| File name: | map quest.exe |
| Full analysis: | https://app.any.run/tasks/857340e3-887c-41a5-ab24-f322f00e7c96 |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 16:07:50 |
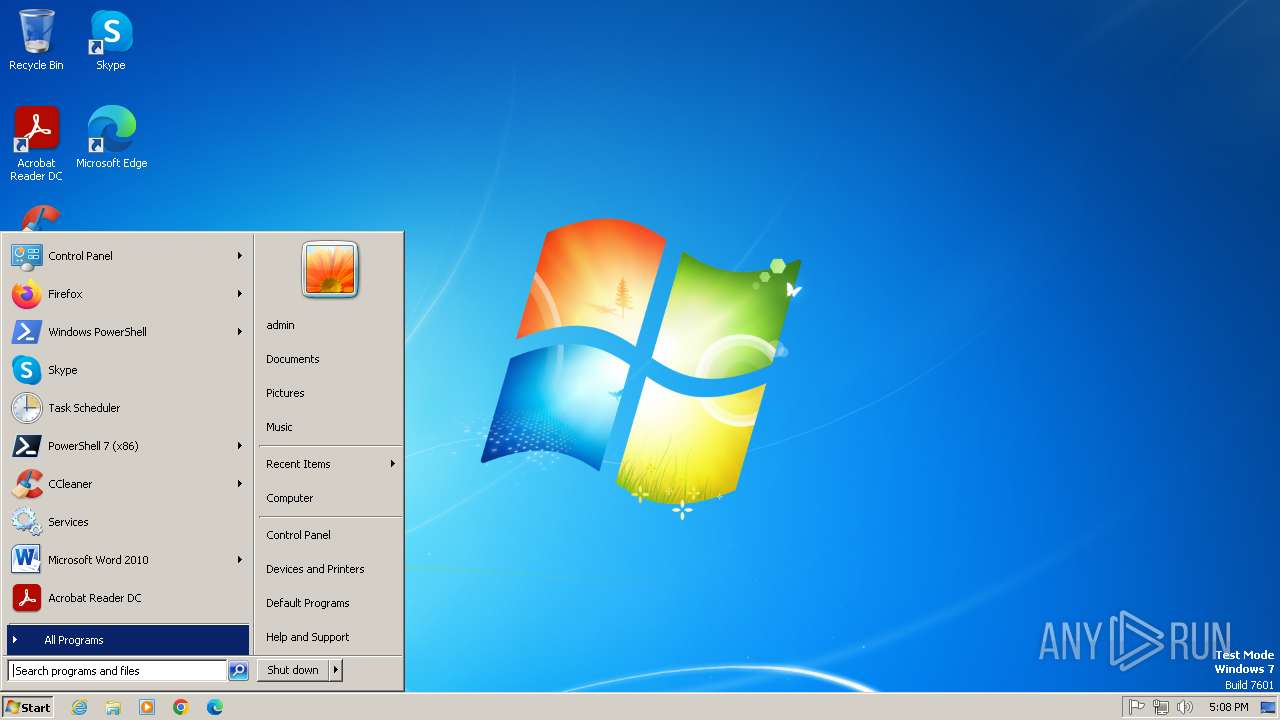
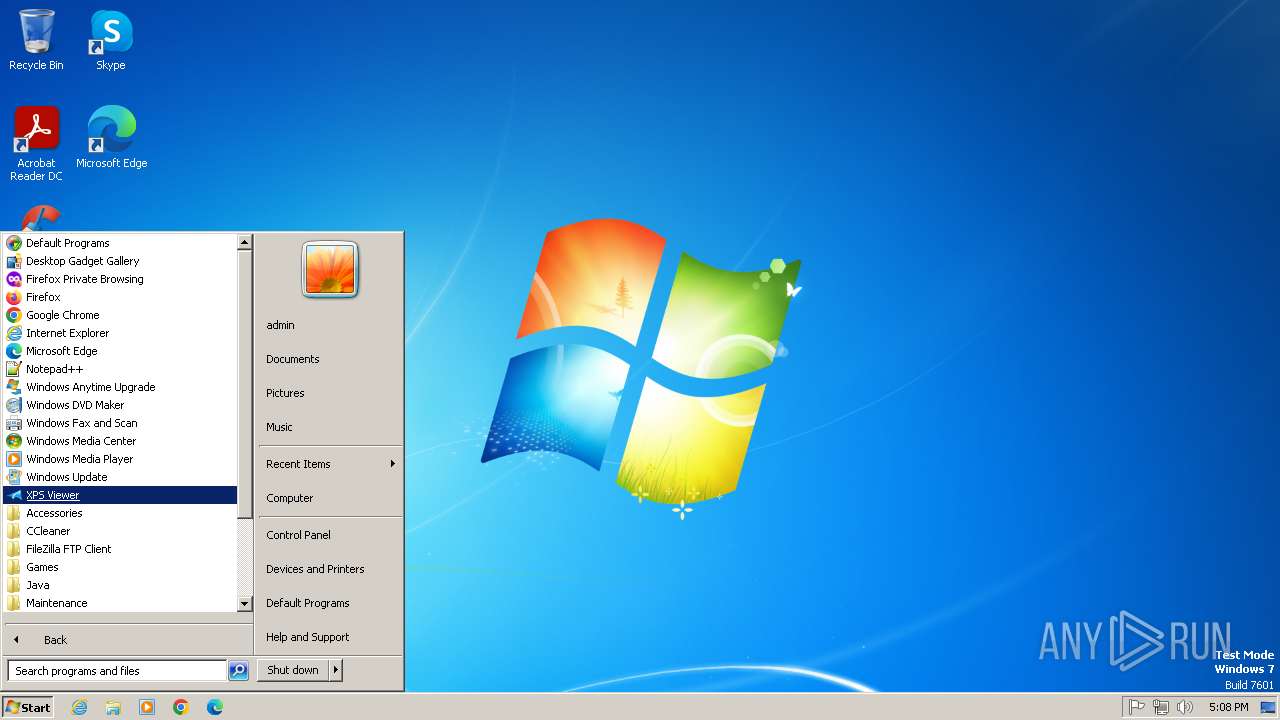
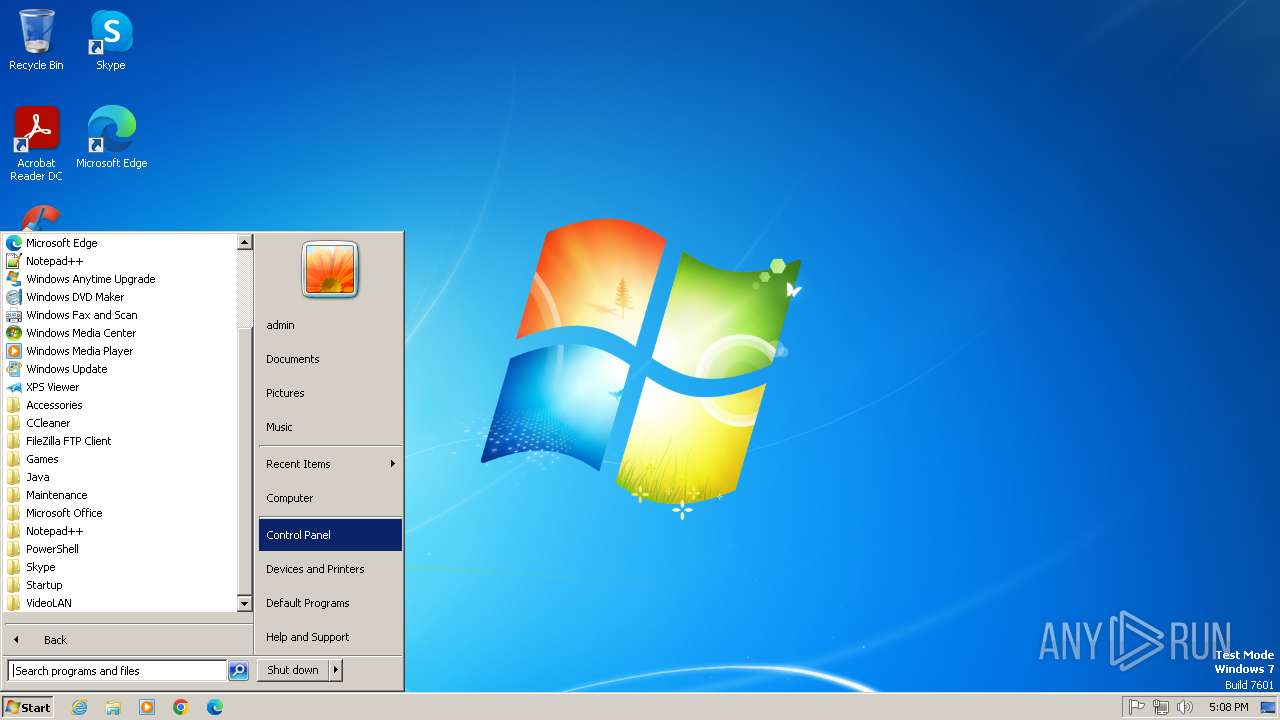
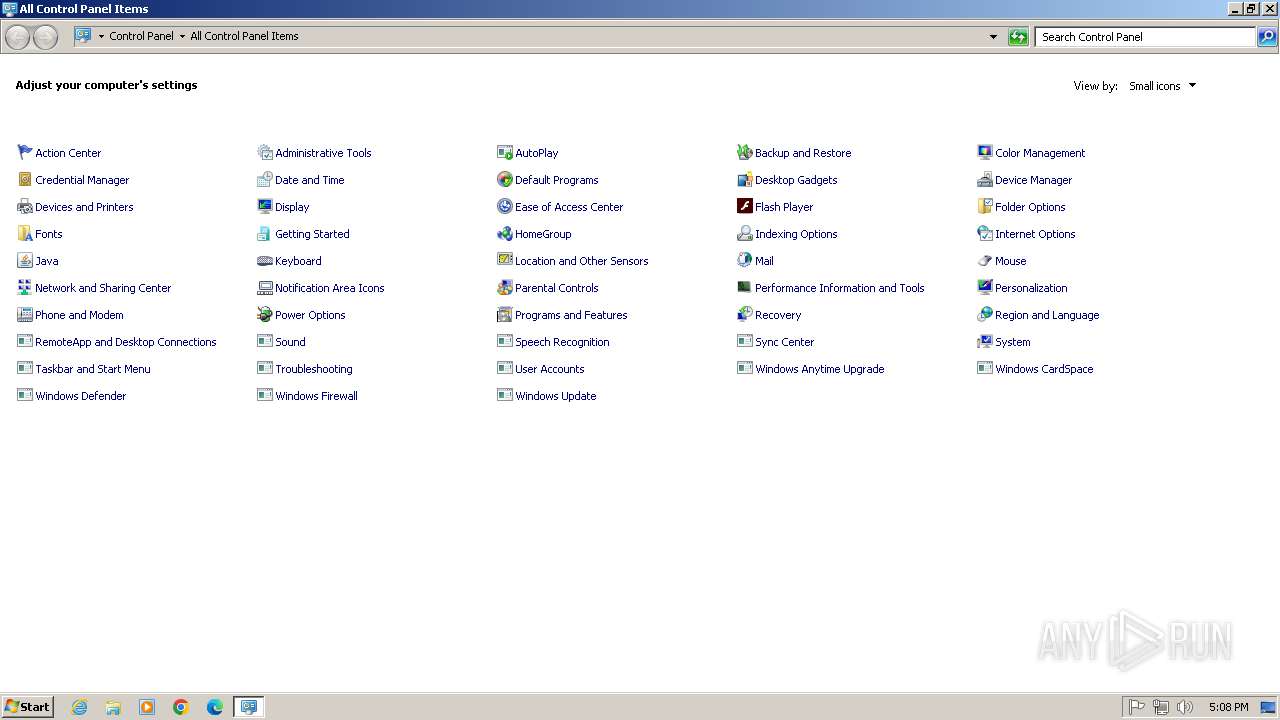
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 56FA0311FEB368E85EE3946187D830E1 |
| SHA1: | 3E481B45962930B89C593EE67961D11491D30294 |
| SHA256: | 82C4D790E66772F86D7918BAAAB590FFFDEC380A6FC6715221F9672E6A3CF320 |
| SSDEEP: | 12288:jGrZqj4G/ujrDi352I6KrkvRmZiyl7IN:jGrZqj4G/uj/i352ItrkvR4f7I |
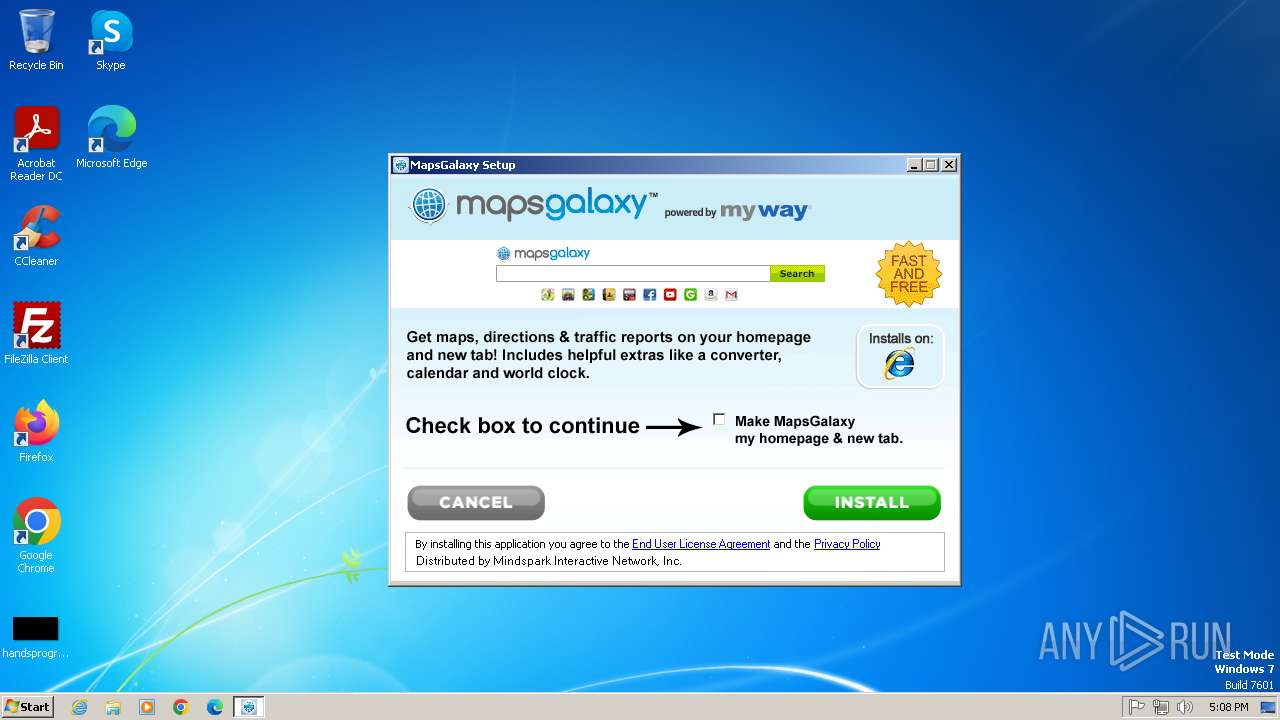
MALICIOUS
Executing a file with an untrusted certificate
- map quest.exe (PID: 3516)
SUSPICIOUS
The process creates files with name similar to system file names
- map quest.exe (PID: 3516)
Malware-specific behavior (creating "System.dll" in Temp)
- map quest.exe (PID: 3516)
Reads the Internet Settings
- map quest.exe (PID: 3516)
Reads security settings of Internet Explorer
- map quest.exe (PID: 3516)
Executable content was dropped or overwritten
- map quest.exe (PID: 3516)
Reads settings of System Certificates
- map quest.exe (PID: 3516)
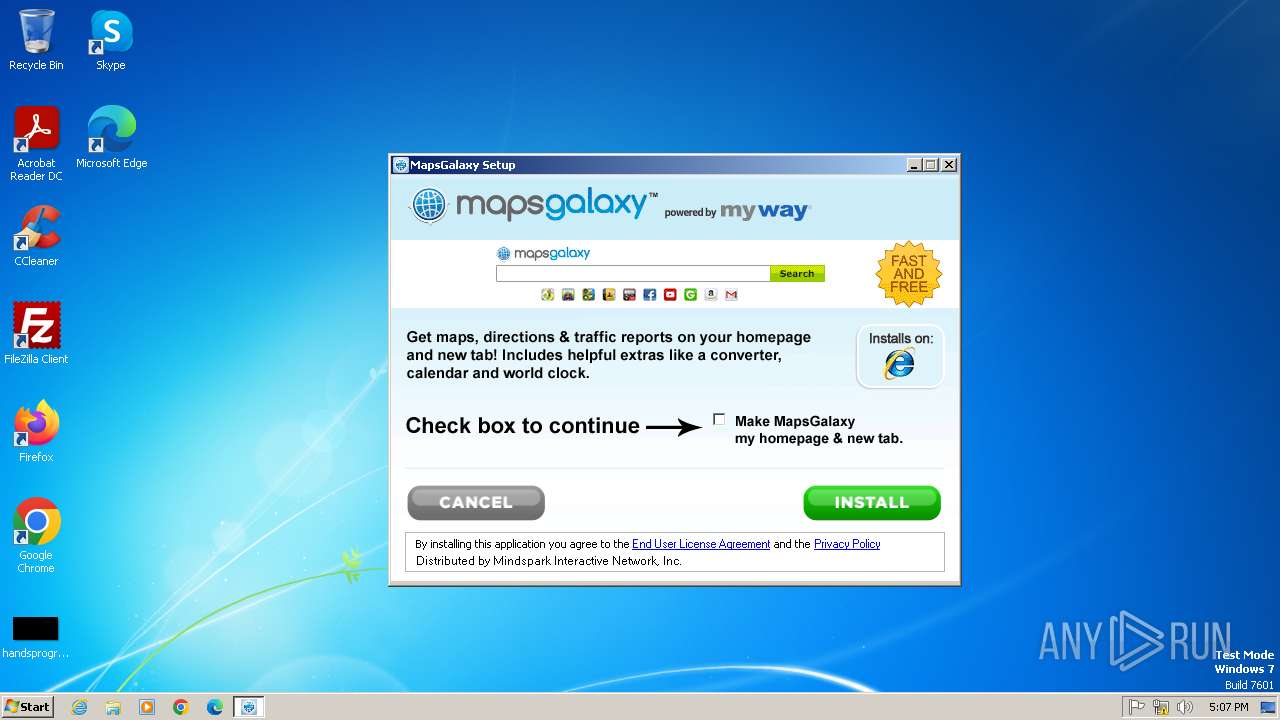
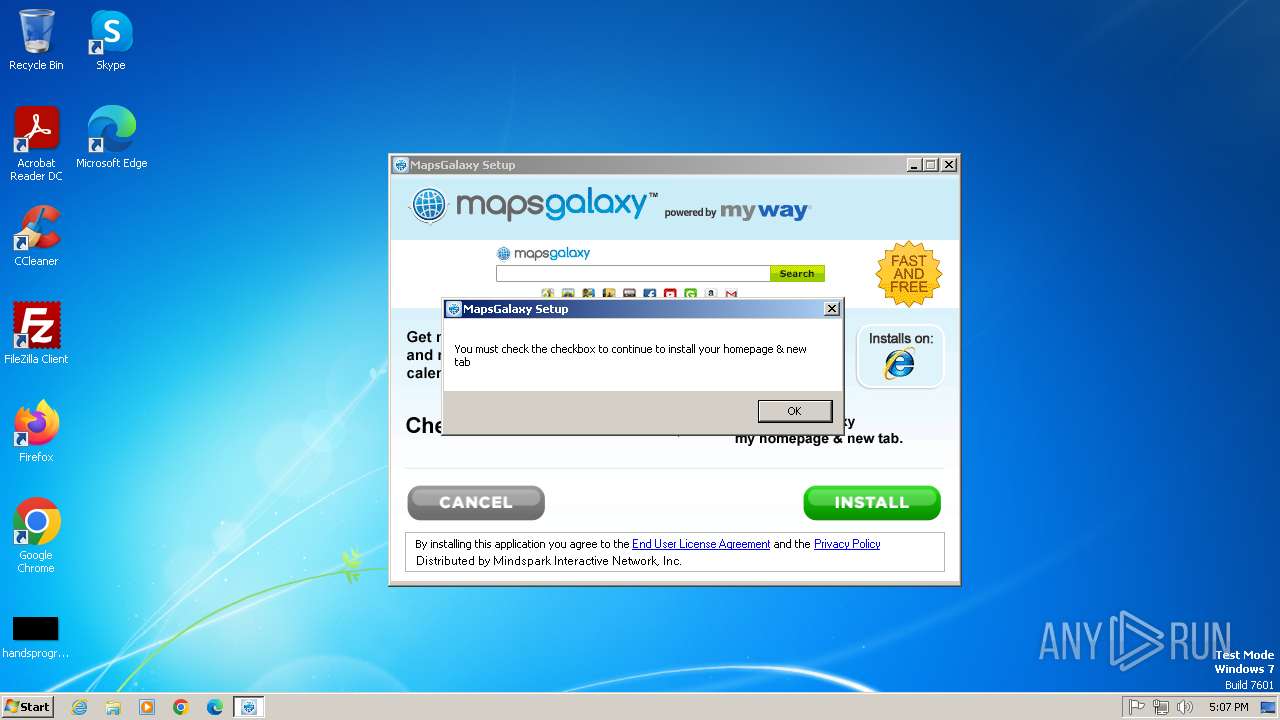
Creates a software uninstall entry
- map quest.exe (PID: 3516)
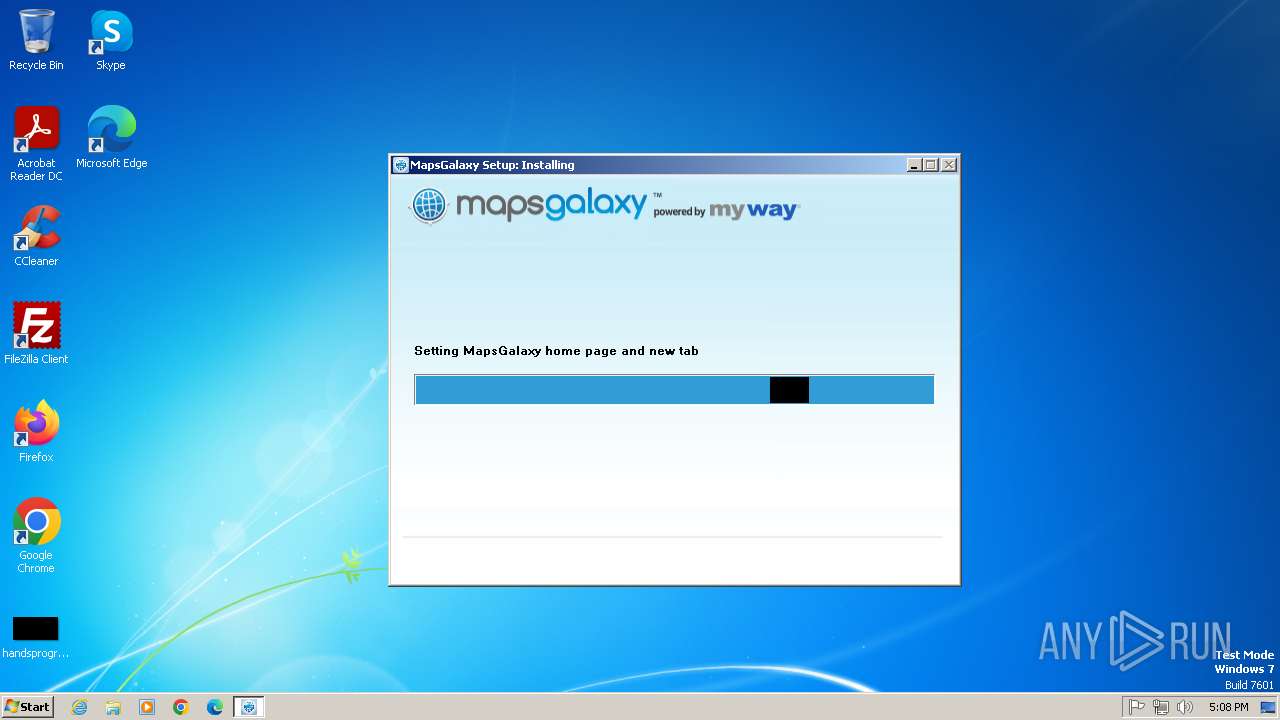
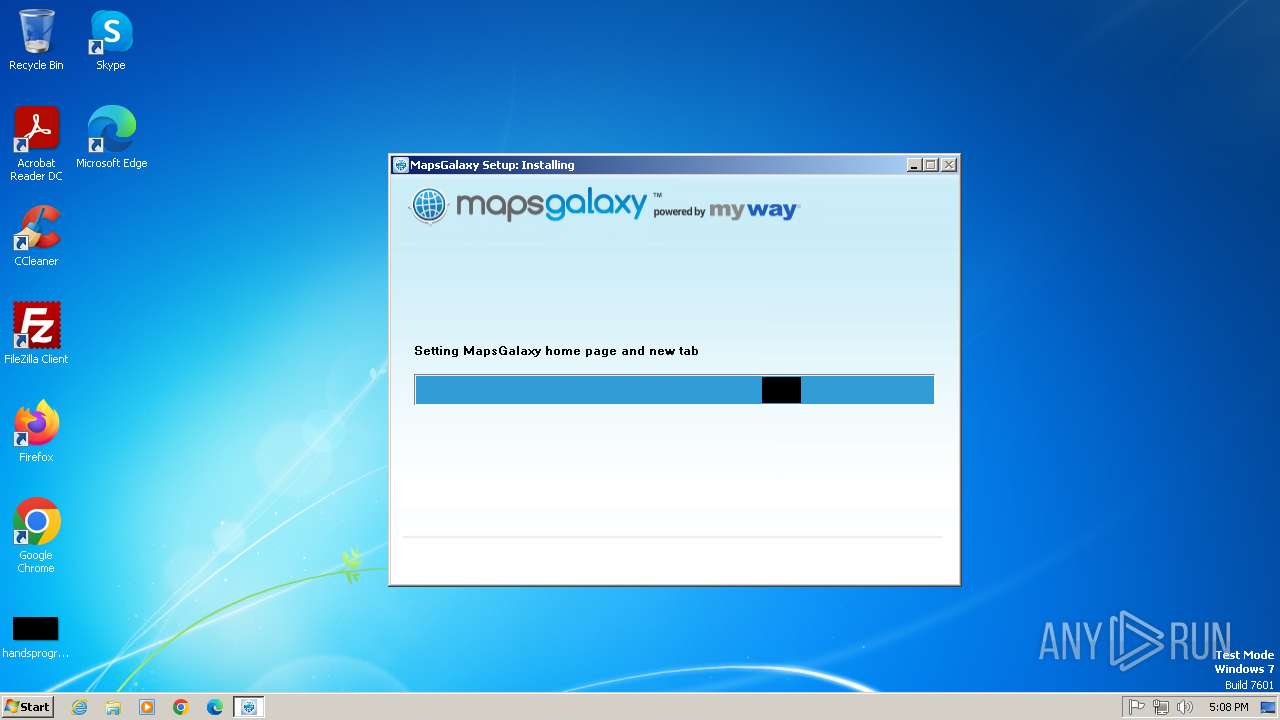
Changes the Home page of Internet Explorer
- map quest.exe (PID: 3516)
Changes the title of the Internet Explorer window
- map quest.exe (PID: 3516)
INFO
Checks supported languages
- map quest.exe (PID: 3516)
The sample compiled with english language support
- map quest.exe (PID: 3516)
Reads the computer name
- map quest.exe (PID: 3516)
Checks proxy server information
- map quest.exe (PID: 3516)
Reads the machine GUID from the registry
- map quest.exe (PID: 3516)
Create files in a temporary directory
- map quest.exe (PID: 3516)
Reads the software policy settings
- map quest.exe (PID: 3516)
Creates files or folders in the user directory
- map quest.exe (PID: 3516)
Application launched itself
- iexplore.exe (PID: 2592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 05:01:44+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3229 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.1.8 |
| ProductVersionNumber: | 2.0.1.8 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | http://www.mindspark.com/ |
| CompanyName: | Mindspark Interactive Network, Inc. |
| FileDescription: | MapsGalaxy Setup |
| FileVersion: | 2.0.1.8 |
| InternalName: | MapsGalaxy |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | MapsGalaxy |
| ProductVersion: | 2.0.1.8 |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2592 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
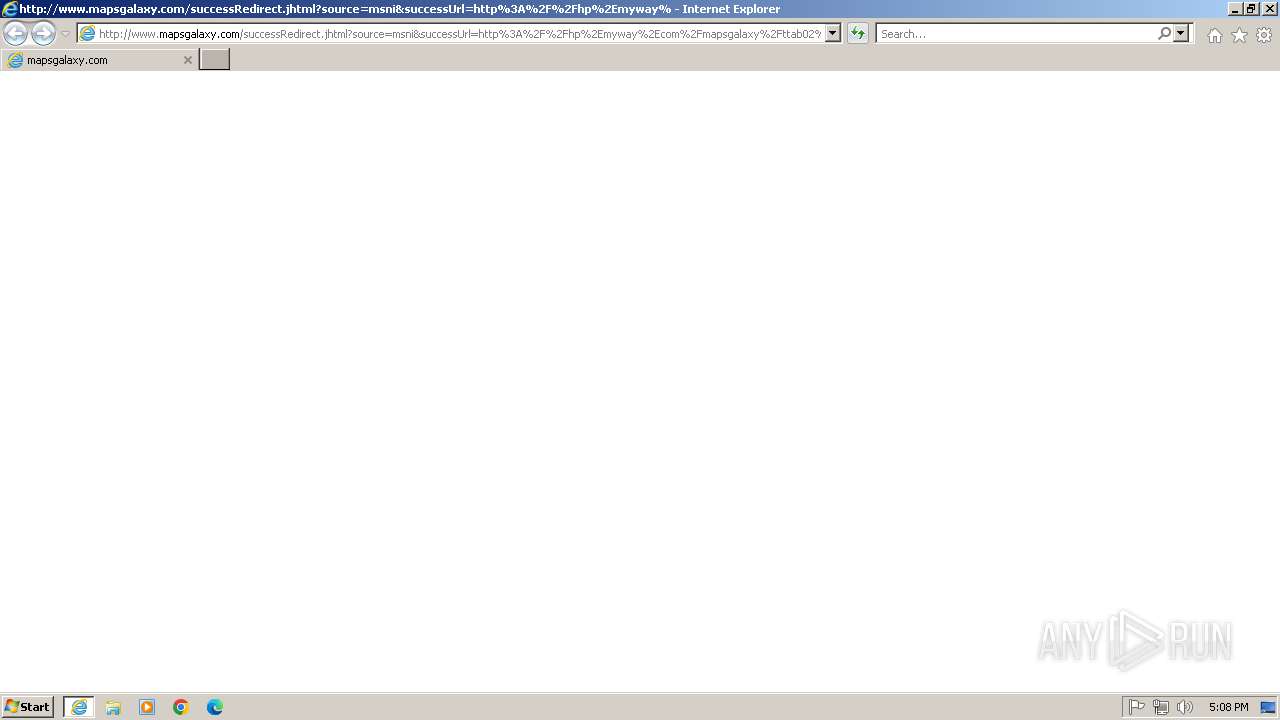
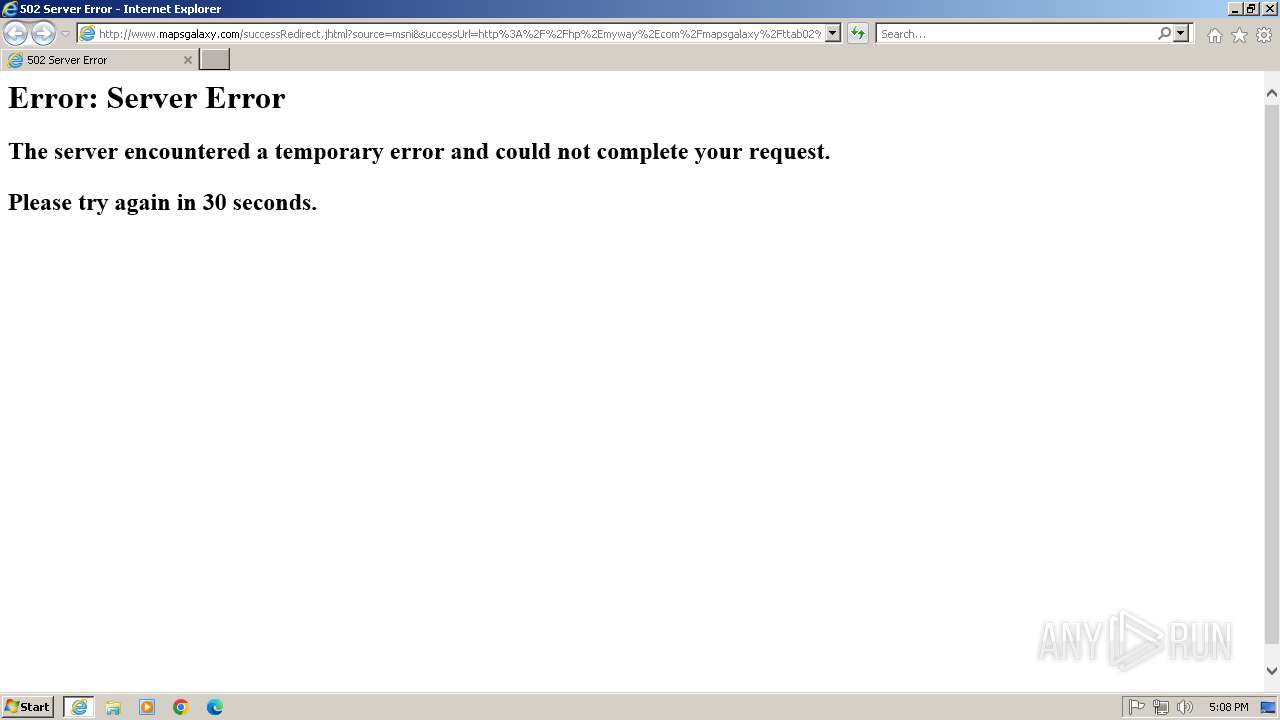
| 2592 | "C:\Program Files\Internet Explorer\iexplore.exe"-noframemerging http://www.mapsgalaxy.com/successRedirect.jhtml?source=msni&successUrl=http%3A%2F%2Fhp%2Emyway%2Ecom%2Fmapsgalaxy%2Fttab02%2Findex%2Ehtml%3Fn%3D78B3D389%26p2%3D%5EUX%5Emni000%5ES16724%26ptb%3D6598D413-639C-4C49-AC3B-CFD8498EAF66&pixelUrl=&coId=0099c47eaf3848d2925ecacb813e3d0f | C:\Program Files\Internet Explorer\iexplore.exe | map quest.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2732 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3516 | "C:\Users\admin\AppData\Local\Temp\map quest.exe" | C:\Users\admin\AppData\Local\Temp\map quest.exe | explorer.exe | ||||||||||||
User: admin Company: Mindspark Interactive Network, Inc. Integrity Level: MEDIUM Description: MapsGalaxy Setup Exit code: 0 Version: 2.0.1.8 Modules
| |||||||||||||||
Total events
16 774
Read events
16 610
Write events
129
Delete events
35
Modification events
| (PID) Process: | (3516) map quest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3516) map quest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3516) map quest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3516) map quest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3516) map quest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (3516) map quest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005F010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3516) map quest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3516) map quest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3516) map quest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3516) map quest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
20
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3516 | map quest.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:E192462F281446B5D1500D474FBACC4B | SHA256:F1BA9F1B63C447682EBF9DE956D0DA2A027B1B779ABEF9522D347D3479139A60 | |||
| 3516 | map quest.exe | C:\Users\admin\AppData\Local\Temp\nsc12B9.tmp\cancel_english_mip_1435256870179.bmp | image | |
MD5:12845D5CC068D0A6942889845974AA16 | SHA256:342CFBBA0DC6B853801FC14B6FE529A242A19A8031956BC9569643F07BB004EC | |||
| 3516 | map quest.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:E9E9804E84E9B48A07A64B64FF963B36 | SHA256:0A4A0DACE3018C7124DCAB402273AD8C24B58E8E9DACA99150B46BCB6CFB09AB | |||
| 3516 | map quest.exe | C:\Users\admin\AppData\Local\Temp\nsc12B9.tmp\nsDialogs.dll | executable | |
MD5:CA3C8F401A0F18EF00252A9FEA9F519B | SHA256:F17D39DEFDD44EAB1EA290B22D13D21DE796C0525D51F9D3F54101379A5A327F | |||
| 3516 | map quest.exe | C:\Users\admin\AppData\Local\Temp\nsc12B9.tmp\MapsGalaxy_Install_v2_1460753458927.bmp | image | |
MD5:CB6C62285D599EE4CBD45460A1BB1276 | SHA256:09338C12ADC9673209053FCF2E70652244809529D36527804DE20237E8BB931B | |||
| 3516 | map quest.exe | C:\Users\admin\AppData\Local\Temp\nsc12B9.tmp\Install_ENG_1435256864492.bmp | image | |
MD5:7078777F775A58435028C19515955085 | SHA256:DF2BD2E2781DAA4D3270FF3BAC2CFAE49FCB42E2A331D10F4F0CBDA2E3B1DDDC | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:639966AEB1B99CBC1FA7ADF9DC40D764 | SHA256:43AB31265491D730C7A814AAC12E8F1690B0FCFBF647536EC93F2149F7C8E1F2 | |||
| 3516 | map quest.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\533CCFF0437D1D3E95E8BB3FEF7317D7 | binary | |
MD5:3F7012E32F0EC252200C0802B29ACC36 | SHA256:63D0AA81131D3402E850A6199A9714ECD2EFBD5E987D42F242034C7E5EFE0448 | |||
| 3516 | map quest.exe | C:\Users\admin\AppData\Local\Temp\nsc12B9.tmp\MIP-mg-03_1458243534779.bmp | image | |
MD5:505AA82BBB520A50D3559DBFDE442EFA | SHA256:07A43ED10E9B2DDCFCF3BB58798D8F317A210143C3B604E69C7BB738970526AF | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
20
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3516 | map quest.exe | GET | 204 | 34.120.232.229:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=Error&errorCode=-16&errorType=nsisError&errorDetails=&platform=vicinio&anxv=2.0.1.8&anxd=2016-05-09&coid=&refPartner=^UX^mni000^S16724&refSub=&anxl=en-US&anxr=2135380452&refCobrand=UX&refCampaign=mni000&refTrack=S16724&refCountry= | unknown | — | — | whitelisted |
3516 | map quest.exe | GET | 204 | 34.120.232.229:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=Error&errorCode=-8&errorType=nsisError&errorDetails=map+quest%2Eexe&platform=vicinio&anxv=2.0.1.8&anxd=2016-05-09&coid=0099c47eaf3848d2925ecacb813e3d0f&refPartner=^UX^mni000^S16724&refSub=&anxl=en-US&anxr=-2107028427&refCobrand=UX&refCampaign=mni000&refTrack=S16724&refCountry= | unknown | — | — | whitelisted |
3516 | map quest.exe | GET | 200 | 2.16.168.117:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgTTSt7lL2v29yQRdfENzOFX9A%3D%3D | unknown | — | — | whitelisted |
3516 | map quest.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
3516 | map quest.exe | GET | 200 | 208.89.74.31:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7befe23c3d9081d6 | unknown | — | — | whitelisted |
3516 | map quest.exe | GET | 204 | 34.120.232.229:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=Error&errorCode=-11&errorType=nsisError&errorDetails=SendRequest+Error&platform=vicinio&anxv=2.0.1.8&anxd=2016-05-09&coid=0099c47eaf3848d2925ecacb813e3d0f&refPartner=^UX^mni000^S16724&refSub=&anxl=en-US&anxr=2018170101&refCobrand=UX&refCampaign=mni000&refTrack=S16724&refCountry= | unknown | — | — | whitelisted |
3516 | map quest.exe | GET | 200 | 2.16.168.117:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgTTSt7lL2v29yQRdfENzOFX9A%3D%3D | unknown | — | — | whitelisted |
3516 | map quest.exe | GET | 204 | 34.120.232.229:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=InstallerInvoked&platform=vicinio&anxv=2.0.1.8&anxd=2016-05-09&coid=0099c47eaf3848d2925ecacb813e3d0f&refPartner=^UX^mni000^S16724&refSub=&anxl=en-US&anxr=2017929322&refCobrand=UX&refCampaign=mni000&refTrack=S16724&refCountry= | unknown | — | — | whitelisted |
3516 | map quest.exe | GET | 204 | 34.120.232.229:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=InstallerFinished&tbUID=6598D413-639C-4C49-AC3B-CFD8498EAF66&tbVer=&platform=vicinio&anxv=2.0.1.8&anxd=2016-05-09&coid=0099c47eaf3848d2925ecacb813e3d0f&refPartner=^UX^mni000^S16724&refSub=&anxl=en-US&anxr=2061863691&refCobrand=UX&refCampaign=mni000&refTrack=S16724&refCountry= | unknown | — | — | whitelisted |
2592 | iexplore.exe | GET | 502 | 35.201.91.40:80 | http://www.mapsgalaxy.com/favicon.ico | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
3516 | map quest.exe | 34.120.232.229:80 | anx.mindspark.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
3516 | map quest.exe | 35.201.91.40:443 | dp.tb.ask.com | GOOGLE | US | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
3516 | map quest.exe | 208.89.74.31:80 | ctldl.windowsupdate.com | — | US | whitelisted |
3516 | map quest.exe | 23.209.209.135:80 | x1.c.lencr.org | PT. Telekomunikasi Selular | ID | whitelisted |
3516 | map quest.exe | 2.16.168.117:80 | r11.o.lencr.org | Akamai International B.V. | RU | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
752 | iexplore.exe | 35.201.91.40:80 | dp.tb.ask.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
anx.mindspark.com |
| whitelisted |
dp.tb.ask.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r11.o.lencr.org |
| whitelisted |
hp.myway.com |
| whitelisted |
www.mapsgalaxy.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |