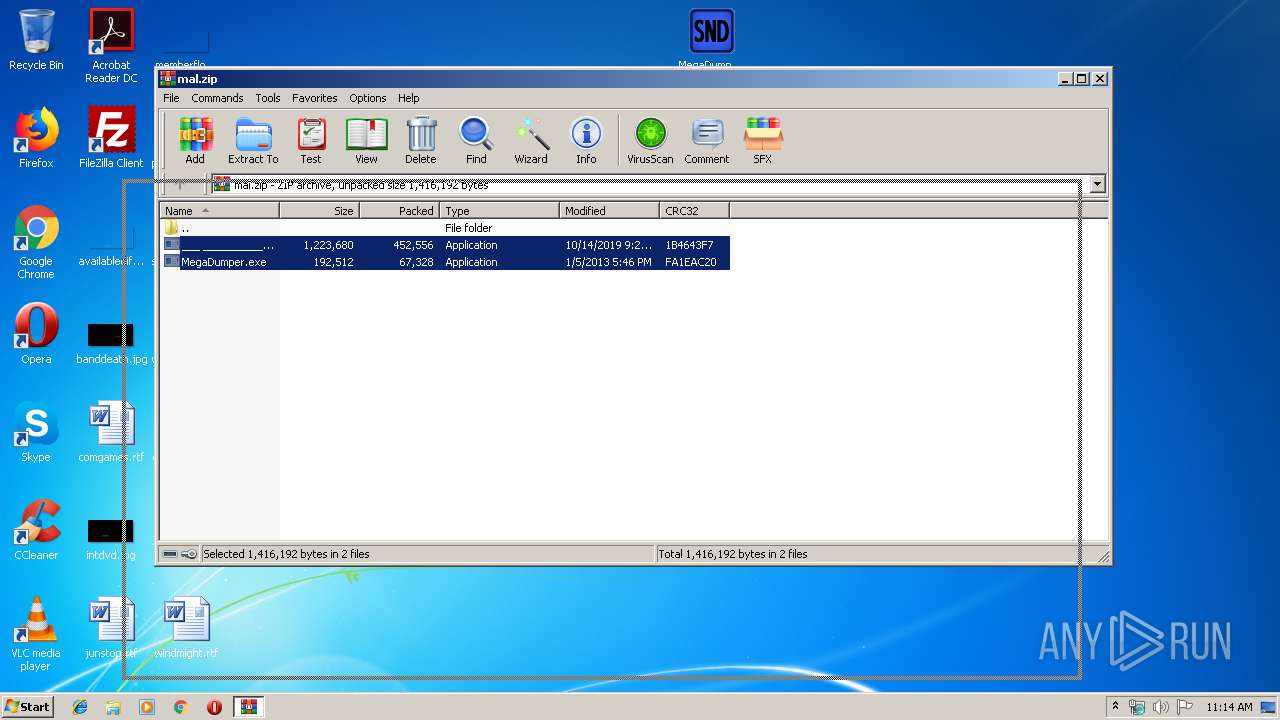
Manual execution by user
- ___ ____________ ________.exe (PID: 2552)
Reads settings of System Certificates
- RegAsm.exe (PID: 2444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2013:01:05 20:46:21 |
| ZipCRC: | 0xfa1eac20 |
| ZipCompressedSize: | 67328 |
| ZipUncompressedSize: | 192512 |
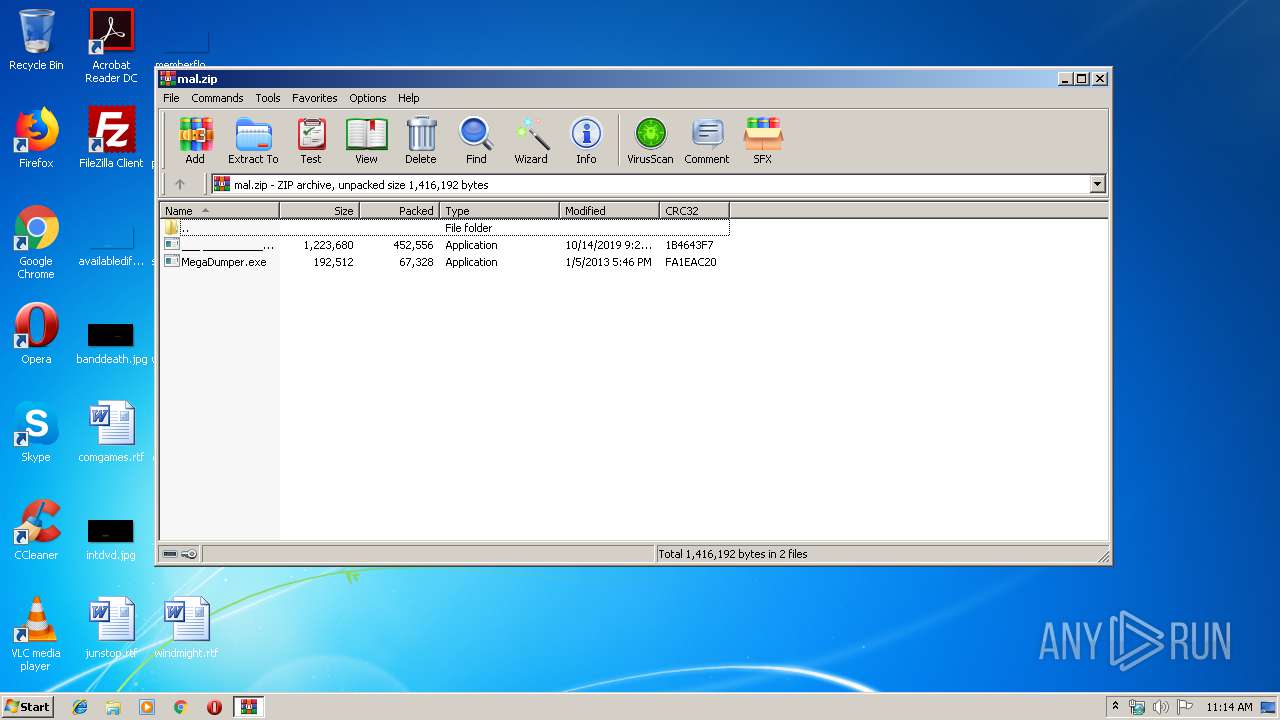
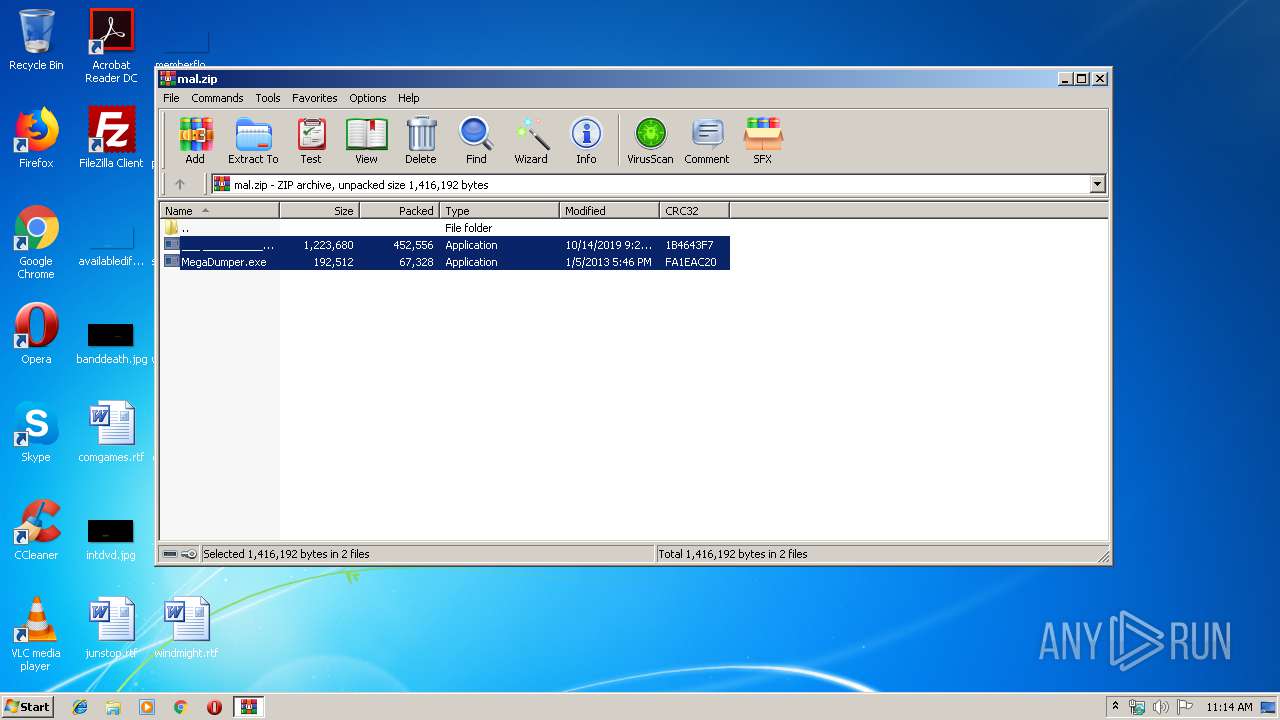
| ZipFileName: | MegaDumper.exe |
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 820 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | — | ___ ____________ ________.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2412 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\mal.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2444 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | ___ ____________ ________.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2552 | "C:\Users\admin\Desktop\___ ____________ ________.exe" | C:\Users\admin\Desktop\___ ____________ ________.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Launcher Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
530
Read events
496
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\mal.zip | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF78000000B400000038040000A9020000 | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2412.7059\MegaDumper.exe | — | |
MD5:— | SHA256:— | |||
| 2412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2412.7059\___ ____________ ________.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2444 | RegAsm.exe | 37.59.89.140:587 | mail.abzmaroc.ma | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mail.abzmaroc.ma |
| suspicious |
Threats
Process | Message |
|---|---|
___ ____________ ________.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
___ ____________ ________.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
___ ____________ ________.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
___ ____________ ________.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
___ ____________ ________.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
___ ____________ ________.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
___ ____________ ________.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, liĊ |
___ ____________ ________.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
___ ____________ ________.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
___ ____________ ________.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|