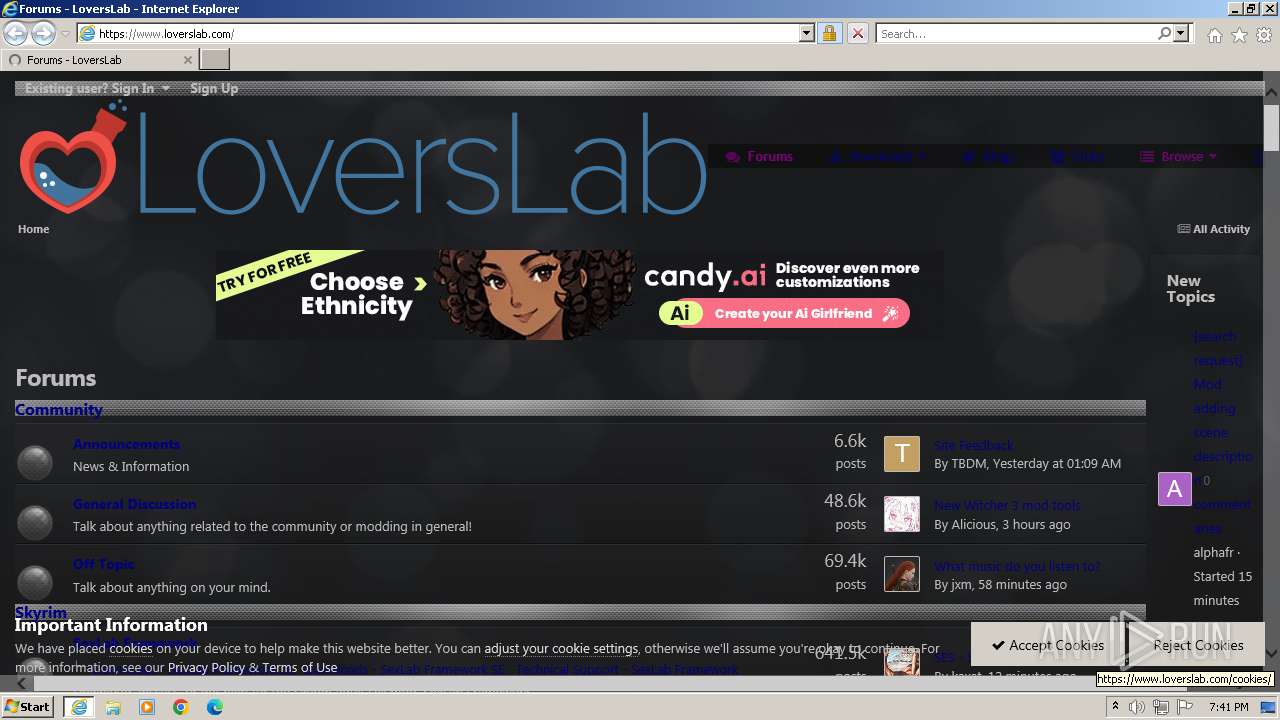
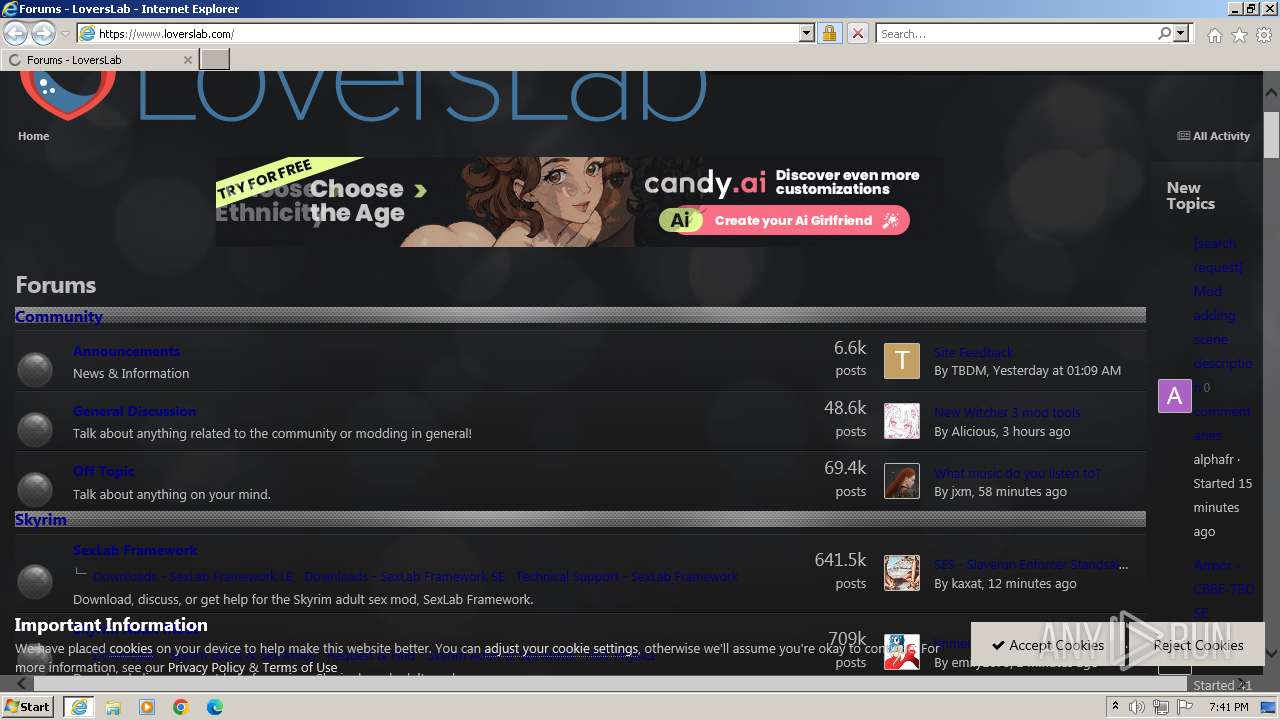
| URL: | www.loverslab.com |
| Full analysis: | https://app.any.run/tasks/b24e9cc8-b477-4022-810f-5840e22b1e28 |
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2024, 18:41:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9A4411D002F0C01FA281BB67B1FC7D27 |
| SHA1: | FB3EEC4B678FC0E9CE2099771DAE12FF70AE444F |
| SHA256: | 82FF6041A6637E9236D99DC3AA227664770A6B1AEF7B6D29A7AF2C57C0A8D1B9 |
| SSDEEP: | 3:ELLK:M2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3984)
Reads the computer name
- wmpnscfg.exe (PID: 312)
Checks supported languages
- wmpnscfg.exe (PID: 312)
Manual execution by a user
- wmpnscfg.exe (PID: 312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3984 | "C:\Program Files\Internet Explorer\iexplore.exe" "www.loverslab.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4040 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3984 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
28 363
Read events
28 234
Write events
94
Delete events
35
Modification events
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31108416 | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31108416 | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
73
Text files
103
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:CFA5E82691410603AC754ED26C49C7E0 | SHA256:A34729DFD3E35796C343A06A1448F7CE2ED1F2B15075D10C87E5B18C08A71DAB | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:6CCC9EC7B4E258782A5DE30FE98359B1 | SHA256:377CF0108819621309AAE2E44B6D96B8121047E6B99C037BDF57BE1F37DC589F | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\OBR40UQO.htm | html | |
MD5:1CCBAC41CC28F29A7B49AAC19EFA3E34 | SHA256:FF1FB56F4721FEAEB186EA8C997BAD6A07D22F5AE5984FBAD561B1068384AAEE | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:6E66BD2D283B36991F7460262E5FF4AE | SHA256:564B4FA6970BF22294BCECA2FB8F53087F3F5DEC9565872D731CEDD80AA9E7C3 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:C90EE62E619D67074019A94B64808BDE | SHA256:FE15FDCD14A279C457F834F51FCFCCD2959B2D5985B9AEC276E5671ED7985ED5 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\05e81b71abe4f22d6eb8d1a929494829_responsive[1].css | text | |
MD5:08BF22349E6BC87CF4D5EC44E8786BA0 | SHA256:57F98EED3BCAA56A1930FD54D8C81C2C56C4AAB62BA2201C05C1CB1538D864D5 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ll.agegate[1].js | html | |
MD5:86DE4314BED281E7BA32059F7B0B1FF9 | SHA256:C1B6B63ABC45175707EC25EE743BBE75E838C662FC3311D402ADA8C4CB312E84 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\90eb5adf50a8c640f633d47fd7eb1778_core[1].css | text | |
MD5:91DC4A3549F3012A32E803A312E10E6A | SHA256:F9097685FE9512C25B7F3FF0D54C28E61F7B0723AE17B41DFCDFF865A505D765 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\5a0da001ccc2200dc5625c3f3934497d_core_responsive[1].css | text | |
MD5:AD1DBD54523F0FDF42EBDAADD00974F2 | SHA256:AE9D33C675A45F0263AC186920780EF9593F2F0FC05CE203A1ED786BE7AFE5E2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
100
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4040 | iexplore.exe | GET | 301 | 104.26.1.96:80 | http://www.loverslab.com/ | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 304 | 23.214.95.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0eb42db1385d6a0b | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQD52znXgmjnXwogfY0LOz7q | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEHJyQIYvow29Ew63GHrhBw4%3D | unknown | — | — | unknown |
4040 | iexplore.exe | GET | — | 23.214.95.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?fc29a11d26449e72 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4040 | iexplore.exe | 104.26.1.96:80 | www.loverslab.com | CLOUDFLARENET | US | unknown |
4040 | iexplore.exe | 104.26.1.96:443 | www.loverslab.com | CLOUDFLARENET | US | unknown |
4040 | iexplore.exe | 23.214.95.202:80 | ctldl.windowsupdate.com | AKAMAI-AS | BR | unknown |
4040 | iexplore.exe | 142.250.181.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
4040 | iexplore.exe | 142.250.185.72:443 | www.googletagmanager.com | GOOGLE | US | unknown |
4040 | iexplore.exe | 185.94.236.246:443 | poweredby.jads.co | Mojohost B.v. | NL | unknown |
4040 | iexplore.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.loverslab.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
static.loverslab.com |
| unknown |
poweredby.jads.co |
| whitelisted |
c.pki.goog |
| unknown |
ocsp.comodoca.com |
| whitelisted |
o.pki.goog |
| unknown |
ocsp.usertrust.com |
| whitelisted |