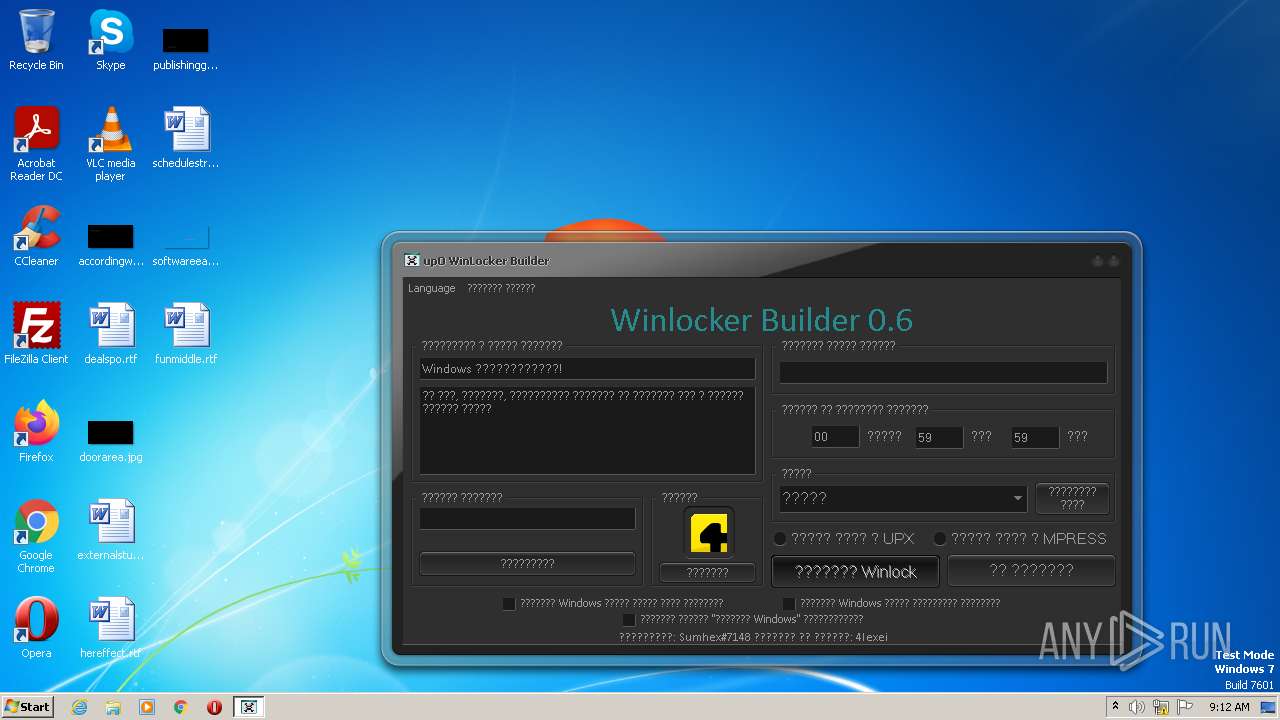
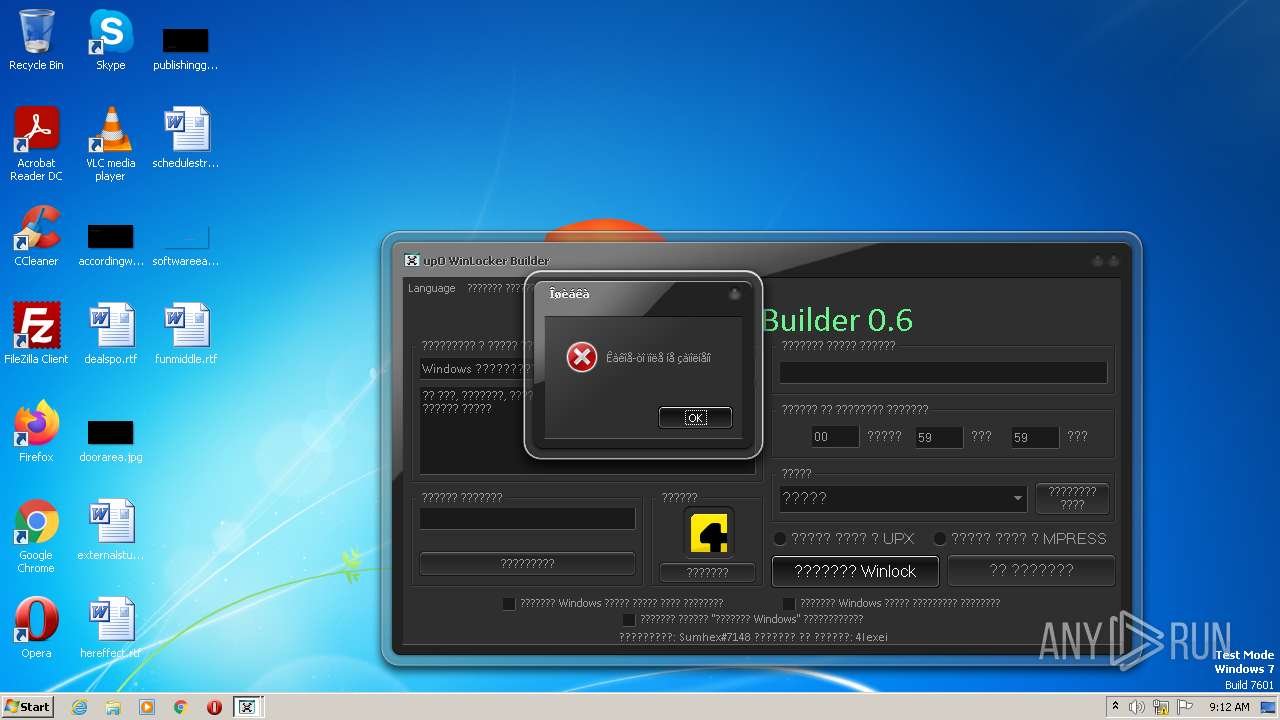
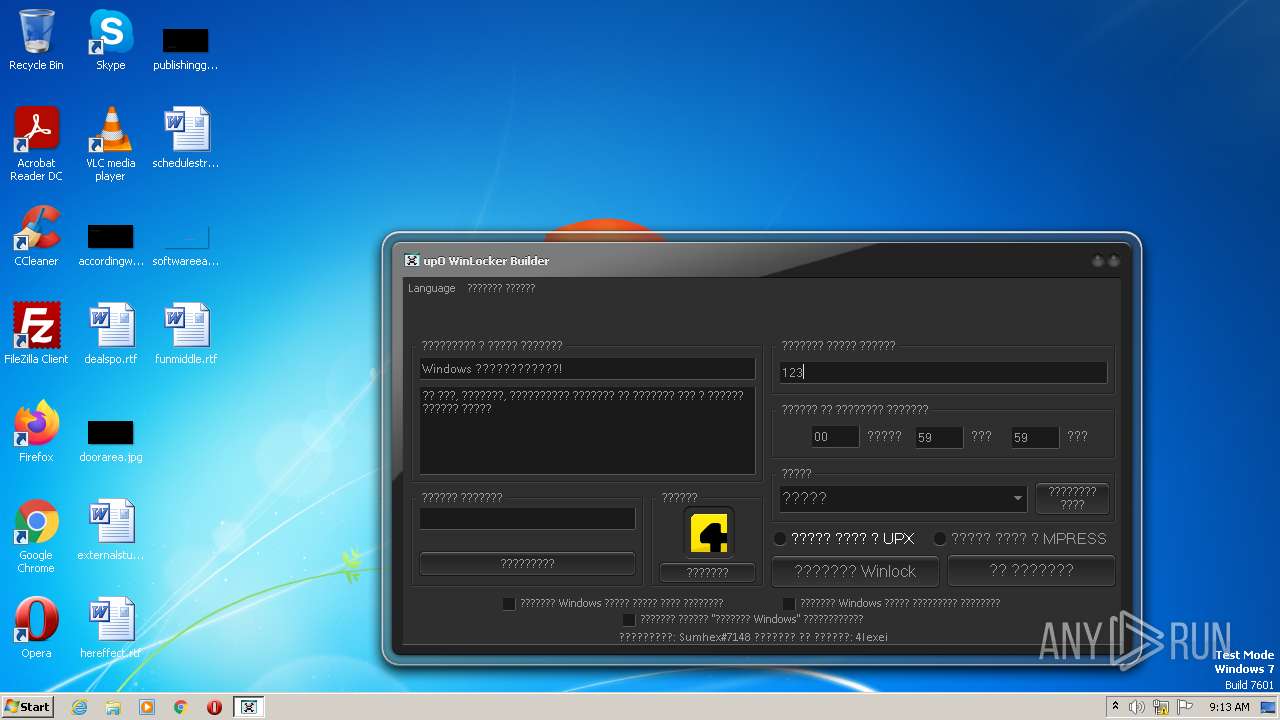
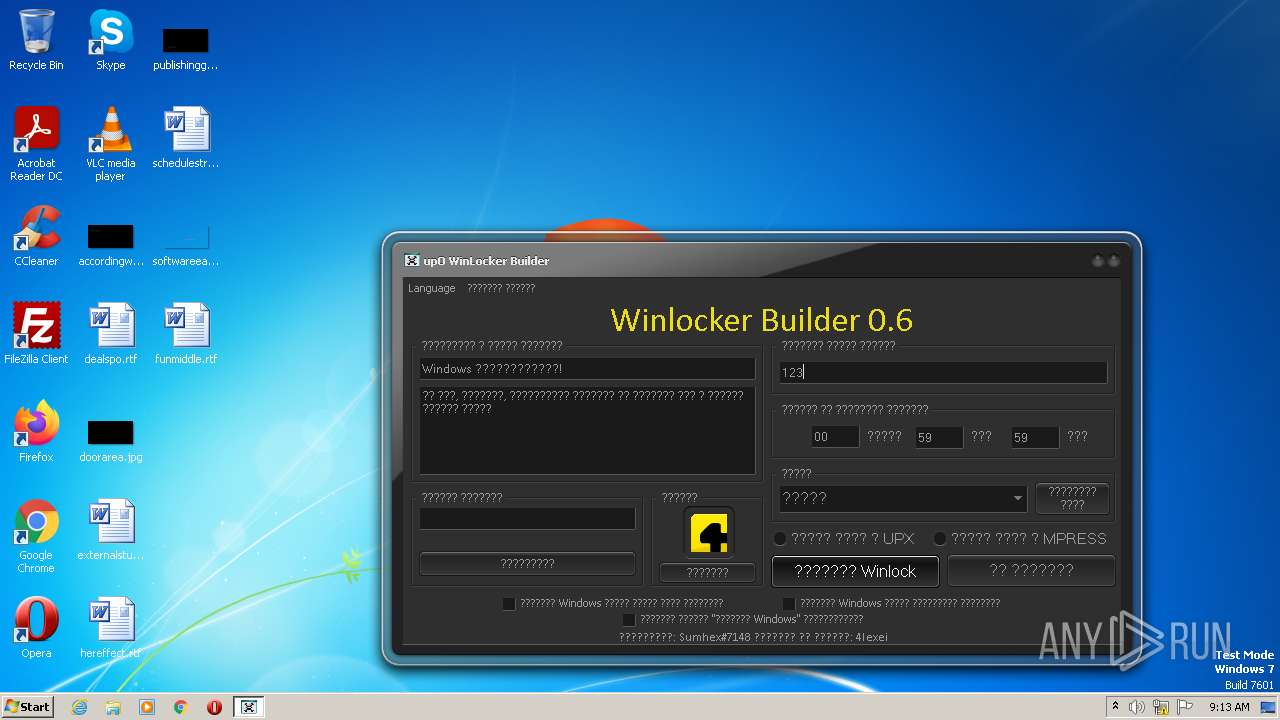
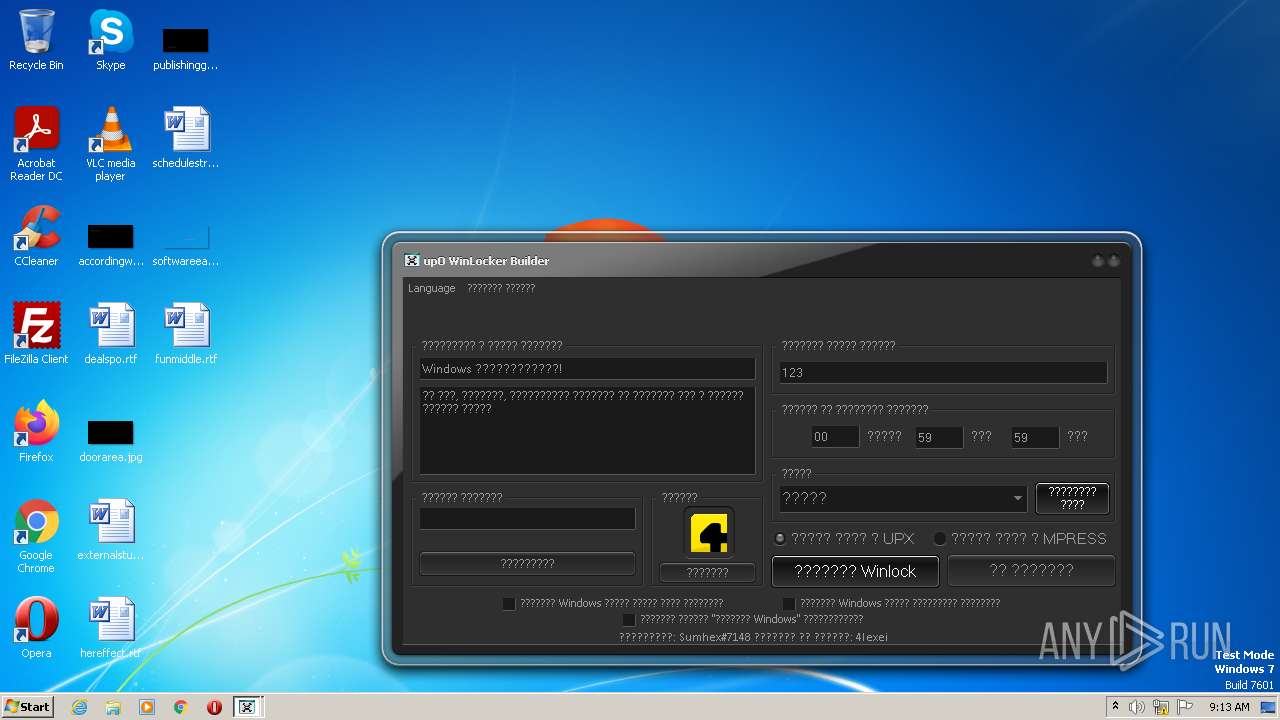
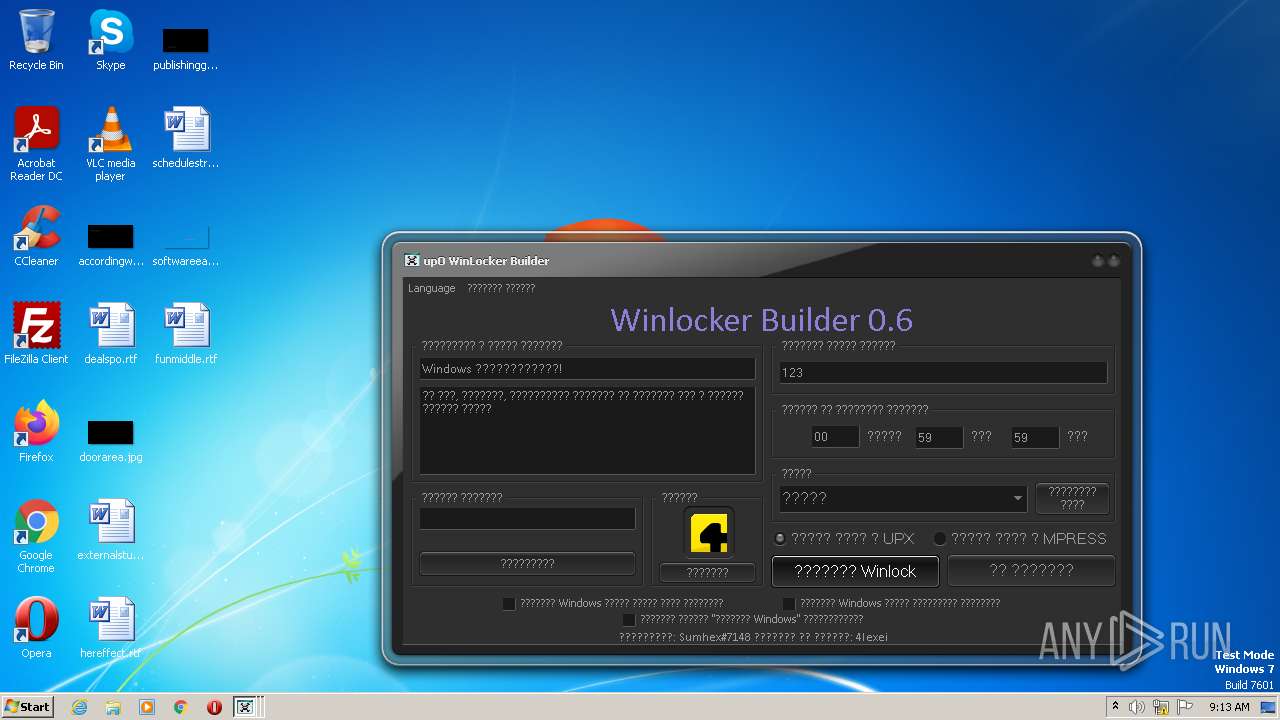
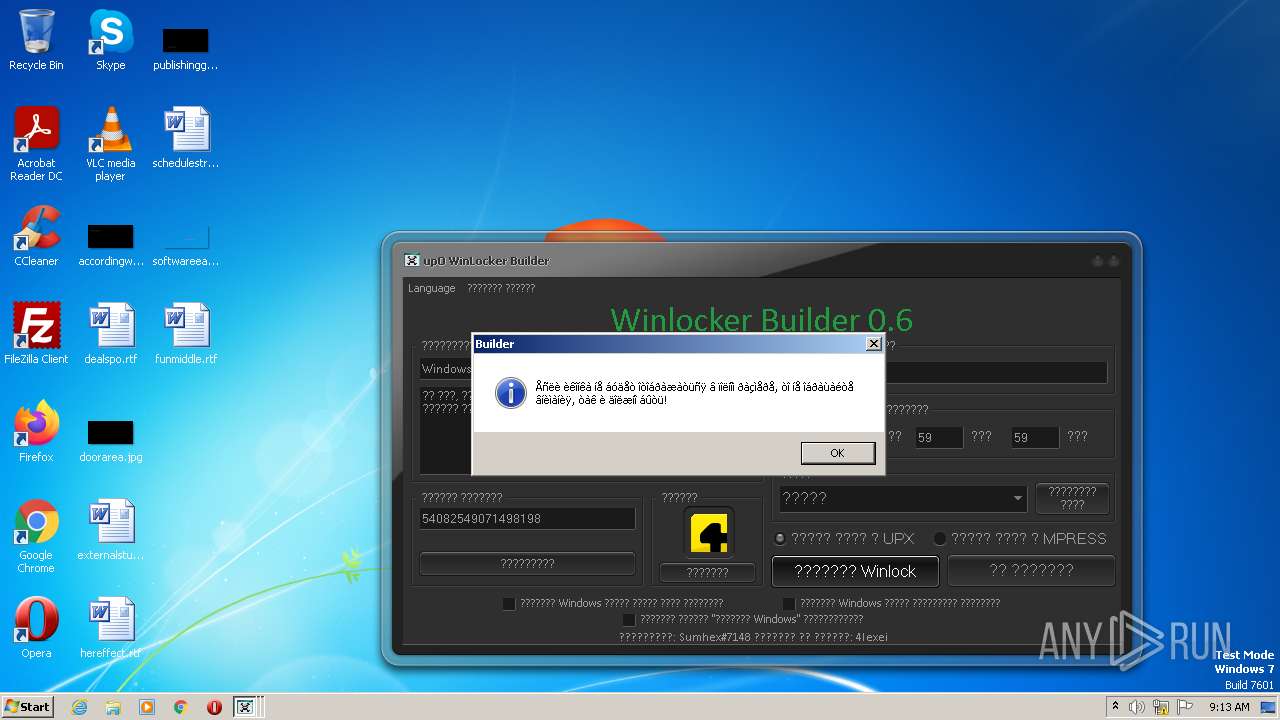
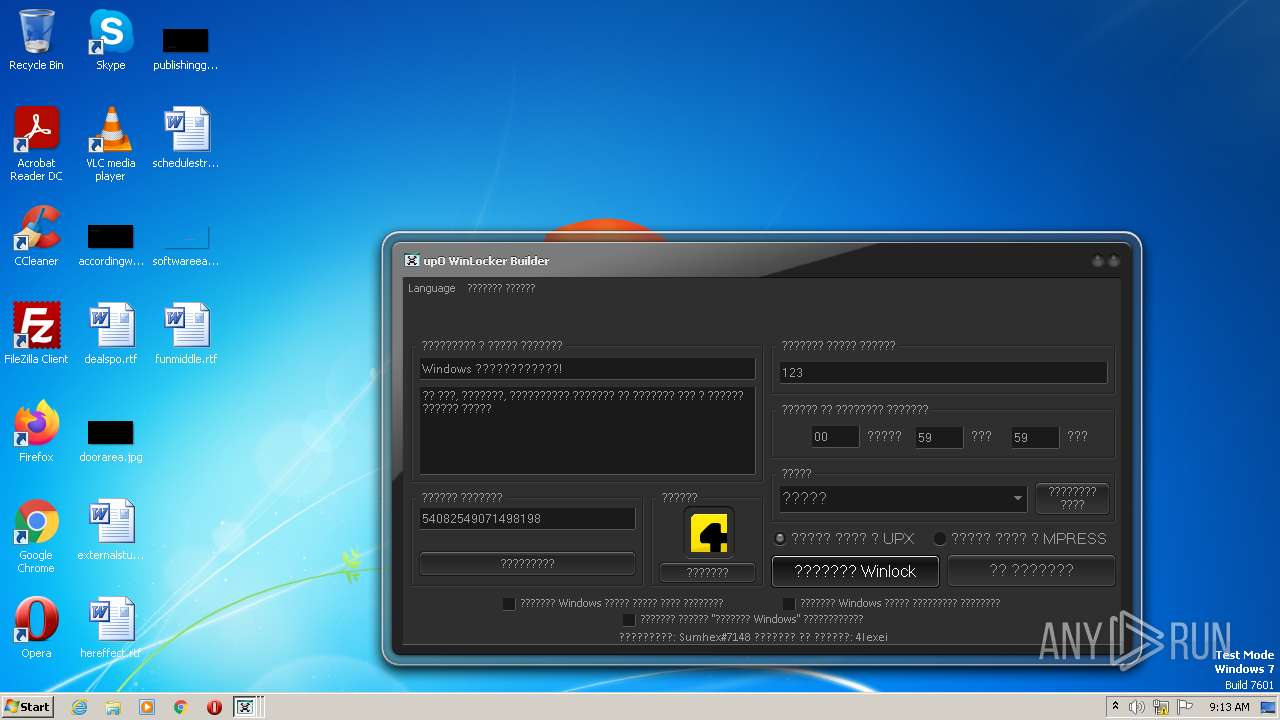
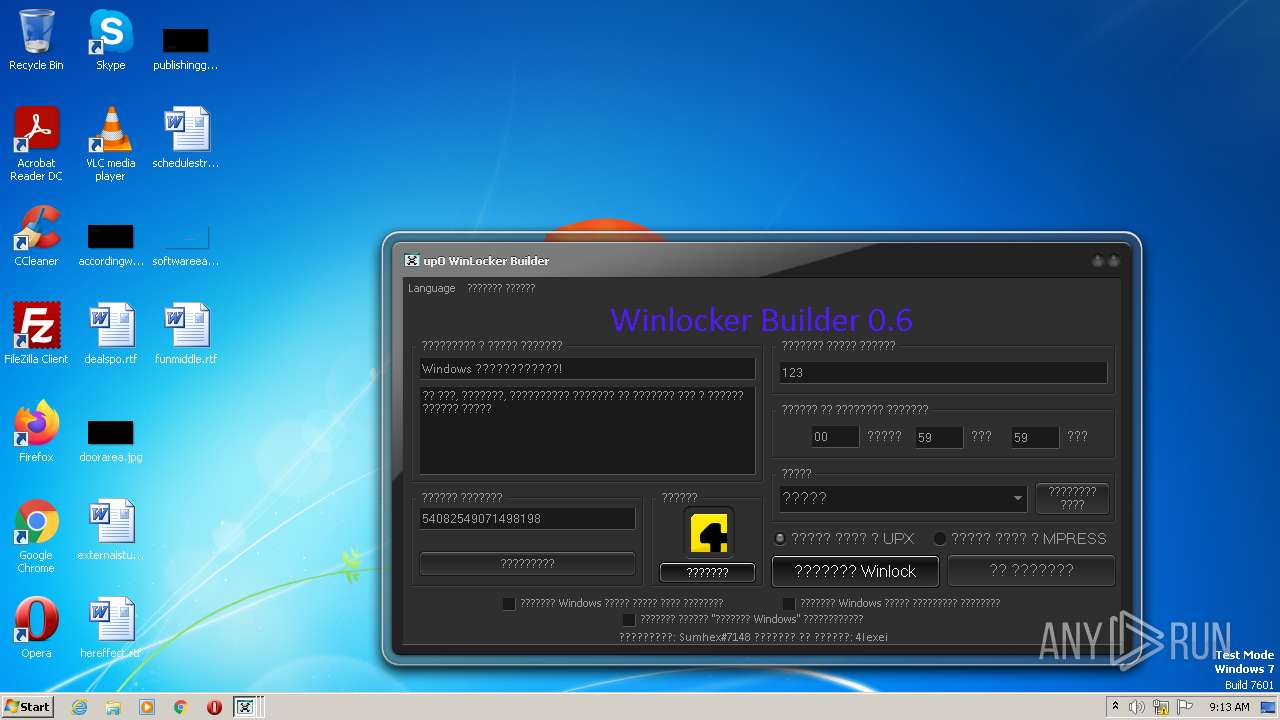
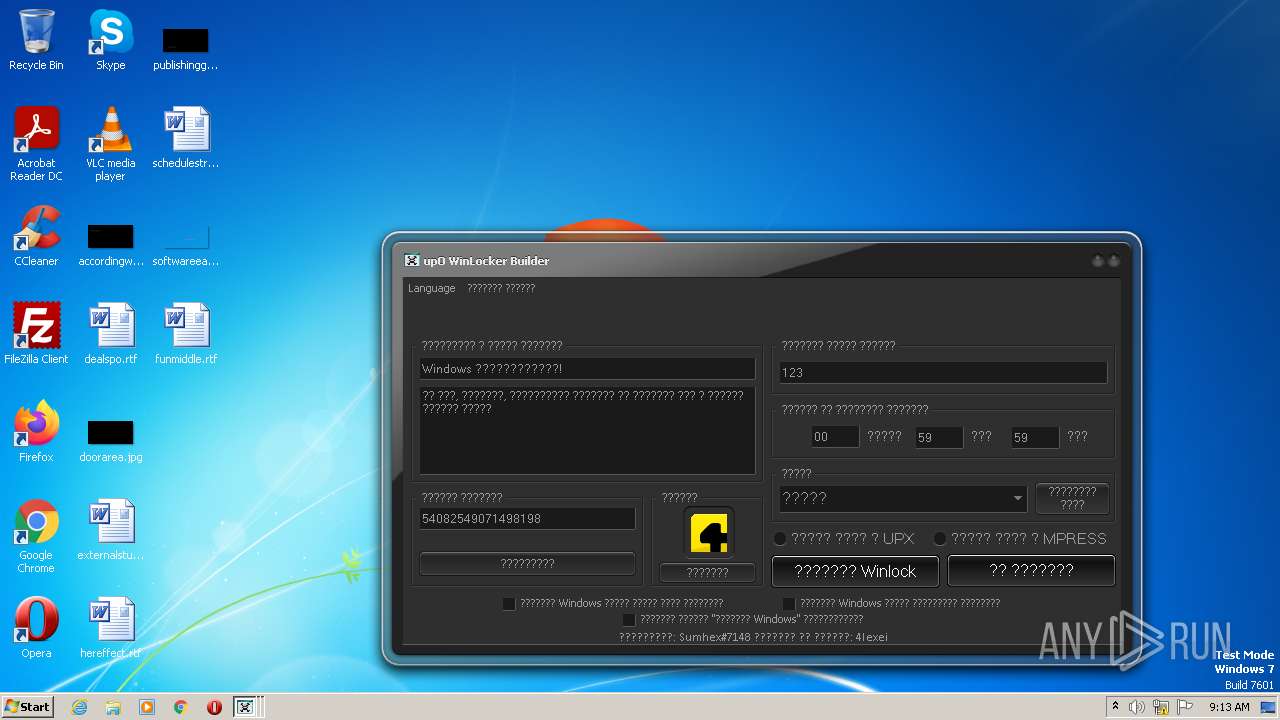
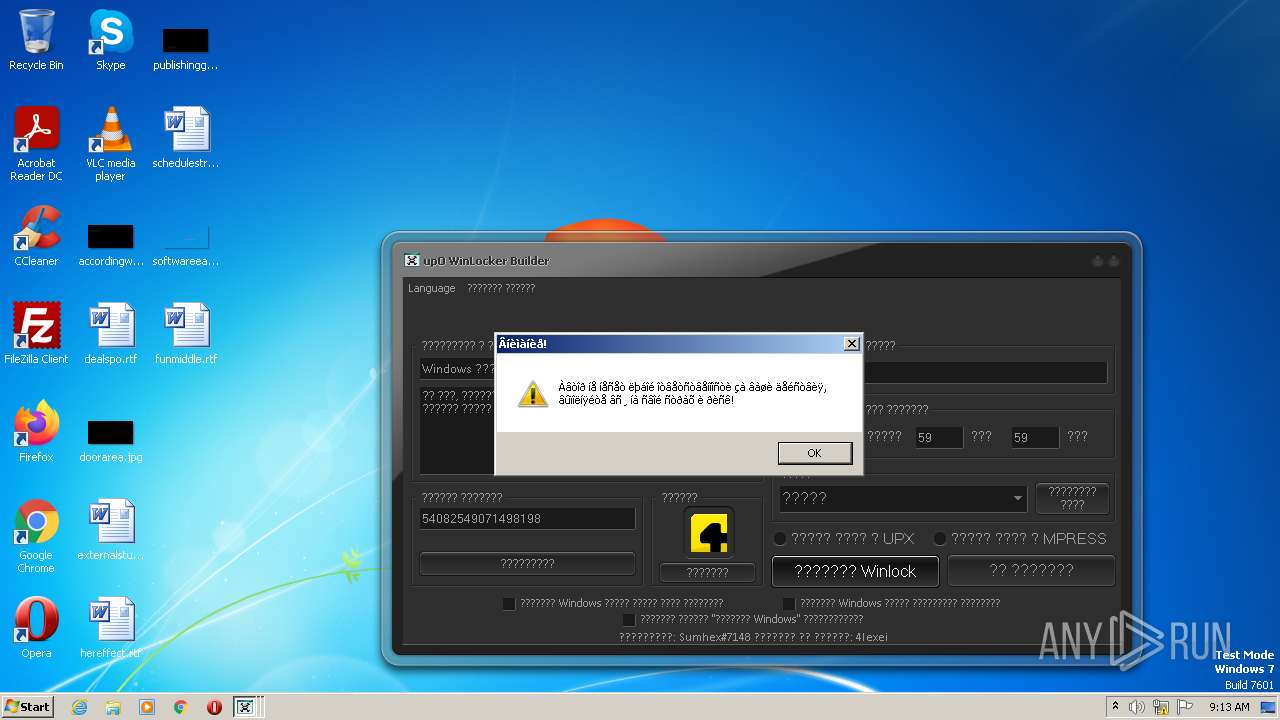
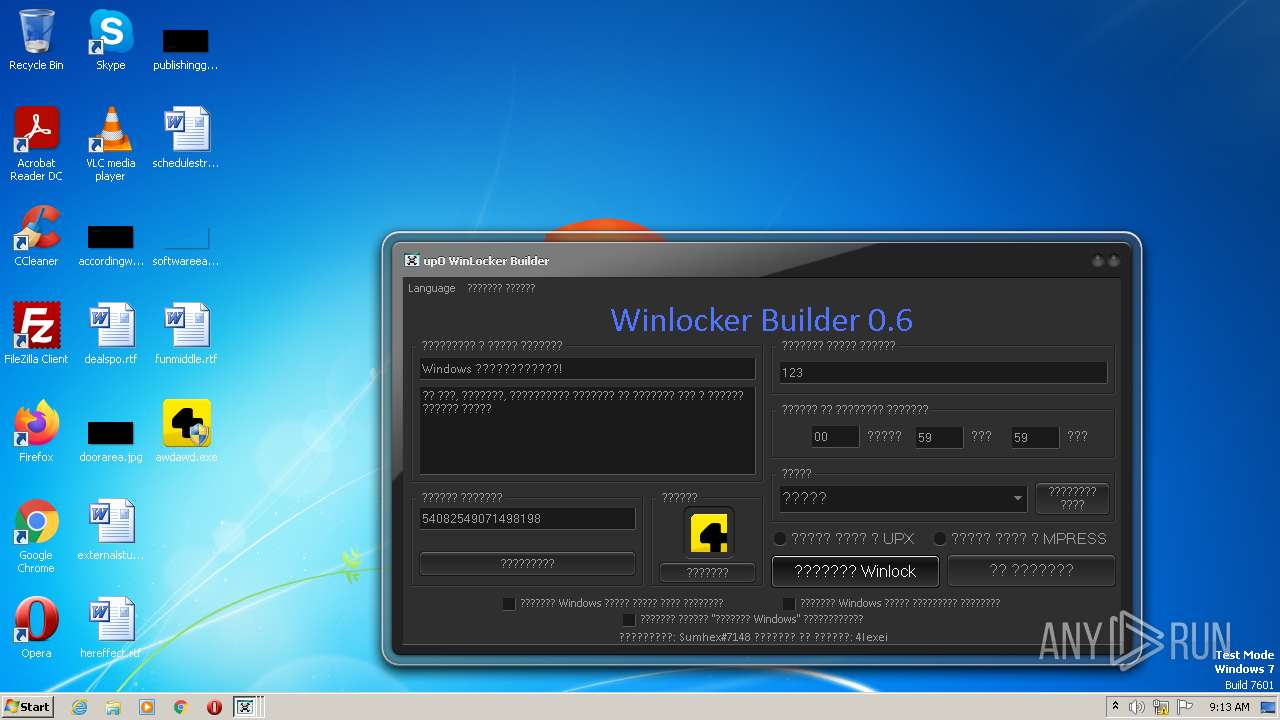
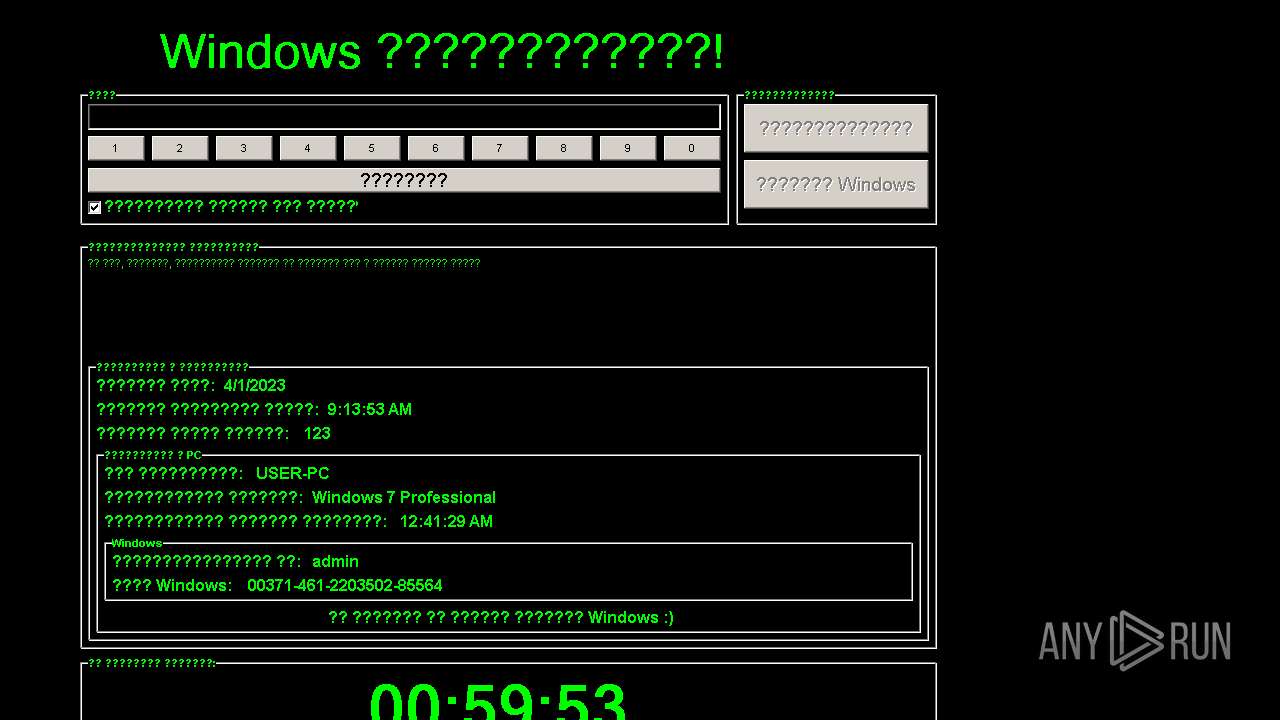
| File name: | upO Builder 0.6.exe |
| Full analysis: | https://app.any.run/tasks/be68b0dd-b4c4-462a-9aef-19deb162c4a8 |
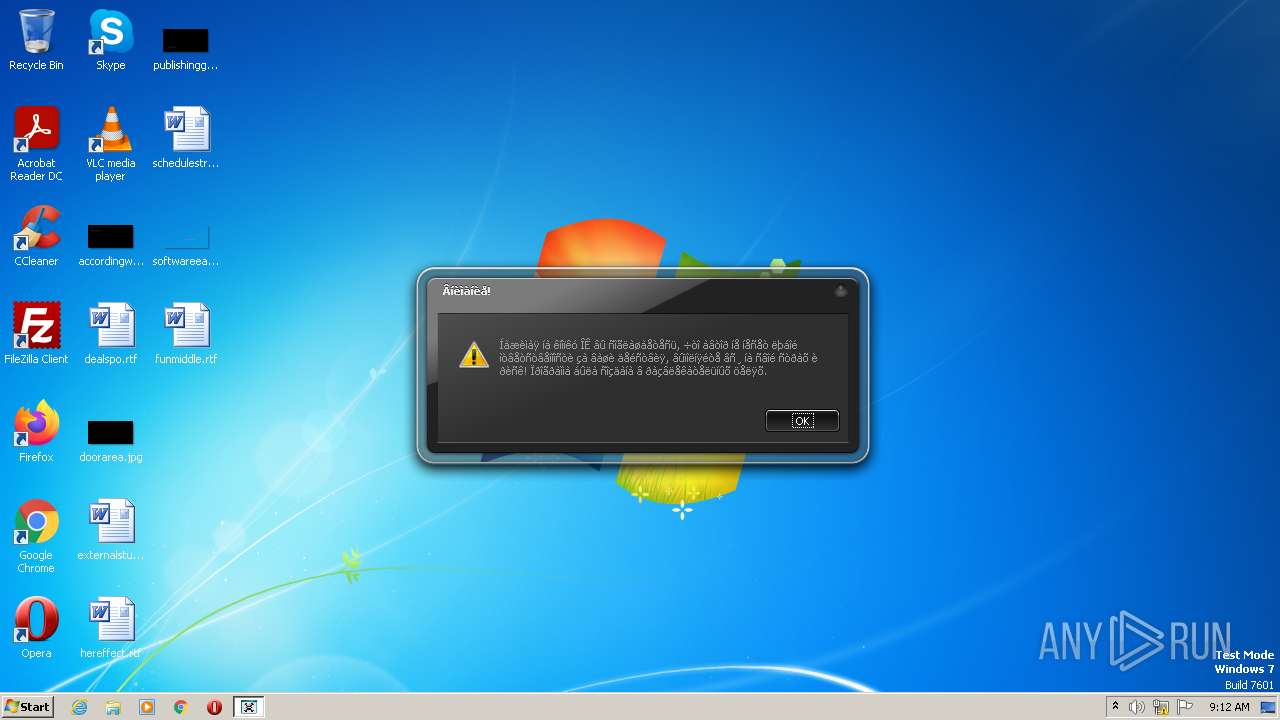
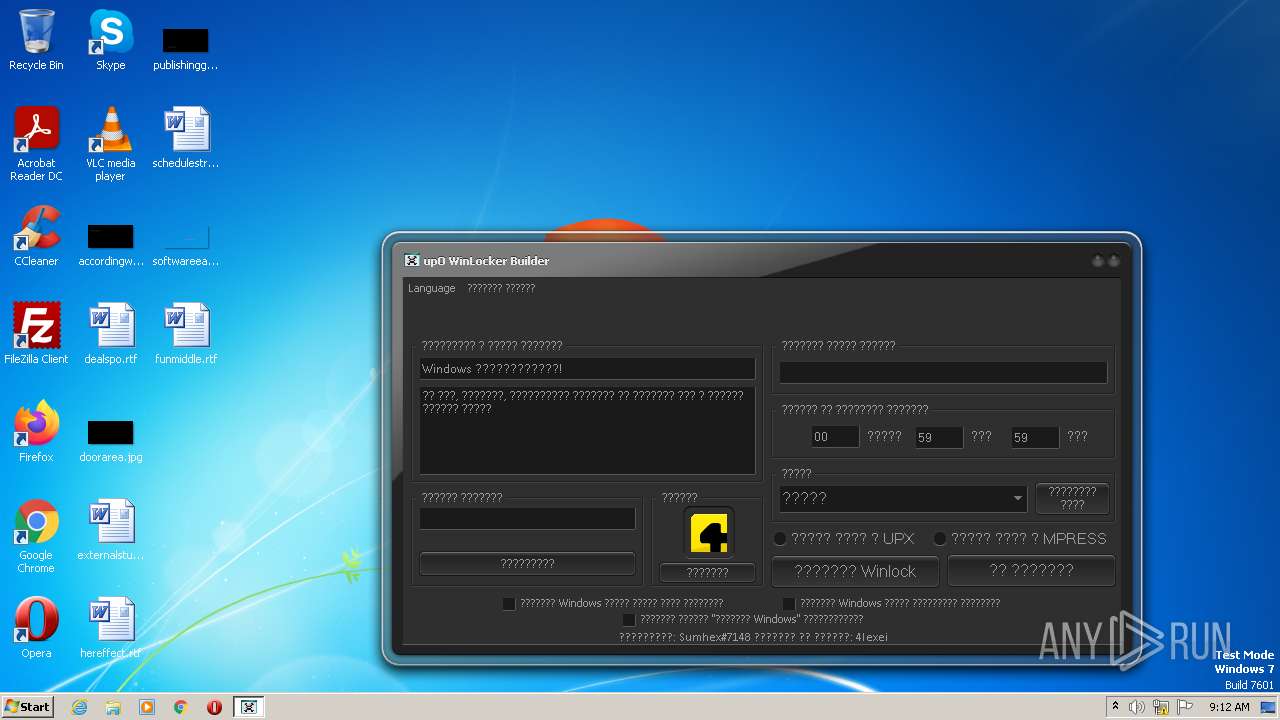
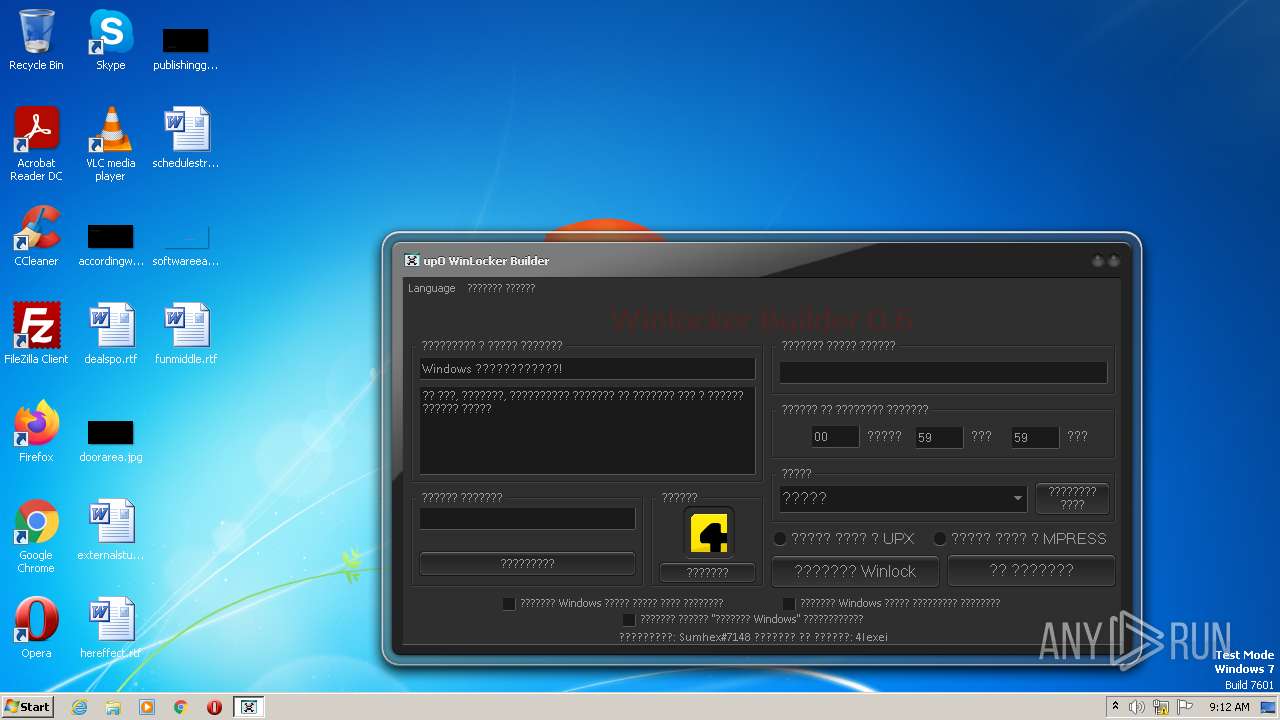
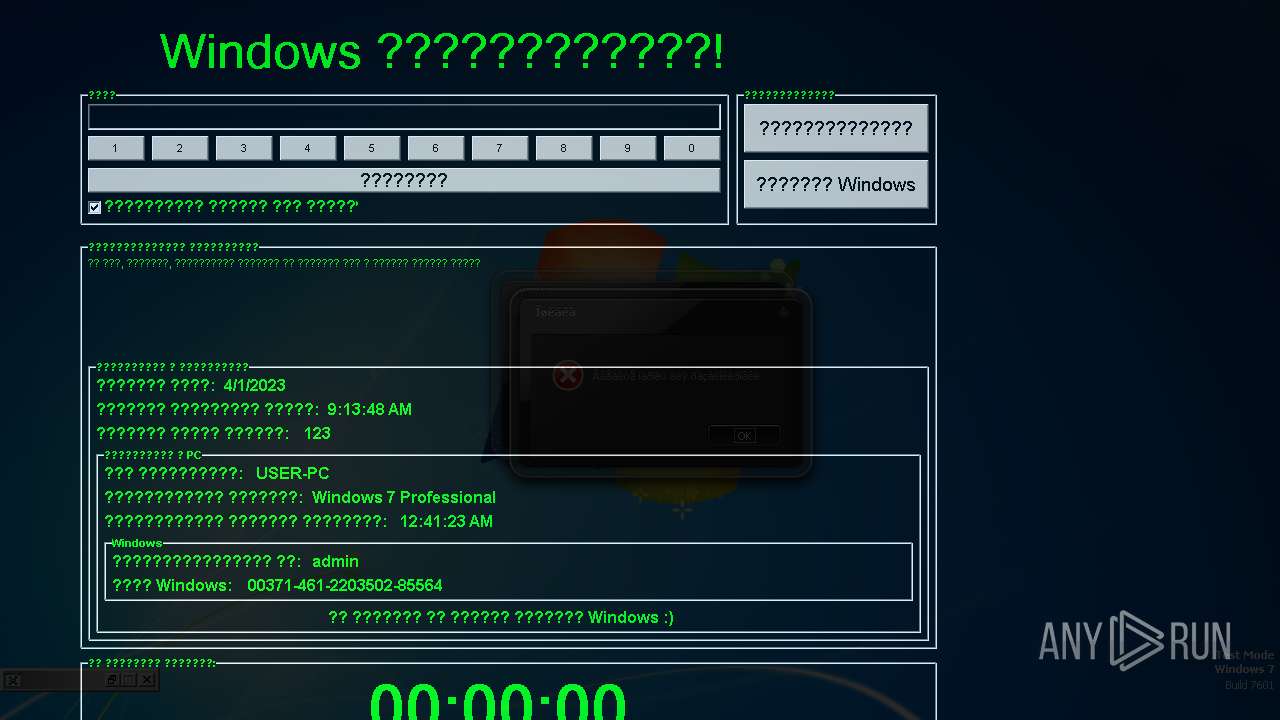
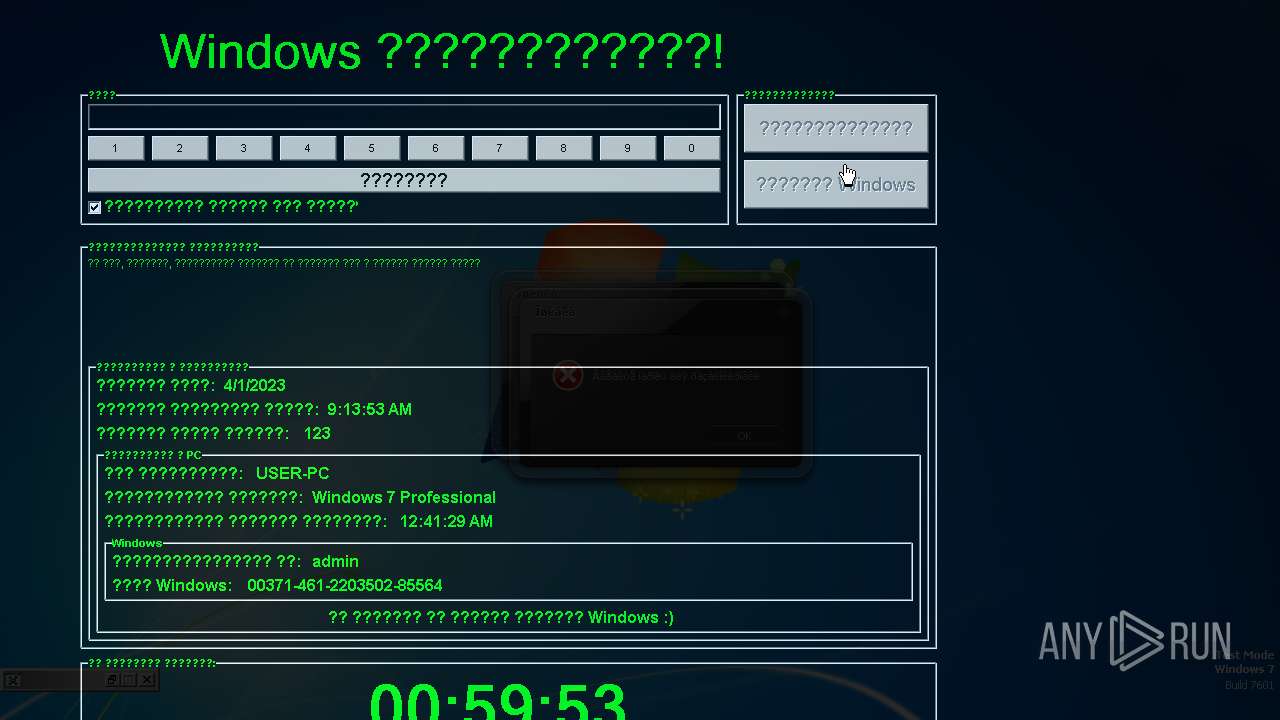
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 08:12:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C49B61A08CA00CB23B1D5834F37AD39F |
| SHA1: | 6E98030D173DC87EFCF43DCA5E3048A9873F3268 |
| SHA256: | 82DF76DB2CEDCBA2C187840297262BAE30D48A8A532D8195563B335A8D6C1E1C |
| SSDEEP: | 49152:mnZf+CxtKCvlLmcVsTTnzJ8kE77818iaVYooTszlhKd:mnsCxtDtr9/77q8DrVLS |
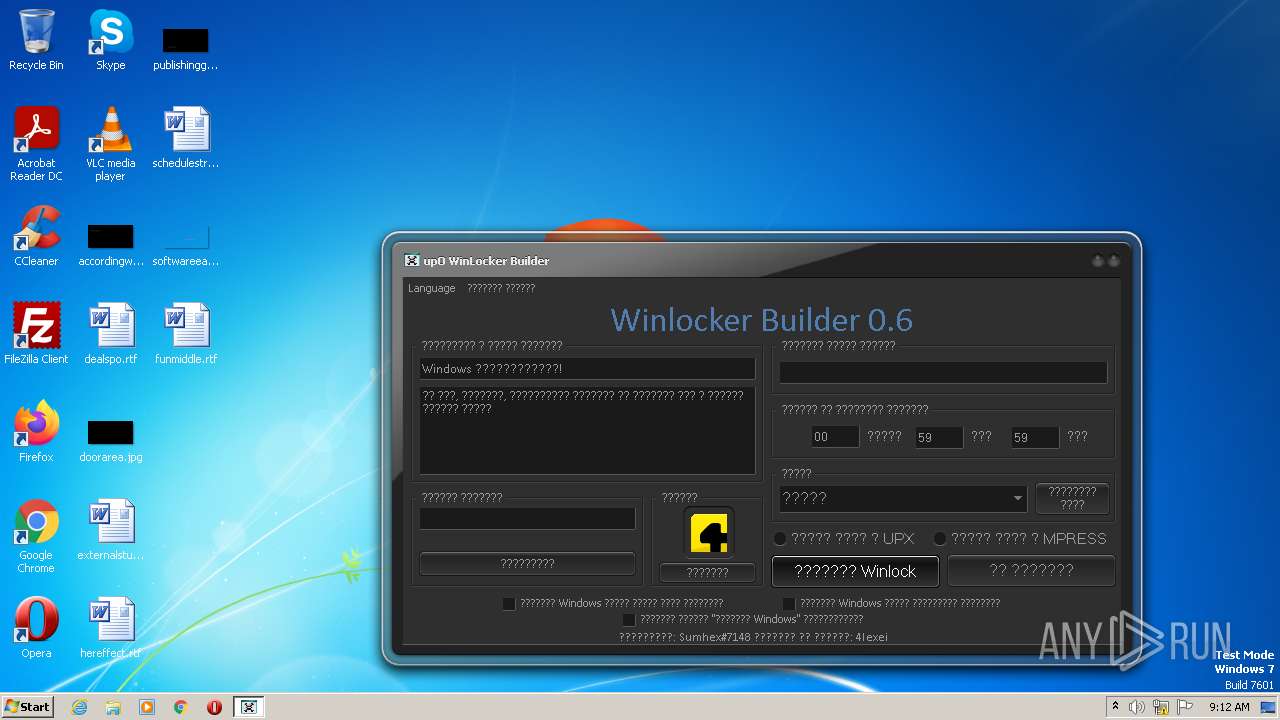
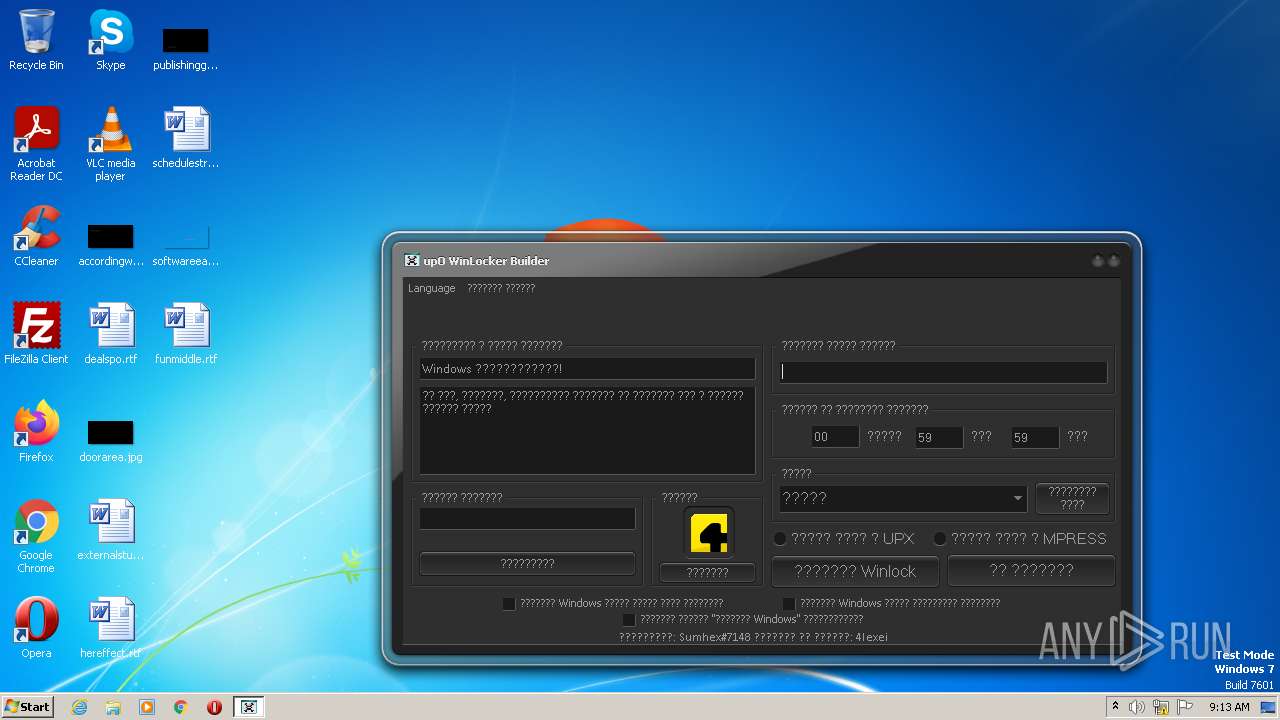
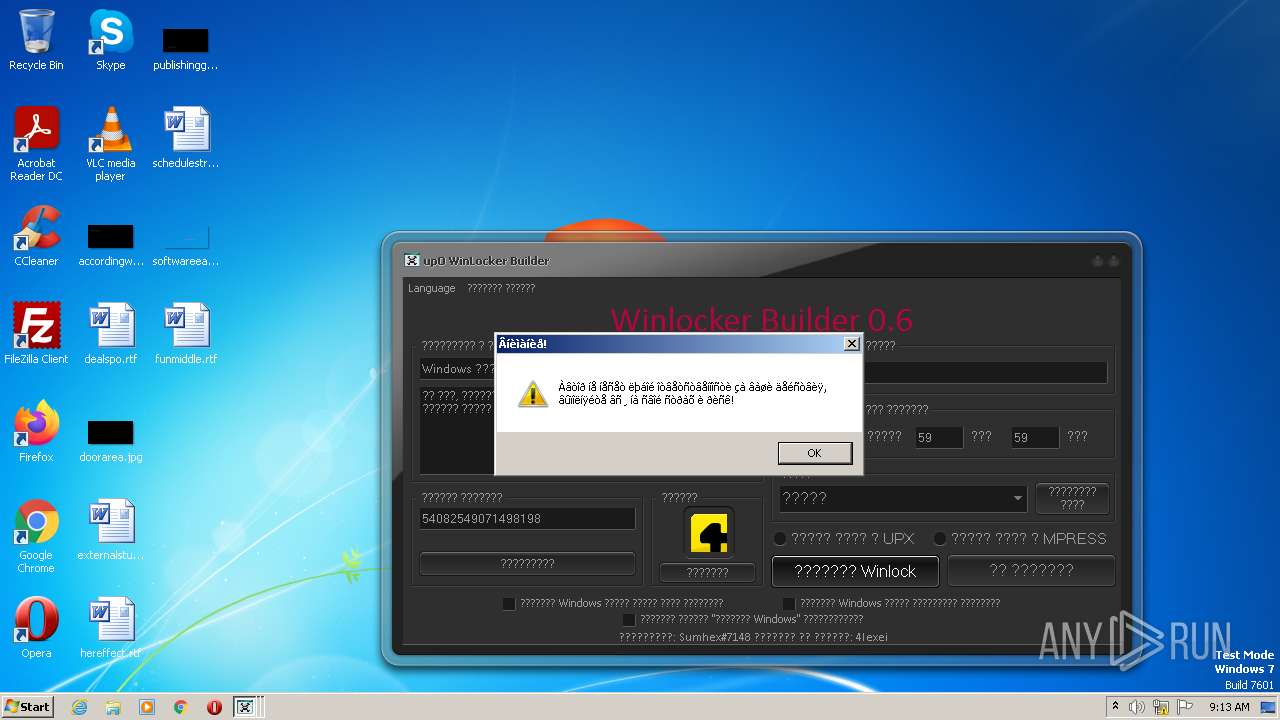
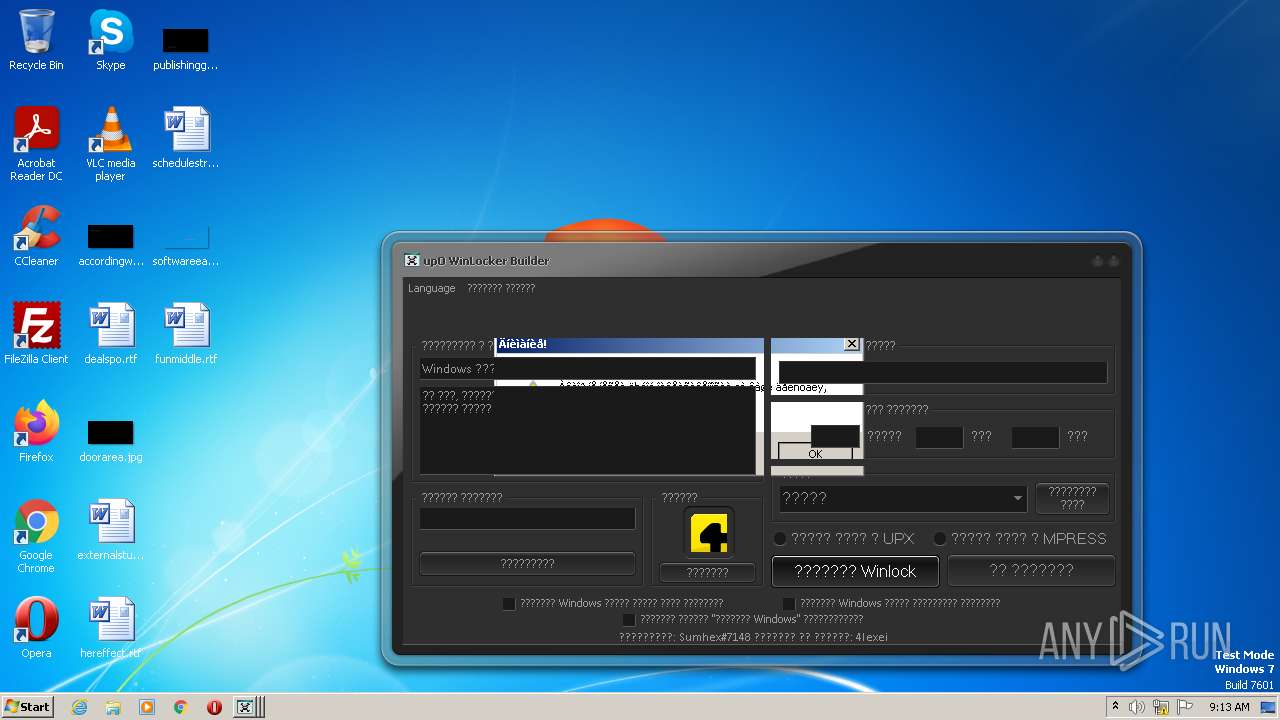
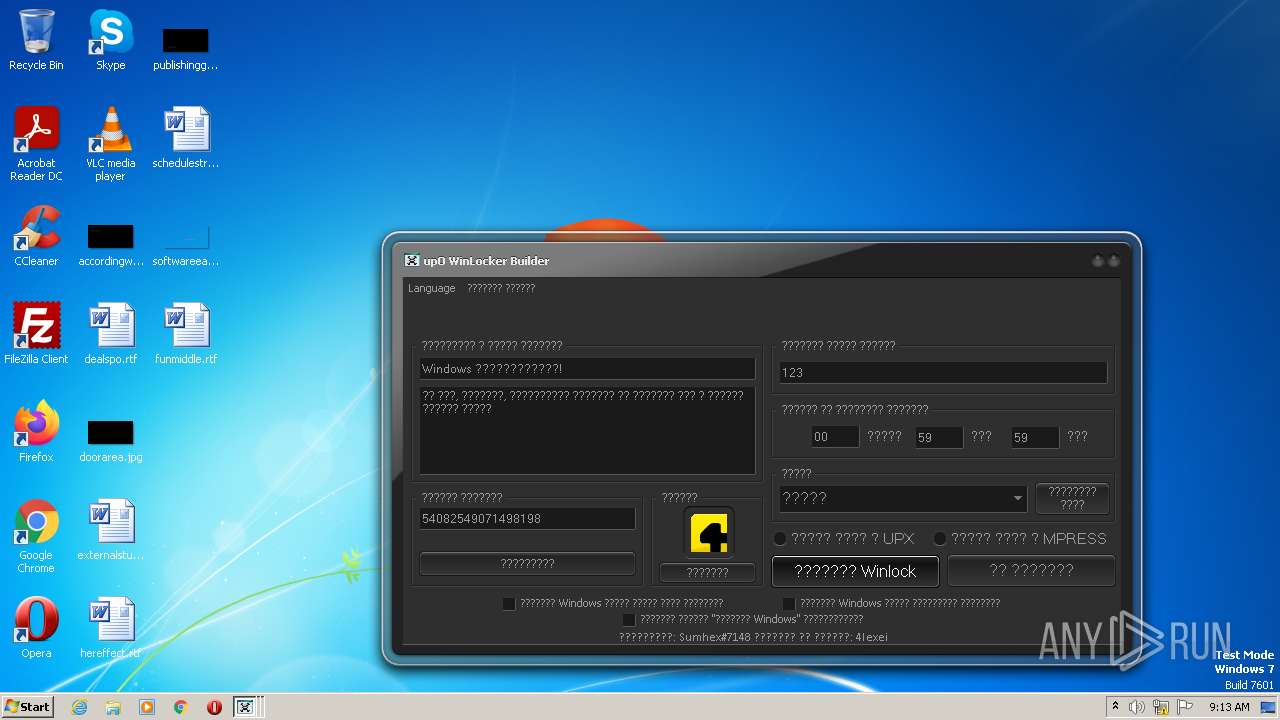
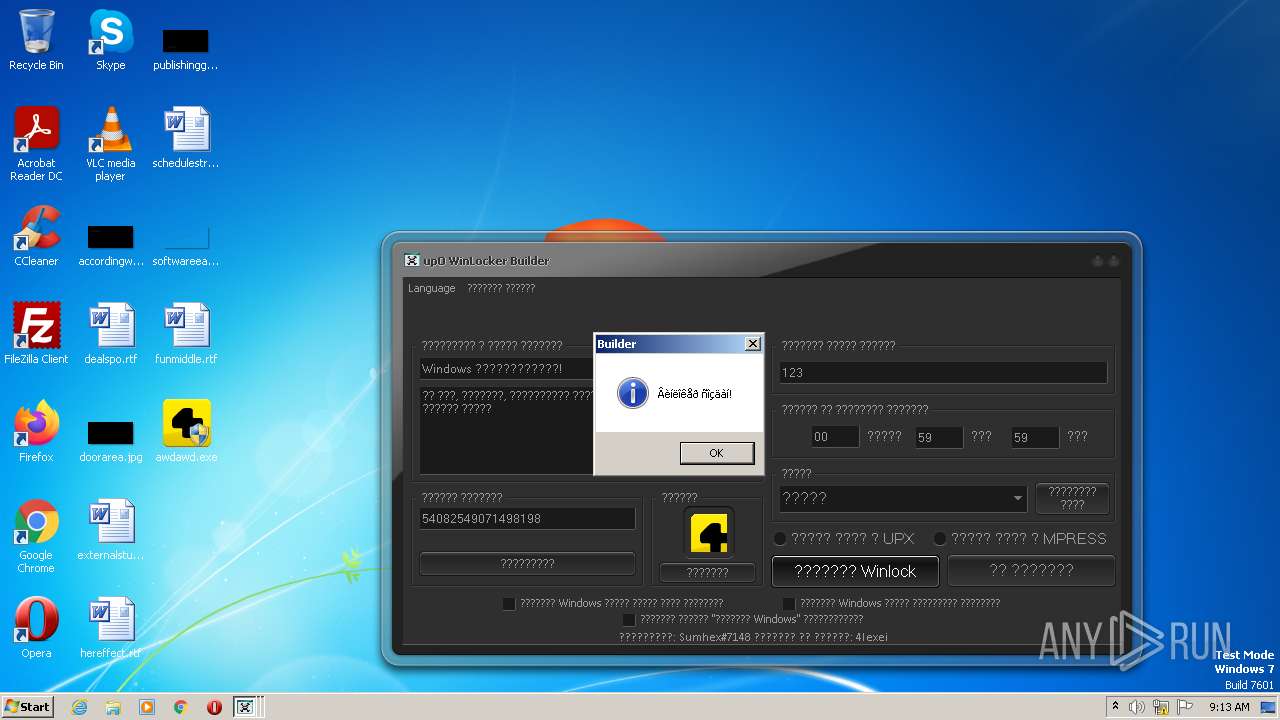
MALICIOUS
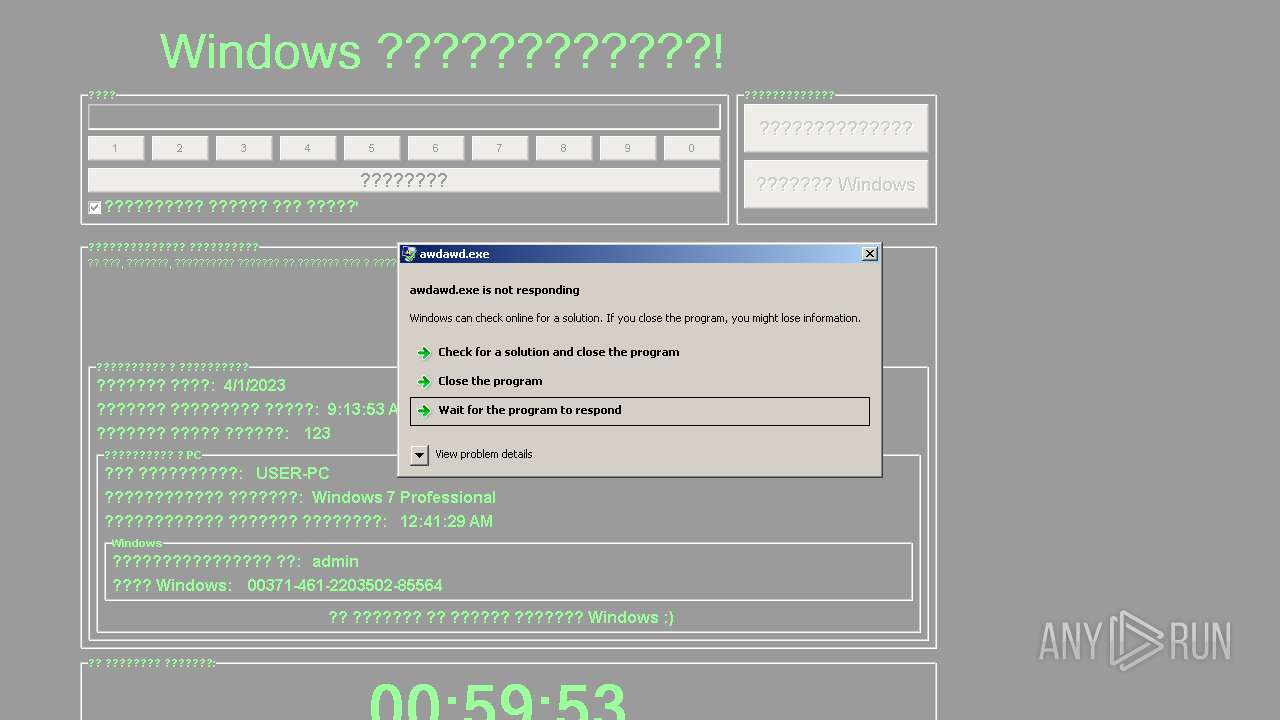
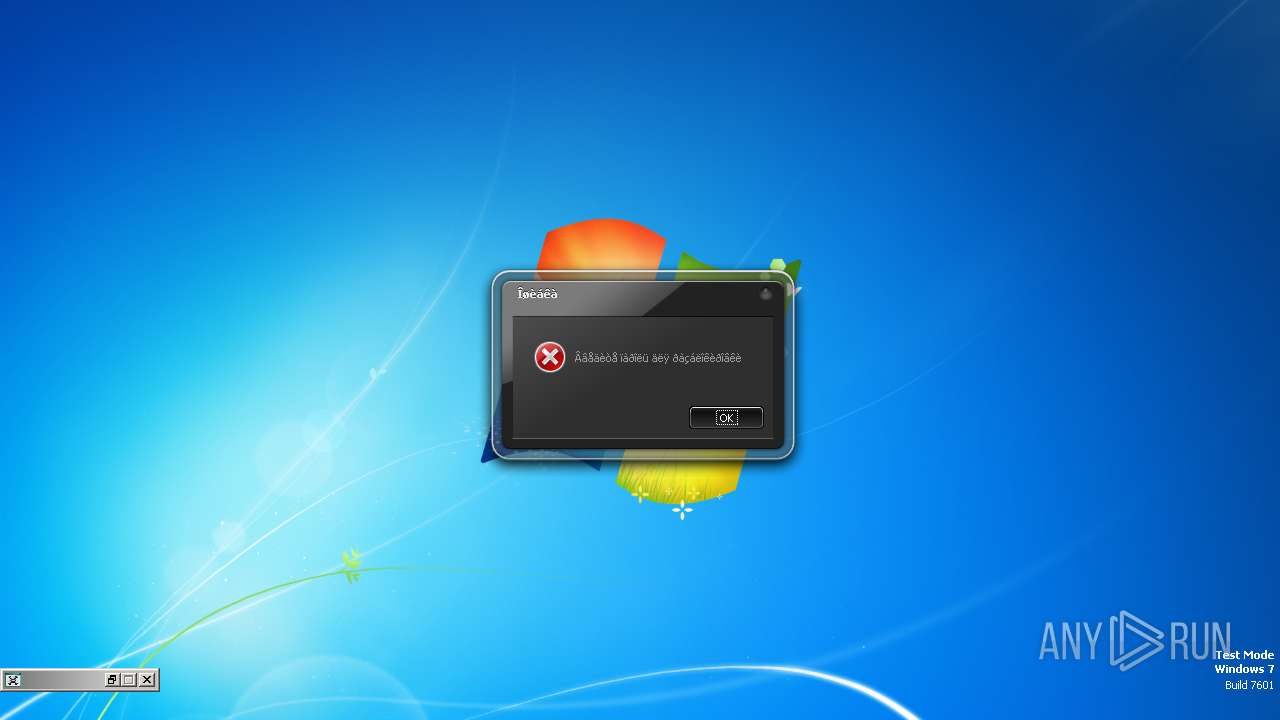
Application was dropped or rewritten from another process
- awdawd.exe (PID: 3732)
- awdawd.exe (PID: 1624)
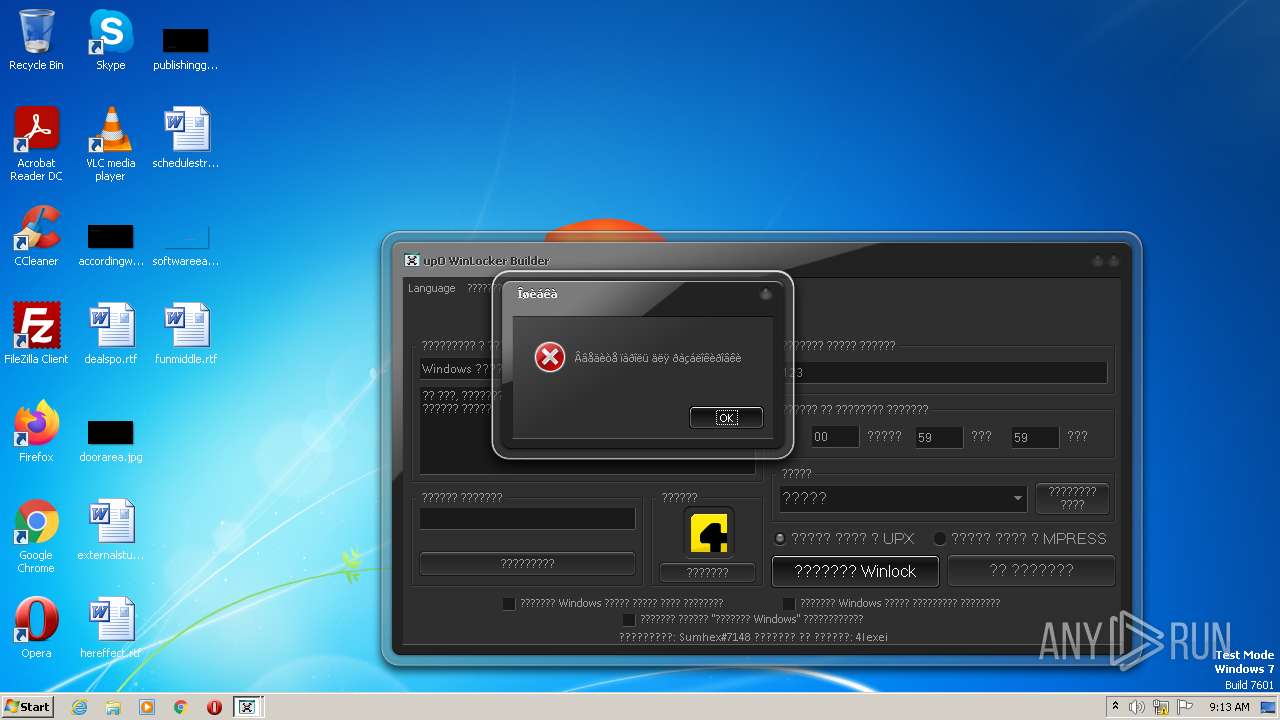
UAC/LUA settings modification
- awdawd.exe (PID: 1624)
Disables Windows Defender
- awdawd.exe (PID: 1624)
SUSPICIOUS
Reads the Internet Settings
- upO Builder 0.6.exe (PID: 3132)
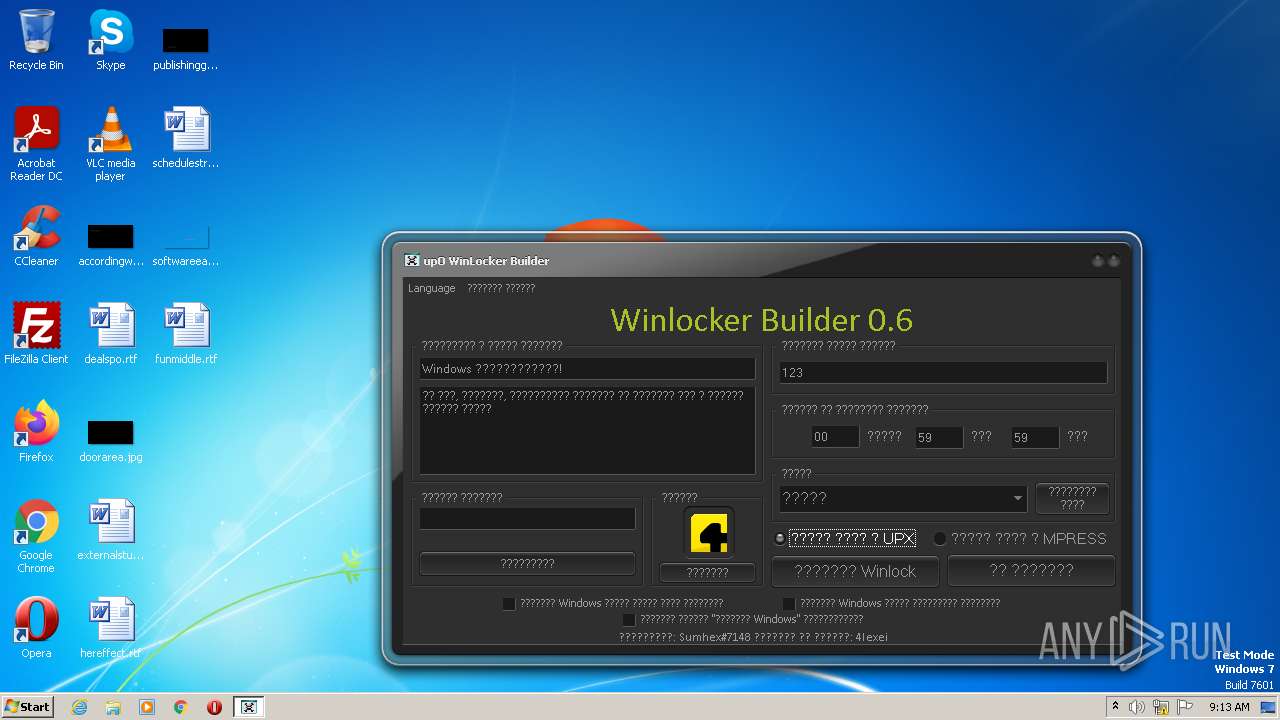
Executable content was dropped or overwritten
- upO Builder 0.6.exe (PID: 3132)
Reads the Windows owner or organization settings
- awdawd.exe (PID: 1624)
INFO
Checks supported languages
- upO Builder 0.6.exe (PID: 3132)
- awdawd.exe (PID: 1624)
Reads the computer name
- upO Builder 0.6.exe (PID: 3132)
- awdawd.exe (PID: 1624)
The process checks LSA protection
- upO Builder 0.6.exe (PID: 3132)
Reads the machine GUID from the registry
- upO Builder 0.6.exe (PID: 3132)
Manual execution by a user
- awdawd.exe (PID: 3732)
- awdawd.exe (PID: 1624)
Reads Windows Product ID
- awdawd.exe (PID: 1624)
Reads product name
- awdawd.exe (PID: 1624)
Reads Environment values
- awdawd.exe (PID: 1624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (44.7) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (30.3) |
| .exe | | | Win32 Executable Borland Delphi 6 (17.6) |
| .exe | | | InstallShield setup (2.8) |
| .exe | | | UPX compressed Win32 Executable (1.8) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x126b04 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2371584 |
| CodeSize: | 1203200 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00125B58 | 0x00125C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52037 |
DATA | 0x00127000 | 0x000051CC | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.53935 |
BSS | 0x0012D000 | 0x000013E9 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0012F000 | 0x00002A00 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.06861 |
.tls | 0x00132000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00133000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x00134000 | 0x0000EF88 | 0x0000F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.67351 |
.rsrc | 0x00143000 | 0x0022C200 | 0x0022C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.30006 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17015 | 752 | UNKNOWN | Russian - Russia | RT_MANIFEST |
2 | 2.80231 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
8 | 2.6633 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3682 | 2.04342 | 76 | UNKNOWN | UNKNOWN | RT_STRING |
3683 | 2.92331 | 170 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
49
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1624 | "C:\Users\admin\Desktop\awdawd.exe" | C:\Users\admin\Desktop\awdawd.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3489660927 Modules
| |||||||||||||||
| 2512 | "C:\Users\admin\AppData\Local\Temp\upO Builder 0.6.exe" | C:\Users\admin\AppData\Local\Temp\upO Builder 0.6.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Local\Temp\upO Builder 0.6.exe" | C:\Users\admin\AppData\Local\Temp\upO Builder 0.6.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3732 | "C:\Users\admin\Desktop\awdawd.exe" | C:\Users\admin\Desktop\awdawd.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
3 266
Read events
3 112
Write events
148
Delete events
6
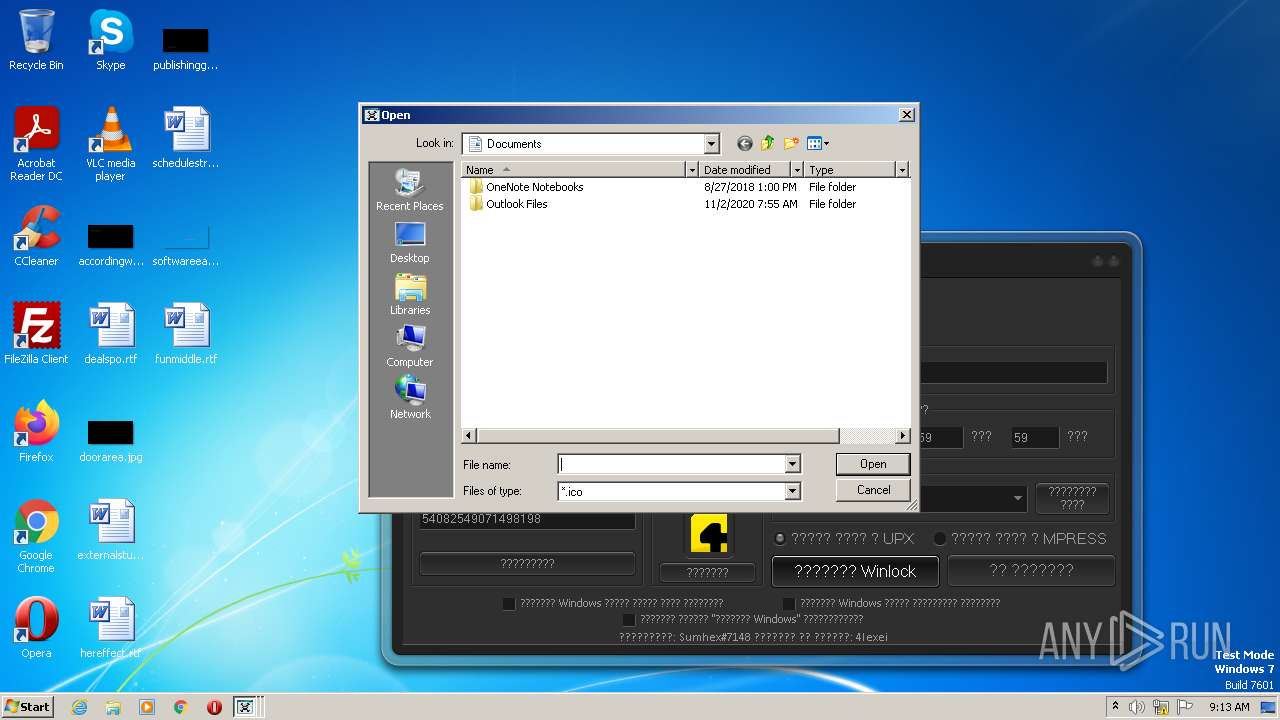
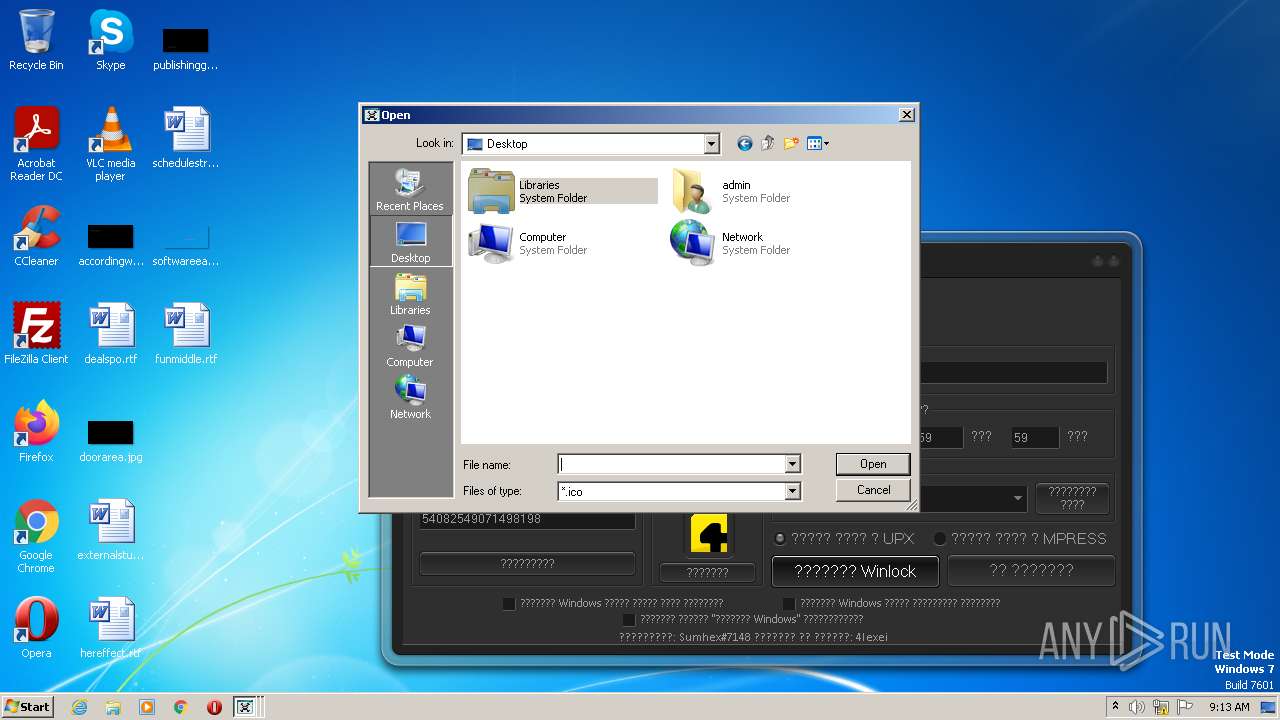
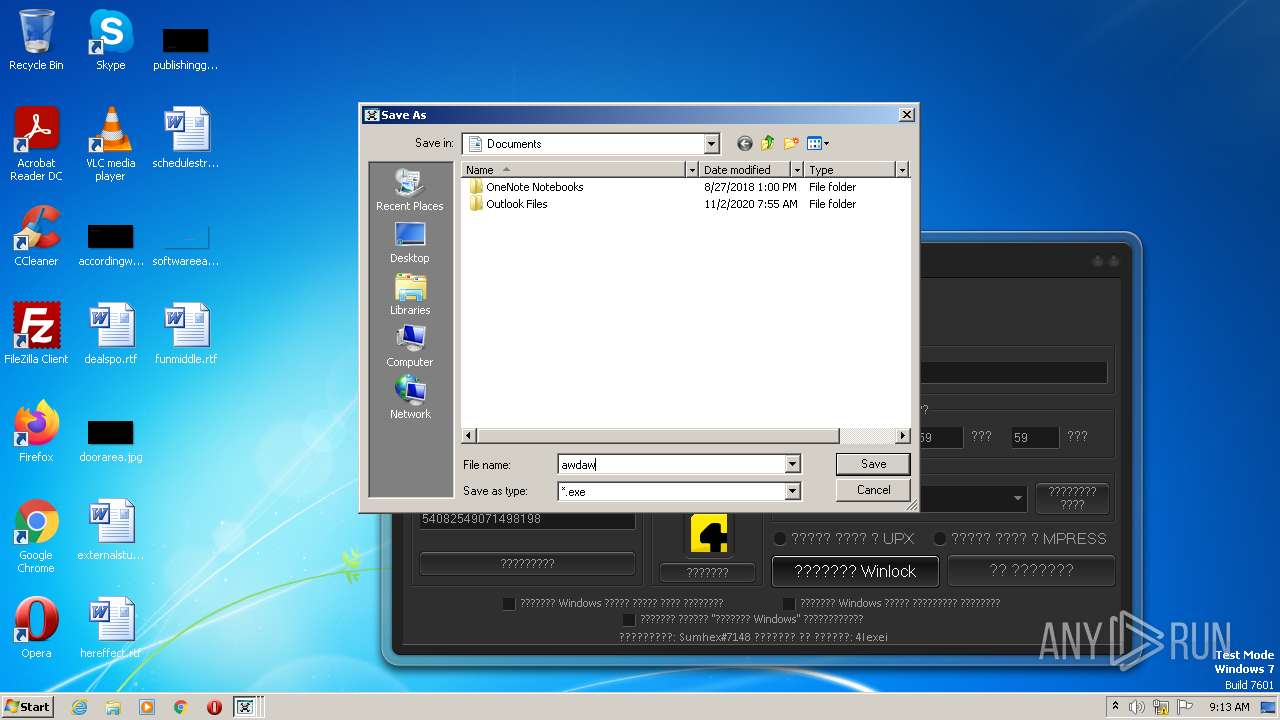
Modification events
| (PID) Process: | (3132) upO Builder 0.6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3132) upO Builder 0.6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3132) upO Builder 0.6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0C000000000000000B00000001000000020000000D00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3132) upO Builder 0.6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000C000000000000000B000000010000000D00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3132) upO Builder 0.6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3132) upO Builder 0.6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3132) upO Builder 0.6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3132) upO Builder 0.6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlgLegacy\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (3132) upO Builder 0.6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlgLegacy\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (3132) upO Builder 0.6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlgLegacy\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | FFlags |
Value: 1 | |||
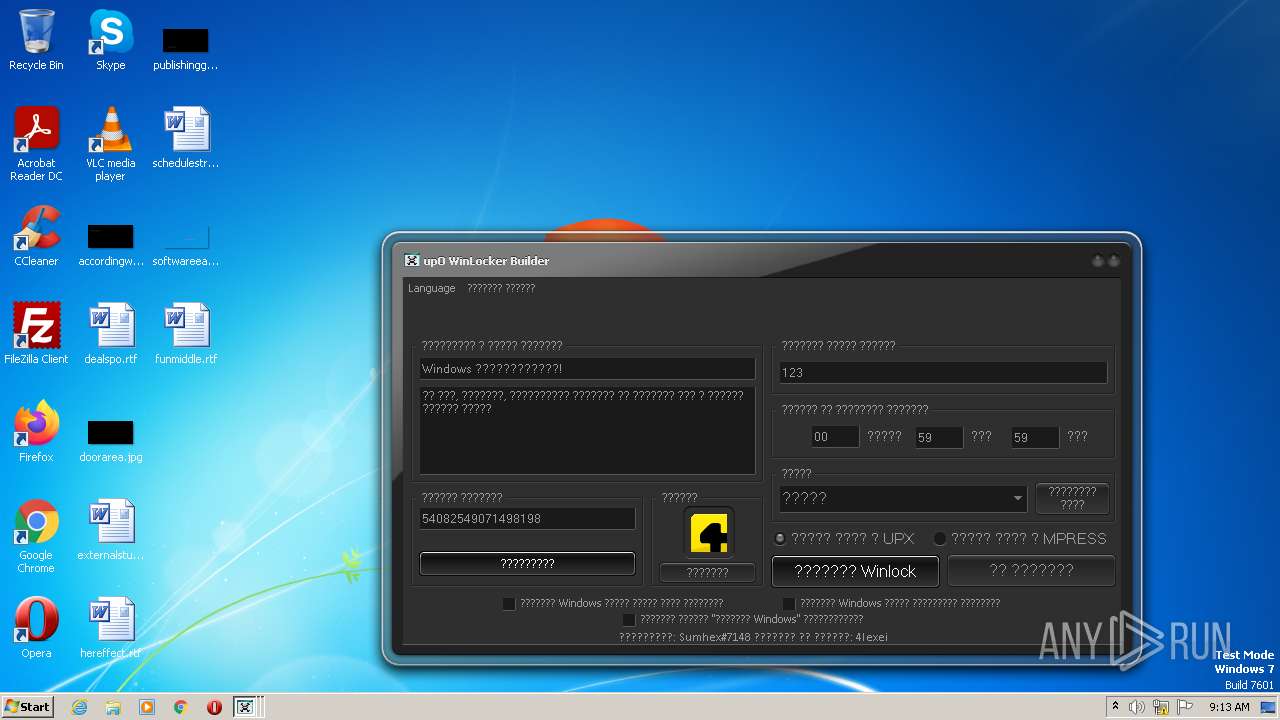
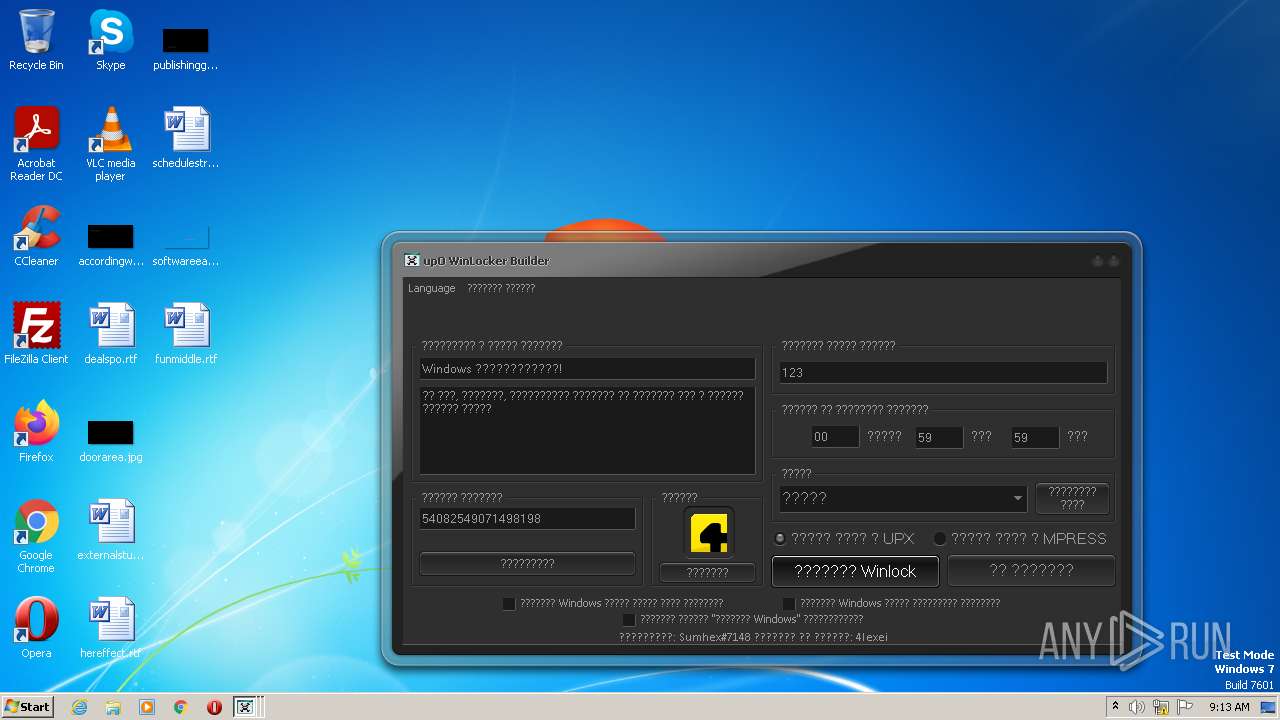
Executable files
34
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3132 | upO Builder 0.6.exe | C:\Users\admin\Desktop\RCXCC25.tmp | executable | |
MD5:— | SHA256:— | |||
| 3132 | upO Builder 0.6.exe | C:\Users\admin\Desktop\RCXCD12.tmp | executable | |
MD5:— | SHA256:— | |||
| 3132 | upO Builder 0.6.exe | C:\Users\admin\Desktop\RCXCD61.tmp | executable | |
MD5:— | SHA256:— | |||
| 3132 | upO Builder 0.6.exe | C:\Users\admin\Desktop\awdawd.exe | executable | |
MD5:— | SHA256:— | |||
| 3132 | upO Builder 0.6.exe | C:\Users\admin\Desktop\RCXCCC3.tmp | executable | |
MD5:— | SHA256:— | |||
| 3132 | upO Builder 0.6.exe | C:\Users\admin\Desktop\RCXCE5F.tmp | executable | |
MD5:— | SHA256:— | |||
| 3132 | upO Builder 0.6.exe | C:\Users\admin\Desktop\RCXCE10.tmp | executable | |
MD5:— | SHA256:— | |||
| 3132 | upO Builder 0.6.exe | C:\Users\admin\Desktop\RCXCDA0.tmp | executable | |
MD5:— | SHA256:— | |||
| 3132 | upO Builder 0.6.exe | C:\Users\admin\Desktop\RCXCDD0.tmp | executable | |
MD5:— | SHA256:— | |||
| 1624 | awdawd.exe | C:\Users\admin\Desktop\Time2.ini | text | |
MD5:EE71EF7E930722B5B29011DD13C1F0BE | SHA256:0DCB9642194F08F6EC65920AB26F5BC10653983CDE9F3A82505E297E44E15C3C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report