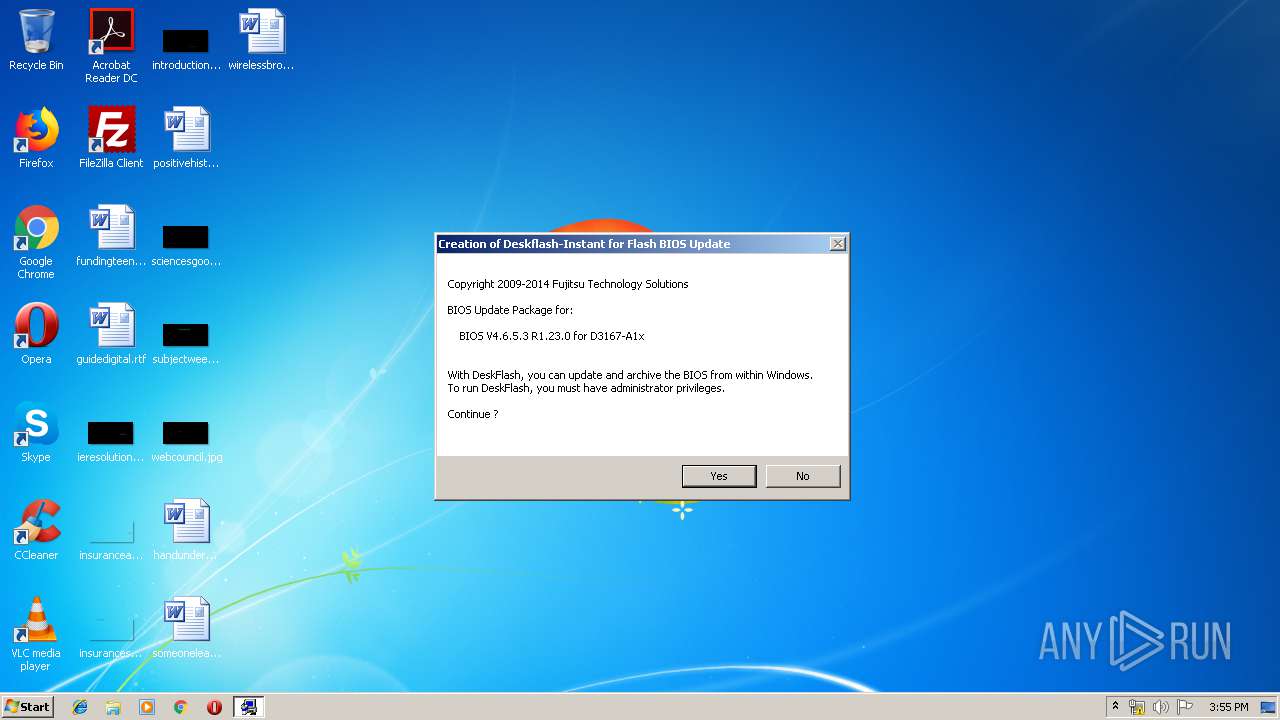
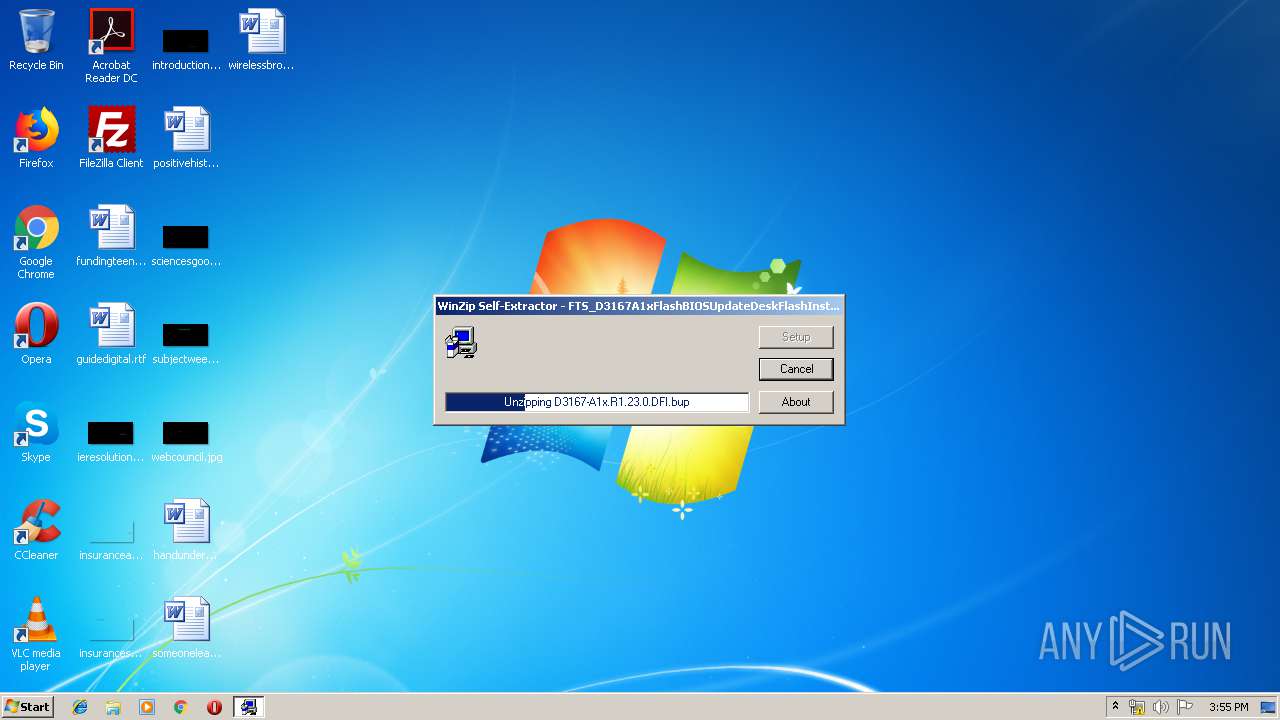
| File name: | FTS_D3167A1xFlashBIOSUpdateDeskFlashInstant_V4653R1230_1119437.EXE |
| Full analysis: | https://app.any.run/tasks/c11452f1-be70-4cb2-8608-c478e684dc75 |
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2019, 14:54:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DF238631CE06025C752F3222A9D8B88C |
| SHA1: | 67C36E09A4912F1BEC81AF2A6C7242B994B37E9A |
| SHA256: | 82E203623DE8B6540BBDBB19894676E57A66A429E339A66E6303641CC2A0BF7E |
| SSDEEP: | 196608:NaeNpy5KjdroAhxOmLIXxHlaIKQd94U+q2g9u1u4rSR:AeNPjJoxX5laIKQXH+Xg92u |
MALICIOUS
Application was dropped or rewritten from another process
- regsvr32.exe (PID: 3668)
- regsvr32.exe (PID: 2912)
- regsvr32.exe (PID: 3044)
- regsvr32.exe (PID: 2156)
- DrvInstall.exe (PID: 2256)
- DskFlash.exe (PID: 2260)
- DskFlash.dat (PID: 3008)
- DF_UEFI.exe (PID: 3764)
- regsvr32.exe (PID: 4076)
- DVAnPMan.exe (PID: 3172)
- HaBFlash.exe (PID: 1332)
- SRP.exe (PID: 2996)
- UpdPnpDr.exe (PID: 3004)
- DrvInstall.exe (PID: 3012)
- UpdPnpDr.exe (PID: 3516)
- RmPnpDr.exe (PID: 3824)
- DskFlash.exe (PID: 656)
- CertMgr.exe (PID: 3944)
- CertMgr.exe (PID: 2188)
- CertMgr.exe (PID: 1440)
- CertMgr.exe (PID: 3628)
- HaBFlash.exe (PID: 3204)
- Setup.exe (PID: 2836)
- DrvInstall.exe (PID: 3724)
- SRP.exe (PID: 1372)
- HaBFlash.exe (PID: 2232)
- DVAnPMan.exe (PID: 3424)
- regsvr32.exe (PID: 3628)
- regsvr32.exe (PID: 2892)
- DrvInstall.exe (PID: 3548)
- RmPnpDr.exe (PID: 2208)
- regsvr32.exe (PID: 3436)
- regsvr32.exe (PID: 352)
- regsvr32.exe (PID: 1088)
- _TinDel.exe (PID: 332)
Loads dropped or rewritten executable
- DF_UEFI.exe (PID: 3764)
- regsvr32.exe (PID: 3668)
- regsvr32.exe (PID: 2912)
- regsvr32.exe (PID: 4076)
- DrvInstall.exe (PID: 2256)
- regsvr32.exe (PID: 3044)
- DrvInstall.exe (PID: 3012)
- DskFlash.exe (PID: 656)
- HaBFlash.exe (PID: 3204)
- regsvr32.exe (PID: 2156)
- Setup.exe (PID: 2836)
- DrvInstall.exe (PID: 3548)
- regsvr32.exe (PID: 2892)
- regsvr32.exe (PID: 3628)
- regsvr32.exe (PID: 3436)
- DrvInstall.exe (PID: 3724)
- regsvr32.exe (PID: 352)
- regsvr32.exe (PID: 1088)
Changes settings of System certificates
- CertMgr.exe (PID: 1440)
- CertMgr.exe (PID: 3944)
- CertMgr.exe (PID: 2188)
- CertMgr.exe (PID: 3628)
- UpdPnpDr.exe (PID: 3004)
SUSPICIOUS
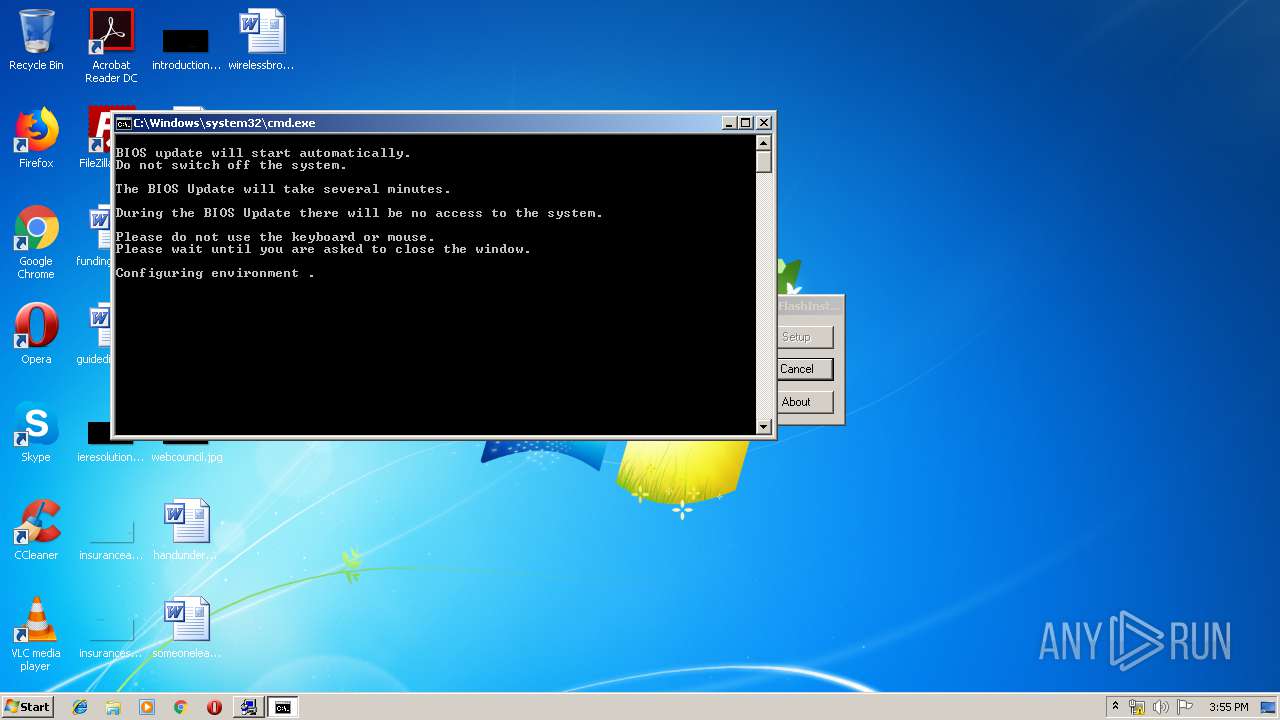
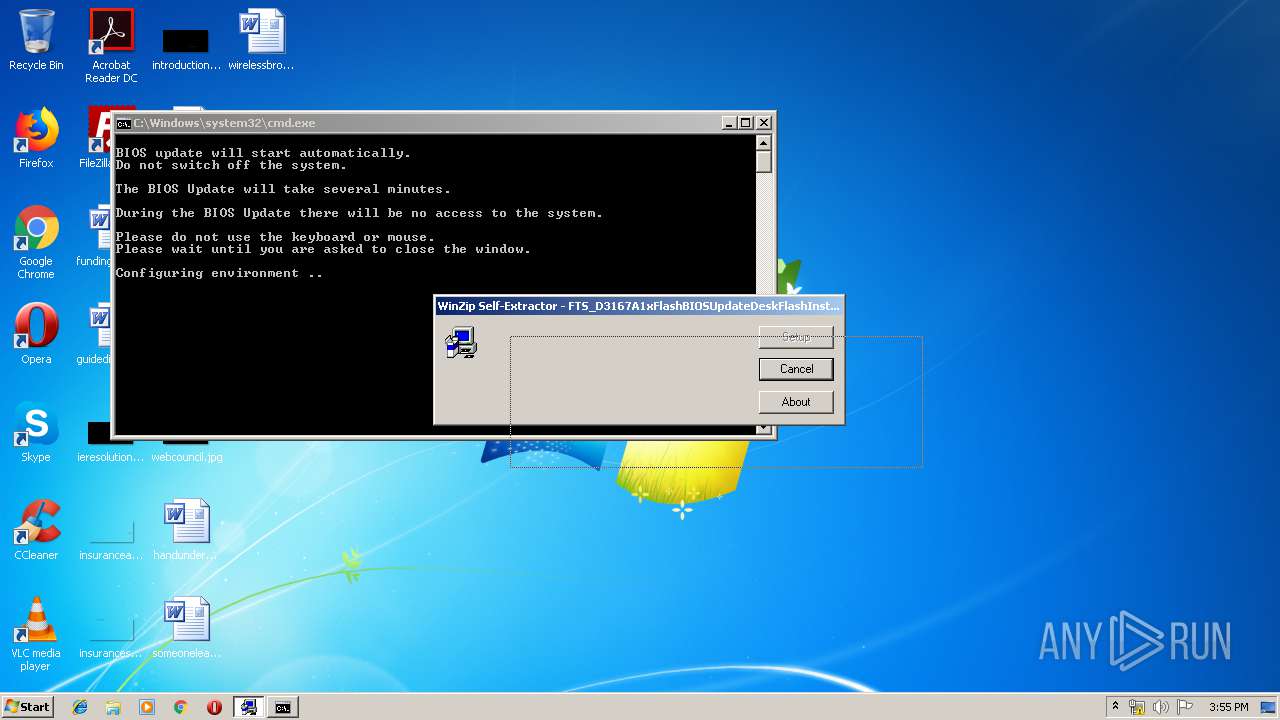
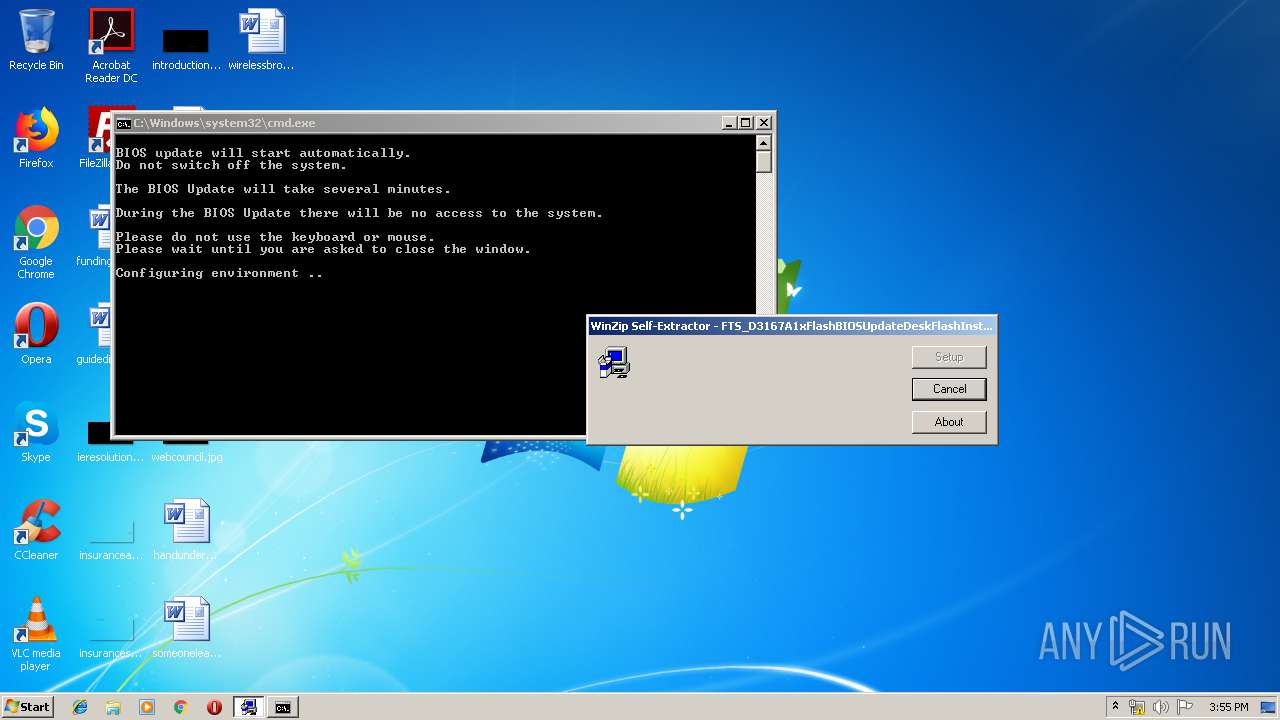
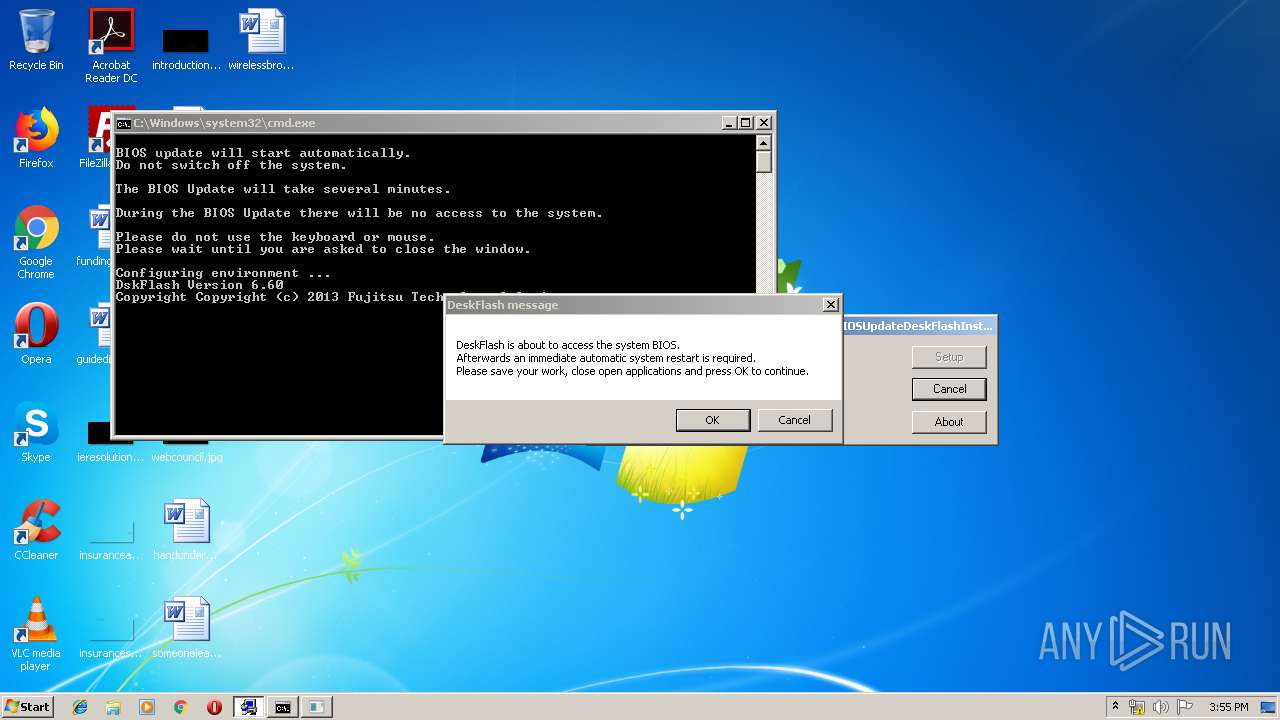
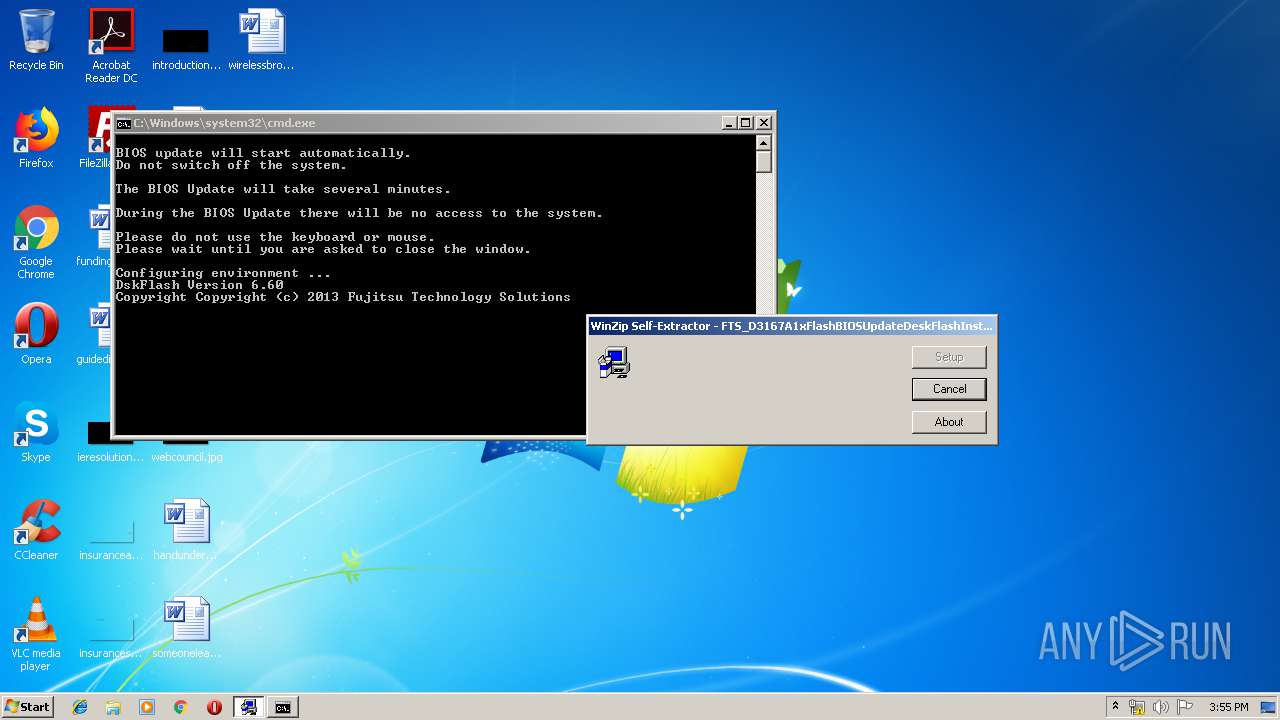
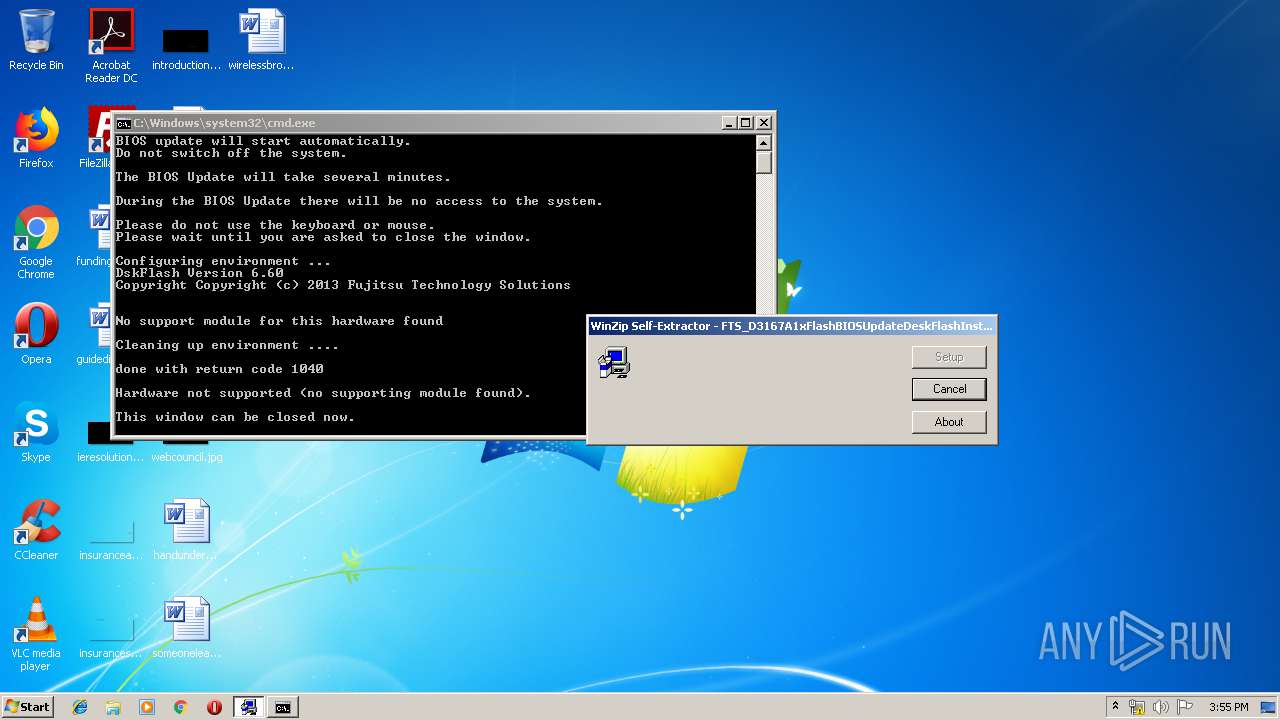
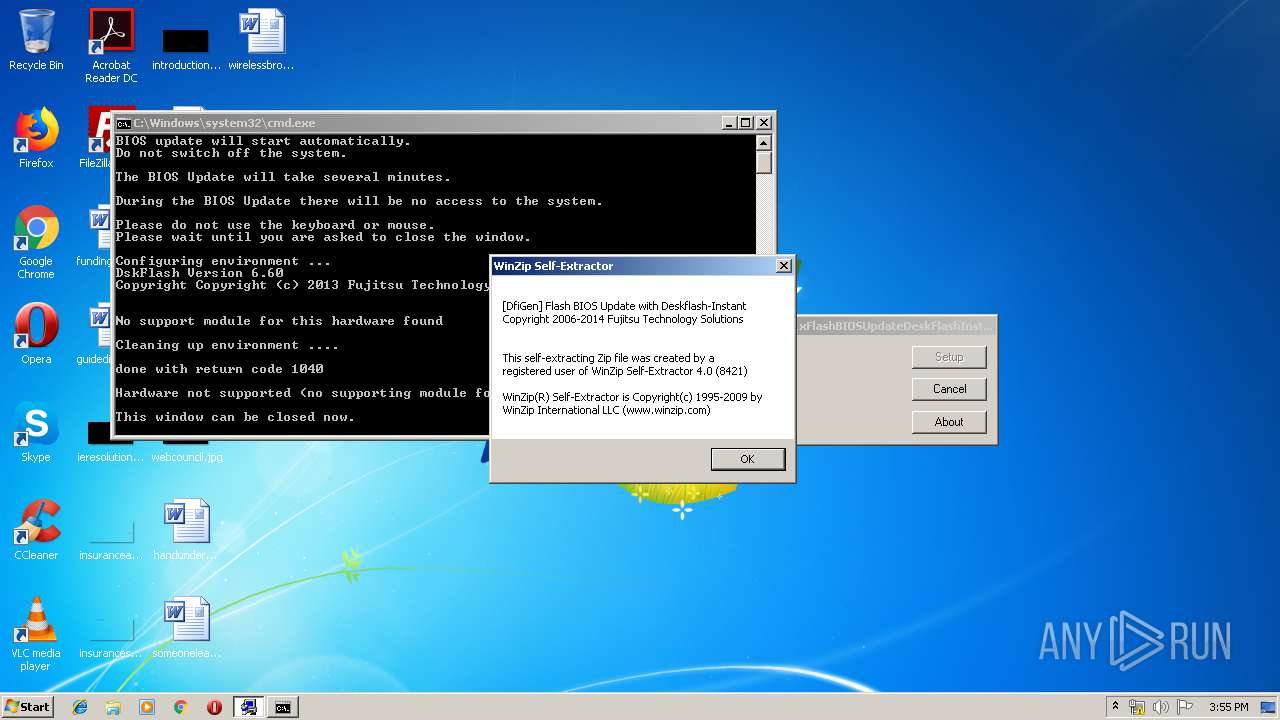
Starts CMD.EXE for commands execution
- FTS_D3167A1xFlashBIOSUpdateDeskFlashInstant_V4653R1230_1119437.EXE (PID: 3956)
Creates COM task schedule object
- regsvr32.exe (PID: 2912)
- regsvr32.exe (PID: 4076)
- regsvr32.exe (PID: 3668)
- regsvr32.exe (PID: 2156)
- regsvr32.exe (PID: 3044)
Starts application with an unusual extension
- DskFlash.exe (PID: 2260)
Executable content was dropped or overwritten
- FTS_D3167A1xFlashBIOSUpdateDeskFlashInstant_V4653R1230_1119437.EXE (PID: 3956)
- DF_UEFI.exe (PID: 3764)
- UpdPnpDr.exe (PID: 3004)
- DrvInst.exe (PID: 1412)
- DrvInst.exe (PID: 3460)
- Setup.exe (PID: 2836)
Adds / modifies Windows certificates
- CertMgr.exe (PID: 2188)
- UpdPnpDr.exe (PID: 3004)
Executed via COM
- DllHost.exe (PID: 3736)
- DrvInst.exe (PID: 2164)
- DrvInst.exe (PID: 3460)
- DrvInst.exe (PID: 1412)
- DrvInst.exe (PID: 3612)
- DllHost.exe (PID: 3368)
- HaBFlash.exe (PID: 3204)
Creates files in the driver directory
- DrvInst.exe (PID: 2164)
- DrvInst.exe (PID: 3460)
- DrvInst.exe (PID: 3612)
- DrvInst.exe (PID: 1412)
Removes files from Windows directory
- DrvInst.exe (PID: 2164)
- DrvInst.exe (PID: 3460)
- DrvInst.exe (PID: 3612)
- DrvInst.exe (PID: 1412)
- DrvInstall.exe (PID: 3012)
- DrvInstall.exe (PID: 3724)
Creates files in the Windows directory
- DrvInst.exe (PID: 2164)
- DrvInst.exe (PID: 3612)
- DrvInst.exe (PID: 1412)
- DrvInst.exe (PID: 3460)
Creates files in the program directory
- DF_UEFI.exe (PID: 3764)
Creates a software uninstall entry
- DF_UEFI.exe (PID: 3764)
Executed as Windows Service
- vssvc.exe (PID: 1664)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (30.7) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (22.2) |
| .exe | | | Win64 Executable (generic) (19.7) |
| .exe | | | Winzip Win32 self-extracting archive (generic) (16.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:02:24 16:50:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 77824 |
| InitializedDataSize: | 40960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaf1e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2009 15:50:34 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Feb-2009 15:50:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00012775 | 0x00013000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50181 |
.rdata | 0x00014000 | 0x00003822 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98659 |
.data | 0x00018000 | 0x0000E6E4 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.97548 |
.rsrc | 0x00027000 | 0x0000368C | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41968 |
_winzip_ | 0x0002B000 | 0x008CC000 | 0x008CC000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.99962 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.82954 | 989 | Latin 1 / Western European | English - United States | RT_MANIFEST |
63 | 3.18826 | 764 | Latin 1 / Western European | English - United States | RT_STRING |
64 | 3.37002 | 1496 | Latin 1 / Western European | English - United States | RT_STRING |
65 | 3.39511 | 2382 | Latin 1 / Western European | English - United States | RT_STRING |
66 | 3.44643 | 2322 | Latin 1 / Western European | English - United States | RT_STRING |
67 | 3.39393 | 1278 | Latin 1 / Western European | English - United States | RT_STRING |
100 | 3.08197 | 290 | Latin 1 / Western European | English - United States | RT_DIALOG |
126 | 3.58134 | 1304 | Latin 1 / Western European | English - United States | RT_STRING |
127 | 2.47759 | 110 | Latin 1 / Western European | English - United States | RT_STRING |
400 | 3.46881 | 402 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
98
Monitored processes
45
Malicious processes
12
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Users\admin\AppData\Local\Temp\_TinDel.exe" | C:\Users\admin\AppData\Local\Temp\_TinDel.exe | — | Setup.exe | |||||||||||
User: admin Company: Tarma Software Research Pty Ltd Integrity Level: HIGH Description: Final cleanup helper Exit code: 0 Version: 2011.06.24.0909A Modules
| |||||||||||||||
| 352 | "C:\Users\admin\AppData\Local\Temp\13ECEBAA\x86\regsvr32.exe" "C:\Program Files\Common Files\Fujitsu\Manageability\AcGabi.dll\1.14\AcGabi.dll" /u | C:\Users\admin\AppData\Local\Temp\13ECEBAA\x86\regsvr32.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Out-of-process DLL registration helper Exit code: 0 Version: 2011.06.24.0909A Modules
| |||||||||||||||
| 656 | "C:\Program Files\Fujitsu\DeskView\Instant\DeskFlash\DskFlash.exe" /UPD /OV /ARB /waithandlerend /quickhandlerend /instant | C:\Program Files\Fujitsu\DeskView\Instant\DeskFlash\DskFlash.exe | — | DskFlash.exe | |||||||||||
User: admin Company: Fujitsu Technology Solutions Integrity Level: HIGH Description: DeskView tool to update and archive BIOS and BIOS settings Exit code: 1040 Version: 6.17 Modules
| |||||||||||||||
| 1088 | "C:\Users\admin\AppData\Local\Temp\13ECEBAA\x86\regsvr32.exe" "C:\Program Files\Common Files\Fujitsu\Manageability\BlBFlash.dll\1.15\BlBFlash.dll" /u | C:\Users\admin\AppData\Local\Temp\13ECEBAA\x86\regsvr32.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Out-of-process DLL registration helper Exit code: 0 Version: 2011.06.24.0909A Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Common Files\Fujitsu\Manageability\HaBFlash.exe\1.15\HaBFlash.exe" /s /regserver | C:\Program Files\Common Files\Fujitsu\Manageability\HaBFlash.exe\1.15\HaBFlash.exe | — | DF_UEFI.exe | |||||||||||
User: admin Company: Fujitsu Technology Solutions Integrity Level: HIGH Description: HaBFlash.exe Exit code: 0 Version: 1.15 Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Fujitsu\DeskView\Instant\Install\SRP.exe" Enable | C:\Program Files\Fujitsu\DeskView\Instant\Install\SRP.exe | — | DF_UEFI.exe | |||||||||||
User: admin Company: Fujitsu Technology Solutions Integrity Level: HIGH Description: SystemRestorePoints functionality Exit code: 0 Version: 1.02 Modules
| |||||||||||||||
| 1412 | DrvInst.exe "2" "211" "ROOT\SYSTEM\0002" "C:\Windows\INF\oem5.inf" "fscgabi.inf:DeviceList.NTx86:DriverInstall:6.0.1.19:root\fscgabi" "69173570f" "000005B4" "00000544" "0000060C" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Fujitsu\DeskView\Instant\Install\CertMgr.exe" /add "C:\Program Files\Fujitsu\DeskView\Instant\Install\3_vs_c3_cs_2010_ca.cer" -s CA -r localMachine | C:\Program Files\Fujitsu\DeskView\Instant\Install\CertMgr.exe | — | DF_UEFI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.0.6001.18000 (longhorn_rtm.080118-1840) Modules
| |||||||||||||||
| 1664 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | "C:\Users\admin\AppData\Local\Temp\13ECEBAA\x86\regsvr32.exe" "C:\Program Files\Common Files\Fujitsu\Manageability\CIAsmbly.dll\1.09\CIAsmbly.dll" /r | C:\Users\admin\AppData\Local\Temp\13ECEBAA\x86\regsvr32.exe | — | DF_UEFI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Out-of-process DLL registration helper Exit code: 0 Version: 2011.06.24.0909A Modules
| |||||||||||||||
Total events
800
Read events
257
Write events
334
Delete events
209
Modification events
| (PID) Process: | (3764) DF_UEFI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B40E0000A6F7FD521D3BD501 | |||
| (PID) Process: | (3764) DF_UEFI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 6FB585177165265A815B2ACFC9C501799B50E8CF1BA3AE1C4FEAA9714D217F9E | |||
| (PID) Process: | (3764) DF_UEFI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3764) DF_UEFI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\Common Files\Fujitsu\Manageability\DVLang.dll\1.22\DVLANG.dll |
Value: 1 | |||
| (PID) Process: | (3764) DF_UEFI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\Common Files\Fujitsu\Manageability\HaBFlash.evt\1.10\HaBFlash.Evt |
Value: 1 | |||
| (PID) Process: | (3764) DF_UEFI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\Common Files\Fujitsu\Manageability\DVAnPMan.exe\1.21\DVAnPMan.exe |
Value: 1 | |||
| (PID) Process: | (3668) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{42E21DD3-55FA-435a-B400-C88C7E744182} |
| Operation: | write | Name: | |
Value: BlBFlash | |||
| (PID) Process: | (3668) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\BlBFlash.DLL |
| Operation: | write | Name: | AppID |
Value: {42E21DD3-55FA-435a-B400-C88C7E744182} | |||
| (PID) Process: | (3668) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\BlBFlash.BlBFlashObj.1.15 |
| Operation: | write | Name: | |
Value: CBlBFlashObj Object | |||
| (PID) Process: | (3668) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\BlBFlash.BlBFlashObj.1.15\CLSID |
| Operation: | write | Name: | |
Value: {0792294A-5FD0-4062-8B4C-FF3C8B98E5C5} | |||
Executable files
43
Suspicious files
25
Text files
158
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3764 | DF_UEFI.exe | C:\Users\admin\AppData\Local\Temp\13ECEBAA.dat | — | |
MD5:— | SHA256:— | |||
| 3956 | FTS_D3167A1xFlashBIOSUpdateDeskFlashInstant_V4653R1230_1119437.EXE | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\D3167-A1x.R1.23.0.DFI.bup | compressed | |
MD5:— | SHA256:— | |||
| 3764 | DF_UEFI.exe | C:\Program Files\Fujitsu\DeskView\Instant\Driver\amd64\fscgabi.cat._tm | — | |
MD5:— | SHA256:— | |||
| 3956 | FTS_D3167A1xFlashBIOSUpdateDeskFlashInstant_V4653R1230_1119437.EXE | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\DeskView.ini | text | |
MD5:3BF9C518F0C04C8A9BD6DF88246544BE | SHA256:1A57229245CB3F7B8B62D0403A59125F47E2F3D1B5A2DE425FCBF041CC5BDF6C | |||
| 3764 | DF_UEFI.exe | C:\Program Files\Fujitsu\DeskView\Instant\Driver\amd64\fscefdmi.cat._tm | — | |
MD5:— | SHA256:— | |||
| 3764 | DF_UEFI.exe | C:\Users\admin\AppData\Local\Temp\13ECEBAA\_Setup.dll | executable | |
MD5:2BA6B8691E8BA016D2705DDB590DE657 | SHA256:FC342456F11123F7061B8D2F508193842D4F6A966A277CA9EB701C676662ACAB | |||
| 3764 | DF_UEFI.exe | C:\Program Files\Fujitsu\DeskView\Instant\Driver\i386\fscgabi.cat._tm | — | |
MD5:— | SHA256:— | |||
| 3956 | FTS_D3167A1xFlashBIOSUpdateDeskFlashInstant_V4653R1230_1119437.EXE | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\DskFlash.exe | executable | |
MD5:BA4C3F666CB70D262A46ED005D25ADDC | SHA256:E873C1D604255D493C09639E910D455C5C8C954FA49A05926B75046D1014AC4B | |||
| 3764 | DF_UEFI.exe | C:\Program Files\Fujitsu\DeskView\Instant\Driver\i386\fscefdmi.cat._tm | — | |
MD5:— | SHA256:— | |||
| 3956 | FTS_D3167A1xFlashBIOSUpdateDeskFlashInstant_V4653R1230_1119437.EXE | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\DATA\DF_UEFI.exe | executable | |
MD5:A3ECF2CF74B296B1CA9E4416314344AF | SHA256:453D11FD754F6CAC05EB7E5E4EFAAA8DF860A42757B67389FBC1F285AF56ACD7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report