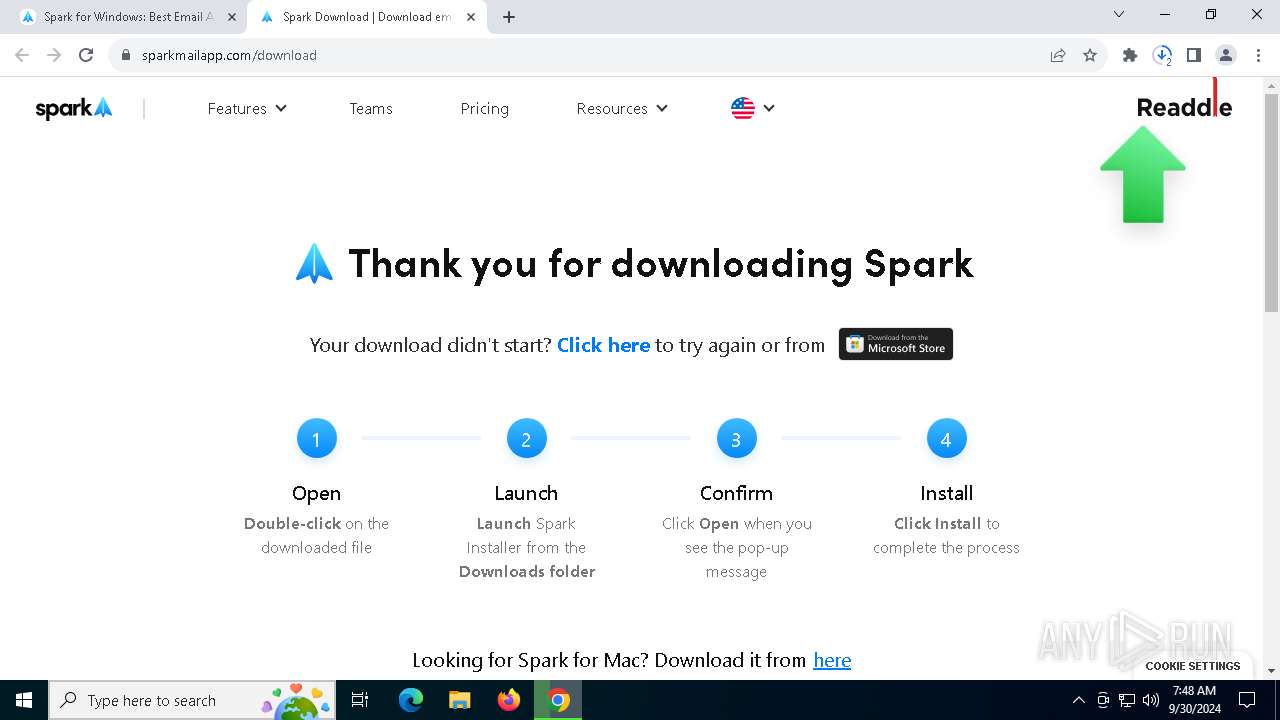
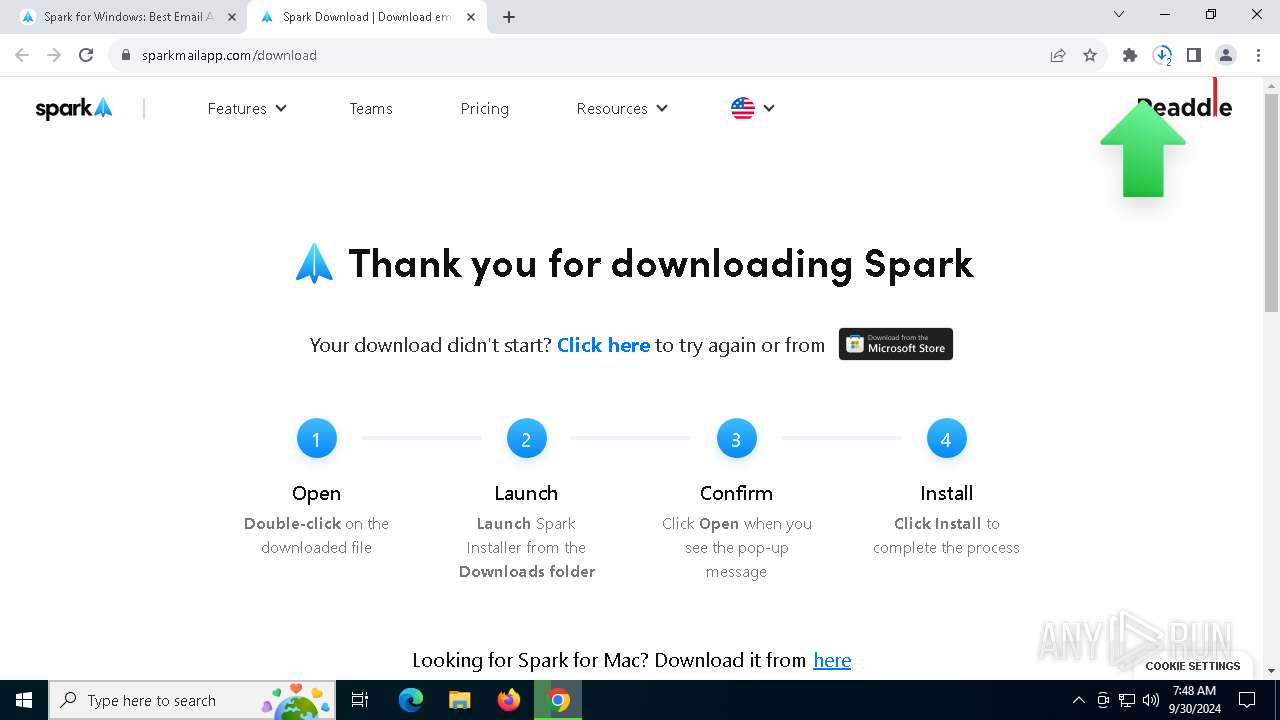
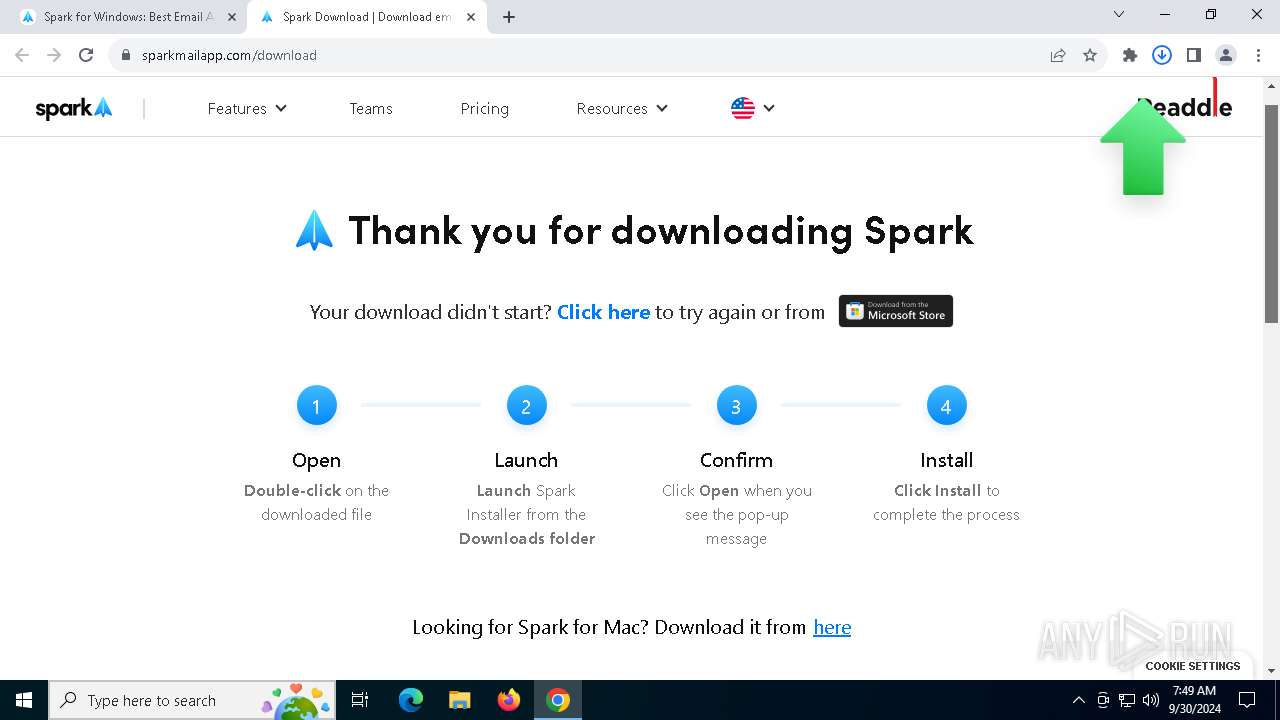
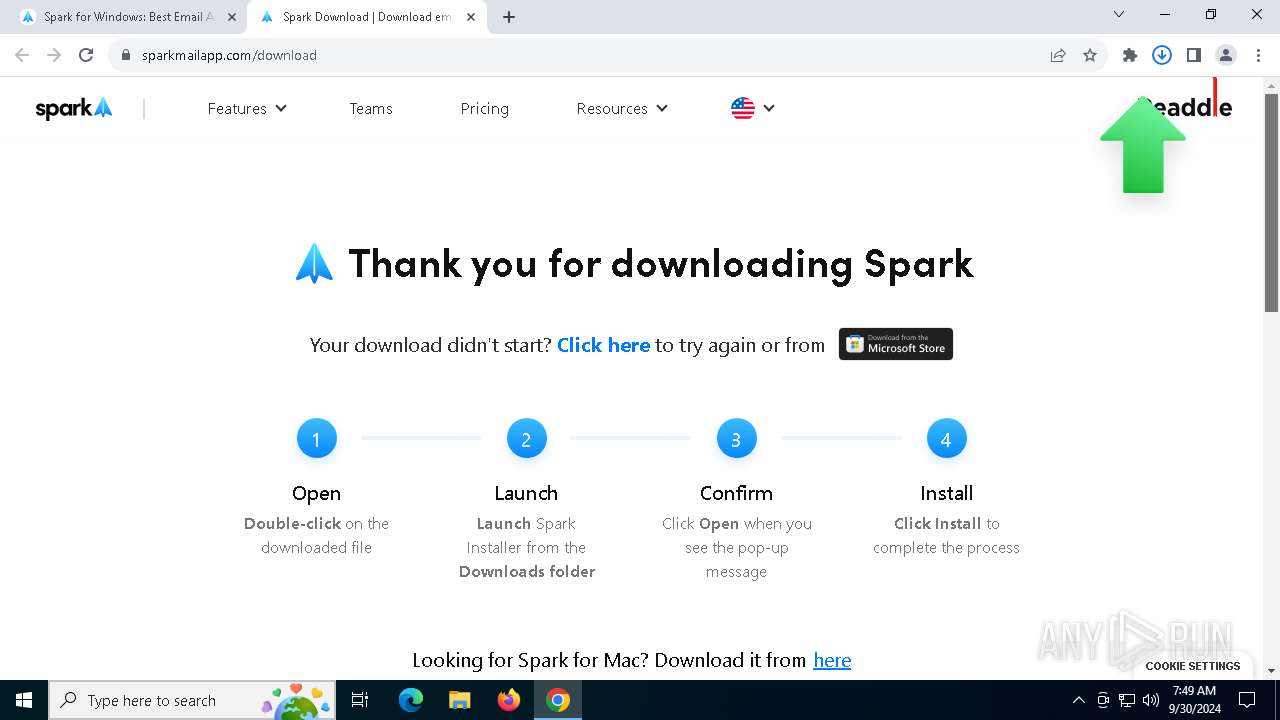
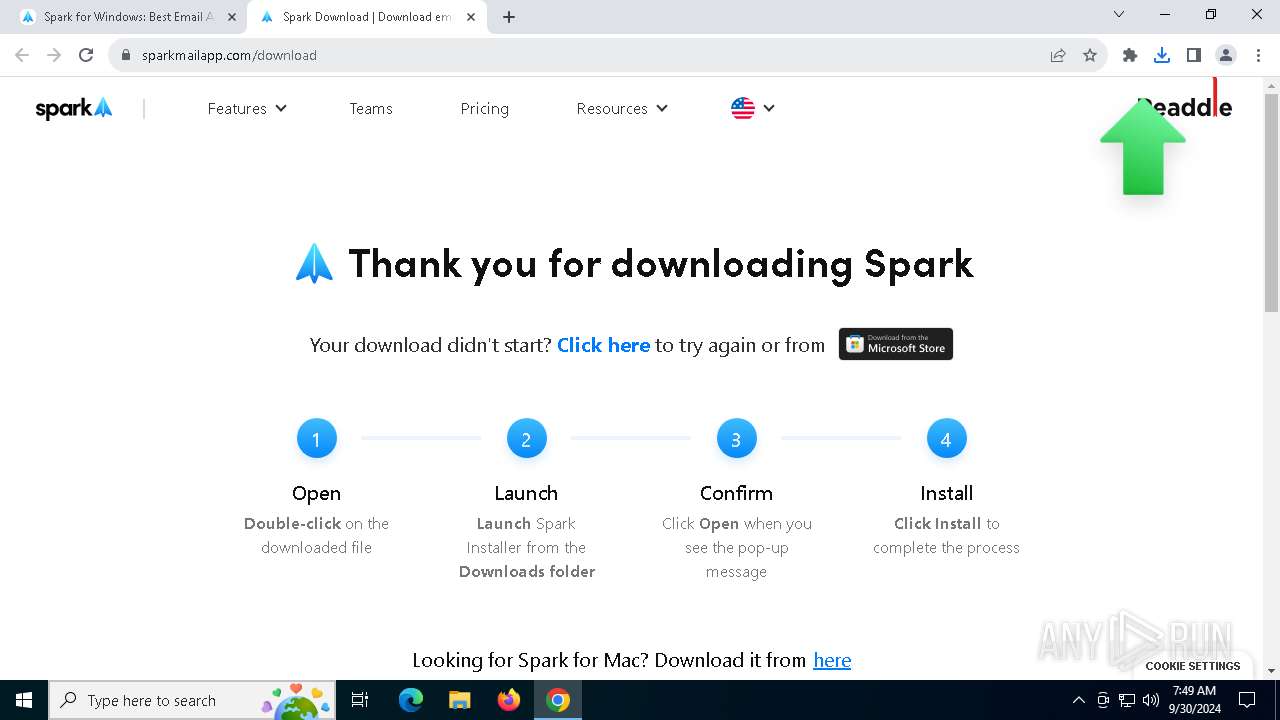
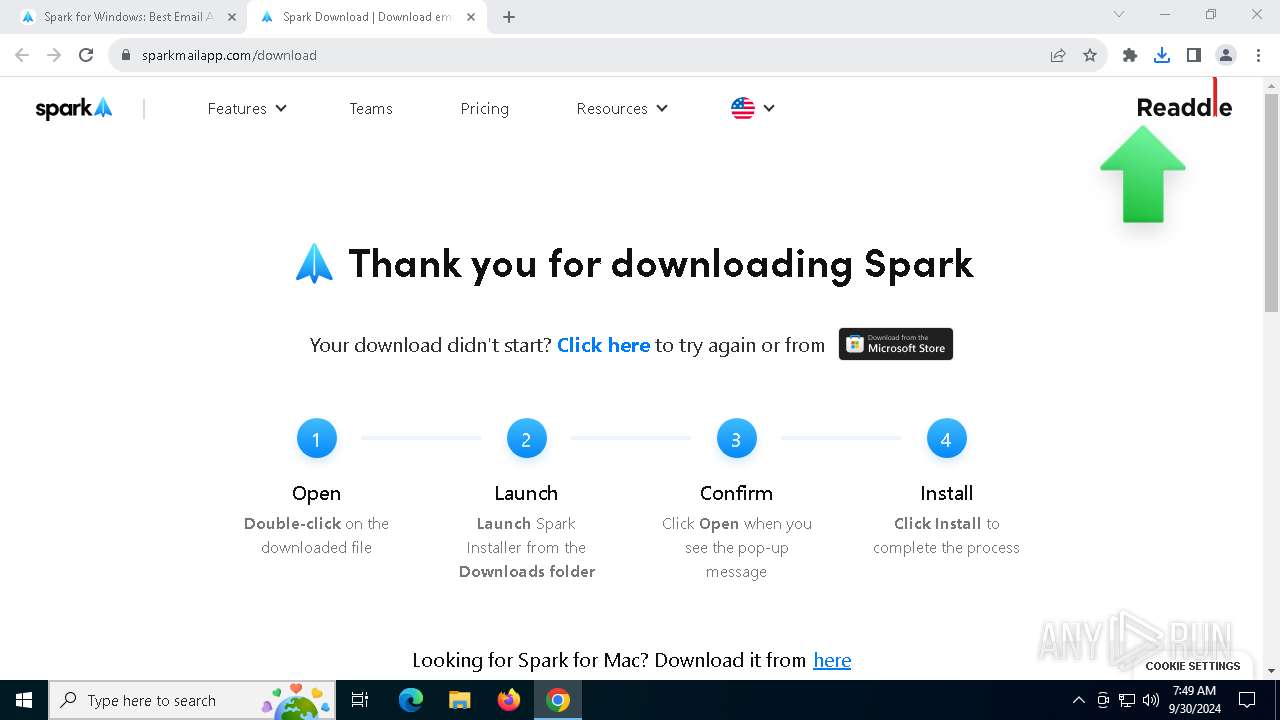
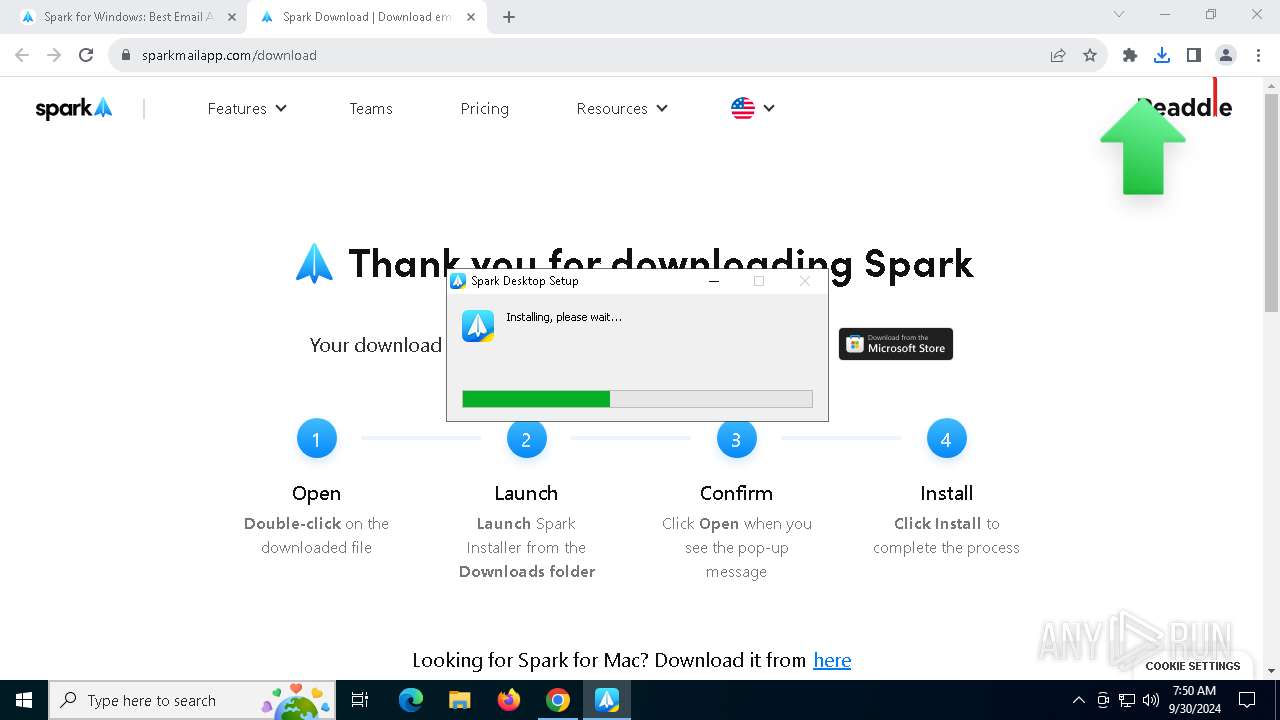
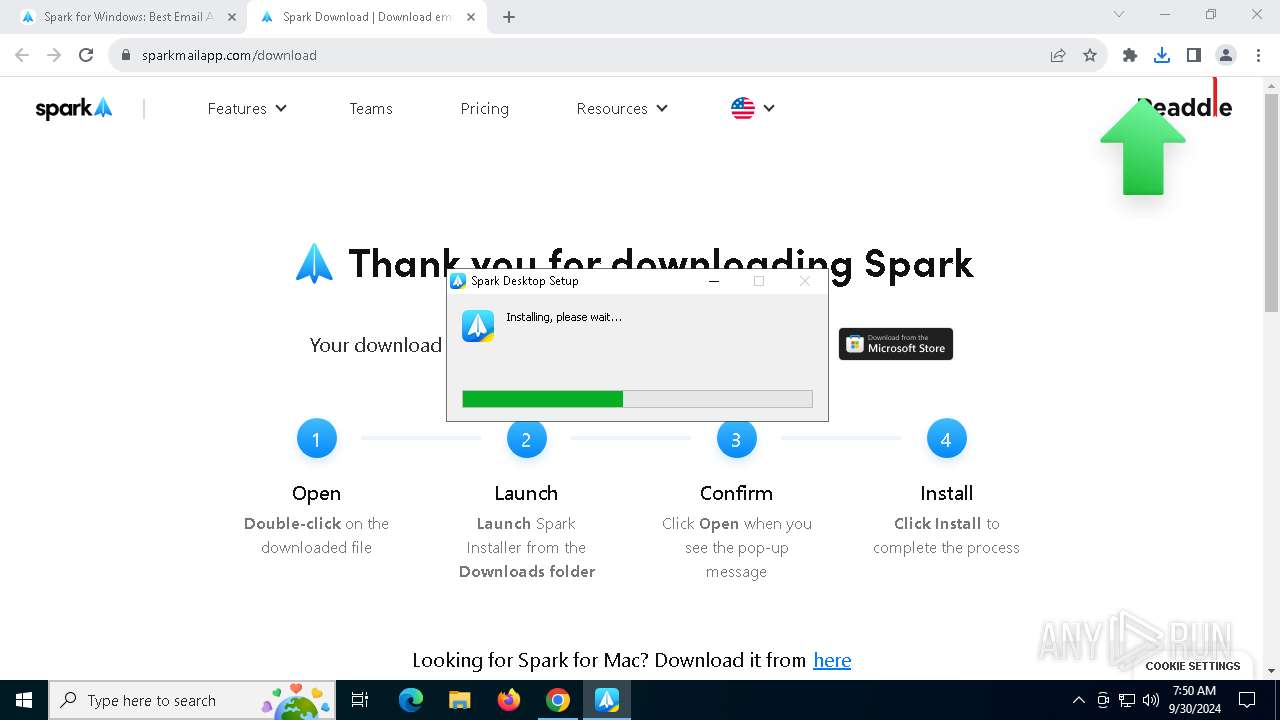
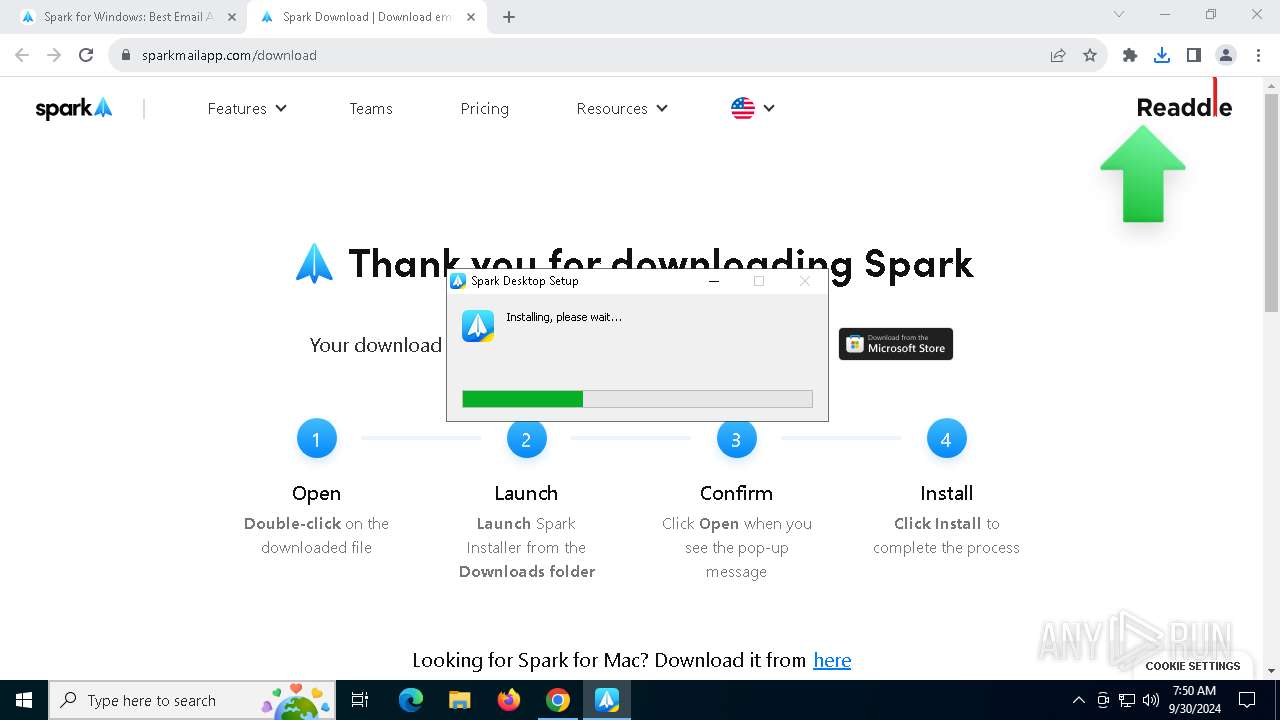
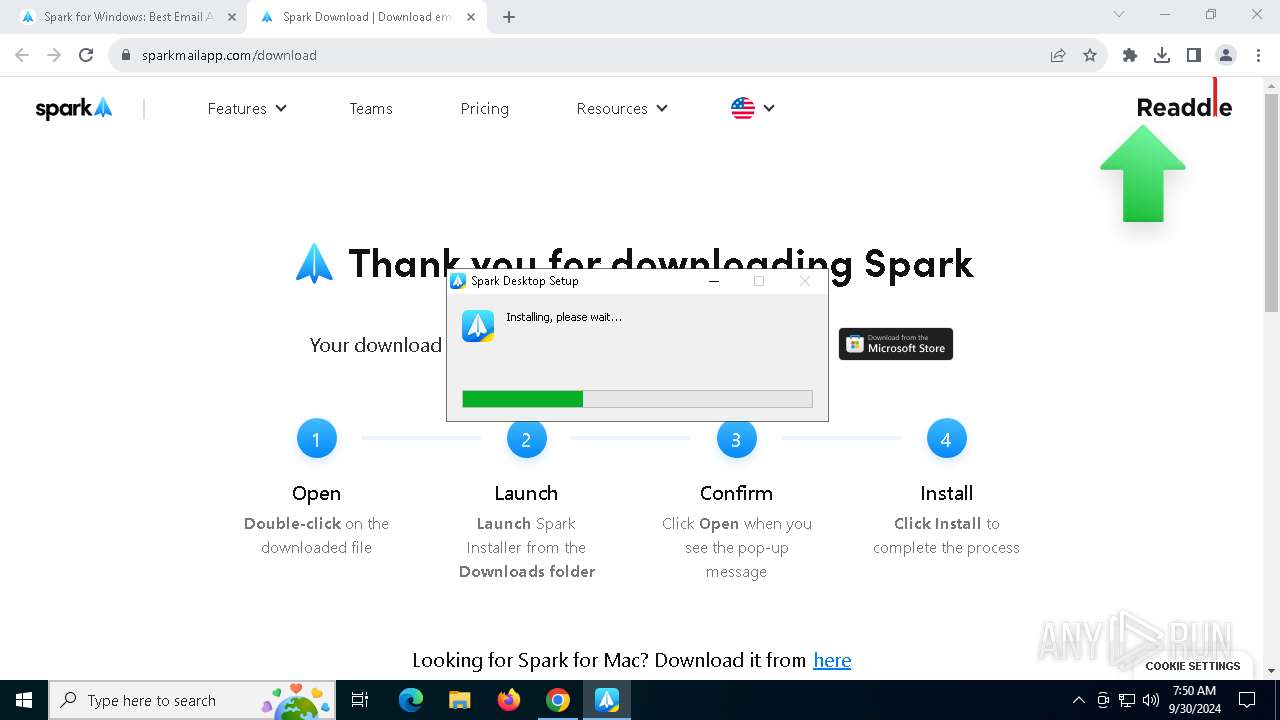
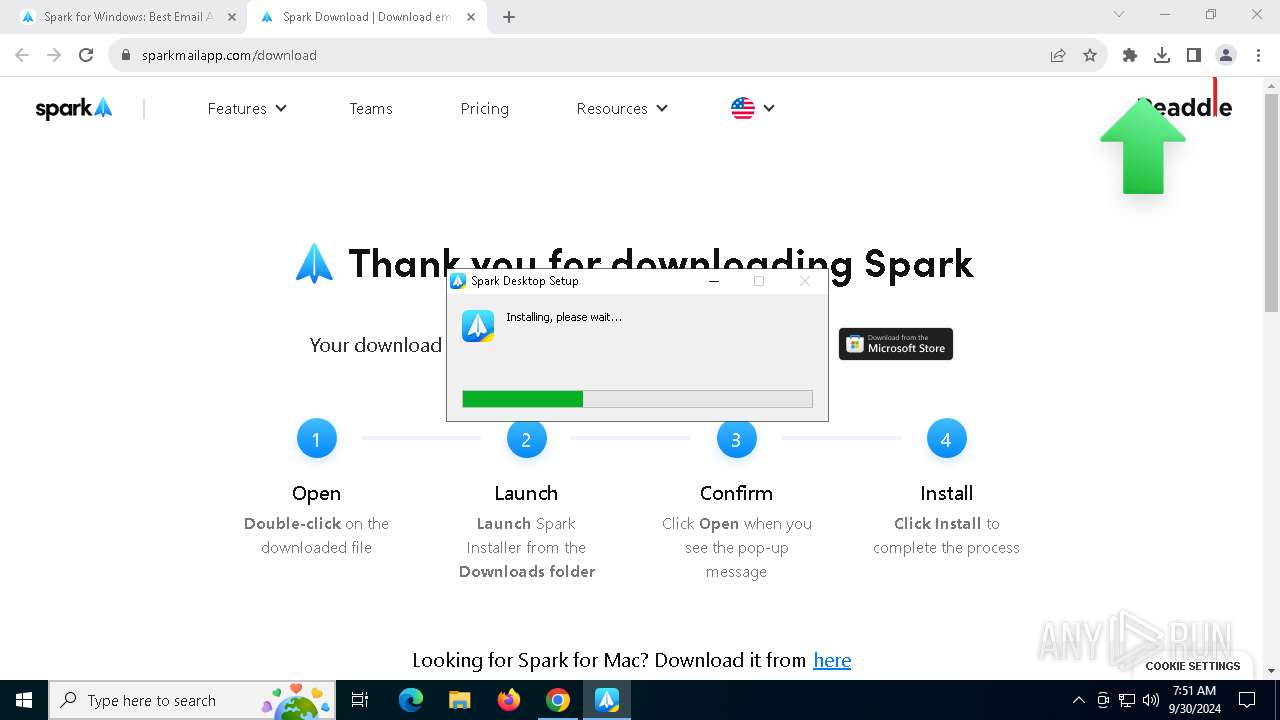
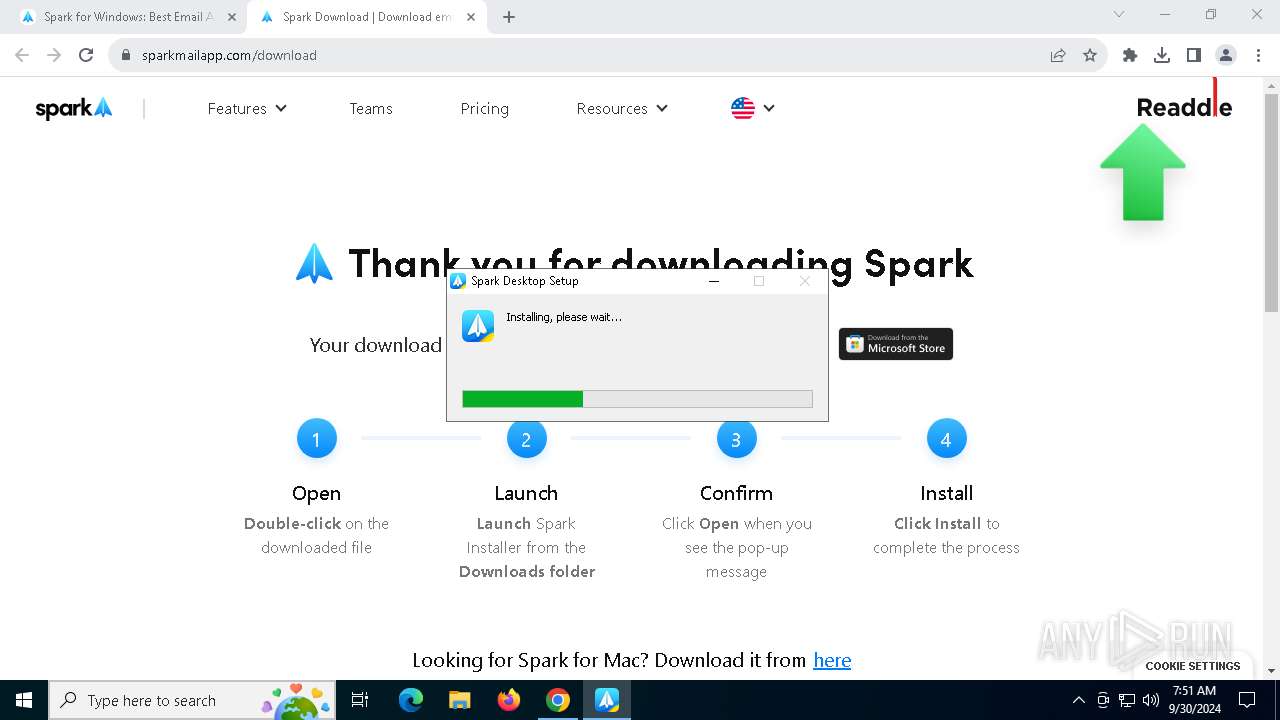
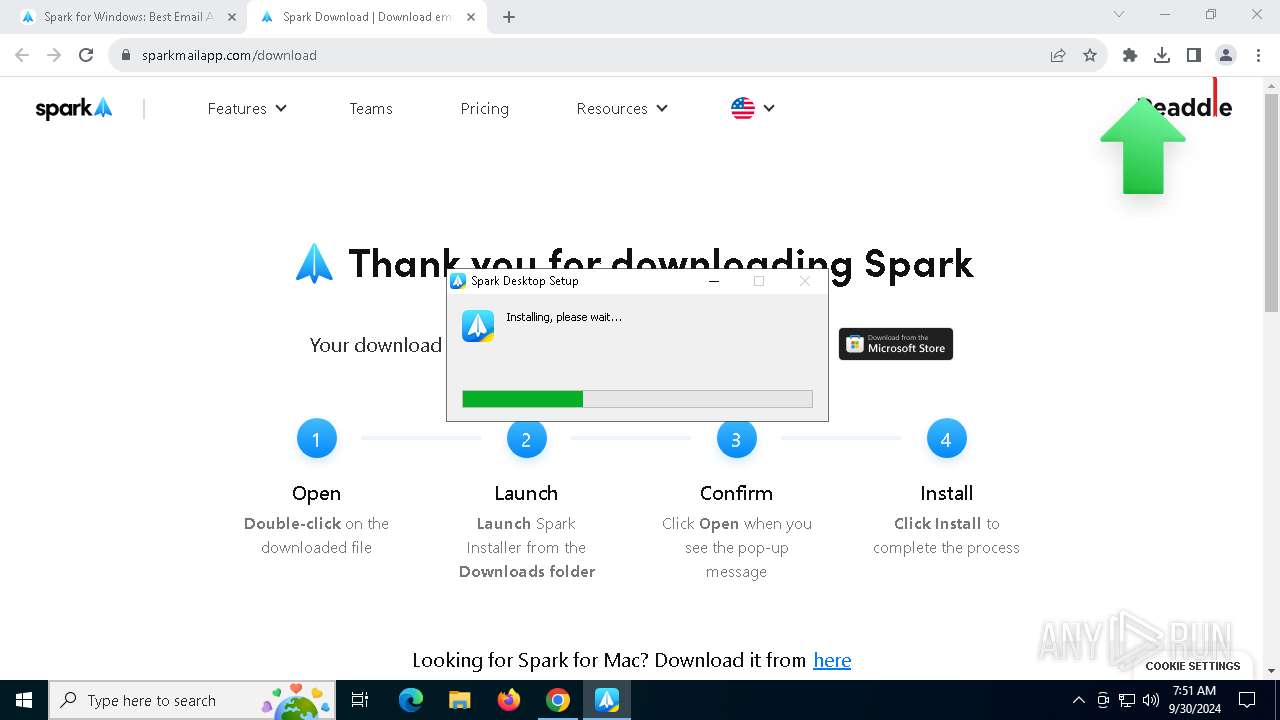
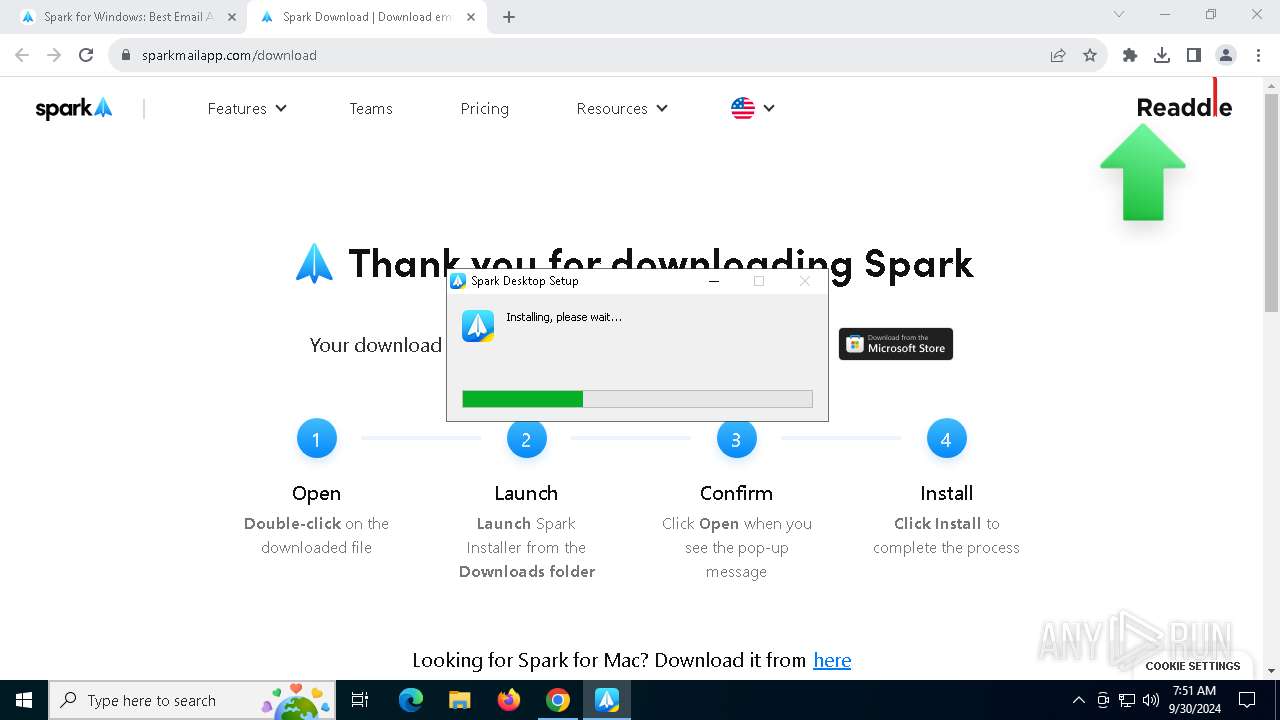
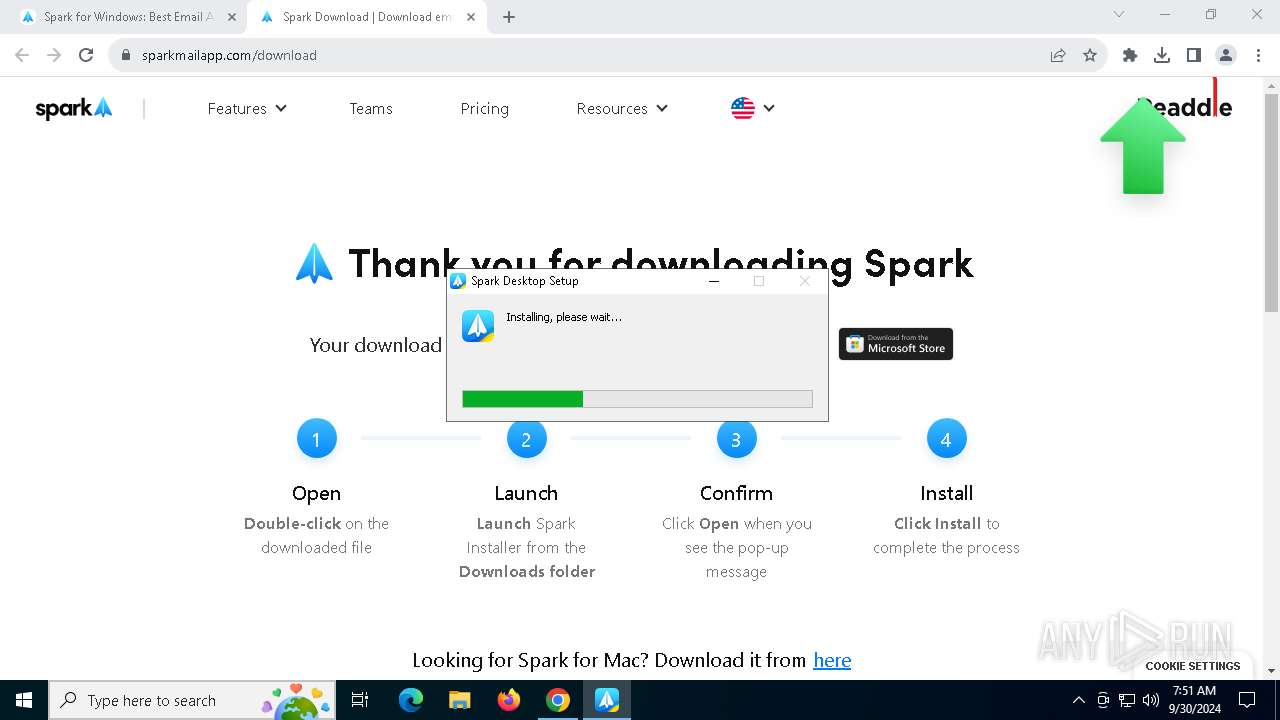
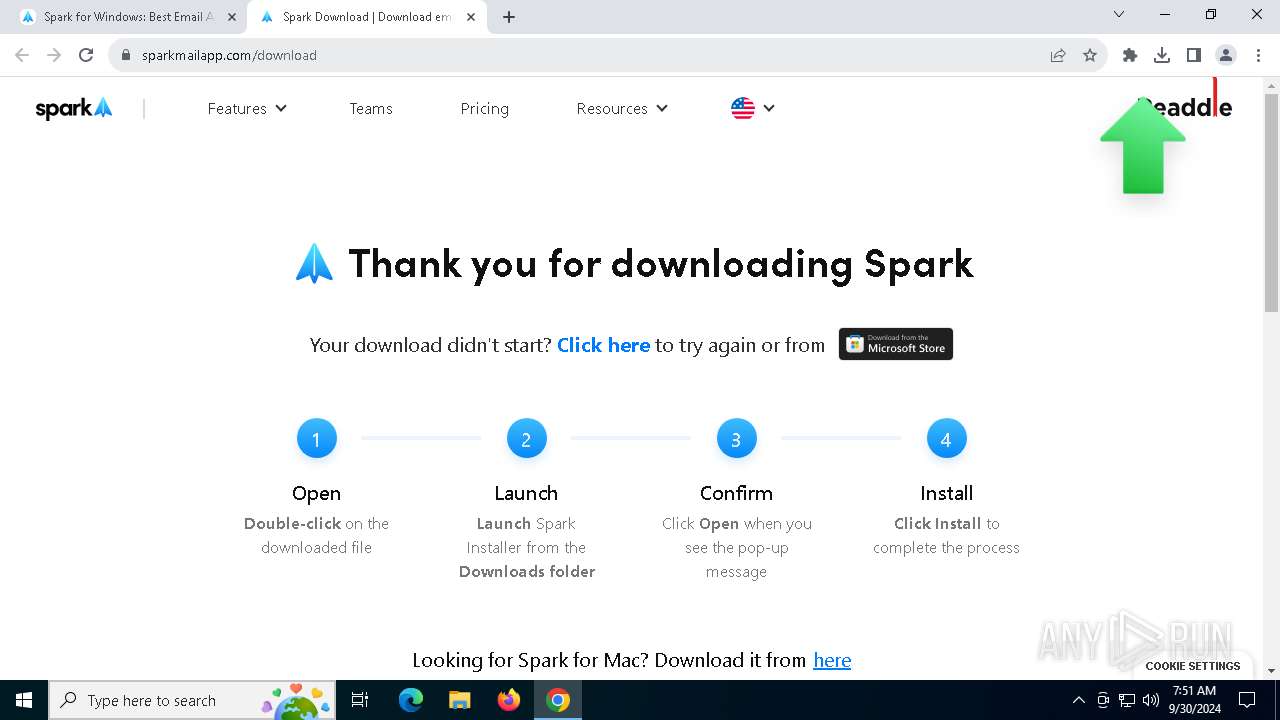
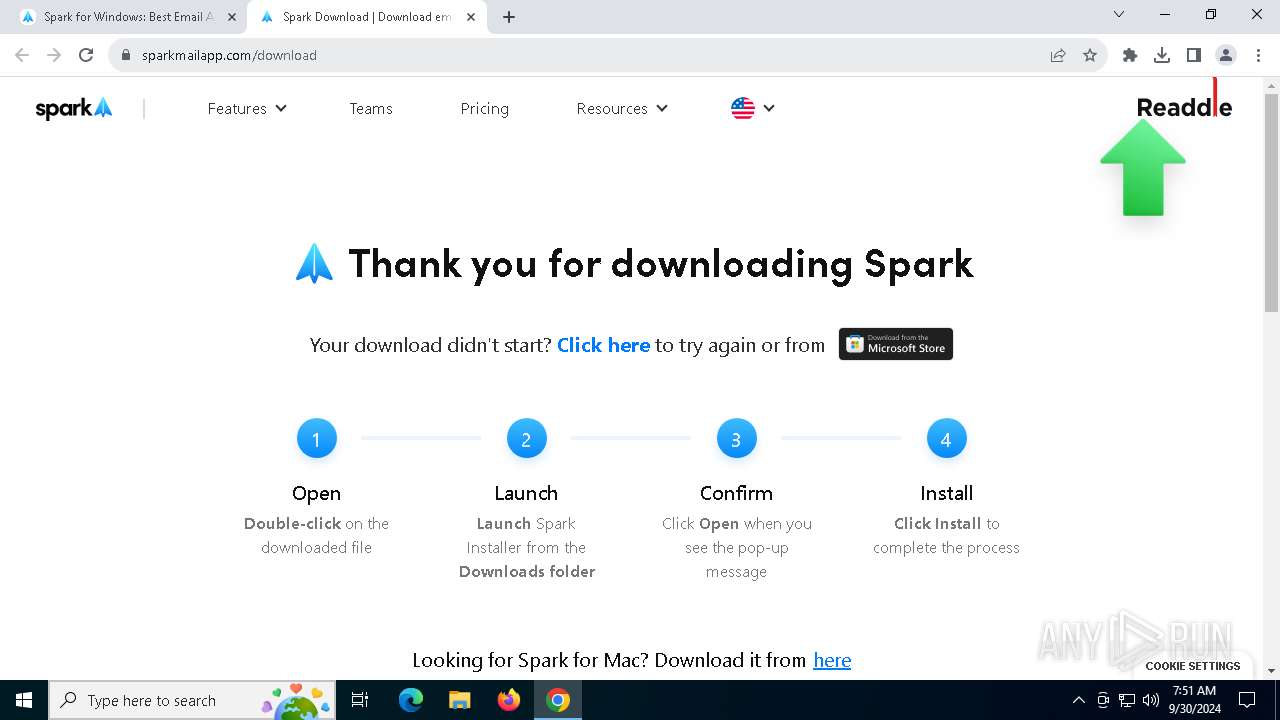
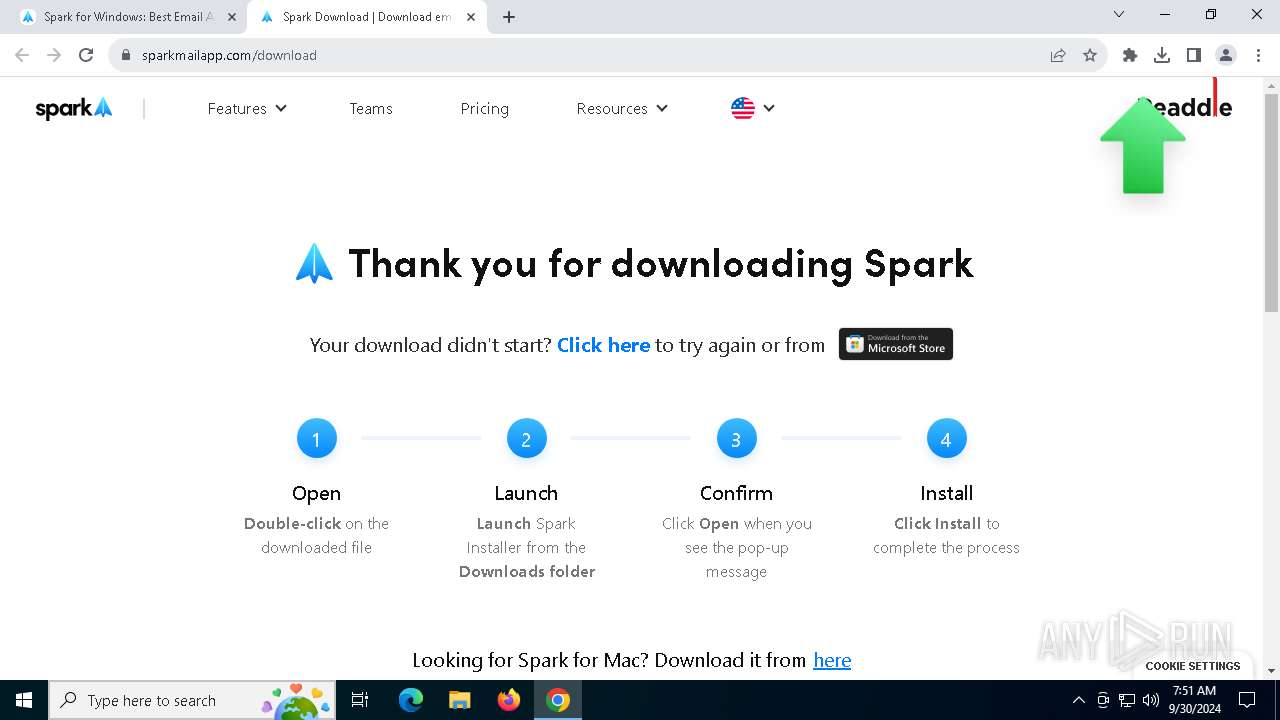
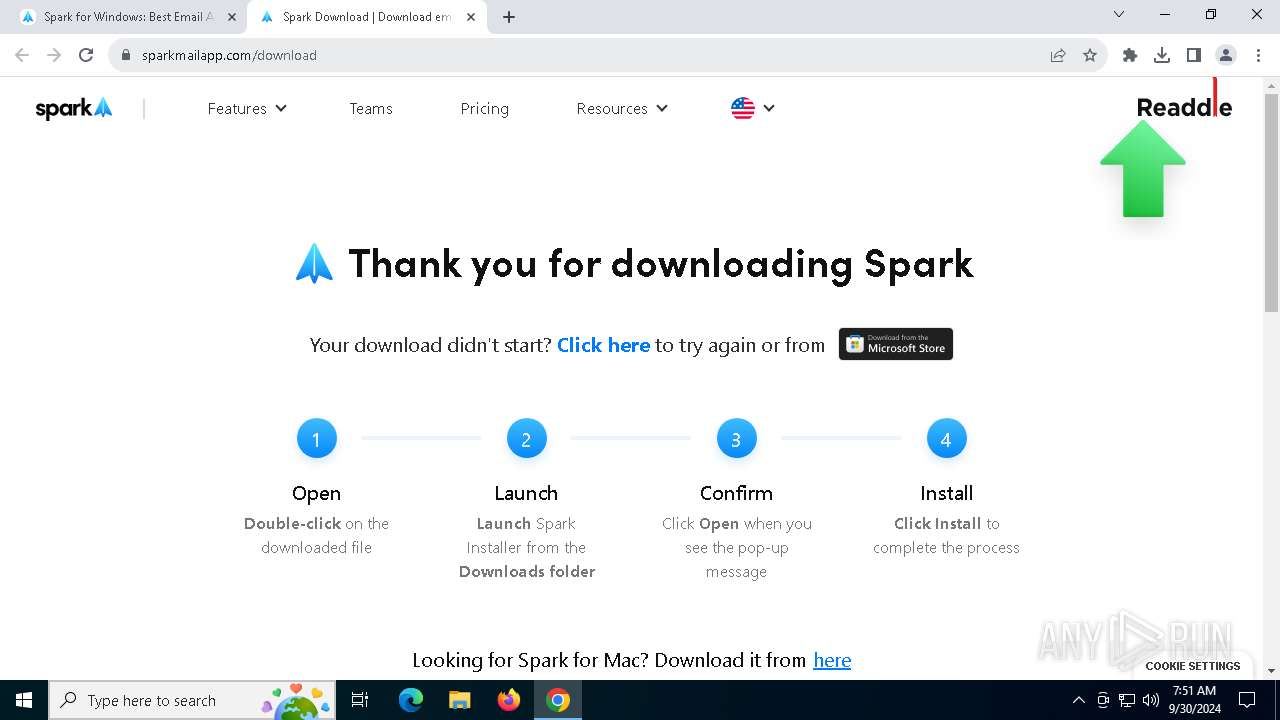
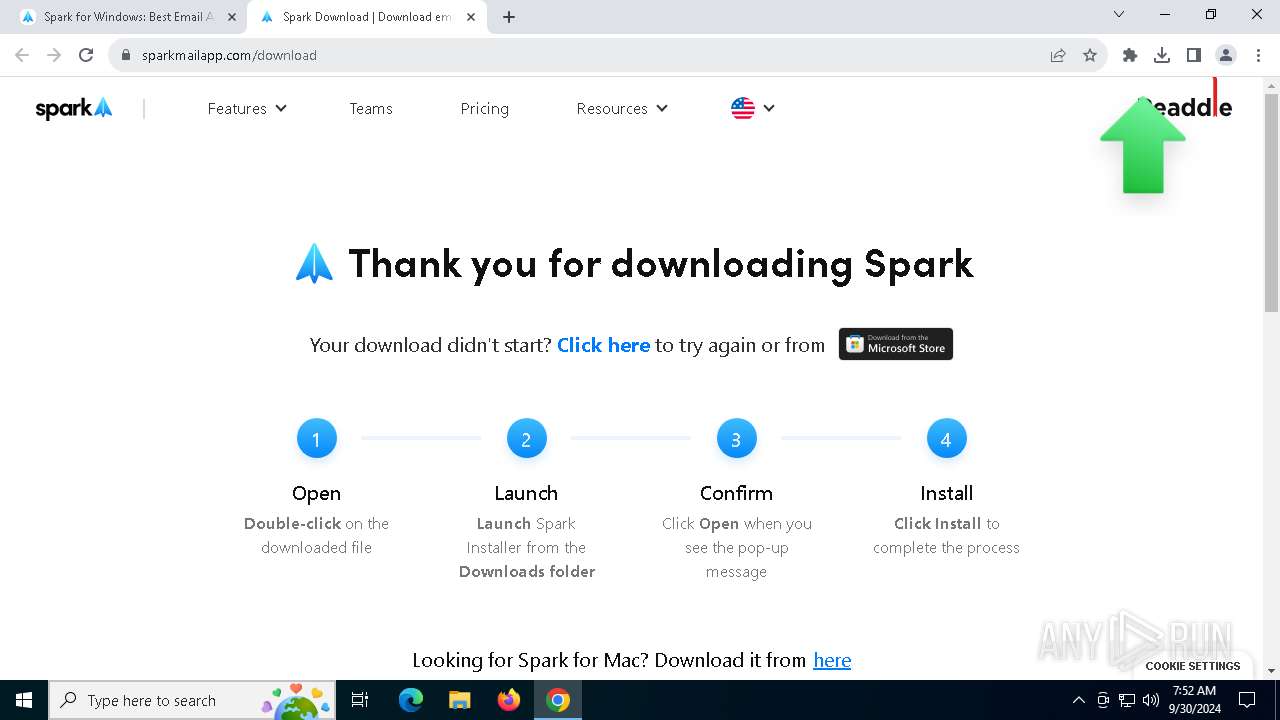
| URL: | https://sparkmailapp.com/source?from=signature |
| Full analysis: | https://app.any.run/tasks/dc4d943e-6f88-4cbe-988a-a0f1e00fc616 |
| Verdict: | Malicious activity |
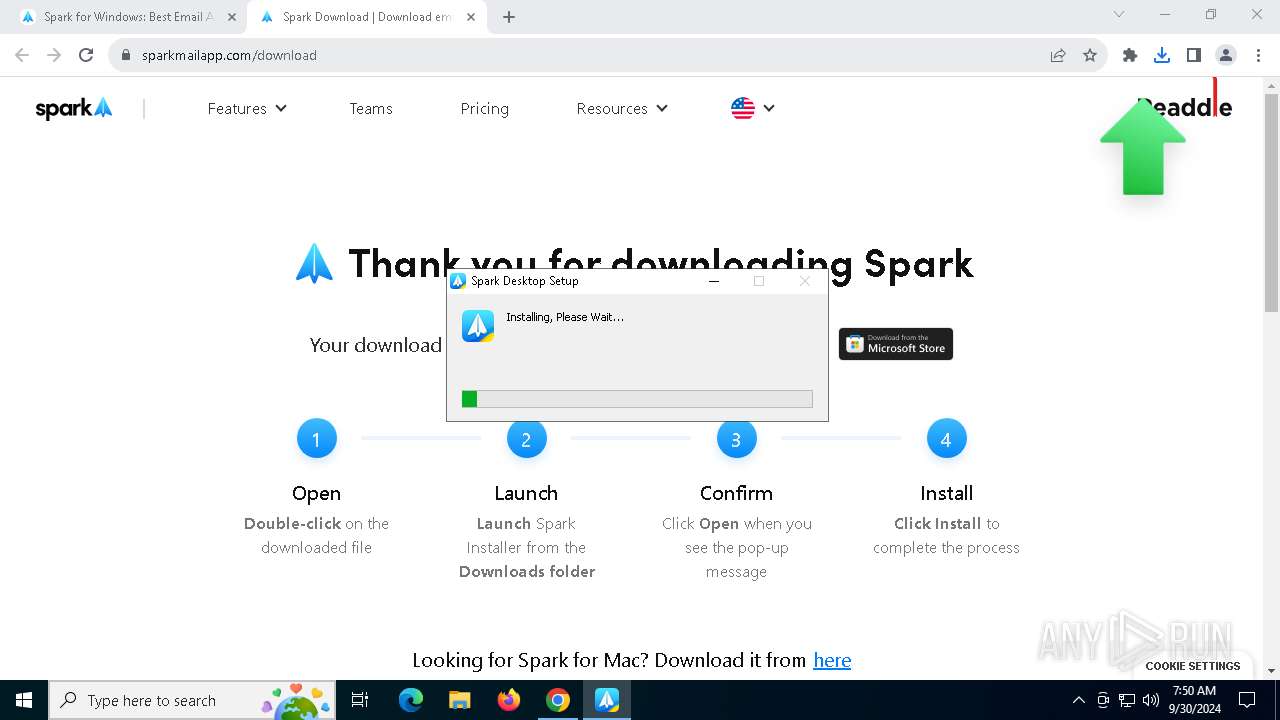
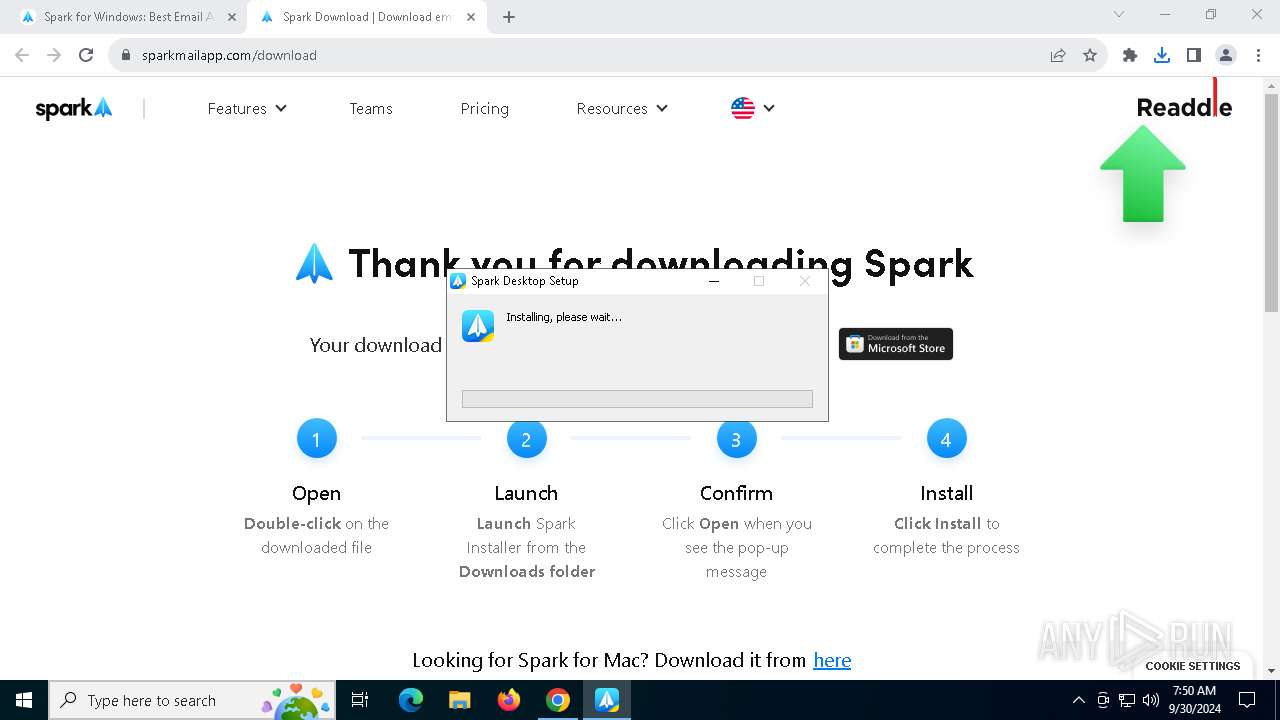
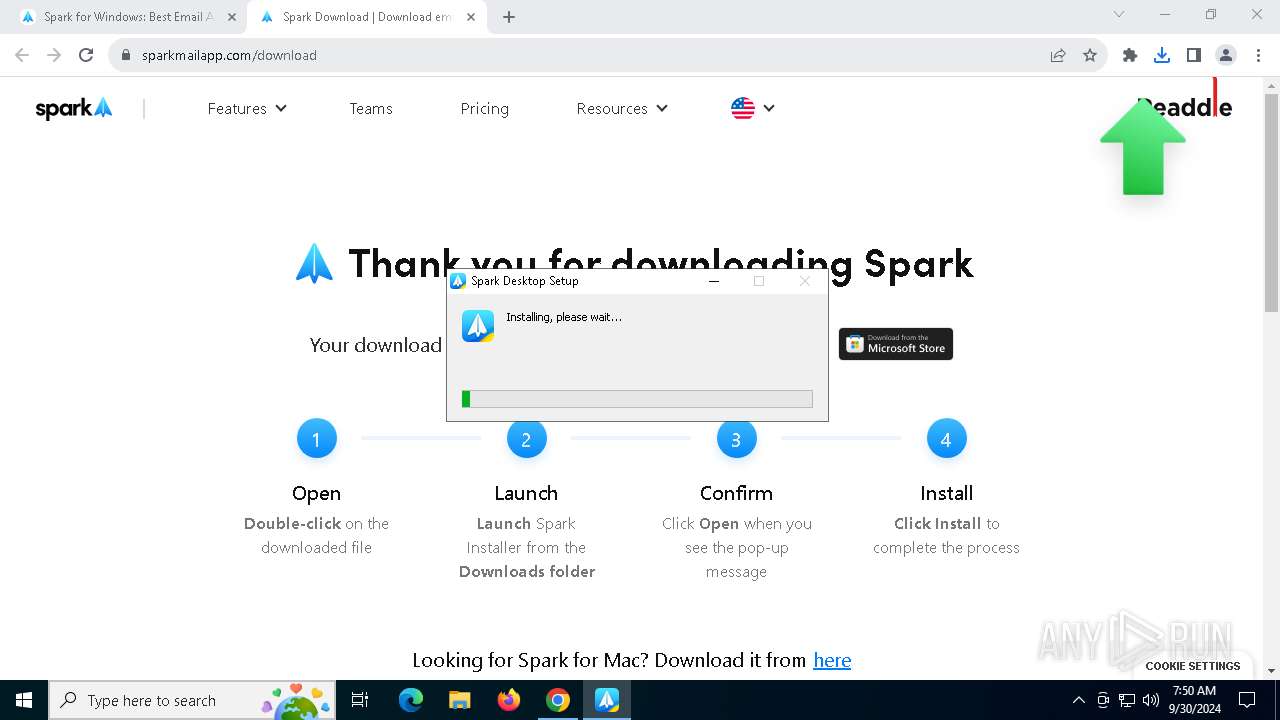
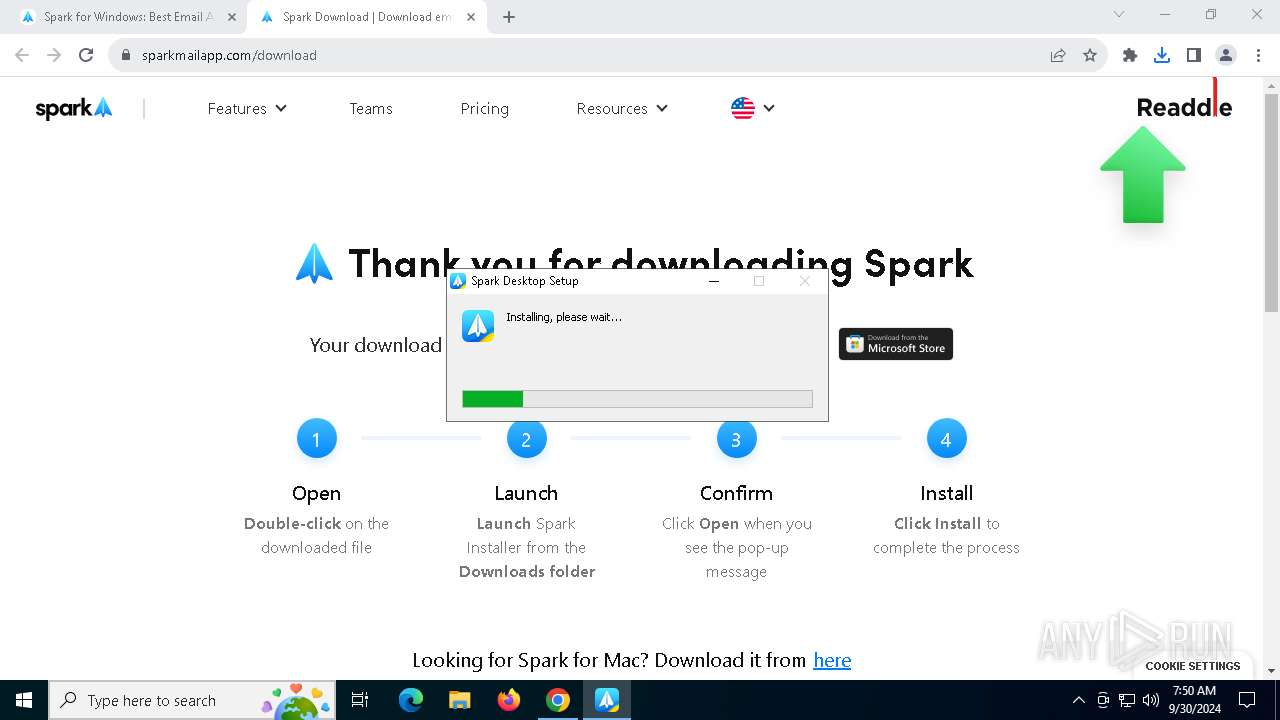
| Analysis date: | September 30, 2024, 07:47:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 48979847C69D775A96C1BAEEF0A2C5A2 |
| SHA1: | C3C9D6680F1D45683F5181ED041D65BDA330000B |
| SHA256: | 82CCA6F1F1E1B10F91DFD7D83D4C0560B2054DD389B67898D5D7DE4638A010FB |
| SSDEEP: | 3:N8YY6y8C6UlRQXAn:2Y1yh6UlRCAn |
MALICIOUS
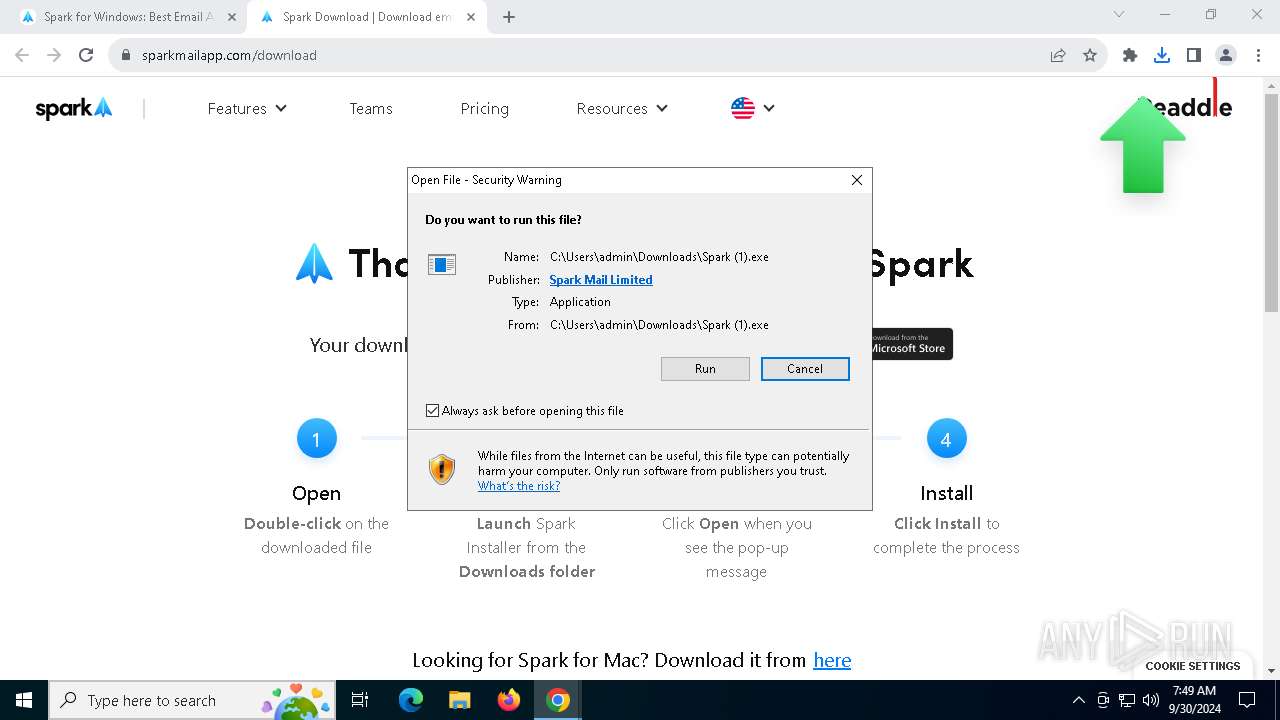
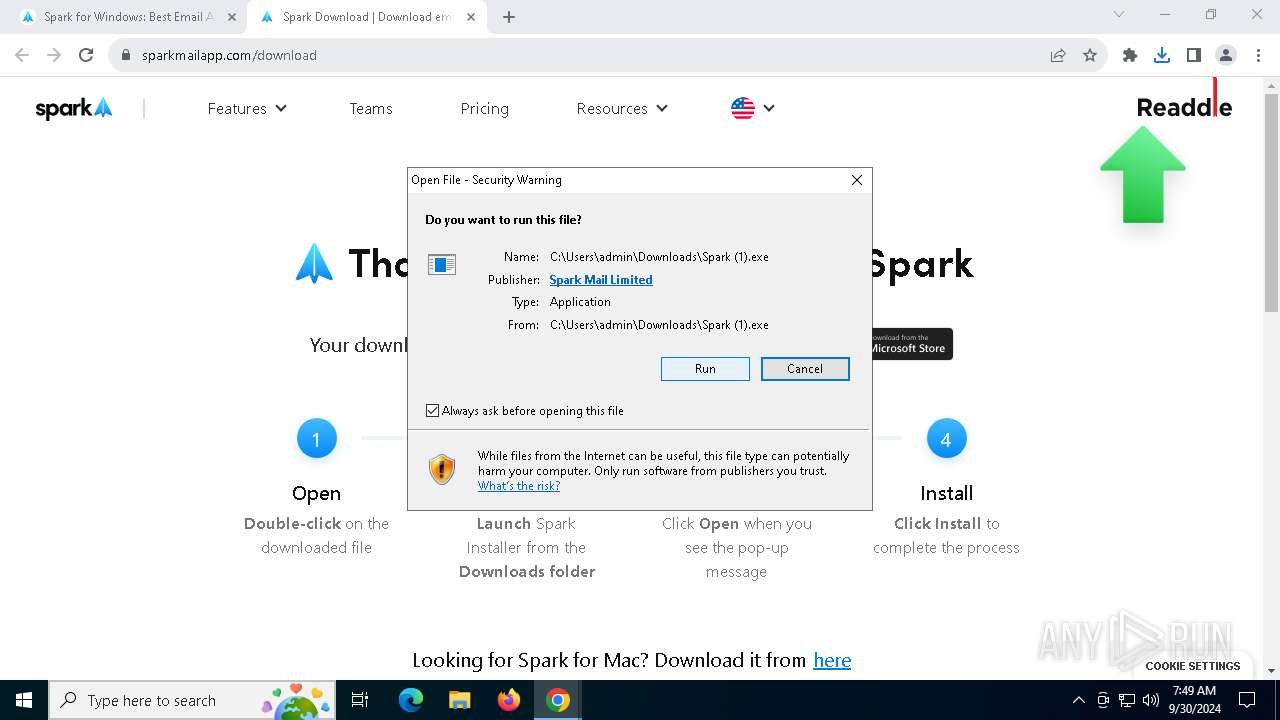
Changes powershell execution policy (Unrestricted)
- Spark Desktop.exe (PID: 68)
Bypass execution policy to execute commands
- powershell.exe (PID: 2956)
SUSPICIOUS
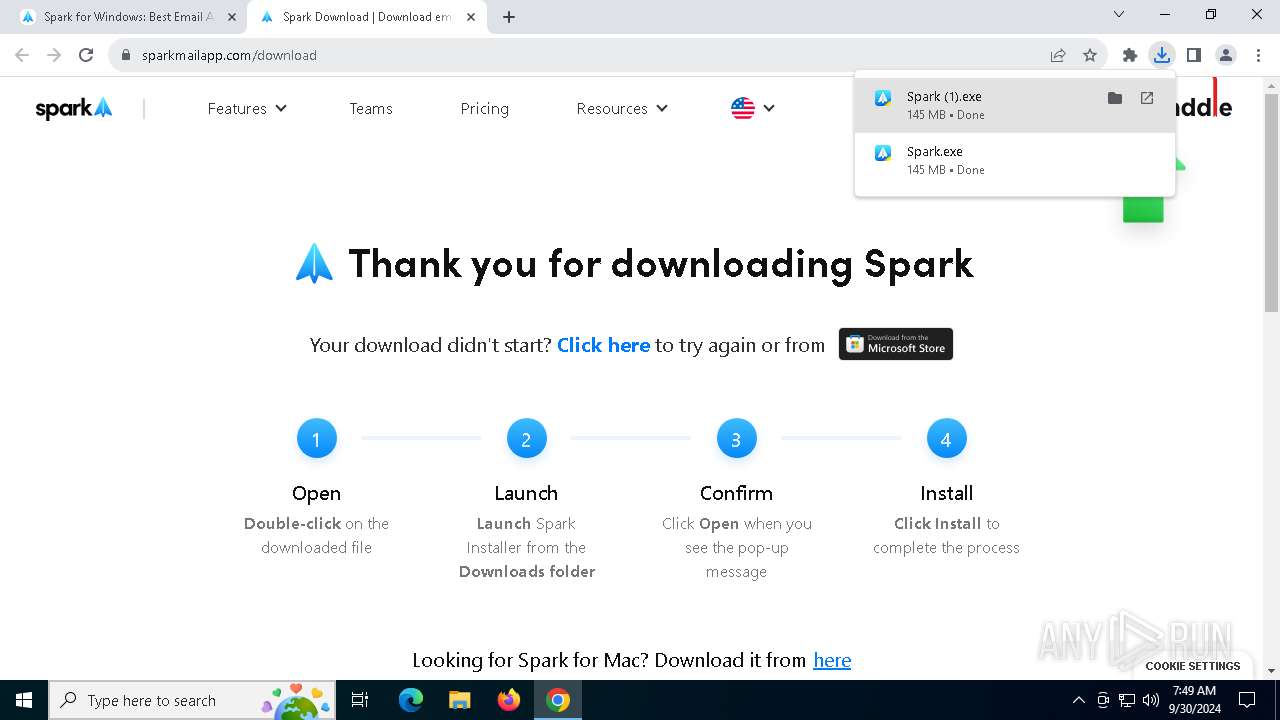
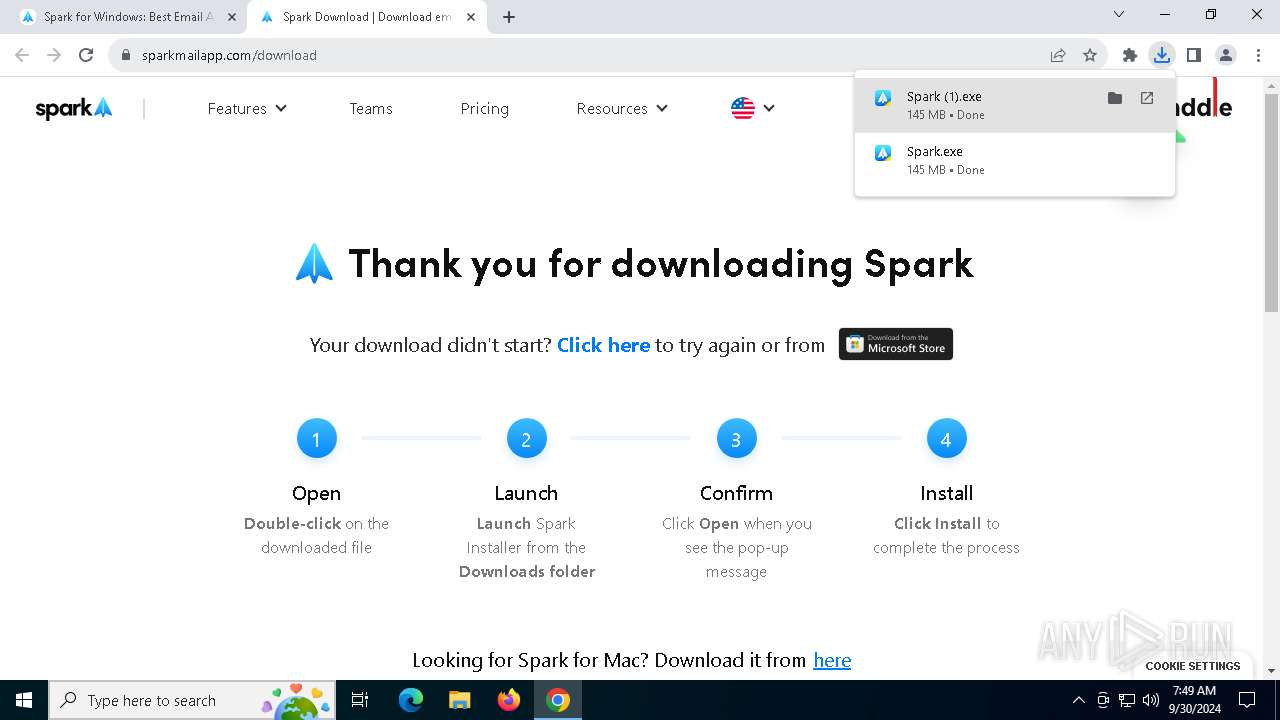
The process creates files with name similar to system file names
- Spark (1).exe (PID: 6088)
Executable content was dropped or overwritten
- Spark (1).exe (PID: 6088)
- Spark Desktop.exe (PID: 68)
Get information on the list of running processes
- cmd.exe (PID: 1728)
- Spark (1).exe (PID: 6088)
Starts CMD.EXE for commands execution
- Spark (1).exe (PID: 6088)
- Spark Desktop.exe (PID: 68)
Reads security settings of Internet Explorer
- Spark (1).exe (PID: 6088)
Creates a software uninstall entry
- Spark (1).exe (PID: 6088)
Starts application with an unusual extension
- cmd.exe (PID: 4040)
Application launched itself
- Spark Desktop.exe (PID: 68)
Base64-obfuscated command line is found
- Spark Desktop.exe (PID: 68)
The process hide an interactive prompt from the user
- Spark Desktop.exe (PID: 68)
BASE64 encoded PowerShell command has been detected
- Spark Desktop.exe (PID: 68)
The process bypasses the loading of PowerShell profile settings
- Spark Desktop.exe (PID: 68)
Starts POWERSHELL.EXE for commands execution
- Spark Desktop.exe (PID: 68)
The process hides Powershell's copyright startup banner
- Spark Desktop.exe (PID: 68)
INFO
The process uses the downloaded file
- chrome.exe (PID: 7228)
- chrome.exe (PID: 6204)
- chrome.exe (PID: 4780)
- Spark (1).exe (PID: 6088)
Executable content was dropped or overwritten
- chrome.exe (PID: 6204)
Checks supported languages
- Spark (1).exe (PID: 6088)
- Spark Desktop.exe (PID: 68)
- chcp.com (PID: 7352)
- Spark Desktop.exe (PID: 7692)
- Spark Desktop.exe (PID: 4316)
- Spark Desktop.exe (PID: 7300)
- Spark Desktop.exe (PID: 4024)
Reads the computer name
- Spark (1).exe (PID: 6088)
- Spark Desktop.exe (PID: 68)
- Spark Desktop.exe (PID: 4024)
- Spark Desktop.exe (PID: 7300)
Reads the software policy settings
- slui.exe (PID: 7468)
- slui.exe (PID: 1808)
Create files in a temporary directory
- Spark (1).exe (PID: 6088)
- Spark Desktop.exe (PID: 68)
Creates files or folders in the user directory
- Spark (1).exe (PID: 6088)
- Spark Desktop.exe (PID: 68)
- Spark Desktop.exe (PID: 7692)
Checks proxy server information
- slui.exe (PID: 1808)
- Spark Desktop.exe (PID: 68)
Application launched itself
- chrome.exe (PID: 6204)
- msedge.exe (PID: 7848)
Manual execution by a user
- Spark Desktop.exe (PID: 68)
Reads product name
- Spark Desktop.exe (PID: 68)
Reads Environment values
- Spark Desktop.exe (PID: 68)
Changes the display of characters in the console
- cmd.exe (PID: 4040)
Process checks computer location settings
- Spark Desktop.exe (PID: 68)
Reads CPU info
- Spark Desktop.exe (PID: 68)
Reads the machine GUID from the registry
- Spark Desktop.exe (PID: 68)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6376)
- powershell.exe (PID: 1244)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
264
Monitored processes
117
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | "C:\Users\admin\AppData\Local\Programs\SparkDesktop\Spark Desktop.exe" | C:\Users\admin\AppData\Local\Programs\SparkDesktop\Spark Desktop.exe | explorer.exe | ||||||||||||
User: admin Company: Spark Mail Limited Integrity Level: MEDIUM Description: Spark Desktop Version: 3.17.8.85592 Modules
| |||||||||||||||
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6116 --field-trial-handle=1888,i,10833146573835854326,16404267105243433780,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 640 | powershell.exe -NoLogo -NoProfile -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Spark Desktop.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7fffd3efdc40,0x7fffd3efdc4c,0x7fffd3efdc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7620 --field-trial-handle=2336,i,12891226755558723007,3088670389493308991,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2468 --field-trial-handle=2336,i,12891226755558723007,3088670389493308991,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1244 | powershell.exe -NoLogo -NoProfile -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Spark Desktop.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5632 --field-trial-handle=1888,i,10833146573835854326,16404267105243433780,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1448 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
110 053
Read events
109 940
Write events
80
Delete events
33
Modification events
| (PID) Process: | (6204) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6204) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6204) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6204) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6204) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6204) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (6204) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (6204) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (6204) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (6204) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
484
Suspicious files
409
Text files
140
Unknown types
293
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF3f878c.TMP | — | |
MD5:— | SHA256:— | |||
| 6204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF3f87ac.TMP | — | |
MD5:— | SHA256:— | |||
| 6204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF3f878c.TMP | — | |
MD5:— | SHA256:— | |||
| 6204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF3f87ac.TMP | — | |
MD5:— | SHA256:— | |||
| 6204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF3f87ea.TMP | — | |
MD5:— | SHA256:— | |||
| 6204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
153
DNS requests
157
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1020 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2980 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7488 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1124 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
7488 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6412 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1124 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
1124 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
1124 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
1124 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1020 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2980 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2980 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2424 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
6204 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3076 | chrome.exe | 76.223.92.135:443 | sparkmailapp.com | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
sparkmailapp.com |
| whitelisted |
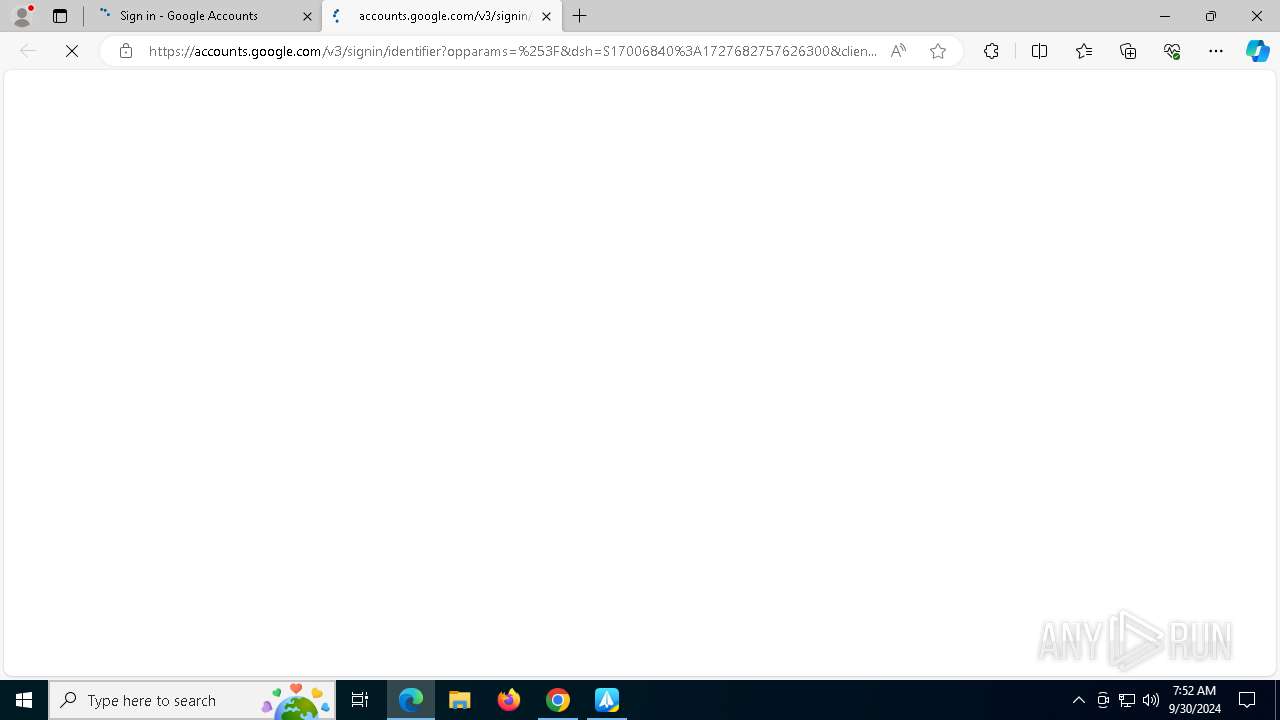
accounts.google.com |
| whitelisted |
geo.cookie-script.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7300 | Spark Desktop.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7300 | Spark Desktop.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |