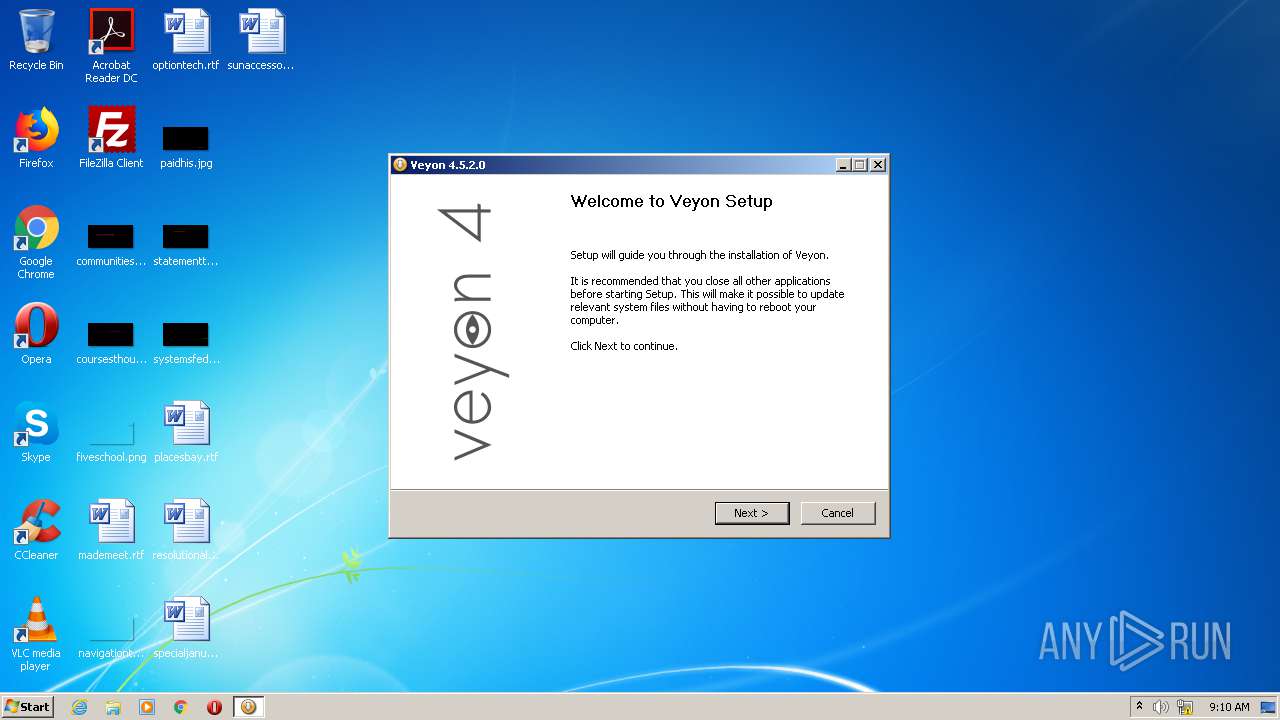
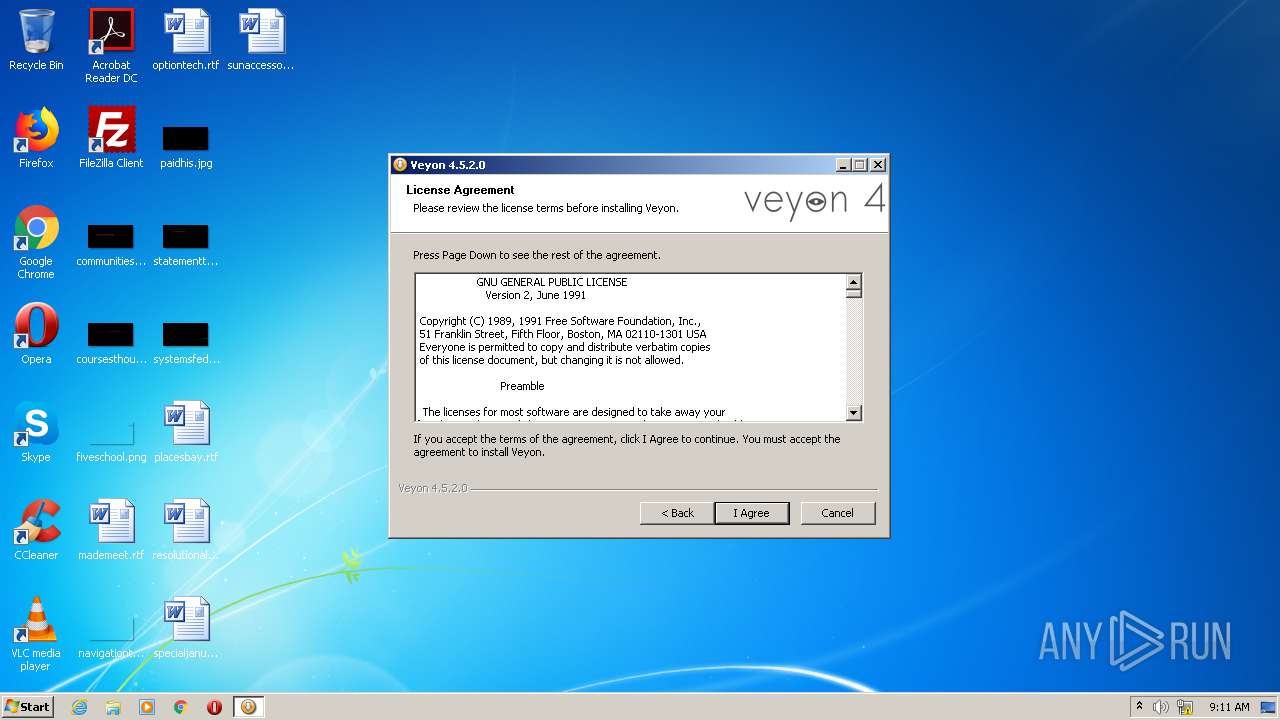
| File name: | veyon-4.5.2.0-win64-setup.exe |
| Full analysis: | https://app.any.run/tasks/9feffe2f-9cbf-4638-bfc3-f8203c9090cd |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2020, 09:10:23 |
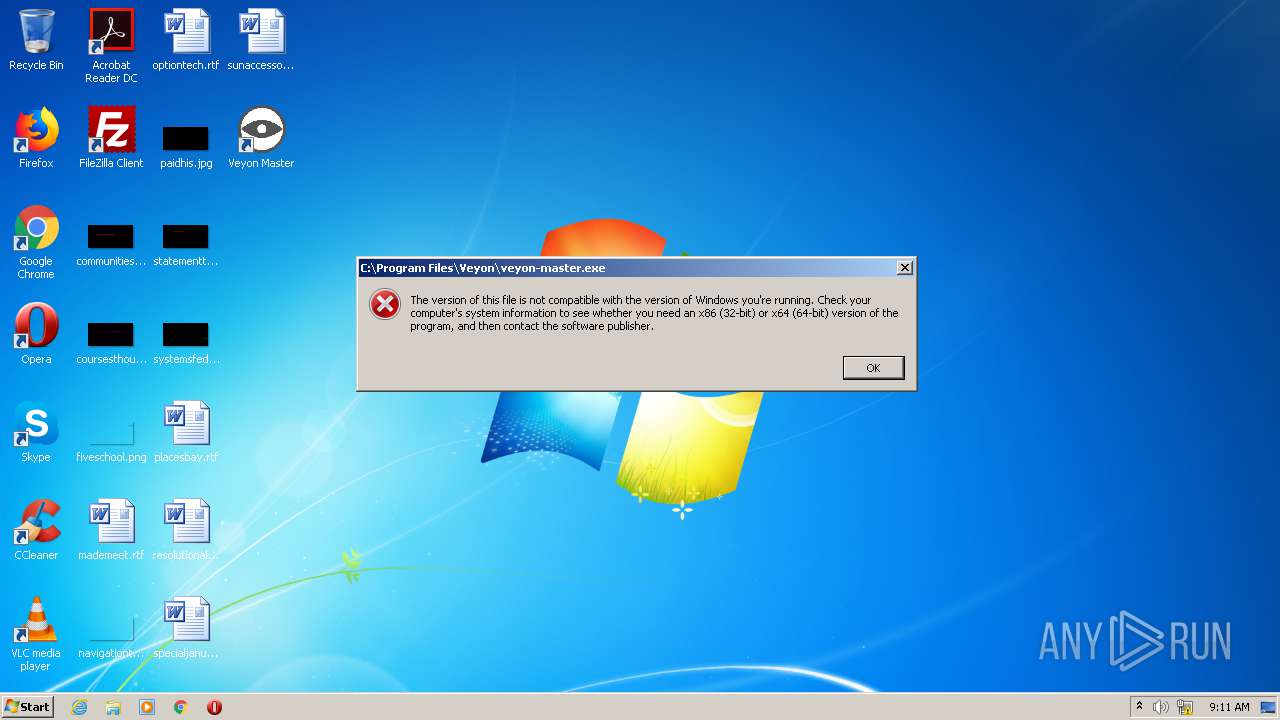
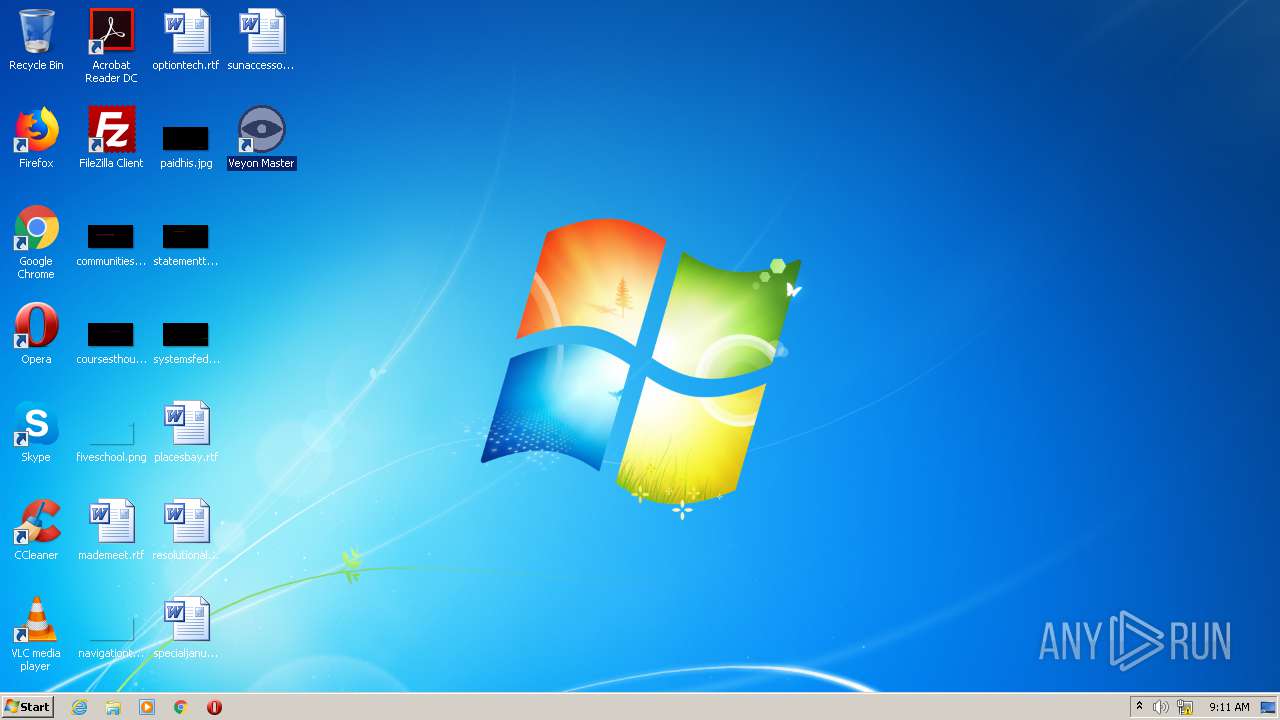
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 22C77DEDDF082F5623C2304D895B5171 |
| SHA1: | 6FF0F5383BF0F634DF48A39E22396E890D73DABA |
| SHA256: | 82D3F1465E1AA9A94D2E5A96BF616DBD0F257F5BFA1F39582E25A7D844DDE4A9 |
| SSDEEP: | 196608:NXBEkjnUhmwFTziUZy1iHY2PVyLjljGZtN+30b/by2BqooizXaUNS/pNsUzuFK5r:VBEkYm8Ty1sVqRaZtNLOaoYNS/H1KKy+ |
MALICIOUS
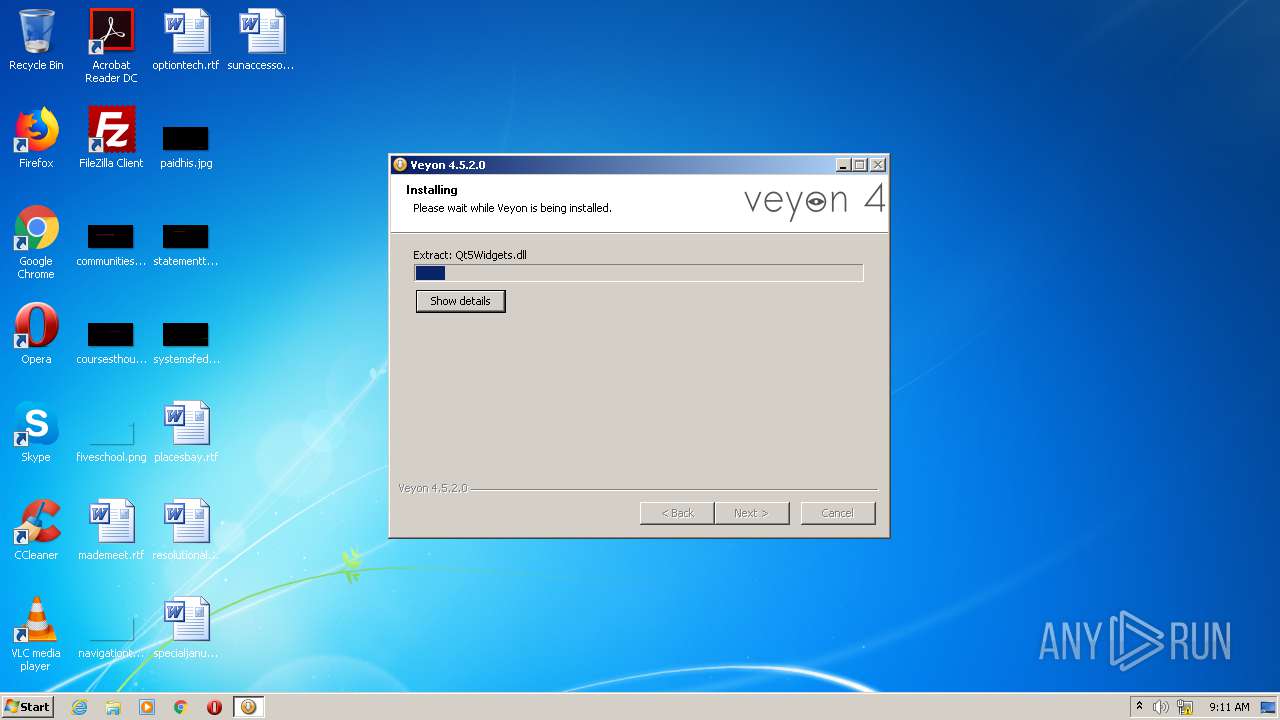
Loads dropped or rewritten executable
- veyon-4.5.2.0-win64-setup.exe (PID: 3112)
SUSPICIOUS
Executable content was dropped or overwritten
- veyon-4.5.2.0-win64-setup.exe (PID: 3112)
Drops a file that was compiled in debug mode
- veyon-4.5.2.0-win64-setup.exe (PID: 3112)
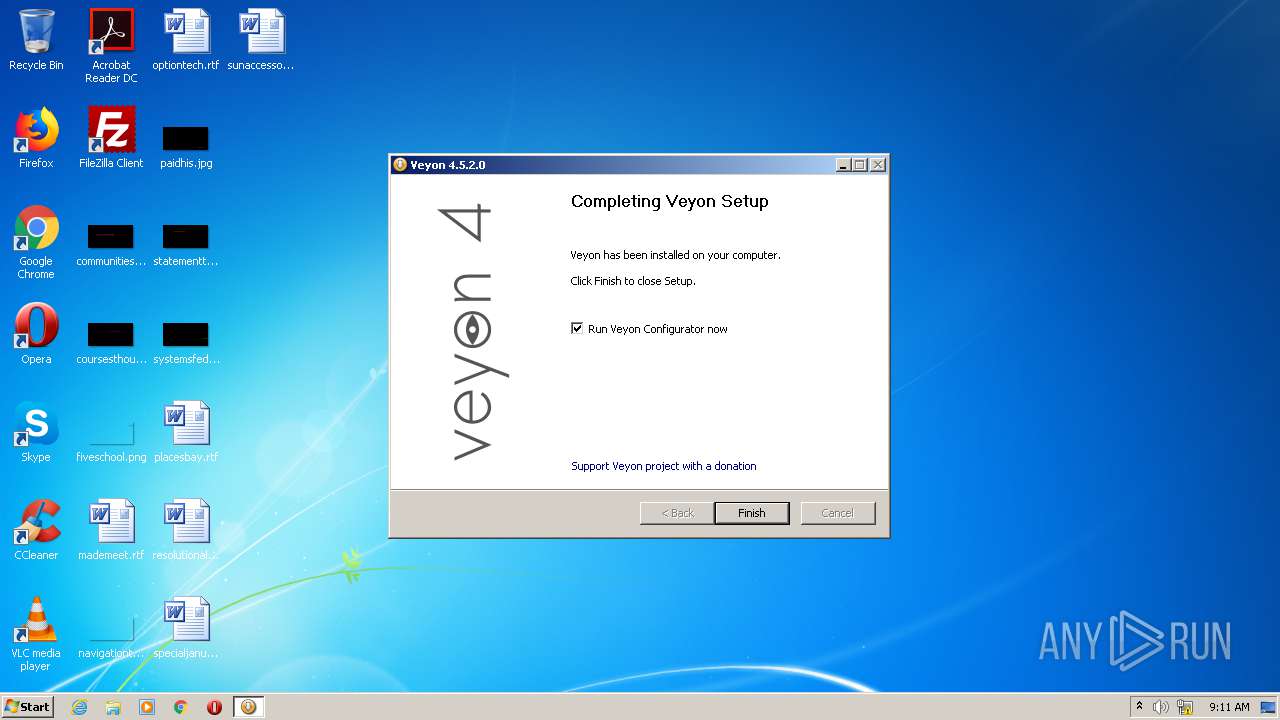
Creates a software uninstall entry
- veyon-4.5.2.0-win64-setup.exe (PID: 3112)
Drops a file with too old compile date
- veyon-4.5.2.0-win64-setup.exe (PID: 3112)
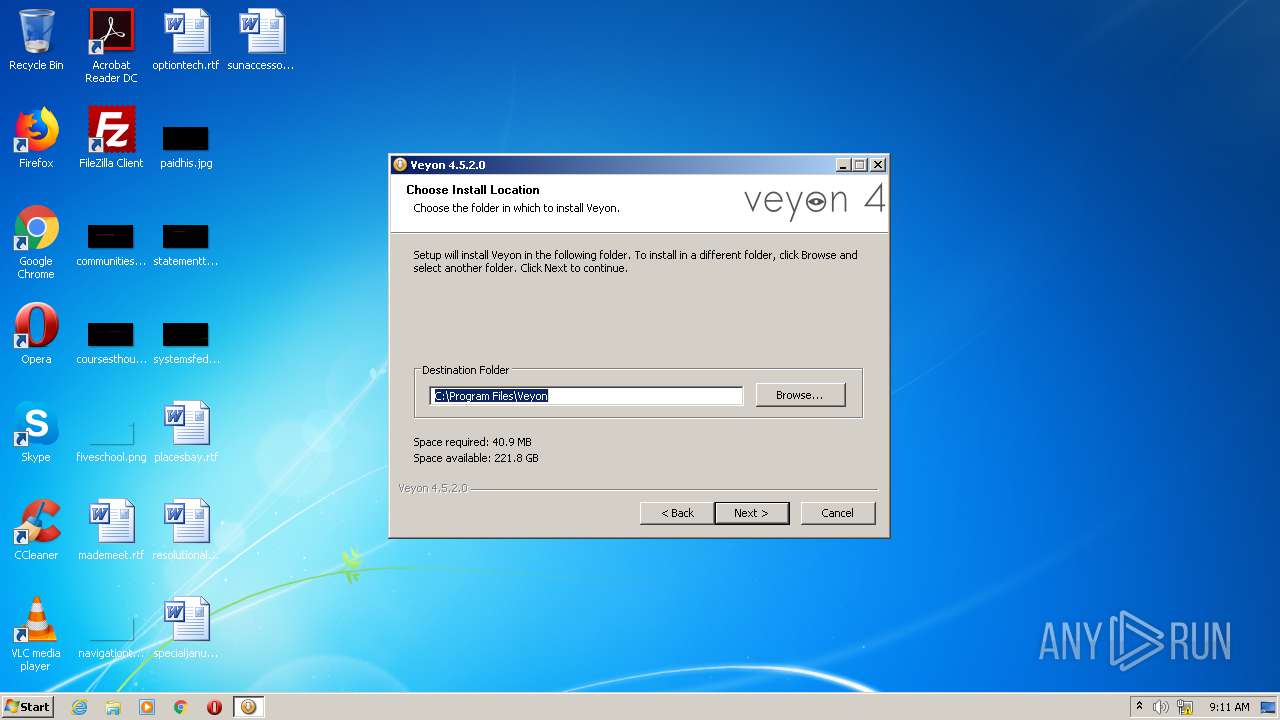
Creates a directory in Program Files
- veyon-4.5.2.0-win64-setup.exe (PID: 3112)
Creates files in the program directory
- veyon-4.5.2.0-win64-setup.exe (PID: 3112)
INFO
Dropped object may contain Bitcoin addresses
- veyon-4.5.2.0-win64-setup.exe (PID: 3112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:31 20:05:25+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.34 |
| CodeSize: | 36864 |
| InitializedDataSize: | 40448 |
| UninitializedDataSize: | 108032 |
| EntryPoint: | 0x433c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.5.2.0 |
| ProductVersionNumber: | 4.5.2.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Veyon Solutions |
| FileDescription: | Veyon Installer |
| FileVersion: | 4.5.2.0 |
| LegalCopyright: | 2004-2020 Veyon Solutions / Tobias Junghans |
| ProductName: | Veyon |
| ProductVersion: | 4.5.2.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Mar-2020 18:05:25 |
| Detected languages: |
|
| CompanyName: | Veyon Solutions |
| FileDescription: | Veyon Installer |
| FileVersion: | 4.5.2.0 |
| LegalCopyright: | 2004-2020 Veyon Solutions / Tobias Junghans |
| ProductName: | Veyon |
| ProductVersion: | 4.5.2.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 31-Mar-2020 18:05:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008F54 | 0x00009000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.9641 |
.data | 0x0000A000 | 0x000000C0 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.42446 |
.rdata | 0x0000B000 | 0x0000736C | 0x00007400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.28118 |
.bss | 0x00013000 | 0x0001A500 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002E000 | 0x0000133C | 0x00001400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.30969 |
.ndata | 0x00030000 | 0x00018000 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00048000 | 0x0000BD80 | 0x0000BE00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98066 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28991 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.61959 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.84061 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.16608 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 3.91942 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 5.42186 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.58096 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 3.74963 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 3.01957 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
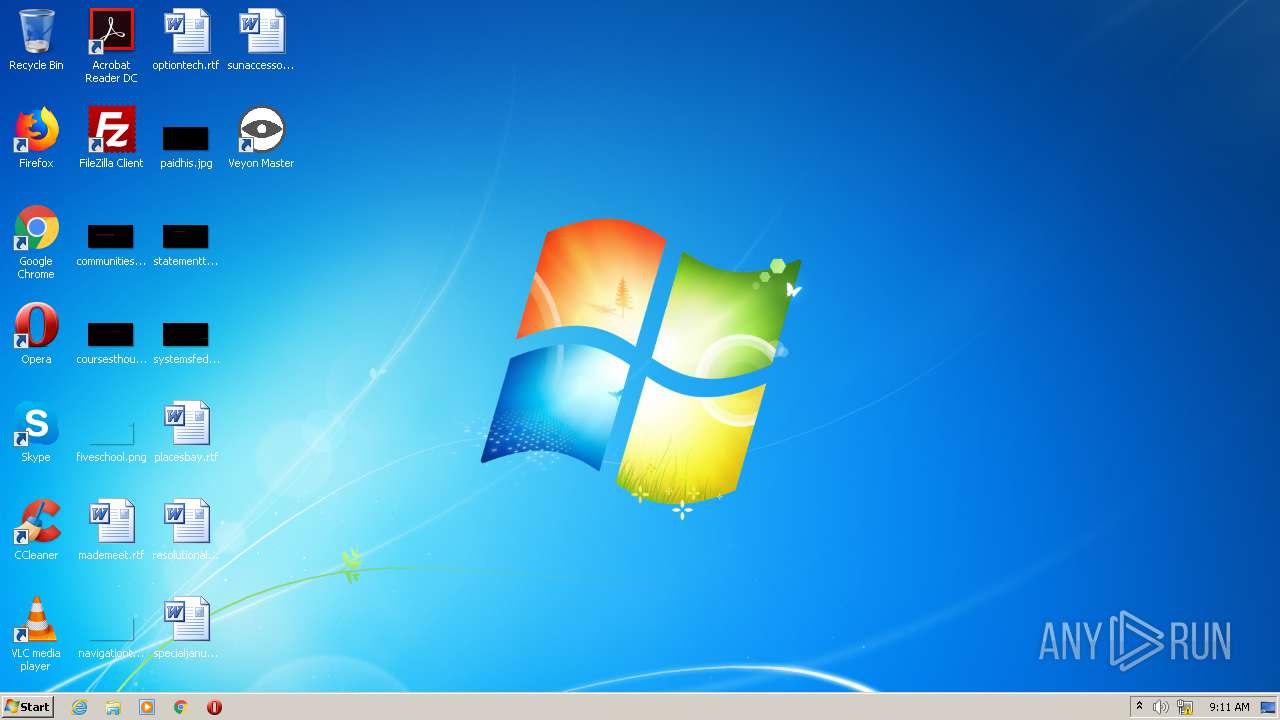
| 3112 | "C:\Users\admin\AppData\Local\Temp\veyon-4.5.2.0-win64-setup.exe" | C:\Users\admin\AppData\Local\Temp\veyon-4.5.2.0-win64-setup.exe | explorer.exe | ||||||||||||
User: admin Company: Veyon Solutions Integrity Level: HIGH Description: Veyon Installer Exit code: 0 Version: 4.5.2.0 Modules
| |||||||||||||||
| 3756 | "C:\Users\admin\AppData\Local\Temp\veyon-4.5.2.0-win64-setup.exe" | C:\Users\admin\AppData\Local\Temp\veyon-4.5.2.0-win64-setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Veyon Solutions Integrity Level: MEDIUM Description: Veyon Installer Exit code: 3221226540 Version: 4.5.2.0 Modules
| |||||||||||||||
Total events
354
Read events
345
Write events
9
Delete events
0
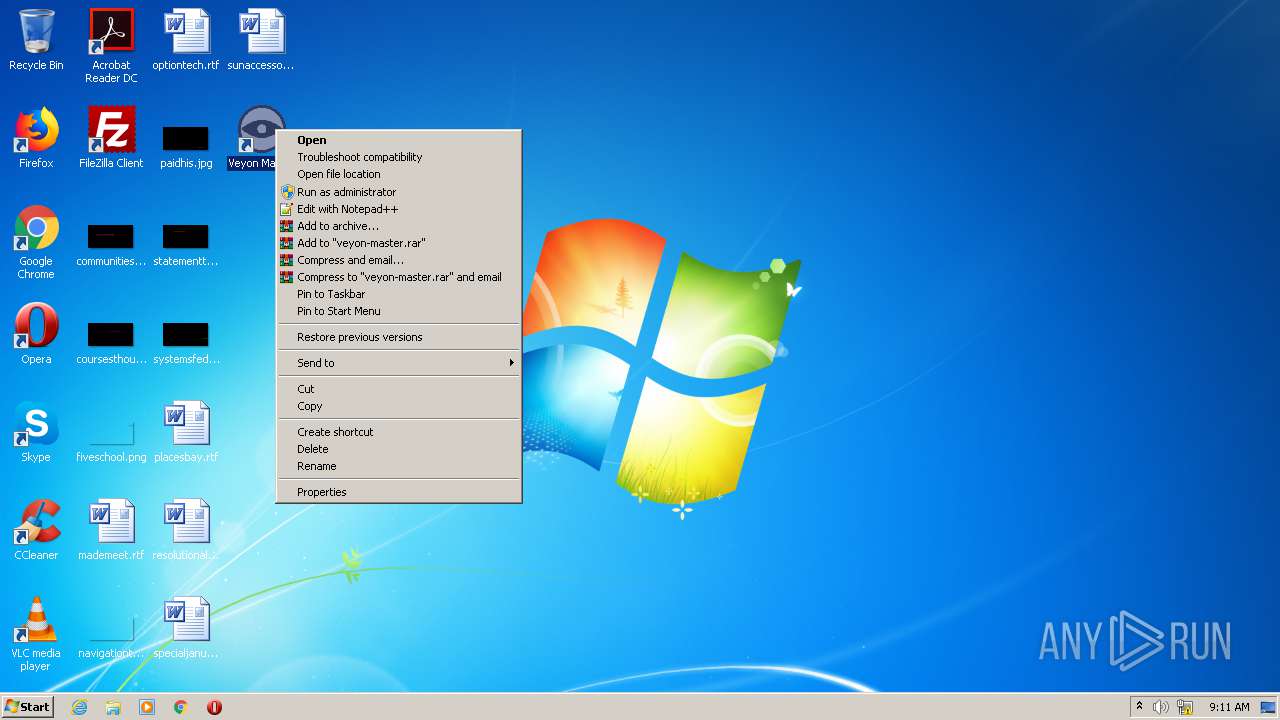
Modification events
| (PID) Process: | (3112) veyon-4.5.2.0-win64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Lsa |
| Operation: | write | Name: | ForceGuest |
Value: 0 | |||
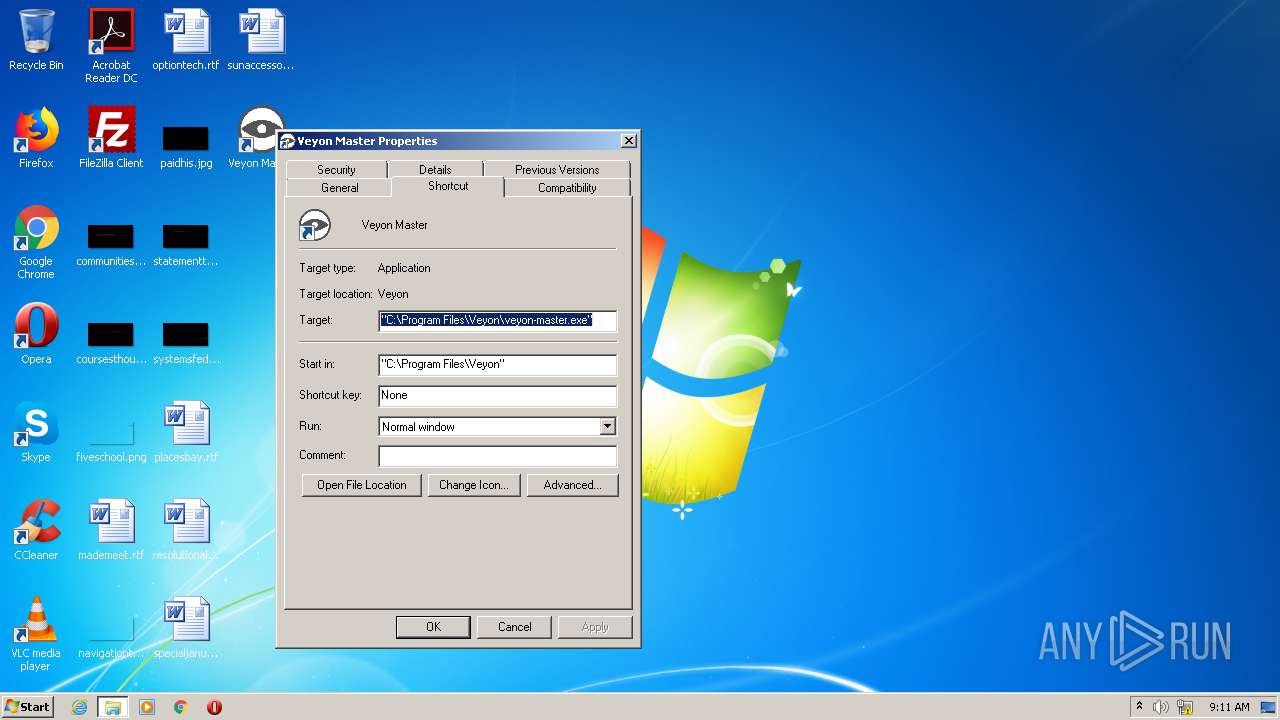
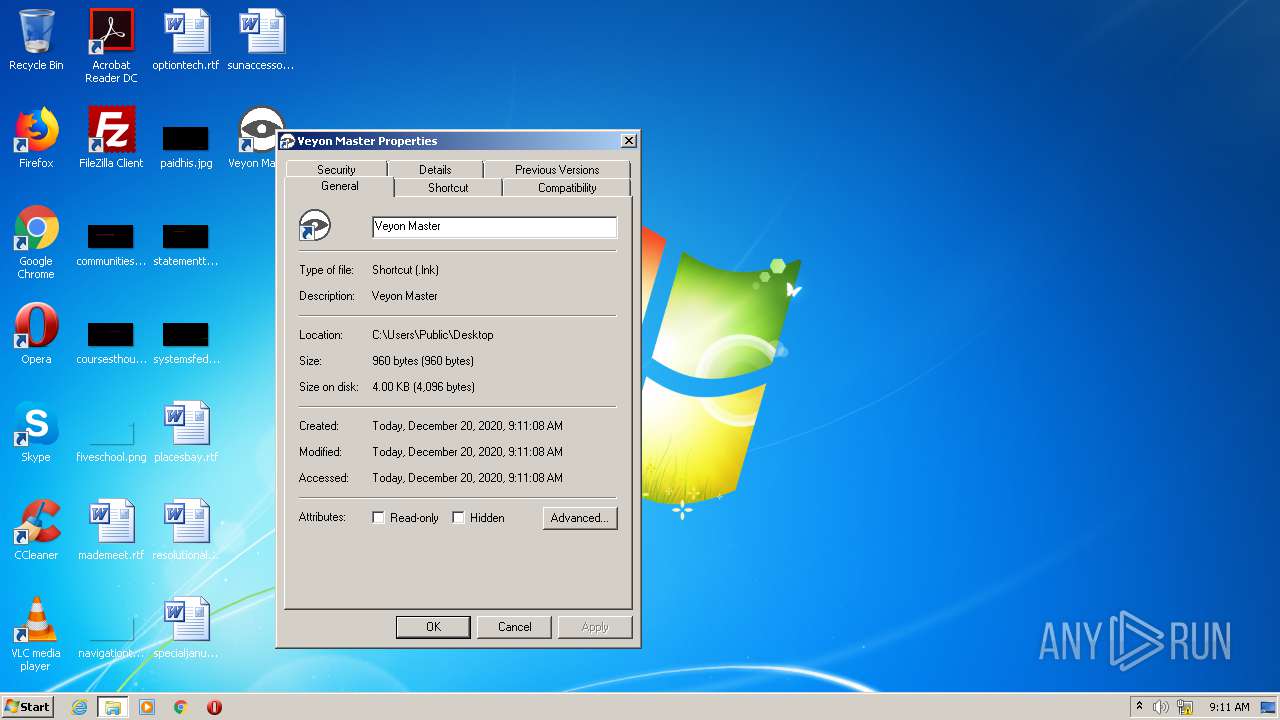
| (PID) Process: | (3112) veyon-4.5.2.0-win64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\veyon-master.exe |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Veyon\veyon-master.exe | |||
| (PID) Process: | (3112) veyon-4.5.2.0-win64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Veyon |
| Operation: | write | Name: | DisplayName |
Value: Veyon | |||
| (PID) Process: | (3112) veyon-4.5.2.0-win64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Veyon |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Veyon\uninstall.exe | |||
| (PID) Process: | (3112) veyon-4.5.2.0-win64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Veyon |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Veyon\veyon-master.exe | |||
| (PID) Process: | (3112) veyon-4.5.2.0-win64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Veyon |
| Operation: | write | Name: | DisplayVersion |
Value: 4.5.2.0 | |||
| (PID) Process: | (3112) veyon-4.5.2.0-win64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Veyon |
| Operation: | write | Name: | Publisher |
Value: Veyon Solutions | |||
| (PID) Process: | (3112) veyon-4.5.2.0-win64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Veyon |
| Operation: | write | Name: | URLInfoAbout |
Value: https://veyon.io | |||
| (PID) Process: | (3112) veyon-4.5.2.0-win64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Veyon |
| Operation: | write | Name: | Installer Language |
Value: 1033 | |||
Executable files
64
Suspicious files
0
Text files
8
Unknown types
69
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3112 | veyon-4.5.2.0-win64-setup.exe | C:\Program Files\Veyon\veyon-worker.exe | executable | |
MD5:1182F1BA36F8F0E54E1EEBCB672509F6 | SHA256:F8FE457B3BD9C06C38784E91C20816BCC84F23267DD82E9686E8A31086C21366 | |||
| 3112 | veyon-4.5.2.0-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsoFA9E.tmp\modern-wizard.bmp | image | |
MD5:A8D81A837E19534E2663FB02A1355BEA | SHA256:2BAD887CD8FA8206FED401C3B1CDEE18AC9A65CFC9F982A95577791226836660 | |||
| 3112 | veyon-4.5.2.0-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsoFA9E.tmp\UserInfo.dll | executable | |
MD5:30B054C33C2EF209071FAA27C38C06A6 | SHA256:09BE55D6FAC9D5DC47F034FF8FBD9E60024AF68EFFD931C5D7AE57809370654C | |||
| 3112 | veyon-4.5.2.0-win64-setup.exe | C:\Program Files\Veyon\interception.dll | executable | |
MD5:7F8AD1A3CD30F1F40D6EE947B900E4A7 | SHA256:1218C8FE7ADD20195504B3CD8DFF72A4DD10C2502AB2258A6A15905B988B5442 | |||
| 3112 | veyon-4.5.2.0-win64-setup.exe | C:\Program Files\Veyon\libcrypto-1_1-x64.dll | executable | |
MD5:93AD794961490FFFF7F6D0F9E3A70C52 | SHA256:45239E881536DF559B4802A0CF64EF23B537E74820FFC7436AE3EDD0E43B0333 | |||
| 3112 | veyon-4.5.2.0-win64-setup.exe | C:\Program Files\Veyon\libgcc_s_seh-1.dll | executable | |
MD5:3BF002392C8333DC05A3E0C1F17F16C8 | SHA256:F0176303AB6E239833339501AECF8D8C7AC6896BF301ECA5E144A38CCDB14692 | |||
| 3112 | veyon-4.5.2.0-win64-setup.exe | C:\Program Files\Veyon\ddengine64.dll | executable | |
MD5:B2A290FA97518F7081F8DA57702A8519 | SHA256:62C3C83B279A9174F8EDEC7F35320648074994B210B3F6228EA5FC823D5E8EDD | |||
| 3112 | veyon-4.5.2.0-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsoFA9E.tmp\modern-header.bmp | image | |
MD5:CA505EE1B37AE9EA906064497276B9D4 | SHA256:479E358E48AEAD66F293DA8556FD3E66D6B14BF94A8C1B5C778D6C8ED4B616B1 | |||
| 3112 | veyon-4.5.2.0-win64-setup.exe | C:\Program Files\Veyon\veyon-server.exe | executable | |
MD5:3769CE97A14E53B2D35252AC895232A2 | SHA256:FC6EA56E343D1A24BA530389337331D3CCAC6E6B1516383922DC76C4468348AE | |||
| 3112 | veyon-4.5.2.0-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsoFA9E.tmp\nsDialogs.dll | executable | |
MD5:5198128986BE9C1CE35727F557A6A1E9 | SHA256:E81473FF4798CA50A951D183759671EEFB6597868C81890E3F67760D47B14004 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report