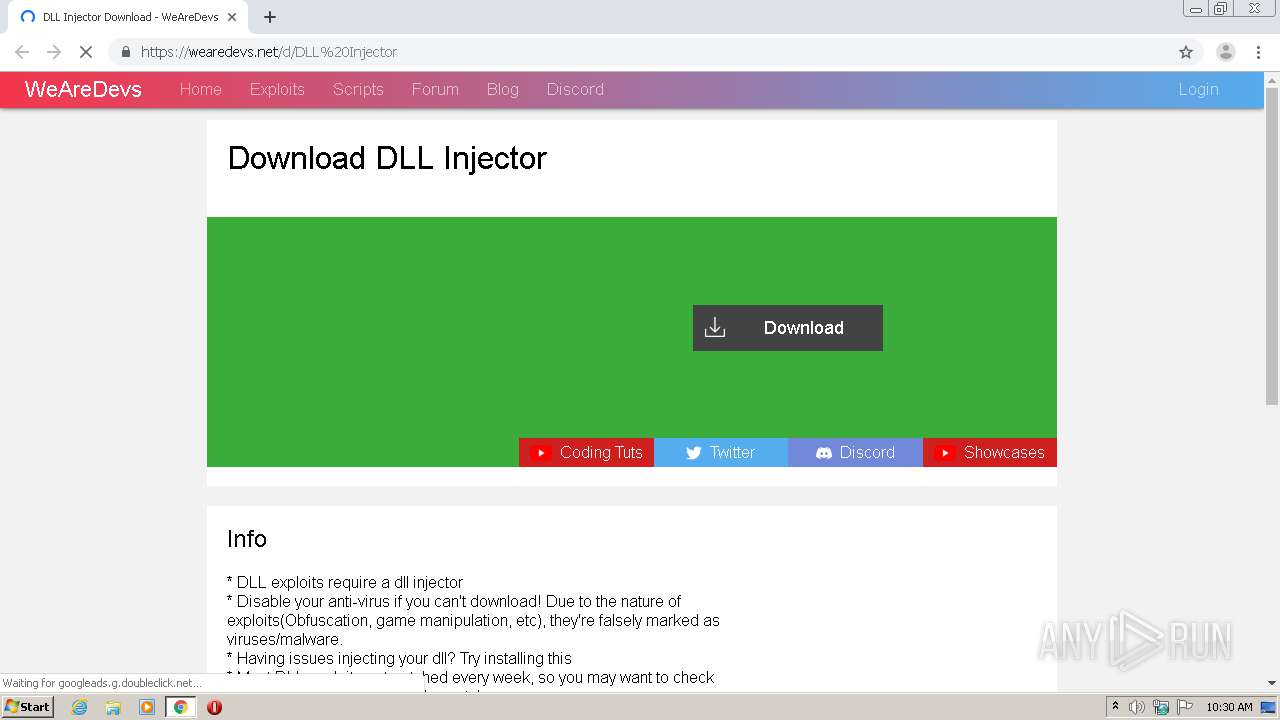
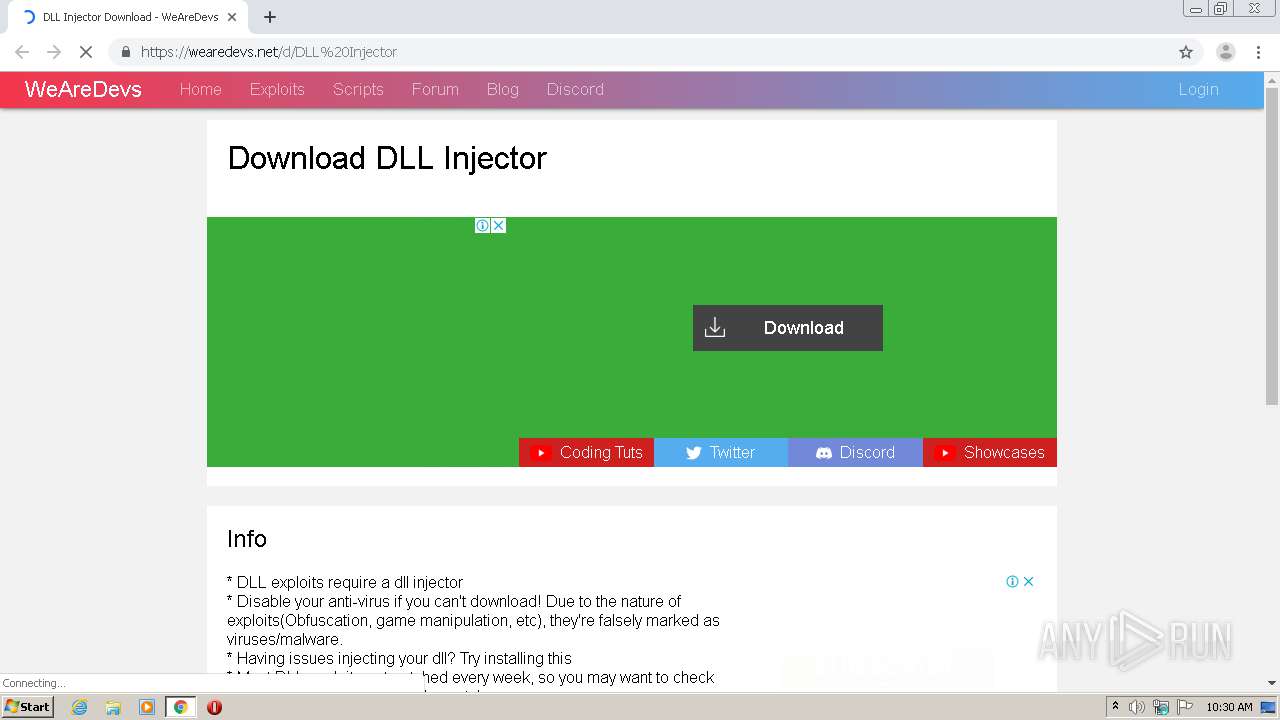
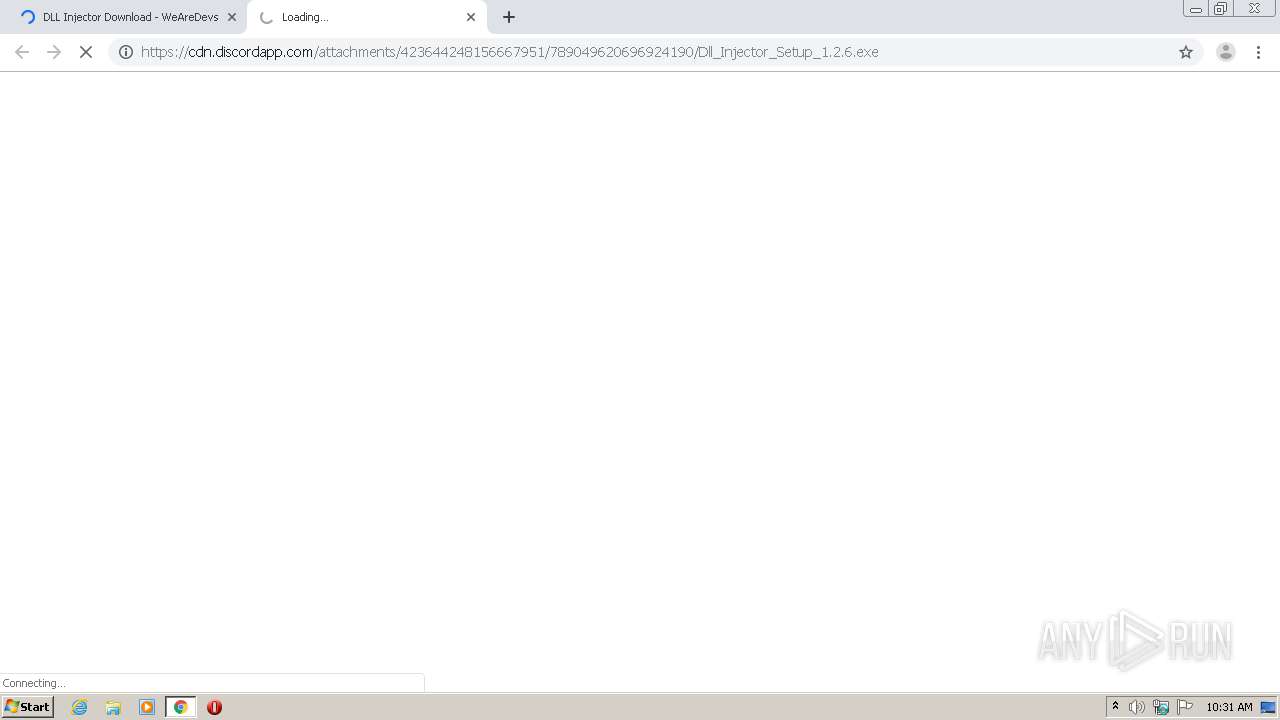
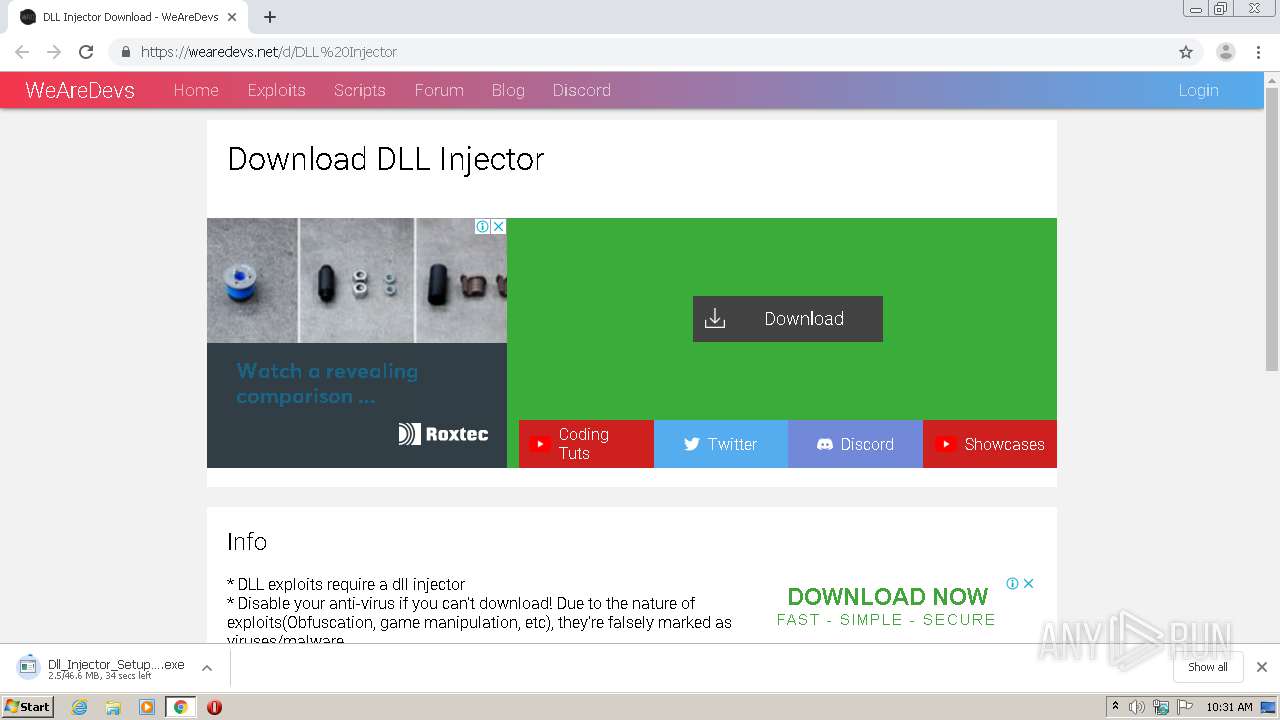
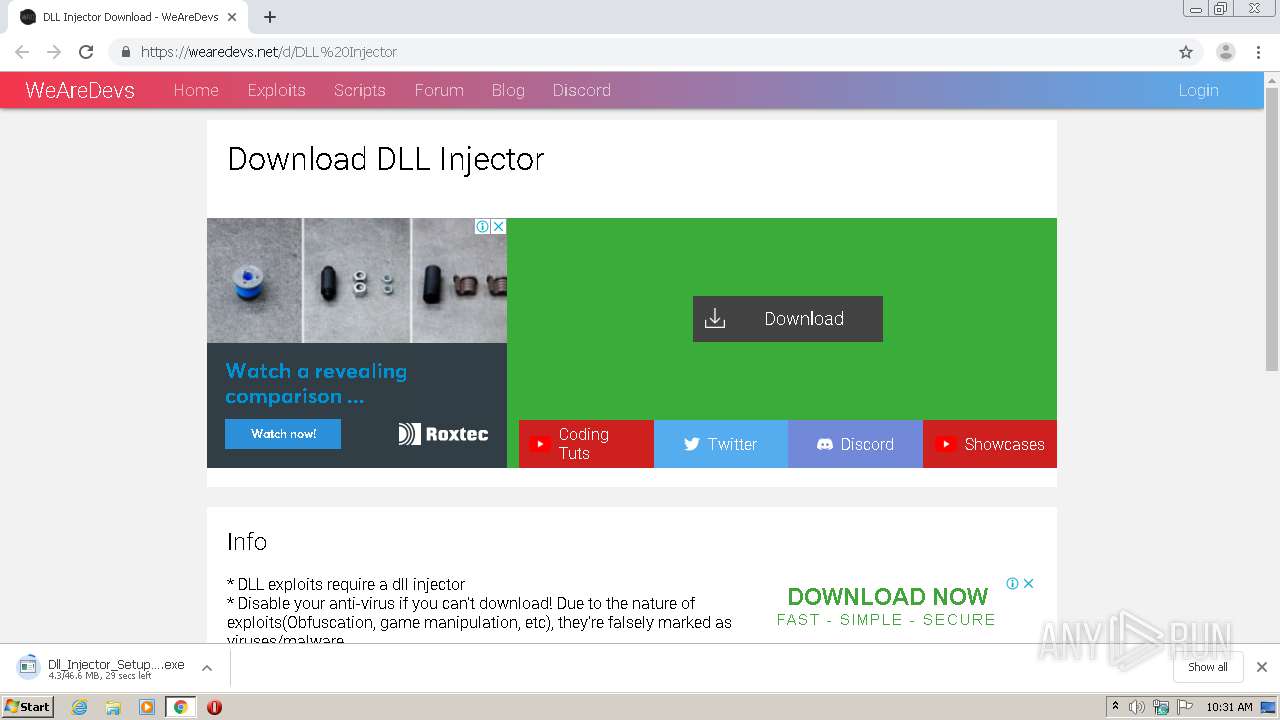
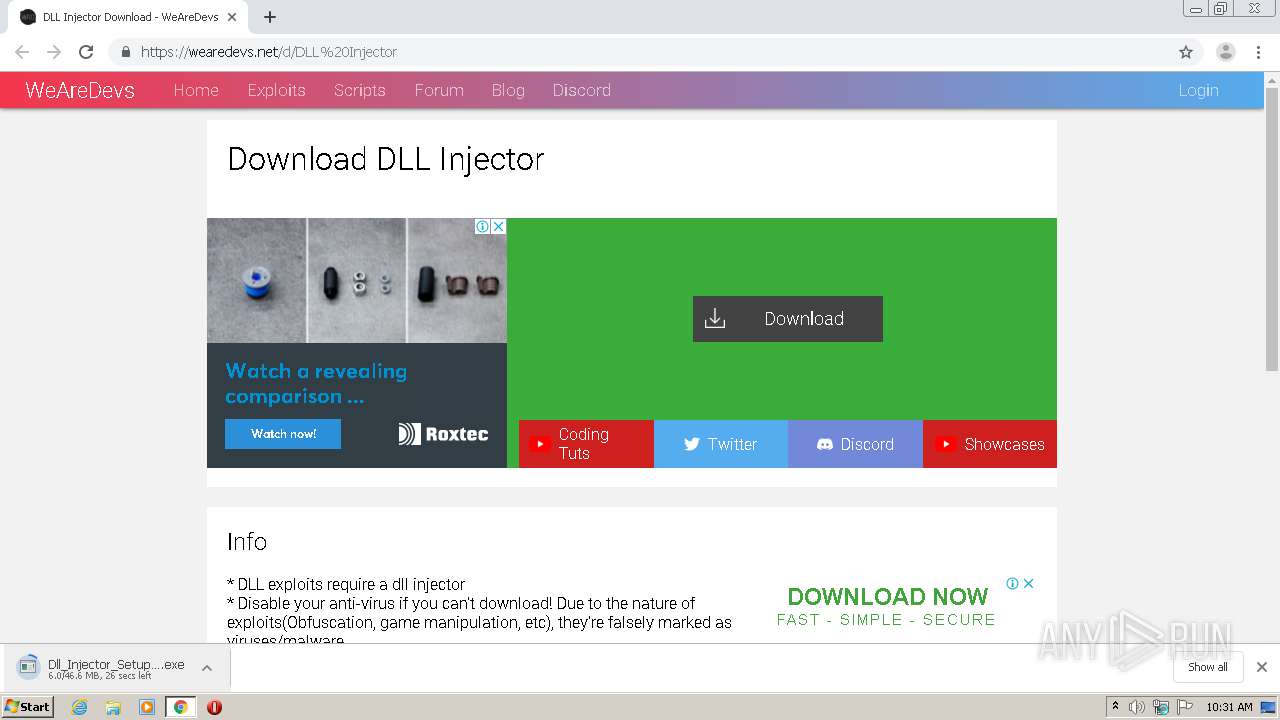
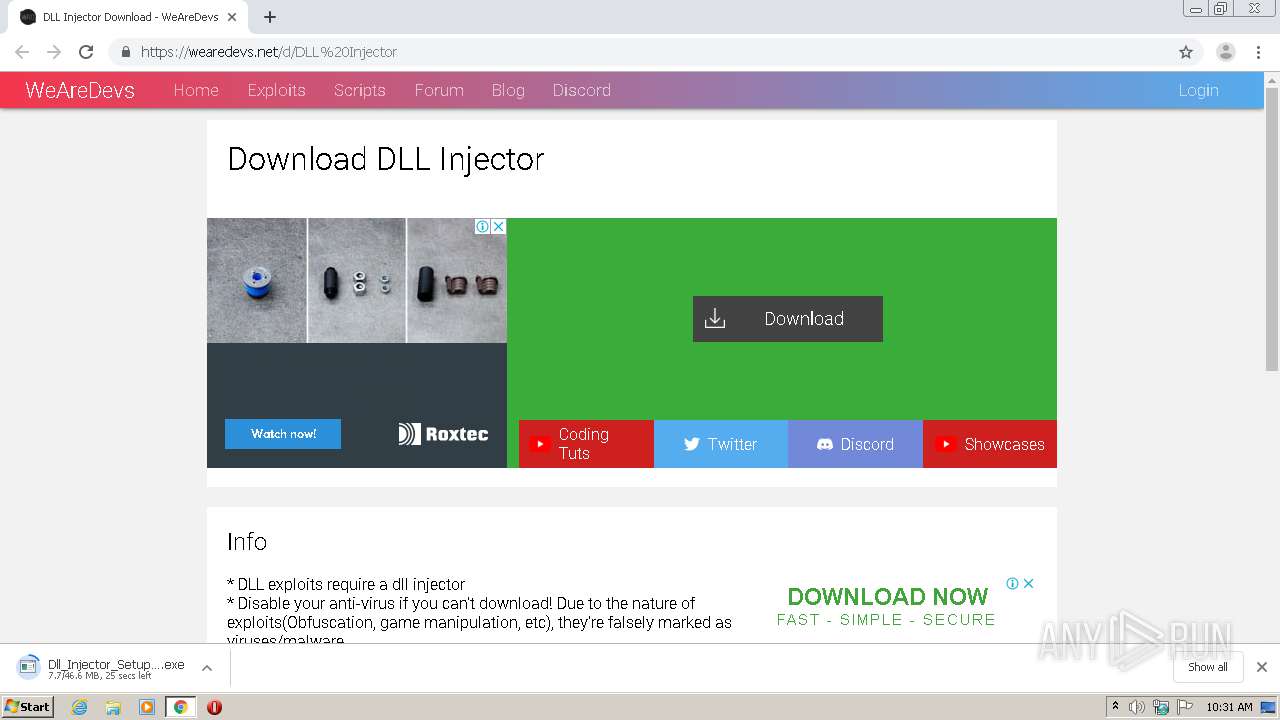
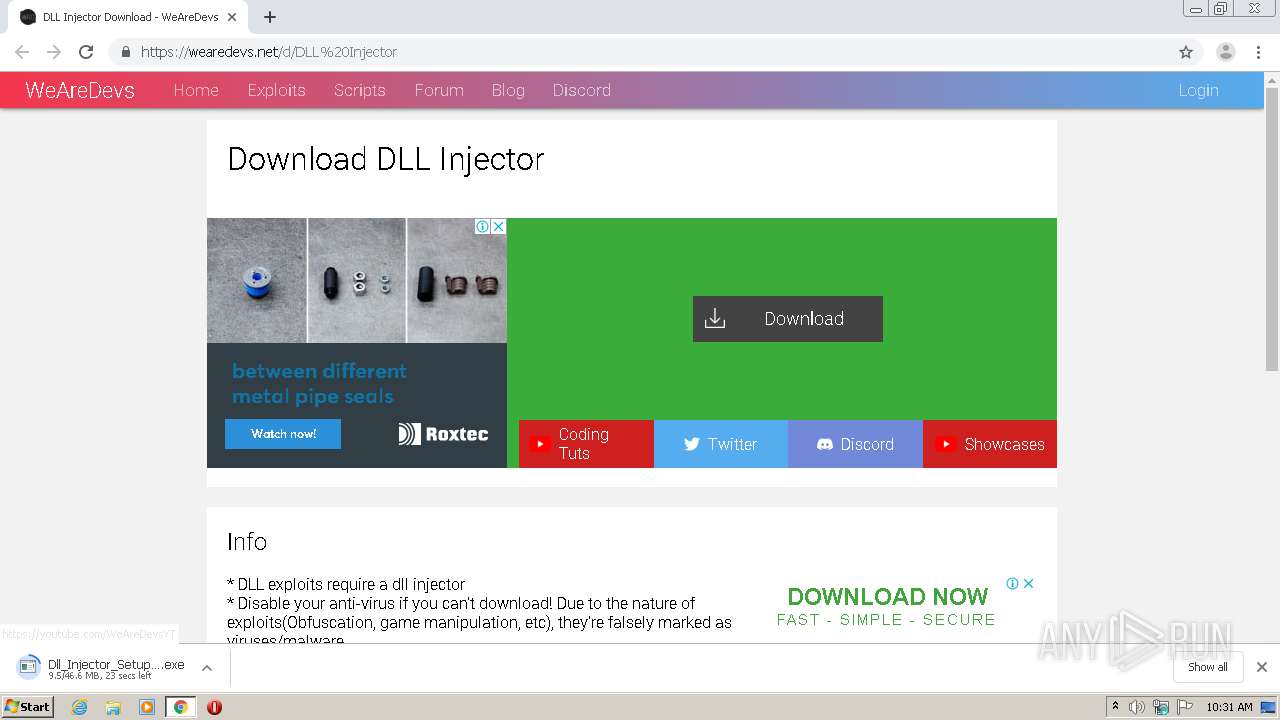
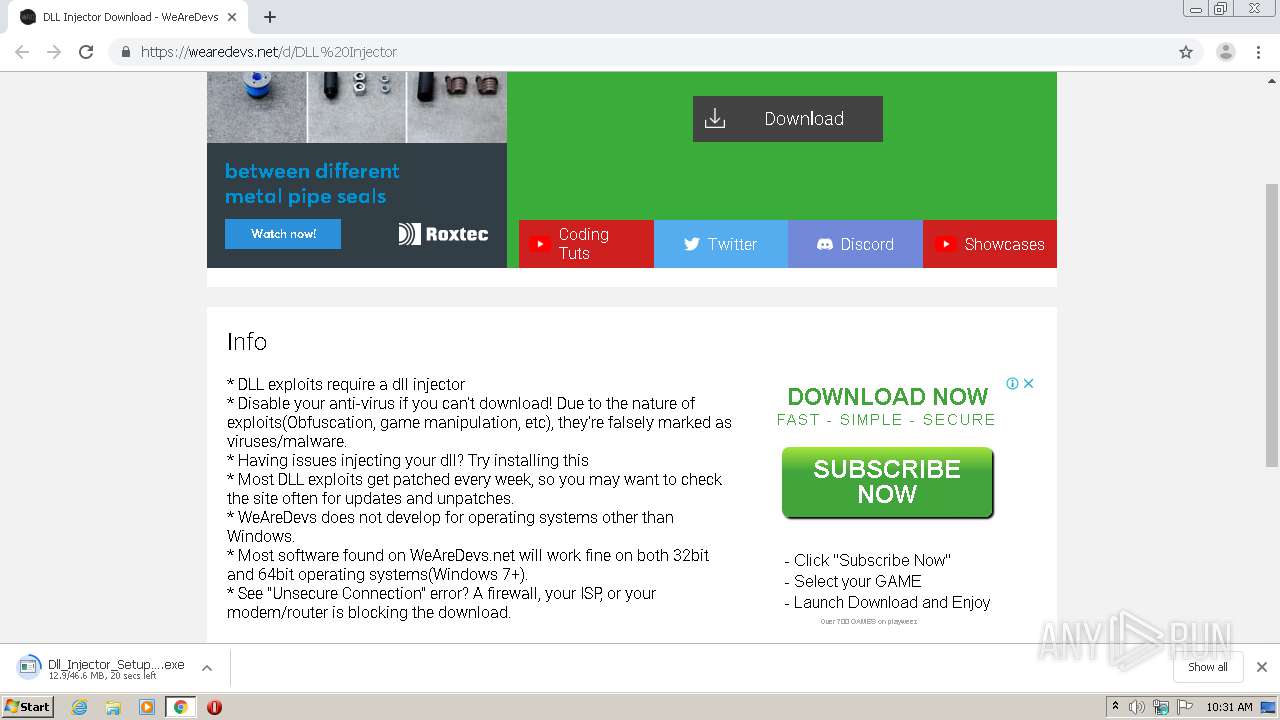
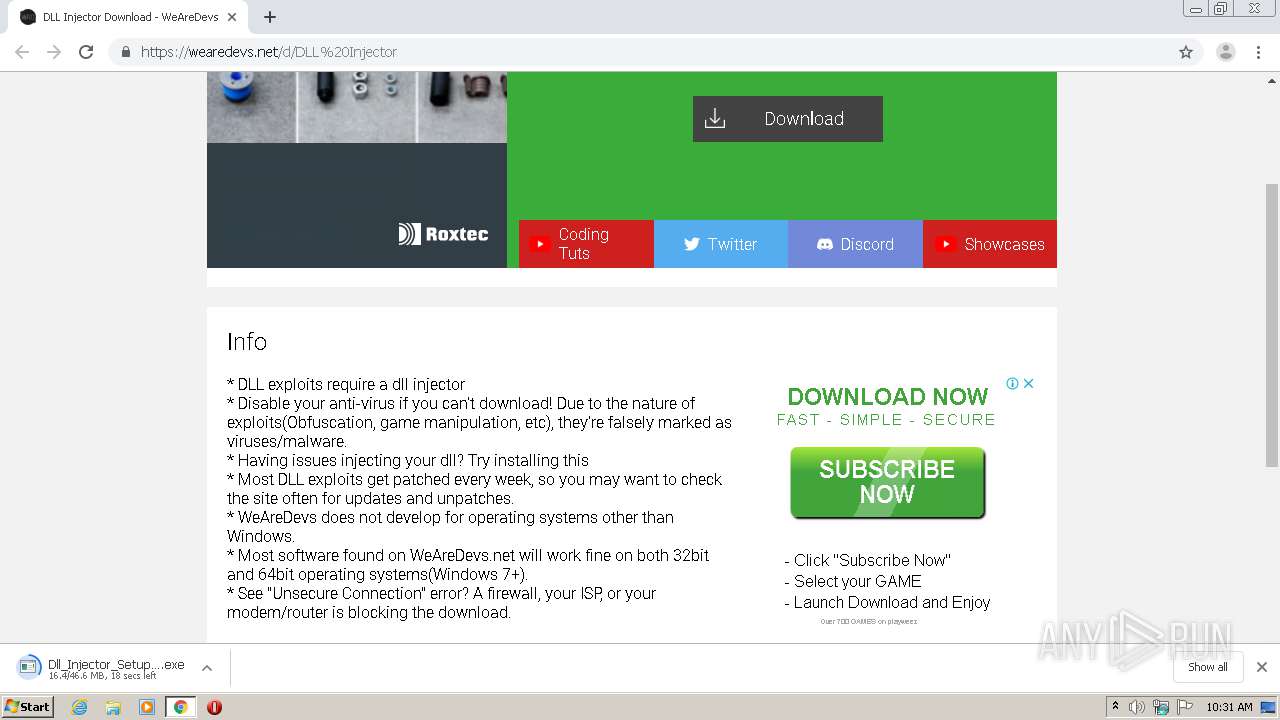
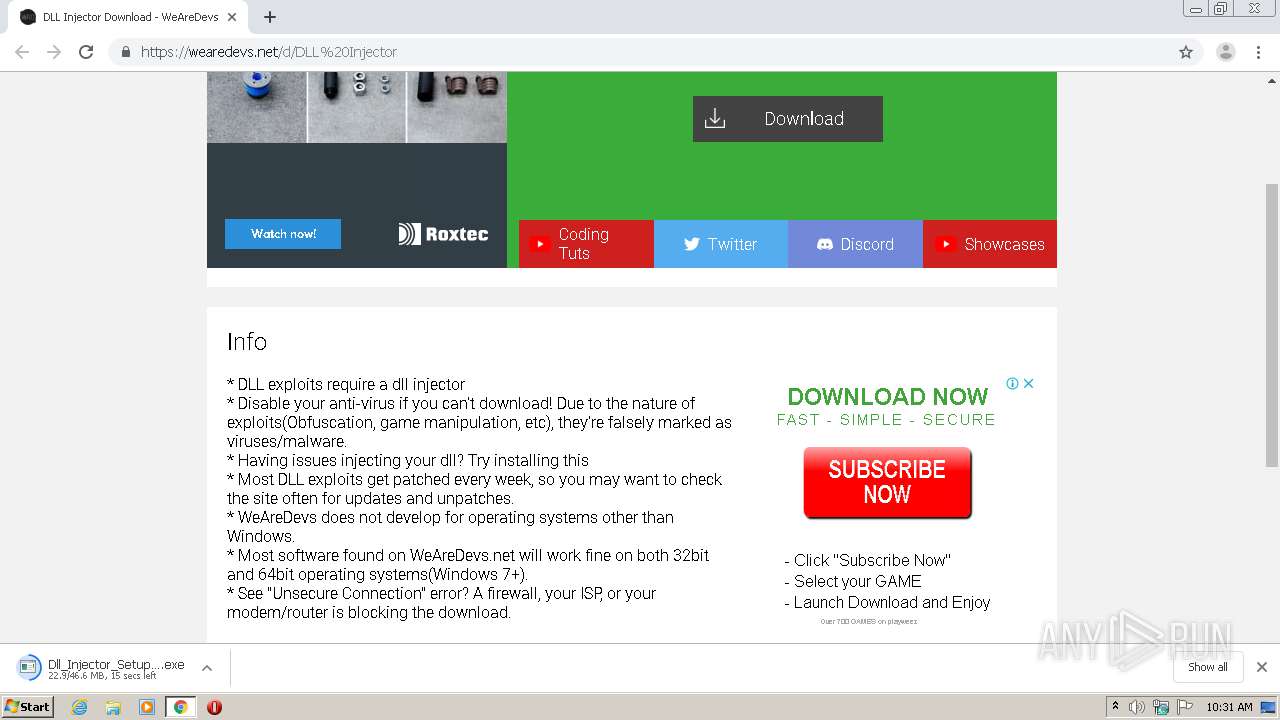
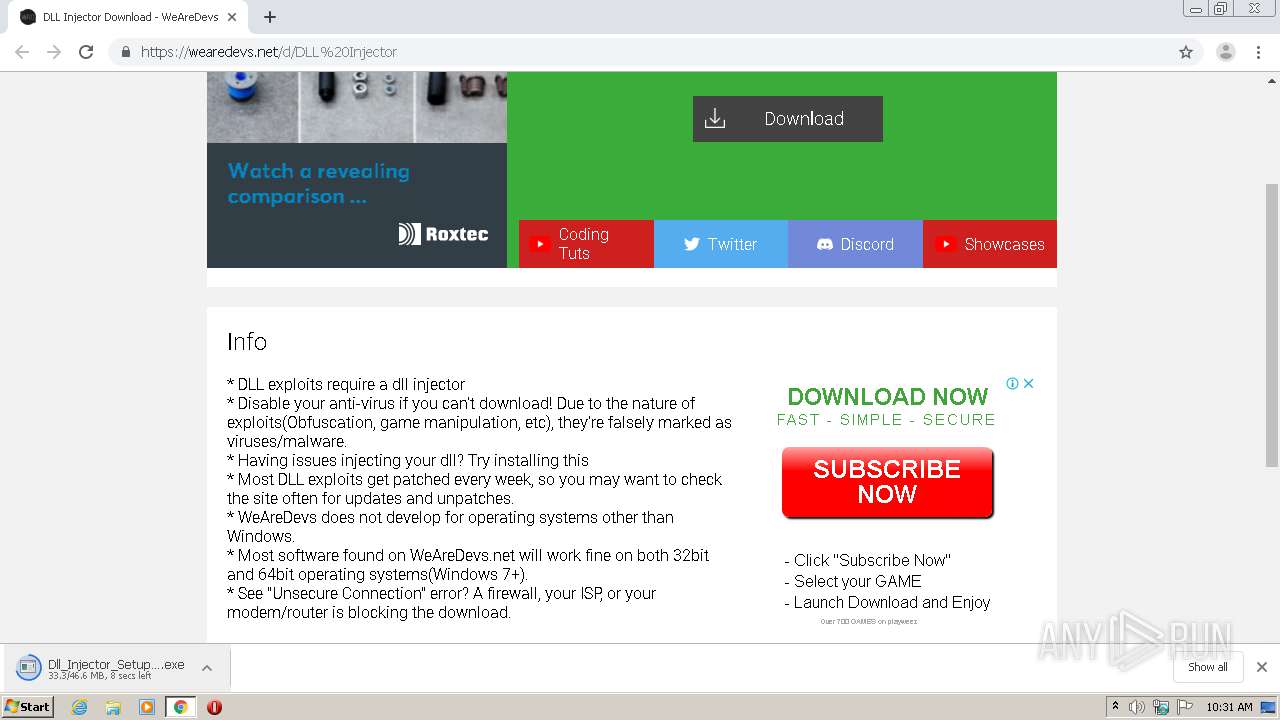
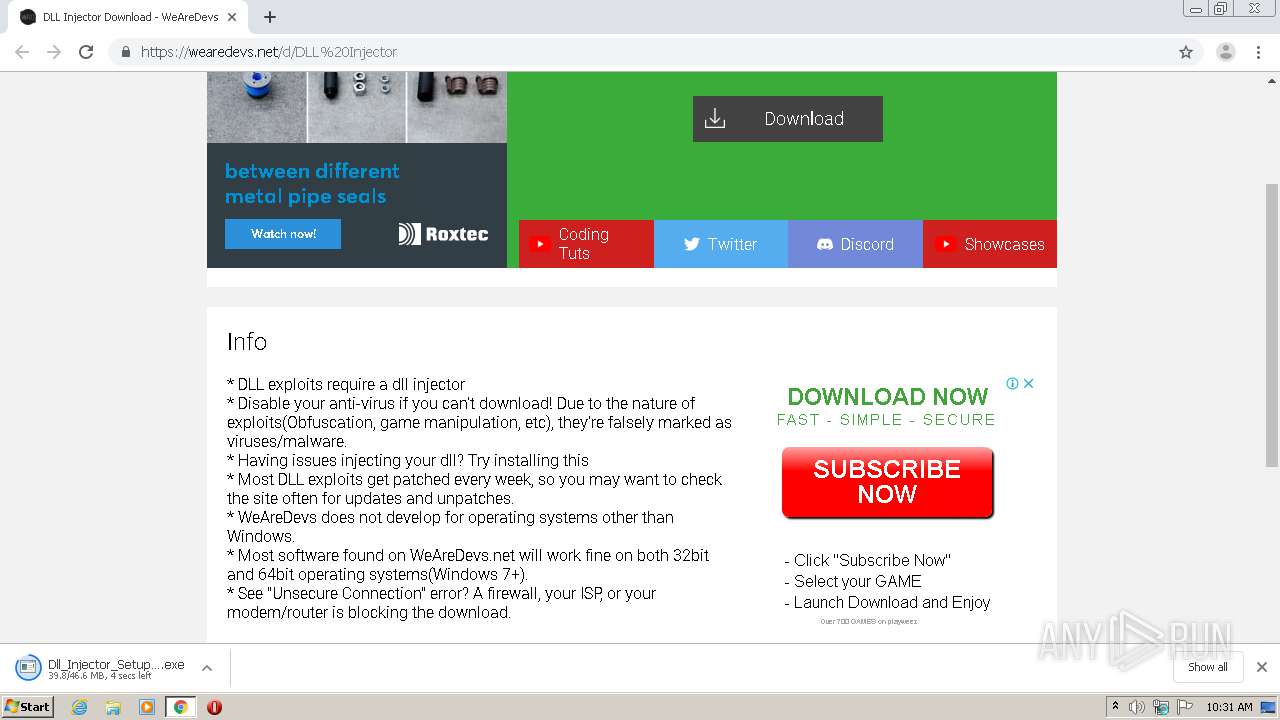
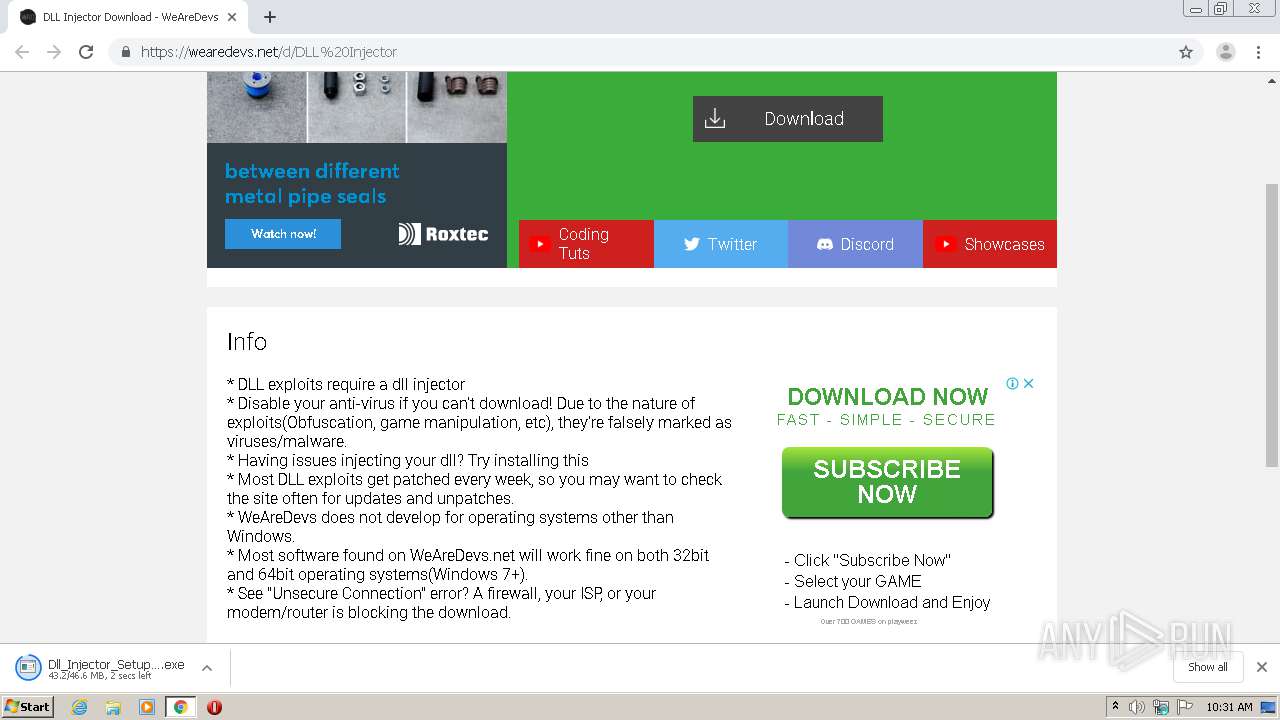
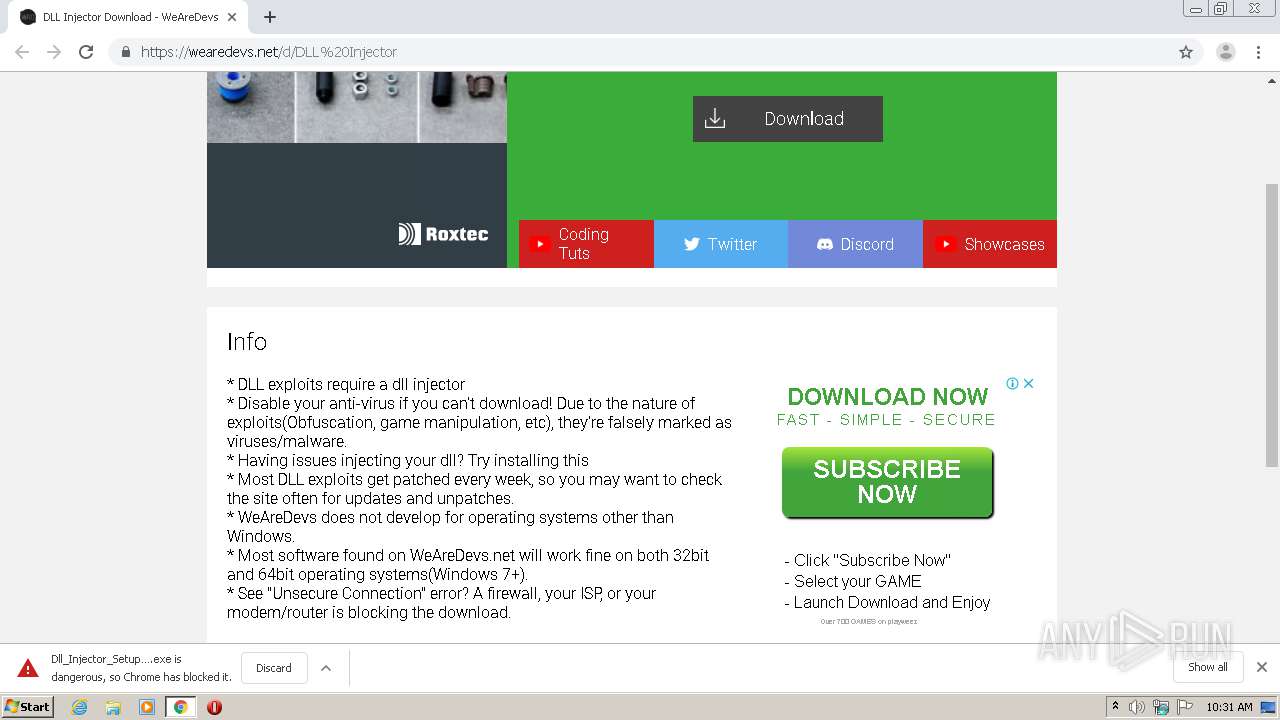
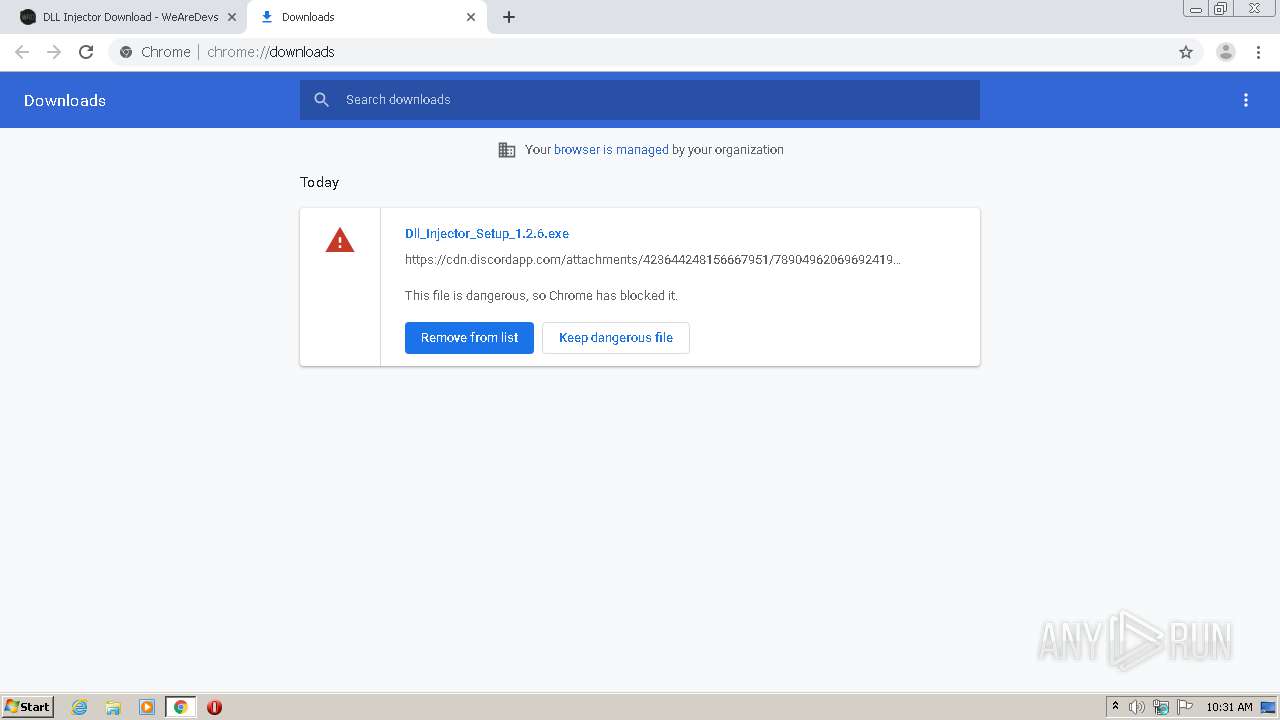
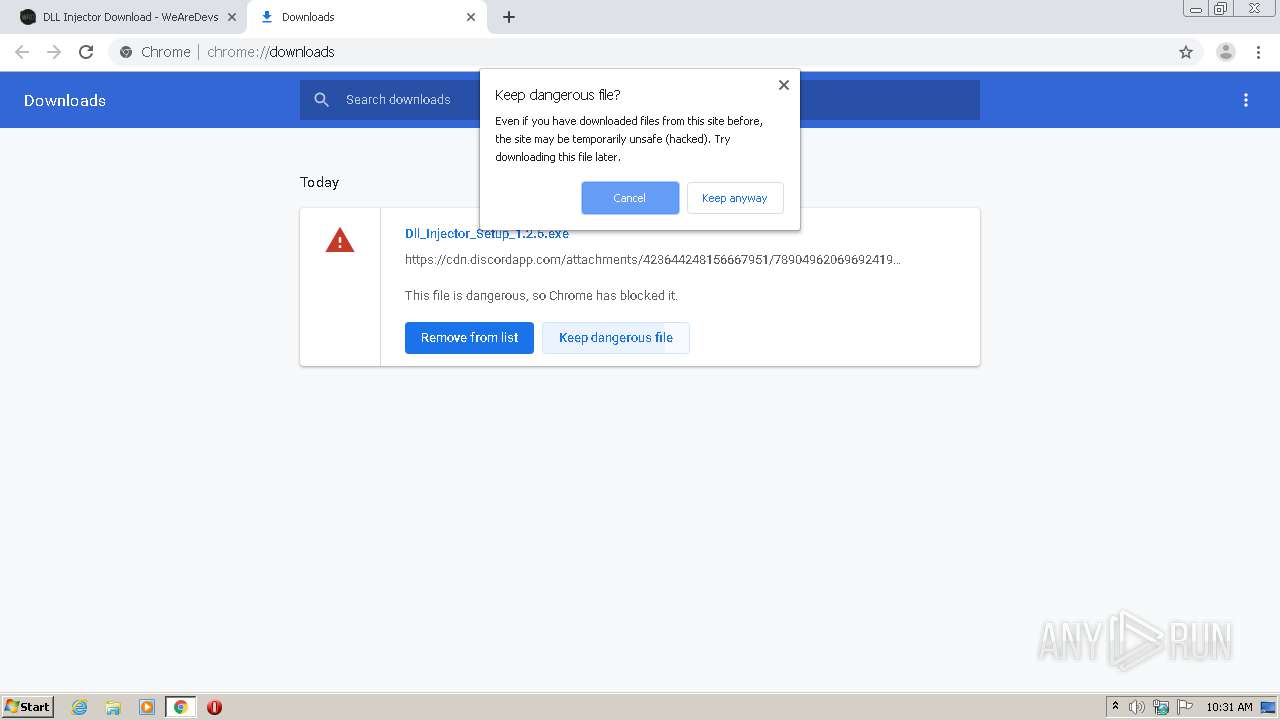
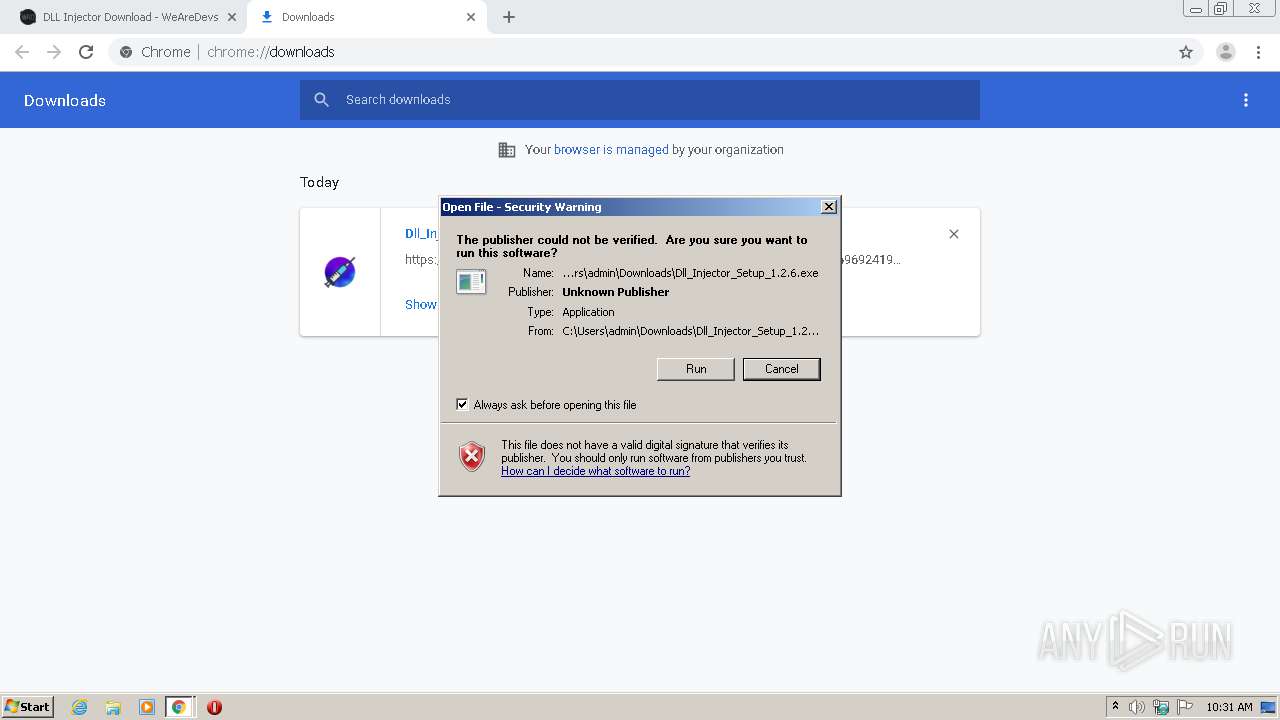
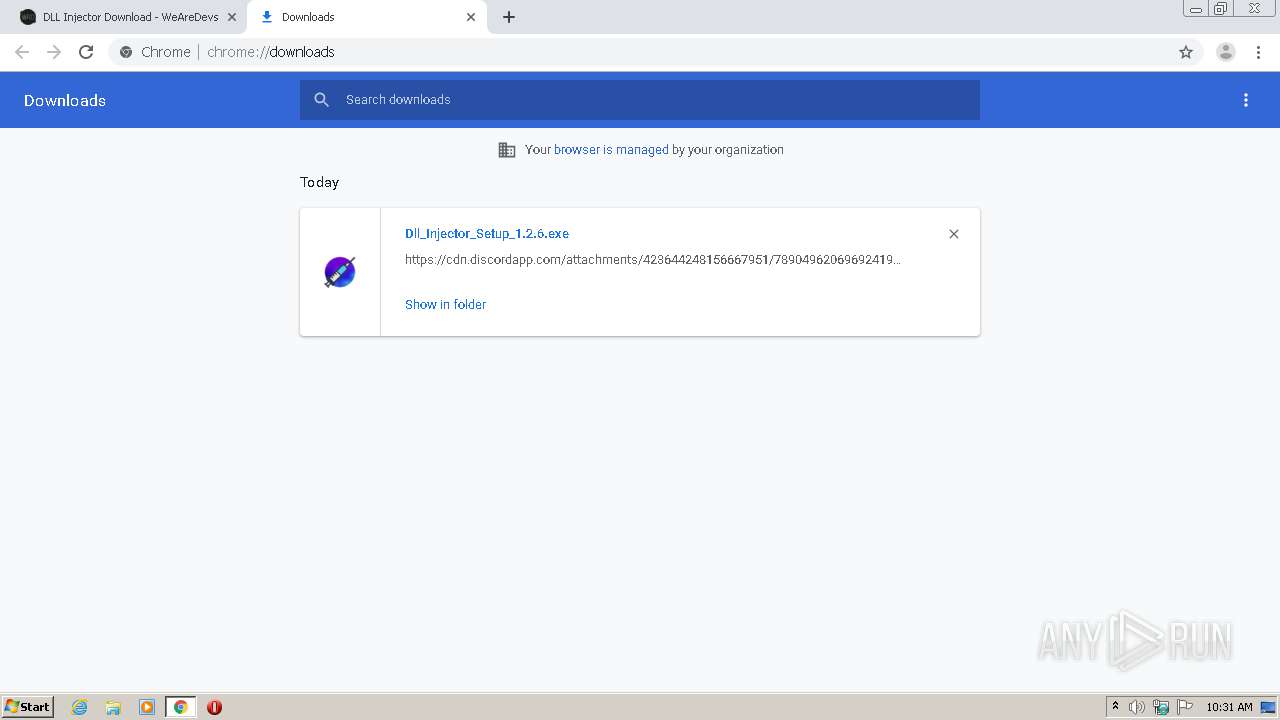
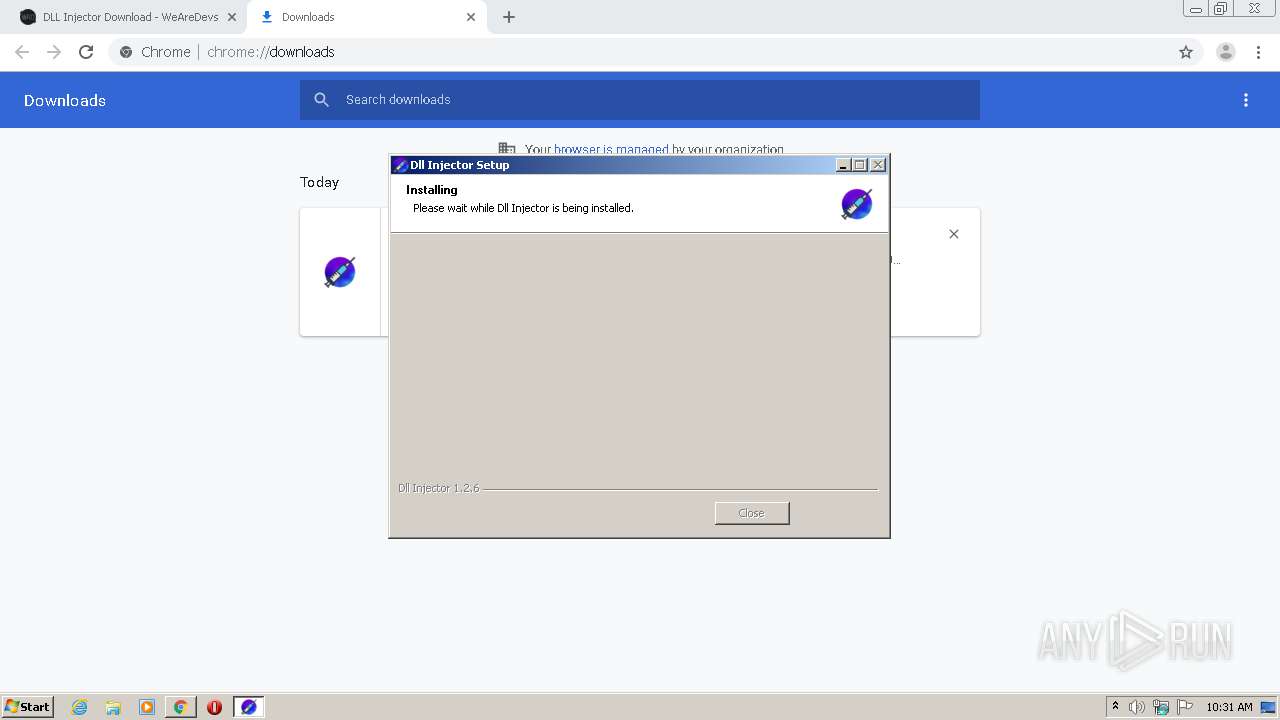
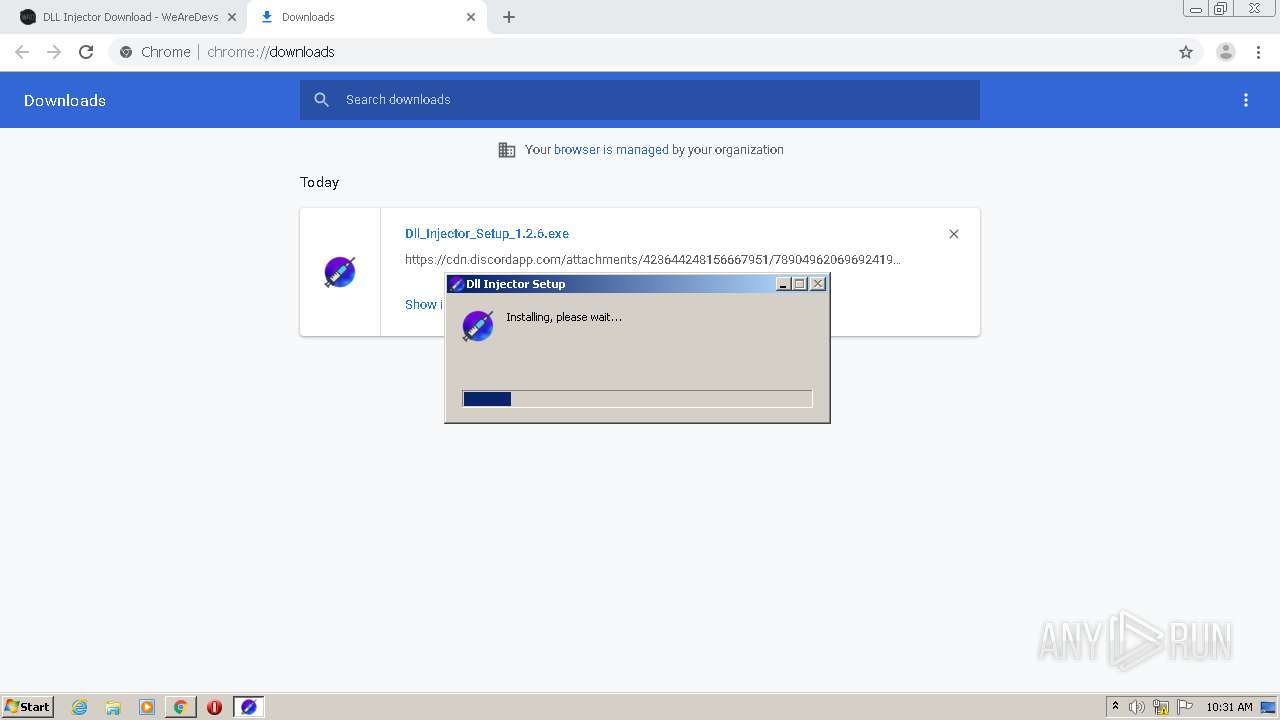
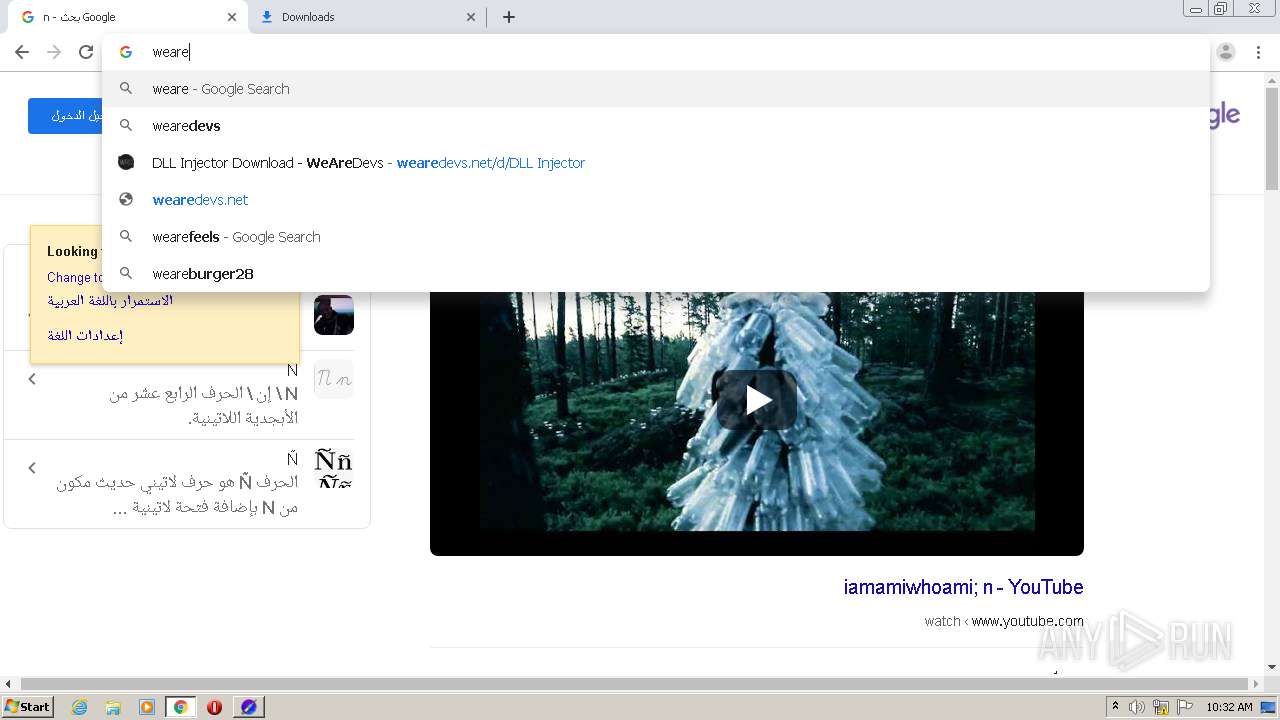
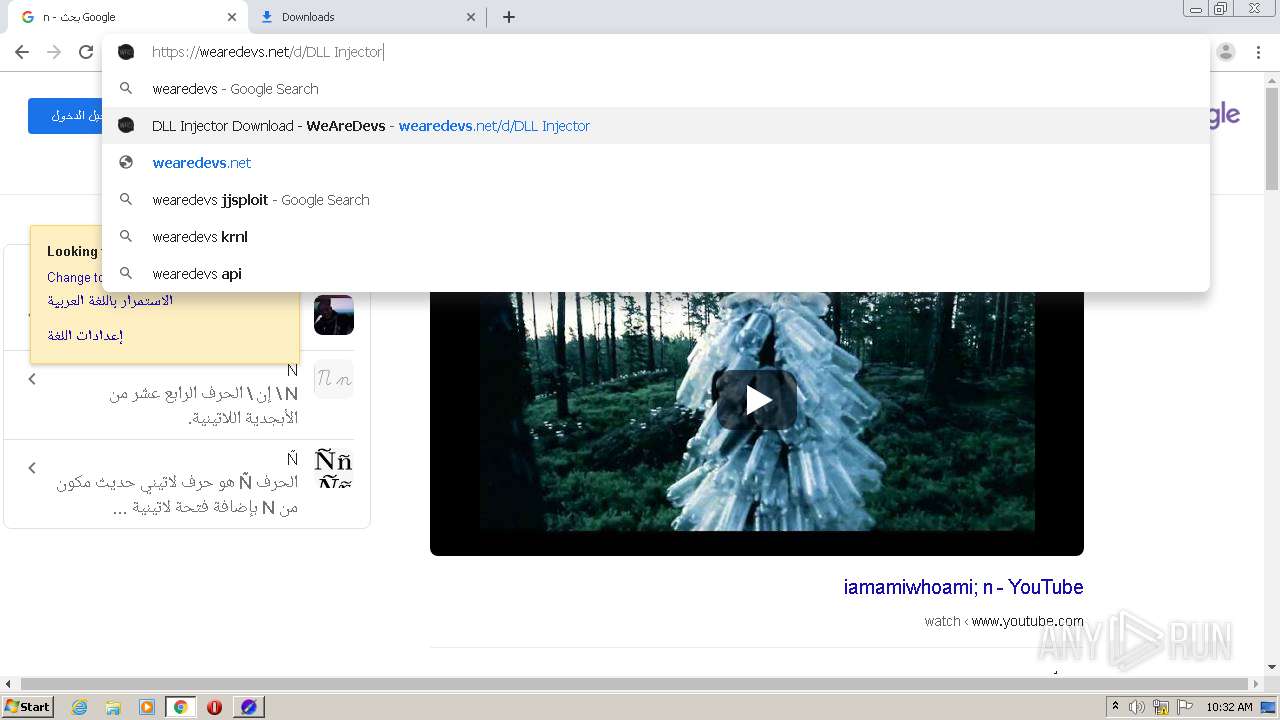
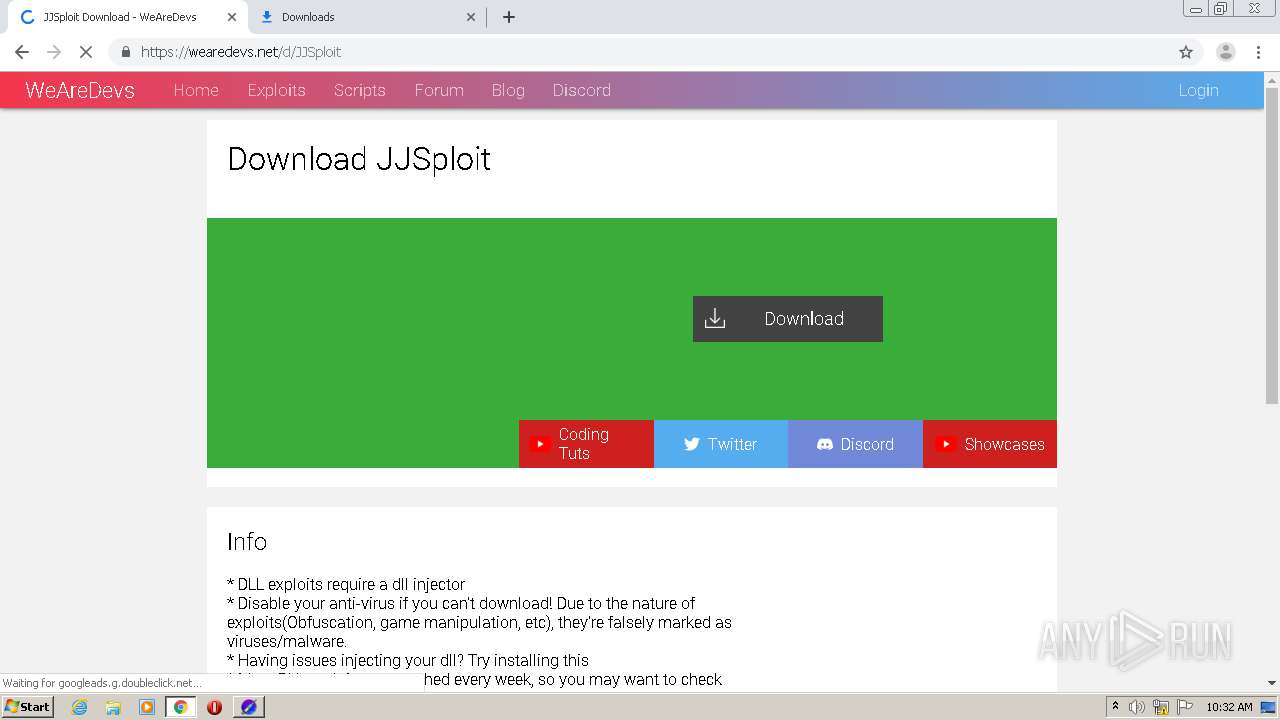
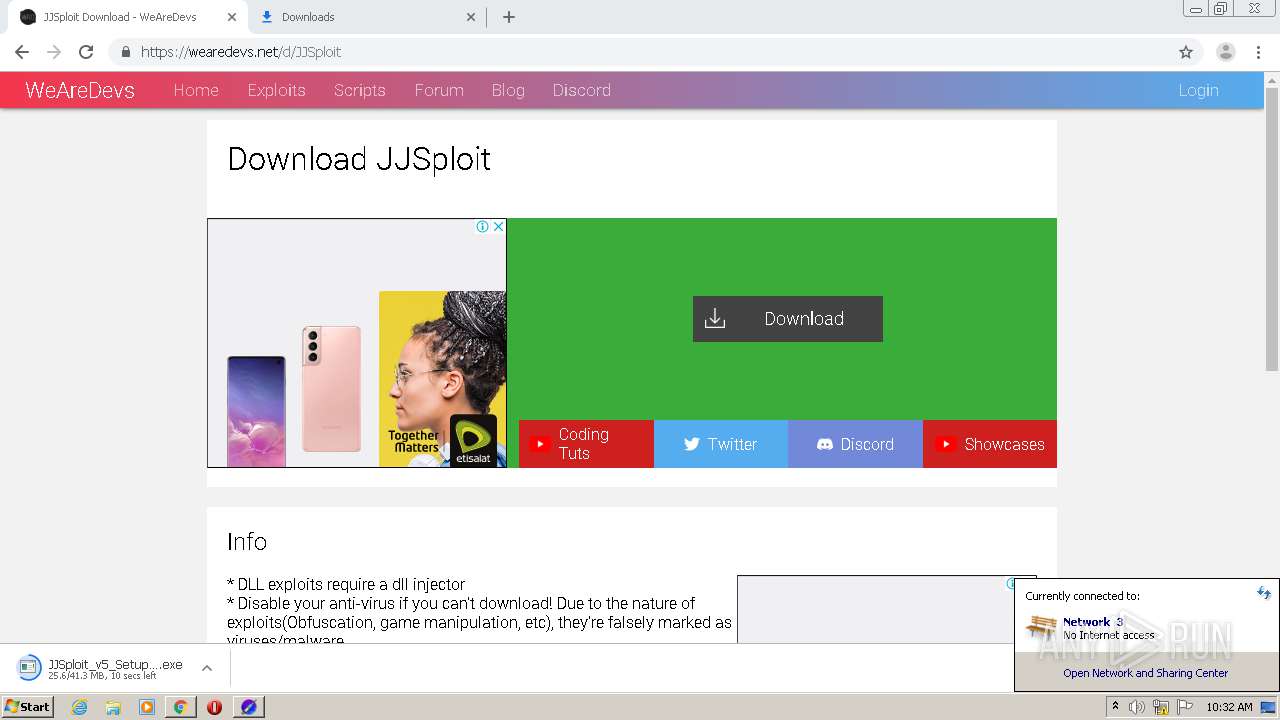
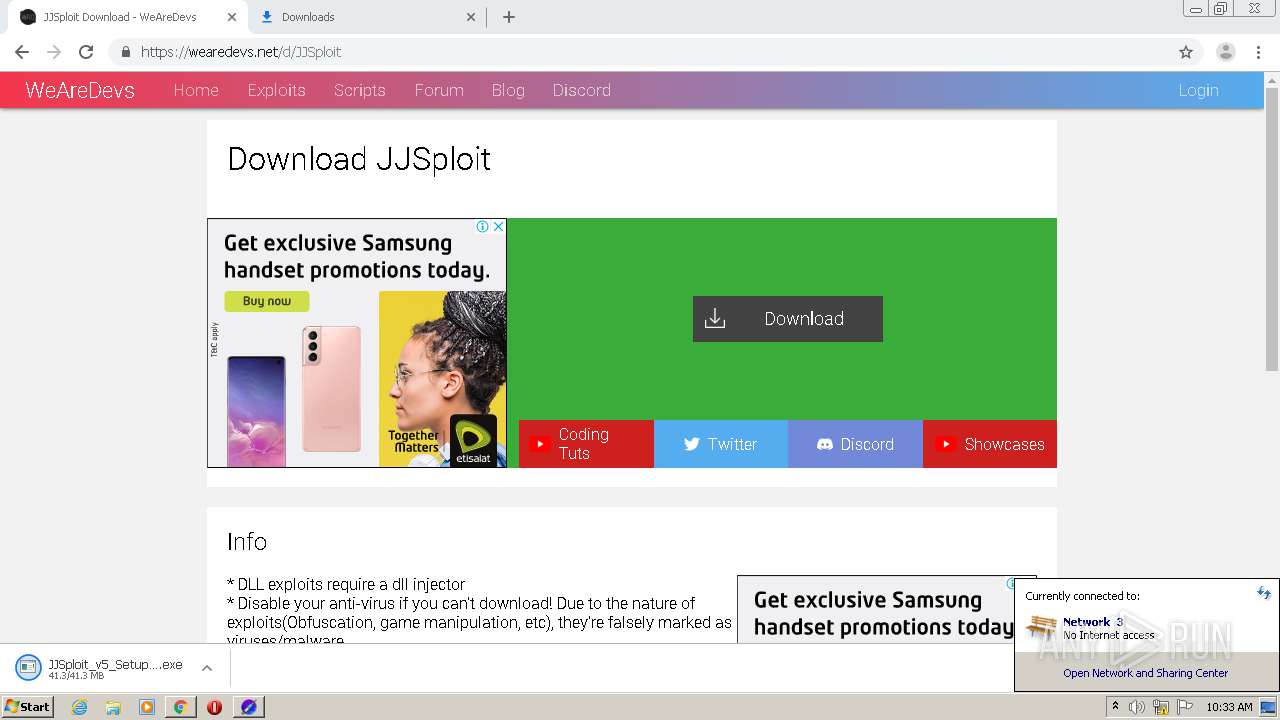
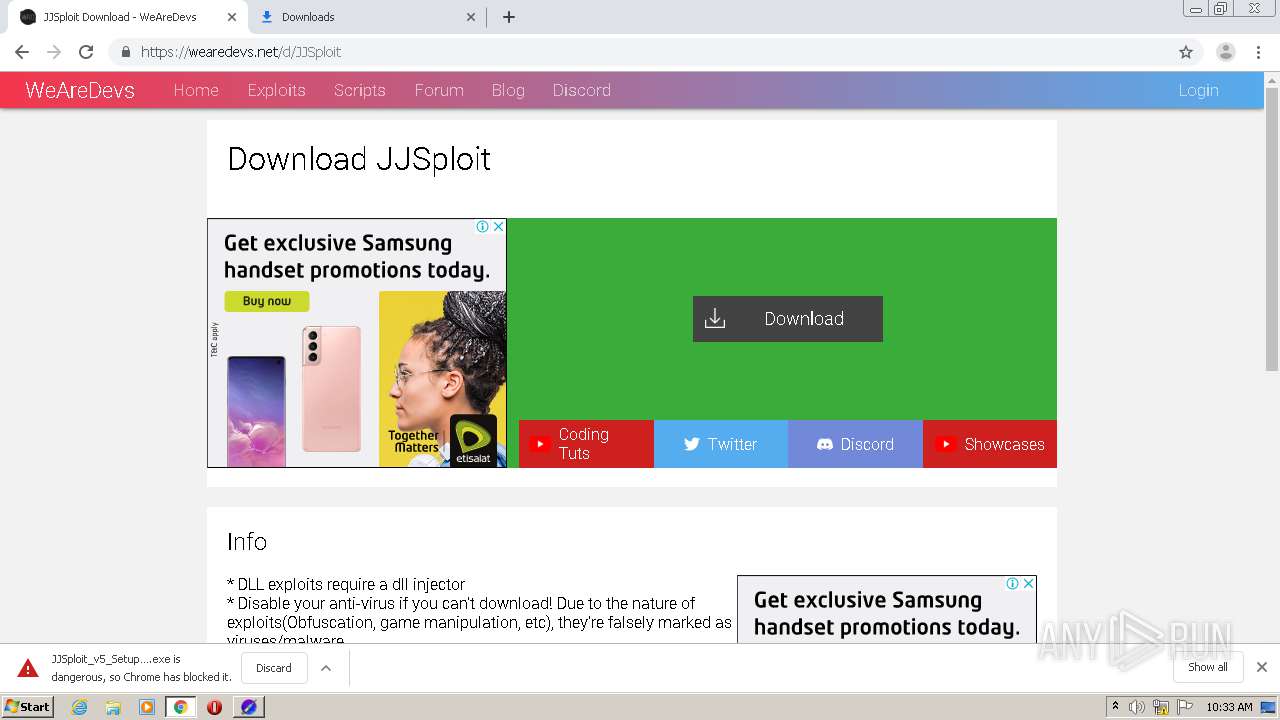
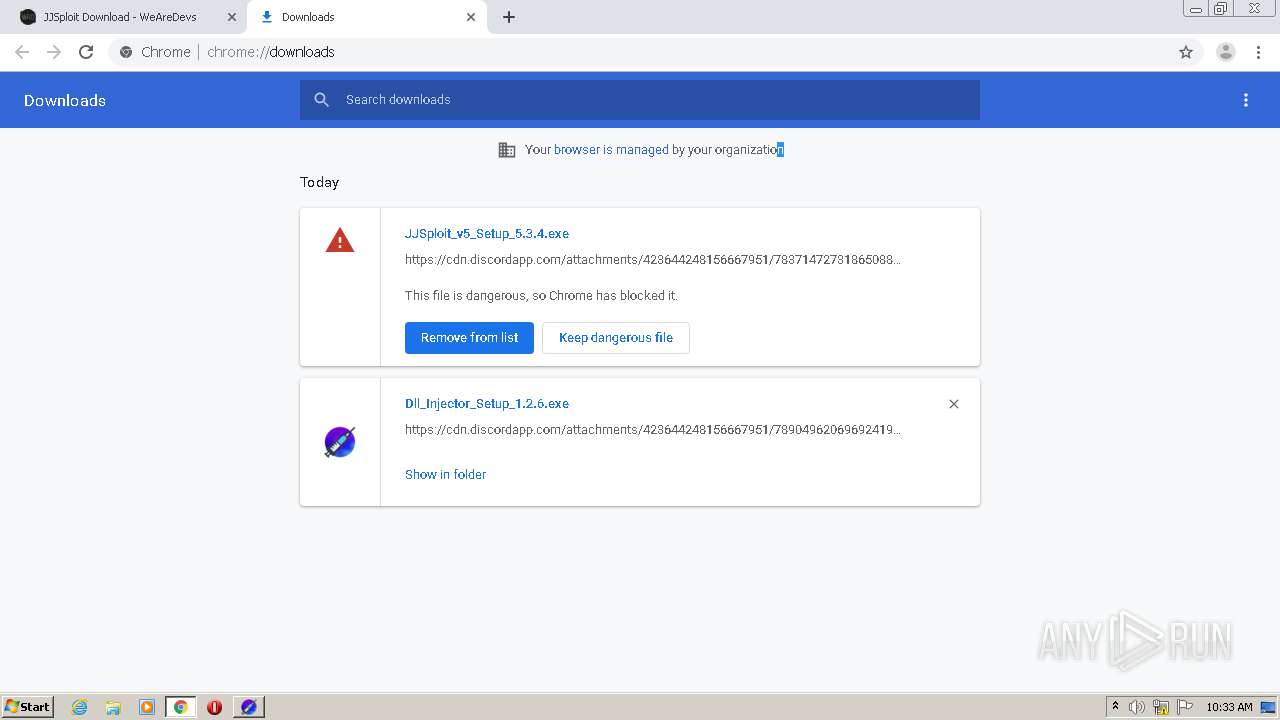
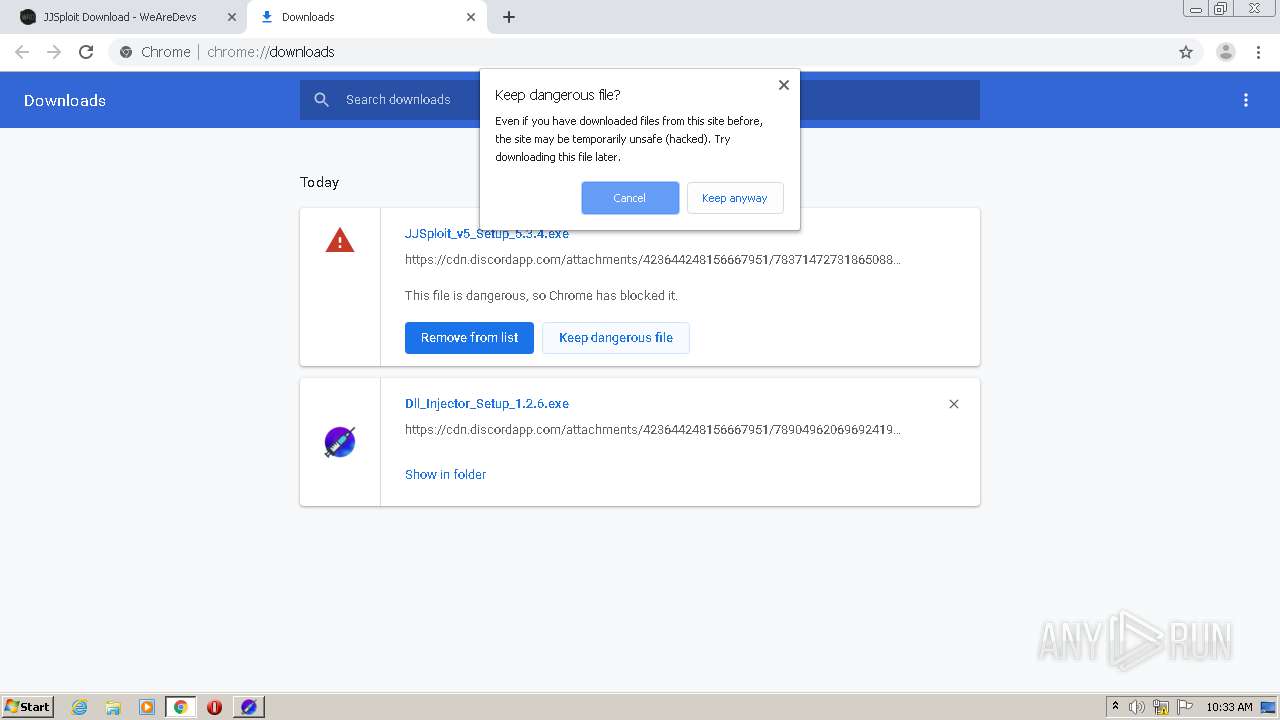
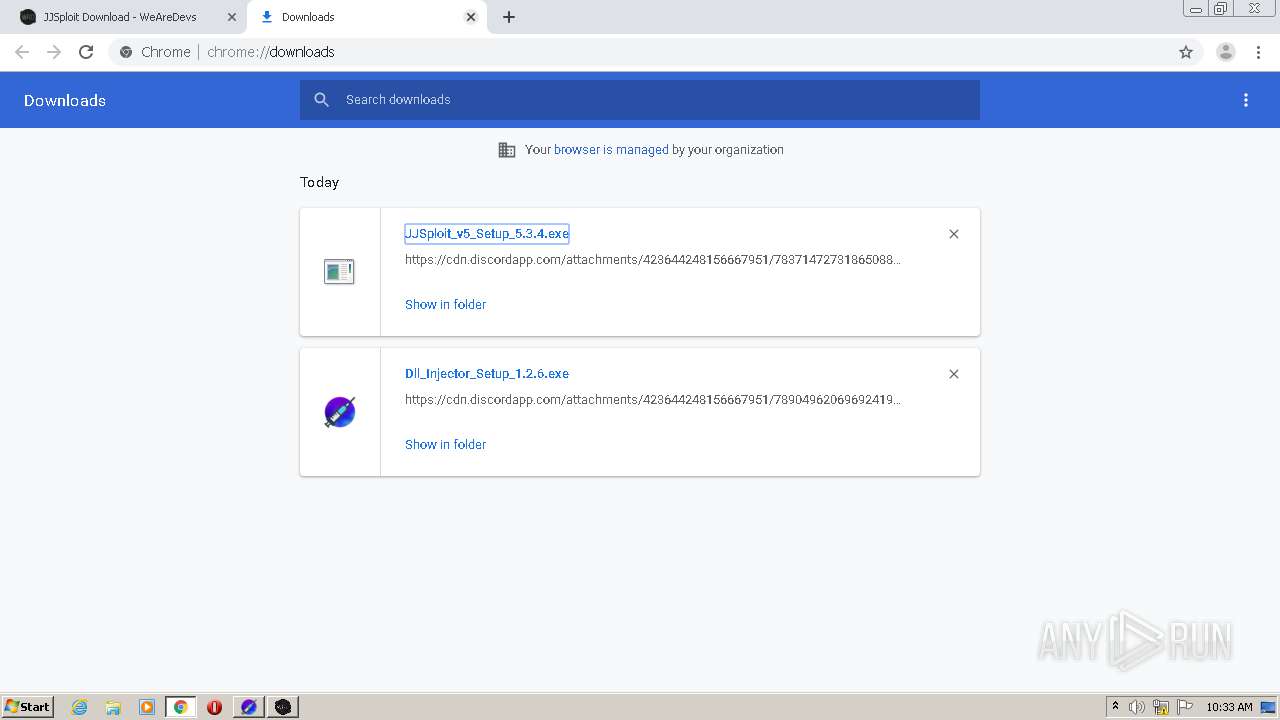
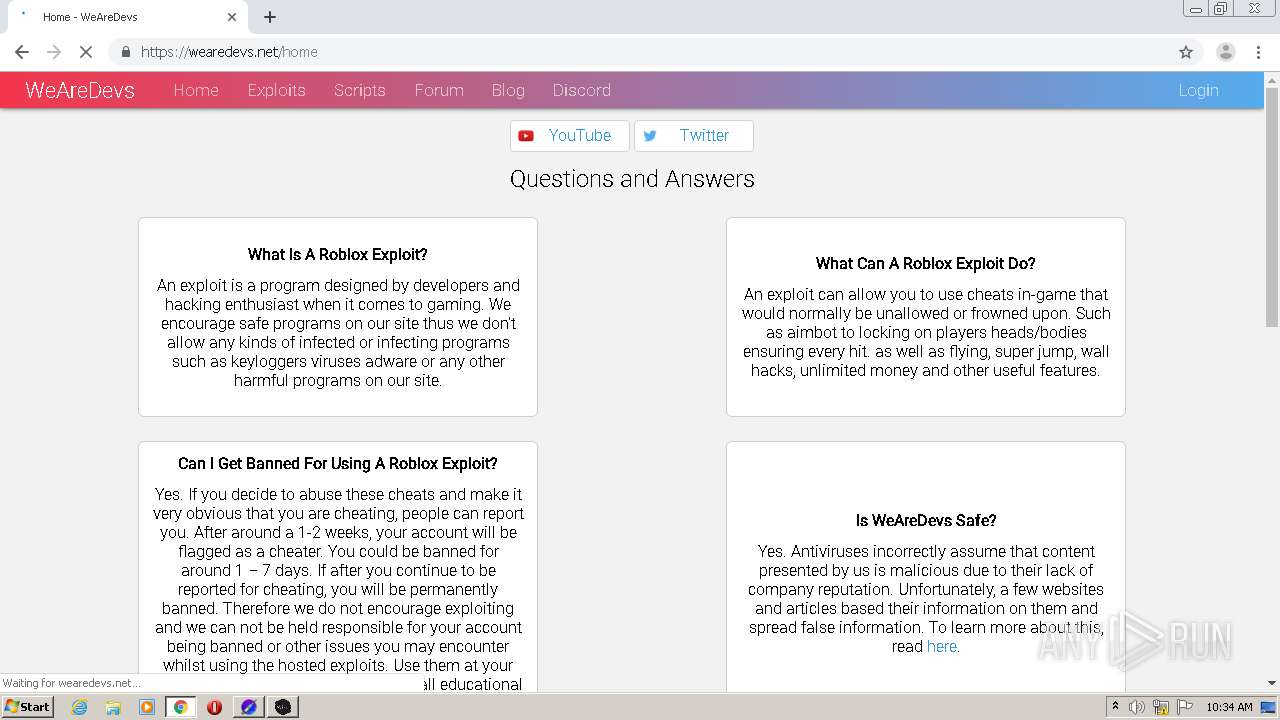
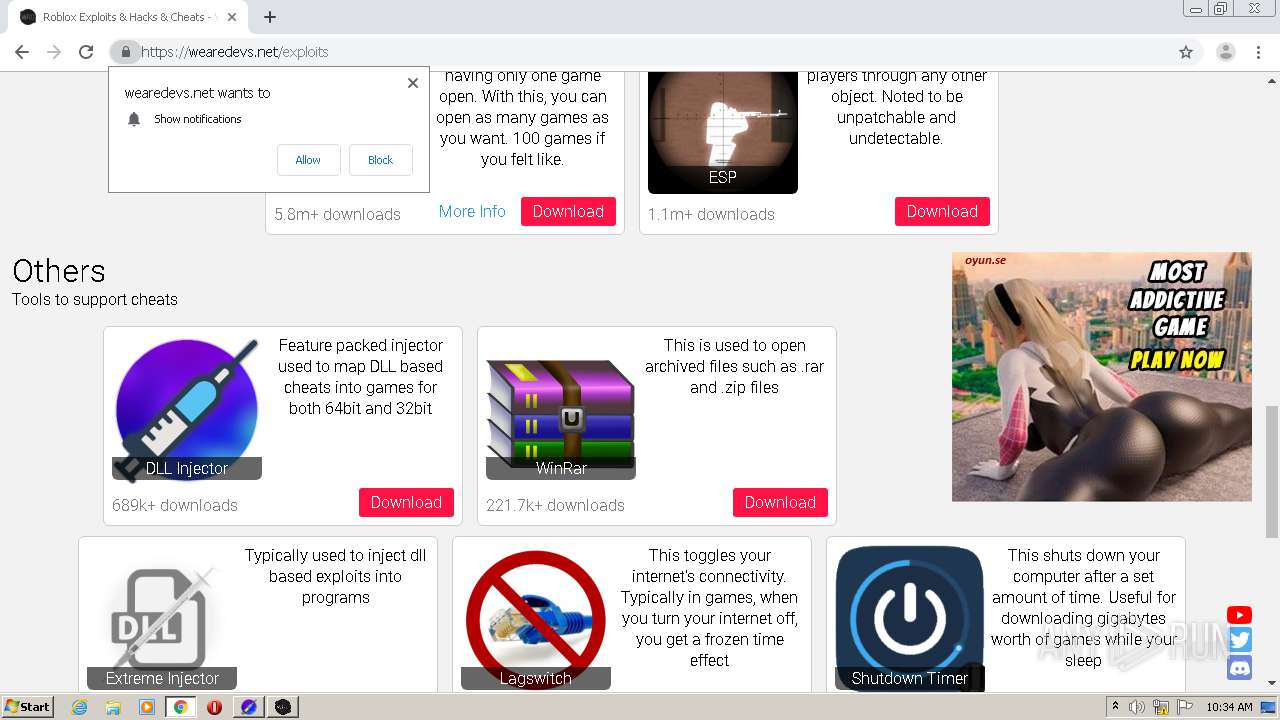
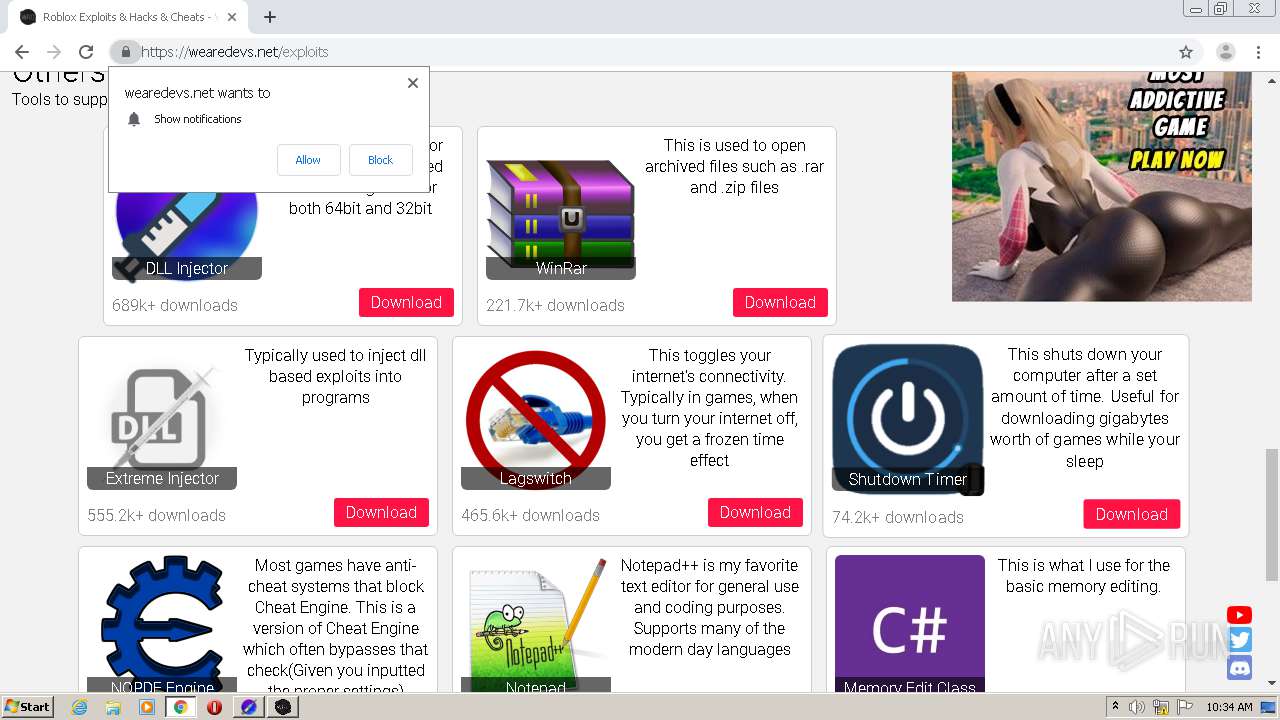
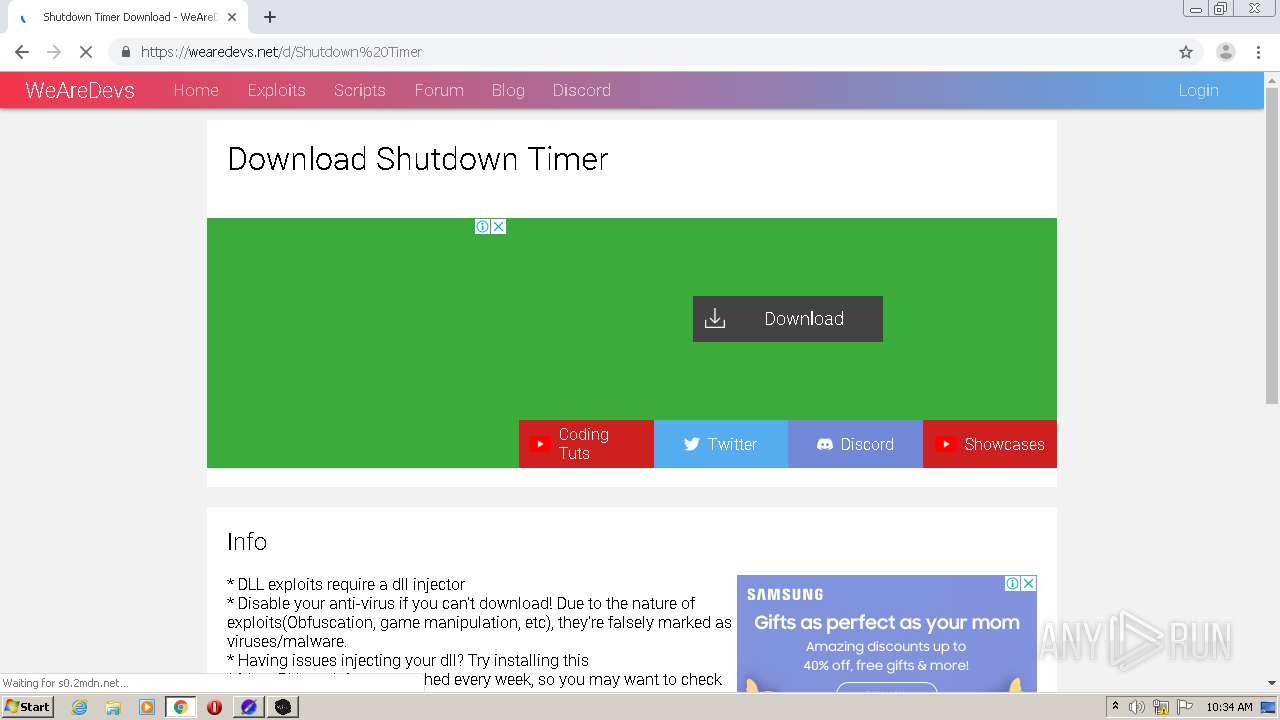
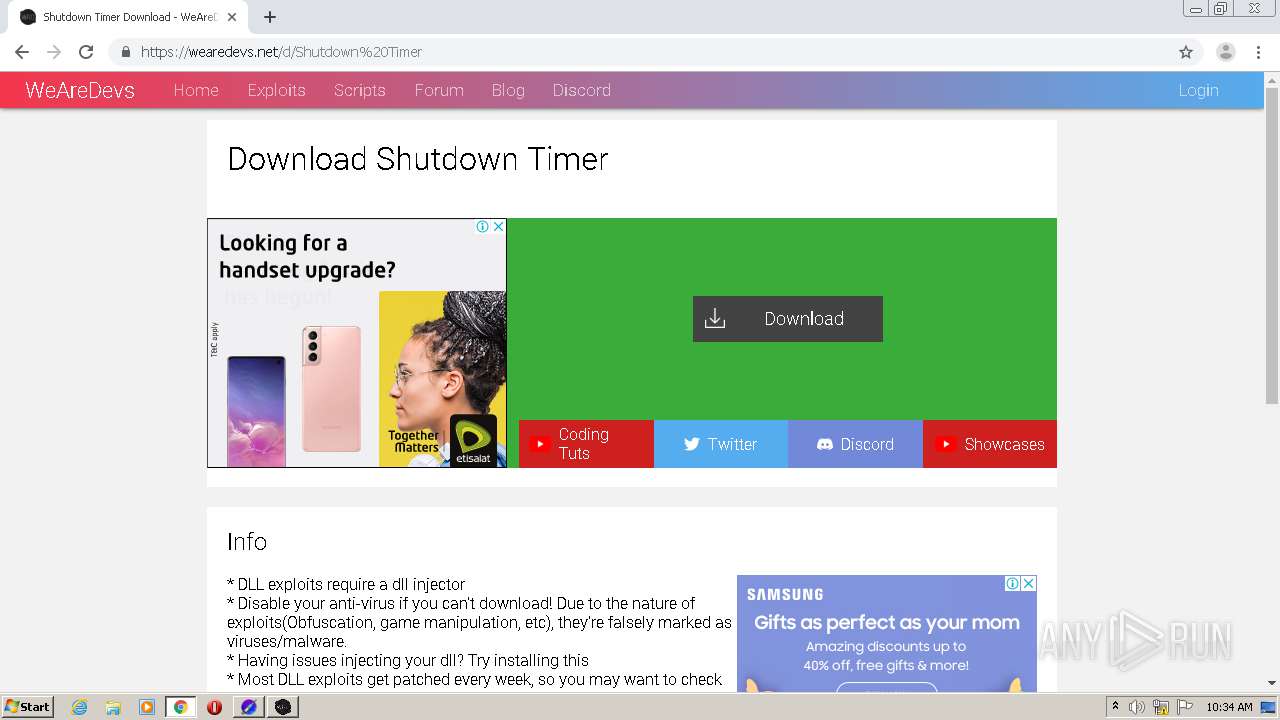
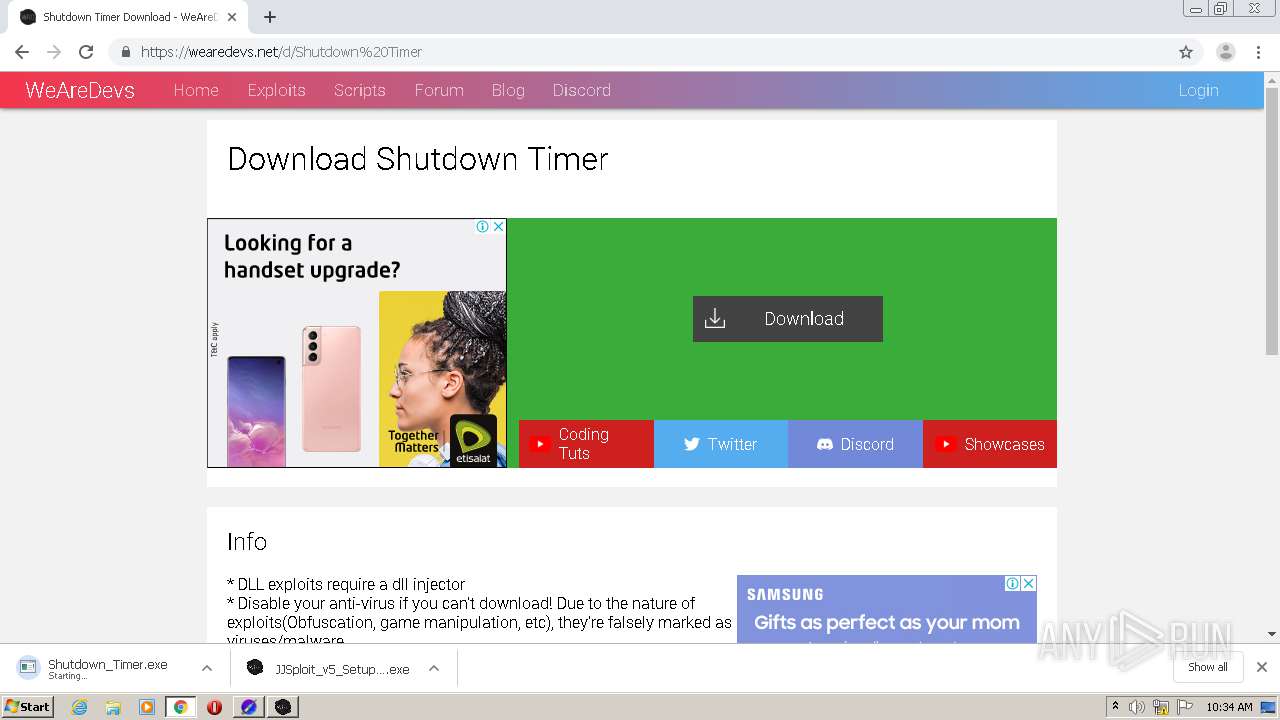
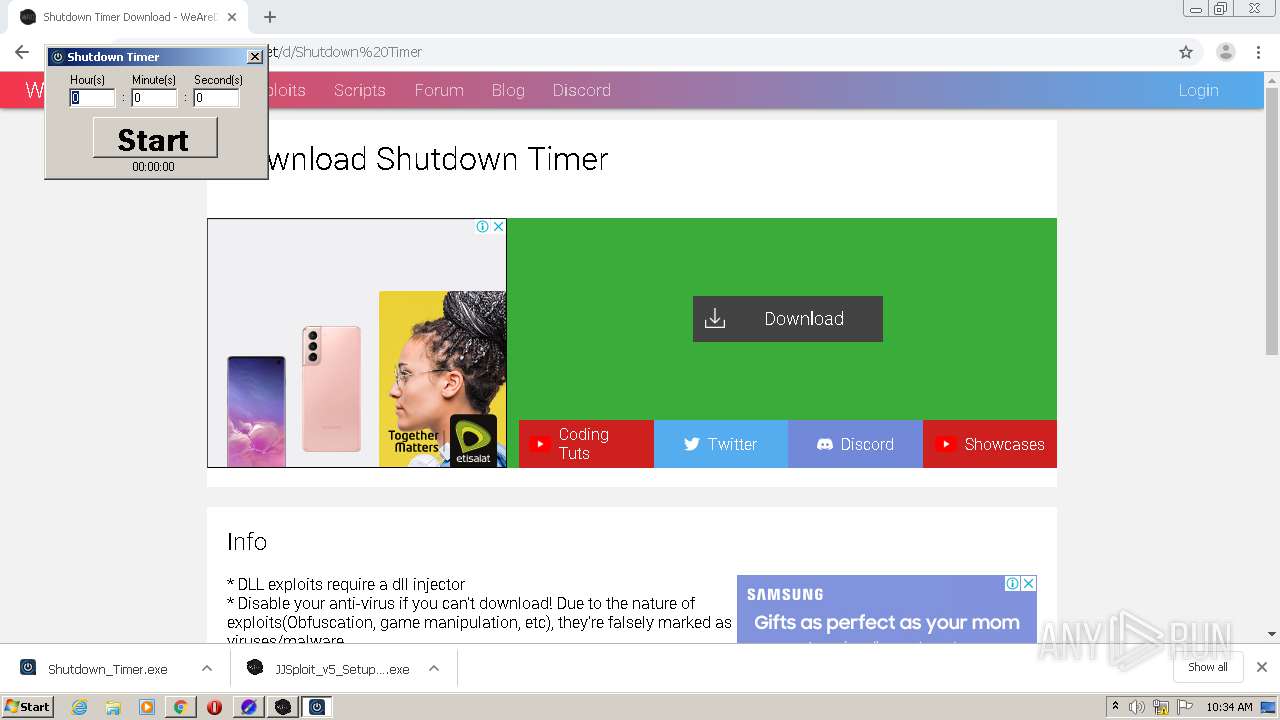
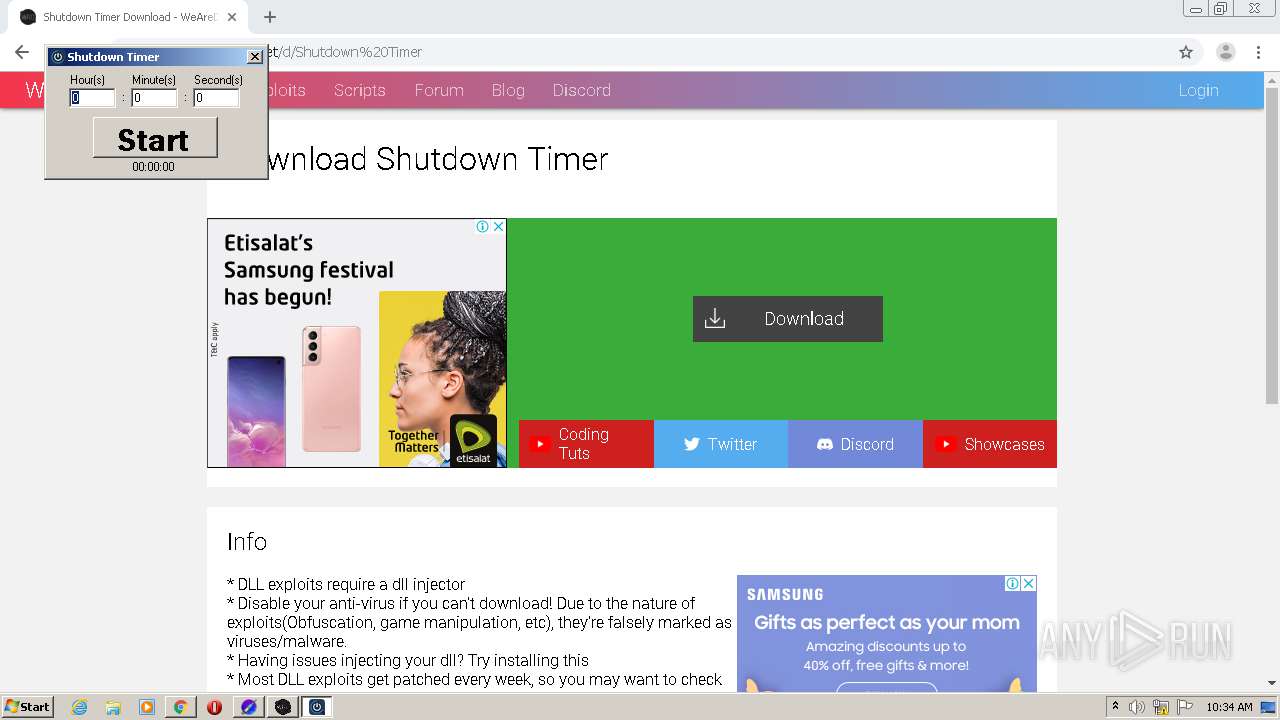
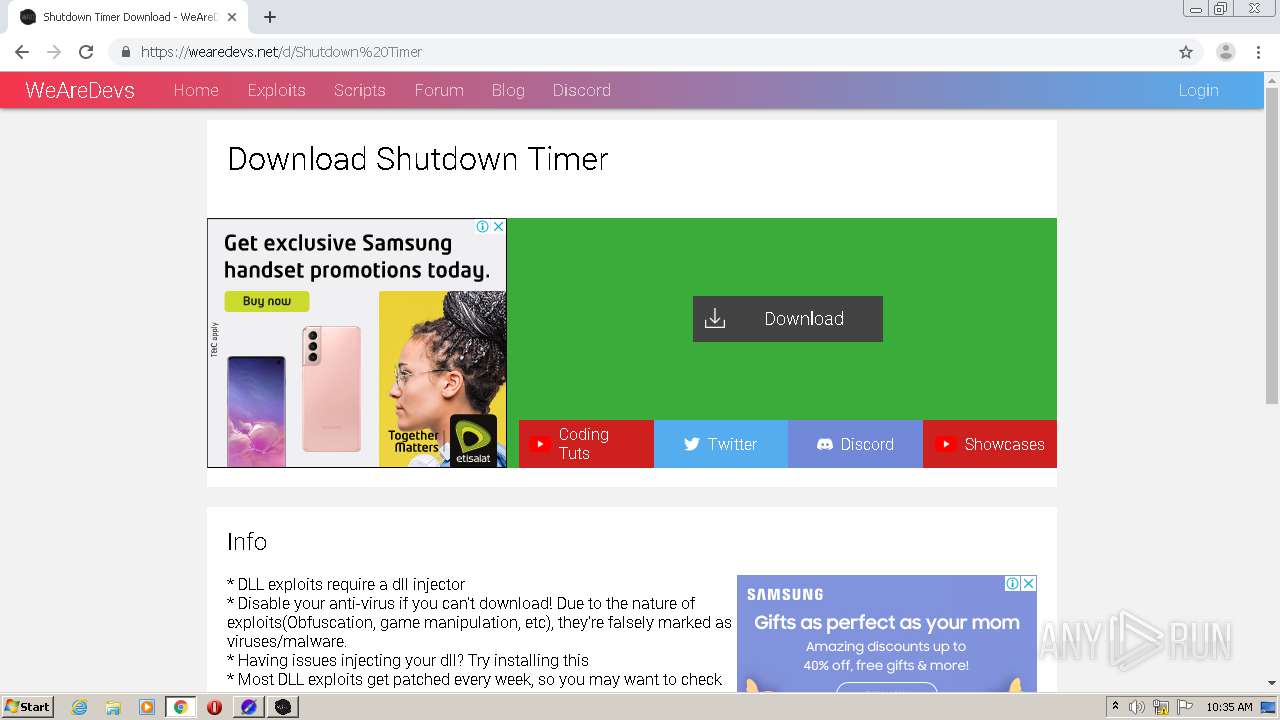
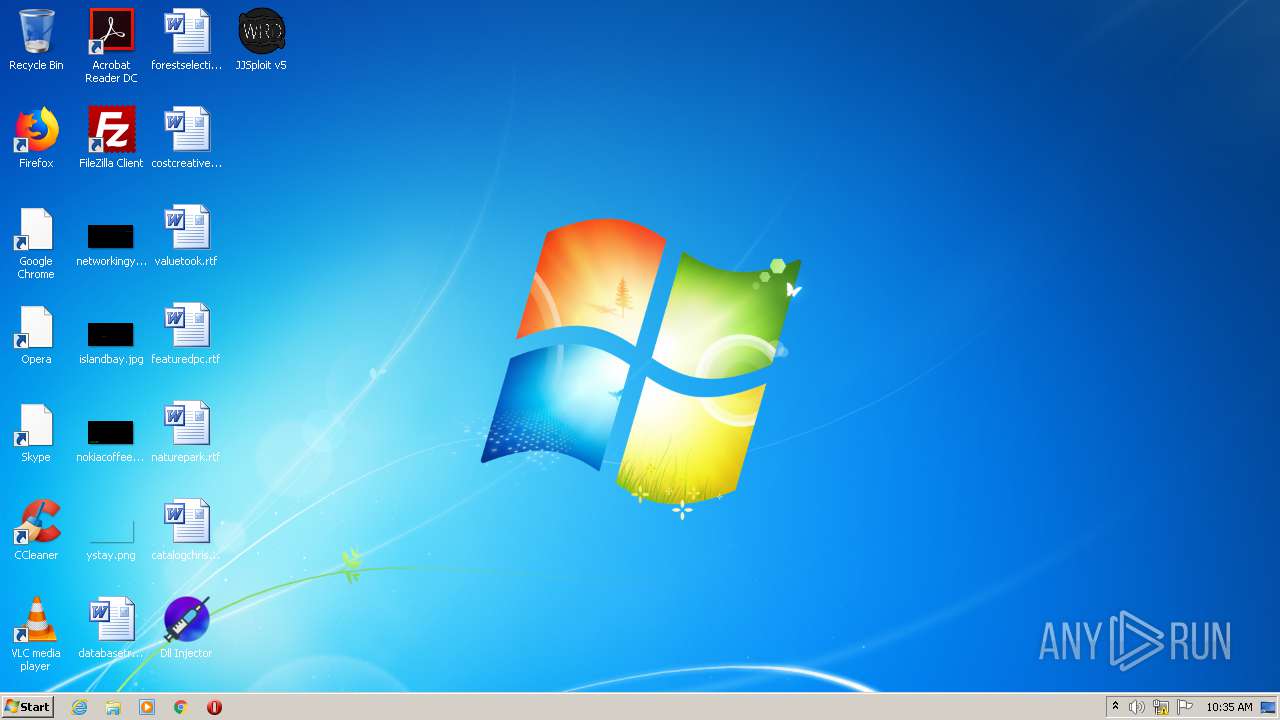
| URL: | https://wearedevs.net/d/DLL%20Injector |
| Full analysis: | https://app.any.run/tasks/96f136d7-ffed-4f56-8a7c-d401b81f309c |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2021, 10:30:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3108173E842607679047455C2A41BA42 |
| SHA1: | 7461E7A6DAA52A84A7F23C3D832F20AB6BB943CB |
| SHA256: | 82E21513EA8902D7014F1C166BD91040E8D887D91EFD93D49E2D30BB9591153D |
| SSDEEP: | 3:N8R/BApK8FLsX:25BuBFC |
MALICIOUS
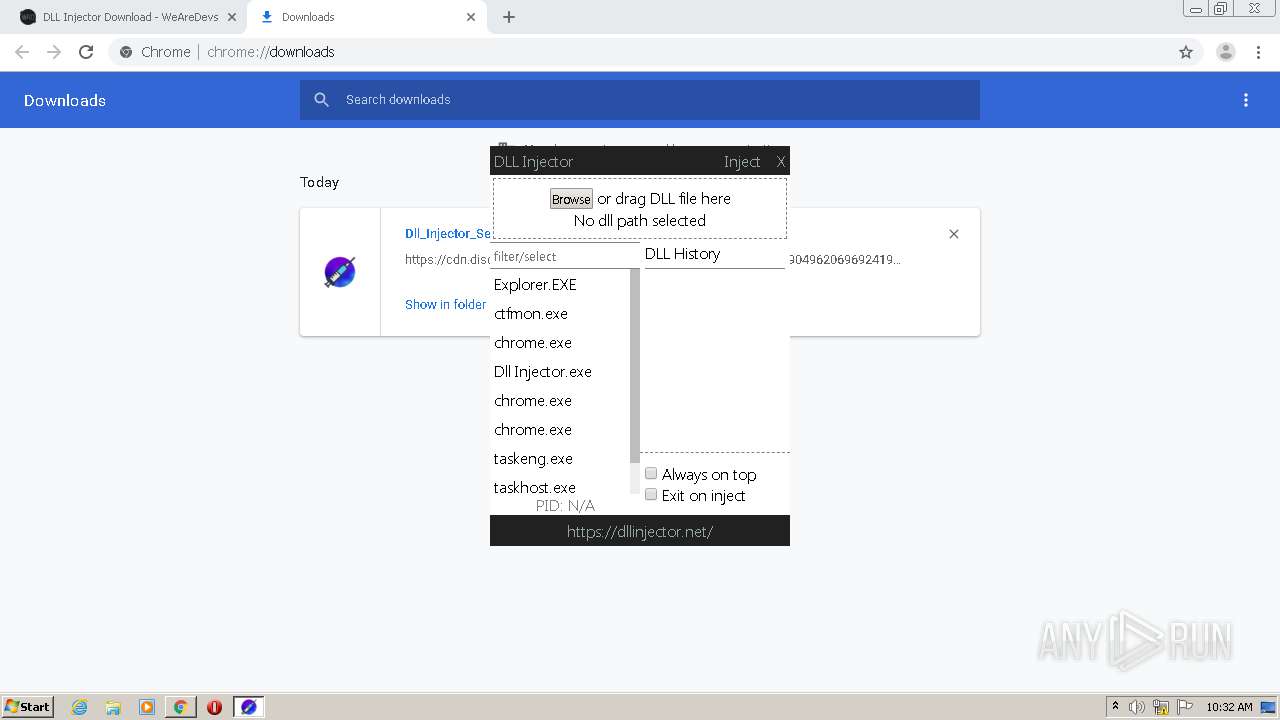
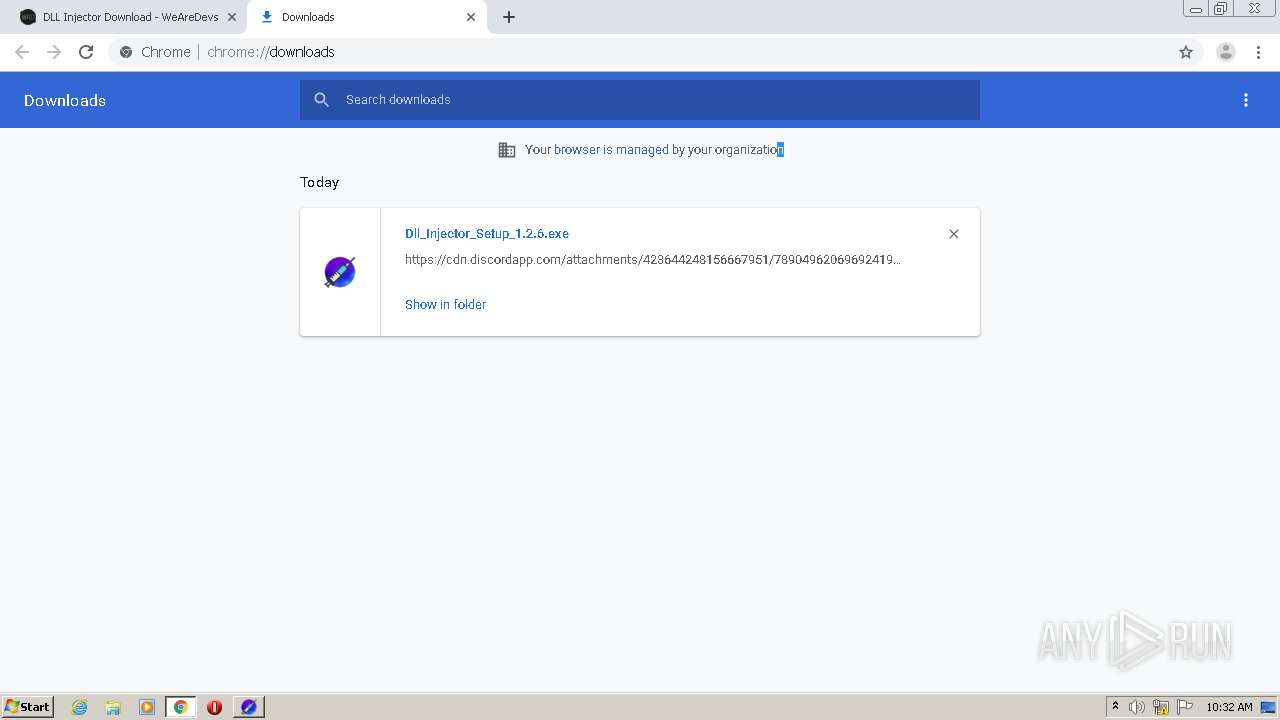
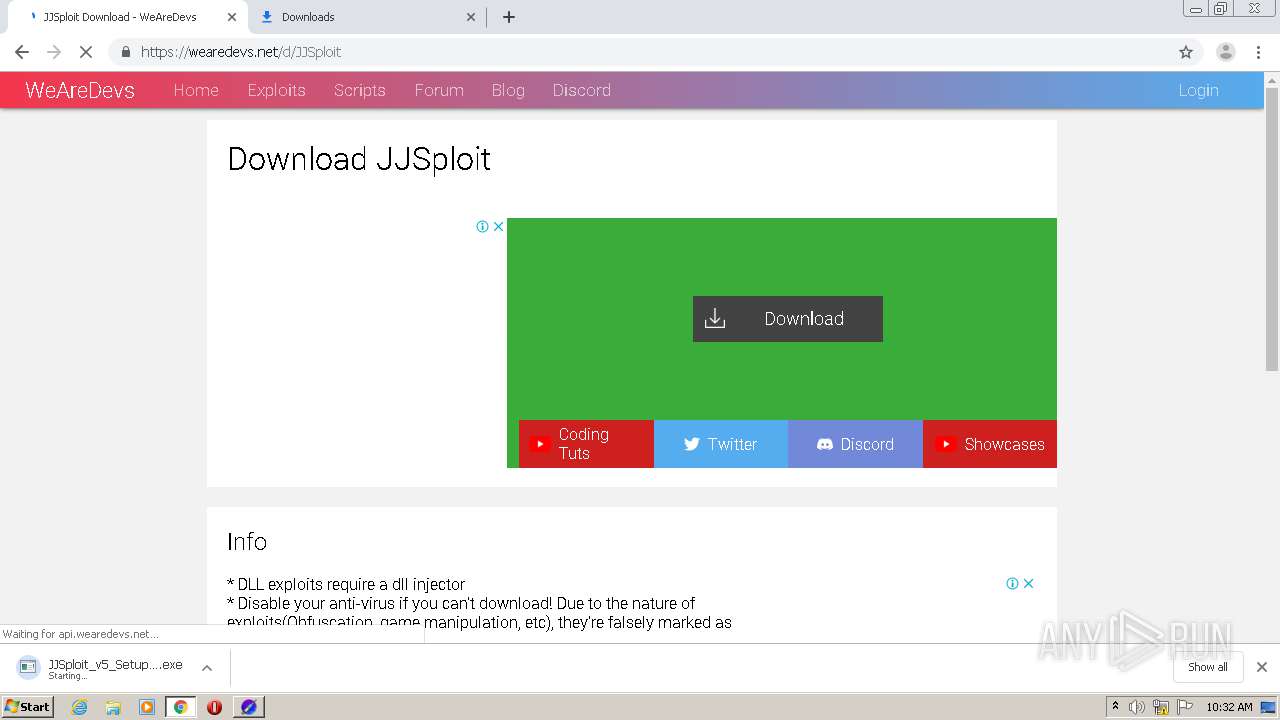
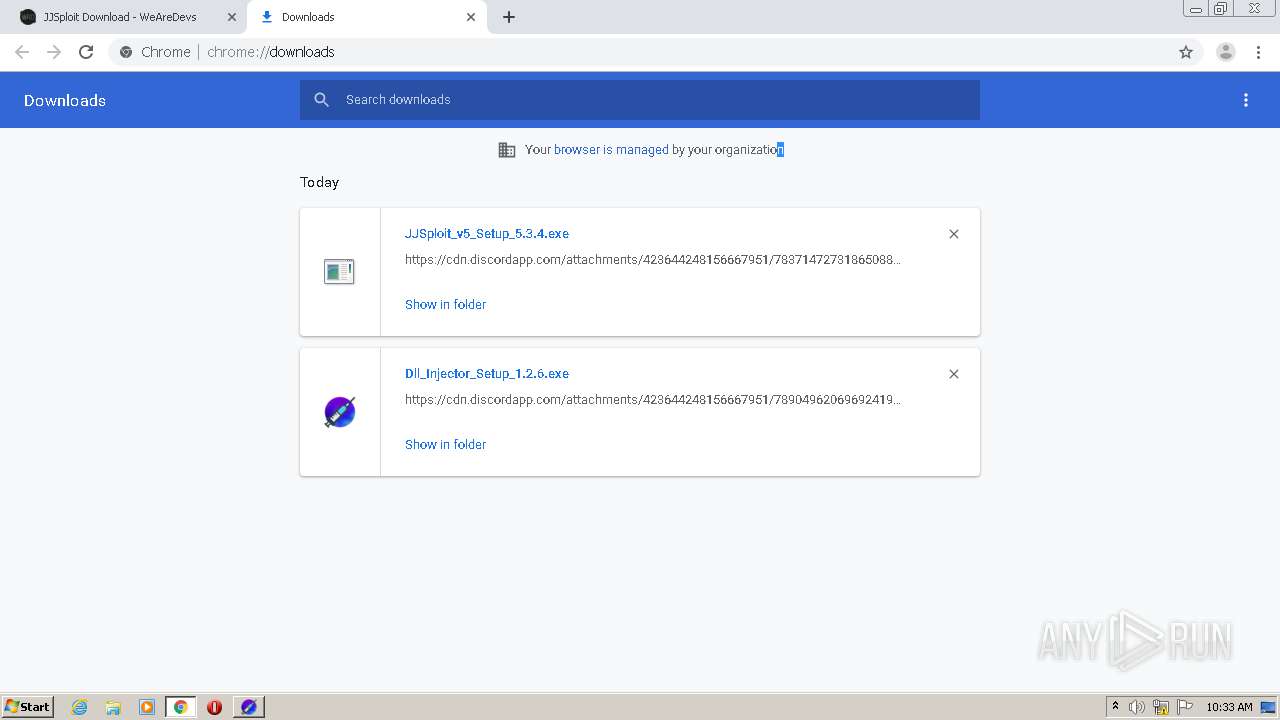
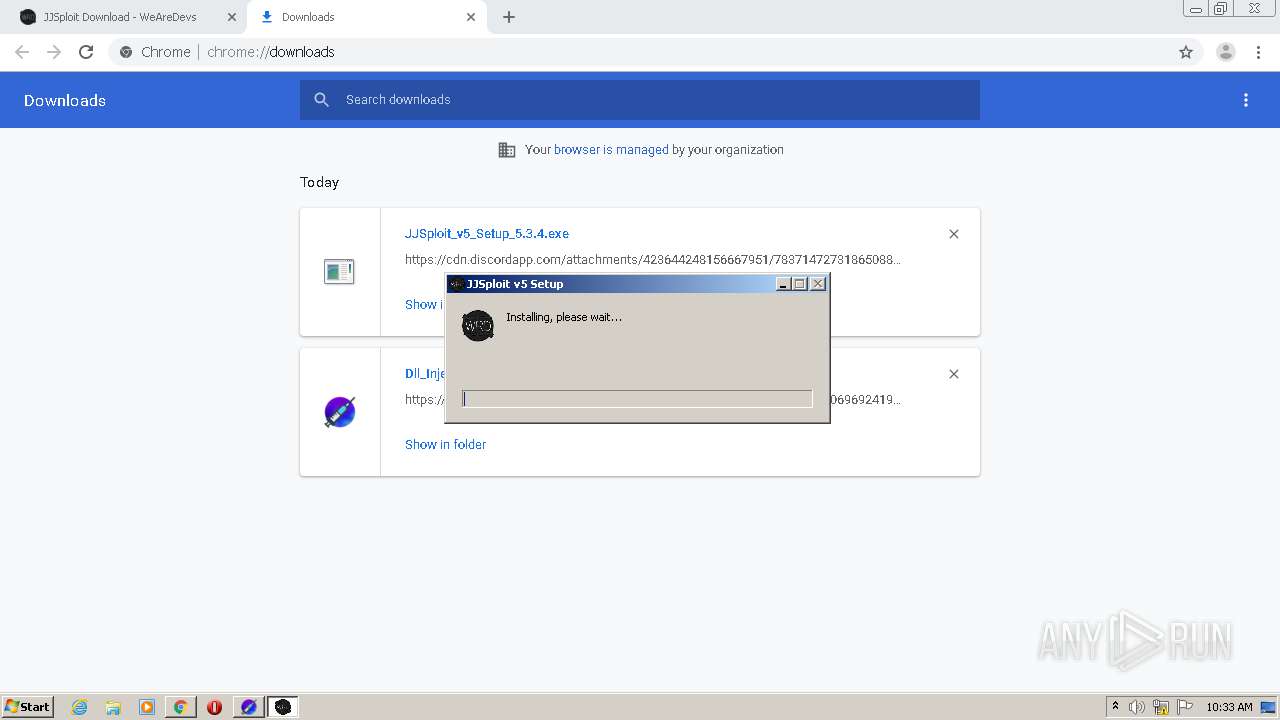
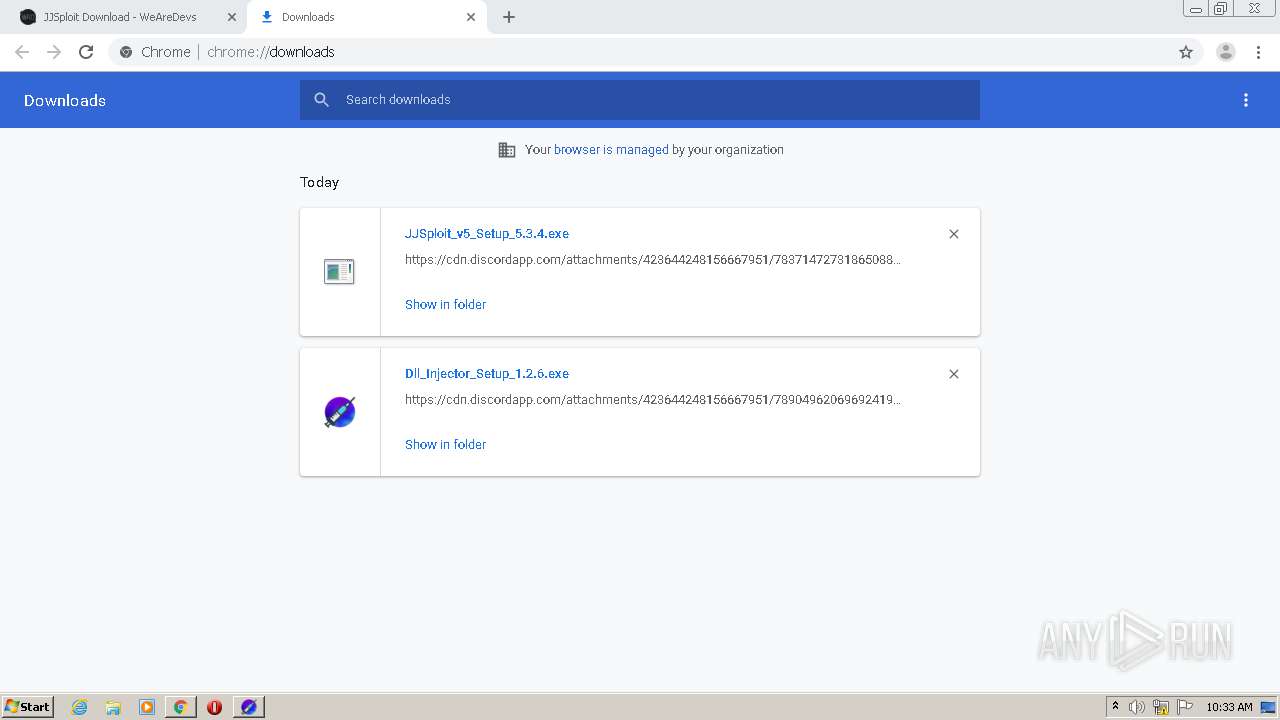
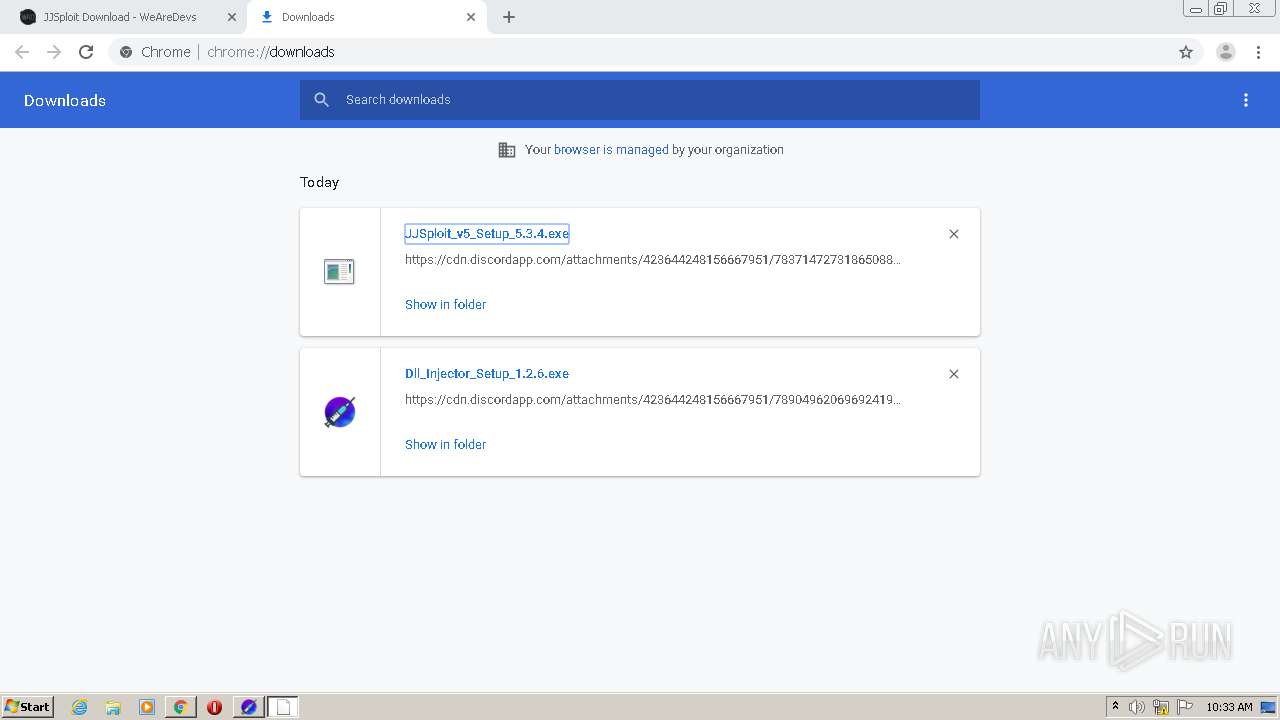
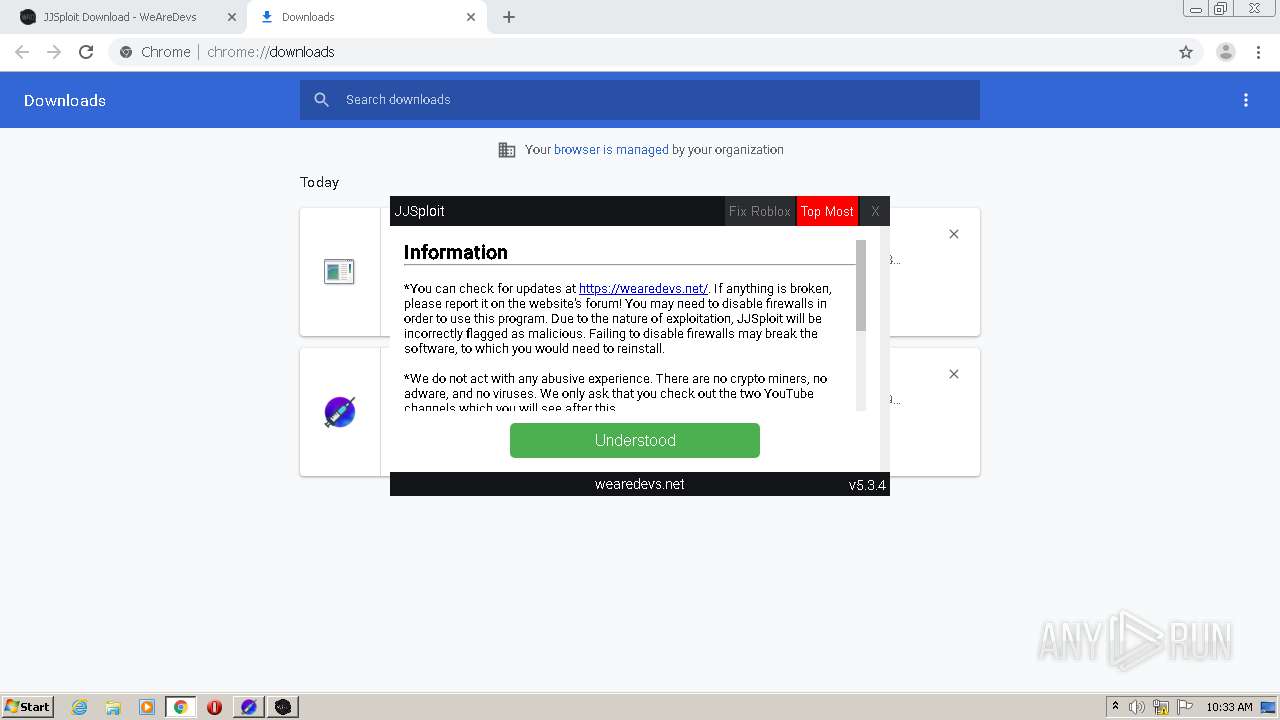
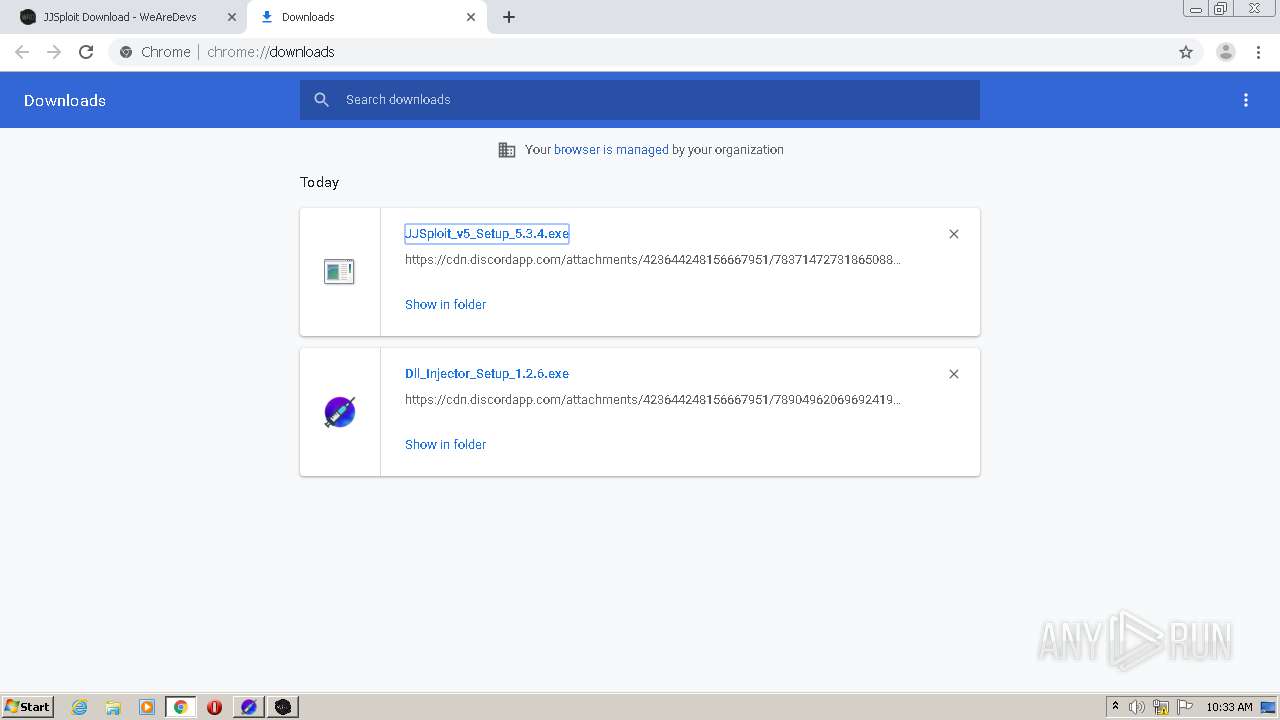
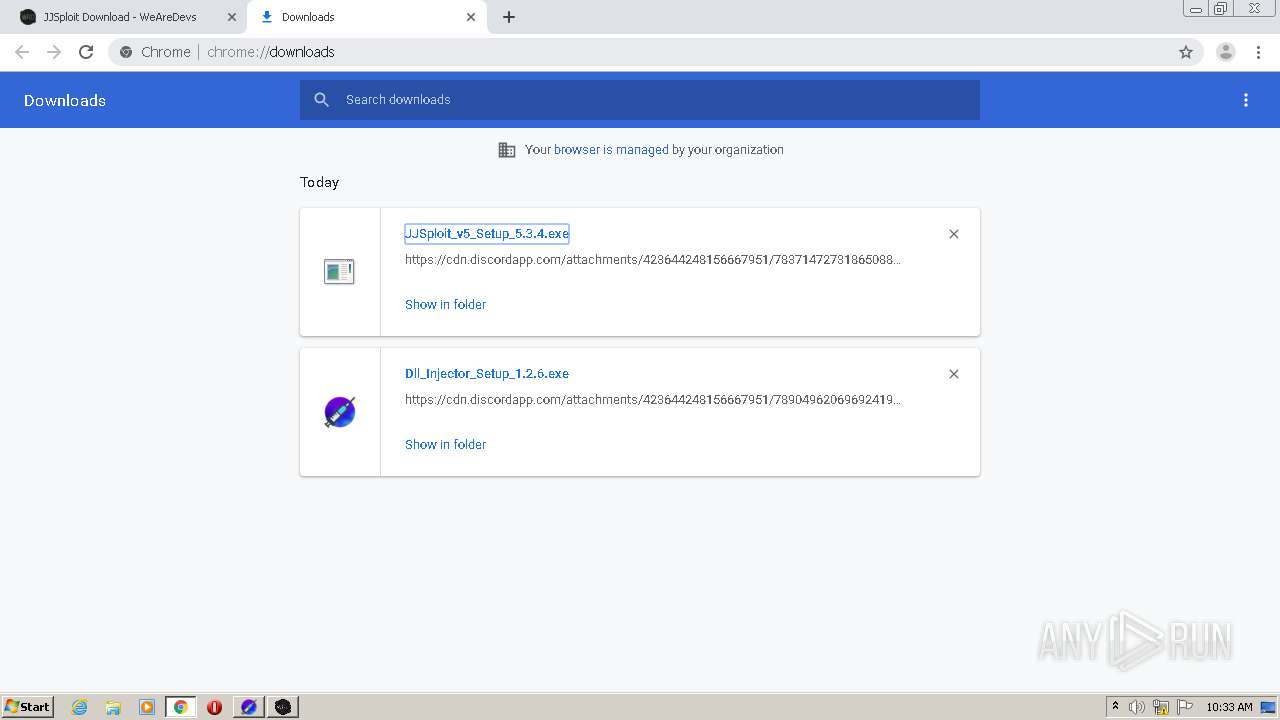
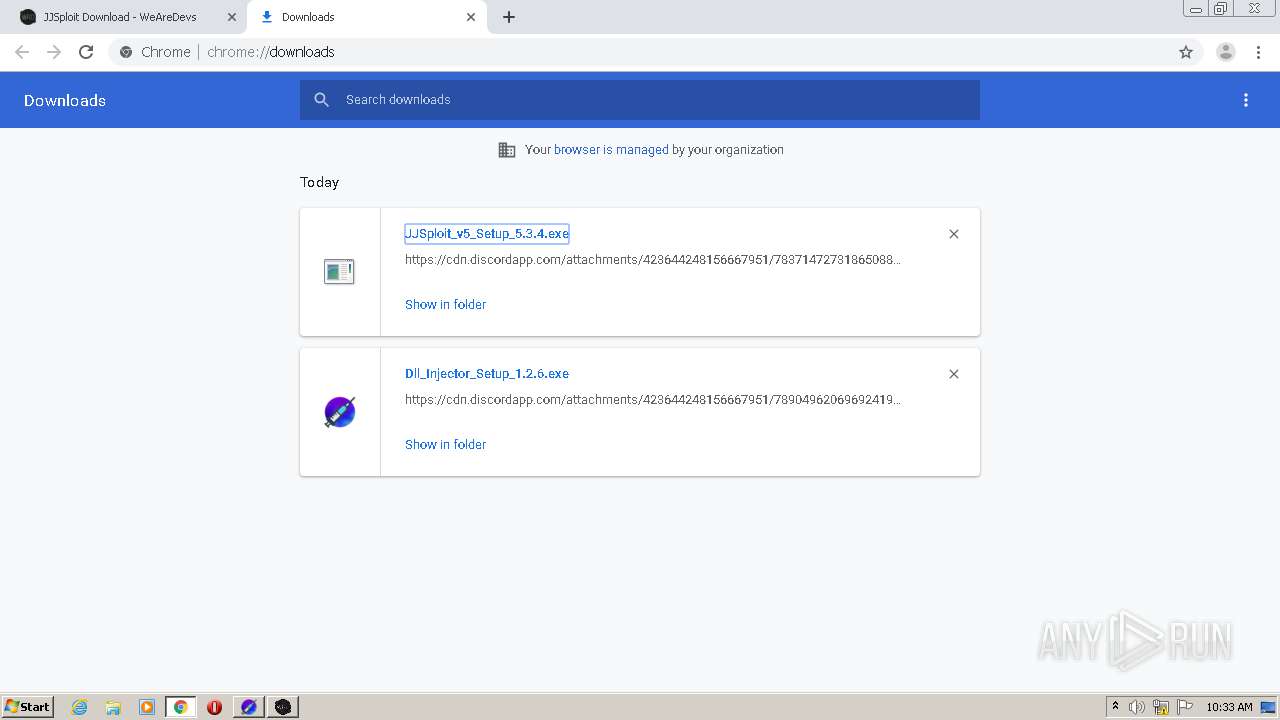
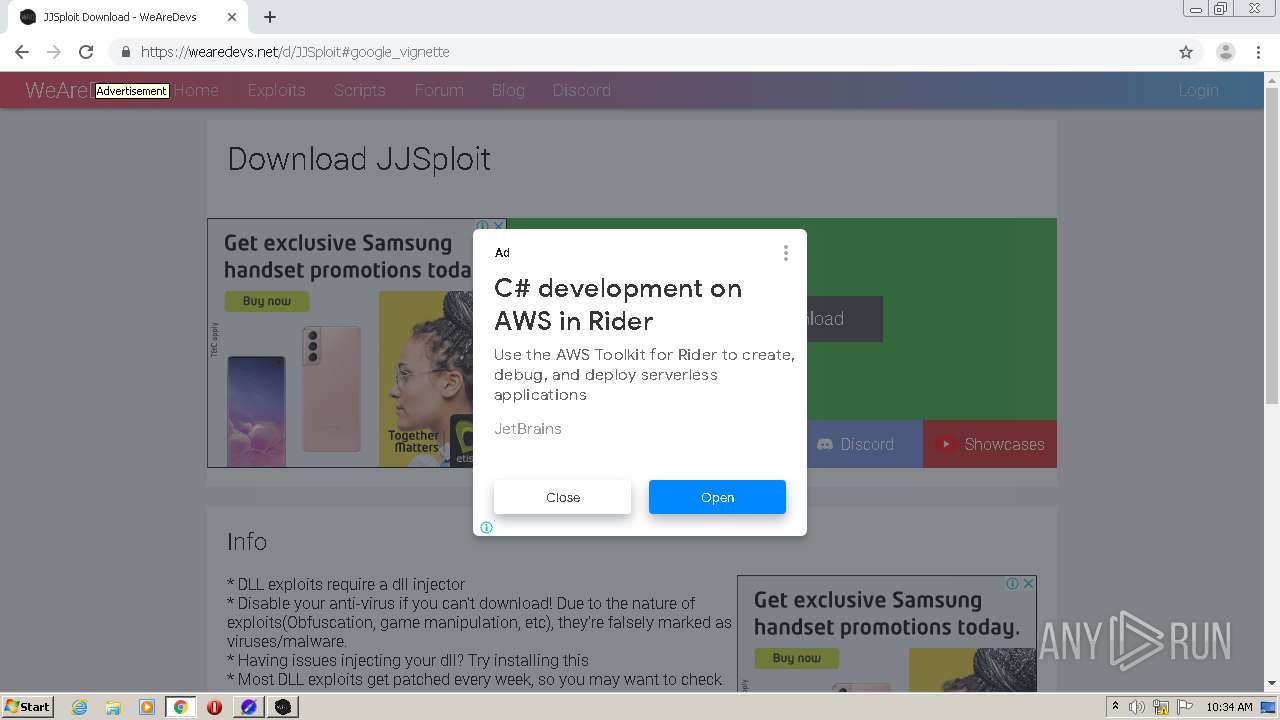
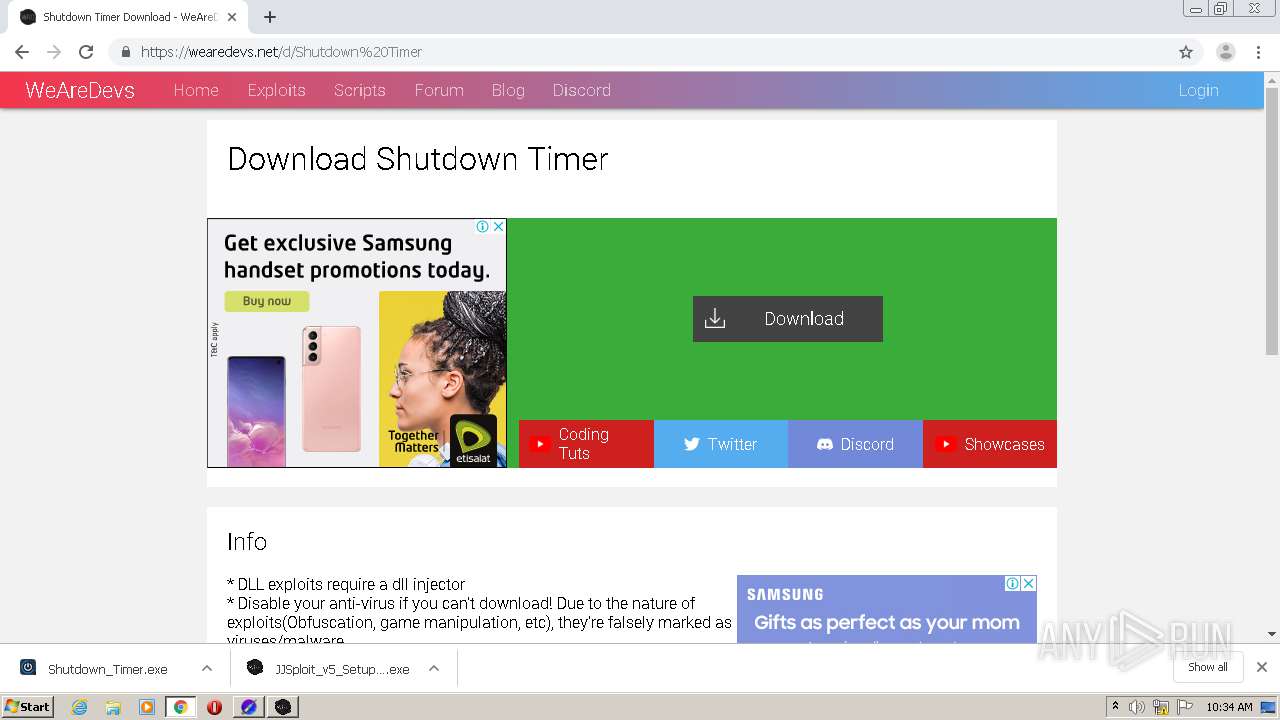
Application was dropped or rewritten from another process
- Dll_Injector_Setup_1.2.6.exe (PID: 2156)
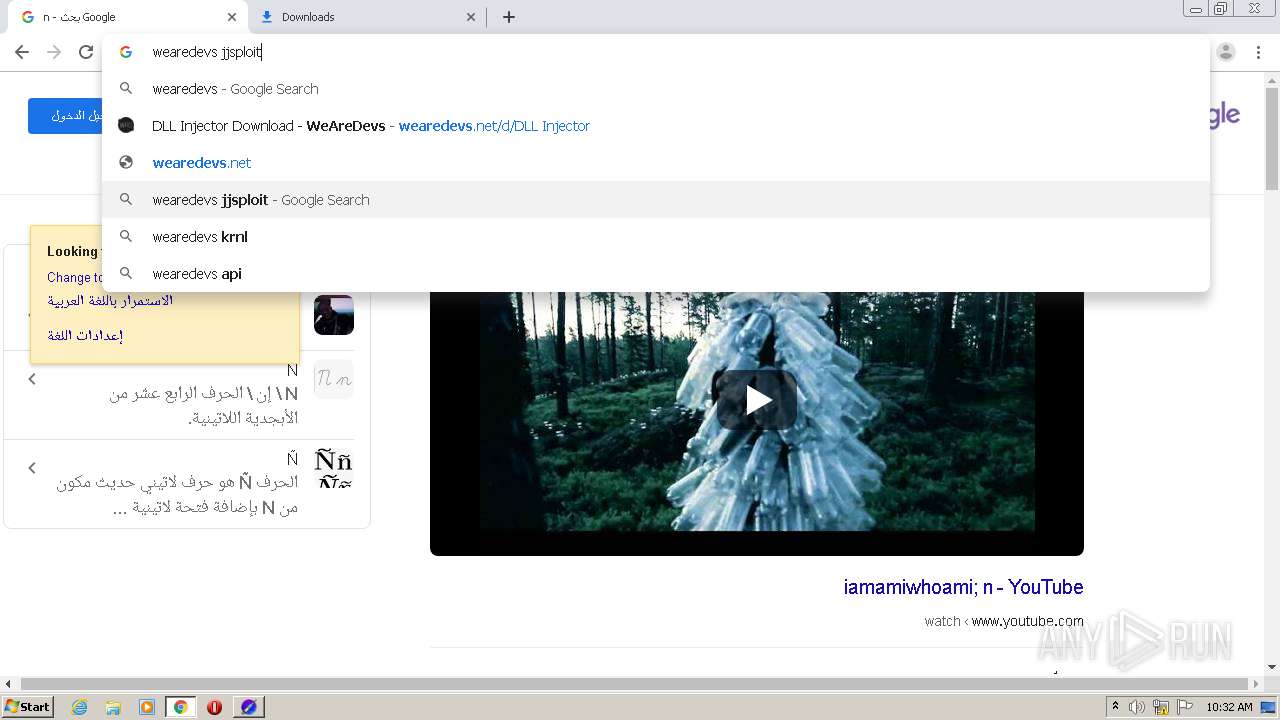
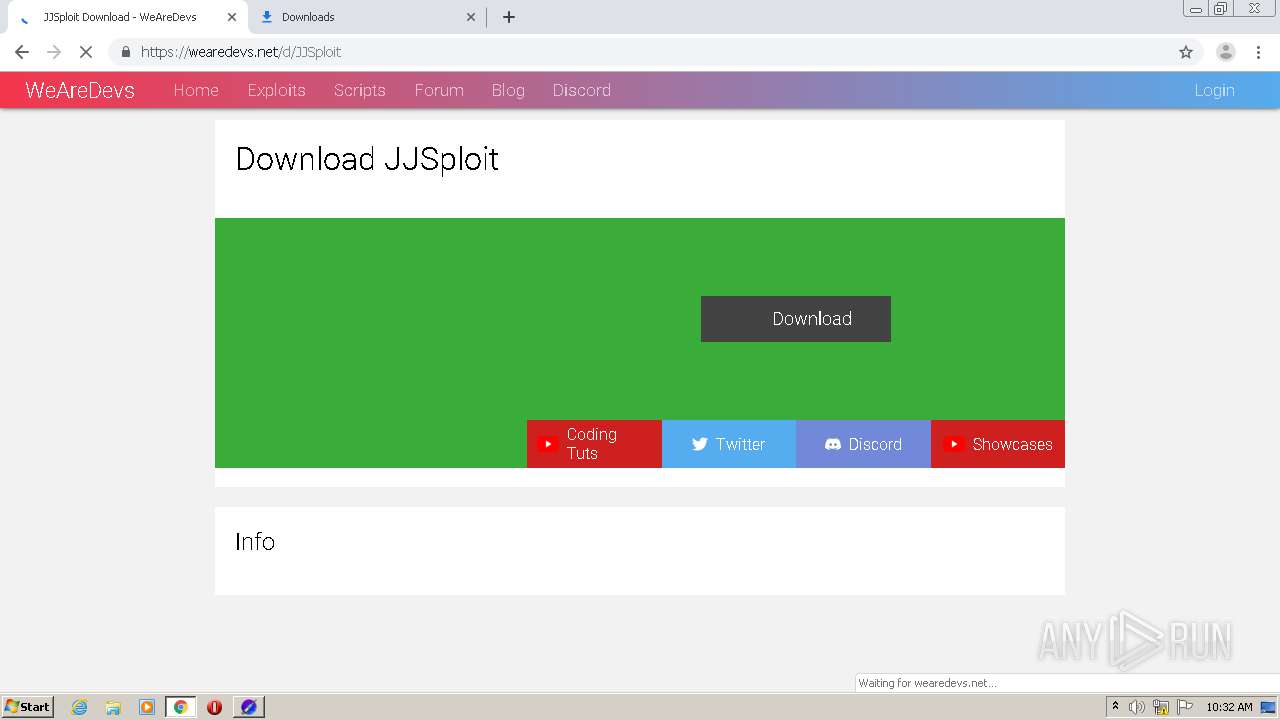
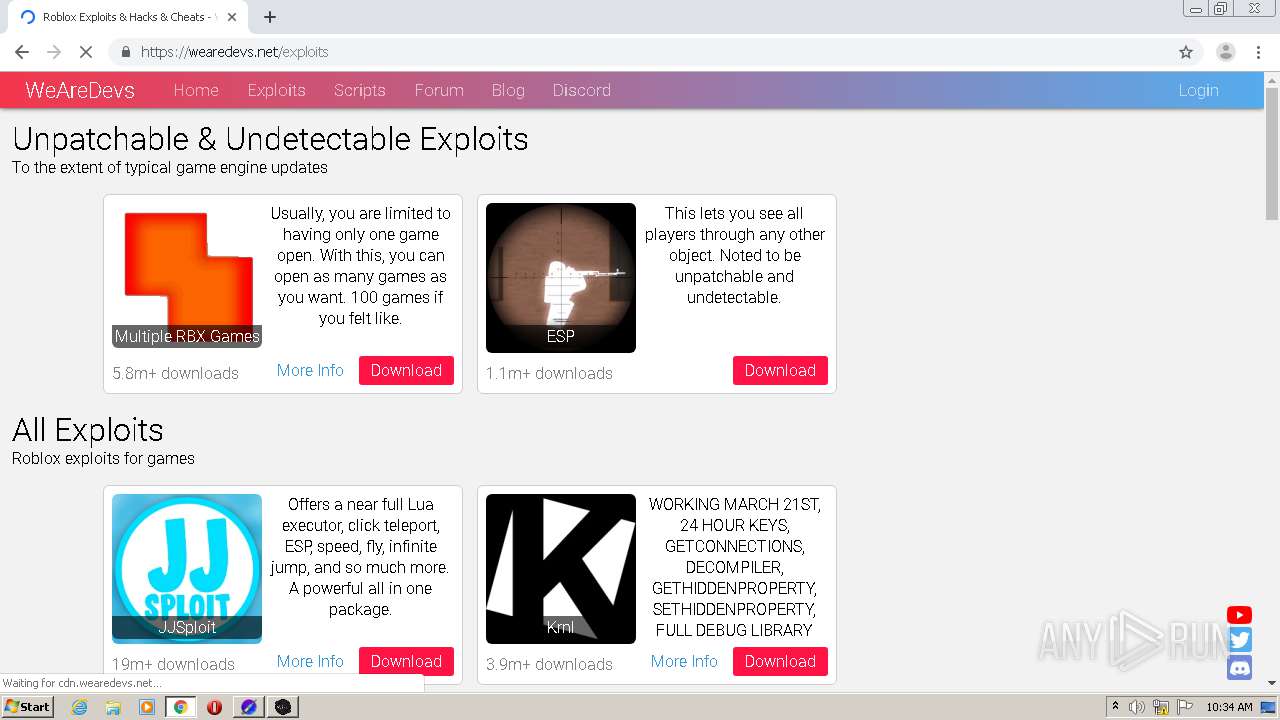
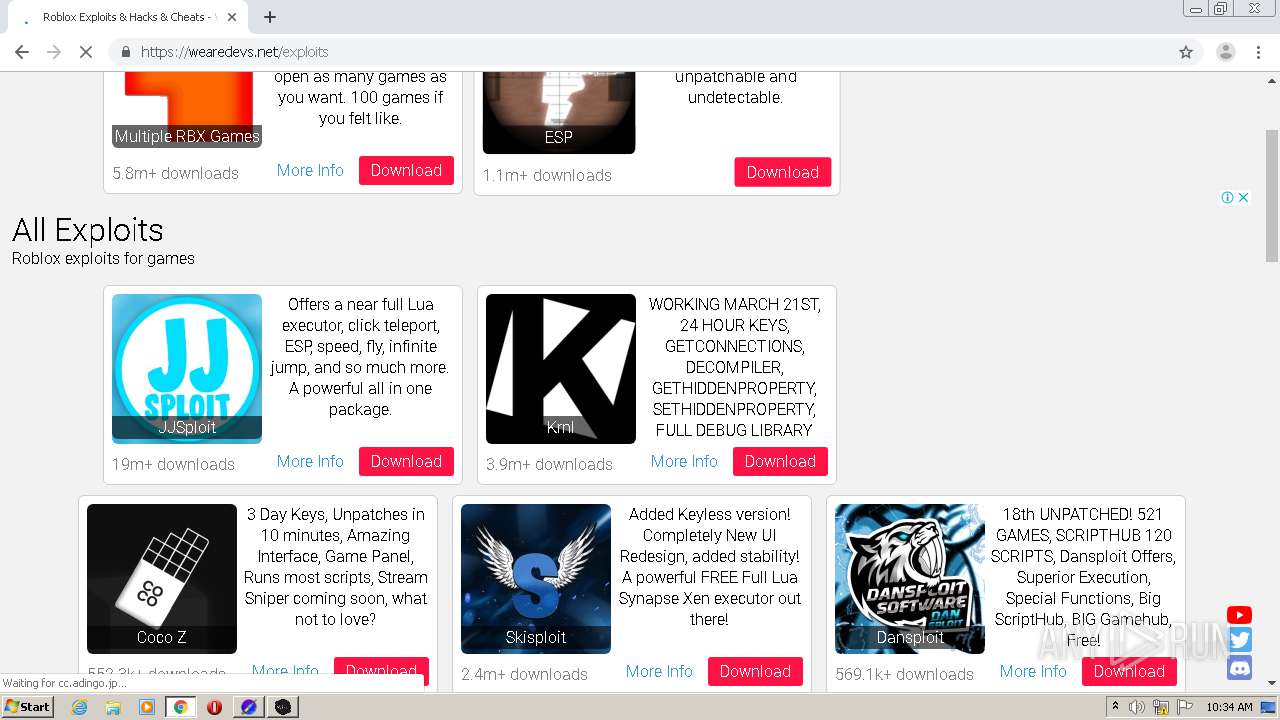
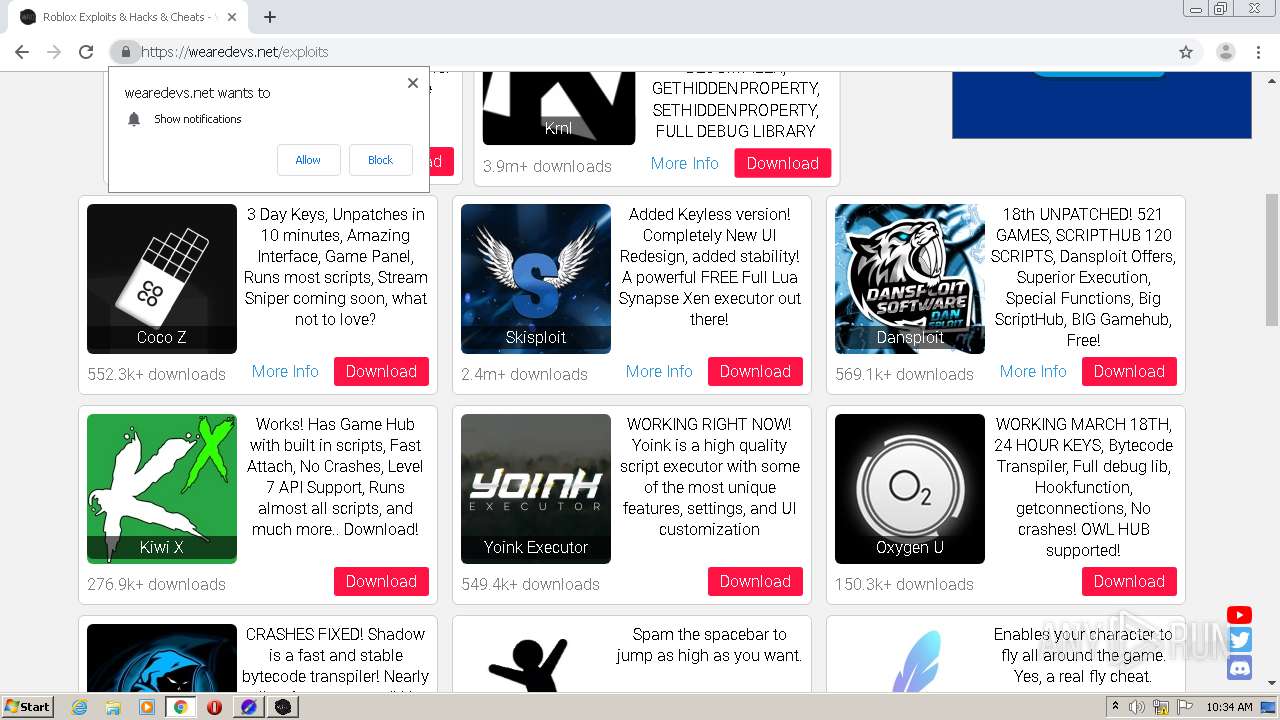
- JJSploit_v5_Setup_5.3.4.exe (PID: 1460)
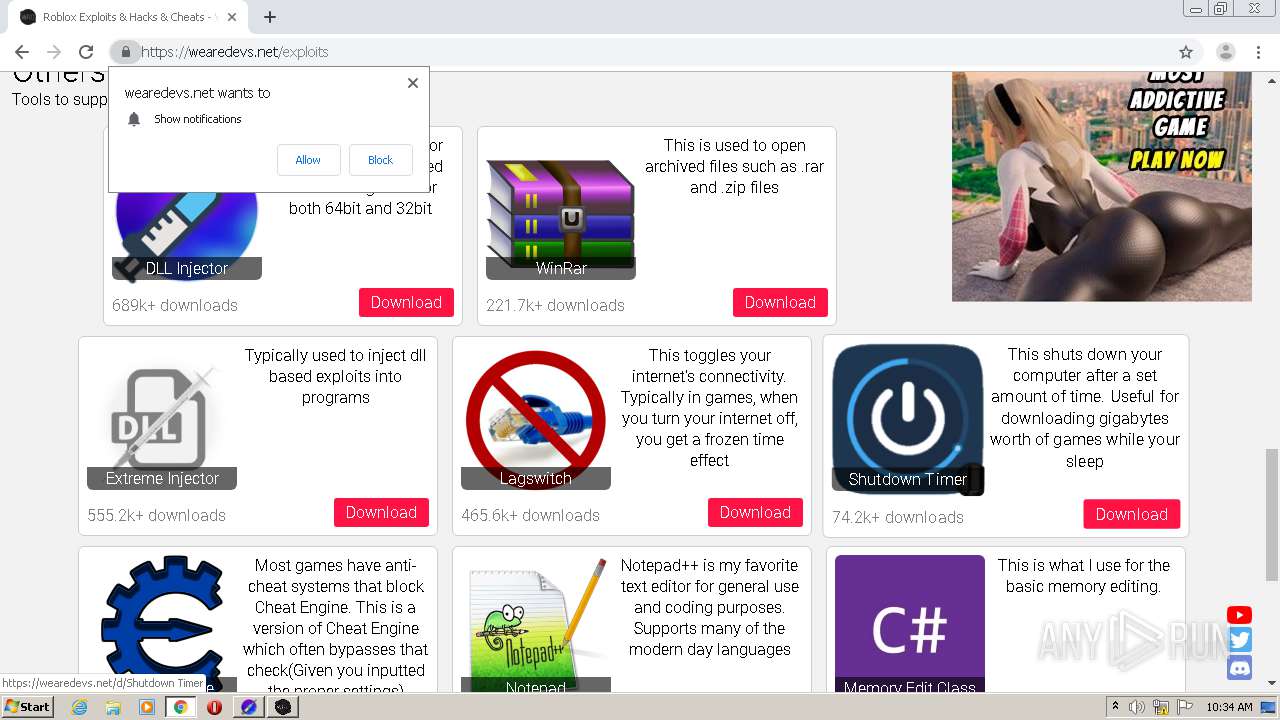
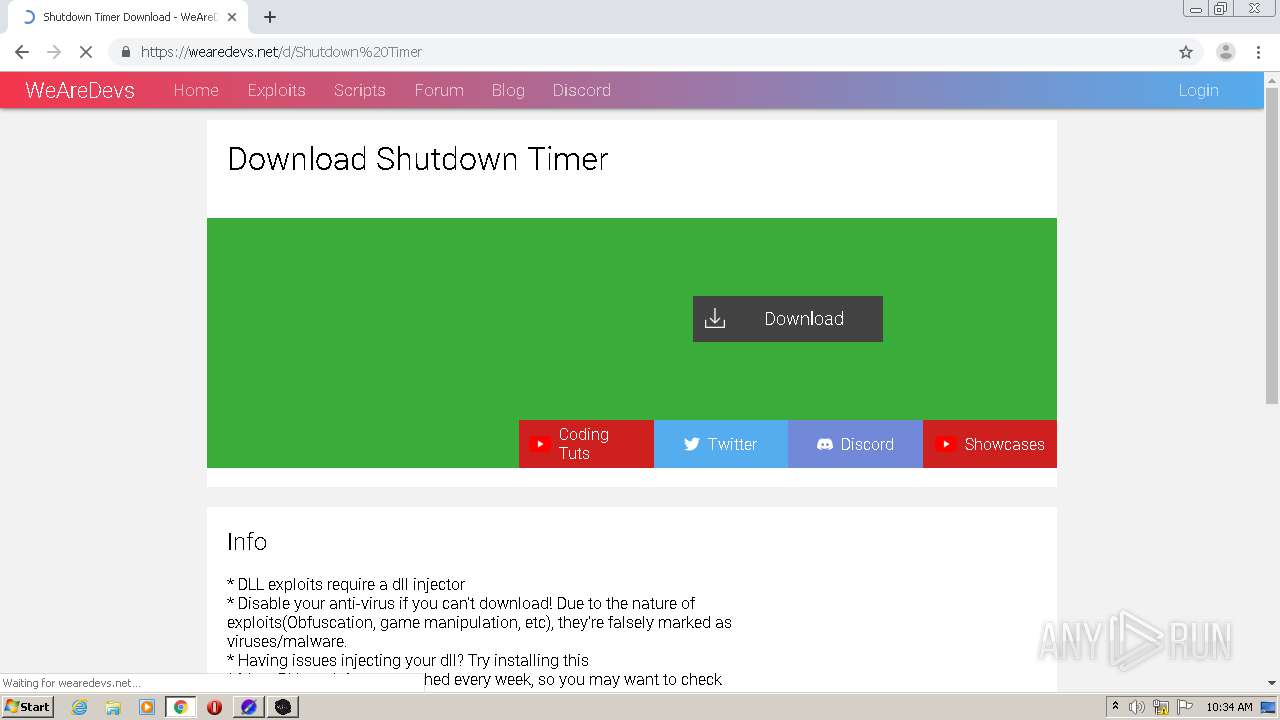
- Shutdown_Timer.exe (PID: 3956)
Loads dropped or rewritten executable
- Dll_Injector_Setup_1.2.6.exe (PID: 2156)
- Dll Injector.exe (PID: 2500)
- Dll Injector.exe (PID: 1456)
- Dll Injector.exe (PID: 2700)
- JJSploit v5.exe (PID: 3032)
- Dll Injector.exe (PID: 1696)
- Dll Injector.exe (PID: 1748)
- JJSploit v5.exe (PID: 3640)
- Dll Injector.exe (PID: 952)
- Dll Injector.exe (PID: 3316)
- Dll Injector.exe (PID: 556)
- JJSploit_v5_Setup_5.3.4.exe (PID: 1460)
- JJSploit v5.exe (PID: 1444)
- Dll Injector.exe (PID: 688)
SUSPICIOUS
Drops a file that was compiled in debug mode
- Dll_Injector_Setup_1.2.6.exe (PID: 2156)
- JJSploit_v5_Setup_5.3.4.exe (PID: 1460)
- JJSploit v5.exe (PID: 3032)
- chrome.exe (PID: 2920)
Executable content was dropped or overwritten
- Dll_Injector_Setup_1.2.6.exe (PID: 2156)
- JJSploit_v5_Setup_5.3.4.exe (PID: 1460)
- JJSploit v5.exe (PID: 3032)
- chrome.exe (PID: 2920)
Drops a file with a compile date too recent
- Dll_Injector_Setup_1.2.6.exe (PID: 2156)
- JJSploit v5.exe (PID: 3032)
Creates a software uninstall entry
- Dll_Injector_Setup_1.2.6.exe (PID: 2156)
- JJSploit_v5_Setup_5.3.4.exe (PID: 1460)
Creates files in the user directory
- Dll_Injector_Setup_1.2.6.exe (PID: 2156)
- Dll Injector.exe (PID: 2500)
- Dll Injector.exe (PID: 688)
- JJSploit_v5_Setup_5.3.4.exe (PID: 1460)
- JJSploit v5.exe (PID: 3032)
Application launched itself
- Dll Injector.exe (PID: 2500)
- JJSploit v5.exe (PID: 3032)
Drops a file with too old compile date
- JJSploit_v5_Setup_5.3.4.exe (PID: 1460)
INFO
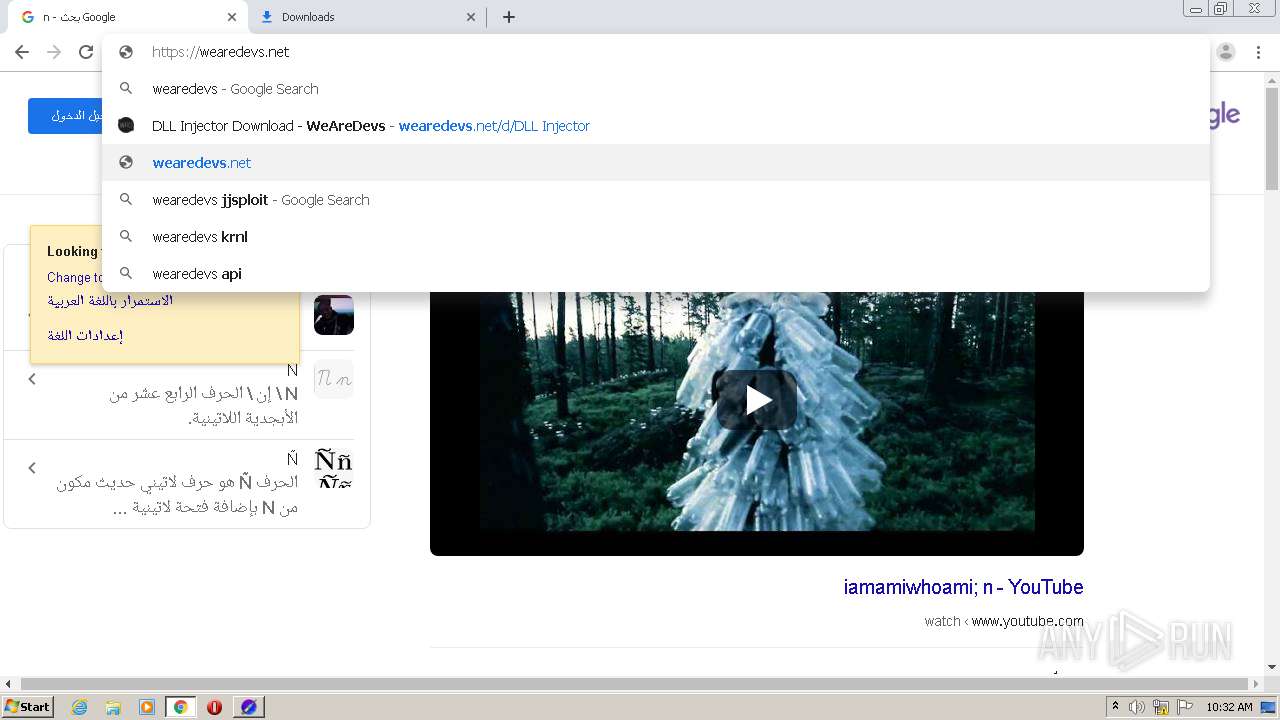
Reads the hosts file
- chrome.exe (PID: 2920)
- chrome.exe (PID: 2932)
- Dll Injector.exe (PID: 2500)
- Dll Injector.exe (PID: 688)
- JJSploit v5.exe (PID: 3032)
Changes default file association
- chrome.exe (PID: 2920)
Application launched itself
- chrome.exe (PID: 2920)
- chrome.exe (PID: 3100)
- chrome.exe (PID: 3516)
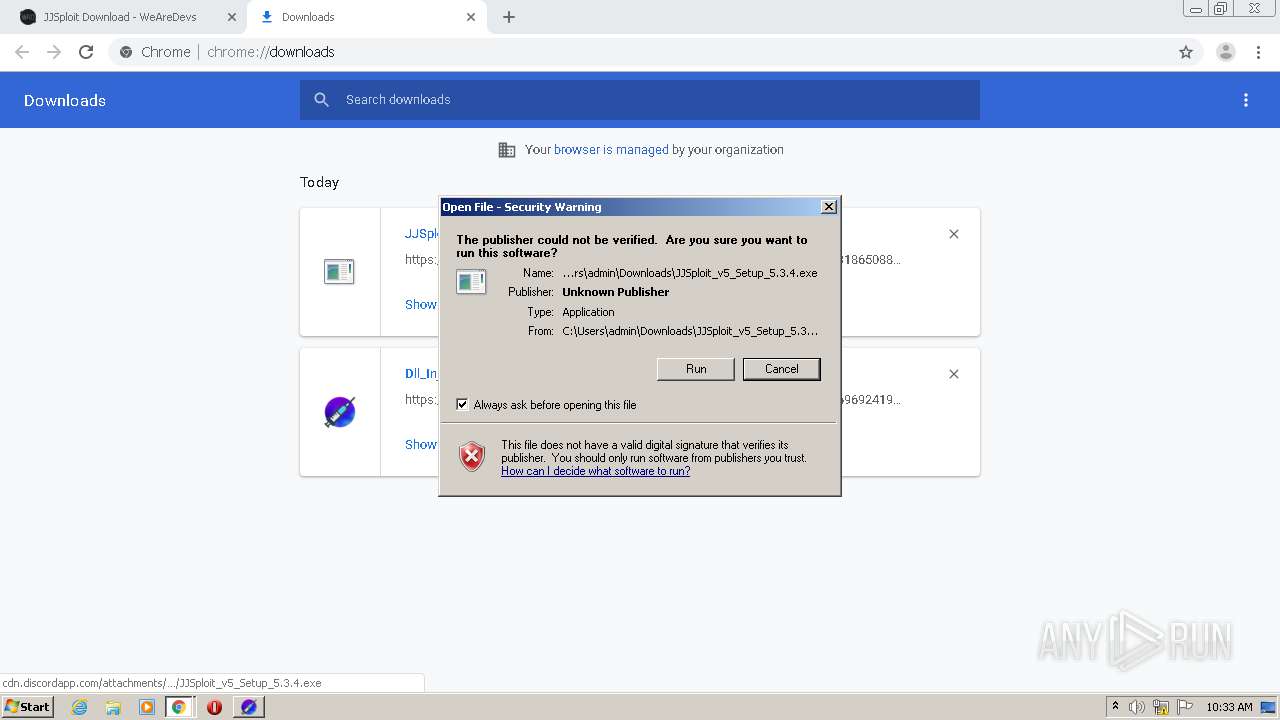
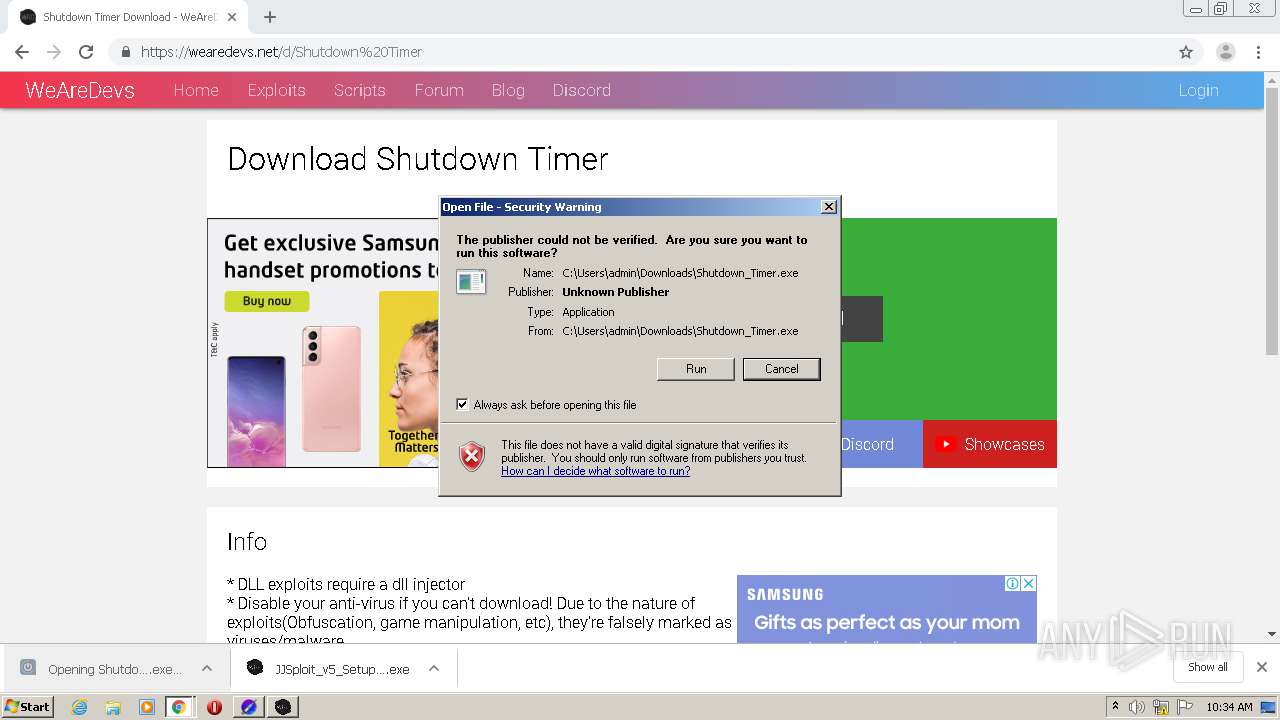
Manual execution by user
- Dll Injector.exe (PID: 2500)
- JJSploit v5.exe (PID: 3032)
Reads settings of System Certificates
- chrome.exe (PID: 2932)
Creates files in the user directory
- chrome.exe (PID: 2920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
108
Monitored processes
62
Malicious processes
5
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Users\admin\AppData\Local\Programs\dllinjector\Dll Injector.exe" --type=gpu-process --field-trial-handle=1024,5730952631218216575,15282705199150304504,131072 --enable-features=WebComponentsV0Enabled --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1188 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\dllinjector\Dll Injector.exe | — | Dll Injector.exe | |||||||||||
User: admin Company: powell.gg Integrity Level: LOW Description: Dll Injector Exit code: 3221225794 Version: 1.2.6 Modules
| |||||||||||||||
| 688 | "C:\Users\admin\AppData\Local\Programs\dllinjector\Dll Injector.exe" --type=utility --field-trial-handle=1024,5730952631218216575,15282705199150304504,131072 --enable-features=WebComponentsV0Enabled --disable-features=SpareRendererForSitePerProcess --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1432 /prefetch:8 | C:\Users\admin\AppData\Local\Programs\dllinjector\Dll Injector.exe | Dll Injector.exe | ||||||||||||
User: admin Company: powell.gg Integrity Level: MEDIUM Description: Dll Injector Exit code: 1073807364 Version: 1.2.6 Modules
| |||||||||||||||
| 952 | "C:\Users\admin\AppData\Local\Programs\dllinjector\Dll Injector.exe" --type=gpu-process --field-trial-handle=1024,5730952631218216575,15282705199150304504,131072 --enable-features=WebComponentsV0Enabled --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1772 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\dllinjector\Dll Injector.exe | — | Dll Injector.exe | |||||||||||
User: admin Company: powell.gg Integrity Level: LOW Description: Dll Injector Exit code: 3221225794 Version: 1.2.6 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,168962880504405073,6961559456149275509,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16365913614985981145 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,168962880504405073,6961559456149275509,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5353409620496957355 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,168962880504405073,6961559456149275509,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6990177295644144521 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,168962880504405073,6961559456149275509,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14772293819889007700 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4568544842413029245 --mojo-platform-channel-handle=1104 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: JJSploit v5 Exit code: 1073807364 Version: 5.3.4 Modules
| |||||||||||||||
| 1456 | "C:\Users\admin\AppData\Local\Programs\dllinjector\Dll Injector.exe" --type=gpu-process --field-trial-handle=1024,5730952631218216575,15282705199150304504,131072 --enable-features=WebComponentsV0Enabled --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\dllinjector\Dll Injector.exe | — | Dll Injector.exe | |||||||||||
User: admin Company: powell.gg Integrity Level: LOW Description: Dll Injector Exit code: 0 Version: 1.2.6 Modules
| |||||||||||||||
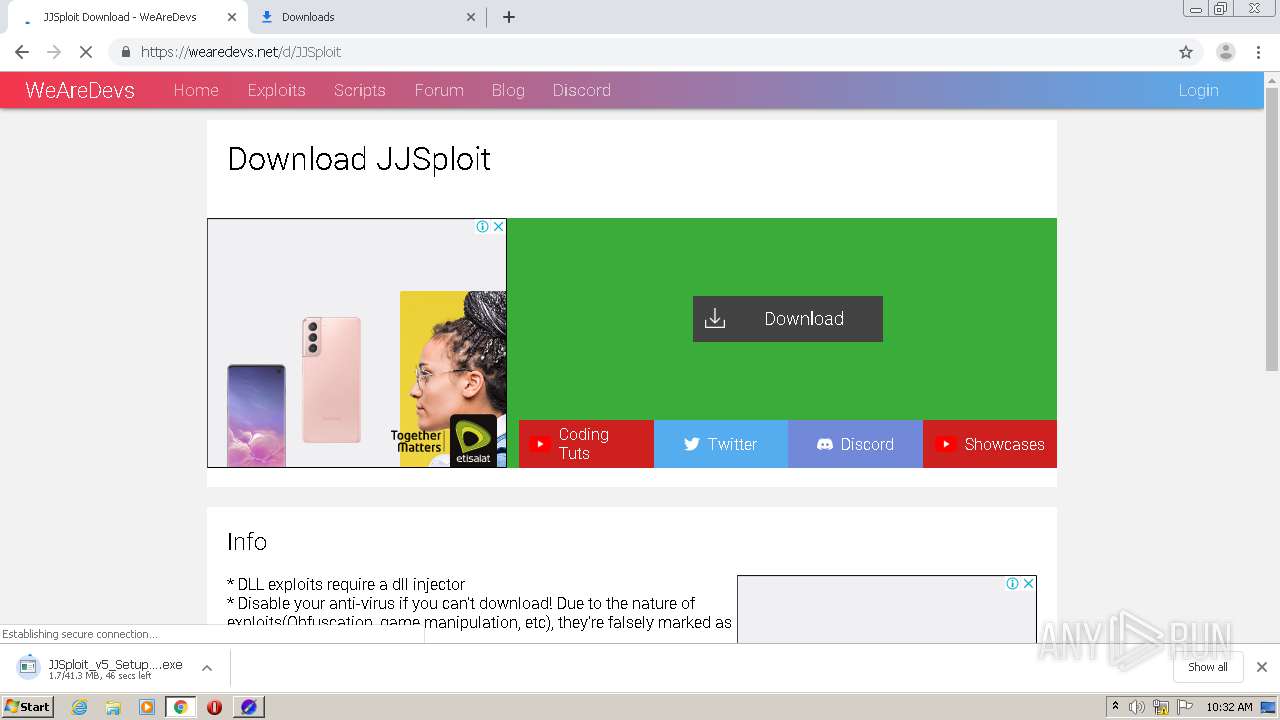
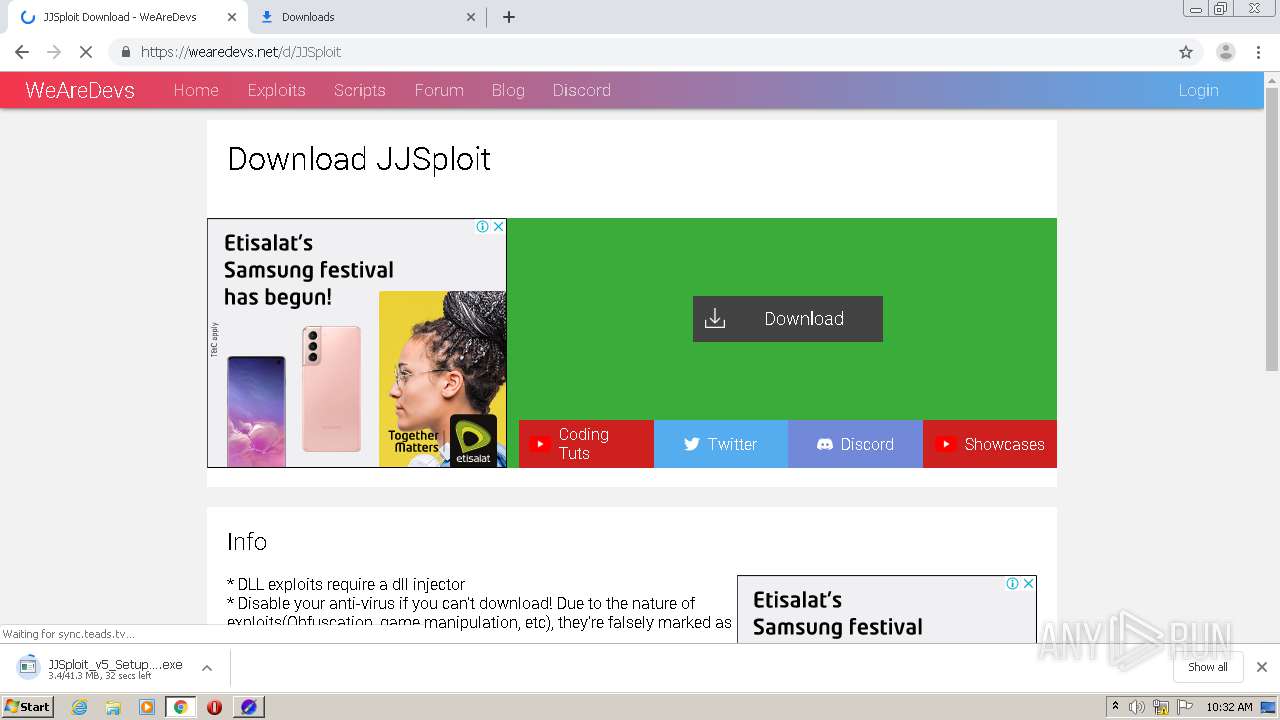
| 1460 | "C:\Users\admin\Downloads\JJSploit_v5_Setup_5.3.4.exe" | C:\Users\admin\Downloads\JJSploit_v5_Setup_5.3.4.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
Total events
2 091
Read events
1 885
Write events
198
Delete events
8
Modification events
| (PID) Process: | (2920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3060) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2920-13260796247965375 |
Value: 259 | |||
| (PID) Process: | (2920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2920) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
44
Suspicious files
284
Text files
197
Unknown types
126
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60572059-B68.pma | — | |
MD5:— | SHA256:— | |||
| 2920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b91efa6a-ea28-433d-8c78-667b5dad62e0.tmp | — | |
MD5:— | SHA256:— | |||
| 2920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 2920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 2920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 2920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF14f7fb.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
147
DNS requests
85
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | chrome.exe | GET | — | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
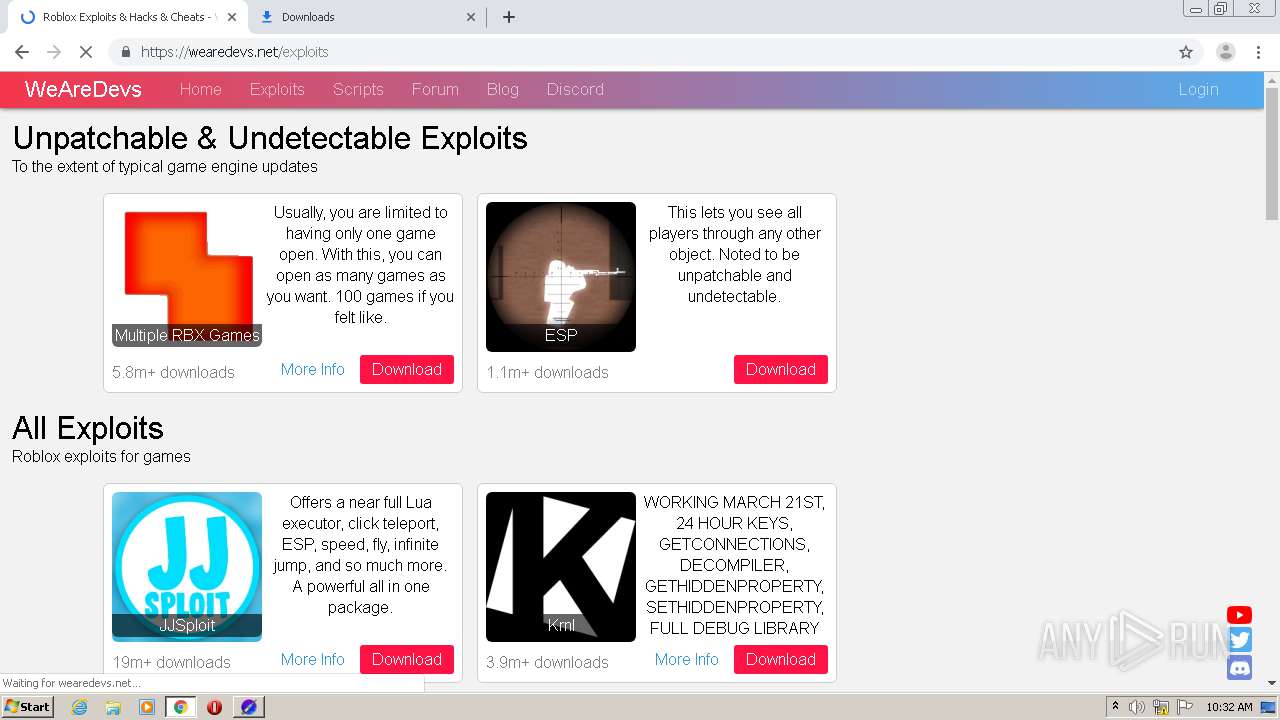
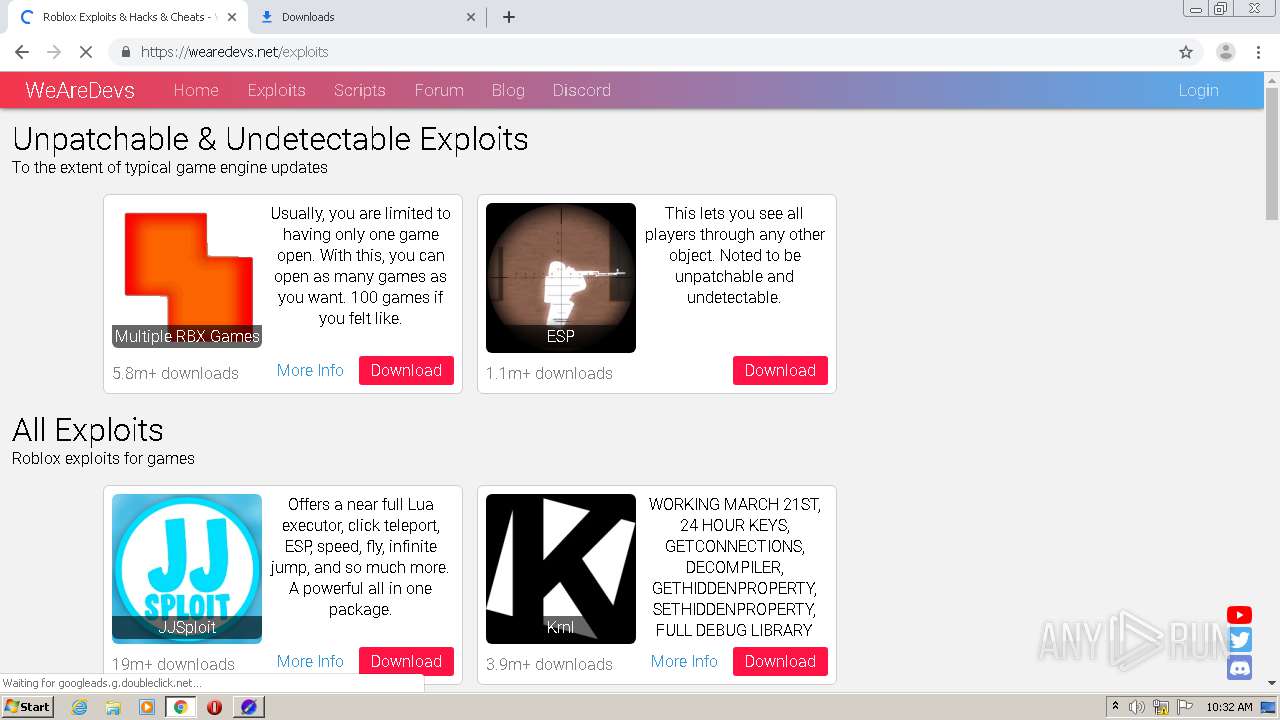
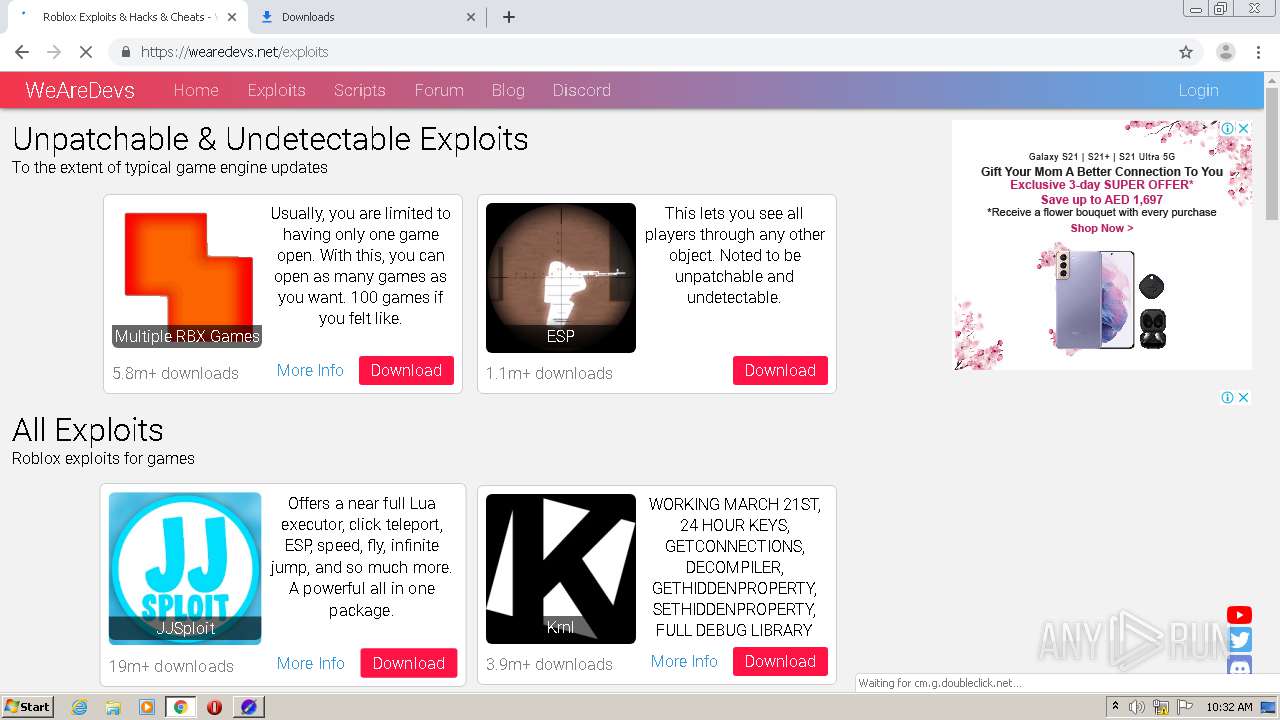
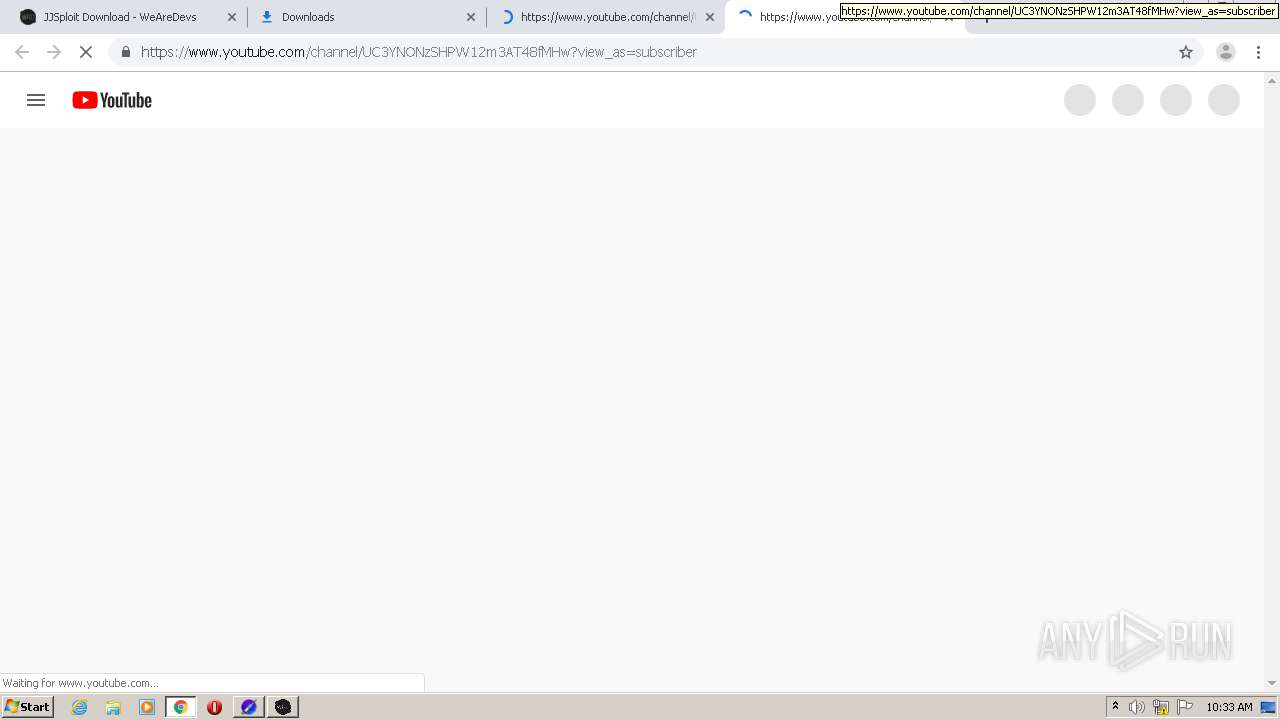
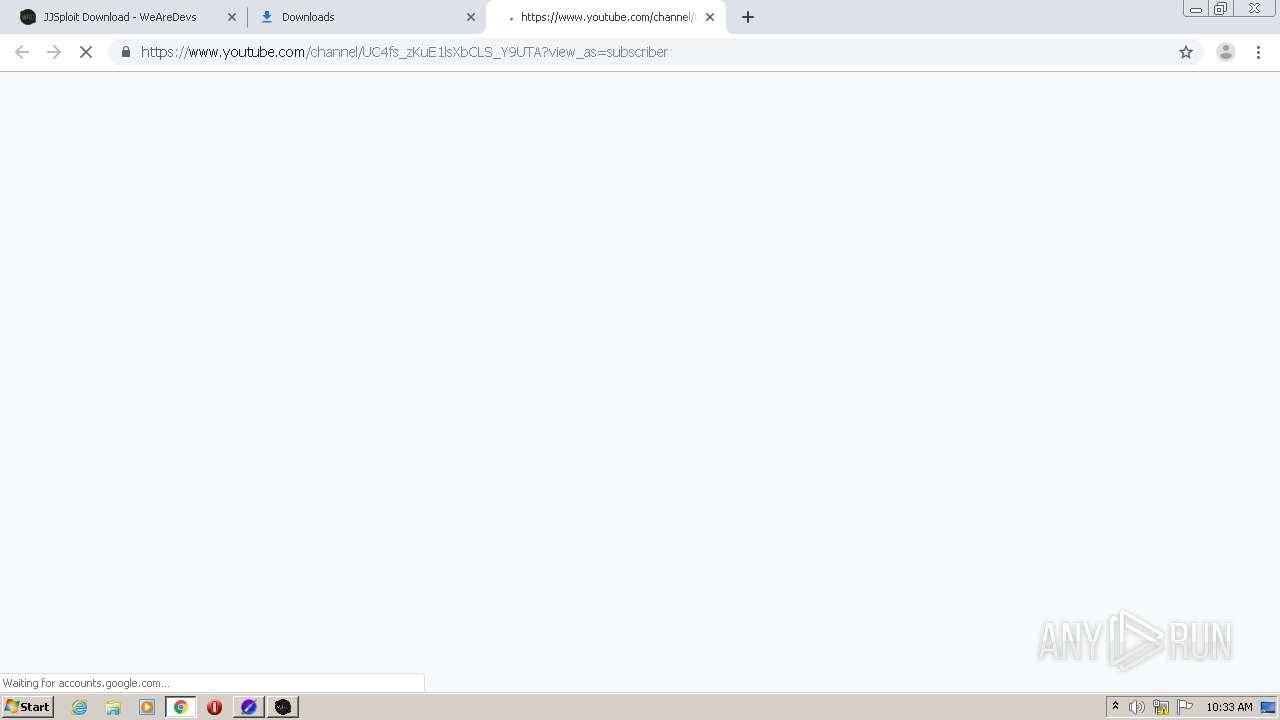
2932 | chrome.exe | 142.250.185.237:443 | accounts.google.com | Google Inc. | US | suspicious |
2932 | chrome.exe | 172.67.71.2:443 | wearedevs.net | — | US | suspicious |
2932 | chrome.exe | 216.58.212.130:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 142.250.185.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 142.250.186.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
2932 | chrome.exe | 142.250.186.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 142.250.186.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2932 | chrome.exe | 216.58.212.163:443 | www.google.ae | Google Inc. | US | whitelisted |
2932 | chrome.exe | 142.250.186.66:443 | partner.googleadservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wearedevs.net |
| whitelisted |
accounts.google.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |