| File name: | MBSetup.exe |
| Full analysis: | https://app.any.run/tasks/8630ca39-6a6d-4ff3-b5e4-69f30270974f |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2021, 02:00:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AA5BE68ABBAA0375968D2FD823EE7DAA |
| SHA1: | EB32F6A92D46C09613B8BC2E24906512CC071E68 |
| SHA256: | 8307CE702F7B0AB96FB1B65B058439B6EF3CDCDA6BB71E7072A09FCDDAE38E71 |
| SSDEEP: | 24576:IhDNV4Dt1PP5aUAdUImUtZpEwCxOrlZZh:5DtRQfdUIZZpEwCxyvZh |
MALICIOUS
Loads dropped or rewritten executable
- MBAMInstallerService.exe (PID: 1308)
- MBAMService.exe (PID: 588)
- mbamtray.exe (PID: 3596)
- mbam.exe (PID: 1392)
Changes settings of System certificates
- certutil.exe (PID: 1756)
- certutil.exe (PID: 2176)
- certutil.exe (PID: 3584)
- certutil.exe (PID: 2440)
- MBAMService.exe (PID: 588)
Application was dropped or rewritten from another process
- MBAMService.exe (PID: 2464)
- MBAMService.exe (PID: 588)
- mbamtray.exe (PID: 3596)
- mbam.exe (PID: 1392)
Drops executable file immediately after starts
- MBAMService.exe (PID: 588)
SUSPICIOUS
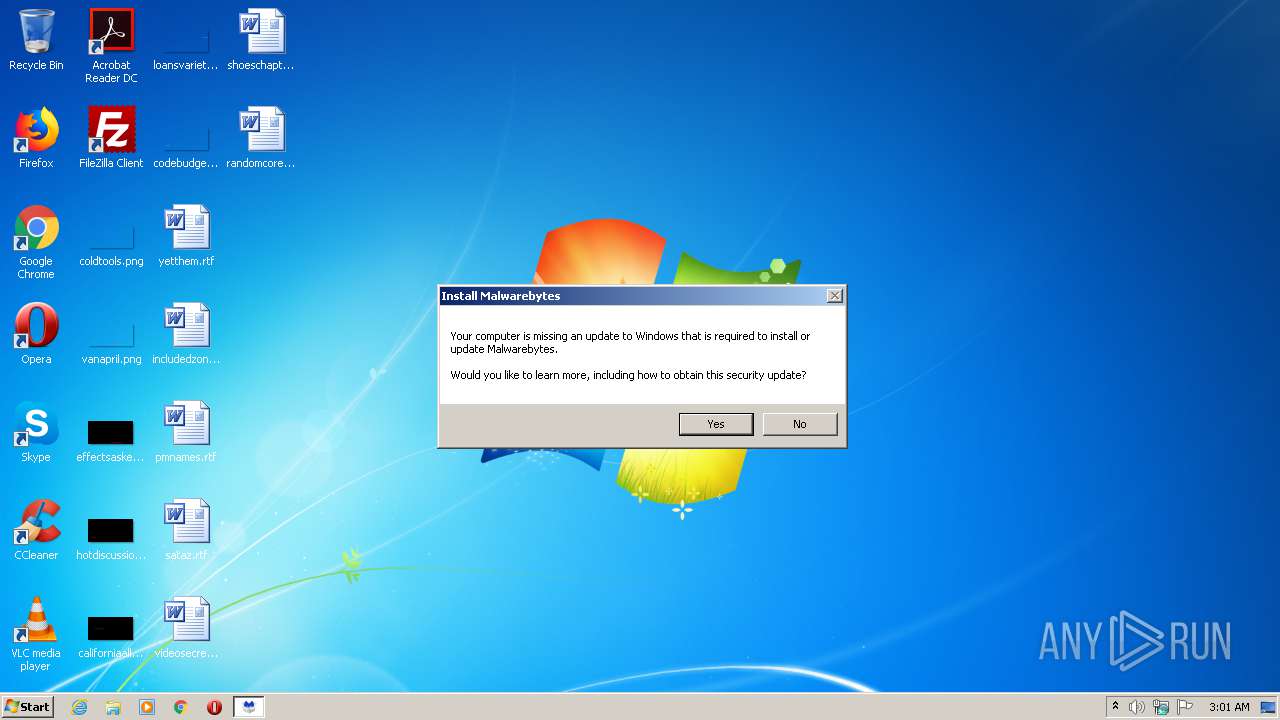
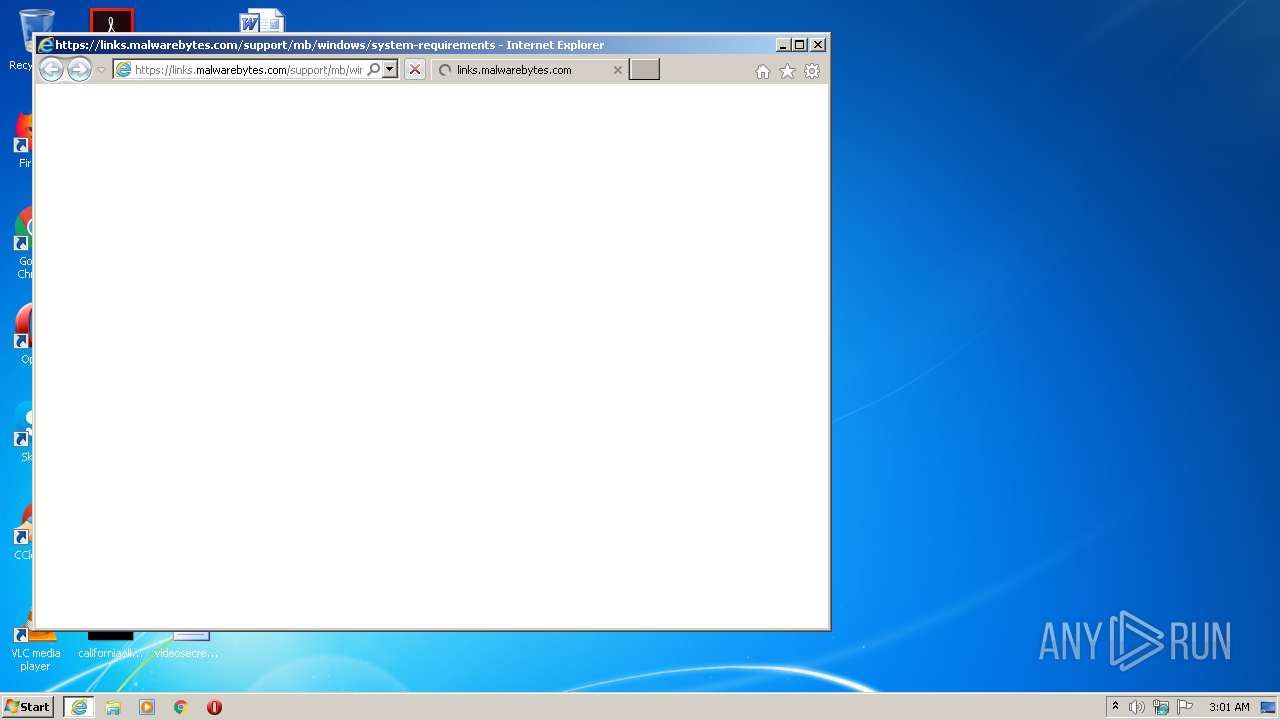
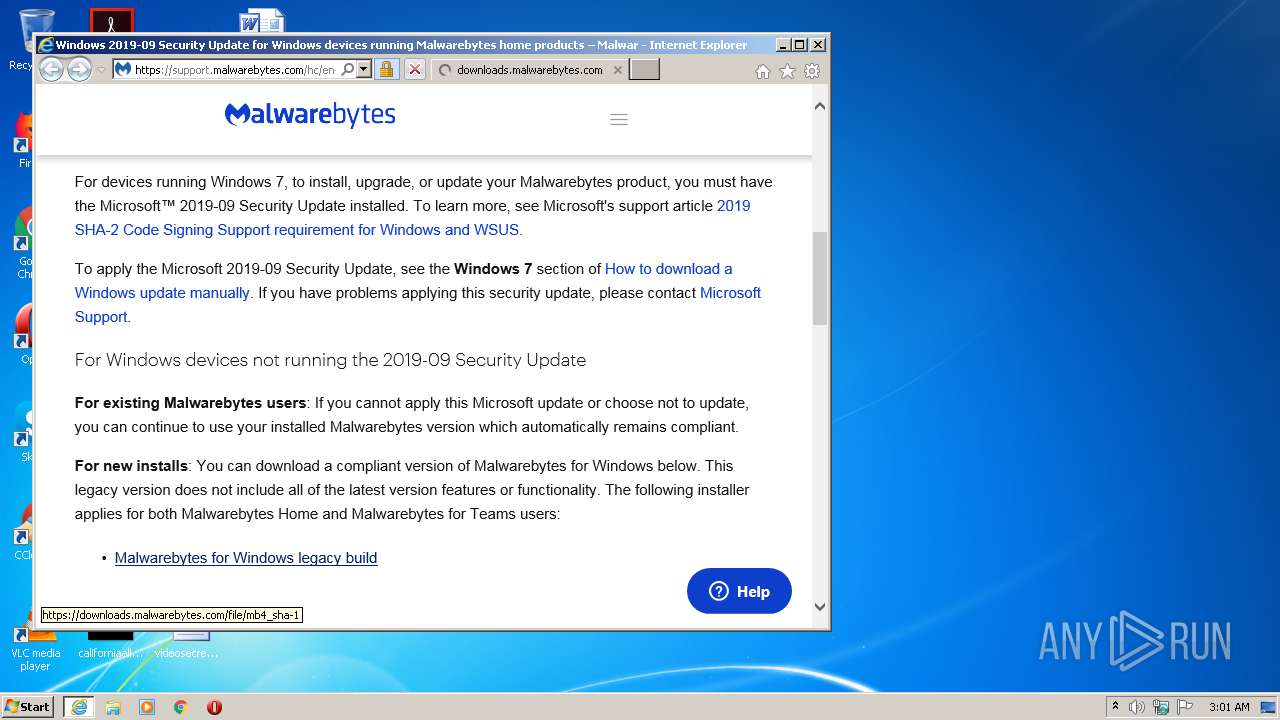
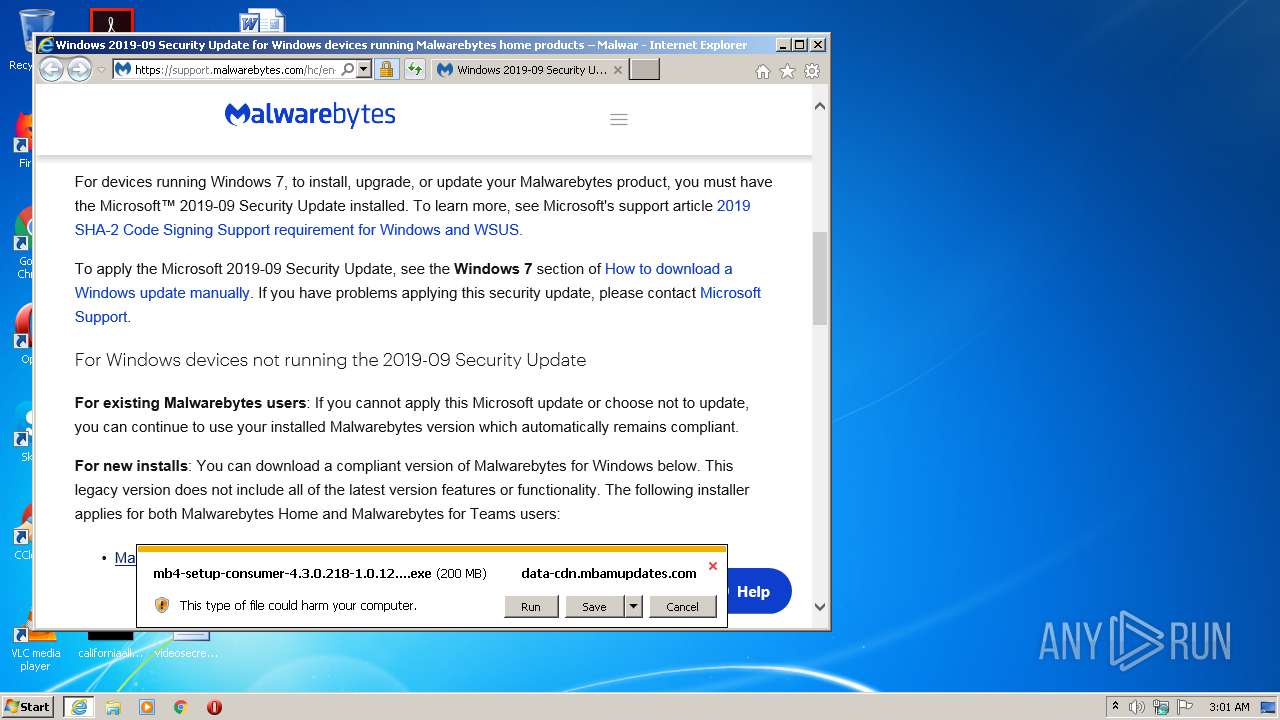
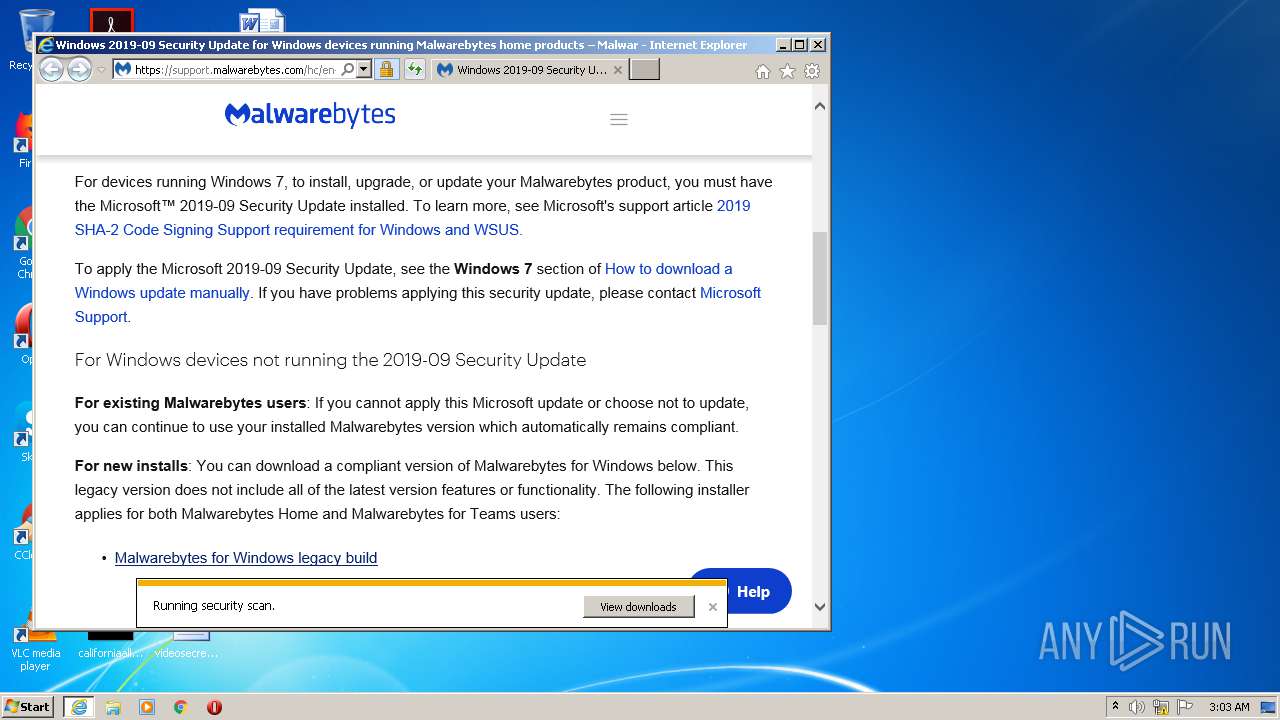
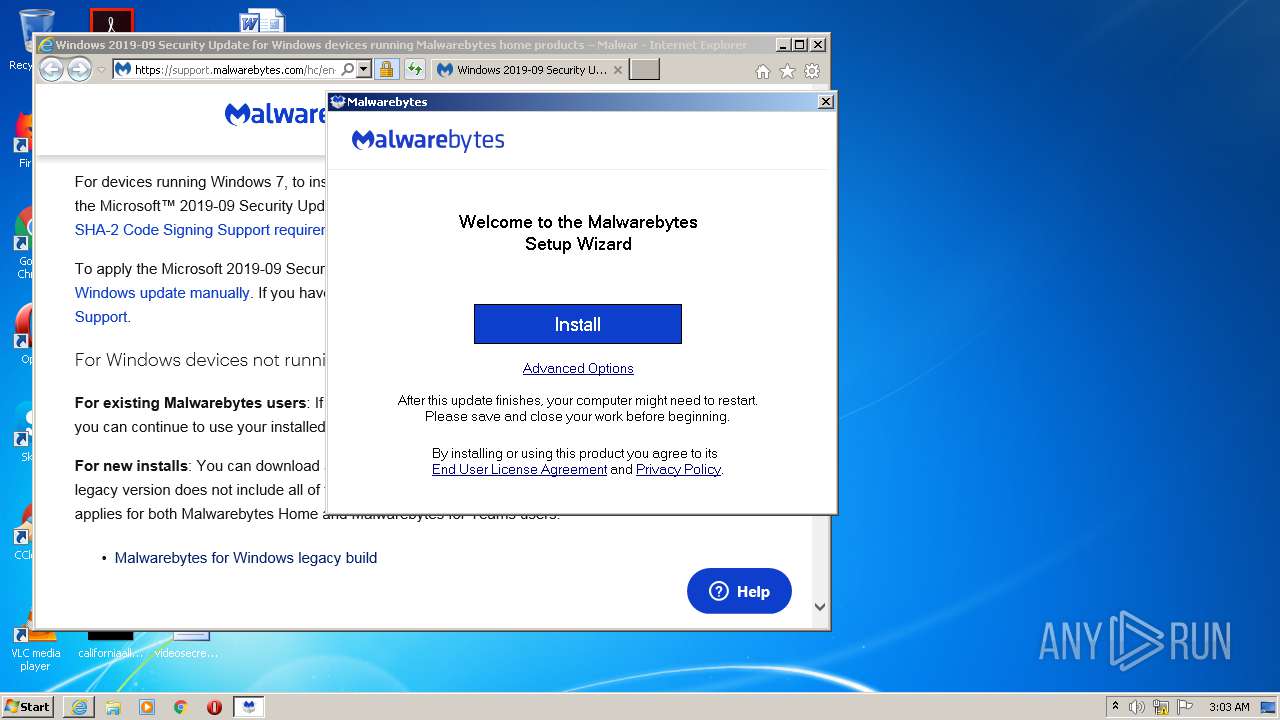
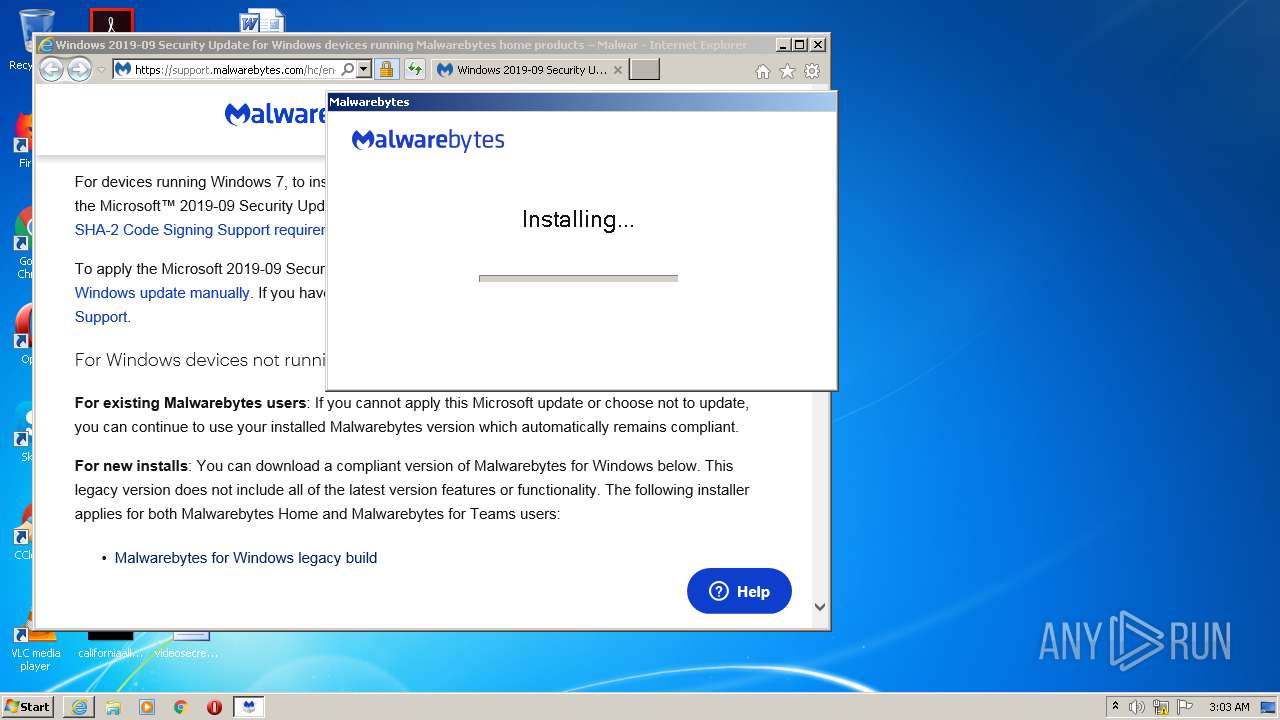
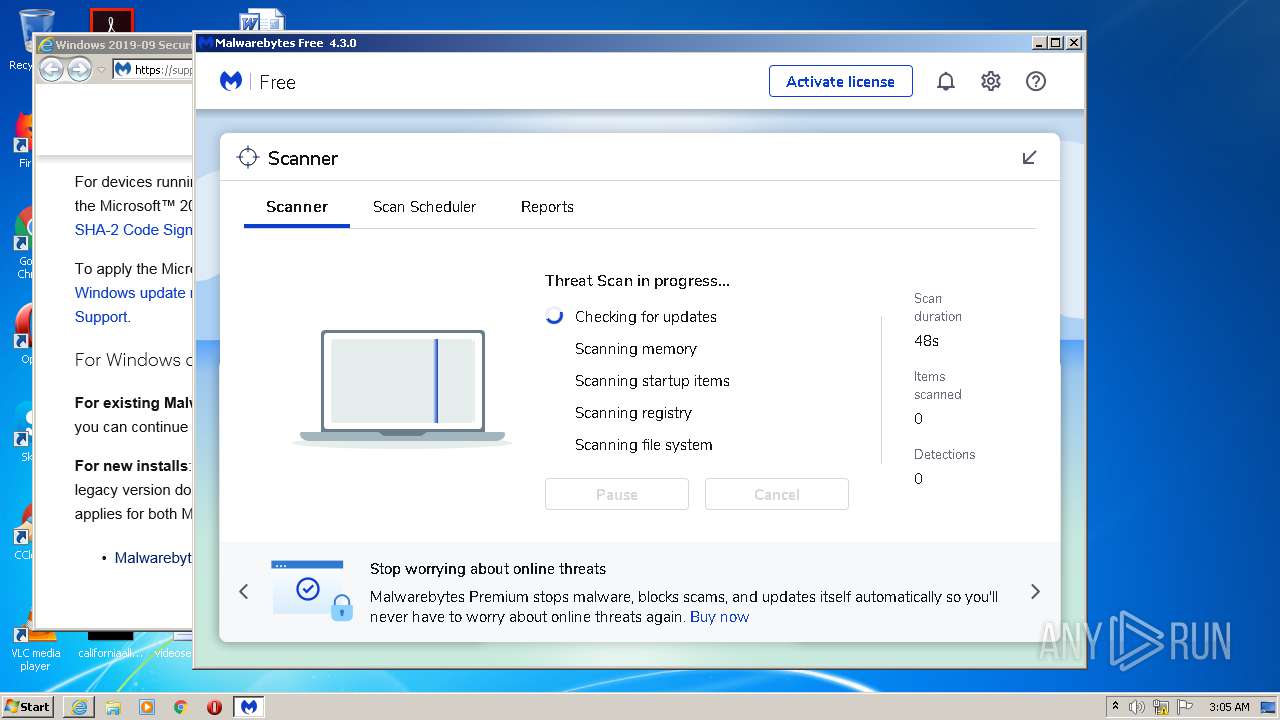
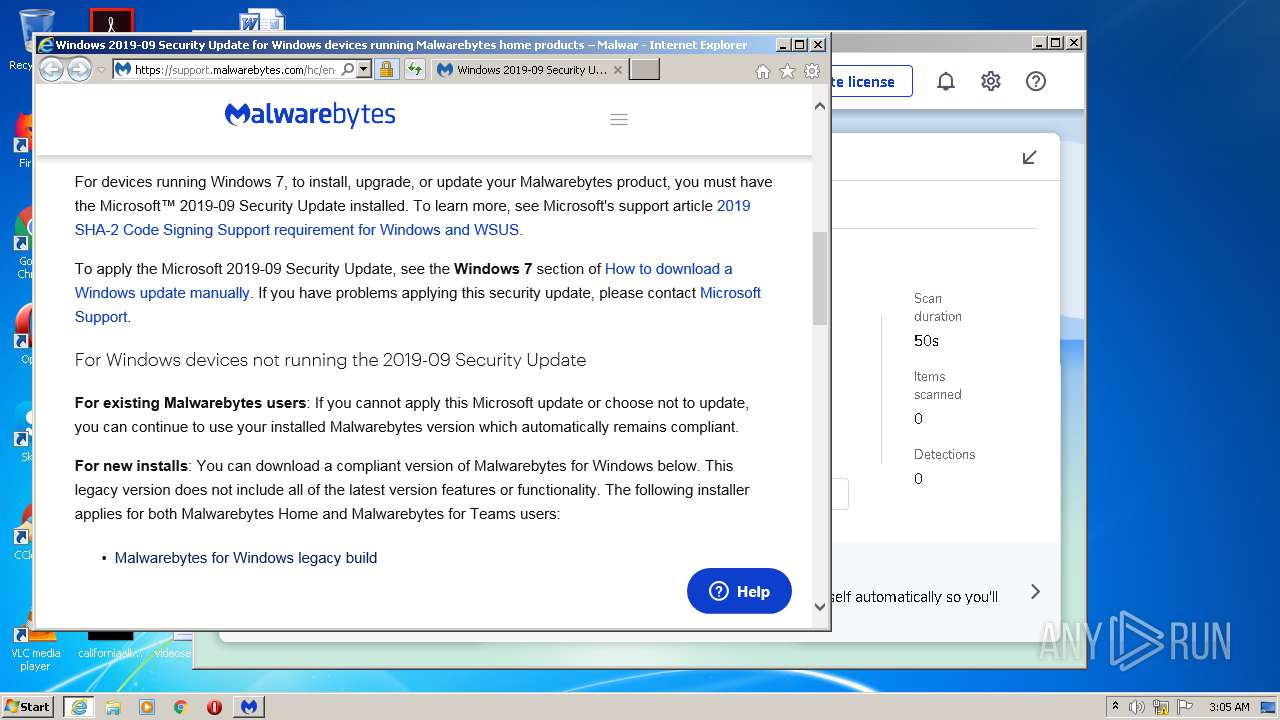
Starts Internet Explorer
- MBSetup.exe (PID: 1912)
Creates files in the Windows directory
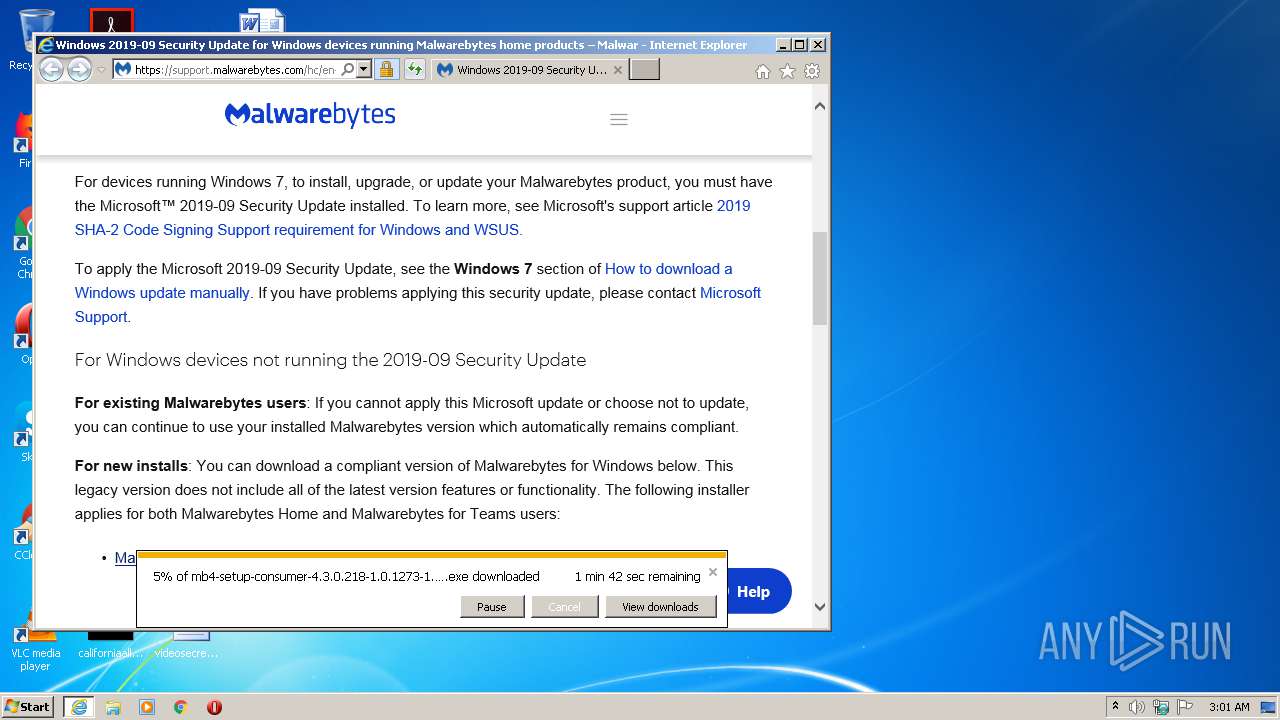
- mb4-setup-consumer-4.3.0.218-1.0.1273-1.0.39721.exe (PID: 4048)
- certutil.exe (PID: 2176)
- certutil.exe (PID: 1756)
- MBAMInstallerService.exe (PID: 1308)
- MBAMService.exe (PID: 2464)
- certutil.exe (PID: 1012)
- certutil.exe (PID: 3000)
- certutil.exe (PID: 3584)
- certutil.exe (PID: 2440)
- MBAMService.exe (PID: 588)
Creates a directory in Program Files
- mb4-setup-consumer-4.3.0.218-1.0.1273-1.0.39721.exe (PID: 4048)
- MBAMInstallerService.exe (PID: 1308)
- MBAMService.exe (PID: 588)
Creates files in the driver directory
- mb4-setup-consumer-4.3.0.218-1.0.1273-1.0.39721.exe (PID: 4048)
- MBAMInstallerService.exe (PID: 1308)
- MBAMService.exe (PID: 588)
Drops a file that was compiled in debug mode
- mb4-setup-consumer-4.3.0.218-1.0.1273-1.0.39721.exe (PID: 4048)
- MBAMInstallerService.exe (PID: 1308)
- MBAMService.exe (PID: 588)
Creates files in the program directory
- mb4-setup-consumer-4.3.0.218-1.0.1273-1.0.39721.exe (PID: 4048)
- MBAMService.exe (PID: 588)
- MBAMInstallerService.exe (PID: 1308)
Removes files from Windows directory
- mb4-setup-consumer-4.3.0.218-1.0.1273-1.0.39721.exe (PID: 4048)
- certutil.exe (PID: 1756)
- certutil.exe (PID: 2176)
- certutil.exe (PID: 1012)
- certutil.exe (PID: 3584)
- certutil.exe (PID: 3000)
- certutil.exe (PID: 2440)
- MBAMInstallerService.exe (PID: 1308)
- MBAMService.exe (PID: 588)
Executable content was dropped or overwritten
- mb4-setup-consumer-4.3.0.218-1.0.1273-1.0.39721.exe (PID: 4048)
- MBAMService.exe (PID: 588)
- MBAMInstallerService.exe (PID: 1308)
Executed as Windows Service
- MBAMInstallerService.exe (PID: 1308)
- MBAMService.exe (PID: 588)
Drops a file with a compile date too recent
- MBAMInstallerService.exe (PID: 1308)
- MBAMService.exe (PID: 588)
Drops a file with too old compile date
- MBAMInstallerService.exe (PID: 1308)
Changes default file association
- MBAMInstallerService.exe (PID: 1308)
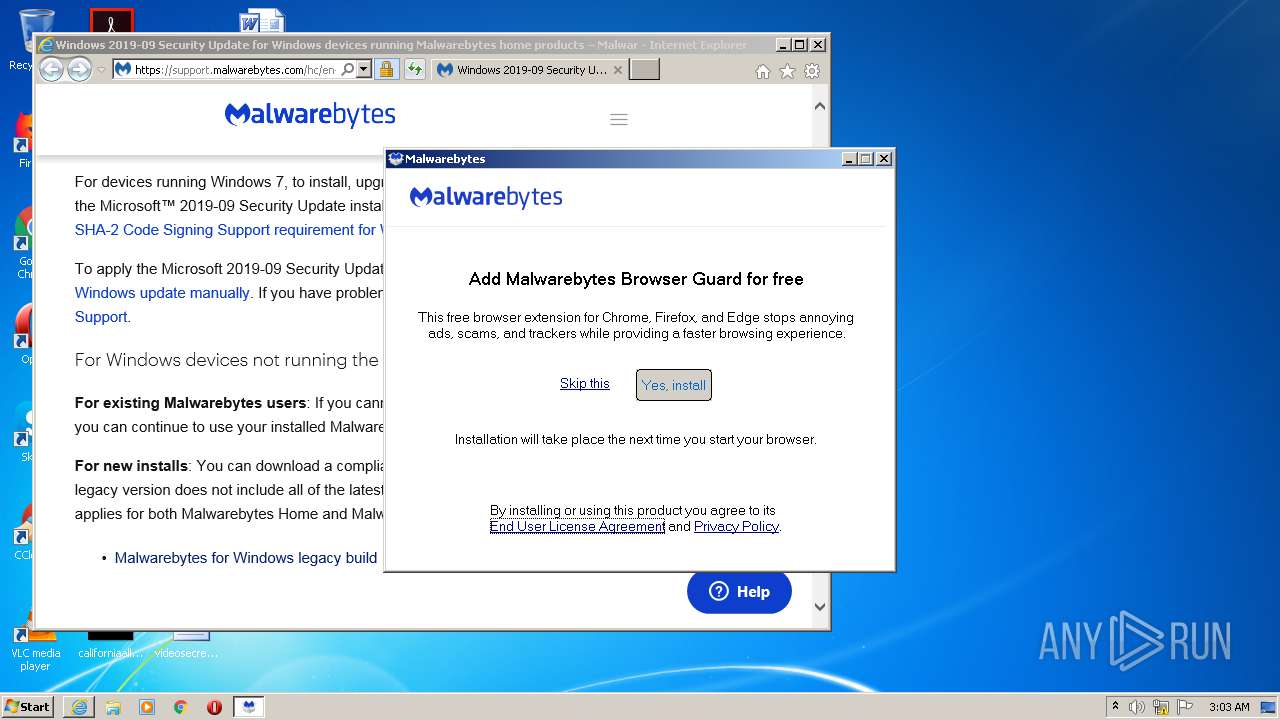
Changes IE settings (feature browser emulation)
- MBAMInstallerService.exe (PID: 1308)
- MBAMService.exe (PID: 588)
Creates or modifies windows services
- MBAMService.exe (PID: 588)
Creates a software uninstall entry
- MBAMInstallerService.exe (PID: 1308)
Creates files in the user directory
- mbam.exe (PID: 1392)
Starts CMD.EXE for commands execution
- MBAMService.exe (PID: 588)
Searches for installed software
- MBAMService.exe (PID: 588)
Creates/Modifies COM task schedule object
- MBAMService.exe (PID: 588)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 1924)
Application launched itself
- iexplore.exe (PID: 380)
Creates files in the user directory
- iexplore.exe (PID: 1924)
- iexplore.exe (PID: 380)
Changes internet zones settings
- iexplore.exe (PID: 380)
Reads settings of System Certificates
- iexplore.exe (PID: 1924)
- iexplore.exe (PID: 380)
- MBAMService.exe (PID: 588)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1924)
- iexplore.exe (PID: 380)
Changes settings of System certificates
- iexplore.exe (PID: 380)
- iexplore.exe (PID: 1924)
Modifies the phishing filter of IE
- iexplore.exe (PID: 380)
Dropped object may contain Bitcoin addresses
- MBAMInstallerService.exe (PID: 1308)
- MBAMService.exe (PID: 588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
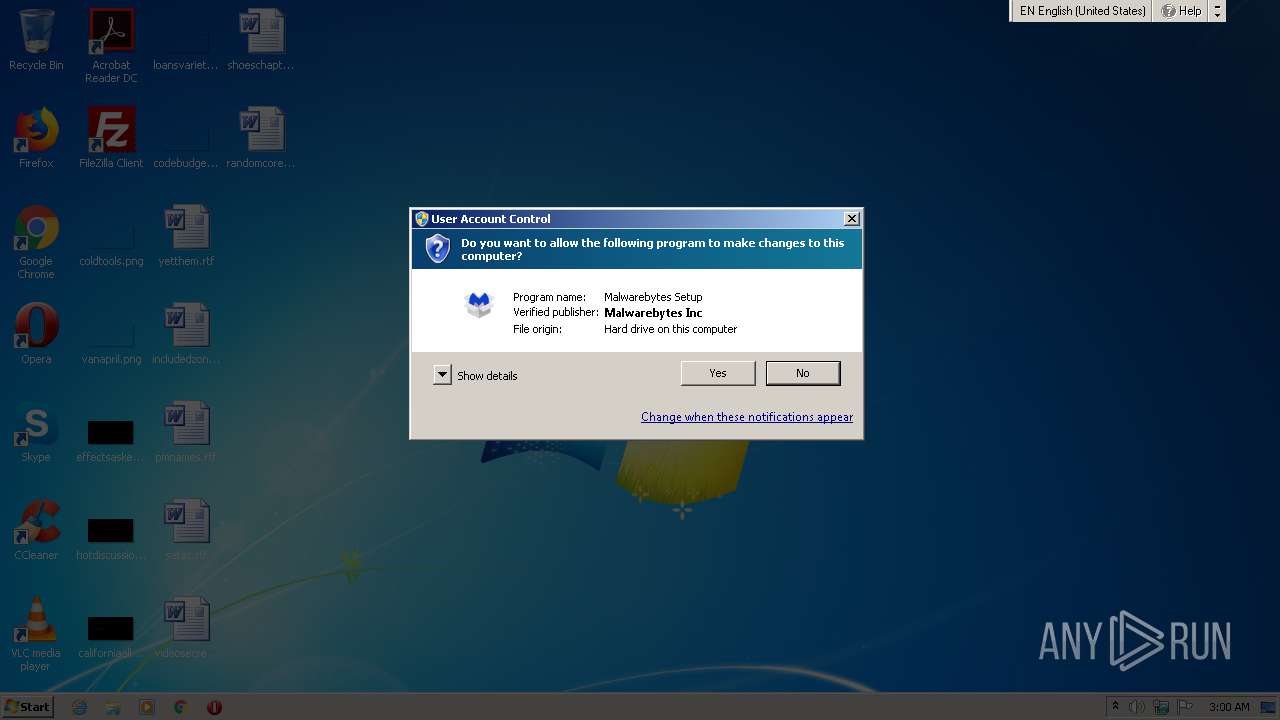
| ProductName: | Malwarebytes |
|---|---|
| OriginalFileName: | MBSetup.exe |
| InternalName: | MBSetup.exe |
| LegalCopyright: | Copyright (C) 2017 - 2020 Malwarebytes, Inc. All rights reserved. |
| FileVersion: | 4.4.0.220 |
| FileDescription: | Malwarebytes Setup |
| CompanyName: | Malwarebytes |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 4.4.0.220 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x4116b |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1530368 |
| CodeSize: | 526336 |
| LinkerVersion: | 14.15 |
| PEType: | PE32 |
| TimeStamp: | 2021:05:05 21:04:54+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-May-2021 19:04:54 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Malwarebytes |
| FileDescription: | Malwarebytes Setup |
| FileVersion: | 4.4.0.220 |
| LegalCopyright: | Copyright (C) 2017 - 2020 Malwarebytes, Inc. All rights reserved. |
| InternalName: | MBSetup.exe |
| OriginalFilename: | MBSetup.exe |
| ProductName: | Malwarebytes |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-May-2021 19:04:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00080727 | 0x00080800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60394 |
.rdata | 0x00082000 | 0x0001FBE2 | 0x0001FC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.1487 |
.data | 0x000A2000 | 0x00005190 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.31089 |
.rsrc | 0x000A8000 | 0x001497D0 | 0x00149800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.66753 |
.reloc | 0x001F2000 | 0x00007394 | 0x00007400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.68618 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.16648 | 1842 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.77507 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 4.01467 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 4.15499 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.31512 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 4.69584 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 4.9625 | 266 | UNKNOWN | UNKNOWN | RT_STRING |
8 | 3.52137 | 110 | UNKNOWN | UNKNOWN | RT_STRING |
9 | 2.1346 | 2216 | UNKNOWN | English - United States | RT_ICON |
10 | 5.354 | 618 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
SHELL32.dll |
USER32.dll |
WINHTTP.dll |
ole32.dll |
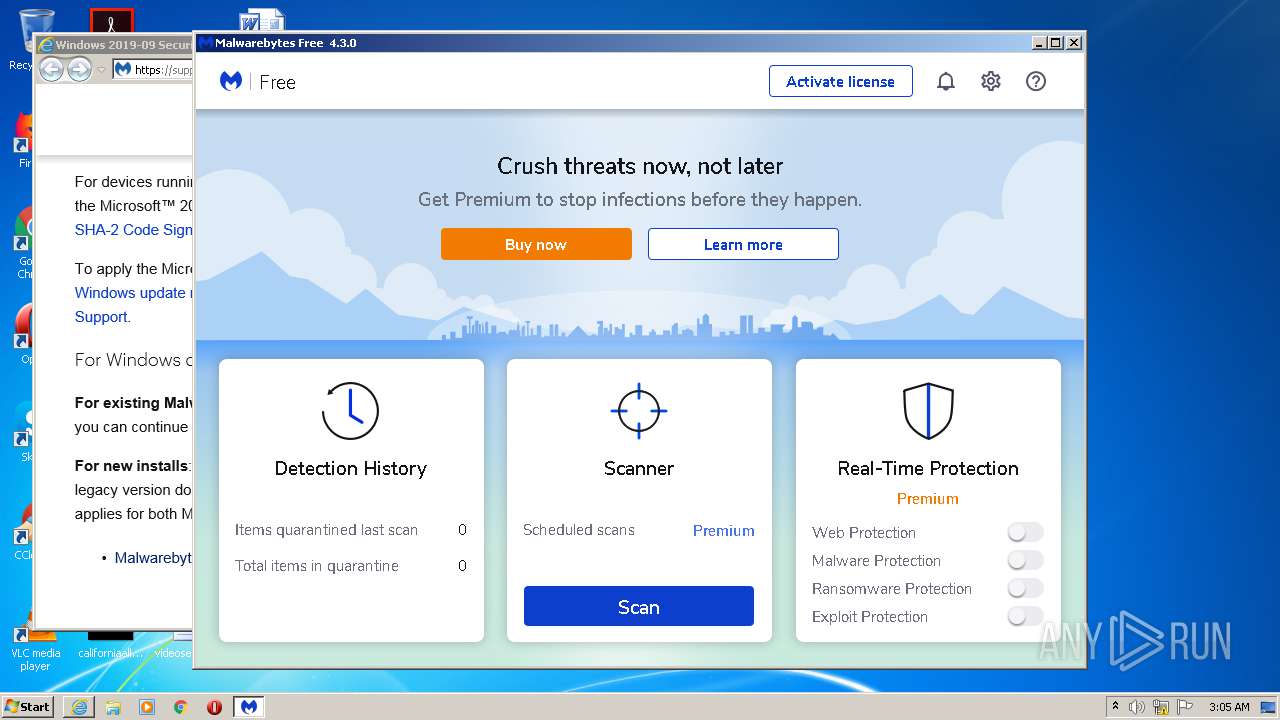
Total processes
75
Monitored processes
22
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 380 | "C:\Program Files\Internet Explorer\iexplore.exe" https://links.malwarebytes.com/support/mb/windows/system-requirements | C:\Program Files\Internet Explorer\iexplore.exe | MBSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 588 | "C:\Program Files\Malwarebytes\Anti-Malware\MBAMService.exe" | C:\Program Files\Malwarebytes\Anti-Malware\MBAMService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Service Exit code: 0 Version: 3.2.0.943 Modules
| |||||||||||||||
| 1012 | certutil.exe -store Root | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1308 | "C:\Users\admin\AppData\Local\Temp\MBAMInstallerService.exe" | C:\Users\admin\AppData\Local\Temp\MBAMInstallerService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Installer Service Exit code: 0 Version: 4.0.0.388 Modules
| |||||||||||||||
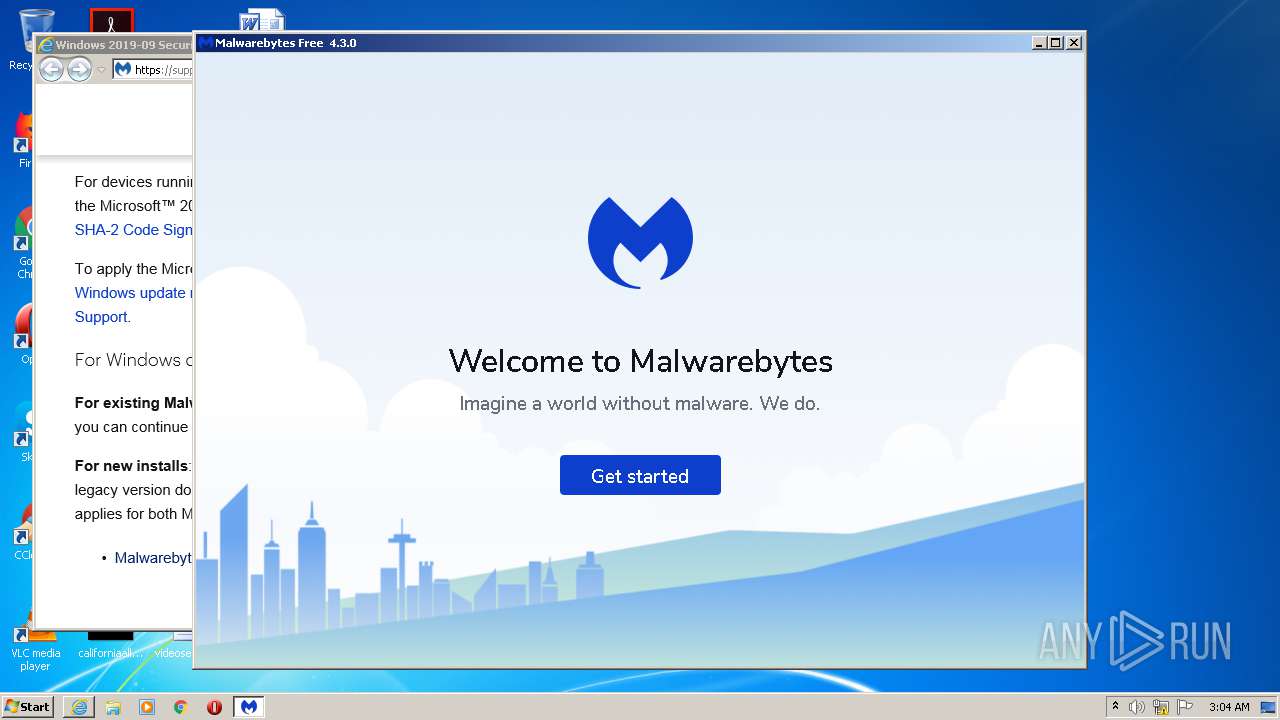
| 1392 | "C:\Program Files\Malwarebytes\Anti-Malware\mbam.exe" | C:\Program Files\Malwarebytes\Anti-Malware\mbam.exe | — | mb4-setup-consumer-4.3.0.218-1.0.1273-1.0.39721.exe | |||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Exit code: 0 Version: 4.0.0.974 Modules
| |||||||||||||||
| 1428 | C:\Windows\system32\cmd.exe /c certutil.exe -f -addStore root C:\PROGRAMDATA\MALWAREBYTES\MBAMSERVICE\dbclsupdate\starfieldrootcag2_new.cer | C:\Windows\system32\cmd.exe | — | MBAMService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1524 | find "Starfield Root Certificate Authority - G2" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1756 | certutil.exe -f -addstore root "C:\Windows\TEMP\MBInstallTemp\servicepkg\DigiCertEVRoot.crt" | C:\Windows\system32\certutil.exe | — | MBAMInstallerService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\AppData\Local\Temp\MBSetup.exe" | C:\Users\admin\AppData\Local\Temp\MBSetup.exe | explorer.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Setup Exit code: 204 Version: 4.4.0.220 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:380 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
4 110
Read events
2 342
Write events
1 758
Delete events
10
Modification events
| (PID) Process: | (1912) MBSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 010000000000000065B5B5D10951D701 | |||
| (PID) Process: | (380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3819909097 | |||
| (PID) Process: | (380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30888201 | |||
| (PID) Process: | (380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A6000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
326
Suspicious files
262
Text files
1 177
Unknown types
102
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1924 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabB4A4.tmp | — | |
MD5:— | SHA256:— | |||
| 1924 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarB4A5.tmp | — | |
MD5:— | SHA256:— | |||
| 1924 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\system-requirements[1].htm | html | |
MD5:— | SHA256:— | |||
| 1924 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 1924 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 1912 | MBSetup.exe | C:\Users\admin\AppData\Local\Temp\mbsetup.log | text | |
MD5:— | SHA256:— | |||
| 1924 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\application-79172500fb4dbec2484043d570946543[1].css | text | |
MD5:— | SHA256:— | |||
| 1924 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\1500004670861[1].htm | html | |
MD5:— | SHA256:— | |||
| 1924 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\644B8874112055B5E195ECB0E8F243A4 | der | |
MD5:— | SHA256:— | |||
| 1924 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\644B8874112055B5E195ECB0E8F243A4 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
94
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1924 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
1924 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEA7rbuoLmJUKAwAAAADMDq4%3D | US | der | 471 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 313 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCHpqj%2FSU2oIwoAAAAAzlPG | US | der | 472 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 313 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
1924 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1924 | iexplore.exe | 13.224.195.128:443 | links.malwarebytes.com | — | US | malicious |
1924 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1924 | iexplore.exe | 104.16.51.111:443 | support.malwarebytes.com | Cloudflare Inc | US | shared |
1924 | iexplore.exe | 88.221.223.58:80 | crl.identrust.com | Akamai International B.V. | — | suspicious |
1924 | iexplore.exe | 104.18.72.113:443 | static.zdassets.com | Cloudflare Inc | US | shared |
1924 | iexplore.exe | 104.16.53.111:443 | support.malwarebytes.com | Cloudflare Inc | US | shared |
1924 | iexplore.exe | 13.224.194.105:443 | d1azc1qln24ryf.cloudfront.net | — | US | unknown |
1924 | iexplore.exe | 13.224.195.54:443 | www.malwarebytes.com | — | US | unknown |
1924 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1924 | iexplore.exe | 142.250.74.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
links.malwarebytes.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
support.malwarebytes.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
static.zdassets.com |
| whitelisted |
p19.zdassets.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
theme.zdassets.com |
| whitelisted |